| File name: | apowermirror-setup.exe |
| Full analysis: | https://app.any.run/tasks/d6f85365-e08d-45f6-a759-a471cebde1ae |
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2021, 13:27:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EE7ADD8DF6AE902757EA73286BBE7854 |
| SHA1: | D1C5E48C7F603D0CA8D60103D5000FA179C6FE6D |
| SHA256: | A05263B8DF7764C6CEB033AA81BC0E1C28D953F23B20EEFC7FE8C8F56F1A8192 |
| SSDEEP: | 49152:5pBedV1Wzv4HAYl30FzozCKoDsT2C3xT+6pbJy:5bc7MdozCdDC3k |
MALICIOUS
Drops executable file immediately after starts
- installer.tmp (PID: 3964)
- installer.exe (PID: 676)
- msiexec.exe (PID: 3596)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2560)
- apowermirror-setup.exe (PID: 580)
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 2176)
- ApowerMirror.exe (PID: 3672)
- svchost.exe (PID: 1672)
- ApowerMirror.exe (PID: 2176)
- ApowerMirror.exe (PID: 3244)
Application was dropped or rewritten from another process
- mDNSResponder.exe (PID: 2240)
- ApowerMirror.exe (PID: 3672)
- ApowerMirror.exe (PID: 3244)
- ApowerMirror.exe (PID: 2176)
Changes settings of System certificates
- svchost.exe (PID: 1672)
SUSPICIOUS
Checks supported languages
- apowermirror-setup.exe (PID: 580)
- installer.exe (PID: 676)
- installer.tmp (PID: 3964)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 1508)
- mDNSResponder.exe (PID: 2240)
- ApowerMirror.exe (PID: 3672)
- ApowerMirror.exe (PID: 3244)
- ApowerMirror.exe (PID: 2176)
Reads the computer name
- apowermirror-setup.exe (PID: 580)
- installer.tmp (PID: 3964)
- mDNSResponder.exe (PID: 2240)
- ApowerMirror.exe (PID: 3672)
- ApowerMirror.exe (PID: 3244)
- ApowerMirror.exe (PID: 2176)
Creates a directory in Program Files
- apowermirror-setup.exe (PID: 580)
- installer.tmp (PID: 3964)
- msiexec.exe (PID: 3596)
Reads Windows owner or organization settings
- installer.tmp (PID: 3964)
- msiexec.exe (PID: 3596)
Executable content was dropped or overwritten
- installer.exe (PID: 676)
- installer.tmp (PID: 3964)
- msiexec.exe (PID: 3596)
Reads the Windows organization settings
- installer.tmp (PID: 3964)
- msiexec.exe (PID: 3596)
Application launched itself
- cmd.exe (PID: 2436)
- cmd.exe (PID: 1508)
- msiexec.exe (PID: 3596)
Starts CMD.EXE for commands execution
- installer.tmp (PID: 3964)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 1508)
Drops a file with too old compile date
- installer.tmp (PID: 3964)
- msiexec.exe (PID: 3596)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2376)
- cmd.exe (PID: 4020)
Uses TASKKILL.EXE to kill process
- installer.tmp (PID: 3964)
Drops a file that was compiled in debug mode
- installer.tmp (PID: 3964)
- msiexec.exe (PID: 3596)
Executed as Windows Service
- msiexec.exe (PID: 3596)
- mDNSResponder.exe (PID: 2240)
Creates files in the user directory
- installer.tmp (PID: 3964)
- ApowerMirror.exe (PID: 3672)
Starts Microsoft Installer
- installer.tmp (PID: 3964)
Searches for installed software
- installer.tmp (PID: 3964)
Creates files in the program directory
- msiexec.exe (PID: 3596)
Creates files in the Windows directory
- msiexec.exe (PID: 3596)
- svchost.exe (PID: 1672)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3596)
Creates a software uninstall entry
- msiexec.exe (PID: 3596)
Changes IE settings (feature browser emulation)
- installer.tmp (PID: 3964)
Uses NETSH.EXE for network configuration
- installer.tmp (PID: 3964)
Reads Environment values
- netsh.exe (PID: 1036)
- netsh.exe (PID: 2408)
- netsh.exe (PID: 3084)
- ApowerMirror.exe (PID: 3672)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2176)
- ApowerMirror.exe (PID: 3672)
Removes files from Windows directory
- svchost.exe (PID: 1672)
Starts Internet Explorer
- apowermirror-setup.exe (PID: 580)
Executed via COM
- POWERPNT.EXE (PID: 1276)
Uses NETSTAT.EXE to discover network connections
- ApowerMirror.exe (PID: 3672)
Reads internet explorer settings
- ApowerMirror.exe (PID: 3672)
INFO
Checks supported languages
- tasklist.exe (PID: 3008)
- find.exe (PID: 2632)
- taskkill.exe (PID: 2504)
- tasklist.exe (PID: 2384)
- taskkill.exe (PID: 2092)
- find.exe (PID: 1956)
- msiexec.exe (PID: 3772)
- msiexec.exe (PID: 3596)
- MsiExec.exe (PID: 1256)
- MsiExec.exe (PID: 1588)
- MsiExec.exe (PID: 2560)
- netsh.exe (PID: 1036)
- netsh.exe (PID: 2408)
- netsh.exe (PID: 3084)
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 2176)
- svchost.exe (PID: 1672)
- netstat.exe (PID: 1840)
- POWERPNT.EXE (PID: 1276)
- WISPTIS.EXE (PID: 3624)
- taskmgr.exe (PID: 2140)
Reads the computer name
- tasklist.exe (PID: 3008)
- taskkill.exe (PID: 2504)
- taskkill.exe (PID: 2092)
- tasklist.exe (PID: 2384)
- msiexec.exe (PID: 3772)
- msiexec.exe (PID: 3596)
- MsiExec.exe (PID: 1256)
- MsiExec.exe (PID: 1588)
- netsh.exe (PID: 1036)
- netsh.exe (PID: 2408)
- netsh.exe (PID: 3084)
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 2176)
- netstat.exe (PID: 1840)
- POWERPNT.EXE (PID: 1276)
- WISPTIS.EXE (PID: 3624)
- taskmgr.exe (PID: 2140)
Application was dropped or rewritten from another process
- installer.tmp (PID: 3964)
Loads dropped or rewritten executable
- installer.tmp (PID: 3964)
Checks Windows Trust Settings
- msiexec.exe (PID: 3596)
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 2176)
Reads settings of System Certificates
- msiexec.exe (PID: 3596)
- iexplore.exe (PID: 2176)
- svchost.exe (PID: 1672)
- iexplore.exe (PID: 3300)
- ApowerMirror.exe (PID: 3672)
Check for Java to be installed
- MsiExec.exe (PID: 1256)
Creates files in the program directory
- installer.tmp (PID: 3964)
Creates a software uninstall entry
- installer.tmp (PID: 3964)
Changes internet zones settings
- iexplore.exe (PID: 3300)
Application launched itself
- iexplore.exe (PID: 3300)
Creates files in the user directory
- iexplore.exe (PID: 2176)
Reads the date of Windows installation
- iexplore.exe (PID: 3300)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2176)
Changes settings of System certificates
- iexplore.exe (PID: 2176)
Reads internet explorer settings
- iexplore.exe (PID: 2176)
Reads the hosts file
- ApowerMirror.exe (PID: 3672)
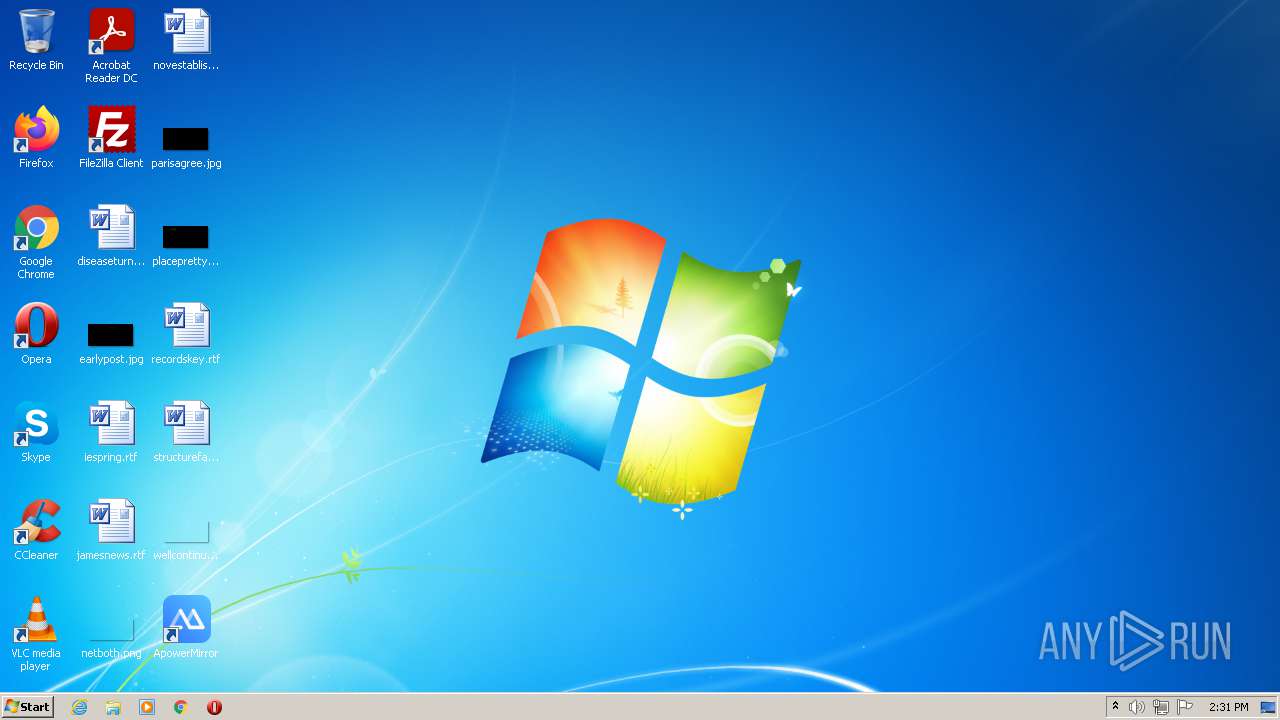
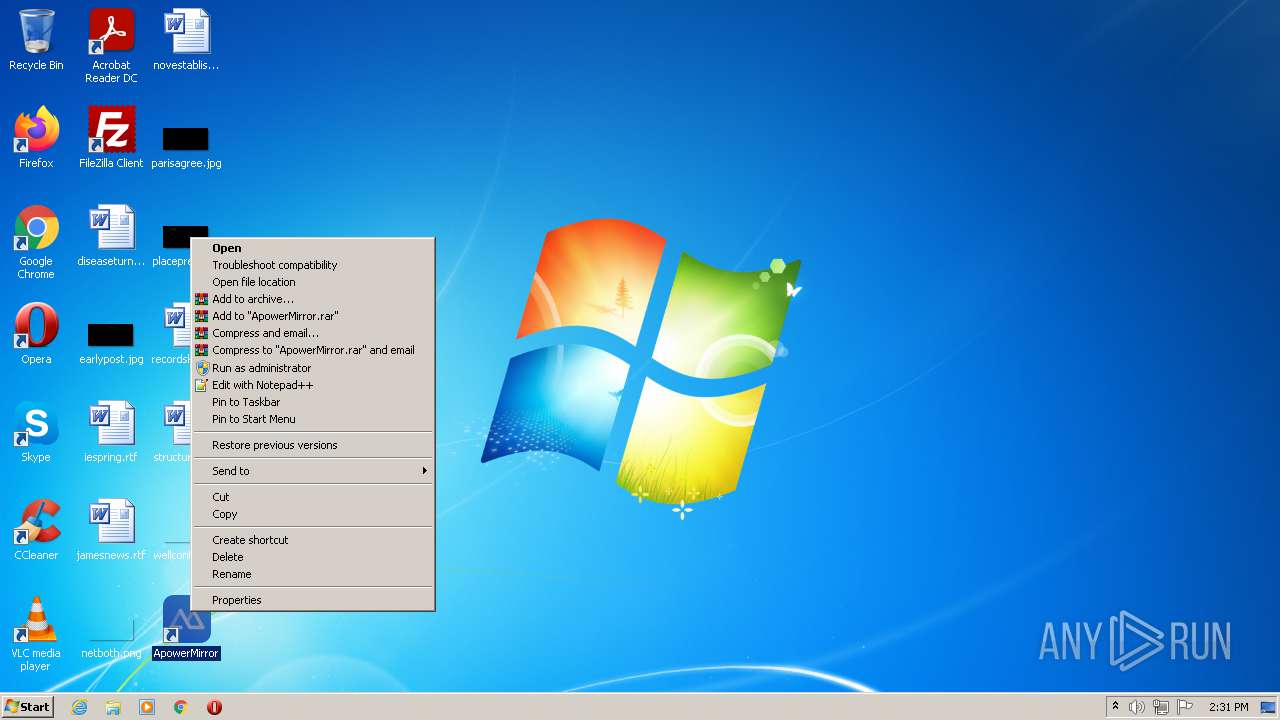
Manual execution by user
- ApowerMirror.exe (PID: 3672)
- ApowerMirror.exe (PID: 2176)
- ApowerMirror.exe (PID: 3244)
- taskmgr.exe (PID: 2140)
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 1276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| ProductVersion: | 1.1.1.2 |
|---|---|
| ProductName: | Apowersoft Installer |
| OriginalFileName: | Apowersoft Installer.exe |
| LegalCopyright: | Copyright (C) 2020 Apowersoft Ltd. |
| InternalName: | Apowersoft Installer.exe |
| FileVersion: | 1.1.1.2 |
| FileDescription: | Apowersoft Installer |
| CompanyName: | Apowersoft |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.1.1.2 |
| FileVersionNumber: | 1.1.1.2 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0xe5a98 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 777728 |
| CodeSize: | 1202176 |
| LinkerVersion: | 14.27 |
| PEType: | PE32 |
| TimeStamp: | 2021:03:22 10:36:49+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Mar-2021 09:36:49 |
| Debug artifacts: |
|
| CompanyName: | Apowersoft |
| FileDescription: | Apowersoft Installer |
| FileVersion: | 1.1.1.2 |
| InternalName: | Apowersoft Installer.exe |
| LegalCopyright: | Copyright (C) 2020 Apowersoft Ltd. |
| OriginalFilename: | Apowersoft Installer.exe |
| ProductName: | Apowersoft Installer |
| ProductVersion: | 1.1.1.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-Mar-2021 09:36:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00125760 | 0x00125800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61584 |
.rdata | 0x00127000 | 0x00048E78 | 0x00049000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.37665 |
.data | 0x00170000 | 0x00005F84 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.32184 |
.rsrc | 0x00176000 | 0x0005D698 | 0x0005D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.65799 |
.reloc | 0x001D4000 | 0x000114D8 | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56826 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.95302 | 2952 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.19327 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.38074 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.47987 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.57426 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.76183 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
102 | 0 | 1 | UNKNOWN | UNKNOWN | DAT |
105 | 5.01071 | 12307 | UNKNOWN | UNKNOWN | XML |
106 | 4.26587 | 426 | UNKNOWN | UNKNOWN | CONF |
107 | 4.31674 | 24985 | UNKNOWN | UNKNOWN | CONF |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
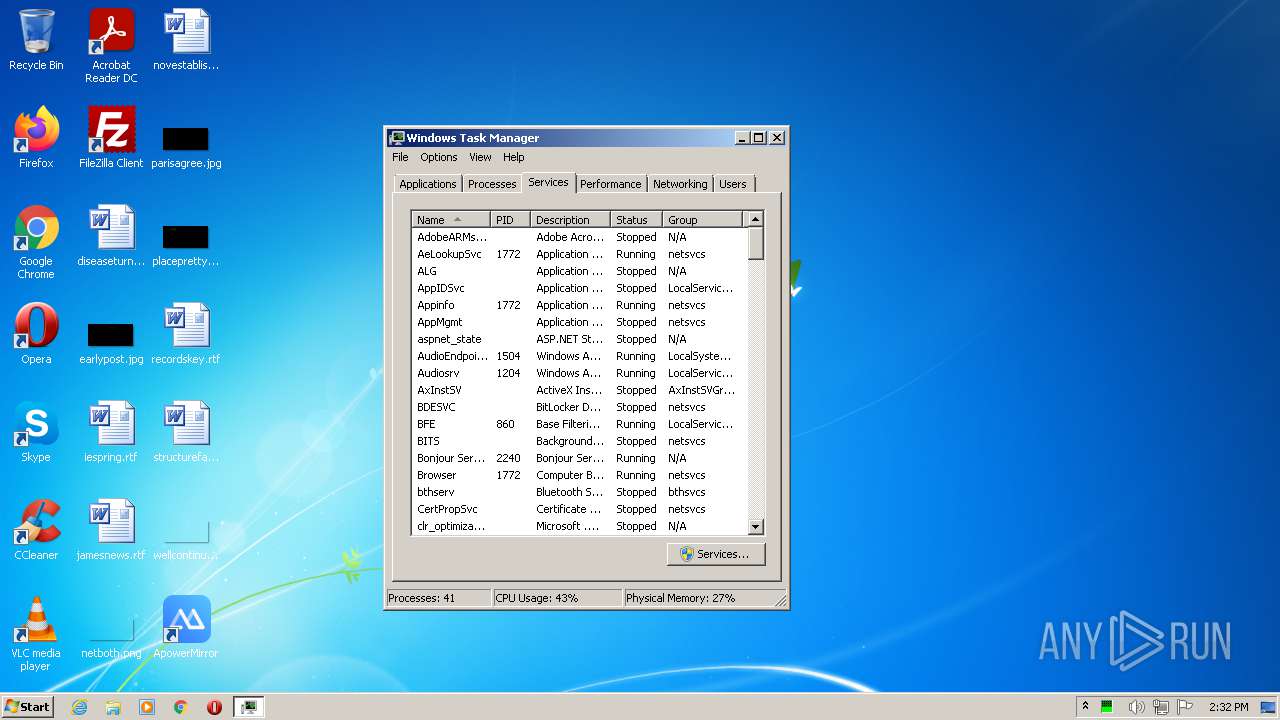
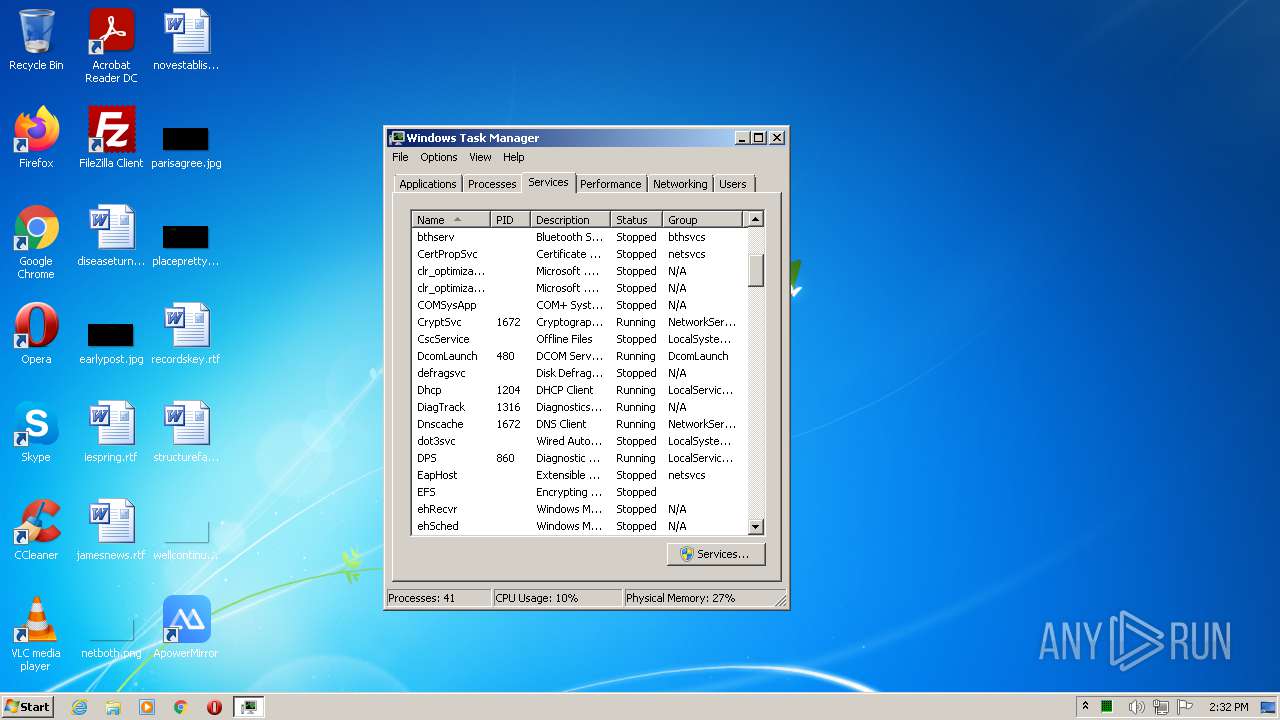
Total processes
87
Monitored processes
34
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Users\admin\Downloads\apowermirror-setup.exe" | C:\Users\admin\Downloads\apowermirror-setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: Apowersoft Integrity Level: HIGH Description: Apowersoft Installer Exit code: 0 Version: 1.1.1.2 Modules
| |||||||||||||||
| 676 | "C:\Users\admin\AppData\Local\Temp\installer.exe" /VERYSILENT /SUPPRESSMSGBOXES /FORCECLOSEAPPLICATIONS /DIR="C:\Program Files\Apowersoft\ApowerMirror" /LANG=English | C:\Users\admin\AppData\Local\Temp\installer.exe | apowermirror-setup.exe | ||||||||||||
User: admin Company: APOWERSOFT LIMITED Integrity Level: HIGH Description: ApowerMirror Setup Exit code: 0 Version: 1.5.9.13 Modules
| |||||||||||||||
| 1036 | "C:\Windows\system32\netsh.exe" advfirewall firewall delete rule name="ApowerMirror" program="C:\Program Files\Apowersoft\ApowerMirror\ApowerMirror.exe" | C:\Windows\system32\netsh.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1256 | C:\Windows\system32\MsiExec.exe -Embedding 0E22468518B15C120FBB495EA056B70F | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" /AUTOMATION -Embedding | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
| 1508 | "C:\Windows\system32\cmd.exe" /C ""C:\Users\admin\AppData\Local\Temp\is-582OB.tmp\KillProcessWithName.bat" "ApowerMirror.exe"" | C:\Windows\system32\cmd.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1588 | C:\Windows\system32\MsiExec.exe -Embedding F886E9F424ADDF5FC703ADA7D90EFC1B E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | netstat.exe -aon | C:\Windows\system32\netstat.exe | — | ApowerMirror.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1956 | find "ApowerMirror.exe" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
41 610
Read events
40 822
Write events
763
Delete events
25
Modification events
| (PID) Process: | (580) apowermirror-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: apowermirror-setup.exe | |||
| (PID) Process: | (580) apowermirror-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (580) apowermirror-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (580) apowermirror-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (580) apowermirror-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3964) installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 7C0F0000253AB16B479BD701 | |||
| (PID) Process: | (3964) installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: A88210775540FF30AE14245A9A022D4678F89B2BFB1121B3E60EE245E5A03851 | |||
| (PID) Process: | (3964) installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3964) installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Apowersoft\ApowerMirror\7z.dll | |||
| (PID) Process: | (3964) installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 7C6860E72C17D66E755EF99A0038472FA08D4E63E073AFA58919579153B0BF64 | |||
Executable files
187
Suspicious files
41
Text files
800
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 580 | apowermirror-setup.exe | C:\Users\admin\AppData\Local\Temp\installer.exe | — | |
MD5:— | SHA256:— | |||
| 580 | apowermirror-setup.exe | C:\Users\admin\AppData\Local\Temp\_gaid.txt | text | |
MD5:— | SHA256:— | |||
| 580 | apowermirror-setup.exe | C:\Users\admin\AppData\Local\Temp\installer.exe.err.log | text | |
MD5:— | SHA256:— | |||
| 676 | installer.exe | C:\Users\admin\AppData\Local\Temp\is-24SV0.tmp\installer.tmp | executable | |
MD5:— | SHA256:— | |||
| 3964 | installer.tmp | C:\Program Files\Apowersoft\ApowerMirror\is-1K63D.tmp | executable | |
MD5:— | SHA256:— | |||
| 3964 | installer.tmp | C:\Program Files\Apowersoft\ApowerMirror\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 3964 | installer.tmp | C:\Program Files\Apowersoft\ApowerMirror\is-FGMN8.tmp | executable | |
MD5:— | SHA256:— | |||
| 3964 | installer.tmp | C:\Program Files\Apowersoft\ApowerMirror\agora_rtc_sdk.dll | executable | |
MD5:— | SHA256:— | |||
| 3964 | installer.tmp | C:\Program Files\Apowersoft\ApowerMirror\is-DSRES.tmp | executable | |
MD5:— | SHA256:— | |||
| 3964 | installer.tmp | C:\Program Files\Apowersoft\ApowerMirror\ApowerMirror.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
67
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
580 | apowermirror-setup.exe | GET | 302 | 47.91.201.11:80 | http://download.aoscdn.com/down.php?softid=apowermirrorinstall | HK | — | — | suspicious |
580 | apowermirror-setup.exe | GET | 200 | 47.244.67.196:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=e615529a4cd3aafaed2134f189cbbfa2&session_id=1630070848&app=ApowerMirror&appid=113&ga_request=https%3A%2F%2Fdownload.aoscdn.com%2Fapi%2Fclient%2Finfo%3Fot%3D1%26mt%3D1630070847%26ct%3D1630070847%26cc%3D4%26tz%3DGMT%252B0100%26ov%3D6.1%26g%3DStandard%2520VGA%2520Graphics%2520Adapter%26h%3Dee7add8df6ae902757ea73286bbe7854&step=1 | US | — | — | suspicious |
580 | apowermirror-setup.exe | GET | 200 | 47.244.67.196:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=e615529a4cd3aafaed2134f189cbbfa2&session_id=1630070848&app=ApowerMirror&appid=113&installed=1&installed_ts=1630070974&step=2 | US | — | — | suspicious |
580 | apowermirror-setup.exe | GET | 200 | 47.244.67.196:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=e615529a4cd3aafaed2134f189cbbfa2&session_id=1630070848&app=ApowerMirror&app_install_path=C%3A%5CProgram%20Files%5CApowersoft%5CApowerMirror&app_lang=English&appid=113&apptype=saas&last_step_duration=5&step=2 | US | — | — | suspicious |
3964 | installer.tmp | GET | 200 | 47.244.67.196:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/win-setup/track?APIVersion=0.6.0&__topic__=install&appid=113&apptype=saas | US | — | — | suspicious |
580 | apowermirror-setup.exe | GET | 200 | 47.244.67.196:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=e615529a4cd3aafaed2134f189cbbfa2&session_id=1630070848&app=ApowerMirror&appid=113&ga_error=&ga_ok=0&ga_response=%7B%22status%22%3A500%2C%22message%22%3A%22SQLSTATE%5BHY000%5D%20%5B2002%5D%20Connection%20timed%20out%20%28SQL%3A%20select%20%60id%60%2C%20%60gaid%60%2C%20%60domain%60%2C%20%60apptype%60%2C%20%60screen_width%60%2C%20%60screen_height%60%2C%20%60timezone%60%2C%20%60track_info%60%2C%20%60cpu_count%60%2C%20%60platform_version%60%2C%20%60clicked_at%60%2C%20%60webgl_render%60%20from%20%60wx_client_infos%60%20where%20%60ip%60%20%3D%20763762185%20and%20%60platform_type%60%20%3D%201%20and%20%60software_hash%60%20%3D%20ee7add8df6ae902757ea73286bbe7854%29%22%7D&gaid=&step=2 | US | — | — | suspicious |
2176 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAJakFrb94kMCgAAAAD6Yis%3D | US | der | 471 b | whitelisted |
2176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR0tOcjGcdlkhVARHvHzj6Qwhh26wQUpI3lvnx55HAjbS4pNK0jWNz1MX8CEAUyD7%2F%2FToWFpJubL4St9ic%3D | US | der | 471 b | whitelisted |
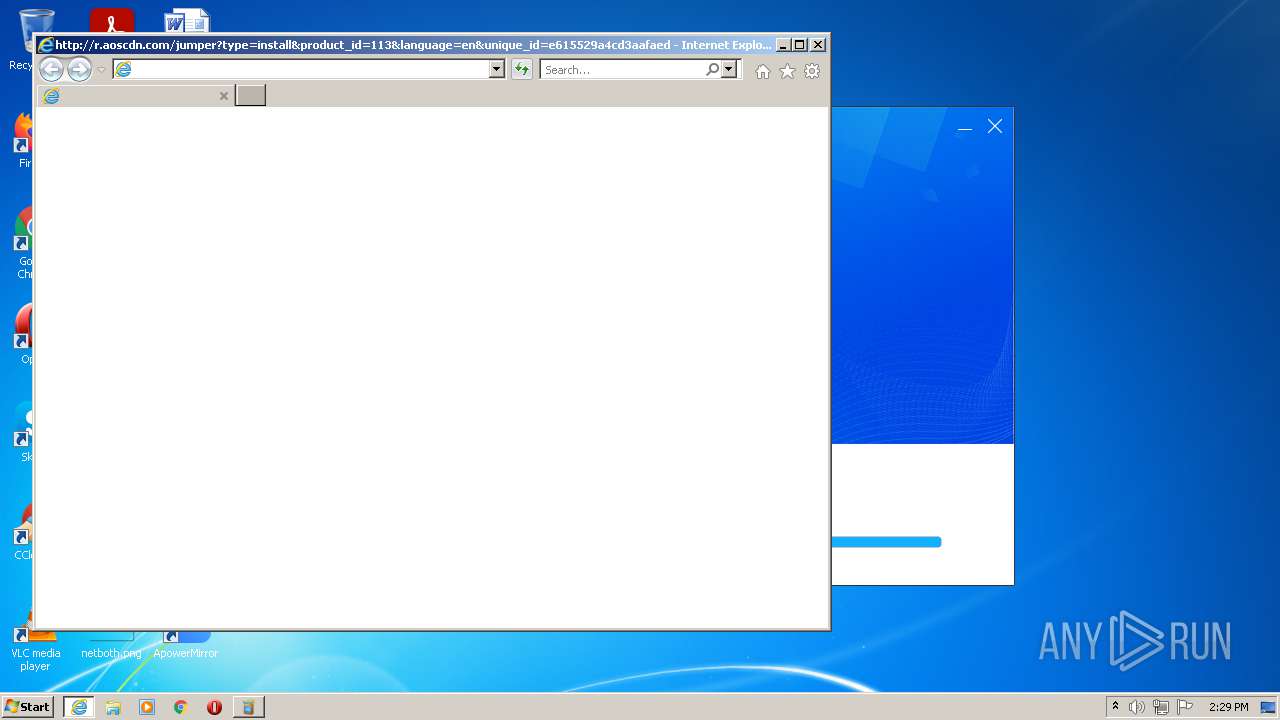
2176 | iexplore.exe | GET | 302 | 47.91.201.11:80 | http://r.aoscdn.com/jumper?type=install&product_id=113&language=en&unique_id=e615529a4cd3aafaed2134f189cbbfa2&apptype=saas&appver=1.5.9.13&first_install_ts=1630070974&ts=1630070974&wxga=&ct=1630070847&mt=1630070847&h=ee7add8df6ae902757ea73286bbe7854&hash=27a6c7bf3c4fadee47efe68293250f60 | HK | html | 1.09 Kb | suspicious |
2176 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2176 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2176 | iexplore.exe | 2.16.218.169:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2176 | iexplore.exe | 18.66.212.155:443 | d3j06uq18x1o3j.cloudfront.net | Massachusetts Institute of Technology | US | unknown |
2176 | iexplore.exe | 13.225.84.42:80 | o.ss2.us | — | US | unknown |
2176 | iexplore.exe | 13.224.89.126:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2176 | iexplore.exe | 142.251.36.232:443 | www.googletagmanager.com | Google Inc. | US | unknown |
2176 | iexplore.exe | 13.225.84.13:80 | ocsp.rootca1.amazontrust.com | — | US | whitelisted |
580 | apowermirror-setup.exe | 47.244.67.196:80 | wx-user-behavior.cn-hongkong.log.aliyuncs.com | — | US | suspicious |
580 | apowermirror-setup.exe | 47.91.201.11:80 | download.aoscdn.com | Alibaba (China) Technology Co., Ltd. | HK | suspicious |
580 | apowermirror-setup.exe | 47.91.201.11:443 | download.aoscdn.com | Alibaba (China) Technology Co., Ltd. | HK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wx-user-behavior.cn-hongkong.log.aliyuncs.com |
| suspicious |
download.aoscdn.com |
| suspicious |
download.apowersoft.info |
| unknown |
r.aoscdn.com |
| suspicious |
www.apowersoft.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
d3j06uq18x1o3j.cloudfront.net |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |