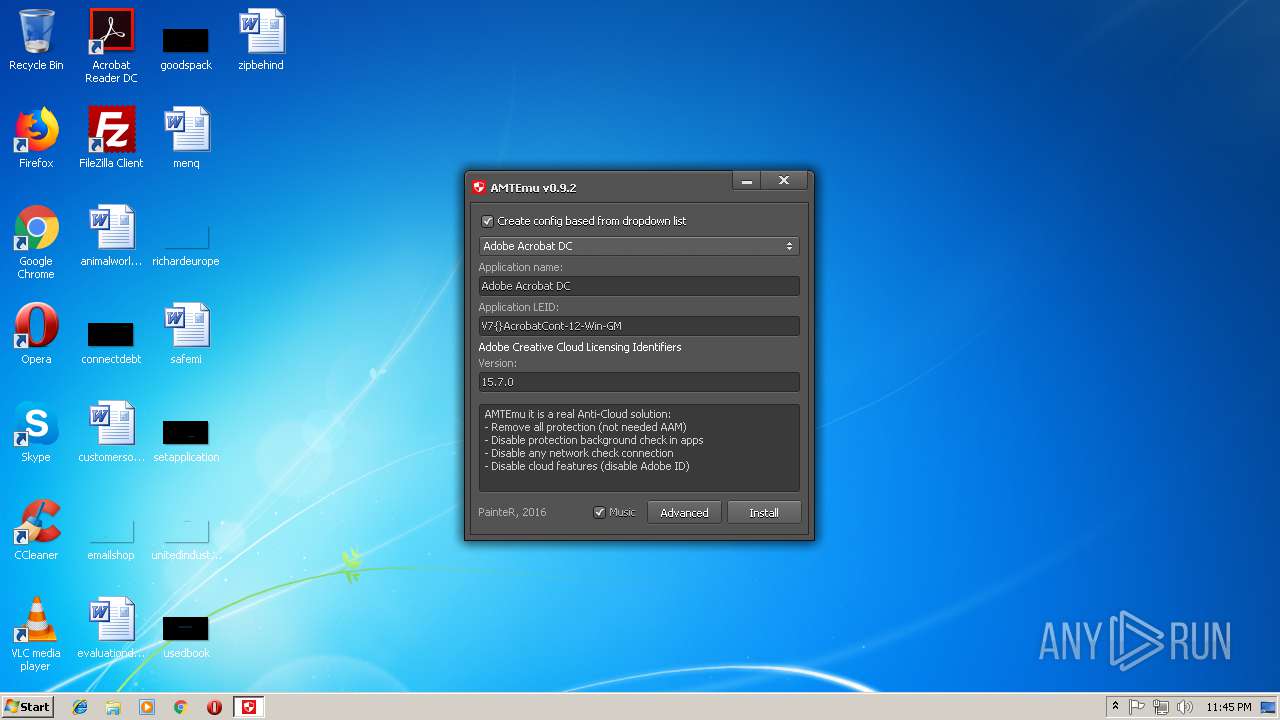
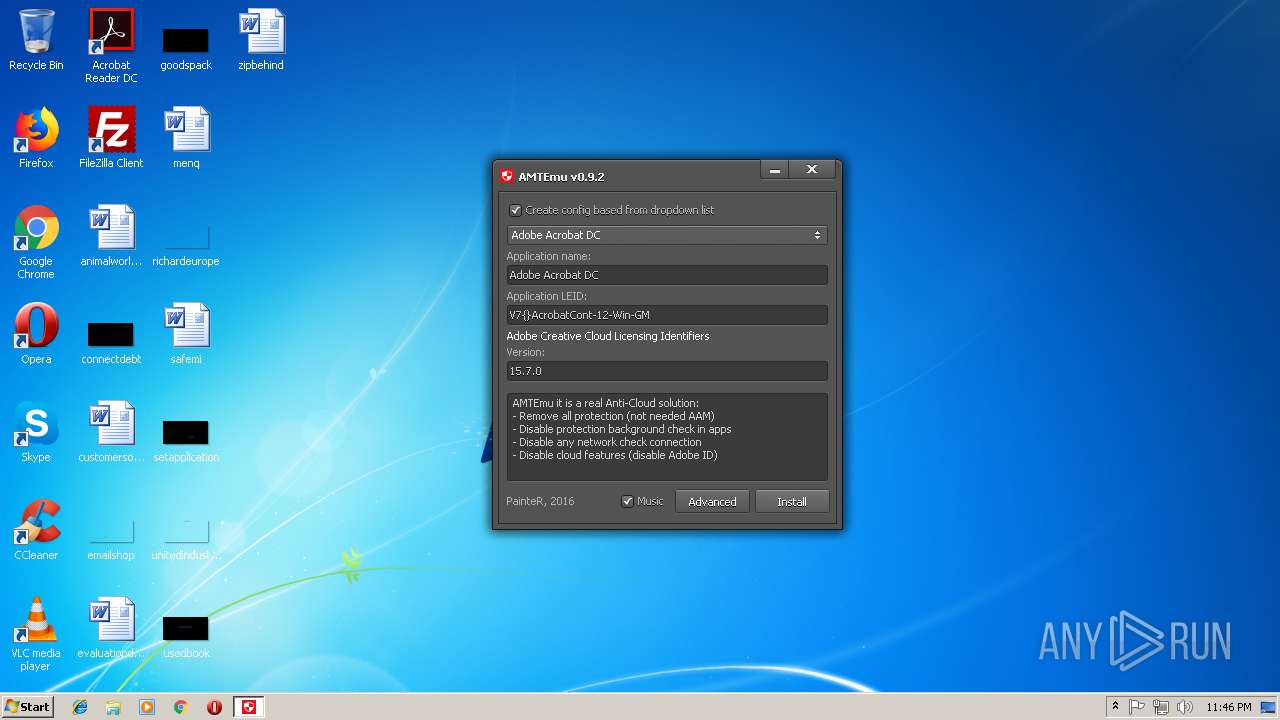
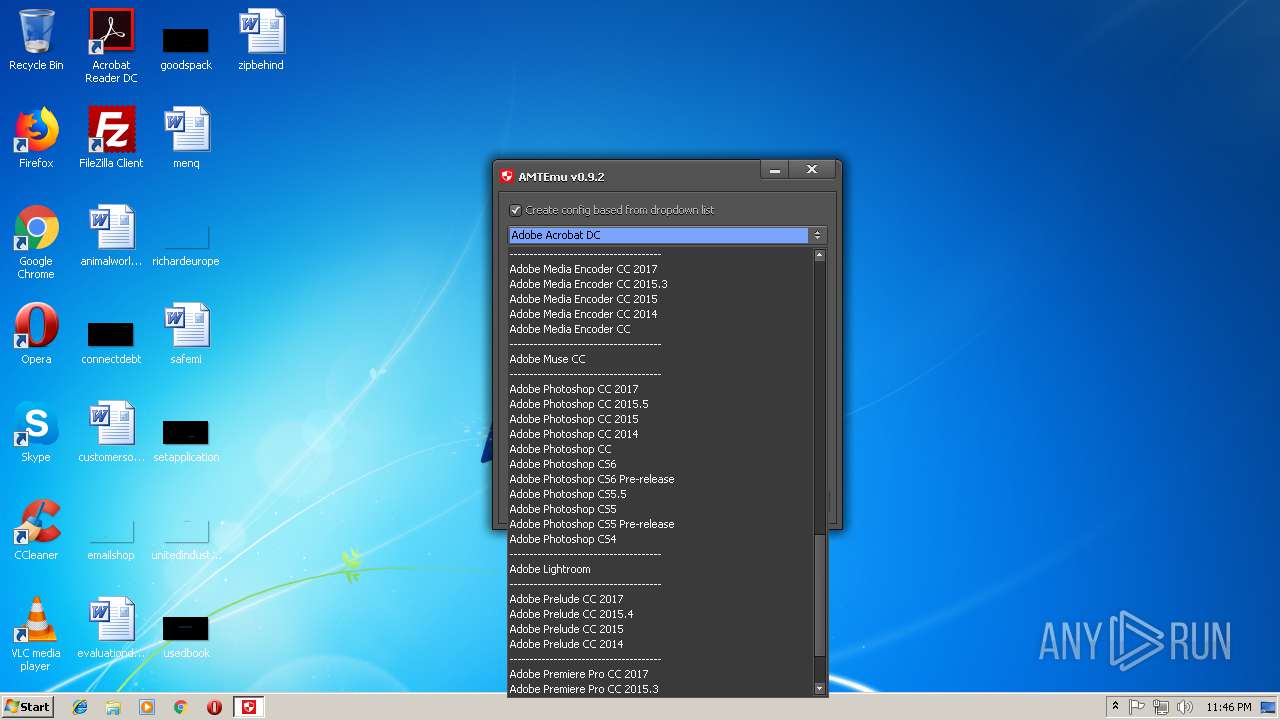
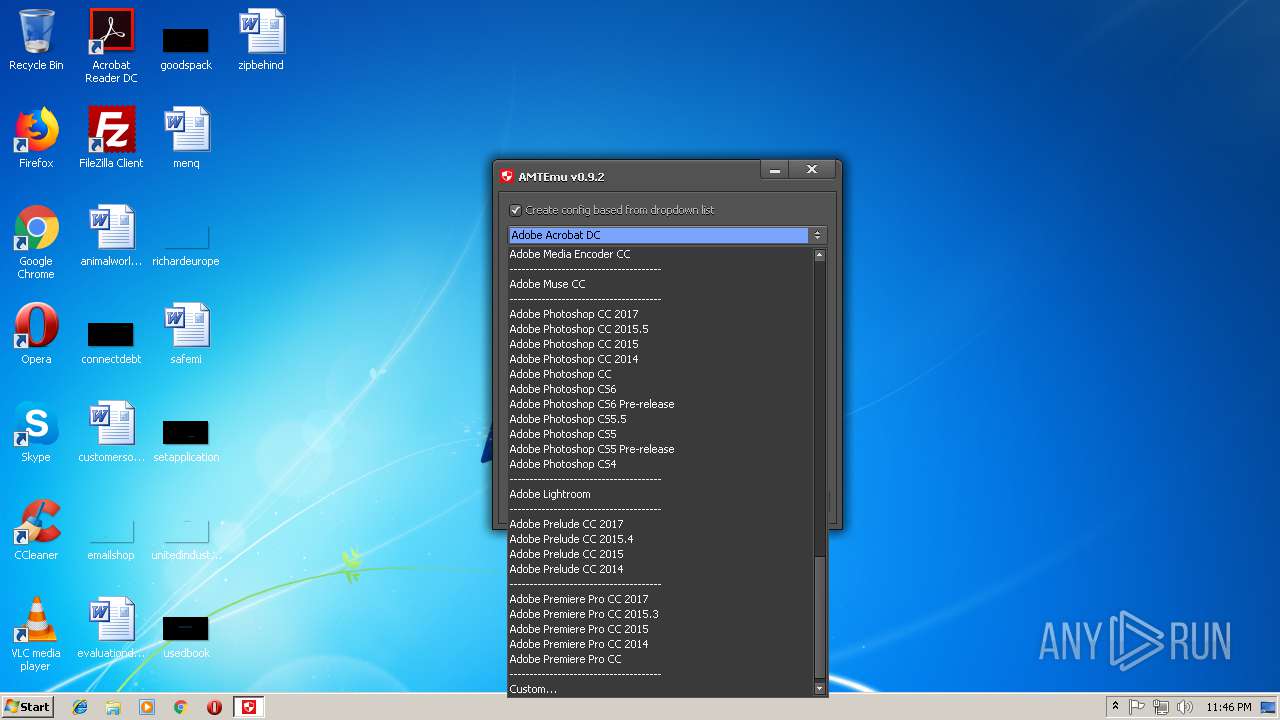
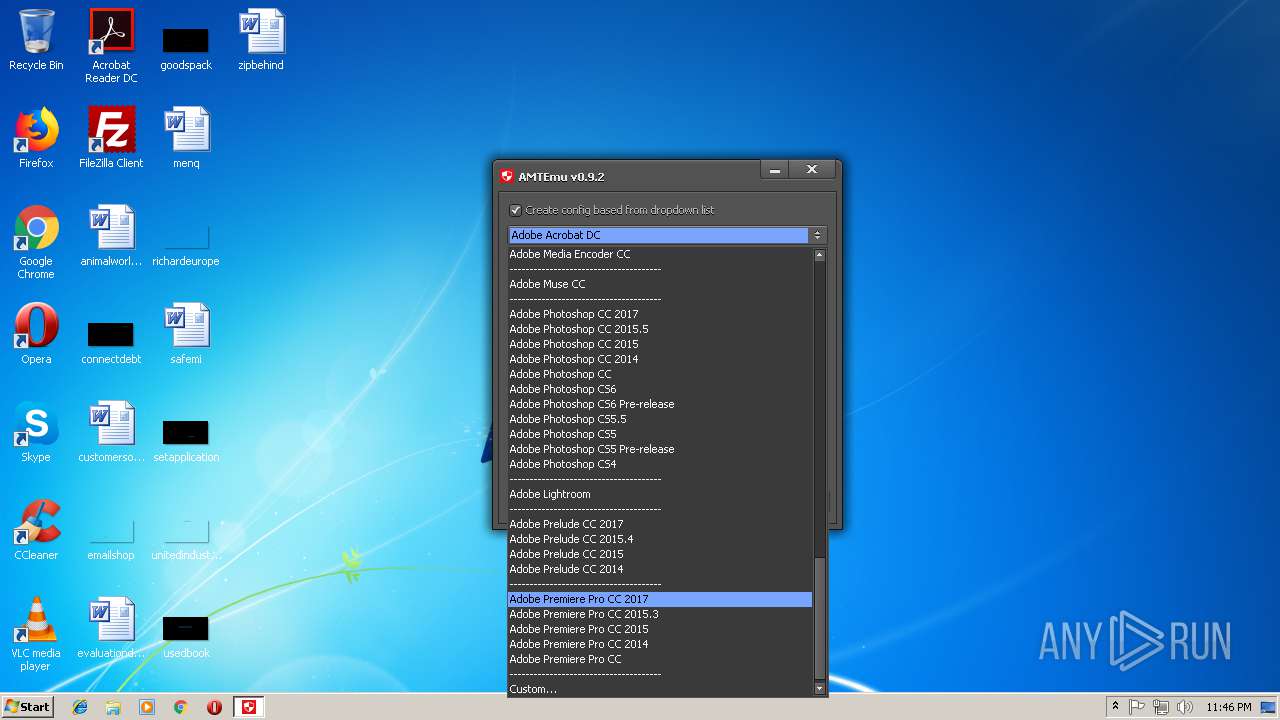
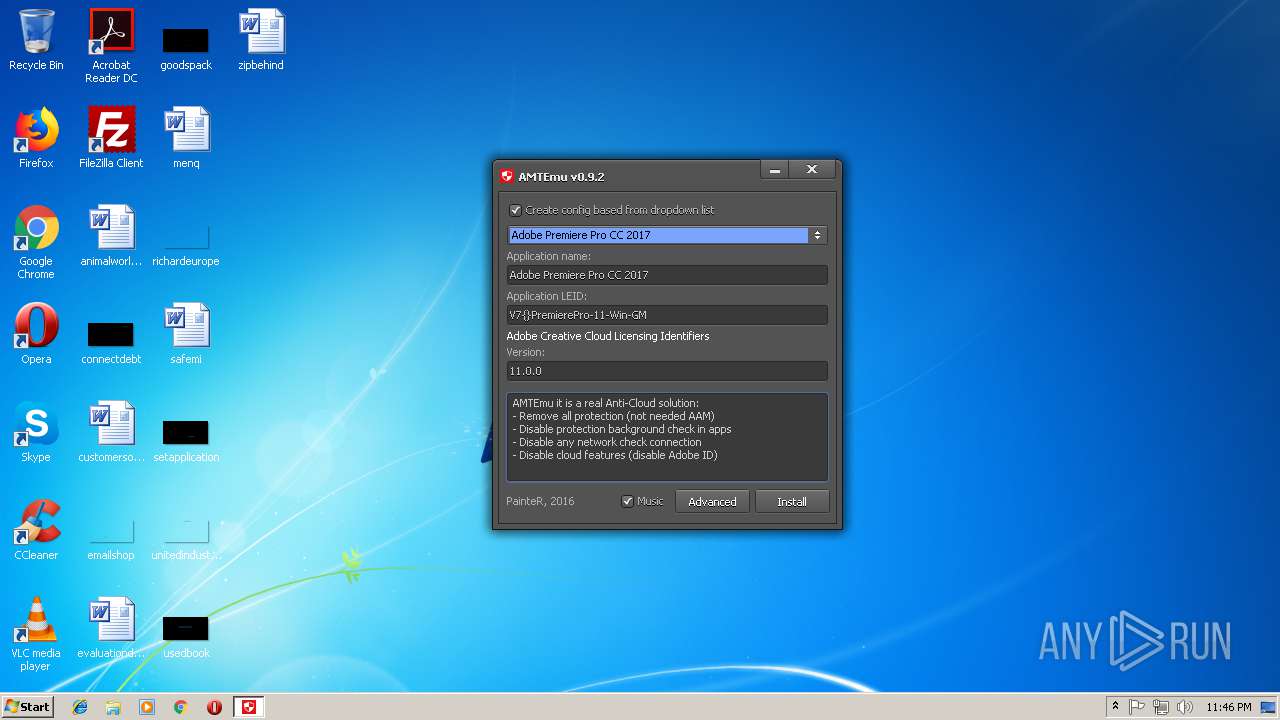
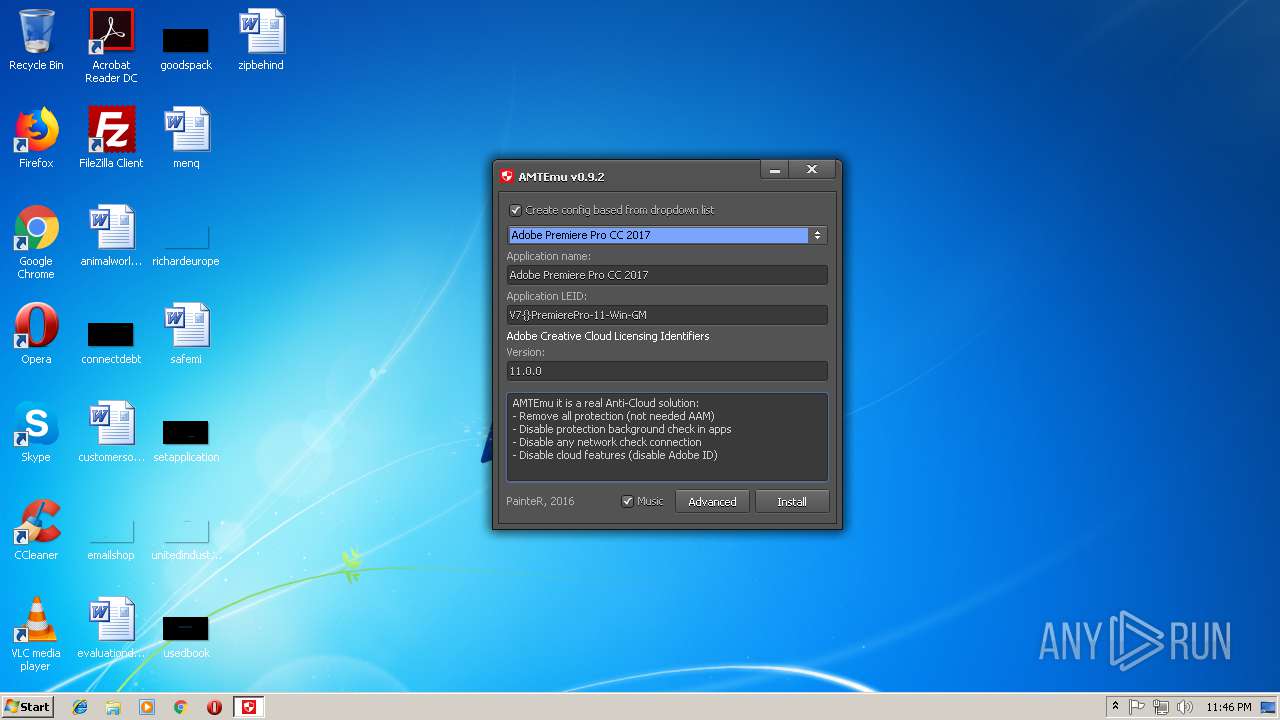
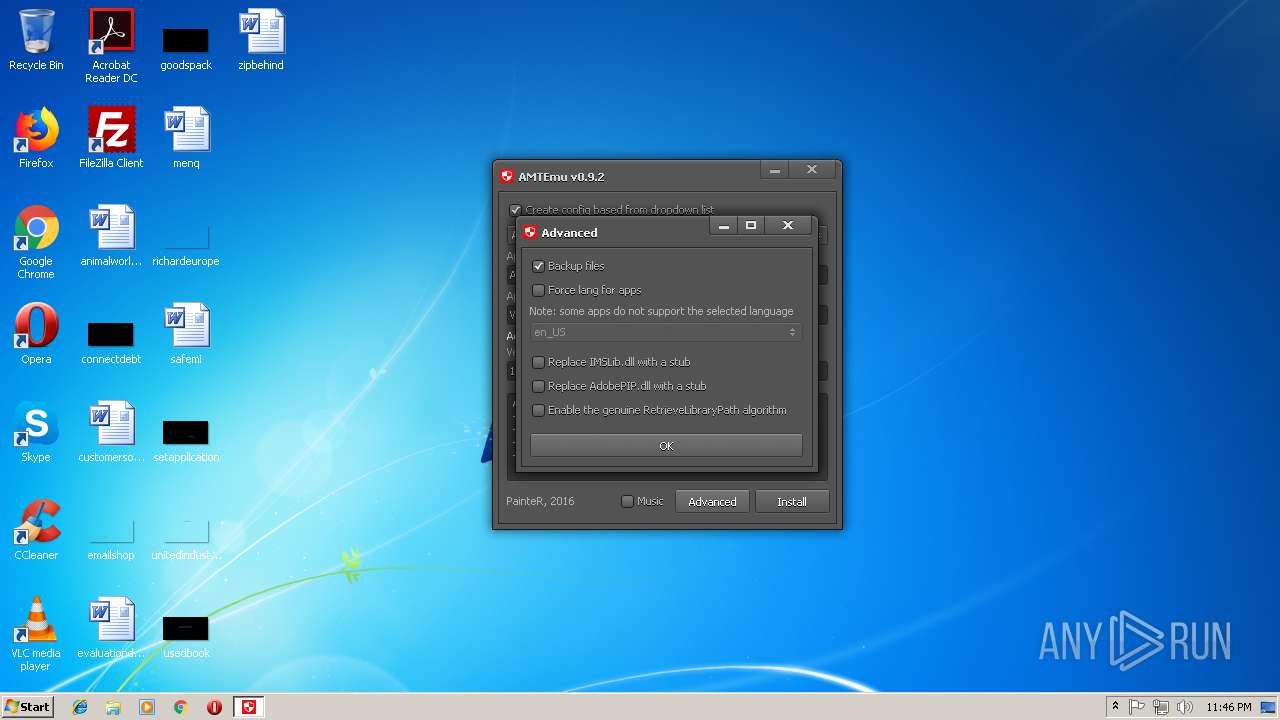
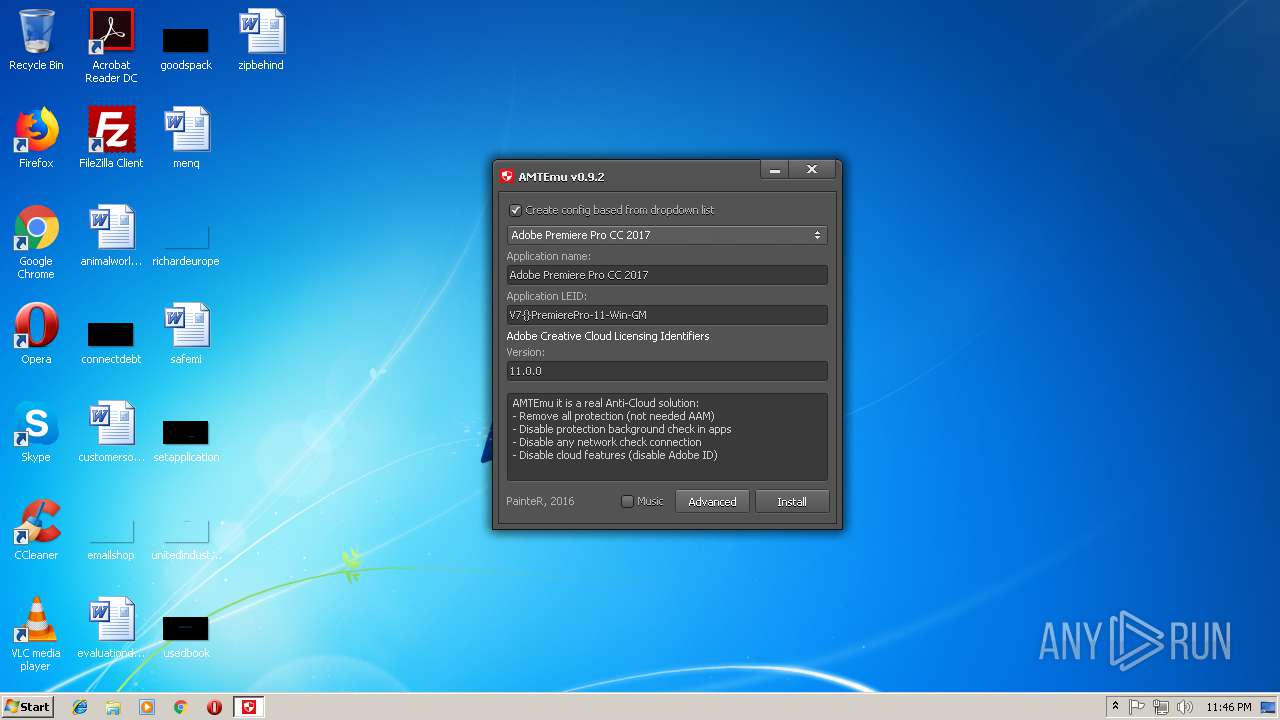
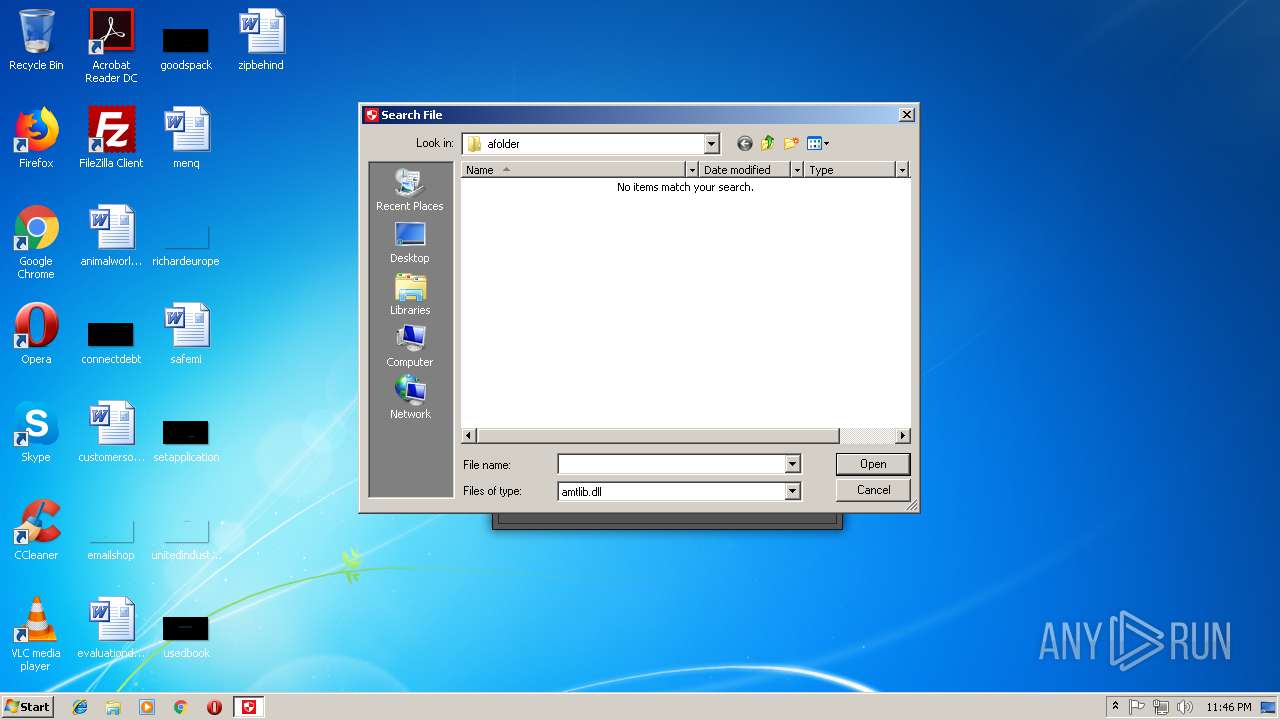
| File name: | amtemu.v0.9.2.win-painter.exe |
| Full analysis: | https://app.any.run/tasks/3a721f84-81fd-4608-be54-eacb49a08ca7 |
| Verdict: | Malicious activity |
| Analysis date: | September 21, 2018, 22:45:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CCF8784C6C5DFEA5EB96F9A1611DF6FA |
| SHA1: | A04D4025CC9281C26E8AAFE7A88CB8E75AE19417 |
| SHA256: | A05F279052E14695AA045606E966A6B1F8FED3A0EC36280F2B60A96106AF5D6D |
| SSDEEP: | 98304:6AI+60FonOHrdPfwboYZvS5DYShYF4e3P+zQhutEeo:RtYnMrdp95DYShY7yQh9v |
MALICIOUS
Loads dropped or rewritten executable
- data.dat (PID: 1072)
Application was dropped or rewritten from another process
- amtemu.v0.9.2.win-painter.exe (PID: 3872)
- data.dat (PID: 1072)
SUSPICIOUS
Starts CMD.EXE for commands execution
- amtemu.v0.9.2.win-painter.exe (PID: 3872)
Creates files in the user directory
- amtemu.v0.9.2.win-painter.exe (PID: 1904)
Executable content was dropped or overwritten
- amtemu.v0.9.2.win-painter.exe (PID: 1904)
- amtemu.v0.9.2.win-painter.exe (PID: 3872)
- data.dat (PID: 1072)
Creates files in the program directory
- amtemu.v0.9.2.win-painter.exe (PID: 1904)
Creates a software uninstall entry
- amtemu.v0.9.2.win-painter.exe (PID: 1904)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3920)
Starts application with an unusual extension
- cmd.exe (PID: 3920)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 36352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | painter |
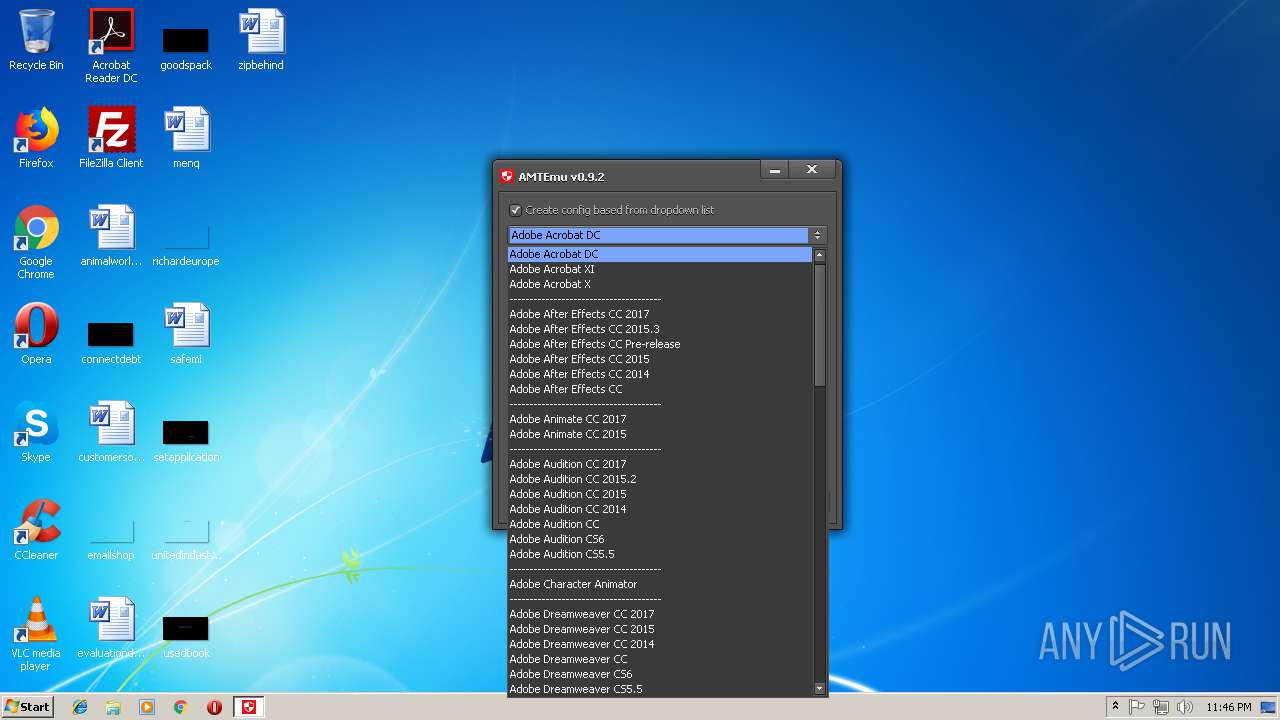
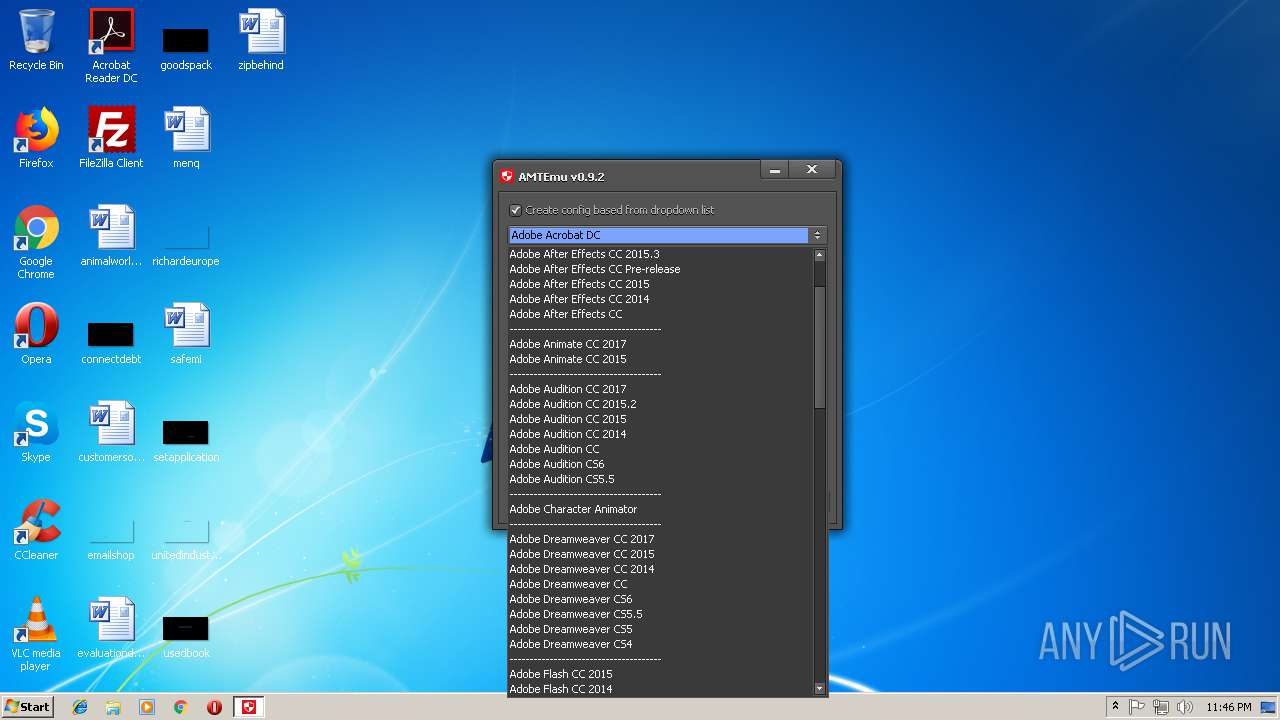
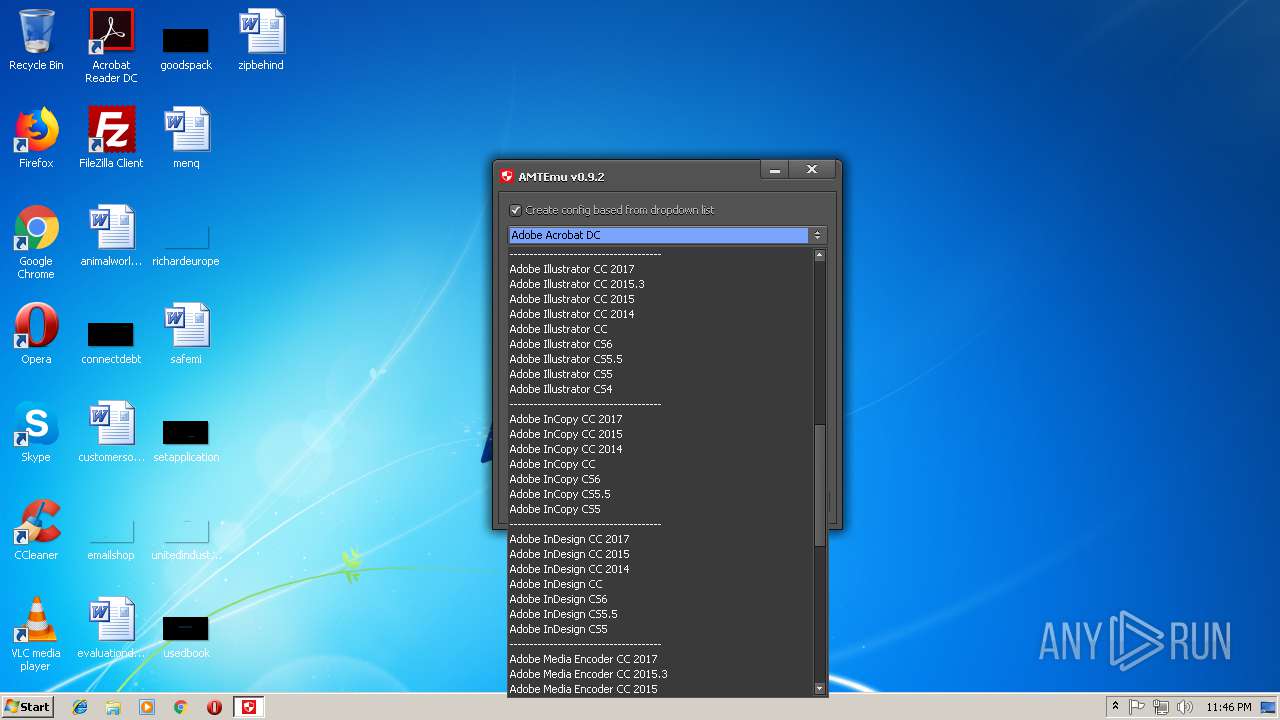
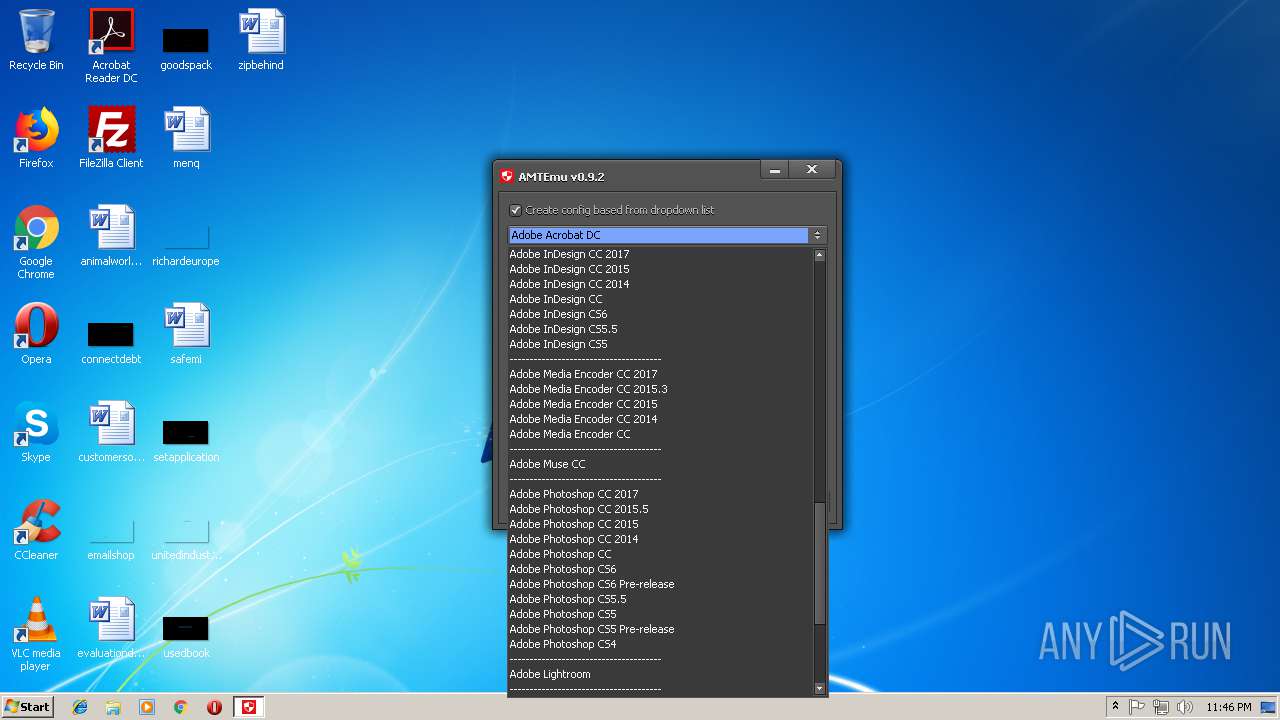
| FileDescription: | amtemu win v0.9.2 Installation |
| FileVersion: | v0.9.2 |
| LegalCopyright: | painter |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | painter |
| FileDescription: | amtemu win v0.9.2 Installation |
| FileVersion: | v0.9.2 |
| LegalCopyright: | painter |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00002FA8 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.76093 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 4.28302 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.32322 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
43
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | C:\Users\admin\AppData\Local\Temp\afolder/data.dat | C:\Users\admin\AppData\Local\Temp\afolder\data.dat | cmd.exe | ||||||||||||
User: admin Company: PainteR Integrity Level: HIGH Description: ProxyEmu Exit code: 0 Version: 0.9.2.0 Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.2.win-painter.exe" | C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.2.win-painter.exe | explorer.exe | ||||||||||||
User: admin Company: painter Integrity Level: HIGH Description: amtemu win v0.9.2 Installation Exit code: 0 Version: v0.9.2 Modules
| |||||||||||||||
| 2764 | FIND /C /I "0.0.0.0 cracksmind.com" C:\Windows\system32\drivers\etc\hosts | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.2.win-painter.exe" | C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.2.win-painter.exe | — | explorer.exe | |||||||||||
User: admin Company: painter Integrity Level: MEDIUM Description: amtemu win v0.9.2 Installation Exit code: 3221226540 Version: v0.9.2 Modules
| |||||||||||||||
| 3076 | FIND /C /I "0.0.0.0 www.cracksmind.com" C:\Windows\system32\drivers\etc\hosts | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | attrib +h C:\Users\admin\AppData\Local\Temp\ytmp | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | "C:\Program Files\painter\amtemu win\amtemu.v0.9.2.win-painter.exe" | C:\Program Files\painter\amtemu win\amtemu.v0.9.2.win-painter.exe | amtemu.v0.9.2.win-painter.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3920 | cmd /c ""C:\Users\admin\AppData\Local\Temp\ytmp\t30846.bat" "C:\Program Files\painter\amtemu win\amtemu.v0.9.2.win-painter.exe" " | C:\Windows\system32\cmd.exe | — | amtemu.v0.9.2.win-painter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
847
Read events
801
Write events
46
Delete events
0
Modification events
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | DisplayName |
Value: amtemu win v0.9.2 | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | DisplayVersion |
Value: v0.9.2 | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | VersionMajor |
Value: 0 | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | VersionMinor |
Value: 9 | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | Publisher |
Value: painter | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\painter\amtemu win\Uninstall.exe | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\painter\amtemu win\Uninstall.exe | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\painter\amtemu win\ | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | InstallSource |
Value: C:\Users\admin\AppData\Local\Temp\ | |||
| (PID) Process: | (1904) amtemu.v0.9.2.win-painter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\amtemu win v0.9.2 |
| Operation: | write | Name: | InstallDate |
Value: 20180921 | |||
Executable files
6
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1904 | amtemu.v0.9.2.win-painter.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 1904 | amtemu.v0.9.2.win-painter.exe | C:\Program Files\painter\amtemu win\Uninstall.exe | executable | |
MD5:F6511E2D0D1BB1484736AE93E128DC9C | SHA256:29CC4BCBEA00D2AE63ED5B741221C4F66FA468EC4DE3AE277E40BB8DD94B0E4D | |||
| 1904 | amtemu.v0.9.2.win-painter.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:8708699D2C73BED30A0A08D80F96D6D7 | SHA256:A32E0A83001D2C5D41649063217923DAC167809CAB50EC5784078E41C9EC0F0F | |||
| 1904 | amtemu.v0.9.2.win-painter.exe | C:\Program Files\painter\amtemu win\amtemu.v0.9.2.win-painter.exe | executable | |
MD5:2E9A254AFCBE642002496A5868EE0B4D | SHA256:CD2D4BC6CAD84FFBE5F77C690EAFF42EA73336A8A89BB9A2A76E8C0B97CE601B | |||
| 1904 | amtemu.v0.9.2.win-painter.exe | C:\Users\admin\AppData\Roaming\launch.exe | executable | |
MD5:5D12FB72AED3759A31FEF3E4CDE0ADF0 | SHA256:F178C49E703CDCDDF430B8608D04F76037F05DEDA8DE64FED3DFFFD5BDE2F07A | |||
| 1904 | amtemu.v0.9.2.win-painter.exe | C:\Program Files\painter\amtemu win\Uninstall.ini | text | |
MD5:CEBCF3425C1D4CC9B525B8403F2A7B13 | SHA256:042D3BB92AFA444E658FBEE164E5CF7DE31839228D3D050B684B770381B3D1AE | |||
| 3920 | cmd.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:D45E623933C1783E87EA79614EEFCF52 | SHA256:1D407E60A4A9EA95B9F3E8ADC47D37FC90140327260ACE83294A58BB789CAED6 | |||
| 3872 | amtemu.v0.9.2.win-painter.exe | C:\Users\admin\AppData\Local\Temp\ytmp\t30846.bat | text | |
MD5:0CF1AD1D592C3463EBEE17FAEBC404D7 | SHA256:EC7851ECB3822F6B77118A8F3BF30B27162640896DDECDD8AB732F9645D1915E | |||
| 3872 | amtemu.v0.9.2.win-painter.exe | C:\Users\admin\AppData\Local\Temp\ytmp\t30898.exe | text | |
MD5:3C52638971EAD82B5929D605C1314EE0 | SHA256:5614459EC05FDF6110FA8CE54C34E859671EEFFBA2B7BB4B1AD6C2C6706855AB | |||
| 1072 | data.dat | C:\Users\admin\AppData\Local\Temp\spc_player.dll | executable | |
MD5:41AFBF49BA7F6EE164F31FAA2CD38E15 | SHA256:50D30B7AA7B9858F91F33165314C7CF7F2ACC97157091676C7E7925E018FD387 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report