| File name: | Jackett.Installer.Windows.exe |
| Full analysis: | https://app.any.run/tasks/d2eb7532-9ab7-4b82-9a02-e3d618cb19cf |
| Verdict: | Malicious activity |
| Analysis date: | August 30, 2019, 12:36:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FE6BF7D74123073ECD3632D14C60ECC4 |
| SHA1: | D32019D6BE27DCB1827A24E96173BBA45D4A0274 |
| SHA256: | A0DE89725C28E0490D9310CEB32A19CCA50107D8E7570F199603C75983CCE115 |
| SSDEEP: | 196608:3jgQqMdnWppU/IH9YuErjJXY3CuJKNwr6zcNa8UJivP:3H4p2DjJXhwxa8UJ+P |
MALICIOUS
Application was dropped or rewritten from another process
- JackettConsole.exe (PID: 3728)
- JackettConsole.exe (PID: 2292)
- JackettConsole.exe (PID: 3208)
- JackettTray.exe (PID: 2564)
- JackettService.exe (PID: 2968)
- JackettConsole.exe (PID: 3672)
- JackettConsole.exe (PID: 3120)
Loads dropped or rewritten executable
- JackettConsole.exe (PID: 3728)
- JackettConsole.exe (PID: 3208)
- JackettService.exe (PID: 2968)
- JackettConsole.exe (PID: 3672)
- JackettConsole.exe (PID: 2292)
- JackettConsole.exe (PID: 3120)
- JackettTray.exe (PID: 2564)
SUSPICIOUS
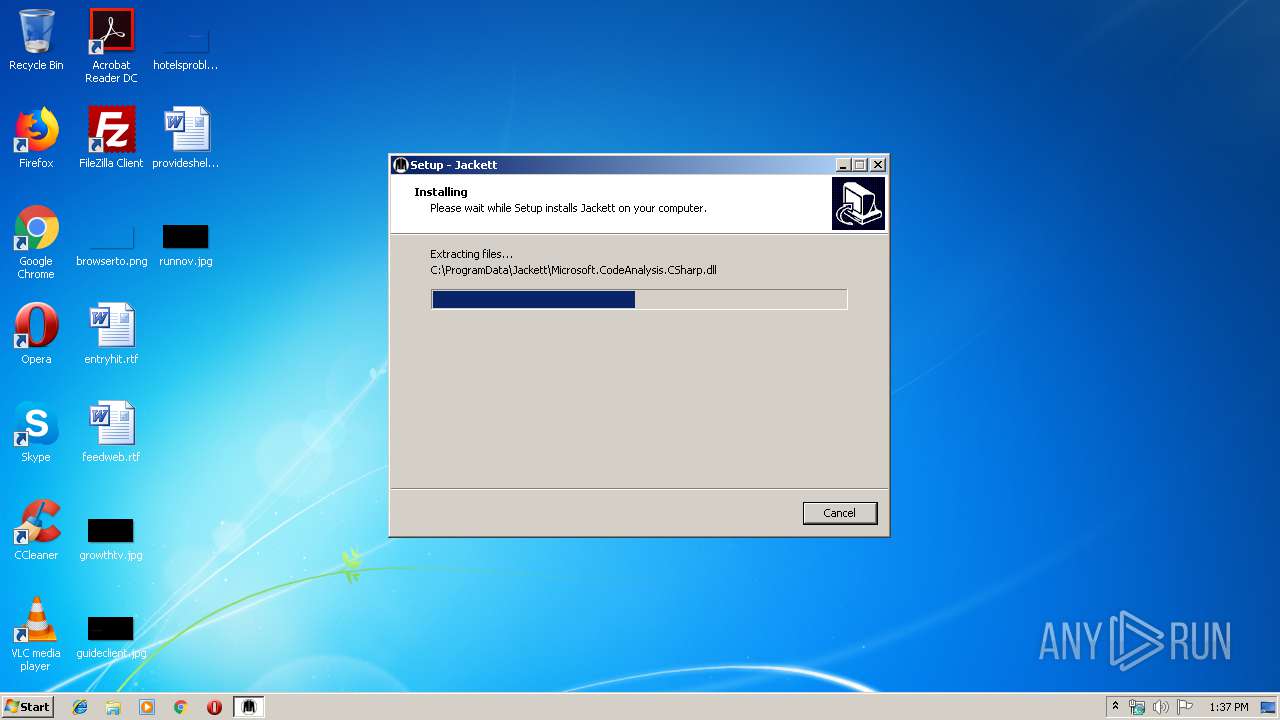
Executable content was dropped or overwritten
- Jackett.Installer.Windows.exe (PID: 3680)
- Jackett.Installer.Windows.exe (PID: 4056)
- Jackett.Installer.Windows.tmp (PID: 2648)
Reads Windows owner or organization settings
- Jackett.Installer.Windows.tmp (PID: 2648)
Reads the Windows organization settings
- Jackett.Installer.Windows.tmp (PID: 2648)
Uses NETSH.EXE for network configuration
- JackettConsole.exe (PID: 3728)
- JackettConsole.exe (PID: 2292)
Starts SC.EXE for service management
- JackettConsole.exe (PID: 3728)
- JackettConsole.exe (PID: 3120)
Creates files in the program directory
- JackettConsole.exe (PID: 3728)
- JackettService.exe (PID: 2968)
- JackettTray.exe (PID: 2564)
- JackettConsole.exe (PID: 3672)
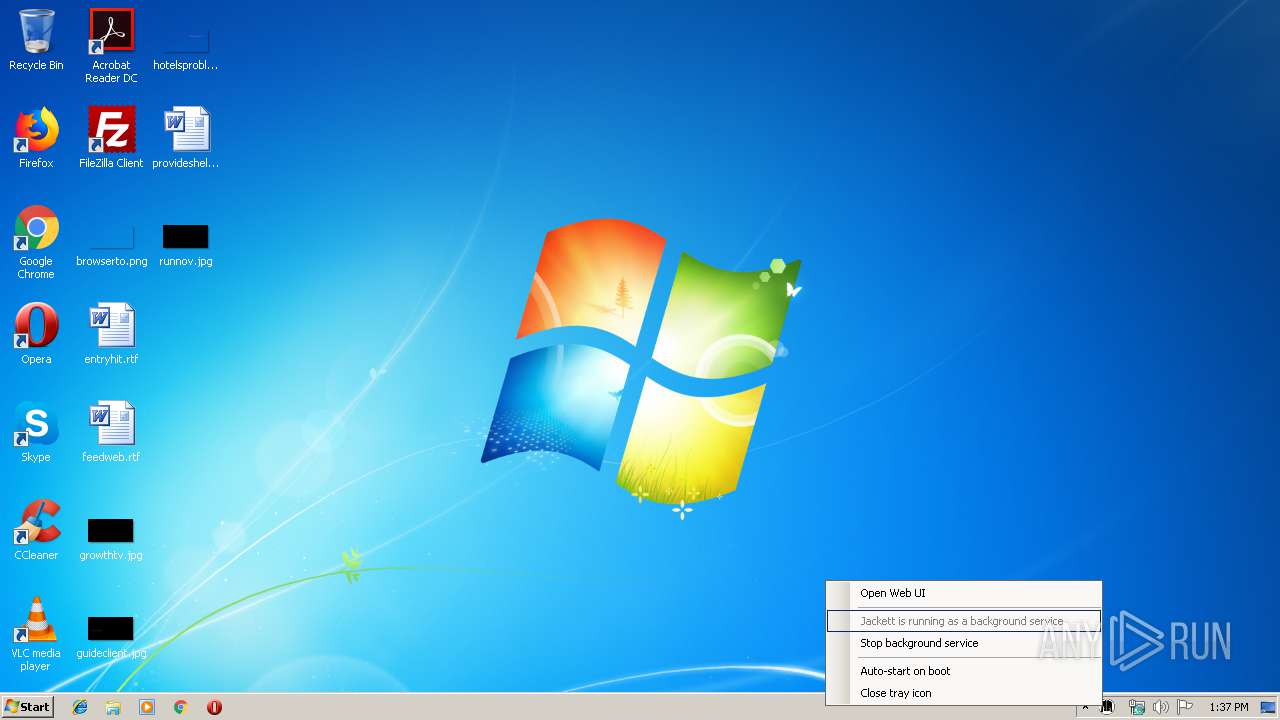
Executed as Windows Service
- JackettService.exe (PID: 2968)
Reads Environment values
- JackettConsole.exe (PID: 3672)
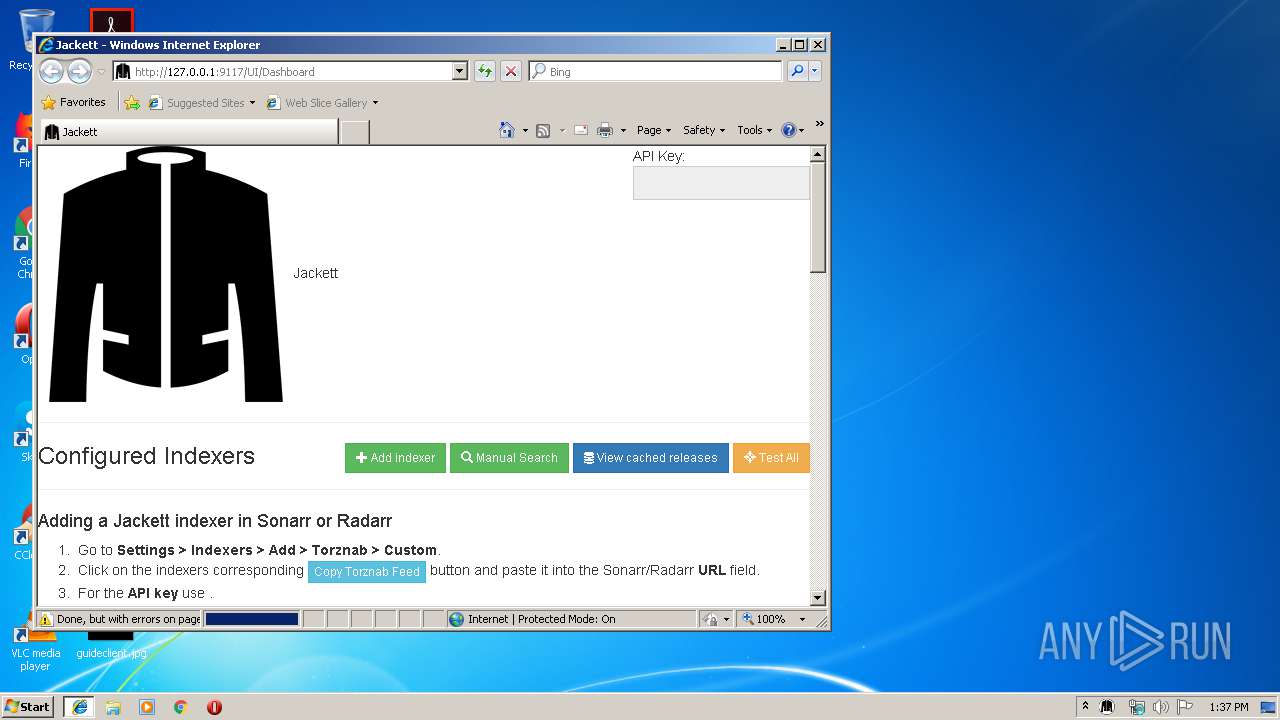
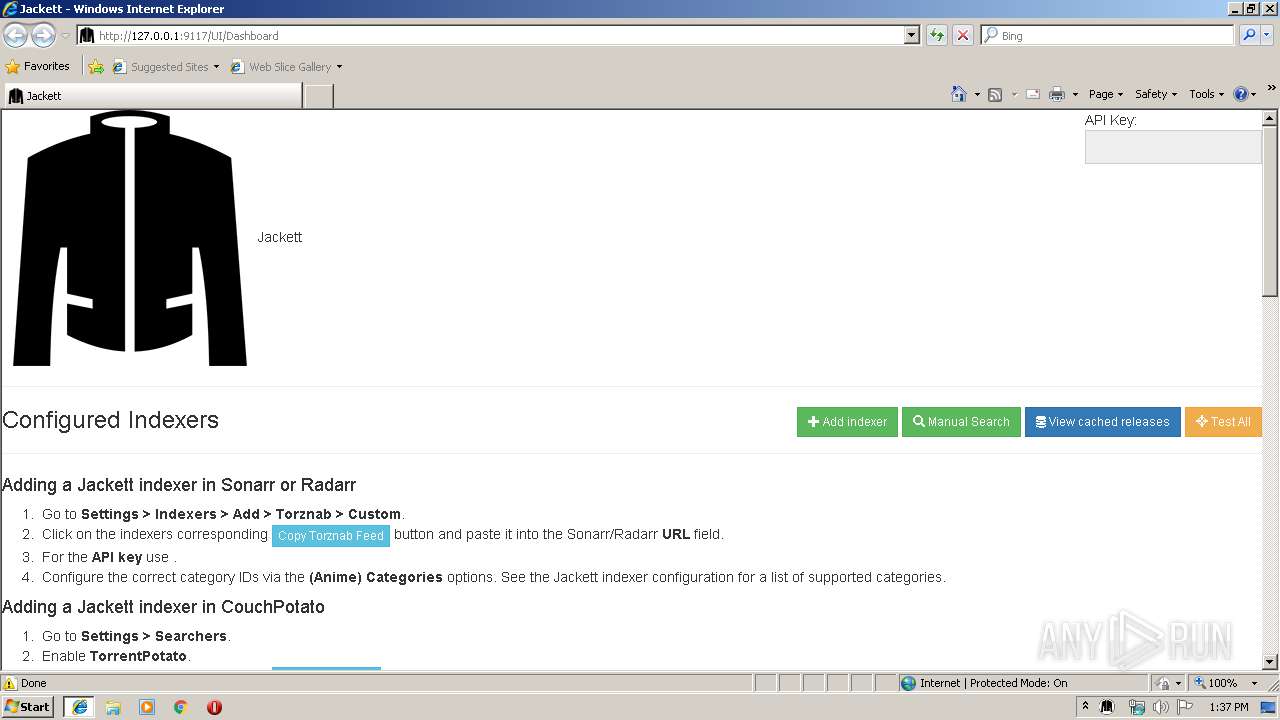
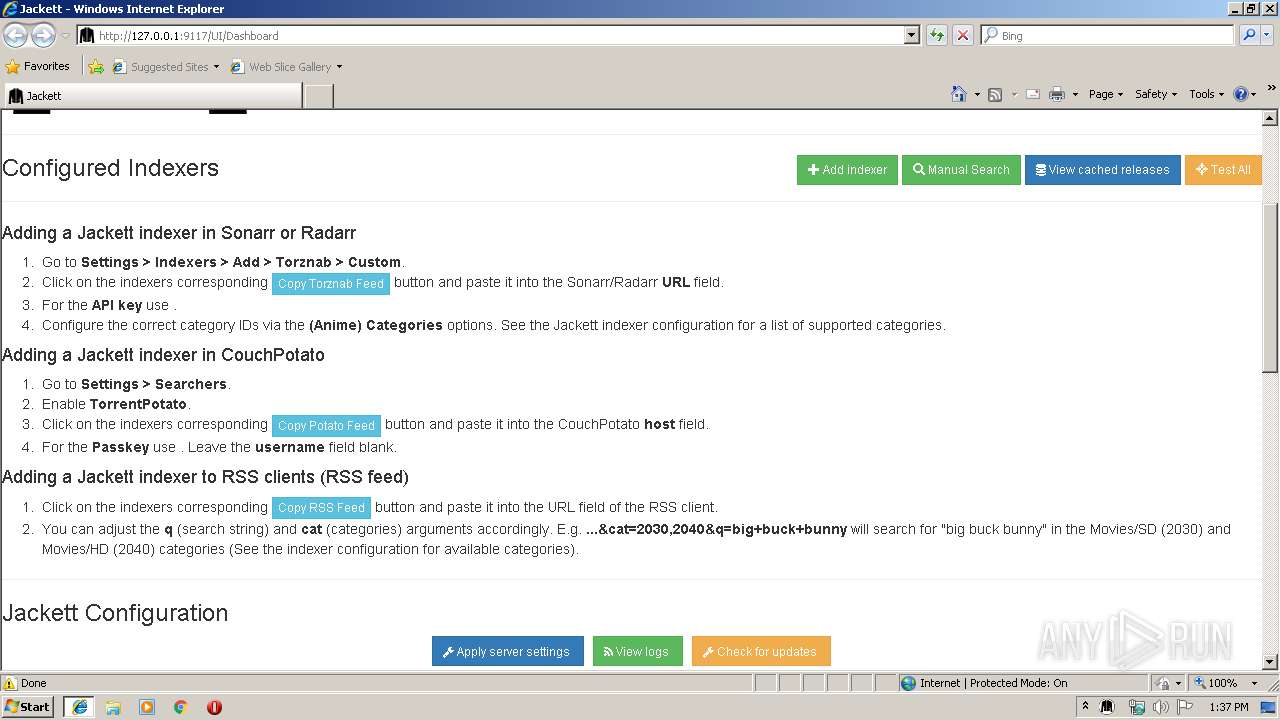
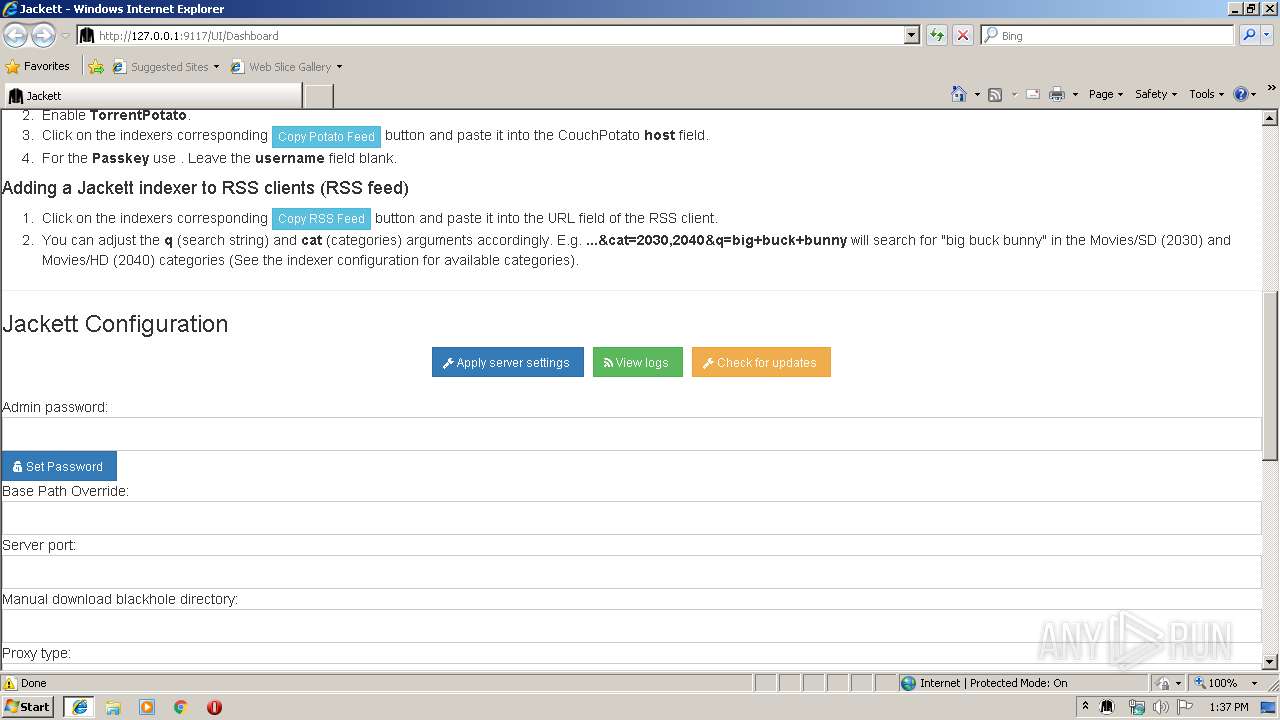
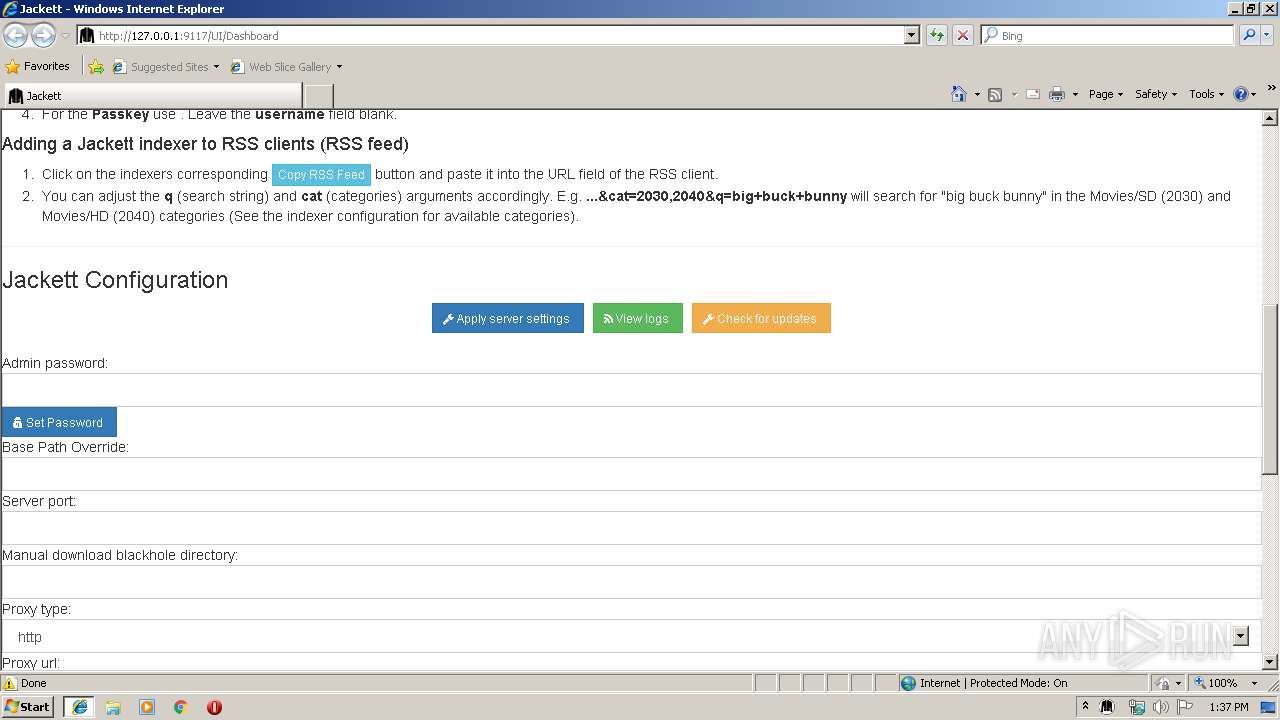
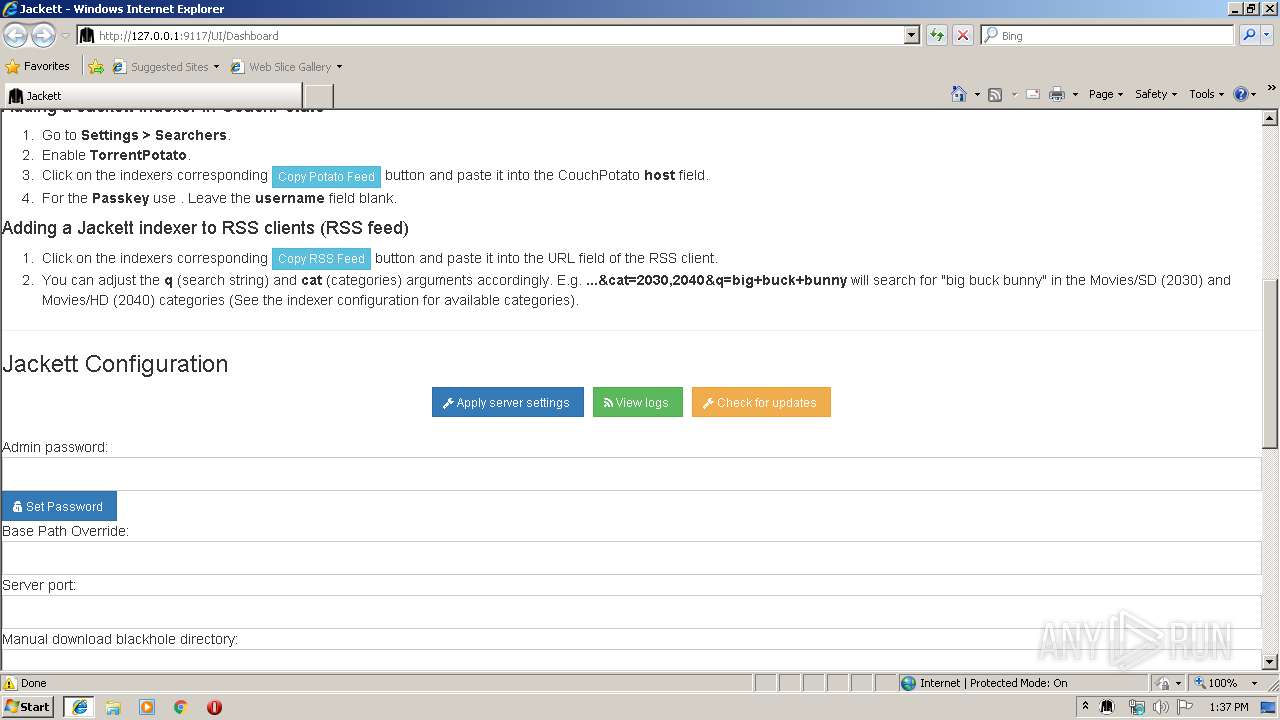
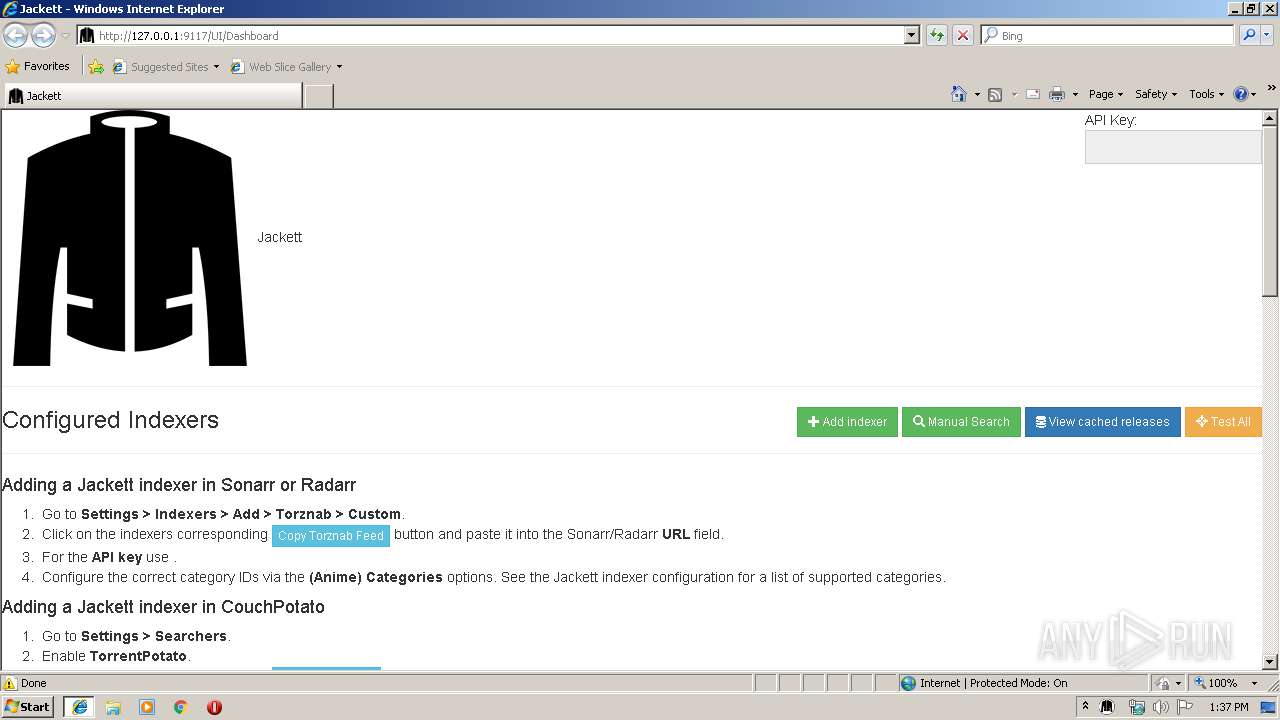
Starts Internet Explorer
- JackettTray.exe (PID: 2564)
INFO
Application was dropped or rewritten from another process
- Jackett.Installer.Windows.tmp (PID: 2552)
- Jackett.Installer.Windows.tmp (PID: 2648)
Dropped object may contain Bitcoin addresses
- Jackett.Installer.Windows.tmp (PID: 2648)
Creates a software uninstall entry
- Jackett.Installer.Windows.tmp (PID: 2648)
Application launched itself
- iexplore.exe (PID: 2196)
Reads Internet Cache Settings
- iexplore.exe (PID: 2284)
Creates files in the user directory
- iexplore.exe (PID: 2284)
Reads internet explorer settings
- iexplore.exe (PID: 2284)
Changes internet zones settings
- iexplore.exe (PID: 2196)
Creates files in the program directory
- Jackett.Installer.Windows.tmp (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 354304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.11.655.0 |
| ProductVersionNumber: | 0.11.655.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Jackett |
| FileDescription: | Jackett Setup |
| FileVersion: | 0.11.655.0 |
| LegalCopyright: | |
| ProductName: | Jackett |
| ProductVersion: | 0.11.655.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Jackett |
| FileDescription: | Jackett Setup |
| FileVersion: | 0.11.655.0 |
| LegalCopyright: | - |
| ProductName: | Jackett |
| ProductVersion: | 0.11.655.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00054610 | 0x00054800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.17753 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.52636 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.22462 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.41625 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.07302 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.5803 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.37476 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 2.19741 | 152104 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.94043 | 12573 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
69
Monitored processes
21
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | "netsh.exe" http delete urlacl http://127.0.0.1:9117/ | C:\Windows\system32\netsh.exe | — | JackettConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Windows\System32\sc.exe" description Jackett "API Support for your favorite torrent trackers" | C:\Windows\System32\sc.exe | — | JackettConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | JackettTray.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2196 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2292 | "C:\ProgramData\Jackett\JackettConsole.exe" --ReserveUrls | C:\ProgramData\Jackett\JackettConsole.exe | — | Jackett.Installer.Windows.tmp | |||||||||||
User: admin Company: JackettConsole Integrity Level: HIGH Description: JackettConsole Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\AppData\Local\Temp\is-QS0J5.tmp\Jackett.Installer.Windows.tmp" /SL5="$20134,7618137,421888,C:\Users\admin\AppData\Local\Temp\Jackett.Installer.Windows.exe" | C:\Users\admin\AppData\Local\Temp\is-QS0J5.tmp\Jackett.Installer.Windows.tmp | — | Jackett.Installer.Windows.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2564 | "C:\ProgramData\Jackett\JackettTray.exe" | C:\ProgramData\Jackett\JackettTray.exe | — | Jackett.Installer.Windows.