| File name: | Virus.exe |
| Full analysis: | https://app.any.run/tasks/2a3e9711-0110-4c57-8ed5-adde3b7dff83 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2024, 16:25:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 739F0E4E9C89F704D553B6C1638A2630 |
| SHA1: | 07F3A108134F132310A93D98F909F492F9990FFF |
| SHA256: | A0EEEB8B83831D6FD9B7C042B8DA87E43DC75D35B6D552B00B08433CB78AC048 |
| SSDEEP: | 6144:hCpVej/t9JAy89+J9Wz0p/y7t6nS54dvQPs3J+VfMZYZnpw:VlP39i09QtudvQPs3JzaB+ |
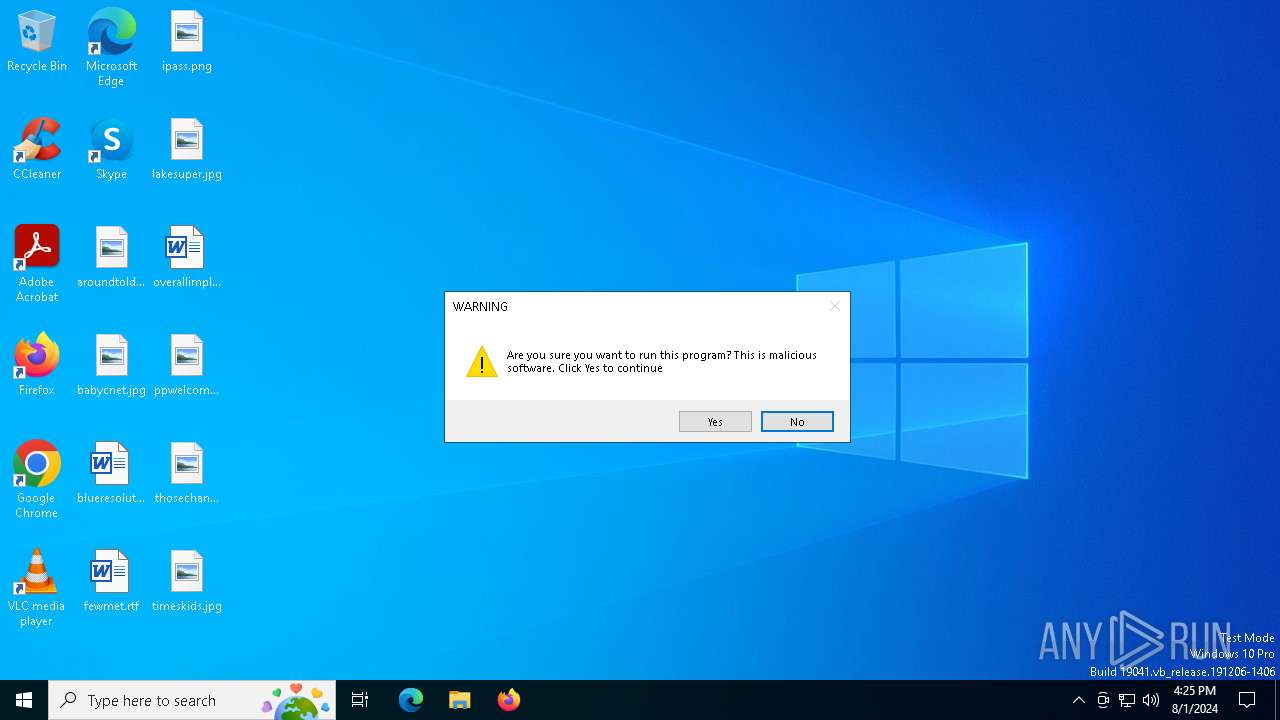
MALICIOUS
Drops the executable file immediately after the start
- Virus.exe (PID: 6320)
- Virus.exe (PID: 6396)
Changes the autorun value in the registry
- MBR.exe (PID: 904)
Uses Task Scheduler to run other applications
- MBR.exe (PID: 904)
SUSPICIOUS
Reads security settings of Internet Explorer
- Virus.exe (PID: 6396)
- Virus.exe (PID: 6320)
- Virus_Destructive.exe (PID: 6544)
Reads the date of Windows installation
- Virus.exe (PID: 6320)
- Virus.exe (PID: 6396)
- Virus_Destructive.exe (PID: 6544)
Application launched itself
- Virus.exe (PID: 6320)
Executing commands from ".cmd" file
- Virus.exe (PID: 6396)
Starts CMD.EXE for commands execution
- Virus.exe (PID: 6396)
- Virus_Destructive.exe (PID: 6544)
Executable content was dropped or overwritten
- Virus.exe (PID: 6396)
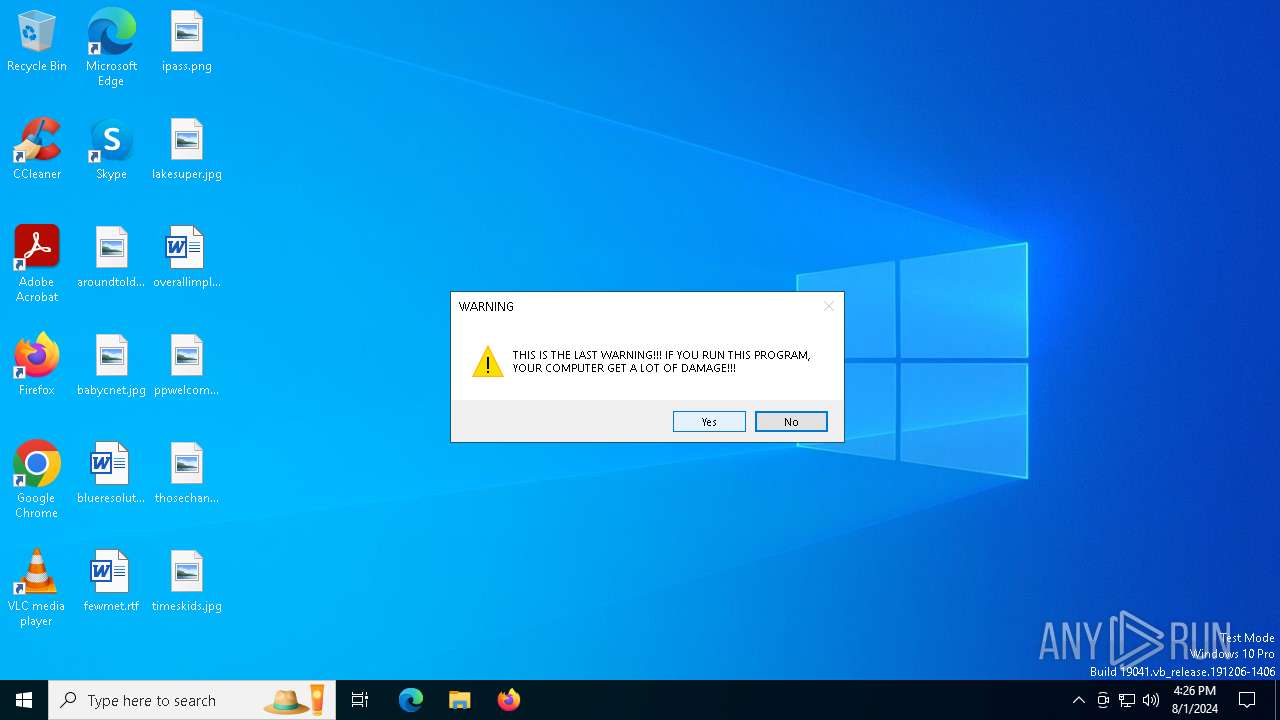
Probably fake Windows Update
- schtasks.exe (PID: 6424)
Uses TASKKILL.EXE to kill process
- Virus_Destructive.exe (PID: 6544)
The process checks if it is being run in the virtual environment
- icacls.exe (PID: 6524)
- icacls.exe (PID: 6316)
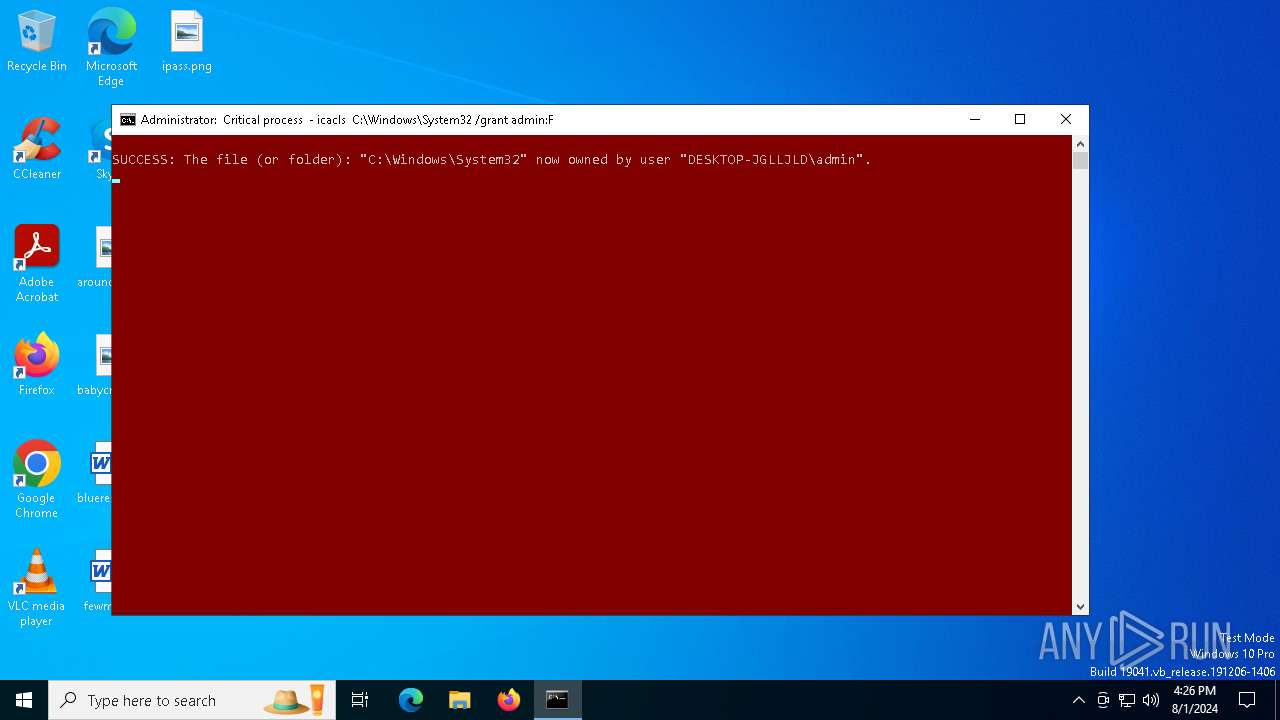
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 3032)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3032)
INFO
Checks supported languages
- Virus.exe (PID: 6320)
- Virus.exe (PID: 6396)
- Virus_Destructive.exe (PID: 6544)
- MBR.exe (PID: 904)
- identity_helper.exe (PID: 7820)
Reads the computer name
- Virus.exe (PID: 6320)
- Virus.exe (PID: 6396)
- Virus_Destructive.exe (PID: 6544)
- identity_helper.exe (PID: 7820)
Process checks computer location settings
- Virus.exe (PID: 6320)
- Virus.exe (PID: 6396)
- Virus_Destructive.exe (PID: 6544)
Create files in a temporary directory
- Virus.exe (PID: 6396)
Reads the machine GUID from the registry
- Virus_Destructive.exe (PID: 6544)
Reads Microsoft Office registry keys
- Virus_Destructive.exe (PID: 6544)
- msedge.exe (PID: 6384)
- msedge.exe (PID: 6532)
Application launched itself
- msedge.exe (PID: 6384)
- msedge.exe (PID: 6532)
Manual execution by a user
- msedge.exe (PID: 6532)
Reads Environment values
- identity_helper.exe (PID: 7820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 22:14:34+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 114176 |
| InitializedDataSize: | 39424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c35f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
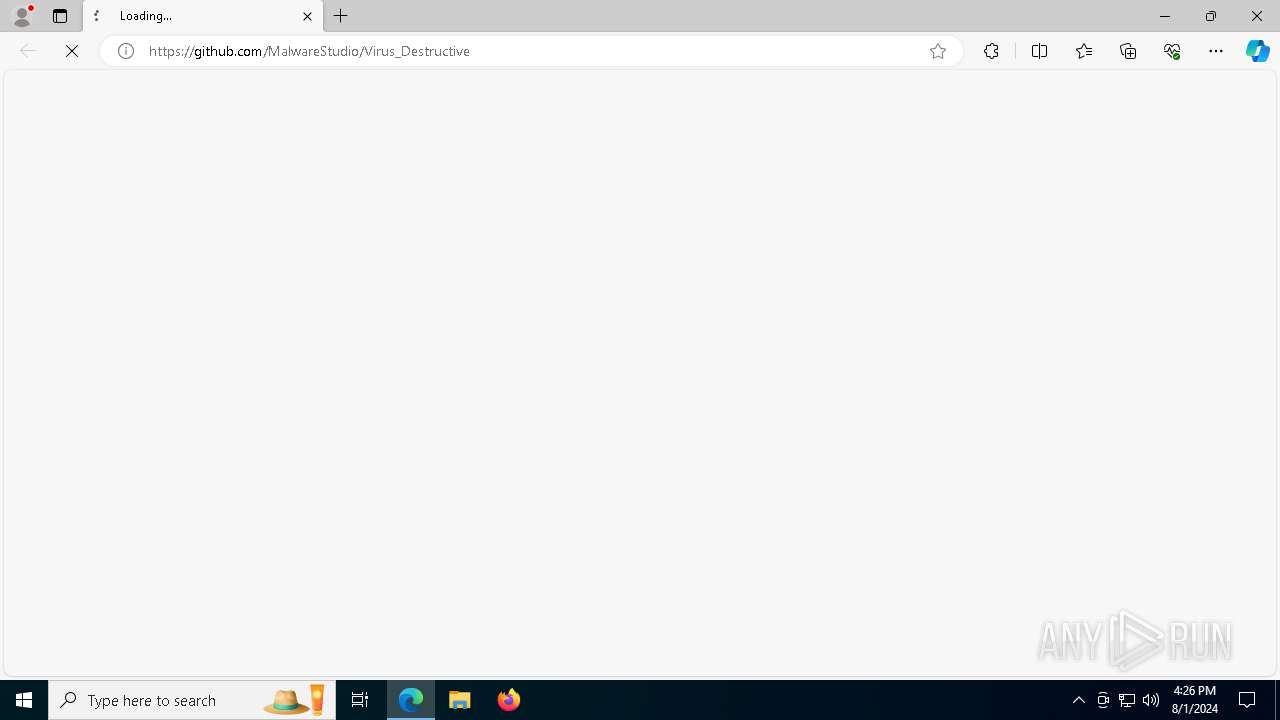
| CompanyName: | Vichingo455 |
| LegalCopyright: | Copyright © 2021-22 Vichingo455 |
| OriginalFileName: | Virus.exe |
| Comments: | Trojan that destroys the system |
| FileVersion: | 2.0.0.0 |
| ProductName: | Trojan that destroys the system |
| ProductVersion: | 2.0.0.0 |
| InternalName: | Virus.exe |
| FileDescription: | Virus |
| Created: | 7z SFX Constructor v4.5.0.0 (http://usbtor.ru/viewtopic.php?t=798) |
| Builder: | Asus 11:46:51 28/12/2021 |
Total processes
221
Monitored processes
82
Malicious processes
6
Suspicious processes
1
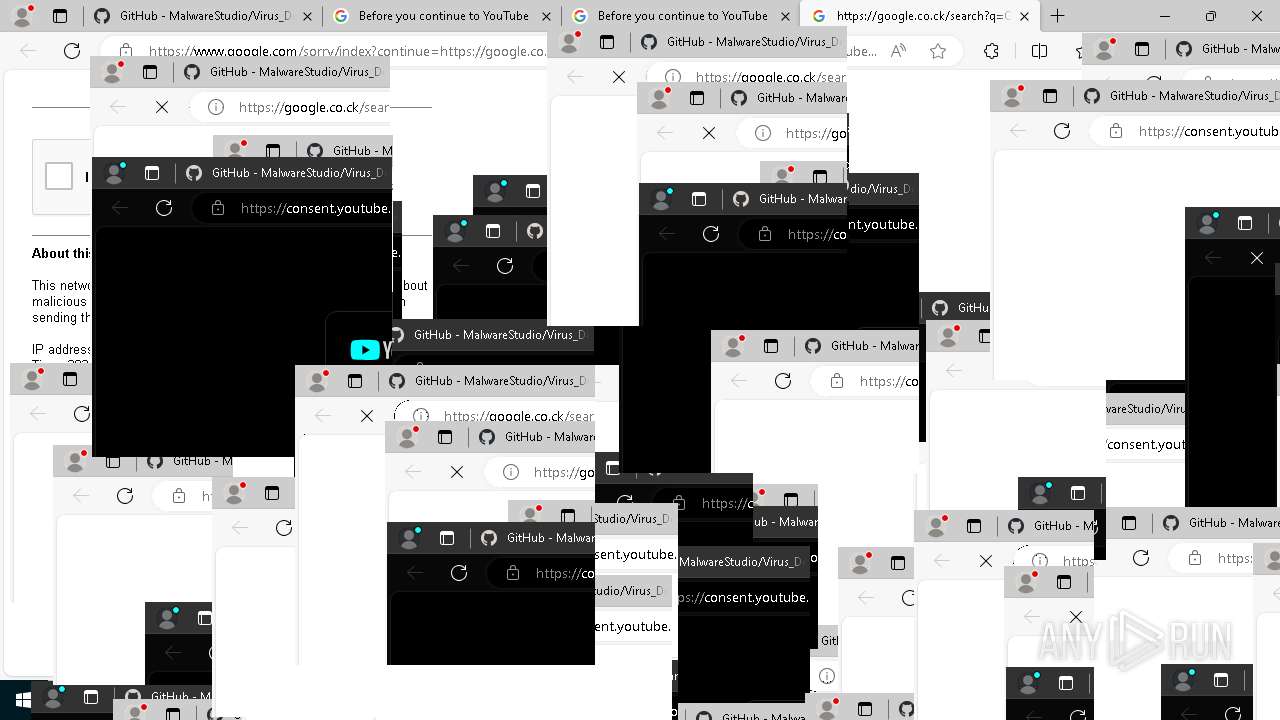
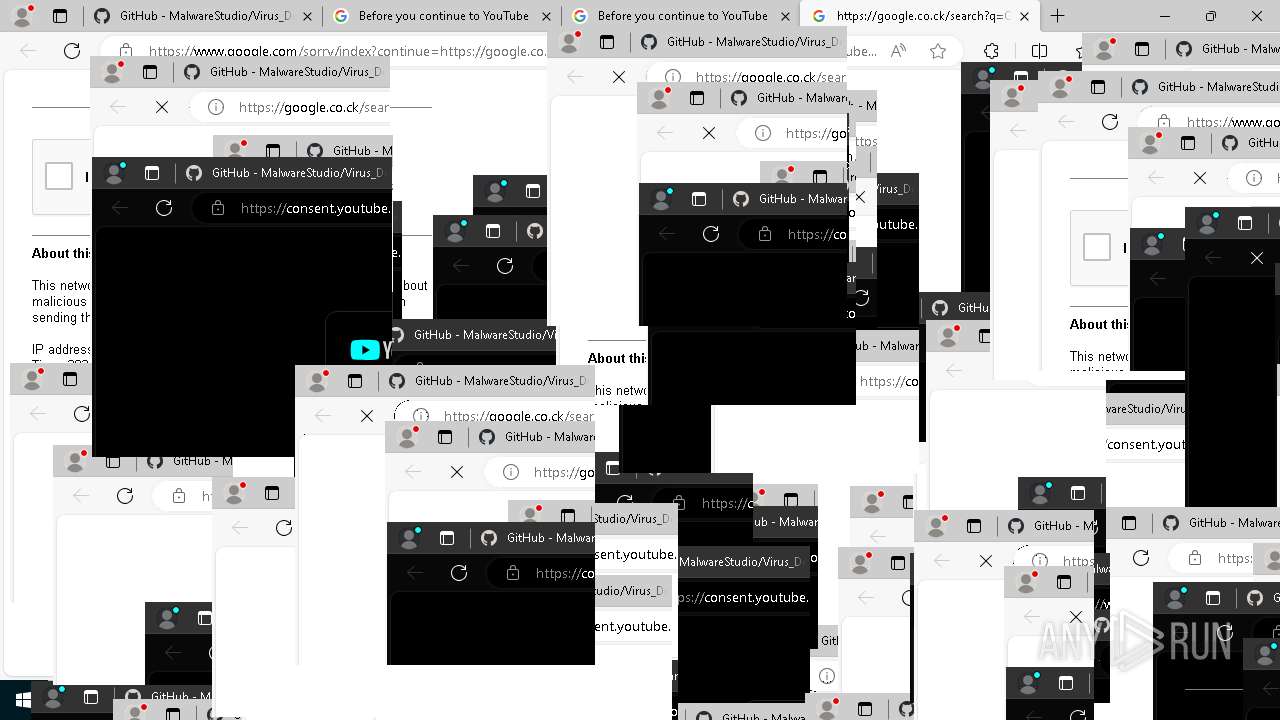
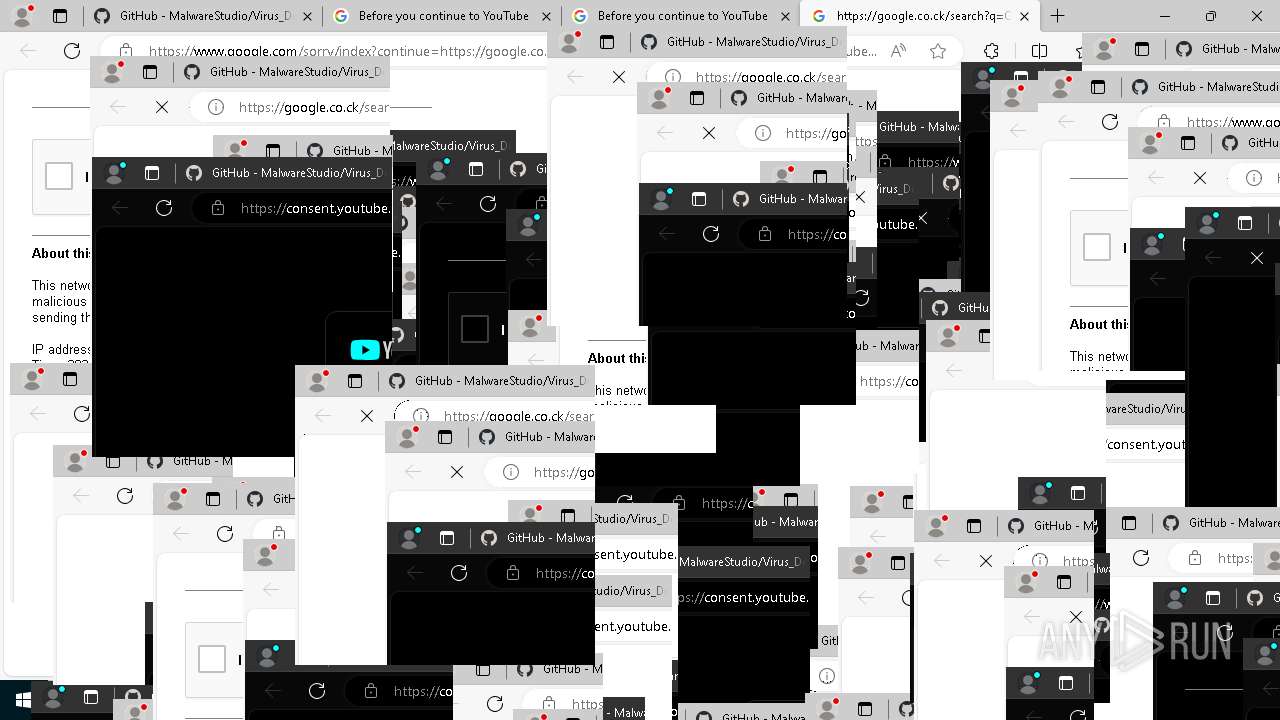
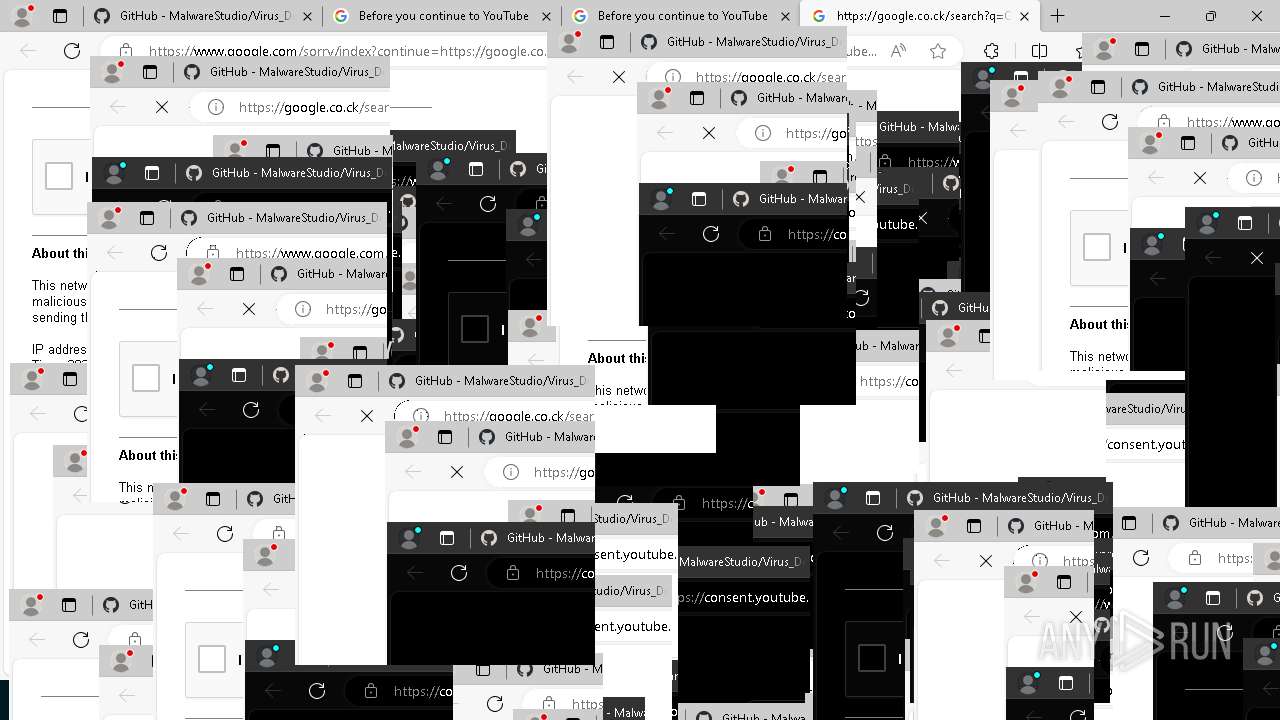
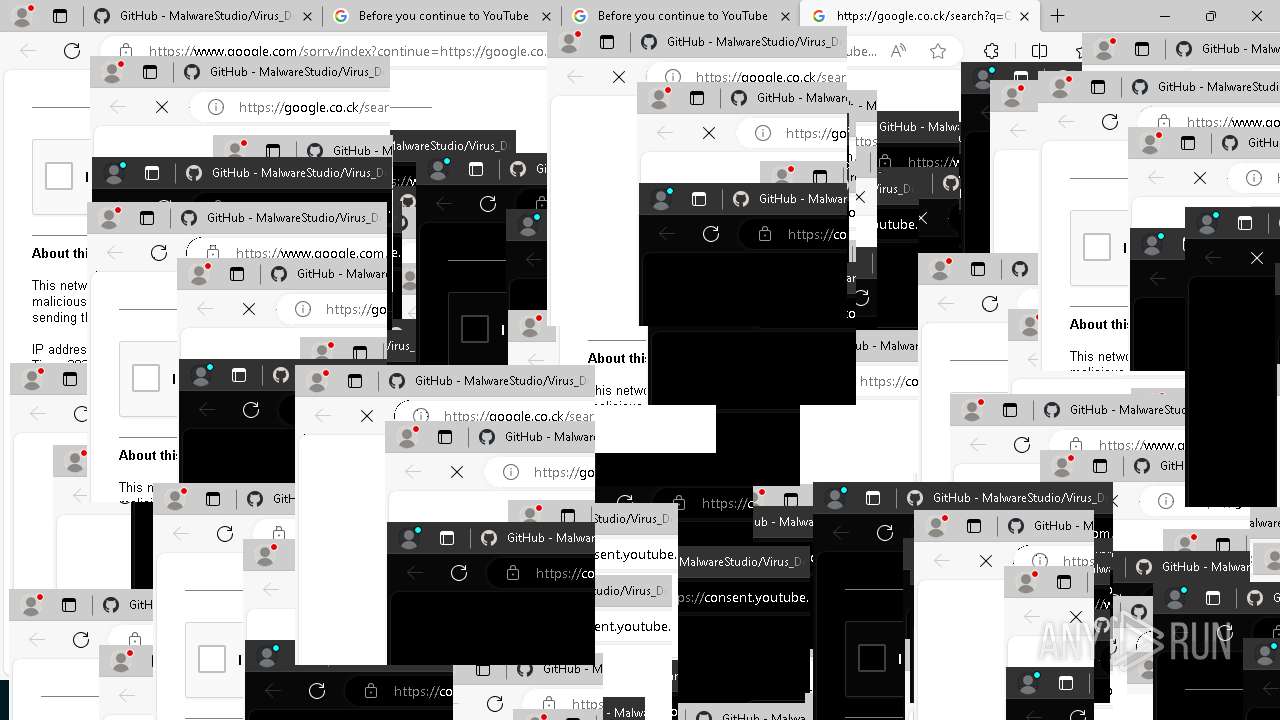
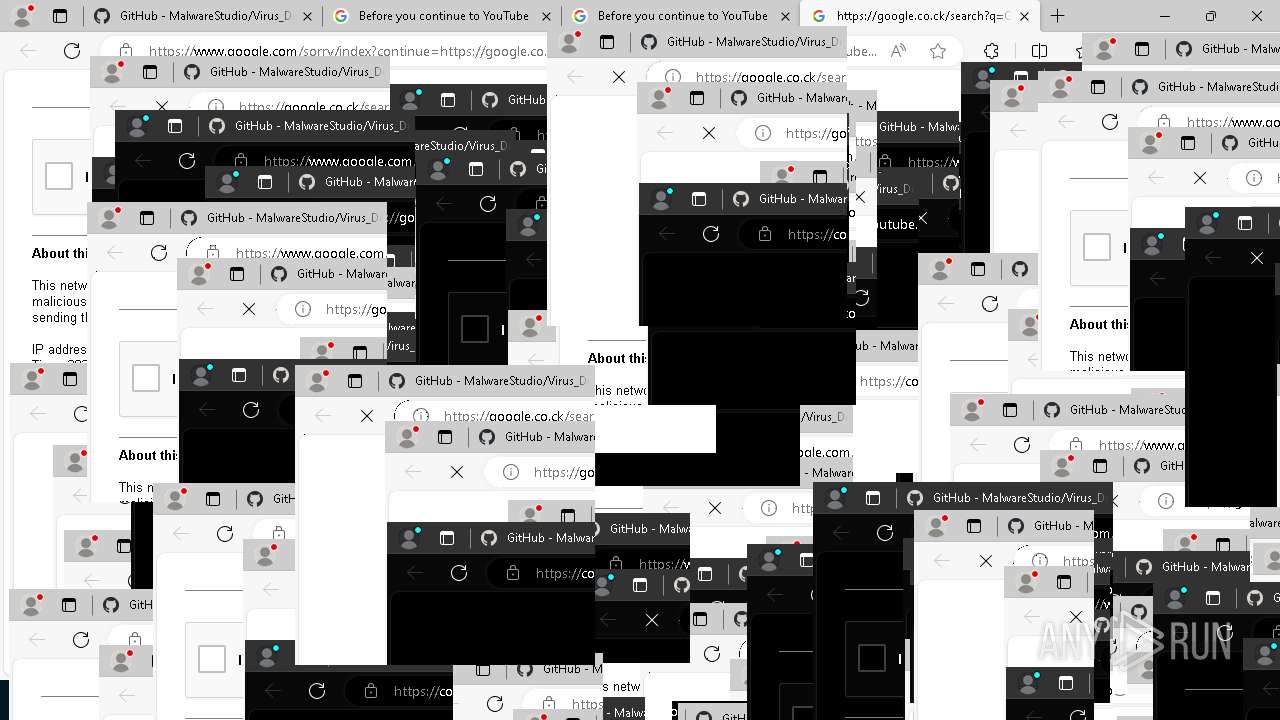
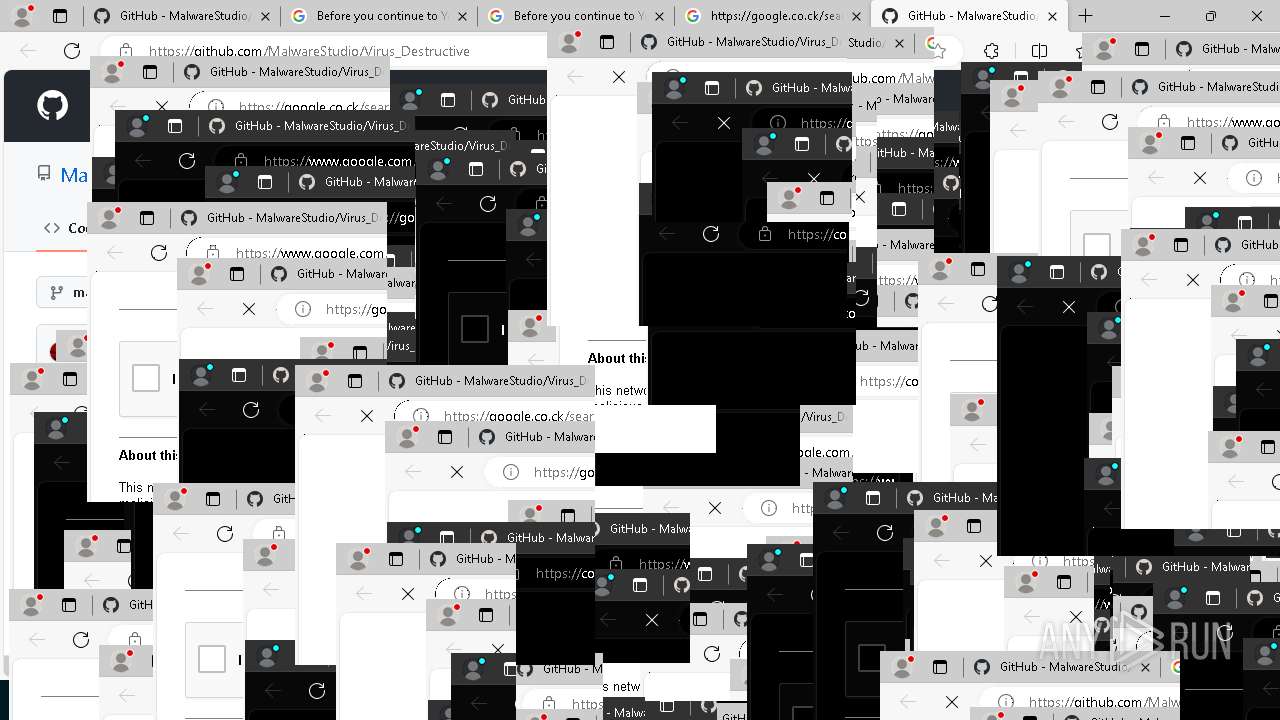
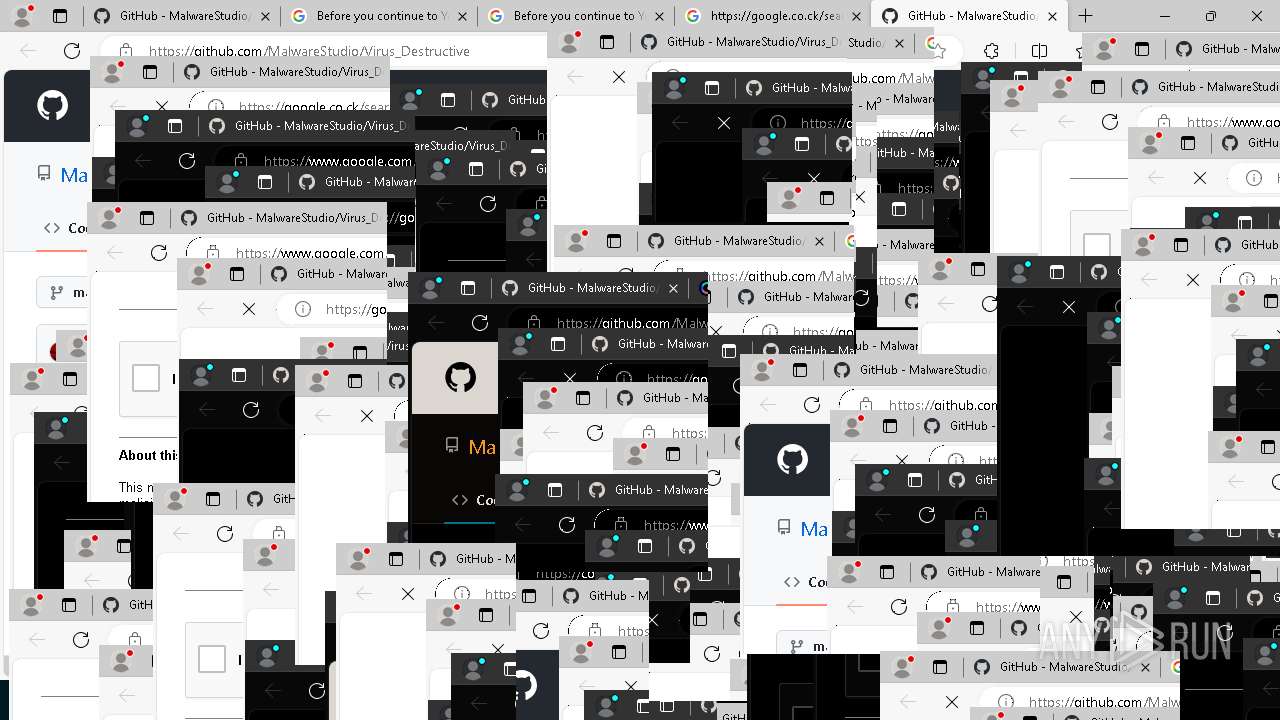
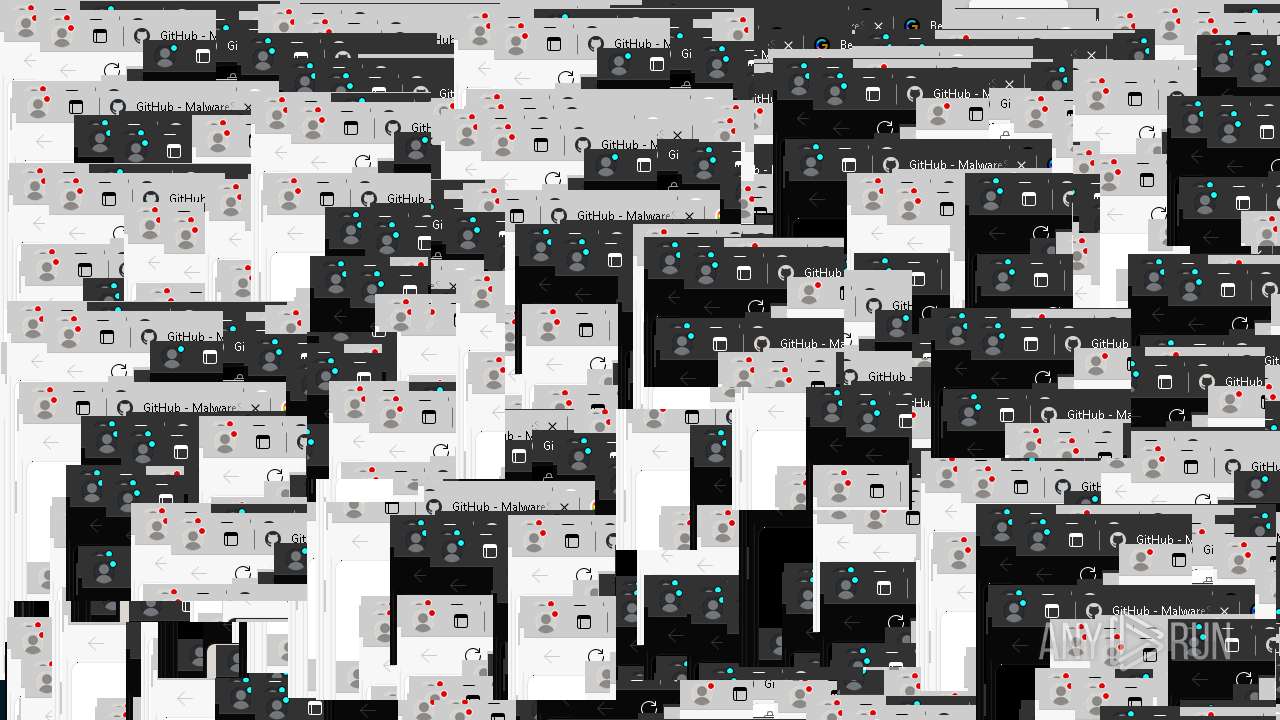
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | reagentc.exe /disable | C:\Windows\System32\ReAgentc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Recovery Agent Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\Users\admin\AppData\Local\Temp\Virus\MBR.exe" | C:\Users\admin\AppData\Local\Temp\Virus\MBR.exe | Virus_Destructive.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=5640 --field-trial-handle=2328,i,9139226387070831347,4111590432612070197,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://google.co.ck/search?q=CYBER+SOLDIER+YouTube+channel | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Virus_Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2748 --field-trial-handle=2328,i,9139226387070831347,4111590432612070197,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1492 | "C:\Windows\System32\taskkill.exe" /f /im taskmgr.exe | C:\Windows\System32\taskkill.exe | — | Virus_Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --mojo-platform-channel-handle=7324 --field-trial-handle=2328,i,9139226387070831347,4111590432612070197,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7292 --field-trial-handle=2328,i,9139226387070831347,4111590432612070197,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=808 --field-trial-handle=2328,i,9139226387070831347,4111590432612070197,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=38 --mojo-platform-channel-handle=7180 --field-trial-handle=2328,i,9139226387070831347,4111590432612070197,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
30 257
Read events
29 932
Write events
259
Delete events
66
Modification events
| (PID) Process: | (6320) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6320) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6320) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6320) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6396) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6396) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6396) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6396) Virus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6544) Virus_Destructive.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6544) Virus_Destructive.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
16
Suspicious files
358
Text files
96
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 904 | MBR.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 640 | ReAgentc.exe | C:\Windows\System32\Recovery\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 640 | ReAgentc.exe | C:\Windows\Panther\UnattendGC\diagwrn.xml | text | |
MD5:E7D61F31E13255B53337512E2D6EDF08 | SHA256:F5FD217C66A78E469FC33EE079506702CA14280B58FEFABFDEEE310F25E314FE | |||
| 6396 | Virus.exe | C:\Users\admin\AppData\Local\Temp\Virus\Virus_Destructive.exe.config | xml | |
MD5:CEBFE157098995082112604CA8730110 | SHA256:DFDF5ECD6291CB0D74B89746B733BC8B1F6E74F00A253DEE15D14891A2CF5BA0 | |||
| 640 | ReAgentc.exe | C:\Windows\System32\Recovery\ReAgent.xml | xml | |
MD5:44B2DA39CEB2C183D5DCD43AA128C2DD | SHA256:894EE2B19608D10DF4BF8B8F5BBCF40CE38C09C1F4C5543B6164F40C04BB270D | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFf5412.TMP | — | |
MD5:— | SHA256:— | |||
| 640 | ReAgentc.exe | C:\Windows\Panther\UnattendGC\diagerr.xml | text | |
MD5:3A8D2D92D67445734789F82D6E6D90A6 | SHA256:E80AA5A43C517844228A67E8A49E30EE8CF68979E54BA0A3FE660C80978808C6 | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 640 | ReAgentc.exe | \\?\Volume{2f5c5e71-85a9-11eb-90a8-9a9b76358421}\EFI\Microsoft\Recovery\BCD | binary | |
MD5:2ED37FE990B6402E9DE3E1AFB29DF8E2 | SHA256:64C2080F3A8D0DE17AFB70721A06A8F95DA89E496E78B0497ECBF7E2ACD8FF8B | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFf5422.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
177
DNS requests
159
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6596 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723131516&P2=404&P3=2&P4=GJK7431VSnkZjge3pfyi0NhxbS2pFMAXMCDeo02%2bNwLlyQi%2fS%2fG7VNP4nBGRDSrwXKZHX8Kp4bvCAH1dJ61s0w%3d%3d | unknown | — | — | whitelisted |
6596 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723131516&P2=404&P3=2&P4=GJK7431VSnkZjge3pfyi0NhxbS2pFMAXMCDeo02%2bNwLlyQi%2fS%2fG7VNP4nBGRDSrwXKZHX8Kp4bvCAH1dJ61s0w%3d%3d | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2608 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7028 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4692 | msedge.exe | GET | 304 | 195.138.255.24:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | whitelisted |
6964 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4692 | msedge.exe | GET | 304 | 23.192.153.142:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
4692 | msedge.exe | GET | 304 | 23.192.153.142:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
6596 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723131516&P2=404&P3=2&P4=GJK7431VSnkZjge3pfyi0NhxbS2pFMAXMCDeo02%2bNwLlyQi%2fS%2fG7VNP4nBGRDSrwXKZHX8Kp4bvCAH1dJ61s0w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1692 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2608 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2608 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4692 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
4692 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |