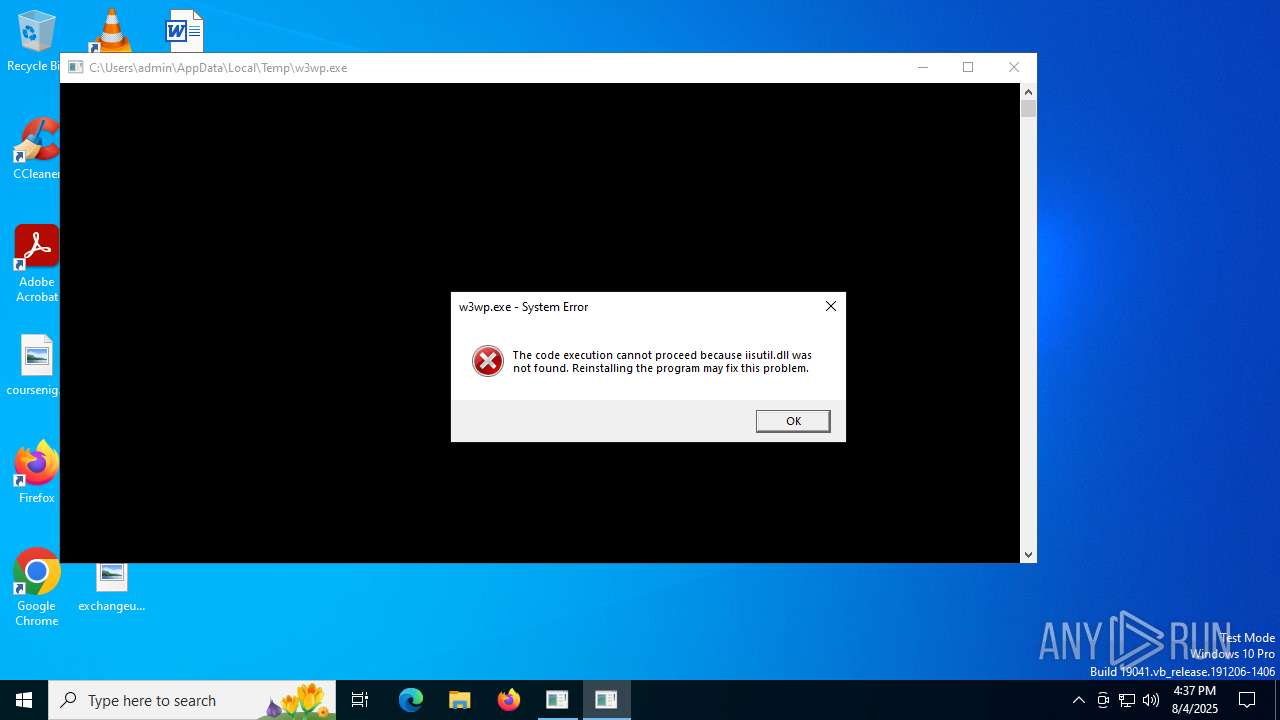
| File name: | w3wp.exe |
| Full analysis: | https://app.any.run/tasks/9cb176b6-60ec-4c10-b839-b9226556f486 |
| Verdict: | Malicious activity |
| Analysis date: | August 04, 2025, 16:37:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | AB6D6849B3B8B8F4A292DC76EBB1243F |
| SHA1: | 54443C275EDDD9BBE75C6D47CF9C24076B5D785C |
| SHA256: | A0A37FDE4D8CD7385E819AFA967BC525231C2F166C38591532D8FEEAB94E40DA |
| SSDEEP: | 768:Eyd3v7/u7ODmptgXvbw8DzAZfQnNUMkkzO:Eyd3v7m7OkgfJAZfQNUMDzO |
MALICIOUS
Changes the autorun value in the registry
- CCleaner64.exe (PID: 828)
SUSPICIOUS
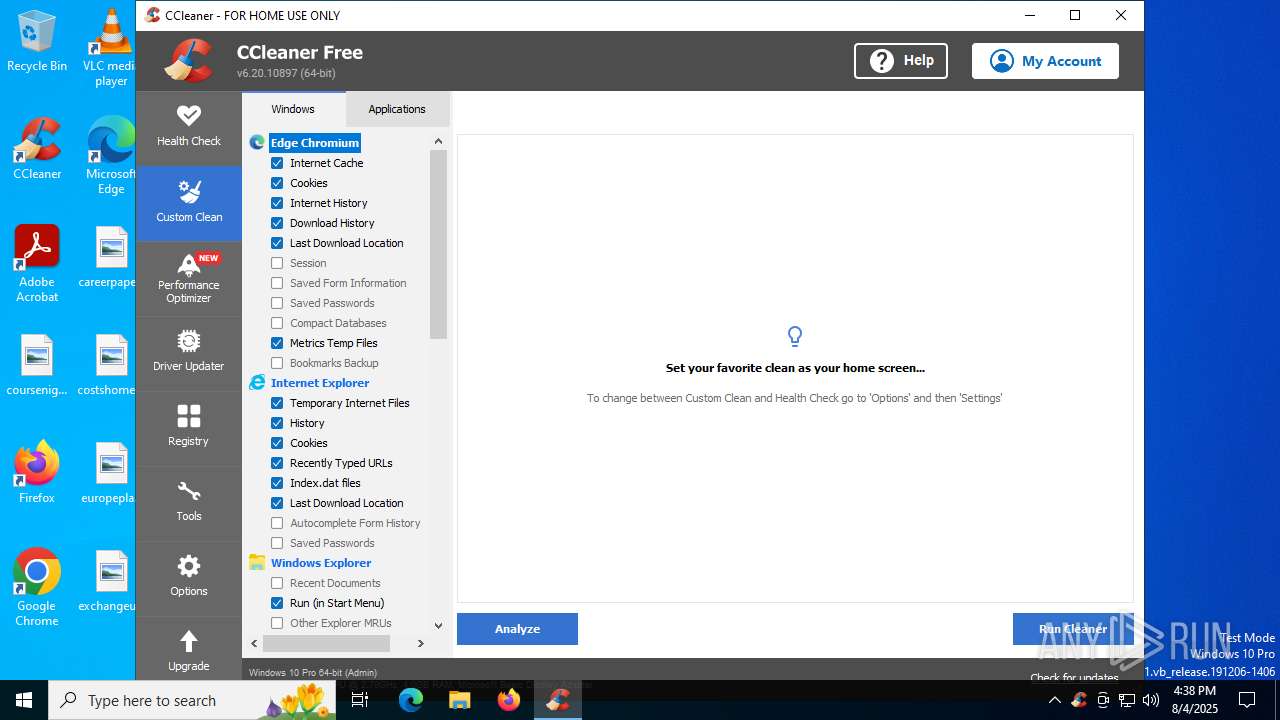
Reads security settings of Internet Explorer
- CCleaner64.exe (PID: 4400)
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Process drops legitimate windows executable
- w3wp.exe (PID: 3580)
Reads the date of Windows installation
- CCleaner64.exe (PID: 4400)
- CCleaner64.exe (PID: 2428)
Application launched itself
- CCleaner64.exe (PID: 4400)
- CCleaner64.exe (PID: 2428)
Starts a Microsoft application from unusual location
- w3wp.exe (PID: 3580)
Reads Internet Explorer settings
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Executable content was dropped or overwritten
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Searches for installed software
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
The process verifies whether the antivirus software is installed
- CCleaner64.exe (PID: 828)
- CCleaner64.exe (PID: 2428)
Checks for external IP
- CCleaner64.exe (PID: 2428)
INFO
Manual execution by a user
- CCleaner64.exe (PID: 4400)
Reads Environment values
- CCleaner64.exe (PID: 4400)
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Process checks computer location settings
- CCleaner64.exe (PID: 4400)
- CCleaner64.exe (PID: 2428)
Reads the computer name
- CCleaner64.exe (PID: 4400)
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Checks supported languages
- CCleaner64.exe (PID: 4400)
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Reads CPU info
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Reads the machine GUID from the registry
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Reads product name
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Creates files in the program directory
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
The sample compiled with english language support
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Reads the software policy settings
- CCleaner64.exe (PID: 2428)
- CCleaner64.exe (PID: 828)
Checks proxy server information
- CCleaner64.exe (PID: 2428)
Creates files or folders in the user directory
- CCleaner64.exe (PID: 2428)
Launching a file from a Registry key
- CCleaner64.exe (PID: 828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2016:07:16 02:27:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 9728 |
| InitializedDataSize: | 15360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e50 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.14393.0 |
| ProductVersionNumber: | 10.0.14393.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | IIS Worker Process |
| FileVersion: | 10.0.14393.0 (rs1_release.160715-1616) |
| InternalName: | w3wp.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | w3wp.exe |
| ProductName: | Internet Information Services |
| ProductVersion: | 10.0.14393.0 |
Total processes
141
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
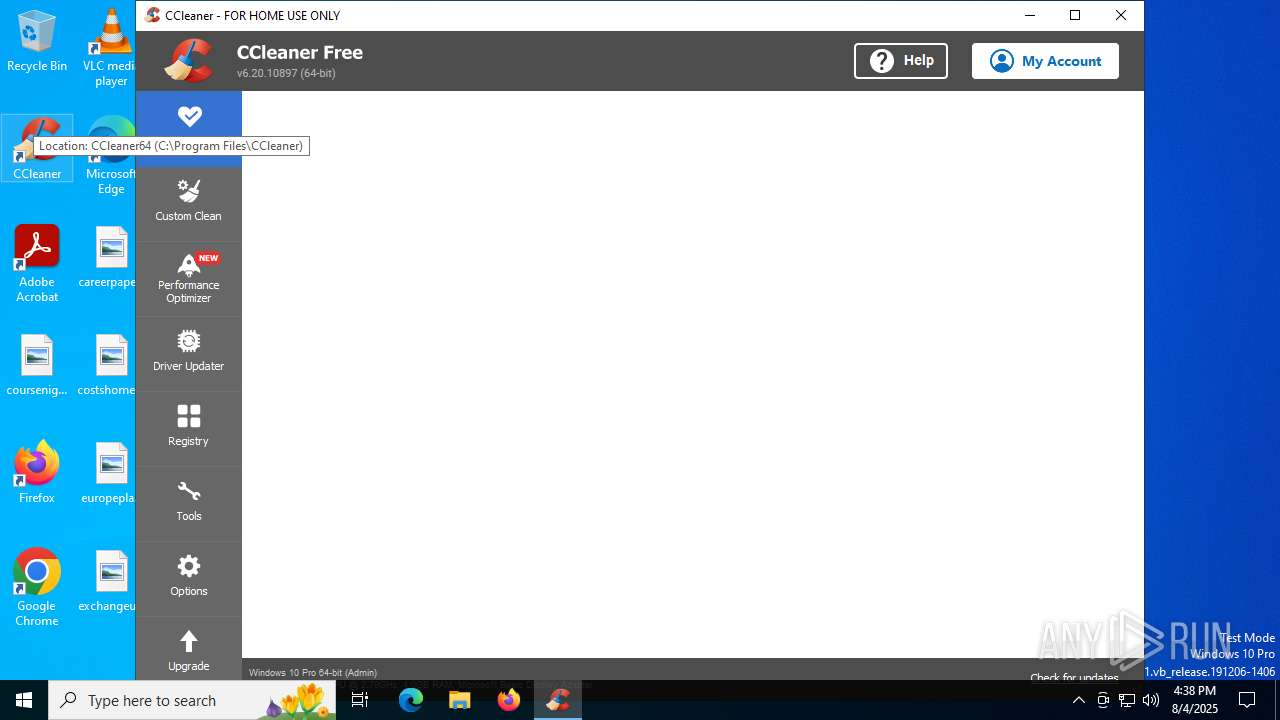
| 828 | "C:\Program Files\CCleaner\CCleaner64.exe" /monitor | C:\Program Files\CCleaner\CCleaner64.exe | CCleaner64.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Version: 6.20.0.10897 Modules
| |||||||||||||||
| 1576 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | w3wp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | "C:\Program Files\CCleaner\CCleaner64.exe" /uac | C:\Program Files\CCleaner\CCleaner64.exe | CCleaner64.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 6.20.0.10897 Modules
| |||||||||||||||
| 3580 | "C:\Users\admin\AppData\Local\Temp\w3wp.exe" | C:\Users\admin\AppData\Local\Temp\w3wp.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IIS Worker Process Exit code: 3221225781 Version: 10.0.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
| 4400 | "C:\Program Files\CCleaner\CCleaner64.exe" | C:\Program Files\CCleaner\CCleaner64.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 6.20.0.10897 Modules
| |||||||||||||||
Total events
17 814
Read events
17 671
Write events
90
Delete events
53
Modification events
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | write | Name: | UpdateBackground |
Value: 1 | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | write | Name: | DAST |
Value: 08/04/2025 16:38:08 | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | write | Name: | T8062 |
Value: 0 | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | CCleaner PostInstall |
Value: | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | write | Name: | FTU |
Value: 06/02/2024|3|1 | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | delete value | Name: | GUID |
Value: | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | delete value | Name: | GD |
Value: | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | delete value | Name: | SetupGD |
Value: | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Piriform\CCleaner |
| Operation: | write | Name: | NumOfOutdatedDrivers |
Value: 0 | |||
| (PID) Process: | (2428) CCleaner64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
4
Suspicious files
11
Text files
6
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | CCleaner64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4X7IVKKKYYR6884H5M6F.temp | binary | |
MD5:C46B95588080015AF8755CE8B229C5D8 | SHA256:275D7E9B06C22D49B9AFB7F081F2147263616B69CB8583A46A8C002AB2424710 | |||
| 2428 | CCleaner64.exe | C:\Program Files\CCleaner\gcapi_dll.dll | executable | |
MD5:F17F96322F8741FE86699963A1812897 | SHA256:8B6CE3A640E2D6F36B0001BE2A1ABB765AE51E62C314A15911E75138CBB544BB | |||
| 2428 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:0843861EEC825DB58E62257893446DDB | SHA256:33D89C37D8DD4C4E5A43C2F6BBD231BC82442609060DFCBF11BADD9B81D10399 | |||
| 2428 | CCleaner64.exe | C:\Program Files\CCleaner\gcapi_17543254882428.dll | executable | |
MD5:F17F96322F8741FE86699963A1812897 | SHA256:8B6CE3A640E2D6F36B0001BE2A1ABB765AE51E62C314A15911E75138CBB544BB | |||
| 2428 | CCleaner64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\ccupdate638_free[1].exe | — | |
MD5:— | SHA256:— | |||
| 2428 | CCleaner64.exe | C:\Program Files\CCleaner\temp_ccupdate\ccupdate638_free.exe | — | |
MD5:— | SHA256:— | |||
| 2428 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:E2C49304AB345AF645364D922A2E9CC6 | SHA256:791EF5EECF56CDABD68588467B1159B99DB4114D4DEB5B0C49081DC3E0F4787F | |||
| 2428 | CCleaner64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ccc0fa1b9f86f7b3.customDestinations-ms | binary | |
MD5:C46B95588080015AF8755CE8B229C5D8 | SHA256:275D7E9B06C22D49B9AFB7F081F2147263616B69CB8583A46A8C002AB2424710 | |||
| 2428 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:1416D299F1D878711CB265A77C144447 | SHA256:1A09ECCF04C0B6AF9901454CA870F21780913DCF103F17A528B6B238A261F166 | |||
| 2428 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:9093620AA89EB4F38EC3FA8F0B019859 | SHA256:7537A6F97C2A504993B8757019548D43A0C20E66729BB67079A38890A690F3E1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
34
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3888 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2428 | CCleaner64.exe | GET | 200 | 2.16.168.113:80 | http://ncc.avast.com/ncc.txt | unknown | — | — | whitelisted |
2428 | CCleaner64.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
2428 | CCleaner64.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
2428 | CCleaner64.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAXfj0A2M0oL7zuU%2F%2F2jetU%3D | unknown | — | — | whitelisted |
2428 | CCleaner64.exe | GET | 200 | 172.217.18.99:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4844 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.29:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ncc.avast.com |
| whitelisted |
analytics.avcdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
2428 | CCleaner64.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
Process | Message |
|---|---|
CCleaner64.exe | [2025-08-04 16:38:08.226] [error ] [settings ] [ 2428: 436] [000000: 0] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner64.exe | [2025-08-04 16:38:08.226] [error ] [ini_access ] [ 2428: 436] [000000: 0] Incorrect ini_accessor configuration! Fixing relative input path to avoid recursion. Input was: Setup
|
CCleaner64.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner64.exe | OnLanguage - en
|
CCleaner64.exe | [2025-08-04 16:38:08.694] [error ] [settings ] [ 2428: 6292] [D2EC45: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner64.exe | [2025-08-04 16:38:08.694] [error ] [Burger ] [ 2428: 6292] [904E07: 253] [23.2.1118.0] [BurgerReporter.cpp] [253] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner64.exe | [2025-08-04 16:38:08.694] [error ] [Burger ] [ 2428: 6292] [904E07: 253] [23.2.1118.0] [BurgerReporter.cpp] [253] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner64.exe | file:///tis/optimizer.tis(1131) : warning :'await' should be used only inside 'async' or 'event'
|
CCleaner64.exe | file:///tis/optimizer.tis(1288) : warning :'async' does not contain any 'await'
|
CCleaner64.exe | startCheckingLicense()
|