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Description: Jackett.Tray Exit code: 0 Version: 0.11.655 Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Local\Temp\is-MF17R.tmp\Jackett.Installer.Windows.tmp" /SL5="$30136,7618137,421888,C:\Users\admin\AppData\Local\Temp\Jackett.Installer.Windows.exe" /SPAWNWND=$2012E /NOTIFYWND=$20134 | C:\Users\admin\AppData\Local\Temp\is-MF17R.tmp\Jackett.Installer.Windows.tmp | Jackett.Installer.Windows.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2896 | "netsh.exe" http delete urlacl http://*:9117/ | C:\Windows\system32\netsh.exe | — | JackettConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | C:\ProgramData\Jackett\JackettService.exe | C:\ProgramData\Jackett\JackettService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Jackett.Service Exit code: 0 Version: 0.11.655 Modules
| |||||||||||||||
Total events
1 401
Read events
1 050
Write events
344
Delete events
7
Modification events
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 580A00009E9D17A12F5FD501 | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: B37774BC6D3369A78DB6712FF10BBA9218B3AF78F77A82A291BD05D444843E98 | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: A815FE8508DC7F5E6603F5CF32DE3938A494BCAE9D4449520185F430637EB265 | |||
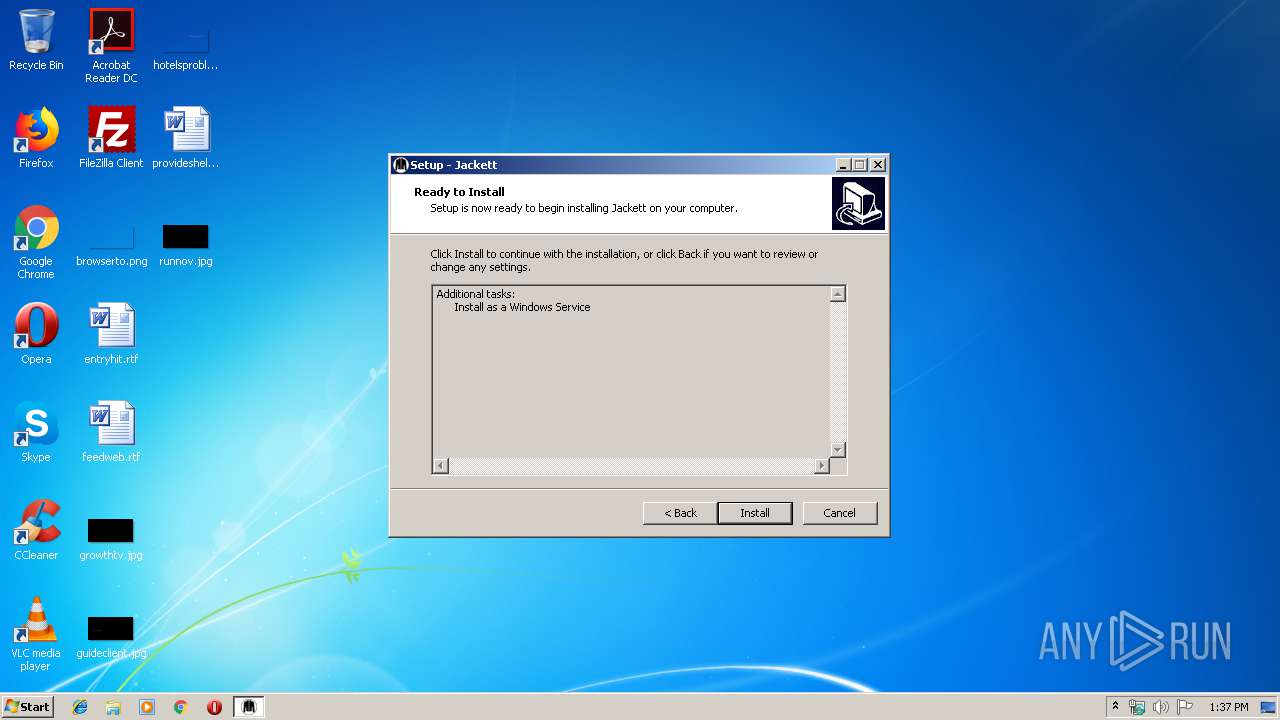
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{C2A9FC00-AA48-4F17-9A72-62FBCEE2785B}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (u) | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{C2A9FC00-AA48-4F17-9A72-62FBCEE2785B}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Jackett | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{C2A9FC00-AA48-4F17-9A72-62FBCEE2785B}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Jackett\ | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{C2A9FC00-AA48-4F17-9A72-62FBCEE2785B}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Jackett | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{C2A9FC00-AA48-4F17-9A72-62FBCEE2785B}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2648) Jackett.Installer.Windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{C2A9FC00-AA48-4F17-9A72-62FBCEE2785B}_is1 |
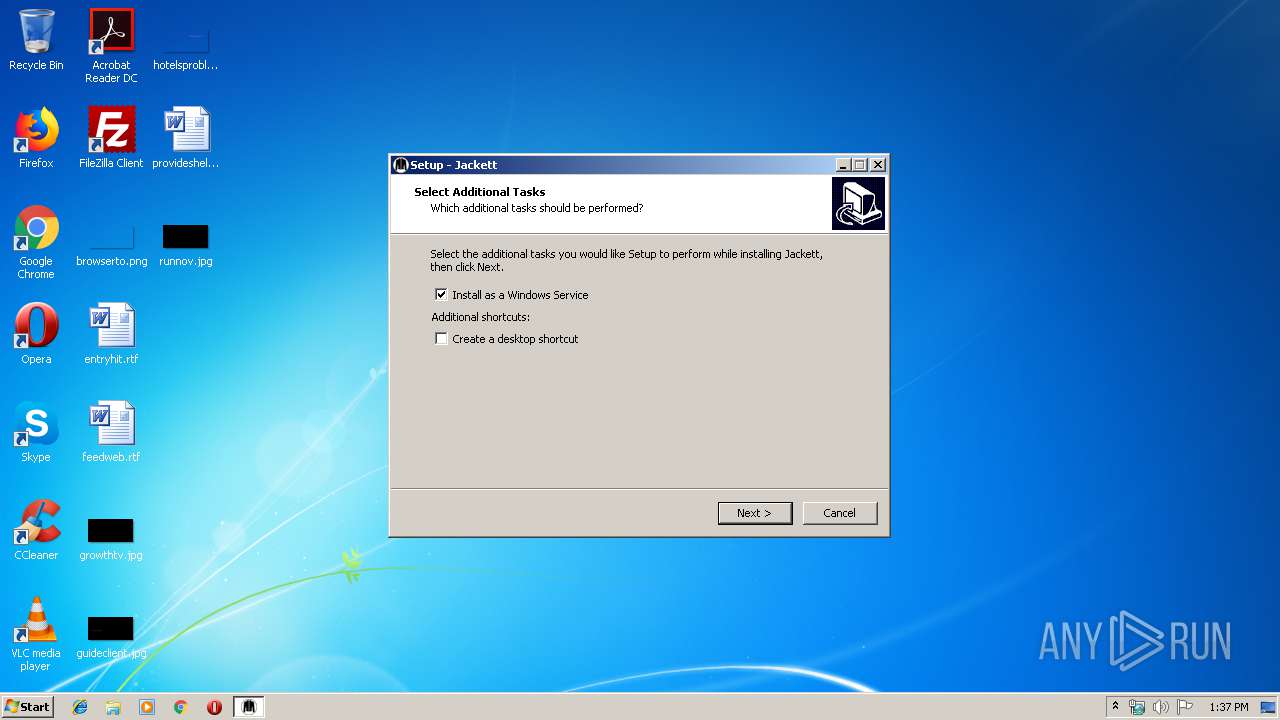
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: windowsservice | |||
Executable files
238
Suspicious files
4
Text files
634
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2648 | Jackett.Installer.Windows.tmp | C:\Program Files\Jackett\is-FJNPQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-46I2U.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-1M60R.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-AK47M.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-2I802.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-PH297.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-JBJ39.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-L6I2P.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-U2BIJ.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | Jackett.Installer.Windows.tmp | C:\ProgramData\Jackett\is-TGBSR.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2196 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2196 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |