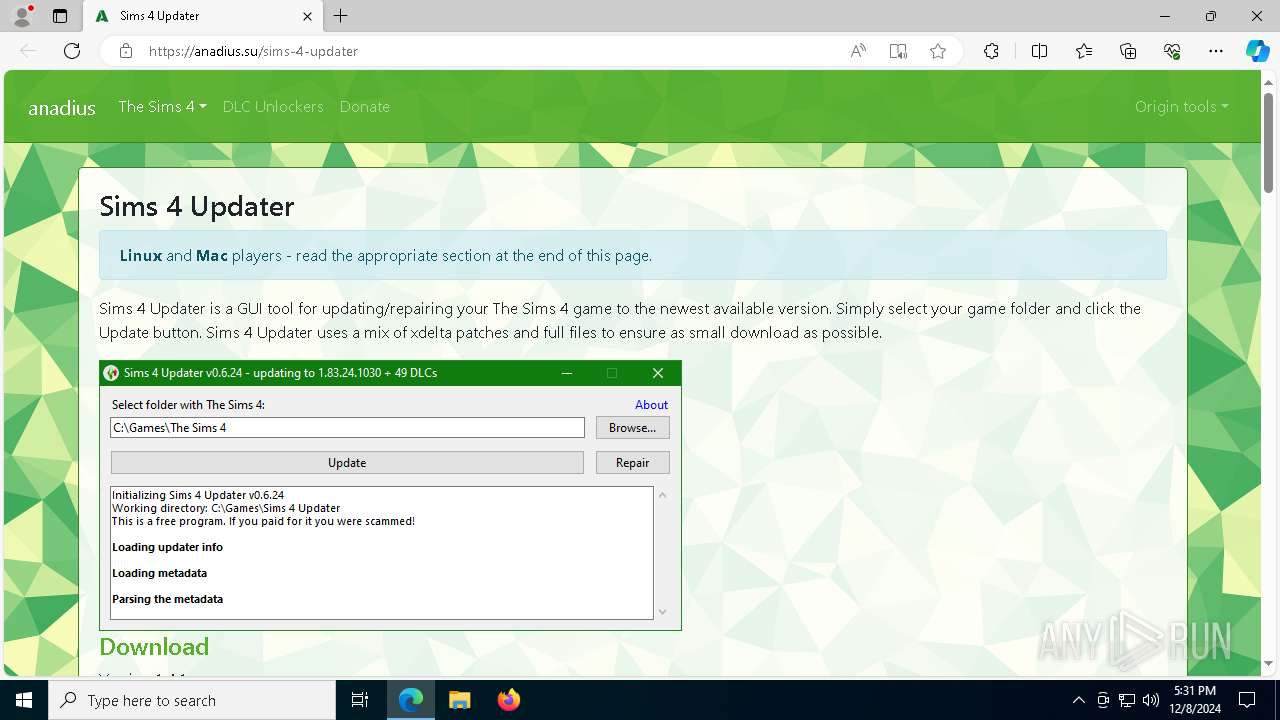
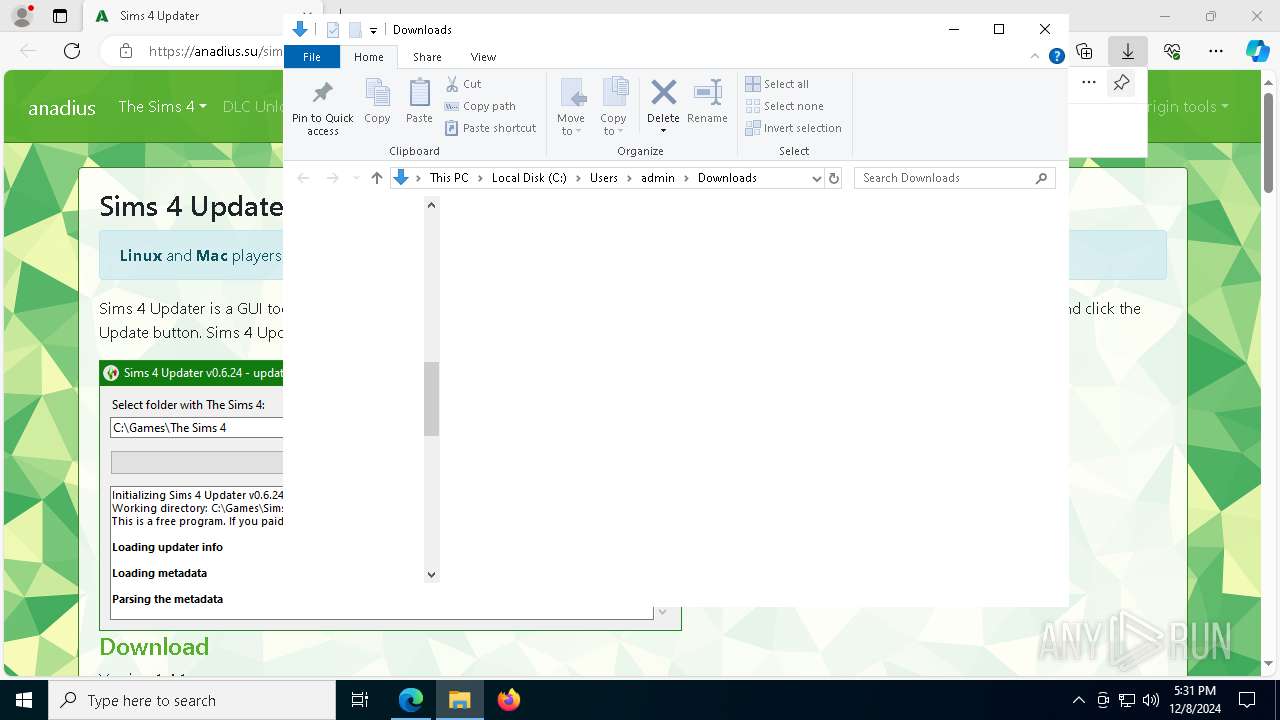
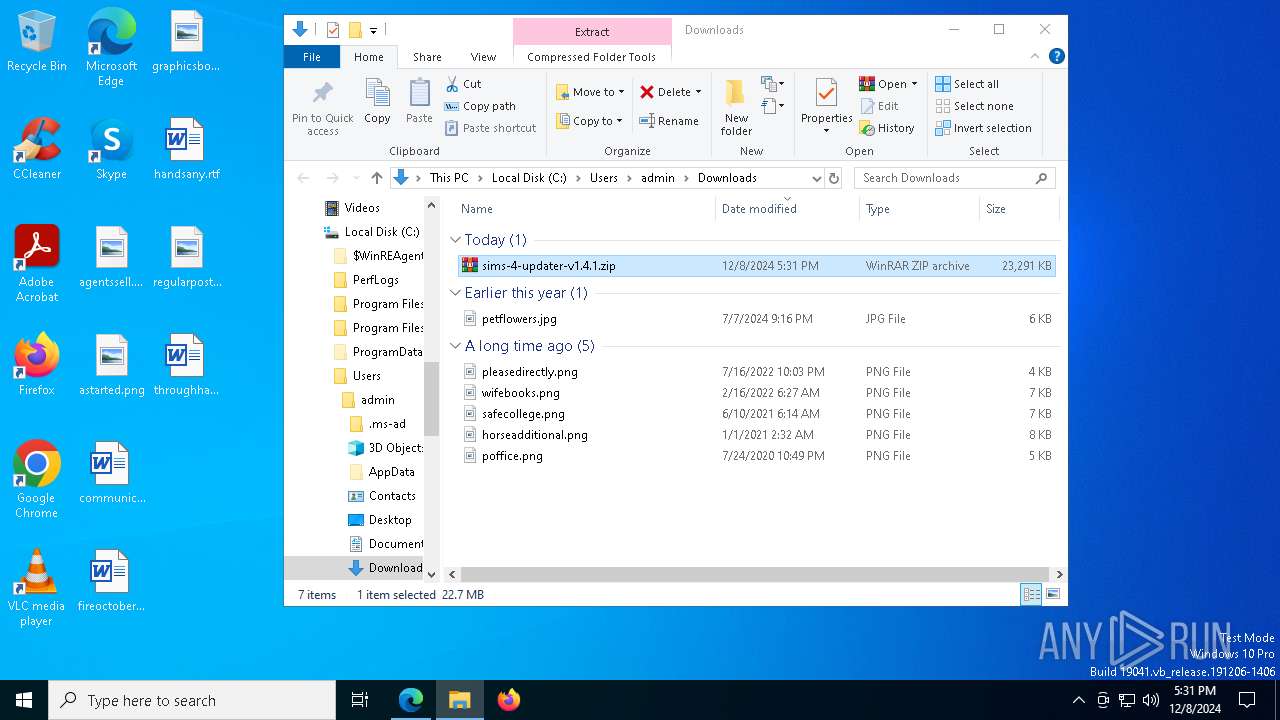
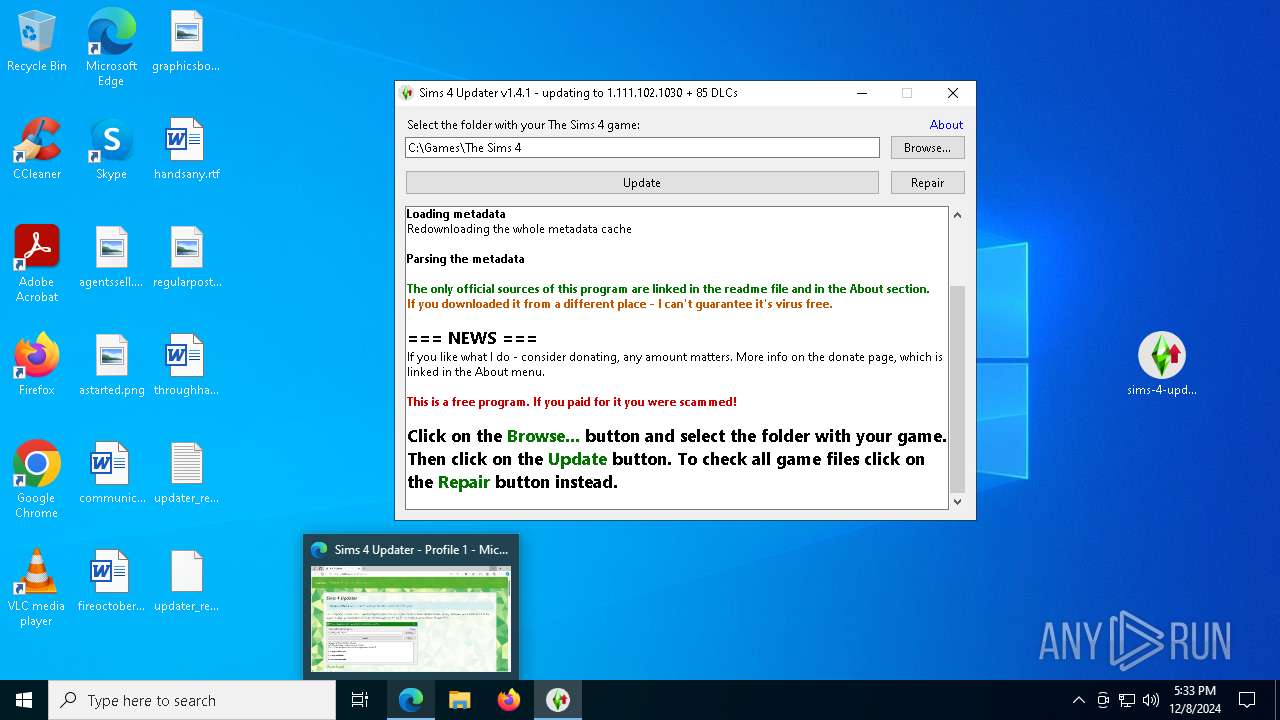
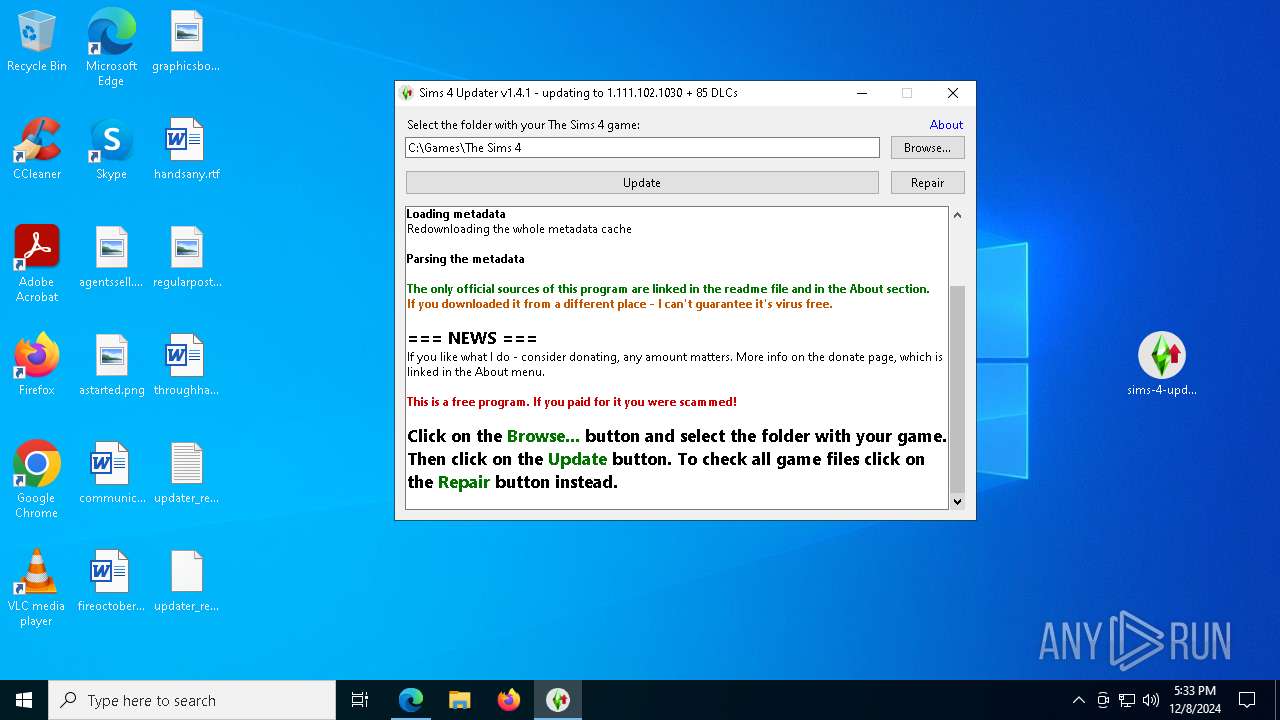
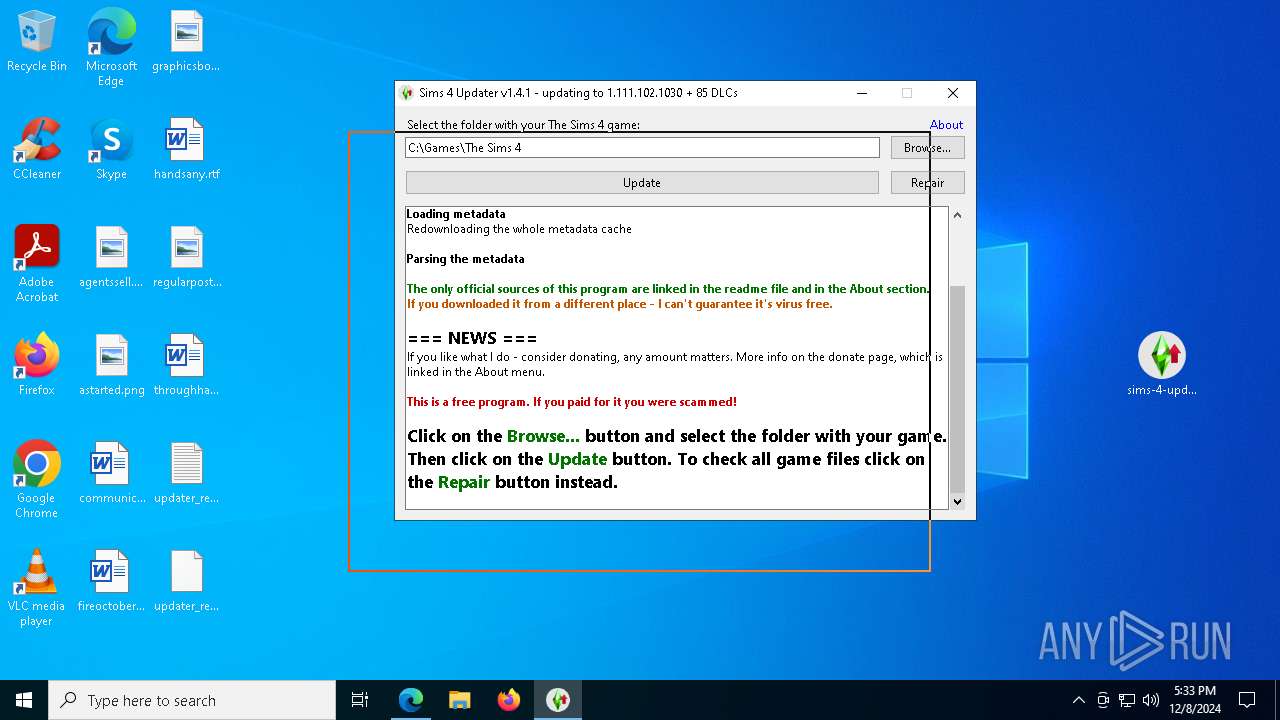
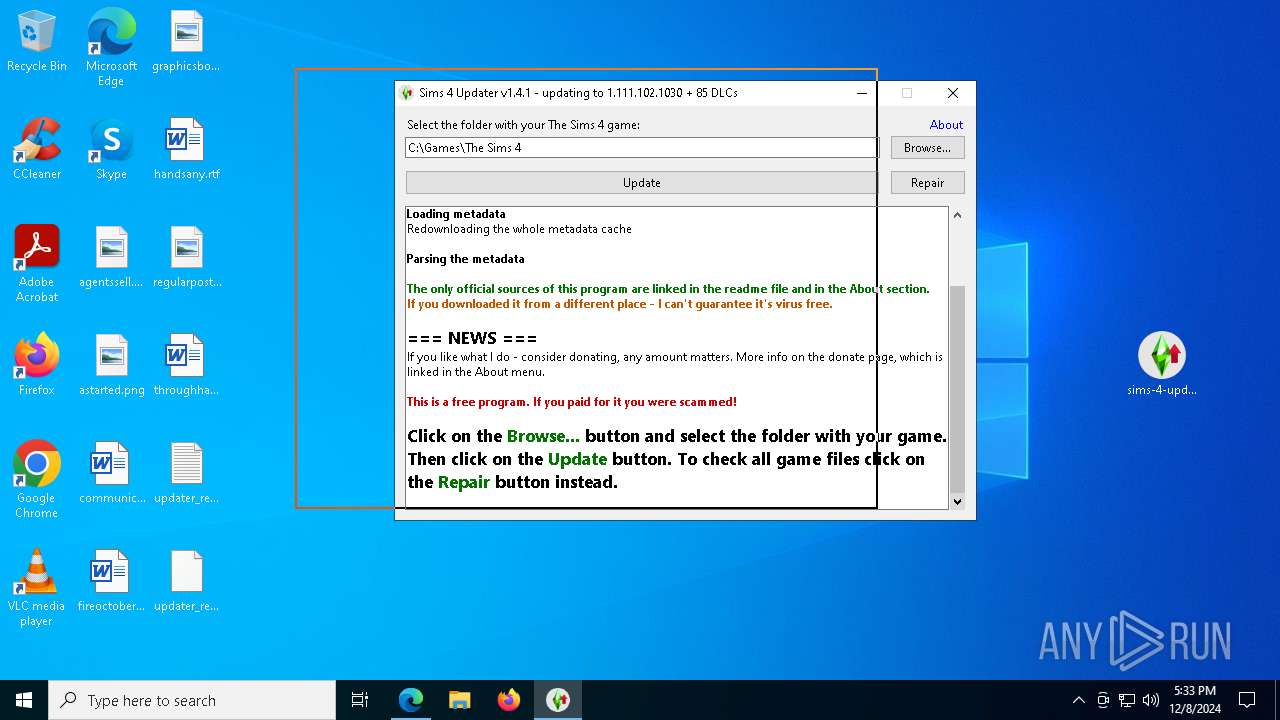
| URL: | https://anadius.su/sims-4-updater |
| Full analysis: | https://app.any.run/tasks/a40d56d8-4bfb-4ae0-a663-e4f2d88d0dc8 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2024, 17:31:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EE4D81BE70C48FE95642798144A91C26 |
| SHA1: | 4BEC542D542F7D7E5F39F4FDE49EFEC59D5E5EA0 |
| SHA256: | A0E8F455220880512354B4E6DCCECCDA67F168B7D5A554BCD9C90BAE7D449980 |
| SSDEEP: | 3:N8HMQAXPRIQQg:2H6Im |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- sims-4-updater-v1.4.1.exe (PID: 5880)
Process drops legitimate windows executable
- sims-4-updater-v1.4.1.exe (PID: 5880)
Process drops python dynamic module
- sims-4-updater-v1.4.1.exe (PID: 5880)
Executable content was dropped or overwritten
- sims-4-updater-v1.4.1.exe (PID: 5880)
Application launched itself
- sims-4-updater-v1.4.1.exe (PID: 5880)
Loads Python modules
- sims-4-updater-v1.4.1.exe (PID: 2200)
Reads security settings of Internet Explorer
- sims-4-updater-v1.4.1.exe (PID: 2200)
Reads the date of Windows installation
- sims-4-updater-v1.4.1.exe (PID: 2200)
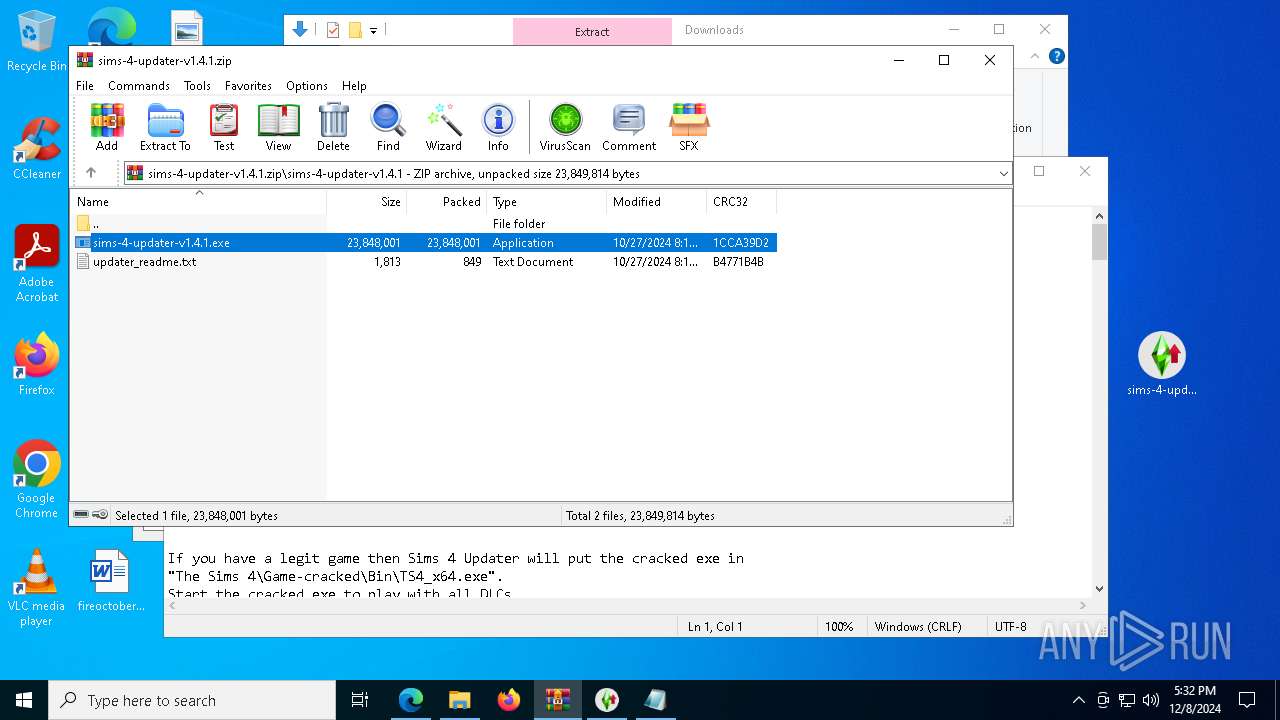
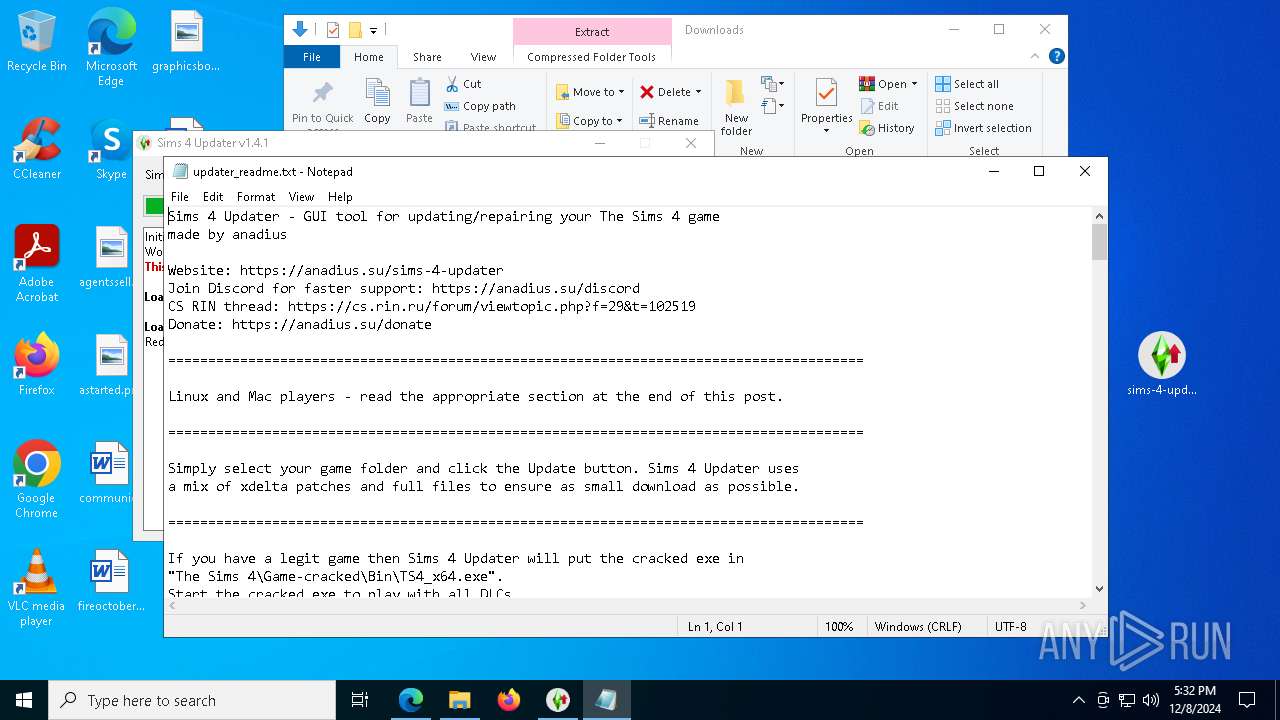
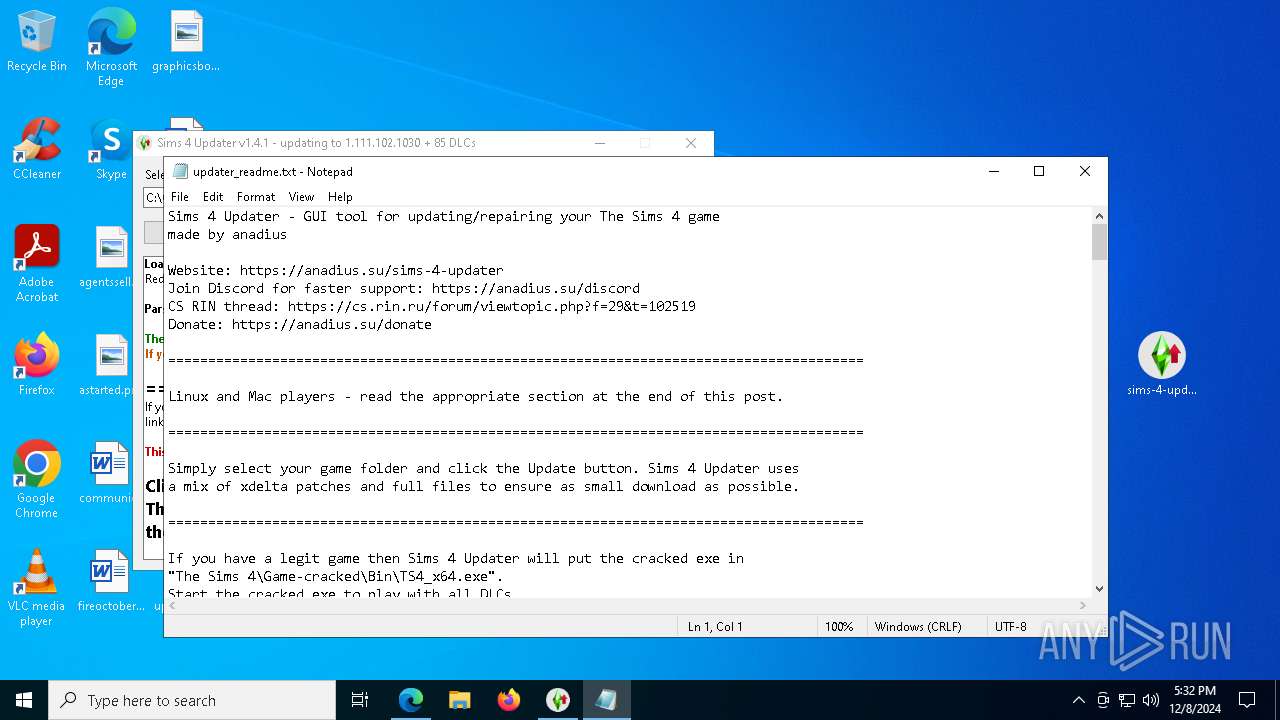
Start notepad (likely ransomware note)
- sims-4-updater-v1.4.1.exe (PID: 2200)
INFO
Reads the computer name
- sims-4-updater-v1.4.1.exe (PID: 5880)
- sims-4-updater-v1.4.1.exe (PID: 2200)
Executable content was dropped or overwritten
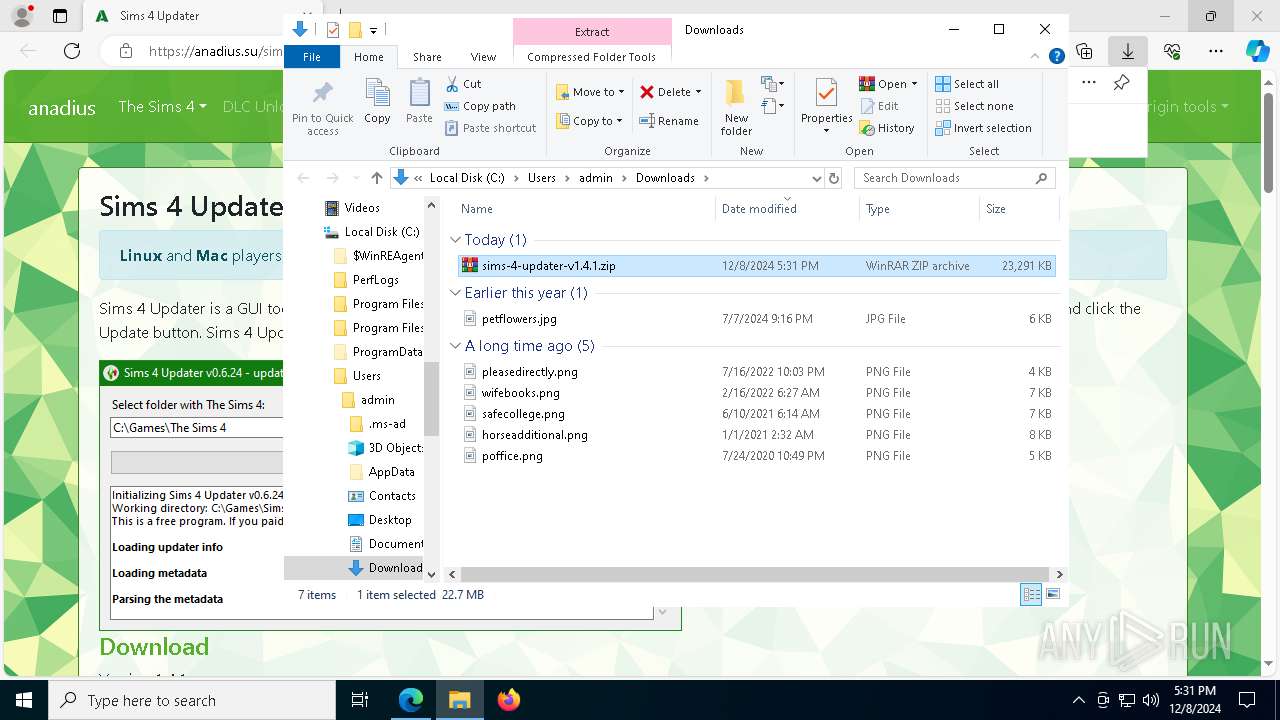
- WinRAR.exe (PID: 7608)
Checks supported languages
- sims-4-updater-v1.4.1.exe (PID: 5880)
- sims-4-updater-v1.4.1.exe (PID: 2200)
Create files in a temporary directory
- sims-4-updater-v1.4.1.exe (PID: 5880)
- sims-4-updater-v1.4.1.exe (PID: 2200)
The process uses the downloaded file
- WinRAR.exe (PID: 7608)
- sims-4-updater-v1.4.1.exe (PID: 2200)
PyInstaller has been detected (YARA)
- sims-4-updater-v1.4.1.exe (PID: 5880)
Process checks computer location settings
- sims-4-updater-v1.4.1.exe (PID: 2200)
Reads the machine GUID from the registry
- sims-4-updater-v1.4.1.exe (PID: 2200)
Checks proxy server information
- sims-4-updater-v1.4.1.exe (PID: 2200)
Reads Microsoft Office registry keys
- sims-4-updater-v1.4.1.exe (PID: 2200)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
183
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | "C:\Users\admin\Desktop\sims-4-updater-v1.4.1.exe" | C:\Users\admin\Desktop\sims-4-updater-v1.4.1.exe | sims-4-updater-v1.4.1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2216 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\updater_readme.txt | C:\Windows\System32\notepad.exe | — | sims-4-updater-v1.4.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
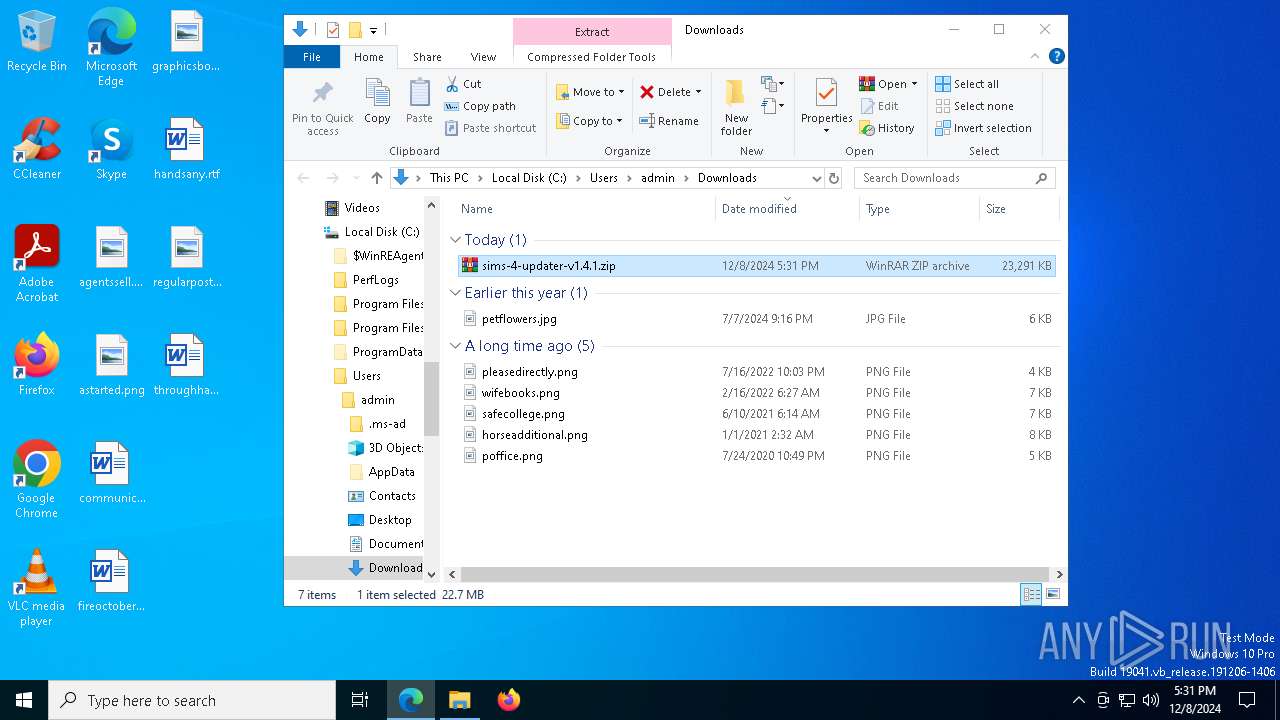
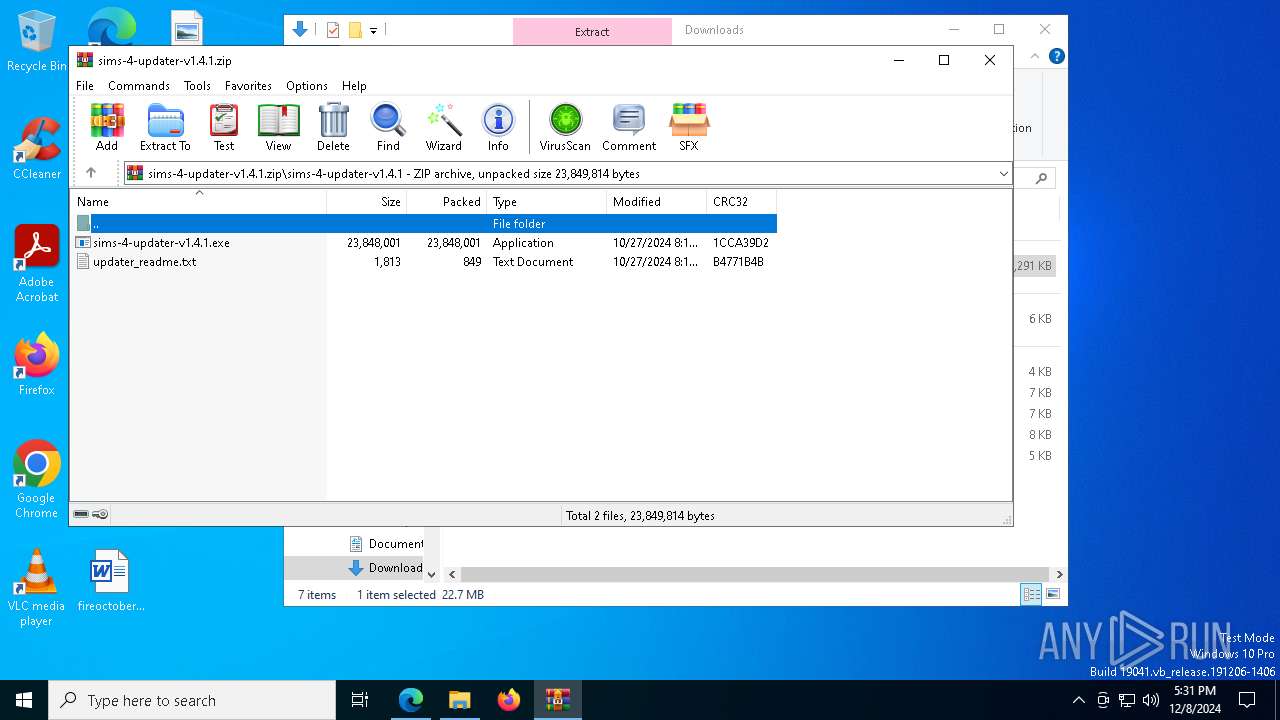
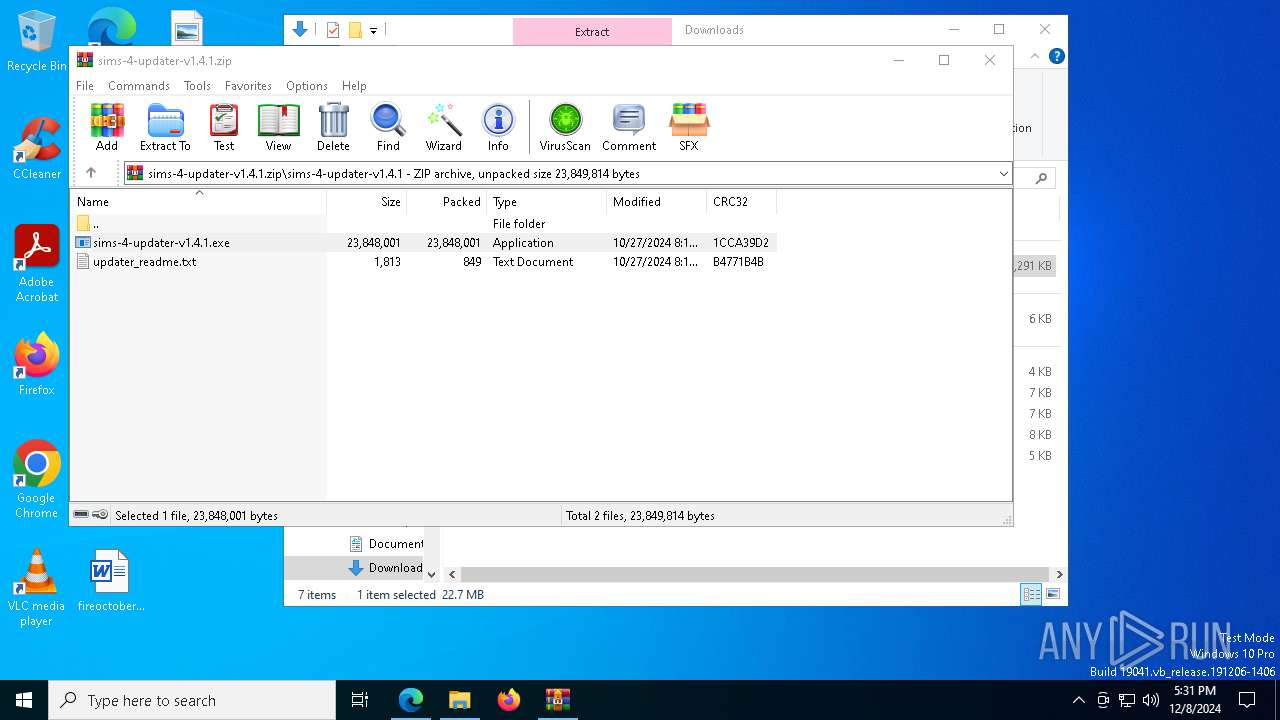
| 5880 | "C:\Users\admin\Desktop\sims-4-updater-v1.4.1.exe" | C:\Users\admin\Desktop\sims-4-updater-v1.4.1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
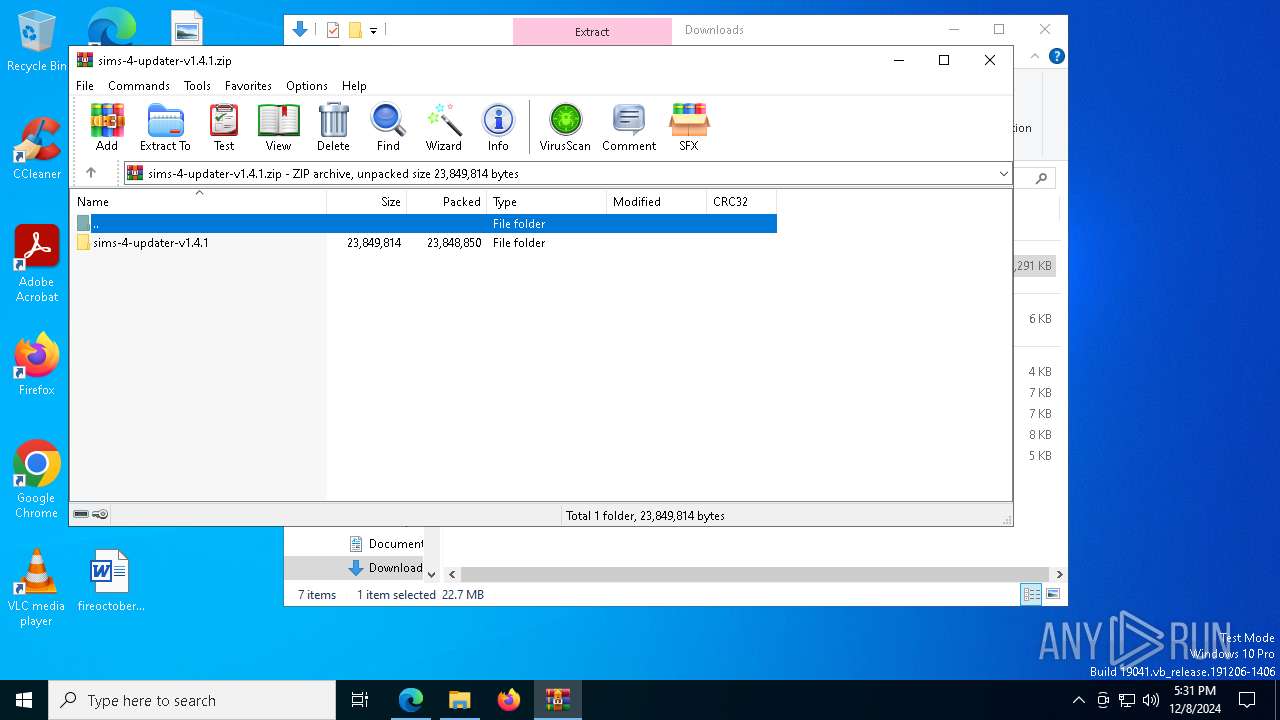
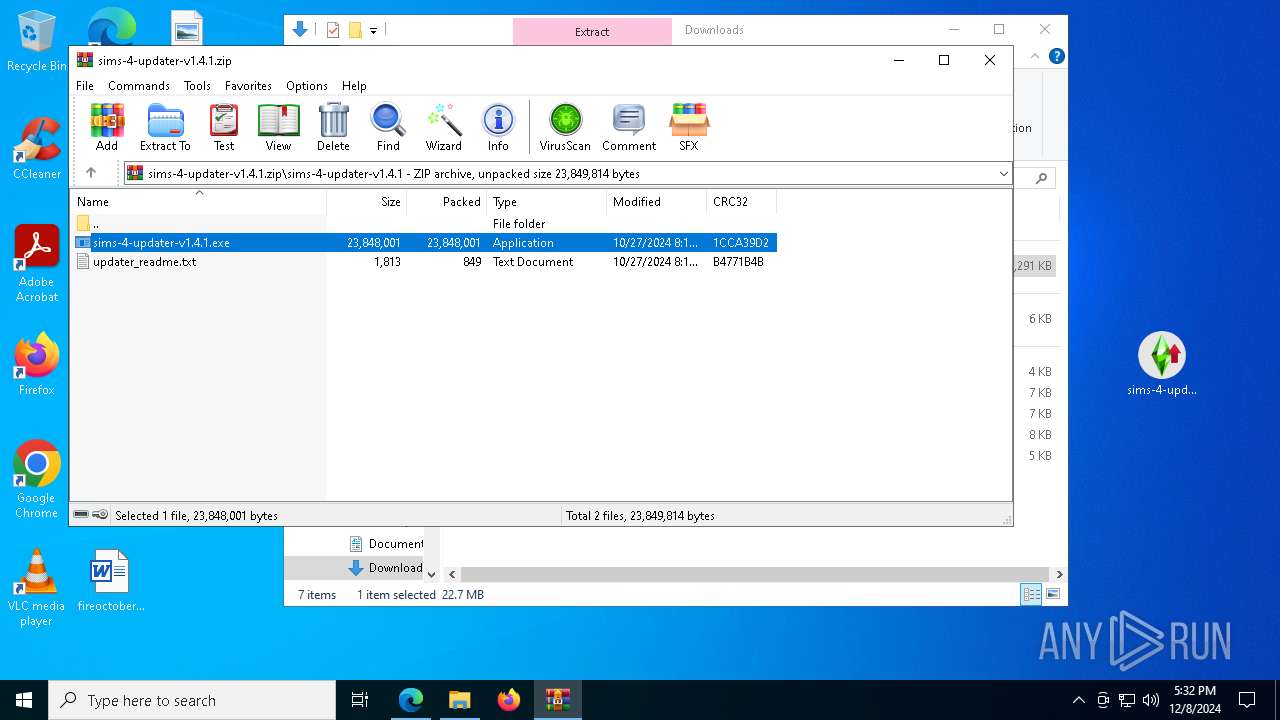
| 7608 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\sims-4-updater-v1.4.1.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 556
Read events
2 537
Write events
19
Delete events
0
Modification events
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\sims-4-updater-v1.4.1.zip | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2200) sims-4-updater-v1.4.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
| (PID) Process: | (7608) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
97
Suspicious files
4
Text files
934
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\VCRUNTIME140_1.dll | executable | |
MD5:135359D350F72AD4BF716B764D39E749 | SHA256:34048ABAA070ECC13B318CEA31425F4CA3EDD133D350318AC65259E6058C8B32 | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\Pythonwin\mfc140u.dll | executable | |
MD5:CD1D99DF975EE5395174DF834E82B256 | SHA256:D8CA1DEA862085F0204680230D29BFF4D168FFF675AB4700EEAF63704D995CB3 | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\VCRUNTIME140.dll | executable | |
MD5:F34EB034AA4A9735218686590CBA2E8B | SHA256:9D2B40F0395CC5D1B4D5EA17B84970C29971D448C37104676DB577586D4AD1B1 | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\_ctypes.pyd | executable | |
MD5:1635A0C5A72DF5AE64072CBB0065AEBE | SHA256:1EA3DD3DF393FA9B27BF6595BE4AC859064CD8EF9908A12378A6021BBA1CB177 | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\_cffi_backend.cp310-win_amd64.pyd | executable | |
MD5:2BAAA98B744915339AE6C016B17C3763 | SHA256:4F1CE205C2BE986C9D38B951B6BCB6045EB363E06DACC069A41941F80BE9068C | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\_asyncio.pyd | executable | |
MD5:33D0B6DE555DDBBBD5CA229BFA91C329 | SHA256:A9A99A2B847E46C0EFCE7FCFEFD27F4BCE58BAF9207277C17BFFD09EF4D274E5 | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\_hashlib.pyd | executable | |
MD5:D4674750C732F0DB4C4DD6A83A9124FE | SHA256:CAA4D2F8795E9A55E128409CC016E2CC5C694CB026D7058FC561E4DD131ED1C9 | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\_decimal.pyd | executable | |
MD5:20C77203DDF9FF2FF96D6D11DEA2EDCF | SHA256:9AAC010A424C757C434C460C3C0A6515D7720966AB64BAD667539282A17B4133 | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\_lzma.pyd | executable | |
MD5:7447EFD8D71E8A1929BE0FAC722B42DC | SHA256:60793C8592193CFBD00FD3E5263BE4315D650BA4F9E4FDA9C45A10642FD998BE | |||
| 5880 | sims-4-updater-v1.4.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI58802\_multiprocessing.pyd | executable | |
MD5:A9A0588711147E01EED59BE23C7944A9 | SHA256:7581EDEA33C1DB0A49B8361E51E6291688601640E57D75909FB2007B2104FA4C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
80
DNS requests
82
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4024 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7760 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
1476 | svchost.exe | GET | 206 | 23.32.238.98:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1734260463&P2=404&P3=2&P4=LJ%2b5W9I2FbJweKsipWQ0EN9LzwGACmE2xrDwaxDvfvCUSzFv0RQi6zqap7xF1W6U656FyWEAceVPOumawDljYw%3d%3d | DE | binary | 9.56 Kb | whitelisted |
7760 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6208 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
1476 | svchost.exe | HEAD | 200 | 23.32.238.98:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1734260463&P2=404&P3=2&P4=LJ%2b5W9I2FbJweKsipWQ0EN9LzwGACmE2xrDwaxDvfvCUSzFv0RQi6zqap7xF1W6U656FyWEAceVPOumawDljYw%3d%3d | DE | — | — | whitelisted |
1476 | svchost.exe | GET | 206 | 23.32.238.98:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1734260463&P2=404&P3=2&P4=LJ%2b5W9I2FbJweKsipWQ0EN9LzwGACmE2xrDwaxDvfvCUSzFv0RQi6zqap7xF1W6U656FyWEAceVPOumawDljYw%3d%3d | DE | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.24.77.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4024 | svchost.exe | 184.24.77.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4024 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 92.123.104.63:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.17.24.14:443 | cdnjs.cloudflare.com | — | — | whitelisted |
— | — | 104.18.11.207:443 | stackpath.bootstrapcdn.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
anadius.su |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |