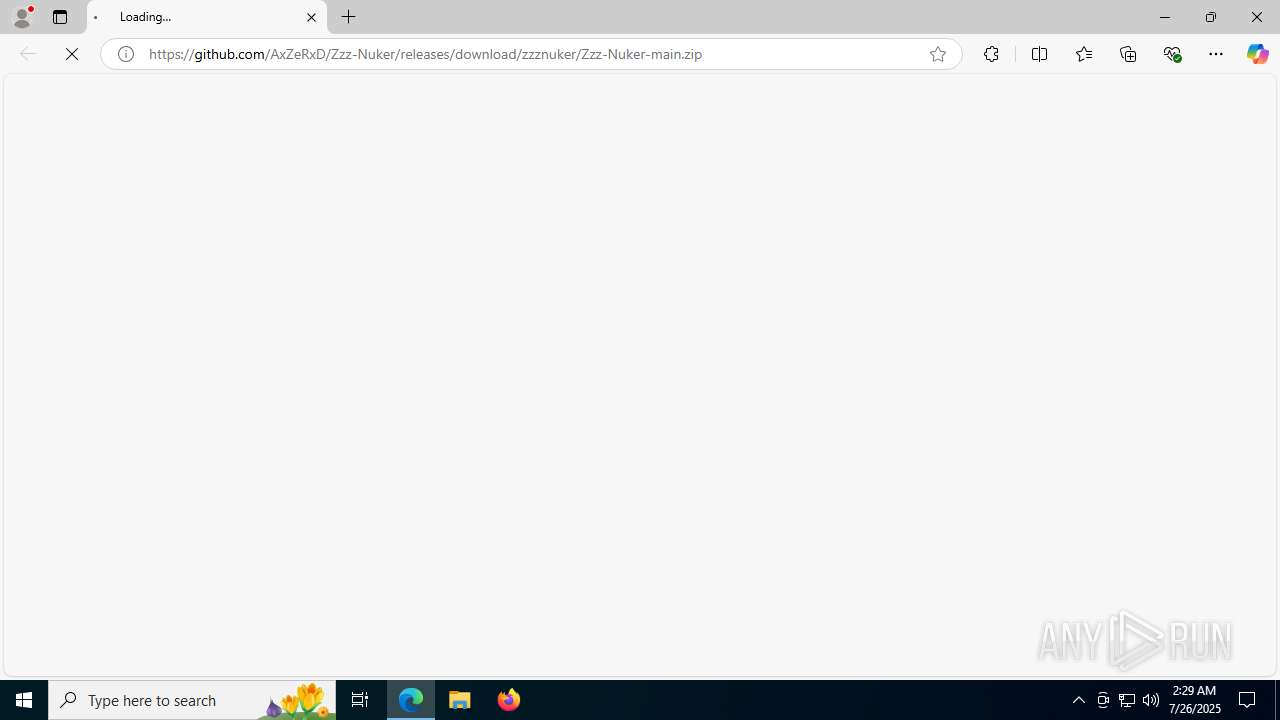
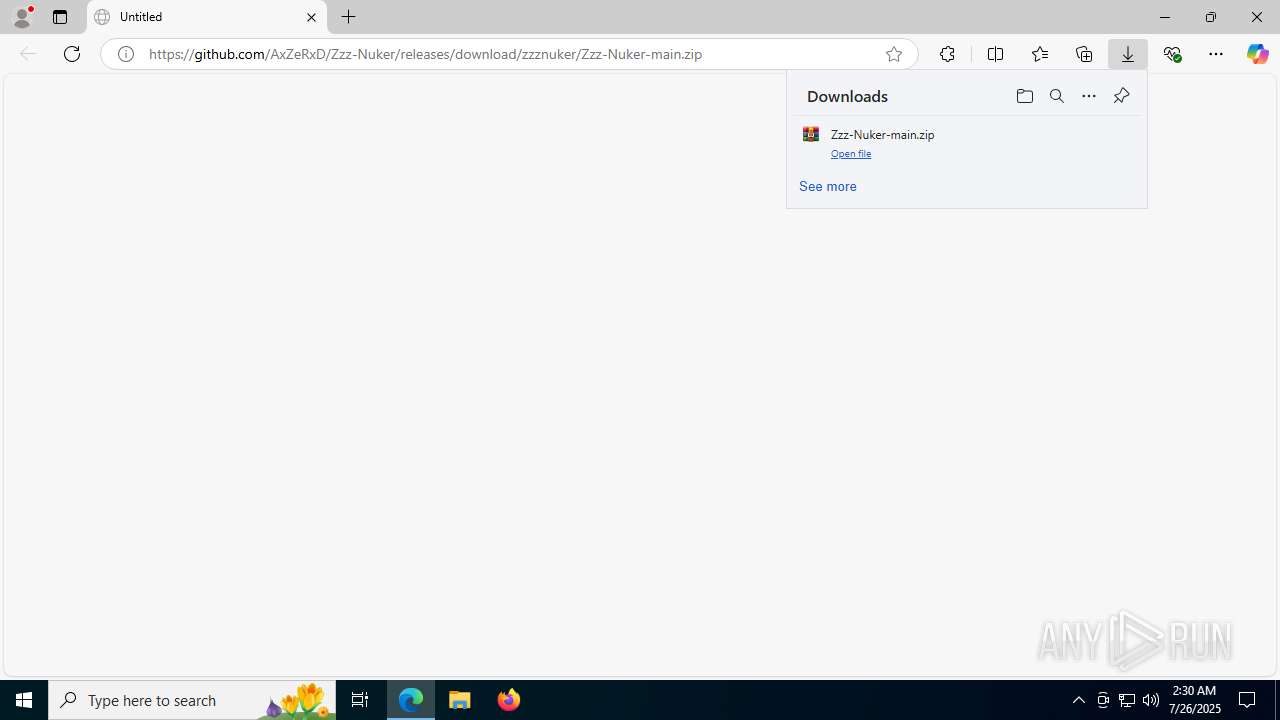
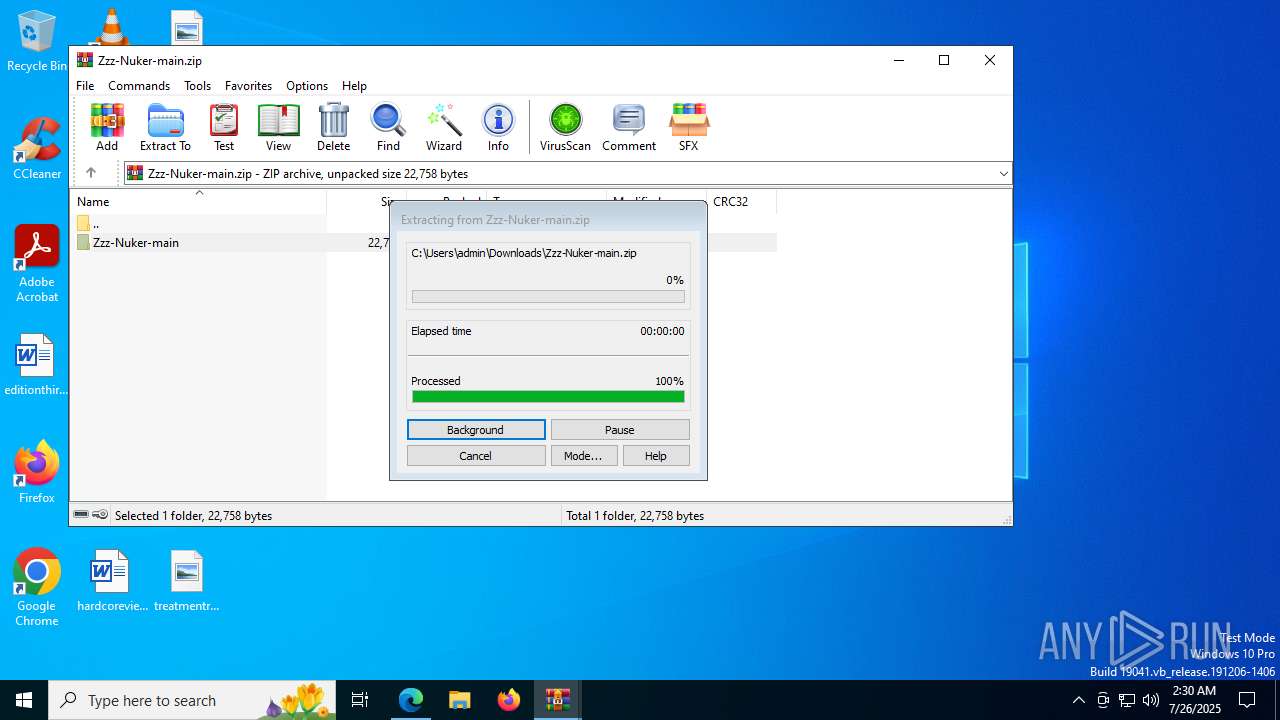
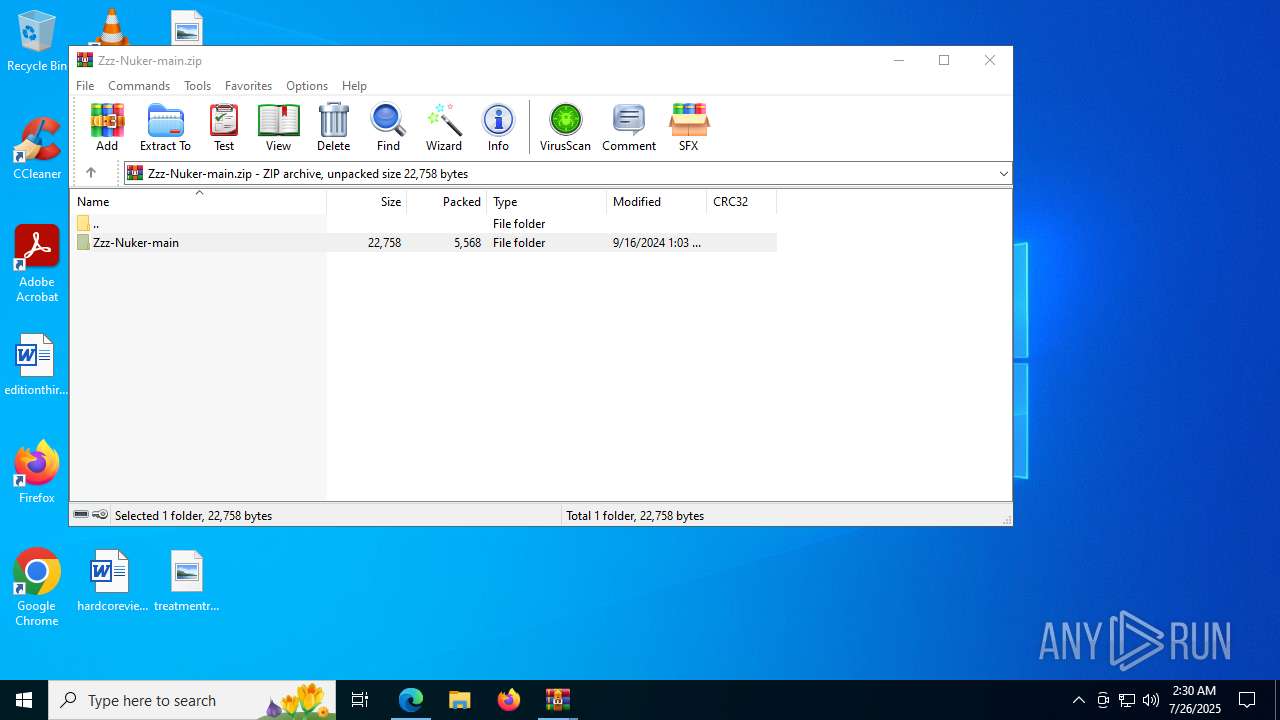
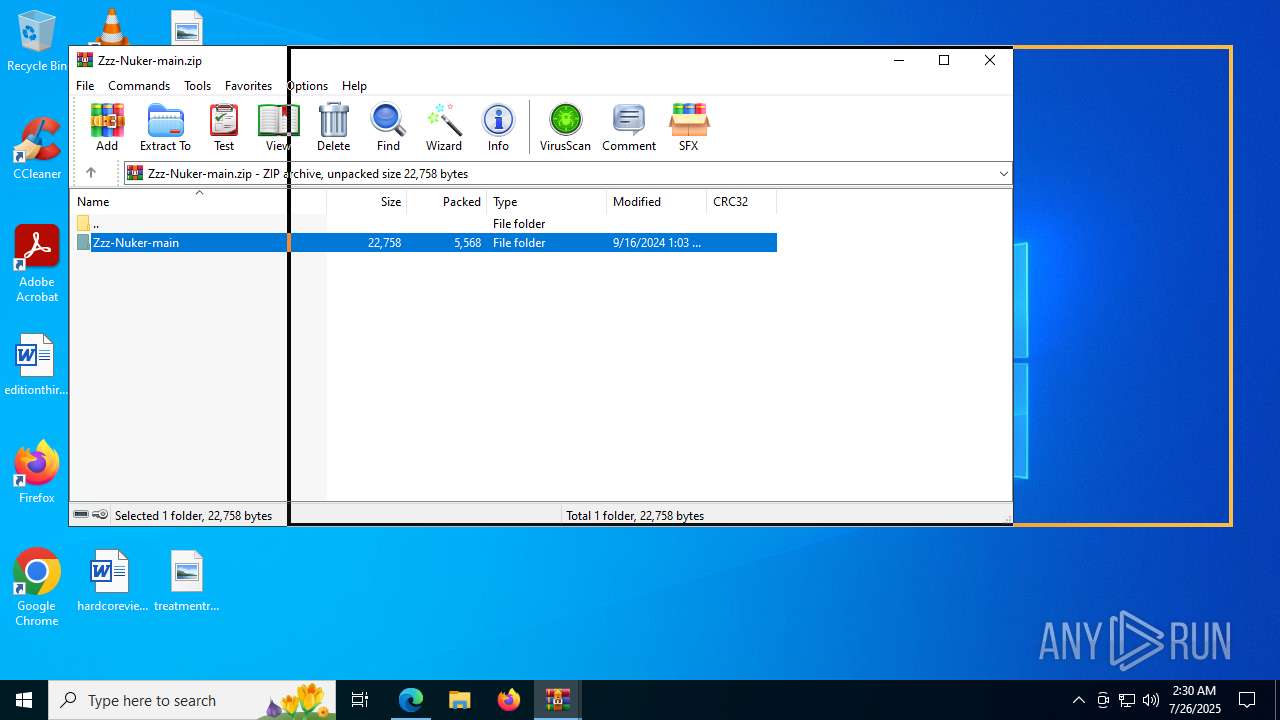
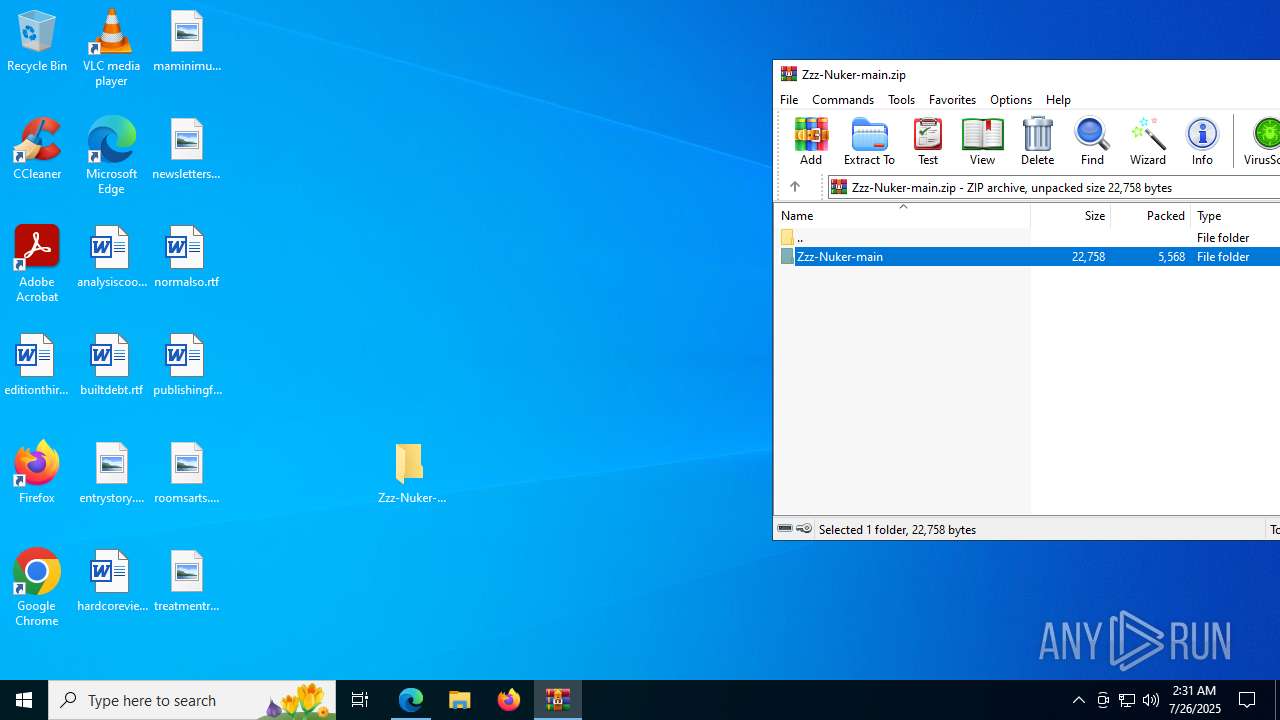
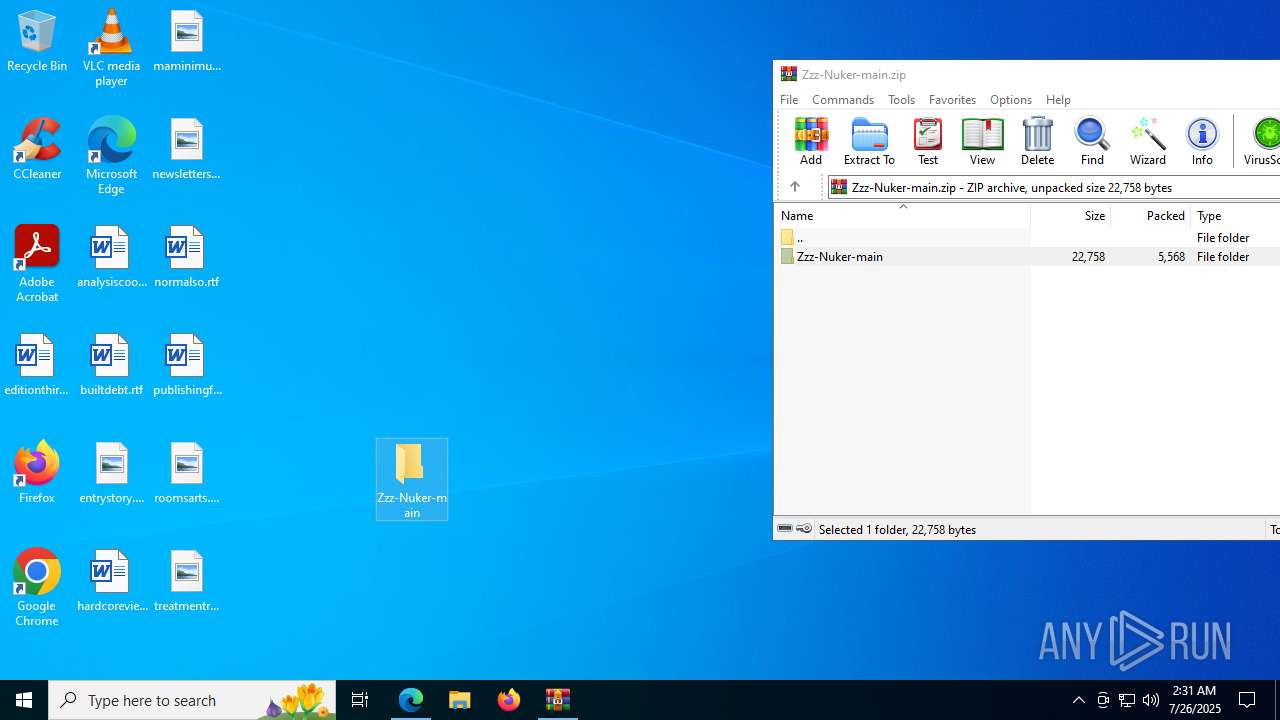
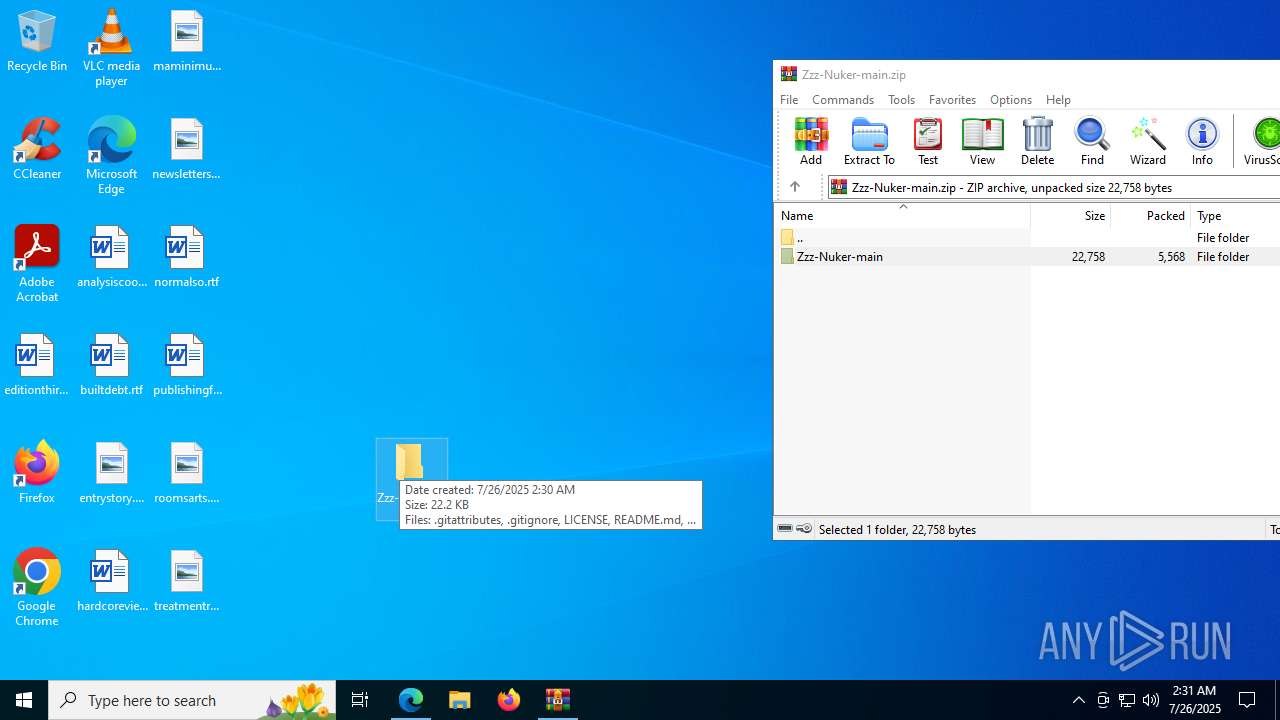
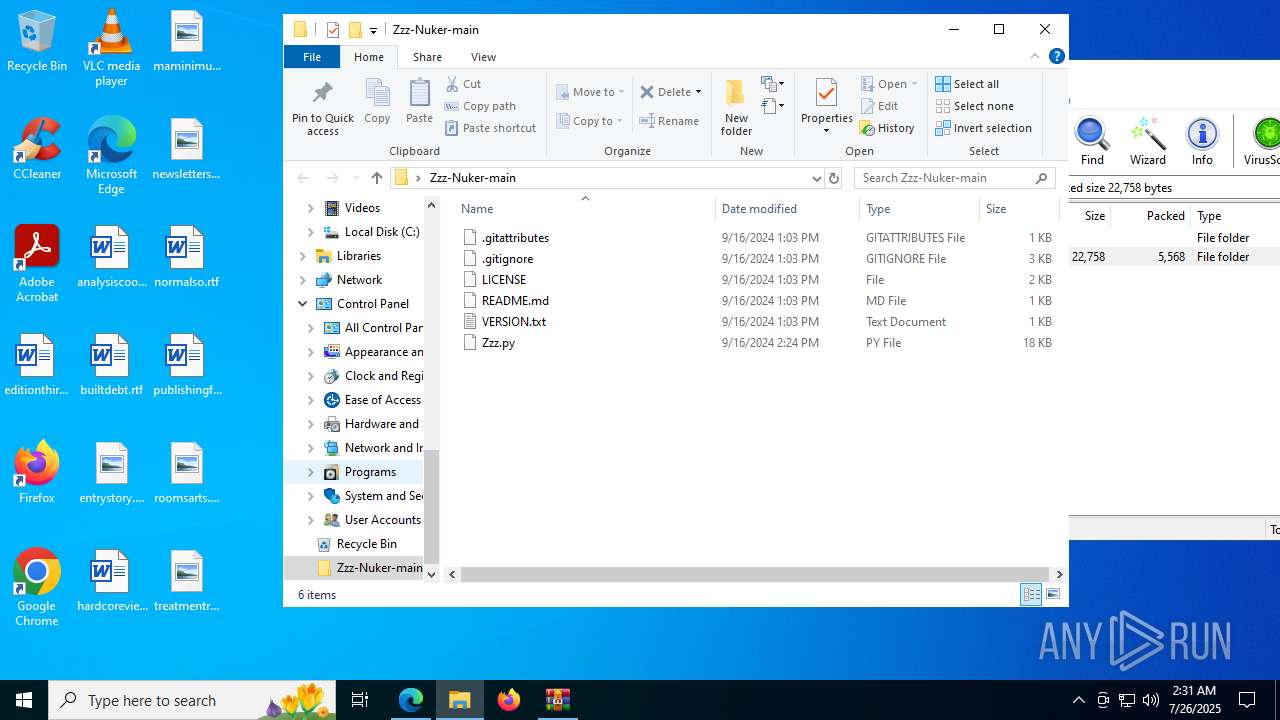
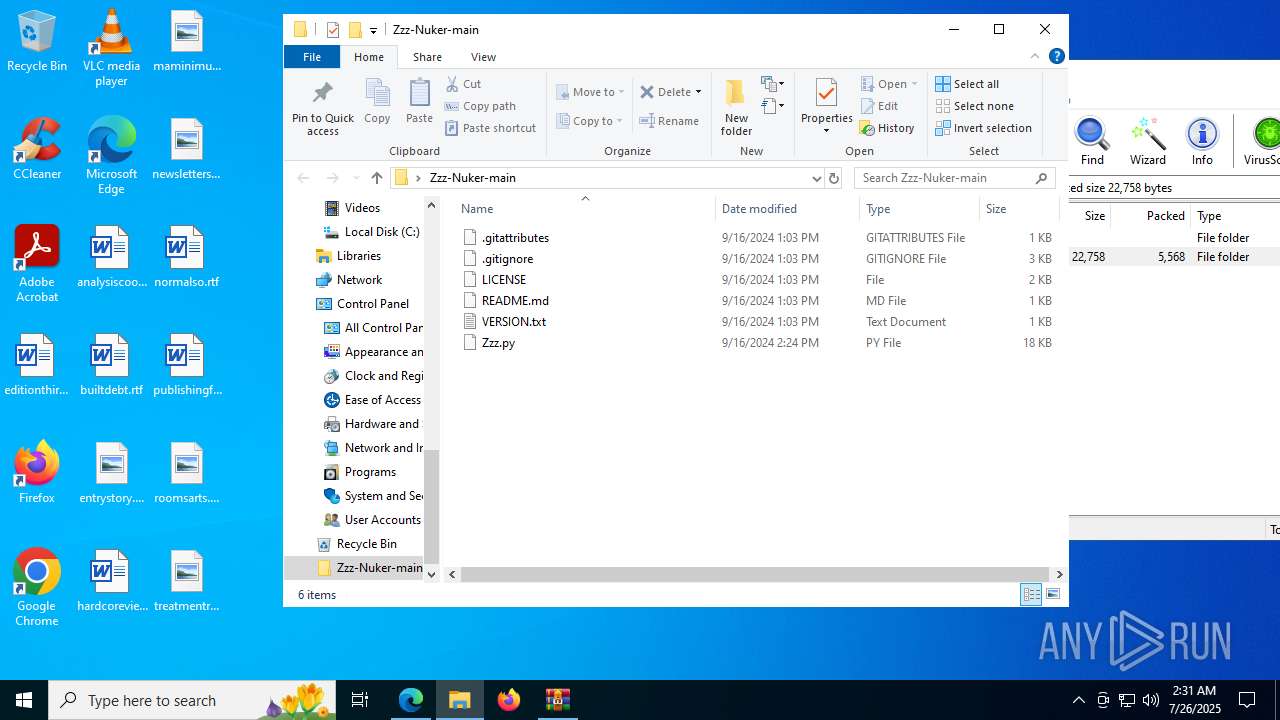
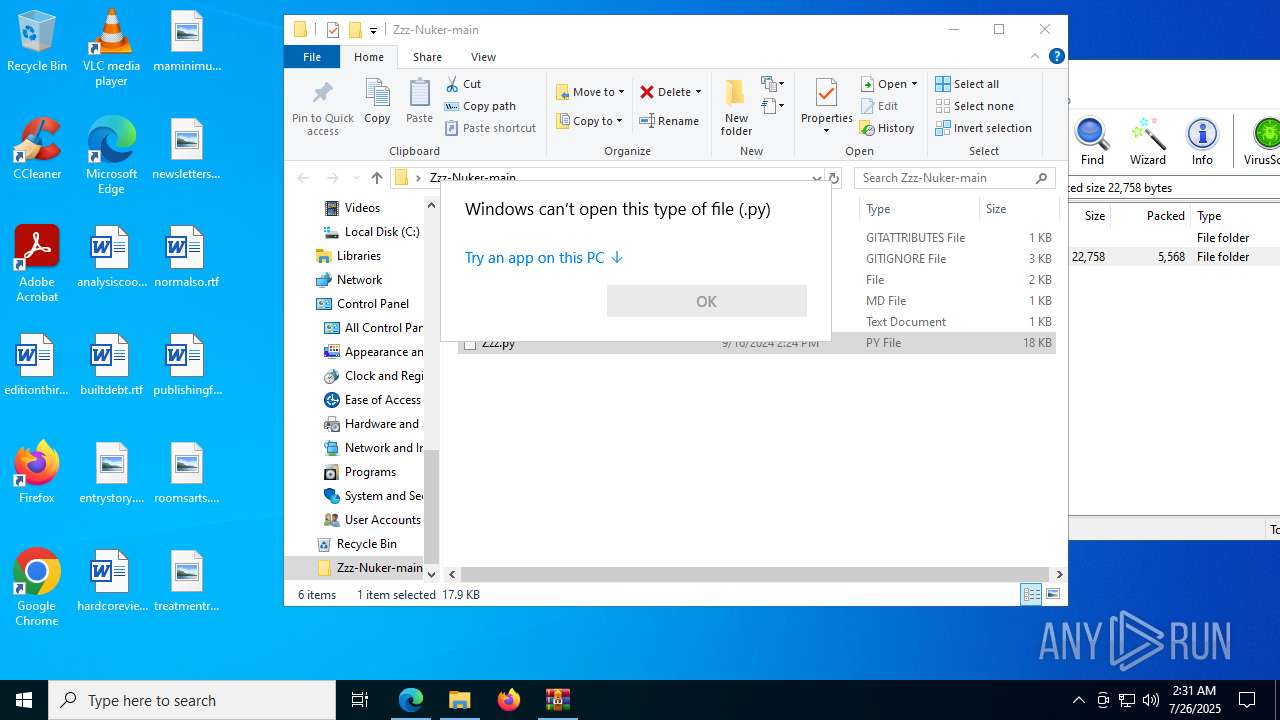
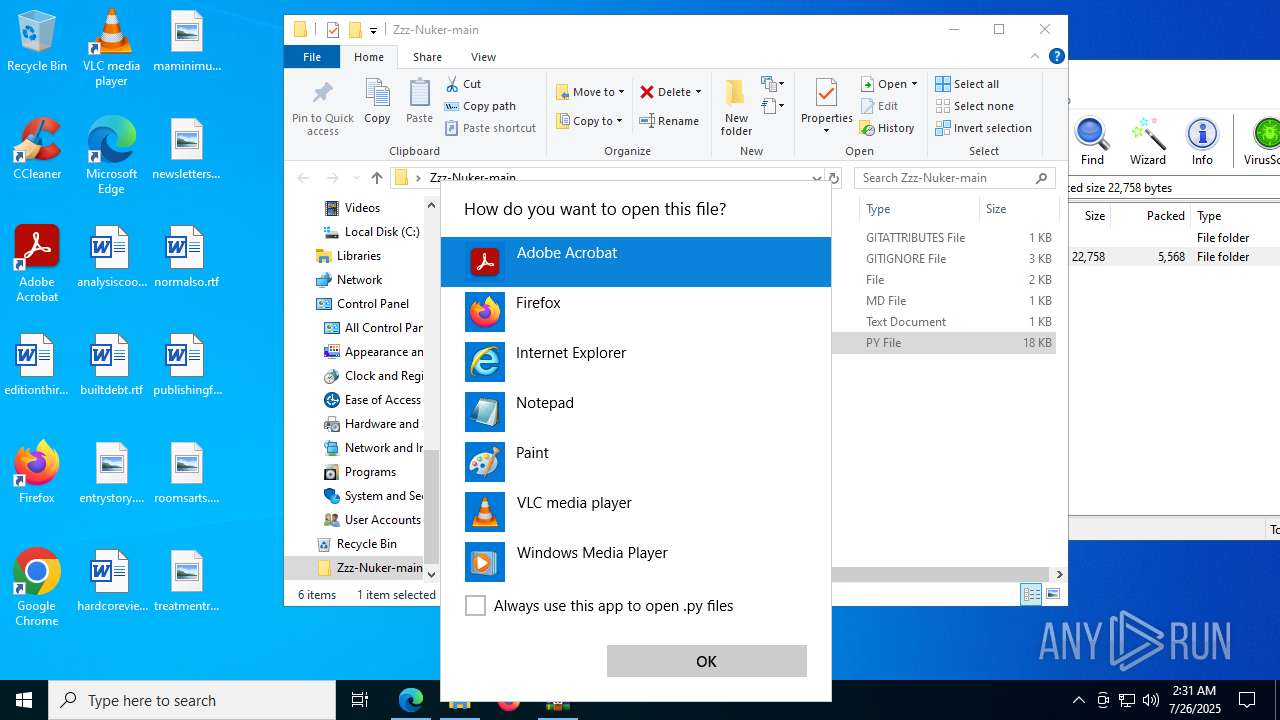
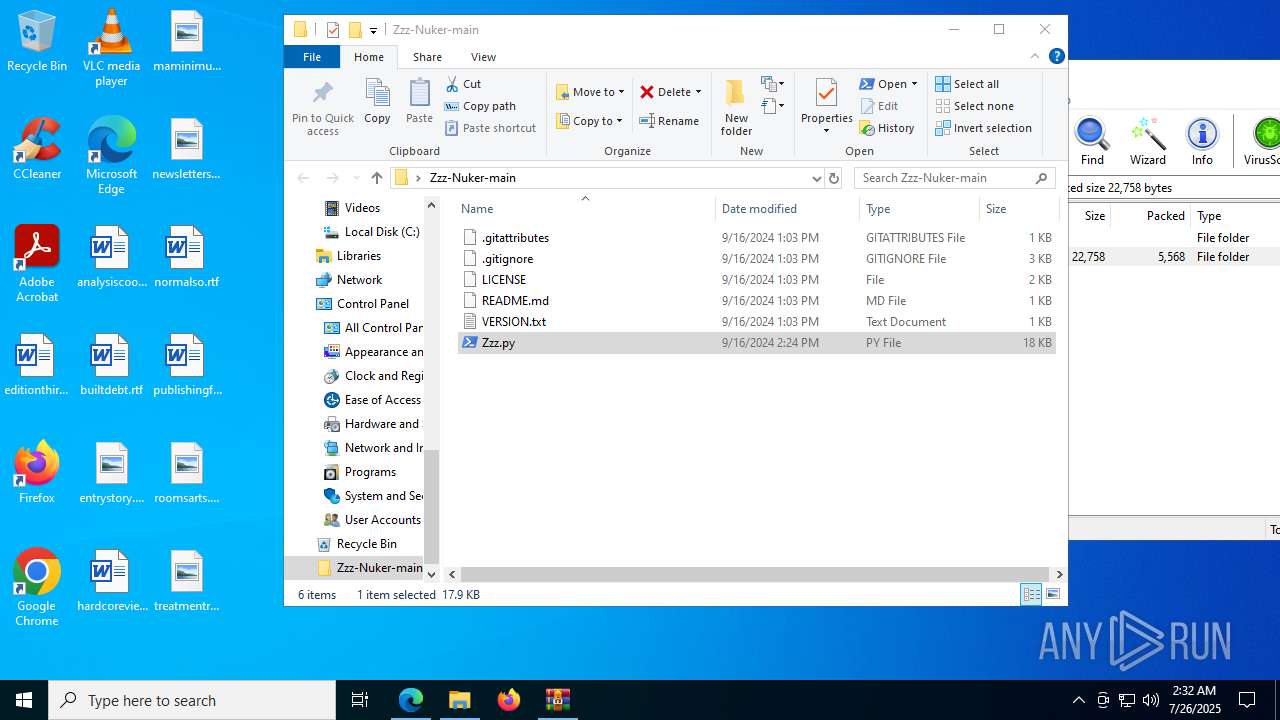
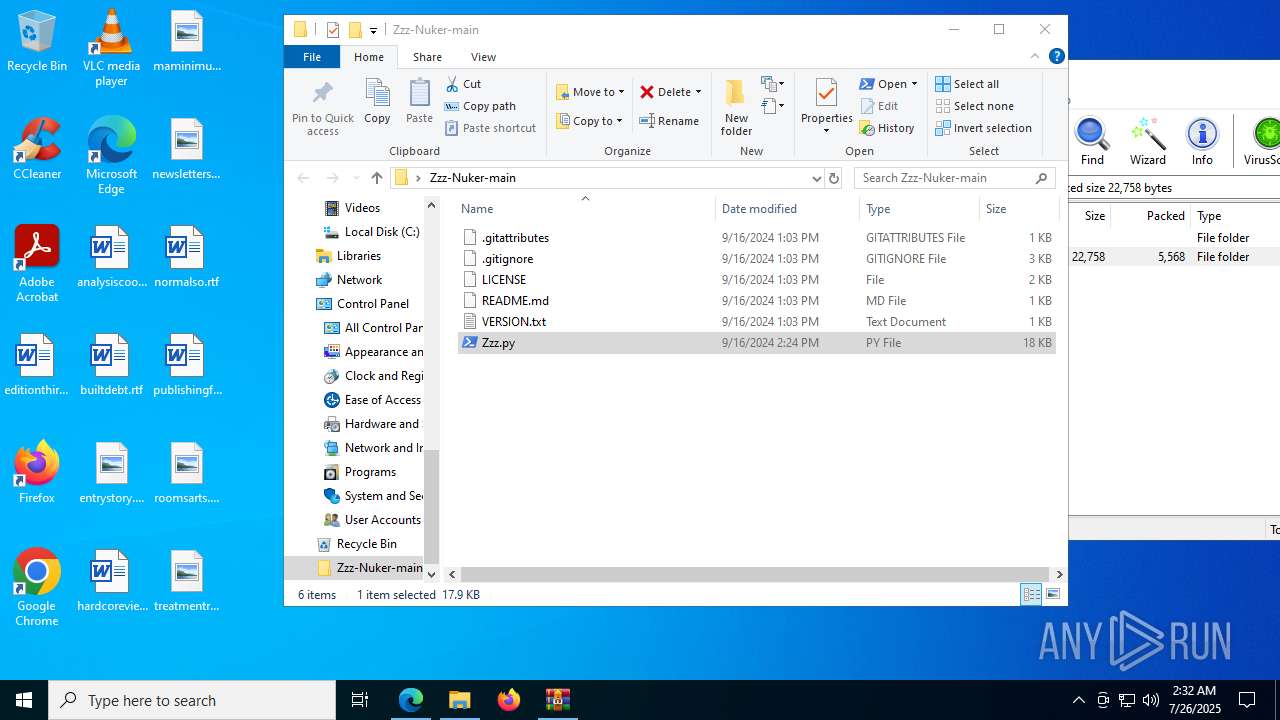
| URL: | https://github.com/AxZeRxD/Zzz-Nuker/releases/download/zzznuker/Zzz-Nuker-main.zip |
| Full analysis: | https://app.any.run/tasks/d6e9f65f-e4c6-4411-9670-b67ade4239dc |
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2025, 02:29:50 |
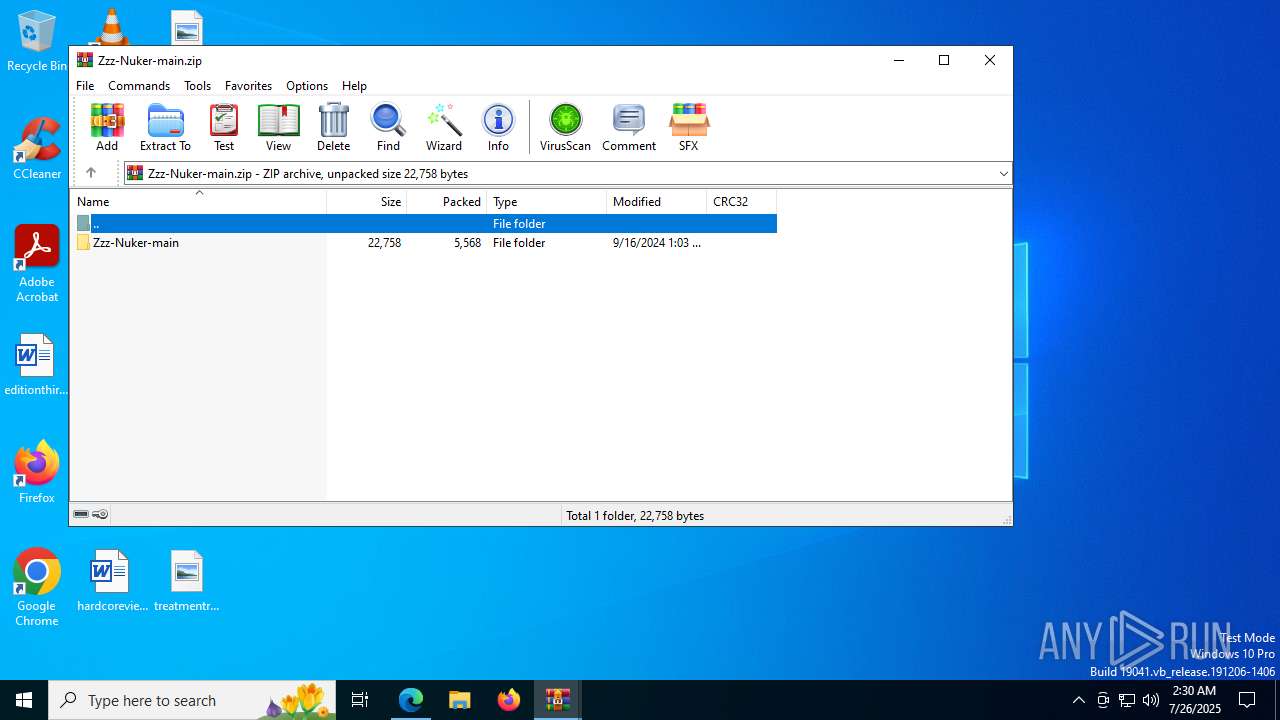
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
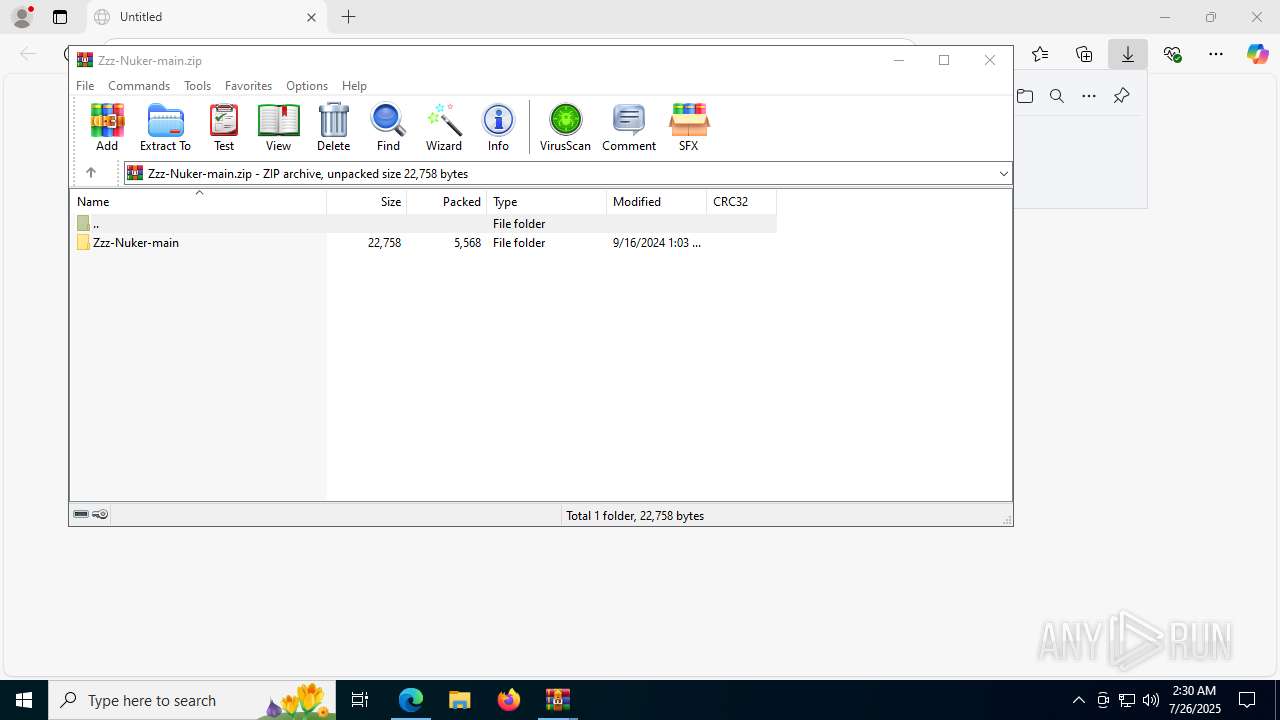
| MD5: | 9B484CAF977351E24A0604DE2266B228 |
| SHA1: | 9A3EDB8582E276F9102BD35353AE85C36B342F4B |
| SHA256: | A05FBB82DEF39EBF729684464576A4C3D47D7ED76E438B4357D9459D8105EABC |
| SSDEEP: | 3:N8tEdlAXKXAOE2kCcvVrbAXI5KLfU:2ujyMhrEnyOF |
MALICIOUS
No malicious indicators.SUSPICIOUS
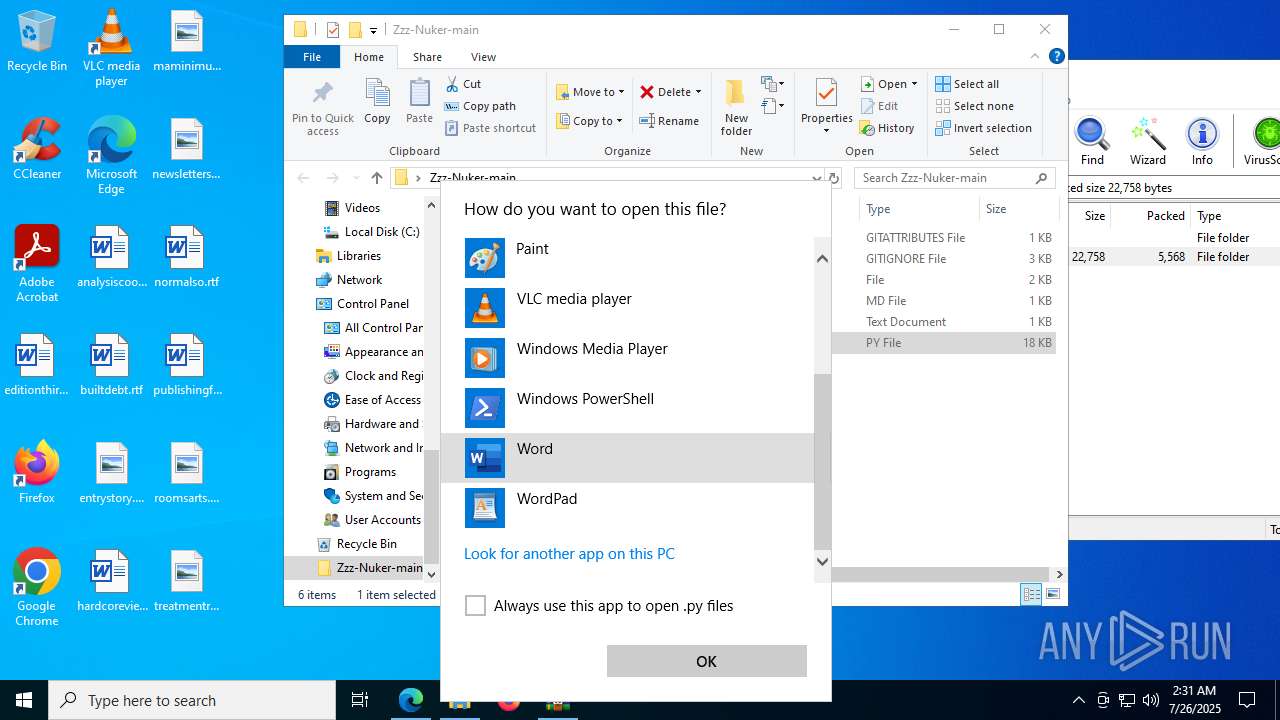
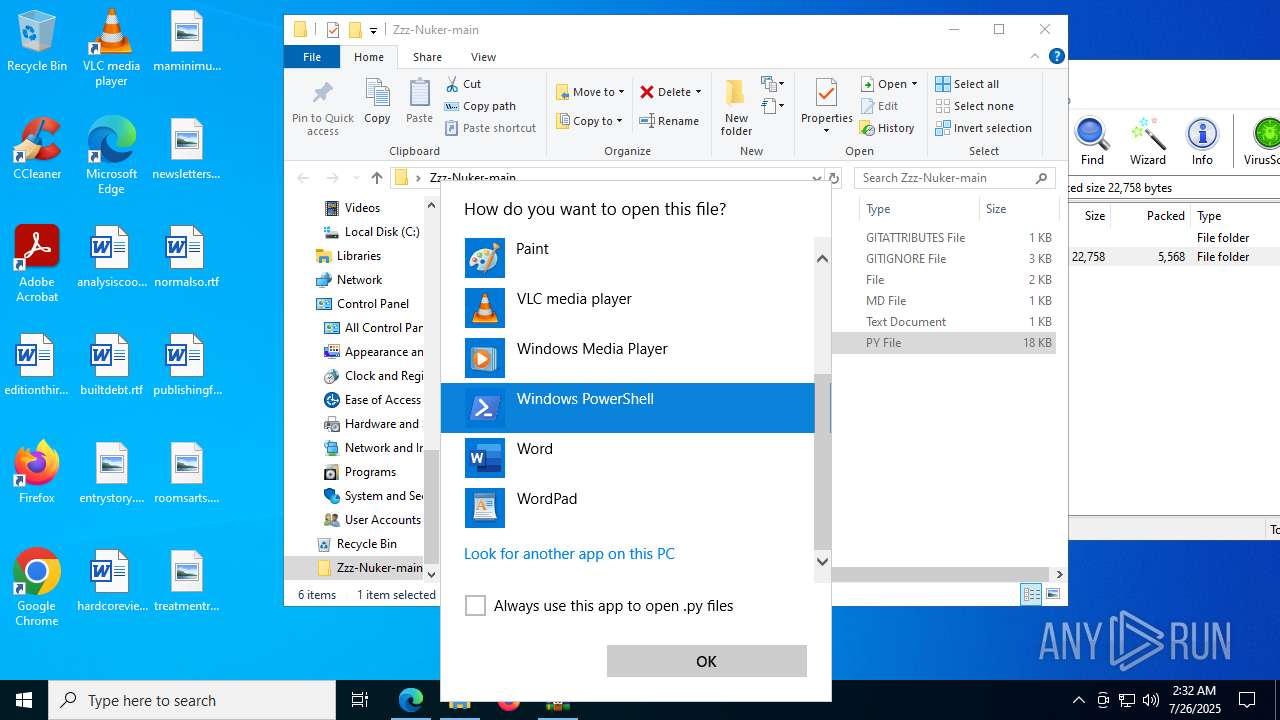
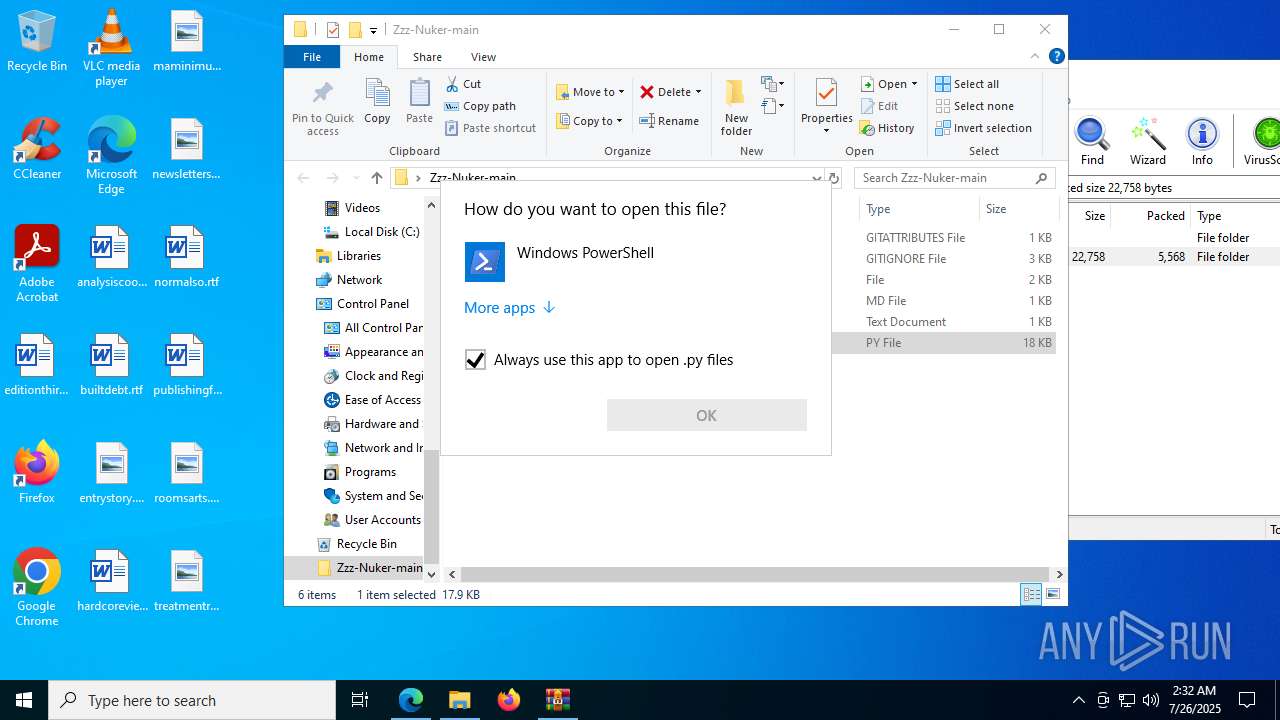
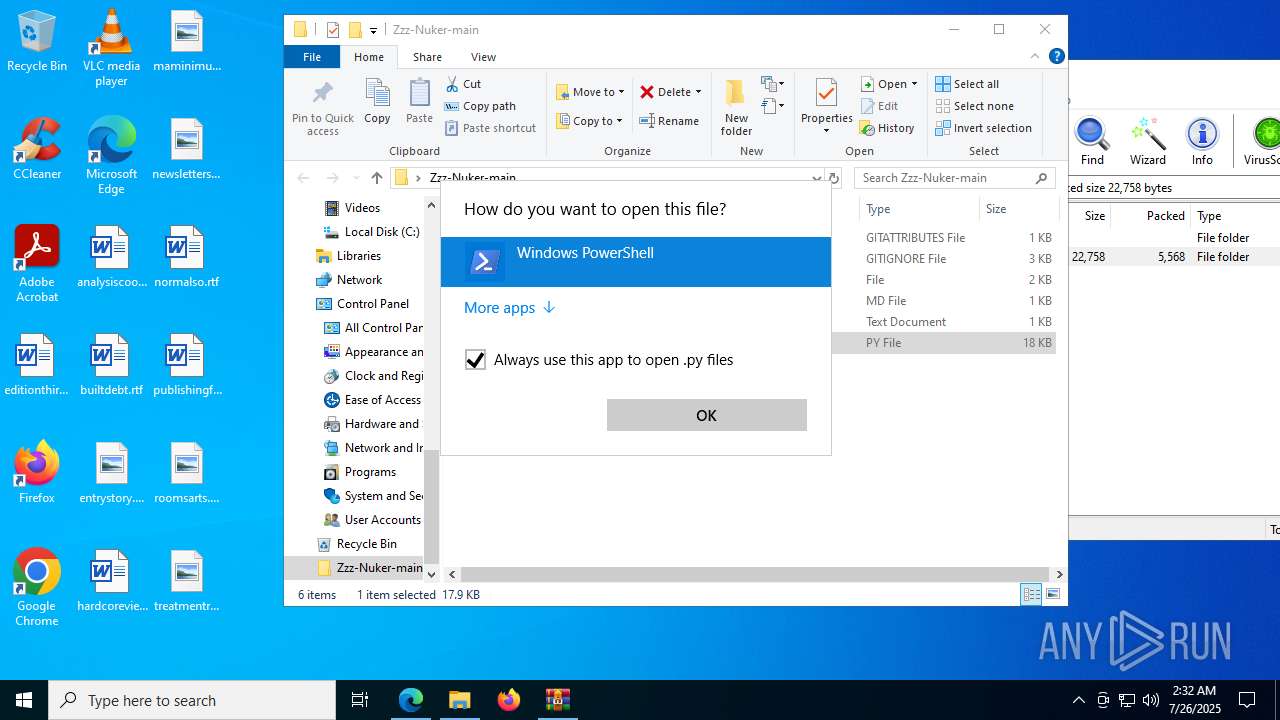
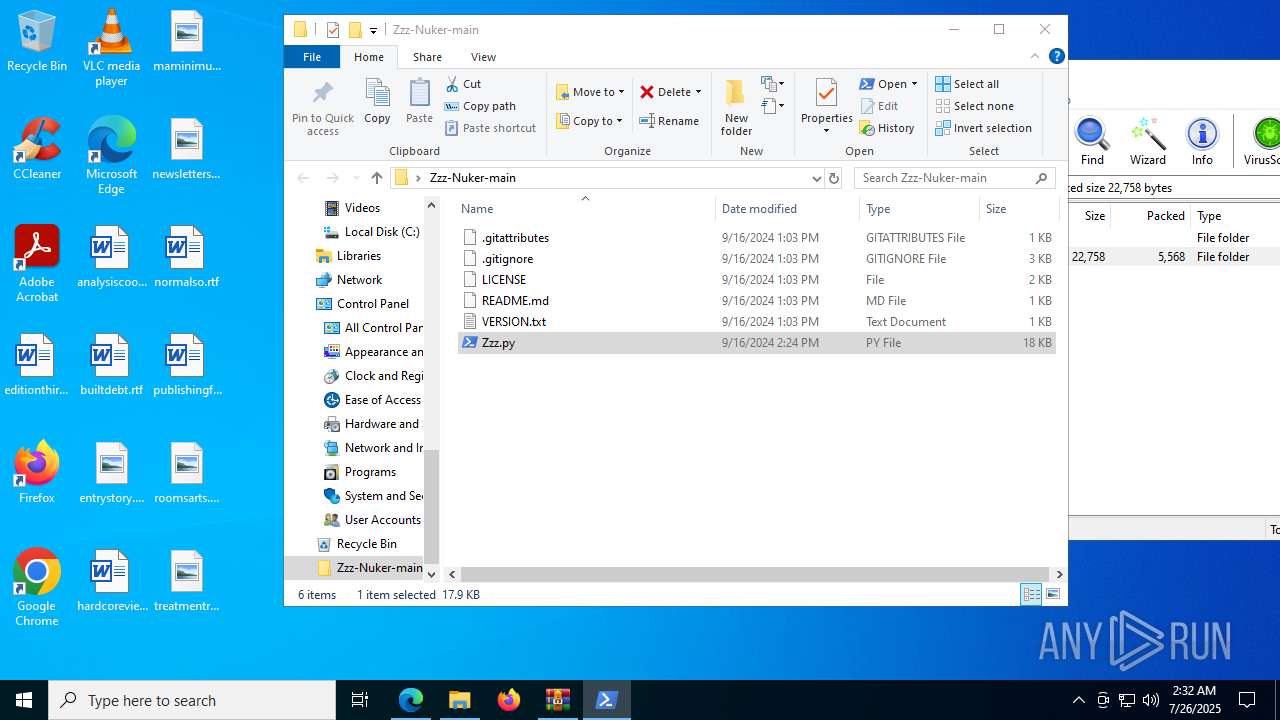
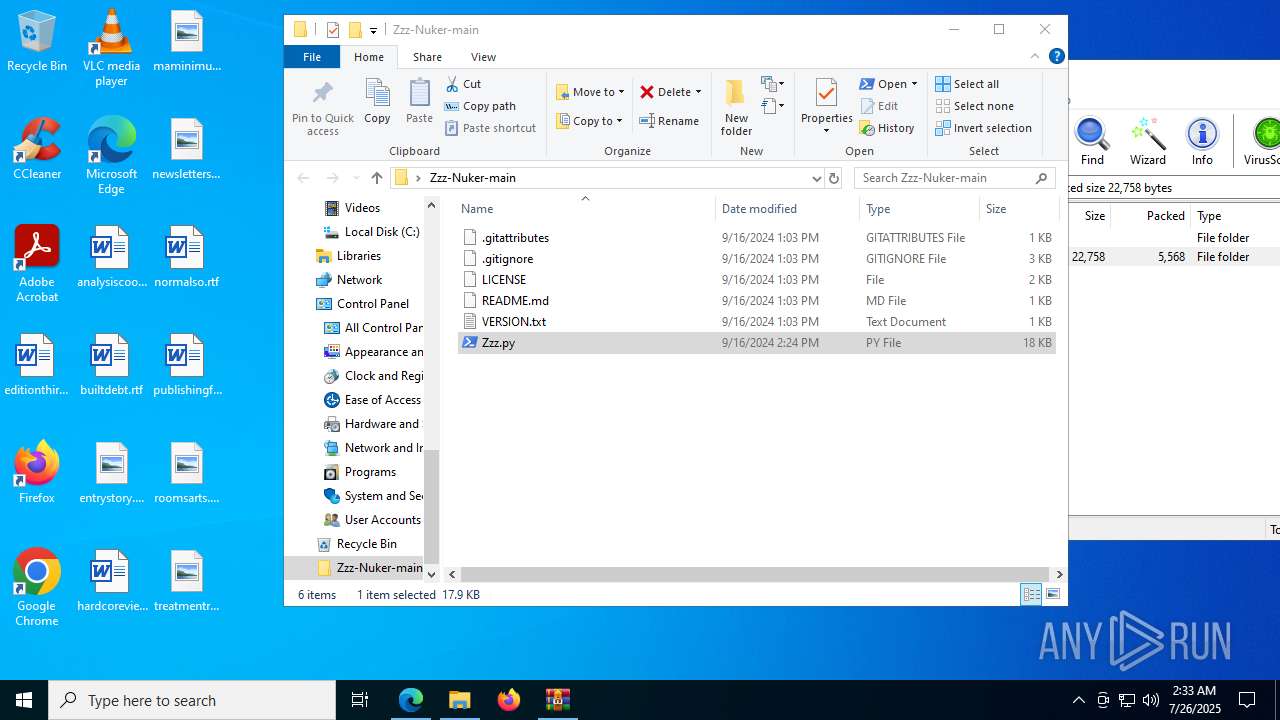
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 8064)
- OpenWith.exe (PID: 7284)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 4832)
- powershell.exe (PID: 7704)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 6288)
- powershell.exe (PID: 7640)
- powershell.exe (PID: 6404)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 432)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7320)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 1100)
- powershell.exe (PID: 684)
- powershell.exe (PID: 2216)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7044)
- powershell.exe (PID: 7892)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 7096)
- powershell.exe (PID: 4448)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 3576)
- powershell.exe (PID: 3688)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 5132)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 5248)
- powershell.exe (PID: 4188)
- powershell.exe (PID: 5028)
- powershell.exe (PID: 7084)
- powershell.exe (PID: 6736)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 7260)
- powershell.exe (PID: 7652)
- powershell.exe (PID: 1332)
- powershell.exe (PID: 6600)
- powershell.exe (PID: 4460)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 4808)
- powershell.exe (PID: 1728)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 7476)
- powershell.exe (PID: 7764)
Application launched itself
- powershell.exe (PID: 7608)
- powershell.exe (PID: 4832)
- powershell.exe (PID: 7704)
- powershell.exe (PID: 6288)
- powershell.exe (PID: 7640)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 432)
- powershell.exe (PID: 6404)
- powershell.exe (PID: 2216)
- powershell.exe (PID: 7320)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 1100)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 4448)
- powershell.exe (PID: 7044)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 7096)
- powershell.exe (PID: 7892)
- powershell.exe (PID: 684)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 3576)
- powershell.exe (PID: 3688)
- powershell.exe (PID: 5132)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 5248)
- powershell.exe (PID: 4188)
- powershell.exe (PID: 7084)
- powershell.exe (PID: 6736)
- powershell.exe (PID: 7260)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 7652)
- powershell.exe (PID: 6600)
- powershell.exe (PID: 4460)
- powershell.exe (PID: 5028)
- powershell.exe (PID: 1332)
- powershell.exe (PID: 4808)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 1728)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 7476)
- powershell.exe (PID: 7764)
INFO
Application launched itself
- msedge.exe (PID: 7020)
Reads the computer name
- identity_helper.exe (PID: 7736)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7020)
- OpenWith.exe (PID: 8064)
- OpenWith.exe (PID: 7284)
Checks supported languages
- identity_helper.exe (PID: 7736)
Reads Environment values
- identity_helper.exe (PID: 7736)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 8064)
- OpenWith.exe (PID: 7284)
Checks proxy server information
- slui.exe (PID: 6876)
Reads the software policy settings
- slui.exe (PID: 6876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
287
Monitored processes
142
Malicious processes
0
Suspicious processes
32
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Desktop\Zzz-Nuker-main\Zzz.py" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Desktop\Zzz-Nuker-main\Zzz.py" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3676,i,17303841337590707657,8985454928483772165,262144 --variations-seed-version --mojo-platform-channel-handle=3708 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Desktop\Zzz-Nuker-main\Zzz.py" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Desktop\Zzz-Nuker-main\Zzz.py" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Desktop\Zzz-Nuker-main\Zzz.py" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6968,i,17303841337590707657,8985454928483772165,262144 --variations-seed-version --mojo-platform-channel-handle=4412 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
249 123
Read events
249 029
Write events
94
Delete events
0
Modification events
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 64F3491E62992F00 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459482 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CDF55522-E5AC-44F1-BDAC-90A8592E269A} | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459482 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {336FE850-21E6-467C-8EB6-D324B0B0407D} | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B5355B1E62992F00 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
10
Suspicious files
431
Text files
170
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18da3e.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18da3e.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18da6d.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18da3e.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18da4e.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
66
DNS requests
66
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6256 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:bCiuJvAW3i6K8KEyyfRmoI3Hx3MJ38pXWud4AsFyU88&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5528 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5528 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7736 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753785202&P2=404&P3=2&P4=fydyQxaYRP2xc9aqVX2CJGKfNdAKzDLnO72N%2f2jyG%2f8TKdfvlTU5qXMVQC4L2s1VJWBOApVmDjGIZWt5sXcEzw%3d%3d | unknown | — | — | whitelisted |
7736 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1753792408&P2=404&P3=2&P4=aH5ipm%2fR%2fCCjl%2bOioyCHLyfF2dxsgTDmg692bkLVyhXrIpEFhBKSINePoL8UZLS8F3bM2gyXzeM%2fOp8jaqv%2fZA%3d%3d | unknown | — | — | whitelisted |
7736 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1753785207&P2=404&P3=2&P4=KHSpeMkfAEYC36GpJq%2fsrxlTh8ya7bs59VTzxpgV%2fnVIjc9f5wbCUDfWhuc63o6EMI%2bJQaIppkvjftWg59Q5qw%3d%3d | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 52.167.17.97:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 52.167.17.97:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5476 | RUXIMICS.exe | 52.167.17.97:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6256 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6256 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6256 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
6256 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6256 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
release-assets.githubusercontent.com |
| unknown |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6256 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |