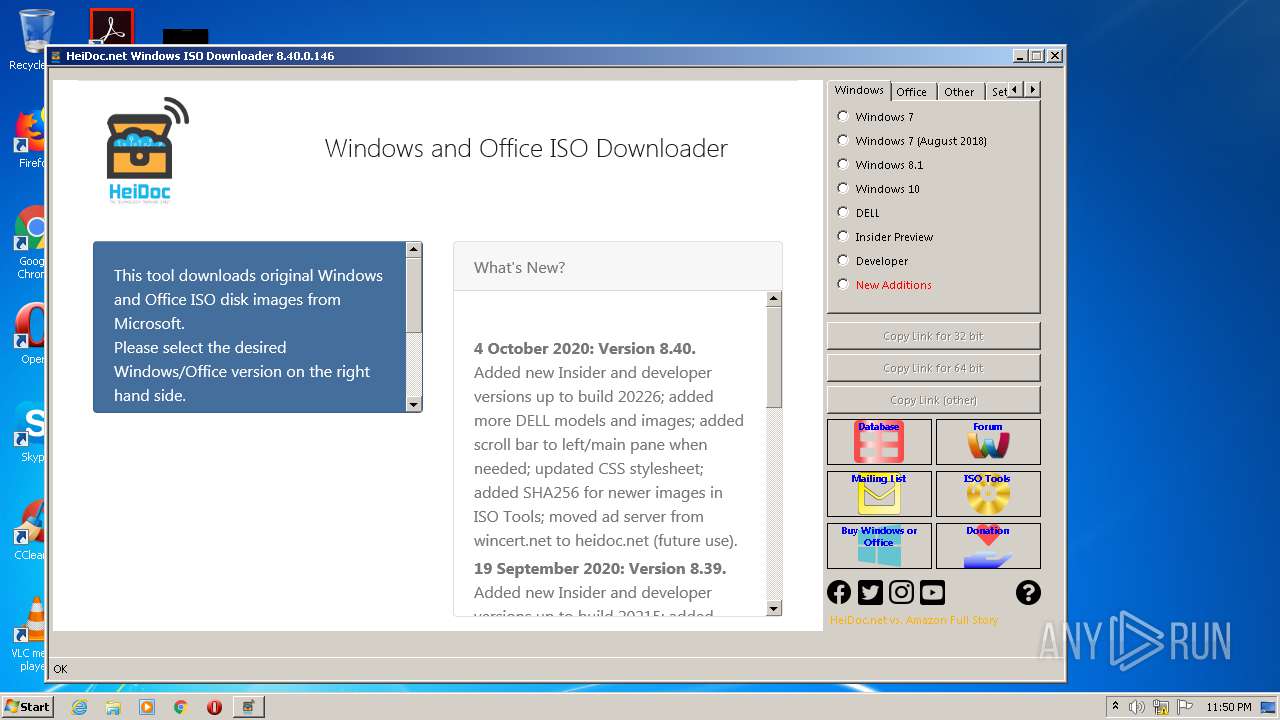
| File name: | Windows-ISO-Downloader (1).exe |
| Full analysis: | https://app.any.run/tasks/2c813825-3d7c-4a3d-ace2-817bb1da771e |
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2020, 22:49:52 |
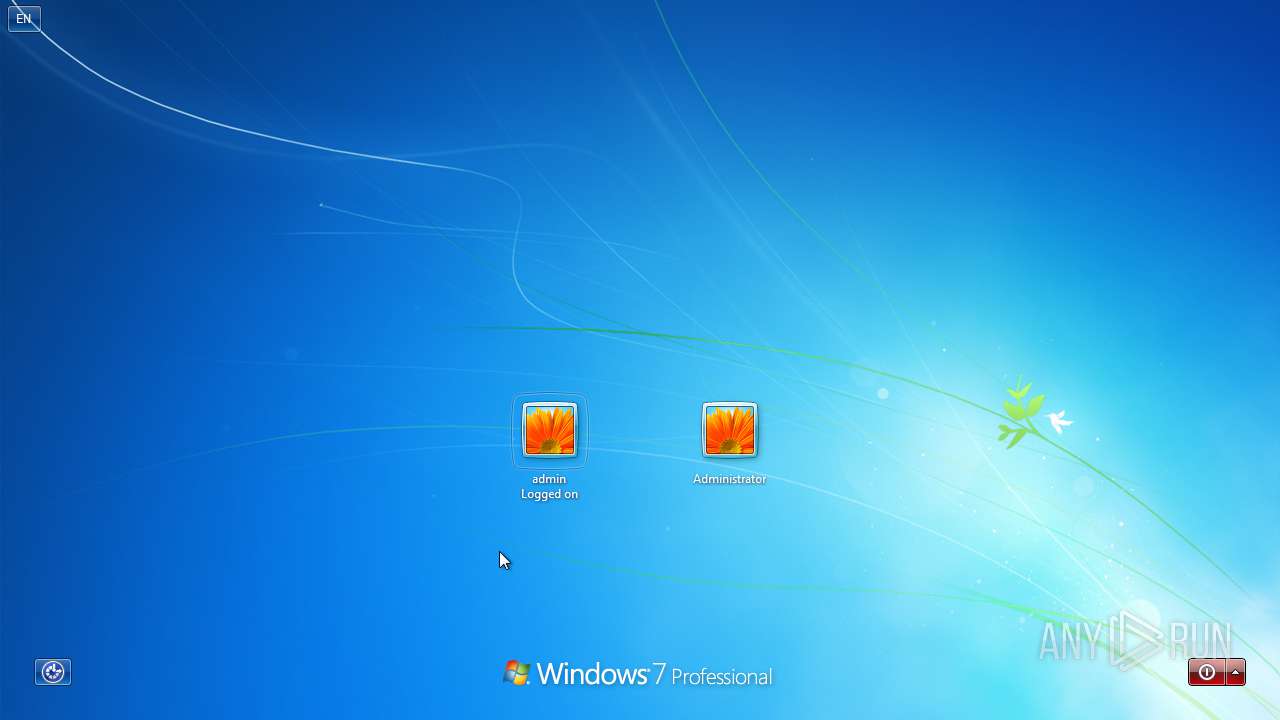
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | ED2B868ED28C16F7F8415678DAC194DD |
| SHA1: | 5B5A0186B79FF5BC564F26E08382D1F3101E37E0 |
| SHA256: | A0B3DEBF9585D1B5E2D233B7449F54CE8D350F6A7AC9016A329CE27B69FC9D38 |
| SSDEEP: | 98304:UI68IzIRIRILg/cFLWoDy9G32dm/RUFVHB/mQJPfb:m5/yWoDy9GGOIlBewr |
MALICIOUS
Changes internet zones settings
- ie4uinit.exe (PID: 2800)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2748)
Changes settings of System certificates
- Windows-ISO-Downloader (1).exe (PID: 3404)
SUSPICIOUS
Reads internet explorer settings
- Windows-ISO-Downloader (1).exe (PID: 3404)
Application launched itself
- ie4uinit.exe (PID: 2800)
- rundll32.exe (PID: 2748)
- chrmstp.exe (PID: 4056)
Reads Internet Cache Settings
- Windows-ISO-Downloader (1).exe (PID: 3404)
- taskhost.exe (PID: 2476)
Creates files in the user directory
- Windows-ISO-Downloader (1).exe (PID: 3404)
Executed as Windows Service
- taskhost.exe (PID: 2476)
Adds / modifies Windows certificates
- Windows-ISO-Downloader (1).exe (PID: 3404)
Creates files in the program directory
- ie4uinit.exe (PID: 2800)
- chrmstp.exe (PID: 4056)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 2800)
- rundll32.exe (PID: 2748)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 2800)
INFO
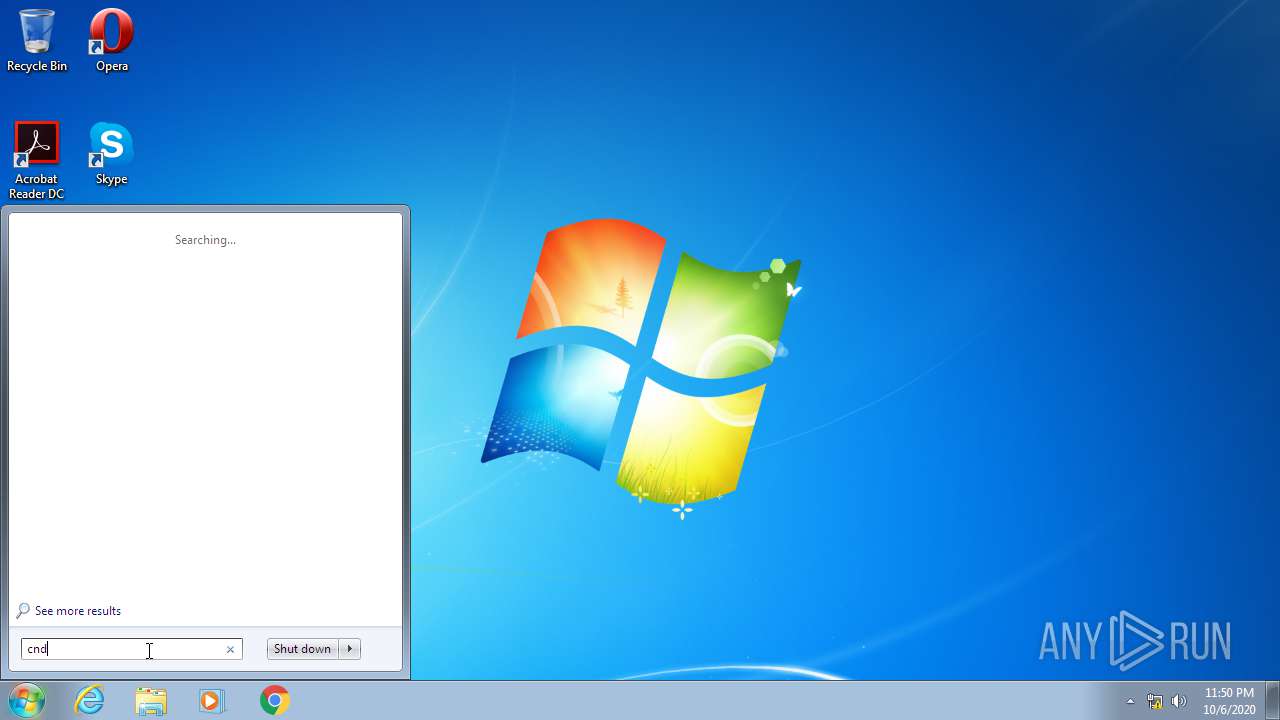
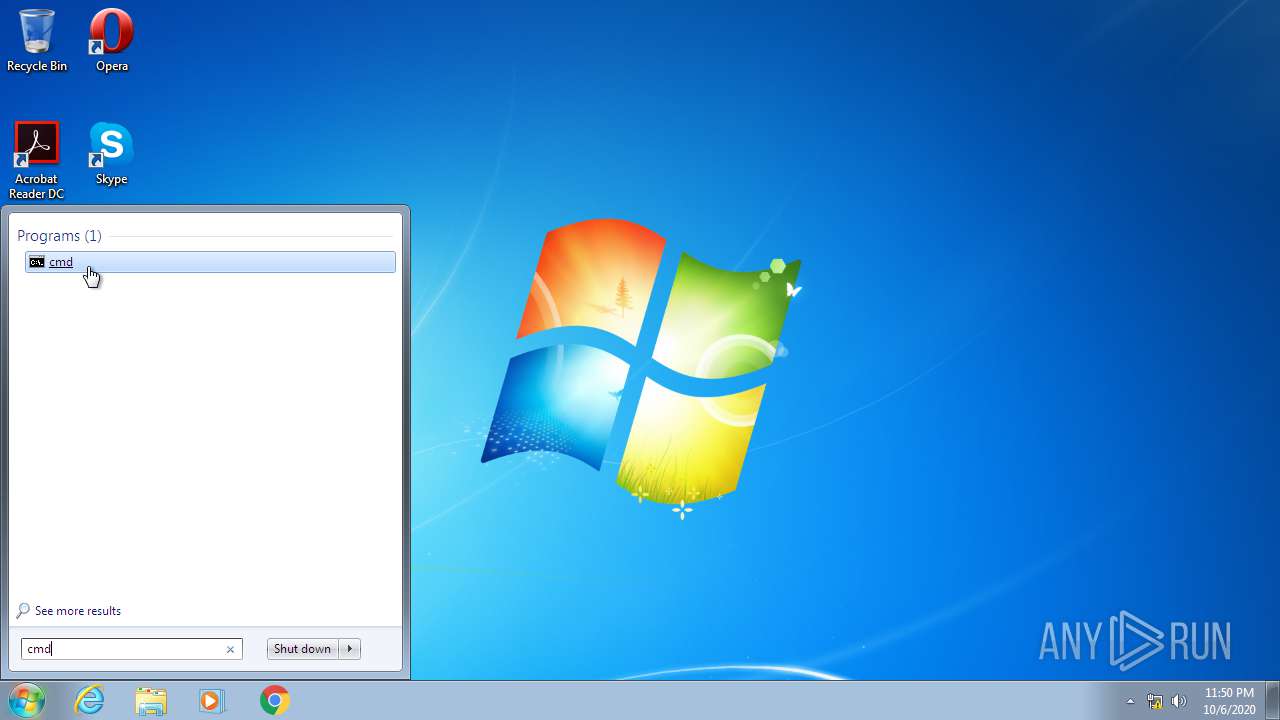
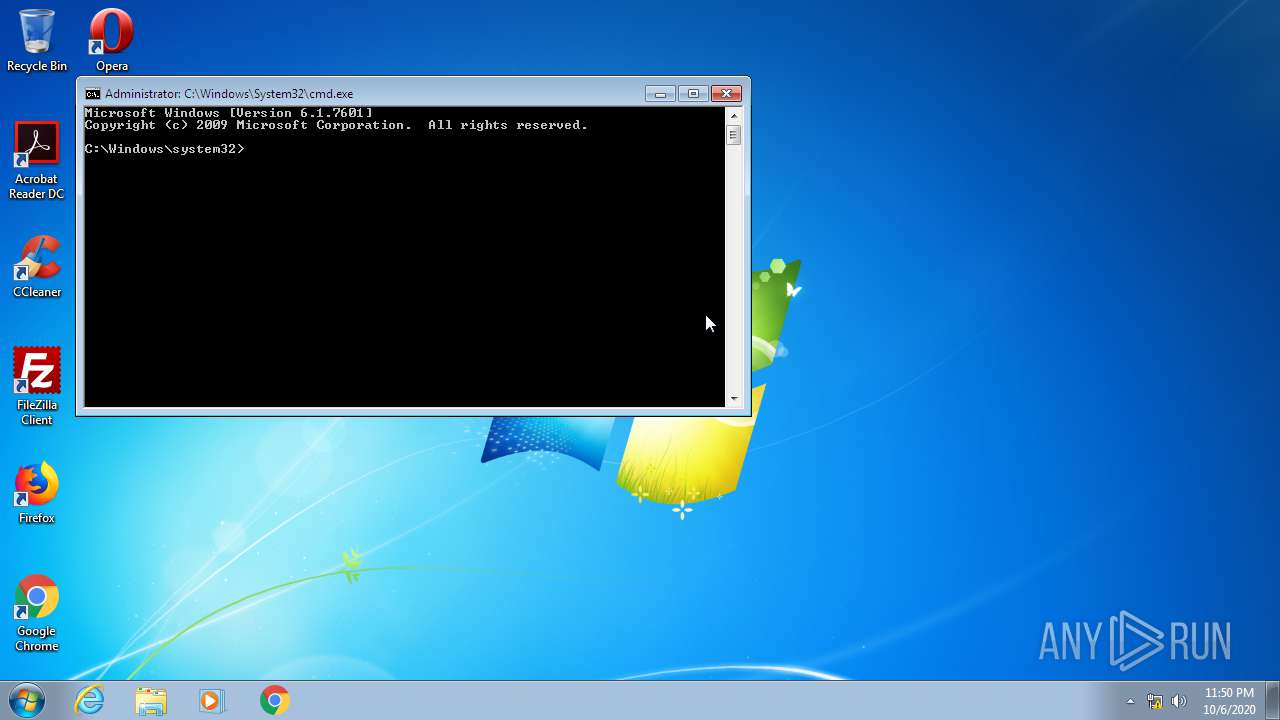
Manual execution by user
- ie4uinit.exe (PID: 2800)
- ie4uinit.exe (PID: 2312)
- chrmstp.exe (PID: 4056)
- cmd.exe (PID: 3388)
- verclsid.exe (PID: 1288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:10:04 02:36:48+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 6288896 |
| InitializedDataSize: | 308736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x601516 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
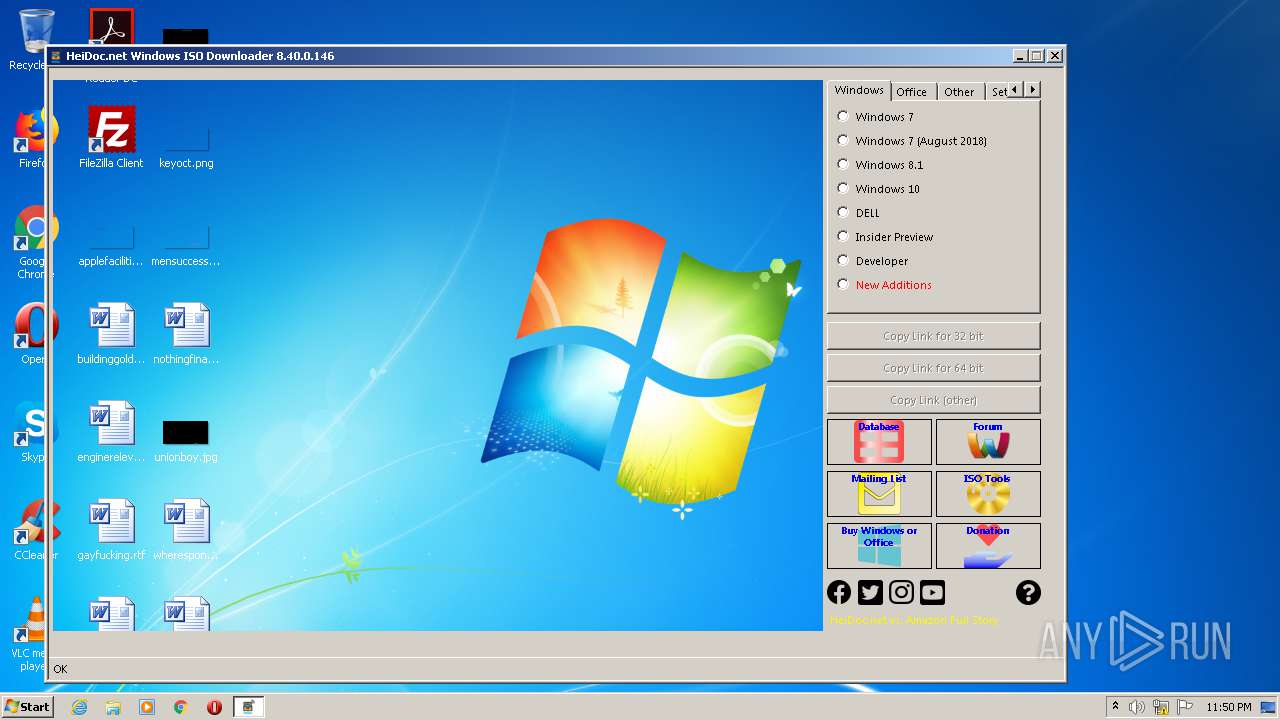
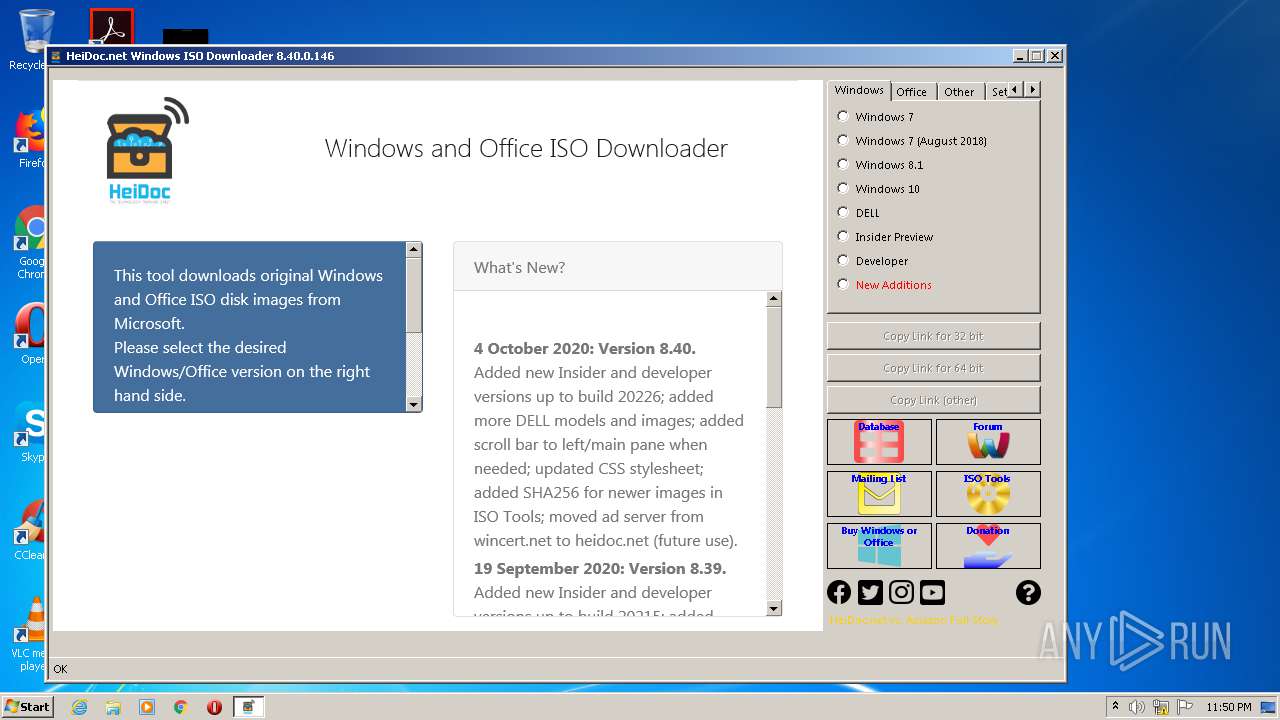
| FileVersionNumber: | 8.40.0.146 |
| ProductVersionNumber: | 8.40.0.146 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | HeiDoc V.O.F. |
| FileDescription: | Windows ISO Downloader |
| FileVersion: | 8.40.0.0146 |
| InternalName: | Windows-ISO-Downloader.exe |
| LegalCopyright: | Copyright © 2016-2020 |
| LegalTrademarks: | - |
| OriginalFileName: | Windows-ISO-Downloader.exe |
| ProductName: | Windows ISO Downloader |
| ProductVersion: | 8.40.0.0146 |
| AssemblyVersion: | 8.40.0.146 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Oct-2020 00:36:48 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | HeiDoc V.O.F. |
| FileDescription: | Windows ISO Downloader |
| FileVersion: | 8.40.0.0146 |
| InternalName: | Windows-ISO-Downloader.exe |
| LegalCopyright: | Copyright © 2016-2020 |
| LegalTrademarks: | - |
| OriginalFilename: | Windows-ISO-Downloader.exe |
| ProductName: | Windows ISO Downloader |
| ProductVersion: | 8.40.0.0146 |
| Assembly Version: | 8.40.0.146 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Oct-2020 00:36:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x005FF51C | 0x005FF600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.87879 |
.rsrc | 0x00602000 | 0x0004B3DC | 0x0004B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.42962 |
.reloc | 0x0064E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.42537 | 962 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 4.66927 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.31647 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.81771 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.50631 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.15714 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.02373 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.78483 | 152104 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 7.95518 | 14279 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 3.07075 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
64
Monitored processes
15
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
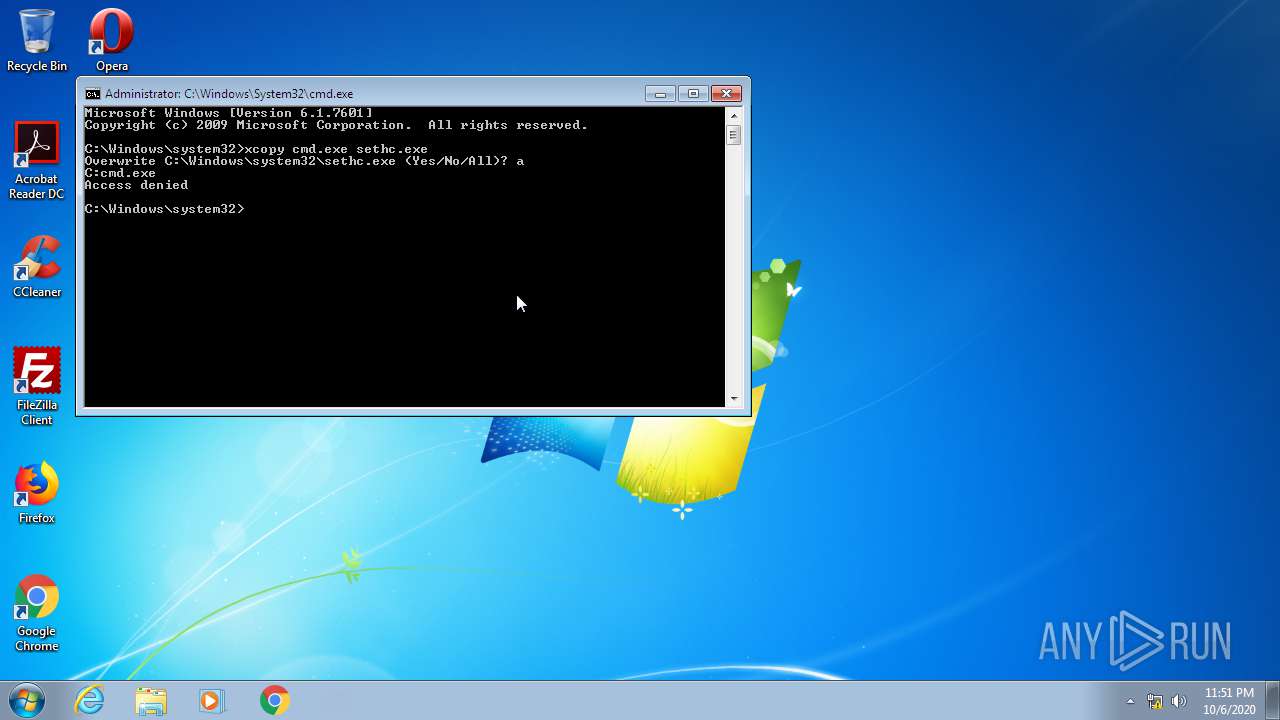
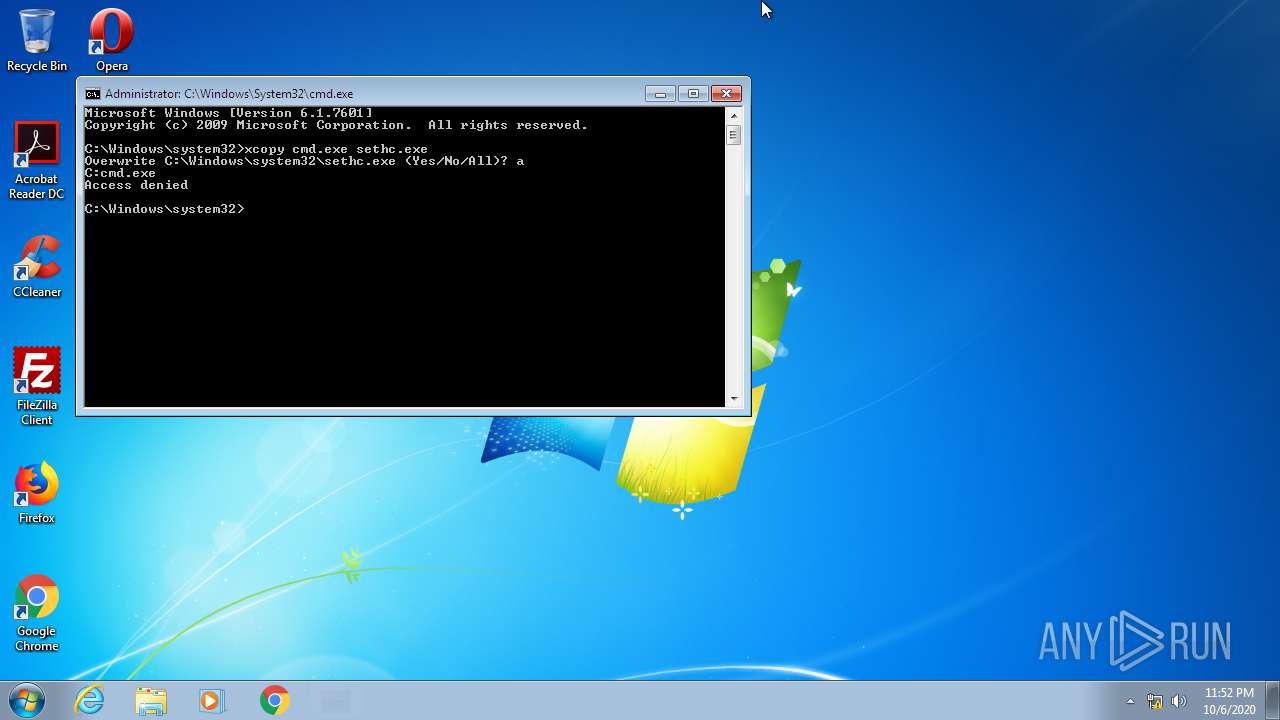
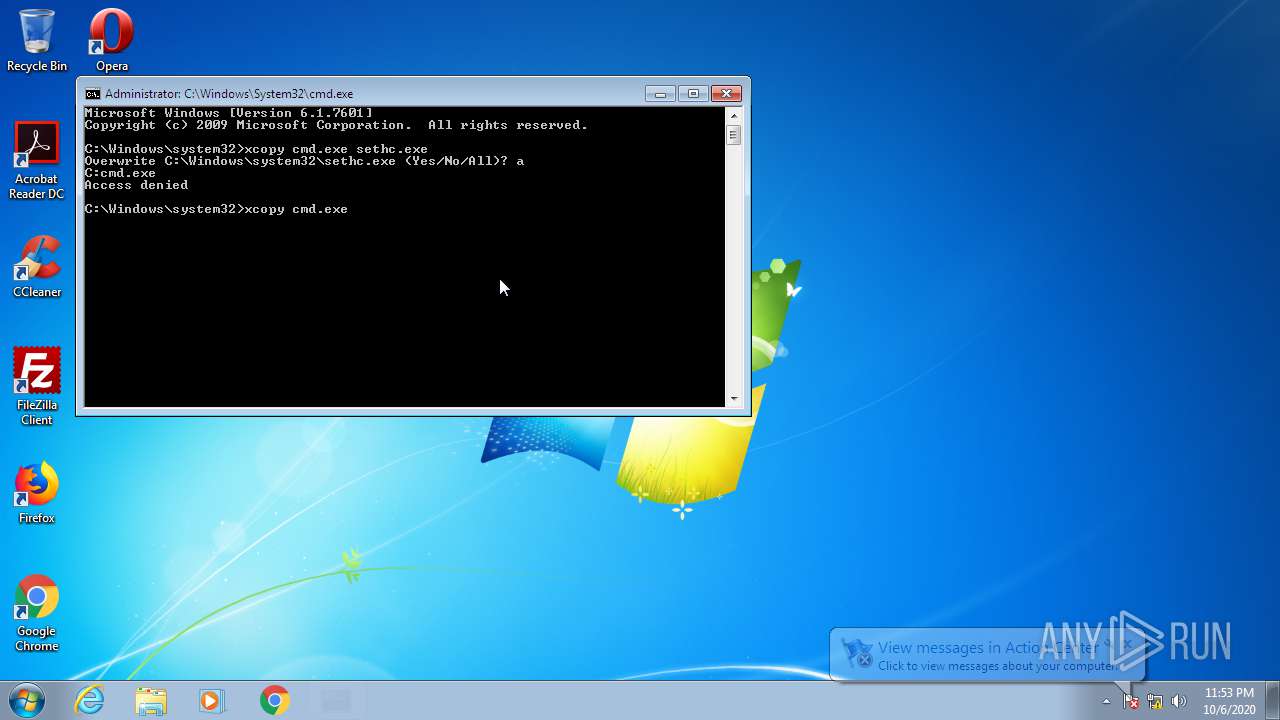
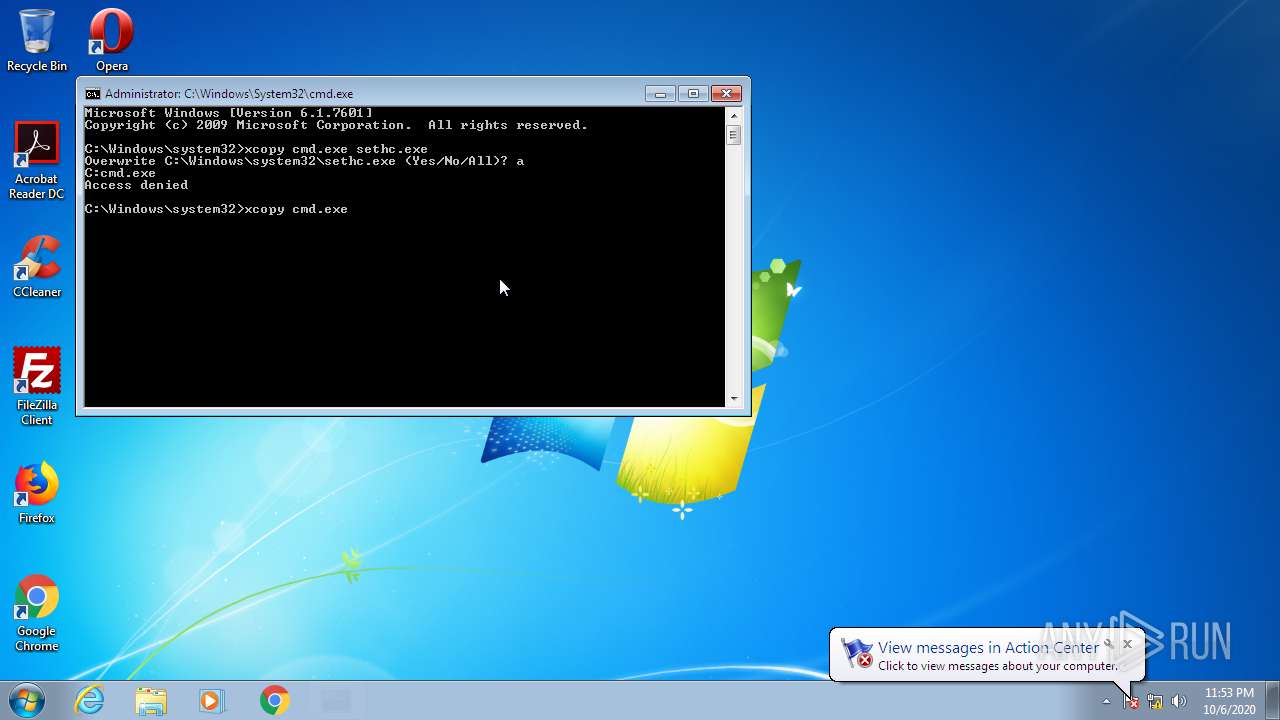
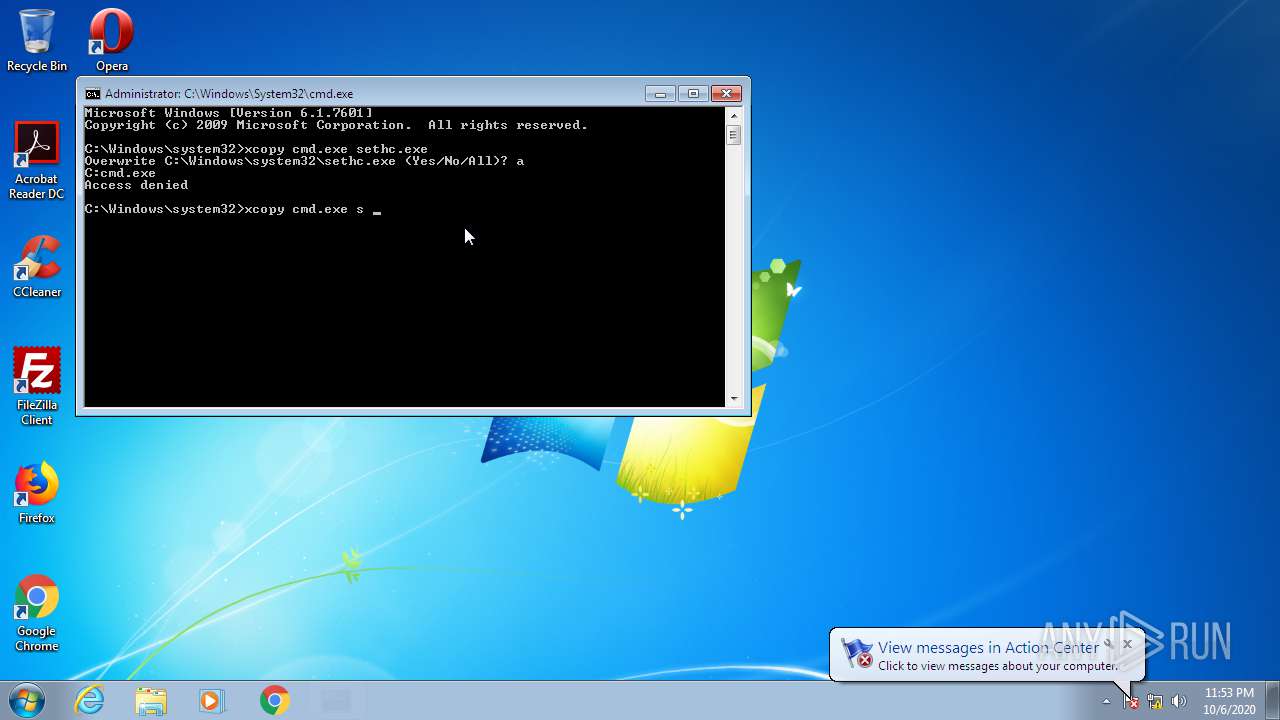
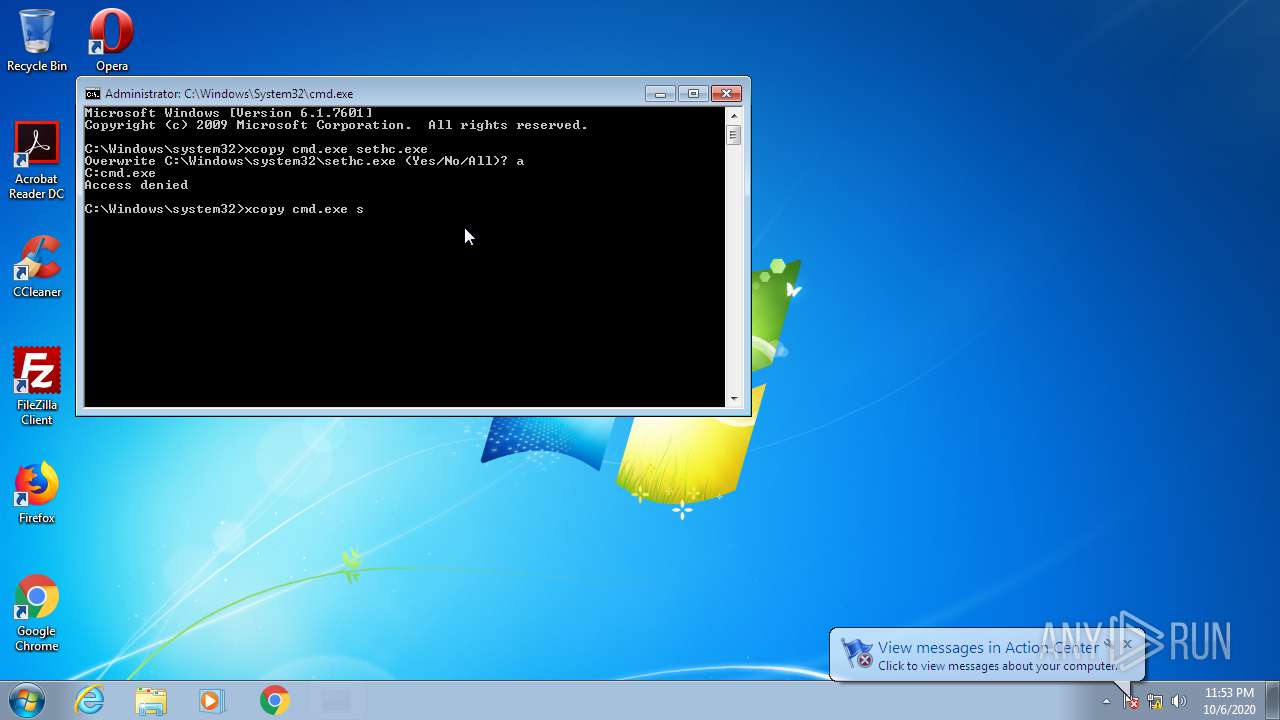
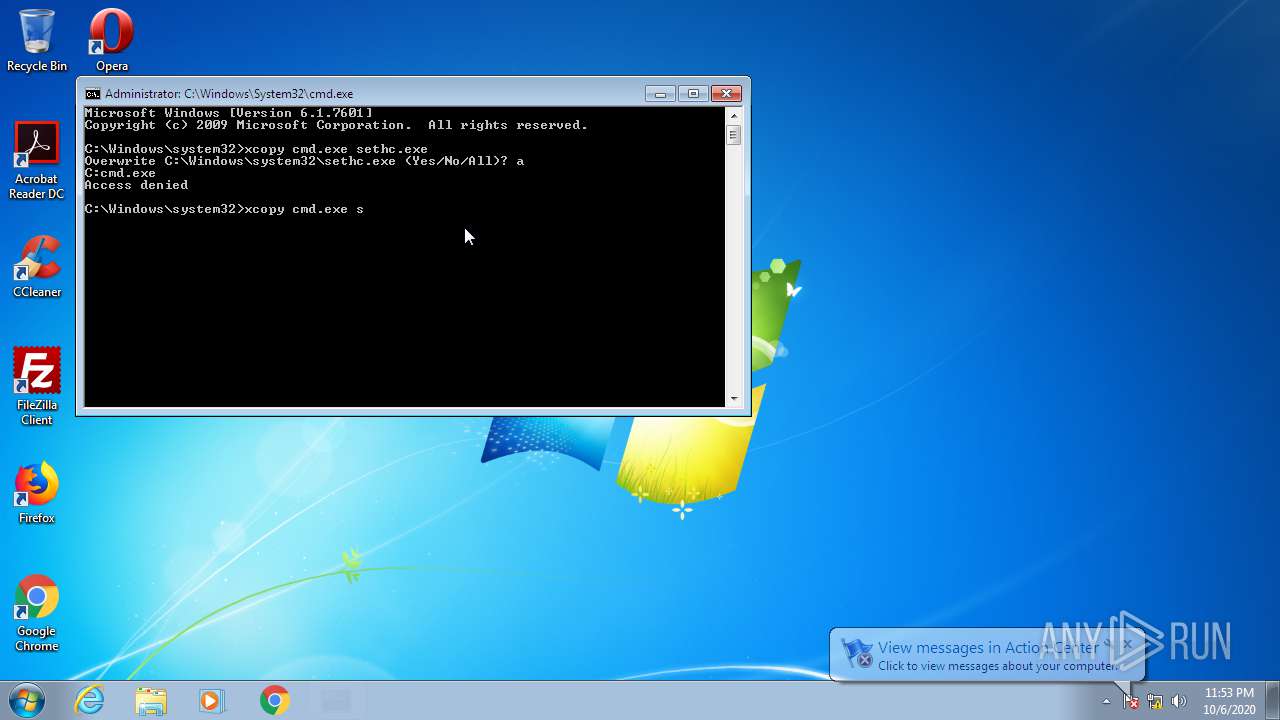
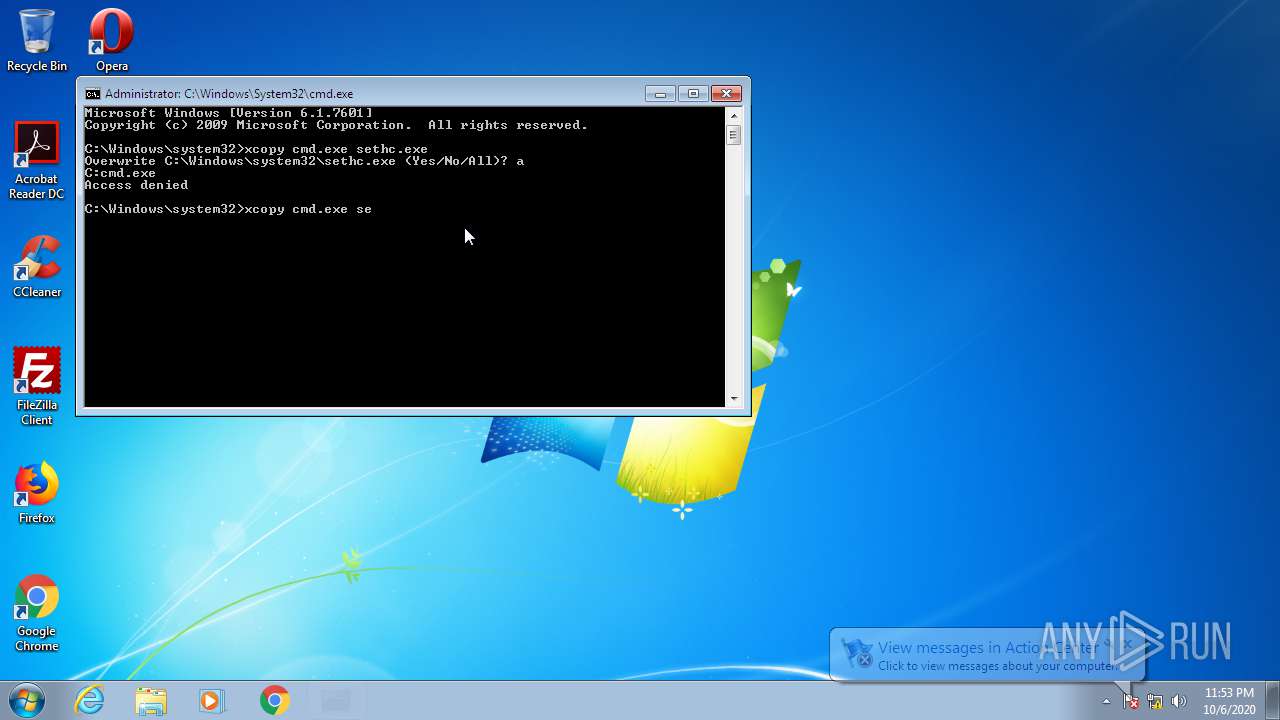
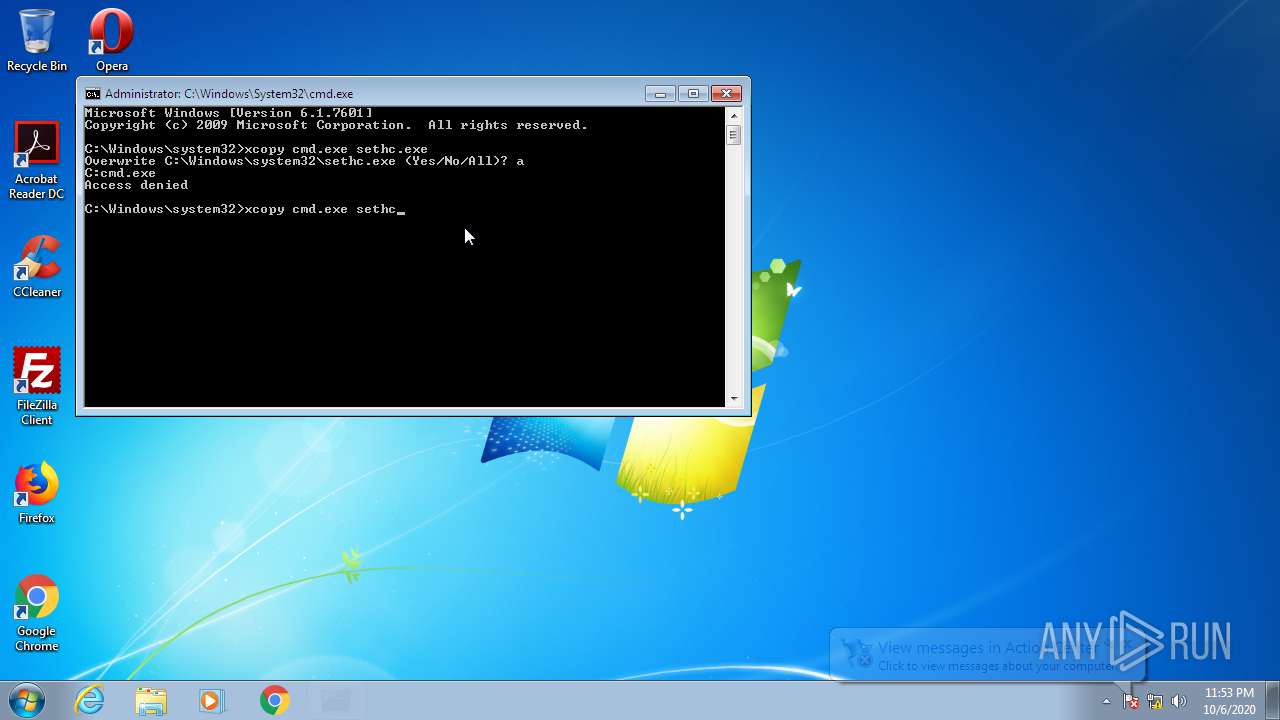
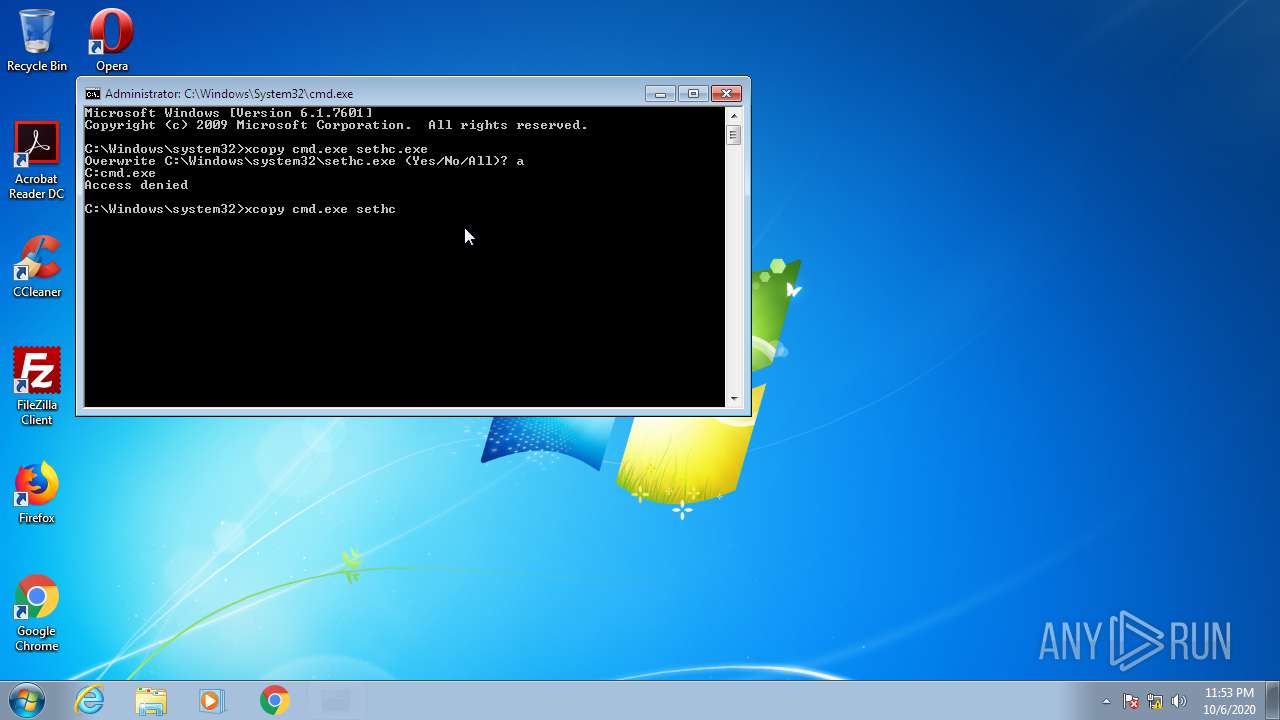
| 632 | xcopy cmd.exe sethc.exe | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1288 | "C:\Windows\system32\verclsid.exe" /S /C {9E175B8B-F52A-11D8-B9A5-505054503030} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1524 | C:\Windows\System32\rundll32 advpack.dll,LaunchINFSectionEx C:\Windows\system32\ieuinit.inf,Install,,36 | C:\Windows\System32\rundll32.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | "C:\Windows\System32\ie4uinit.exe" -DisableSSL3 | C:\Windows\System32\ie4uinit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2476 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | C:\Windows\System32\rundll32 C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m | C:\Windows\System32\rundll32.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | "C:\Windows\System32\ie4uinit.exe" -UserConfig | C:\Windows\System32\ie4uinit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2884 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\system32\RunDll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\system32\RunDll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3208 | xcopy cmd.exe sethc.exe | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
844
Read events
469
Write events
368
Delete events
7
Modification events
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3404) Windows-ISO-Downloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Windows-ISO-Downloader (1)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
22
Text files
84
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\Local\Temp\Cab6343.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\Local\Temp\Tar6344.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\KJGK6NZQ.txt | — | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\www-player-vflRjH--Z[1].css | — | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\css2[1].css | text | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_B692386BB395D0D1B54DEE15DF22E03C | binary | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_B692386BB395D0D1B54DEE15DF22E03C | der | |
MD5:— | SHA256:— | |||
| 3404 | Windows-ISO-Downloader (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_93BB5A29A73AA40D558BAE7D8E0C12DD | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
12
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | Windows-ISO-Downloader (1).exe | 104.168.147.90:443 | www.heidoc.net | Hostwinds LLC. | US | unknown |
3404 | Windows-ISO-Downloader (1).exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 172.217.23.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 216.58.212.142:443 | s.ytimg.com | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 172.217.21.193:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 216.58.208.38:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 216.58.205.246:443 | i.ytimg.com | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 216.58.212.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3404 | Windows-ISO-Downloader (1).exe | 172.217.18.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.heidoc.net |
| whitelisted |
aa.online-metrix.net |
| whitelisted |
c.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.youtube.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
static.doubleclick.net |
| whitelisted |