| File name: | Demo.exe |
| Full analysis: | https://app.any.run/tasks/08f6d68c-d0c9-4304-bcbb-1b2f3dab9b96 |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2022, 12:55:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8E5AB927B57966CB59A9BCFC88D54ECC |
| SHA1: | B56147A7C103E31E3F390062072891DC21F39713 |
| SHA256: | A02B814E1AFB9CD910C22912E59F7B13C090F74266E904A5619119CBA80BE691 |
| SSDEEP: | 3072:BlUlrptzBe3l3bJGAyMAYrd+Oj5HGDyNrbPEYgR:Uze3N8pYr0u5mmbPEYg |
MALICIOUS
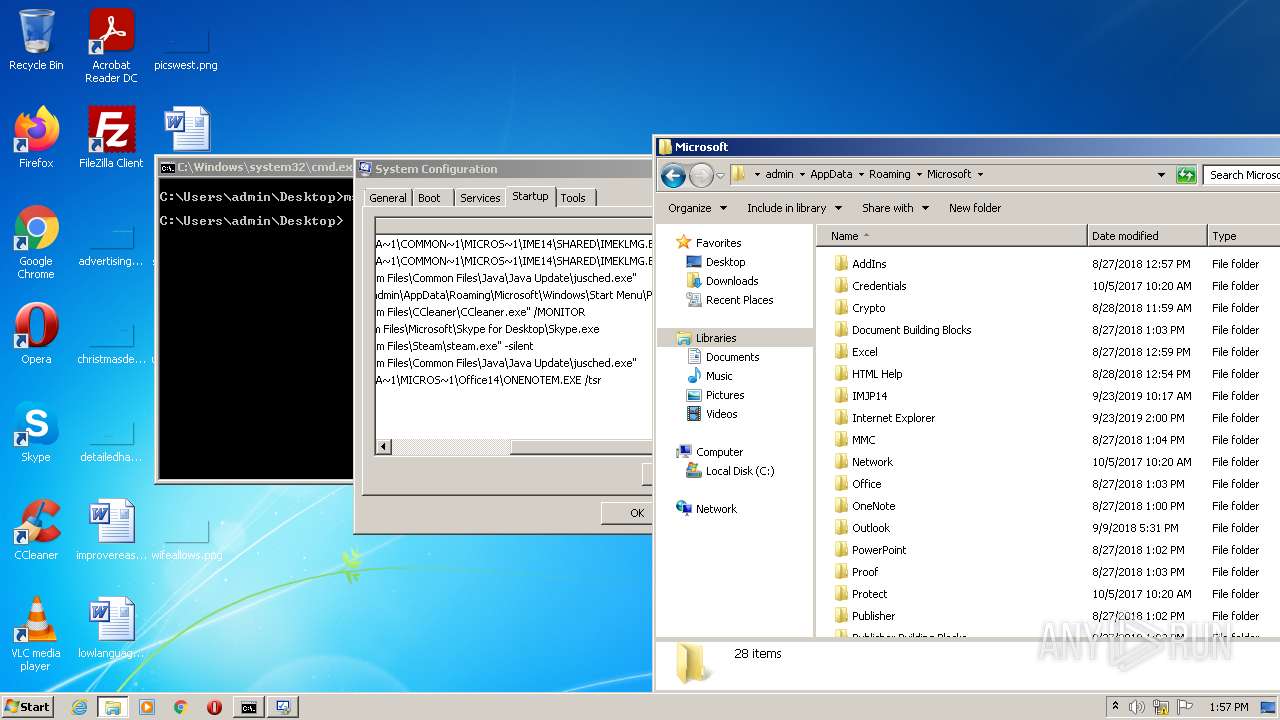
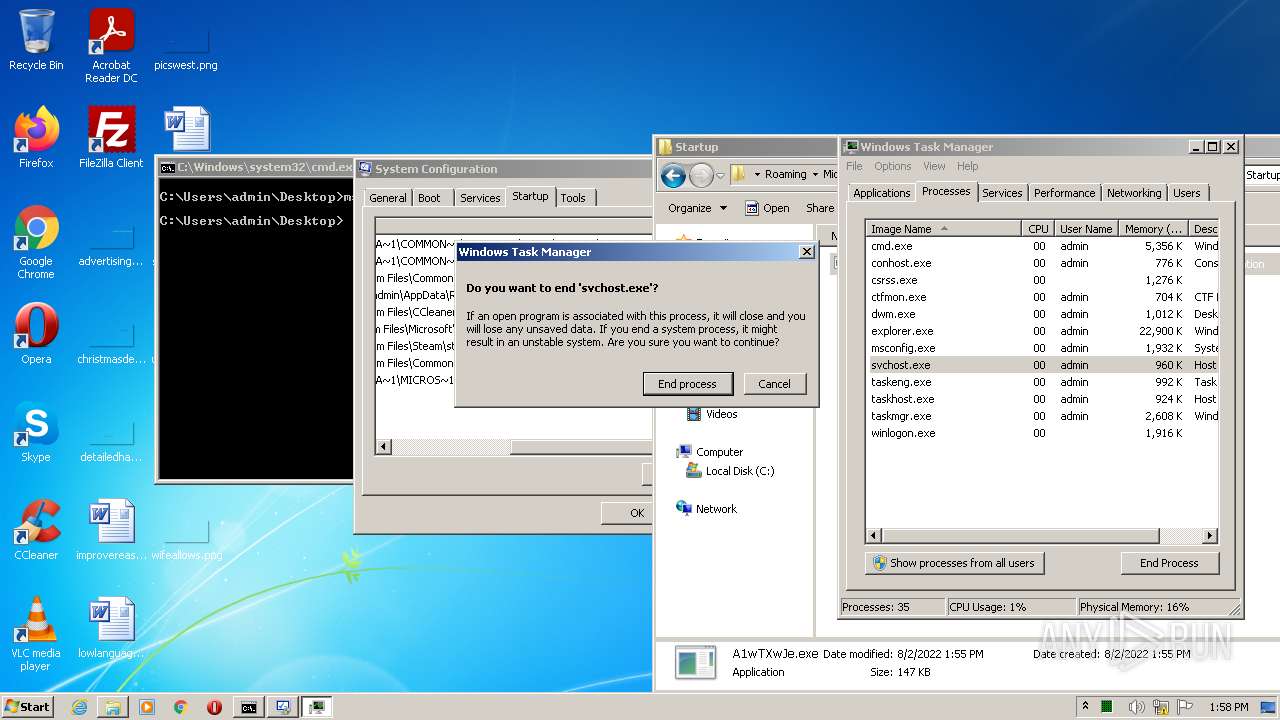
Steals credentials from Web Browsers
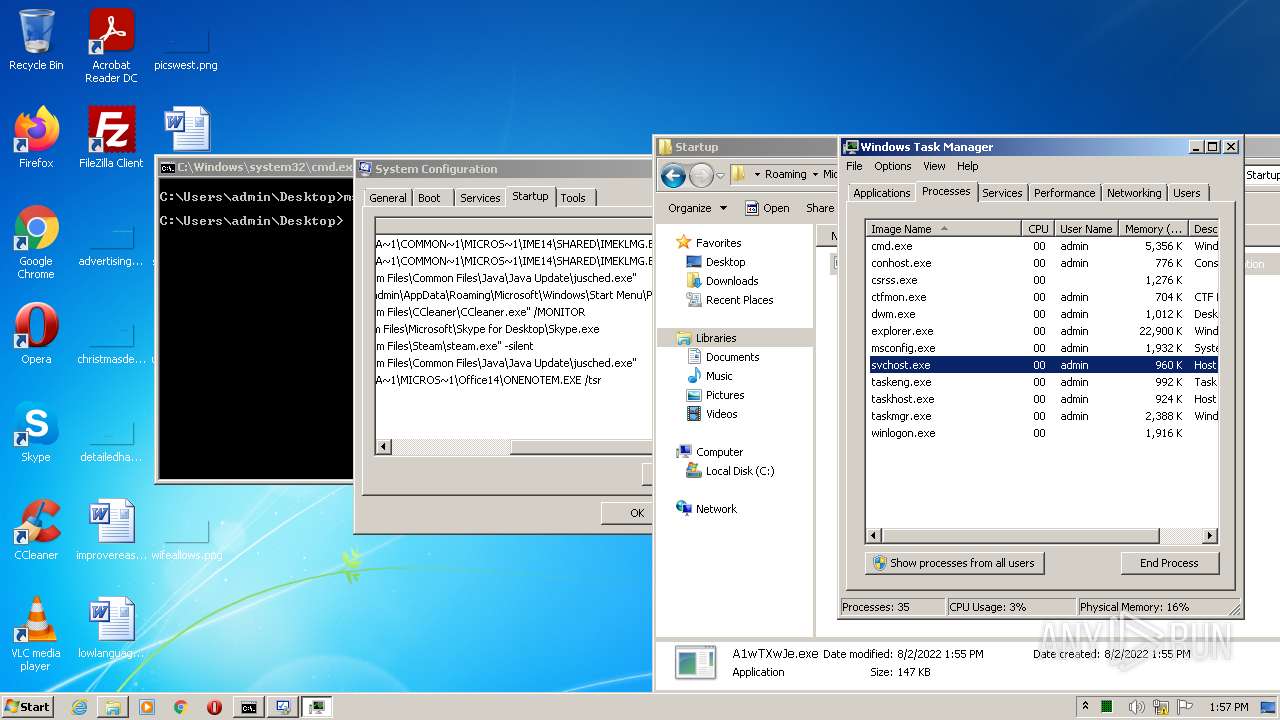
- svchost.exe (PID: 3156)
Actions looks like stealing of personal data
- svchost.exe (PID: 3156)
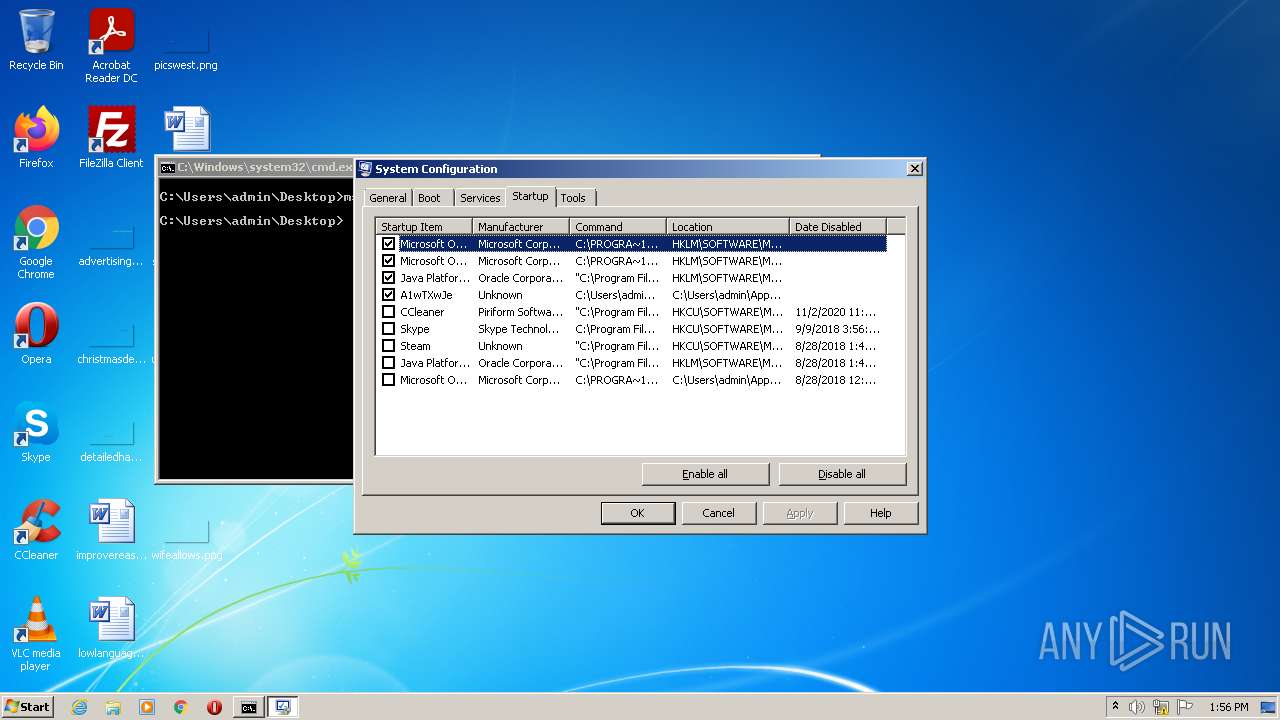
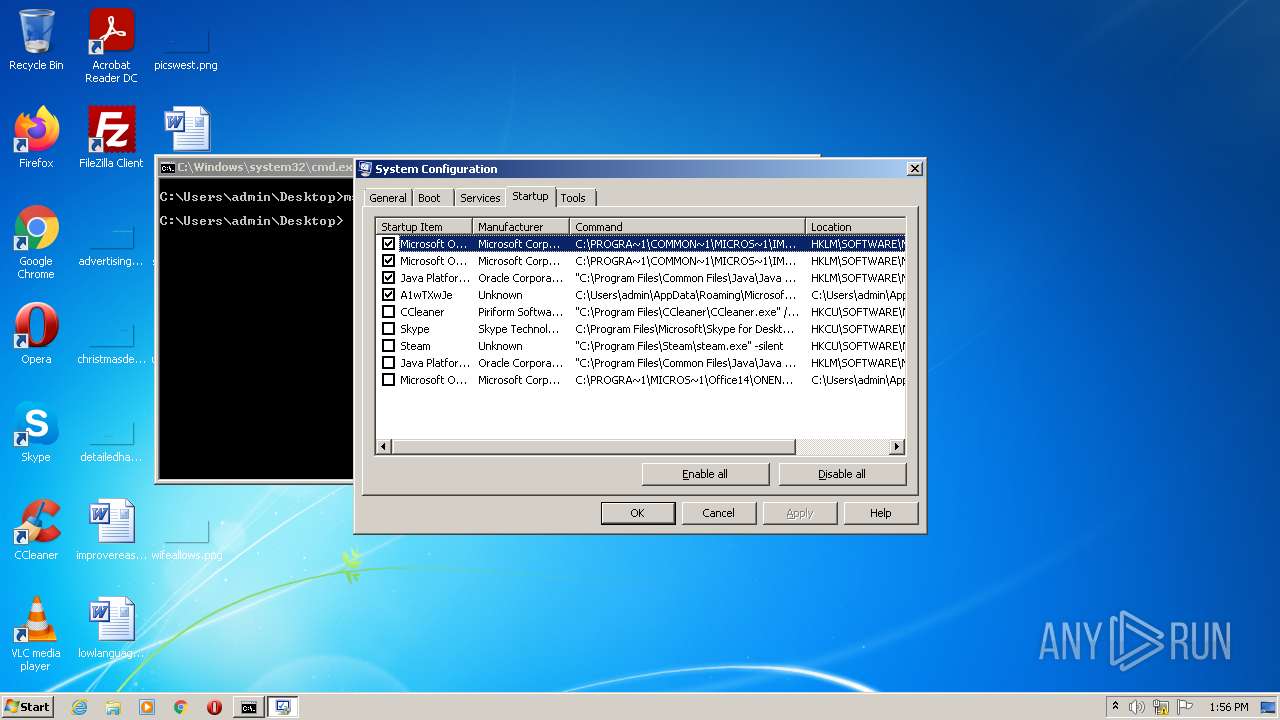
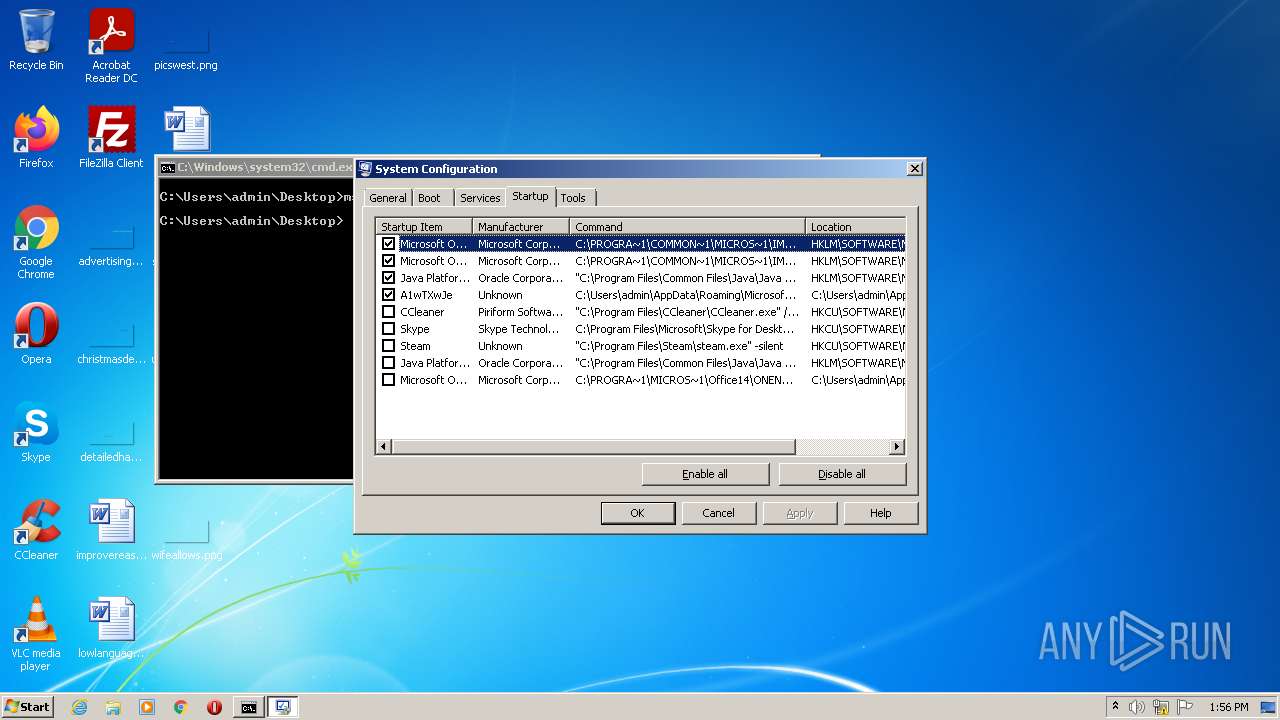
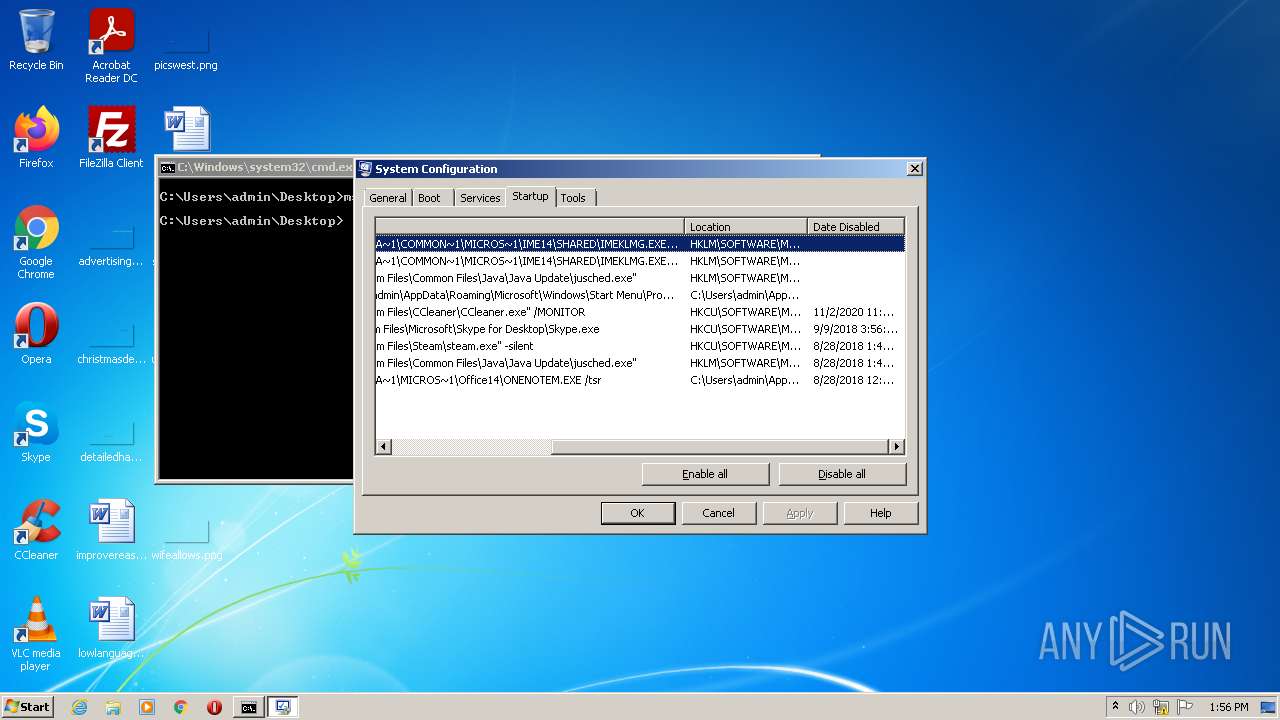
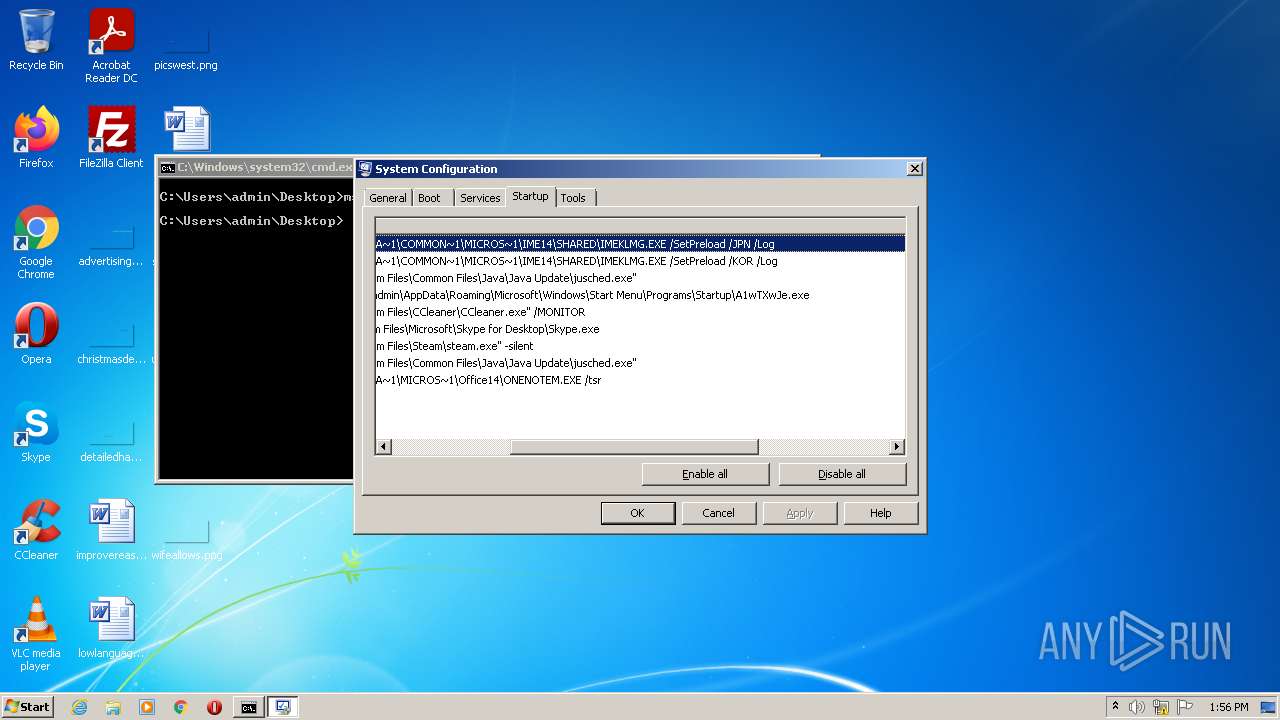
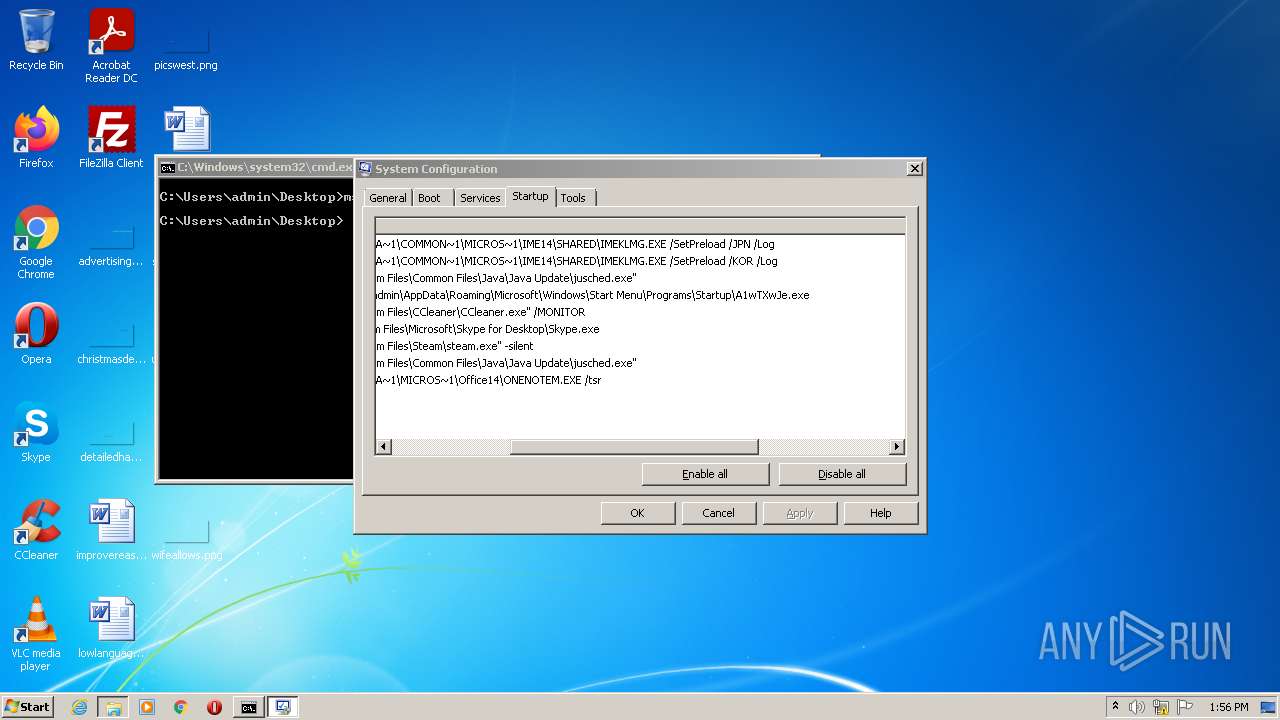
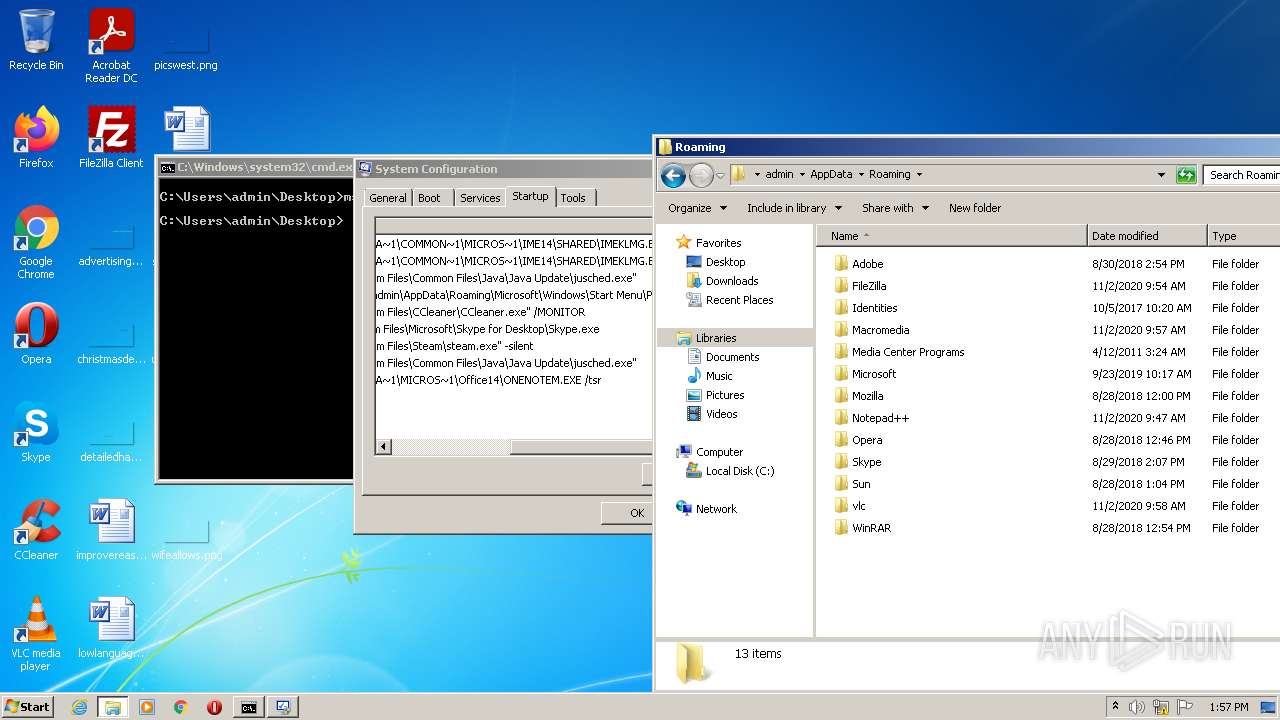
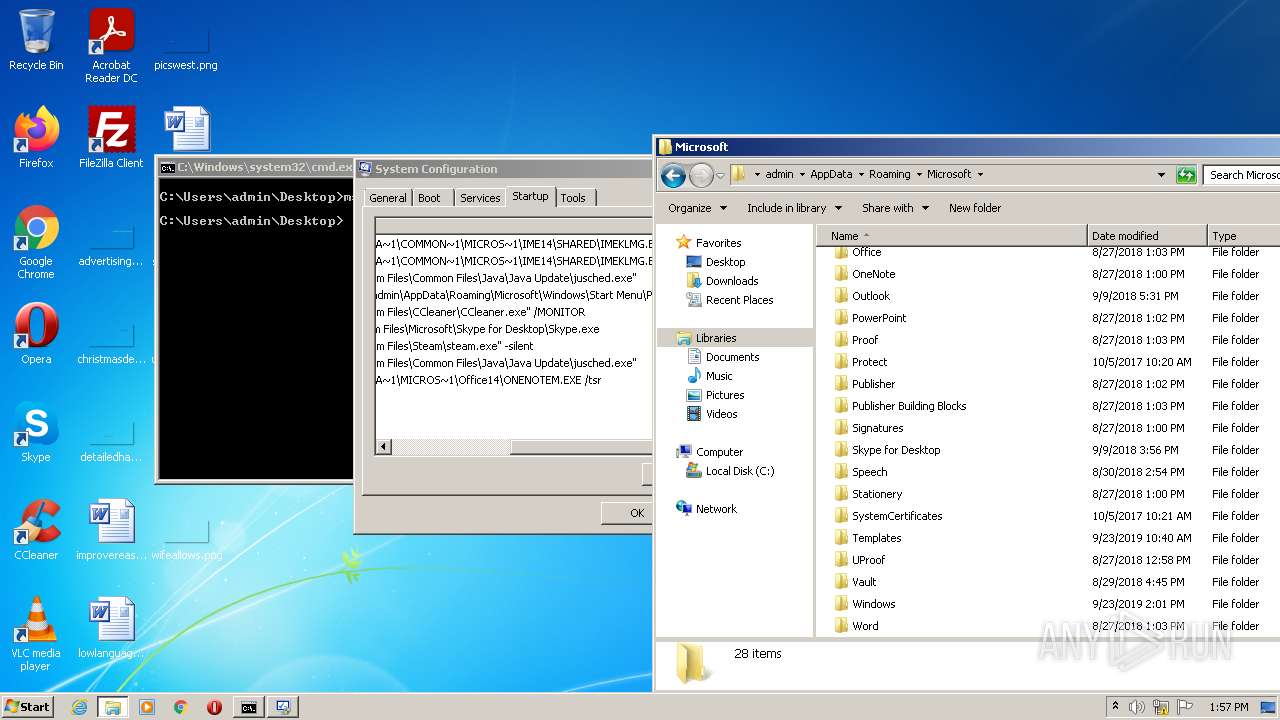
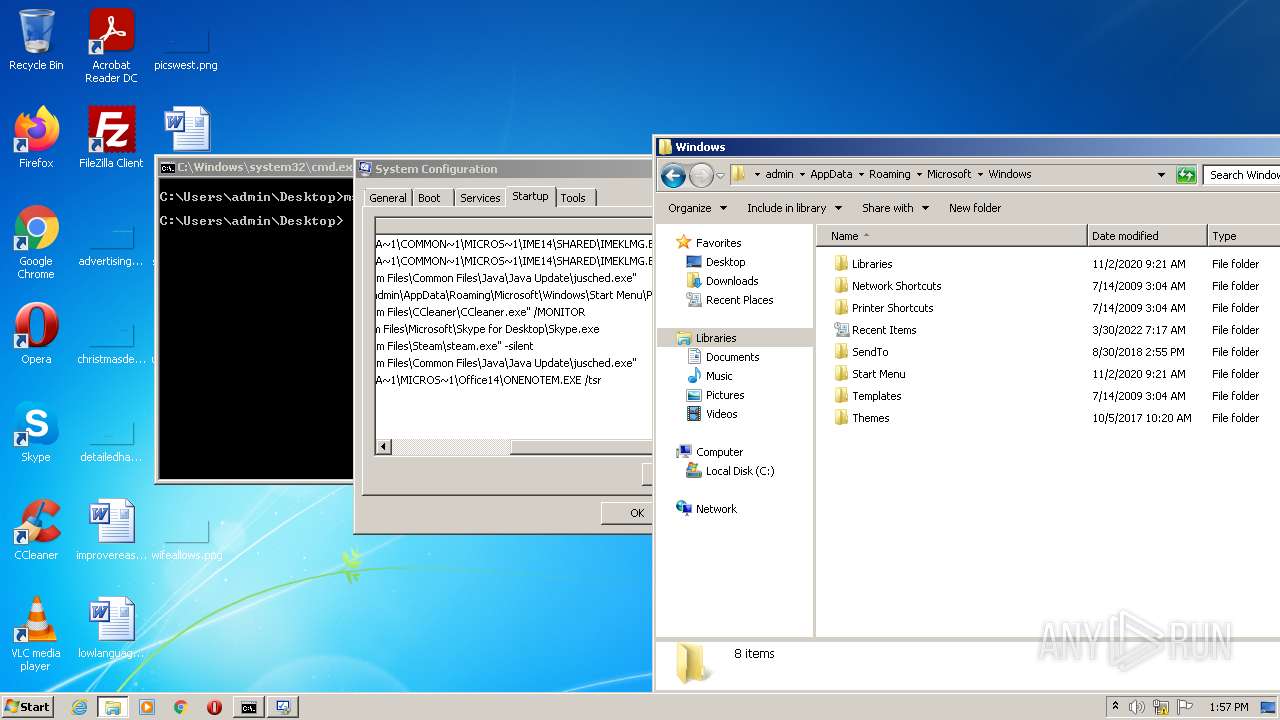
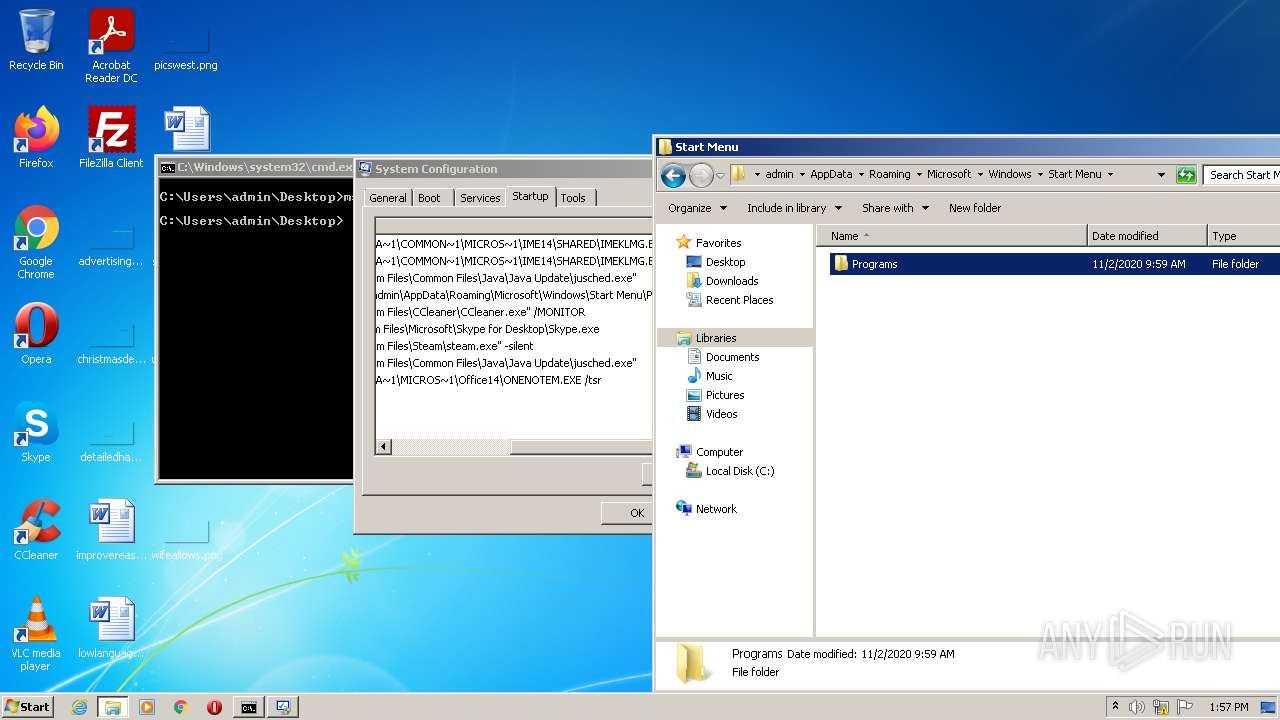
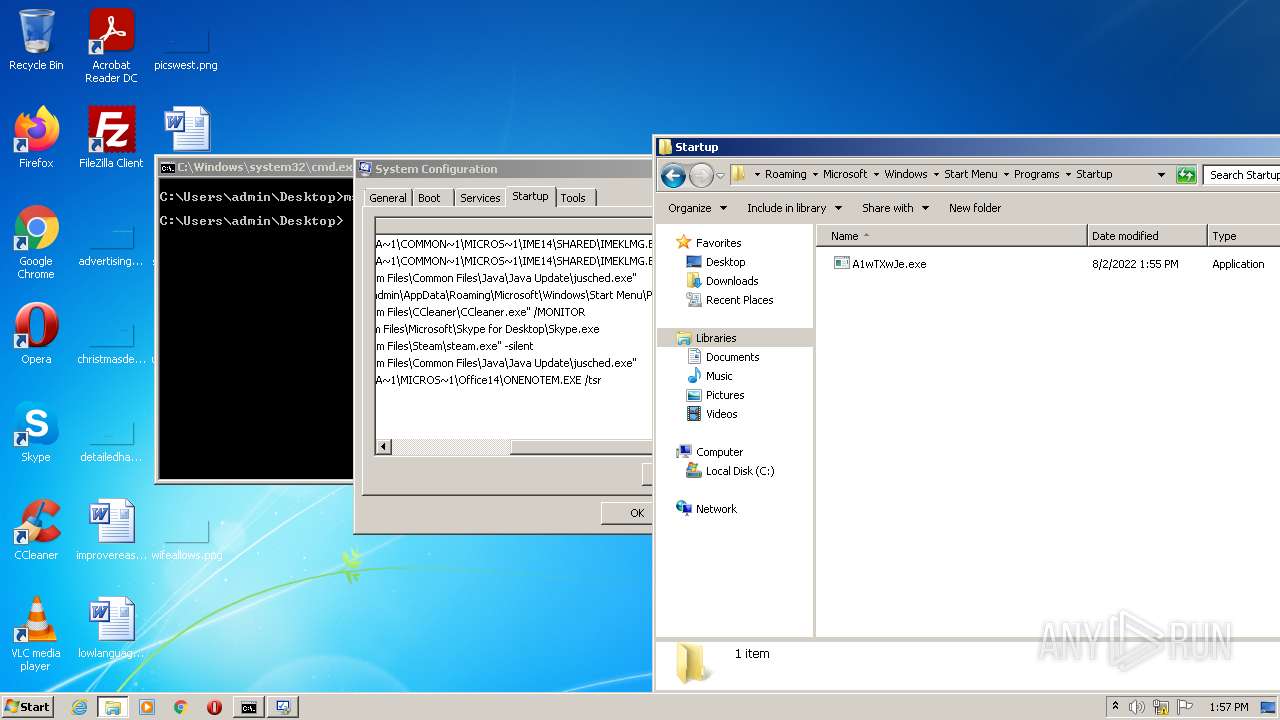
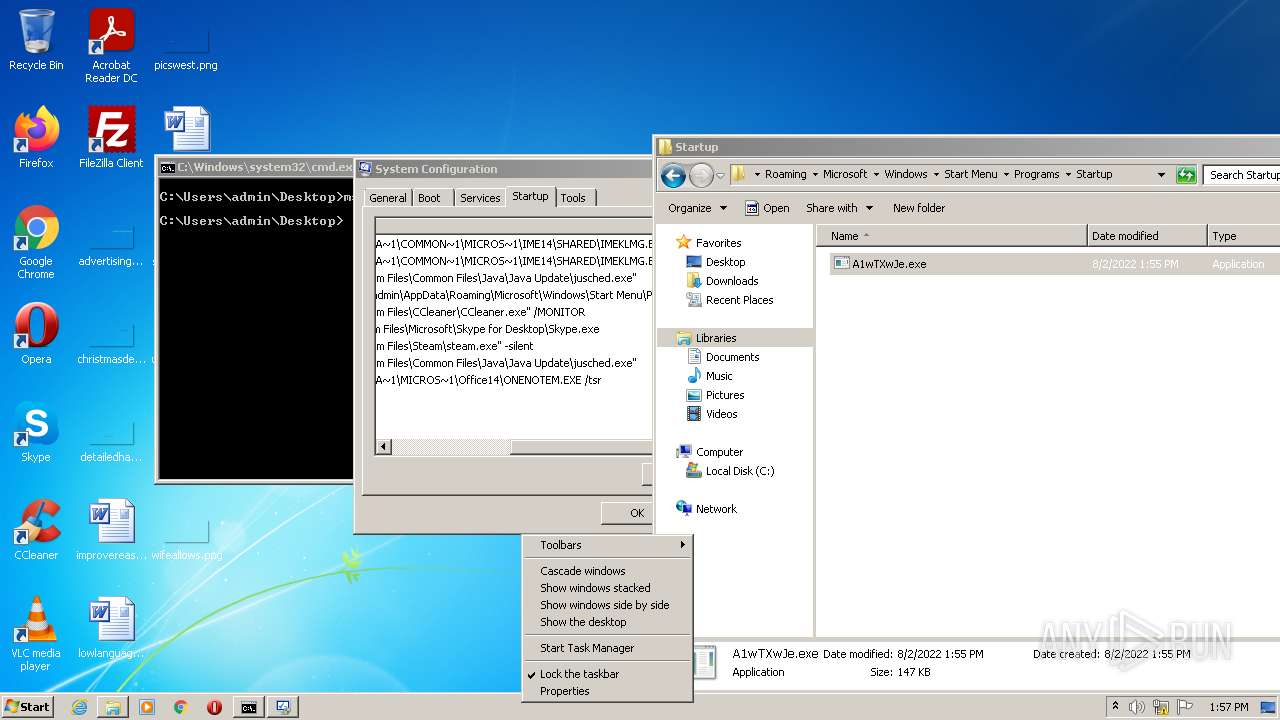
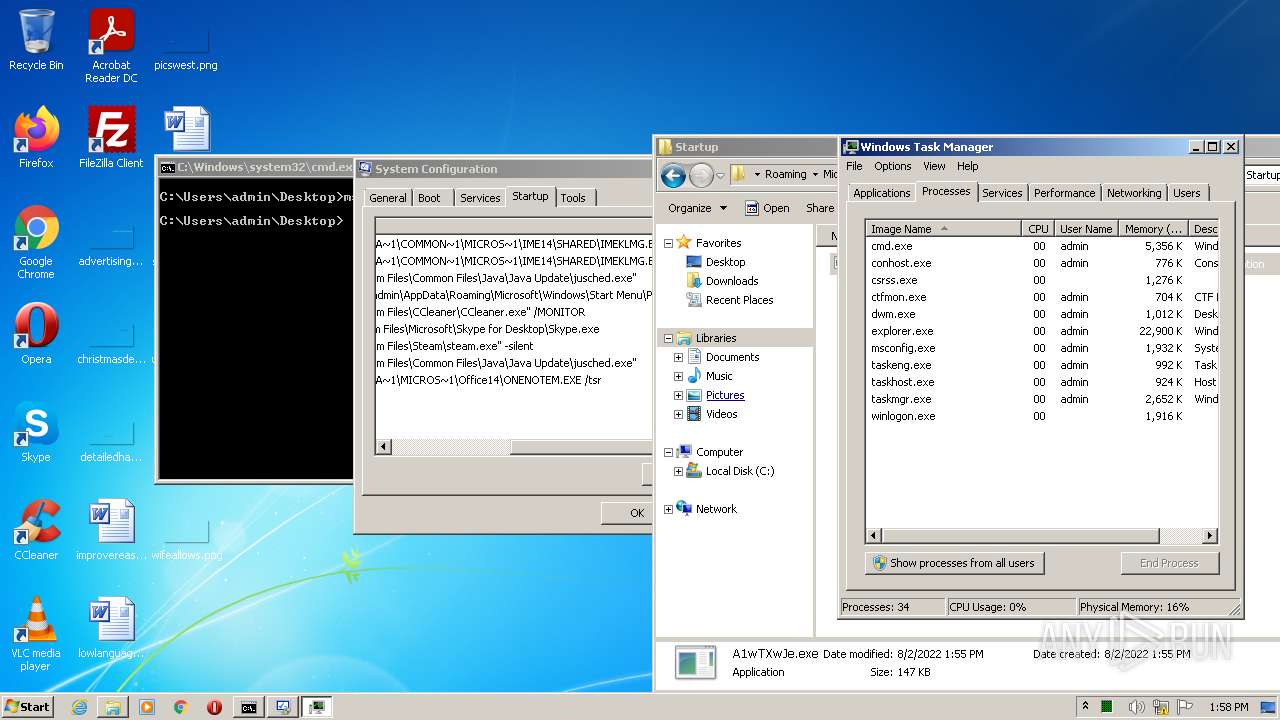
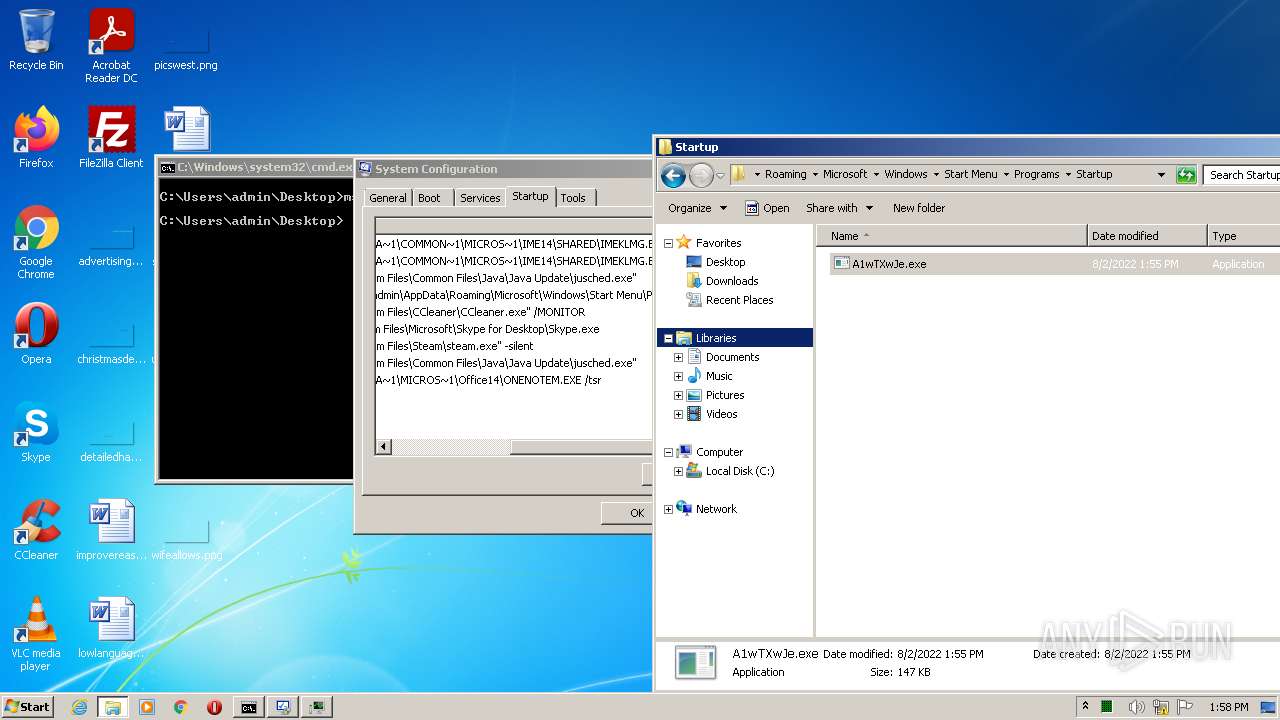
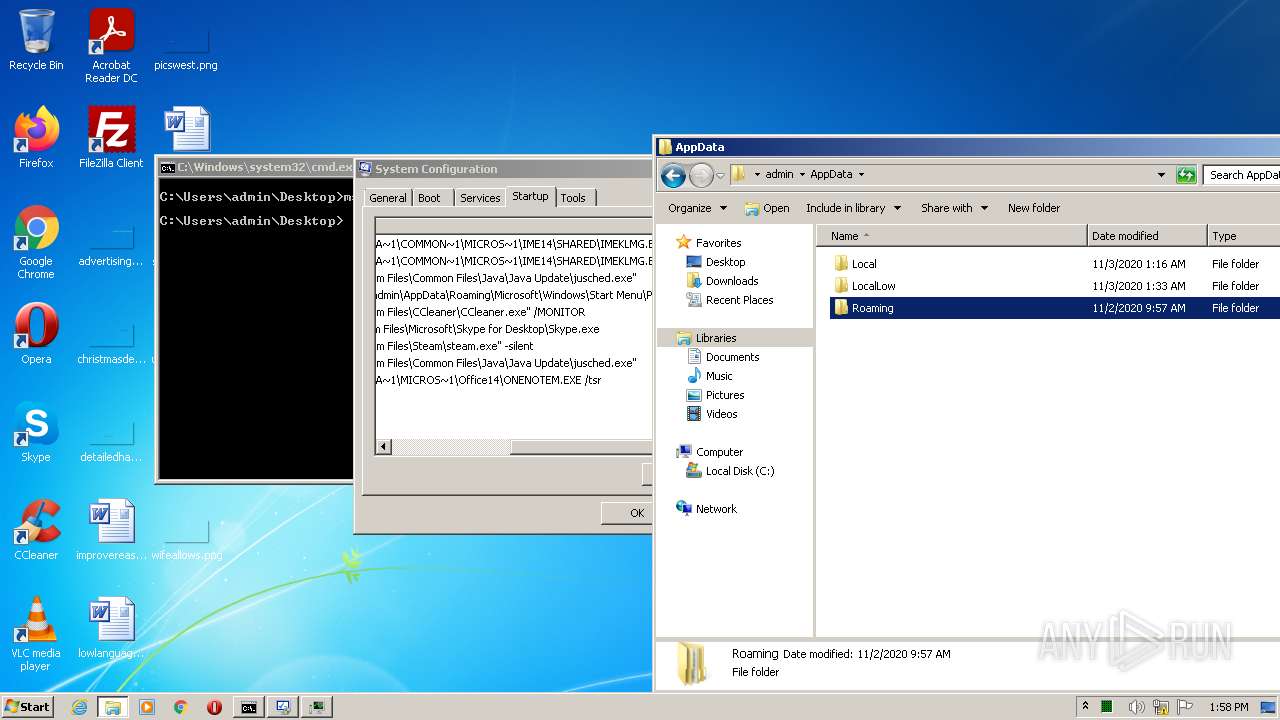
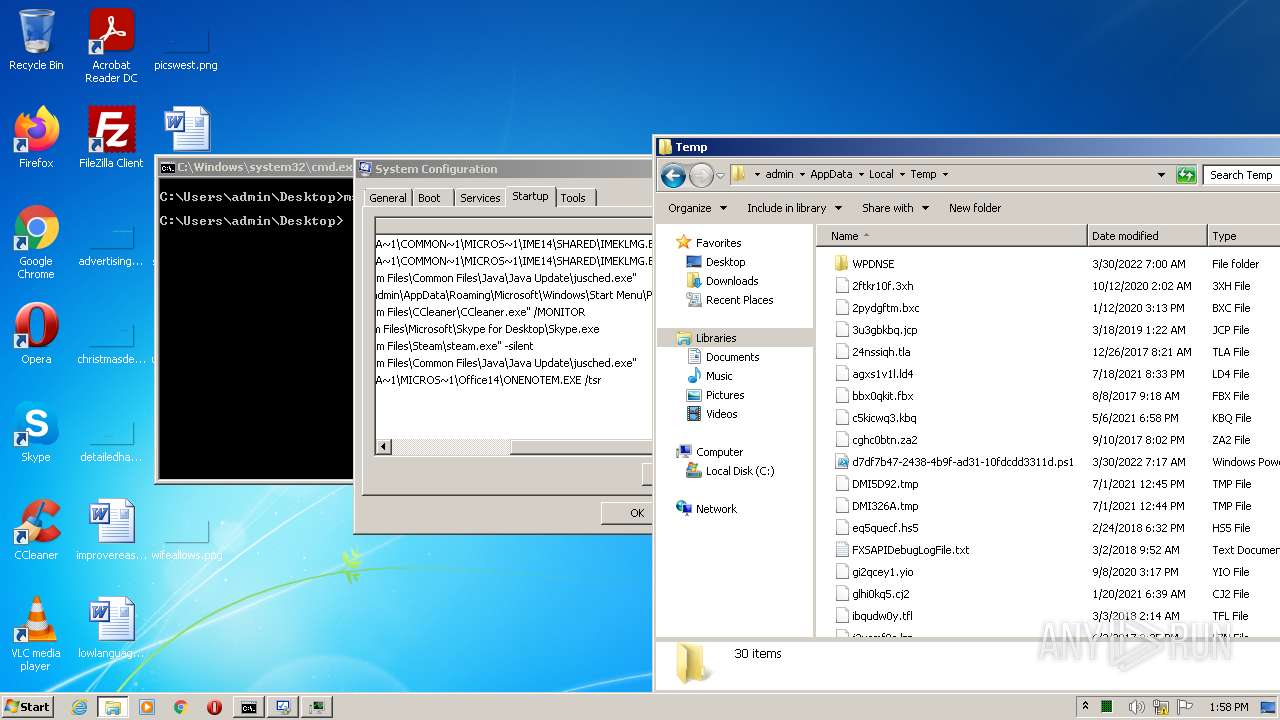
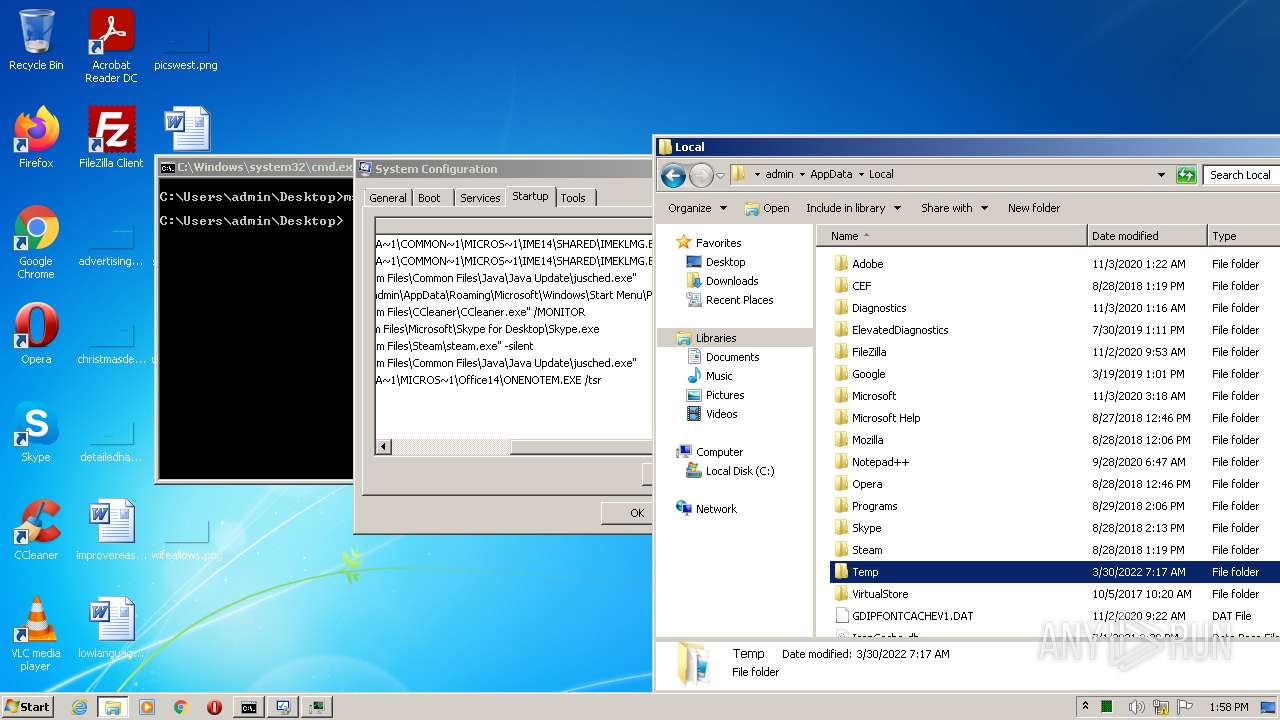
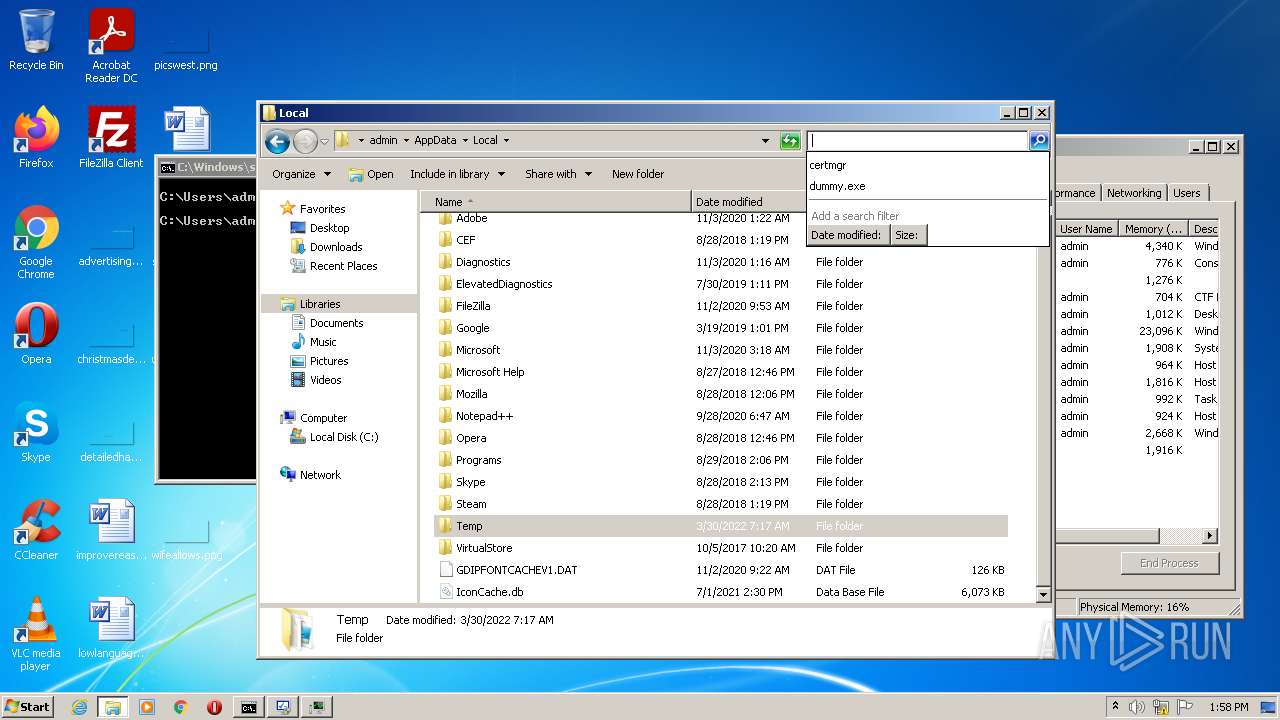
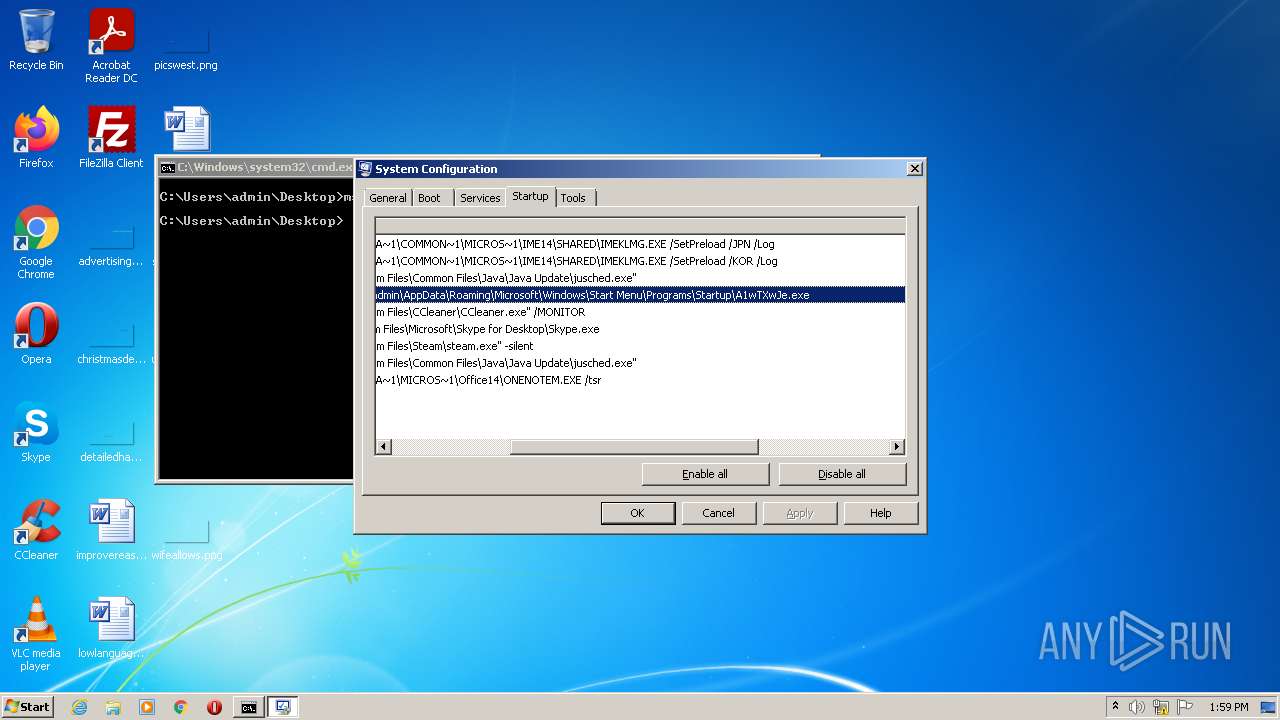
Writes to a start menu file
- svchost.exe (PID: 3156)
Drops executable file immediately after starts
- svchost.exe (PID: 3156)
SUSPICIOUS
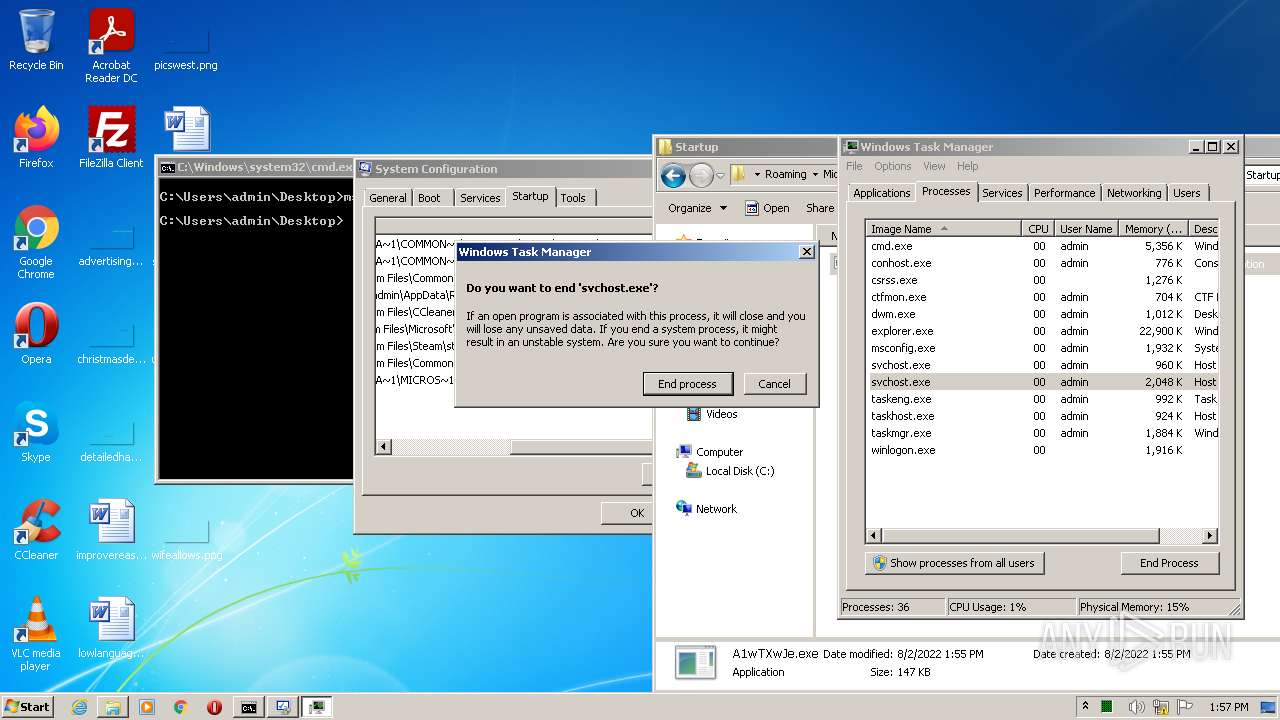
Application launched itself
- svchost.exe (PID: 3156)
- svchost.exe (PID: 3856)
Reads the computer name
- Demo.exe (PID: 2832)
- cmd.exe (PID: 1776)
- A1wTXwJe.exe (PID: 2388)
- A1wTXwJe.exe (PID: 2652)
Checks supported languages
- Demo.exe (PID: 2832)
- cmd.exe (PID: 1776)
- A1wTXwJe.exe (PID: 2652)
- A1wTXwJe.exe (PID: 2388)
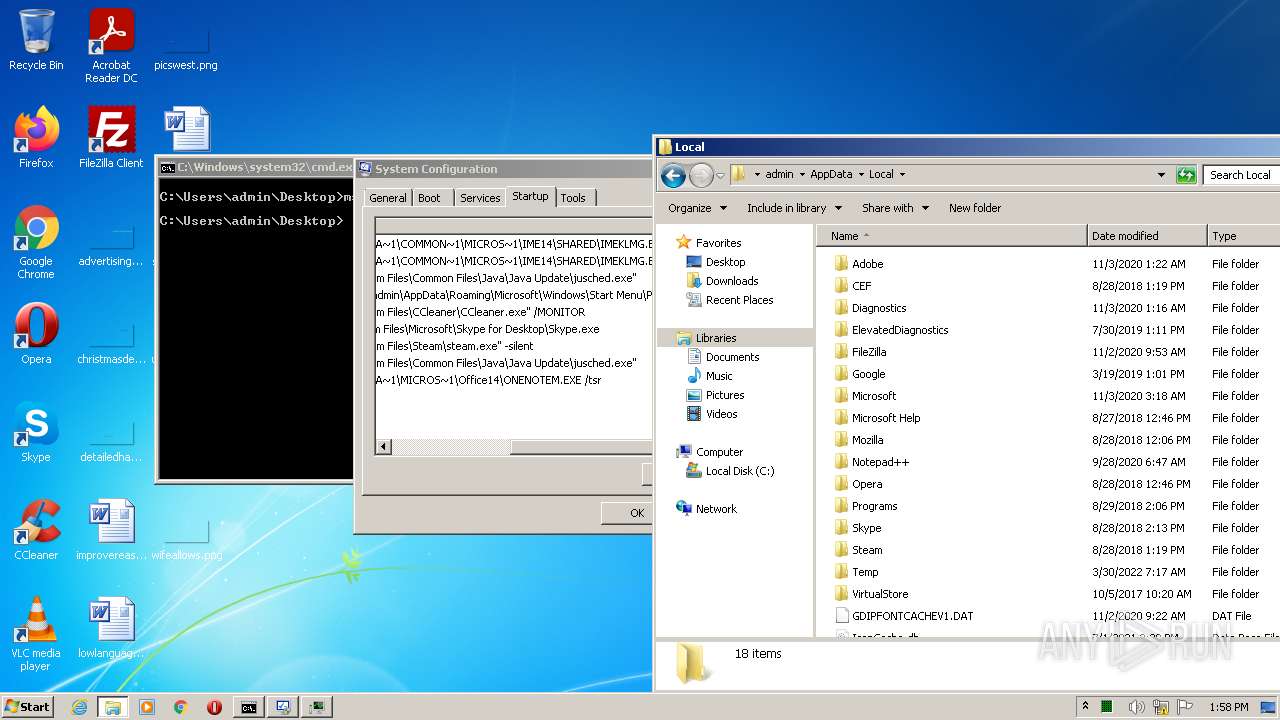
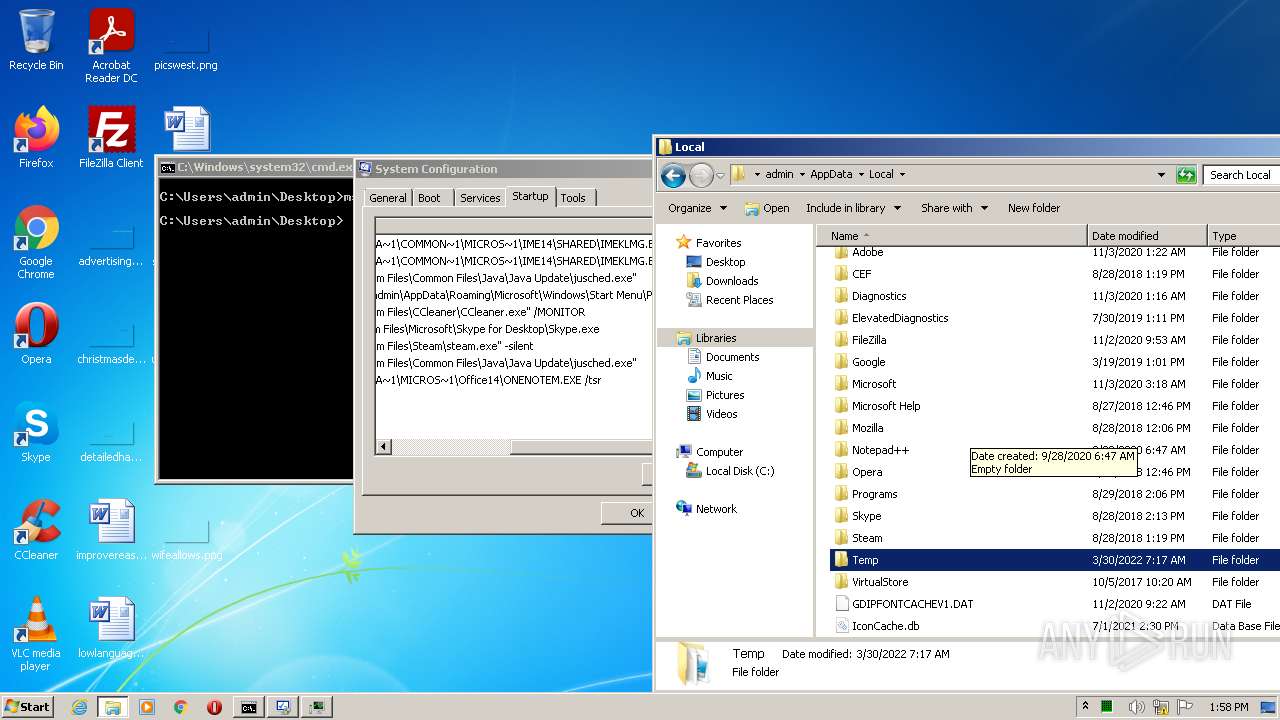
Creates files in the program directory
- svchost.exe (PID: 3156)
Executable content was dropped or overwritten
- svchost.exe (PID: 3156)
Drops a file with a compile date too recent
- svchost.exe (PID: 3156)
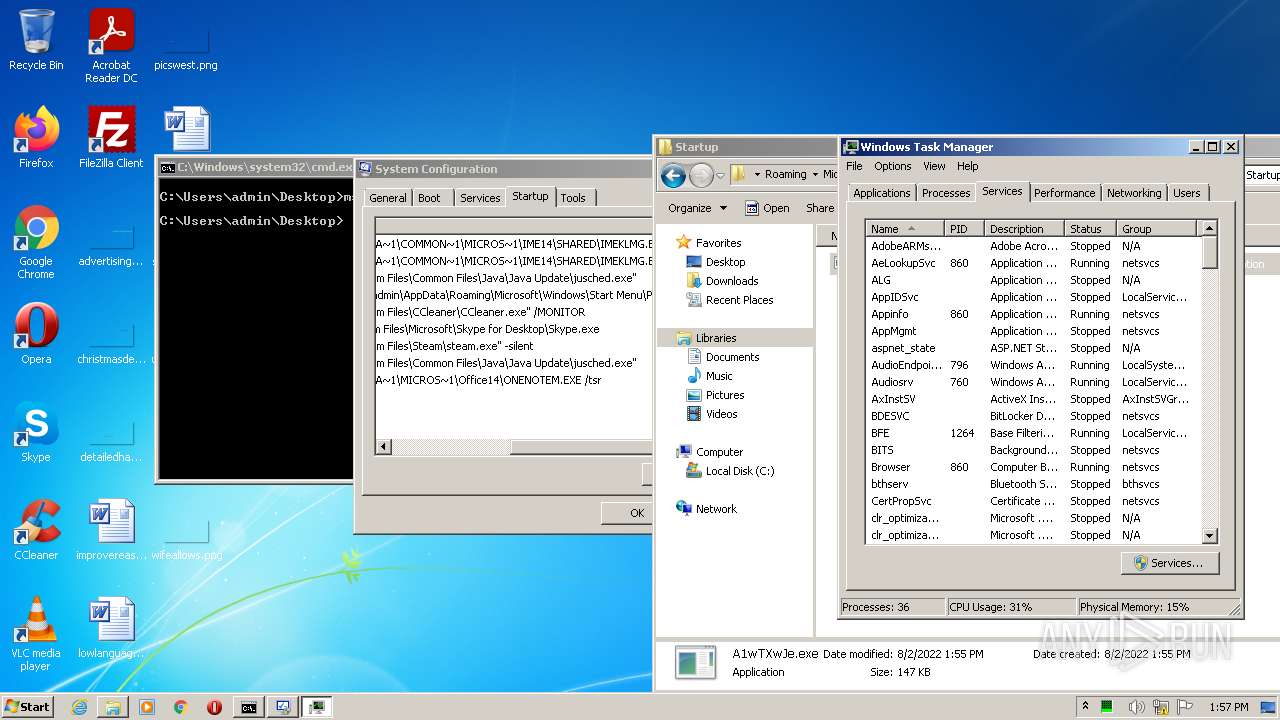
INFO
Checks supported languages
- svchost.exe (PID: 3156)
- svchost.exe (PID: 1800)
- taskmgr.exe (PID: 3144)
- msconfig.exe (PID: 2252)
- explorer.exe (PID: 3224)
- taskmgr.exe (PID: 3080)
- svchost.exe (PID: 3856)
- svchost.exe (PID: 620)
Reads the computer name
- svchost.exe (PID: 3156)
- taskmgr.exe (PID: 3144)
- msconfig.exe (PID: 2252)
- explorer.exe (PID: 3224)
- taskmgr.exe (PID: 3080)
- svchost.exe (PID: 3856)
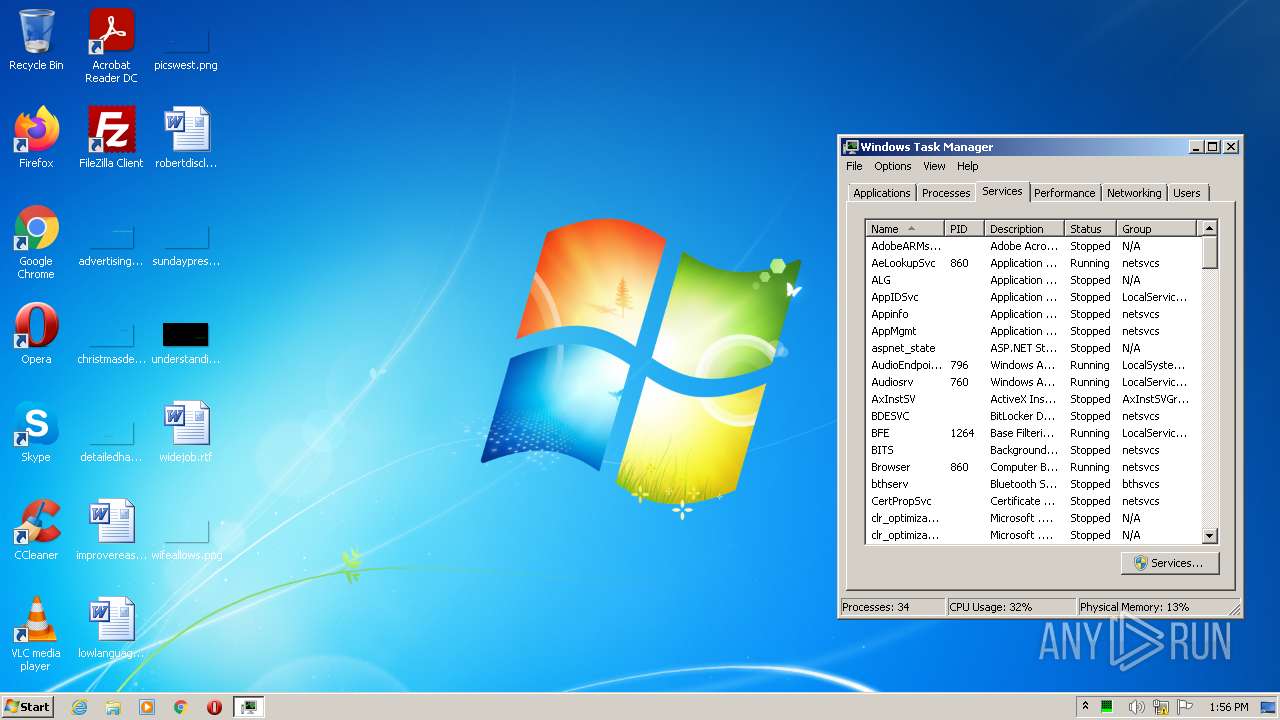
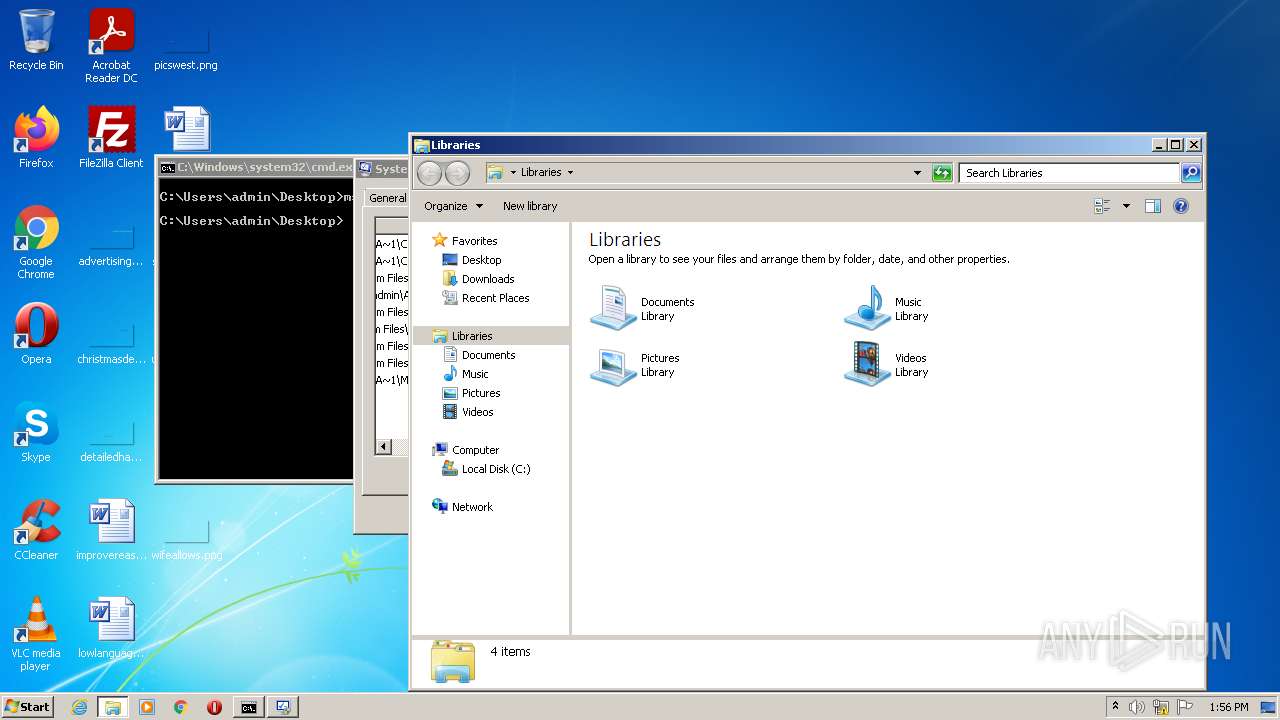
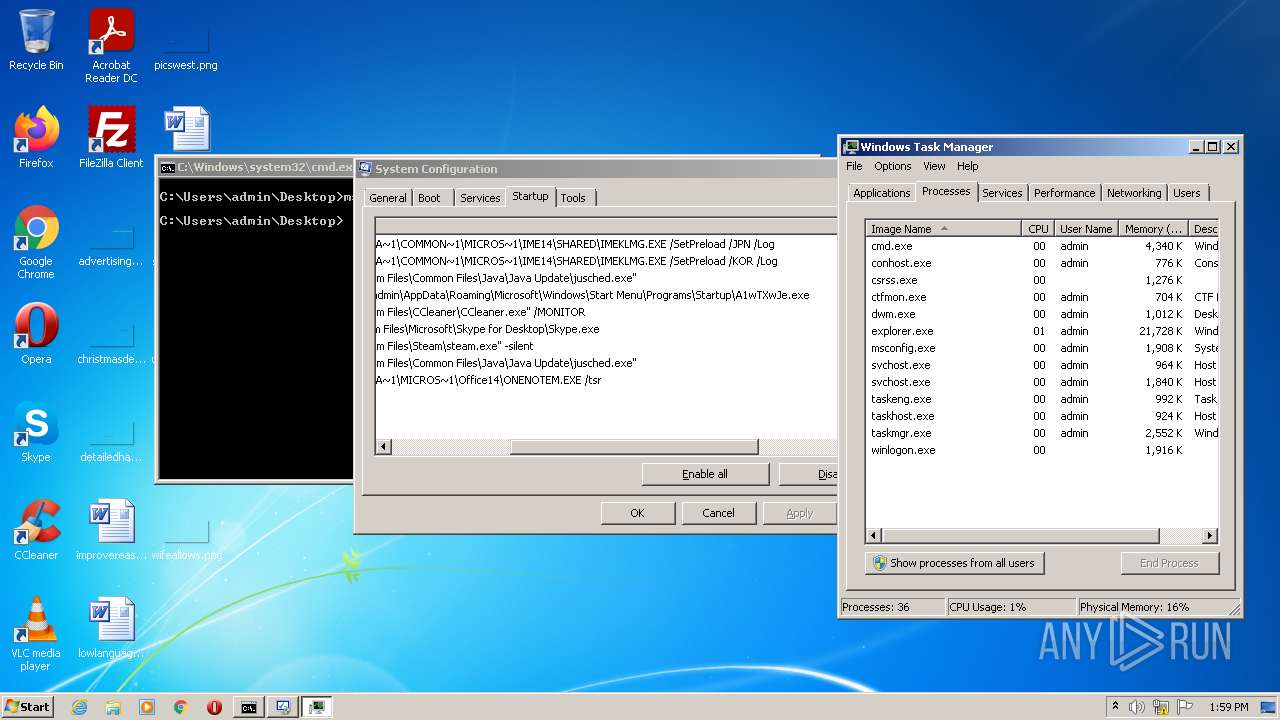
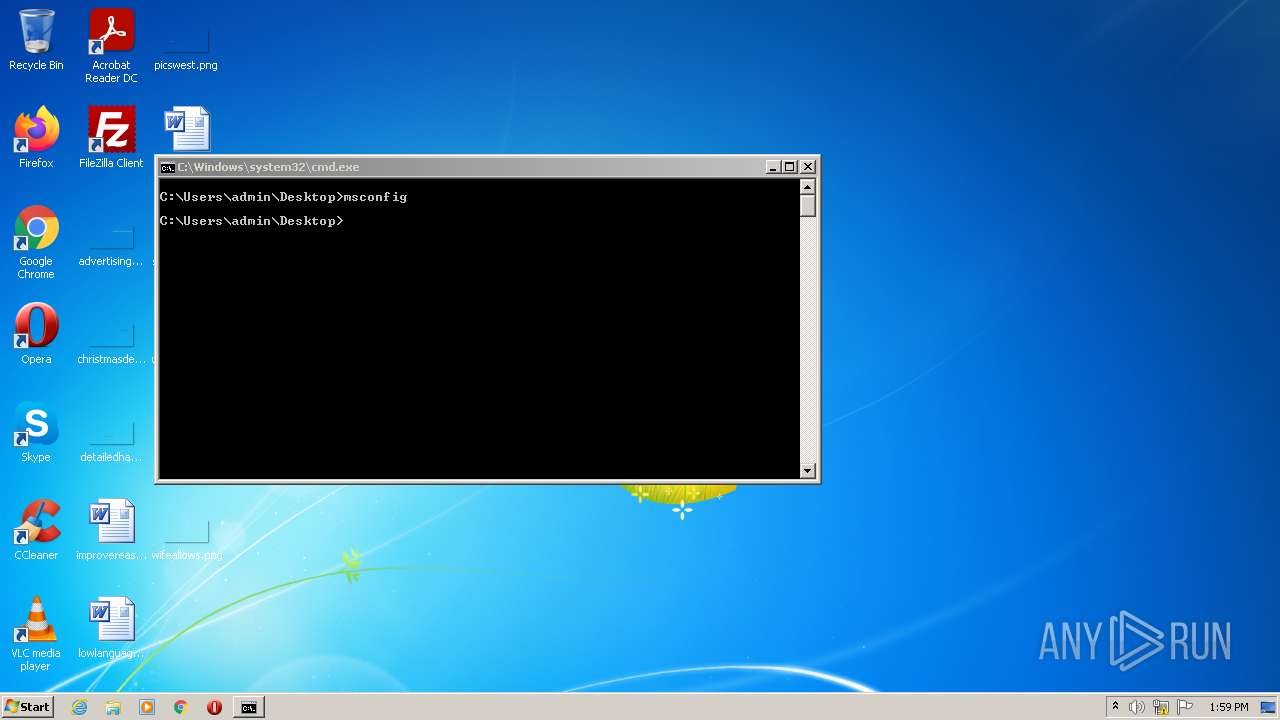
Manual execution by user
- taskmgr.exe (PID: 3144)
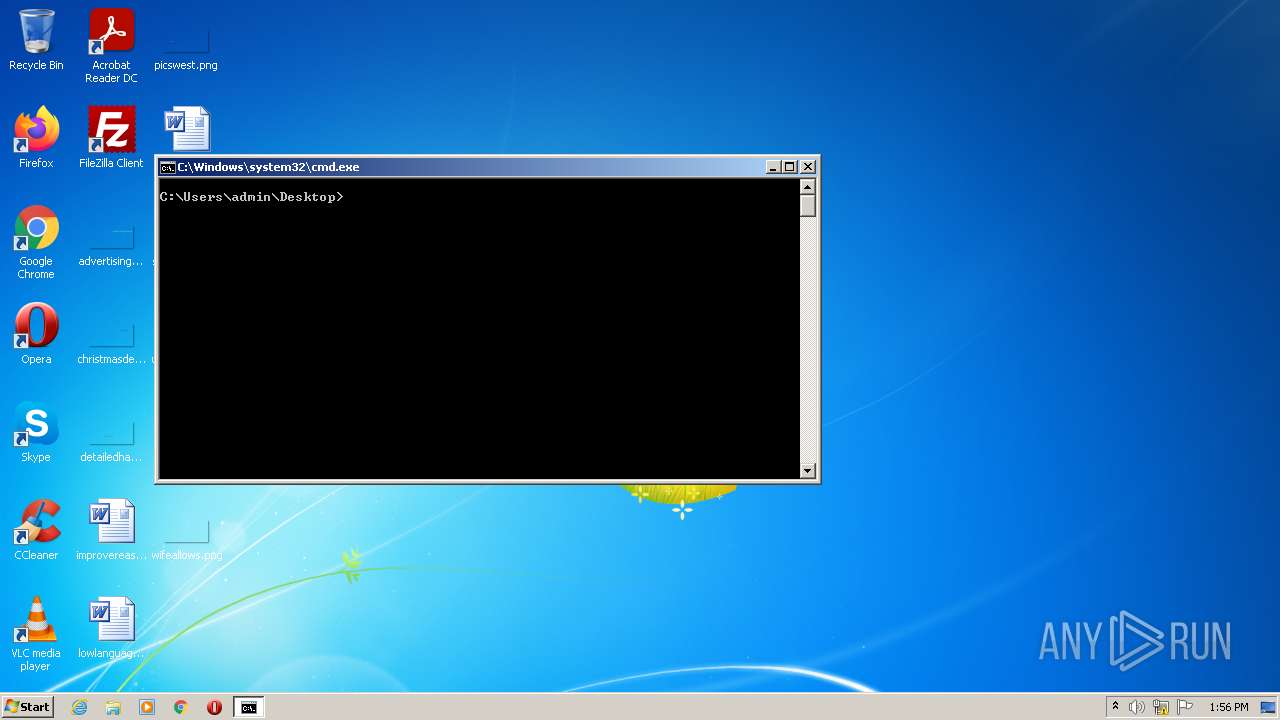
- cmd.exe (PID: 1776)
- explorer.exe (PID: 3224)
- A1wTXwJe.exe (PID: 2388)
- taskmgr.exe (PID: 3080)
- A1wTXwJe.exe (PID: 2652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x4559 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 89088 |
| CodeSize: | 127488 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2017:04:19 20:10:05+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Apr-2017 18:10:05 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Apr-2017 18:10:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F0D4 | 0x0001F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42906 |
.rdata | 0x00021000 | 0x00001F9E | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.89212 |
.data | 0x00023000 | 0x000124BC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.88902 |
.rsrc | 0x00036000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71377 |
.reloc | 0x00037000 | 0x00001260 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.74524 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Total processes
56
Monitored processes
14
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1776 | "cmd.exe" /s /k pushd "C:\Users\admin\Desktop" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1800 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
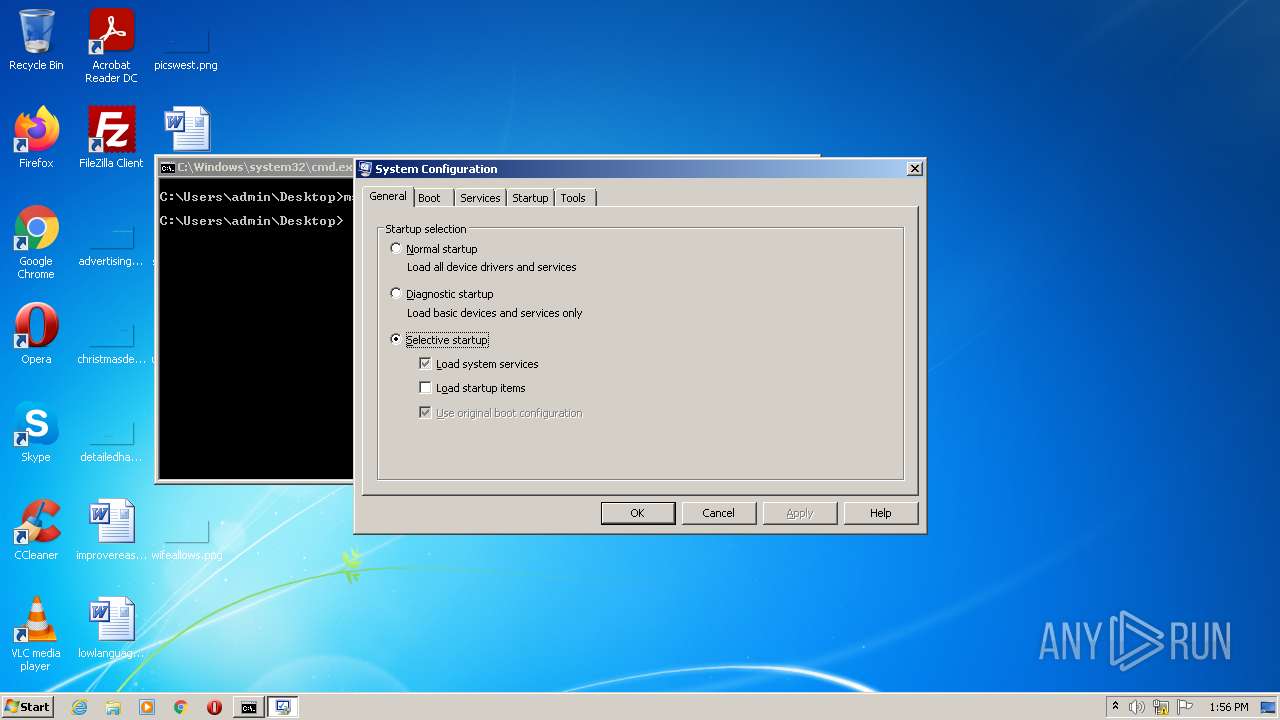
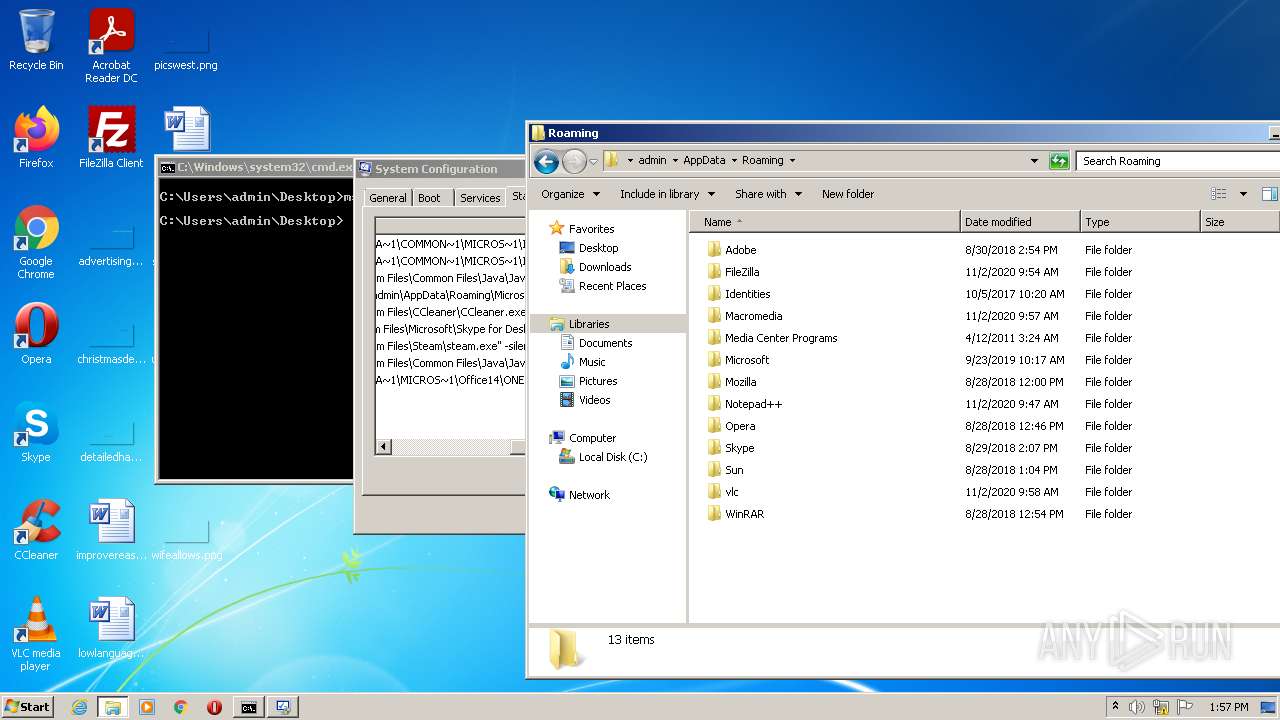
| 2252 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Configuration Utility Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
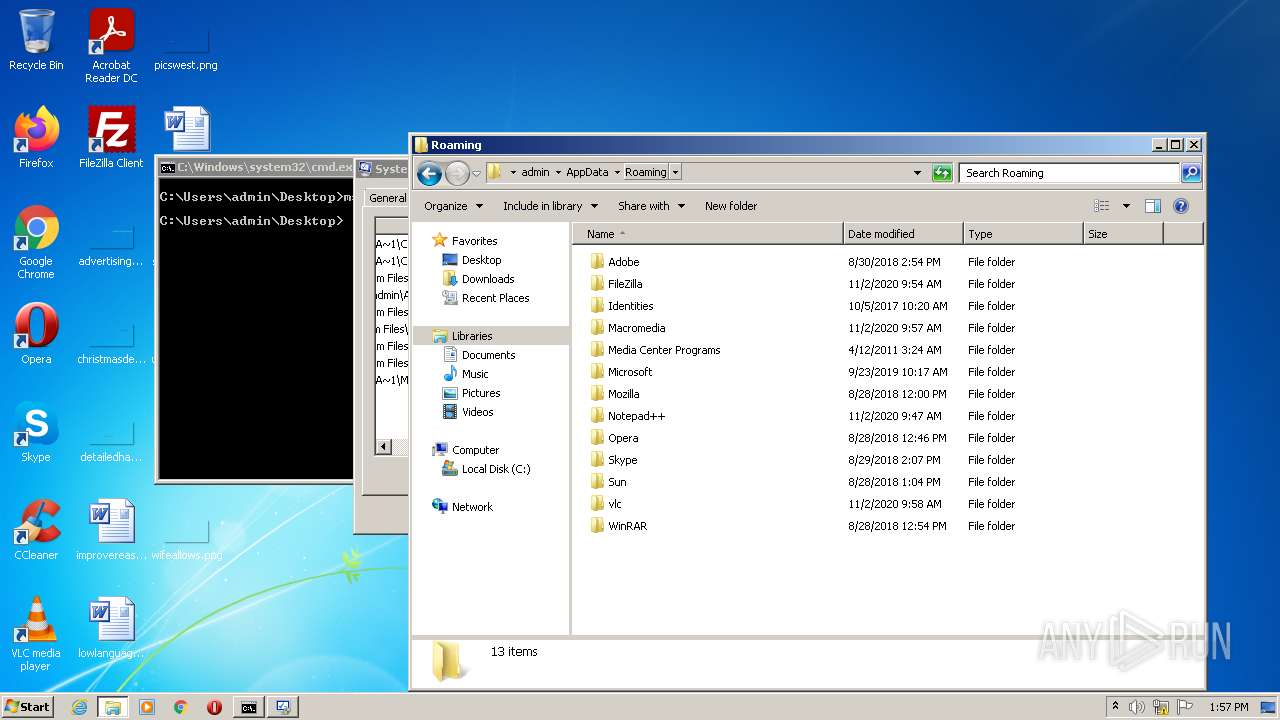
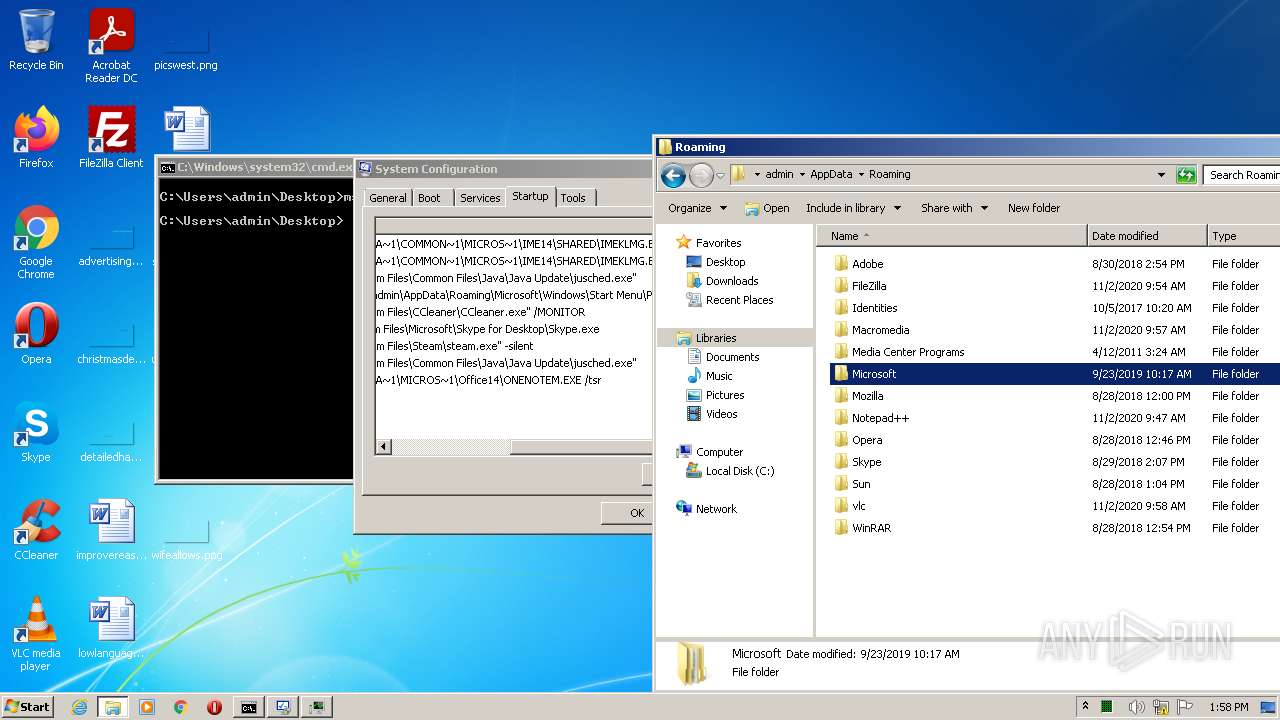
| 2388 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\A1wTXwJe.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\A1wTXwJe.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2652 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\A1wTXwJe.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\A1wTXwJe.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2832 | "C:\Users\admin\Desktop\Demo.exe" | C:\Users\admin\Desktop\Demo.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3080 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 513
Read events
2 501
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3144) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (3144) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000004503000086000000DD0400006C0200000200000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (1776) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1776) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1776) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1776) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3080) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (3080) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000004503000086000000DD0400006C0200000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
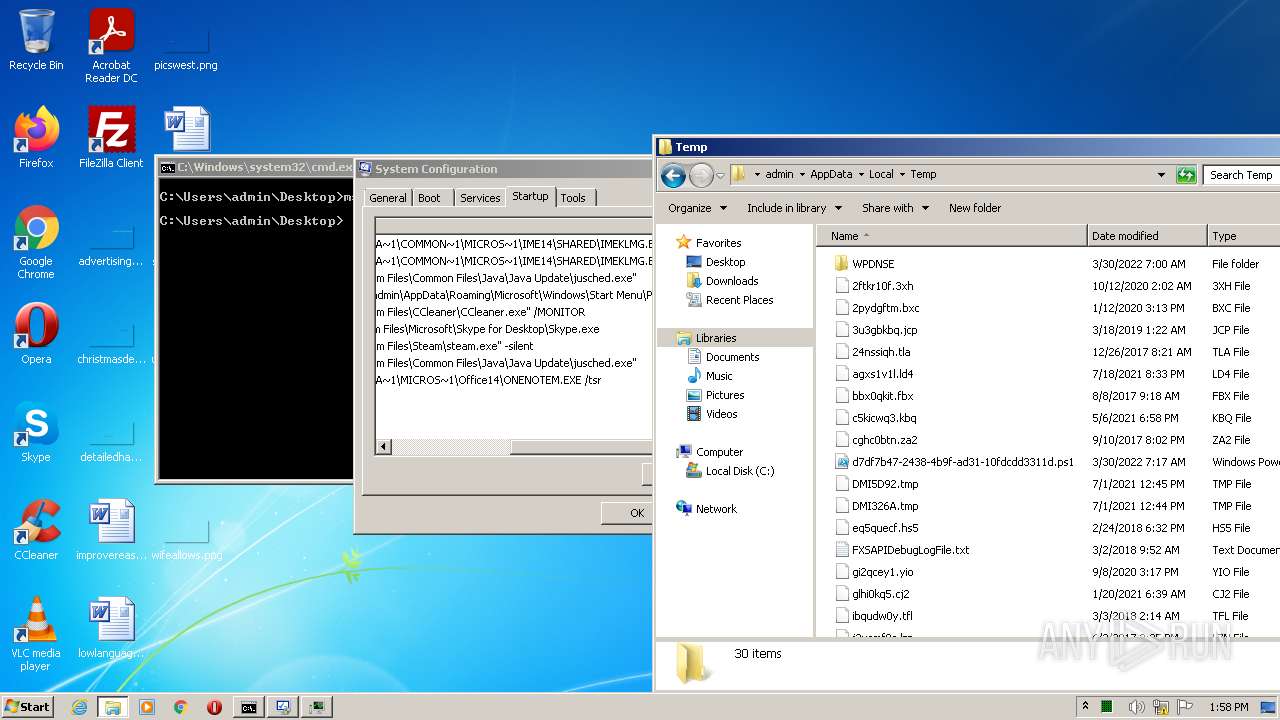
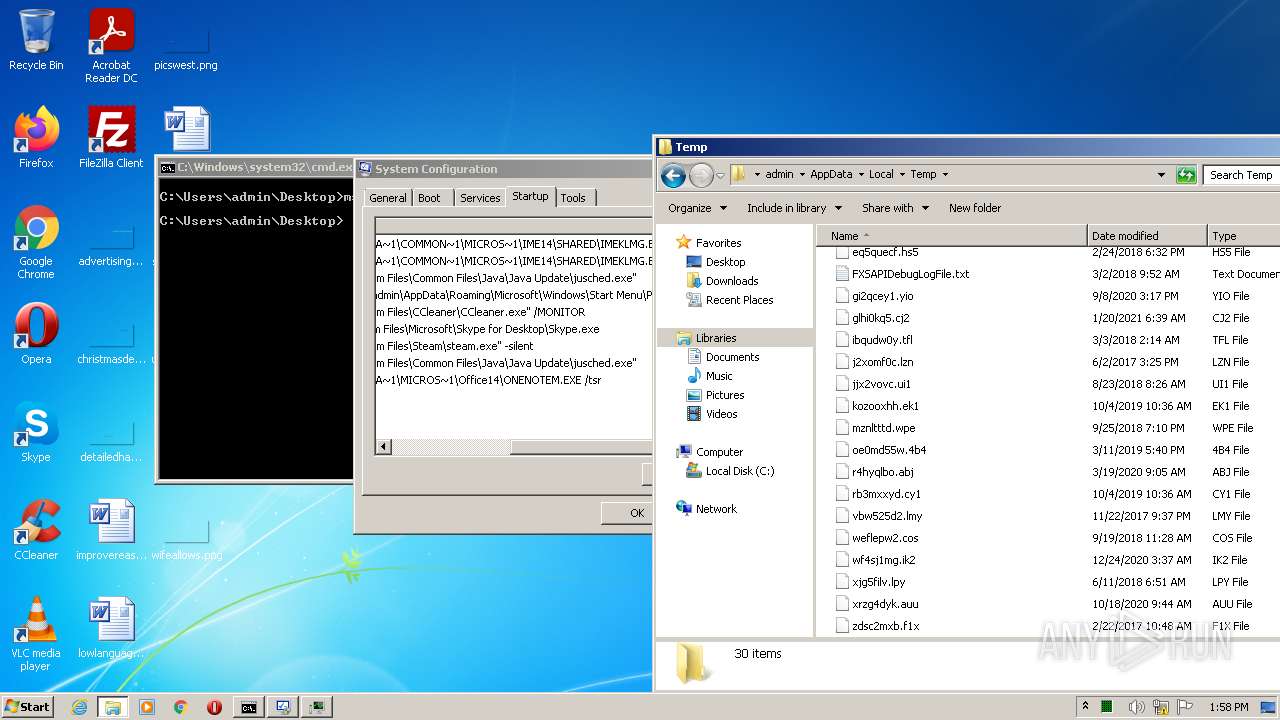
Executable files
2
Suspicious files
7
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | svchost.exe | C:\ProgramData\Mozilla\A1wTXwJeZldfWVUMBA.bin | — | |
MD5:— | SHA256:— | |||
| 3156 | svchost.exe | C:\Users\Public\Favorites\A1wTXwJe.exe | executable | |
MD5:8E5AB927B57966CB59A9BCFC88D54ECC | SHA256:A02B814E1AFB9CD910C22912E59F7B13C090F74266E904A5619119CBA80BE691 | |||
| 3156 | svchost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\A1wTXwJe.exe | executable | |
MD5:8E5AB927B57966CB59A9BCFC88D54ECC | SHA256:A02B814E1AFB9CD910C22912E59F7B13C090F74266E904A5619119CBA80BE691 | |||
| 3156 | svchost.exe | C:\ProgramData\Mozilla\1090765.txt | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
| 3156 | svchost.exe | C:\ProgramData\1090765.txt | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
| 3156 | svchost.exe | C:\ProgramData\Adobe\1090765.txt | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
| 3156 | svchost.exe | C:\ProgramData\Skype\1090765.txt | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
| 3156 | svchost.exe | C:\Users\Public\Documents\1090765.txt | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
| 3156 | svchost.exe | C:\ProgramData\Oracle\1090765.txt | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
| 3156 | svchost.exe | C:\Users\Public\Favorites\1090765.txt | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report