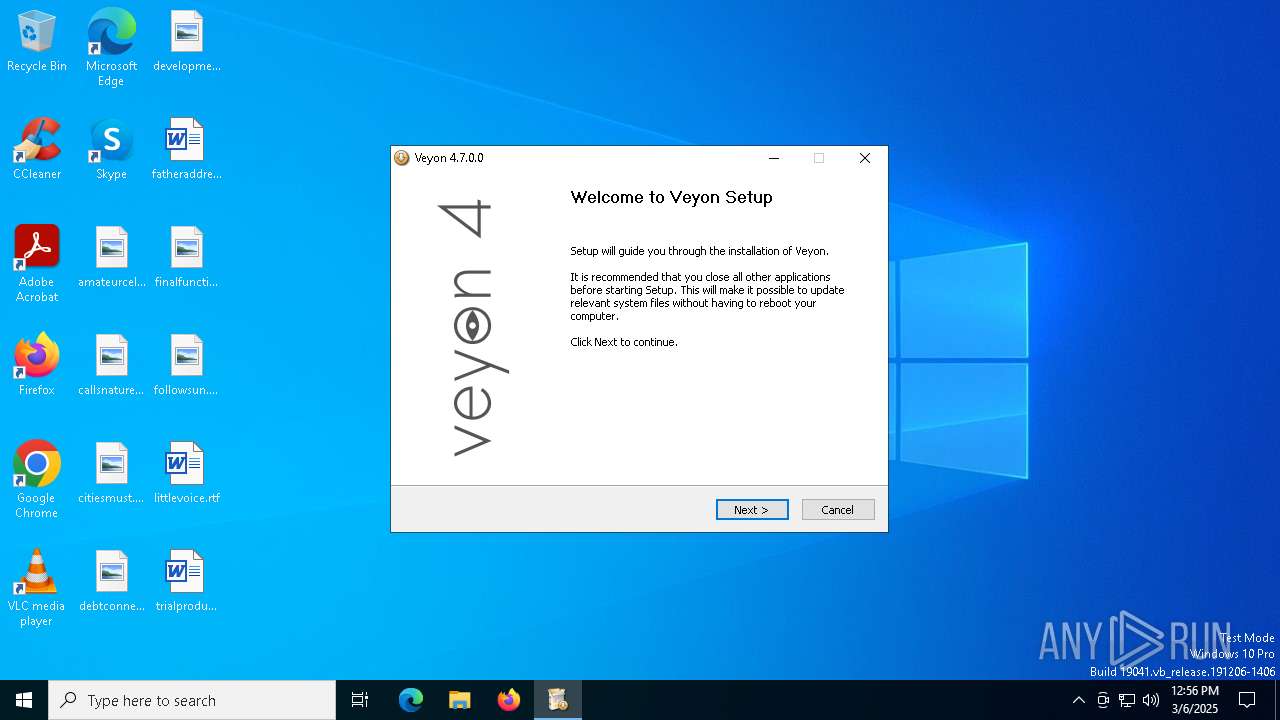
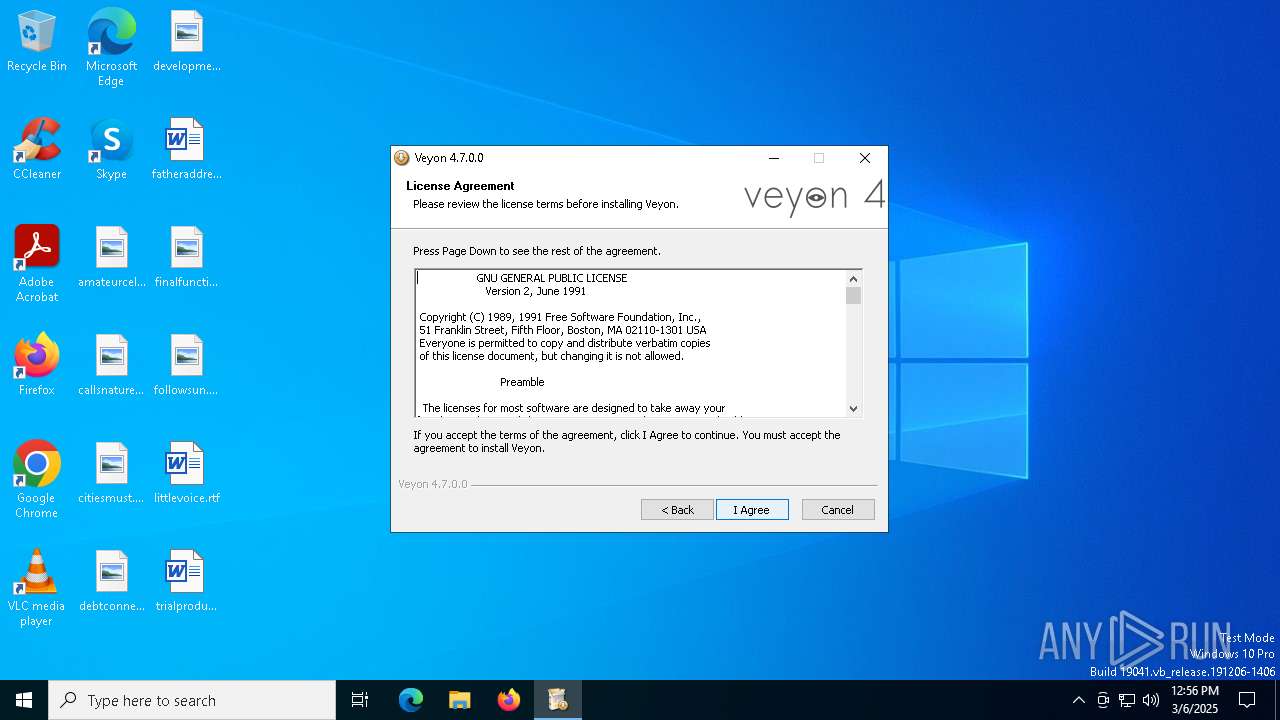
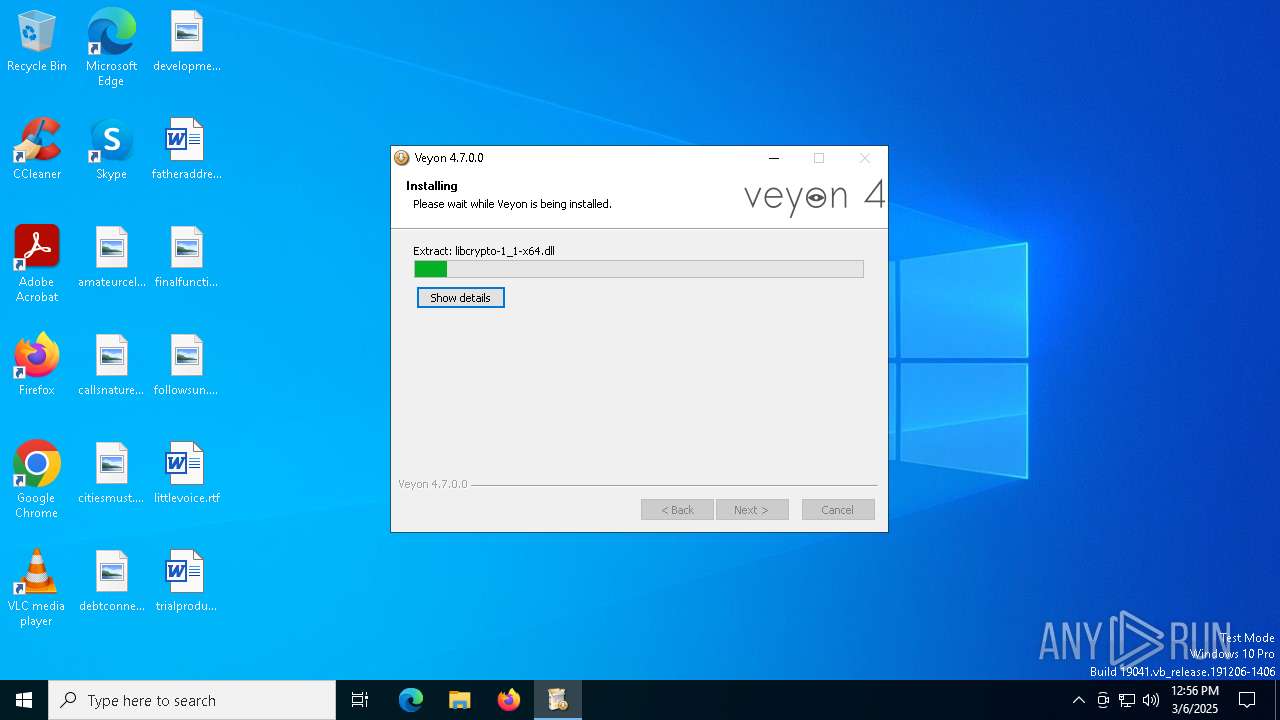
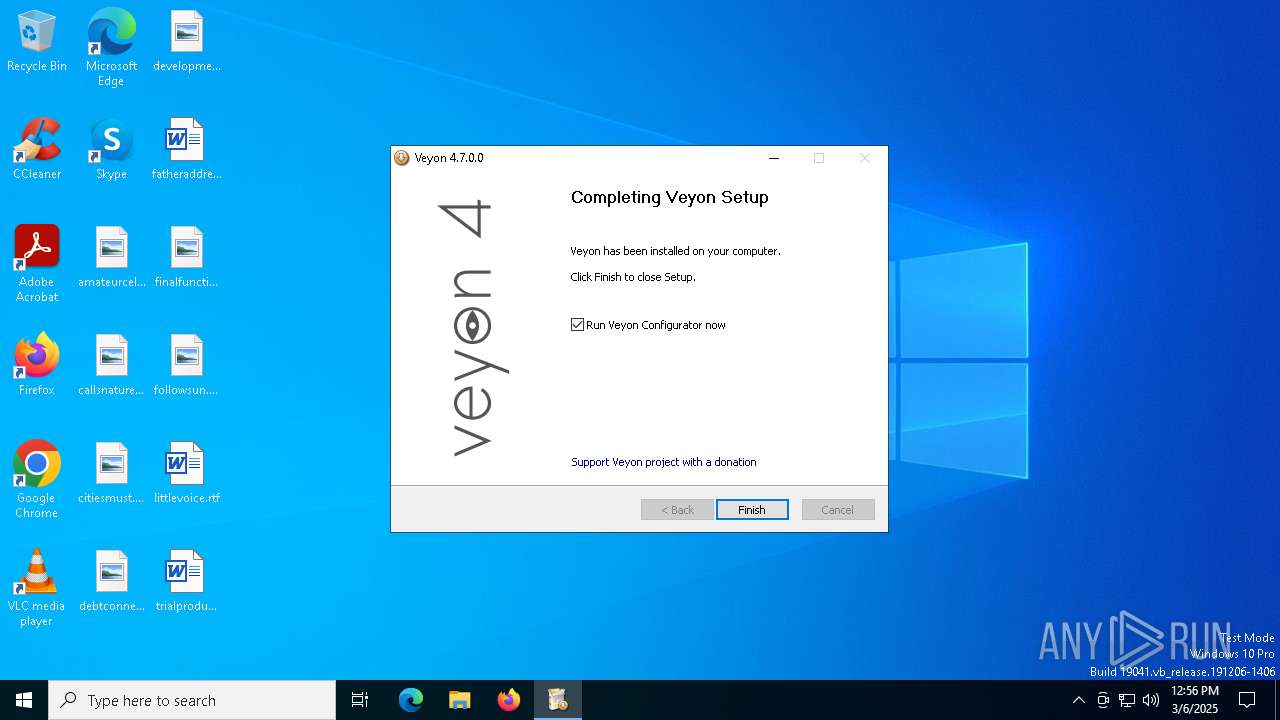
| File name: | veyon-4.7.0.0-win64-setup.exe |
| Full analysis: | https://app.any.run/tasks/57b6e4b6-848d-473d-b7f4-0b8ace9a8fd9 |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2025, 12:56:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive, 7 sections |
| MD5: | A90A78FD1DB75DFFE3C2E55D5B96EA25 |
| SHA1: | 0F6FC9473808ACBC51DFE782A46CAC101CAB7123 |
| SHA256: | A0B45783F769A01E5FE8A9637A8A7B6255A606AE32A2297D0FAD984A8FA5B620 |
| SSDEEP: | 98304:i0HWJso1Tcbi72cYojEJ6UlftExtCXBN52R4pt+DGPADXDYwFPuoRZJK3+1/zR6H:EWooo2VzFcjI25+J |
MALICIOUS
No malicious indicators.SUSPICIOUS
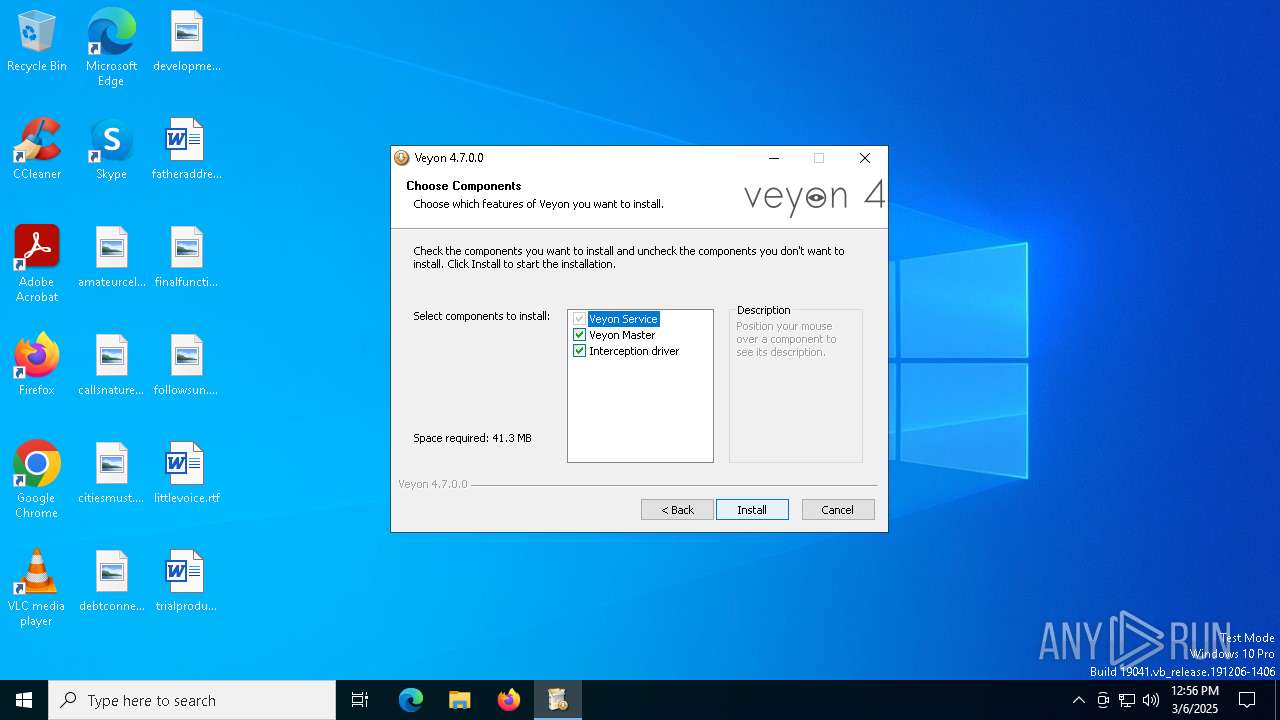
Executable content was dropped or overwritten
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
- install-interception.exe (PID: 5608)
Malware-specific behavior (creating "System.dll" in Temp)
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
There is functionality for taking screenshot (YARA)
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
- veyon-worker.exe (PID: 4220)
- veyon-service.exe (PID: 2108)
The process creates files with name similar to system file names
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
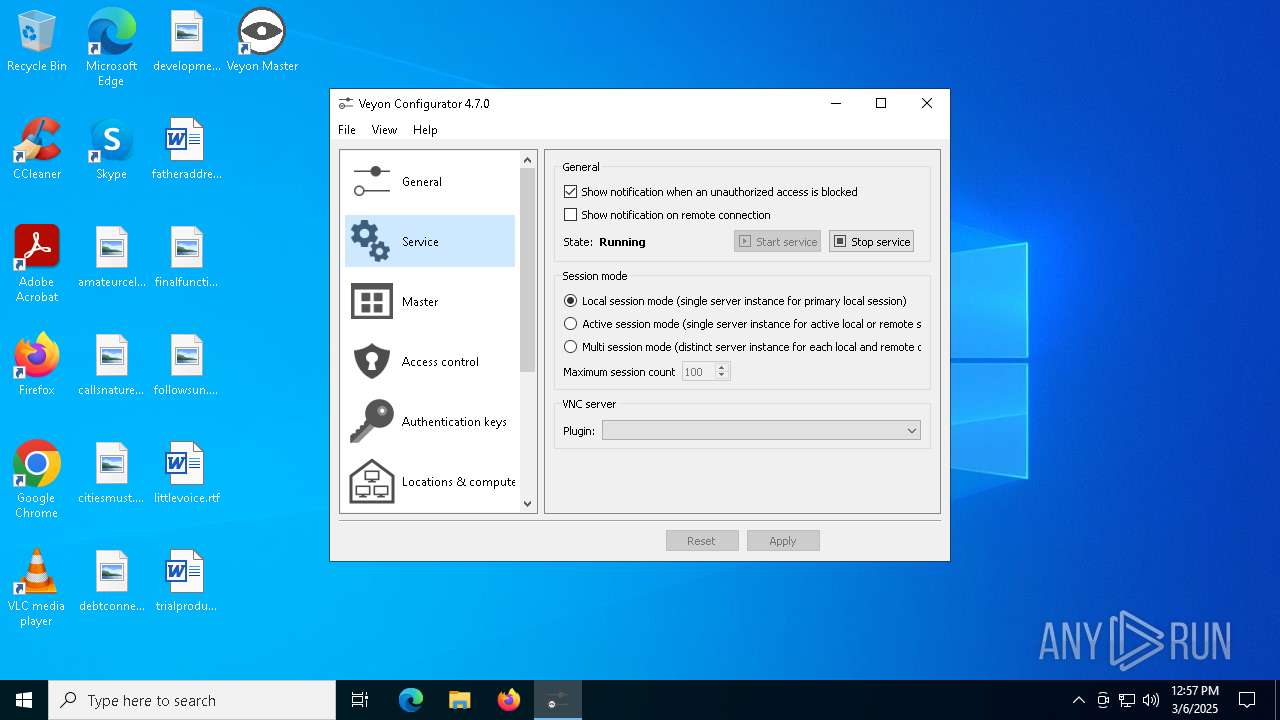
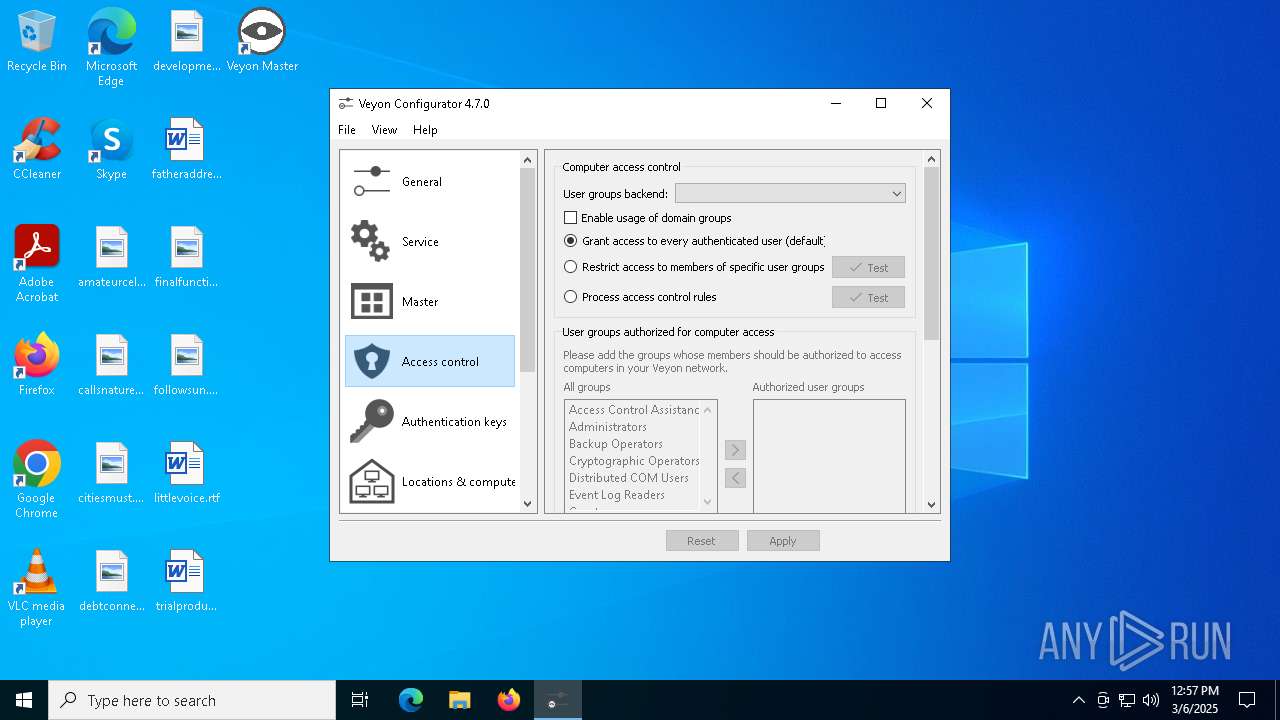
Executes as Windows Service
- veyon-service.exe (PID: 8084)
- veyon-service.exe (PID: 2108)
Creates a software uninstall entry
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
Creates files in the driver directory
- install-interception.exe (PID: 5608)
Creates or modifies Windows services
- install-interception.exe (PID: 5608)
Drops a system driver (possible attempt to evade defenses)
- install-interception.exe (PID: 5608)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8180)
- BackgroundTransferHost.exe (PID: 6540)
- BackgroundTransferHost.exe (PID: 4000)
- BackgroundTransferHost.exe (PID: 1532)
Reads the computer name
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
- veyon-wcli.exe (PID: 7896)
- veyon-wcli.exe (PID: 7680)
- veyon-server.exe (PID: 7892)
- veyon-service.exe (PID: 8084)
- veyon-worker.exe (PID: 4220)
- veyon-wcli.exe (PID: 7584)
- veyon-wcli.exe (PID: 8064)
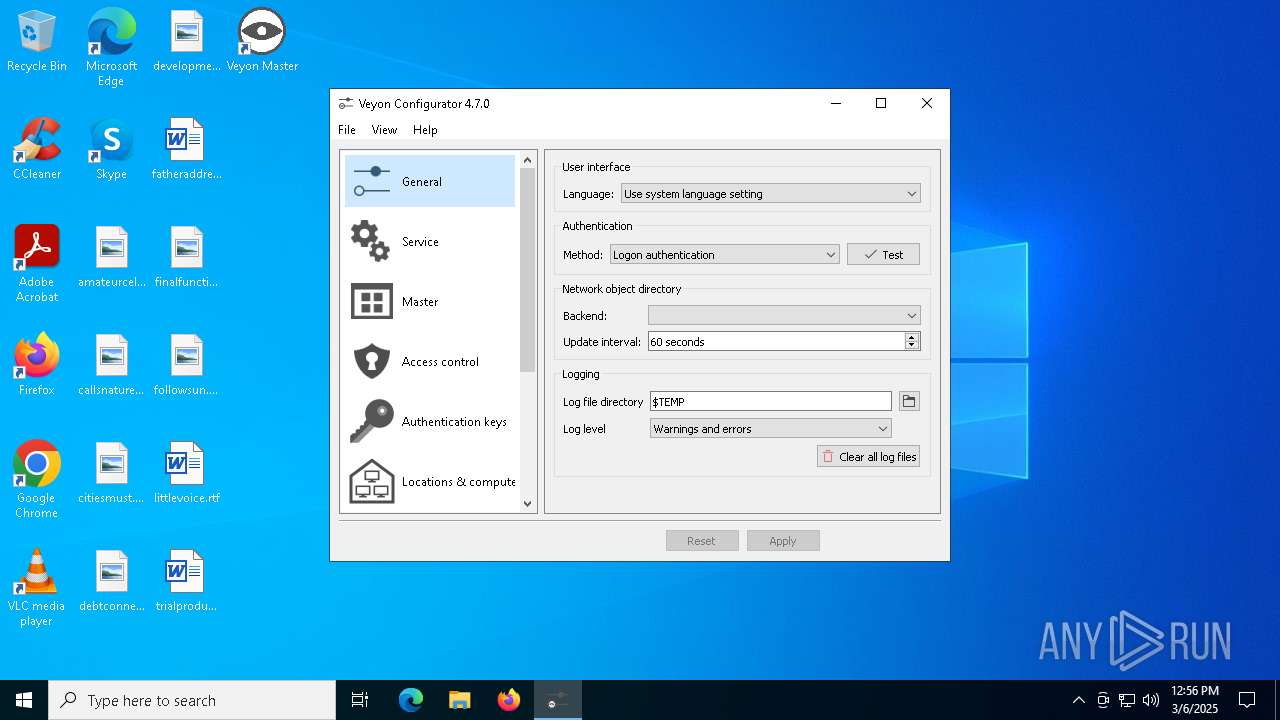
- veyon-configurator.exe (PID: 2772)
- veyon-service.exe (PID: 2108)
- ShellExperienceHost.exe (PID: 7224)
- veyon-master.exe (PID: 8016)
- veyon-worker.exe (PID: 7440)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8180)
- slui.exe (PID: 2088)
Checks supported languages
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
- veyon-wcli.exe (PID: 7896)
- veyon-wcli.exe (PID: 7680)
- veyon-wcli.exe (PID: 7584)
- veyon-wcli.exe (PID: 8064)
- veyon-service.exe (PID: 8084)
- veyon-server.exe (PID: 7892)
- veyon-worker.exe (PID: 4220)
- veyon-configurator.exe (PID: 2772)
- veyon-service.exe (PID: 2108)
- install-interception.exe (PID: 5608)
- ShellExperienceHost.exe (PID: 7224)
- veyon-master.exe (PID: 8016)
- veyon-worker.exe (PID: 7440)
Create files in a temporary directory
- veyon-wcli.exe (PID: 7896)
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
- veyon-worker.exe (PID: 4220)
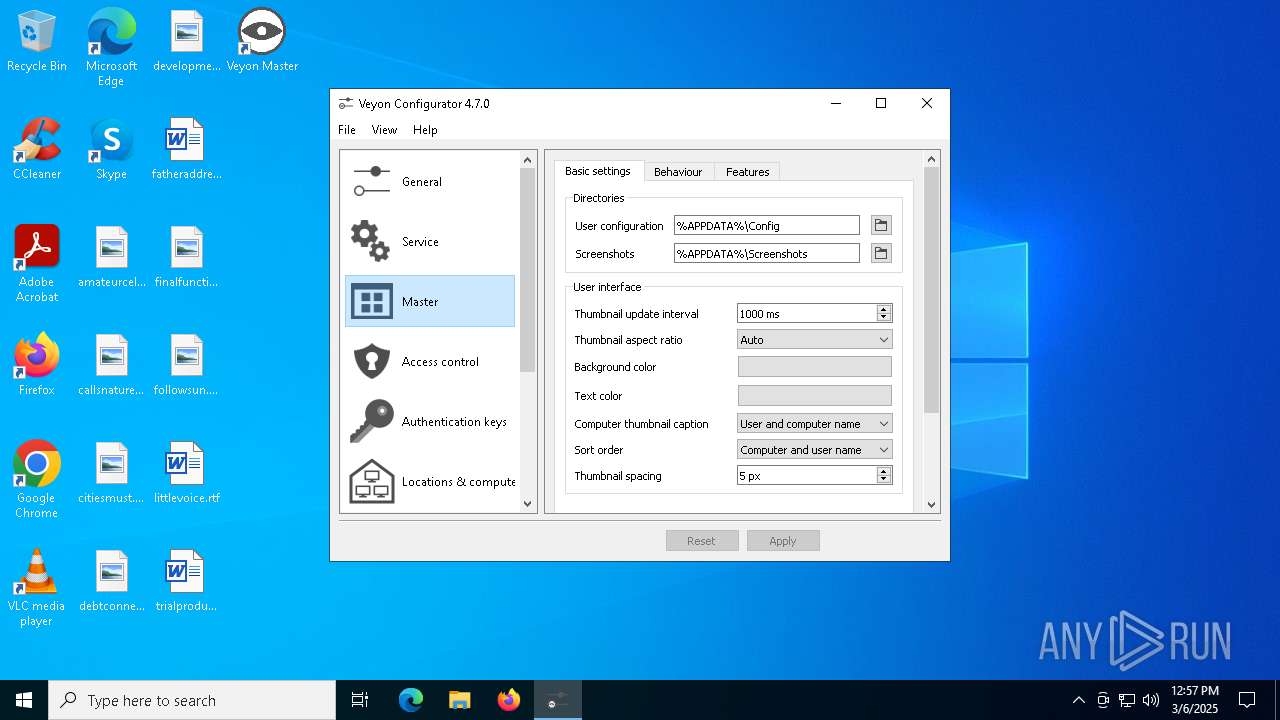
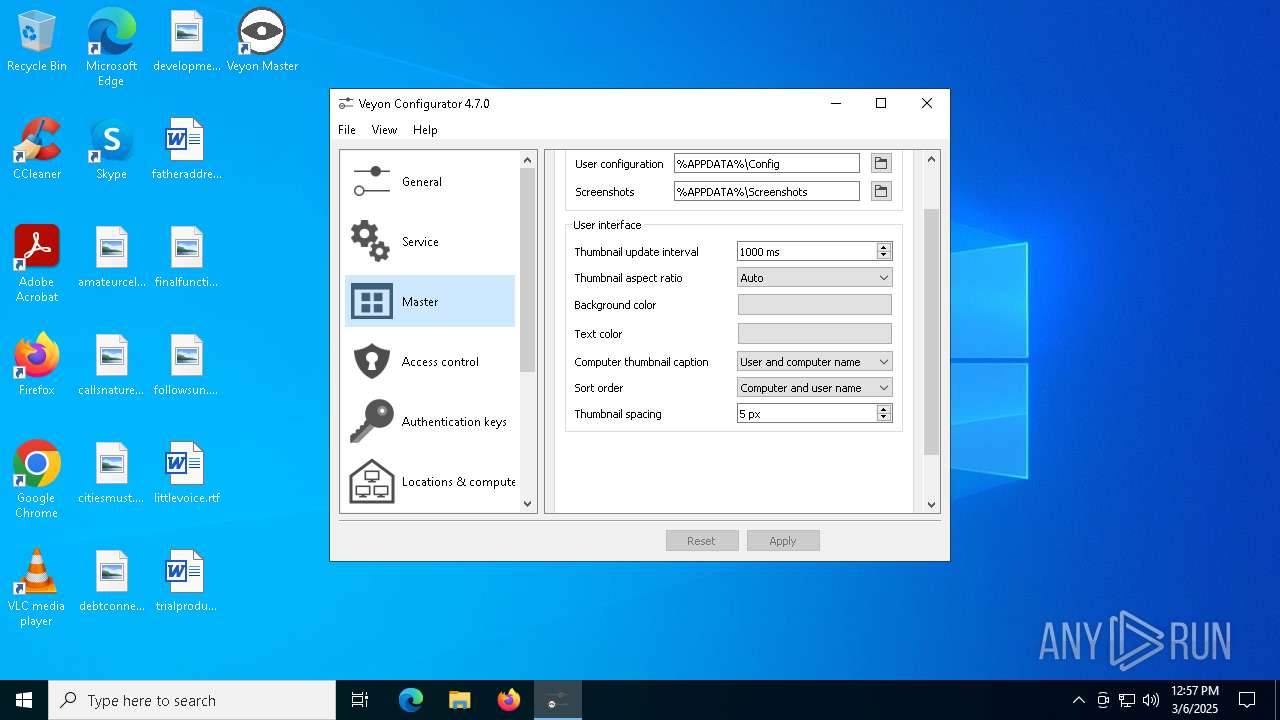
- veyon-configurator.exe (PID: 2772)
- veyon-master.exe (PID: 8016)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8180)
- veyon-master.exe (PID: 8016)
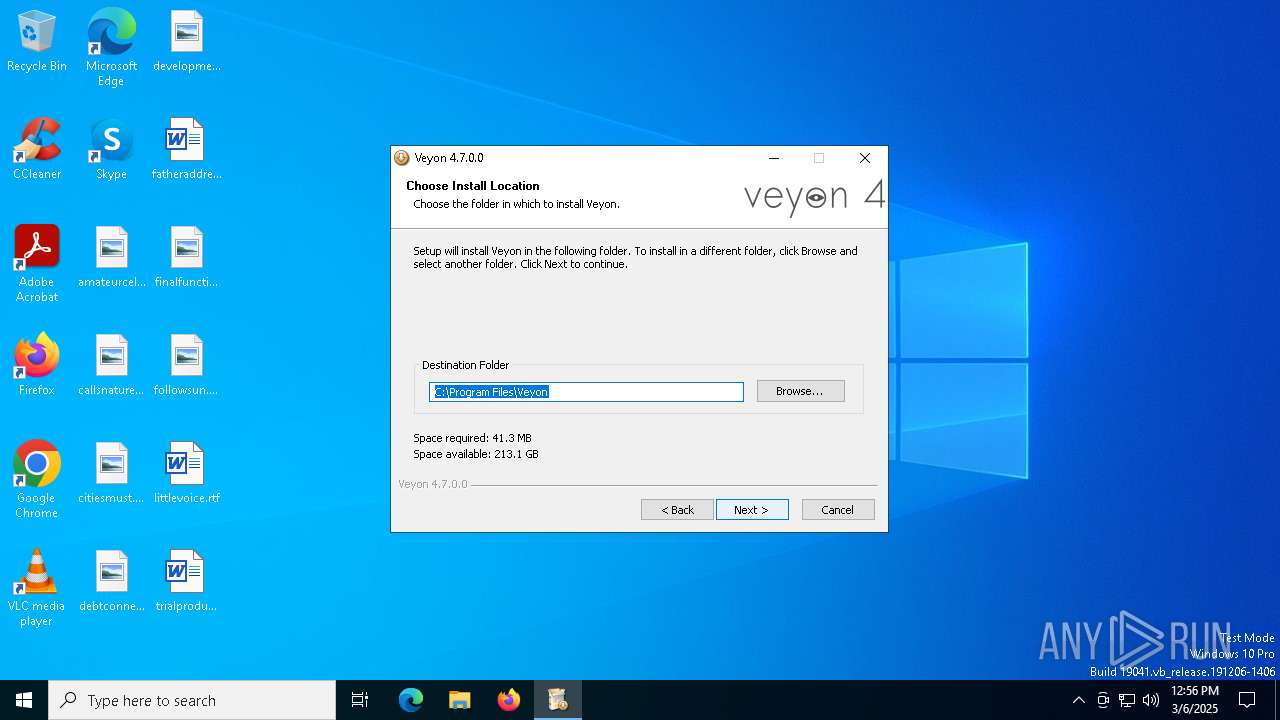
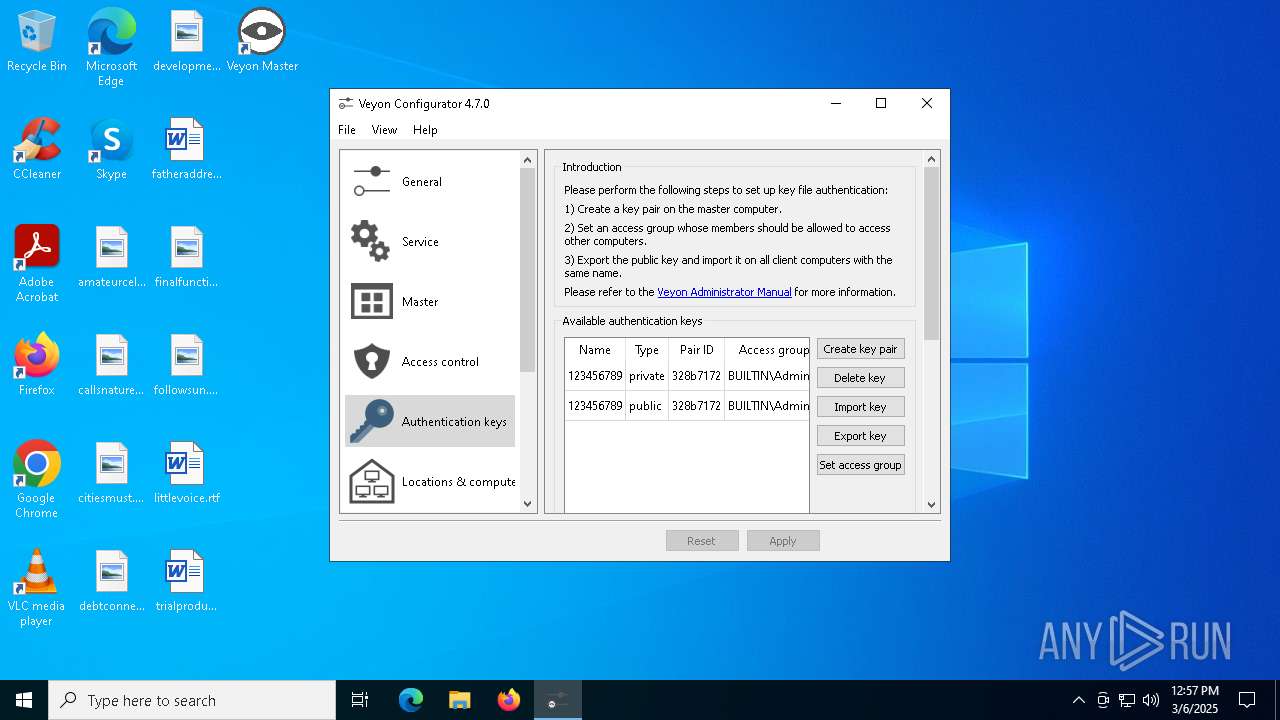
Creates files in the program directory
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
- veyon-configurator.exe (PID: 2772)
Reads the machine GUID from the registry
- veyon-wcli.exe (PID: 7896)
- veyon-wcli.exe (PID: 7680)
- veyon-wcli.exe (PID: 7584)
- veyon-wcli.exe (PID: 8064)
- veyon-service.exe (PID: 8084)
- veyon-server.exe (PID: 7892)
- veyon-worker.exe (PID: 4220)
- veyon-configurator.exe (PID: 2772)
- veyon-service.exe (PID: 2108)
- veyon-server.exe (PID: 7568)
- veyon-master.exe (PID: 8016)
- veyon-worker.exe (PID: 7440)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8180)
The sample compiled with english language support
- veyon-4.7.0.0-win64-setup.exe (PID: 7980)
- install-interception.exe (PID: 5608)
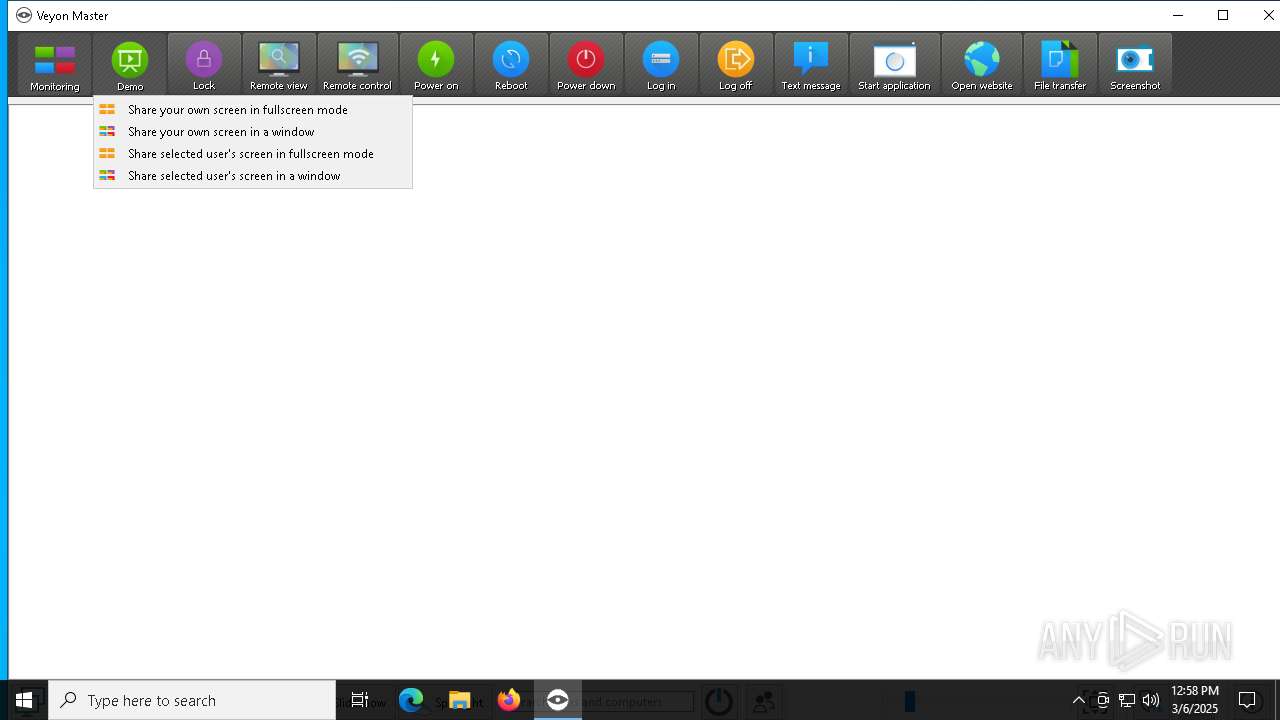
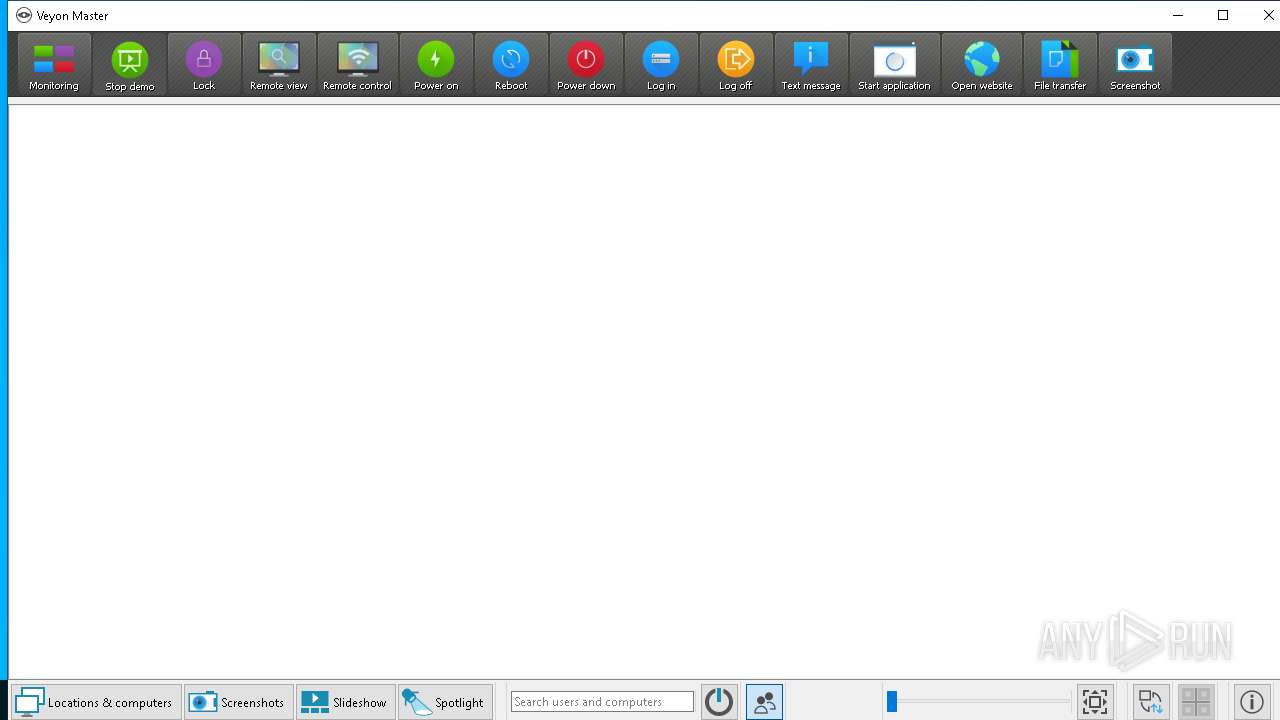
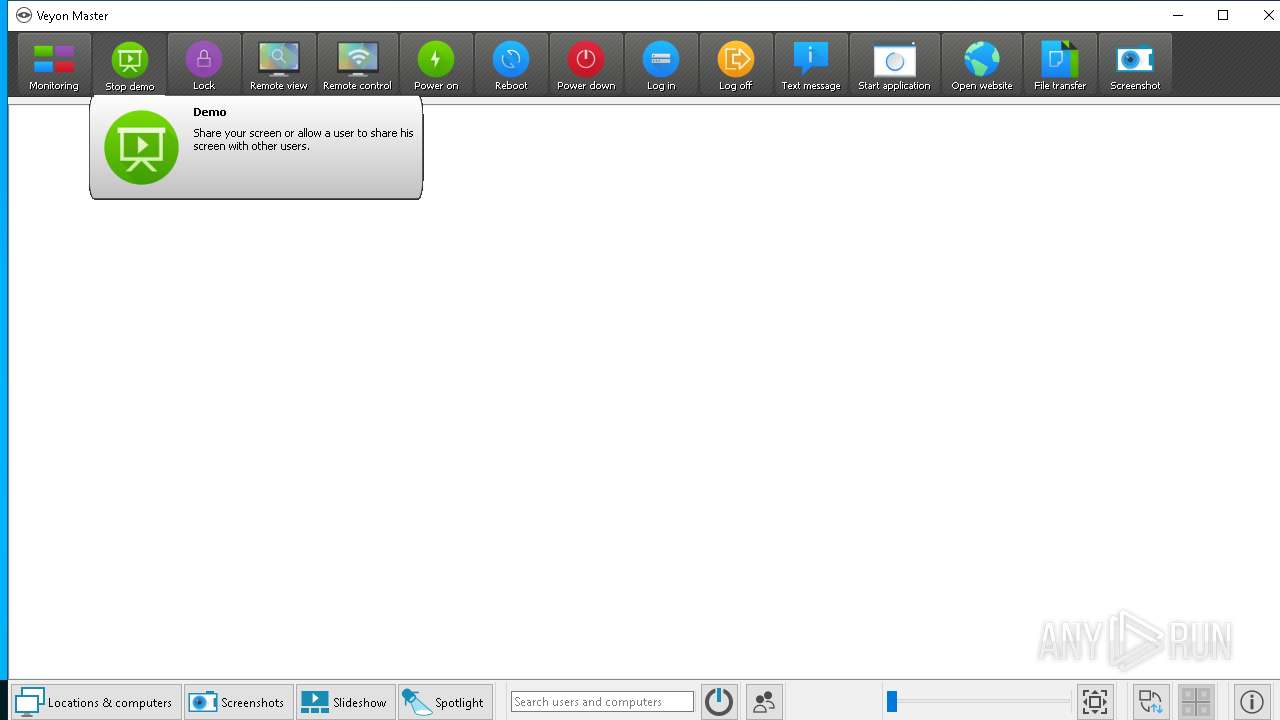
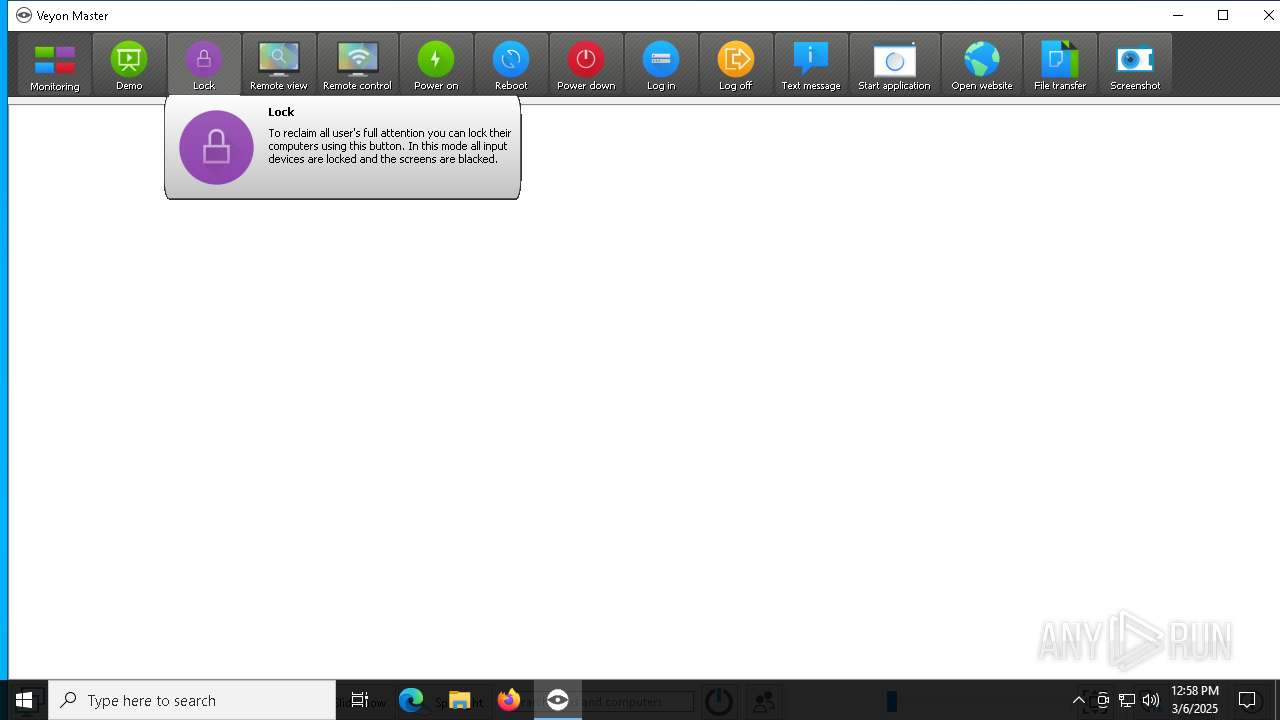
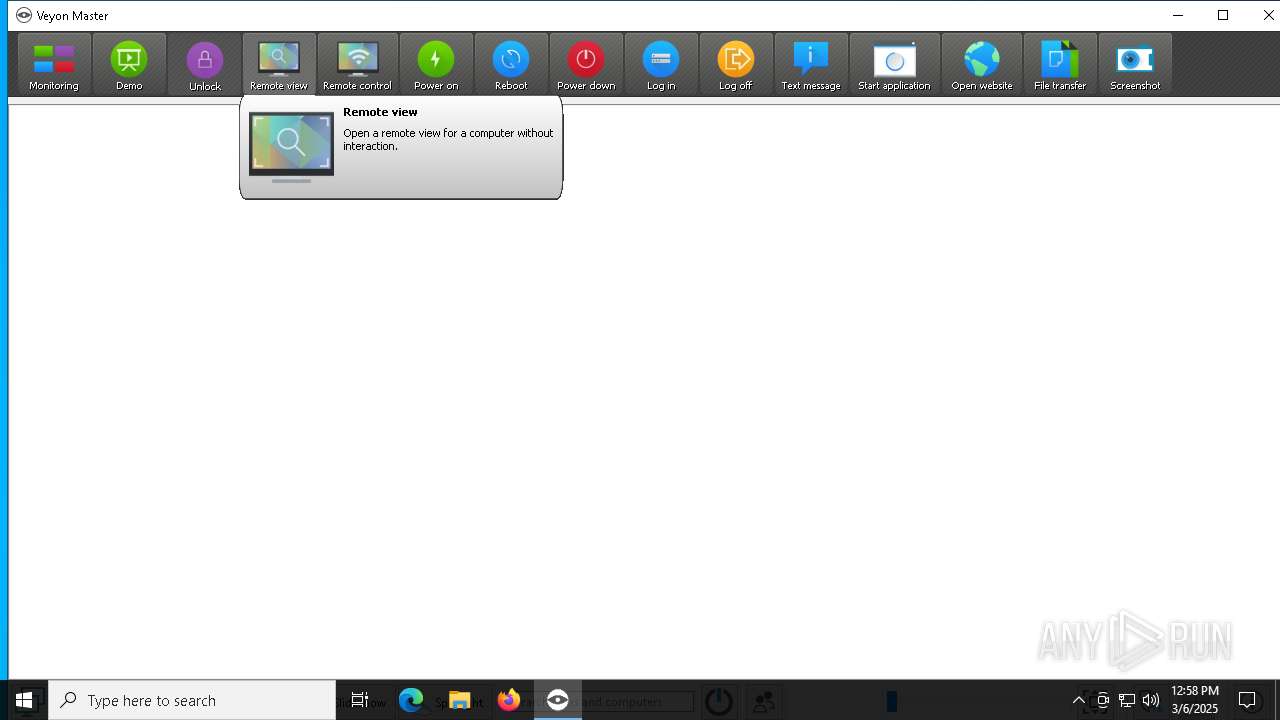
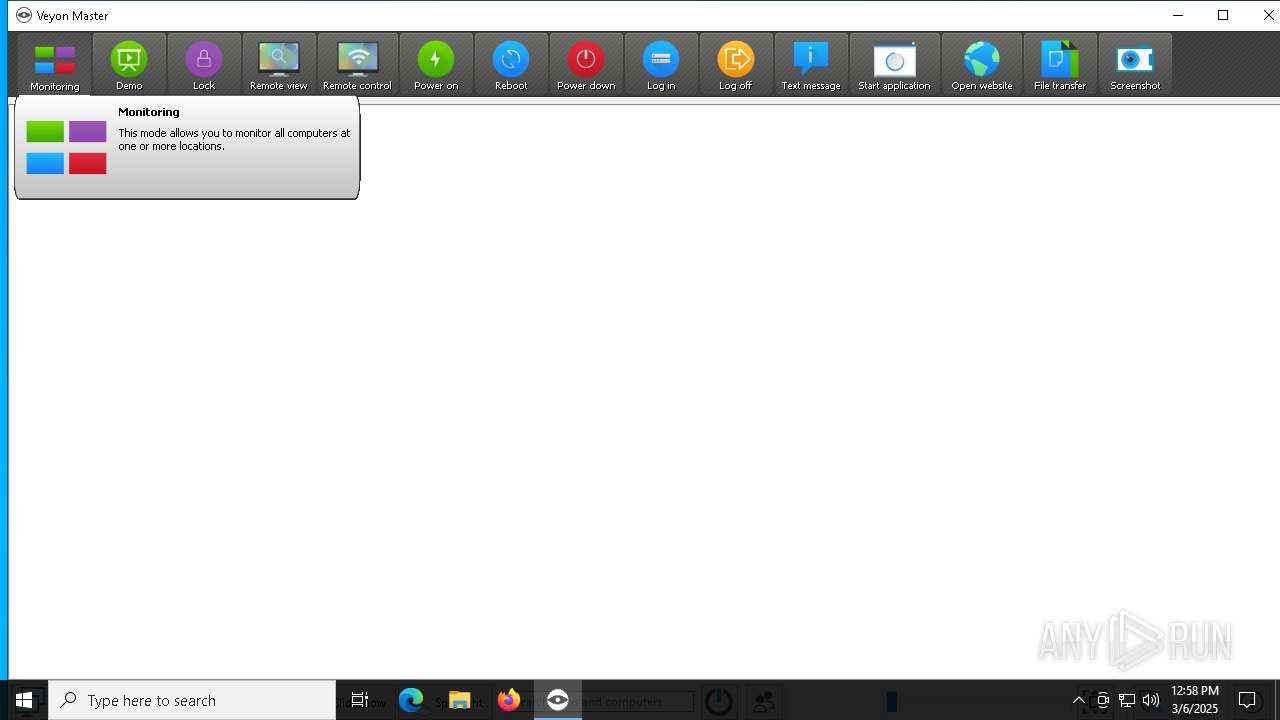
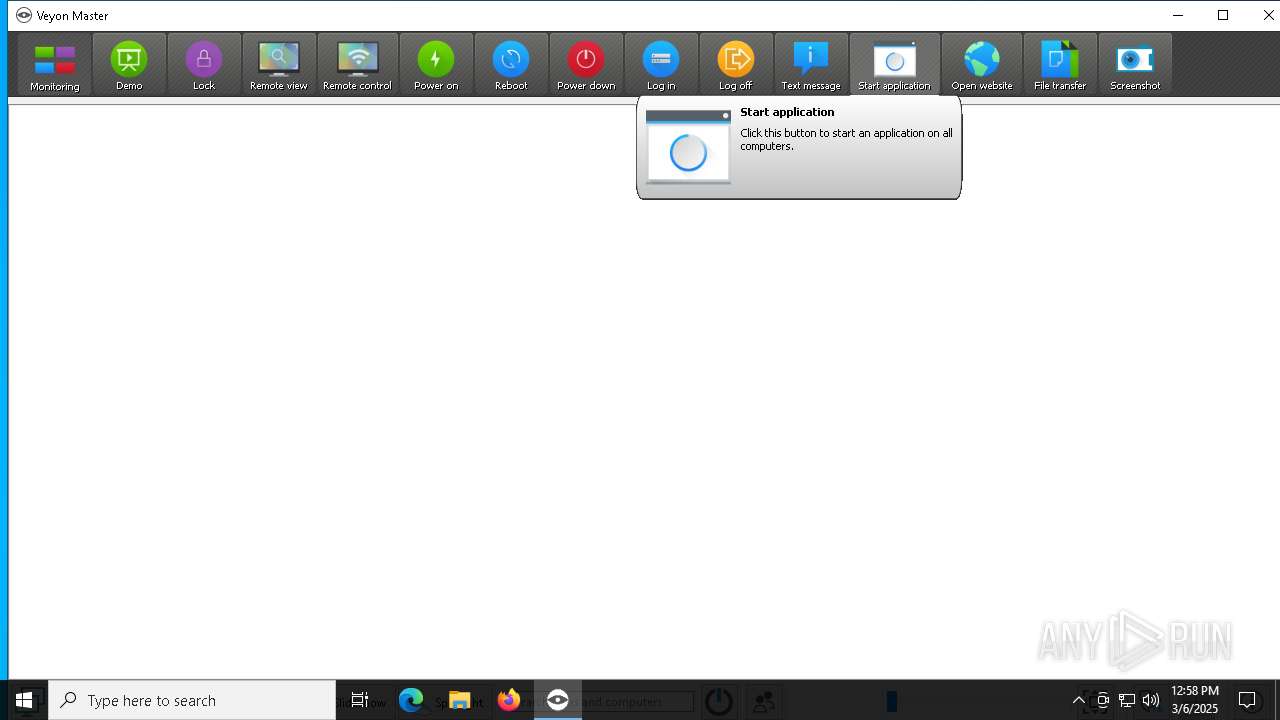
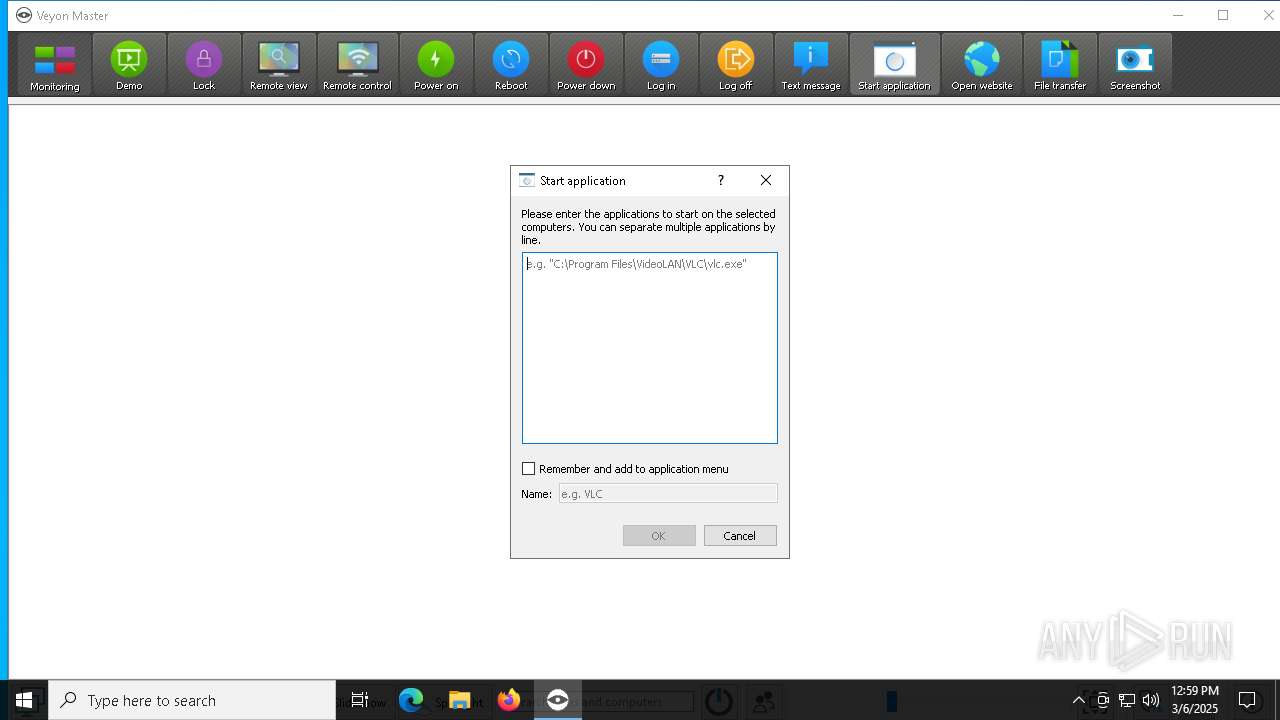
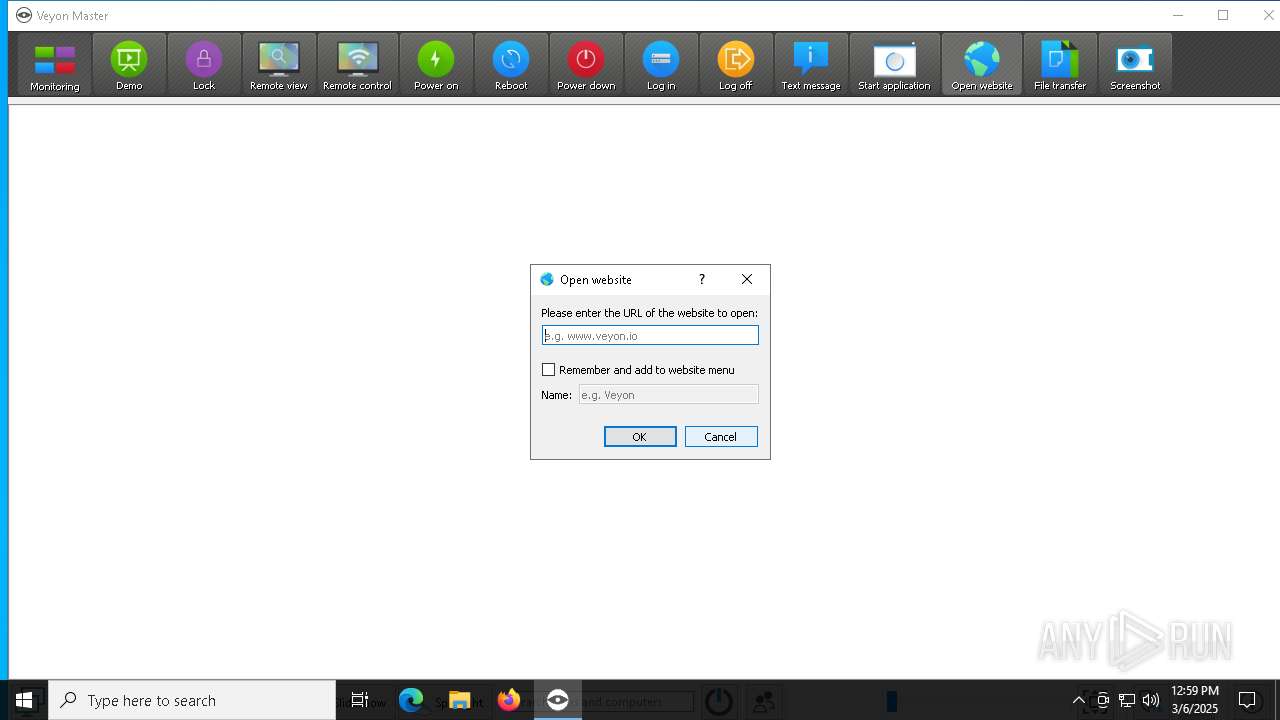
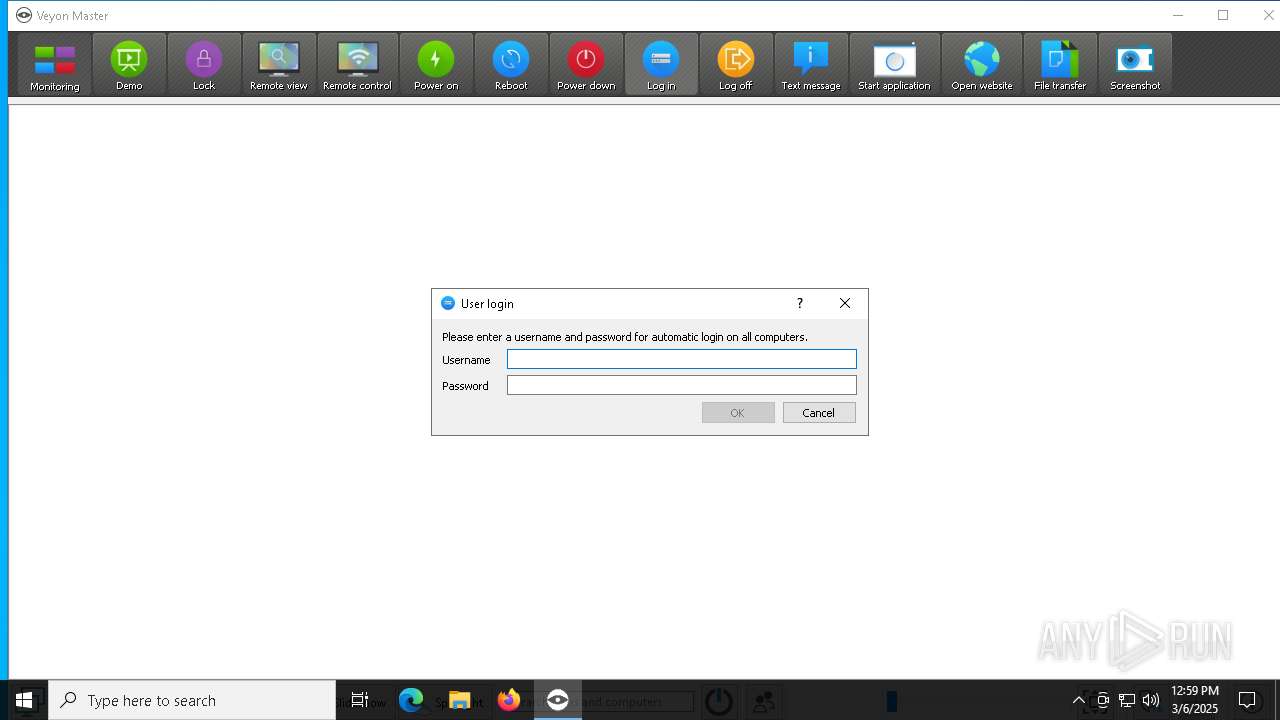
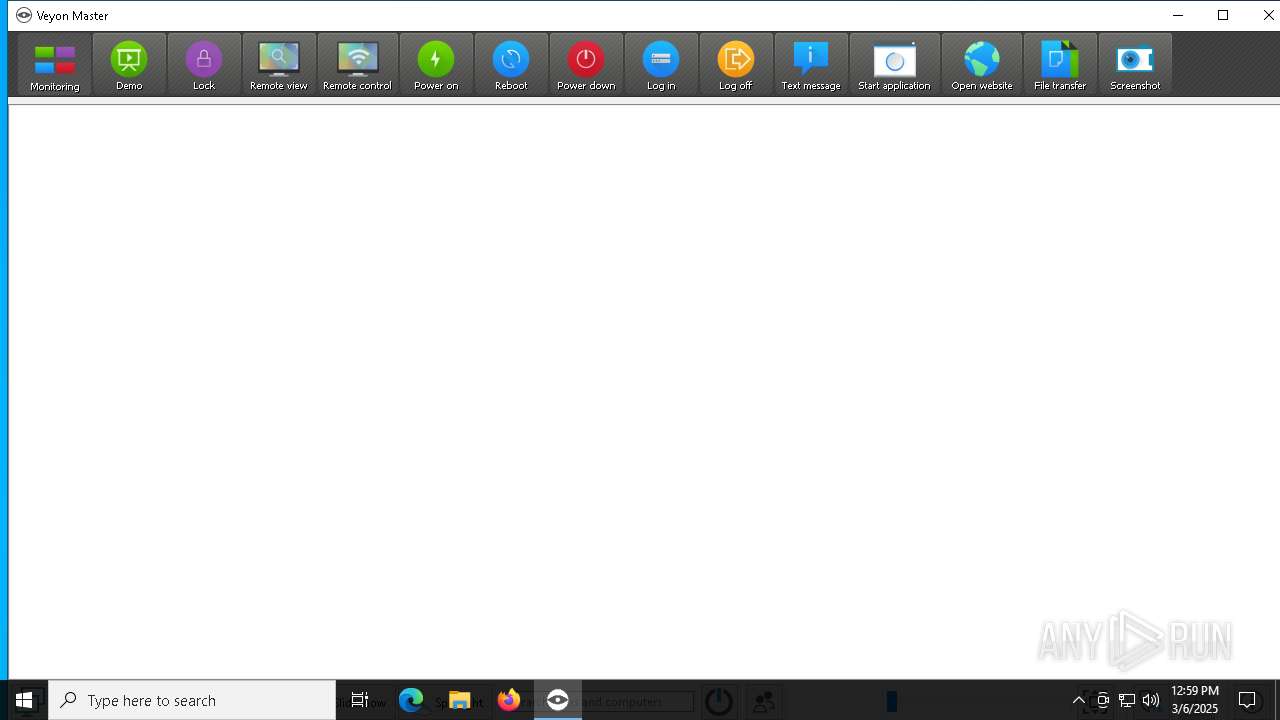
Manual execution by a user
- veyon-master.exe (PID: 8016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:31 18:05:25+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.34 |
| CodeSize: | 36864 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | 108032 |
| EntryPoint: | 0x433c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.7.0.0 |
| ProductVersionNumber: | 4.7.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Veyon Solutions |
| FileDescription: | Veyon Installer |
| FileVersion: | 4.7.0.0 |
| LegalCopyright: | 2004-2021 Veyon Solutions / Tobias Junghans |
| ProductName: | Veyon |
| ProductVersion: | 4.7.0.0 |
Total processes
165
Monitored processes
23
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1532 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Veyon\veyon-service.exe" | C:\Program Files\Veyon\veyon-service.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Veyon Solutions Integrity Level: SYSTEM Description: Veyon Service Version: 4.7.0 Modules
| |||||||||||||||
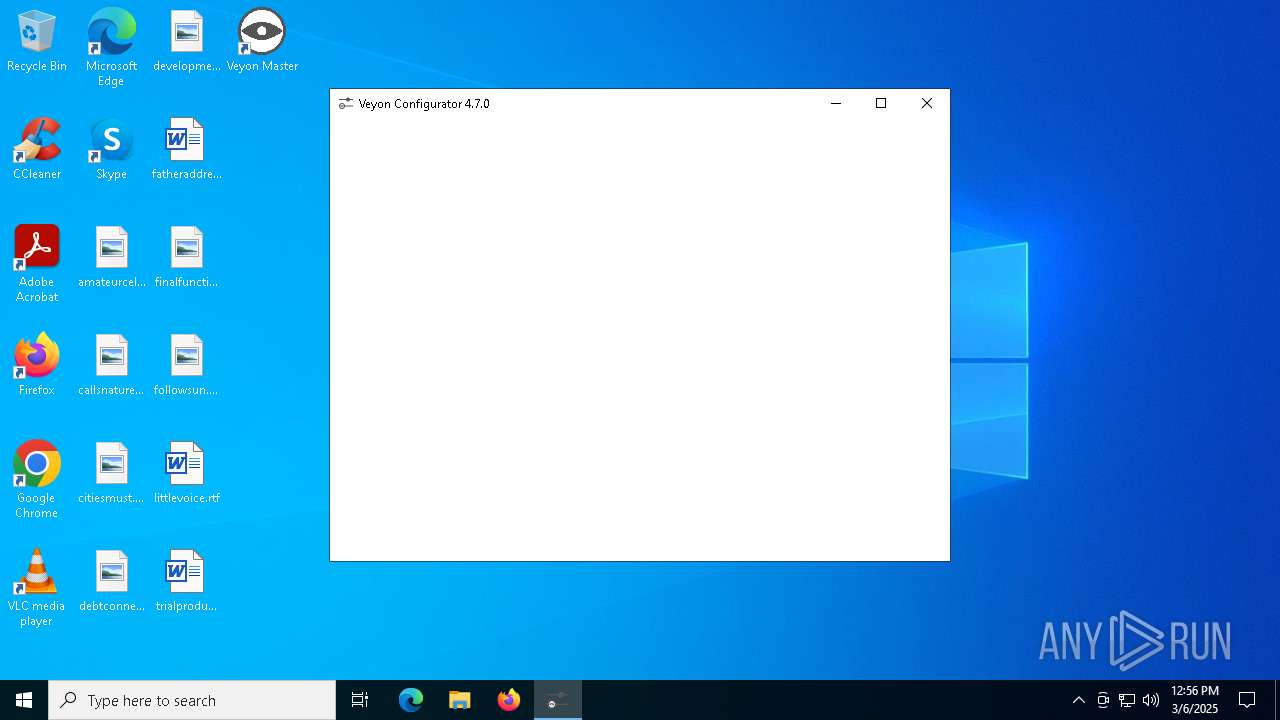
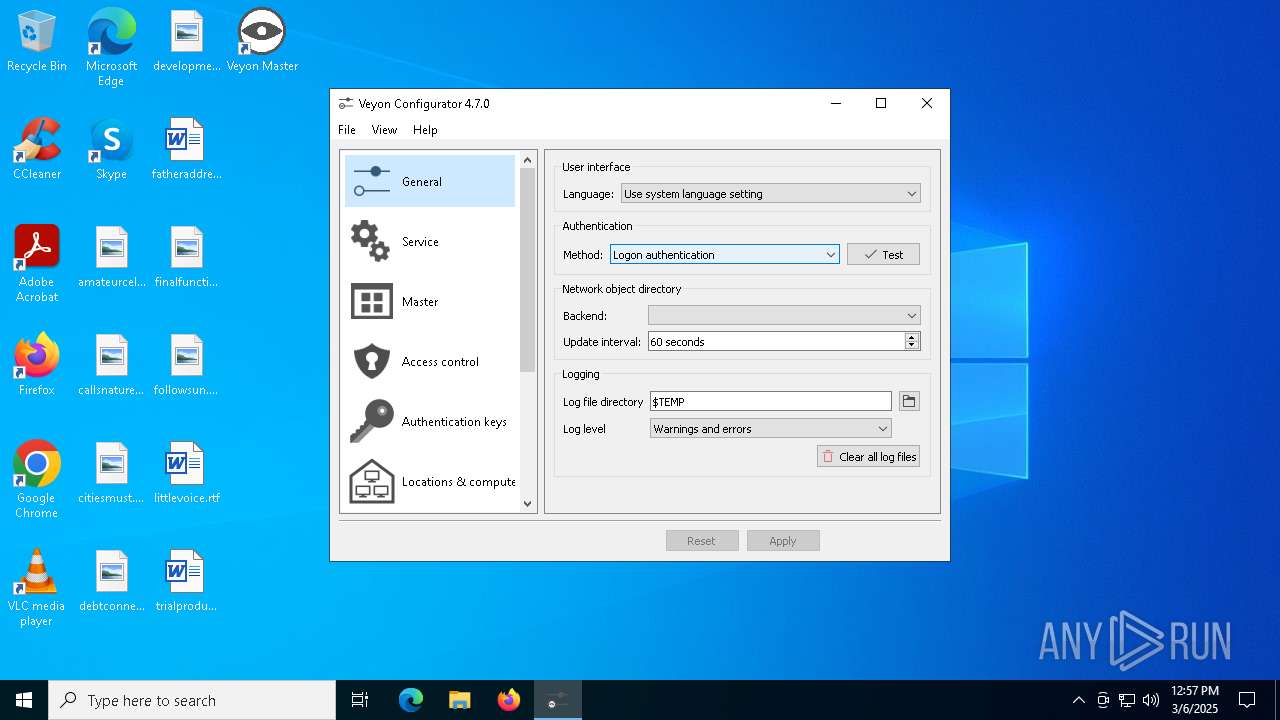
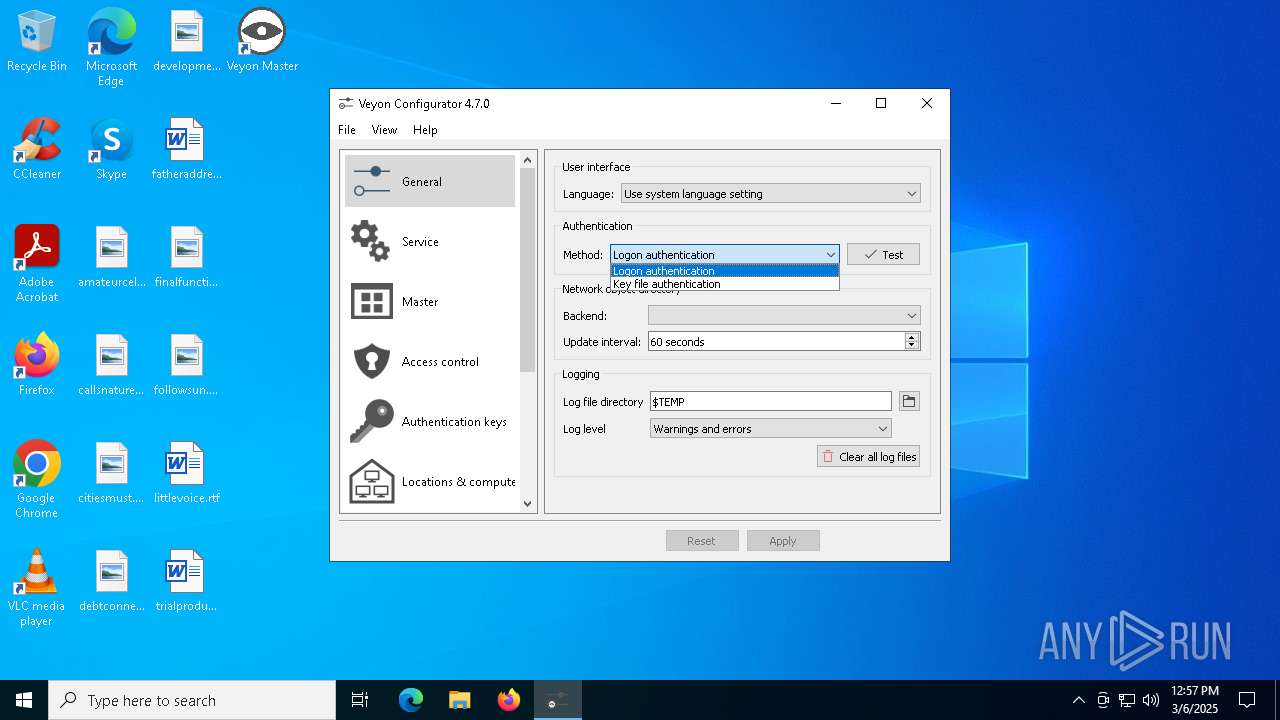
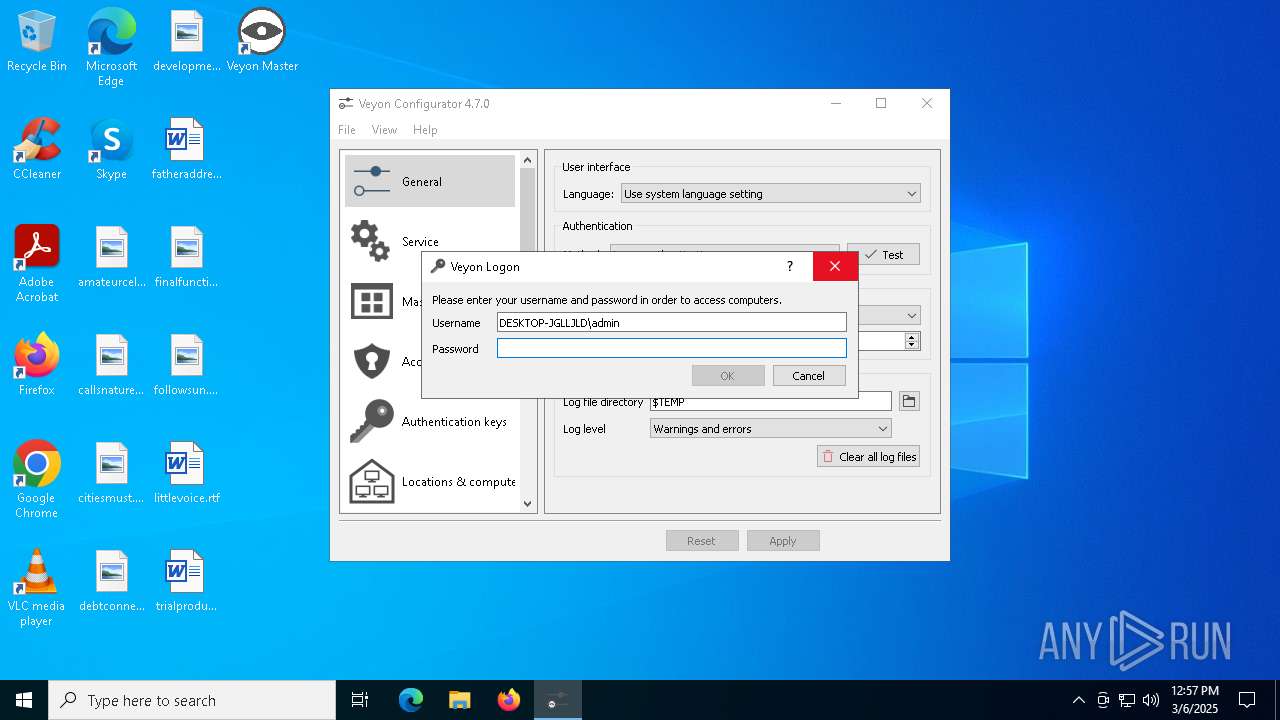
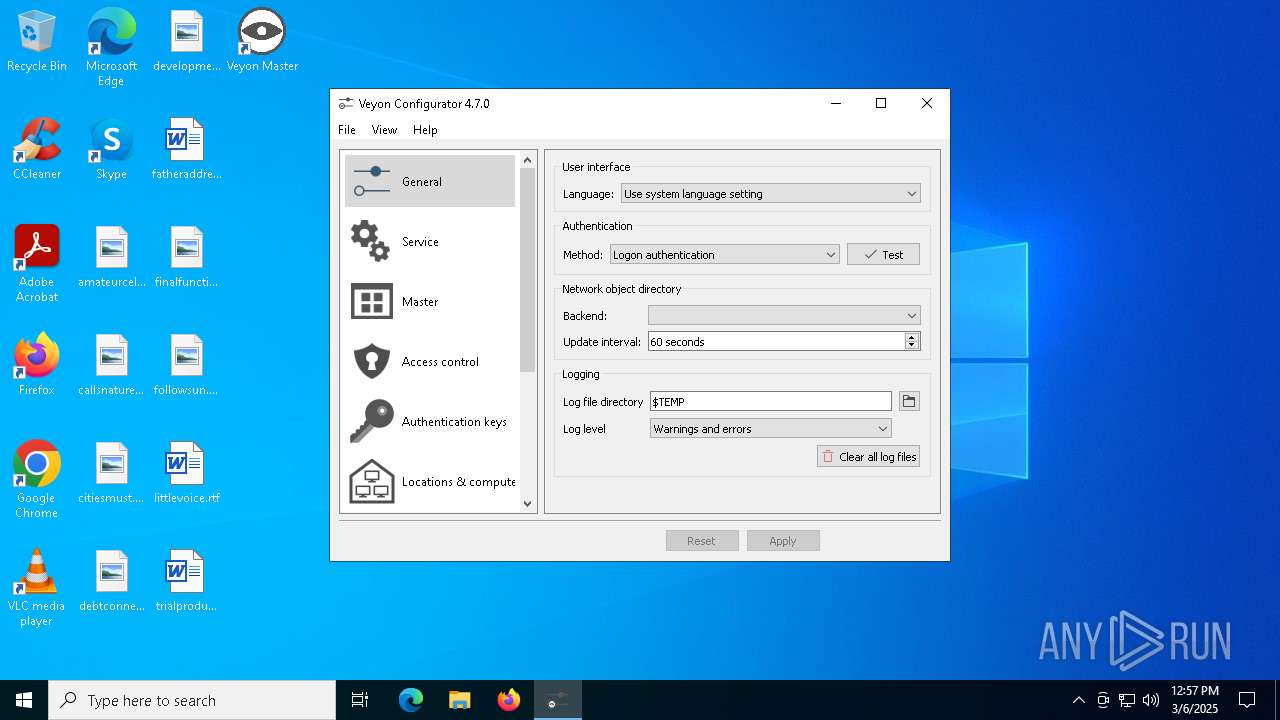
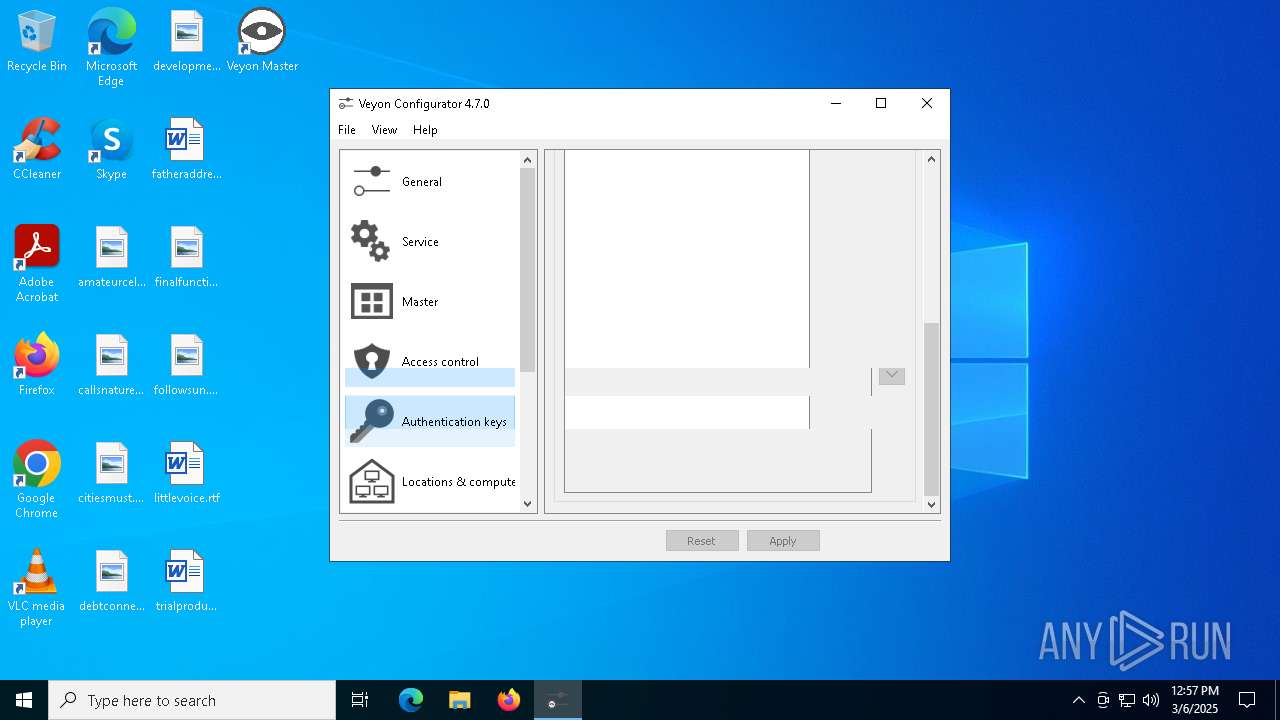
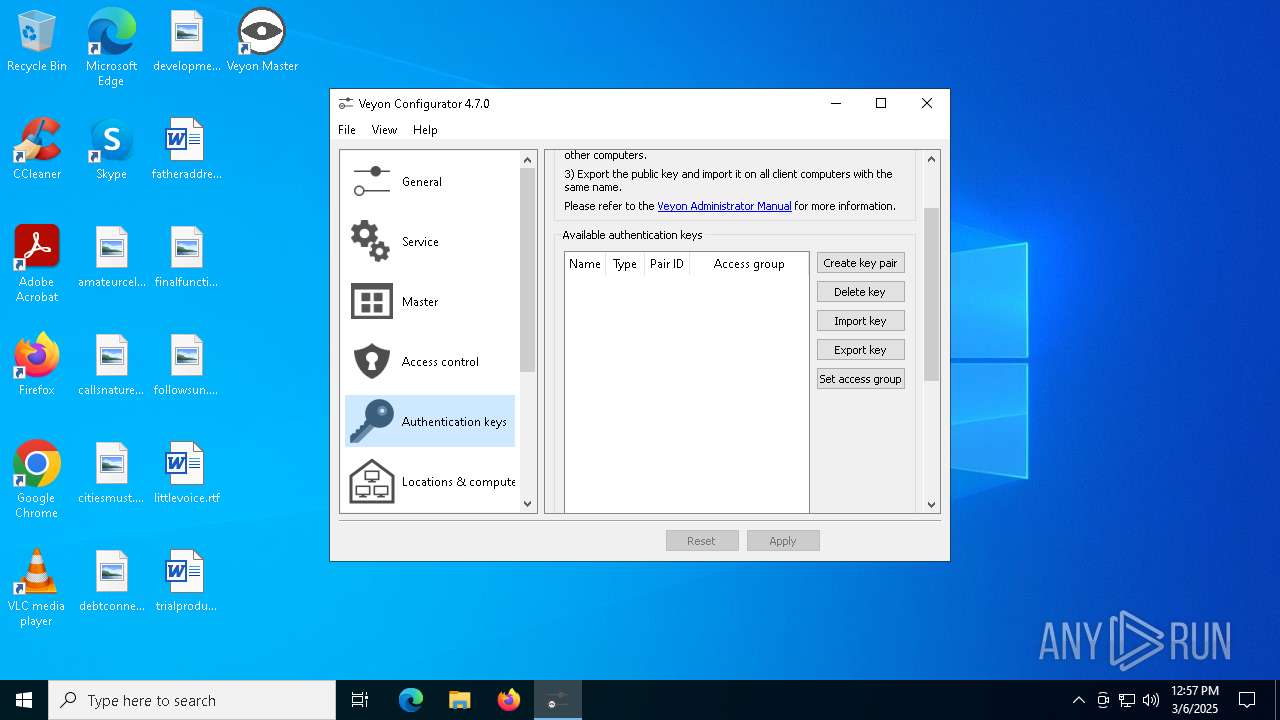
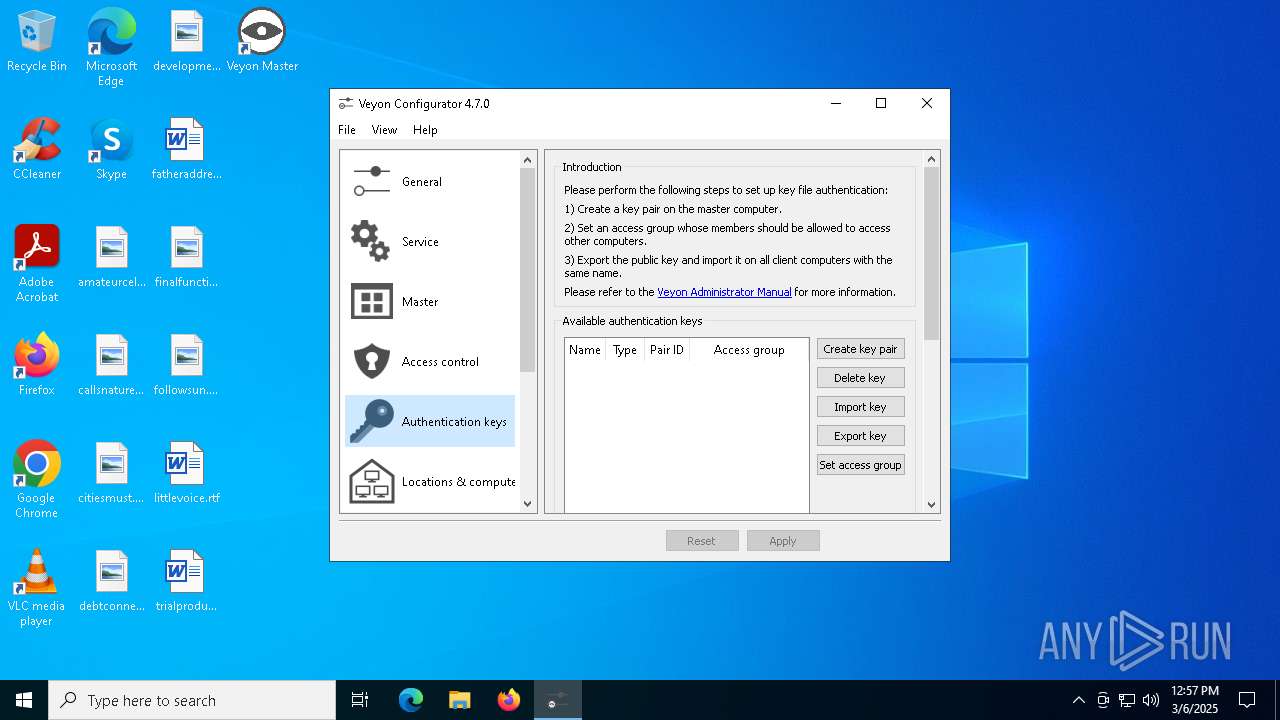
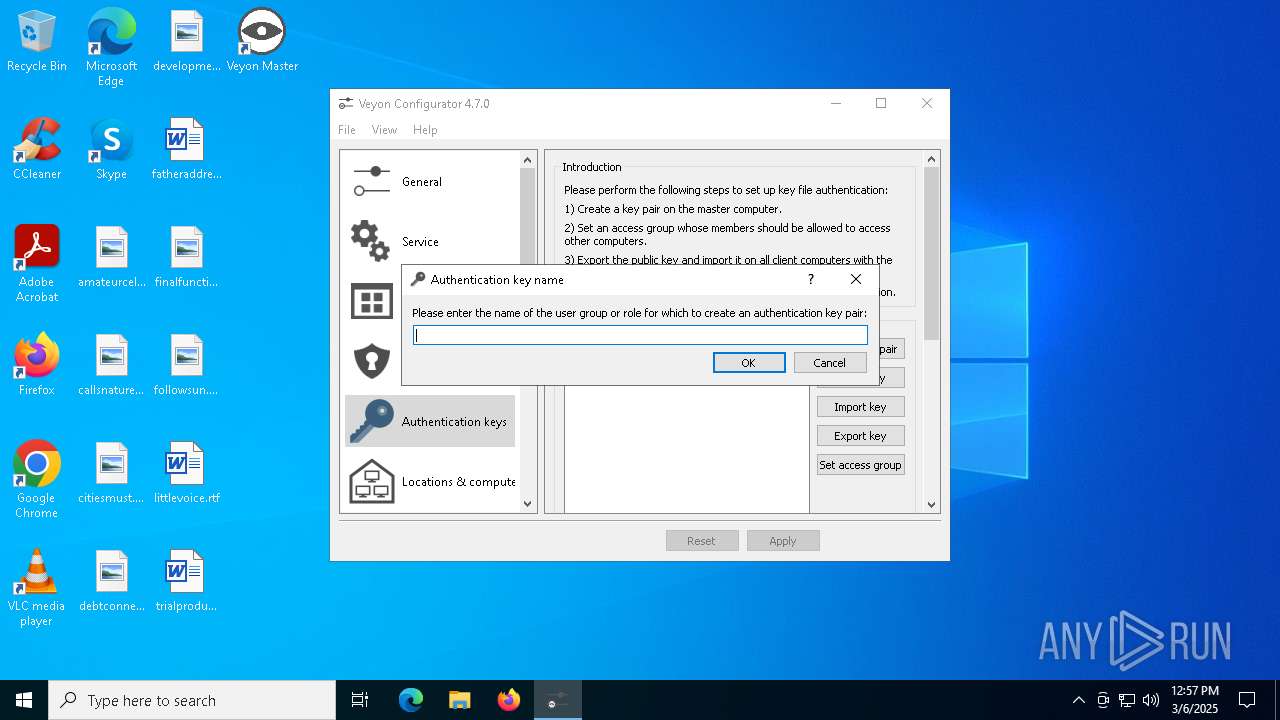
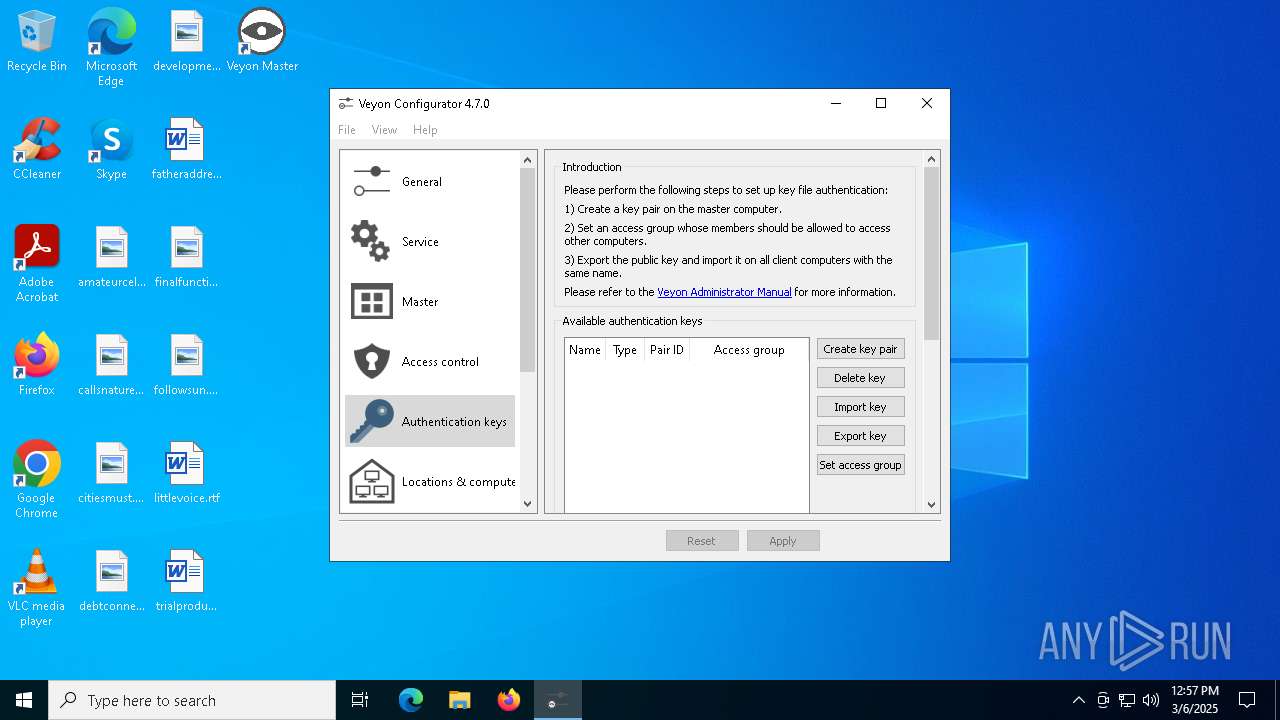
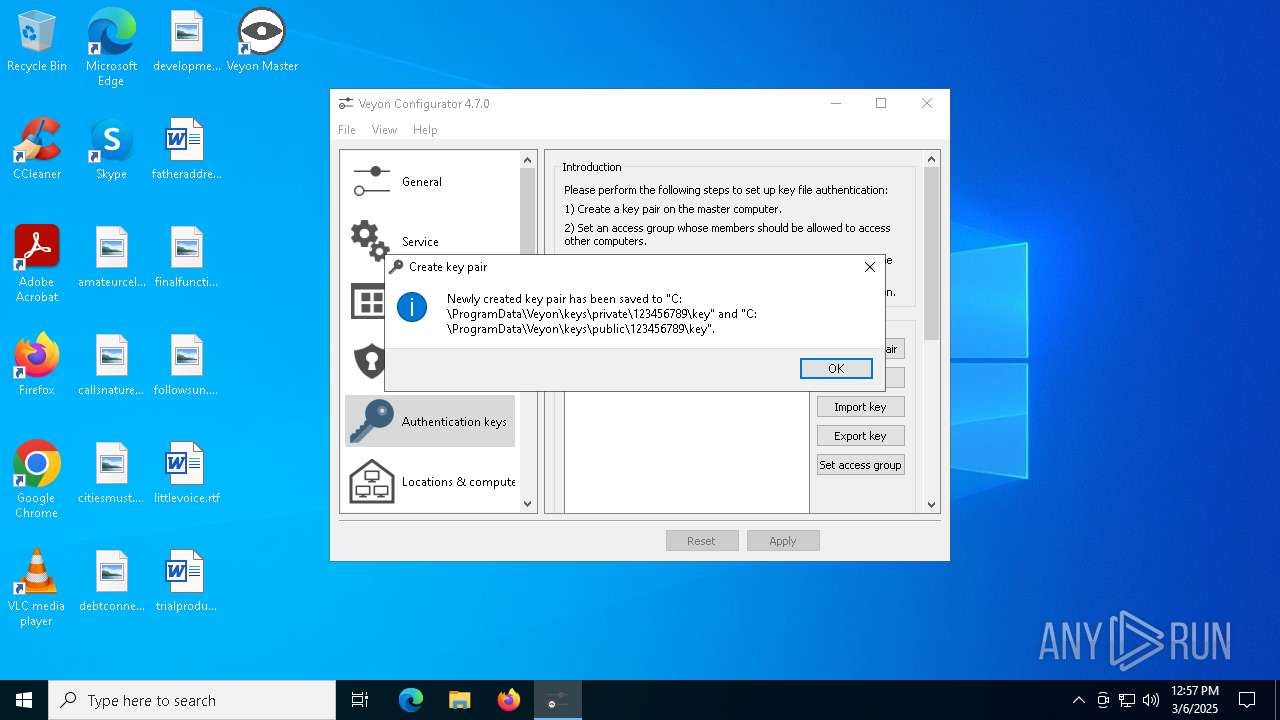
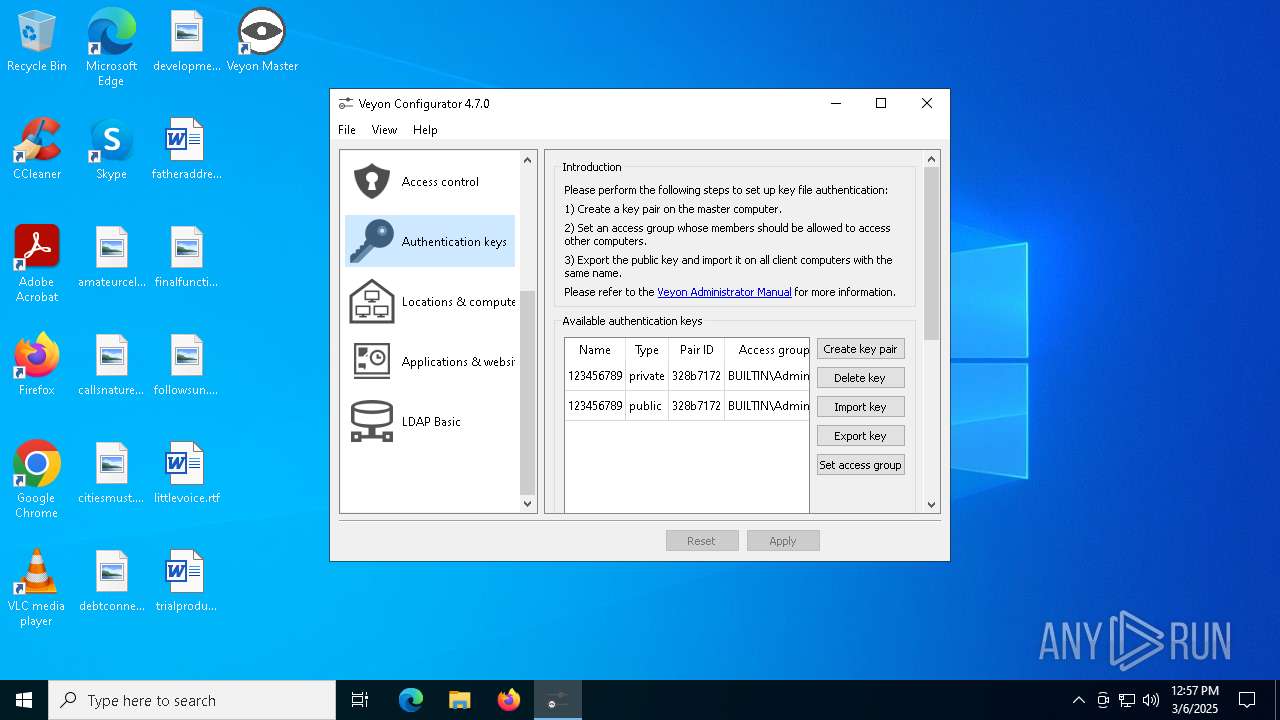
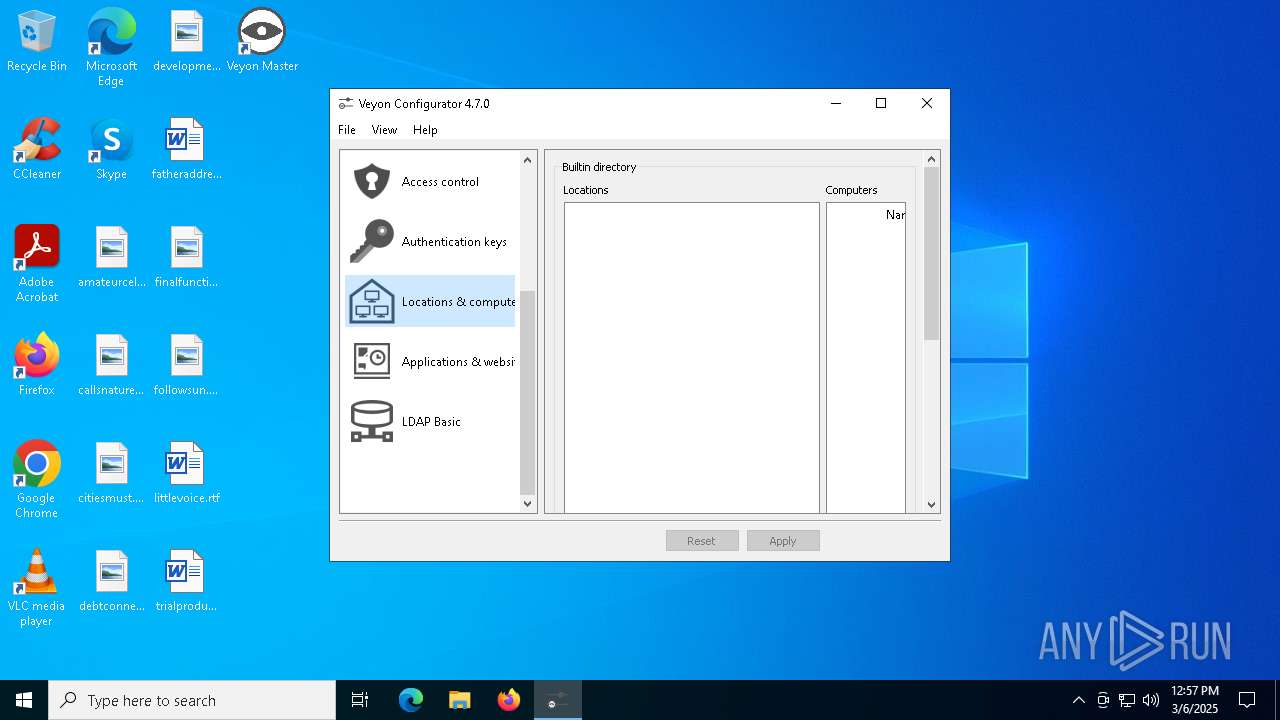
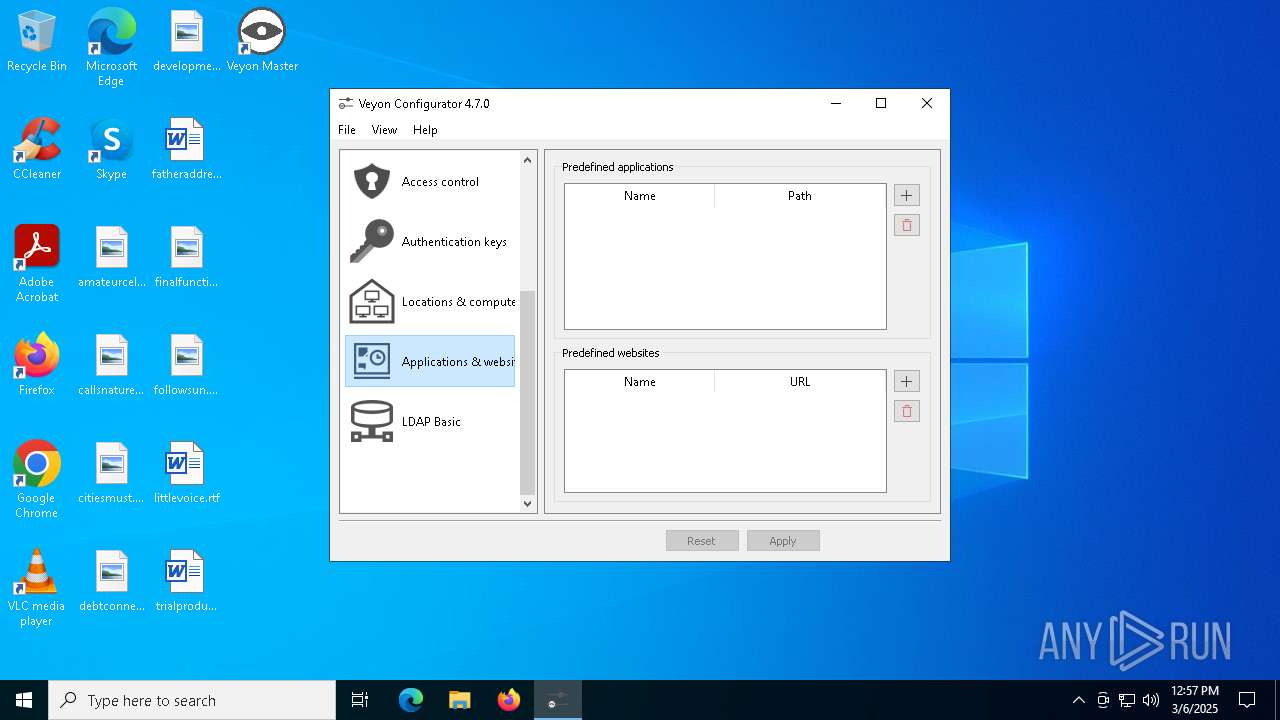
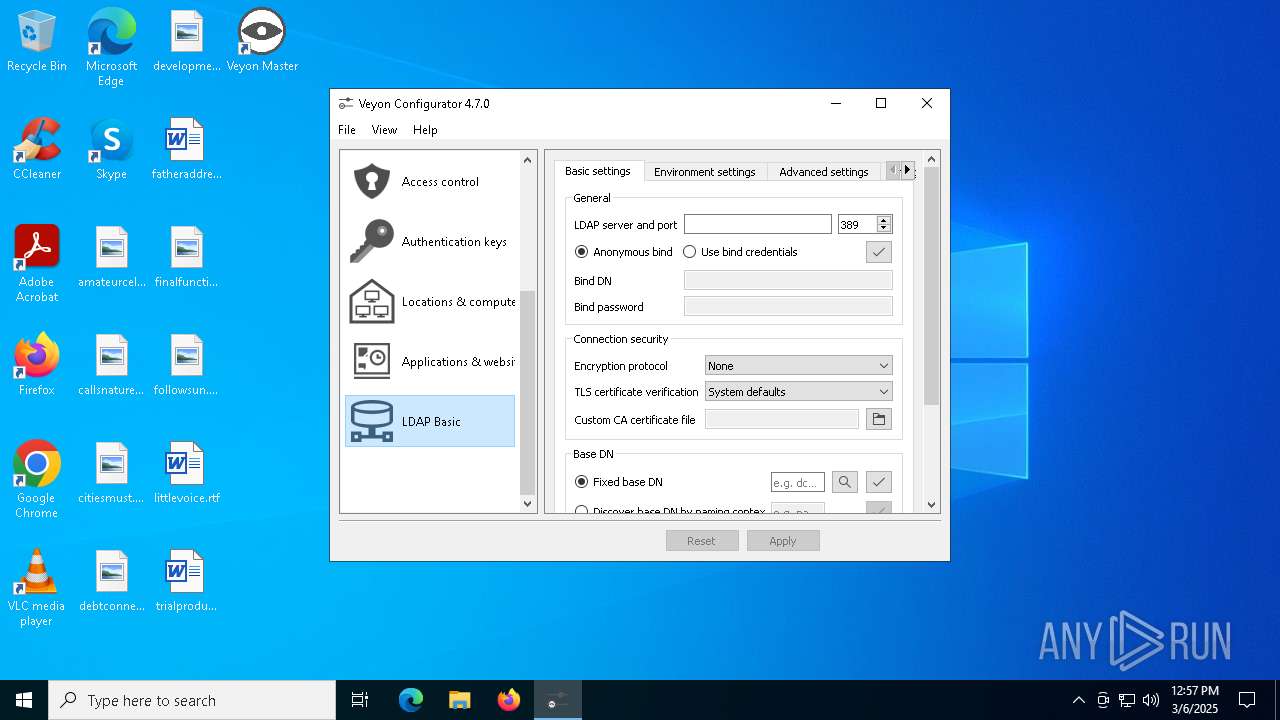
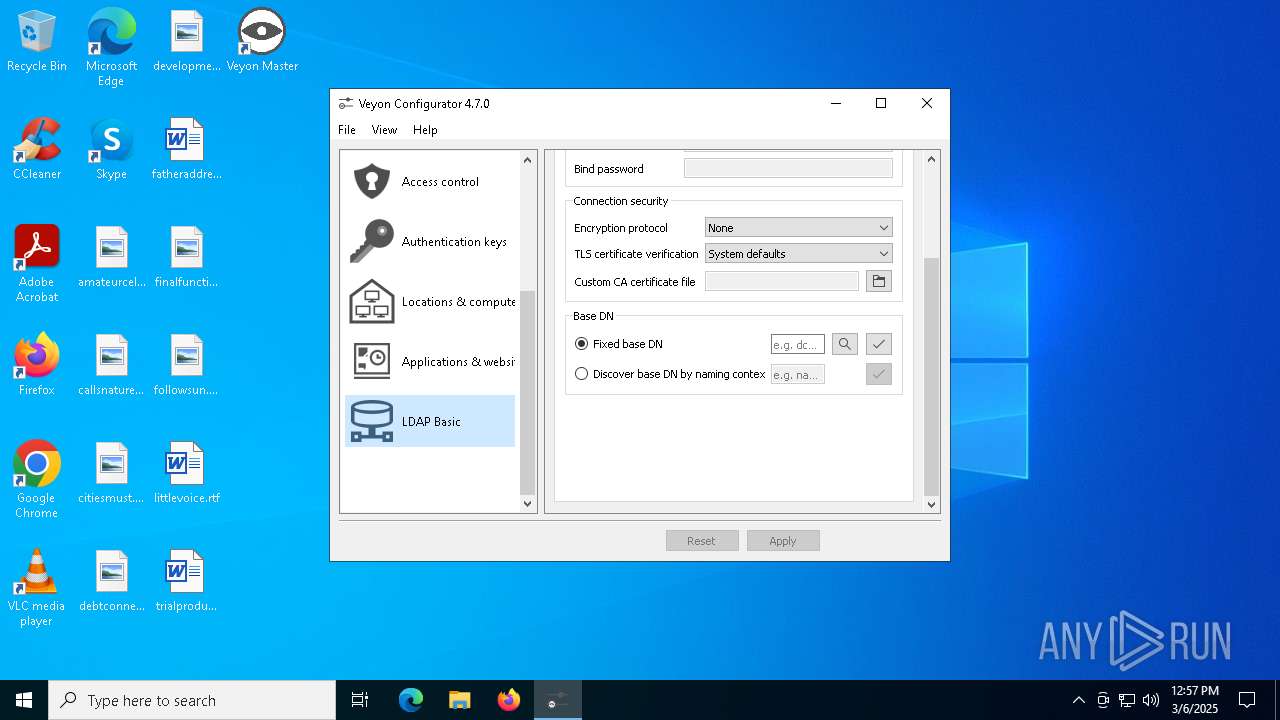
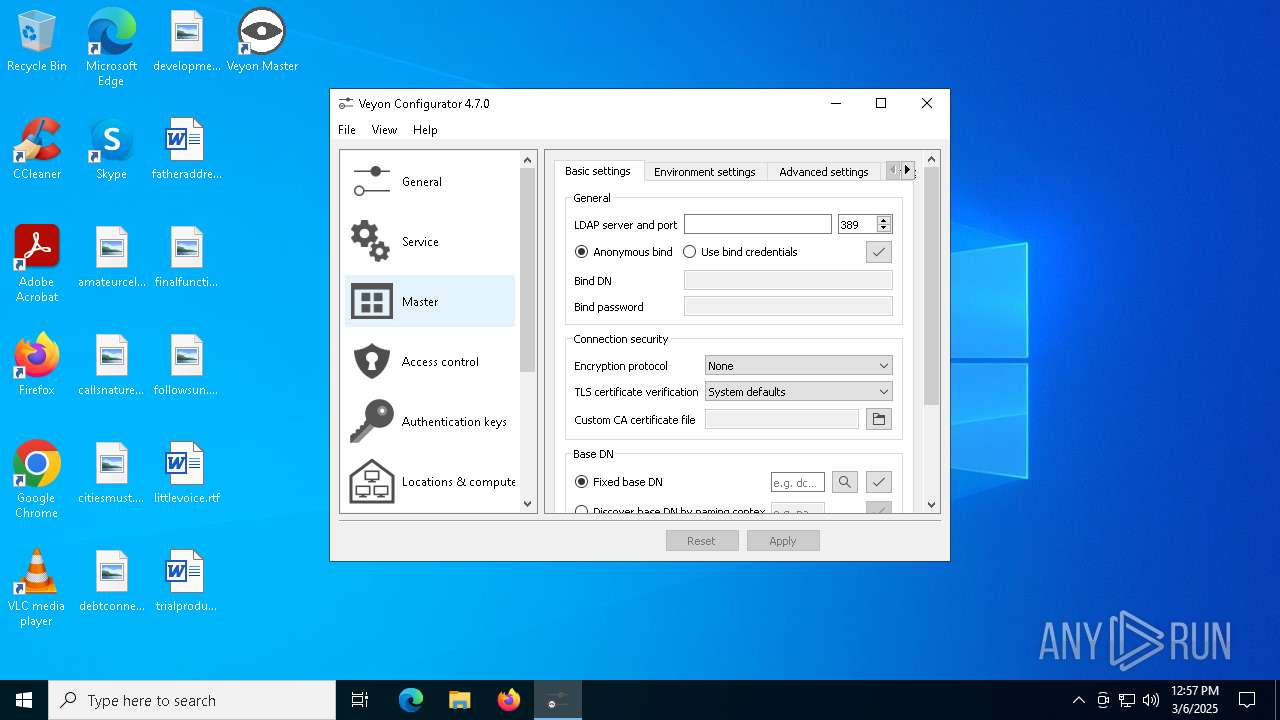
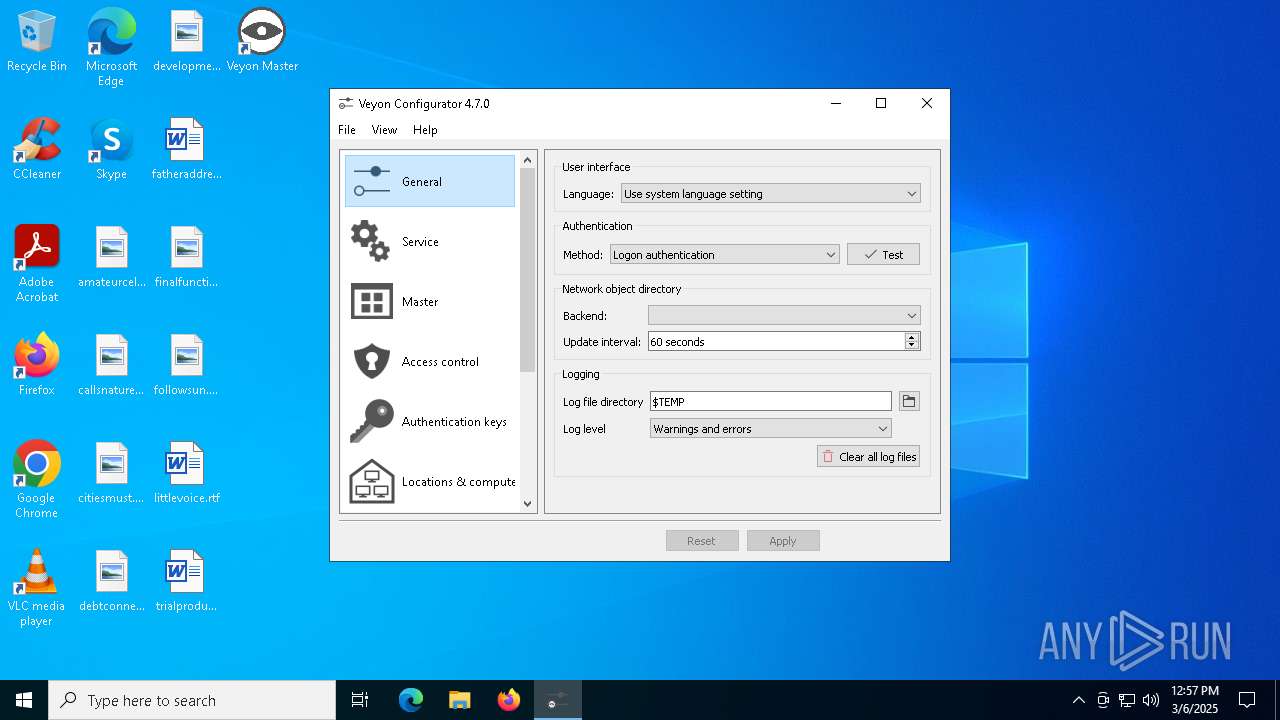
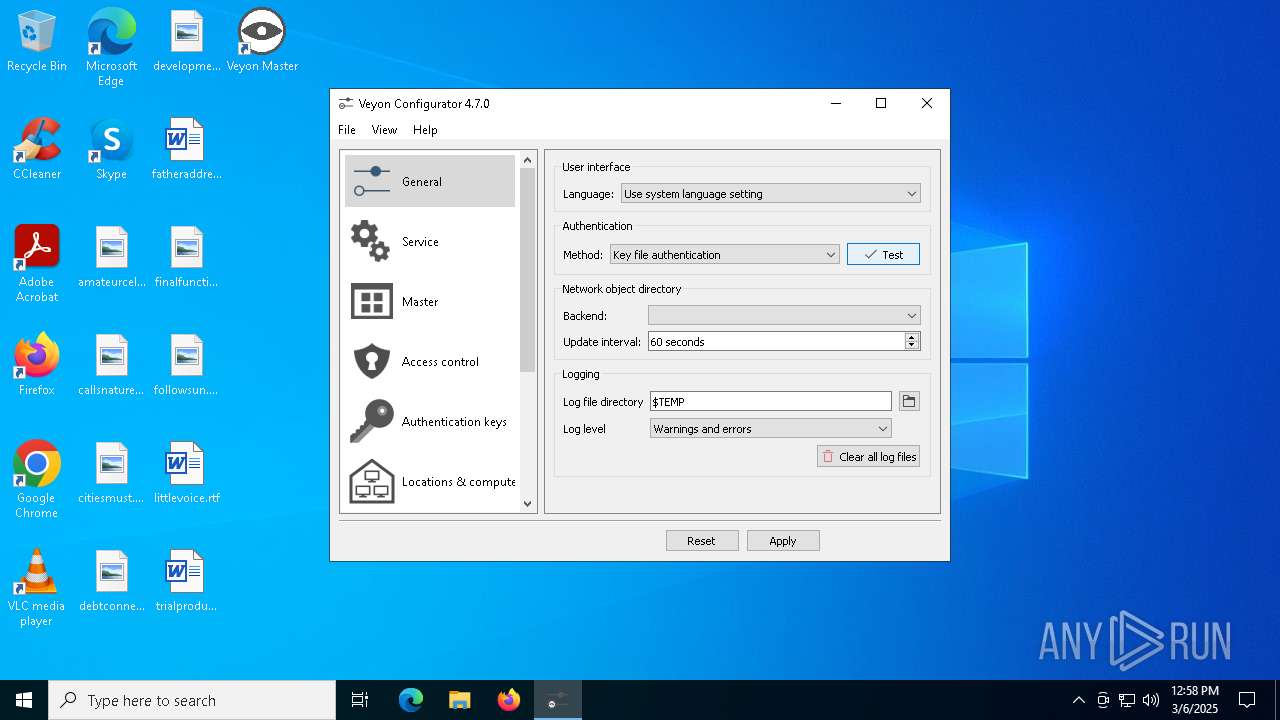
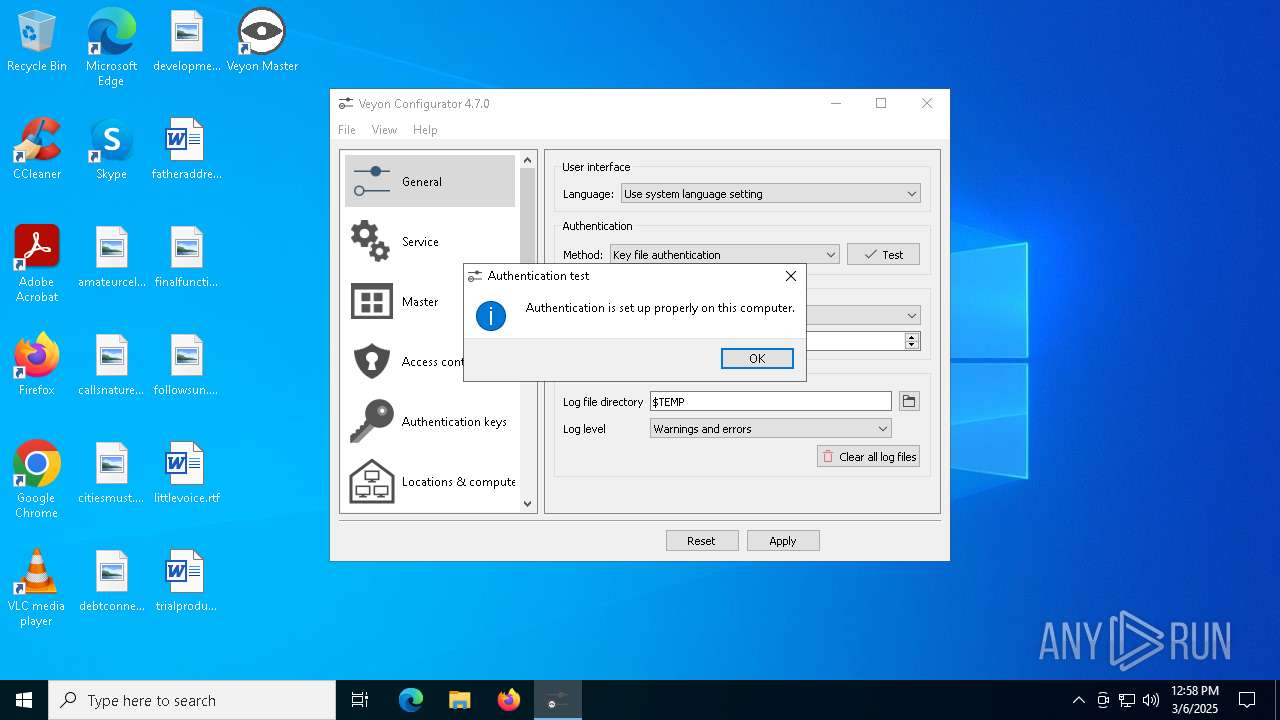
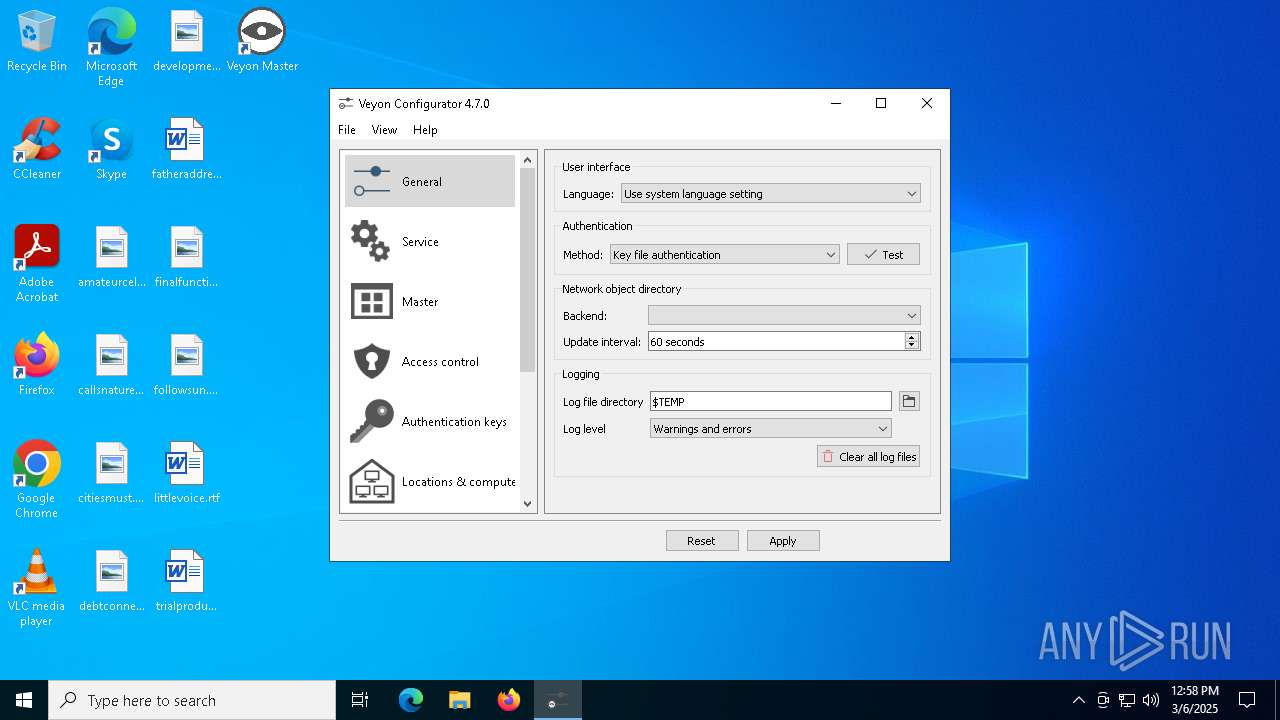
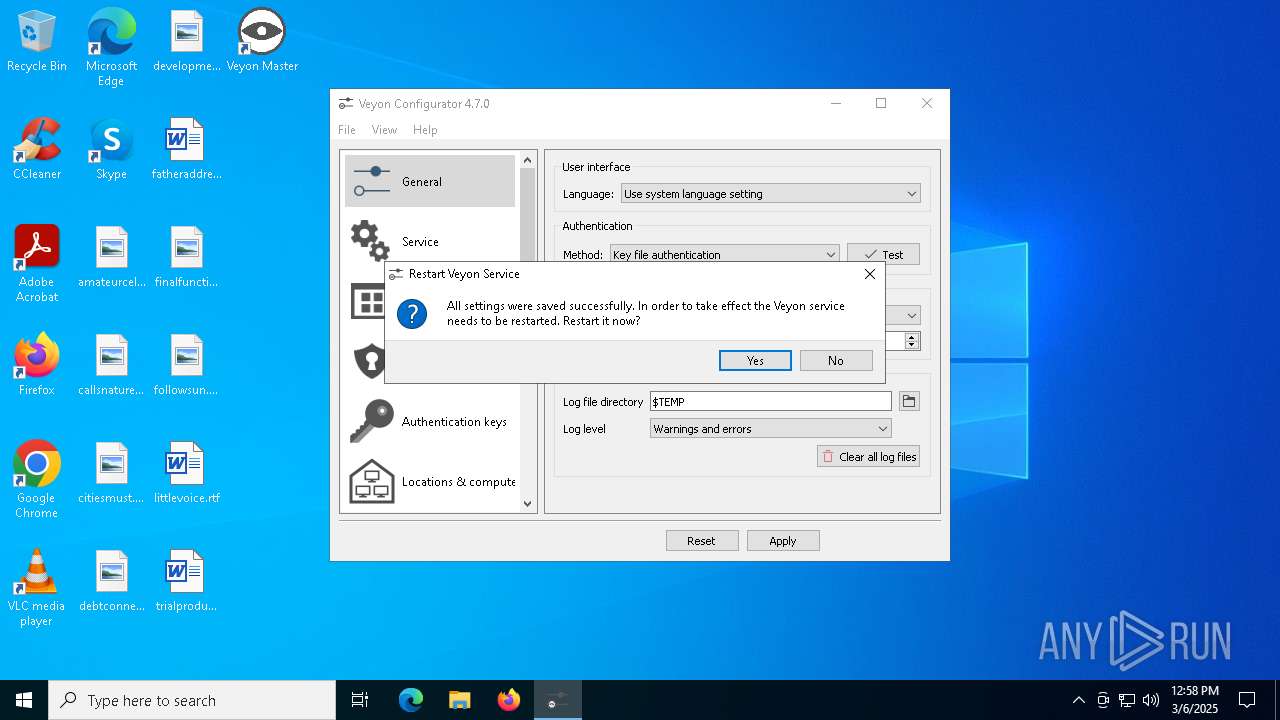
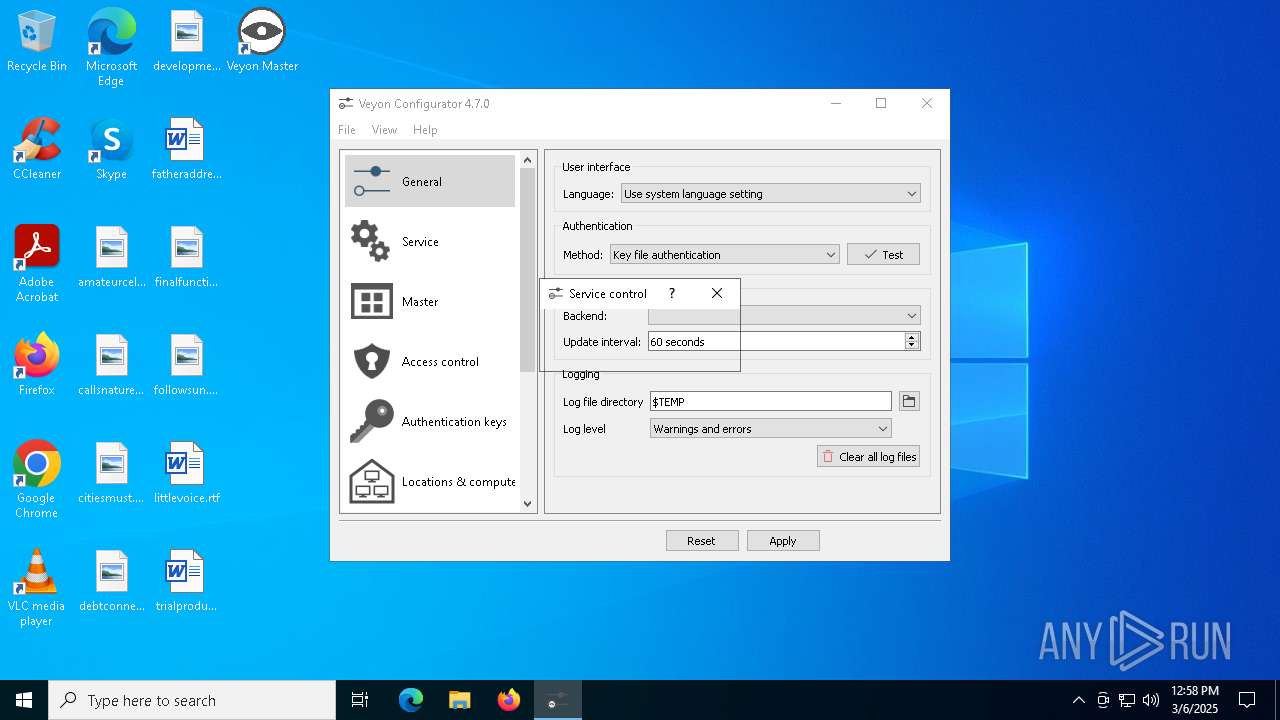
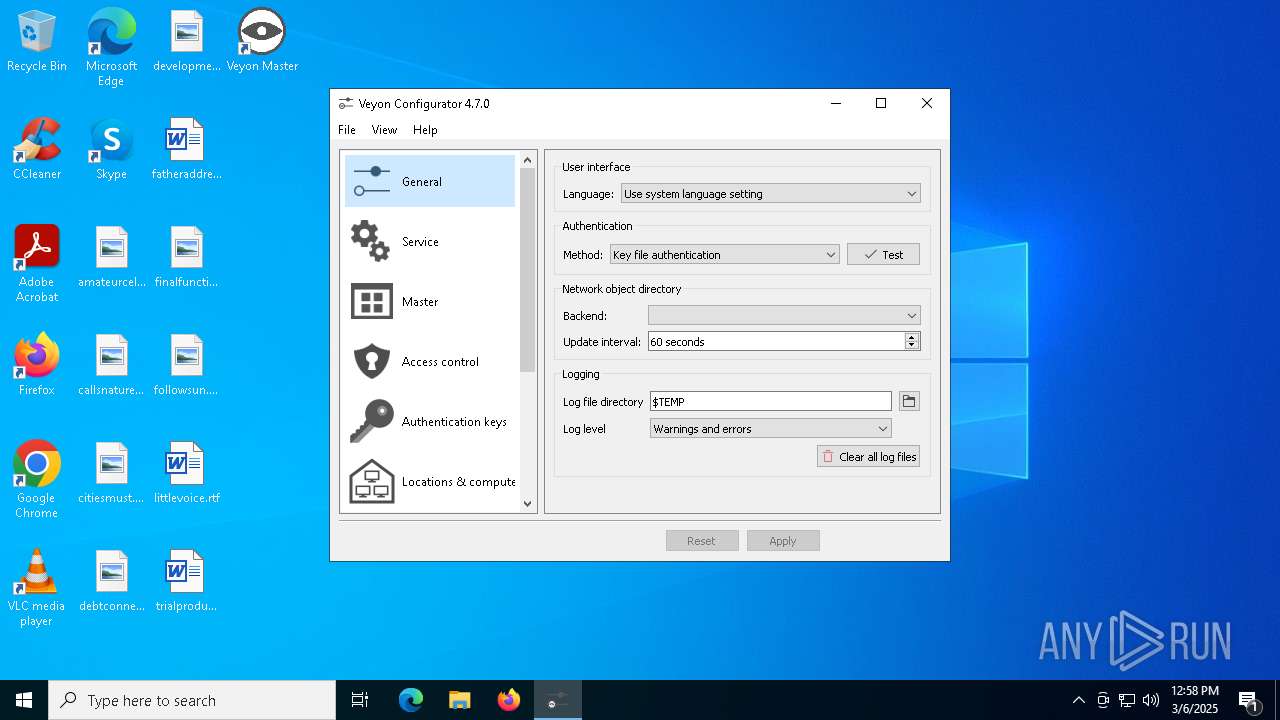
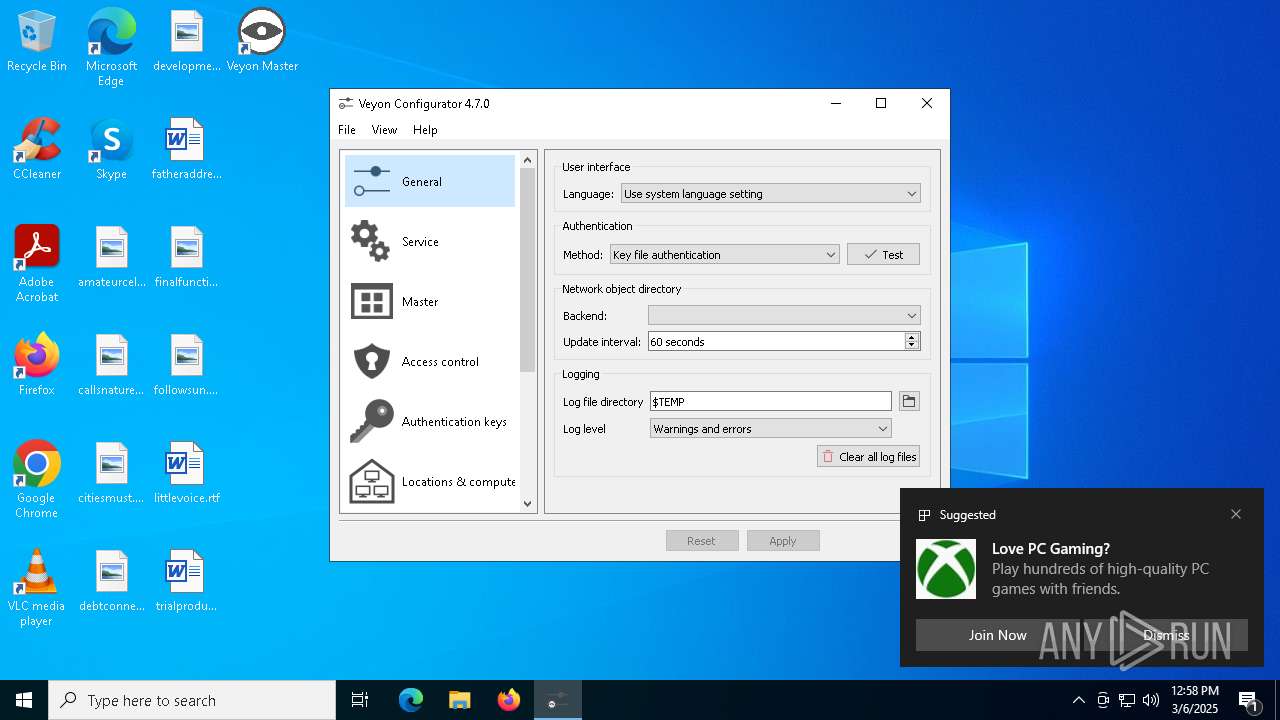
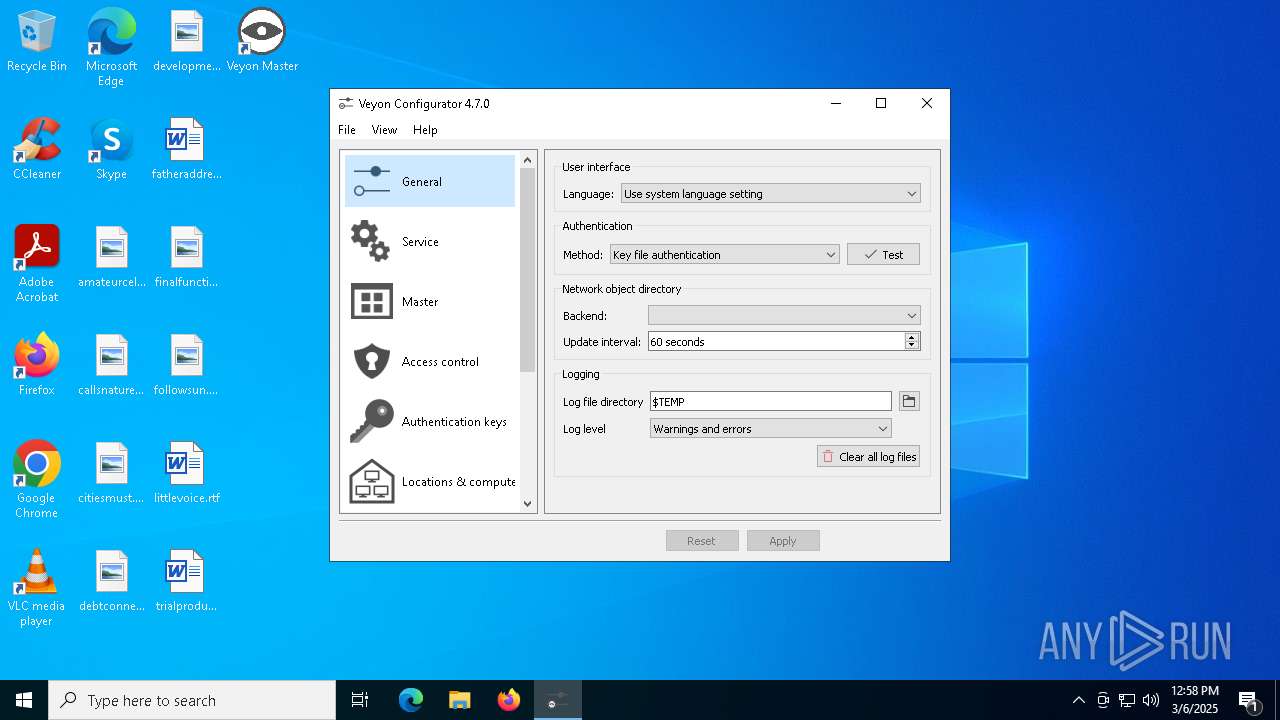
| 2772 | "C:\Program Files\Veyon\veyon-configurator.exe" | C:\Program Files\Veyon\veyon-configurator.exe | — | veyon-4.7.0.0-win64-setup.exe | |||||||||||
User: admin Company: Veyon Solutions Integrity Level: HIGH Description: Veyon Configurator Exit code: 0 Version: 4.7.0 Modules
| |||||||||||||||
| 4000 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4220 | "C:\Program Files\Veyon\veyon-worker.exe" {8e997d84-ebb9-430f-8f72-d45d9821963d} | C:\Program Files\Veyon\veyon-worker.exe | — | veyon-server.exe | |||||||||||
User: admin Company: Veyon Solutions Integrity Level: MEDIUM Description: Veyon Exit code: 0 Version: 4.7.0 Modules
| |||||||||||||||
| 5124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | install-interception.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5608 | "C:\Program Files\Veyon\interception\install-interception.exe" /install | C:\Program Files\Veyon\interception\install-interception.exe | veyon-service.exe | ||||||||||||
User: SYSTEM Company: Francisco Lopes Integrity Level: SYSTEM Description: Interception command line installation tool Exit code: 0 Version: 1.00 built by: WinDDK Modules
| |||||||||||||||
| 6540 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7224 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 851
Read events
9 731
Write events
111
Delete events
9
Modification events
| (PID) Process: | (8180) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8180) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8180) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1532) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1532) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1532) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6540) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
63
Suspicious files
79
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8180 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\cb989374-46ff-4249-9bad-e231e577c1e4.down_data | — | |
MD5:— | SHA256:— | |||
| 7980 | veyon-4.7.0.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsgD380.tmp\modern-header.bmp | binary | |
MD5:CA505EE1B37AE9EA906064497276B9D4 | SHA256:479E358E48AEAD66F293DA8556FD3E66D6B14BF94A8C1B5C778D6C8ED4B616B1 | |||
| 7980 | veyon-4.7.0.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsgD380.tmp\UserInfo.dll | executable | |
MD5:30B054C33C2EF209071FAA27C38C06A6 | SHA256:09BE55D6FAC9D5DC47F034FF8FBD9E60024AF68EFFD931C5D7AE57809370654C | |||
| 7980 | veyon-4.7.0.0-win64-setup.exe | C:\Program Files\Veyon\veyon-server.exe | executable | |
MD5:E35B7A0A0B91D44EC7F55E4C1C522BA4 | SHA256:7953CCF15100D4382ABD63838BDDBF8C1EDD5723ACFC7F91491CC5754C1FE68C | |||
| 7980 | veyon-4.7.0.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsgD380.tmp\nsDialogs.dll | executable | |
MD5:5198128986BE9C1CE35727F557A6A1E9 | SHA256:E81473FF4798CA50A951D183759671EEFB6597868C81890E3F67760D47B14004 | |||
| 7980 | veyon-4.7.0.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsgD380.tmp\modern-wizard.bmp | binary | |
MD5:A8D81A837E19534E2663FB02A1355BEA | SHA256:2BAD887CD8FA8206FED401C3B1CDEE18AC9A65CFC9F982A95577791226836660 | |||
| 7980 | veyon-4.7.0.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsgD380.tmp\System.dll | executable | |
MD5:825B584EA5FCB8F9173539EA0421CB65 | SHA256:21B23E46F2737B89200F90A2A783289F37D6B713161243677419849B2BCEEC66 | |||
| 8180 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:CBDC9B9481DAF706E1E4BFC11B34A167 | SHA256:8928AAE7656C6AA8365EE8945792B22A92C46528EB3D11B81BE45202C01A5952 | |||
| 8180 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:38989CDC9B939CBF439472EC8FEBE5D7 | SHA256:0188CCDAB61284075618619F99DBB9FC9BA066DF5B1FF02EC5684476CABA0732 | |||
| 8180 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\cb989374-46ff-4249-9bad-e231e577c1e4.8be7b4de-0ec8-47d8-8273-18d2bca7b276.down_meta | binary | |
MD5:A6E3FE4490BA9A51FB4BA857F7DEBBD8 | SHA256:F8848745158E2A9386DAE1F79A95254BD415830EC2CD61E02A209527CD9C1F14 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
30
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
732 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8180 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6752 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6752 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
732 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
732 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
8180 | BackgroundTransferHost.exe | 104.126.37.184:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
8180 | BackgroundTransferHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |