| File name: | ROTANOTEDKSID-Clean.exe |
| Full analysis: | https://app.any.run/tasks/94dd01c2-972f-4b8d-a1d5-4a9a5f2a5a7e |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2021, 16:25:02 |
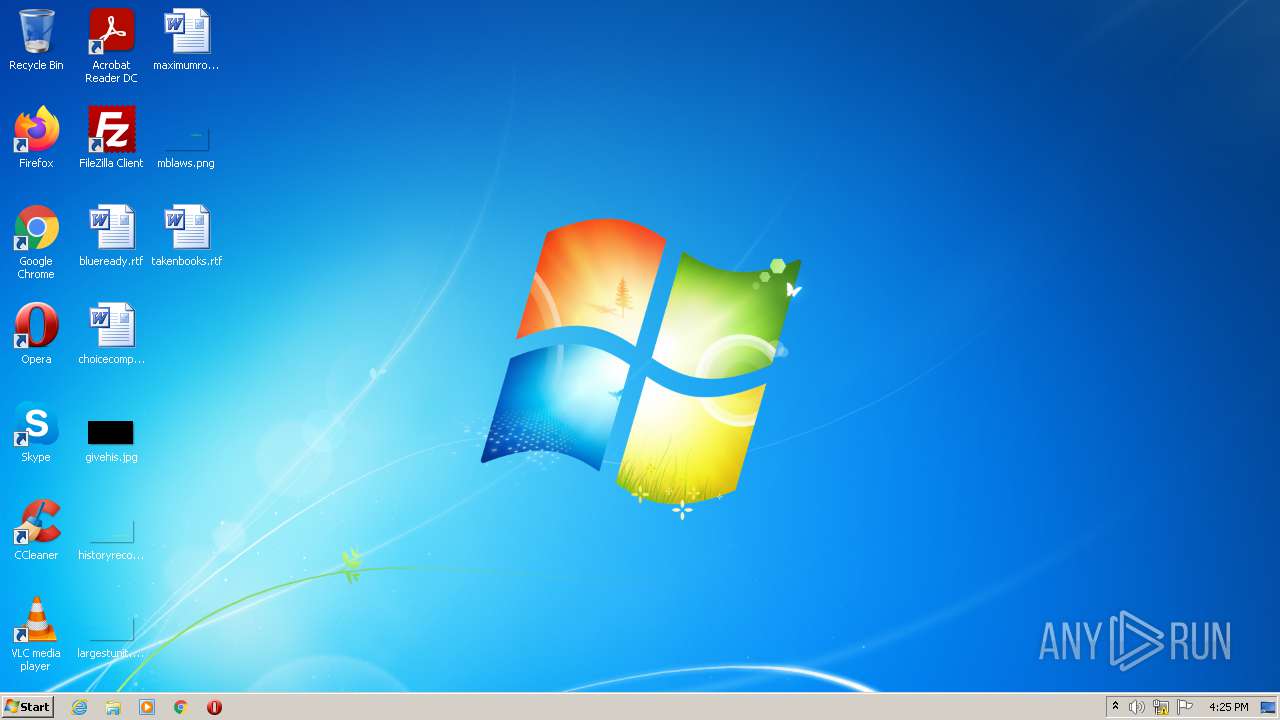
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | F853C1980A53AFCE89EBFF98D7C838E8 |
| SHA1: | 2FE4C81DCDF29E160C63576D1FC0C0BB88C2BB62 |
| SHA256: | A0CF3857C27C583483D336AADF3A0489E51872E597F4555916F9F344268D5D65 |
| SSDEEP: | 196608:N5X0mb7YaLaLHakCvQzKBJ2vy6lu4+Vxf+N3HeQSAFMjR:Y8HLcHzSvEqp4+Hf+x8J |
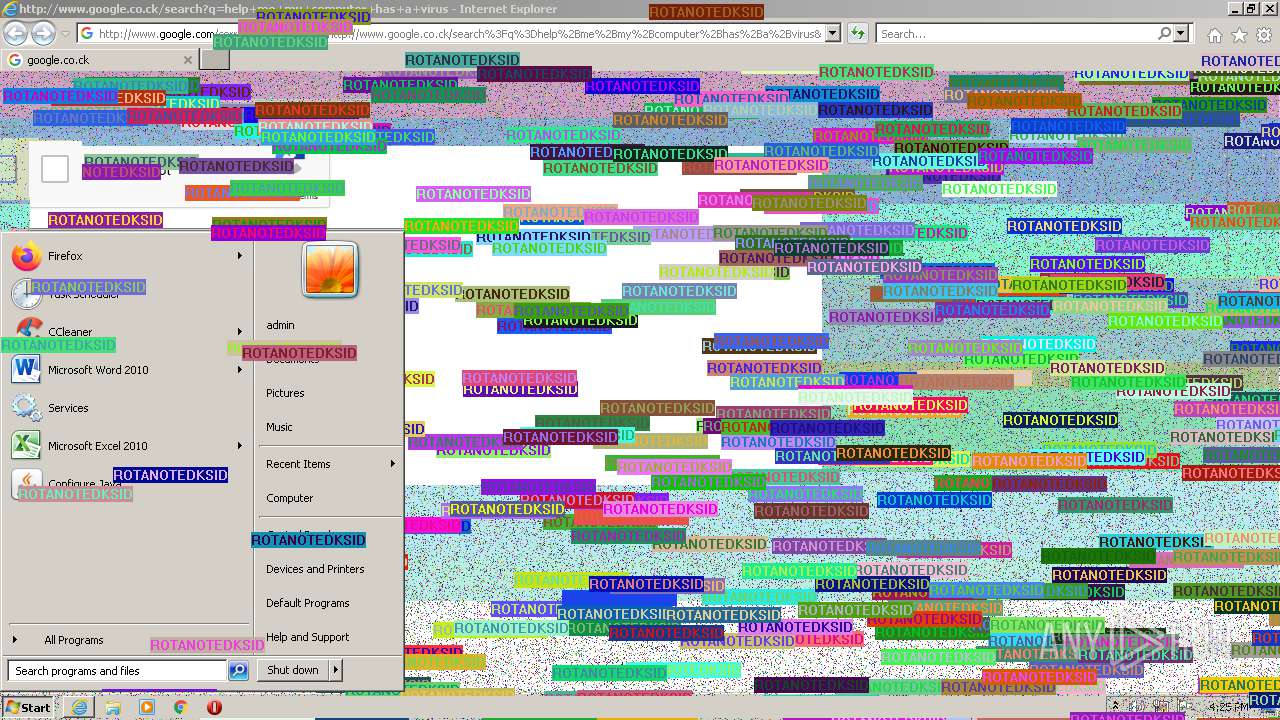
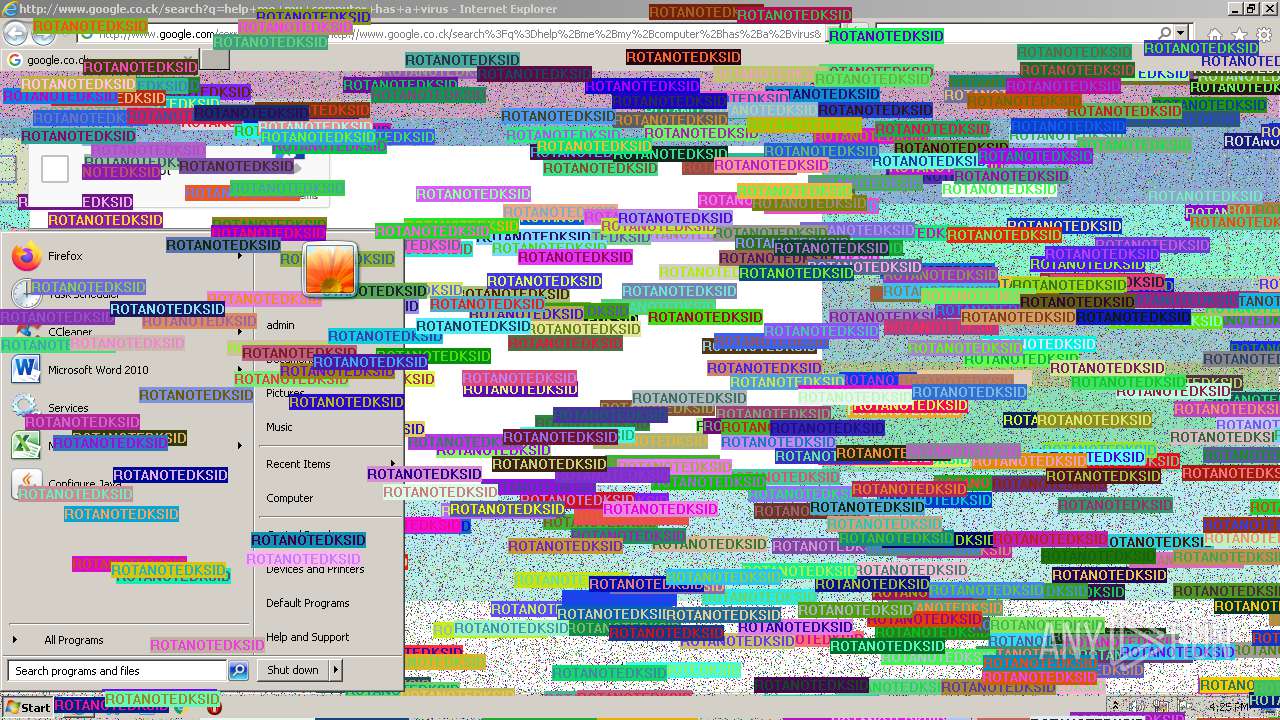
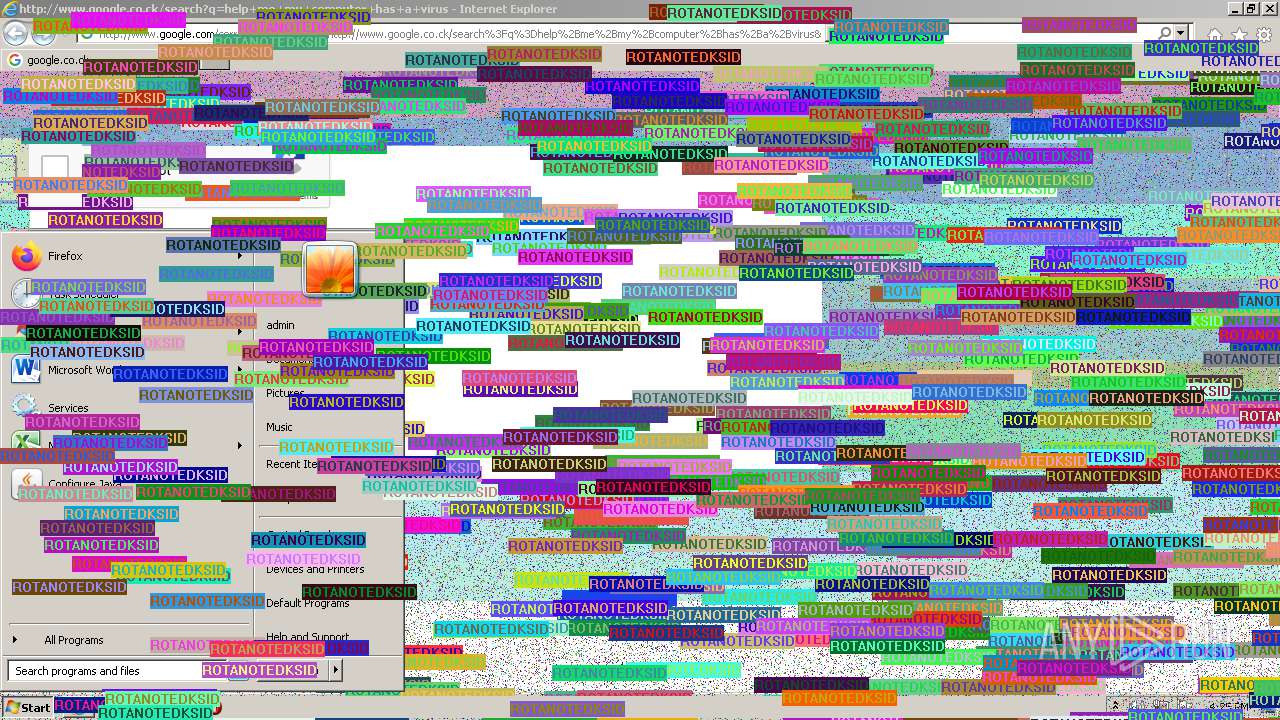
MALICIOUS
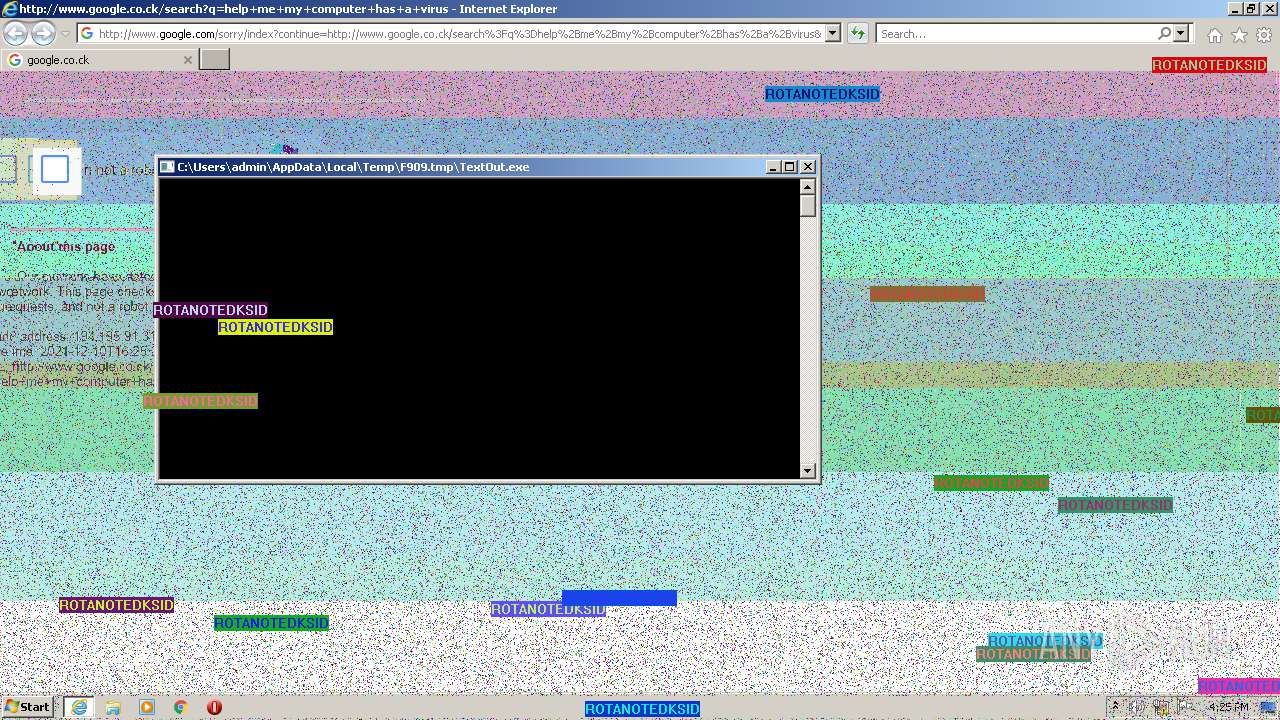
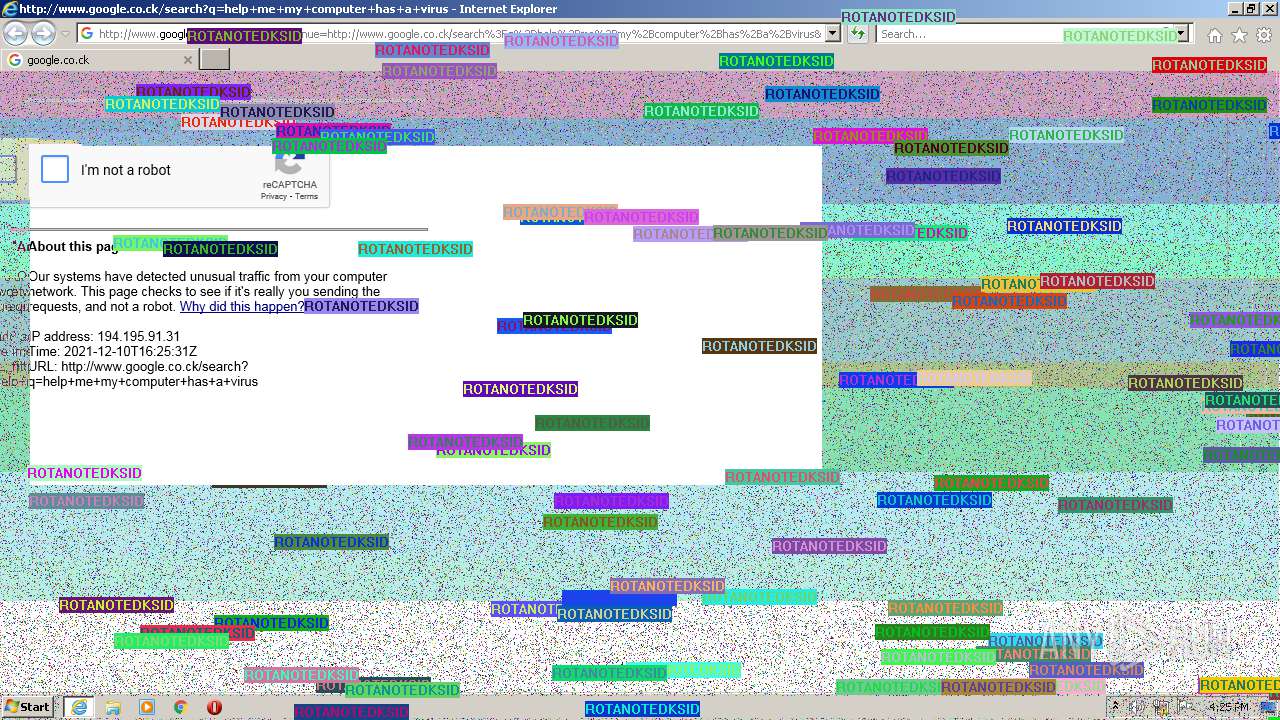
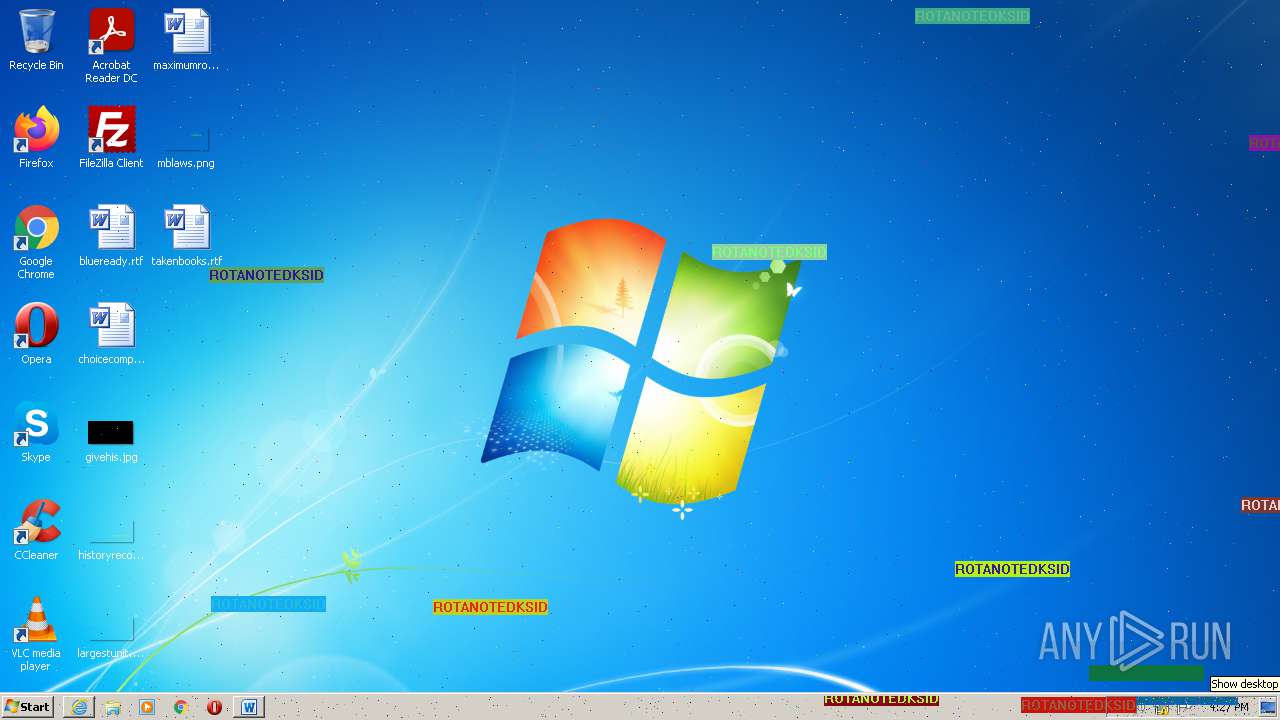
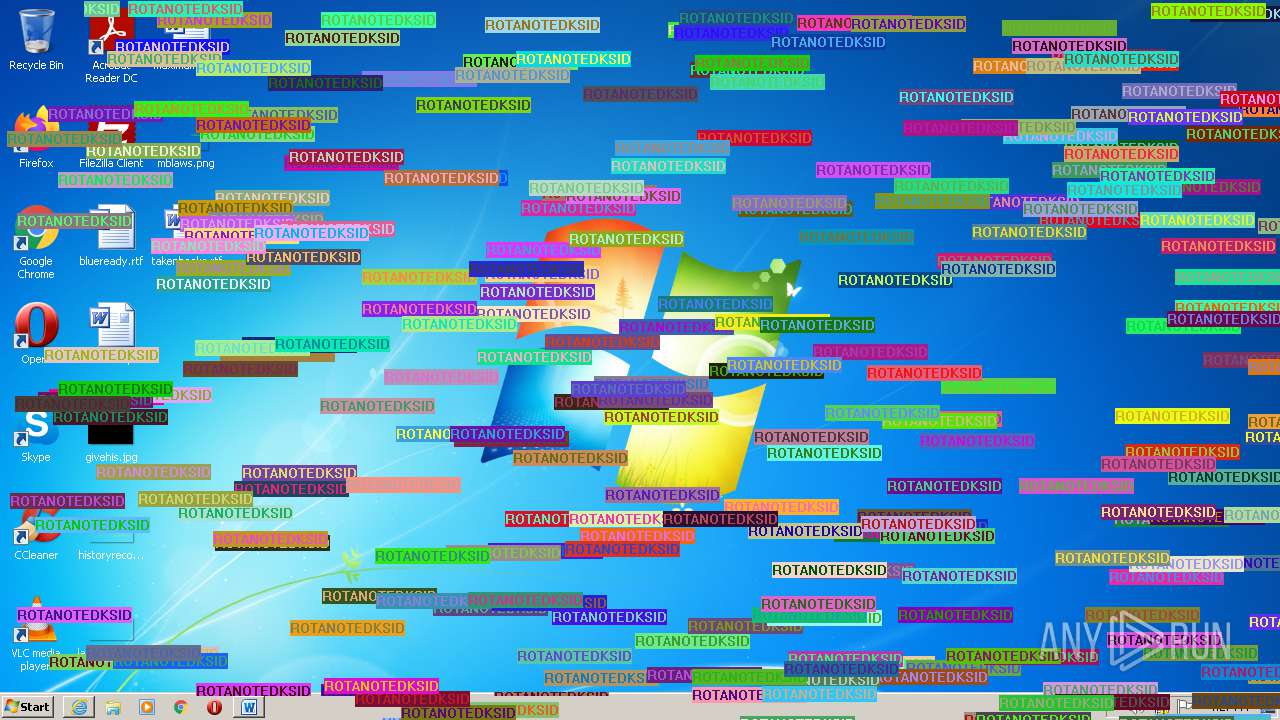
Application was dropped or rewritten from another process
- MouseDraw.exe (PID: 3128)
- TextOut.exe (PID: 2436)
- gl.exe (PID: 2232)
- pixels.exe (PID: 2332)
- masher.exe (PID: 3812)
SUSPICIOUS
Checks supported languages
- ROTANOTEDKSID-Clean.exe (PID: 2344)
- cmd.exe (PID: 3748)
- WScript.exe (PID: 3492)
- MouseDraw.exe (PID: 3128)
- pixels.exe (PID: 2332)
- gl.exe (PID: 2232)
- TextOut.exe (PID: 2436)
- masher.exe (PID: 3812)
Reads the computer name
- ROTANOTEDKSID-Clean.exe (PID: 2344)
- cmd.exe (PID: 3748)
- WScript.exe (PID: 3492)
Executable content was dropped or overwritten
- ROTANOTEDKSID-Clean.exe (PID: 2344)
Starts CMD.EXE for commands execution
- ROTANOTEDKSID-Clean.exe (PID: 2344)
Executes scripts
- cmd.exe (PID: 3748)
Drops a file that was compiled in debug mode
- ROTANOTEDKSID-Clean.exe (PID: 2344)
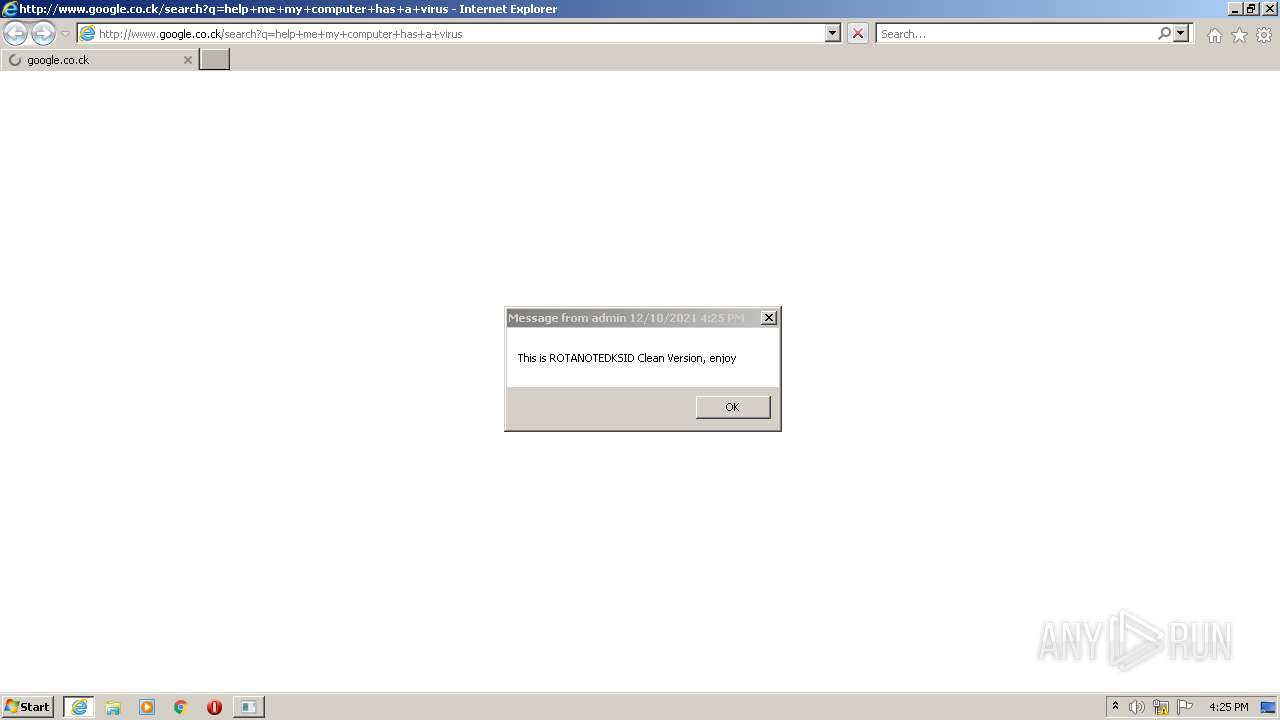
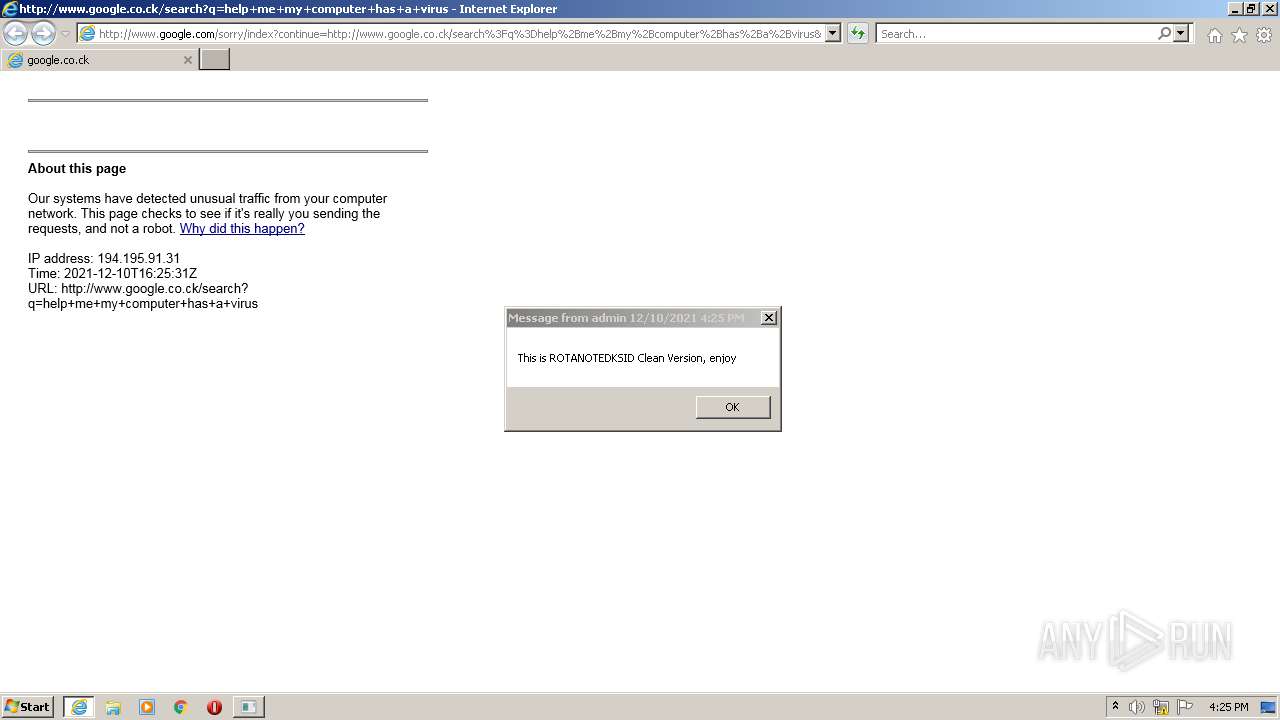
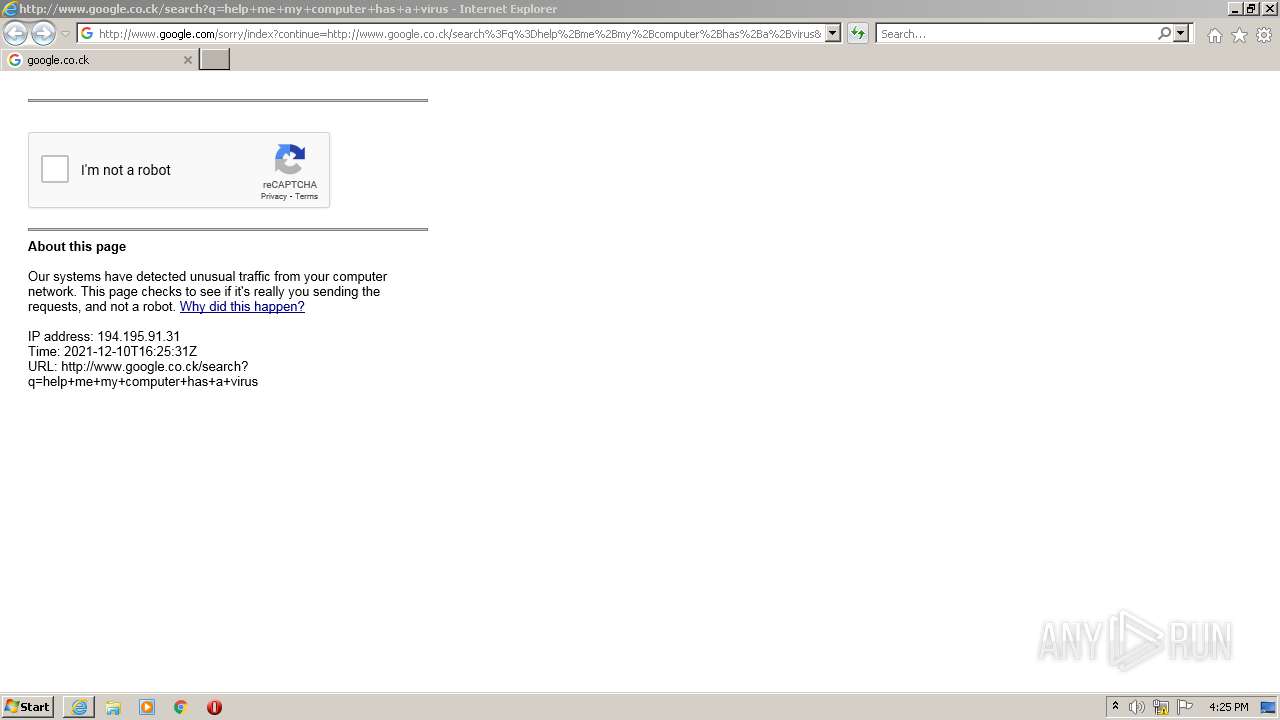
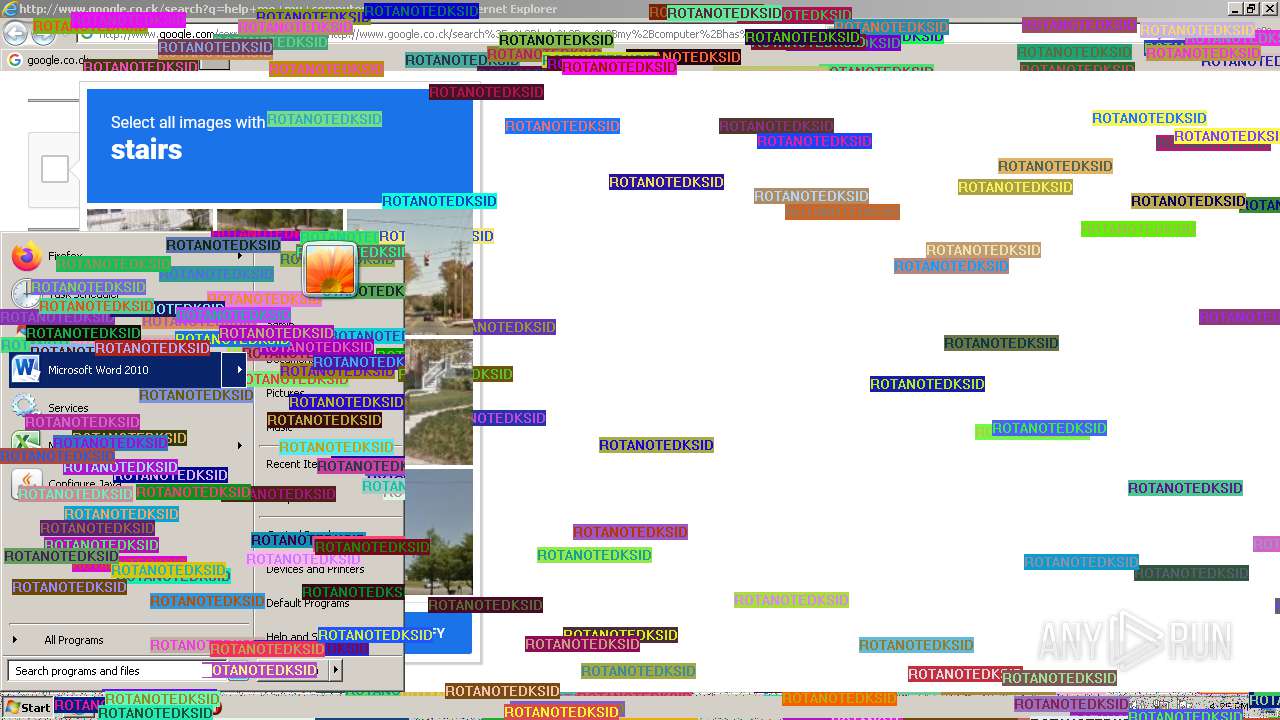
Starts Internet Explorer
- cmd.exe (PID: 3748)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3196)
INFO
Checks supported languages
- msg.exe (PID: 2856)
- timeout.exe (PID: 2280)
- timeout.exe (PID: 4084)
- iexplore.exe (PID: 1304)
- iexplore.exe (PID: 3196)
- timeout.exe (PID: 1760)
- timeout.exe (PID: 1340)
- timeout.exe (PID: 2184)
- WINWORD.EXE (PID: 3388)
Reads the computer name
- msg.exe (PID: 2856)
- iexplore.exe (PID: 1304)
- iexplore.exe (PID: 3196)
- WINWORD.EXE (PID: 3388)
Checks Windows Trust Settings
- WScript.exe (PID: 3492)
- iexplore.exe (PID: 3196)
- iexplore.exe (PID: 1304)
Application launched itself
- iexplore.exe (PID: 1304)
Reads internet explorer settings
- iexplore.exe (PID: 3196)
Reads settings of System Certificates
- iexplore.exe (PID: 3196)
- iexplore.exe (PID: 1304)
Creates files in the user directory
- iexplore.exe (PID: 3196)
- WINWORD.EXE (PID: 3388)
- iexplore.exe (PID: 1304)
Changes internet zones settings
- iexplore.exe (PID: 1304)
Manual execution by user
- WINWORD.EXE (PID: 3388)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1304)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3388)
Changes settings of System certificates
- iexplore.exe (PID: 1304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x174b4c0 |
| UninitializedDataSize: | 13660160 |
| InitializedDataSize: | 4096 |
| CodeSize: | 10768384 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2010:11:08 14:12:07+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Nov-2010 13:12:07 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Nov-2010 13:12:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00D07000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00D08000 | 0x00A45000 | 0x00A44200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99998 |
.rsrc | 0x0174D000 | 0x00001000 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.89333 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 7.40242 | 341 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F | 0 | 24366800 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
I | 6.48393 | 120 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 4.52356 | 23 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 2.58496 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
59
Monitored processes
17
Malicious processes
1
Suspicious processes
1
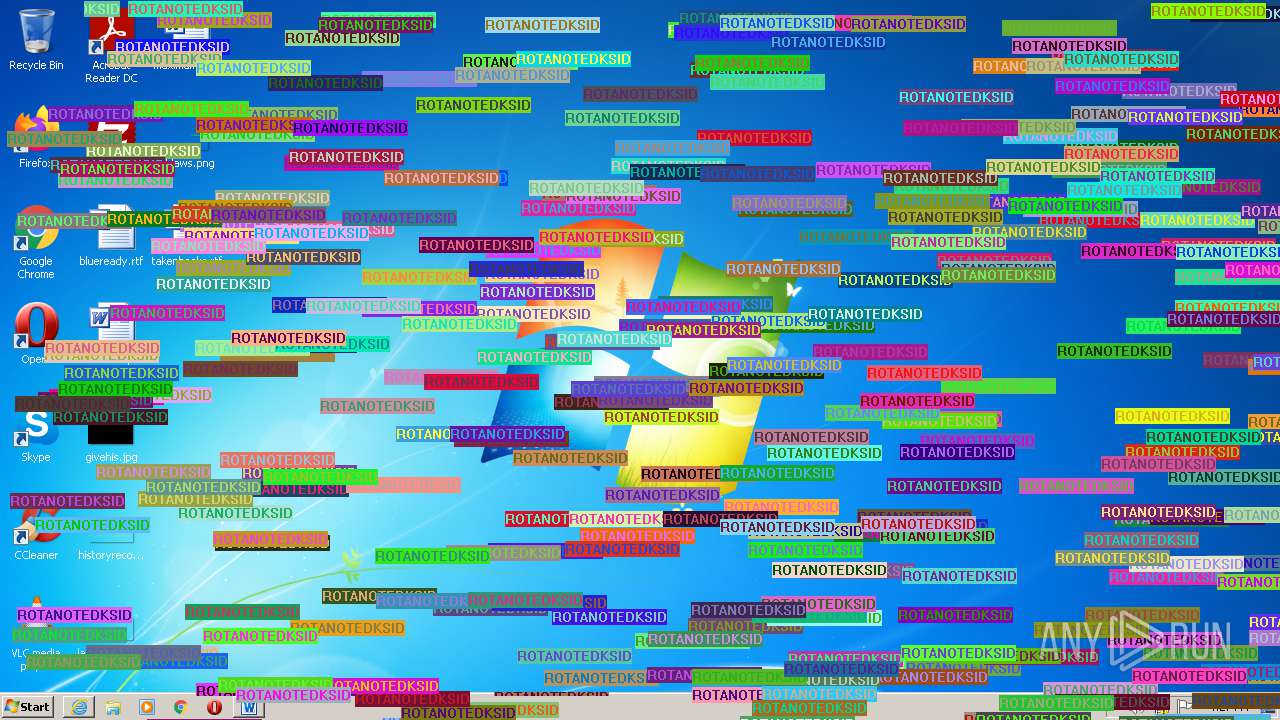
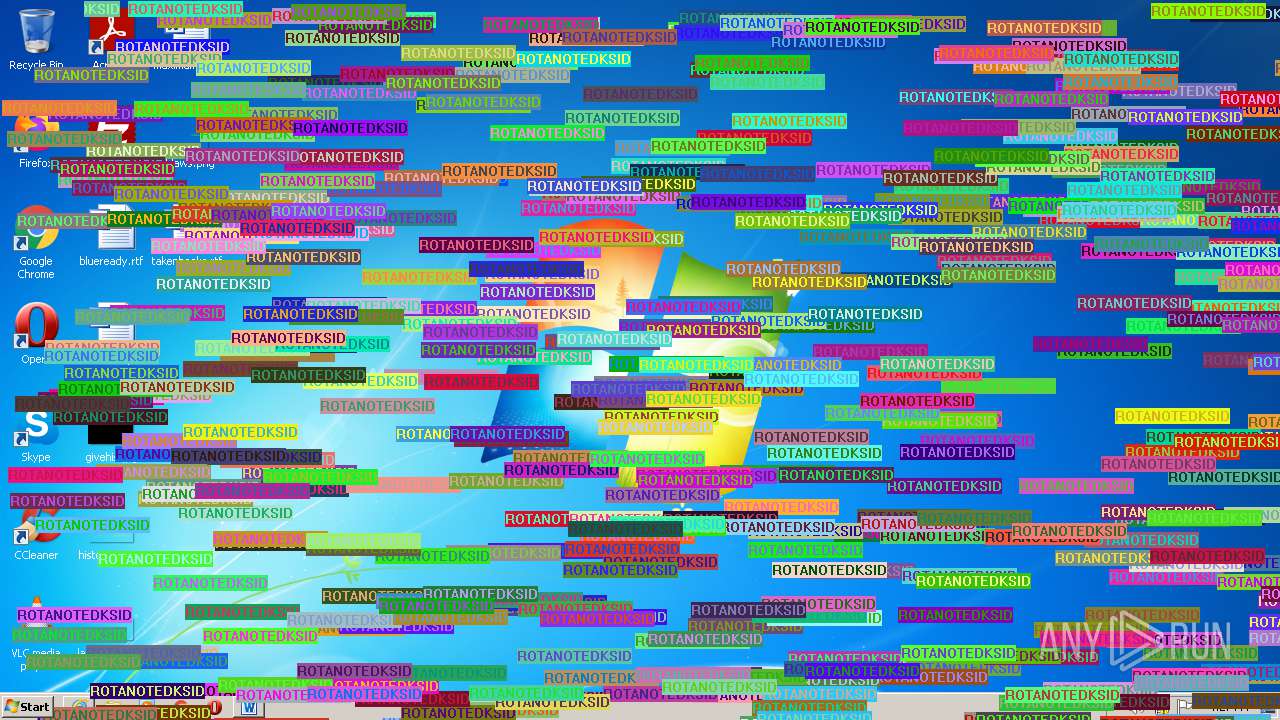
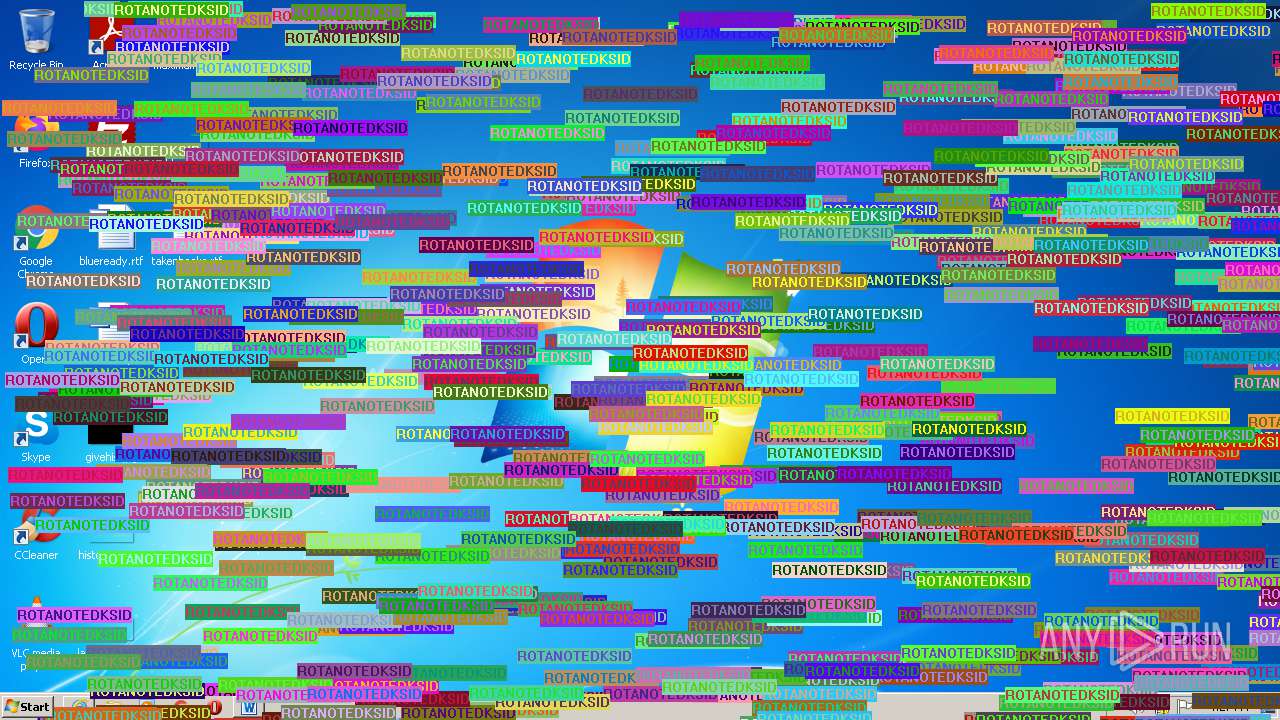
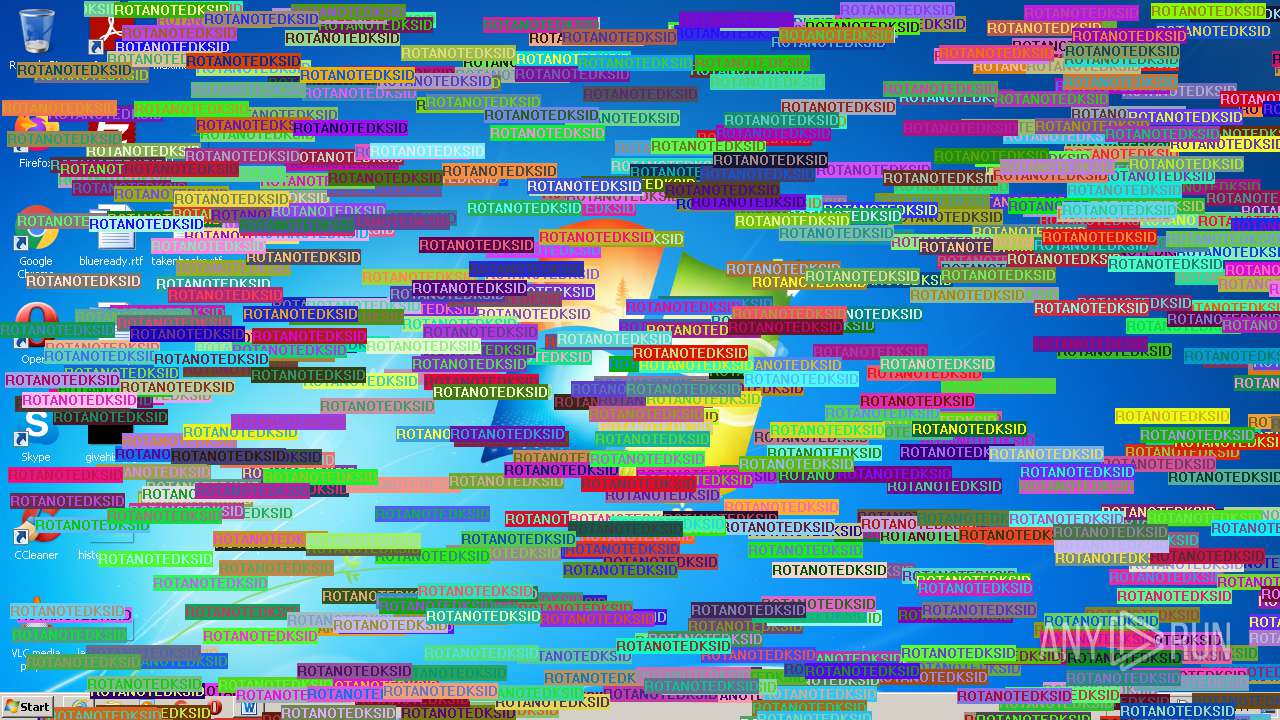
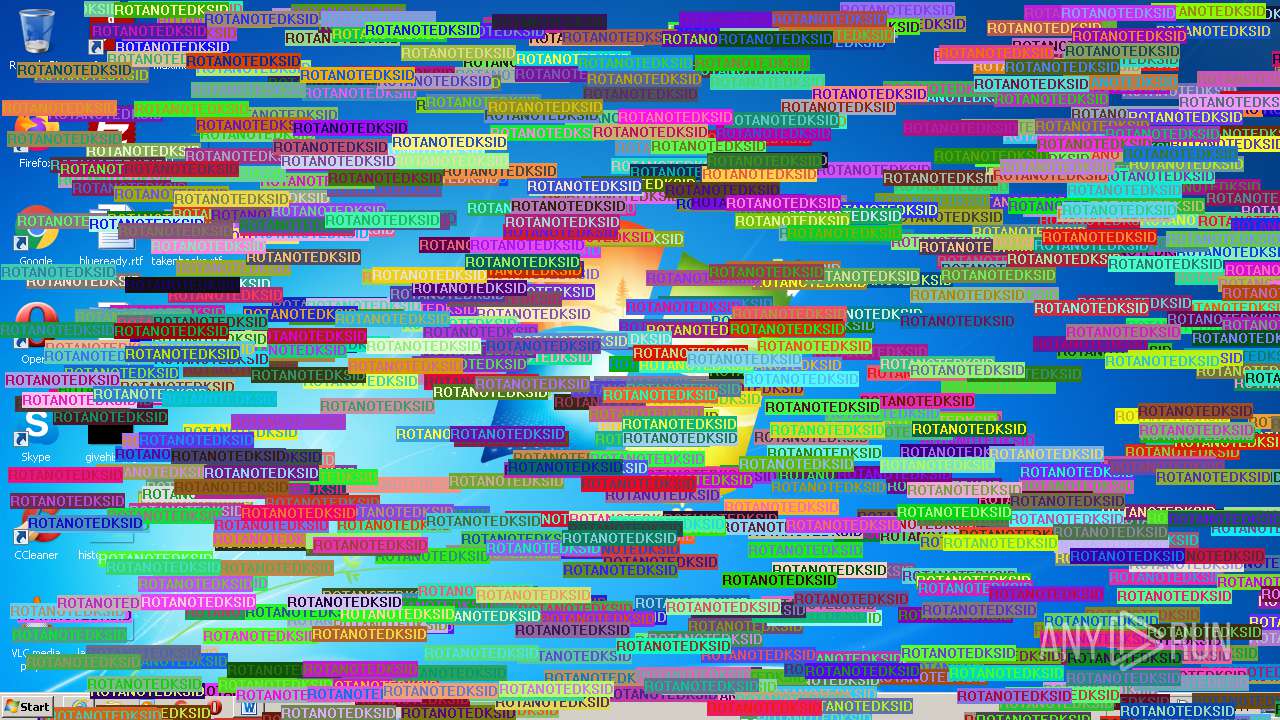
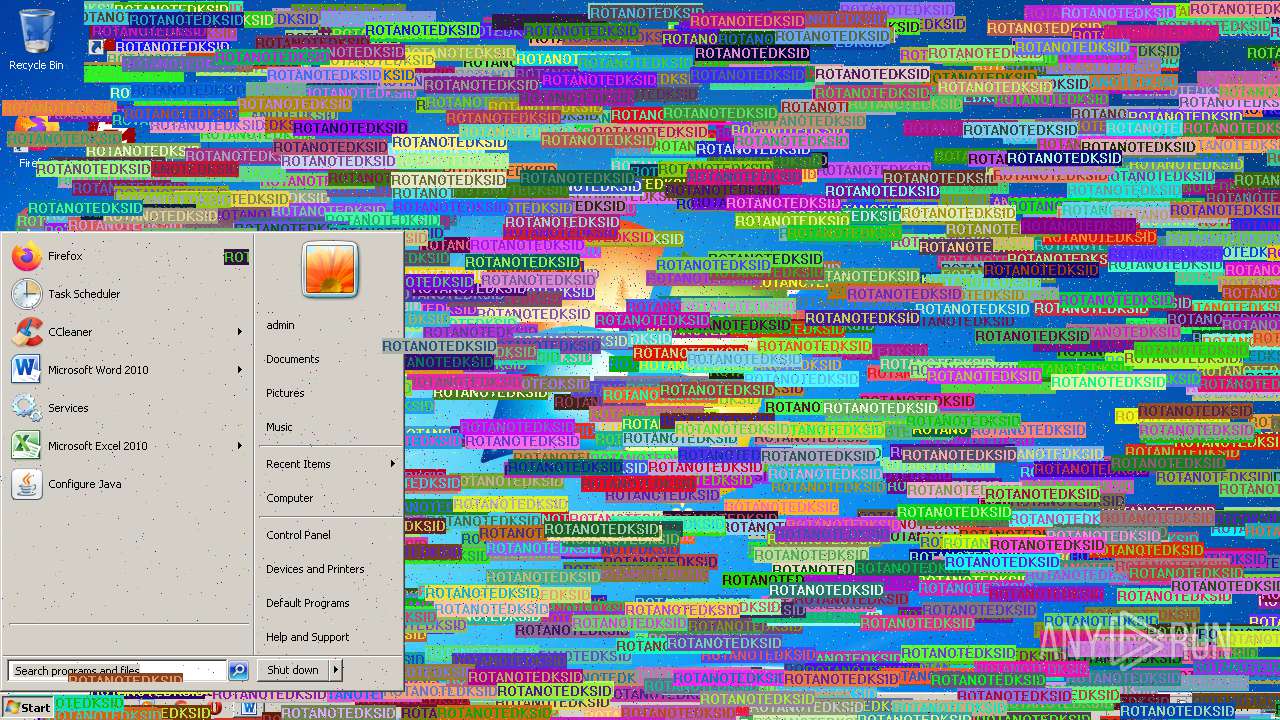
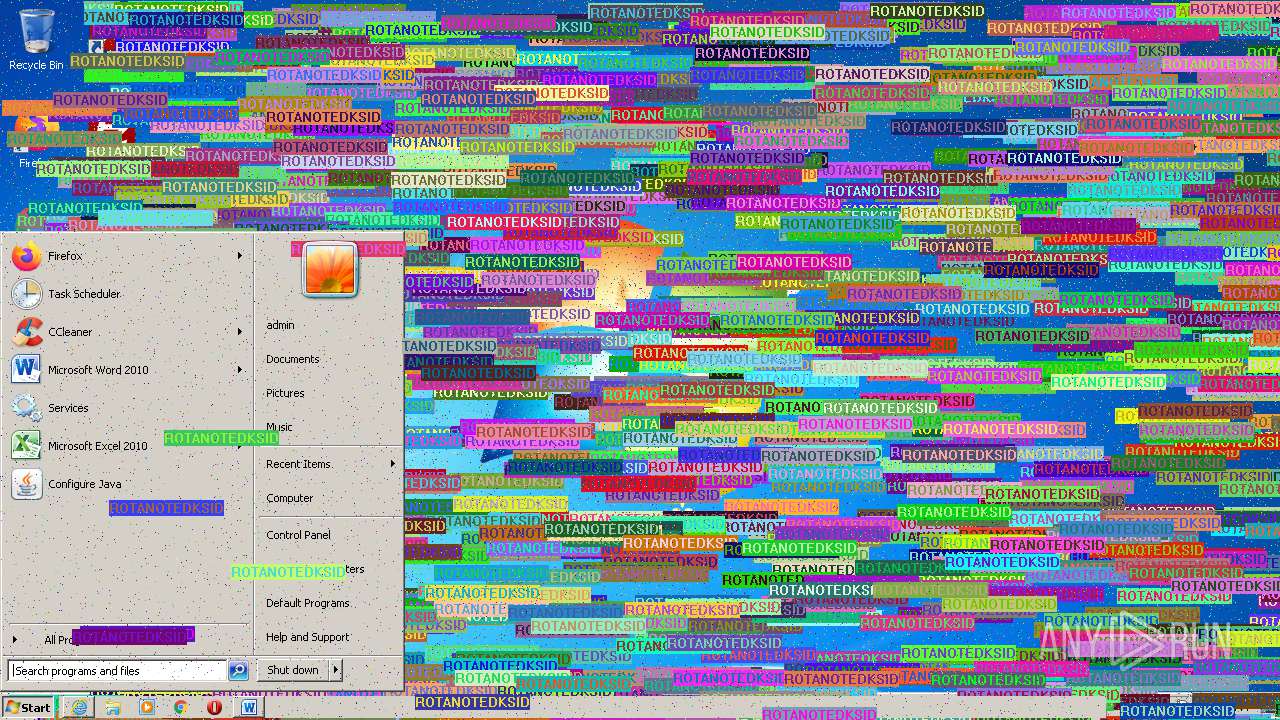
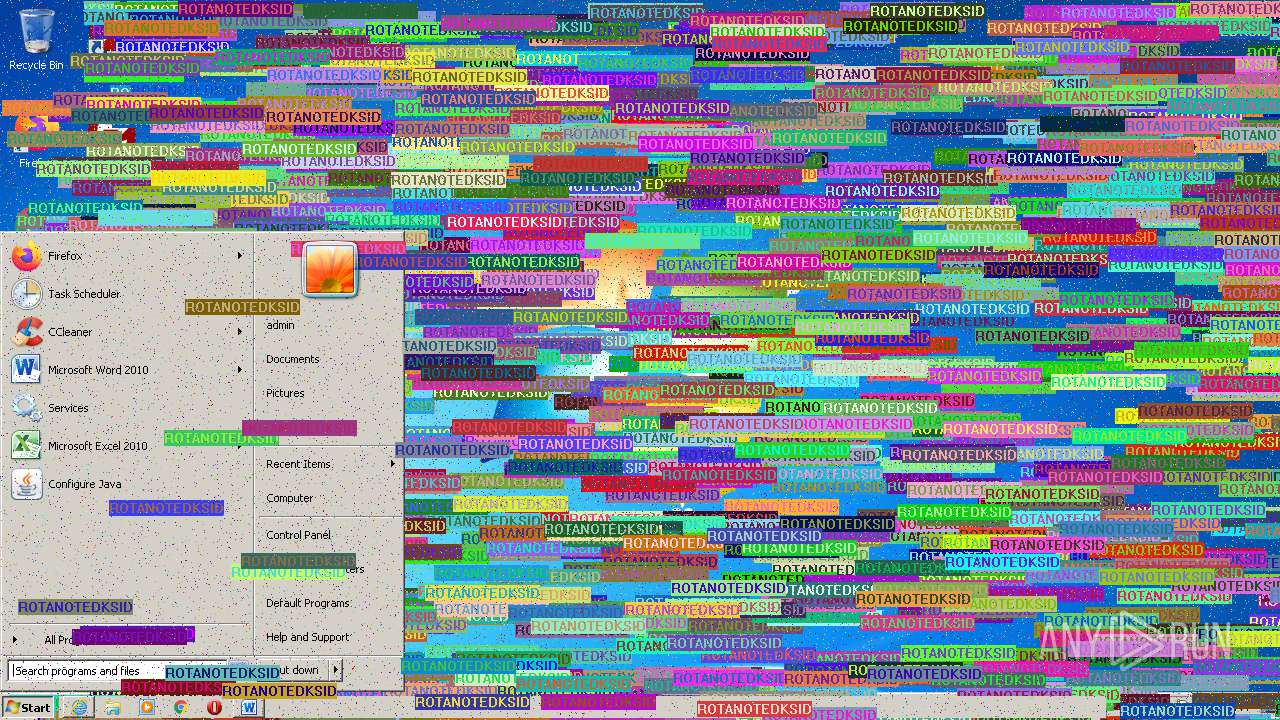
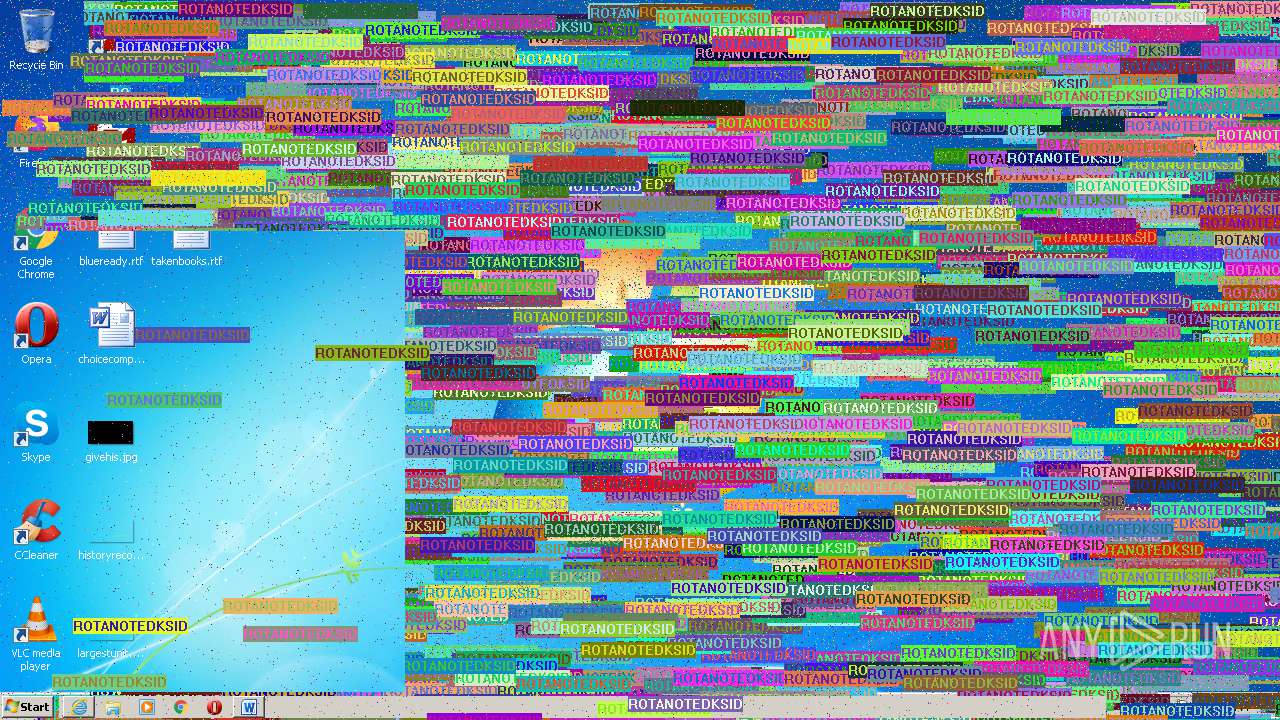
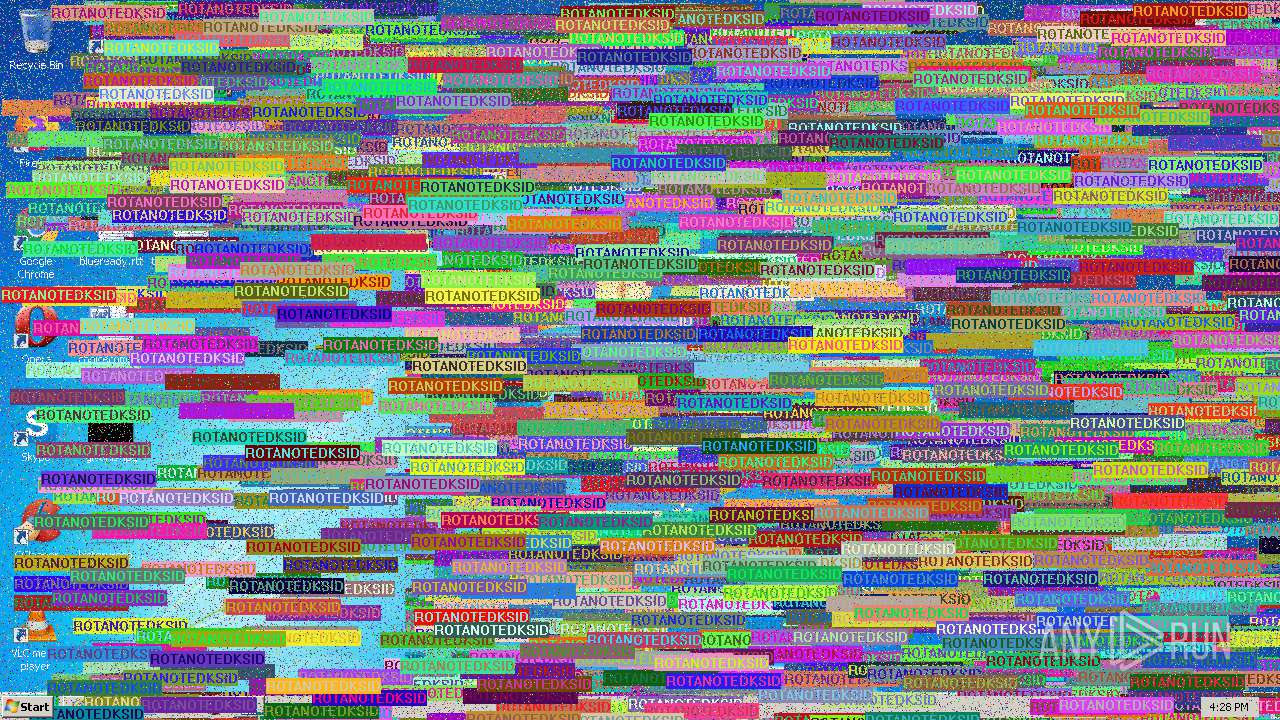
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
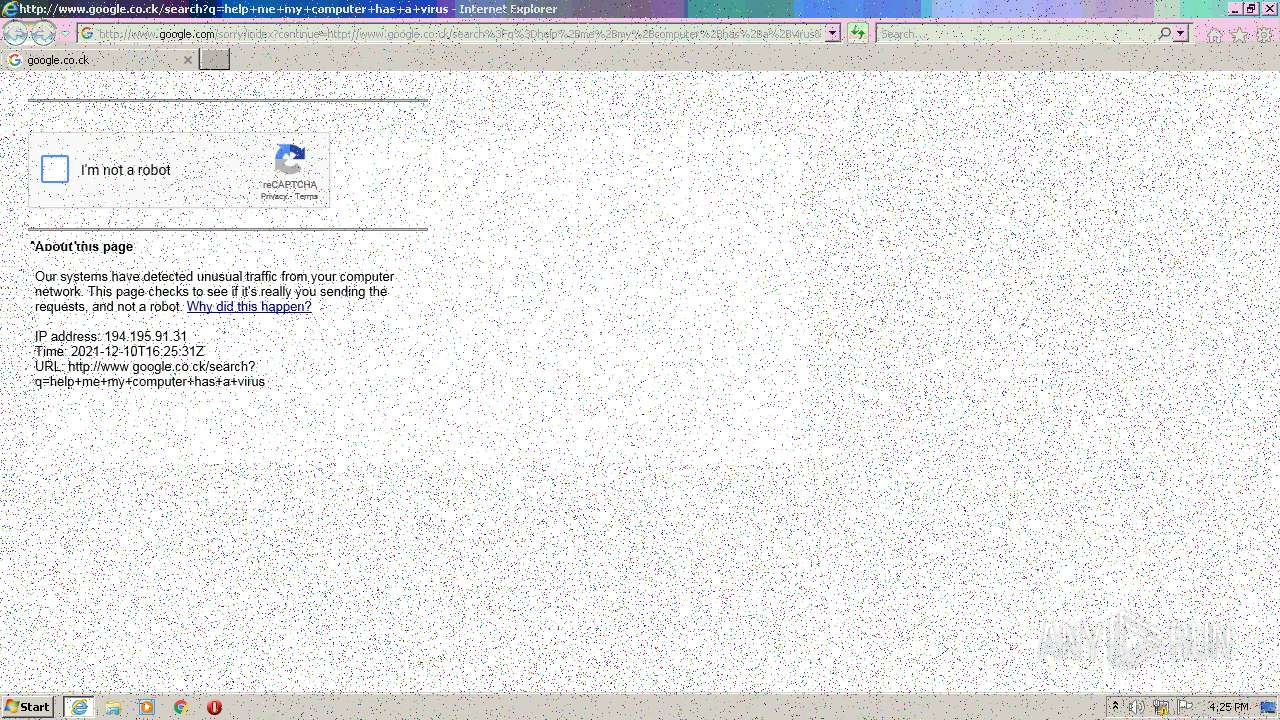
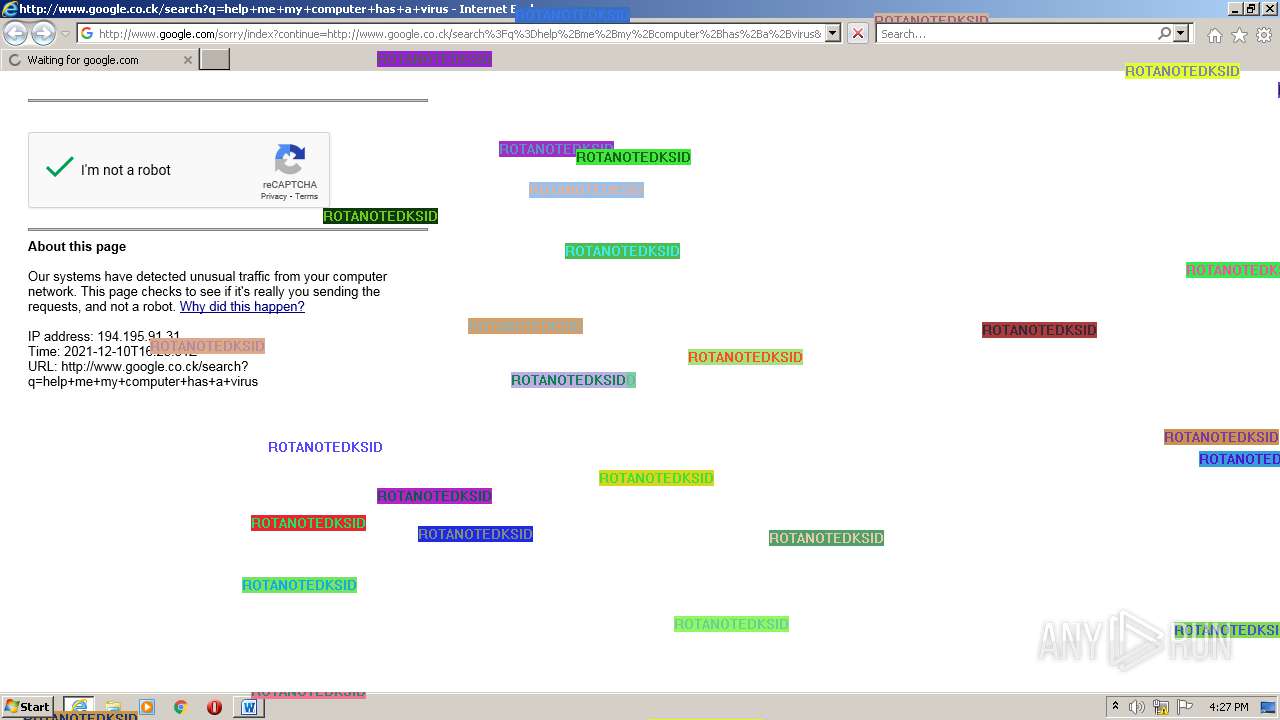
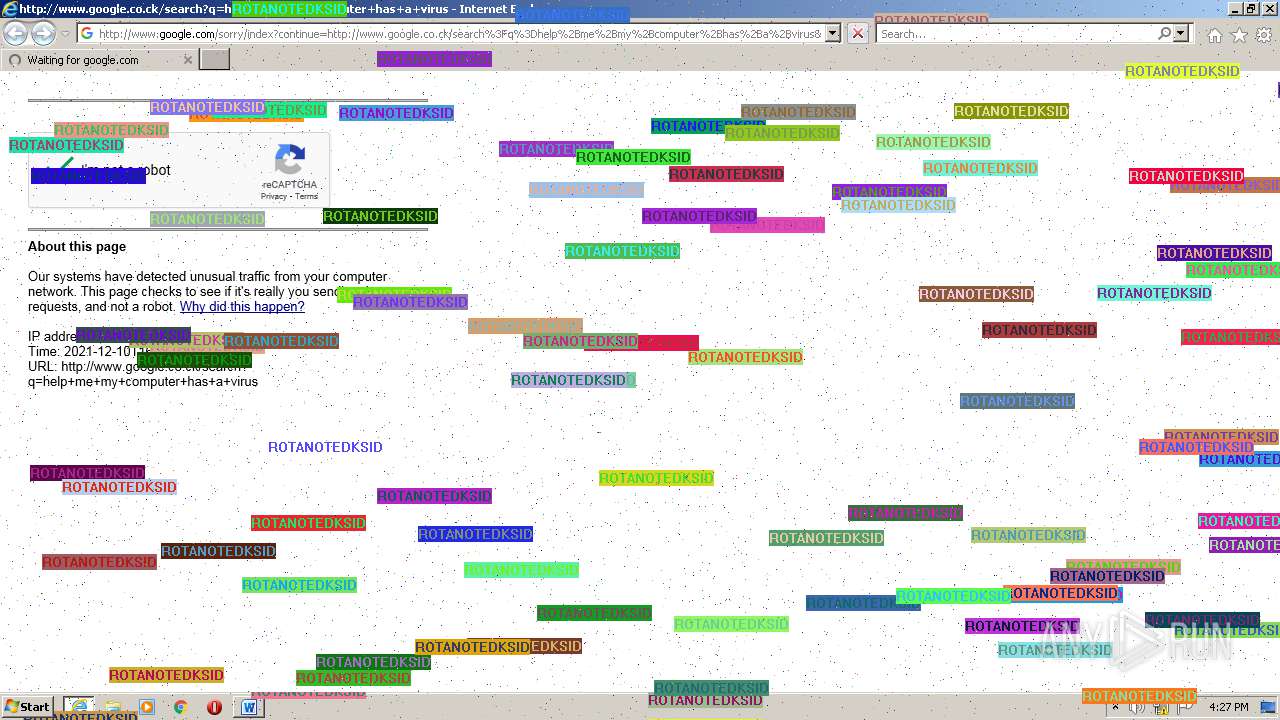
| 1304 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.google.co.ck/search?q=help+me+my+computer+has+a+virus | C:\Program Files\Internet Explorer\iexplore.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1340 | timeout 5 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1760 | timeout 10 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | timeout 30 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
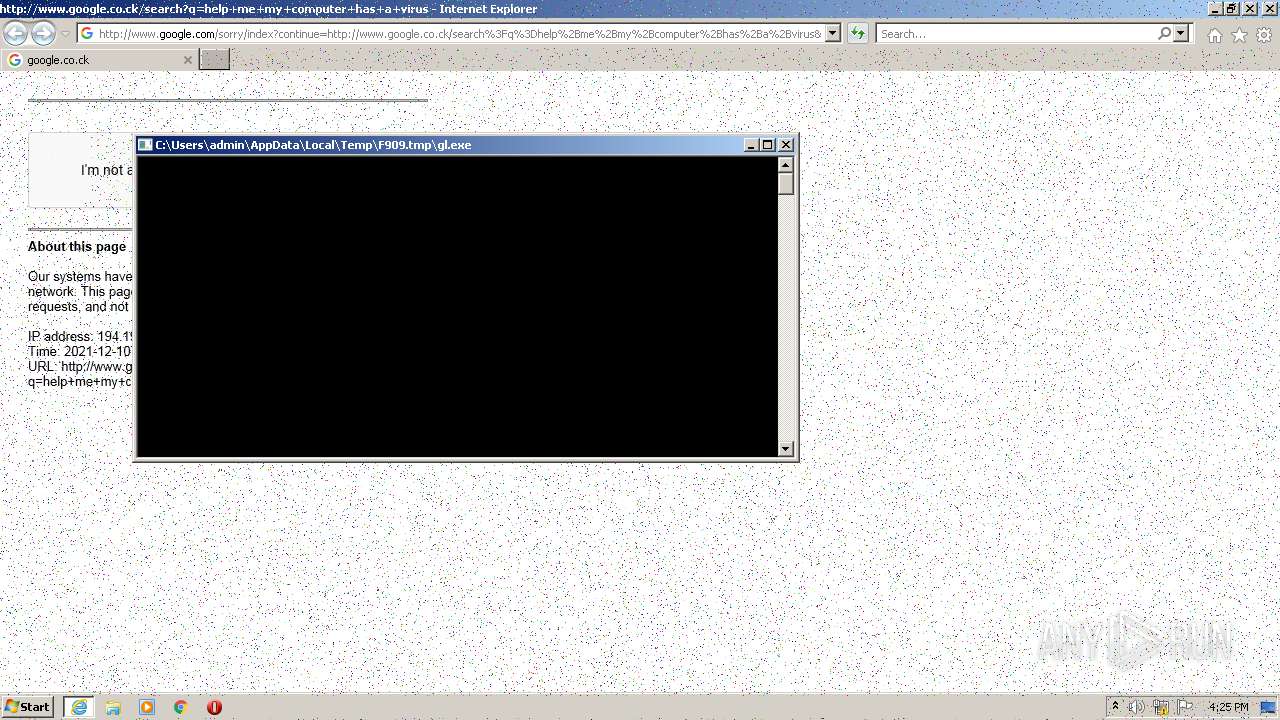
| 2232 | gl.exe | C:\Users\admin\AppData\Local\Temp\F909.tmp\gl.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2280 | timeout 5 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | pixels.exe | C:\Users\admin\AppData\Local\Temp\F909.tmp\pixels.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Local\Temp\ROTANOTEDKSID-Clean.exe" | C:\Users\admin\AppData\Local\Temp\ROTANOTEDKSID-Clean.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2436 | TextOut.exe | C:\Users\admin\AppData\Local\Temp\F909.tmp\TextOut.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2856 | msg * This is ROTANOTEDKSID Clean Version, enjoy | C:\Windows\system32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Message Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 708
Read events
16 849
Write events
689
Delete events
170
Modification events
| (PID) Process: | (2344) ROTANOTEDKSID-Clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2344) ROTANOTEDKSID-Clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2344) ROTANOTEDKSID-Clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2344) ROTANOTEDKSID-Clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3748) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3748) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3748) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3748) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3492) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {E46787A1-4629-4423-A693-BE1F003B2742} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 010000000000000027620288E2EDD701 | |||
| (PID) Process: | (3492) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | LastScreensaverSetThreadExecutionState |
Value: | |||
Executable files
5
Suspicious files
12
Text files
27
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | ROTANOTEDKSID-Clean.exe | C:\Users\admin\AppData\Local\Temp\F909.tmp\boom.wav | — | |
MD5:— | SHA256:— | |||
| 2344 | ROTANOTEDKSID-Clean.exe | C:\Users\admin\AppData\Local\Temp\F909.tmp\snd.vbs | text | |
MD5:7F1F2F18B81C7FF47430C518DEFB9F48 | SHA256:208337C0A3656061AD50D85B608CC0FEC353F71D16CCD6896AAE2ED4E5BDFA58 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\recaptcha__en[1].js | text | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_372439F36B9916D184DAE33F964401E9 | der | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\265C0DEB29181DD1891051371C5F863A_8765BBA90BB648A0F9D8A21C36EE4B24 | der | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_372439F36B9916D184DAE33F964401E9 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
33
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECfNBPn5G9WUCgAAAAEiTgk%3D | US | der | 471 b | whitelisted |
1304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3196 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3196 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDASfELQlAj2goAAAABIlBD | US | der | 472 b | whitelisted |
1304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
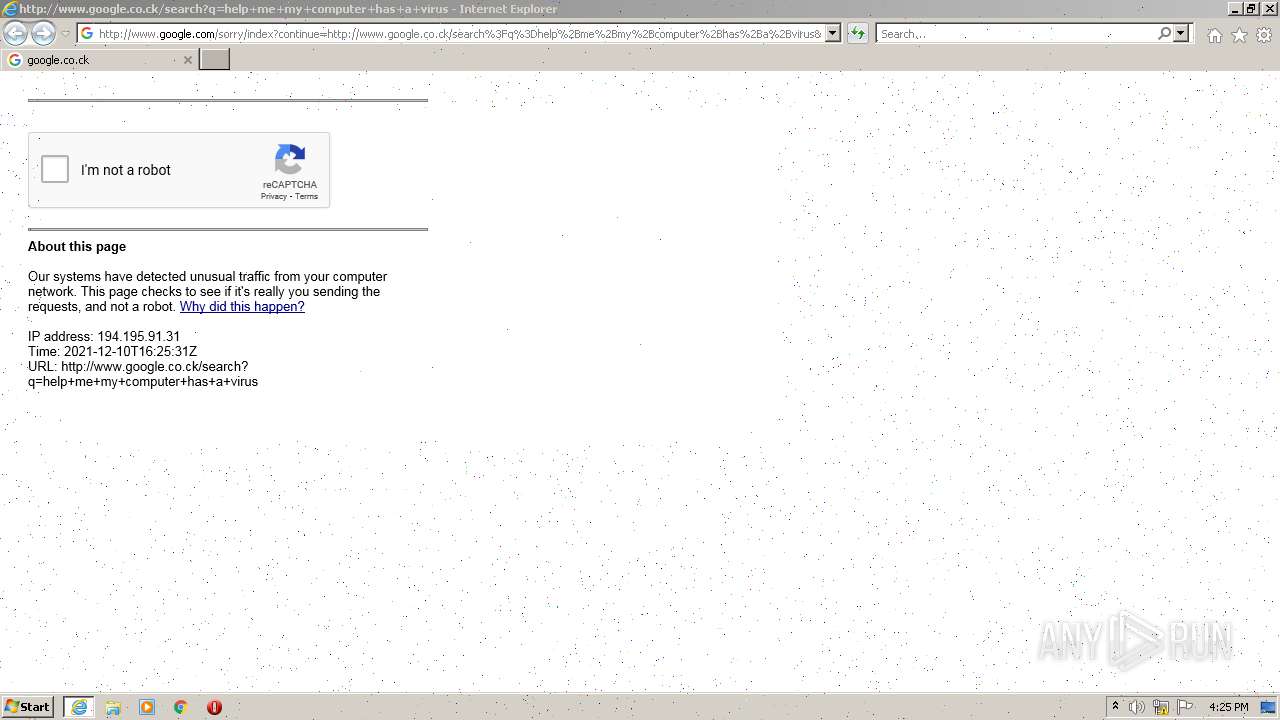
3196 | iexplore.exe | GET | 302 | 142.250.185.227:80 | http://www.google.co.ck/search?q=help+me+my+computer+has+a+virus | US | html | 371 b | whitelisted |
1304 | iexplore.exe | GET | 200 | 142.250.185.228:80 | http://www.google.com/favicon.ico | US | image | 1.46 Kb | malicious |
3196 | iexplore.exe | POST | 302 | 142.250.185.228:80 | http://www.google.com/sorry/index | US | html | 473 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3196 | iexplore.exe | 142.250.185.227:80 | www.google.co.ck | Google Inc. | US | whitelisted |
3196 | iexplore.exe | 142.250.185.228:80 | www.google.com | Google Inc. | US | whitelisted |
3196 | iexplore.exe | 23.32.238.192:80 | ctldl.windowsupdate.com | XO Communications | US | unknown |
3196 | iexplore.exe | 142.250.185.228:443 | www.google.com | Google Inc. | US | whitelisted |
3196 | iexplore.exe | 142.250.185.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3196 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1304 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1304 | iexplore.exe | 142.250.185.228:80 | www.google.com | Google Inc. | US | whitelisted |
1304 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1304 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.co.ck |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |