| File name: | AOL-Desktop-9.8.exe |
| Full analysis: | https://app.any.run/tasks/d55c067c-a246-4431-a0d9-2c7a838e5c52 |
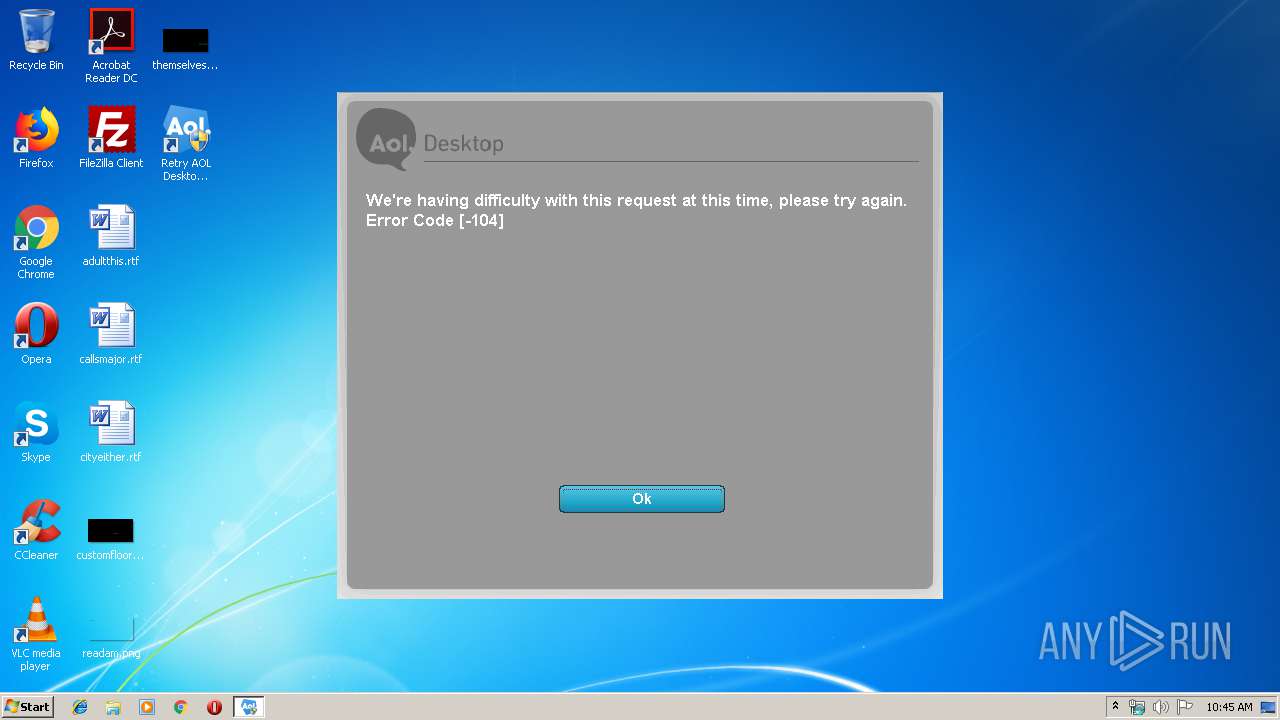
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 09:45:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 9E82567FD033CA2704FA7F47C1CC0BCE |
| SHA1: | 08670B1E9817BDBEB5D90DEE61024D60F72FE85D |
| SHA256: | A0DCDABB1D30C91E4ED6A289041BBF66BC03567F77F3A5DE37C978A6A41A4EB4 |
| SSDEEP: | 6144:FWmZJLC/MiH+az/MeFE8lb6QgJHCC1t4bbDfLL09Q:FtCkjilb6QgJHCRbDjLf |
MALICIOUS
Changes settings of System certificates
- roadie.exe (PID: 4024)
- AOL-Desktop-9.8.exe (PID: 3216)
Loads dropped or rewritten executable
- AOL-Desktop-9.8.exe (PID: 3216)
- roadie.exe (PID: 4024)
Application was dropped or rewritten from another process
- roadie.exe (PID: 4024)
SUSPICIOUS
Executable content was dropped or overwritten
- AOL-Desktop-9.8.exe (PID: 3216)
Adds / modifies Windows certificates
- roadie.exe (PID: 4024)
Reads internet explorer settings
- roadie.exe (PID: 4024)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:07:21 16:14:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 26624 |
| InitializedDataSize: | 129536 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3af4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.4346.14.1 |
| ProductVersionNumber: | 0.4346.14.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | AOL Inc. |
| FileDescription: | AOL Download Utility 0.4346.14.1.1 |
| FileVersion: | 0.4346.14.1.1 |
| LegalCopyright: | © 2015 AOL Inc. All Rights Reserved. |
| LegalTrademarks: | AOL is a trademark of AOL Inc. |
| OriginalFileName: | AOL_Desktop_9.8.exe |
| ProductName: | AOL Download Utility |
| ProductVersion: | 0.4346.14.1.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Jul-2009 14:14:14 |
| Detected languages: |
|
| CompanyName: | AOL Inc. |
| FileDescription: | AOL Download Utility 0.4346.14.1.1 |
| FileVersion: | 0.4346.14.1.1 |
| LegalCopyright: | © 2015 AOL Inc. All Rights Reserved. |
| LegalTrademarks: | AOL is a trademark of AOL Inc. |
| OriginalFilename: | AOL_Desktop_9.8.exe |
| ProductName: | AOL Download Utility |
| ProductVersion: | 0.4346.14.1.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Jul-2009 14:14:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000665A | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39361 |
.rdata | 0x00008000 | 0x00001DCA | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.41144 |
.data | 0x0000A000 | 0x0001C494 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.28059 |
.ndata | 0x00027000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002F000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.48358 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11451 | 829 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3216 | "C:\Users\admin\AppData\Local\Temp\AOL-Desktop-9.8.exe" | C:\Users\admin\AppData\Local\Temp\AOL-Desktop-9.8.exe | explorer.exe | ||||||||||||
User: admin Company: AOL Inc. Integrity Level: HIGH Description: AOL Download Utility 0.4346.14.1.1 Exit code: 0 Version: 0.4346.14.1.1 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\AOL-Desktop-9.8.exe" | C:\Users\admin\AppData\Local\Temp\AOL-Desktop-9.8.exe | — | explorer.exe | |||||||||||
User: admin Company: AOL Inc. Integrity Level: MEDIUM Description: AOL Download Utility 0.4346.14.1.1 Exit code: 3221226540 Version: 0.4346.14.1.1 Modules
| |||||||||||||||
| 4024 | C:\Users\admin\AppData\Local\Temp\roadie.exe | C:\Users\admin\AppData\Local\Temp\roadie.exe | AOL-Desktop-9.8.exe | ||||||||||||
User: admin Company: AOL Inc. Integrity Level: HIGH Description: Application Downloader Exit code: 4294967192 Version: 1.8.7.1 Modules
| |||||||||||||||
Total events
451
Read events
392
Write events
57
Delete events
2
Modification events
| (PID) Process: | (3216) AOL-Desktop-9.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\A1446BCE0C874DF0F2C3F61DA5C9A2BCF9DAB204 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000A1446BCE0C874DF0F2C3F61DA5C9A2BCF9DAB20420000000010000002F0400003082042B30820313A003020102020107300D06092A864886F70D01010505003063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F726974792031301E170D3034303630343137323633395A170D3239303630343137323633395A3067310B30090603550406130255533111300F0603550408130856697267696E6961310F300D0603550407130644756C6C6573311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E311630140603550403130D414F4C204D656D62657220434130820122300D06092A864886F70D01010105000382010F003082010A0282010100F863D8F1CCD6116F05E1D69F43272725FAAF678774ACDCD6FCC29ABD33724E65B05ACDEBF8A96948396E682E71166E9E597CC27CCDED6E43D809424E0D9A7DEEB55A2381D2A45BA951541CDFF684DF19C33E942D8DBA10F8E843080F32356C3531F8D6D3FC0931D6A9A17A2006590CE02B8D84C337A0081EF1357310DD4FFD0C7293266EAFC51C39E3CAF3956F30C2853D4D8420C83E3DD040D6FE064A18730B6E5767DB83C1136697D3BD59BC7EFA2F364514CDBCBFAB6877BF48EB11894E6A84F35D1CE56B6A00E66B8D48A409B921DC2D6629F4569EF00568FFCCC1C988BCD22C0BAF1D741A8668A46D1474EC2480F895B9F32E3C3D206F090238EA3A38050203010001A381E53081E2300E0603551D0F0101FF040403020186301D0603551D0E0416041461A6996D249F0E1188E639E0FE74D1056952A943301F0603551D2304183016801400ADD9A3F679F66E74A97F333D8117D74CCF33DE300F0603551D130101FF040530030101FF30480603551D200441303F303D0604551D20003035303306082B06010505070201162768747470733A2F2F706B692D696E666F2E616F6C2E636F6D2F414F4C2F696E6465782E68746D6C30350603551D1F042E302C302AA028A0268624687474703A2F2F63726C2E616F6C2E636F6D2F414F4C2F4D617374657243524C2E63726C300D06092A864886F70D010105050003820101000C9DBCCC1DD42E911BAFA03AEBCD5EFC252A298EB320E01737FAFCBBC5B514BB1C660E6F585FC671D01389C7AD230BED4CB858C1E3C2A4244C65760DB386644F28BACF96F8659A0E8226F582854E3520B345CC60EE0F4E20943A2B2FCB23109B461B7EC356754924A4B84D9F1C68D4E6F22FAF8EED2BB7E5966B1C3D8DBF20D36F2D542F9C7935FDDA06DE6820204BAF5DAB5E66C314647BF702E62796AD181EABF38260FC4C5FB60A527B9E9C3B2ECE3C425F366D6BFEA1768A2221FD5BE8BD7F9FCE5174486CACB5D1A26AFA0744DED0DBA98D181FF1B9C5E82AEBBA3D3B188CC00C30B3C9211C334C3A4953D4A8BABA38233D3A65825E797115F8252B7D19 | |||
| (PID) Process: | (3216) AOL-Desktop-9.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\3921C115C15D0ECA5CCB5BC4F07D21D8050B566A |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000003921C115C15D0ECA5CCB5BC4F07D21D8050B566A2000000001000000A8030000308203A43082028CA003020102020101300D06092A864886F70D01010505003063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F726974792031301E170D3032303532383036303030305A170D3337313131393230343330305A3063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F72697479203130820122300D06092A864886F70D01010105000382010F003082010A0282010100A82FE8A469060347C3E92A98FF19A2709AC650B27EA5DF684D1B7C0FB697687D2DA68B97E96486C9A3EFA086BF60659C4B5488C248C54A39BF14E35955E519B474C8B405395C16A5E29505E012AE598BA23368581CA6D415B7D89FD7DC71AB7E9ABF9B8E330F22FD1F2EE70736EF6239C5DDCBBA251423DE0CC63D3CCE8208E6663EDA513B163AA3057FA0DC87D59CFC72A9A07D78E4B731551E65BBD461B02160ED103272C592251EF8904A187847DF7E30373E501BDB1CD36B9A865307B0EFAC0678F88499FE218D4C80B60C82F66670791AD34FA3CFF1CF46B04B0F3EDD8862B88CA909283B7AC797E11EE5F49FC0C0AE24A0C8A1D90FD67B268269323DA70203010001A3633061300F0603551D130101FF040530030101FF301D0603551D0E0416041400ADD9A3F679F66E74A97F333D8117D74CCF33DE301F0603551D2304183016801400ADD9A3F679F66E74A97F333D8117D74CCF33DE300E0603551D0F0101FF040403020186300D06092A864886F70D010105050003820101007C8AD11F183782E0B8B0A3ED5695C862619C05A2CDC2622661CD1016D7CCB46534D0118AADA8A90566EF74F36D5F9D99AFF68BFBEB52B20598A26F2AC554BD25BD5FAEC886EA462CC1B3BDC1E9497018169708138C20E01B2E3A47CB1EE40030955BF445A3C01AB0014EABBDC0236E633F804AC507EDDCE26FC7C162F1E372D604C874670BFA88ABA101C86FF014AFD299CD51937EED2E38C7BDCE46503D72E379259D9B882B1020DDA5B8329F8DE029DF21748682DB2F8230C6C73586B3F9965F46DB0C45FDF350C36FC6C348AD46A6E127470A1D0E9BB6C2777F63F2E07D1ABEFCE0DFD7C7A76CB0F9AEBA3CFD74B411E8580D80BCD3A8803A99ED75CC467B | |||
| (PID) Process: | (4024) roadie.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3216) AOL-Desktop-9.8.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\AOL-Desktop-9.8.exe | |||
| (PID) Process: | (4024) roadie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\3921C115C15D0ECA5CCB5BC4F07D21D8050B566A |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000014000000B31DA18FBA765C5ED3DF3080593871DB9E0DCC290300000001000000140000003921C115C15D0ECA5CCB5BC4F07D21D8050B566A2000000001000000A8030000308203A43082028CA003020102020101300D06092A864886F70D01010505003063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F726974792031301E170D3032303532383036303030305A170D3337313131393230343330305A3063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F72697479203130820122300D06092A864886F70D01010105000382010F003082010A0282010100A82FE8A469060347C3E92A98FF19A2709AC650B27EA5DF684D1B7C0FB697687D2DA68B97E96486C9A3EFA086BF60659C4B5488C248C54A39BF14E35955E519B474C8B405395C16A5E29505E012AE598BA23368581CA6D415B7D89FD7DC71AB7E9ABF9B8E330F22FD1F2EE70736EF6239C5DDCBBA251423DE0CC63D3CCE8208E6663EDA513B163AA3057FA0DC87D59CFC72A9A07D78E4B731551E65BBD461B02160ED103272C592251EF8904A187847DF7E30373E501BDB1CD36B9A865307B0EFAC0678F88499FE218D4C80B60C82F66670791AD34FA3CFF1CF46B04B0F3EDD8862B88CA909283B7AC797E11EE5F49FC0C0AE24A0C8A1D90FD67B268269323DA70203010001A3633061300F0603551D130101FF040530030101FF301D0603551D0E0416041400ADD9A3F679F66E74A97F333D8117D74CCF33DE301F0603551D2304183016801400ADD9A3F679F66E74A97F333D8117D74CCF33DE300E0603551D0F0101FF040403020186300D06092A864886F70D010105050003820101007C8AD11F183782E0B8B0A3ED5695C862619C05A2CDC2622661CD1016D7CCB46534D0118AADA8A90566EF74F36D5F9D99AFF68BFBEB52B20598A26F2AC554BD25BD5FAEC886EA462CC1B3BDC1E9497018169708138C20E01B2E3A47CB1EE40030955BF445A3C01AB0014EABBDC0236E633F804AC507EDDCE26FC7C162F1E372D604C874670BFA88ABA101C86FF014AFD299CD51937EED2E38C7BDCE46503D72E379259D9B882B1020DDA5B8329F8DE029DF21748682DB2F8230C6C73586B3F9965F46DB0C45FDF350C36FC6C348AD46A6E127470A1D0E9BB6C2777F63F2E07D1ABEFCE0DFD7C7A76CB0F9AEBA3CFD74B411E8580D80BCD3A8803A99ED75CC467B | |||
| (PID) Process: | (4024) roadie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\801D62D07B449D5C5C035C98EA61FA443C2A58FE |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000014000000F53631B5177626EB6541DF5563C8187D9DCA421A09000000010000005E000000305C06082B0601050507030306082B0601050507030106082B0601050507030206082B0601050507030406082B0601050508020206082B0601050507030606082B0601050507030706082B06010505070308060A2B0601040182370A030453000000010000002400000030223020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C014000000010000001400000055E481D11180BED889B908A331F9A1240916B9701D0000000100000010000000E871723E266F38AF5D49CDA2A502669C0B000000010000001000000045006E00740072007500730074000000030000000100000014000000801D62D07B449D5C5C035C98EA61FA443C2A58FE2000000001000000600400003082045C30820344A00302010202043863B966300D06092A864886F70D01010505003081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F7269747920283230343829301E170D3939313232343137353035315A170D3139313232343138323035315A3081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F726974792028323034382930820122300D06092A864886F70D01010105000382010F003082010A0282010100AD4D4BA91286B2EAA320071516642A2B4BD1BF0B4A4D8EED8076A567B77840C07342C868C0DB532BDD5EB8769835938B1A9D7C133A0E1F5BB71ECFE524141EB181A98D7DB8CC6B4B03F1020CDCABA54024007F7494A19D0829B3880BF587779D55CDE4C37ED76A64AB851486955B9732506F3DC8BA660CE3FCBDB849C176894919FDC0A8BD89A3672FC69FBC711960B82DE92CC99076667B94E2AF78D665535D3CD69CB2CF2903F92FA450B2D448CE0532558AFDB2644C0EE4980775DB7FDFB9085560853029F97B48A46986E3353F1E865D7A7A15BDEF008E1522541700902693BC0E496891BFF847D39D9542C10E4DDF6F26CFC3182162664370D6D5C007E10203010001A3743072301106096086480186F8420101040403020007301F0603551D2304183016801455E481D11180BED889B908A331F9A1240916B970301D0603551D0E0416041455E481D11180BED889B908A331F9A1240916B970301D06092A864886F67D0741000410300E1B0856352E303A342E3003020490300D06092A864886F70D010105050003820101005947AC21848A17C99C89531EBA80851AC63C4E3EB19CB67CC6925D186402E3D3060811617C63E32B9D31037076D2A328A0F4BB9A6373ED6DE52ADBED14A92BC63611D02BEB078BA5DA9E5C199D5612F55429C805EDB2122A8DF4031BFFE7921087B03AB5C39D053712A3C7F415B9D5A439169B533A2391F1A882A26A8868C1790222BCAAA6D6AEDFB0145FB887D0DD7C7F7BFFAF1CCFE6DB07AD5EDB859DD02B0D33DB04D1E64940132B76FB3EE99C890F15CE18B08578214F6B4F0EFA3667CD07F2FF08D0E2DED9BF2AAFB88786213C04CAB794687FCF3CE998D738FFECC0D950F02E4B58AE466FD02EC360DA725572BD4C459E61BABF84819203D1D2697CC5 | |||
| (PID) Process: | (4024) roadie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\3921C115C15D0ECA5CCB5BC4F07D21D8050B566A |
| Operation: | write | Name: | Blob |
Value: 14000000010000001400000000ADD9A3F679F66E74A97F333D8117D74CCF33DE0300000001000000140000003921C115C15D0ECA5CCB5BC4F07D21D8050B566A0F0000000100000014000000B31DA18FBA765C5ED3DF3080593871DB9E0DCC292000000001000000A8030000308203A43082028CA003020102020101300D06092A864886F70D01010505003063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F726974792031301E170D3032303532383036303030305A170D3337313131393230343330305A3063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F72697479203130820122300D06092A864886F70D01010105000382010F003082010A0282010100A82FE8A469060347C3E92A98FF19A2709AC650B27EA5DF684D1B7C0FB697687D2DA68B97E96486C9A3EFA086BF60659C4B5488C248C54A39BF14E35955E519B474C8B405395C16A5E29505E012AE598BA23368581CA6D415B7D89FD7DC71AB7E9ABF9B8E330F22FD1F2EE70736EF6239C5DDCBBA251423DE0CC63D3CCE8208E6663EDA513B163AA3057FA0DC87D59CFC72A9A07D78E4B731551E65BBD461B02160ED103272C592251EF8904A187847DF7E30373E501BDB1CD36B9A865307B0EFAC0678F88499FE218D4C80B60C82F66670791AD34FA3CFF1CF46B04B0F3EDD8862B88CA909283B7AC797E11EE5F49FC0C0AE24A0C8A1D90FD67B268269323DA70203010001A3633061300F0603551D130101FF040530030101FF301D0603551D0E0416041400ADD9A3F679F66E74A97F333D8117D74CCF33DE301F0603551D2304183016801400ADD9A3F679F66E74A97F333D8117D74CCF33DE300E0603551D0F0101FF040403020186300D06092A864886F70D010105050003820101007C8AD11F183782E0B8B0A3ED5695C862619C05A2CDC2622661CD1016D7CCB46534D0118AADA8A90566EF74F36D5F9D99AFF68BFBEB52B20598A26F2AC554BD25BD5FAEC886EA462CC1B3BDC1E9497018169708138C20E01B2E3A47CB1EE40030955BF445A3C01AB0014EABBDC0236E633F804AC507EDDCE26FC7C162F1E372D604C874670BFA88ABA101C86FF014AFD299CD51937EED2E38C7BDCE46503D72E379259D9B882B1020DDA5B8329F8DE029DF21748682DB2F8230C6C73586B3F9965F46DB0C45FDF350C36FC6C348AD46A6E127470A1D0E9BB6C2777F63F2E07D1ABEFCE0DFD7C7A76CB0F9AEBA3CFD74B411E8580D80BCD3A8803A99ED75CC467B | |||
| (PID) Process: | (4024) roadie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\A1446BCE0C874DF0F2C3F61DA5C9A2BCF9DAB204 |
| Operation: | write | Name: | Blob |
Value: 14000000010000001400000061A6996D249F0E1188E639E0FE74D1056952A943030000000100000014000000A1446BCE0C874DF0F2C3F61DA5C9A2BCF9DAB20420000000010000002F0400003082042B30820313A003020102020107300D06092A864886F70D01010505003063310B3009060355040613025553311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E313630340603550403132D416D6572696361204F6E6C696E6520526F6F742043657274696669636174696F6E20417574686F726974792031301E170D3034303630343137323633395A170D3239303630343137323633395A3067310B30090603550406130255533111300F0603550408130856697267696E6961310F300D0603550407130644756C6C6573311C301A060355040A1313416D6572696361204F6E6C696E6520496E632E311630140603550403130D414F4C204D656D62657220434130820122300D06092A864886F70D01010105000382010F003082010A0282010100F863D8F1CCD6116F05E1D69F43272725FAAF678774ACDCD6FCC29ABD33724E65B05ACDEBF8A96948396E682E71166E9E597CC27CCDED6E43D809424E0D9A7DEEB55A2381D2A45BA951541CDFF684DF19C33E942D8DBA10F8E843080F32356C3531F8D6D3FC0931D6A9A17A2006590CE02B8D84C337A0081EF1357310DD4FFD0C7293266EAFC51C39E3CAF3956F30C2853D4D8420C83E3DD040D6FE064A18730B6E5767DB83C1136697D3BD59BC7EFA2F364514CDBCBFAB6877BF48EB11894E6A84F35D1CE56B6A00E66B8D48A409B921DC2D6629F4569EF00568FFCCC1C988BCD22C0BAF1D741A8668A46D1474EC2480F895B9F32E3C3D206F090238EA3A38050203010001A381E53081E2300E0603551D0F0101FF040403020186301D0603551D0E0416041461A6996D249F0E1188E639E0FE74D1056952A943301F0603551D2304183016801400ADD9A3F679F66E74A97F333D8117D74CCF33DE300F0603551D130101FF040530030101FF30480603551D200441303F303D0604551D20003035303306082B06010505070201162768747470733A2F2F706B692D696E666F2E616F6C2E636F6D2F414F4C2F696E6465782E68746D6C30350603551D1F042E302C302AA028A0268624687474703A2F2F63726C2E616F6C2E636F6D2F414F4C2F4D617374657243524C2E63726C300D06092A864886F70D010105050003820101000C9DBCCC1DD42E911BAFA03AEBCD5EFC252A298EB320E01737FAFCBBC5B514BB1C660E6F585FC671D01389C7AD230BED4CB858C1E3C2A4244C65760DB386644F28BACF96F8659A0E8226F582854E3520B345CC60EE0F4E20943A2B2FCB23109B461B7EC356754924A4B84D9F1C68D4E6F22FAF8EED2BB7E5966B1C3D8DBF20D36F2D542F9C7935FDDA06DE6820204BAF5DAB5E66C314647BF702E62796AD181EABF38260FC4C5FB60A527B9E9C3B2ECE3C425F366D6BFEA1768A2221FD5BE8BD7F9FCE5174486CACB5D1A26AFA0744DED0DBA98D181FF1B9C5E82AEBBA3D3B188CC00C30B3C9211C334C3A4953D4A8BABA38233D3A65825E797115F8252B7D19 | |||
| (PID) Process: | (4024) roadie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\801D62D07B449D5C5C035C98EA61FA443C2A58FE |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000BA21EA20D6DDDB8FC1578B40ADA1FCFC030000000100000014000000801D62D07B449D5C5C035C98EA61FA443C2A58FE0B000000010000001000000045006E007400720075007300740000001D0000000100000010000000E871723E266F38AF5D49CDA2A502669C14000000010000001400000055E481D11180BED889B908A331F9A1240916B97053000000010000002400000030223020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C009000000010000005E000000305C06082B0601050507030306082B0601050507030106082B0601050507030206082B0601050507030406082B0601050508020206082B0601050507030606082B0601050507030706082B06010505070308060A2B0601040182370A03040F0000000100000014000000F53631B5177626EB6541DF5563C8187D9DCA421A2000000001000000600400003082045C30820344A00302010202043863B966300D06092A864886F70D01010505003081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F7269747920283230343829301E170D3939313232343137353035315A170D3139313232343138323035315A3081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F726974792028323034382930820122300D06092A864886F70D01010105000382010F003082010A0282010100AD4D4BA91286B2EAA320071516642A2B4BD1BF0B4A4D8EED8076A567B77840C07342C868C0DB532BDD5EB8769835938B1A9D7C133A0E1F5BB71ECFE524141EB181A98D7DB8CC6B4B03F1020CDCABA54024007F7494A19D0829B3880BF587779D55CDE4C37ED76A64AB851486955B9732506F3DC8BA660CE3FCBDB849C176894919FDC0A8BD89A3672FC69FBC711960B82DE92CC99076667B94E2AF78D665535D3CD69CB2CF2903F92FA450B2D448CE0532558AFDB2644C0EE4980775DB7FDFB9085560853029F97B48A46986E3353F1E865D7A7A15BDEF008E1522541700902693BC0E496891BFF847D39D9542C10E4DDF6F26CFC3182162664370D6D5C007E10203010001A3743072301106096086480186F8420101040403020007301F0603551D2304183016801455E481D11180BED889B908A331F9A1240916B970301D0603551D0E0416041455E481D11180BED889B908A331F9A1240916B970301D06092A864886F67D0741000410300E1B0856352E303A342E3003020490300D06092A864886F70D010105050003820101005947AC21848A17C99C89531EBA80851AC63C4E3EB19CB67CC6925D186402E3D3060811617C63E32B9D31037076D2A328A0F4BB9A6373ED6DE52ADBED14A92BC63611D02BEB078BA5DA9E5C199D5612F55429C805EDB2122A8DF4031BFFE7921087B03AB5C39D053712A3C7F415B9D5A439169B533A2391F1A882A26A8868C1790222BCAAA6D6AEDFB0145FB887D0DD7C7F7BFFAF1CCFE6DB07AD5EDB859DD02B0D33DB04D1E64940132B76FB3EE99C890F15CE18B08578214F6B4F0EFA3667CD07F2FF08D0E2DED9BF2AAFB88786213C04CAB794687FCF3CE998D738FFECC0D950F02E4B58AE466FD02EC360DA725572BD4C459E61BABF84819203D1D2697CC5 | |||
| (PID) Process: | (4024) roadie.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\801D62D07B449D5C5C035C98EA61FA443C2A58FE |
| Operation: | write | Name: | Blob |
Value: 19000000010000001000000091FAD483F14848A8A69B18B805CDBB3A0F0000000100000014000000F53631B5177626EB6541DF5563C8187D9DCA421A09000000010000005E000000305C06082B0601050507030306082B0601050507030106082B0601050507030206082B0601050507030406082B0601050508020206082B0601050507030606082B0601050507030706082B06010505070308060A2B0601040182370A030453000000010000002400000030223020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C014000000010000001400000055E481D11180BED889B908A331F9A1240916B9701D0000000100000010000000E871723E266F38AF5D49CDA2A502669C0B000000010000001000000045006E00740072007500730074000000030000000100000014000000801D62D07B449D5C5C035C98EA61FA443C2A58FE040000000100000010000000BA21EA20D6DDDB8FC1578B40ADA1FCFC2000000001000000600400003082045C30820344A00302010202043863B966300D06092A864886F70D01010505003081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F7269747920283230343829301E170D3939313232343137353035315A170D3139313232343138323035315A3081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F726974792028323034382930820122300D06092A864886F70D01010105000382010F003082010A0282010100AD4D4BA91286B2EAA320071516642A2B4BD1BF0B4A4D8EED8076A567B77840C07342C868C0DB532BDD5EB8769835938B1A9D7C133A0E1F5BB71ECFE524141EB181A98D7DB8CC6B4B03F1020CDCABA54024007F7494A19D0829B3880BF587779D55CDE4C37ED76A64AB851486955B9732506F3DC8BA660CE3FCBDB849C176894919FDC0A8BD89A3672FC69FBC711960B82DE92CC99076667B94E2AF78D665535D3CD69CB2CF2903F92FA450B2D448CE0532558AFDB2644C0EE4980775DB7FDFB9085560853029F97B48A46986E3353F1E865D7A7A15BDEF008E1522541700902693BC0E496891BFF847D39D9542C10E4DDF6F26CFC3182162664370D6D5C007E10203010001A3743072301106096086480186F8420101040403020007301F0603551D2304183016801455E481D11180BED889B908A331F9A1240916B970301D0603551D0E0416041455E481D11180BED889B908A331F9A1240916B970301D06092A864886F67D0741000410300E1B0856352E303A342E3003020490300D06092A864886F70D010105050003820101005947AC21848A17C99C89531EBA80851AC63C4E3EB19CB67CC6925D186402E3D3060811617C63E32B9D31037076D2A328A0F4BB9A6373ED6DE52ADBED14A92BC63611D02BEB078BA5DA9E5C199D5612F55429C805EDB2122A8DF4031BFFE7921087B03AB5C39D053712A3C7F415B9D5A439169B533A2391F1A882A26A8868C1790222BCAAA6D6AEDFB0145FB887D0DD7C7F7BFFAF1CCFE6DB07AD5EDB859DD02B0D33DB04D1E64940132B76FB3EE99C890F15CE18B08578214F6B4F0EFA3667CD07F2FF08D0E2DED9BF2AAFB88786213C04CAB794687FCF3CE998D738FFECC0D950F02E4B58AE466FD02EC360DA725572BD4C459E61BABF84819203D1D2697CC5 | |||
Executable files
3
Suspicious files
1
Text files
56
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\nsq9E0C.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\nsa9DFB.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\dlgui.dll | executable | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\nsq9E0C.tmp\CertHelper.dll | executable | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\html\CancelConfirm.htm | html | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\roadie.bin | binary | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\roadie.ini | text | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\html\DownloadError.htm | html | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\html\Cancelled.htm | html | |
MD5:— | SHA256:— | |||
| 3216 | AOL-Desktop-9.8.exe | C:\Users\admin\AppData\Local\Temp\roadie.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4024 | roadie.exe | 172.217.23.174:80 | google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.newaol.com |
| unknown |
google.com |
| malicious |