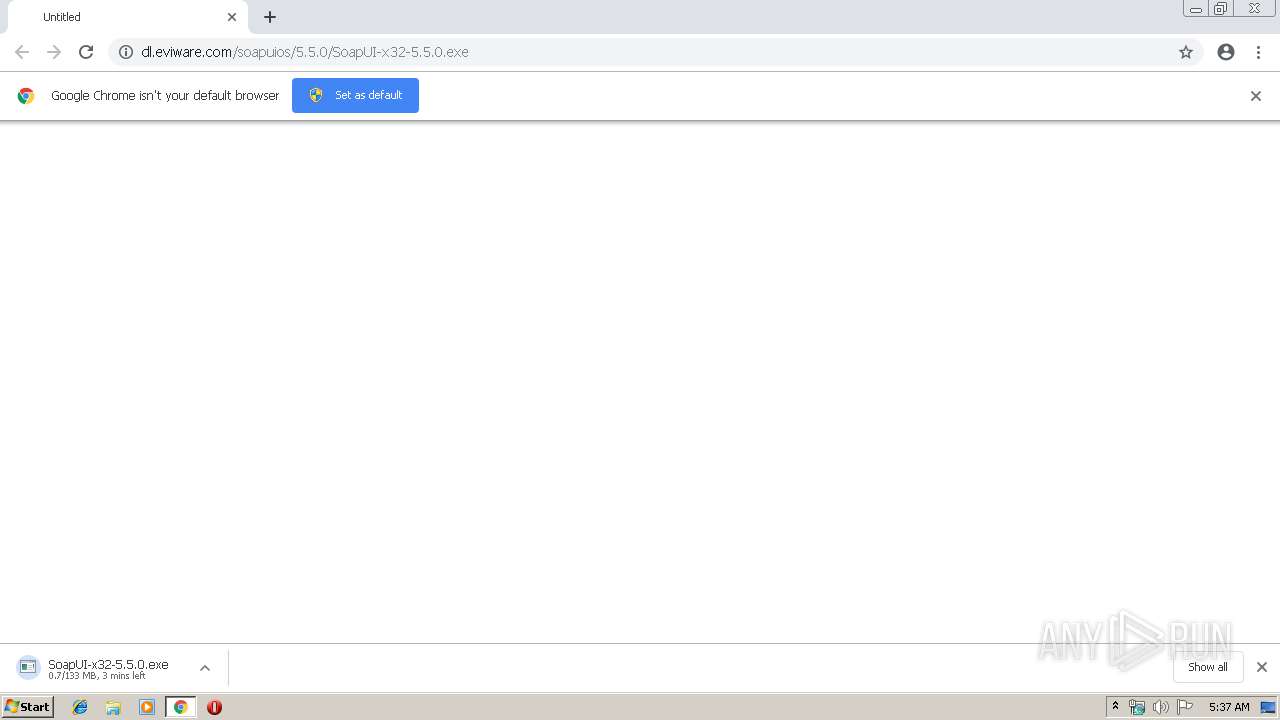
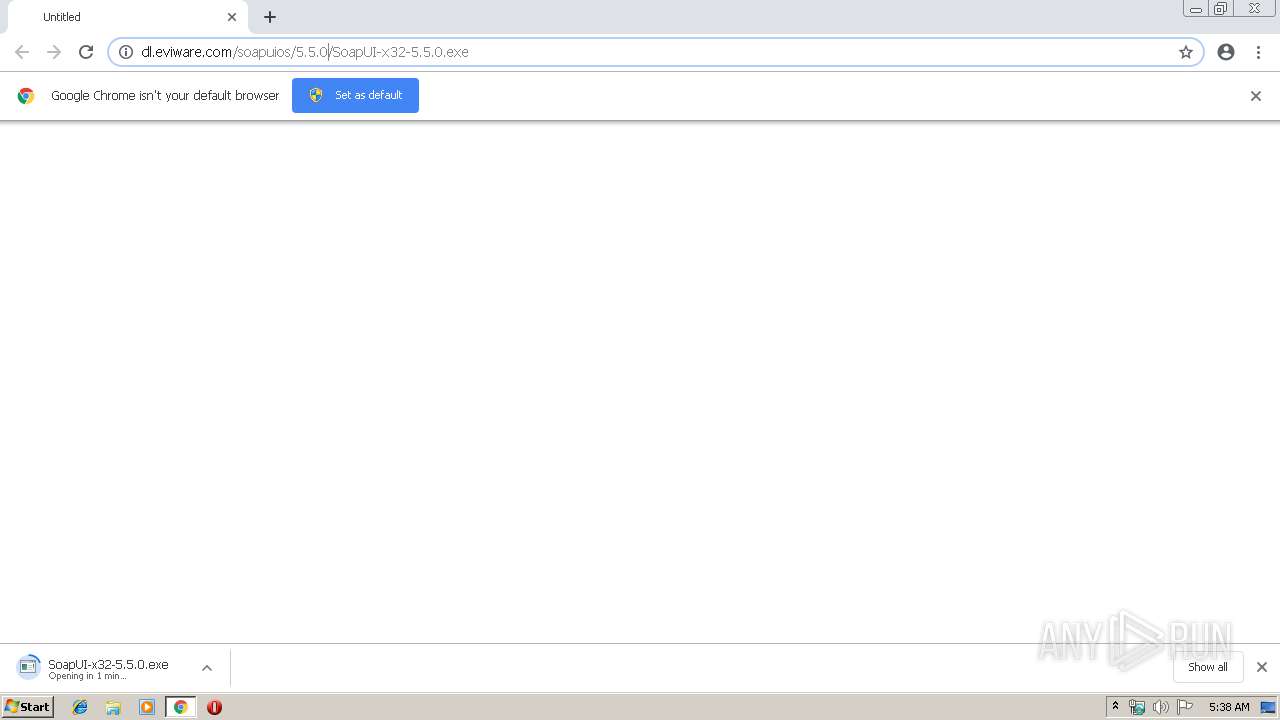
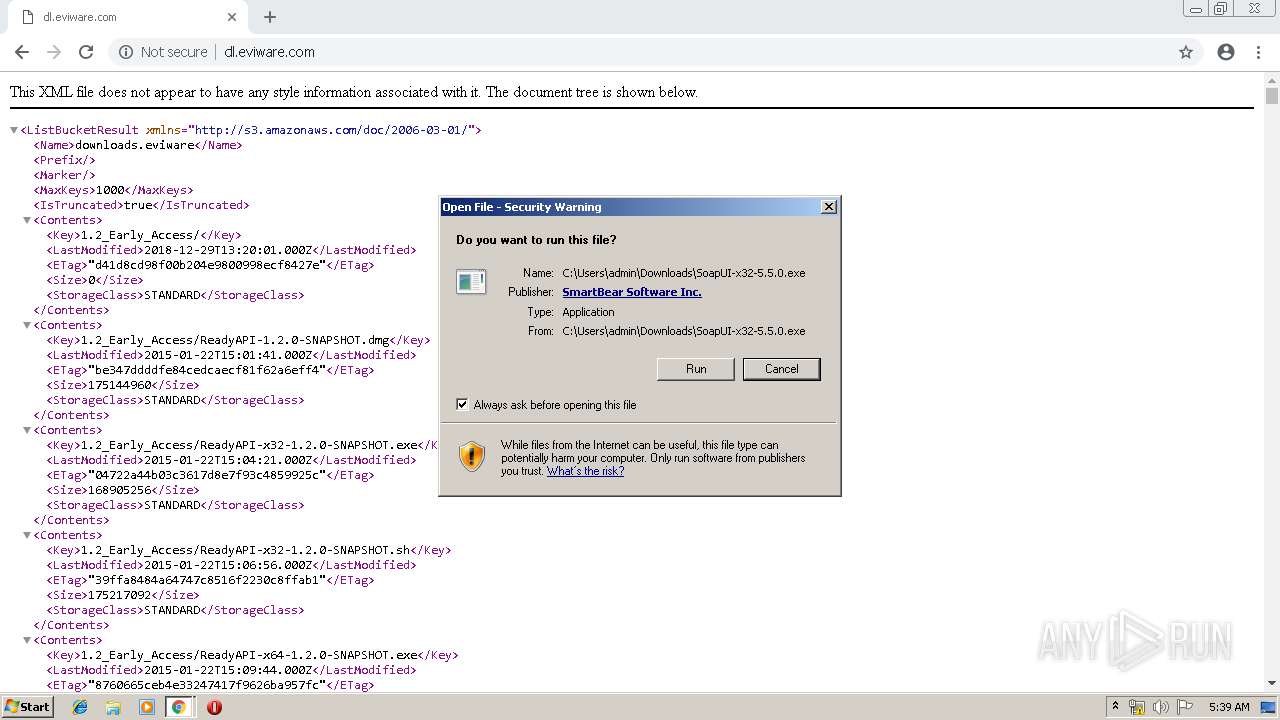
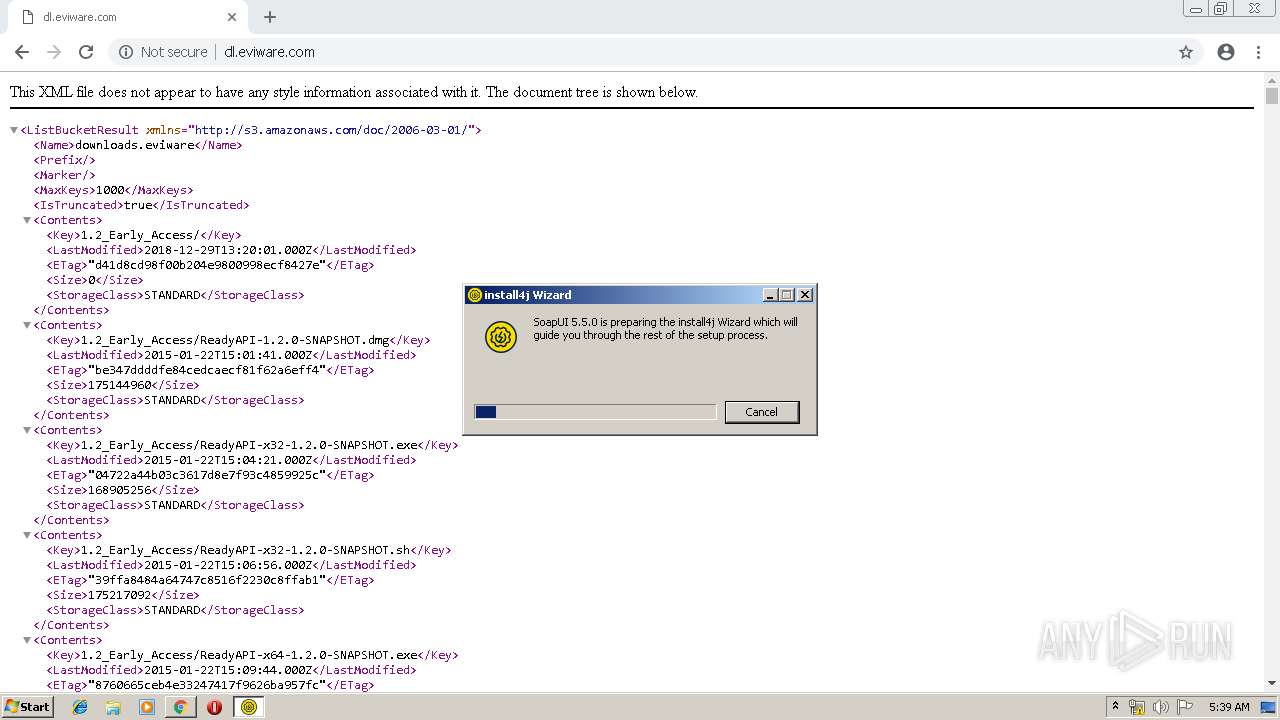
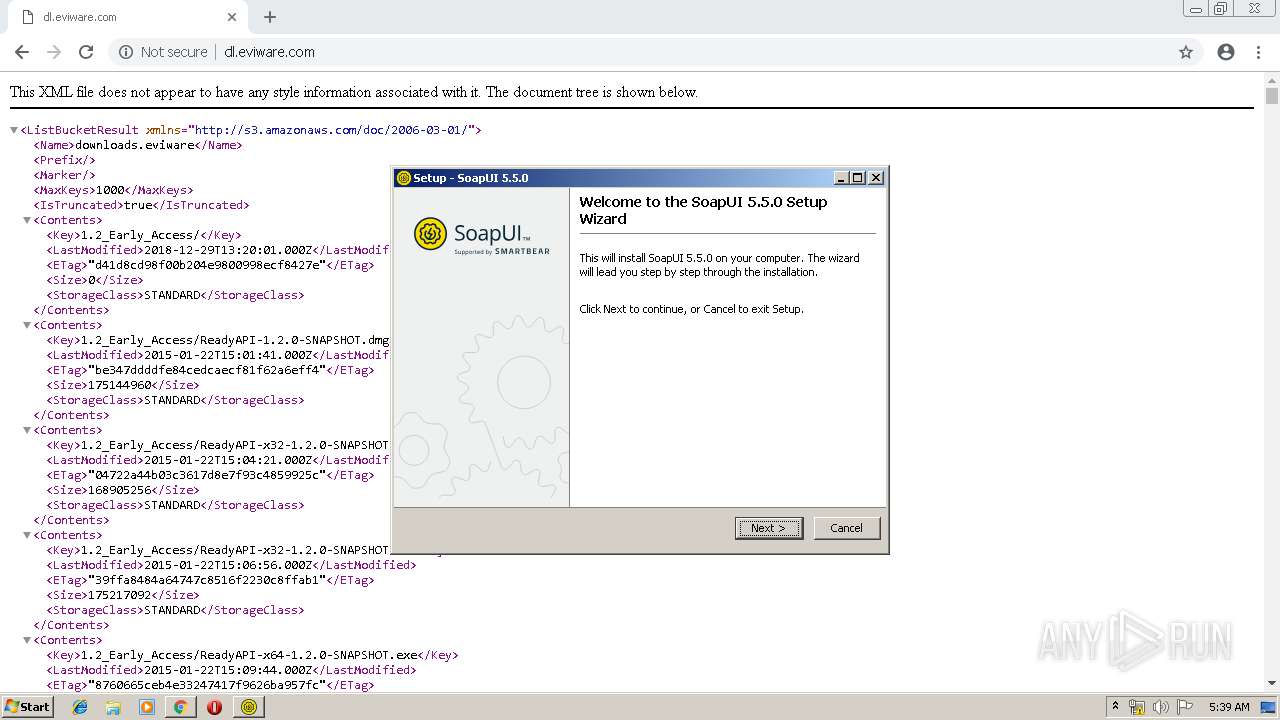
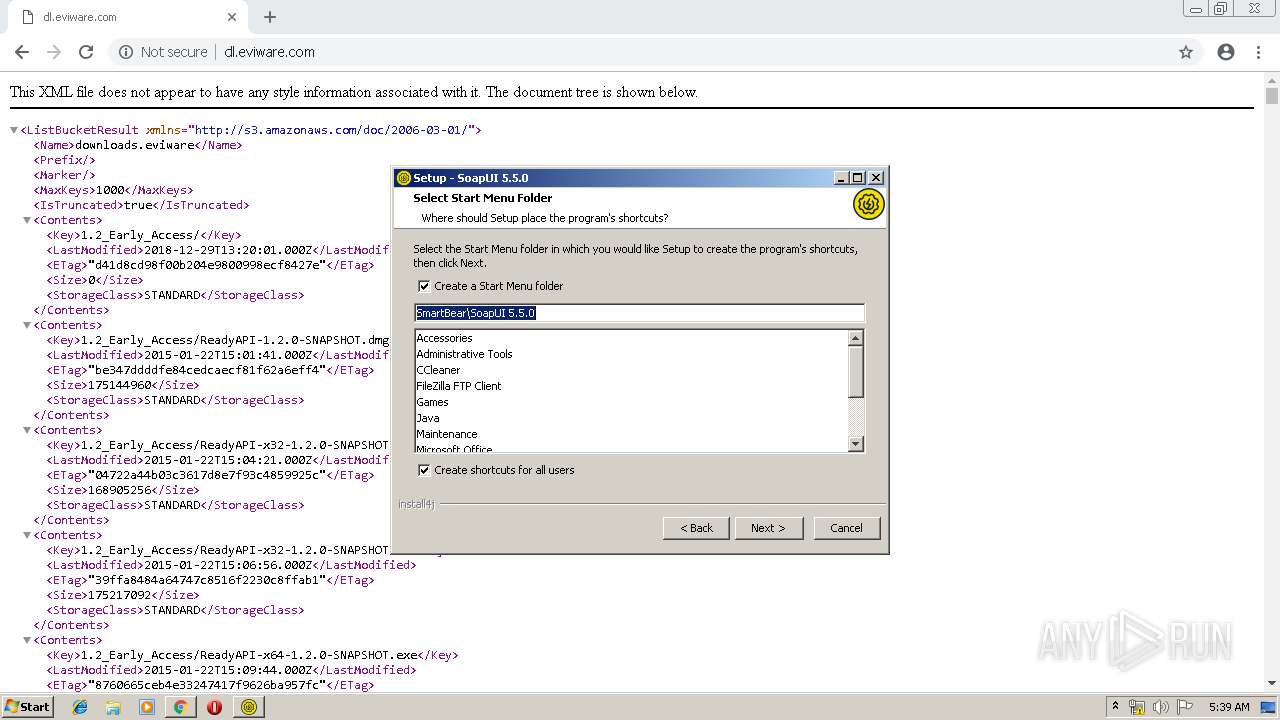
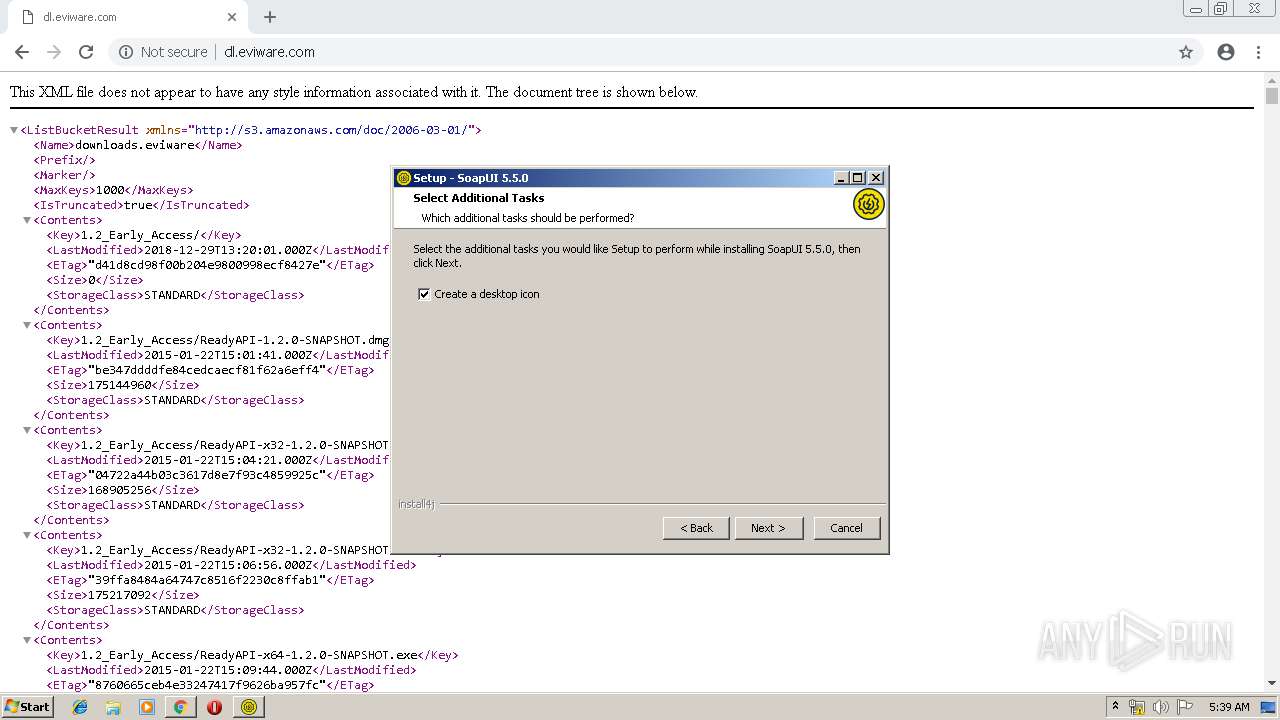
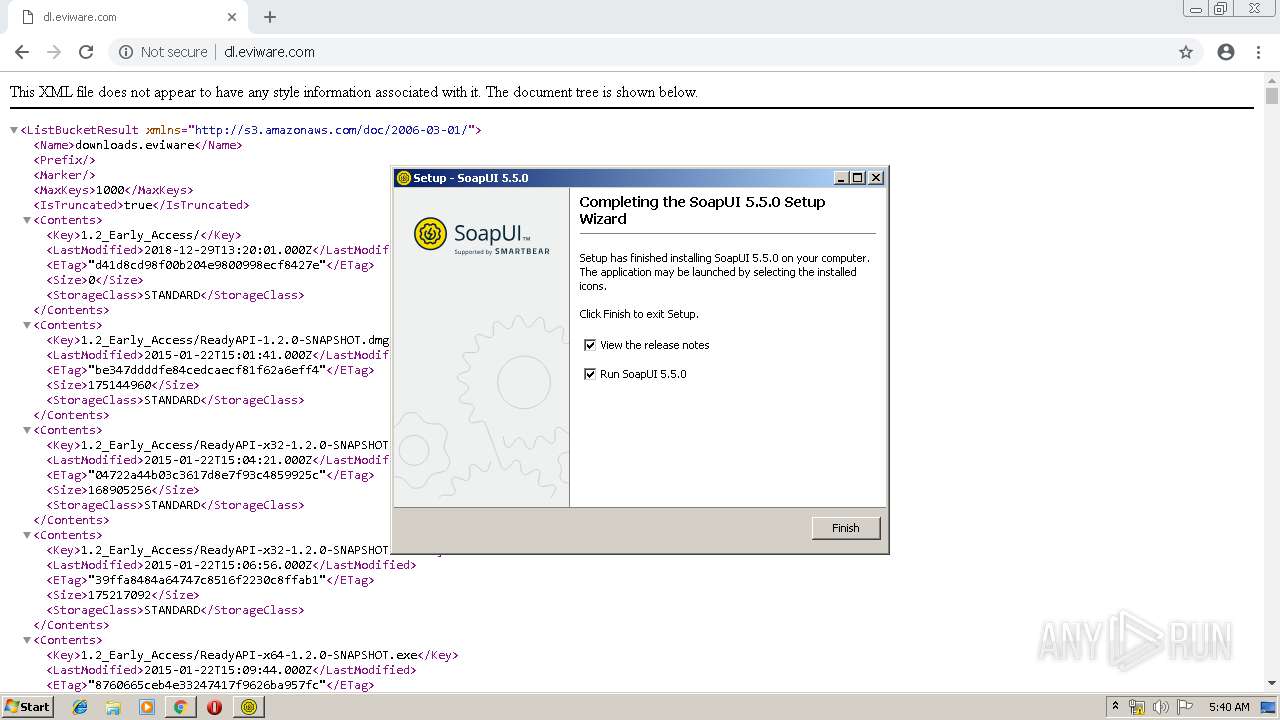
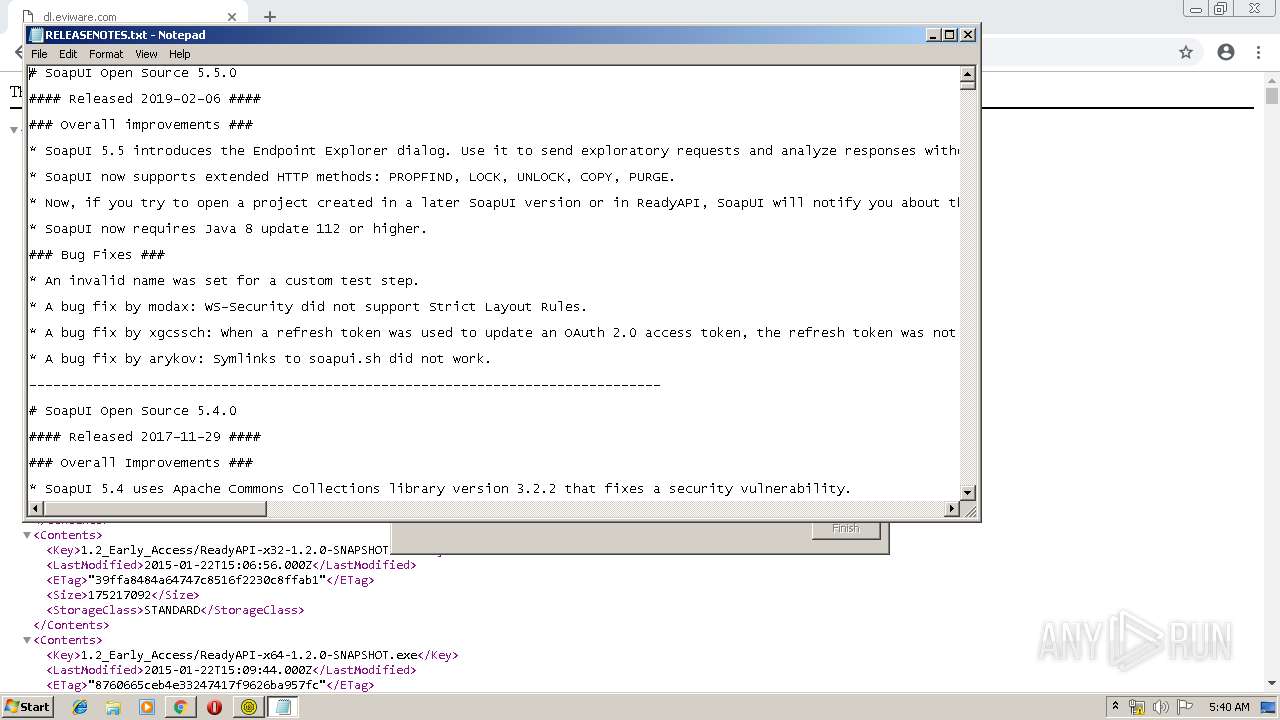
| URL: | http://dl.eviware.com/soapuios/5.5.0/SoapUI-x32-5.5.0.exe |
| Full analysis: | https://app.any.run/tasks/329936c8-9909-4dd5-a394-b65bca6ced96 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 05:37:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 063A9A7240B939E356A71FFE30A6BD13 |
| SHA1: | 7F6A84F6335B3D4EA8EB6D050D28C2AC36C5BA78 |
| SHA256: | A0EBAE64EC1E956FE53076ADBD654D65F49F5652BA491691789956F94C4F64FC |
| SSDEEP: | 3:N1KaJnZKmK8SlwsIdQ5QhkA:CaJX9SqpdQ5QhJ |
MALICIOUS
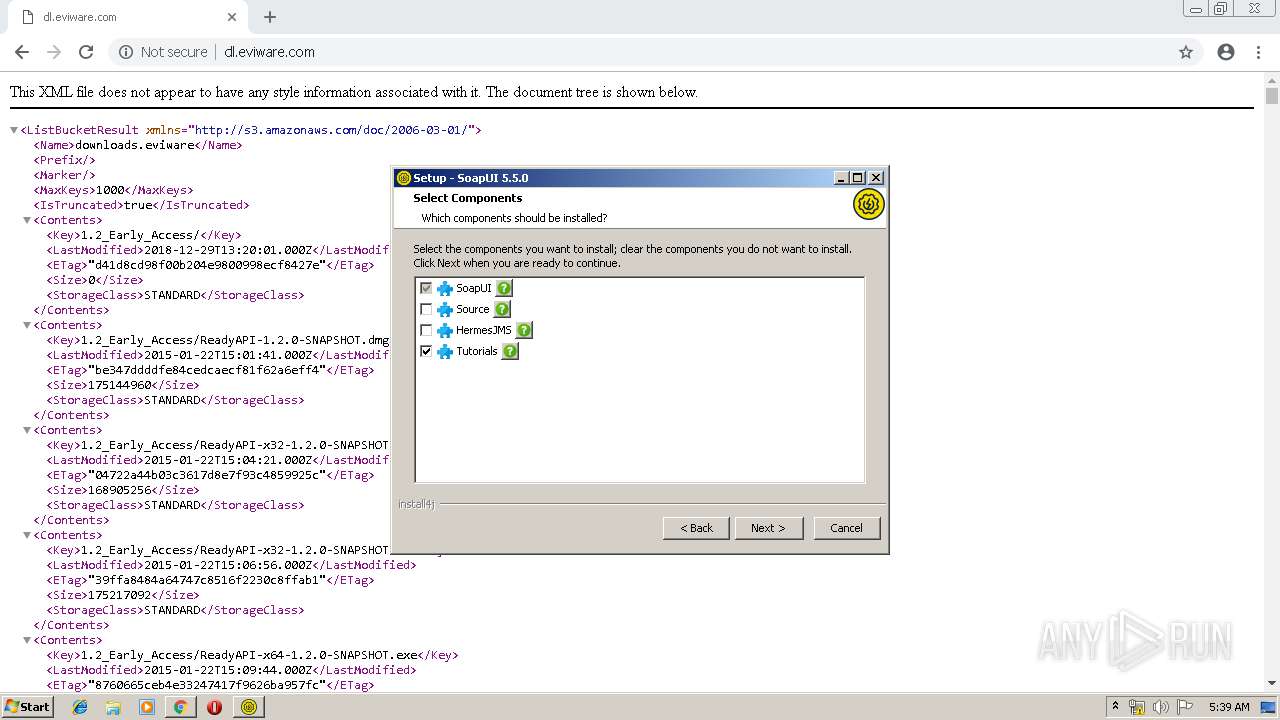
Loads dropped or rewritten executable
- unpack200.exe (PID: 2260)
- unpack200.exe (PID: 2384)
- unpack200.exe (PID: 4016)
- unpack200.exe (PID: 3436)
- unpack200.exe (PID: 3008)
- unpack200.exe (PID: 3320)
- unpack200.exe (PID: 560)
- unpack200.exe (PID: 3168)
- unpack200.exe (PID: 2780)
- unpack200.exe (PID: 3324)
- unpack200.exe (PID: 1936)
- unpack200.exe (PID: 2016)
- SoapUI-x32-5.5.0.exe (PID: 1052)
- SoapUI-x32-5.5.0.exe (PID: 3432)
- unpack200.exe (PID: 2328)
- unpack200.exe (PID: 1144)
- unpack200.exe (PID: 1048)
- java.exe (PID: 2280)
- SoapUI-5.5.0.exe (PID: 3900)
- java.exe (PID: 1180)
- unpack200.exe (PID: 2832)
- java.exe (PID: 2160)
- cmd.exe (PID: 964)
- unpack200.exe (PID: 2632)
- unpack200.exe (PID: 2276)
- javaw.exe (PID: 888)
Application was dropped or rewritten from another process
- SoapUI-x32-5.5.0.exe (PID: 1052)
- unpack200.exe (PID: 3320)
- unpack200.exe (PID: 560)
- unpack200.exe (PID: 3168)
- unpack200.exe (PID: 1144)
- unpack200.exe (PID: 2260)
- unpack200.exe (PID: 2276)
- unpack200.exe (PID: 2632)
- unpack200.exe (PID: 2328)
- unpack200.exe (PID: 2832)
- unpack200.exe (PID: 1048)
- unpack200.exe (PID: 3008)
- unpack200.exe (PID: 2384)
- unpack200.exe (PID: 4016)
- unpack200.exe (PID: 1936)
- unpack200.exe (PID: 3324)
- unpack200.exe (PID: 2780)
- unpack200.exe (PID: 3436)
- java.exe (PID: 2160)
- SoapUI-x32-5.5.0.exe (PID: 3812)
- SoapUI-5.5.0.exe (PID: 3900)
- javaw.exe (PID: 888)
- java.exe (PID: 2280)
- SoapUI-x32-5.5.0.exe (PID: 3432)
- java.exe (PID: 1180)
- unpack200.exe (PID: 2016)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1708)
Executable content was dropped or overwritten
- chrome.exe (PID: 1708)
- SoapUI-x32-5.5.0.exe (PID: 1052)
- SoapUI-5.5.0.exe (PID: 3900)
- SoapUI-x32-5.5.0.exe (PID: 3432)
Uses ICACLS.EXE to modify access control list
- java.exe (PID: 2280)
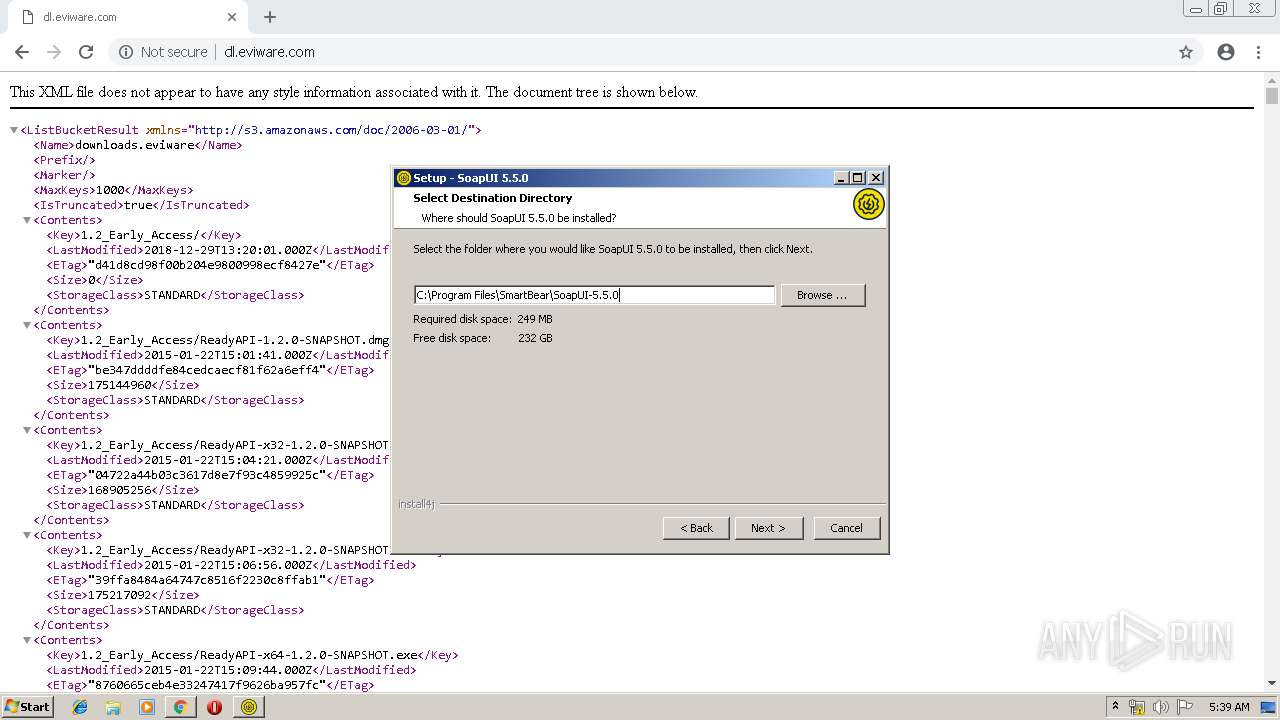
Creates files in the program directory
- java.exe (PID: 2280)
- javaw.exe (PID: 888)
- SoapUI-x32-5.5.0.exe (PID: 3432)
- java.exe (PID: 1180)
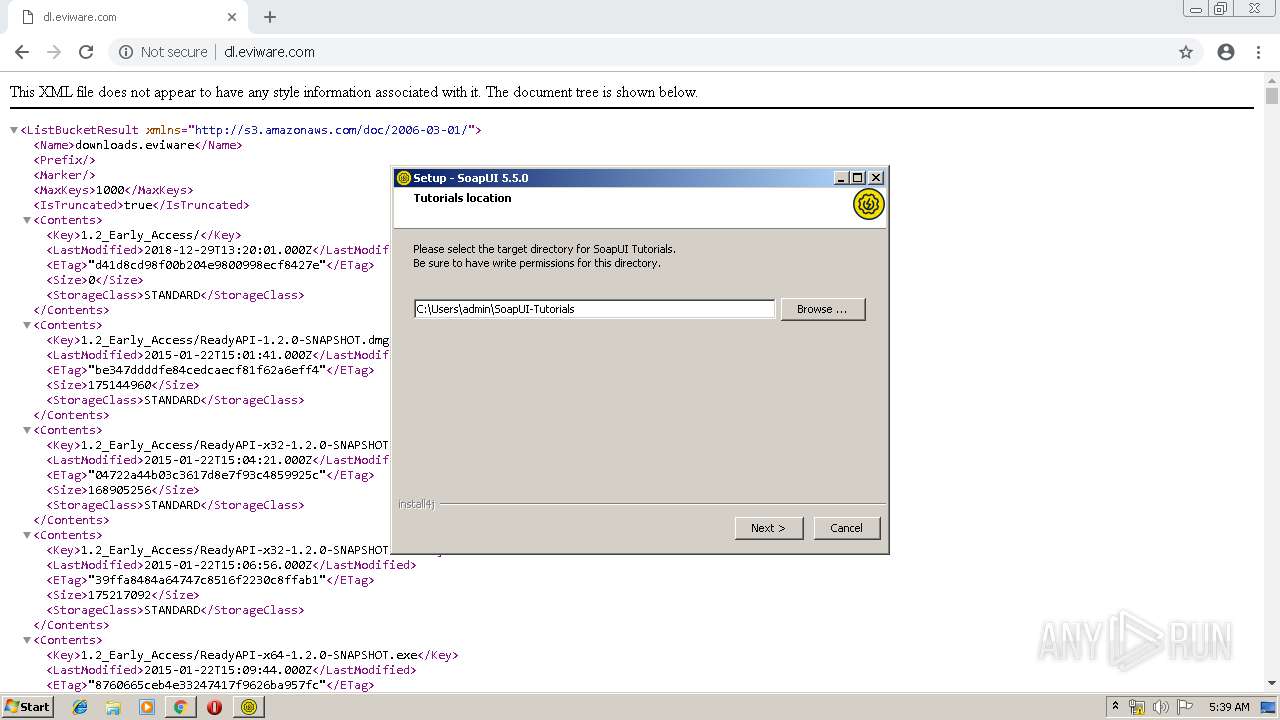
Creates files in the user directory
- SoapUI-x32-5.5.0.exe (PID: 1052)
- SoapUI-5.5.0.exe (PID: 3900)
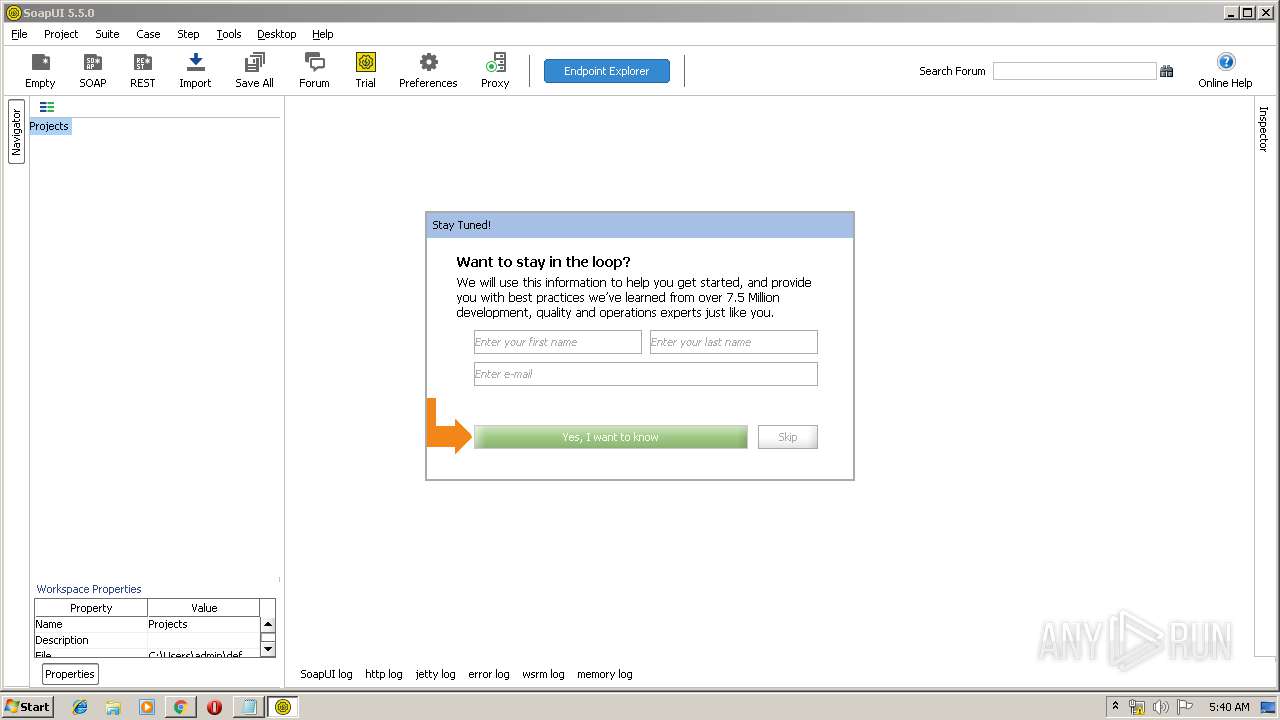
Searches for installed software
- SoapUI-x32-5.5.0.exe (PID: 3432)
Starts CMD.EXE for commands execution
- SoapUI-x32-5.5.0.exe (PID: 1052)
- SoapUI-x32-5.5.0.exe (PID: 3432)
Application launched itself
- SoapUI-x32-5.5.0.exe (PID: 1052)
Creates a software uninstall entry
- SoapUI-x32-5.5.0.exe (PID: 3432)
INFO
Application launched itself
- chrome.exe (PID: 1708)
Dropped object may contain Bitcoin addresses
- SoapUI-x32-5.5.0.exe (PID: 1052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
47
Malicious processes
10
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12557945561294777422 --mojo-platform-channel-handle=3172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
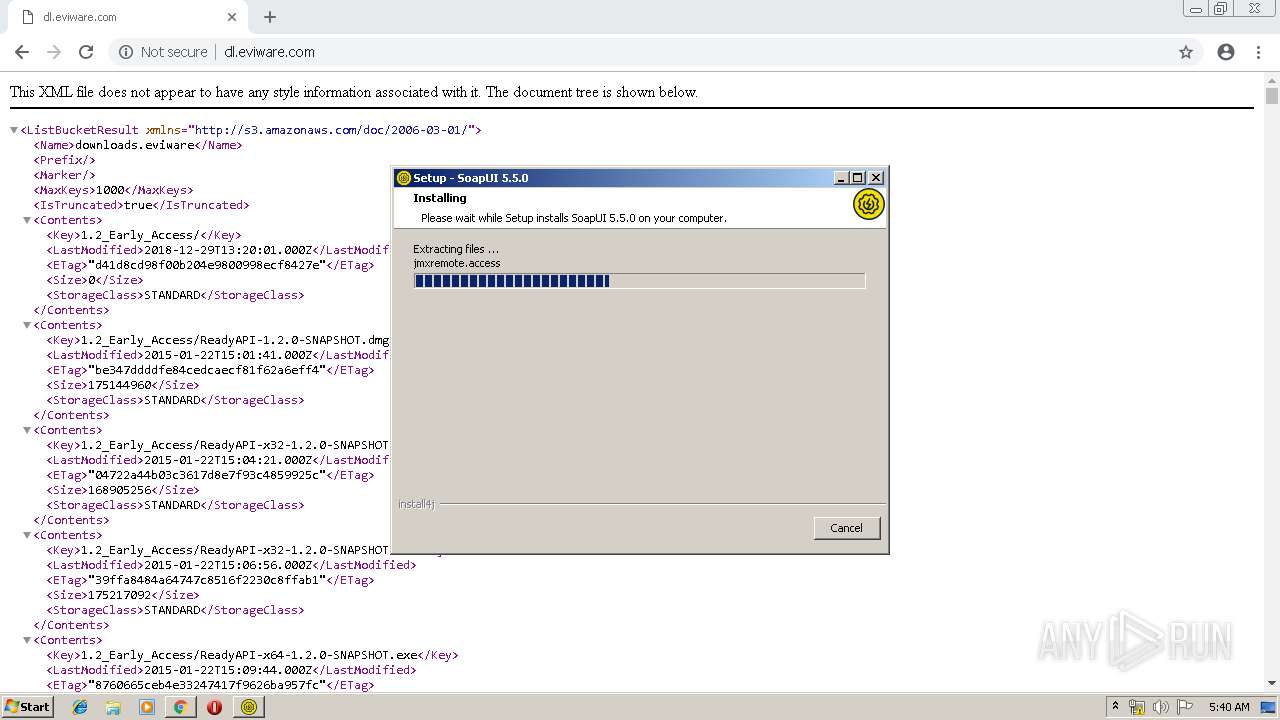
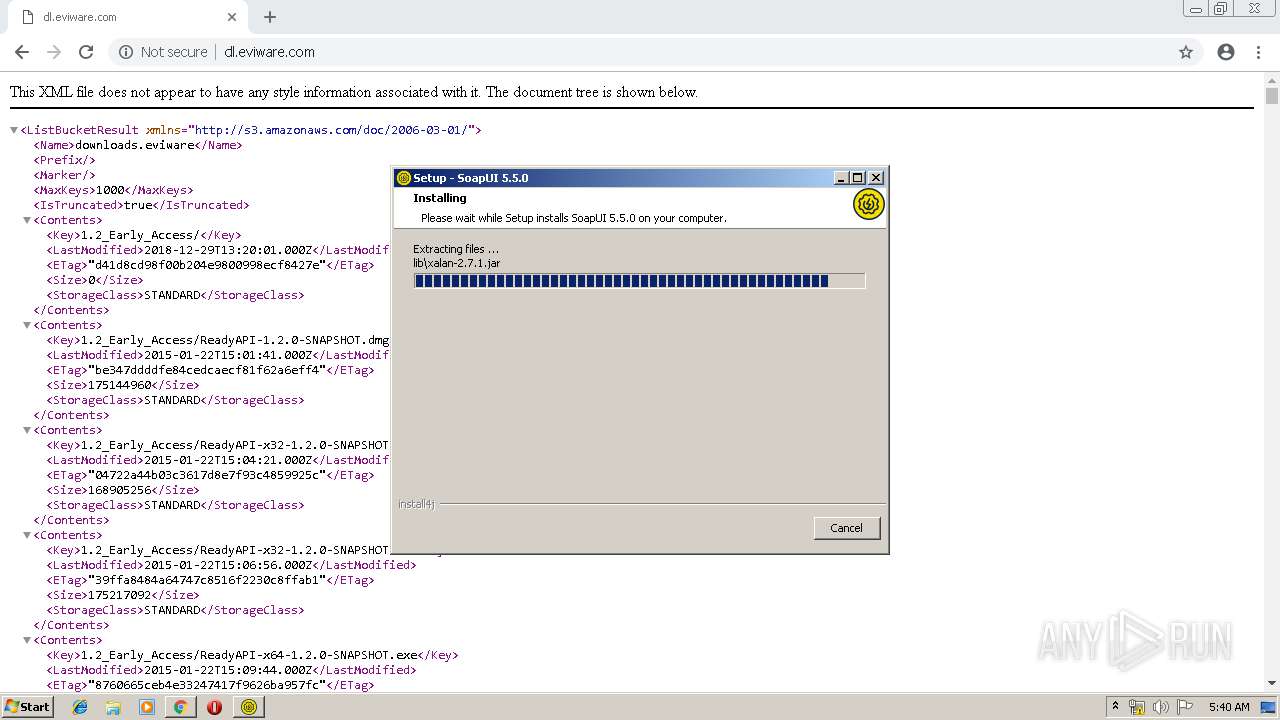
| 560 | -r "jre\lib\jfr.jar.pack" "jre\lib\jfr.jar" | C:\Users\admin\AppData\Local\Temp\e4jFE38.tmp_dir1553146766\jre\bin\unpack200.exe | — | SoapUI-x32-5.5.0.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1810.13 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4268689619836751399 --mojo-platform-channel-handle=2740 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 888 | "C:\Program Files\SmartBear\SoapUI-5.5.0\jre\bin\javaw.exe" -Xshare:dump | C:\Program Files\SmartBear\SoapUI-5.5.0\jre\bin\javaw.exe | — | SoapUI-x32-5.5.0.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1810.13 Modules
| |||||||||||||||
| 964 | C:\Windows\system32\cmd.exe /D /C C:\Users\admin\AppData\Local\Temp\i4j5451156446709607480.bat | C:\Windows\system32\cmd.exe | — | SoapUI-x32-5.5.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1048 | -r "jre\lib\rt.jar.pack" "jre\lib\rt.jar" | C:\Users\admin\AppData\Local\Temp\e4jFE38.tmp_dir1553146766\jre\bin\unpack200.exe | — | SoapUI-x32-5.5.0.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1810.13 Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\Downloads\SoapUI-x32-5.5.0.exe" | C:\Users\admin\Downloads\SoapUI-x32-5.5.0.exe | chrome.exe | ||||||||||||
User: admin Company: SmartBear Software Integrity Level: MEDIUM Description: SoapUI 5.5.0 Exit code: 0 Version: 5.5.0 Modules
| |||||||||||||||
| 1144 | -r "jre\lib\jsse.jar.pack" "jre\lib\jsse.jar" | C:\Users\admin\AppData\Local\Temp\e4jFE38.tmp_dir1553146766\jre\bin\unpack200.exe | — | SoapUI-x32-5.5.0.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1810.13 Modules
| |||||||||||||||
| 1180 | c:\PROGRA~1\SMARTB~1\SOAPUI~1.0\jre\bin\java.exe -version | c:\PROGRA~1\SMARTB~1\SOAPUI~1.0\jre\bin\java.exe | — | SoapUI-5.5.0.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1810.13 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10020157524976597362 --mojo-platform-channel-handle=3024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 554
Read events
1 432
Write events
116
Delete events
6
Modification events
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1708-13197620269678500 |
Value: 259 | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1708) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
385
Suspicious files
162
Text files
544
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fd83e5f2-e0aa-4b24-86f4-512d39398dd1.tmp | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1708 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
13
DNS requests
9
Threats
2
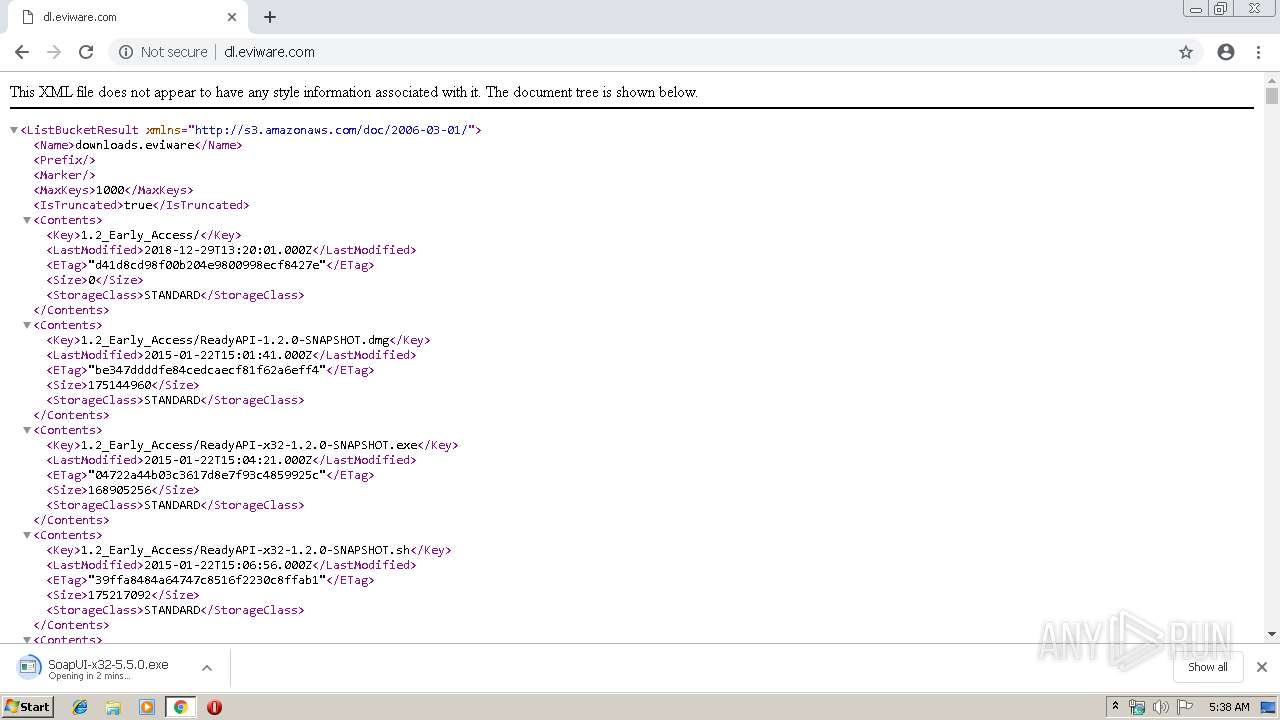
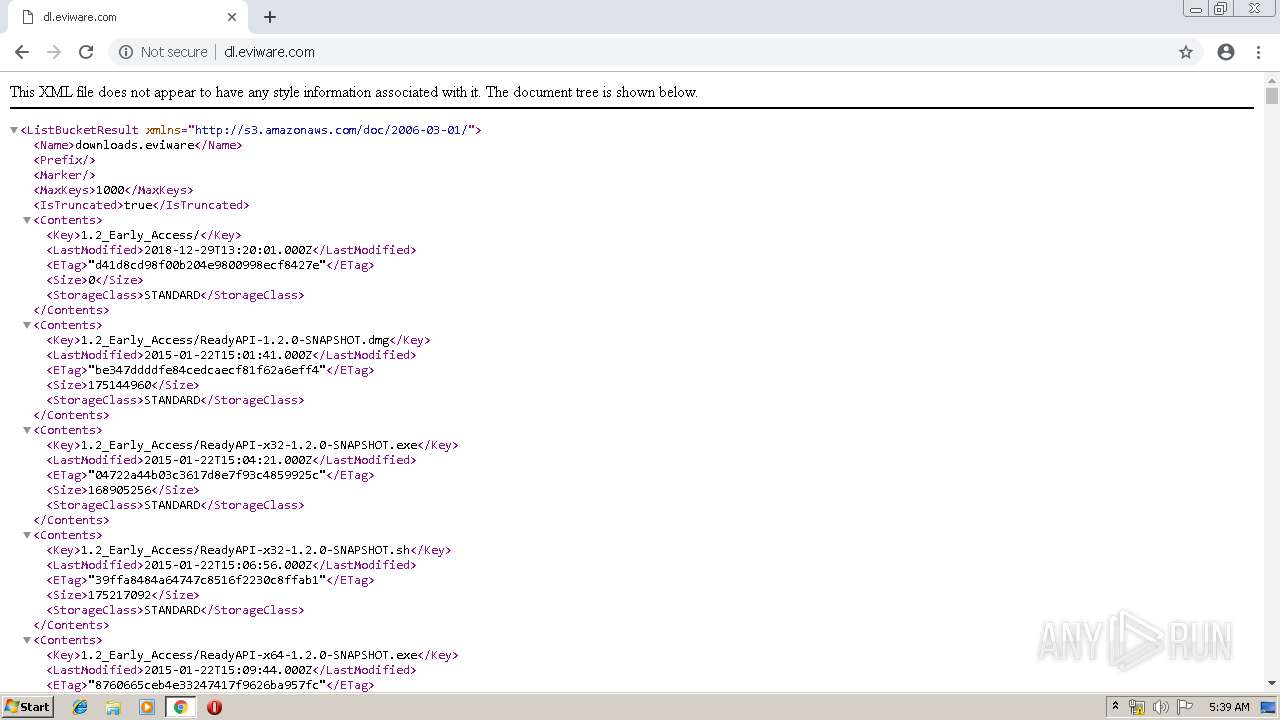
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
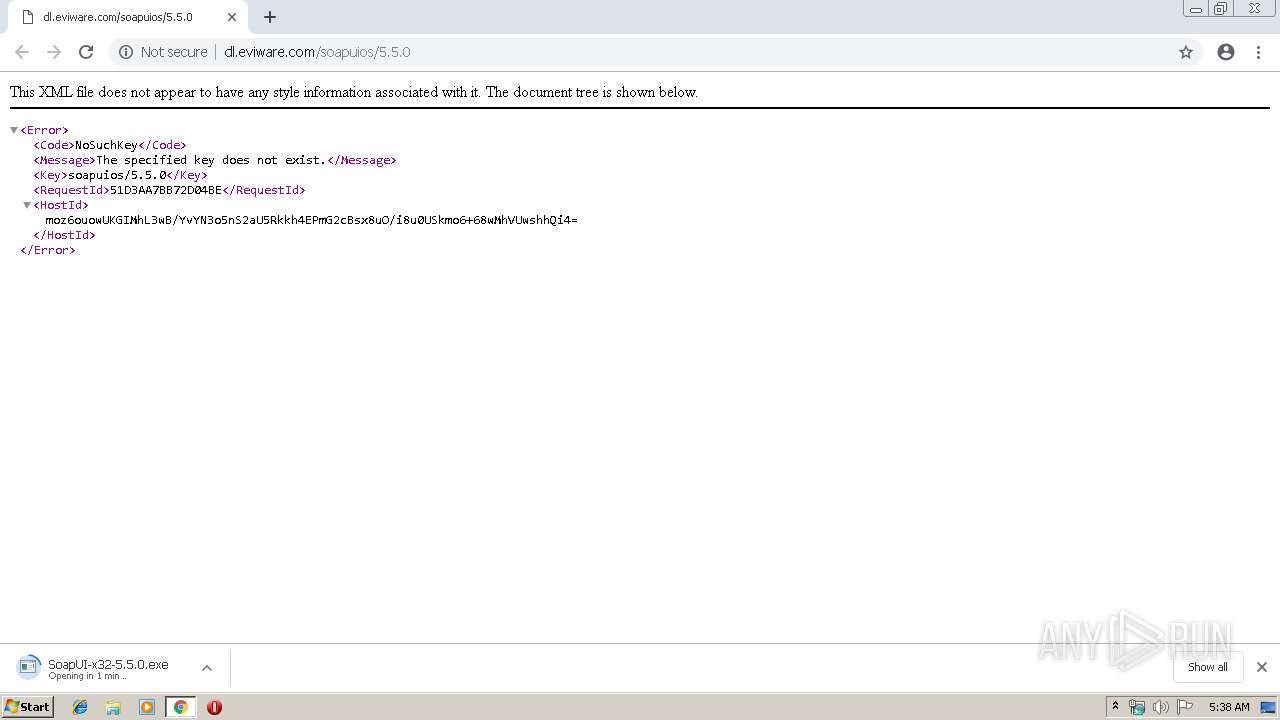
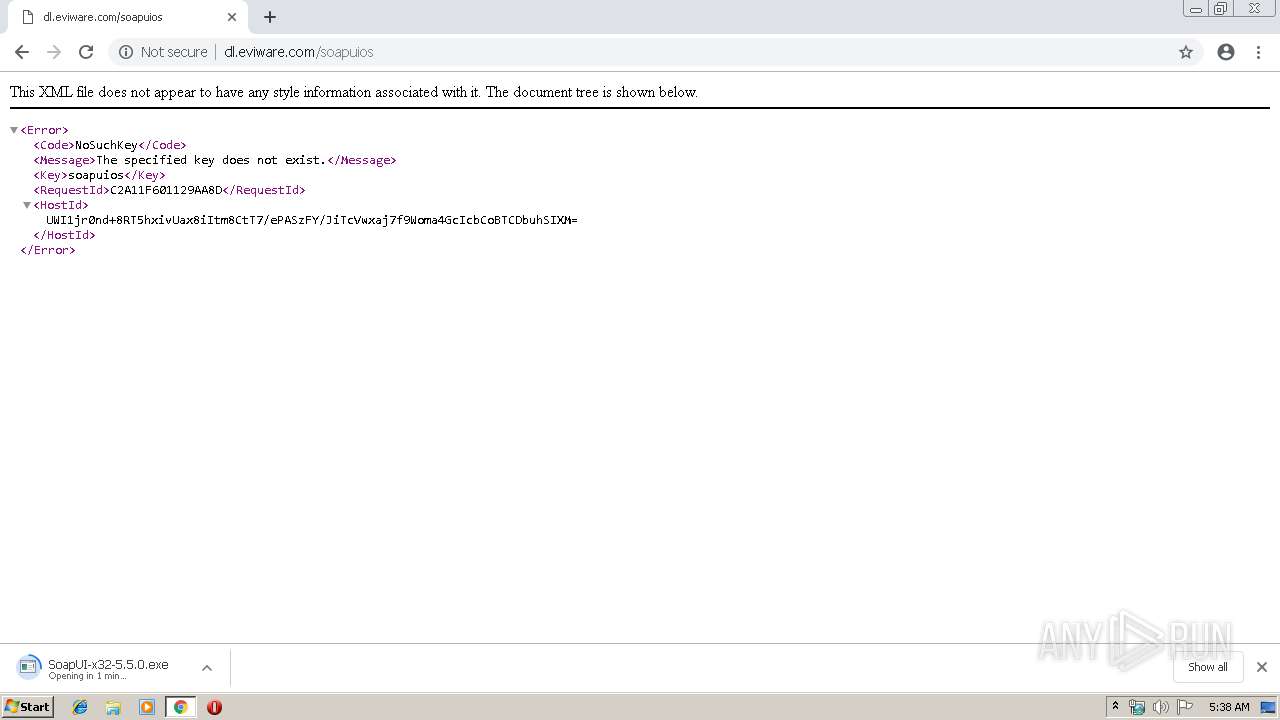
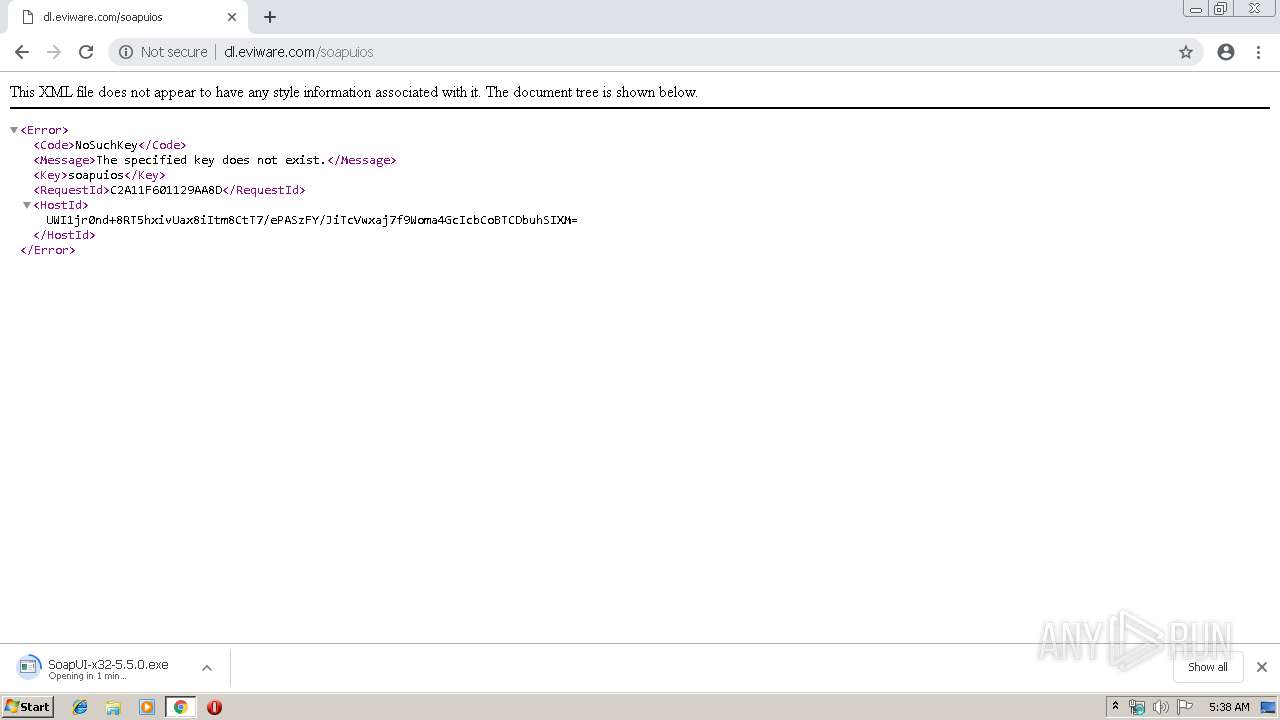
3420 | chrome.exe | GET | 404 | 52.85.221.37:80 | http://dl.eviware.com/favicon.ico | US | xml | 282 b | whitelisted |
3420 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
3420 | chrome.exe | GET | 404 | 52.85.221.37:80 | http://dl.eviware.com/soapuios | US | xml | 279 b | whitelisted |
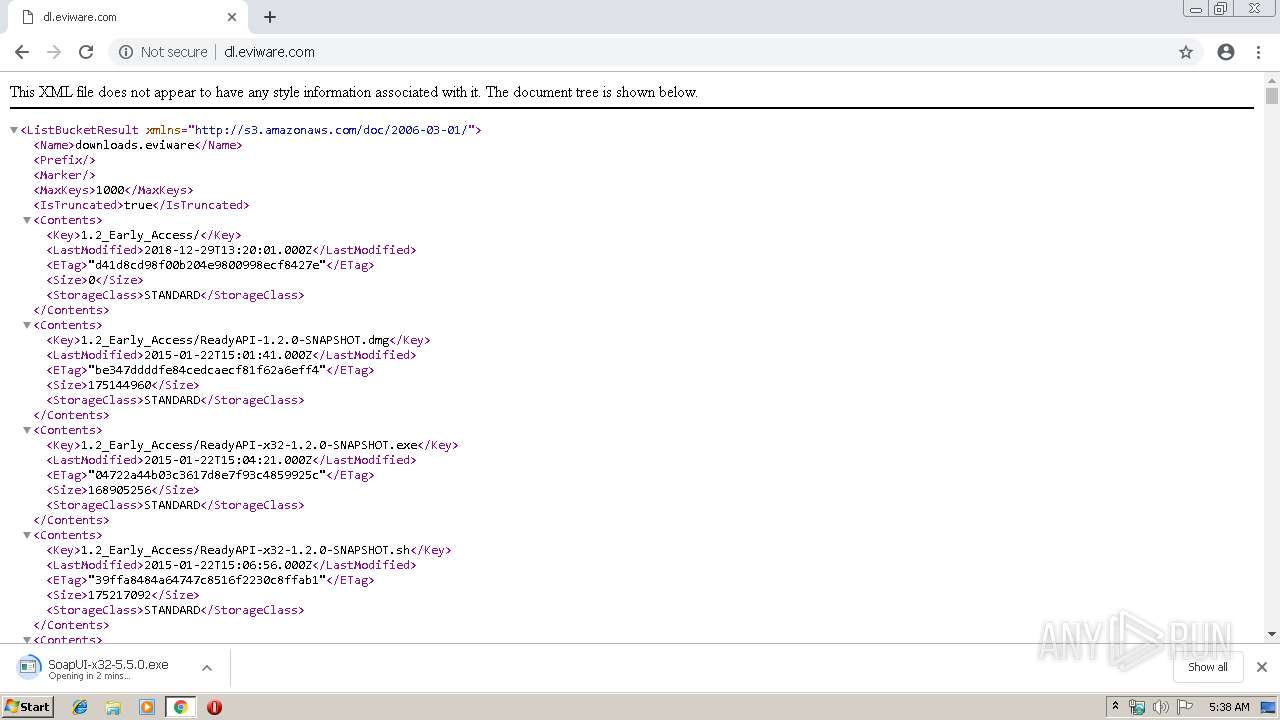
3420 | chrome.exe | GET | 200 | 52.85.221.37:80 | http://dl.eviware.com/ | US | xml | 254 Kb | whitelisted |
3420 | chrome.exe | GET | 200 | 74.125.173.166:80 | http://r1---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.83&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1553146577&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3420 | chrome.exe | GET | — | 52.85.221.37:80 | http://dl.eviware.com/soapuios/5.5.0/SoapUI-x32-5.5.0.exe | US | — | — | whitelisted |
3420 | chrome.exe | GET | 404 | 52.85.221.37:80 | http://dl.eviware.com/soapuios/5.5.0 | US | xml | 285 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3420 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 216.58.207.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 74.125.173.166:80 | r1---sn-1gieen7e.gvt1.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 52.85.221.37:80 | dl.eviware.com | Amazon.com, Inc. | US | suspicious |
3420 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.eviware.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-1gieen7e.gvt1.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3420 | chrome.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
3420 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |