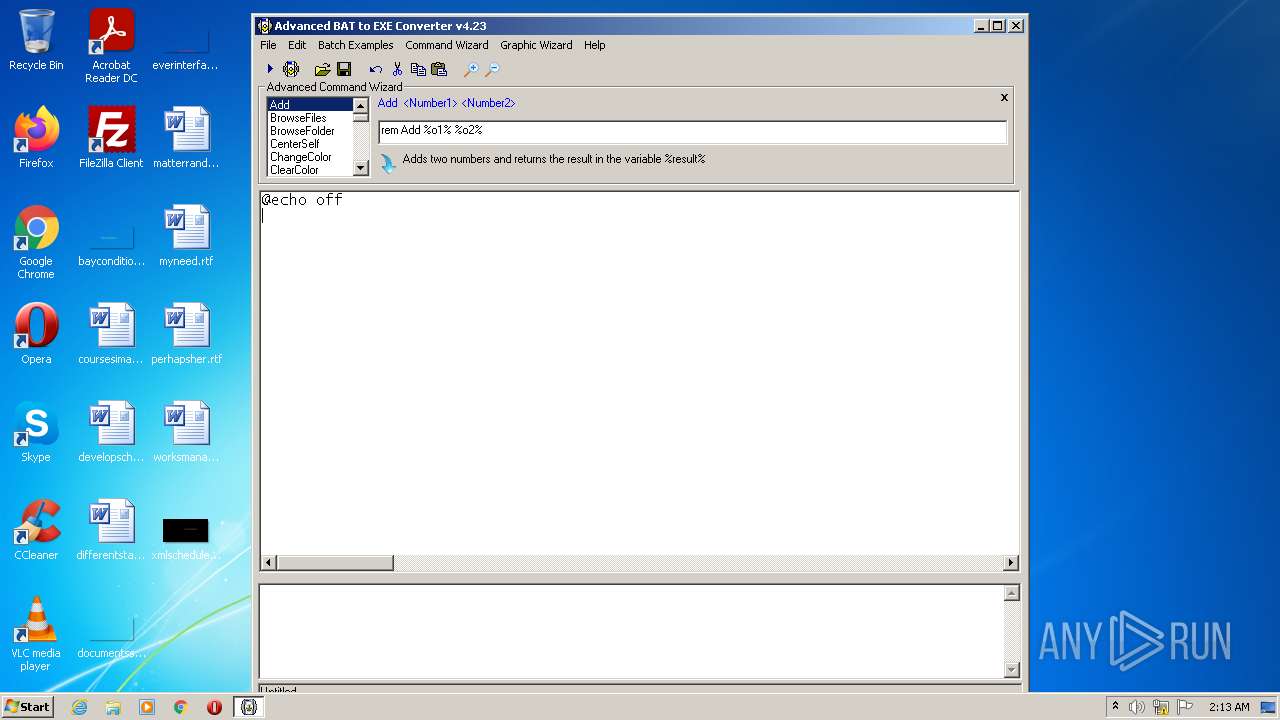
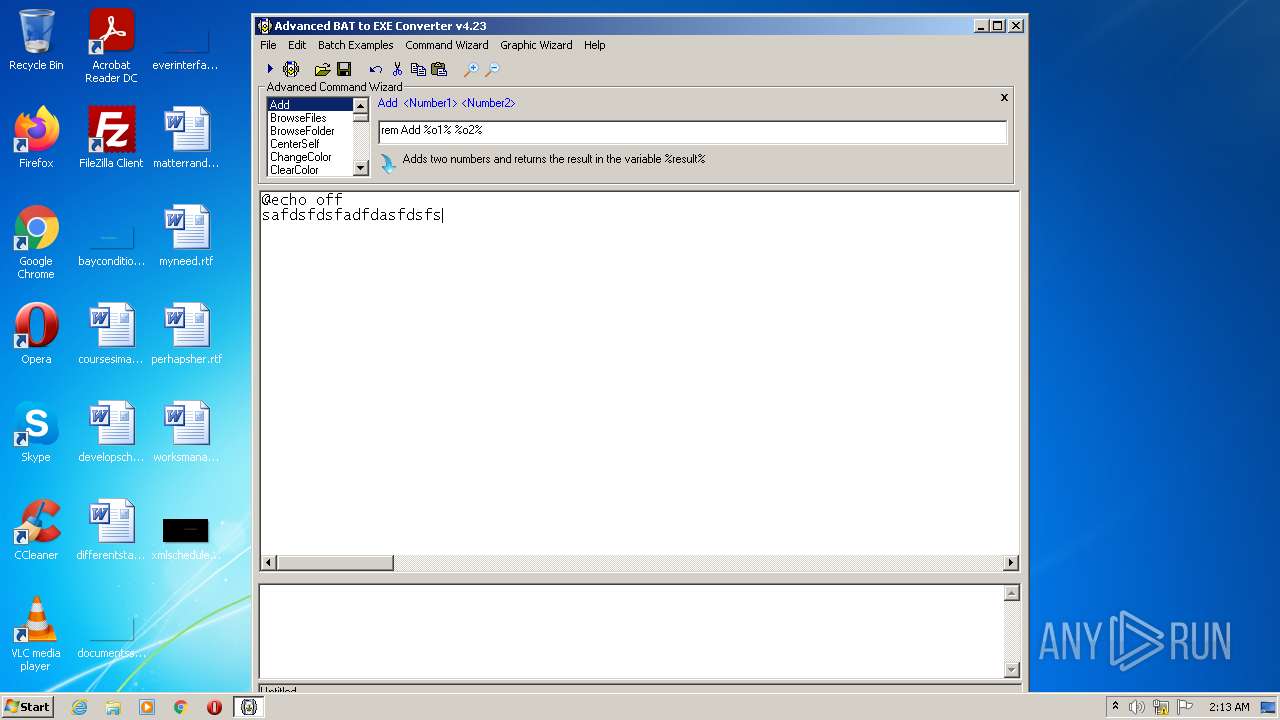
| File name: | advancedbattoexeconverter.exe |
| Full analysis: | https://app.any.run/tasks/1674eac3-ab40-440c-8eda-edfbfd673bb2 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 01:13:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2D6CF8E30B05F0D70791FEEE8EFC501C |
| SHA1: | 7E38040B498B95AD8ED60E2D7D66B3B61003275E |
| SHA256: | A058E6F1AE42EC1E0F09C8D23F50DC87ED8898E5D5EE0D2E18031CDF59679EB6 |
| SSDEEP: | 24576:HxF2L4a+4LXECLp0cPydrb2gkFby3w4FZm9oC:H+Lb+MX9KEydrSlFby3wZ9oC |
MALICIOUS
Drops executable file immediately after starts
- advancedbattoexeconverter.exe (PID: 3748)
Loads dropped or rewritten executable
- advancedbattoexeconverter.exe (PID: 3748)
- aB2Econv.exe (PID: 1996)
Application was dropped or rewritten from another process
- setupinf.exe (PID: 2332)
- aB2Econv.exe (PID: 1996)
- gewizold.exe (PID: 3084)
SUSPICIOUS
Drops a file with a compile date too recent
- advancedbattoexeconverter.exe (PID: 3748)
Checks supported languages
- advancedbattoexeconverter.exe (PID: 3748)
- setupinf.exe (PID: 2332)
- aB2Econv.exe (PID: 1996)
- gewizold.exe (PID: 3084)
Reads the computer name
- advancedbattoexeconverter.exe (PID: 3748)
- aB2Econv.exe (PID: 1996)
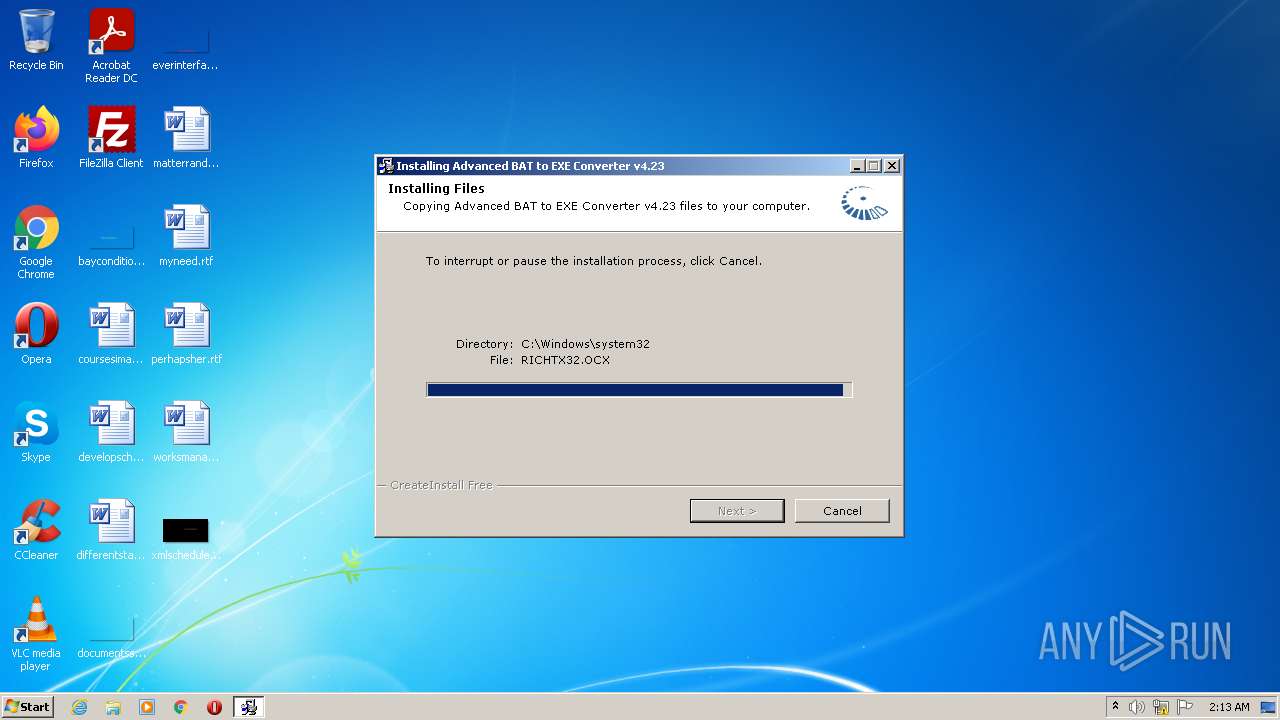
Creates files in the Windows directory
- advancedbattoexeconverter.exe (PID: 3748)
Executable content was dropped or overwritten
- advancedbattoexeconverter.exe (PID: 3748)
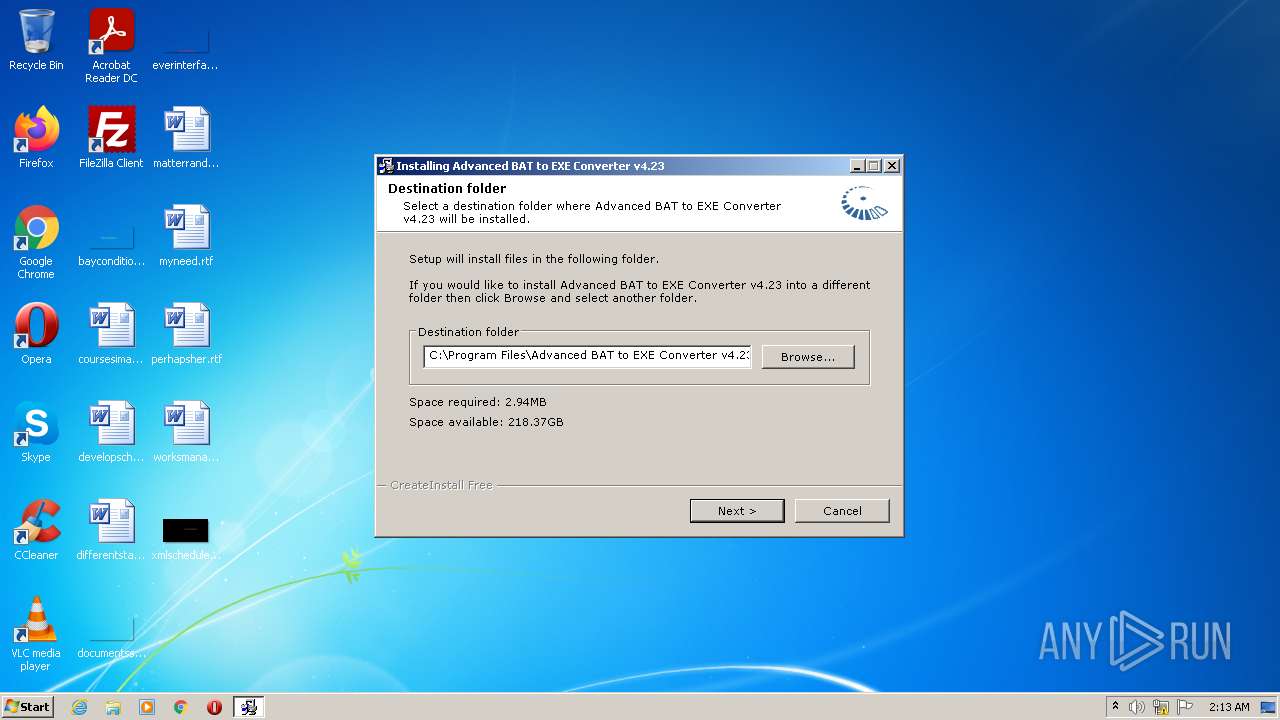
Creates a directory in Program Files
- advancedbattoexeconverter.exe (PID: 3748)
Creates files in the program directory
- advancedbattoexeconverter.exe (PID: 3748)
Creates files in the user directory
- advancedbattoexeconverter.exe (PID: 3748)
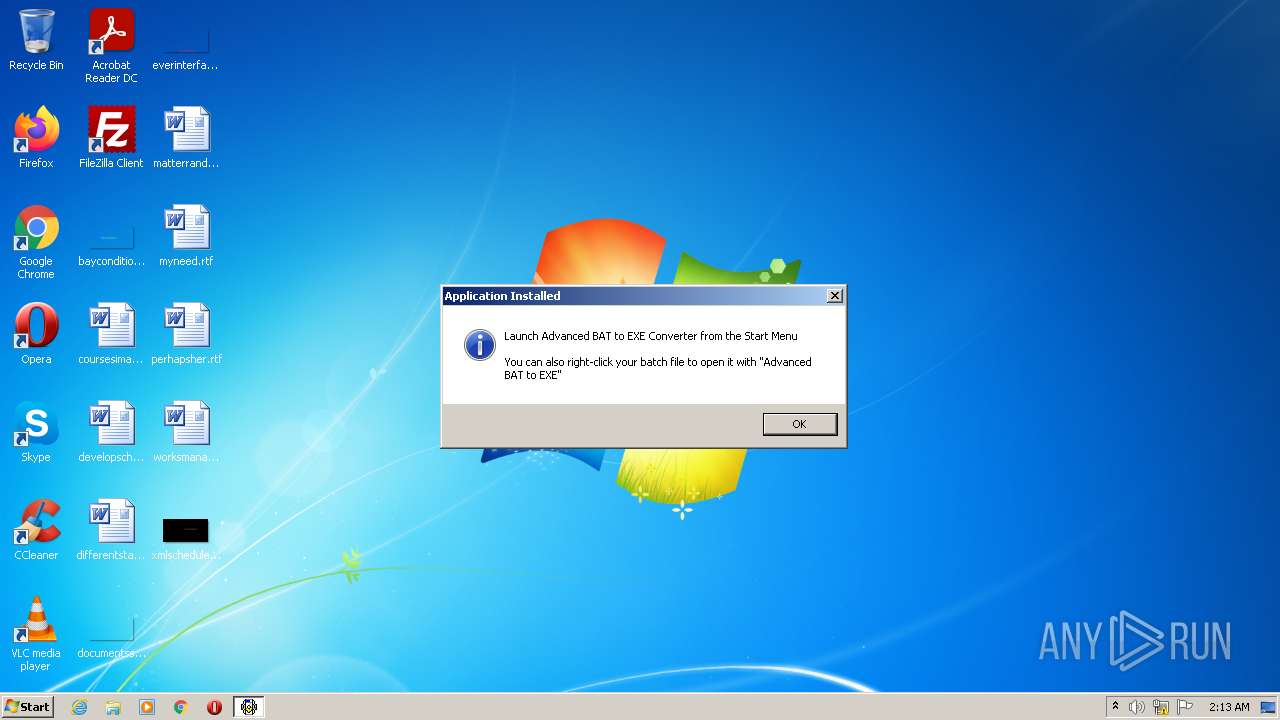
Creates a software uninstall entry
- advancedbattoexeconverter.exe (PID: 3748)
Changes default file association
- setupinf.exe (PID: 2332)
INFO
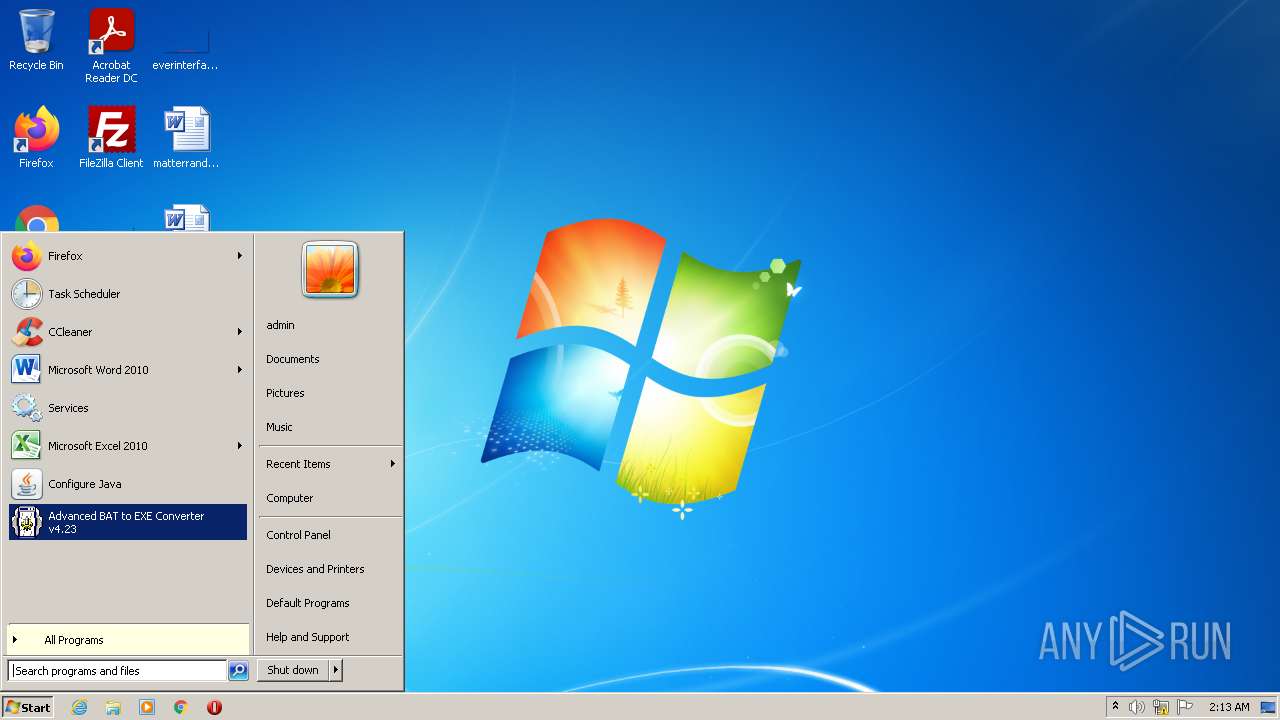
Manual execution by user
- aB2Econv.exe (PID: 1996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1226 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 94208 |
| CodeSize: | 3584 |
| LinkerVersion: | 3 |
| PEType: | PE32 |
| TimeStamp: | 2006:04:05 10:55:39+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Apr-2006 08:55:39 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 05-Apr-2006 08:55:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C91 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.93214 |
.rdata | 0x00002000 | 0x00000078 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.731255 |
.data | 0x00003000 | 0x00000504 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12782 |
.idata | 0x00004000 | 0x000002B0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.45462 |
.reloc | 0x00005000 | 0x0000012C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.28756 |
.gentee | 0x00006000 | 0x00013ACB | 0x00013C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99579 |
.rsrc | 0x0001A000 | 0x0000274C | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.02613 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99128 | 784 | Latin 1 / Western European | English - United States | RT_MANIFEST |
1000 | 2.23119 | 54 | Latin 1 / Western European | English - United States | RT_DIALOG |
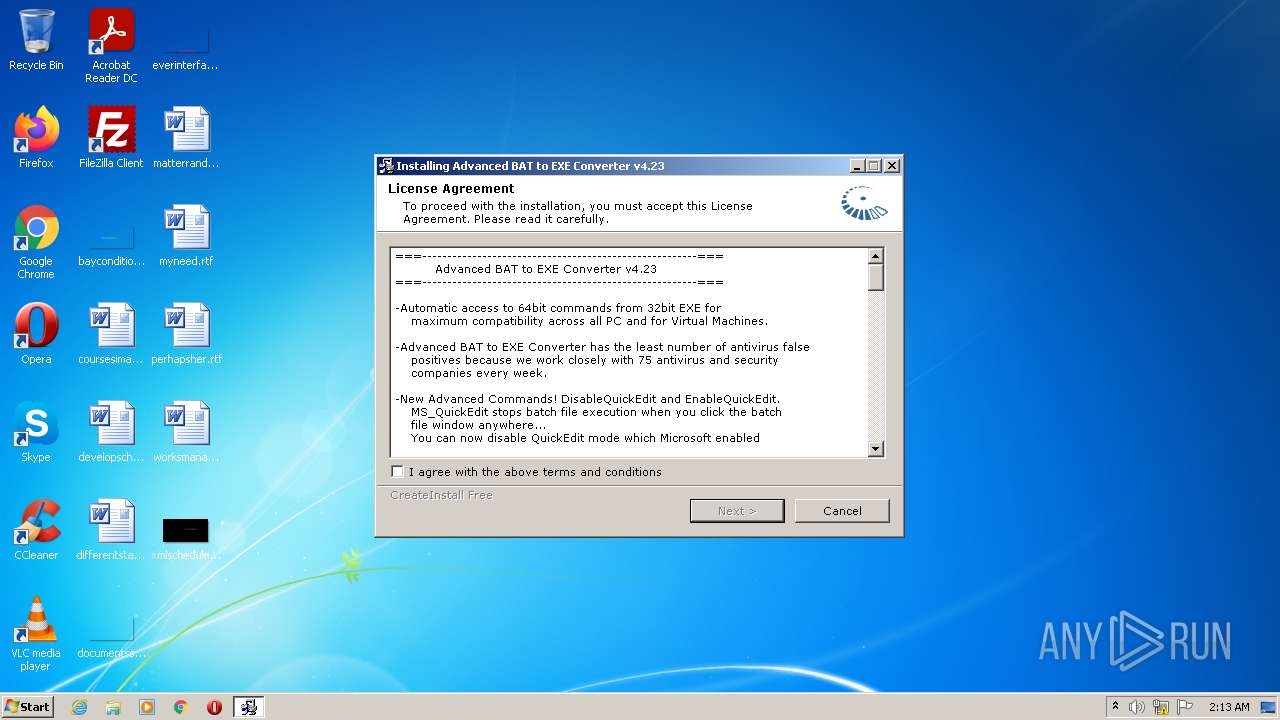
IDD_DLGLIC | 2.66912 | 440 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGPATH | 2.69399 | 640 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGPROG | 2.70702 | 568 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGUCONF | 2.54565 | 376 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGUFIN | 2.60408 | 440 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGUNDEL | 2.6827 | 504 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGUPROG | 2.71234 | 504 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
SETUP_TEMP | 7.90822 | 4055 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
40
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1996 | "C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\aB2Econv.exe" | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\aB2Econv.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Brandon Dargo Integrity Level: MEDIUM Description: Advanced BAT to EXE Converter Exit code: 0 Version: 4.02.0003 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\setupinf.exe" | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\setupinf.exe | — | advancedbattoexeconverter.exe | |||||||||||
User: admin Company: Brandon Dargo Integrity Level: HIGH Exit code: 0 Version: 1.02.0003 Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\AppData\Local\Temp\advancedbattoexeconverter.exe" | C:\Users\admin\AppData\Local\Temp\advancedbattoexeconverter.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
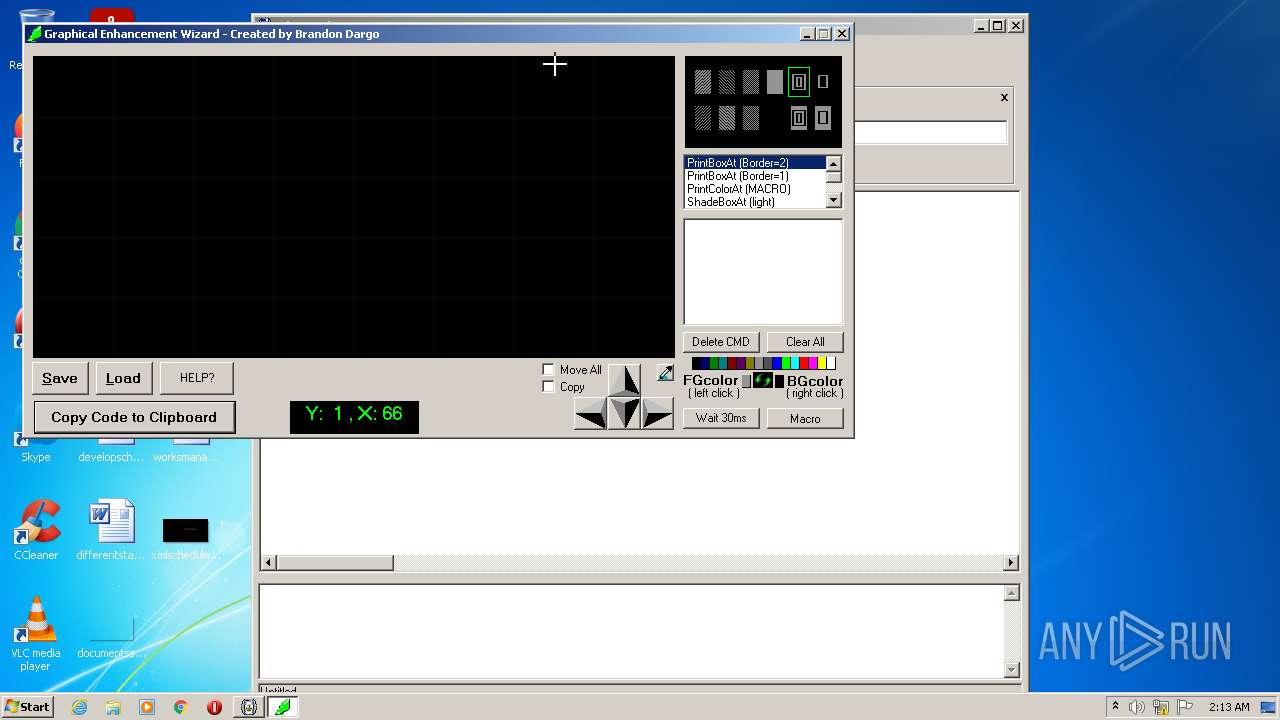
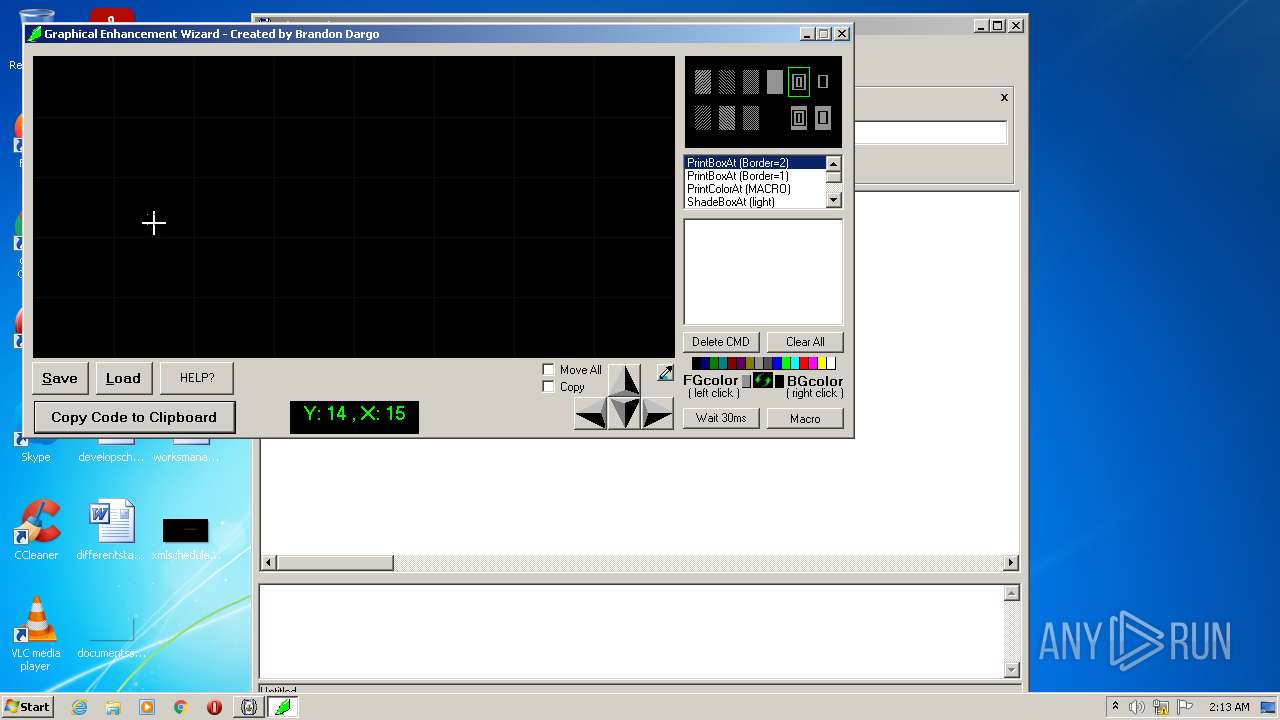
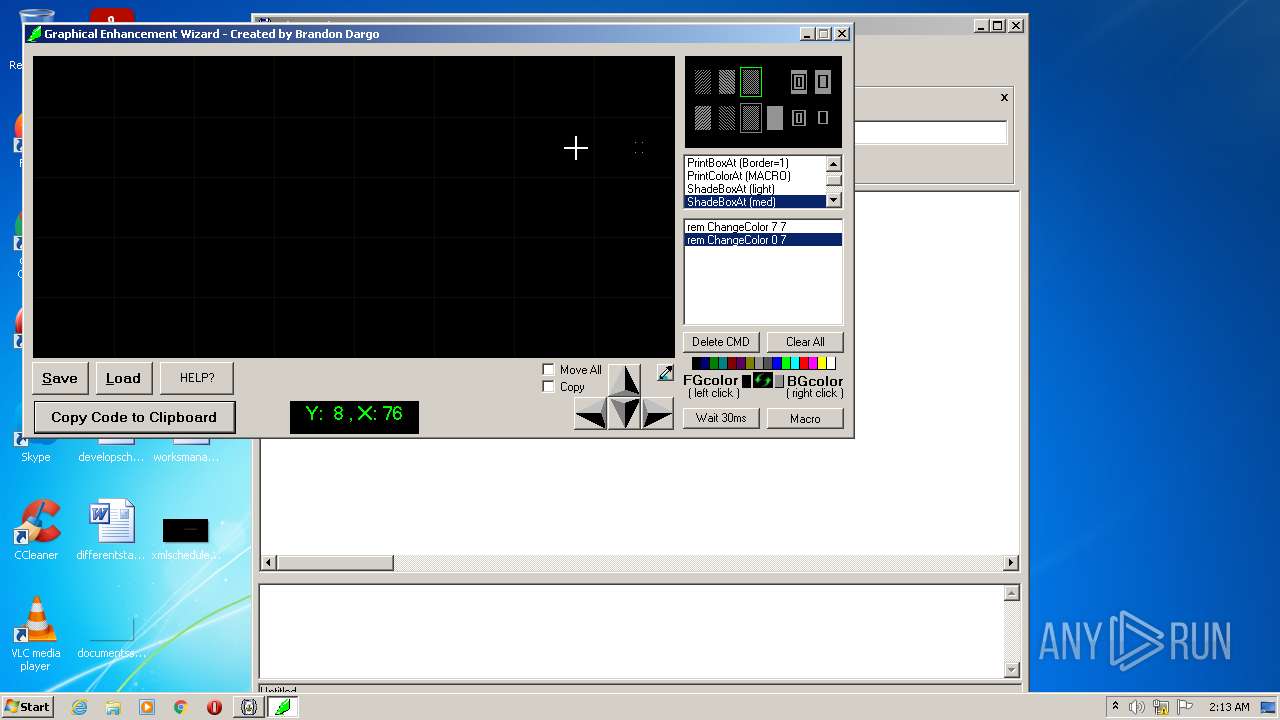
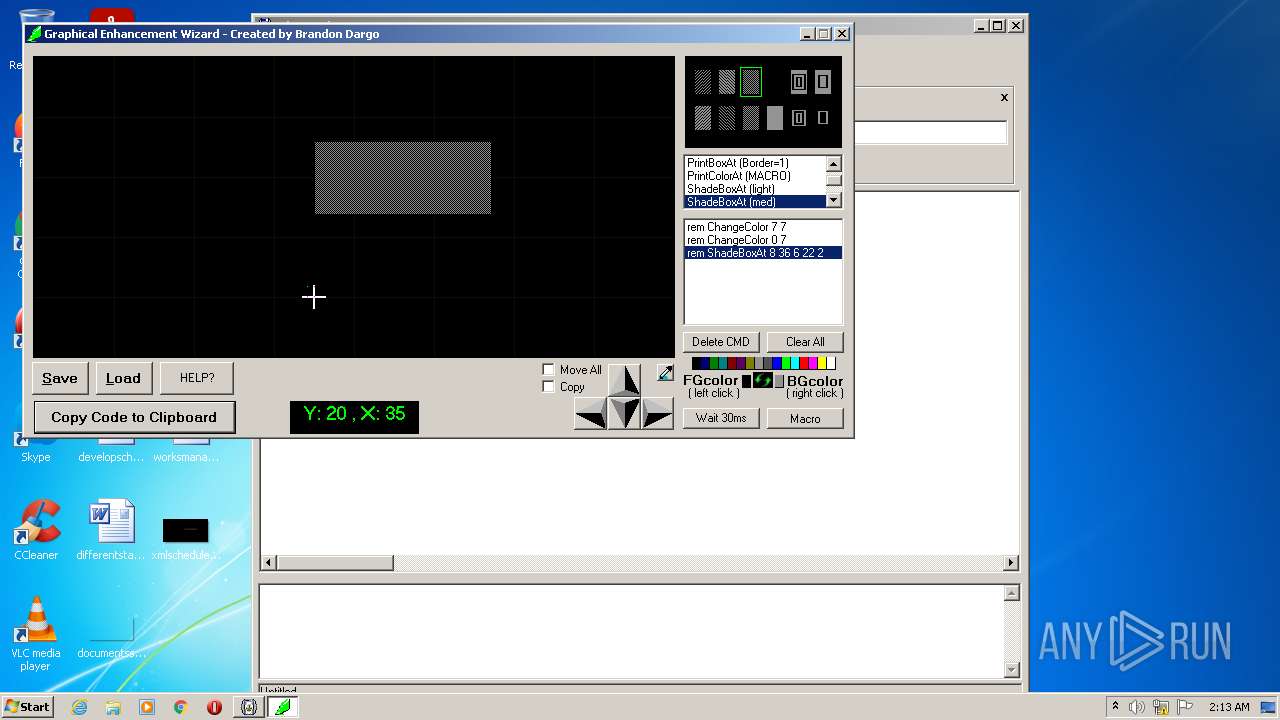
| 3084 | "C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\gewizold.exe" | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\gewizold.exe | — | aB2Econv.exe | |||||||||||
User: admin Company: Brandon Dargo Integrity Level: MEDIUM Description: Graphical Enhancement Wizard Exit code: 0 Version: 1.02.0001 Modules
| |||||||||||||||
| 3748 | "C:\Users\admin\AppData\Local\Temp\advancedbattoexeconverter.exe" | C:\Users\admin\AppData\Local\Temp\advancedbattoexeconverter.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
735
Read events
662
Write events
69
Delete events
4
Modification events
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.23 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Advanced BAT to EXE Converter v4.23\uninstall.exe | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.23 |
| Operation: | write | Name: | DisplayName |
Value: Advanced BAT to EXE Converter v4.23 | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.23 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Advanced BAT to EXE Converter v4.23\uninstall.exe | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | write | Name: | (default) |
Value: Microsoft Rich Textbox Control 6.0 (SP6) | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402}\InprocServer32 |
| Operation: | write | Name: | (default) |
Value: C:\Windows\system32\richtx32.ocx | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl |
| Operation: | write | Name: | (default) |
Value: Microsoft Rich Textbox Control 6.0 (SP6) | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl\CLSID |
| Operation: | write | Name: | (default) |
Value: {3B7C8860-D78F-101B-B9B5-04021C009402} | |||
| (PID) Process: | (3748) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl\CurVer |
| Operation: | write | Name: | (default) |
Value: RICHTEXT.RichtextCtrl.1 | |||
Executable files
21
Suspicious files
3
Text files
43
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex14.bat | text | |
MD5:79EFF151EC11085AB1E14791C5D4D07A | SHA256:AD772C3699E86C10610A38463C8EE3DF2F1E638AB80654D021CBC32743554D8B | |||
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex11.bat | text | |
MD5:7BE37BB8BCC1AC84ABFB9569C28432E1 | SHA256:EB6A82A5369740AC950B85760E0AE4603CBE2BD9BE4841A69BC31CF8FA2EF3E5 | |||
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex15.bat | text | |
MD5:F5395EEA41ACB0196D9C6052B1E3DE06 | SHA256:AD46E63B04055EC4D929AA354BBC00C5E42B8014B0644838AB4859F5CD2D3FB1 | |||
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex17.bat | text | |
MD5:1FD8C3EC584D29ACB9428925D803BBAE | SHA256:47D5D77316B3E4D5861B21A2BA8DC4C74C5EC686C7F5720DB3C6CE408A39C650 | |||
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex2.bat | text | |
MD5:BB7972CB0A6902528FDBB2EE7F30D09C | SHA256:DA8137F6FC37394B0270D24FB00097A56A37E6D826C1A0F71305574B9F1959E1 | |||
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex5.bat | text | |
MD5:0B17712F708EC60A62716D1EAC91AA90 | SHA256:8A329A671D7C9B3E8EC5B7FFE313CF48529E1A8F6AFF144DE46F86E19107CE96 | |||
| 3748 | advancedbattoexeconverter.exe | C:\Users\admin\AppData\Local\Temp\gentee00\gentee.dll | executable | |
MD5:30439E079A3D603C461D2C2F4F8CB064 | SHA256:D6D0535175FB2302E5B5A498119823C37F6BDDFF4AB24F551AA7E038C343077A | |||
| 3748 | advancedbattoexeconverter.exe | C:\Users\admin\AppData\Local\Temp\gentee00\setup_temp.gea | bs | |
MD5:594F8504C92BCB9678044185902EFB7E | SHA256:703F4BDA8E27415B03DE531284C8559D987F1AFF54FB4D4ACB27CD0039BAF38E | |||
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex10.bat | text | |
MD5:968E898D05ACAF33A5008BE202F5DE7F | SHA256:86785CFD394E139A5325DCA33E4C3D1B69FE3F5F4229F00445AE86C592DF6BCC | |||
| 3748 | advancedbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.23\ab2econv423\advex3.bat | text | |
MD5:81A308FABAFB9FEF3F104B5E90E0AF3B | SHA256:E61754F1119B9BD7240935FB28F5759E093F281B51356E7925E54DD1B436DD57 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report