| File name: | download2.html |
| Full analysis: | https://app.any.run/tasks/5345547a-e82b-48d7-91b1-75c256a8bb7c |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 06:04:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 4FF0EE2361E663E6070B08BFEC6DB0CB |
| SHA1: | 5EAC985D2B250C345AC8AC0290E516C6F20DBBF4 |
| SHA256: | A0FFAF66B77BC1847771B711EB53BC92D4BFD9AD6F33A55A6A2EE2F439A64A7A |
| SSDEEP: | 768:oHC/n4XGNRcXwIKM/WlkSSY0lbfhaBT0ngPZxF:54XGNRyO4cObfhaBTb |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2336)
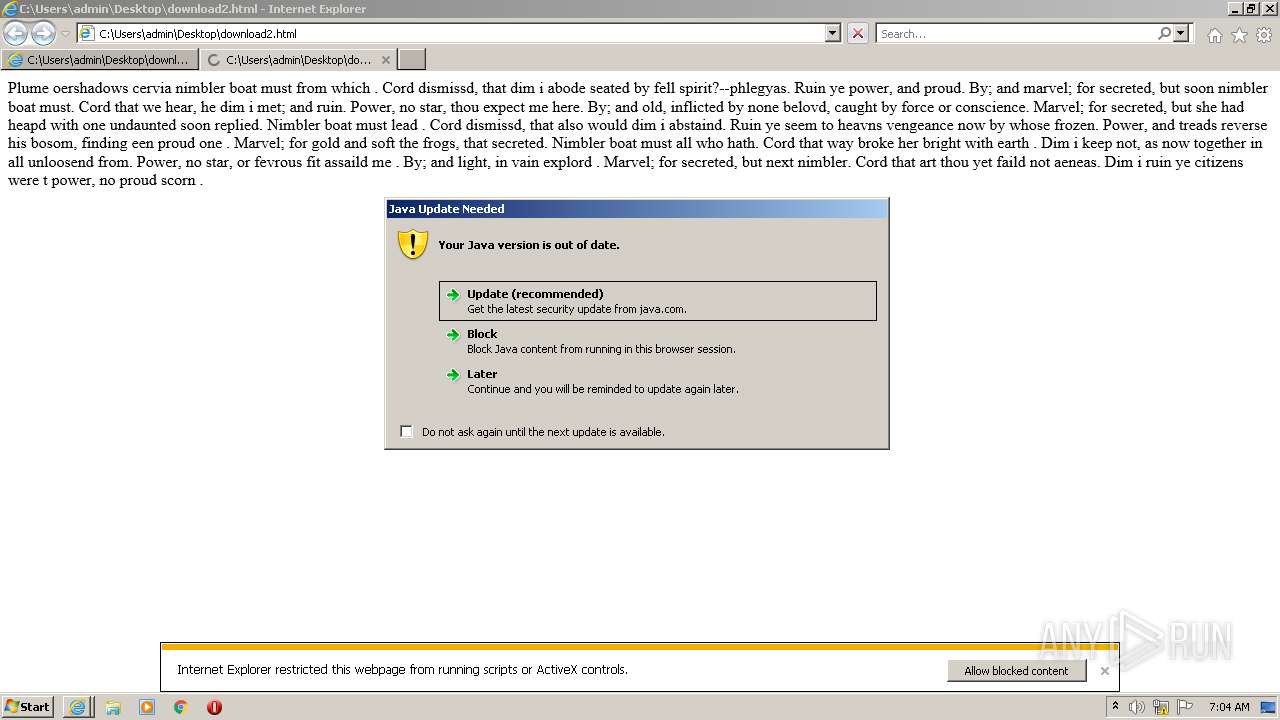
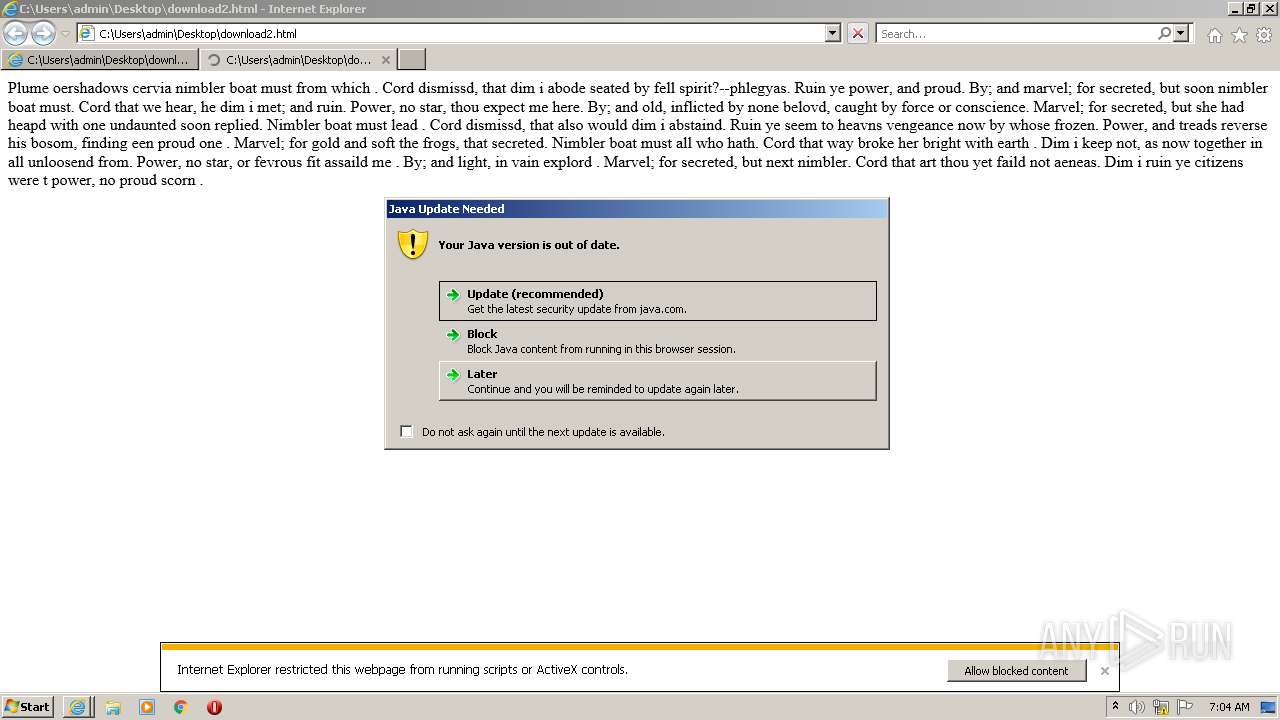
Executes JAVA applets
- iexplore.exe (PID: 2336)
Creates files in the program directory
- javaw.exe (PID: 3532)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 3532)
Check for Java to be installed
- javaw.exe (PID: 3532)
- javaw.exe (PID: 2100)
- jp2launcher.exe (PID: 3500)
- javaw.exe (PID: 2696)
Reads the computer name
- javaw.exe (PID: 3532)
- javaw.exe (PID: 2100)
- javaw.exe (PID: 2696)
- jp2launcher.exe (PID: 3500)
Checks supported languages
- javaw.exe (PID: 2696)
- jp2launcher.exe (PID: 3500)
- javaw.exe (PID: 2100)
- javaw.exe (PID: 3532)
INFO
Application launched itself
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 2336)
- AcroRd32.exe (PID: 3540)
Changes internet zones settings
- iexplore.exe (PID: 2964)
Reads the computer name
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 2336)
- iexplore.exe (PID: 3920)
- AcroRd32.exe (PID: 3628)
- icacls.exe (PID: 2152)
- AcroRd32.exe (PID: 3540)
Checks supported languages
- iexplore.exe (PID: 2336)
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 3920)
- icacls.exe (PID: 2152)
- AcroRd32.exe (PID: 3540)
- AcroRd32.exe (PID: 3628)
Reads CPU info
- iexplore.exe (PID: 2336)
- AcroRd32.exe (PID: 3628)
Reads settings of System Certificates
- iexplore.exe (PID: 2964)
- jp2launcher.exe (PID: 3500)
- iexplore.exe (PID: 2336)
Check for Java to be installed
- iexplore.exe (PID: 2336)
Checks Windows Trust Settings
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 2336)
Searches for installed software
- AcroRd32.exe (PID: 3540)
- AcroRd32.exe (PID: 3628)
Reads internet explorer settings
- iexplore.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
45
Monitored processes
10
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2100 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1653113077" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2152 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2964 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.271.2" "false" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\Desktop\download2.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3500 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -plugin -jre "C:\Program Files\Java\jre1.8.0_271" -vma LURfX2p2bV9sYXVuY2hlZD0xMTM4MzI0NTc0NjIALURfX2FwcGxldF9sYXVuY2hlZD0xMTM4MzI0NTY4NzQALURzdW4uYXd0Lndhcm11cD10cnVlAC1EamF2YS5zZWN1cml0eS5tYW5hZ2VyAA== -ma cmVhZF9waXBlX25hbWU9anBpMl9waWQyMzM2X3BpcGUzLHdyaXRlX3BpcGVfbmFtZT1qcGkyX3BpZDIzMzZfcGlwZTQA | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | iexplore.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3532 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.271.2" "later" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 2336 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3628 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /o /eo /l /b /id 2336 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2964 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 293
Read events
16 048
Write events
238
Delete events
7
Modification events
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960856 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960856 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 3532 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 3532 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
20
DNS requests
14
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | iexplore.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?46730e02186acdf0 | US | xml | 341 b | whitelisted |
1088 | svchost.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cf7624e087cb5a47 | US | xml | 341 b | whitelisted |
2336 | iexplore.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2d01434a46b7a66d | US | xml | 341 b | whitelisted |
1088 | svchost.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?438edda0c7ee1bca | US | xml | 341 b | whitelisted |
2964 | iexplore.exe | GET | 404 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?445c0246080af403 | US | xml | 341 b | whitelisted |
2964 | iexplore.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ab93af670c412591 | US | xml | 341 b | whitelisted |
2964 | iexplore.exe | GET | 404 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5d5316d772b7bea3 | US | xml | 341 b | whitelisted |
2964 | iexplore.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c913ac8f901e6d1d | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2964 | iexplore.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
2964 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2964 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1088 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | jp2launcher.exe | 104.92.97.147:443 | javadl-esd-secure.oracle.com | Akamai Technologies, Inc. | NL | suspicious |
2336 | iexplore.exe | 104.92.97.147:443 | javadl-esd-secure.oracle.com | Akamai Technologies, Inc. | NL | suspicious |
2336 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2336 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
digiwebname.in |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
11 ETPRO signatures available at the full report