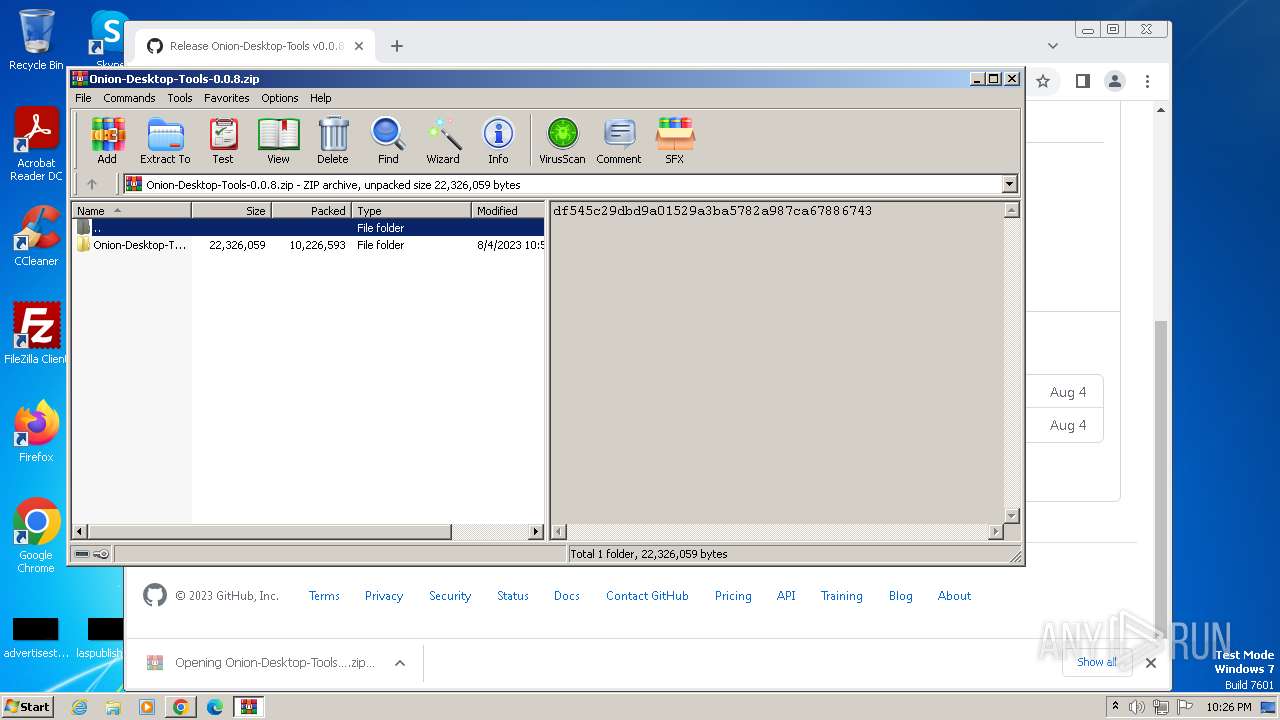
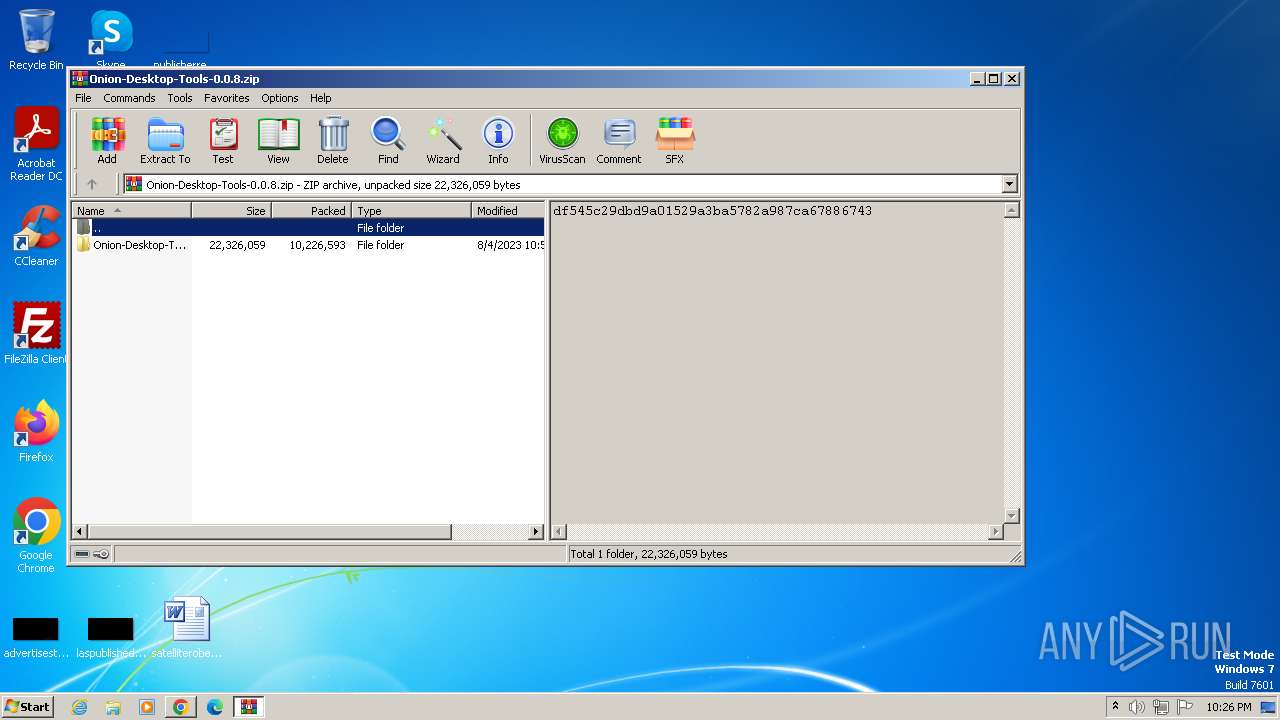
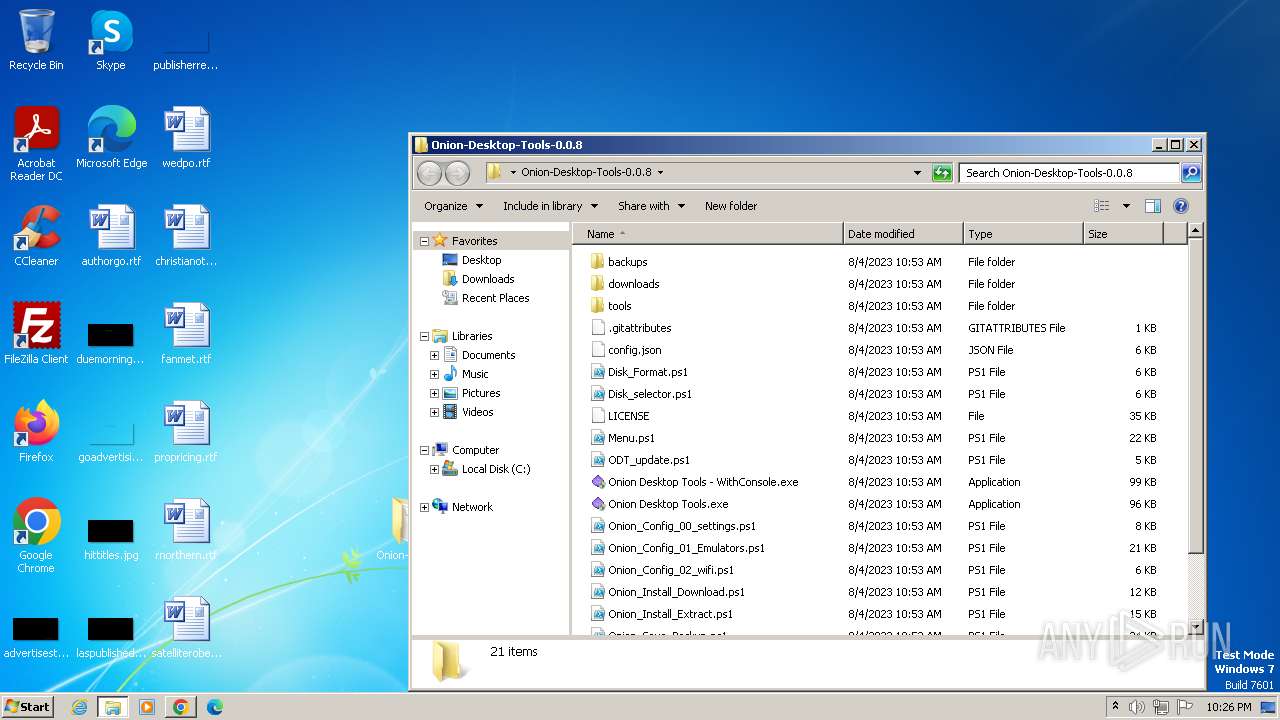
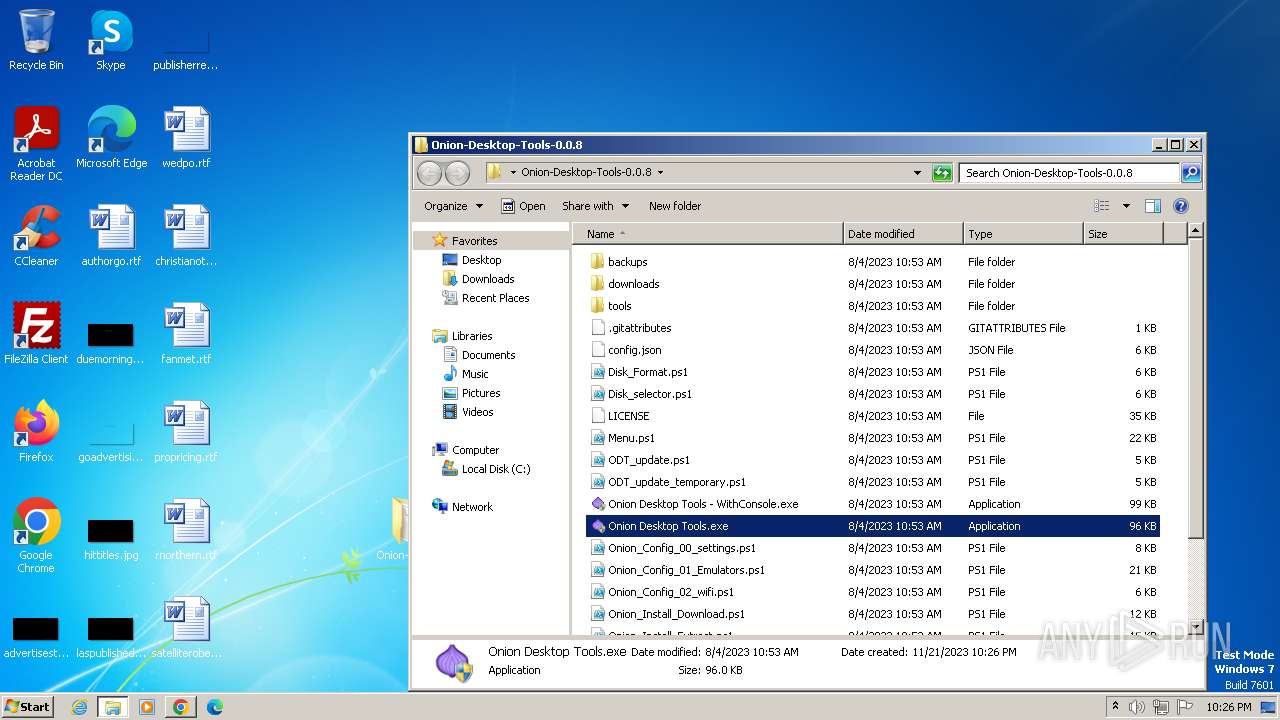
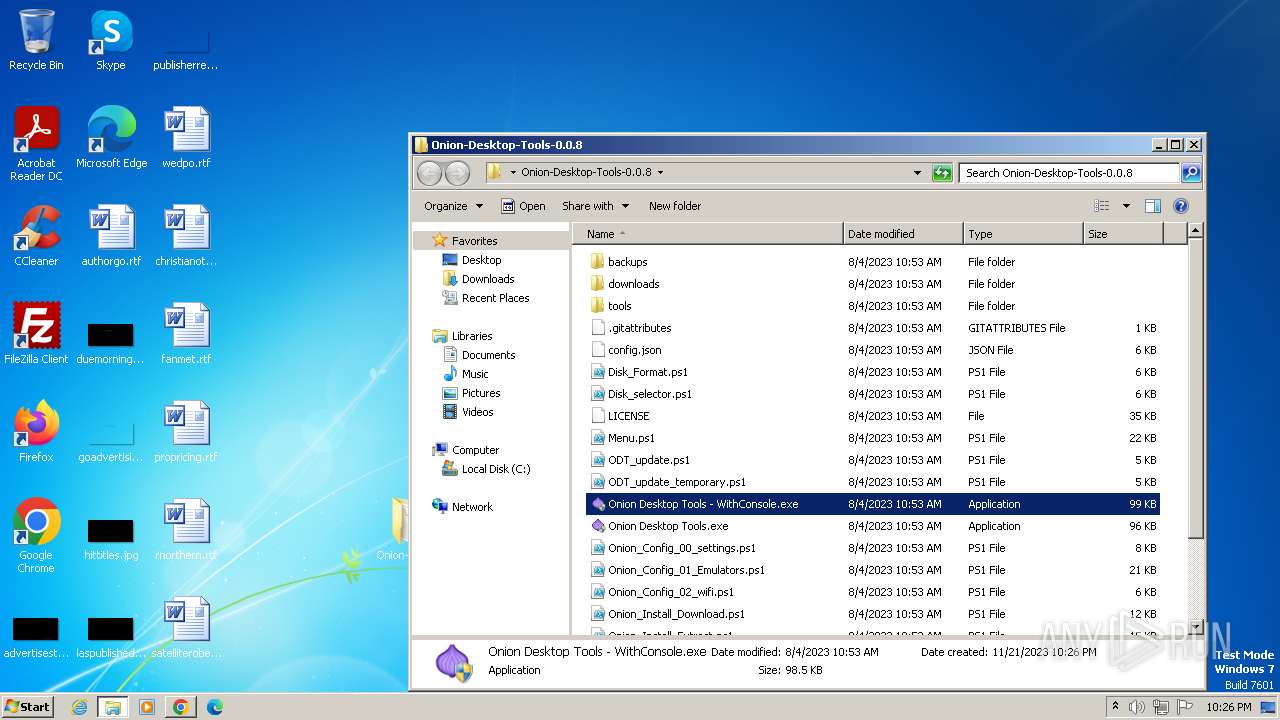
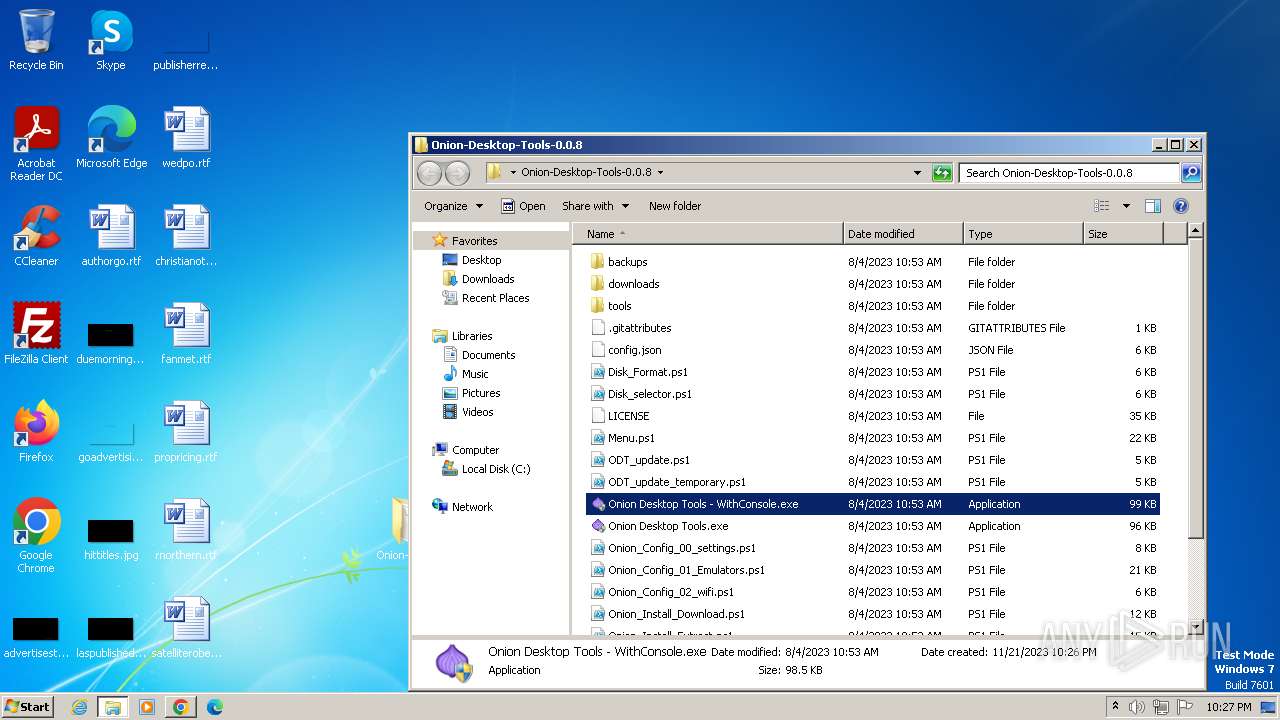
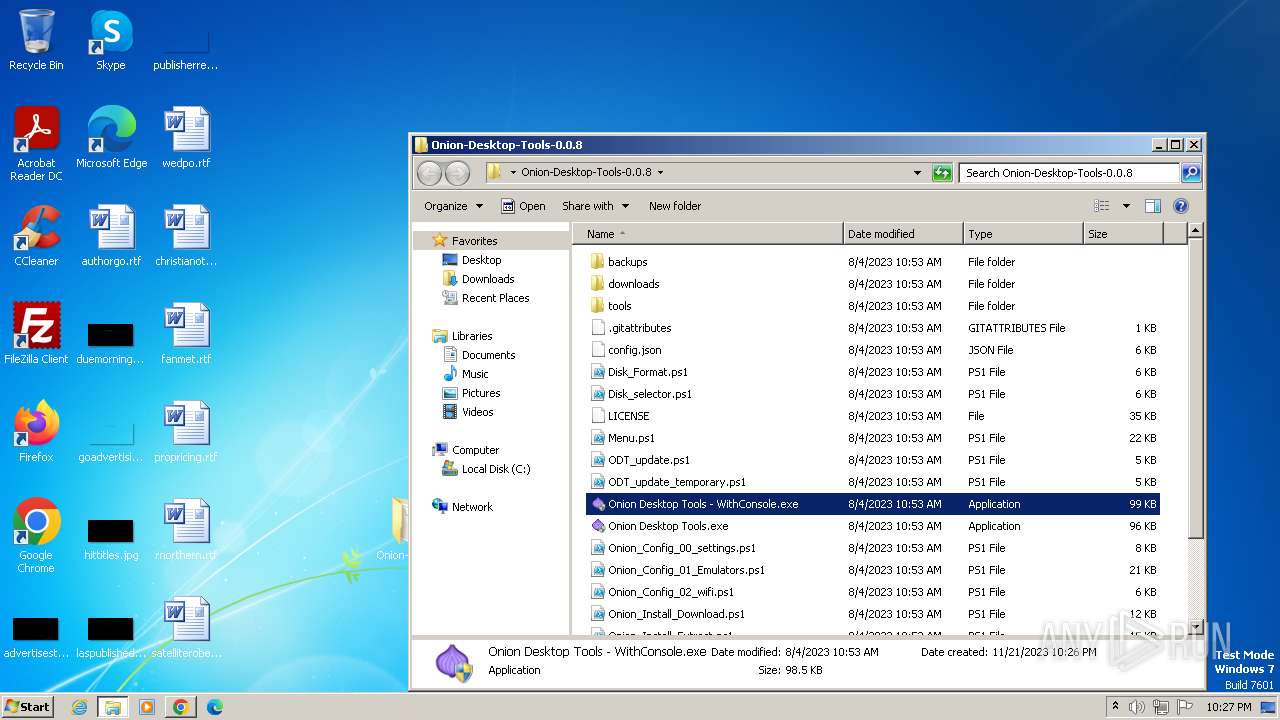
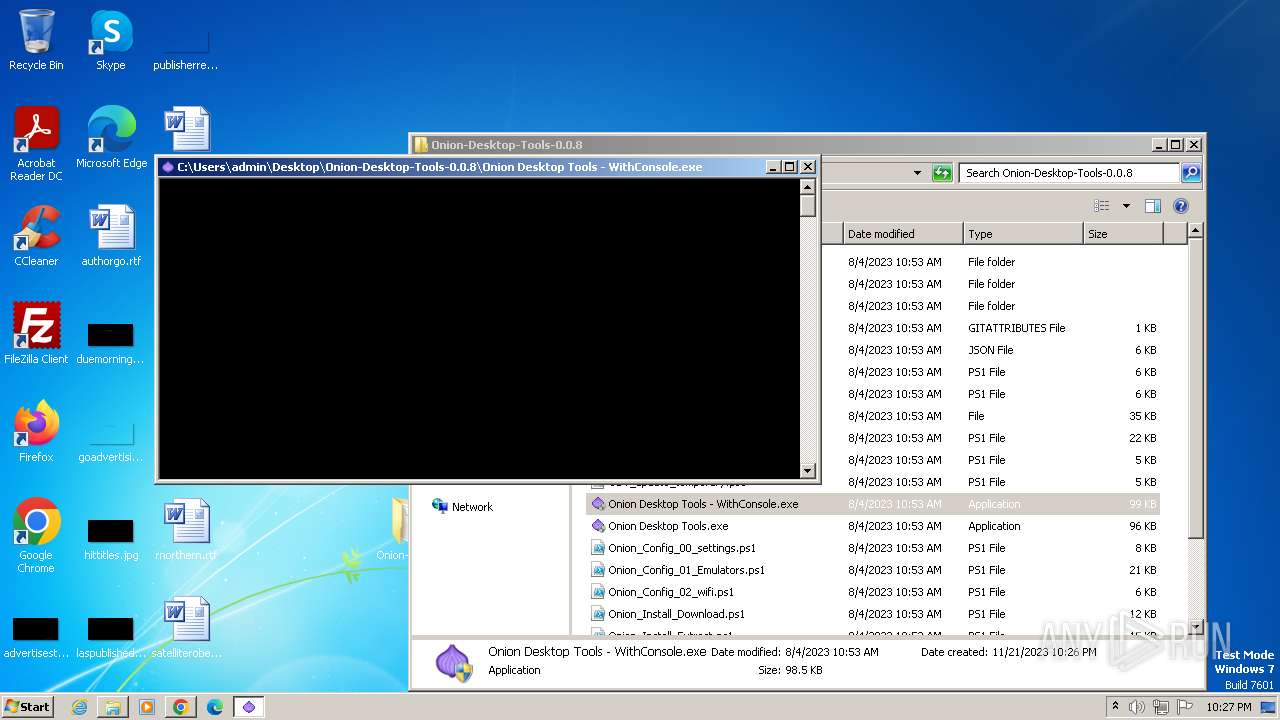
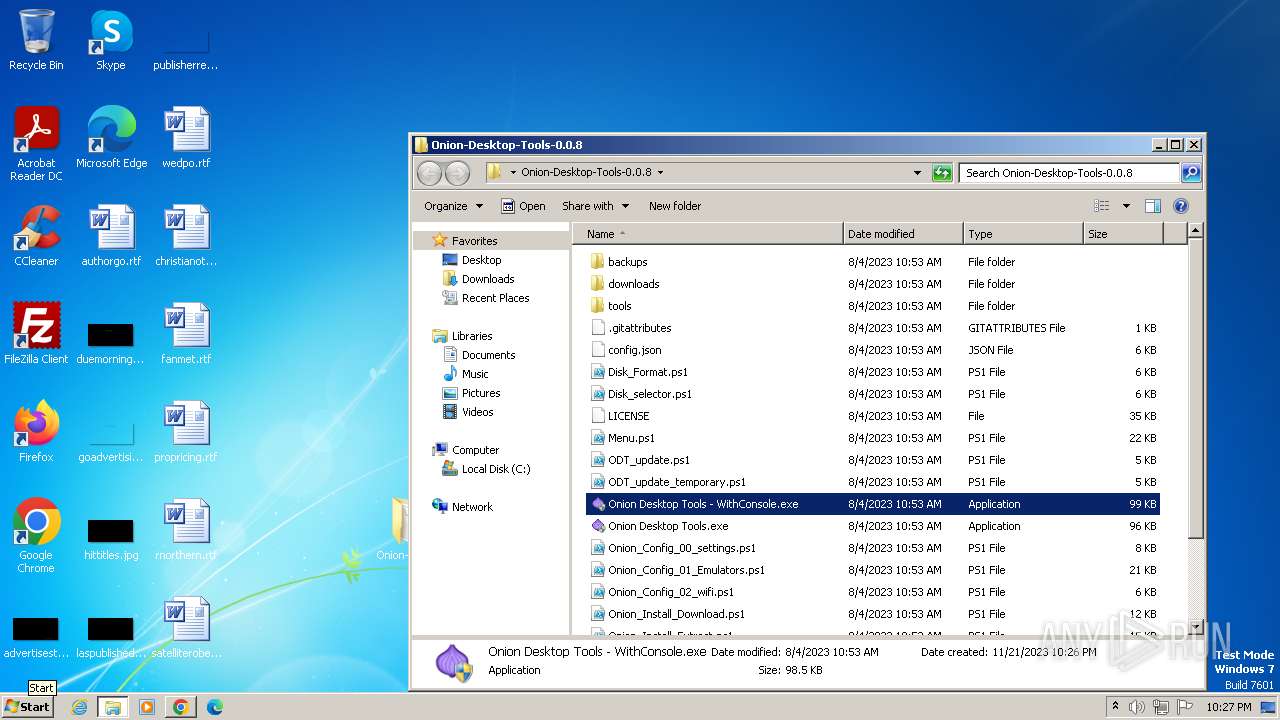
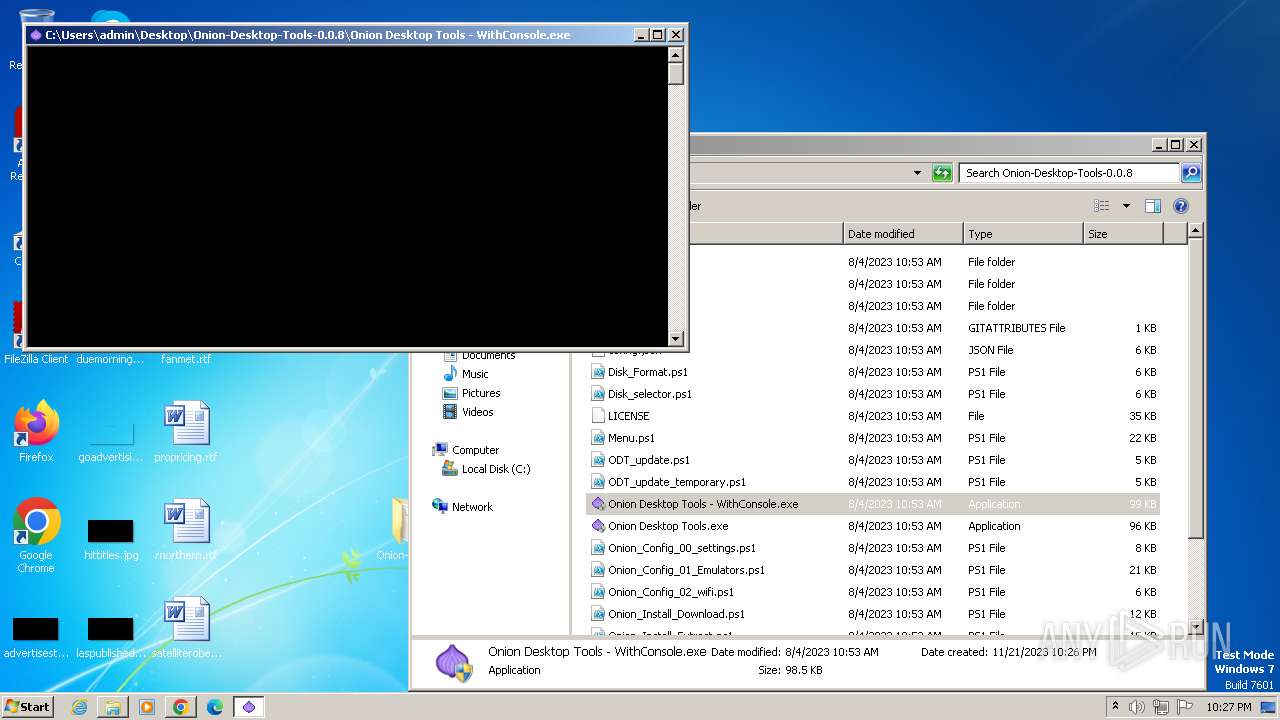
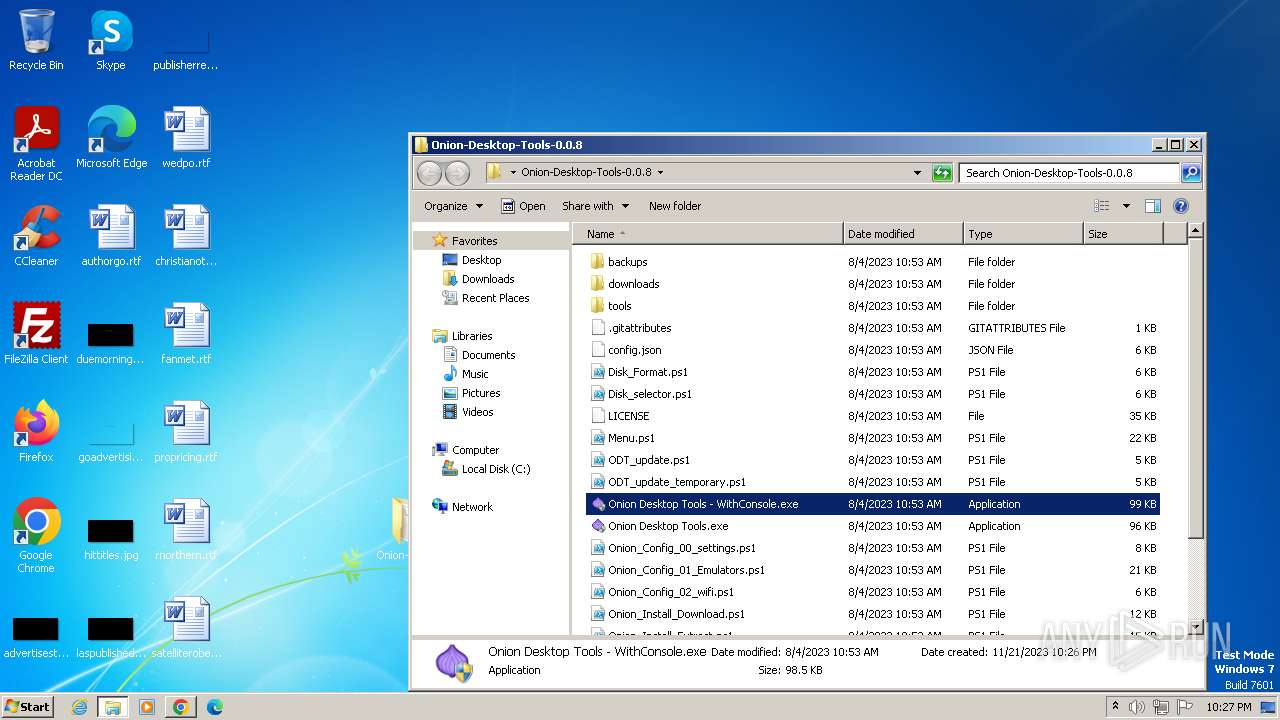
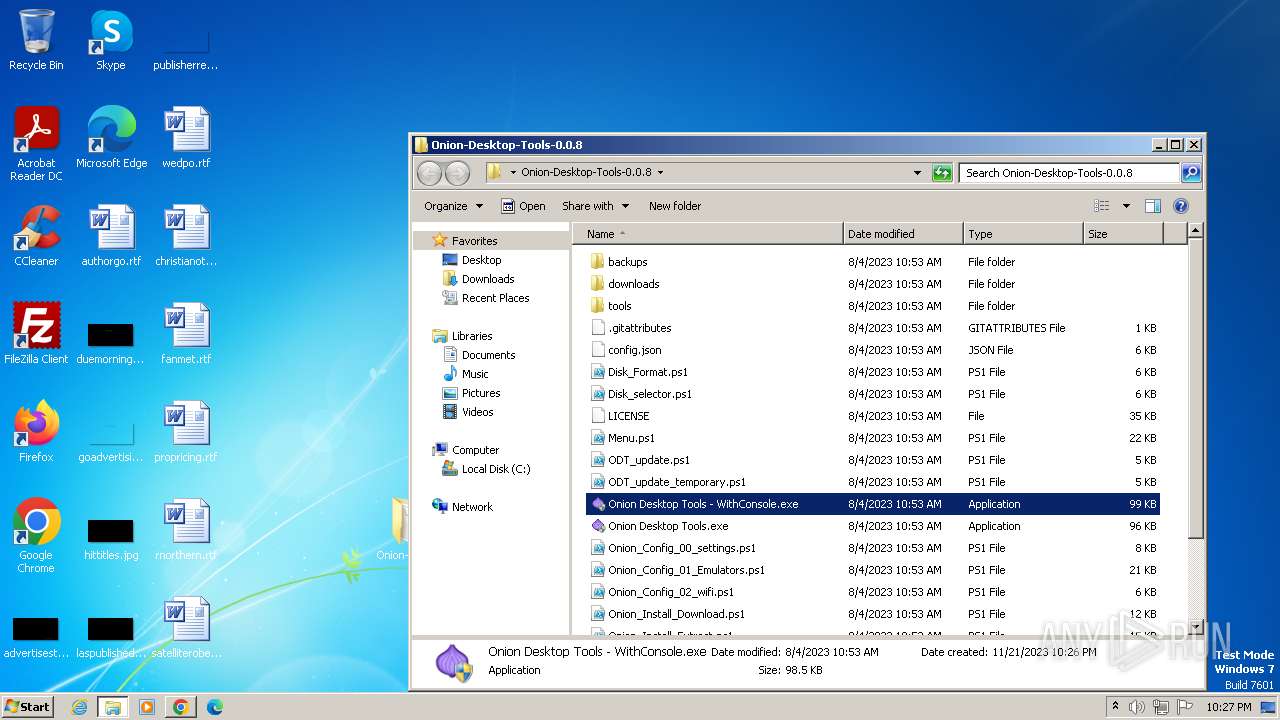
| File name: | Onion Desktop Tools.exe |
| Full analysis: | https://app.any.run/tasks/0144db13-0045-4f74-8b2f-a209da06ab28 |
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2023, 22:24:39 |
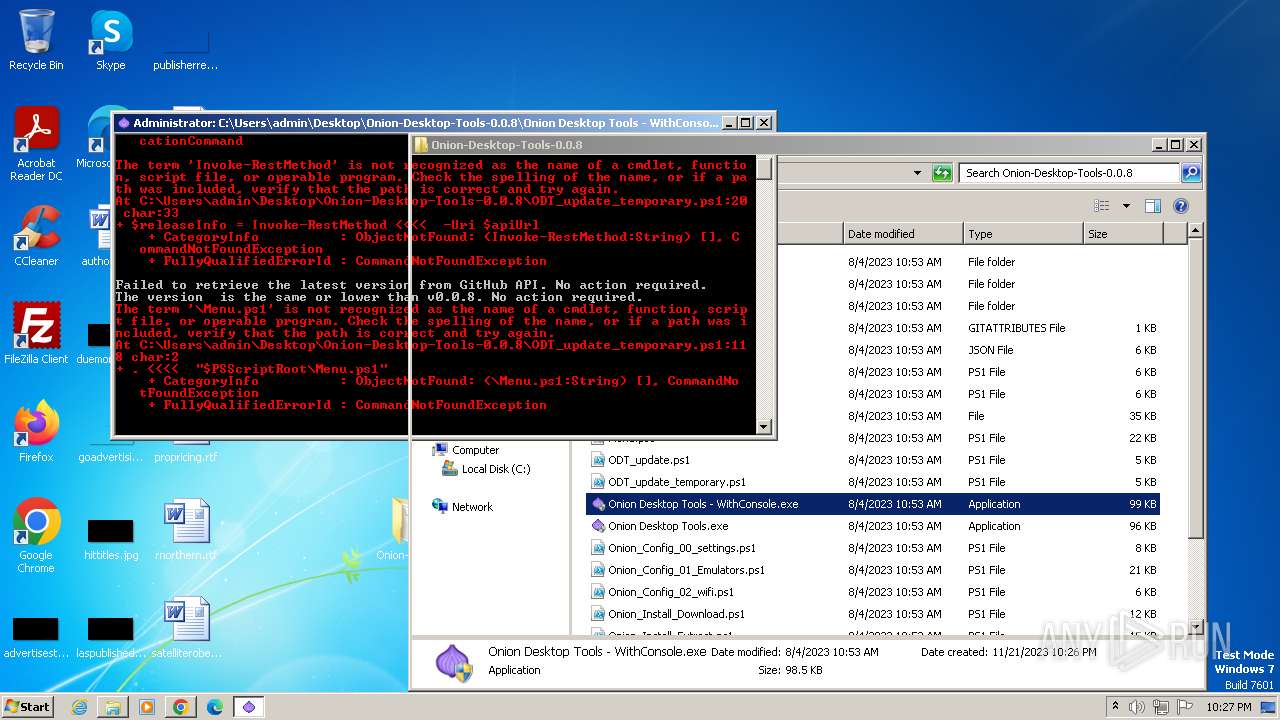
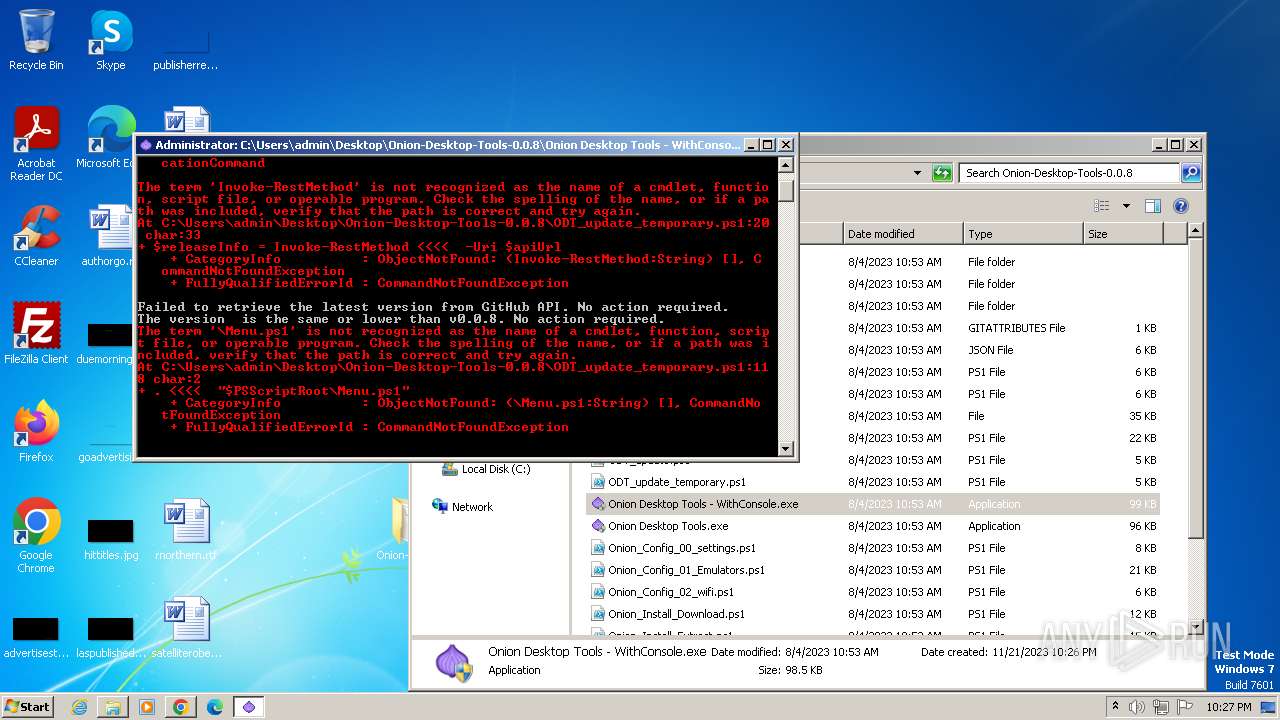
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A4708BD0740DCB46A339EA893995544A |
| SHA1: | 4B92177FD30EF93403C1B2E9BB69755ECC0A7301 |
| SHA256: | A1192B8D70FC90CABC8BB9F8C2BD52B3558B16C3D84C822E5E9EEBF7A0F5A43B |
| SSDEEP: | 3072:EyD/R2Sindoy8scpRTeJmyxCsVCgTivioNbMb2LRh:5SigTizNba2LRh |
MALICIOUS
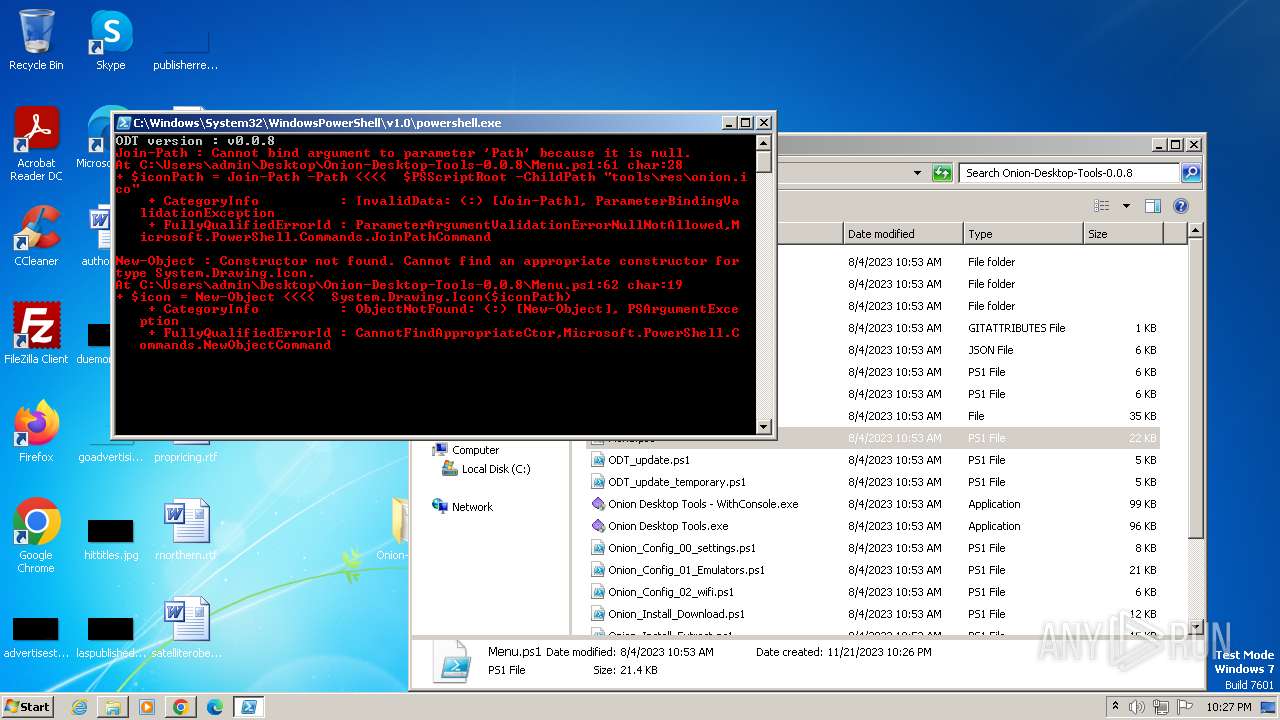
Bypass execution policy to execute commands
- powershell.exe (PID: 3408)
- powershell.exe (PID: 296)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 1160)
- powershell.exe (PID: 756)
- powershell.exe (PID: 1004)
- powershell.exe (PID: 2464)
- powershell.exe (PID: 2540)
- powershell.exe (PID: 3084)
- powershell.exe (PID: 3580)
- powershell.exe (PID: 1824)
- powershell.exe (PID: 3800)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3572)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 860)
- cmd.exe (PID: 3600)
- cmd.exe (PID: 2496)
- cmd.exe (PID: 1064)
- cmd.exe (PID: 1736)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 3056)
- cmd.exe (PID: 276)
SUSPICIOUS
Reads the Internet Settings
- Onion Desktop Tools.exe (PID: 3228)
- Onion Desktop Tools.exe (PID: 4004)
- Onion Desktop Tools.exe (PID: 2108)
- Onion Desktop Tools.exe (PID: 3460)
- powershell.exe (PID: 1876)
Starts CMD.EXE for commands execution
- Onion Desktop Tools.exe (PID: 3228)
- Onion Desktop Tools.exe (PID: 4004)
- Onion Desktop Tools.exe (PID: 2108)
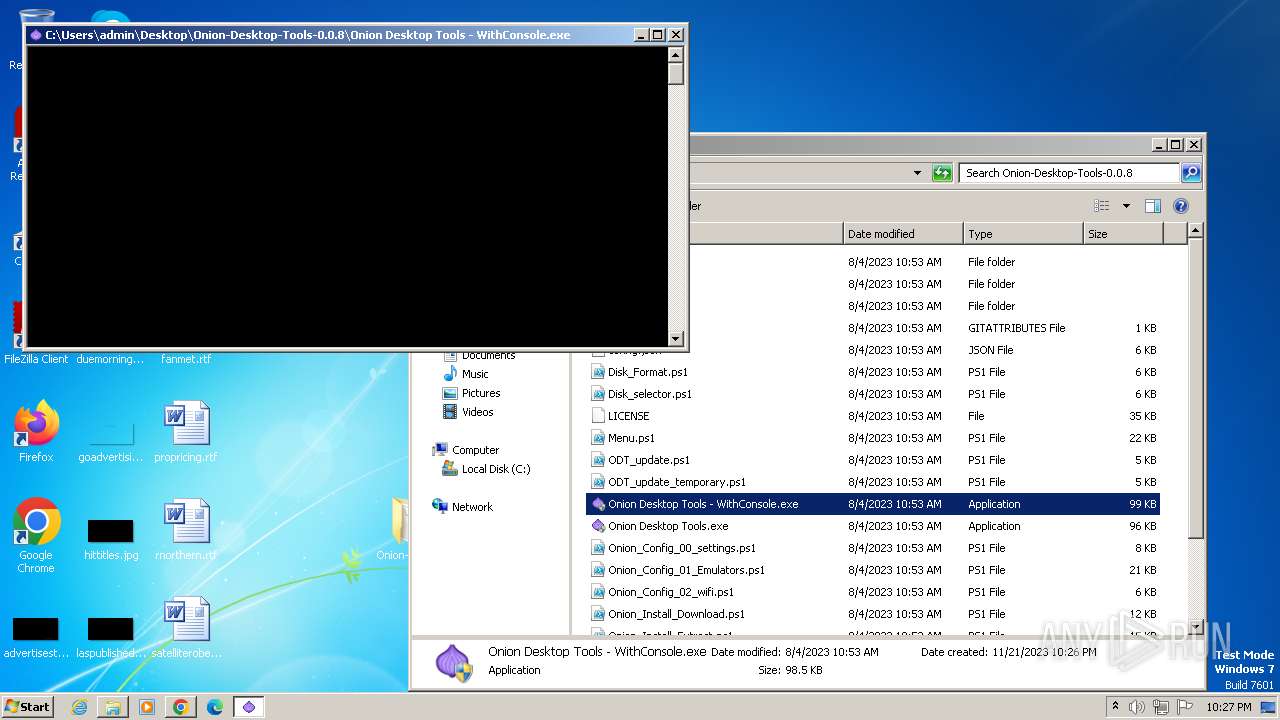
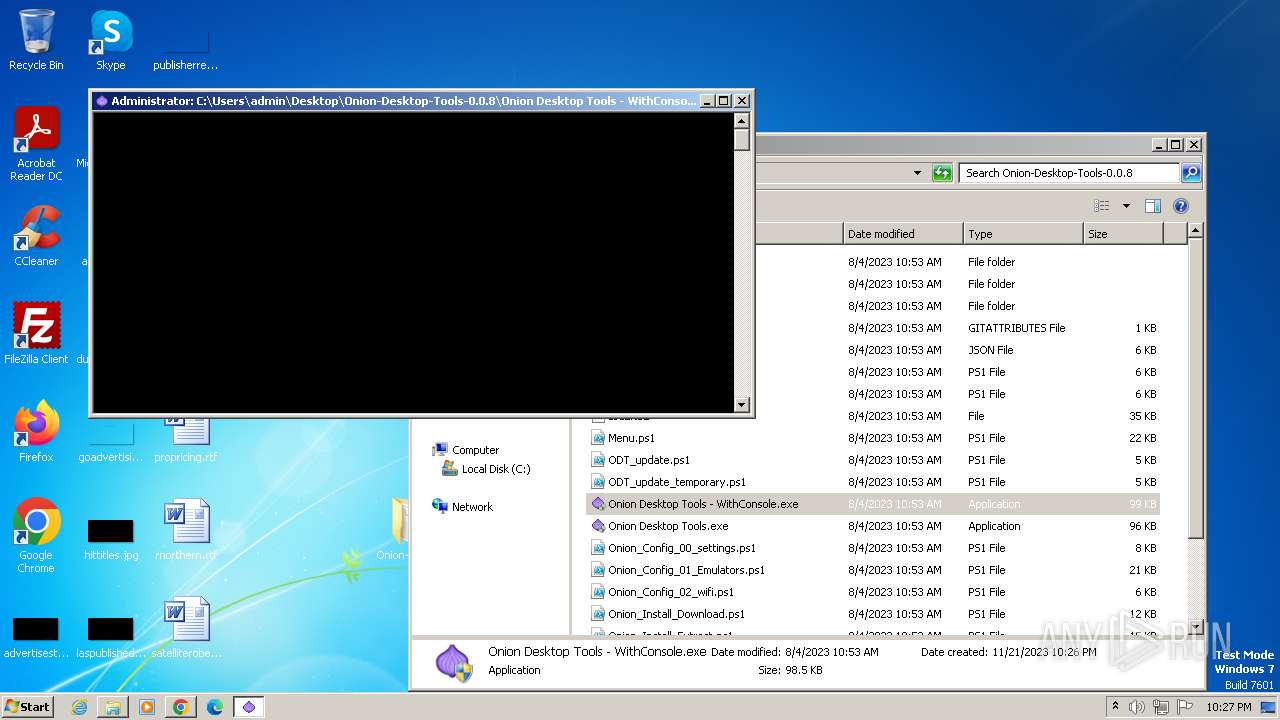
- Onion Desktop Tools - WithConsole.exe (PID: 1664)
- Onion Desktop Tools - WithConsole.exe (PID: 4068)
- Onion Desktop Tools - WithConsole.exe (PID: 2948)
- Onion Desktop Tools - WithConsole.exe (PID: 2732)
- Onion Desktop Tools - WithConsole.exe (PID: 844)
- Onion Desktop Tools - WithConsole.exe (PID: 3368)
- Onion Desktop Tools.exe (PID: 3460)
- Onion Desktop Tools - WithConsole.exe (PID: 3804)
- Onion Desktop Tools - WithConsole.exe (PID: 3372)
Executing commands from a ".bat" file
- Onion Desktop Tools.exe (PID: 3228)
- Onion Desktop Tools.exe (PID: 4004)
- Onion Desktop Tools.exe (PID: 2108)
- Onion Desktop Tools - WithConsole.exe (PID: 1664)
- Onion Desktop Tools - WithConsole.exe (PID: 4068)
- Onion Desktop Tools - WithConsole.exe (PID: 2948)
- Onion Desktop Tools - WithConsole.exe (PID: 2732)
- Onion Desktop Tools - WithConsole.exe (PID: 844)
- Onion Desktop Tools - WithConsole.exe (PID: 3368)
- Onion Desktop Tools.exe (PID: 3460)
- Onion Desktop Tools - WithConsole.exe (PID: 3372)
- Onion Desktop Tools - WithConsole.exe (PID: 3804)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3572)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 3600)
- cmd.exe (PID: 860)
- cmd.exe (PID: 2496)
- cmd.exe (PID: 1064)
- cmd.exe (PID: 1736)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 3056)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 276)
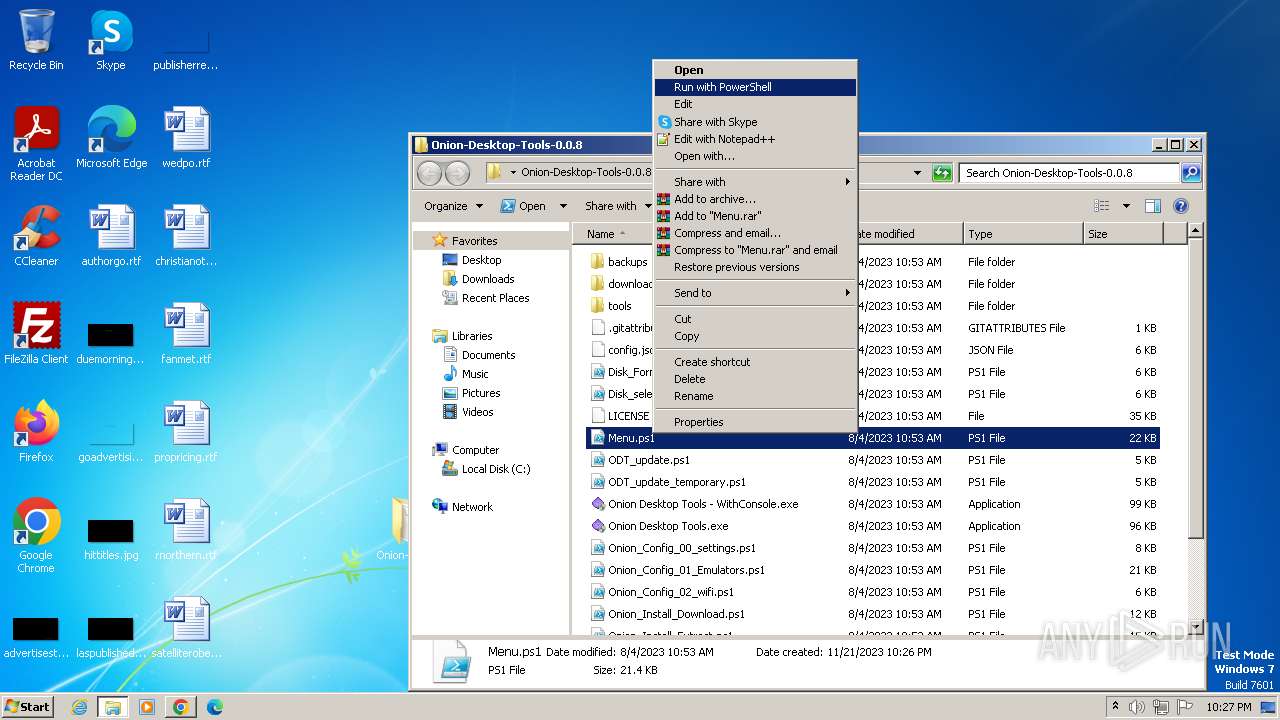
The process executes Powershell scripts
- cmd.exe (PID: 3572)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 860)
- cmd.exe (PID: 3600)
- cmd.exe (PID: 2496)
- cmd.exe (PID: 1064)
- cmd.exe (PID: 1736)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 3056)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 276)
Powershell version downgrade attack
- powershell.exe (PID: 3408)
- powershell.exe (PID: 296)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 1160)
- powershell.exe (PID: 756)
- powershell.exe (PID: 2464)
- powershell.exe (PID: 1004)
- powershell.exe (PID: 2540)
- powershell.exe (PID: 3084)
- powershell.exe (PID: 3580)
- powershell.exe (PID: 1824)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 1876)
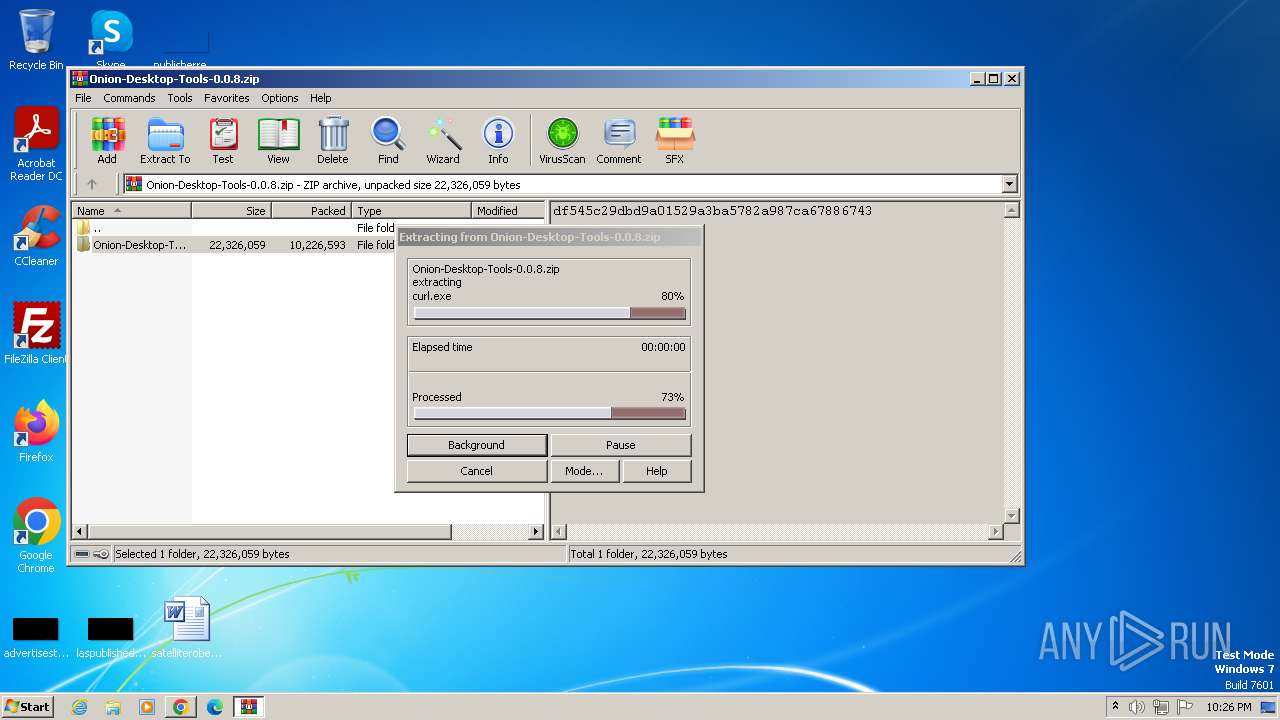
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 2652)
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 2652)
INFO
Checks supported languages
- Onion Desktop Tools.exe (PID: 3228)
- wmpnscfg.exe (PID: 556)
- Onion Desktop Tools.exe (PID: 4004)
- Onion Desktop Tools.exe (PID: 2108)
- Onion Desktop Tools - WithConsole.exe (PID: 1664)
- Onion Desktop Tools - WithConsole.exe (PID: 4068)
- Onion Desktop Tools - WithConsole.exe (PID: 2948)
- Onion Desktop Tools - WithConsole.exe (PID: 2732)
- Onion Desktop Tools - WithConsole.exe (PID: 844)
- Onion Desktop Tools.exe (PID: 3460)
- Onion Desktop Tools - WithConsole.exe (PID: 3368)
- Onion Desktop Tools - WithConsole.exe (PID: 3804)
- Onion Desktop Tools - WithConsole.exe (PID: 3372)
Reads the computer name
- Onion Desktop Tools.exe (PID: 3228)
- wmpnscfg.exe (PID: 556)
- Onion Desktop Tools.exe (PID: 4004)
- Onion Desktop Tools.exe (PID: 2108)
- Onion Desktop Tools.exe (PID: 3460)
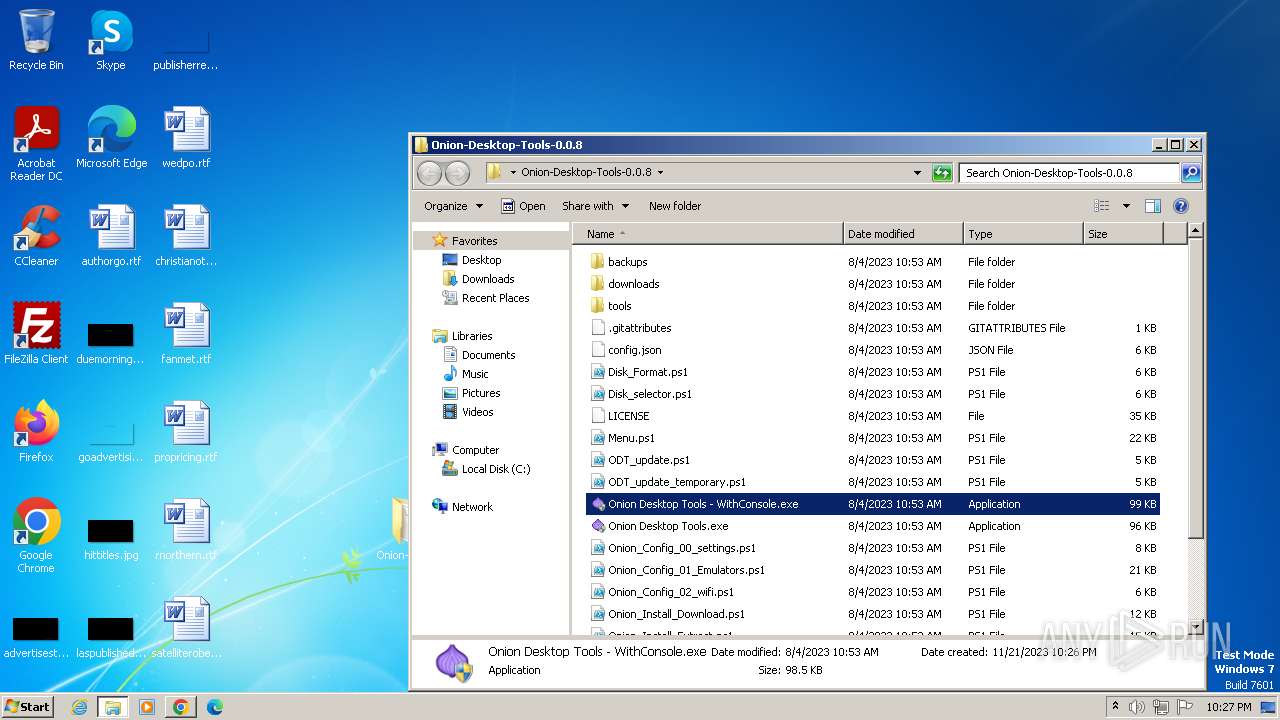
Manual execution by a user
- chrome.exe (PID: 3688)
- wmpnscfg.exe (PID: 556)
- Onion Desktop Tools.exe (PID: 2932)
- Onion Desktop Tools.exe (PID: 4004)
- Onion Desktop Tools.exe (PID: 2108)
- Onion Desktop Tools - WithConsole.exe (PID: 2296)
- Onion Desktop Tools - WithConsole.exe (PID: 1664)
- Onion Desktop Tools.exe (PID: 1856)
- Onion Desktop Tools - WithConsole.exe (PID: 4068)
- Onion Desktop Tools - WithConsole.exe (PID: 1816)
- Onion Desktop Tools - WithConsole.exe (PID: 948)
- Onion Desktop Tools - WithConsole.exe (PID: 2948)
- Onion Desktop Tools - WithConsole.exe (PID: 1016)
- Onion Desktop Tools - WithConsole.exe (PID: 2732)
- Onion Desktop Tools - WithConsole.exe (PID: 844)
- Onion Desktop Tools - WithConsole.exe (PID: 552)
- Onion Desktop Tools - WithConsole.exe (PID: 3336)
- Onion Desktop Tools - WithConsole.exe (PID: 3368)
- Onion Desktop Tools.exe (PID: 1872)
- Onion Desktop Tools.exe (PID: 3460)
- Onion Desktop Tools - WithConsole.exe (PID: 3836)
- Onion Desktop Tools - WithConsole.exe (PID: 3372)
- Onion Desktop Tools - WithConsole.exe (PID: 3804)
- Onion Desktop Tools - WithConsole.exe (PID: 2896)
- powershell.exe (PID: 1876)
Application launched itself
- chrome.exe (PID: 3688)
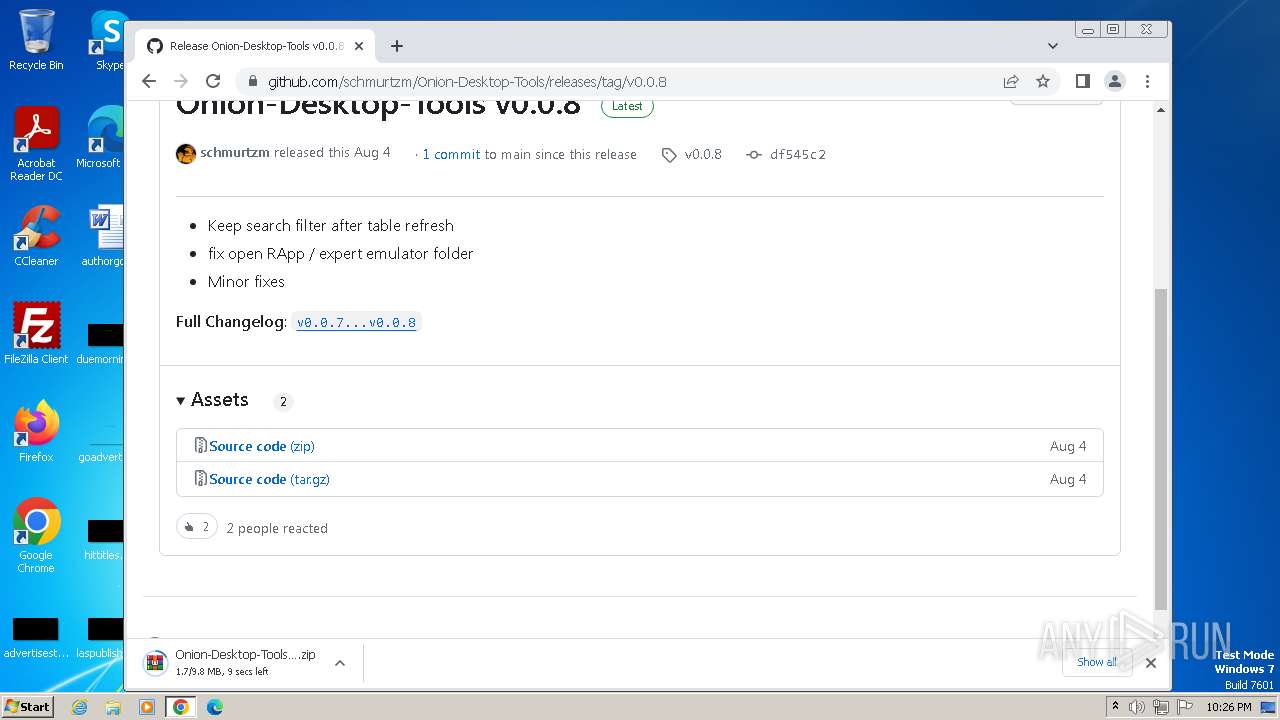
The process uses the downloaded file
- chrome.exe (PID: 2120)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 2620)
- WinRAR.exe (PID: 2652)
- chrome.exe (PID: 900)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 556)
Create files in a temporary directory
- Onion Desktop Tools.exe (PID: 3228)
- Onion Desktop Tools.exe (PID: 4004)
- Onion Desktop Tools.exe (PID: 2108)
- Onion Desktop Tools - WithConsole.exe (PID: 1664)
- Onion Desktop Tools - WithConsole.exe (PID: 4068)
- Onion Desktop Tools - WithConsole.exe (PID: 2948)
- Onion Desktop Tools - WithConsole.exe (PID: 2732)
- Onion Desktop Tools - WithConsole.exe (PID: 844)
- Onion Desktop Tools - WithConsole.exe (PID: 3368)
- Onion Desktop Tools.exe (PID: 3460)
- Onion Desktop Tools - WithConsole.exe (PID: 3804)
- Onion Desktop Tools - WithConsole.exe (PID: 3372)
Drops the executable file immediately after the start
- chrome.exe (PID: 3032)
- WinRAR.exe (PID: 2652)
Reads Internet Explorer settings
- powershell.exe (PID: 1876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:00+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 67584 |
| InitializedDataSize: | 29696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | Onion Desktop Tools Launcher |
| CompanyName: | Onion UI |
Total processes
147
Monitored processes
74
Malicious processes
37
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\DA6D.tmp\DA6E.tmp\DA6F.bat "C:\Users\admin\Desktop\Onion-Desktop-Tools-0.0.8\Onion Desktop Tools - WithConsole.exe"" | C:\Windows\System32\cmd.exe | — | Onion Desktop Tools - WithConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 296 | powershell -ExecutionPolicy Bypass -File ODT_update_temporary.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Users\admin\Desktop\Onion-Desktop-Tools-0.0.8\Onion Desktop Tools - WithConsole.exe" | C:\Users\admin\Desktop\Onion-Desktop-Tools-0.0.8\Onion Desktop Tools - WithConsole.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3772 --field-trial-handle=1172,i,18428199883515042161,12915354618313588992,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 756 | powershell -ExecutionPolicy Bypass -File ODT_update_temporary.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1532 --field-trial-handle=1172,i,18428199883515042161,12915354618313588992,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 844 | "C:\Users\admin\Desktop\Onion-Desktop-Tools-0.0.8\Onion Desktop Tools - WithConsole.exe" | C:\Users\admin\Desktop\Onion-Desktop-Tools-0.0.8\Onion Desktop Tools - WithConsole.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 860 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\7683.tmp\7684.tmp\7694.bat "C:\Users\admin\Desktop\Onion-Desktop-Tools-0.0.8\Onion Desktop Tools - WithConsole.exe"" | C:\Windows\System32\cmd.exe | — | Onion Desktop Tools - WithConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2424 --field-trial-handle=1172,i,18428199883515042161,12915354618313588992,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
22 255
Read events
21 382
Write events
869
Delete events
4
Modification events
| (PID) Process: | (3228) Onion Desktop Tools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3228) Onion Desktop Tools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3228) Onion Desktop Tools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3228) Onion Desktop Tools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3408) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
Executable files
21
Suspicious files
243
Text files
72
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF16ea36.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3408 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EYA8KTT1HA4O1JUERMG9.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF16ea26.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3408 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1672b4.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 3688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF16ec78.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3228 | Onion Desktop Tools.exe | C:\Users\admin\AppData\Local\Temp\7208.tmp\7209.tmp\720A.bat | text | |
MD5:CA46EA3BEB3F07280A07D6A0C9C1A5DF | SHA256:4C840D2FF3154ACD63A952E4CC6EB56F8010185D2129FA6A212EA0A73F2312B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
42
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cm732ab5cbk7z3qxwtvrk47qp4_421/lmelglejhemejginpboagddgdfbepgmp_421_all_ZZ_adyh3sucdkooppg4oi3lj5o3if3q.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cm732ab5cbk7z3qxwtvrk47qp4_421/lmelglejhemejginpboagddgdfbepgmp_421_all_ZZ_adyh3sucdkooppg4oi3lj5o3if3q.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cm732ab5cbk7z3qxwtvrk47qp4_421/lmelglejhemejginpboagddgdfbepgmp_421_all_ZZ_adyh3sucdkooppg4oi3lj5o3if3q.crx3 | unknown | binary | 9.91 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cm732ab5cbk7z3qxwtvrk47qp4_421/lmelglejhemejginpboagddgdfbepgmp_421_all_ZZ_adyh3sucdkooppg4oi3lj5o3if3q.crx3 | unknown | binary | 9.85 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cm732ab5cbk7z3qxwtvrk47qp4_421/lmelglejhemejginpboagddgdfbepgmp_421_all_ZZ_adyh3sucdkooppg4oi3lj5o3if3q.crx3 | unknown | binary | 5.96 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3688 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3748 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3748 | chrome.exe | 142.250.185.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
3748 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
3748 | chrome.exe | 142.250.186.163:443 | update.googleapis.com | GOOGLE | US | whitelisted |
3688 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
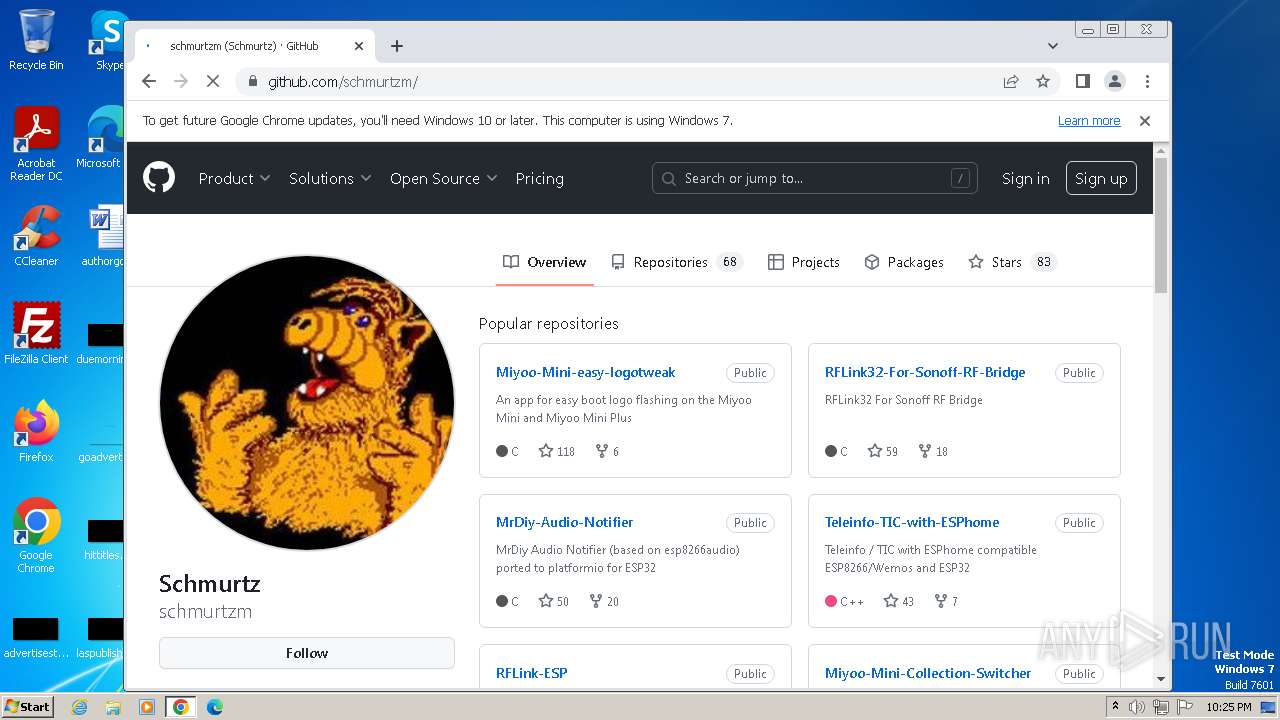
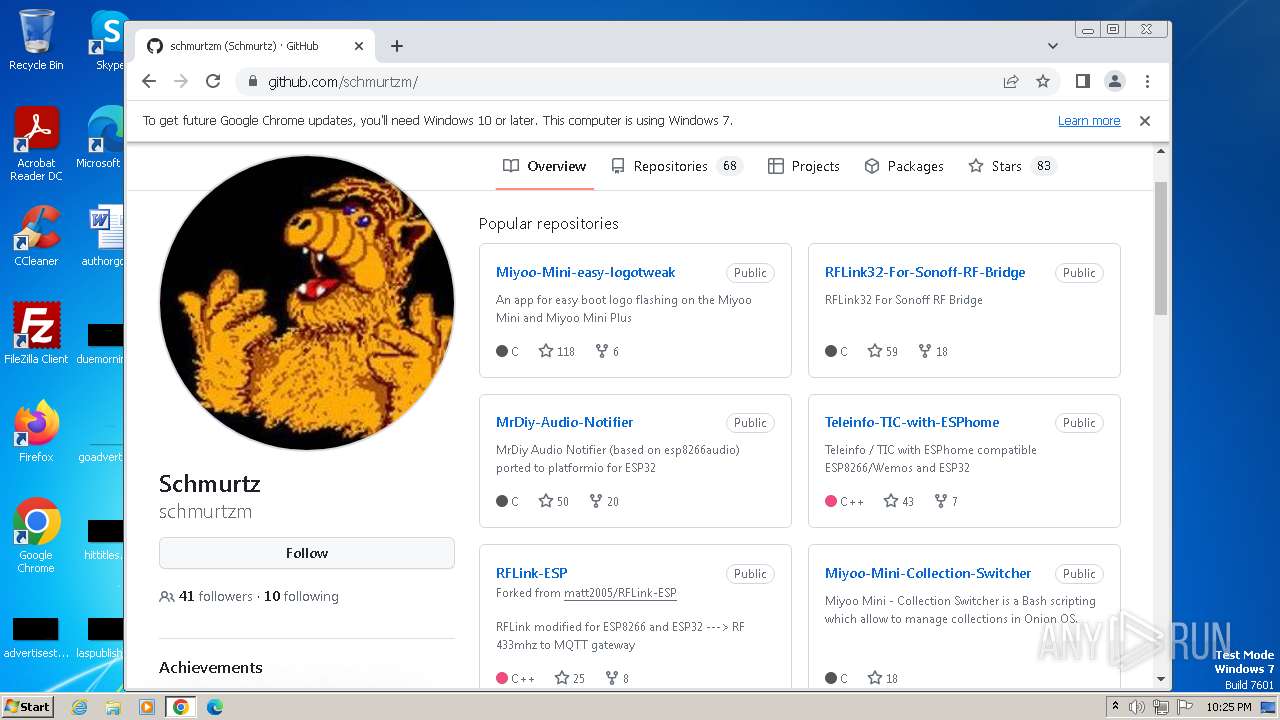
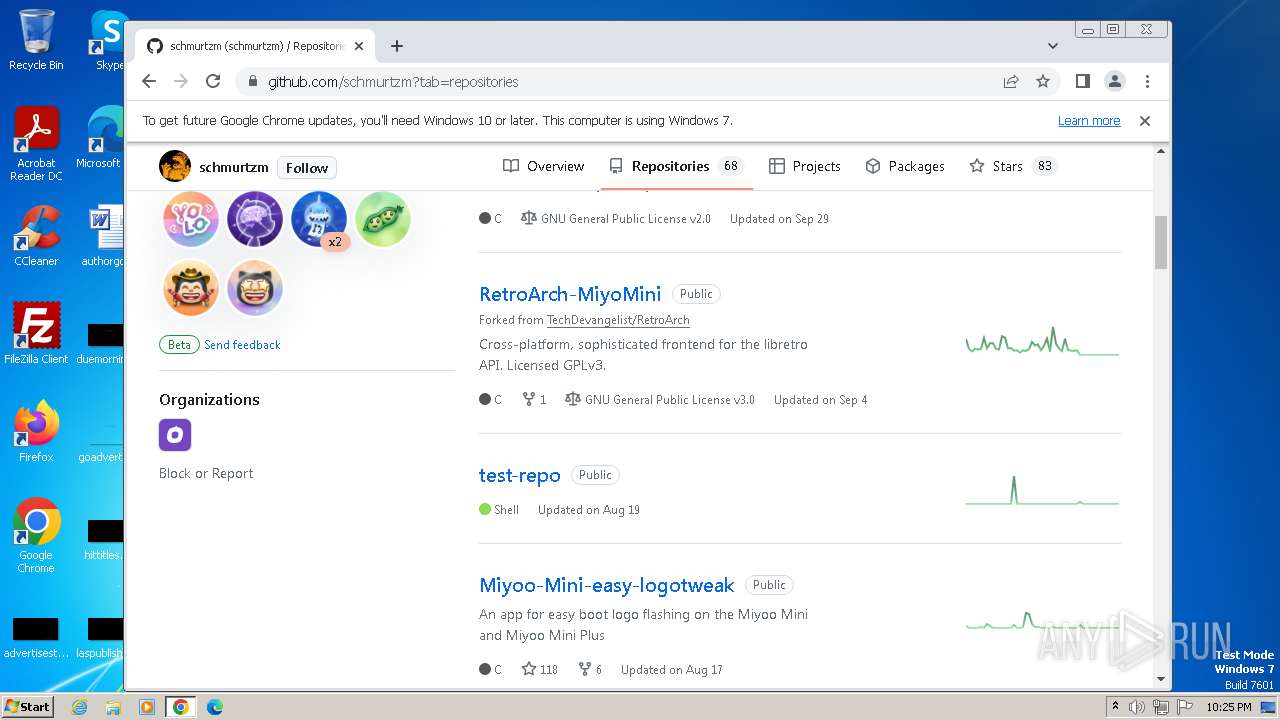
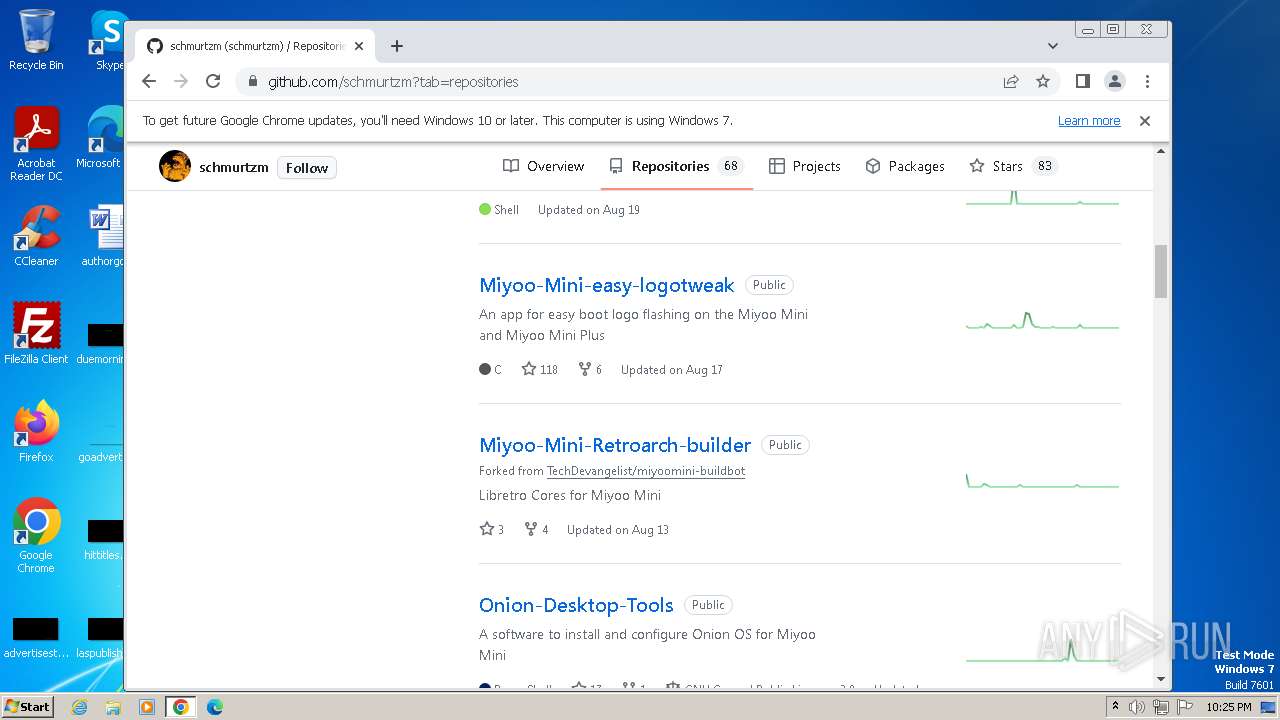
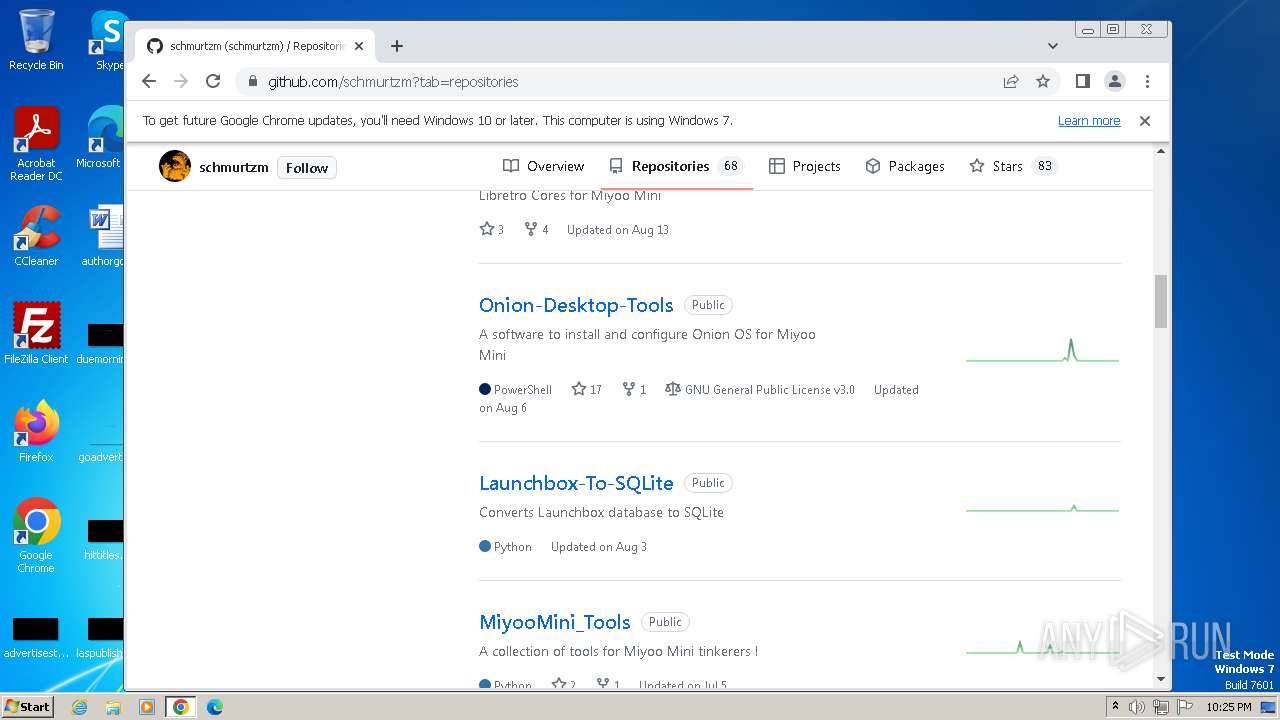
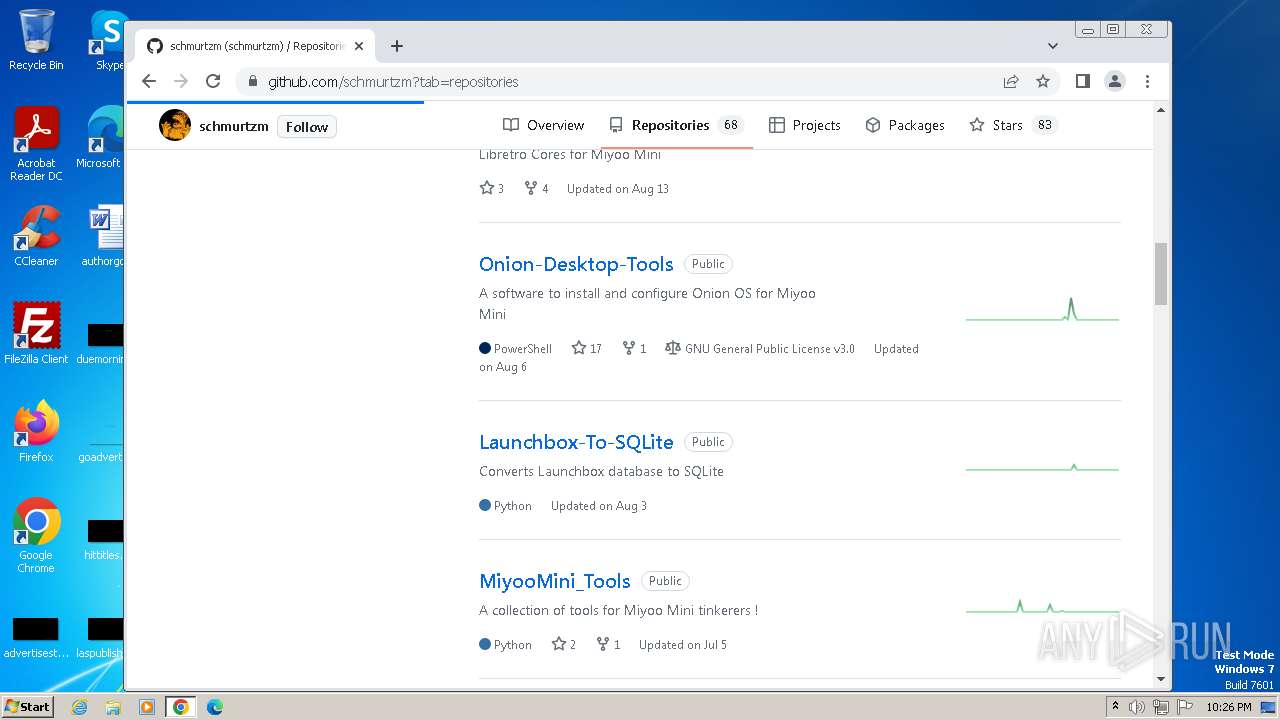
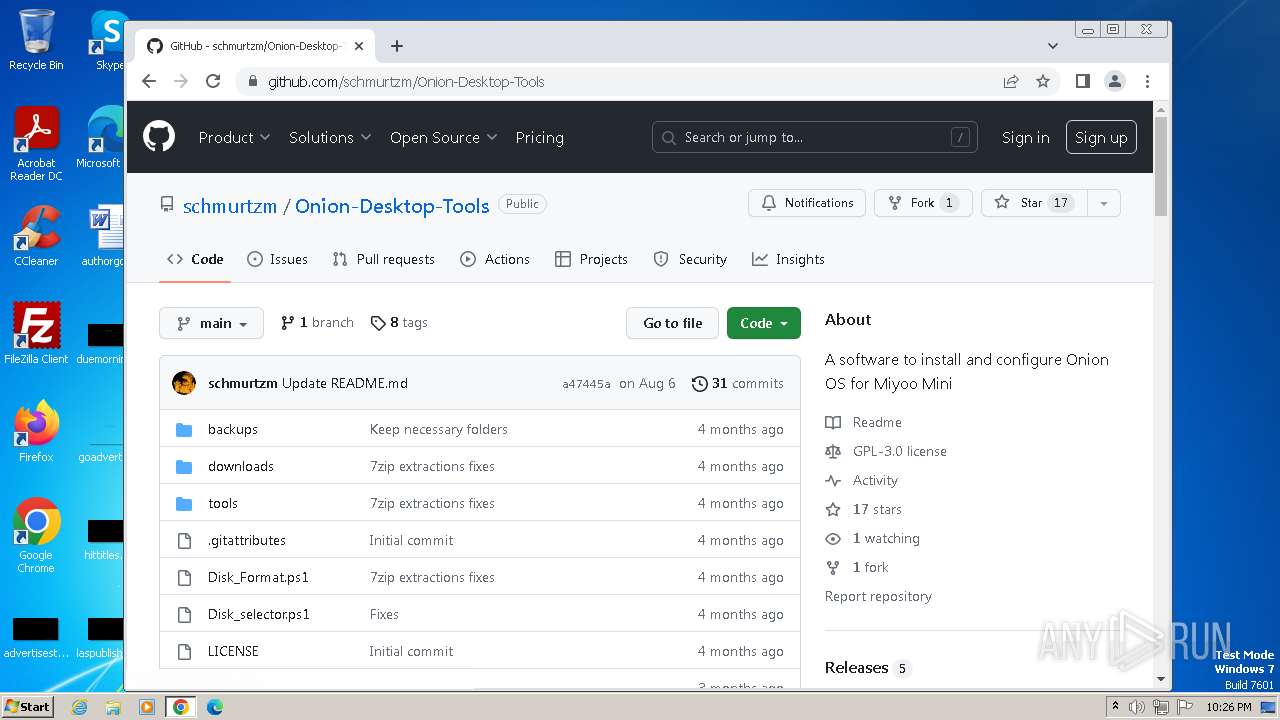
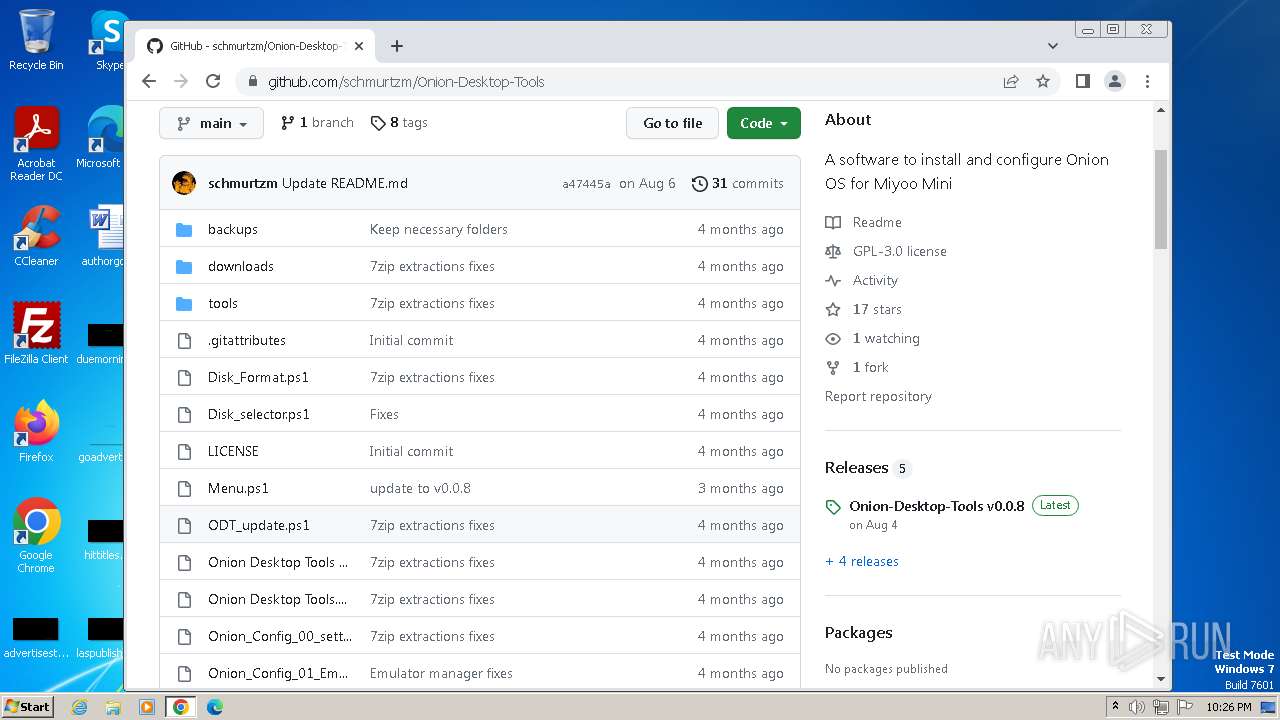
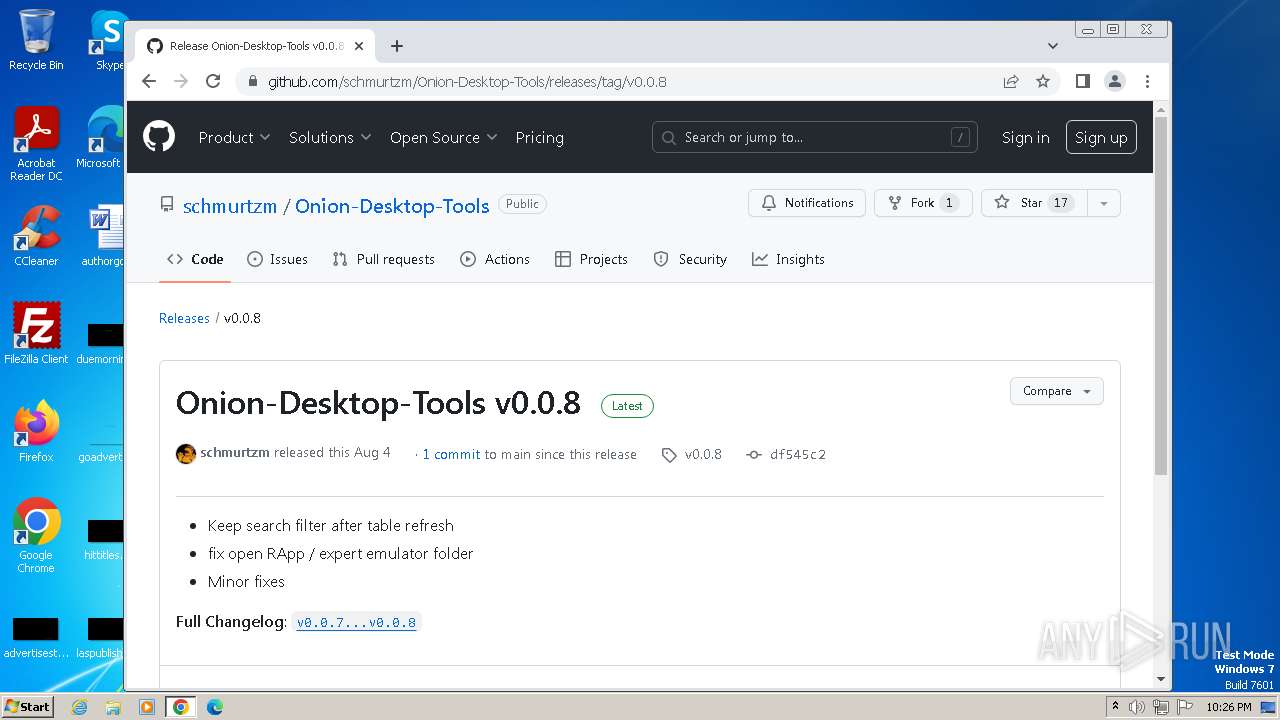
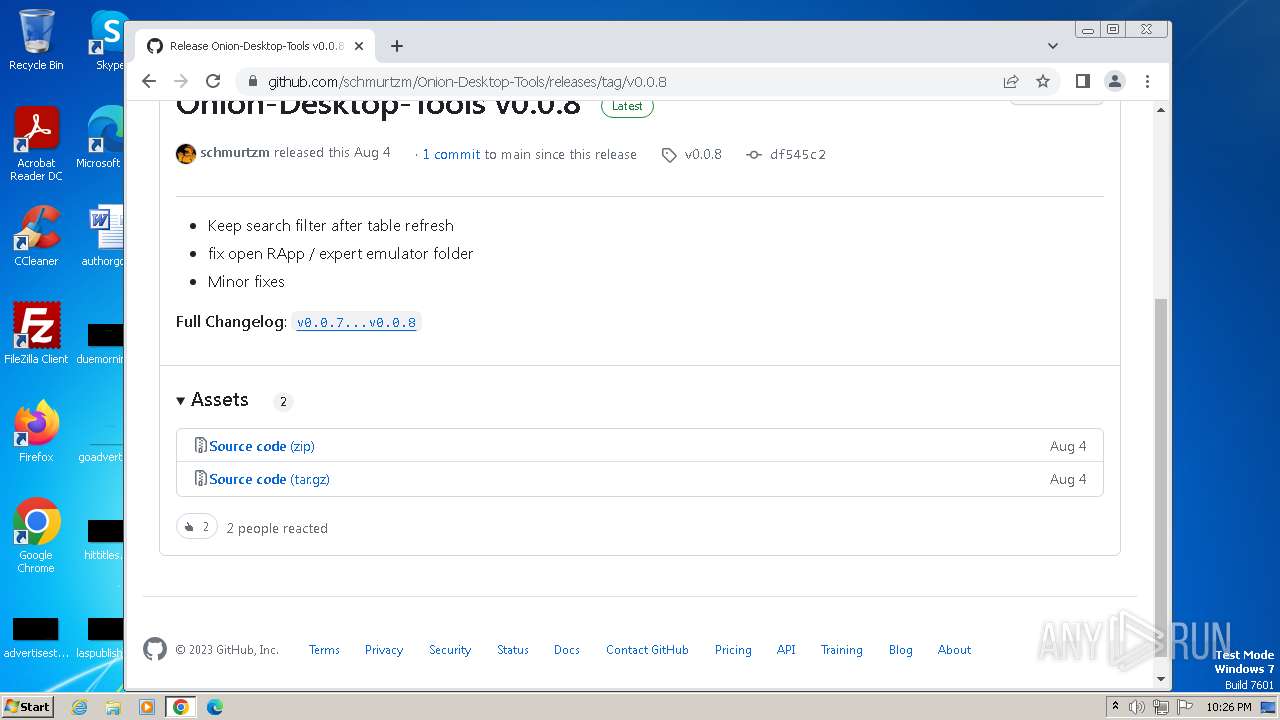
github.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |