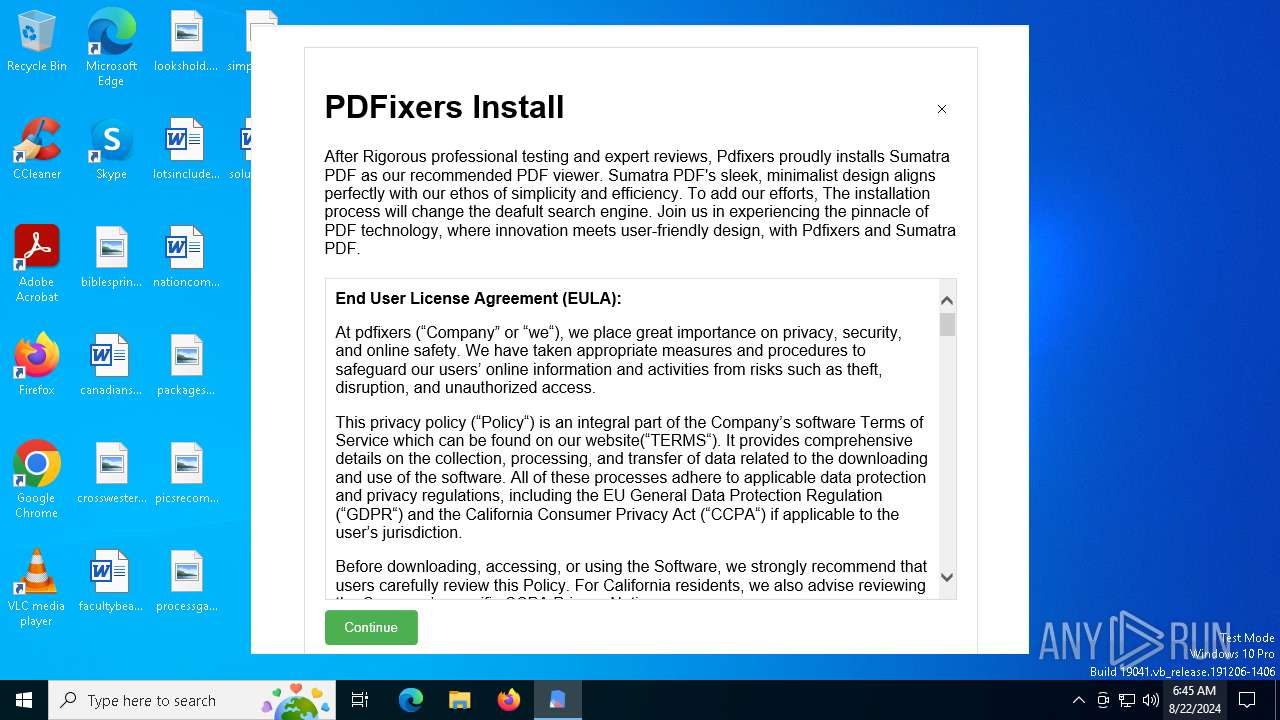
| File name: | PDFixers.exe |
| Full analysis: | https://app.any.run/tasks/adcf08d7-299f-464e-be59-275687364d81 |
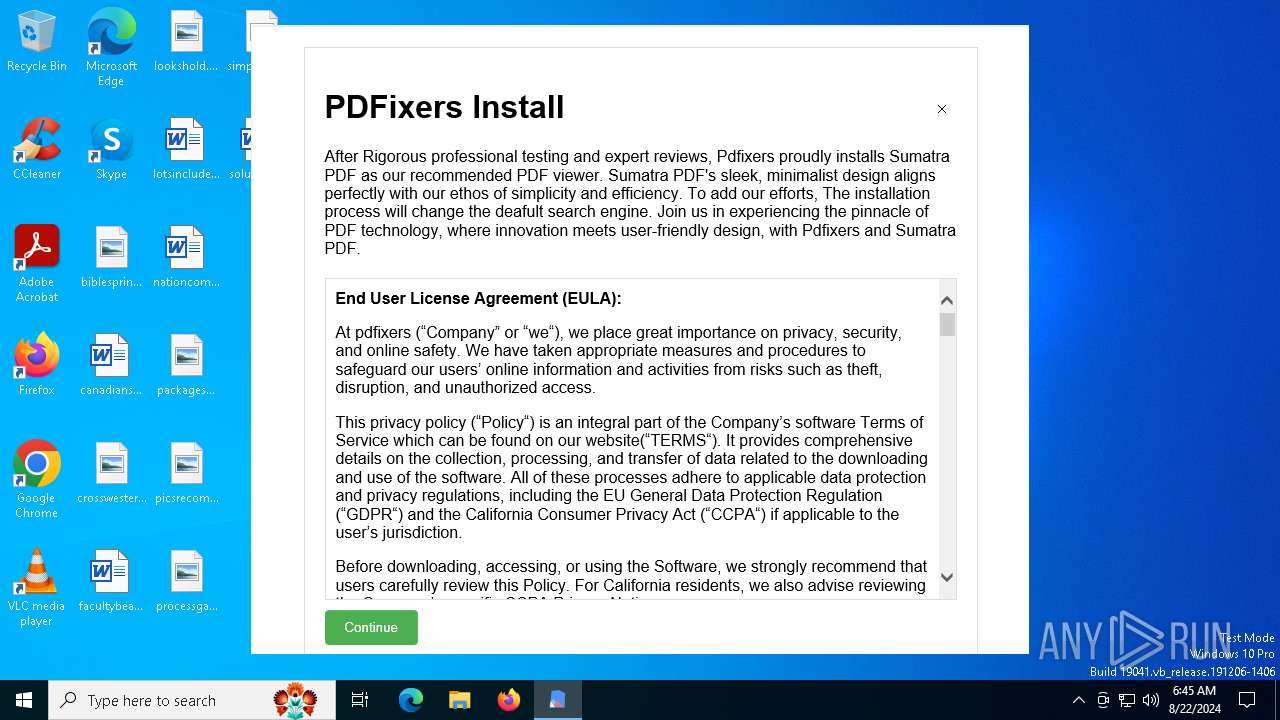
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 06:45:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows |
| MD5: | B4440EEA7367C3FB04A89225DF4022A6 |
| SHA1: | 5A6C01F821F10F6ED1F1283ECBA36C5BACFB5838 |
| SHA256: | A024A18E27707738ADCD7B5A740C5A93534B4B8C9D3B947F6D85740AF19D17D0 |
| SSDEEP: | 98304:NKaPGf3Lx51clR43g0ZtKC5/TF4i9bYvQCPjhPXq2fZWwZmchG6QjvOr/av7Vx6U:Lm3qrzPw0jtrQp |
MALICIOUS
Scans artifacts that could help determine the target
- PDFixers.exe (PID: 6748)
SUSPICIOUS
Reads security settings of Internet Explorer
- PDFixers.exe (PID: 6748)
Drops the executable file immediately after the start
- PDFixers.exe (PID: 6748)
Reads Microsoft Outlook installation path
- PDFixers.exe (PID: 6748)
Reads Internet Explorer settings
- PDFixers.exe (PID: 6748)
Checks Windows Trust Settings
- PDFixers.exe (PID: 6748)
INFO
Reads the computer name
- PDFixers.exe (PID: 6748)
Checks supported languages
- PDFixers.exe (PID: 6748)
Reads the machine GUID from the registry
- PDFixers.exe (PID: 6748)
Process checks Internet Explorer phishing filters
- PDFixers.exe (PID: 6748)
Checks proxy server information
- PDFixers.exe (PID: 6748)
Reads the software policy settings
- PDFixers.exe (PID: 6748)
Creates files or folders in the user directory
- PDFixers.exe (PID: 6748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2054:11:16 06:26:21+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 80 |
| CodeSize: | 8382976 |
| InitializedDataSize: | 112128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Pdfixers |
| FileVersion: | 1.0.0.0 |
| InternalName: | Pdfixers.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Pdfixers.exe |
| ProductName: | Pdfixers |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
145
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 5712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6748 | "C:\Users\admin\AppData\Local\Temp\PDFixers.exe" | C:\Users\admin\AppData\Local\Temp\PDFixers.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Pdfixers Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 971
Read events
1 960
Write events
11
Delete events
0
Modification events
| (PID) Process: | (6748) PDFixers.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6748) PDFixers.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6748) PDFixers.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6748) PDFixers.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6748) PDFixers.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6748) PDFixers.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6748) PDFixers.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
12
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6748 | PDFixers.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\AT0K8AW3.htm | html | |
MD5:CDA63CB71D7977B010E34ACF88FA213D | SHA256:5367D53EEA9A13F15A8C0DEABCC29EC4ED1FC4ED8DD6EC27809711FDCA4D6B9F | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | der | |
MD5:7FB5FA1534DCF77F2125B2403B30A0EE | SHA256:33A39E9EC2133230533A686EC43760026E014A3828C703707ACBC150FE40FD6F | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:E13CC4D47506D2E843F6BE5F3B20E456 | SHA256:482BCA7D7CE23A2CE4383AE7F38AC2A7C67C7BCE5188AEF2922E6A414592B18A | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:CFB6DB993EE3B44C1BC2A4556378C0DC | SHA256:DDADE0233BB9800AB76D070E7CA443659E8521803884FF8F3A79DC7EB7D381F7 | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4FA45AE1010E09657982D8D28B3BD38E_BE32D9F1882B93E37445F58E05C44495 | der | |
MD5:E0C50D942EB3DCFACB16E473499E4F82 | SHA256:63897126B3840D76366B12A3A096F47131F3B34AA5C240B66BB10D2667128D1D | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4FA45AE1010E09657982D8D28B3BD38E_BE32D9F1882B93E37445F58E05C44495 | binary | |
MD5:4A73959F551B6DB45CE4E86D9AF3F51E | SHA256:DBBE35DA00833EF69648C5103720BF2CBE0E6DBA6D9786BF9DDB31F072A3489E | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\font[1].eot | binary | |
MD5:C6B85601ADBF8C674B4B444DAD696A5D | SHA256:EC8671B432FF49E1E77F48692397E57ECFA584555AC664C932DCCEA0C9A16044 | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:971C514F84BBA0785F80AA1C23EDFD79 | SHA256:F157ED17FCAF8837FA82F8B69973848C9B10A02636848F995698212A08F31895 | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | der | |
MD5:E935BC5762068CAF3E24A2683B1B8A88 | SHA256:A8ACCFCFEB51BD73DF23B91F4D89FF1A9EB7438EF5B12E8AFDA1A6FF1769E89D | |||
| 6748 | PDFixers.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:42474E0E3B092DFD6B81318B67ED788B | SHA256:5013FB3E897F420F42380DD34EEB7121C5FF1B8270BB07BA0B345B687F10BA64 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
73
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6748 | PDFixers.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/r4.crl | US | binary | 436 b | whitelisted |
6748 | PDFixers.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQDAezvzBOn2FxIghPLaMkP6 | US | binary | 472 b | whitelisted |
6748 | PDFixers.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
6748 | PDFixers.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQCjHbN8Q48ByBJsBZfEZOeO | US | binary | 472 b | whitelisted |
2228 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6748 | PDFixers.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/r1.crl | US | binary | 854 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4080 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4876 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
368 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6748 | PDFixers.exe | 172.67.147.142:443 | pixel.pdfixers.com | CLOUDFLARENET | US | unknown |
6748 | PDFixers.exe | 142.250.181.227:80 | c.pki.goog | GOOGLE | US | whitelisted |
6748 | PDFixers.exe | 142.250.184.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
6748 | PDFixers.exe | 216.58.206.67:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2228 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2228 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
pixel.pdfixers.com |
| unknown |
c.pki.goog |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
o.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |