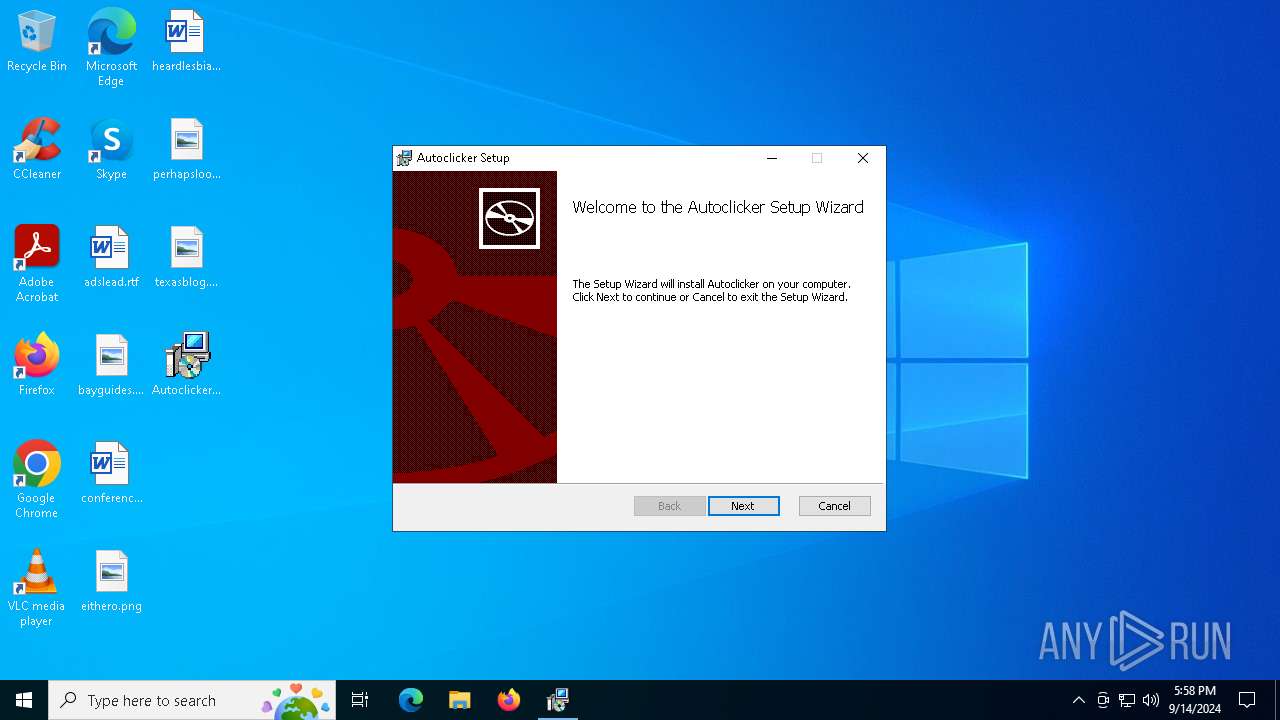
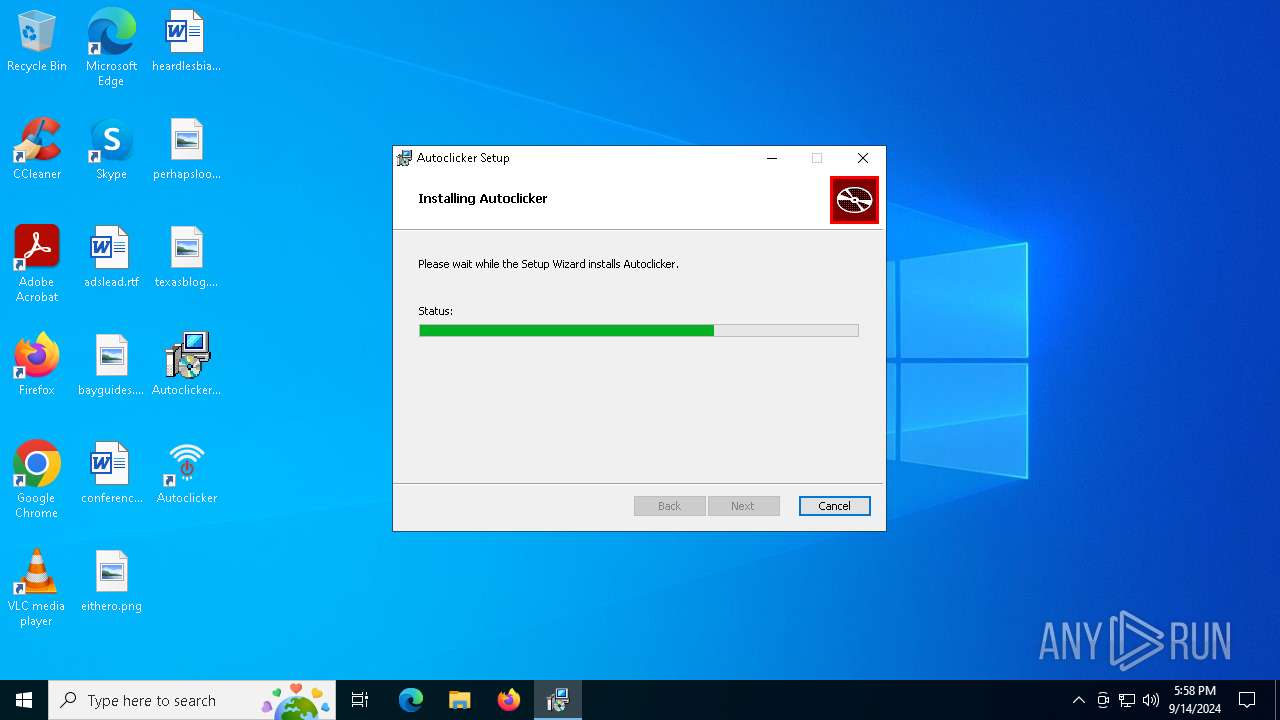
| File name: | Autoclicker2.0.0x86enUS.msi |
| Full analysis: | https://app.any.run/tasks/131a058f-017f-4f9a-a51e-d33f06872471 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | September 14, 2024, 17:58:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Autoclicker, Author: wearedevs, Keywords: Installer, Comments: This installer database contains the logic and data required to install Autoclicker., Template: Intel;0, Revision Number: {5624BB2D-F8EC-49E2-8510-30DAFC860021}, Create Time/Date: Fri Aug 9 12:44:24 2024, Last Saved Time/Date: Fri Aug 9 12:44:24 2024, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 3231CA7759E7949C7F028B35E1C5B804 |
| SHA1: | 77039469545996F7C766489FB3757CED80AEC102 |
| SHA256: | A11A6E5A4339A120F1C9E6B5C9C7C702DA254139DCB5E856809B7959086F011E |
| SSDEEP: | 98304:jPfnDtbPdunaUf+bsrCUjBHimCehDexMUw/HIUe/TtqxvWo47Lxyo+ILWhwwkHPx:7sI+8 |
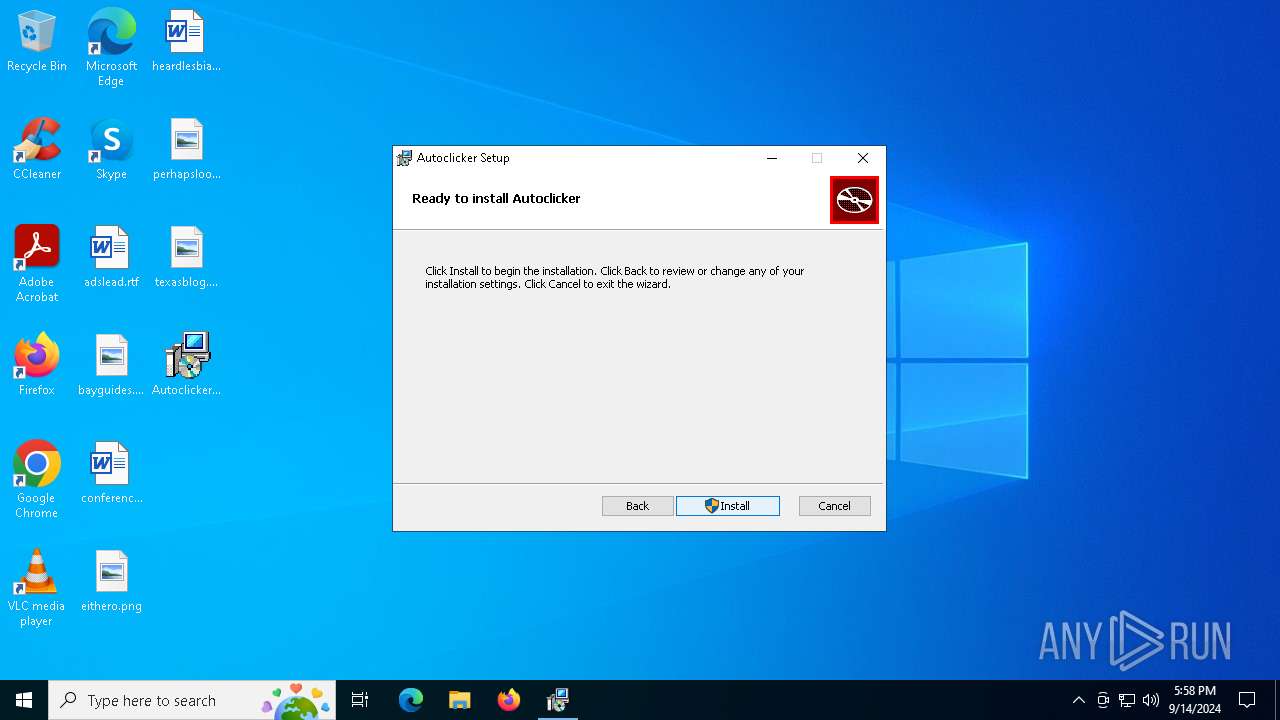
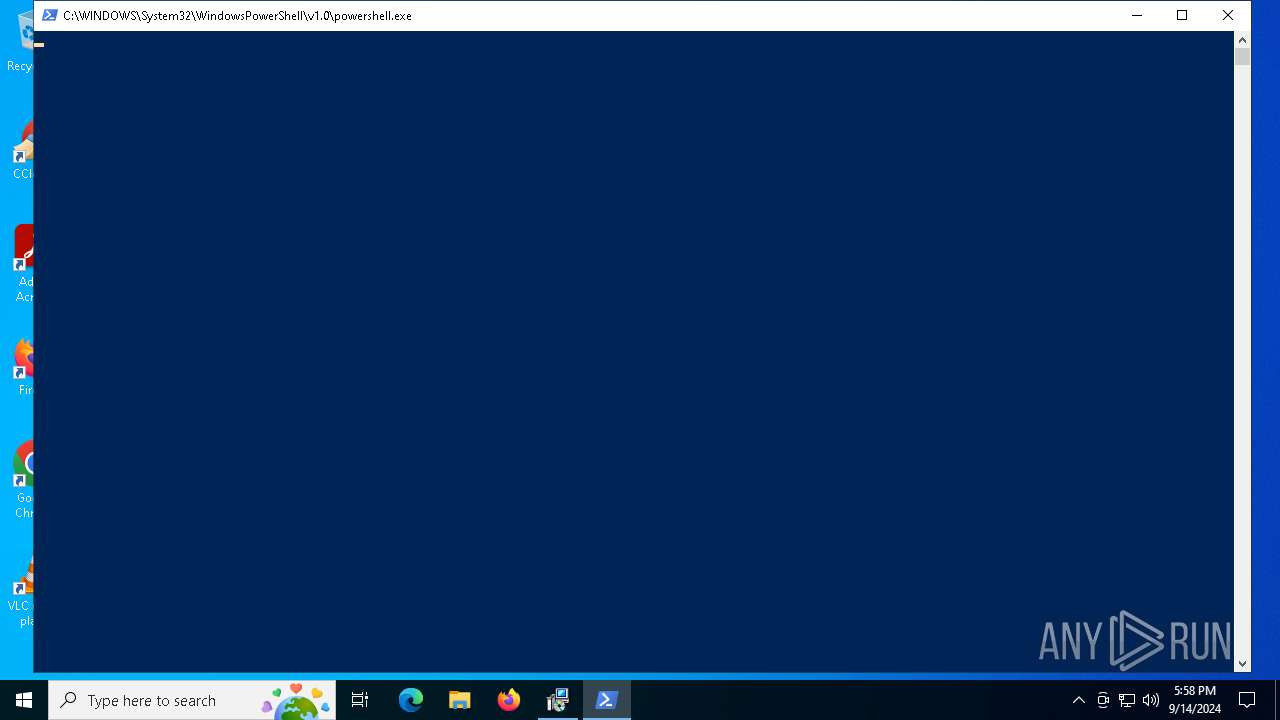
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3140)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 3584)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1116)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6744)
Request a resource from the Internet using PowerShell's cmdlet
- msiexec.exe (PID: 6744)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6744)
Downloads file from URI
- powershell.exe (PID: 3140)
Powershell scripting: start process
- msiexec.exe (PID: 6744)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6744)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 3140)
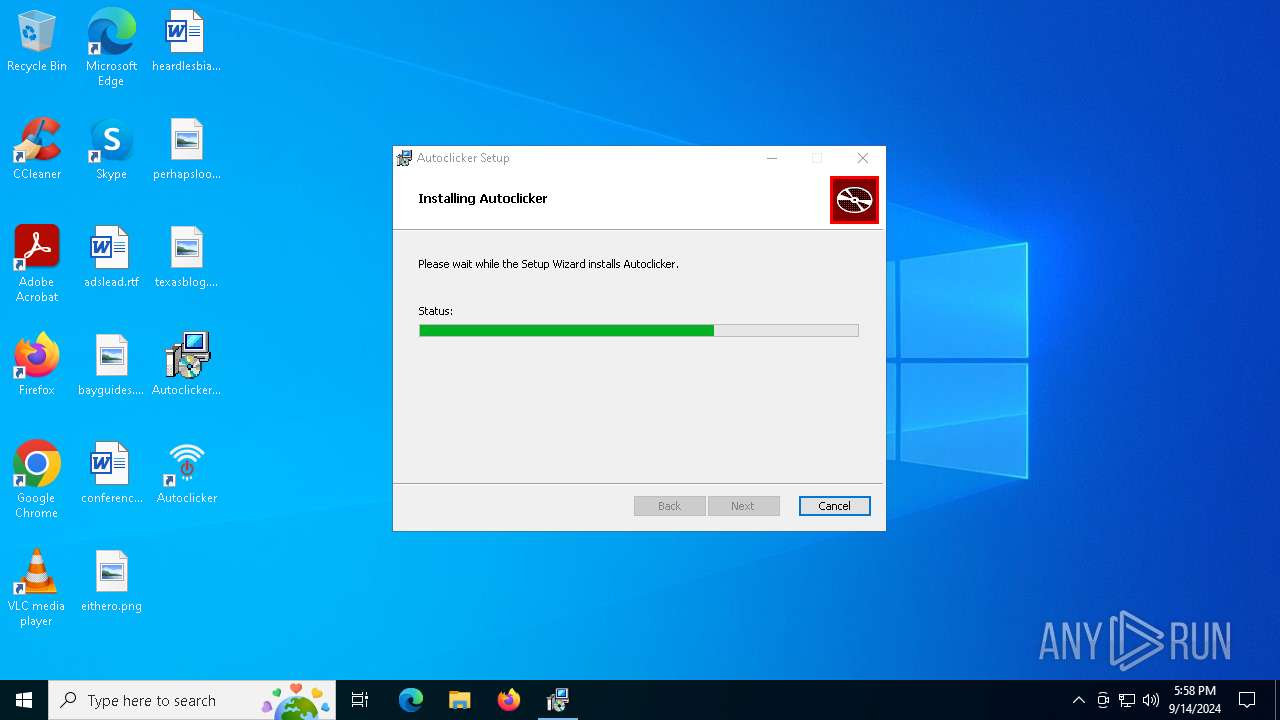
Executable content was dropped or overwritten
- powershell.exe (PID: 3140)
- MicrosoftEdgeWebview2Setup.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 3584)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 3584)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 3584)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3812)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6560)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 232)
- MicrosoftEdgeUpdate.exe (PID: 6692)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 3584)
Potential Corporate Privacy Violation
- svchost.exe (PID: 6832)
INFO
Reads the computer name
- msiexec.exe (PID: 6744)
- msiexec.exe (PID: 5160)
- MicrosoftEdgeUpdate.exe (PID: 3584)
- MicrosoftEdgeUpdate.exe (PID: 6692)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3812)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6560)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 232)
- MicrosoftEdgeUpdate.exe (PID: 6336)
- MicrosoftEdgeUpdate.exe (PID: 4160)
- MicrosoftEdgeUpdate.exe (PID: 6264)
Checks supported languages
- msiexec.exe (PID: 6744)
- msiexec.exe (PID: 5160)
- MicrosoftEdgeWebview2Setup.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 3584)
- MicrosoftEdgeUpdate.exe (PID: 6692)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3812)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 232)
- MicrosoftEdgeUpdate.exe (PID: 6336)
- MicrosoftEdgeUpdate.exe (PID: 4160)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6560)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4192)
- msiexec.exe (PID: 6744)
Creates a software uninstall entry
- msiexec.exe (PID: 6744)
Disables trace logs
- powershell.exe (PID: 3140)
Checks proxy server information
- powershell.exe (PID: 3140)
- MicrosoftEdgeUpdate.exe (PID: 6336)
- MicrosoftEdgeUpdate.exe (PID: 6264)
The process uses the downloaded file
- powershell.exe (PID: 3140)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 6148)
Create files in a temporary directory
- MicrosoftEdgeUpdate.exe (PID: 3584)
- MicrosoftEdgeWebview2Setup.exe (PID: 6148)
- svchost.exe (PID: 6832)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 3584)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 6336)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 3584)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 6336)
- MicrosoftEdgeUpdate.exe (PID: 6264)
Reads the machine GUID from the registry
- MicrosoftEdgeUpdate.exe (PID: 6336)
- MicrosoftEdgeUpdate.exe (PID: 6264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Autoclicker |
| Author: | wearedevs |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Autoclicker. |
| Template: | Intel;0 |
| RevisionNumber: | {5624BB2D-F8EC-49E2-8510-30DAFC860021} |
| CreateDate: | 2024:08:09 12:44:24 |
| ModifyDate: | 2024:08:09 12:44:24 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
143
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.19\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.19\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.19 Modules
| |||||||||||||||
| 1116 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3584 | C:\Users\admin\AppData\Local\Temp\EU5806.tmp\MicrosoftEdgeUpdate.exe /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Users\admin\AppData\Local\Temp\EU5806.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.19 Modules
| |||||||||||||||
| 3812 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.19\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.19\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.19 Modules
| |||||||||||||||
| 4160 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{0A700F4E-8A96-4CBC-8F2D-BC00A65400A5}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.19 Modules
| |||||||||||||||
| 4192 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\Autoclicker2.0.0x86enUS.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5160 | C:\Windows\syswow64\MsiExec.exe -Embedding E462377BD2DCE61968E2A5C40EE955B7 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 471
Read events
17 226
Write events
3 202
Delete events
43
Modification events
| (PID) Process: | (6832) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\BITS |
| Operation: | write | Name: | PerfMMFileName |
Value: Global\MMF_BITSfed3ed5b-0d0d-46fc-86b8-aa5cbb0d33b8 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000F37CA7ADCF06DB01581A000094190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000F37CA7ADCF06DB01581A000094190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000029E4E7ADCF06DB01581A000094190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000029E4E7ADCF06DB01581A000094190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000009447EAADCF06DB01581A000094190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000C80EEFADCF06DB01581A000094190000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000056E863AECF06DB01581A000094190000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6744) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000005B9F68AECF06DB01581A0000F40C0000E8030000010000000000000000000000FE13A45B8529834ABC4E3DBDD936AA4200000000000000000000000000000000 | |||
Executable files
206
Suspicious files
15
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6744 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6744 | msiexec.exe | C:\Windows\Installer\130533.msi | executable | |
MD5:3231CA7759E7949C7F028B35E1C5B804 | SHA256:A11A6E5A4339A120F1C9E6B5C9C7C702DA254139DCB5E856809B7959086F011E | |||
| 6832 | svchost.exe | C:\ProgramData\Microsoft\Network\Downloader\qmgr.db | edb | |
MD5:104E1C582A0CFF92D1C0C80315B87EC6 | SHA256:4136D336A485B0111180E022A0C842F5FC719EE76C5406BAC4773249DABCA56D | |||
| 6744 | msiexec.exe | C:\Program Files (x86)\Autoclicker\Autoclicker.exe | executable | |
MD5:322C55FA9C047E94D7AF4EF278B51C83 | SHA256:34CA722A2DE227A2F5B93F719927150B1CBC8E10CFC905DAE752591C425CBDF1 | |||
| 6744 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Autoclicker\Autoclicker.lnk | binary | |
MD5:79856954EA0E5FA50258B0115F19FC32 | SHA256:124ECC4A7FE0A4CD703641806B4E6CD73509F77263B7A7B6F47419AD5B206730 | |||
| 6744 | msiexec.exe | C:\Windows\Temp\~DFA4769D8E176324A1.TMP | binary | |
MD5:28F92A7DB666E612233ABD0A0C69561B | SHA256:23092B63438BD386A58BE1A16EAD69E916A17DF50CDDA1F0E1878944636C4BF6 | |||
| 6744 | msiexec.exe | C:\Windows\Installer\{967EAFBA-179E-4AEF-A956-879C88C6CD6F}\ProductIcon | image | |
MD5:1FB7536E404FC55DBF628B206BF2343E | SHA256:4D7863FE515D420AFE6D353EAD3D72D6B7D1EFC632837689C76E8ECD354DC94D | |||
| 6744 | msiexec.exe | C:\Windows\Temp\~DFAA433BF797646287.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 6744 | msiexec.exe | C:\Program Files (x86)\Autoclicker\resources\db.json | binary | |
MD5:DEEF4170609ED9D916C542B85781B4C4 | SHA256:5A0FB5F4E5DCF5DEF4E6FEA7205F1DDDBE9B6B2417F51F931F4FAFFC05599DF1 | |||
| 6744 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Autoclicker\Autoclicker.lnk~RF130a06.TMP | binary | |
MD5:79856954EA0E5FA50258B0115F19FC32 | SHA256:124ECC4A7FE0A4CD703641806B4E6CD73509F77263B7A7B6F47419AD5B206730 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
23
DNS requests
9
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7128 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7072 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 301 | 184.30.21.171:443 | https://go.microsoft.com/fwlink/p/?LinkId=2124703 | unknown | — | — | unknown |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6832 | svchost.exe | HEAD | 200 | 23.48.23.42:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3c0de2bf-65bf-49d5-acb1-379ba8215c60?P1=1726941541&P2=404&P3=2&P4=jsAV3aF%2fSck%2fSSxeMGvjF1fNg71wH3VxQjZQxr5Ollzn34Wra%2fgwP6QTbob%2b3fwfQLA00CWYHWpjVq42k%2fFBSQ%3d%3d | unknown | — | — | whitelisted |
6832 | svchost.exe | GET | — | 23.48.23.42:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3c0de2bf-65bf-49d5-acb1-379ba8215c60?P1=1726941541&P2=404&P3=2&P4=jsAV3aF%2fSck%2fSSxeMGvjF1fNg71wH3VxQjZQxr5Ollzn34Wra%2fgwP6QTbob%2b3fwfQLA00CWYHWpjVq42k%2fFBSQ%3d%3d | unknown | — | — | whitelisted |
— | — | POST | 200 | 13.95.26.4:443 | https://msedge.api.cdp.microsoft.com/api/v1.1/internal/contents/Browser/namespaces/Default/names/msedgewebview-stable-win-x64/versions/128.0.2739.79/files?action=GenerateDownloadInfo&foregroundPriority=true | unknown | text | 6.72 Kb | unknown |
— | — | POST | 200 | 13.95.26.4:443 | https://msedge.api.cdp.microsoft.com/api/v2/contents/Browser/namespaces/Default/names?action=batchupdates | unknown | text | 103 b | unknown |
— | — | GET | 200 | 152.199.21.175:443 | https://msedge.sf.dl.delivery.mp.microsoft.com/filestreamingservice/files/657da03c-2d6c-4d00-893f-d6c129225760/MicrosoftEdgeWebview2Setup.exe | unknown | executable | 1.56 Mb | unknown |
— | — | GET | 200 | 52.123.243.93:443 | https://config.edge.skype.com/config/v1/EdgeUpdate/1.3.195.19?clientId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&appChannel_edgeupdate=6&appConsentState_edgeupdate=0&appDayOfInstall_edgeupdate=0&appInactivityBadgeApplied_edgeupdate=0&appInactivityBadgeCleared_edgeupdate=0&appInactivityBadgeDuration_edgeupdate=0&appInstallTimeDiffSec_edgeupdate=0&appIsPinnedSystem_edgeupdate=false&appLastLaunchCount_edgeupdate=0&appLastLaunchTime_edgeupdate=0&appLastLaunchTimeJson_edgeupdate=0&appLastLaunchTimeDaysAgo_edgeupdate=0&appVersion_edgeupdate=1.3.195.19&appUpdateCheckIsUpdateDisabled_edgeupdate=false&appUpdatesAllowedForMeteredNetworks_edgeupdate=false&hwDiskType=2&hwHasSsse3=true&hwLogicalCpus=4&hwPhysmemory=4&isCTADevice=false&isMsftDomainJoined=false&oemProductManufacturer=DELL&oemProductName=DELL&osArch=x64&osIsDefaultNetworkConnectionMetered=false&osIsInLockdownMode=false&osIsWIP=false&osPlatform=win&osProductType=48&osVersion=10.0.19045.4046&requestCheckPeriodSec=-1&requestDomainJoined=false&requestInstallSource=otherinstallcmd&requestIsMachine=false&requestOmahaShellVersion=1.3.195.19&requestOmahaVersion=1.3.195.19 | unknown | binary | 234 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7128 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7072 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7128 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7072 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
msedge.api.cdp.microsoft.com |
| whitelisted |
msedge.f.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6832 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |