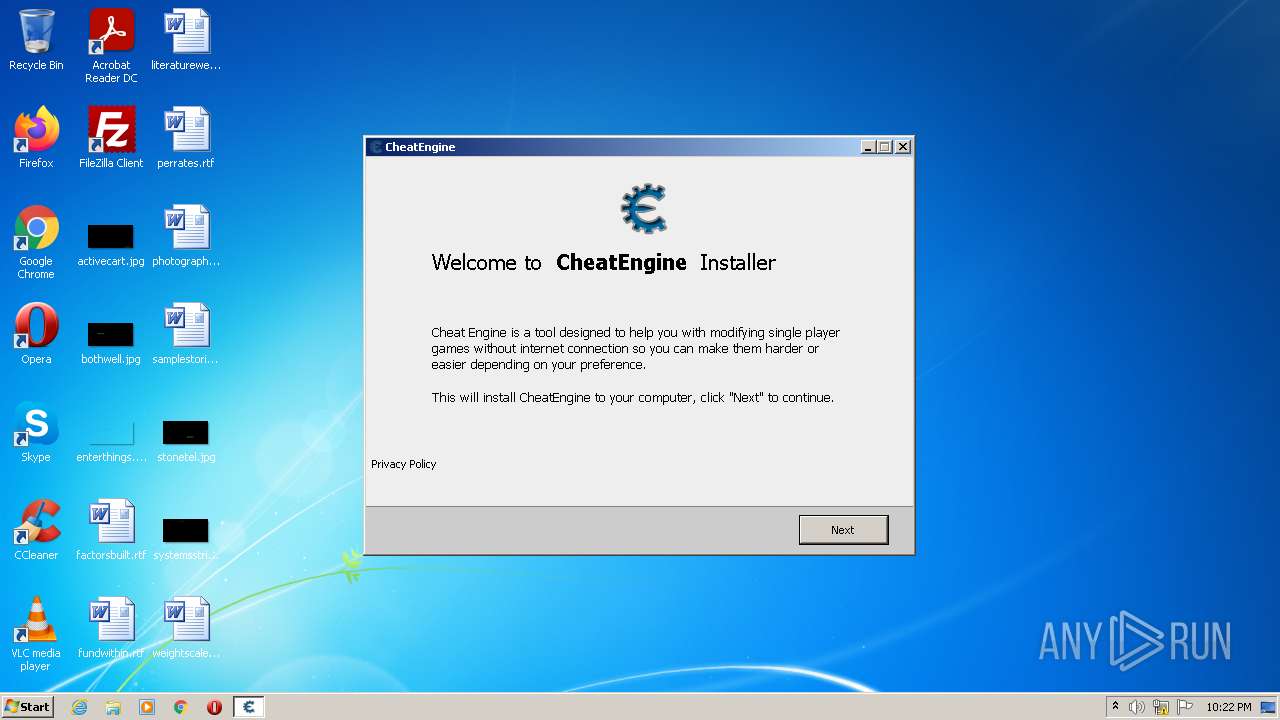
| File name: | CheatEngine74-A.exe |
| Full analysis: | https://app.any.run/tasks/f1046656-7a2b-4d11-8460-c6874b4a40de |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2022, 21:21:48 |
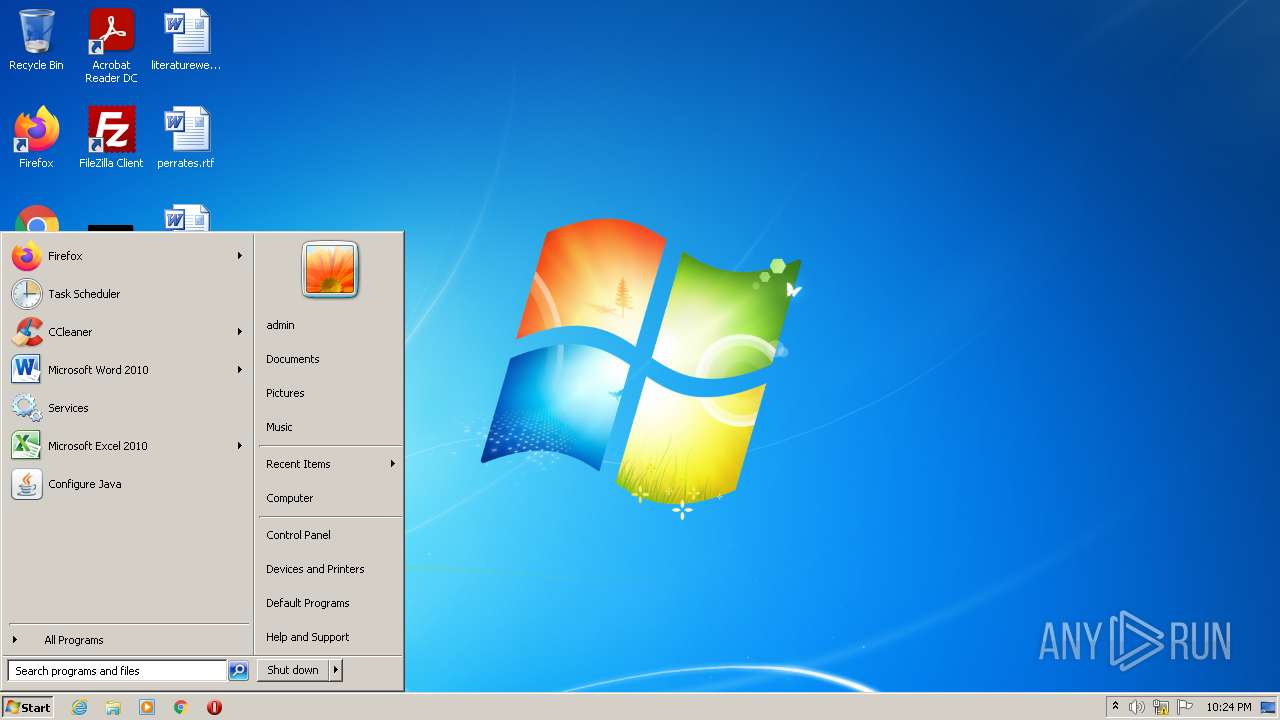
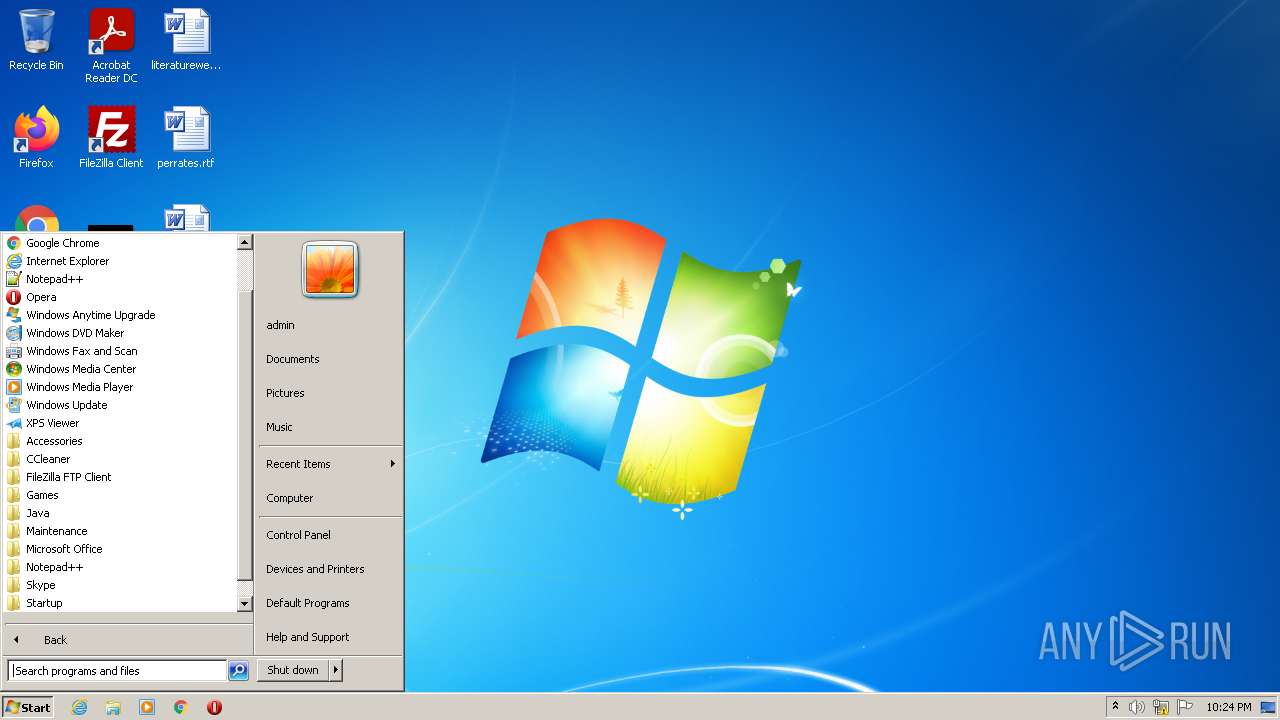
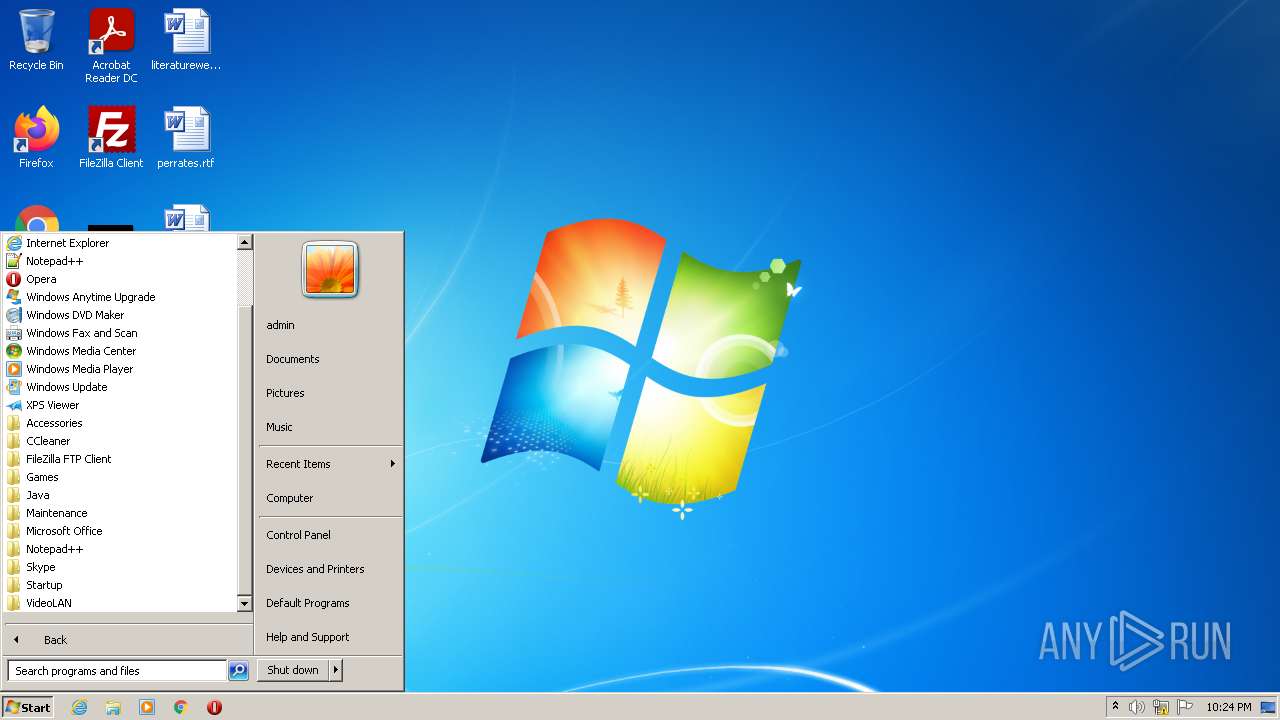
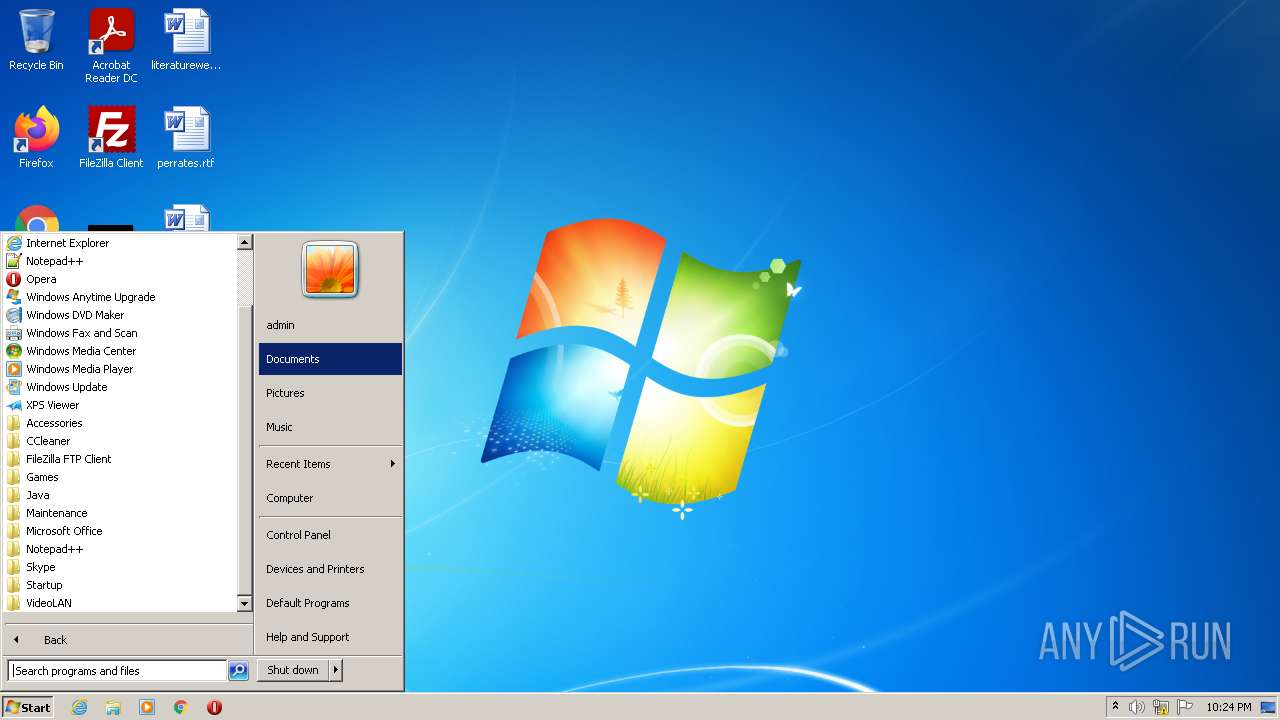
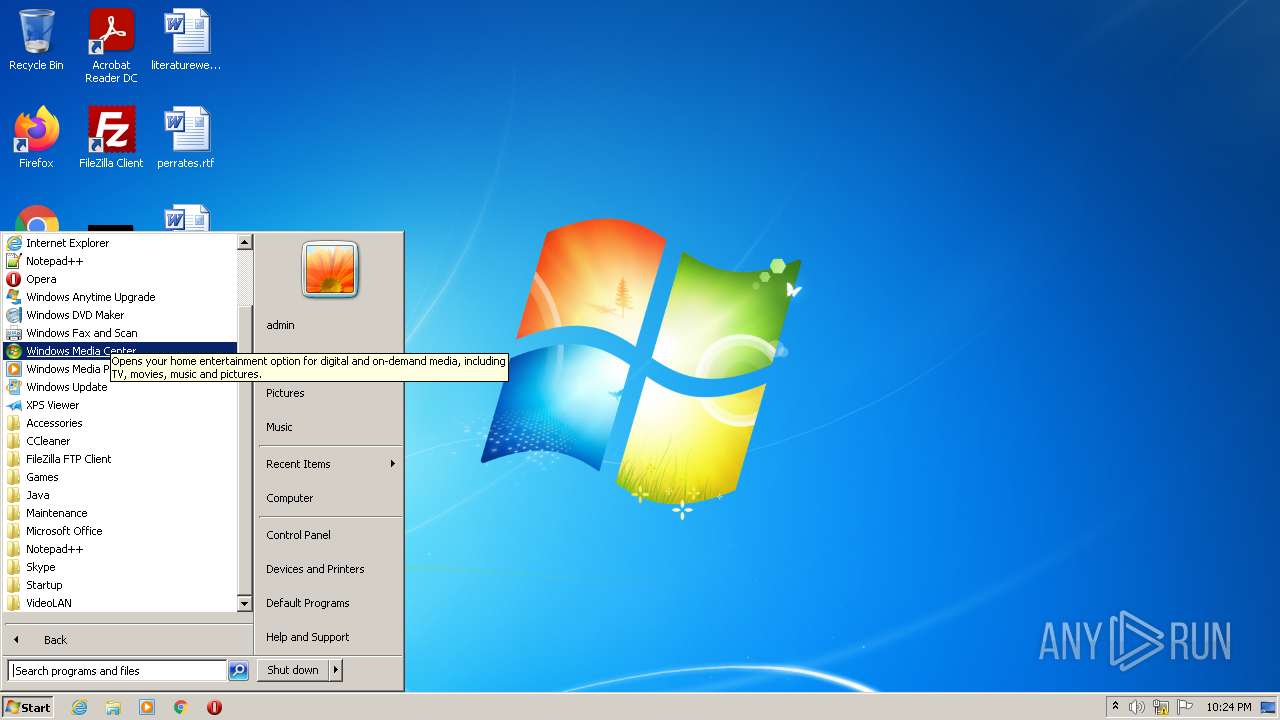
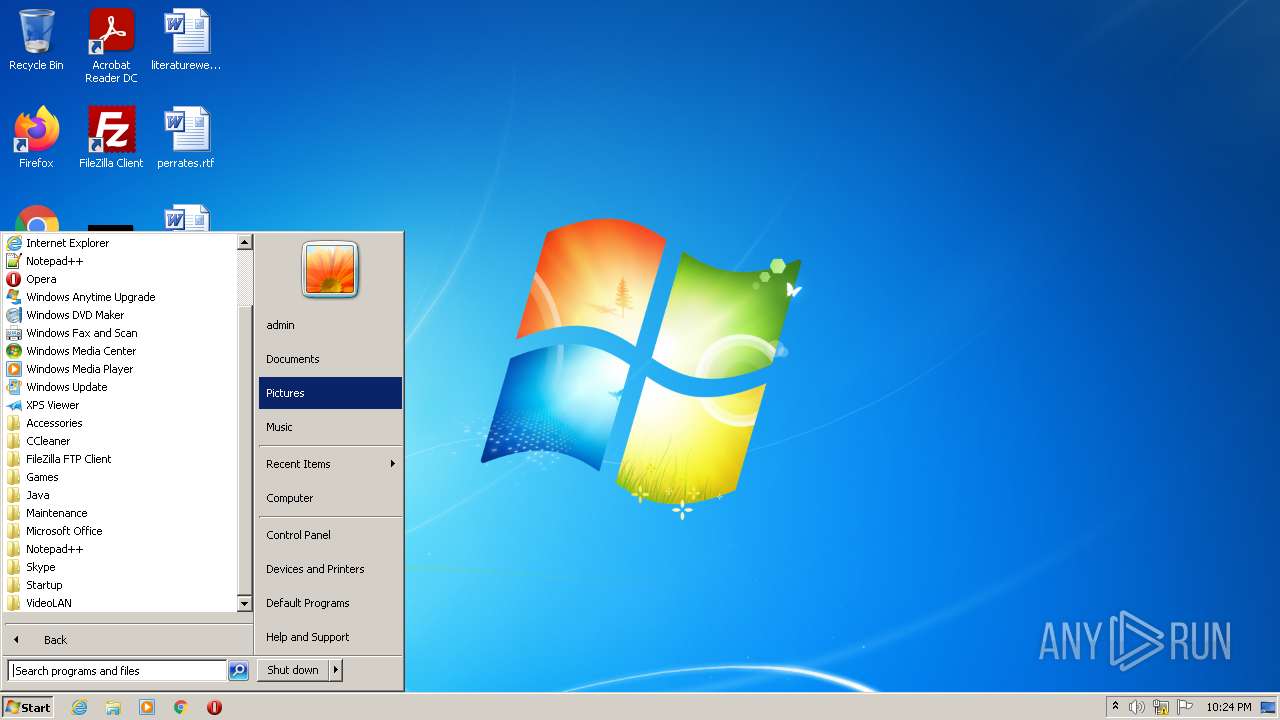
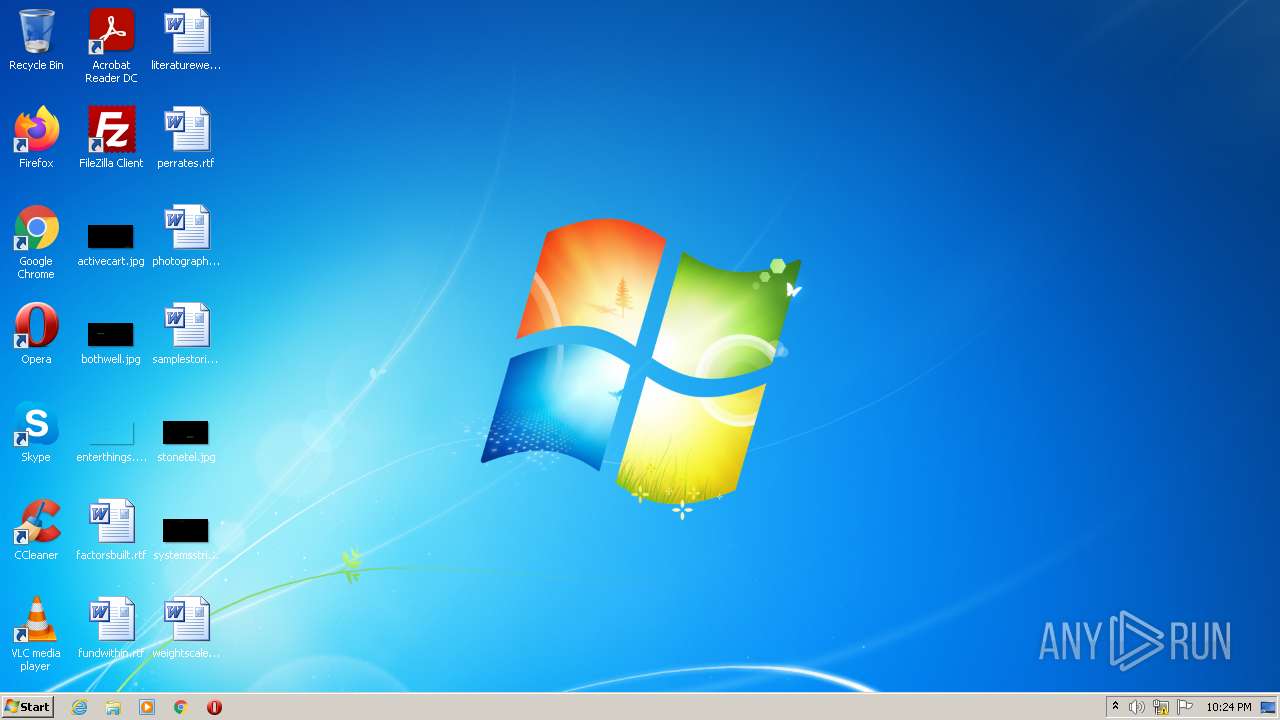
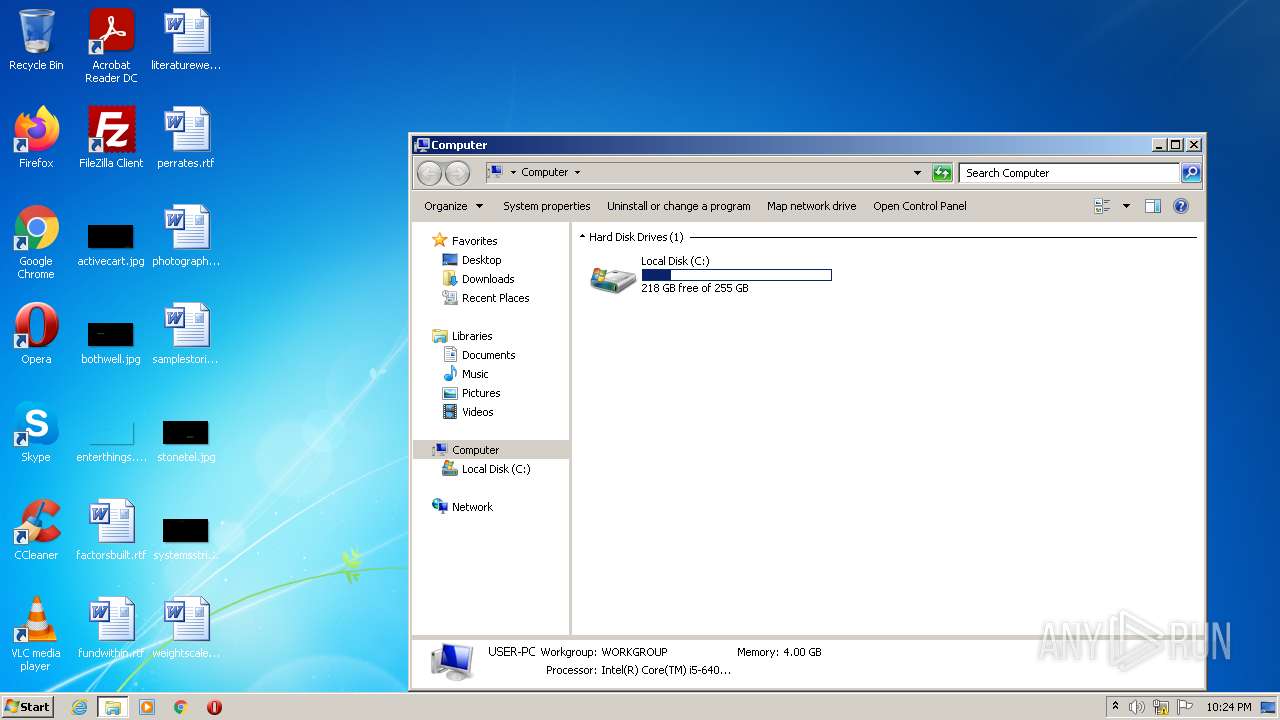
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EB562B2356A43480B9409540798D1938 |
| SHA1: | 8DFA96D17B10234D9C427BBD7C08F46AD20E8E7A |
| SHA256: | A0C20DB46E22B3FB840A16CA81735887234D5A7CF0DC06A483267C5BCD3BFE4C |
| SSDEEP: | 98304:ASiB4opH4opH4opuE9vBurw1EdKKBEXJhJ/:eDBDBDl2KKB2N |
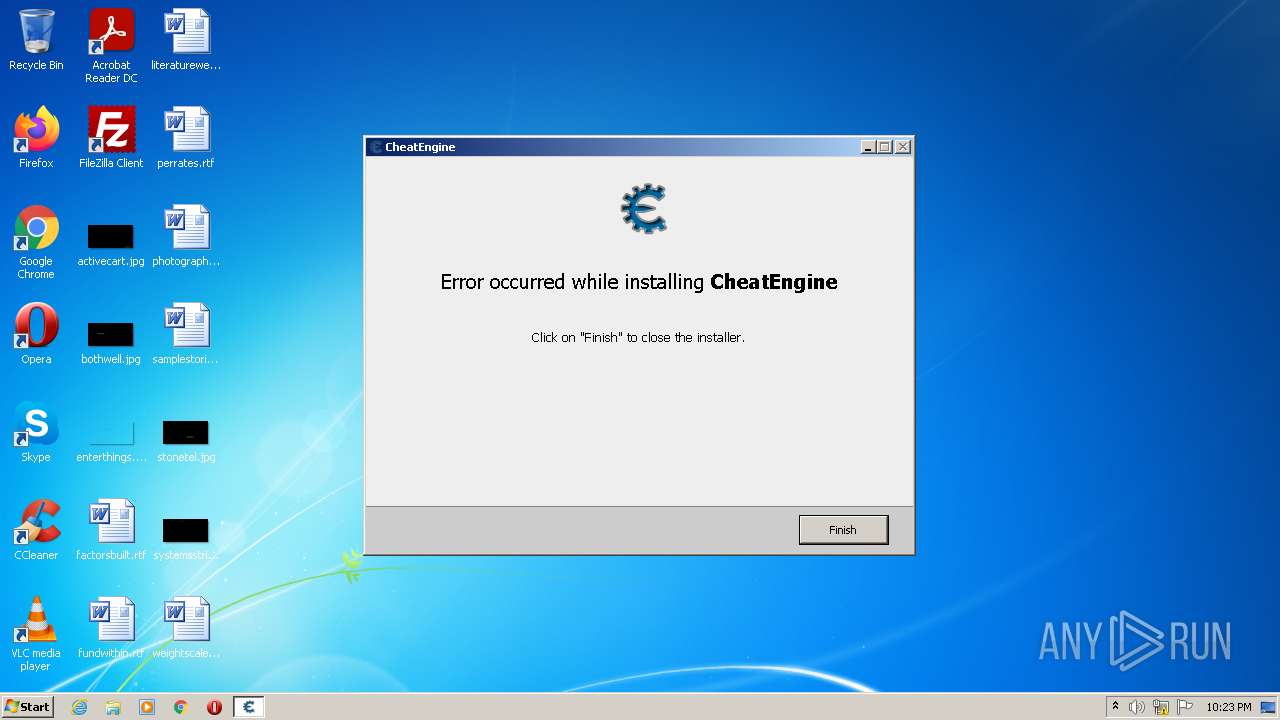
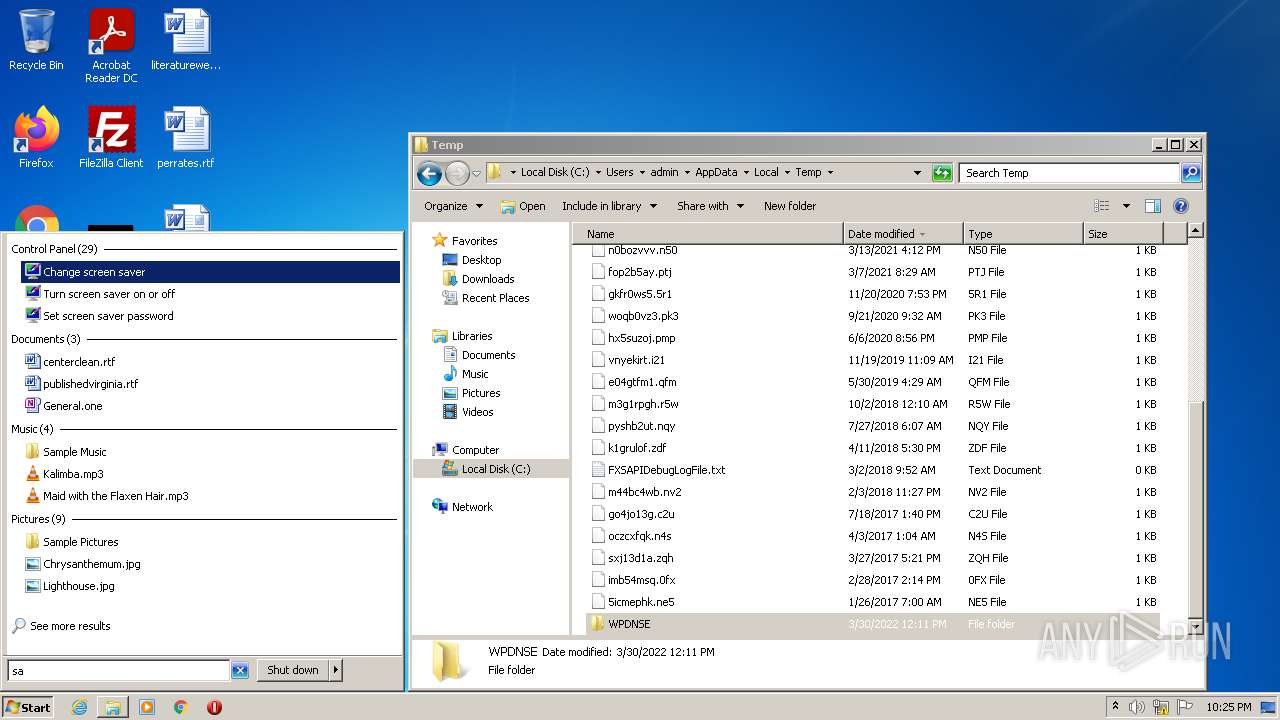
MALICIOUS
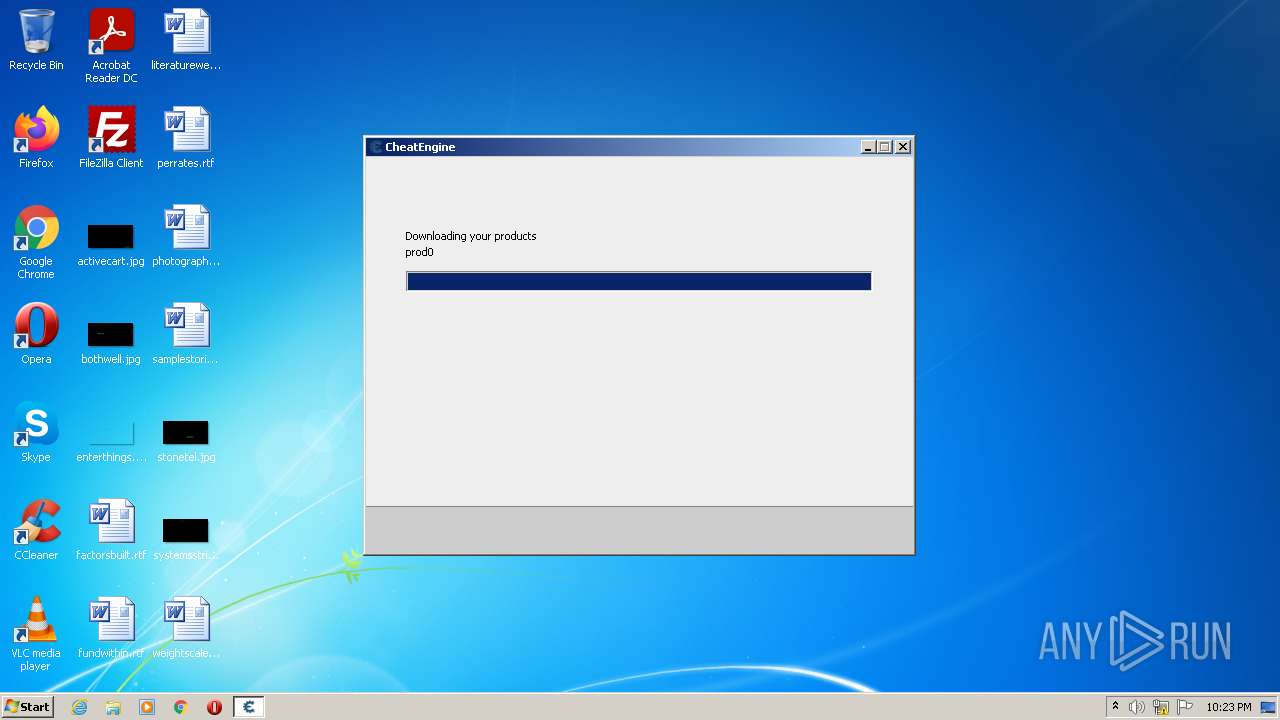
Drops executable file immediately after starts
- CheatEngine74-A.exe (PID: 2516)
- CheatEngine74-A.exe (PID: 3032)
- CheatEngine74-A.tmp (PID: 2832)
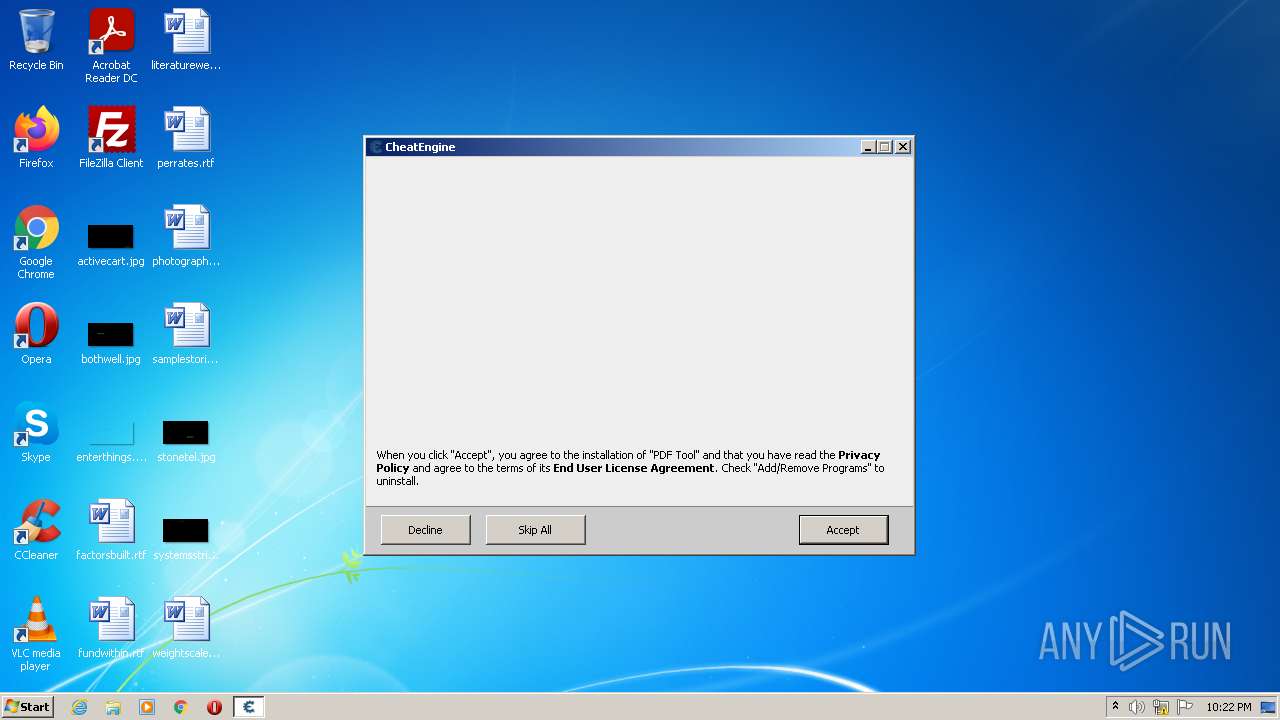
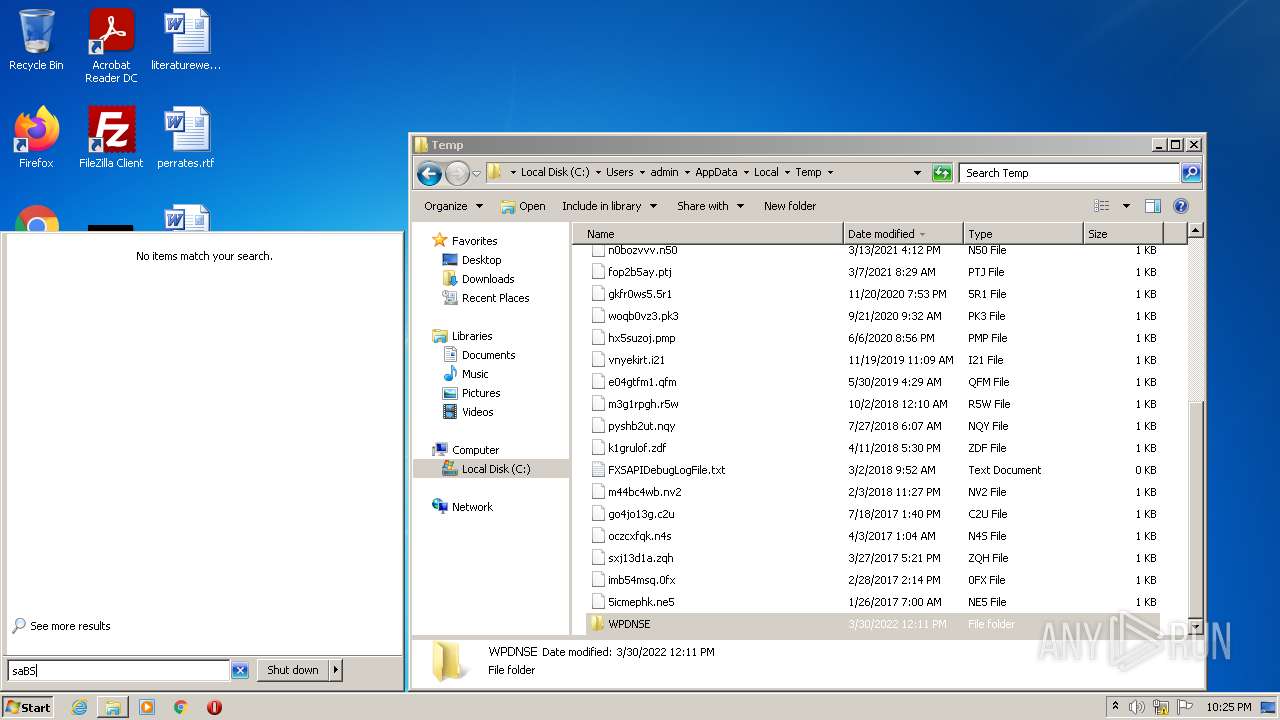
Application was dropped or rewritten from another process
- PDFToolsWebInstallerBasic.exe (PID: 2472)
- saBSI.exe (PID: 2804)
Changes settings of System certificates
- saBSI.exe (PID: 2804)
SUSPICIOUS
Drops a file with a compile date too recent
- CheatEngine74-A.exe (PID: 2516)
- CheatEngine74-A.exe (PID: 3032)
- CheatEngine74-A.tmp (PID: 2832)
Executable content was dropped or overwritten
- CheatEngine74-A.exe (PID: 2516)
- CheatEngine74-A.exe (PID: 3032)
- CheatEngine74-A.tmp (PID: 2832)
Checks supported languages
- CheatEngine74-A.exe (PID: 2516)
- CheatEngine74-A.tmp (PID: 2672)
- CheatEngine74-A.exe (PID: 3032)
- CheatEngine74-A.tmp (PID: 2832)
- PDFToolsWebInstallerBasic.exe (PID: 2472)
- saBSI.exe (PID: 2804)
Reads the computer name
- CheatEngine74-A.tmp (PID: 2672)
- CheatEngine74-A.tmp (PID: 2832)
- PDFToolsWebInstallerBasic.exe (PID: 2472)
- saBSI.exe (PID: 2804)
Reads Windows owner or organization settings
- CheatEngine74-A.tmp (PID: 2832)
Reads the Windows organization settings
- CheatEngine74-A.tmp (PID: 2832)
Reads Environment values
- PDFToolsWebInstallerBasic.exe (PID: 2472)
Adds / modifies Windows certificates
- saBSI.exe (PID: 2804)
Creates files in the program directory
- saBSI.exe (PID: 2804)
INFO
Application was dropped or rewritten from another process
- CheatEngine74-A.tmp (PID: 2672)
- CheatEngine74-A.tmp (PID: 2832)
Loads dropped or rewritten executable
- CheatEngine74-A.tmp (PID: 2832)
Reads settings of System Certificates
- CheatEngine74-A.tmp (PID: 2832)
- saBSI.exe (PID: 2804)
Checks Windows Trust Settings
- saBSI.exe (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | 7.4.0 |
|---|---|
| ProductName: | EngineGame |
| OriginalFileName: | |
| LegalCopyright: | |
| FileVersion: | 7.4.0 |
| FileDescription: | EngineGame Installer |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 7.4.0.0 |
| FileVersionNumber: | 7.4.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 102912 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | EngineGame Installer |
| FileVersion: | 7.4.0 |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | EngineGame |
| ProductVersion: | 7.4.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x0001438C | 0x00014400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.12423 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.00833 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.56385 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.06349 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.9804 | 51953 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
49
Monitored processes
6
Malicious processes
6
Suspicious processes
0
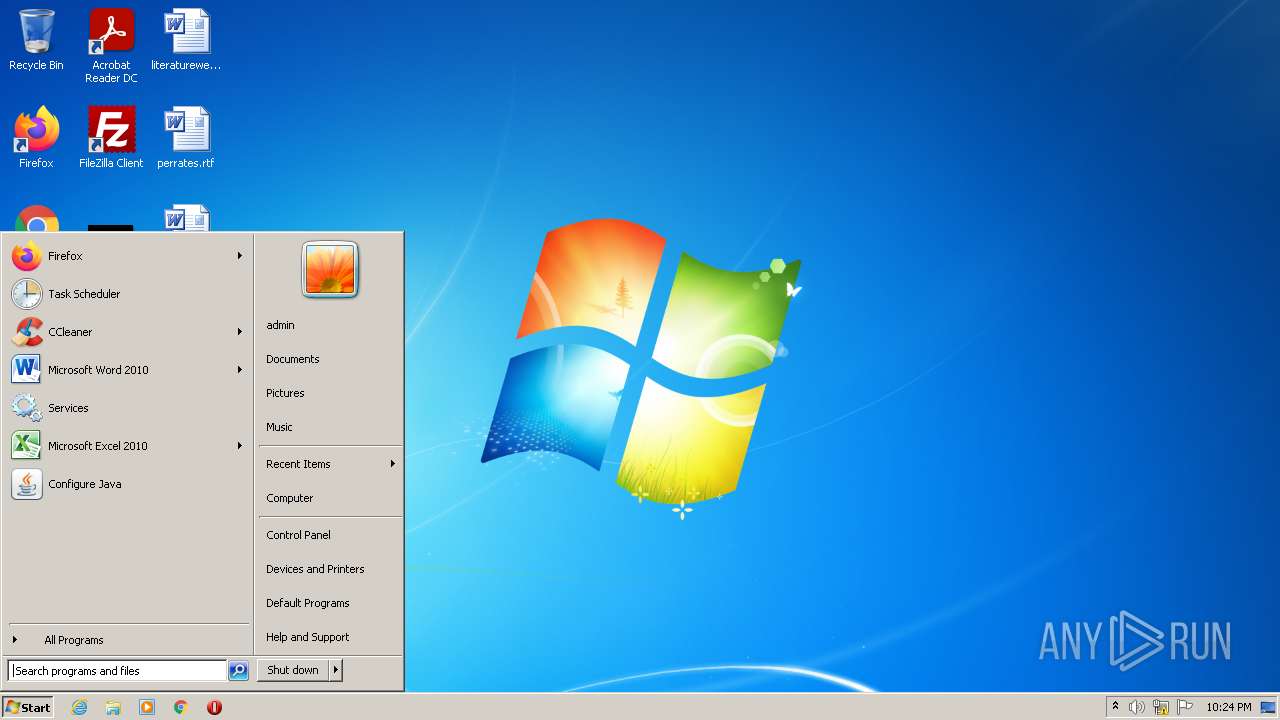
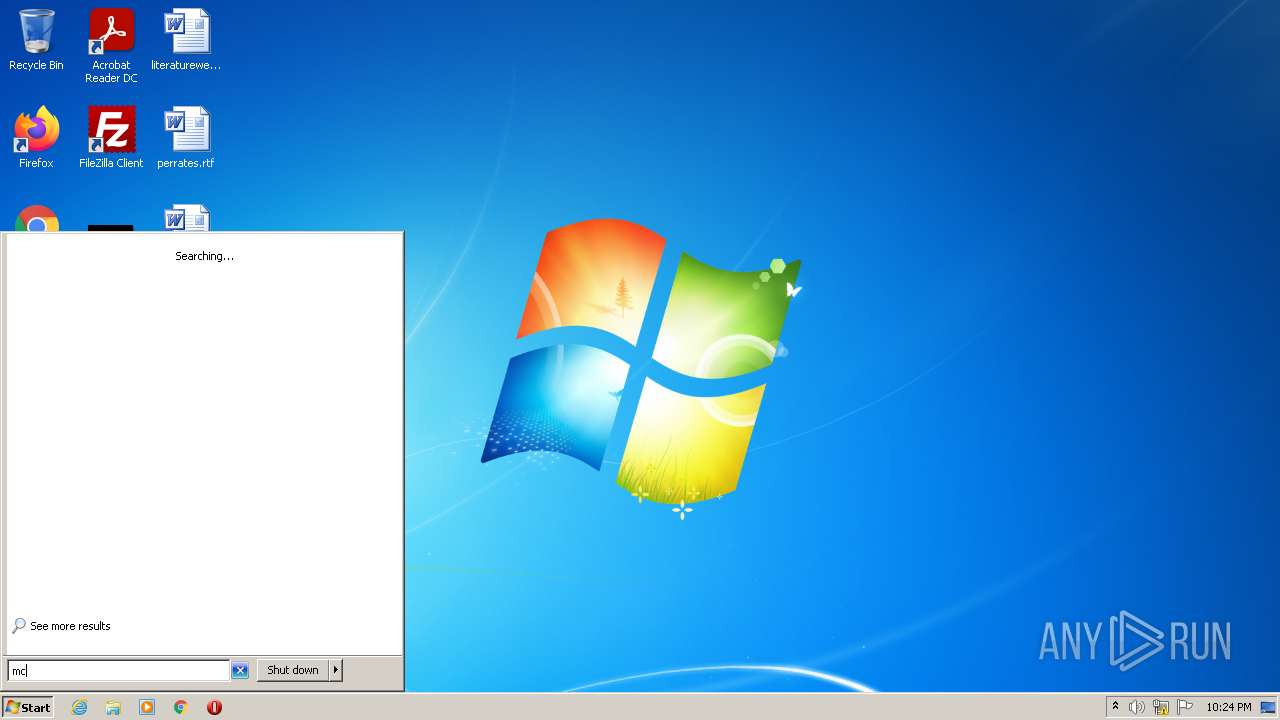
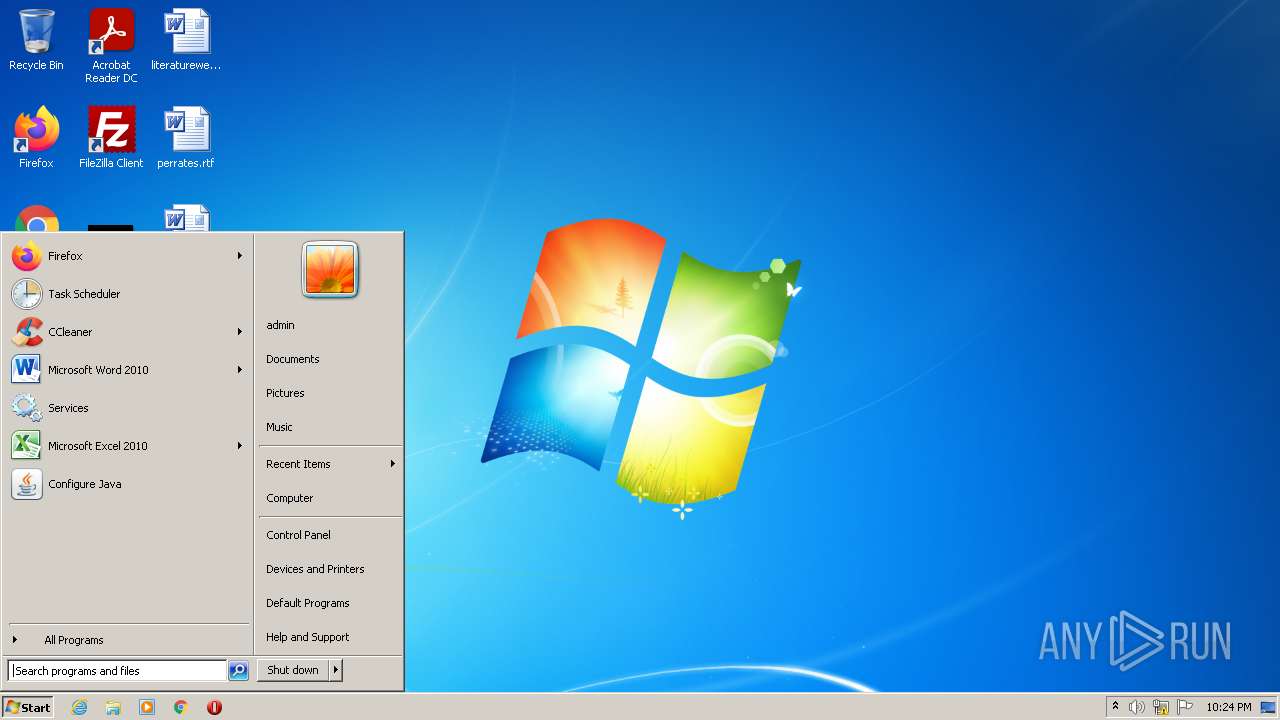
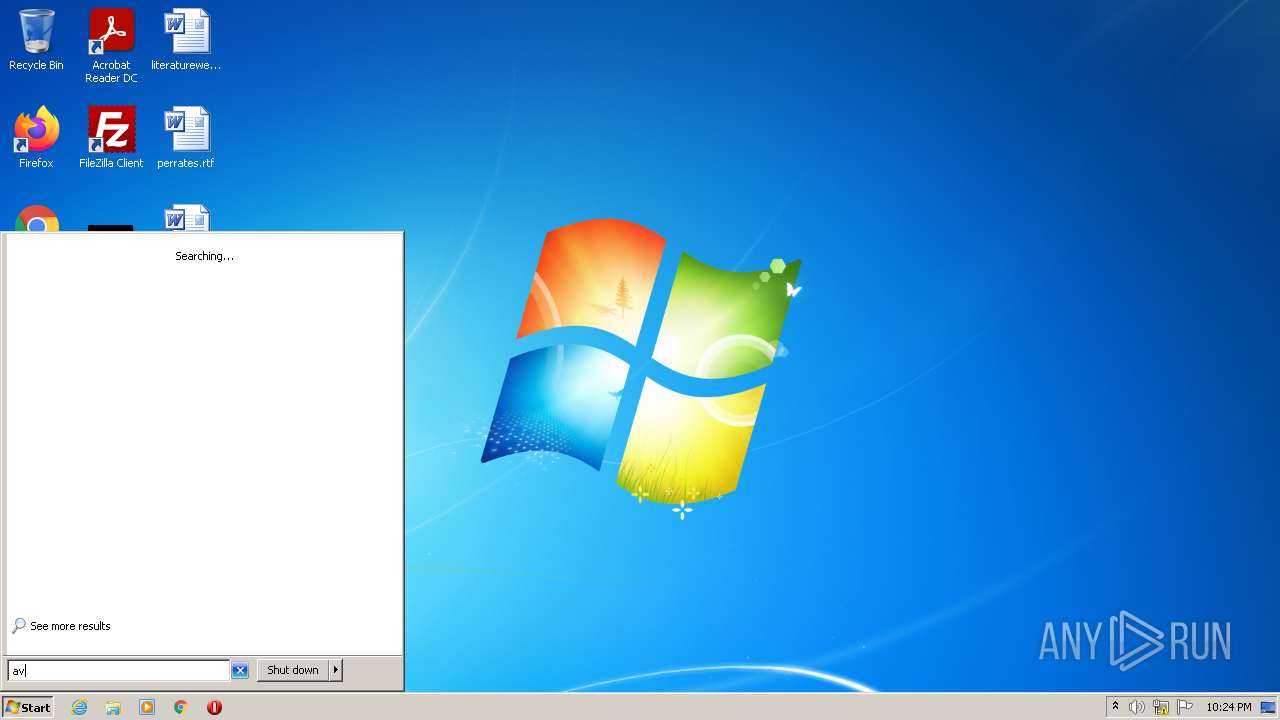
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
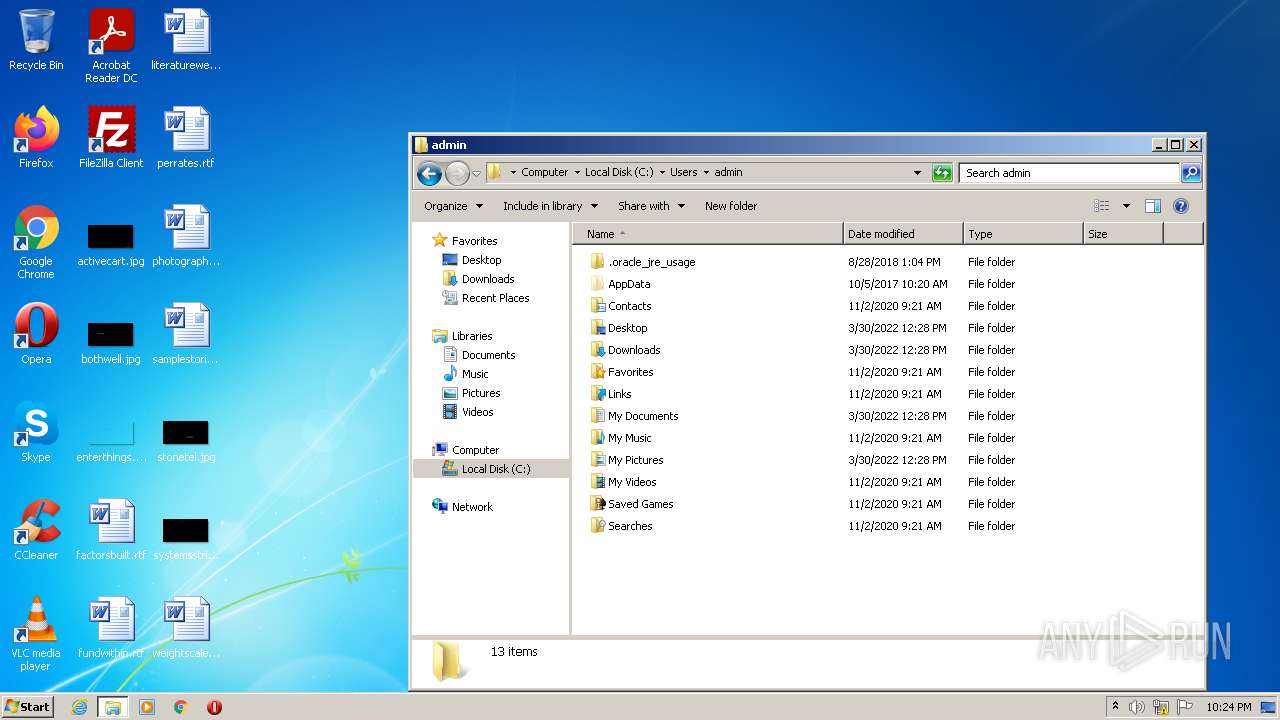
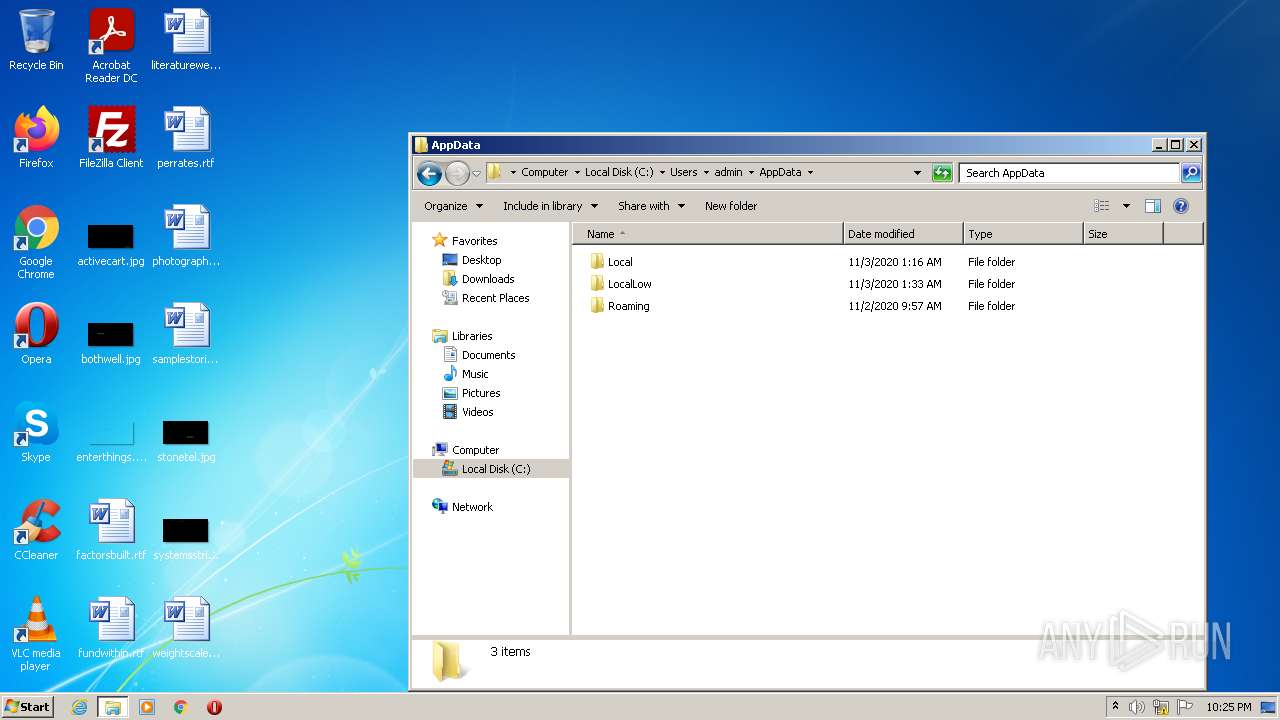
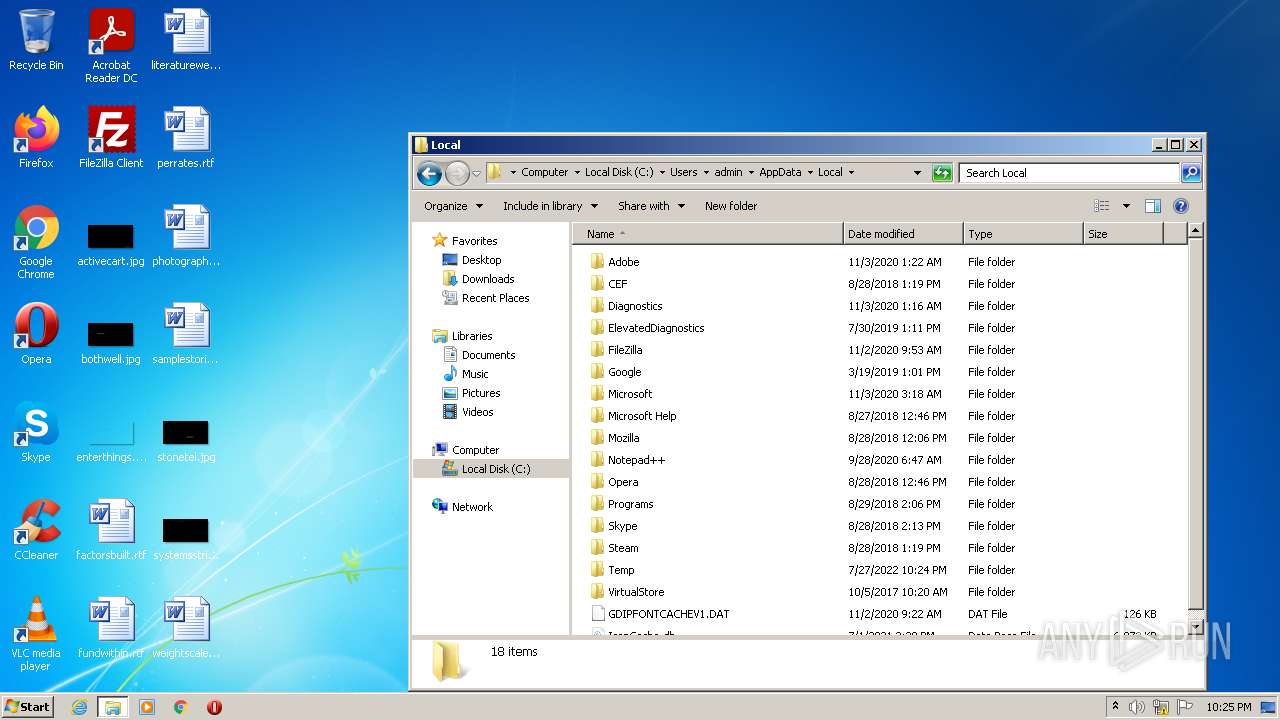
| 2472 | "C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod0_extract\PDFToolsWebInstallerBasic.exe" /quiet /p=2u6vxGh3aOlCbhsMDh5wihhAq4InN1ElWRcR5cJzwOqBJP3ymZmClmOie9E4RoDigLw02ebRR6cIXhGNU | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod0_extract\PDFToolsWebInstallerBasic.exe | CheatEngine74-A.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: WebInstallerBasic Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\CheatEngine74-A.exe" | C:\Users\admin\AppData\Local\Temp\CheatEngine74-A.exe | Explorer.EXE | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: EngineGame Installer Exit code: 2 Version: 7.4.0 Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\is-7HO4Q.tmp\CheatEngine74-A.tmp" /SL5="$20138,2408085,845312,C:\Users\admin\AppData\Local\Temp\CheatEngine74-A.exe" | C:\Users\admin\AppData\Local\Temp\is-7HO4Q.tmp\CheatEngine74-A.tmp | — | CheatEngine74-A.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2804 | "C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\saBSI.exe" /affid 91082 PaidDistribution=true | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\saBSI.exe | CheatEngine74-A.tmp | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee WebAdvisor(bootstrap installer) Exit code: 4294967295 Version: 4,1,1,663 Modules
| |||||||||||||||
| 2832 | "C:\Users\admin\AppData\Local\Temp\is-7R417.tmp\CheatEngine74-A.tmp" /SL5="$2013A,2408085,845312,C:\Users\admin\AppData\Local\Temp\CheatEngine74-A.exe" /SPAWNWND=$20130 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-7R417.tmp\CheatEngine74-A.tmp | CheatEngine74-A.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3032 | "C:\Users\admin\AppData\Local\Temp\CheatEngine74-A.exe" /SPAWNWND=$20130 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\CheatEngine74-A.exe | CheatEngine74-A.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: EngineGame Installer Exit code: 2 Version: 7.4.0 Modules
| |||||||||||||||
Total events
7 970
Read events
7 908
Write events
58
Delete events
4
Modification events
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 100B0000B284E0E5FEA1D801 | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 77DBFE7773C2E0FBD8DCF74C3909F70AE833DCF00F63973838B70ADDD9EC12A7 | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E607070003001B00150017002E002700010000001E768127E028094199FEB9D127C57AFE | |||
| (PID) Process: | (2832) CheatEngine74-A.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000ACB79927FFA1D801 | |||
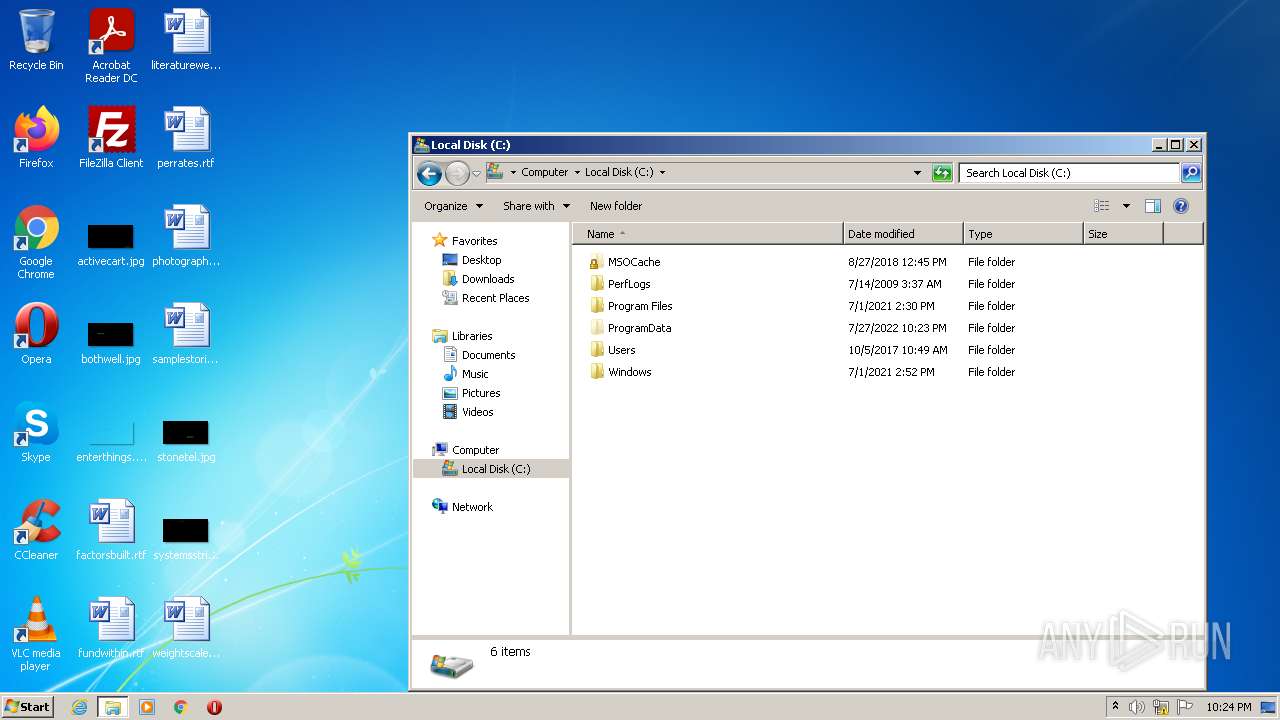
Executable files
7
Suspicious files
6
Text files
10
Unknown types
0
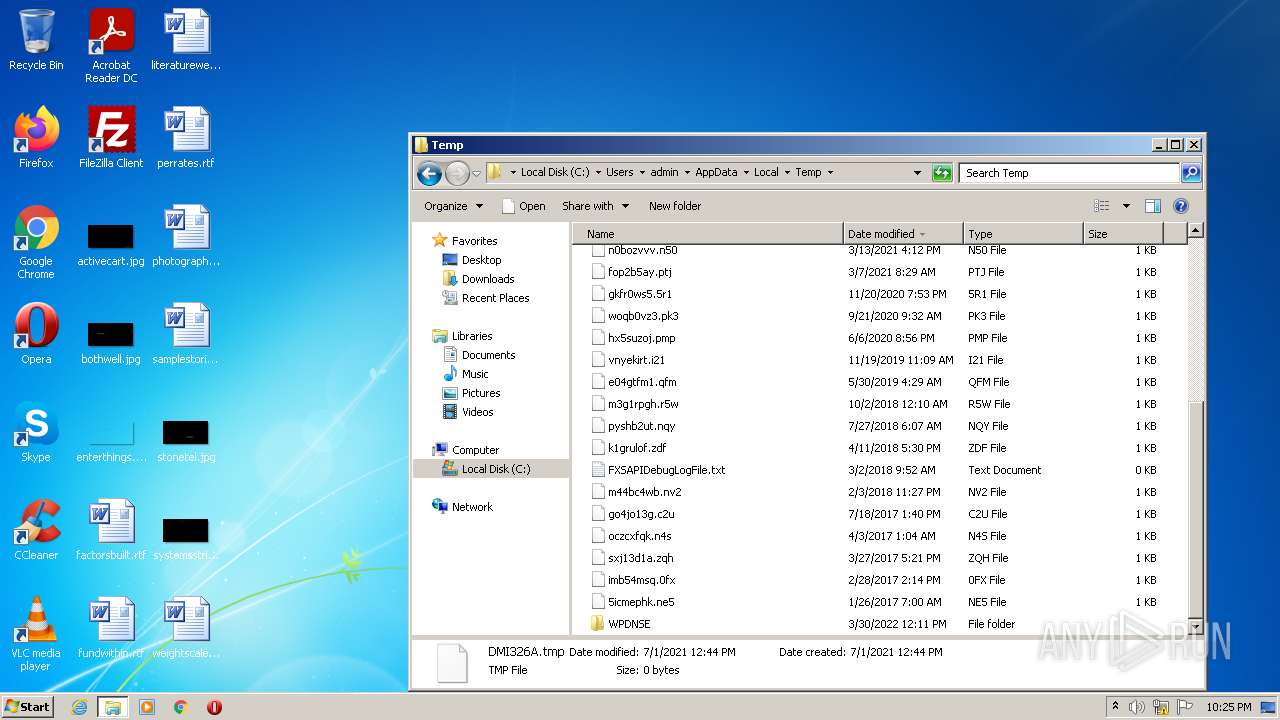
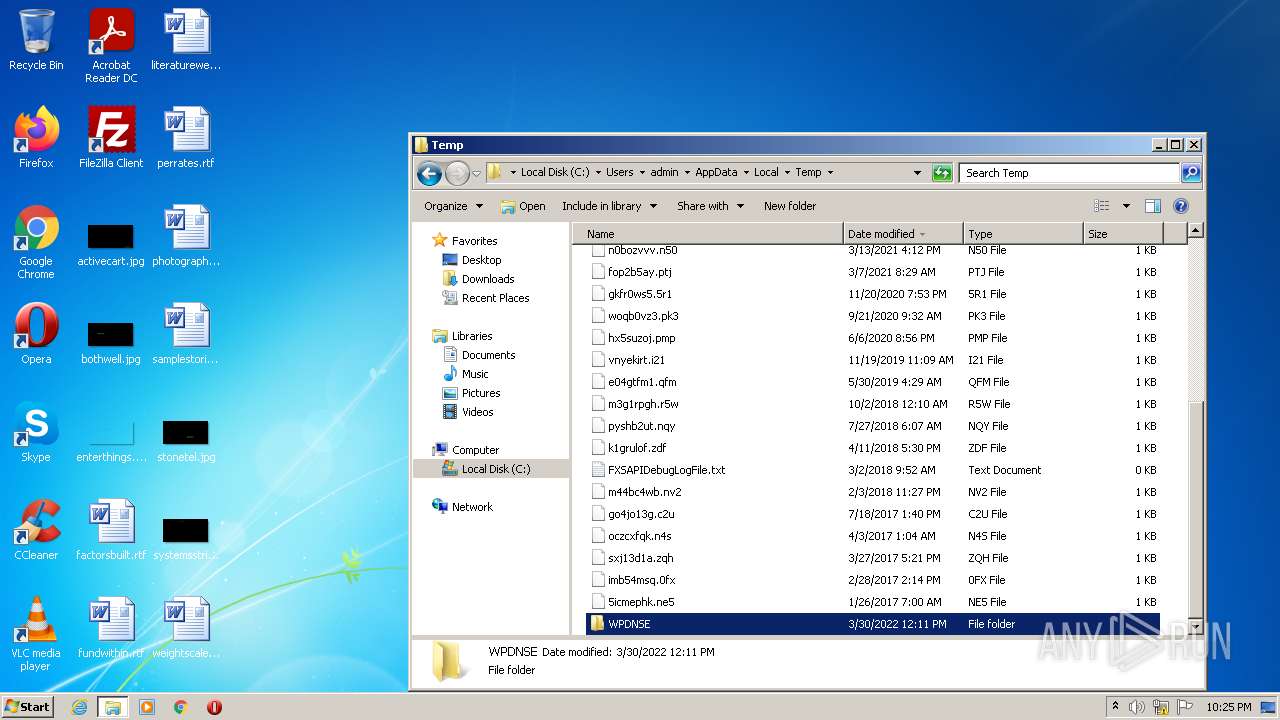
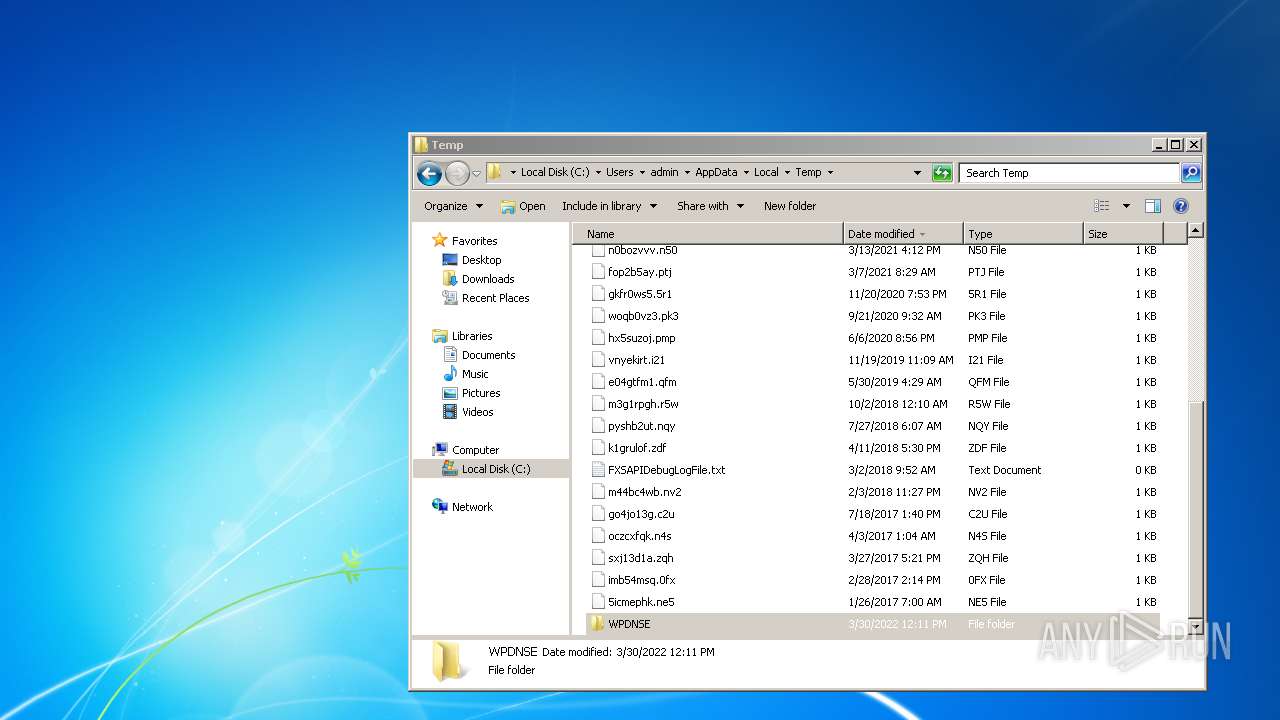
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
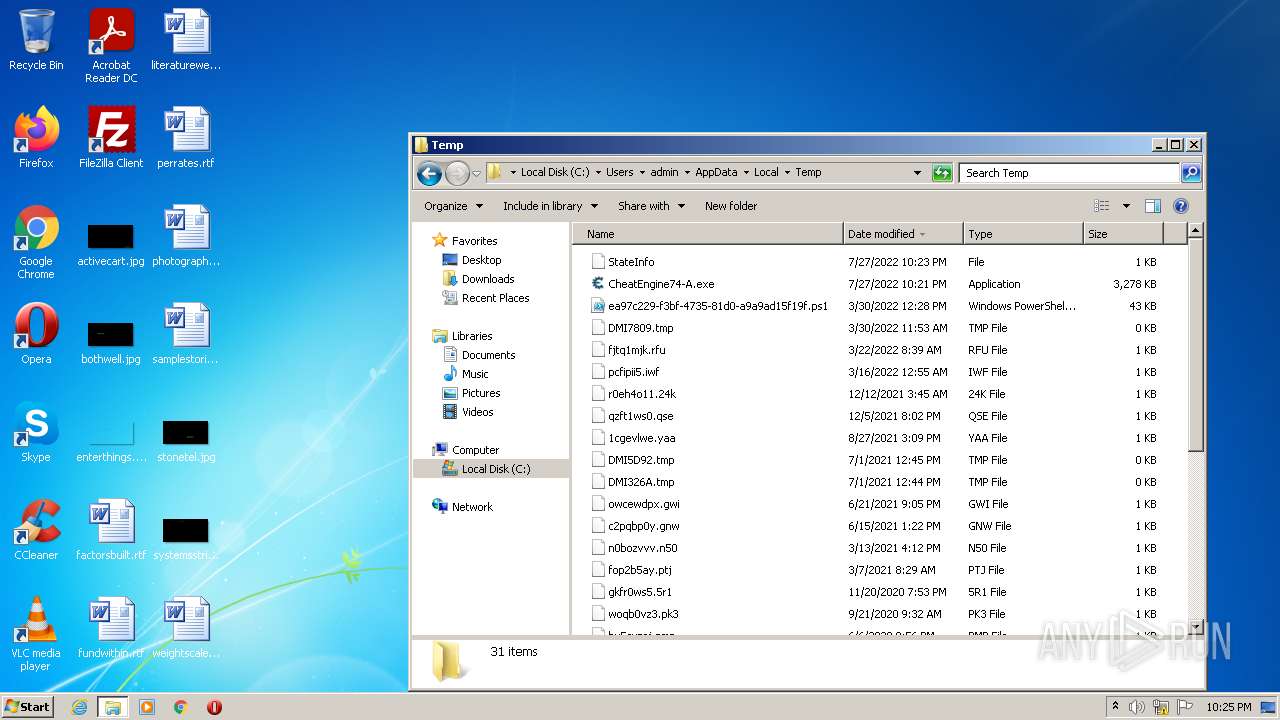
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\is-OAI5I.tmp | image | |
MD5:— | SHA256:— | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\PDF-Tool.png | image | |
MD5:— | SHA256:— | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\is-JHBOP.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\is-PCKBK.tmp | executable | |
MD5:— | SHA256:— | |||
| 3032 | CheatEngine74-A.exe | C:\Users\admin\AppData\Local\Temp\is-7R417.tmp\CheatEngine74-A.tmp | executable | |
MD5:9858749C3A44DE91503BA1124F98A4F0 | SHA256:058A000842E85DBF501D6FC76FA4A73E13B31102367D06D459C8BA8E7E91A201 | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\zbShieldUtils.dll | executable | |
MD5:E1F18A22199C6F6AA5D87B24E5B39EF1 | SHA256:62C56C8CF2AC6521CE047B73AA99B6D3952CA53F11D34B00E98D17674A2FC10D | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod0 | compressed | |
MD5:— | SHA256:— | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\botva2.dll | executable | |
MD5:67965A5957A61867D661F05AE1F4773E | SHA256:450B9B0BA25BF068AFBC2B23D252585A19E282939BF38326384EA9112DFD0105 | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod0.zip | compressed | |
MD5:— | SHA256:— | |||
| 2832 | CheatEngine74-A.tmp | C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod0_extract\PDFToolsWebInstallerBasic.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
17
DNS requests
6
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 99.86.240.15:443 | pdf-tool.com | AT&T Services, Inc. | US | unknown |
2804 | saBSI.exe | 54.200.67.7:443 | apis.mosaic.analytics.awscommon.mcafee.com | Amazon.com, Inc. | US | unknown |
2804 | saBSI.exe | 23.35.236.229:443 | sadownload.mcafee.com | Zayo Bandwidth Inc | US | suspicious |
2832 | CheatEngine74-A.tmp | 13.32.23.57:443 | d2oq4dwfbh6gxl.cloudfront.net | Amazon.com, Inc. | US | unknown |
2832 | CheatEngine74-A.tmp | 18.66.17.104:443 | d2oq4dwfbh6gxl.cloudfront.net | Massachusetts Institute of Technology | US | unknown |
2804 | saBSI.exe | 104.208.16.0:443 | cu1pehnswad01.servicebus.windows.net | Microsoft Corporation | US | unknown |
2832 | CheatEngine74-A.tmp | 13.32.23.101:443 | d2oq4dwfbh6gxl.cloudfront.net | Amazon.com, Inc. | US | malicious |
— | — | 13.32.23.57:443 | d2oq4dwfbh6gxl.cloudfront.net | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d2oq4dwfbh6gxl.cloudfront.net |
| whitelisted |
pdf-tool.com |
| malicious |
cu1pehnswad01.servicebus.windows.net |
| whitelisted |
apis.mosaic.analytics.awscommon.mcafee.com |
| unknown |
sadownload.mcafee.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2804 | saBSI.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2804 | saBSI.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-JV7OH.tmp\prod1_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|