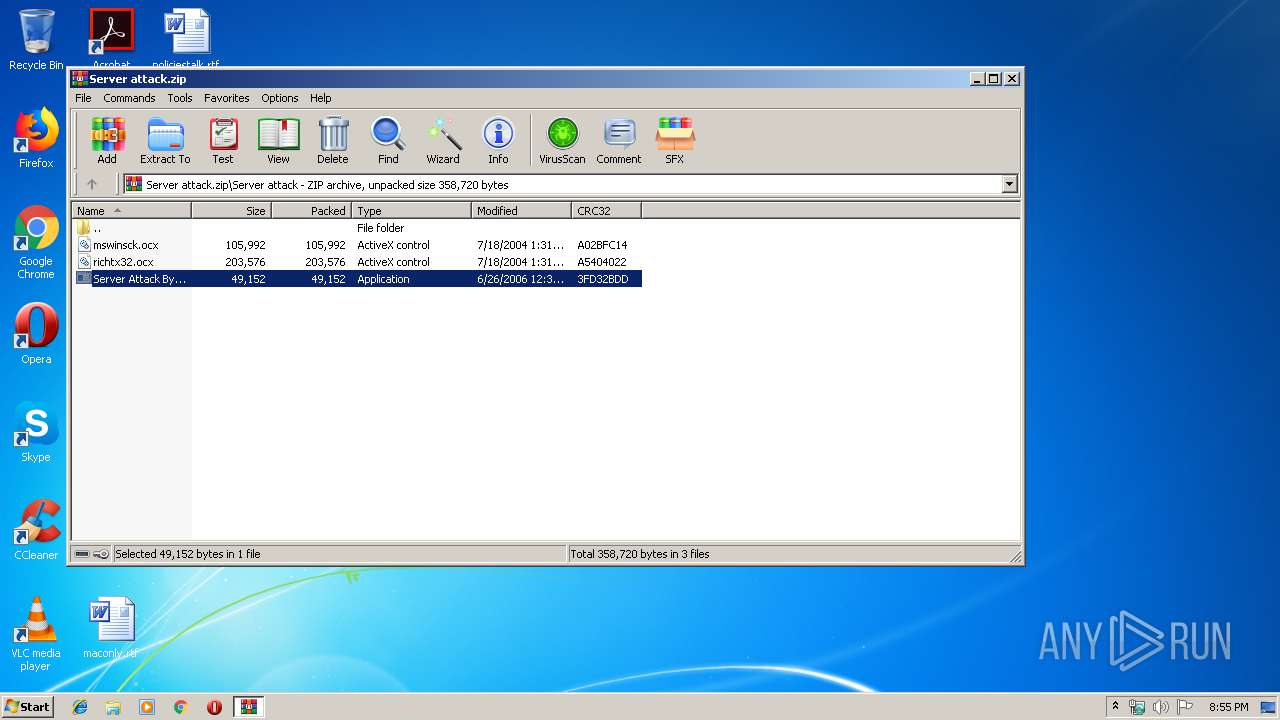
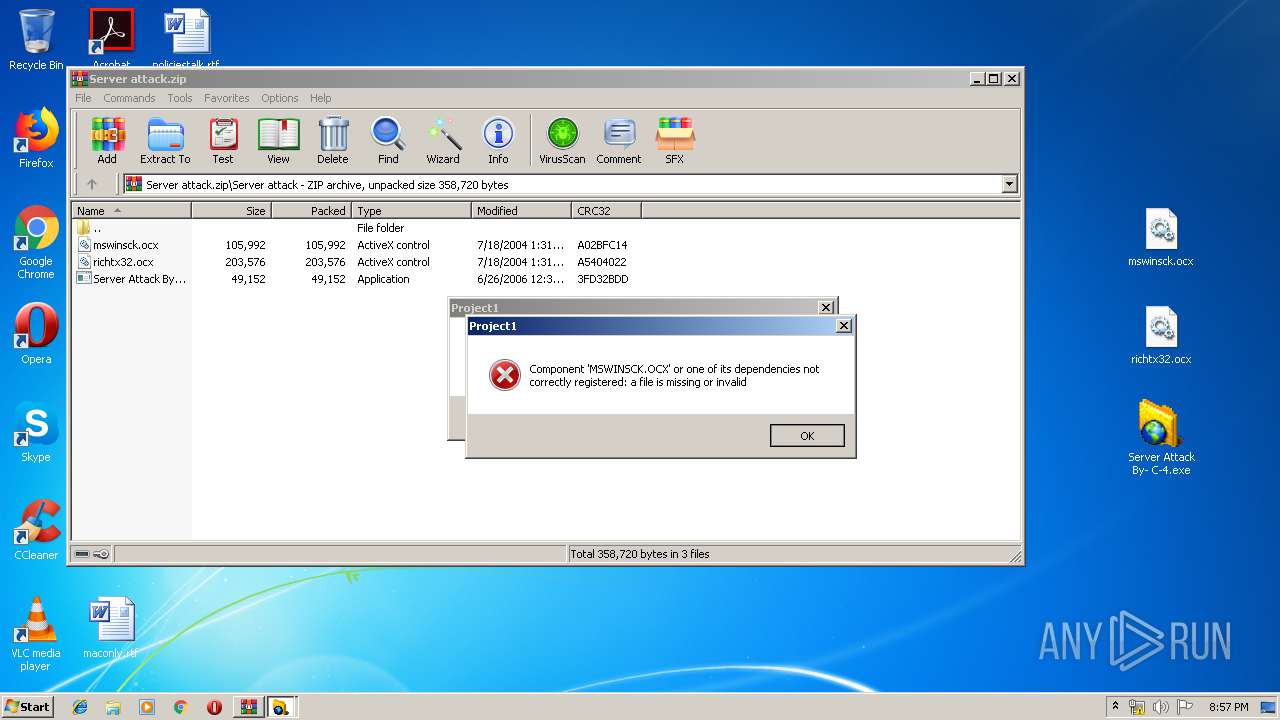
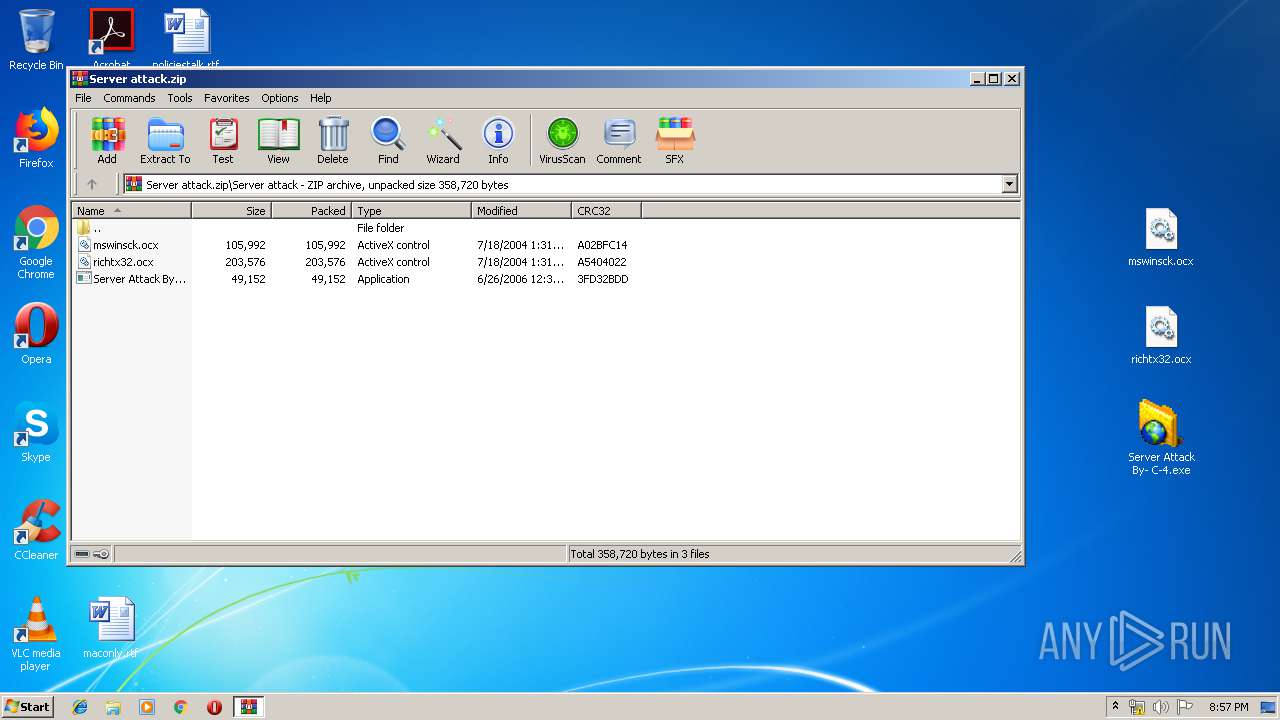
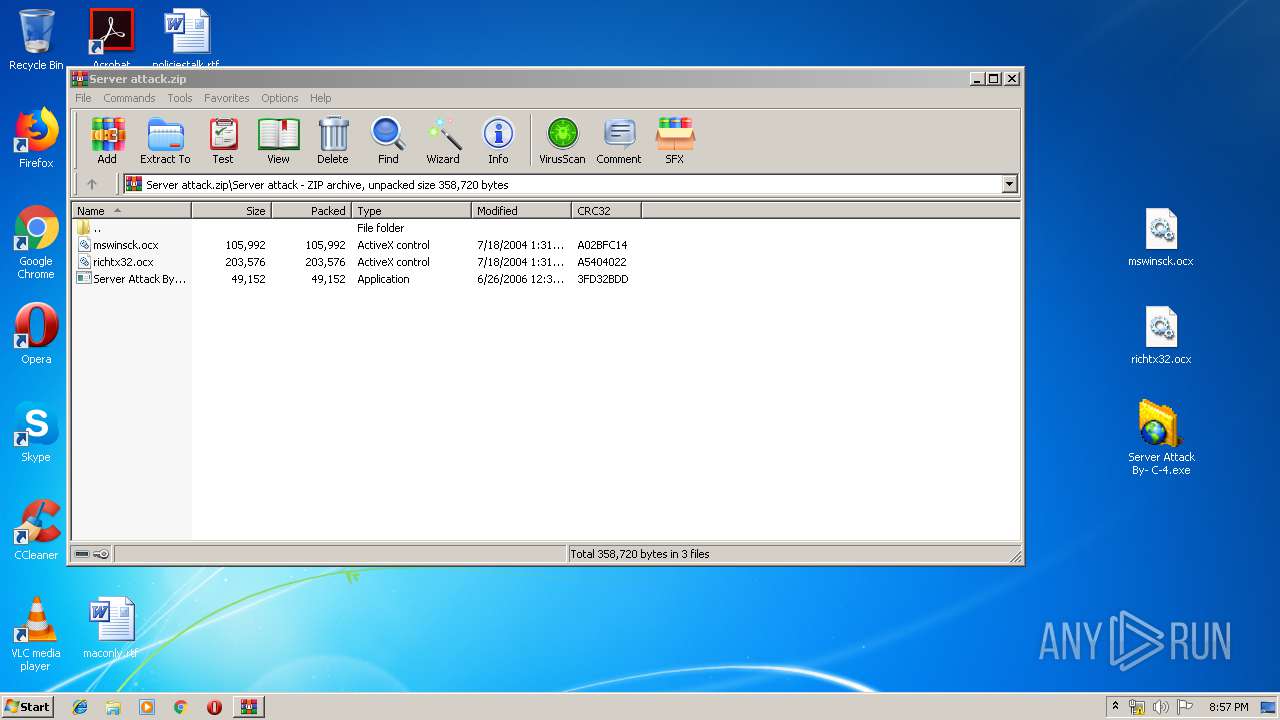
| File name: | Server attack.zip |
| Full analysis: | https://app.any.run/tasks/30f07579-e888-4f63-85b6-f0c66a9f487e |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 19:55:20 |
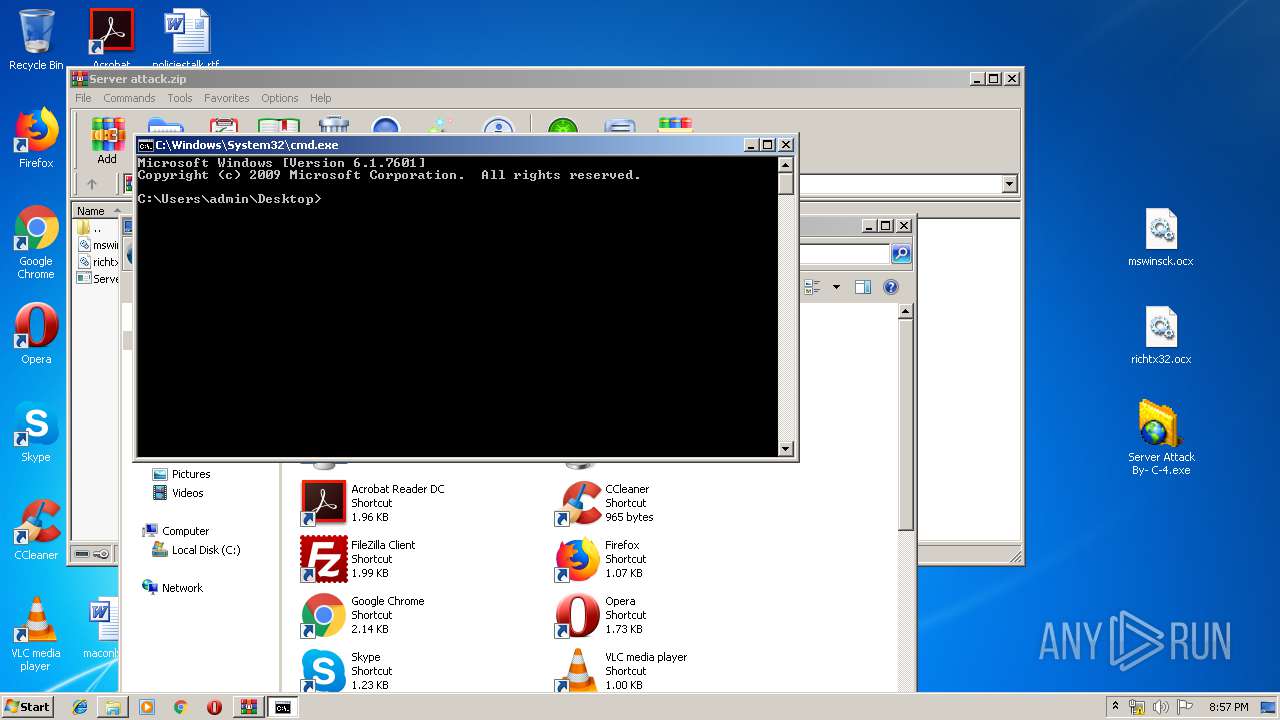
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8E411DC4F7224DC875380575F57218B6 |
| SHA1: | 39BDAF11DE0AF051A9F9ADEAAD804AA8F079836C |
| SHA256: | A0C65DBD27B4478D806299F10014DCA8B457A8793BBBA2FE1E71CCFF1E50E325 |
| SSDEEP: | 6144:e7IknjbYqRsdw8R/i+EbsI8HgNWRNGq+FdgJU3/j6pKrc8w:yINqRMw8U+EGgNWRN2Fdp6Ircf |
MALICIOUS
Application was dropped or rewritten from another process
- Server Attack By- C-4.exe (PID: 2856)
- Server Attack By- C-4.exe (PID: 2648)
- Server Attack By- C-4.exe (PID: 3872)
- Server Attack By- C-4.exe (PID: 2680)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 316)
- Server Attack By- C-4.exe (PID: 2856)
- Server Attack By- C-4.exe (PID: 2648)
- Server Attack By- C-4.exe (PID: 3872)
- Server Attack By- C-4.exe (PID: 2680)
- regsvr32.exe (PID: 3812)
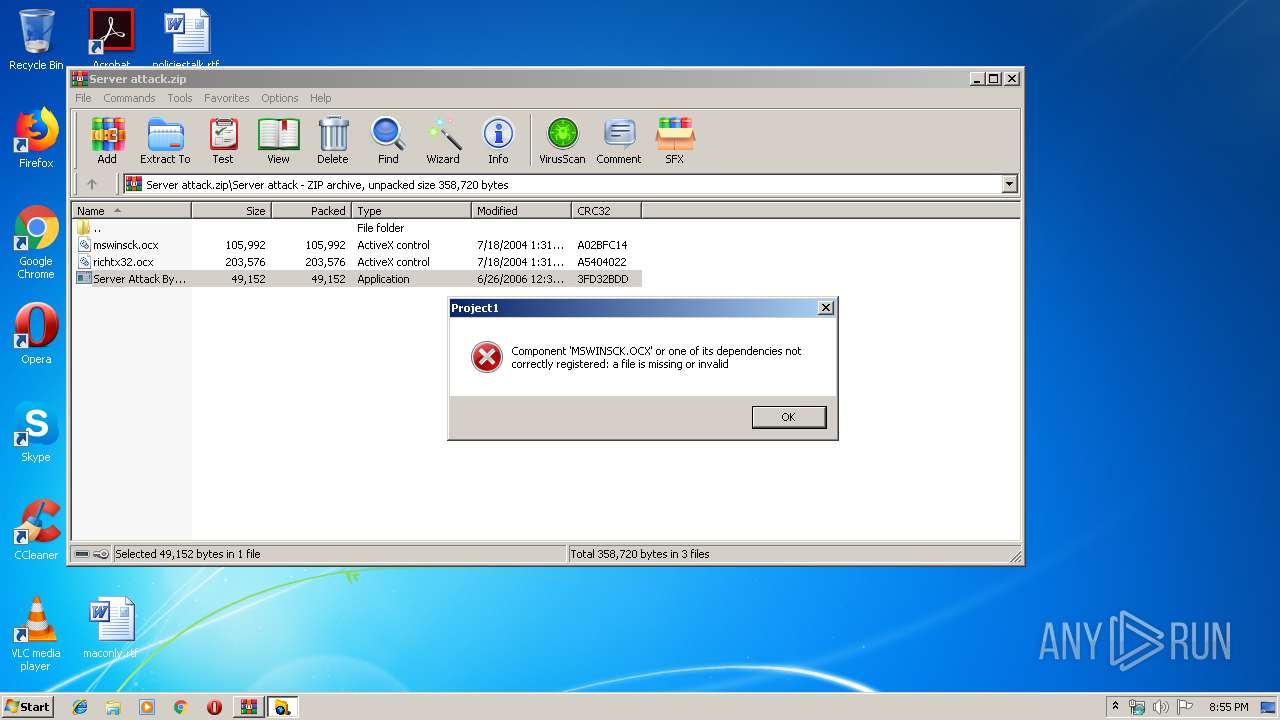
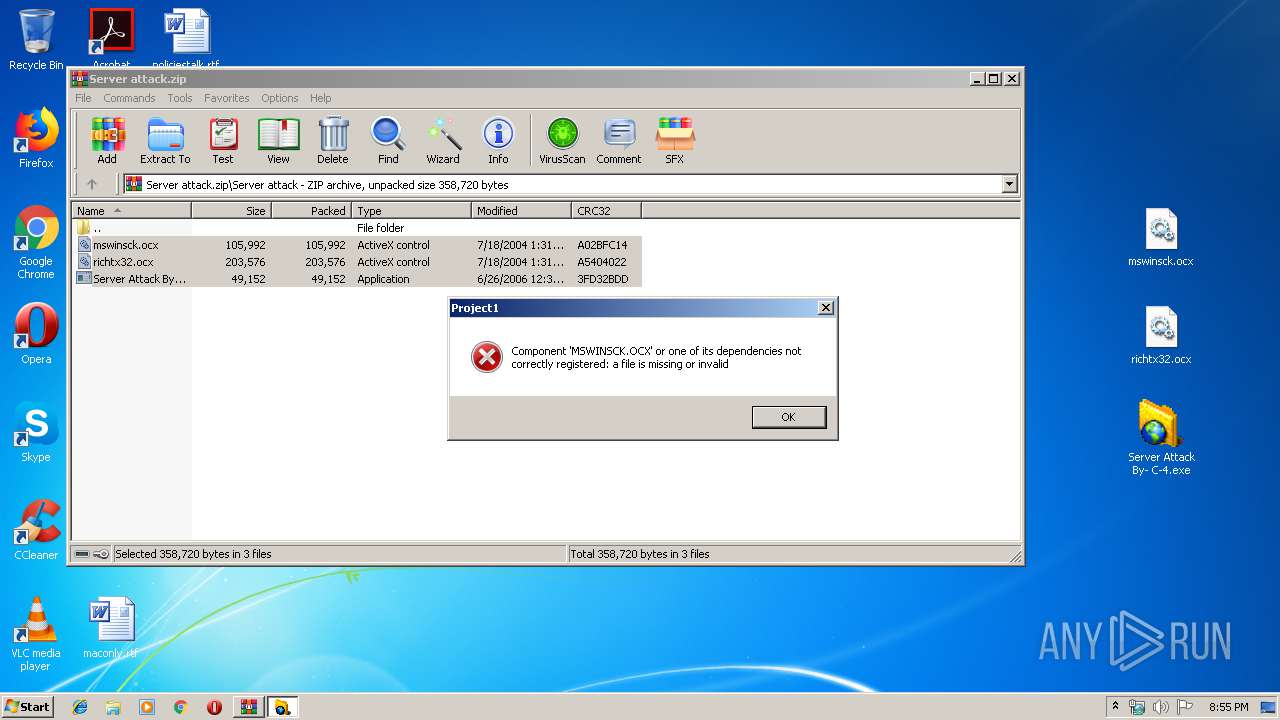
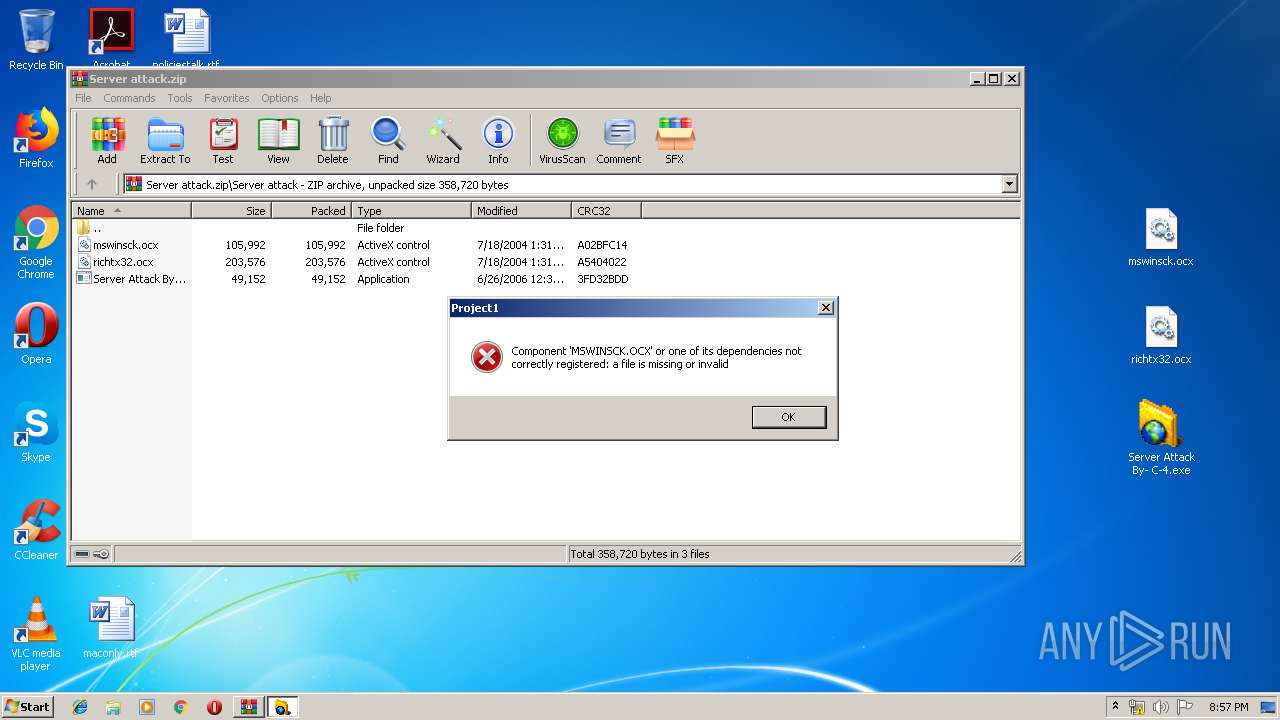
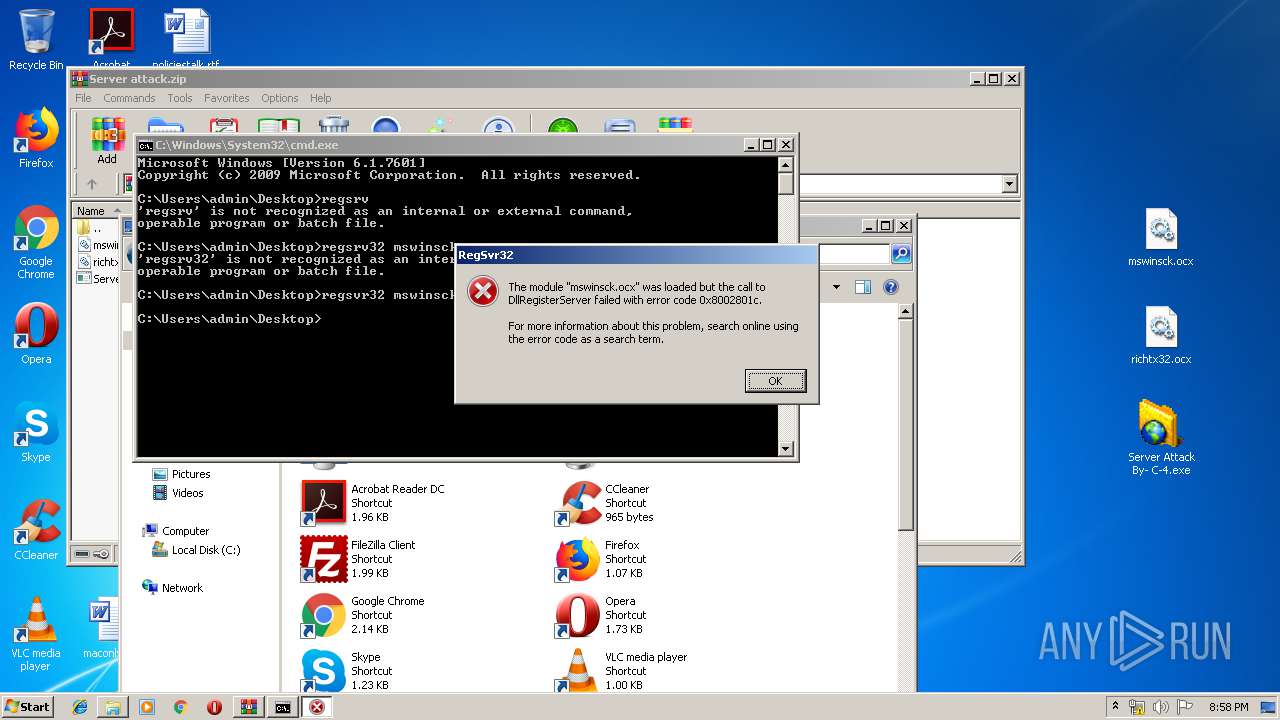
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 3688)
SUSPICIOUS
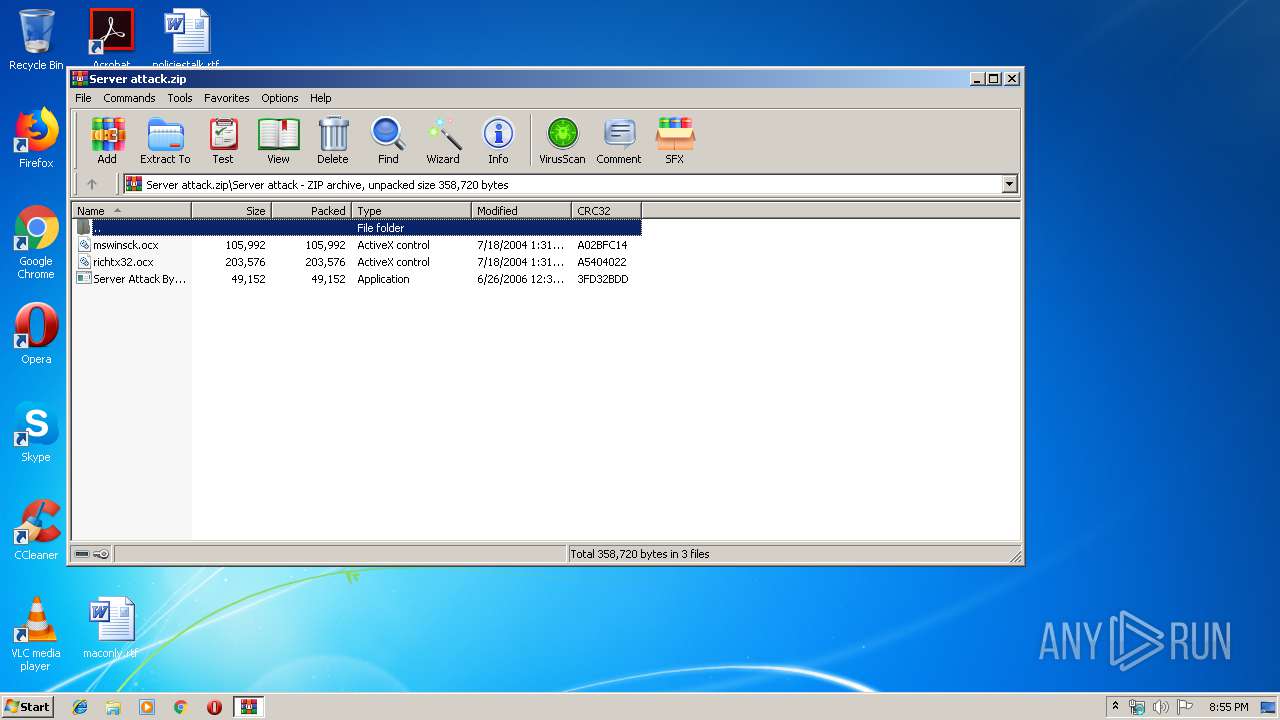
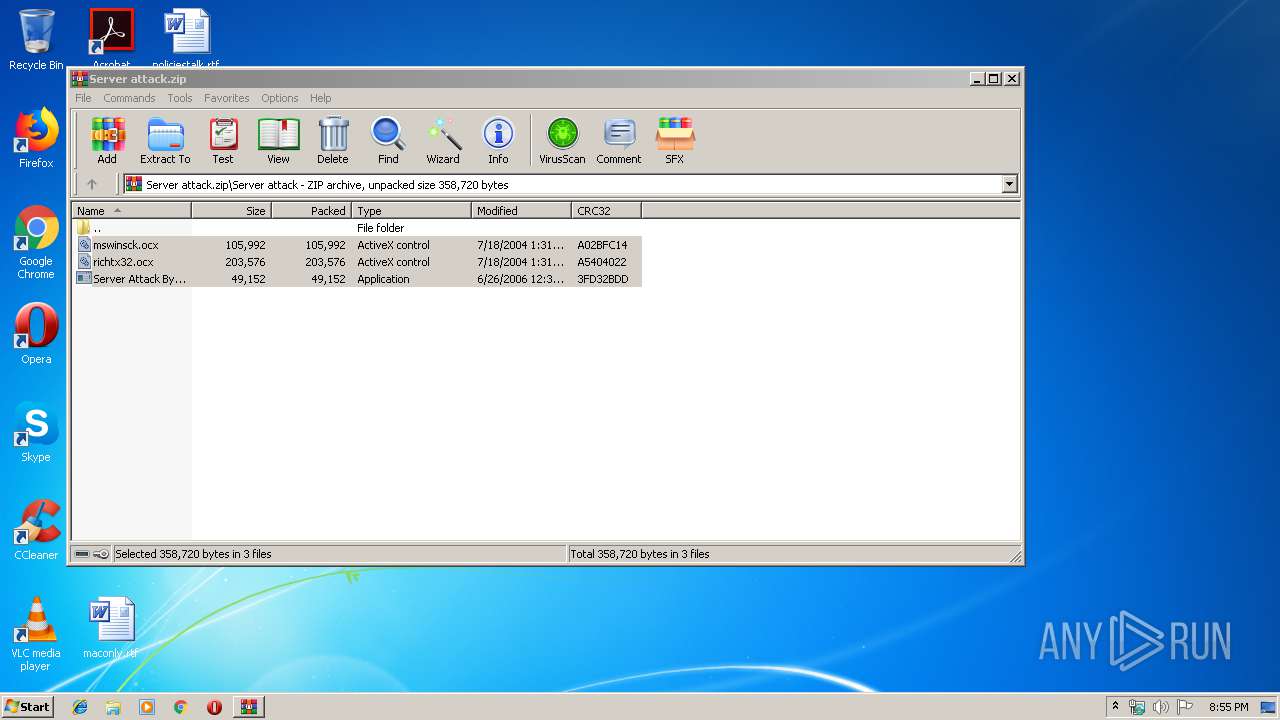
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2904)
INFO
Manual execution by user
- Server Attack By- C-4.exe (PID: 2648)
- Server Attack By- C-4.exe (PID: 3872)
- Server Attack By- C-4.exe (PID: 2680)
- cmd.exe (PID: 3688)
- explorer.exe (PID: 1788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
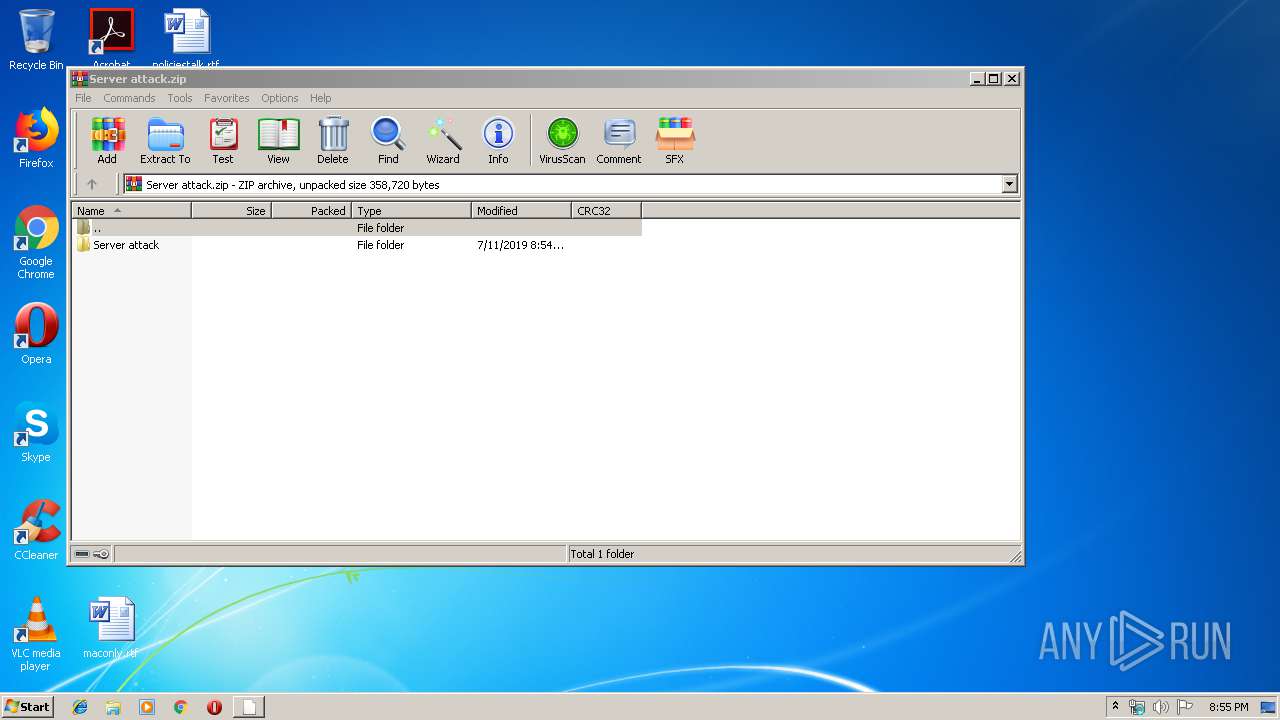
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:07:11 21:54:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Server attack/ |
Total processes
45
Monitored processes
9
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1788 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
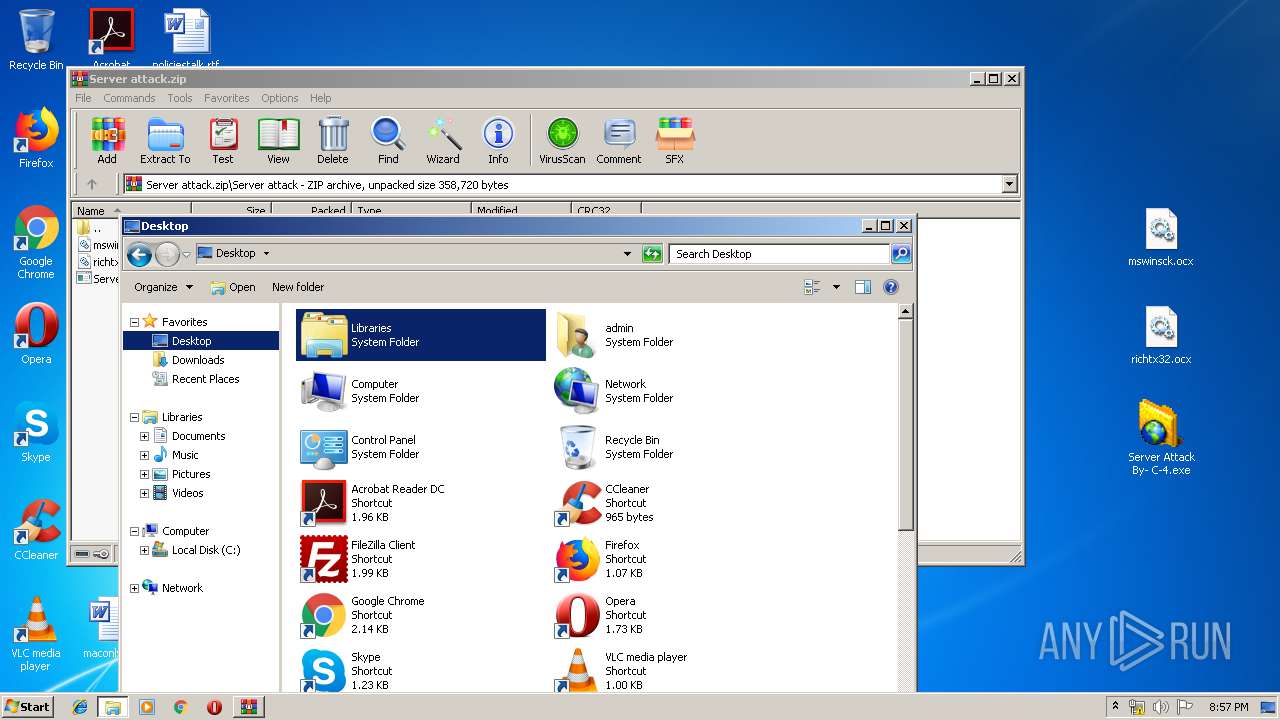
| 2648 | "C:\Users\admin\Desktop\Server Attack By- C-4.exe" | C:\Users\admin\Desktop\Server Attack By- C-4.exe | — | explorer.exe | |||||||||||
User: admin Company: Explicit - Freaks Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2680 | "C:\Users\admin\Desktop\Server Attack By- C-4.exe" | C:\Users\admin\Desktop\Server Attack By- C-4.exe | — | explorer.exe | |||||||||||
User: admin Company: Explicit - Freaks Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2856 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.45262\Server attack\Server Attack By- C-4.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.45262\Server attack\Server Attack By- C-4.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Explicit - Freaks Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
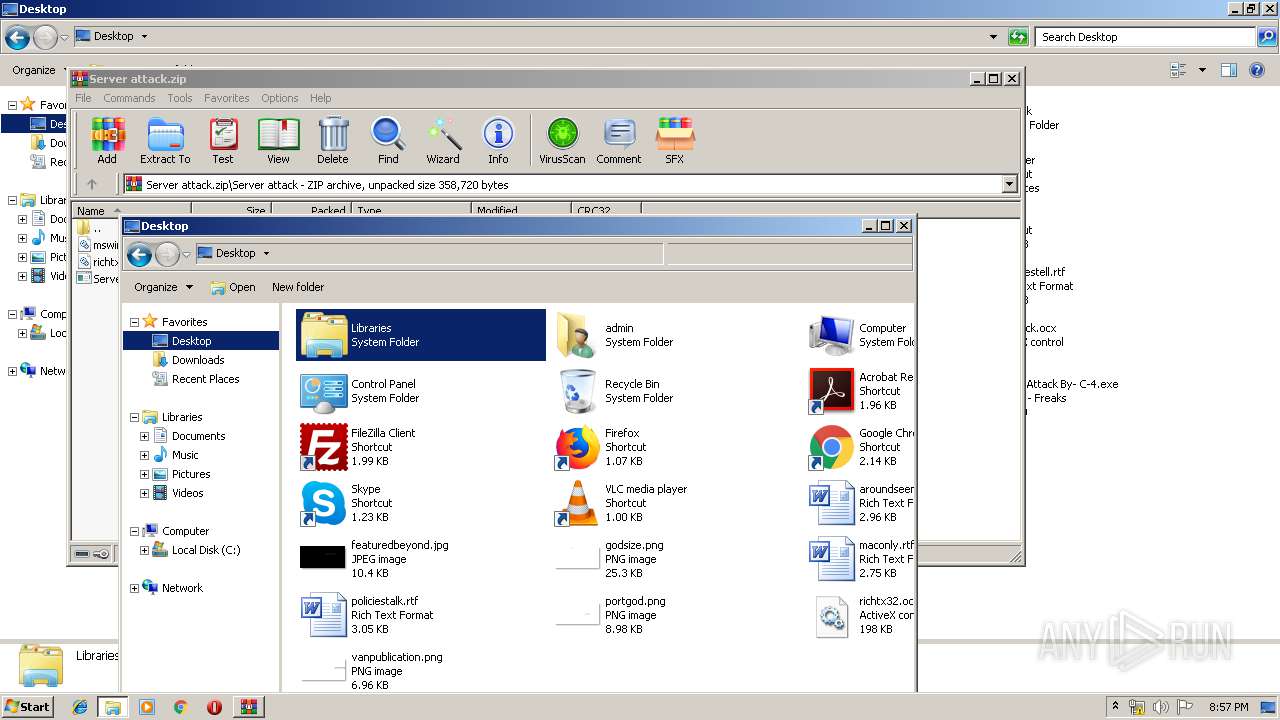
| 2904 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Server attack.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3688 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3812 | regsvr32 mswinsck.ocx | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\Desktop\Server Attack By- C-4.exe" | C:\Users\admin\Desktop\Server Attack By- C-4.exe | — | explorer.exe | |||||||||||
User: admin Company: Explicit - Freaks Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
459
Read events
447
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Server attack.zip | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
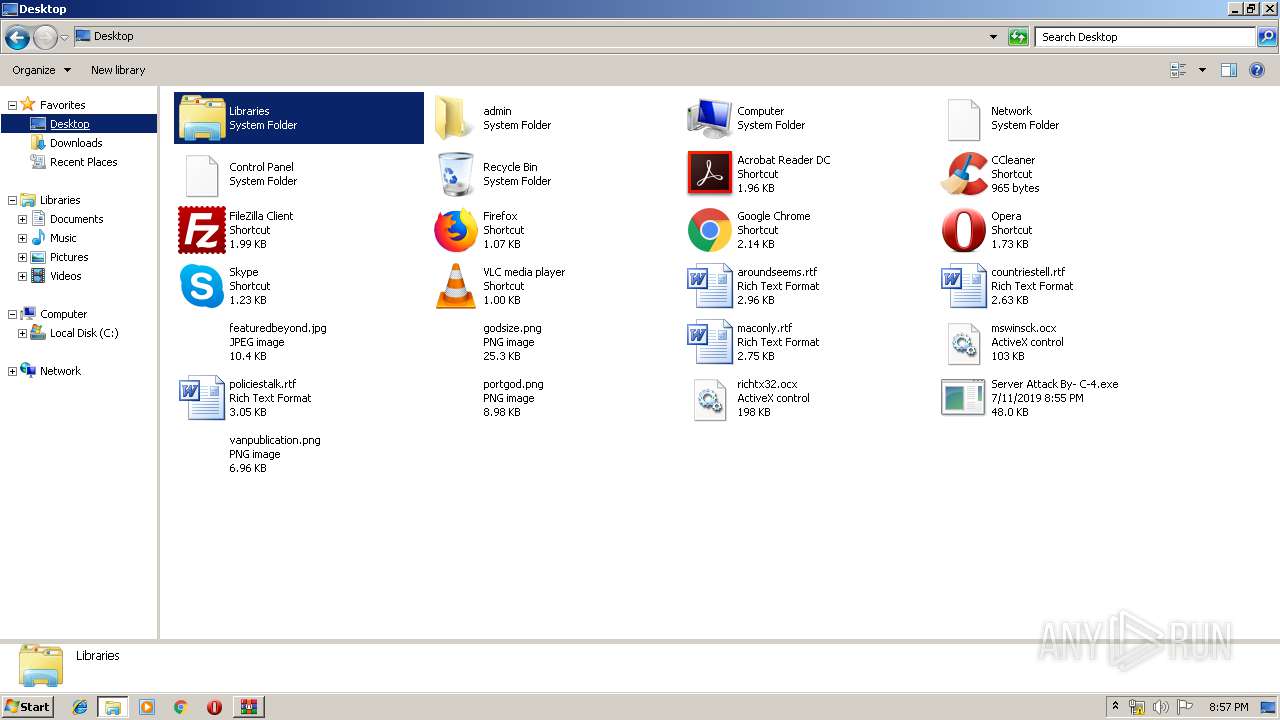
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | Server Attack By- C-4.exe | C:\Users\admin\AppData\Local\Temp\~DF08BFCFADB37CD5C4.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2904.45635\Server attack\mswinsck.ocx | — | |
MD5:— | SHA256:— | |||
| 2904 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2904.45635\Server attack\richtx32.ocx | — | |
MD5:— | SHA256:— | |||
| 2904 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2904.45635\Server attack\Server Attack By- C-4.exe | — | |
MD5:— | SHA256:— | |||
| 2648 | Server Attack By- C-4.exe | C:\Users\admin\AppData\Local\Temp\~DF3337FE3652914114.TMP | — | |
MD5:— | SHA256:— | |||
| 2680 | Server Attack By- C-4.exe | C:\Users\admin\AppData\Local\Temp\~DF90008144527932D2.TMP | — | |
MD5:— | SHA256:— | |||
| 3872 | Server Attack By- C-4.exe | C:\Users\admin\AppData\Local\Temp\~DF0F77C636831906D8.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.45262\Server attack\Server Attack By- C-4.exe | executable | |
MD5:86F9033E934D795E3AFC8C4EA3CC1BEB | SHA256:59731B0FD7A5981DFA5241BAFEB7EC2B20581EE5E8D3A6A02E6BAFAD6C77C63F | |||
| 2904 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.45262\Server attack\richtx32.ocx | executable | |
MD5:722435BA4D18F1704B43E823A12E489A | SHA256:7D59A8CC7A5C16B3B0E0E67C65CF98C45158909F95CA3A5C96B946FDEE42C095 | |||
| 2904 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.45262\Server attack\mswinsck.ocx | executable | |
MD5:3B425DC5C3FC4DFEF9497AB3F26544D1 | SHA256:CAB5F72FB38C14E709BDAB58C4F3A1DB9569ECBE76F92A560F00E7A4A0ED1F72 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report