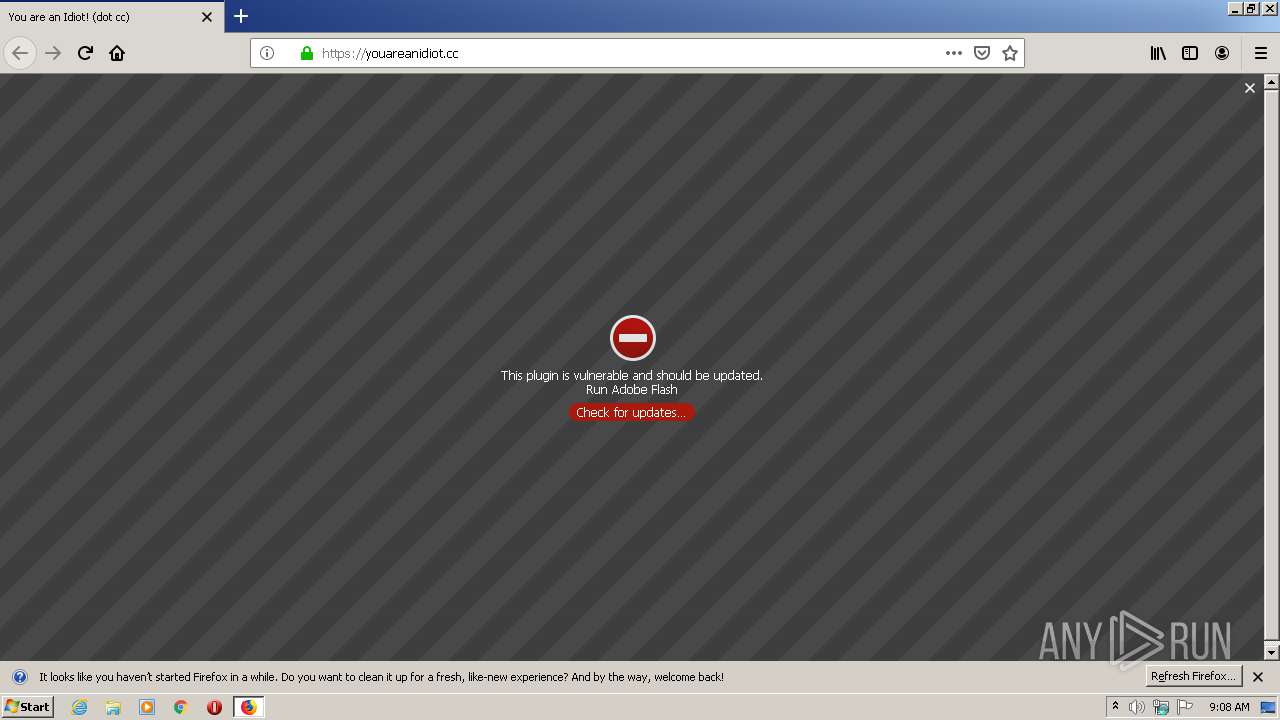
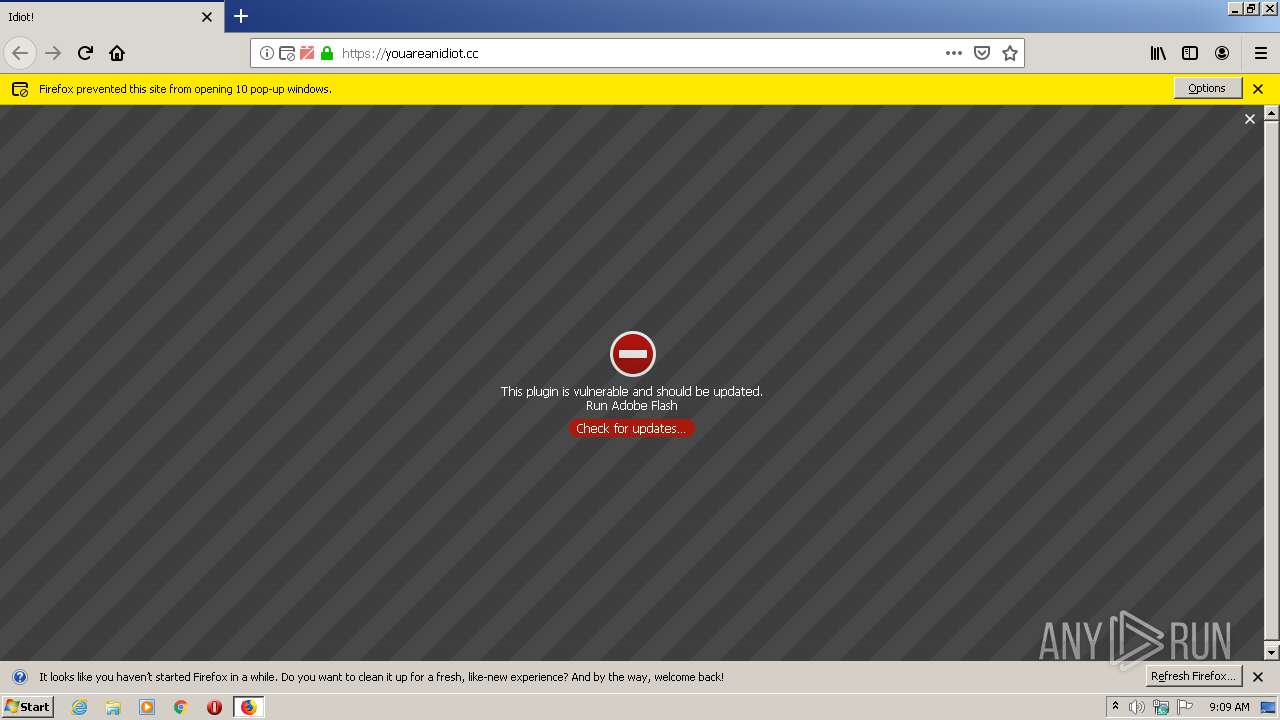
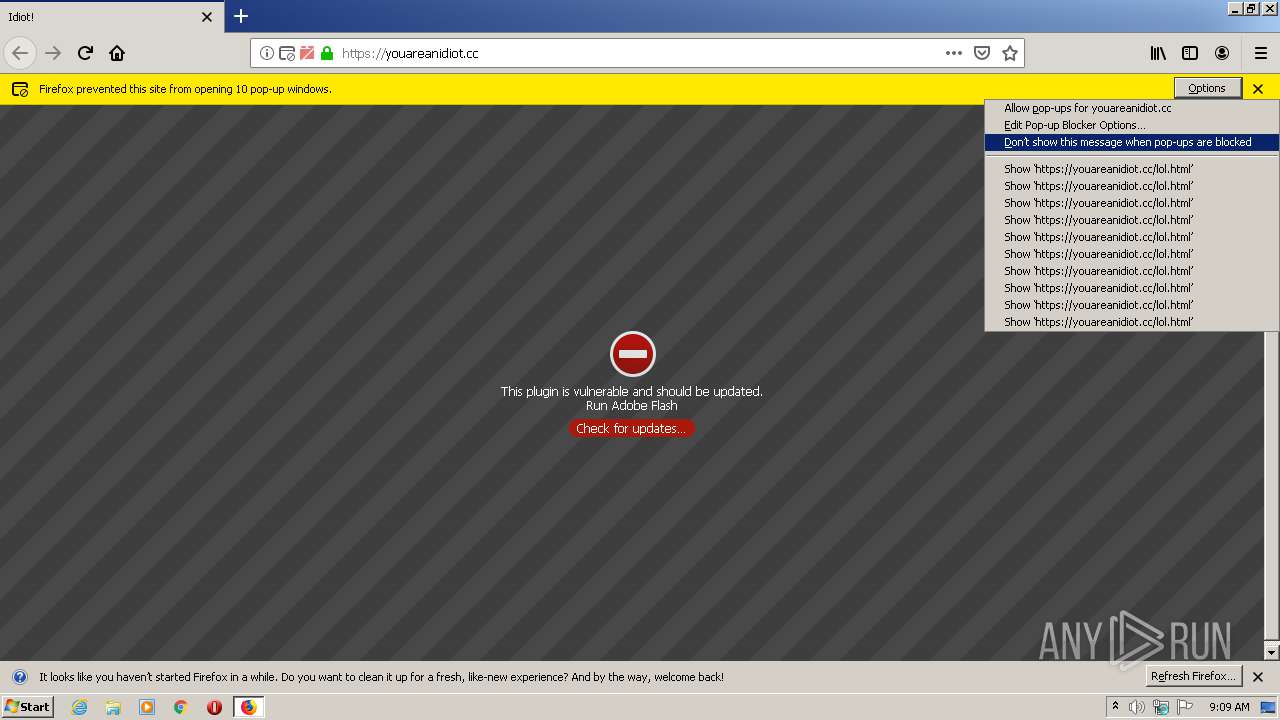
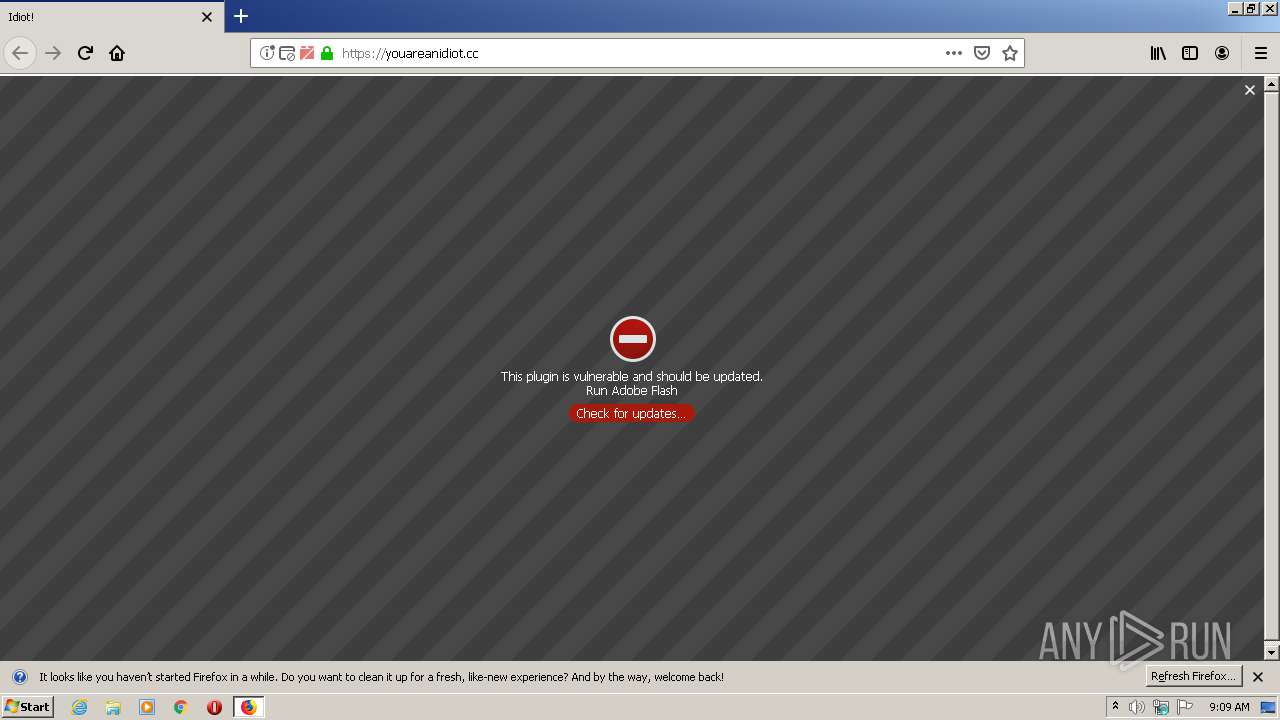
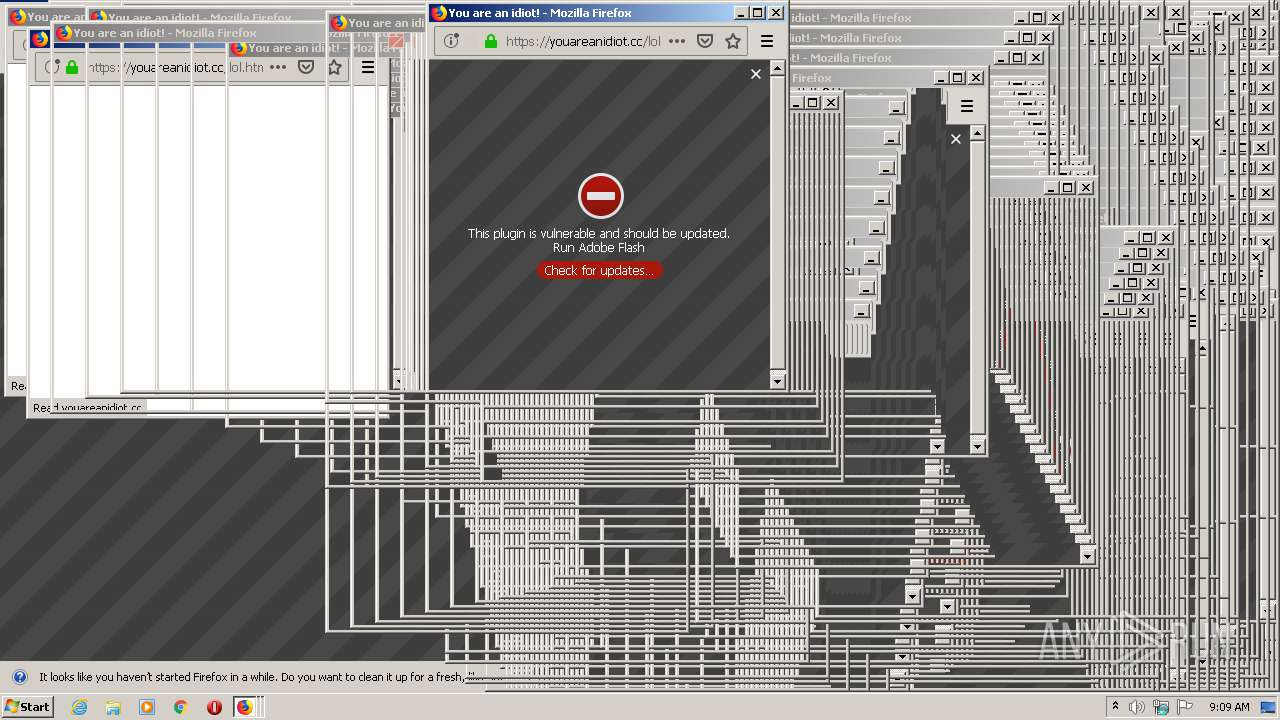
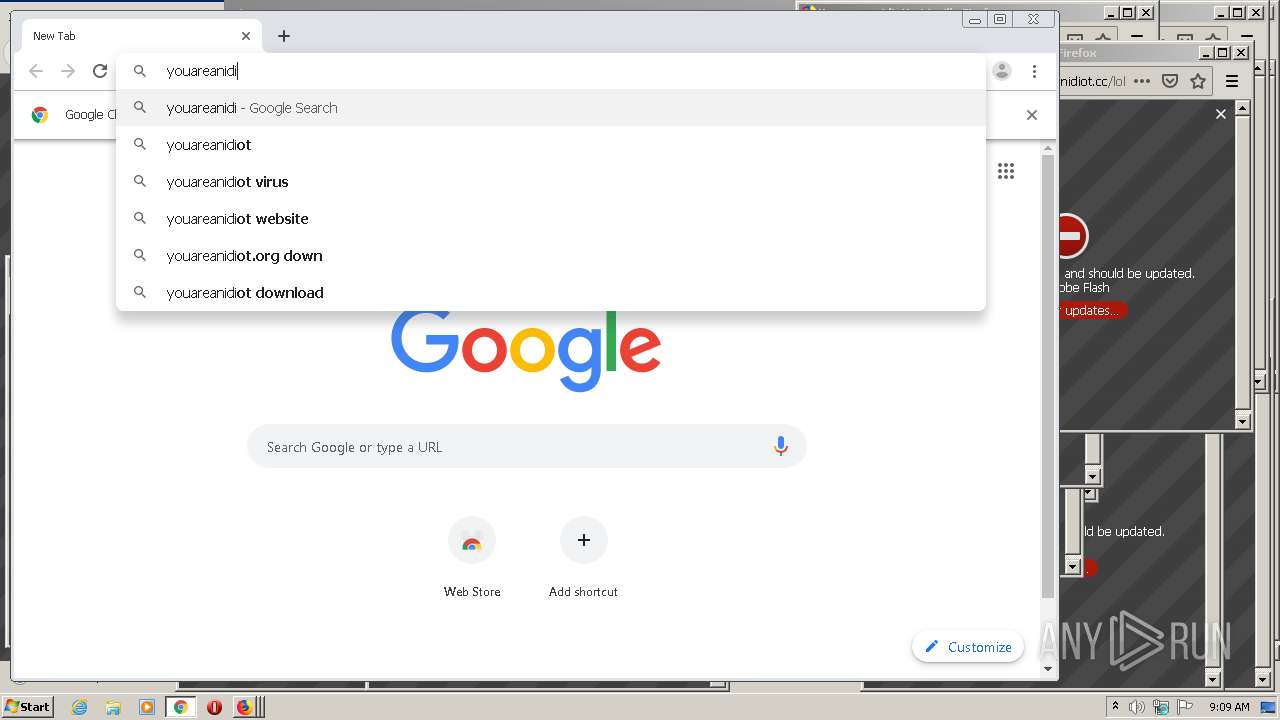
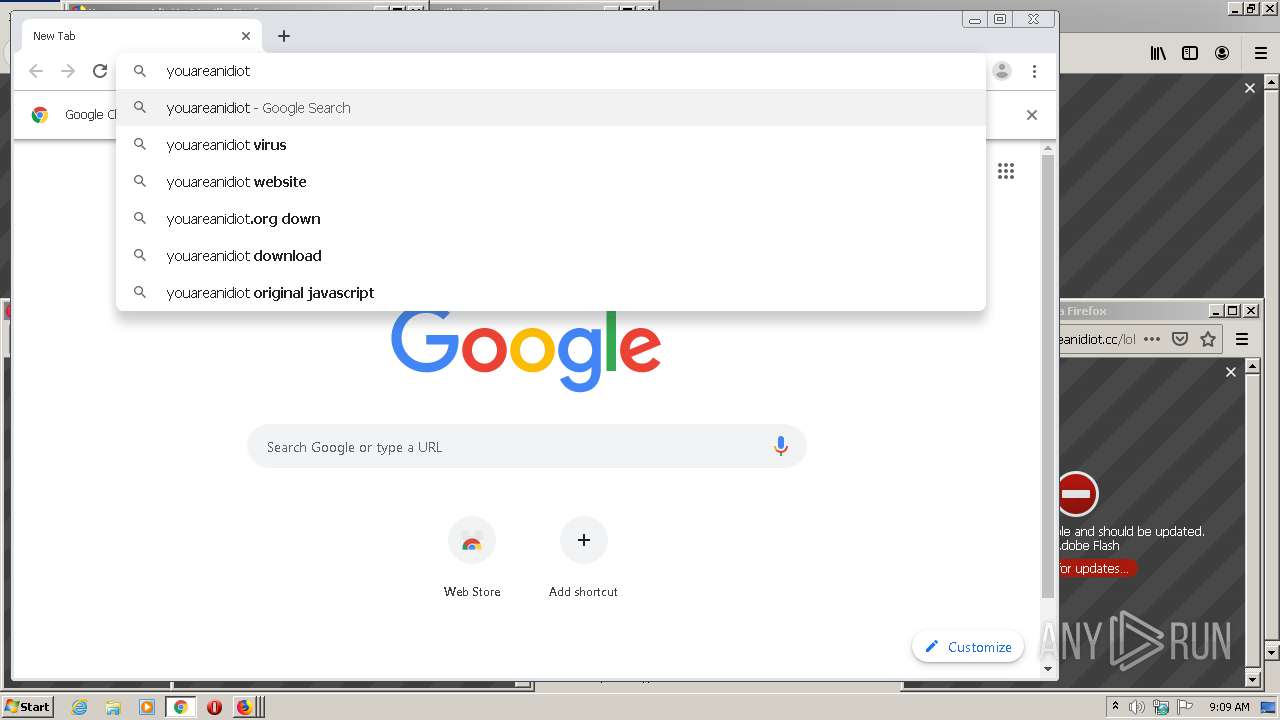
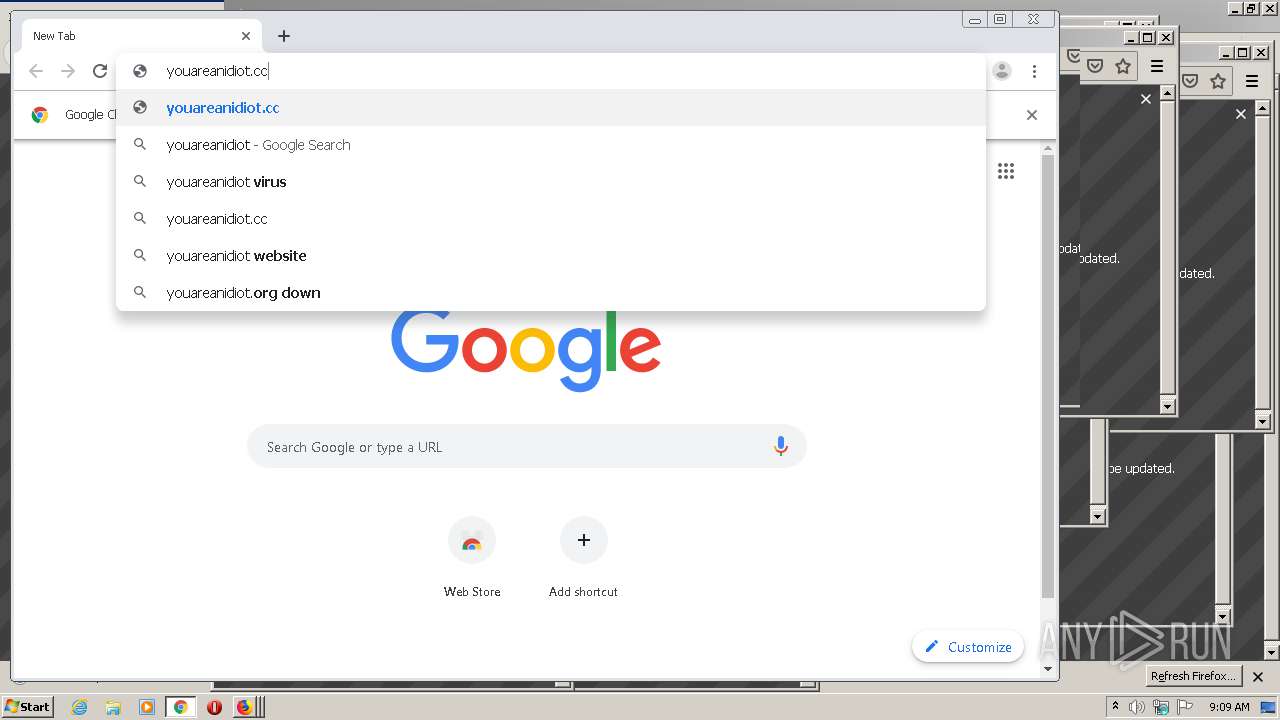
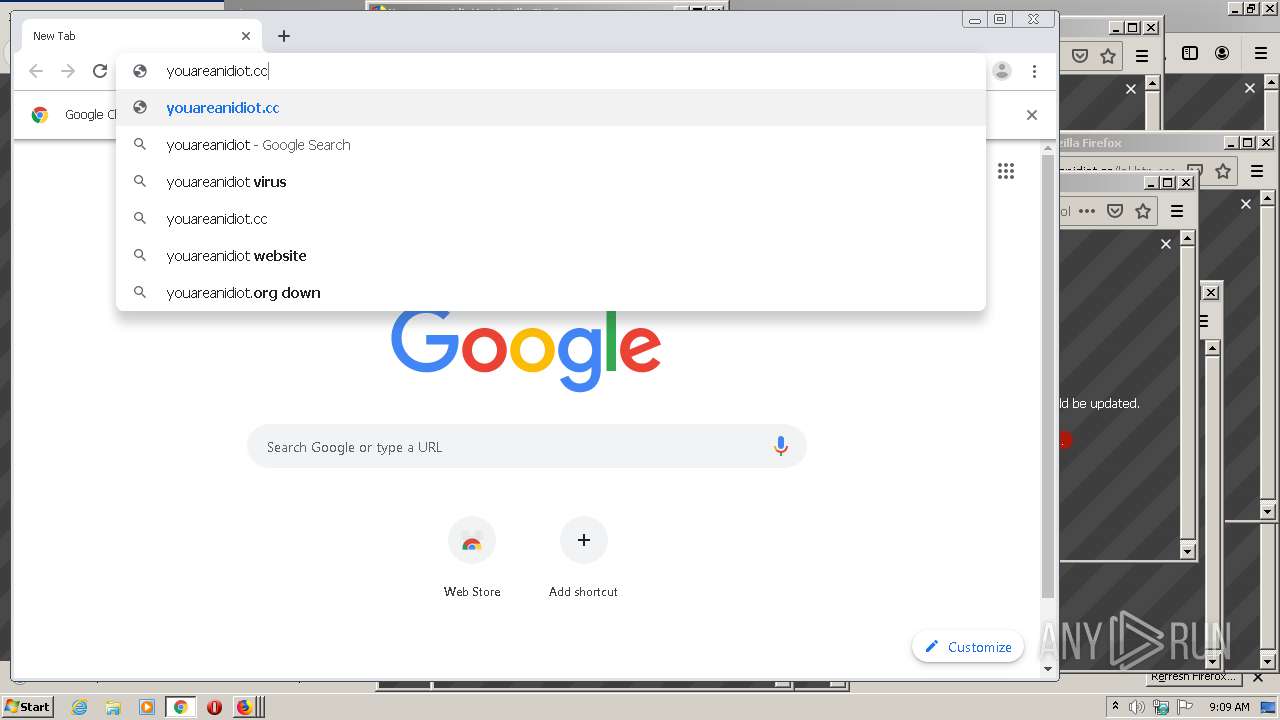
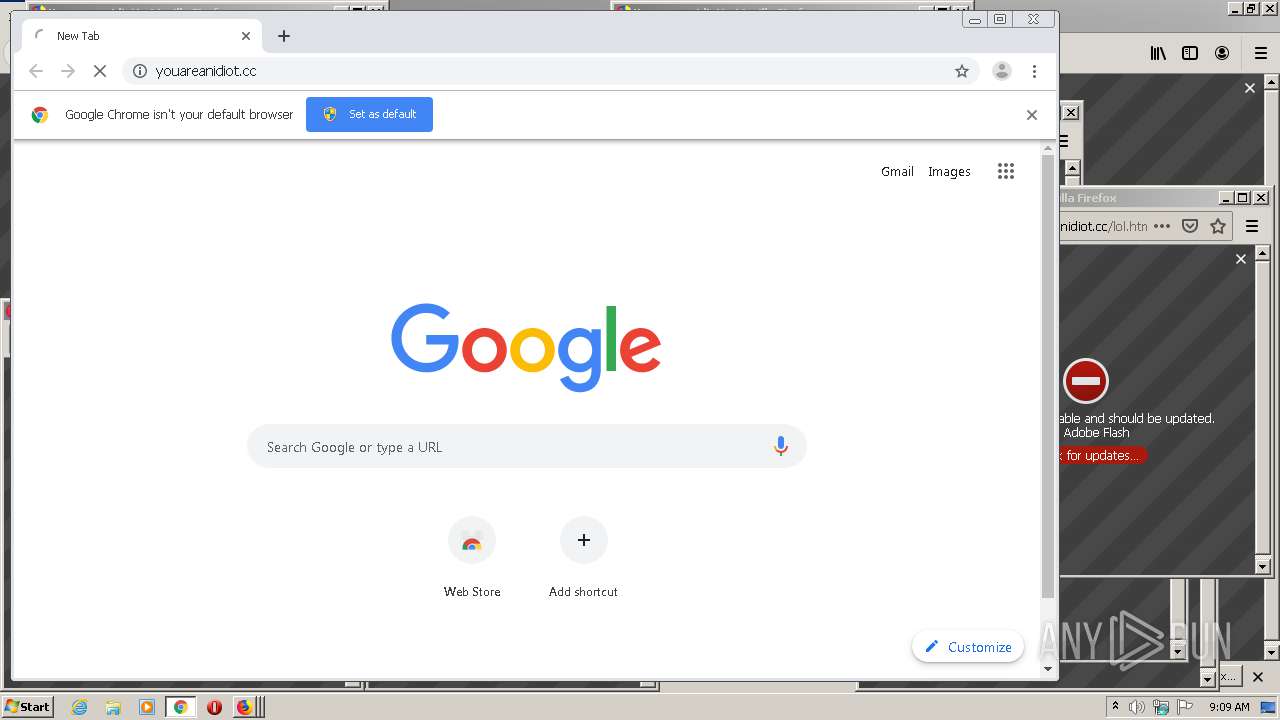
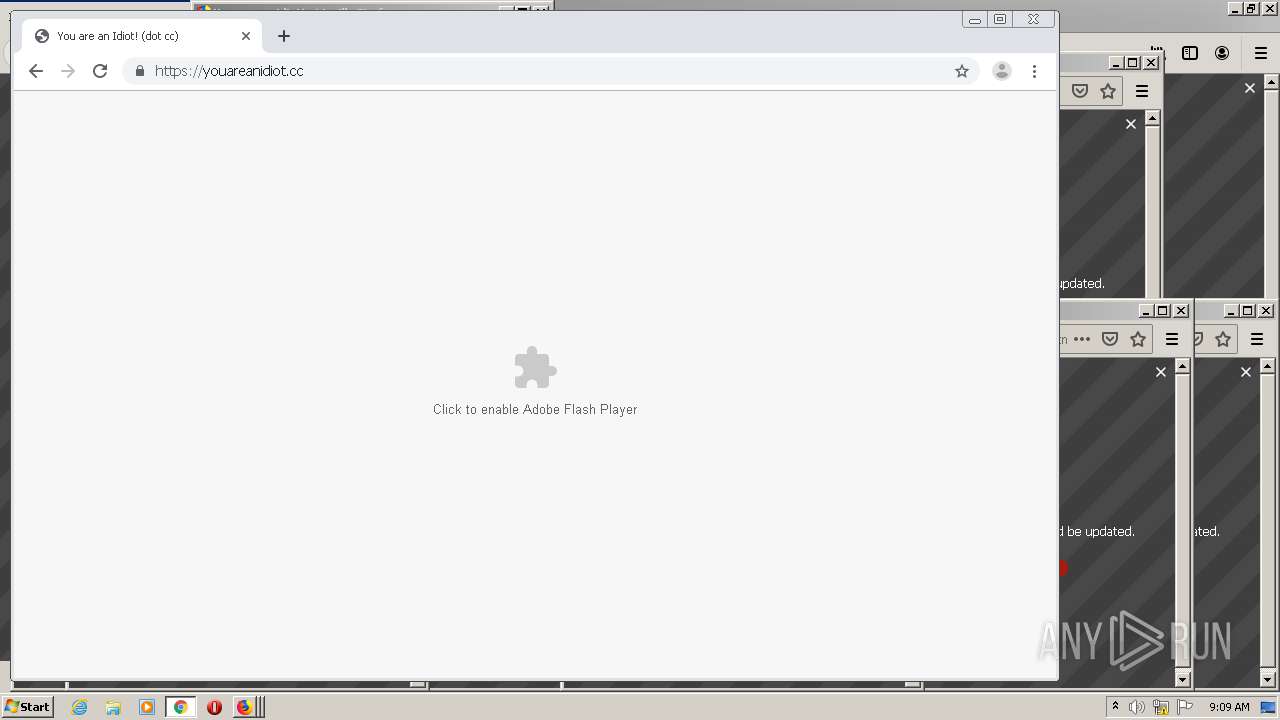
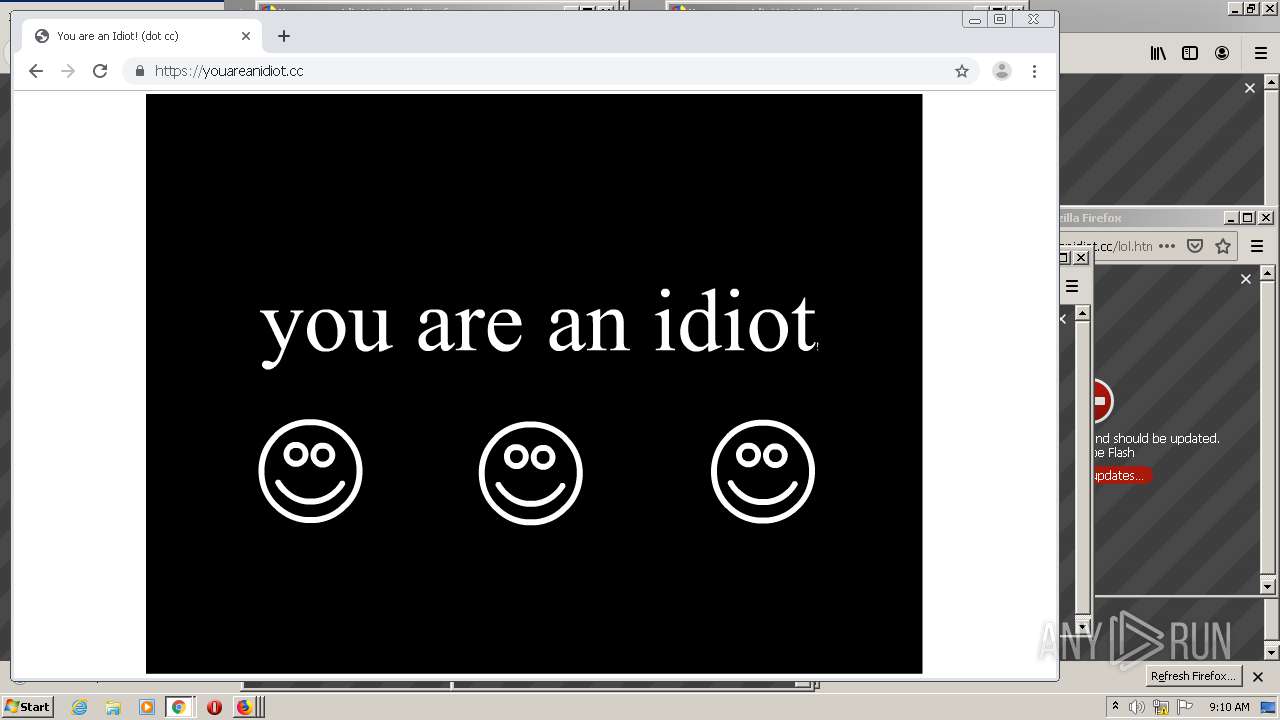
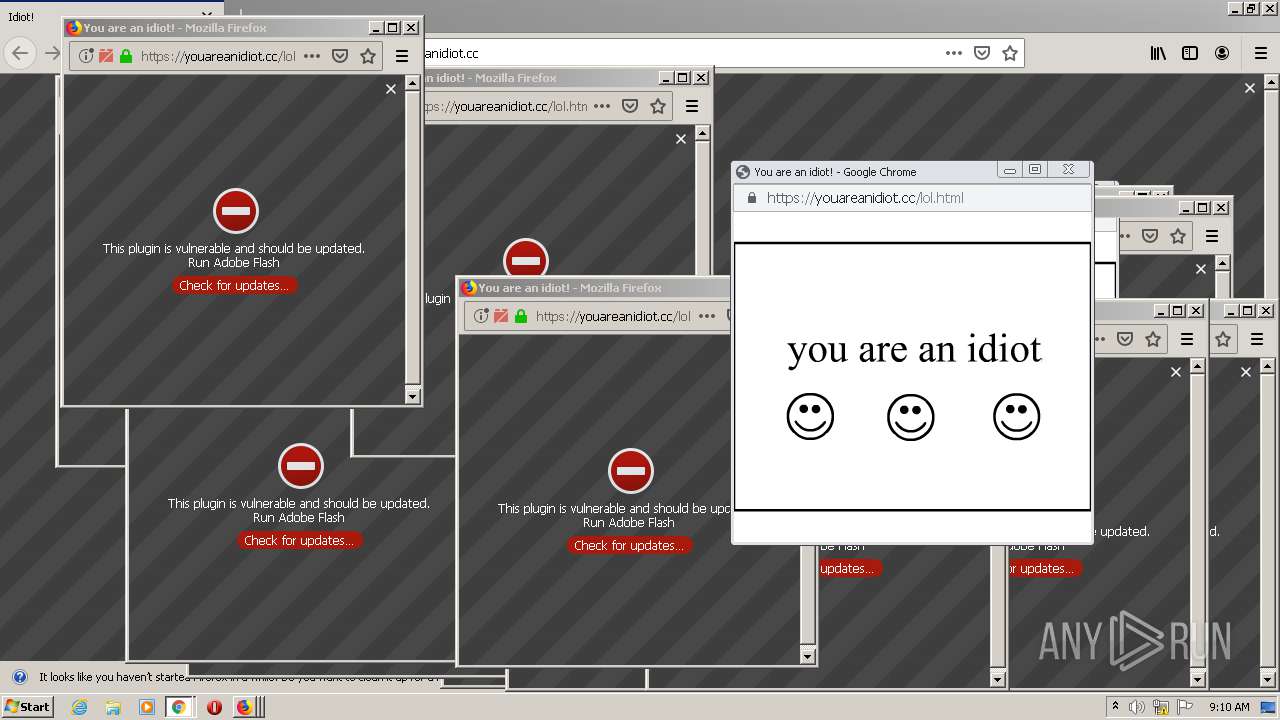
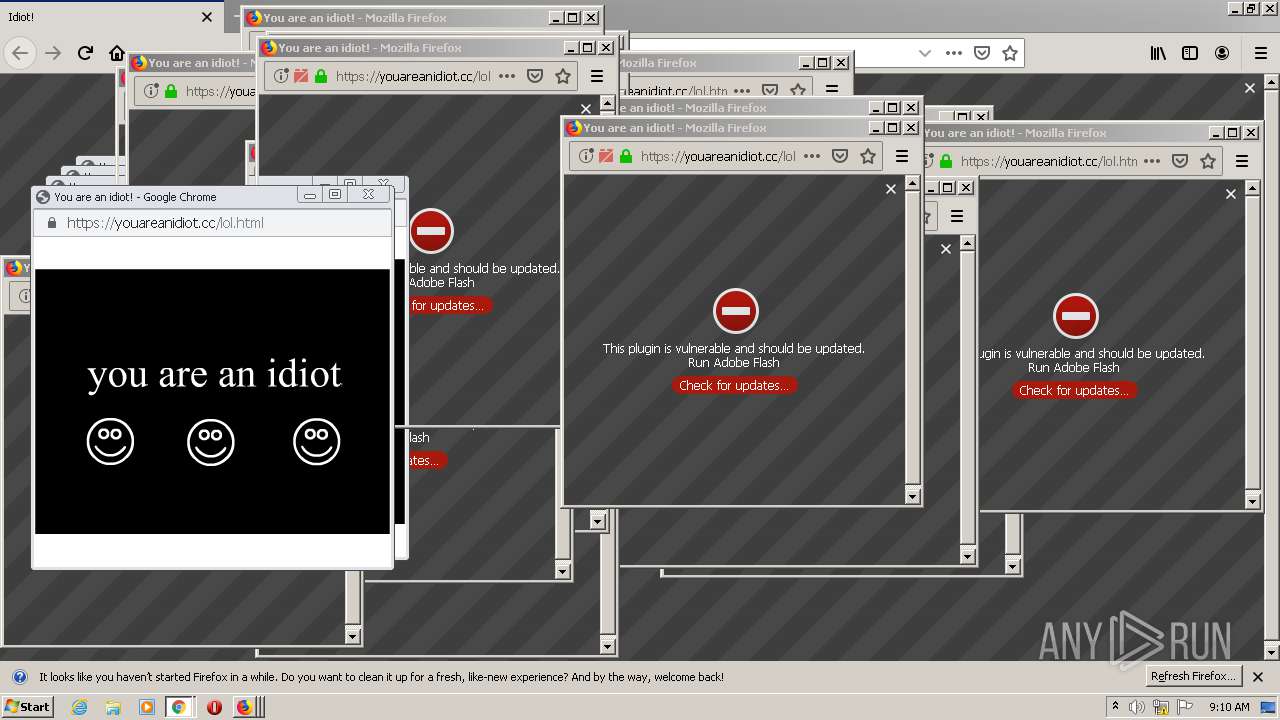
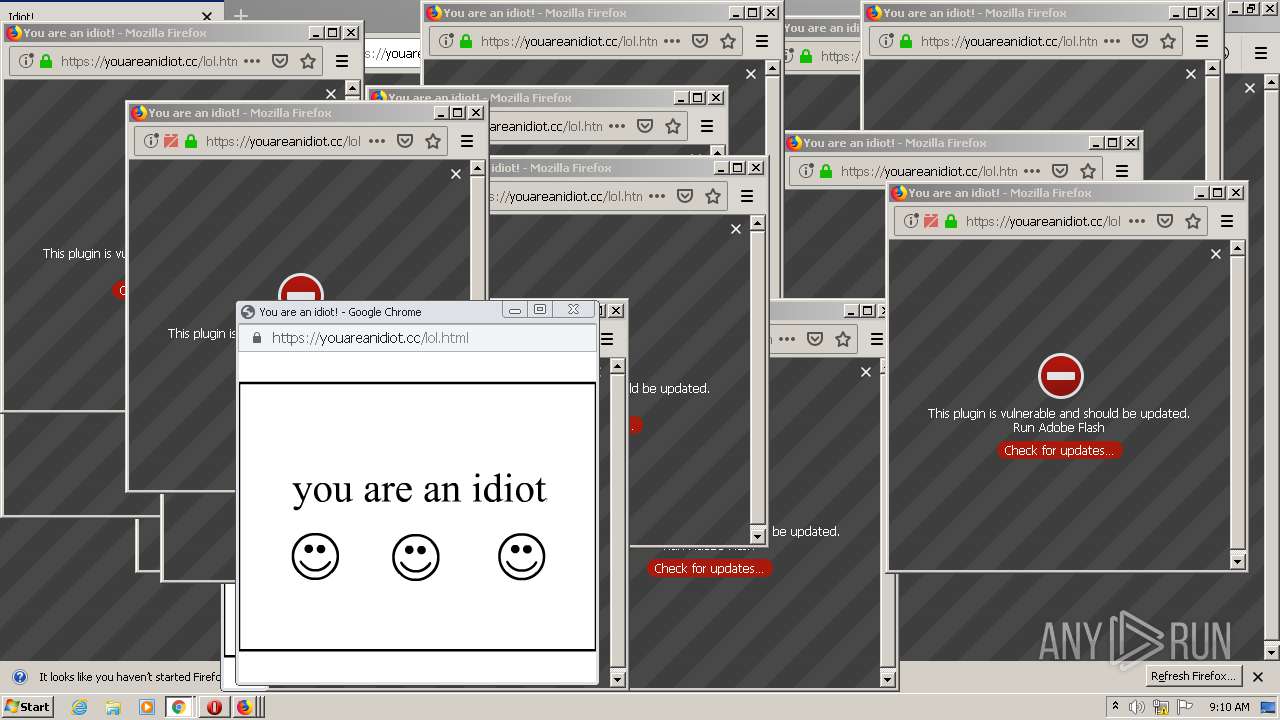
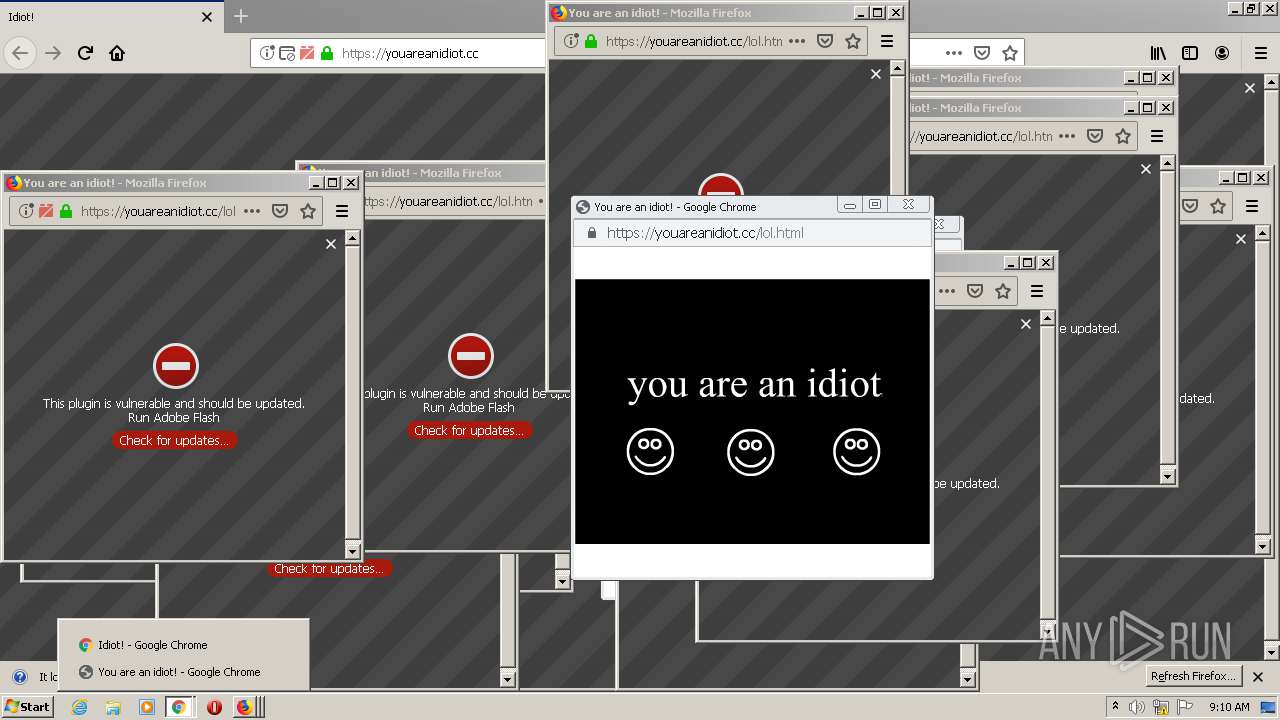
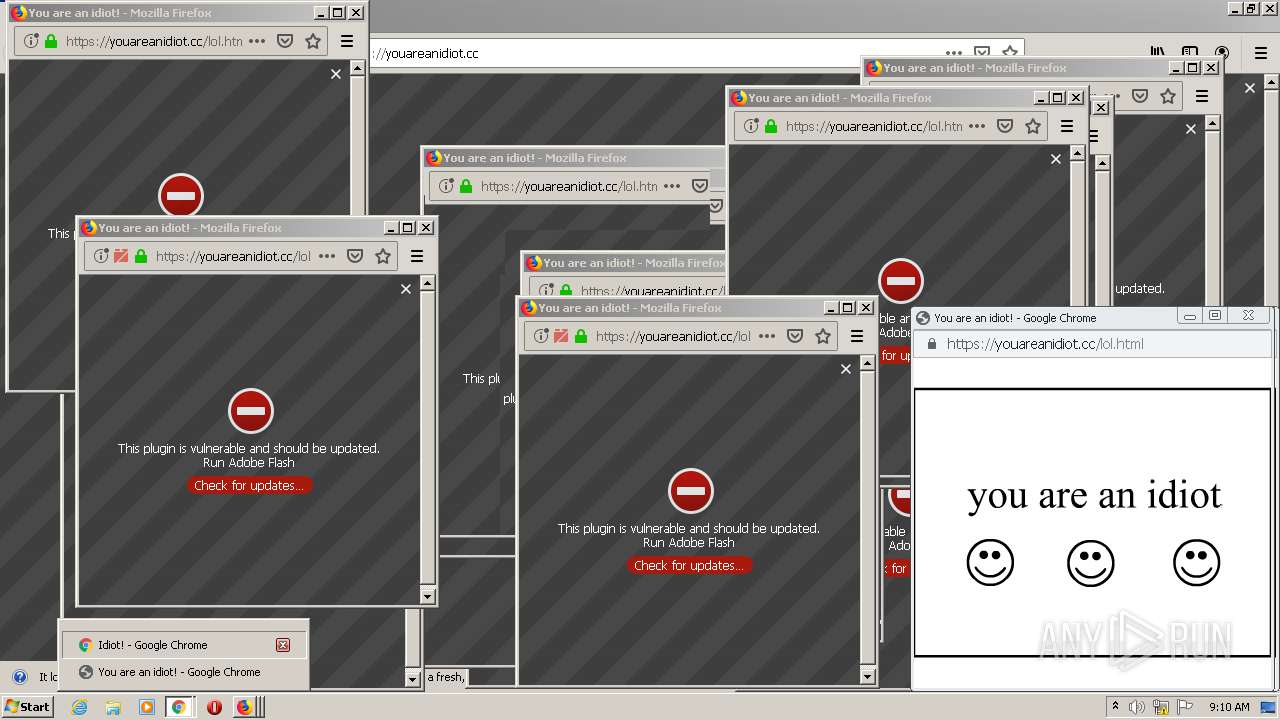
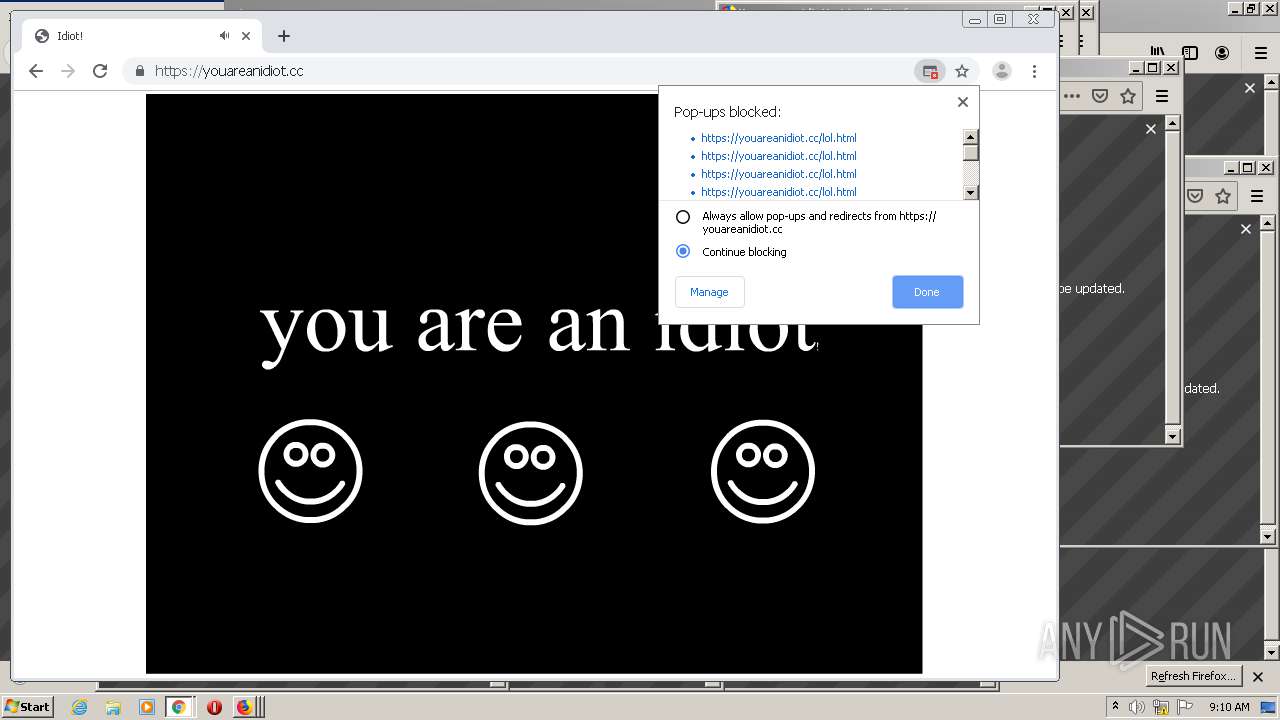
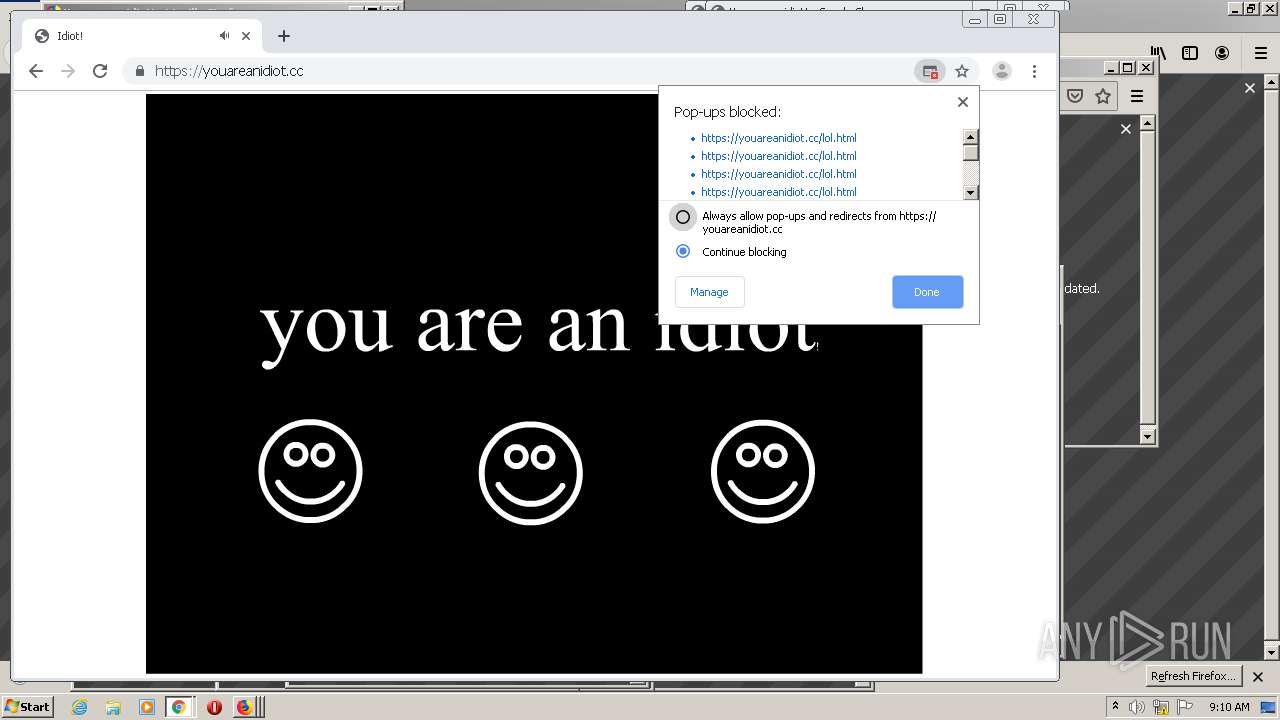
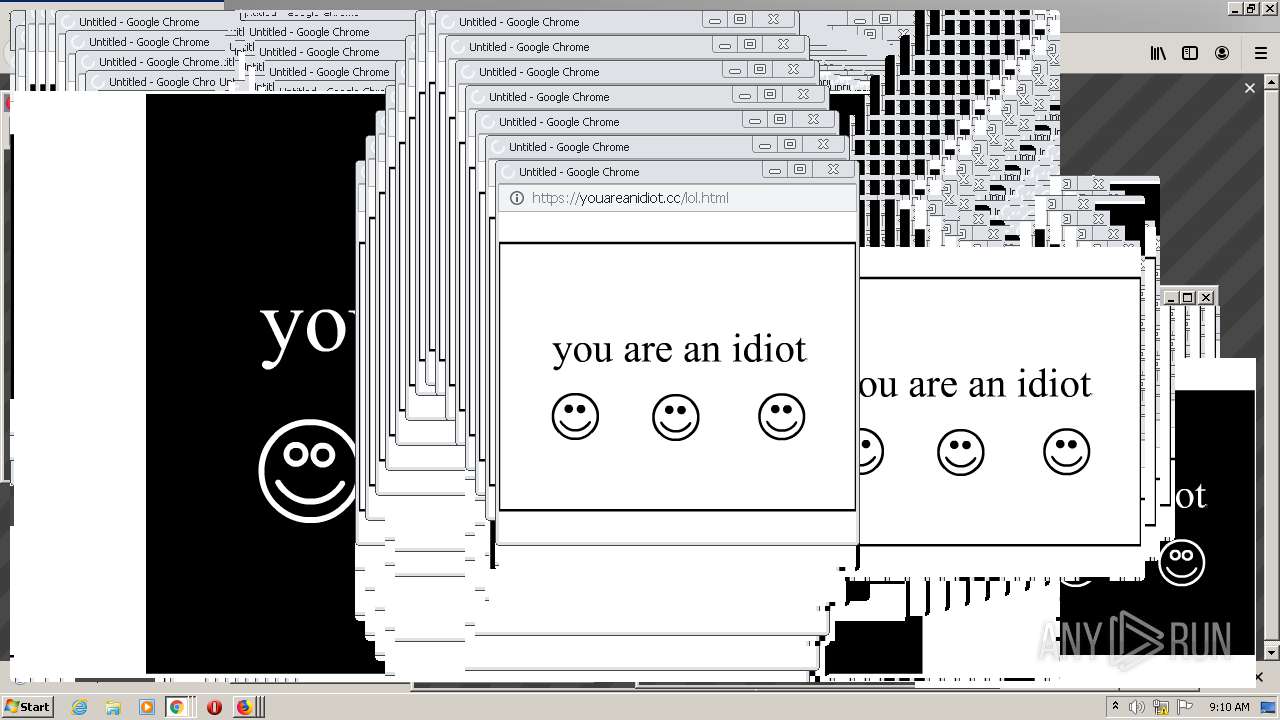
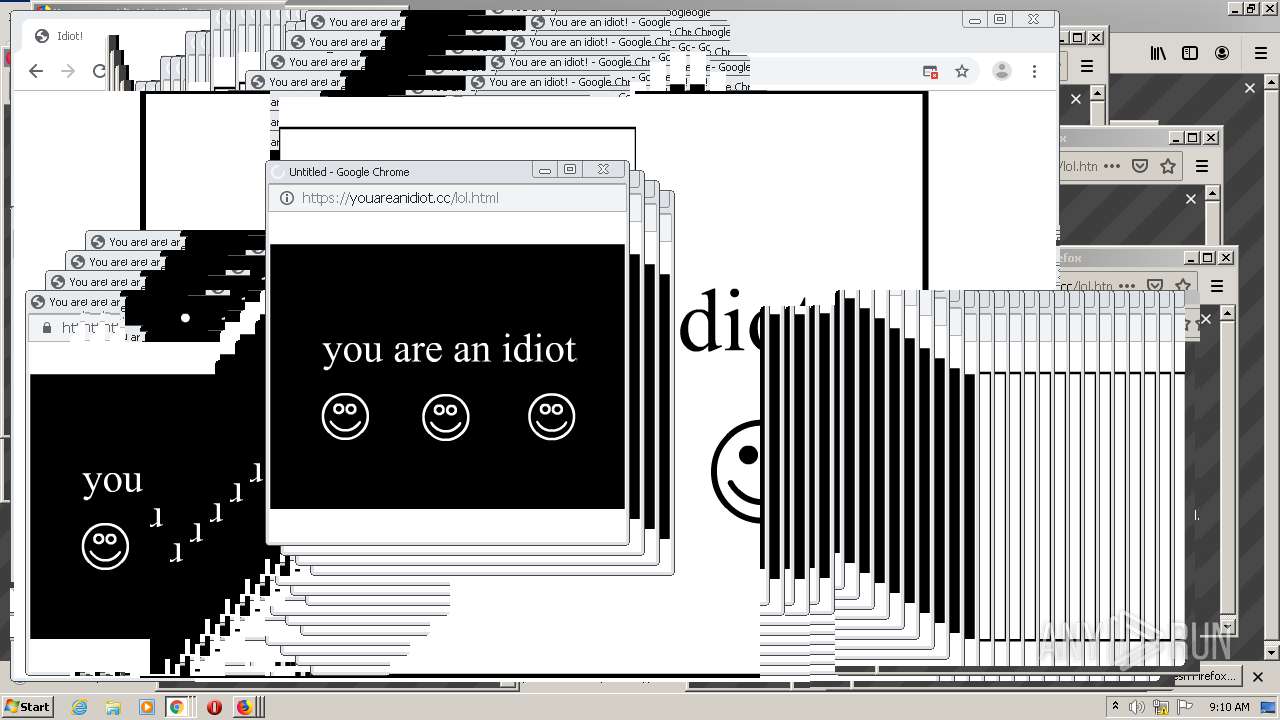
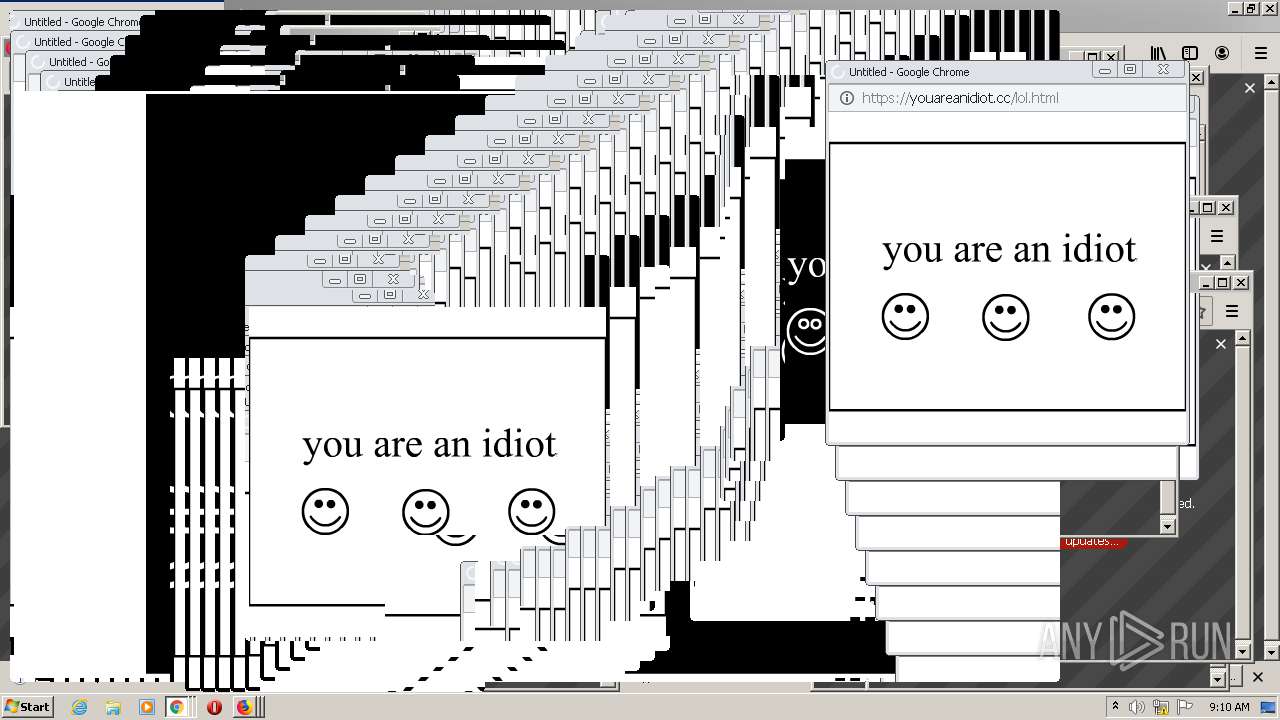
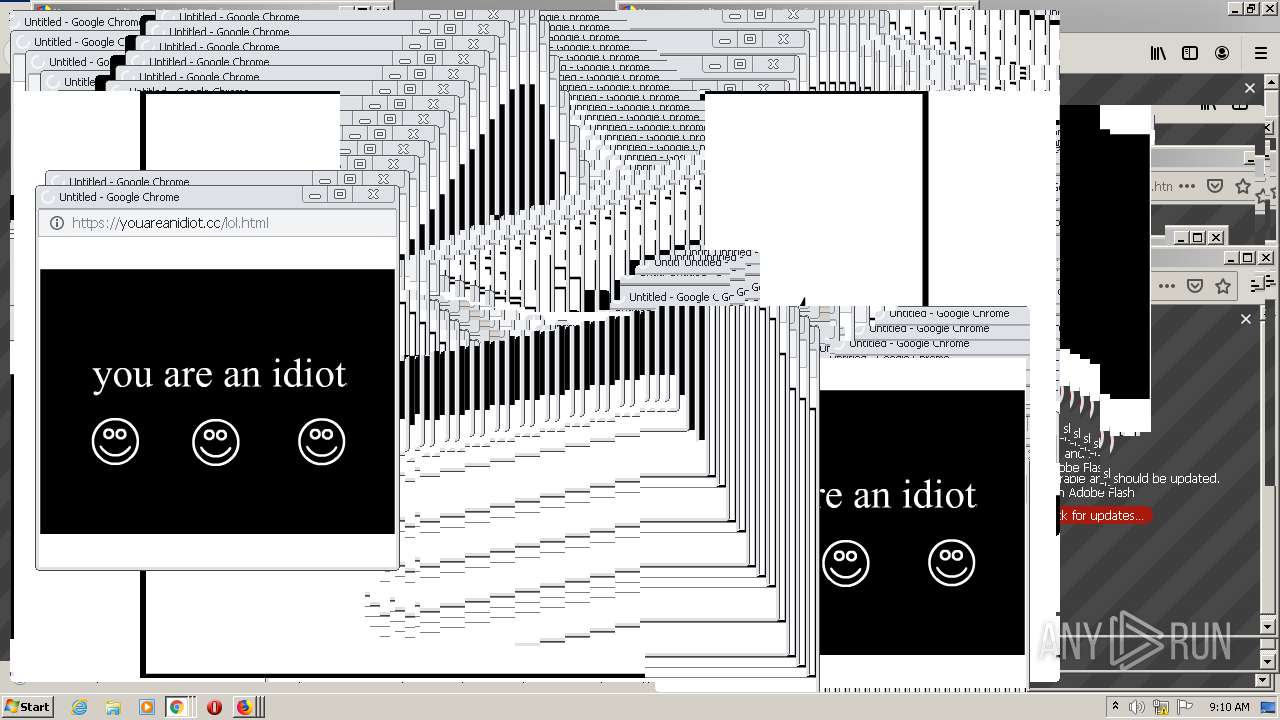
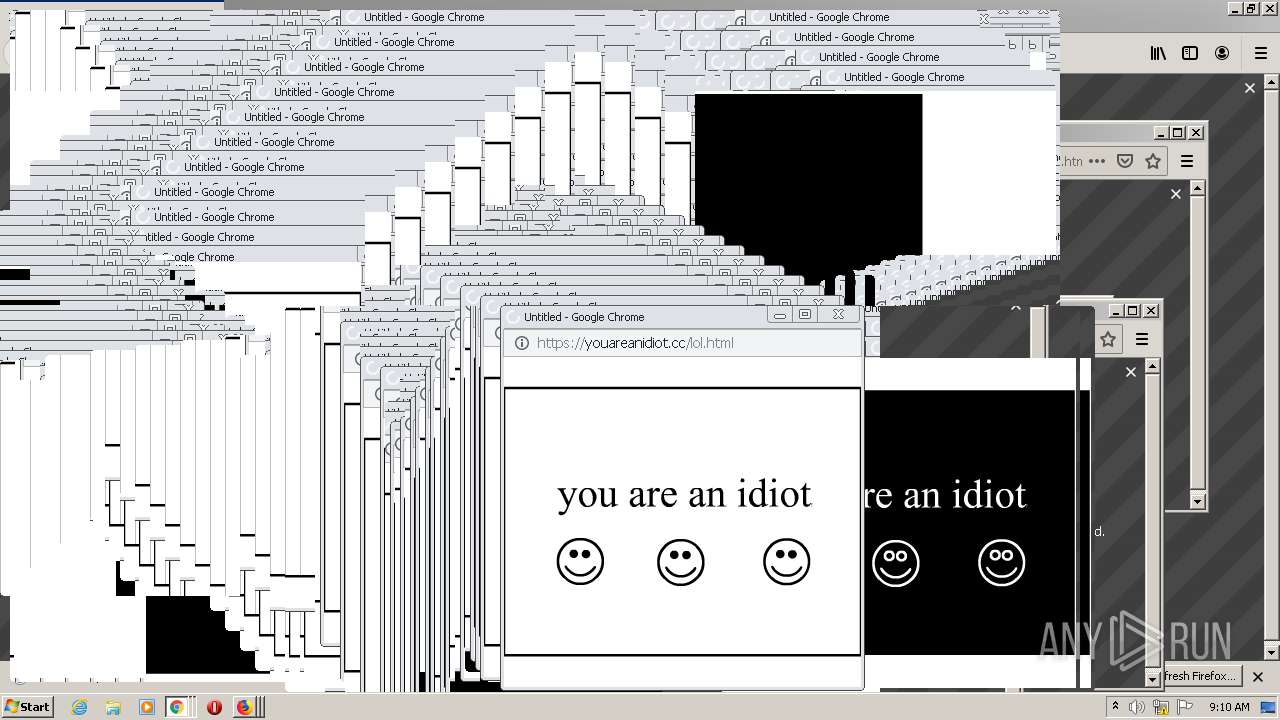
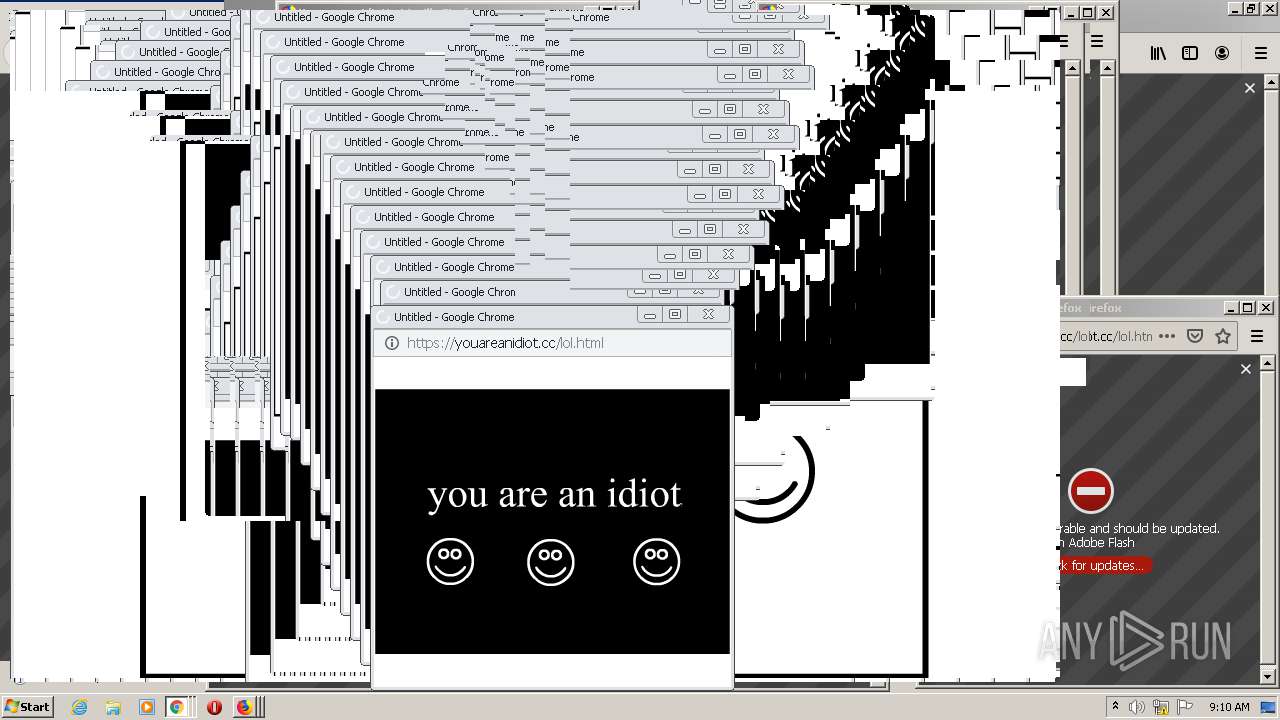
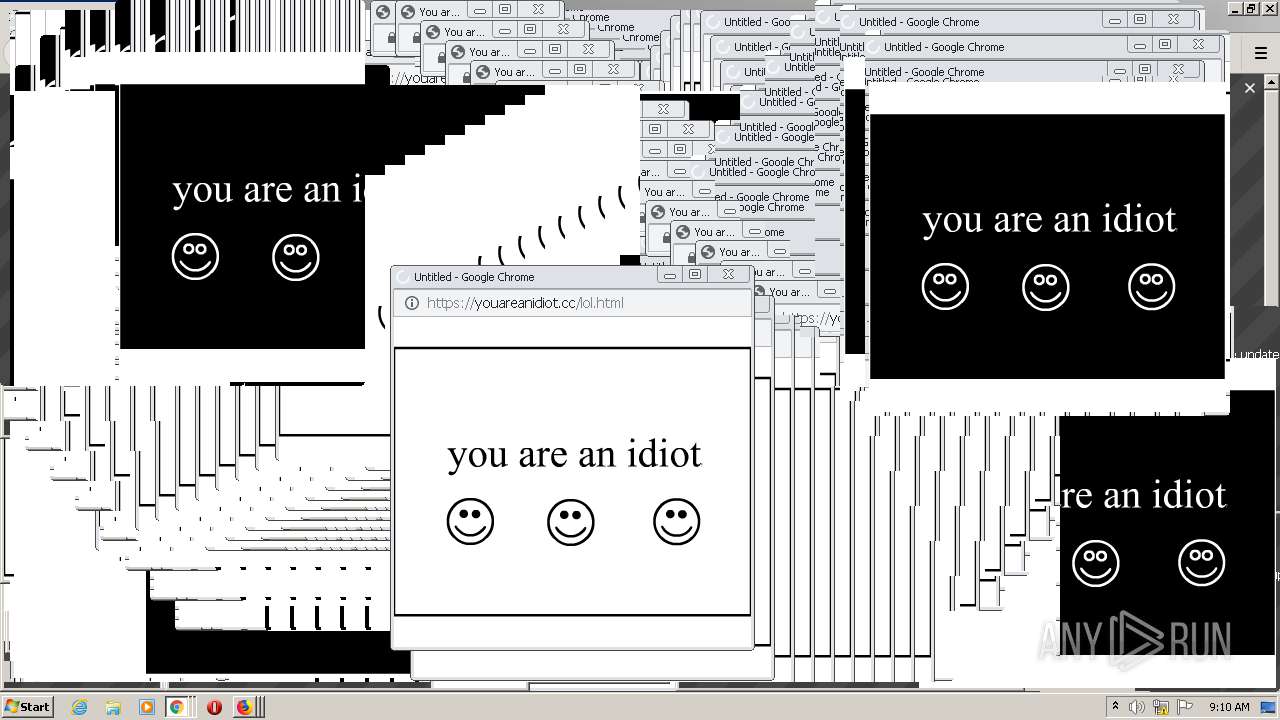
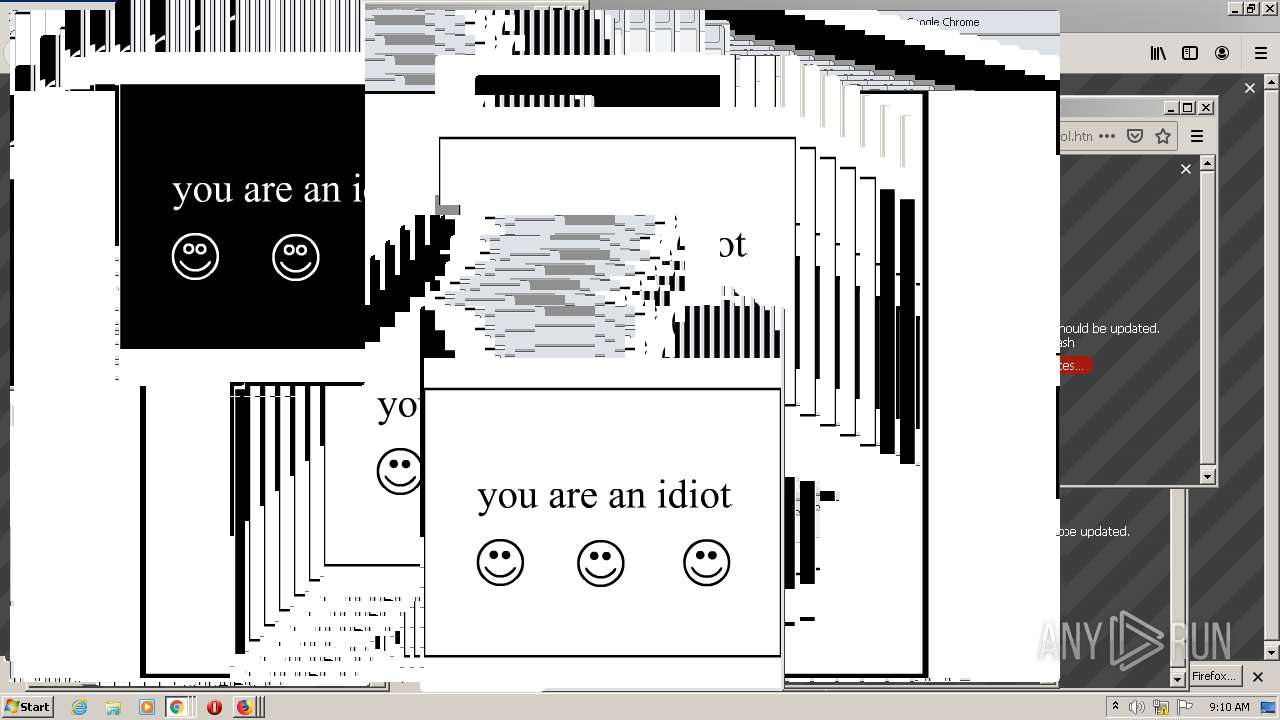
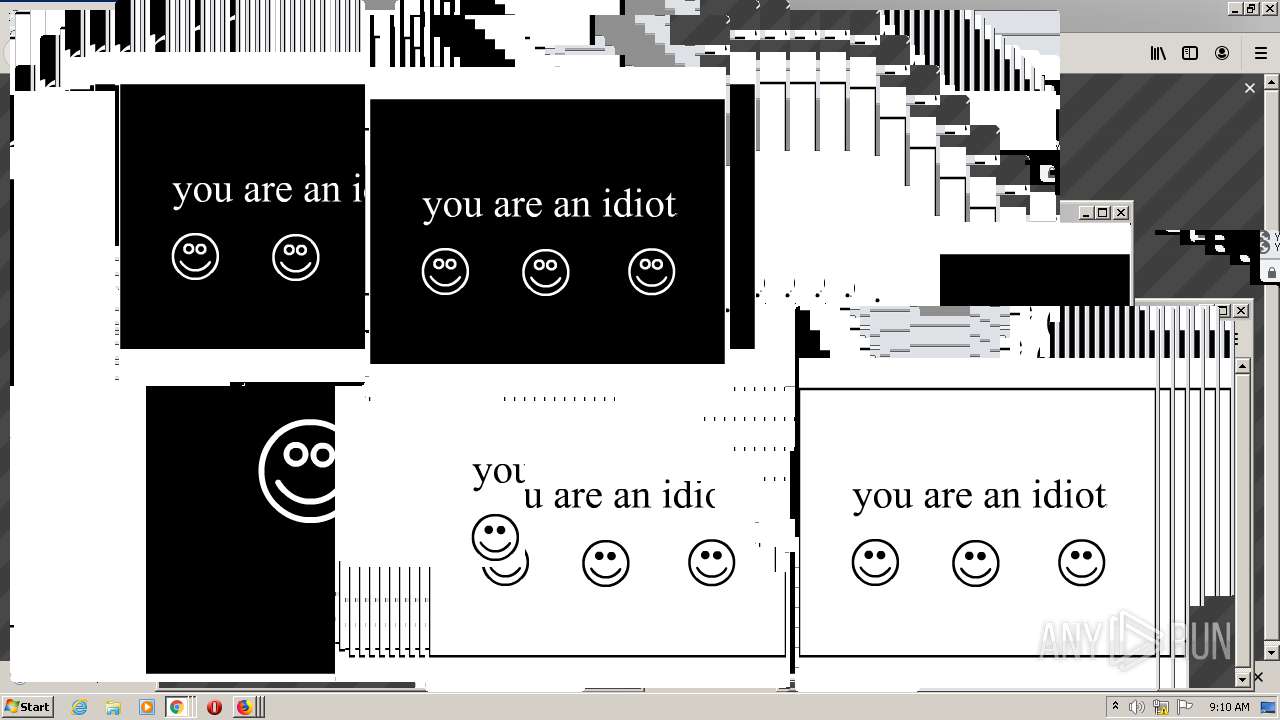
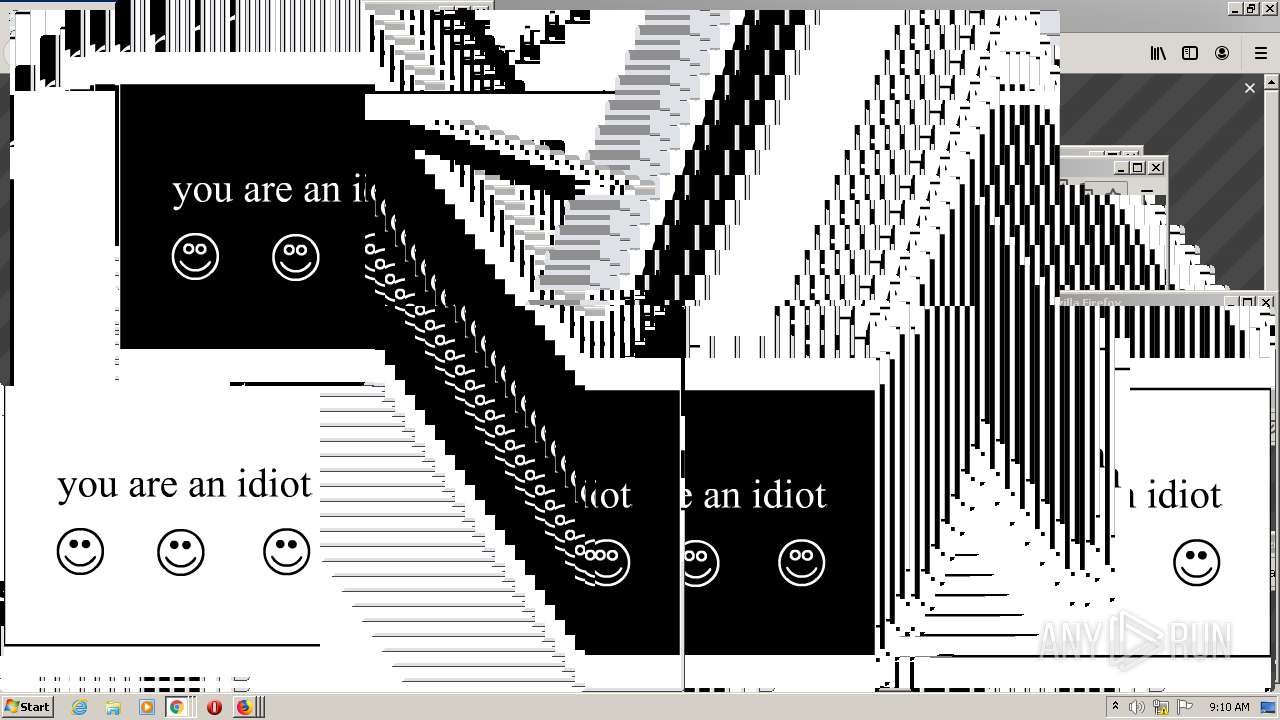
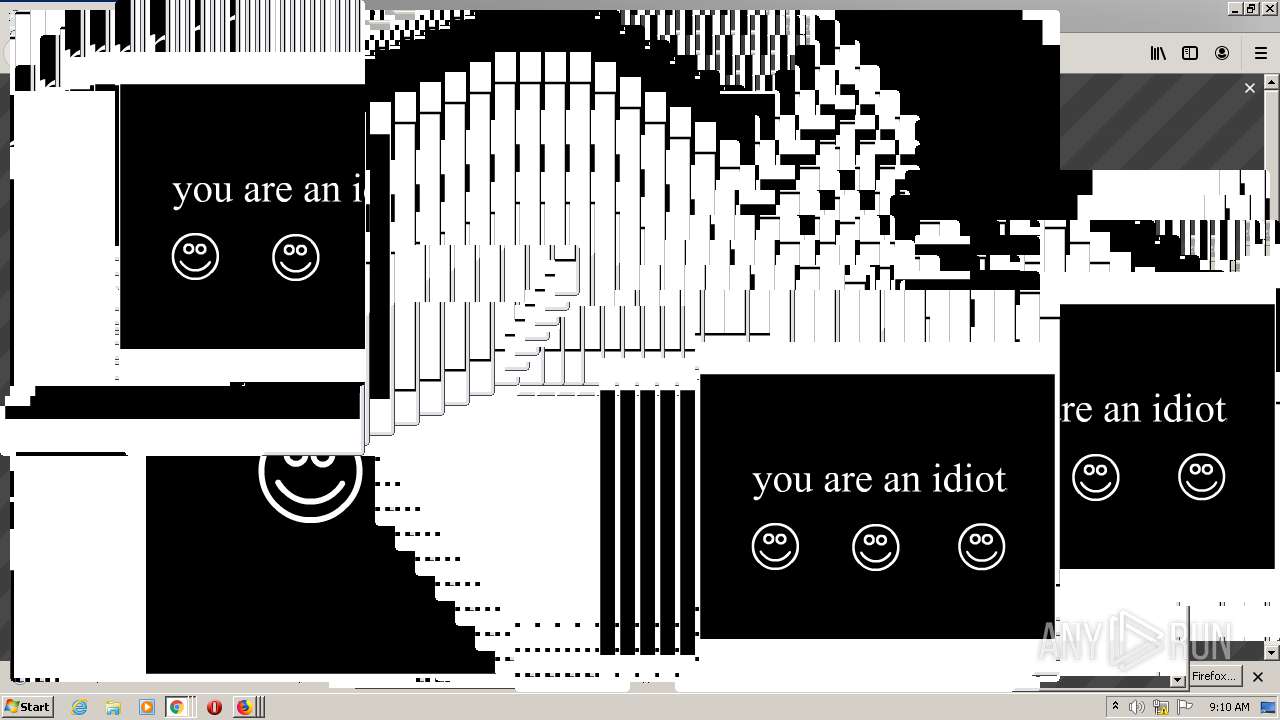
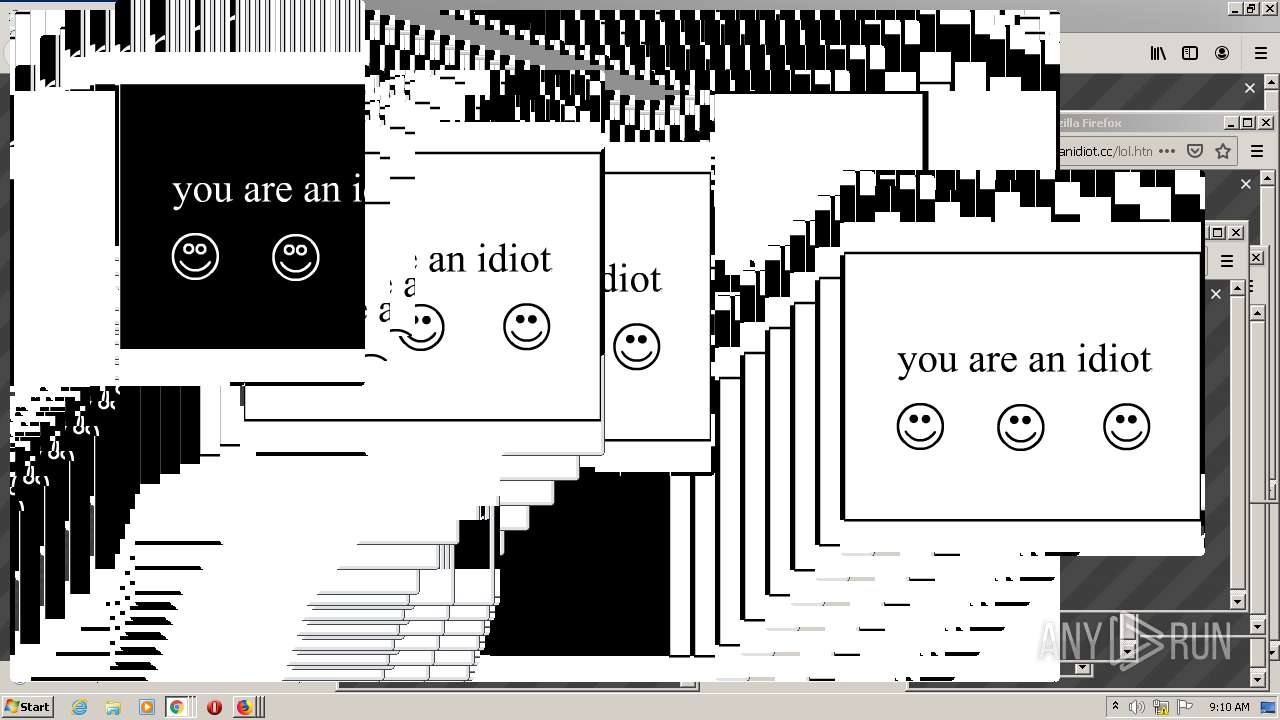
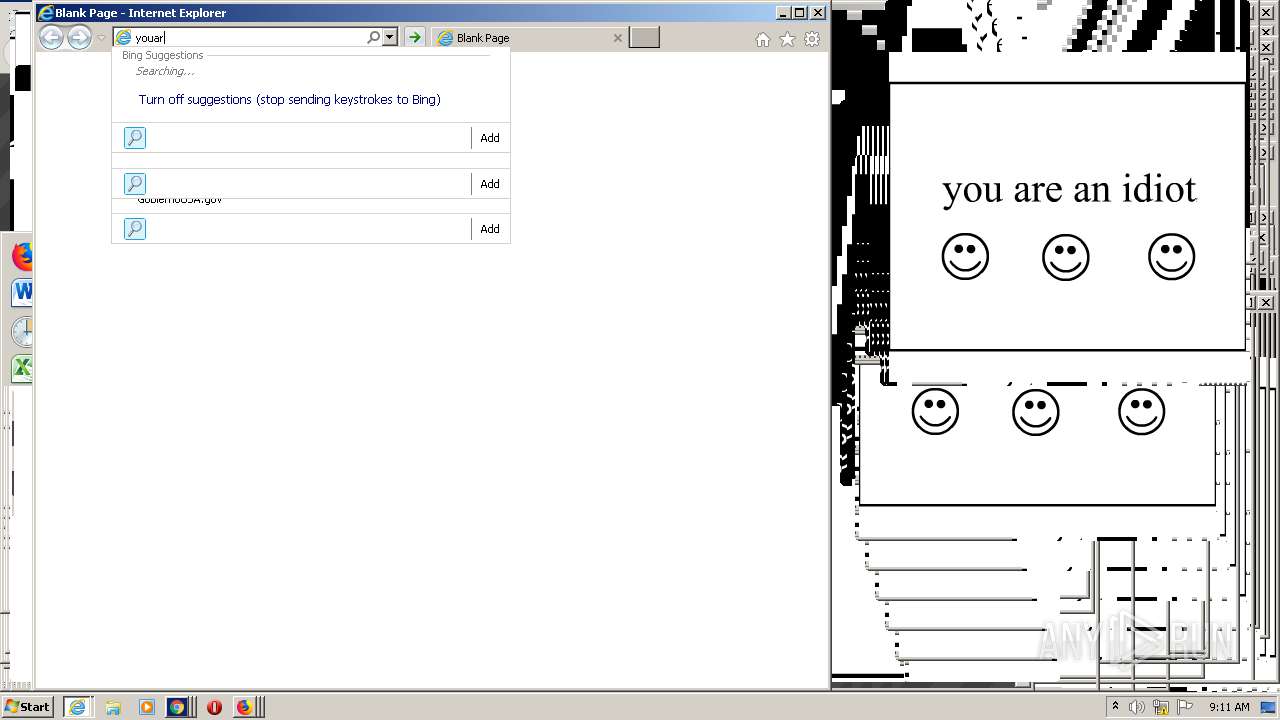
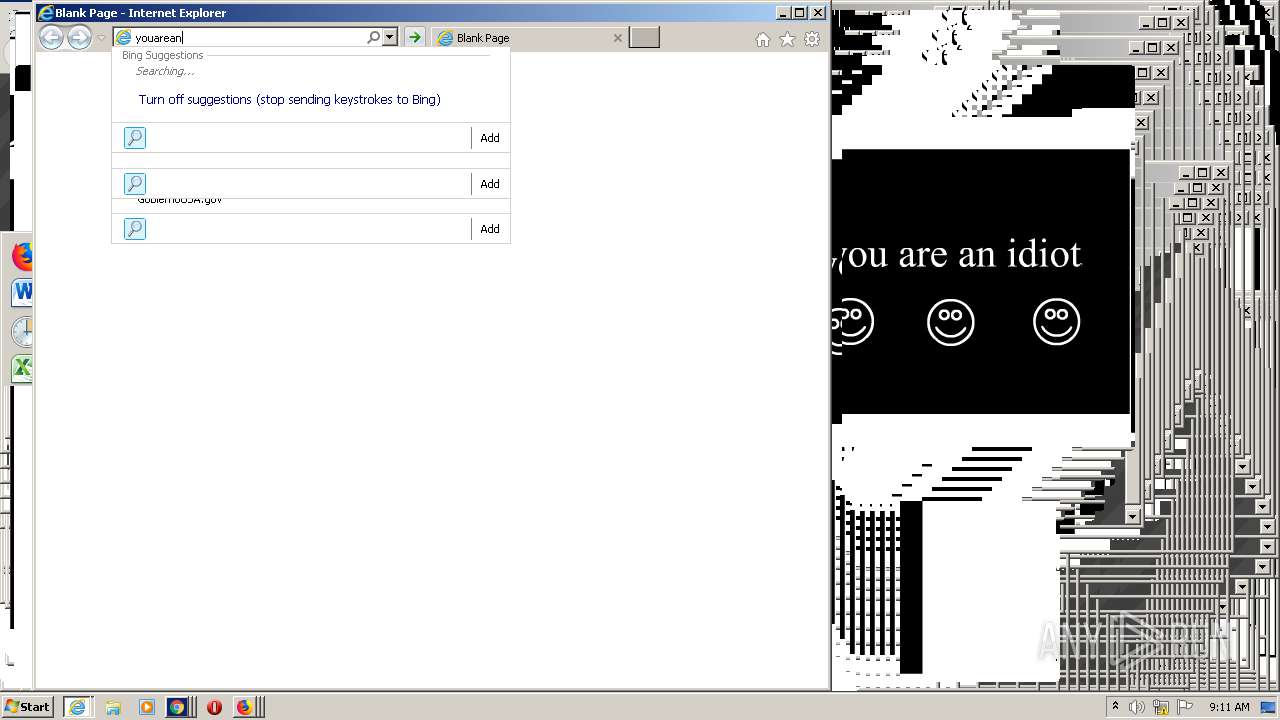
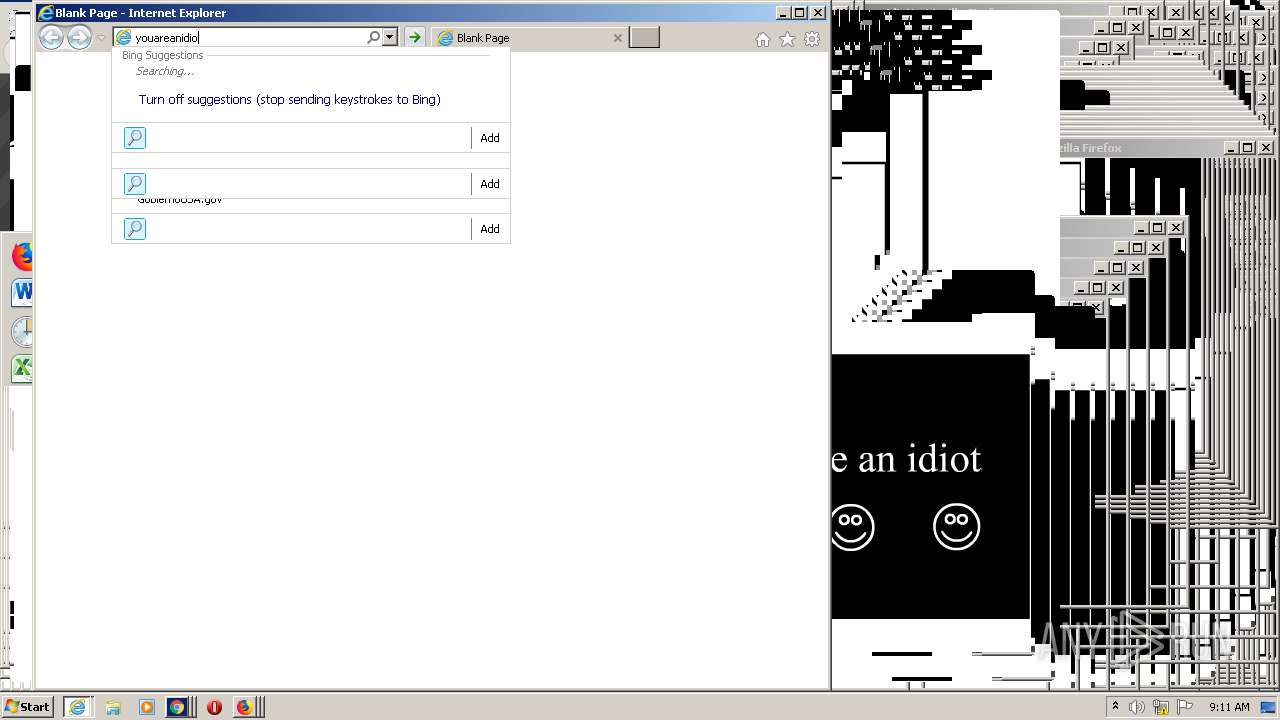
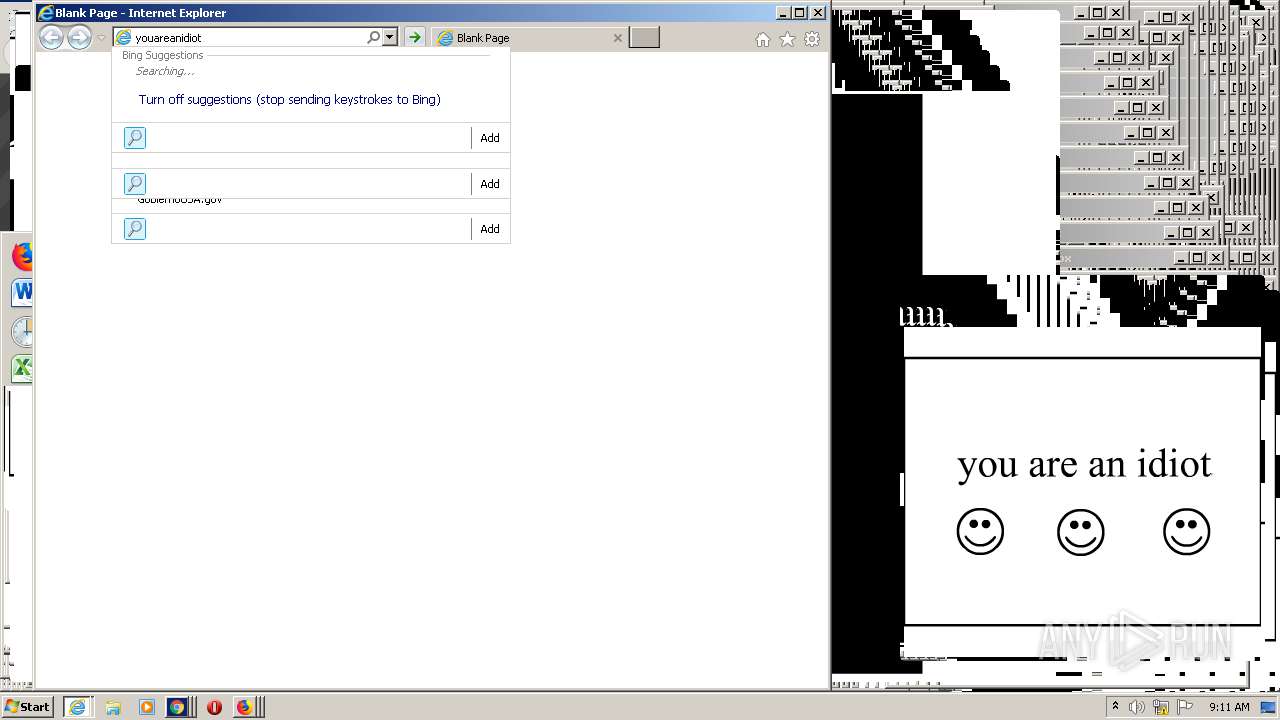
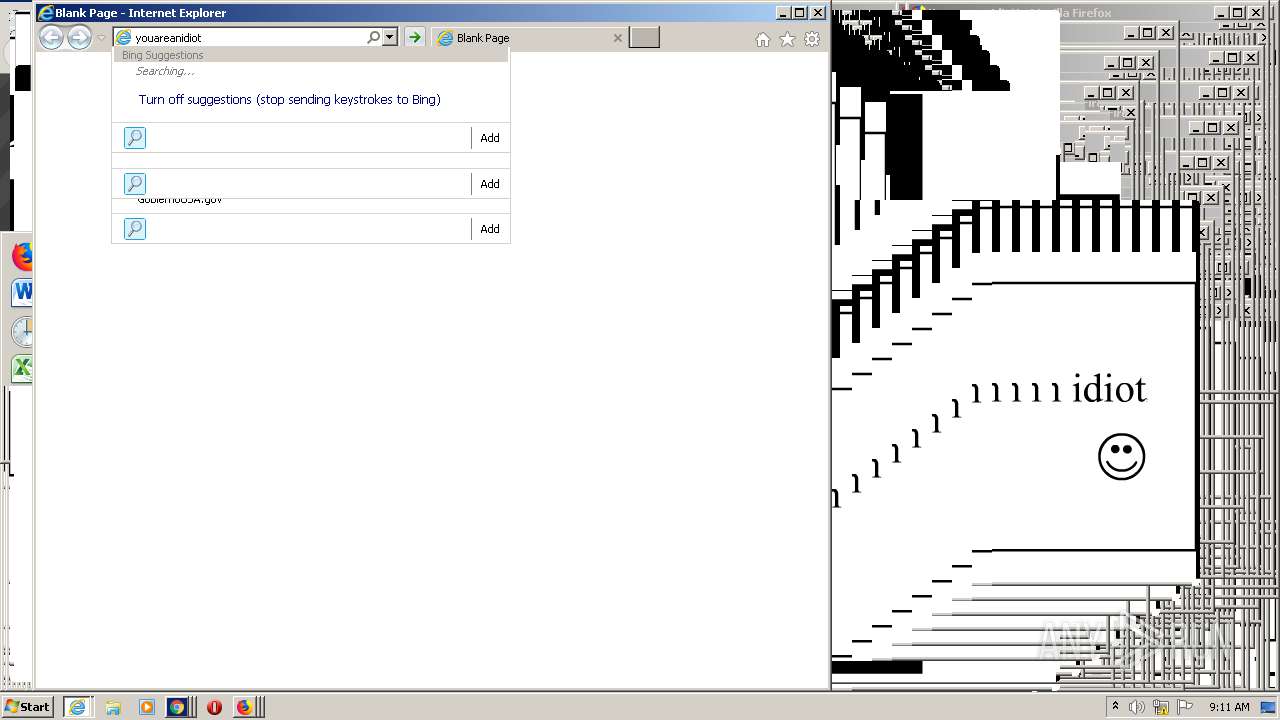
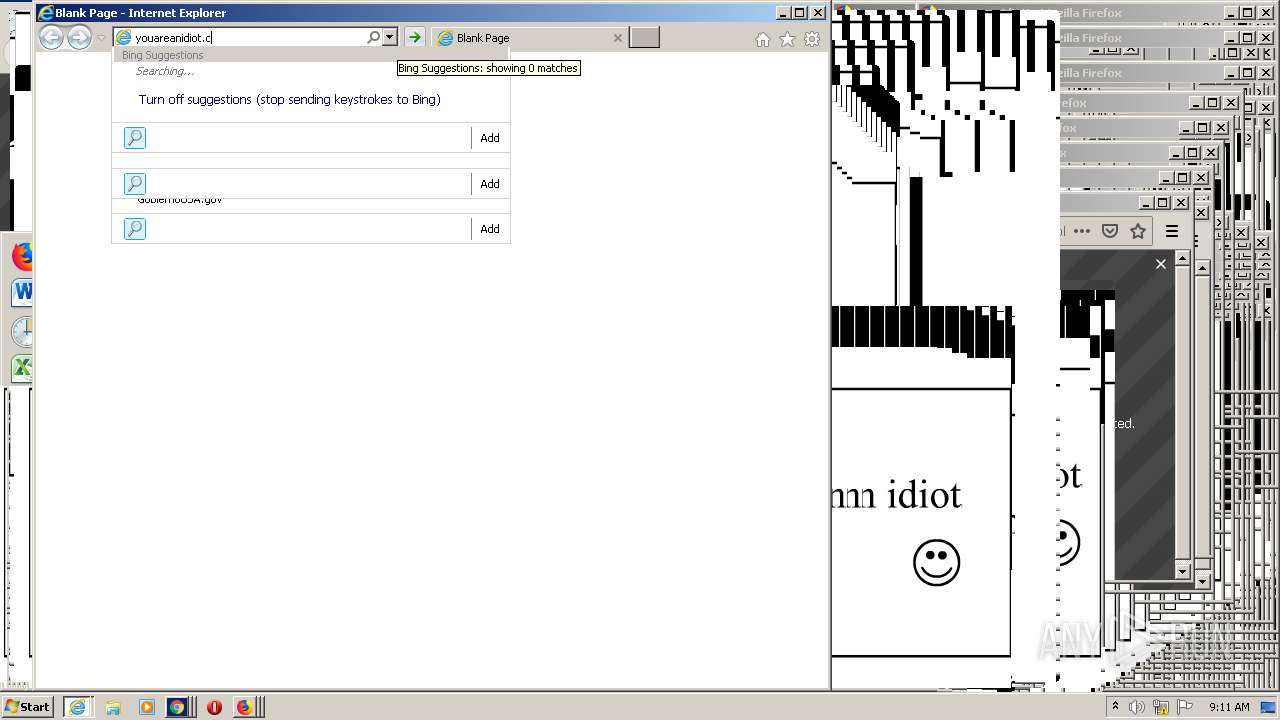
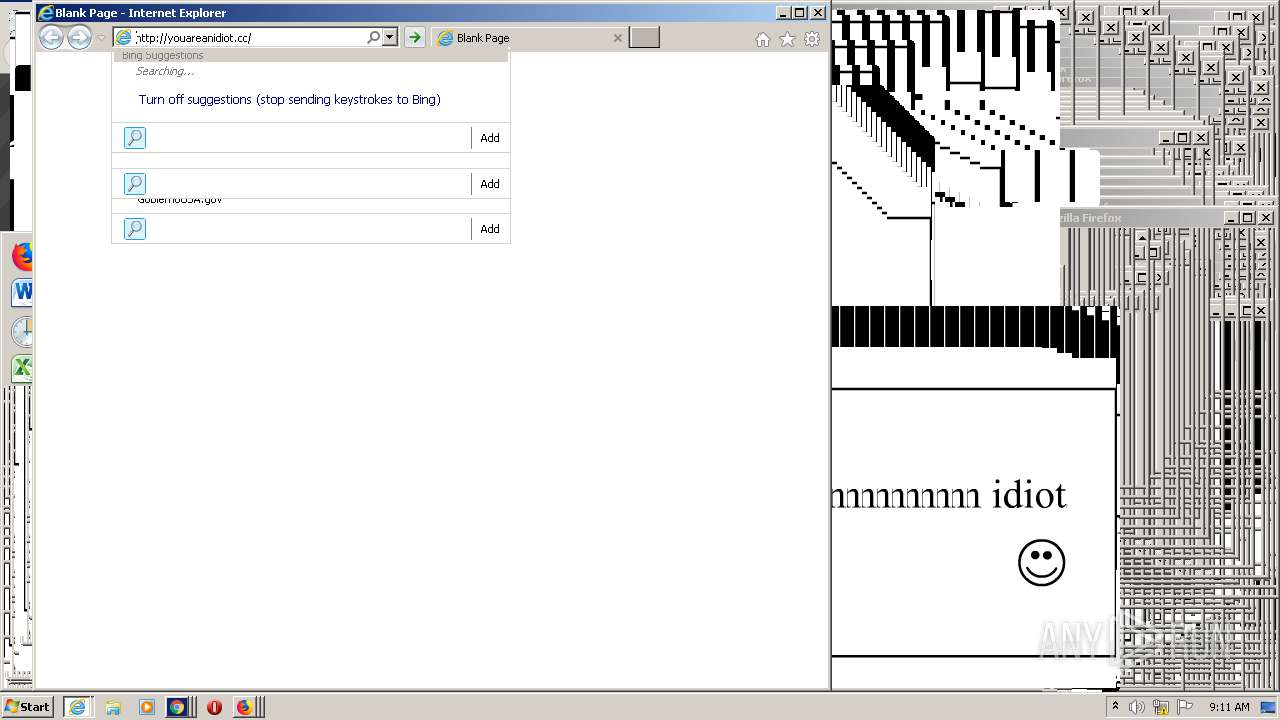
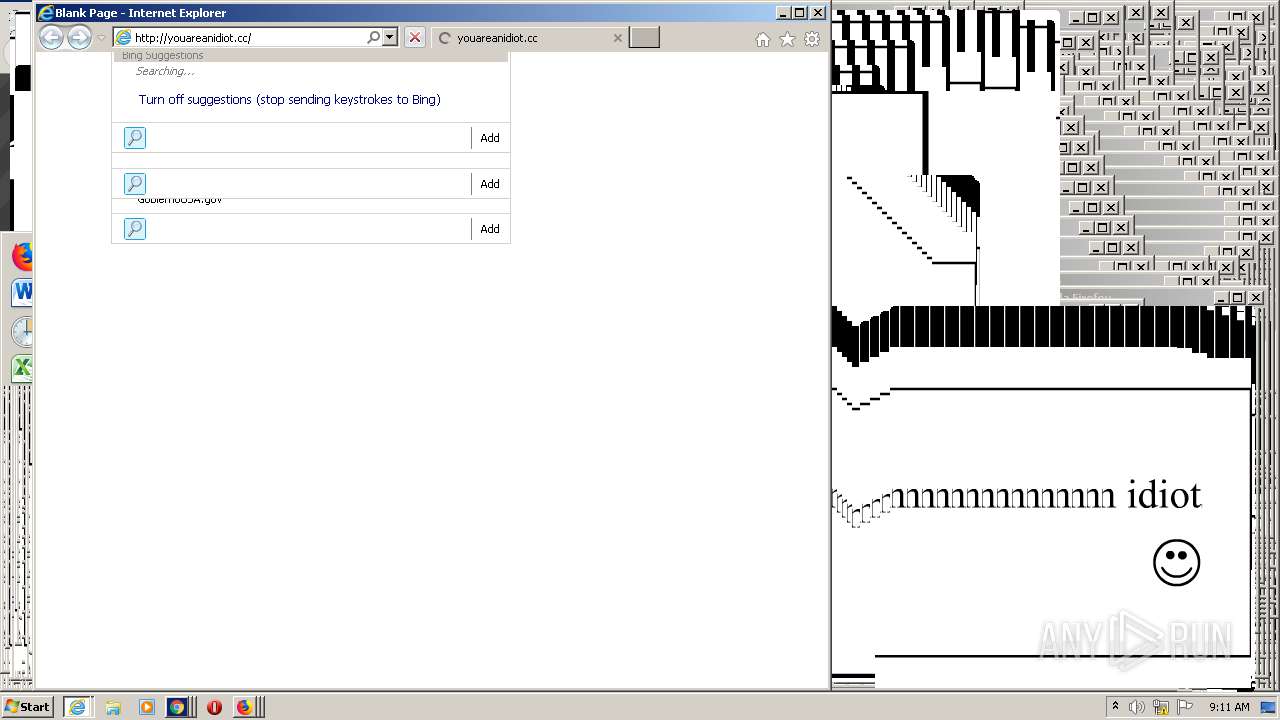
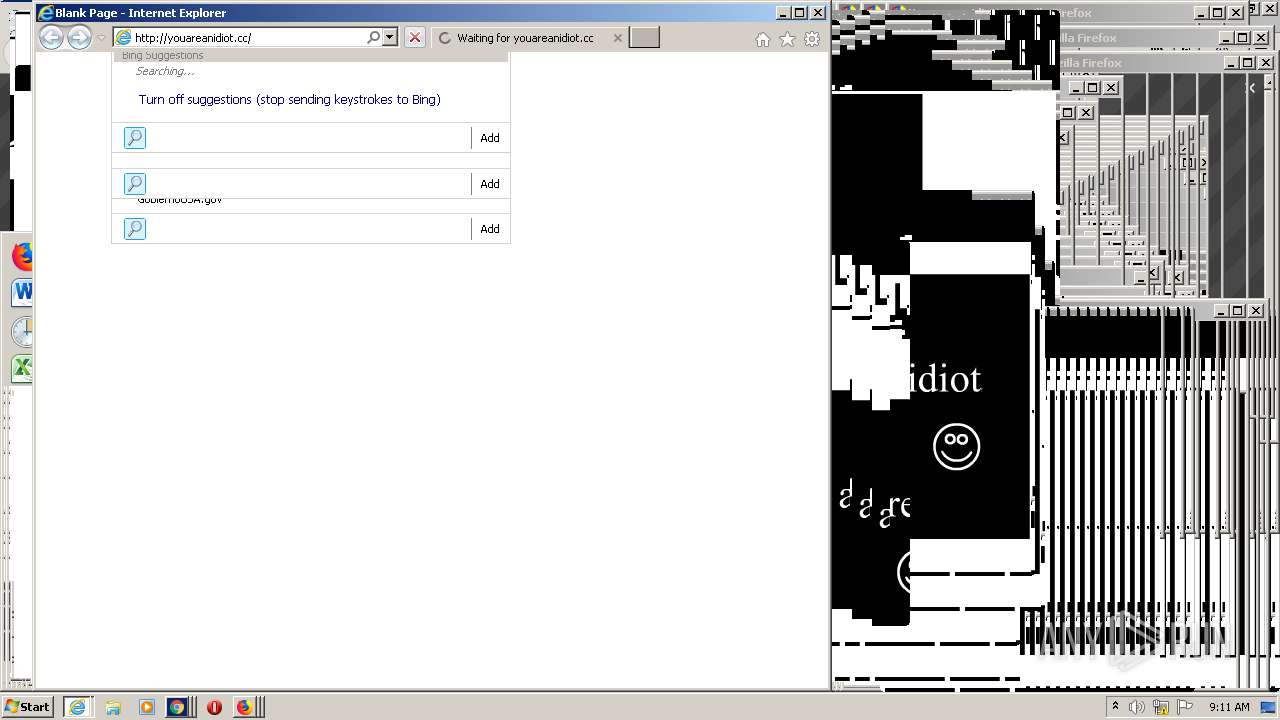
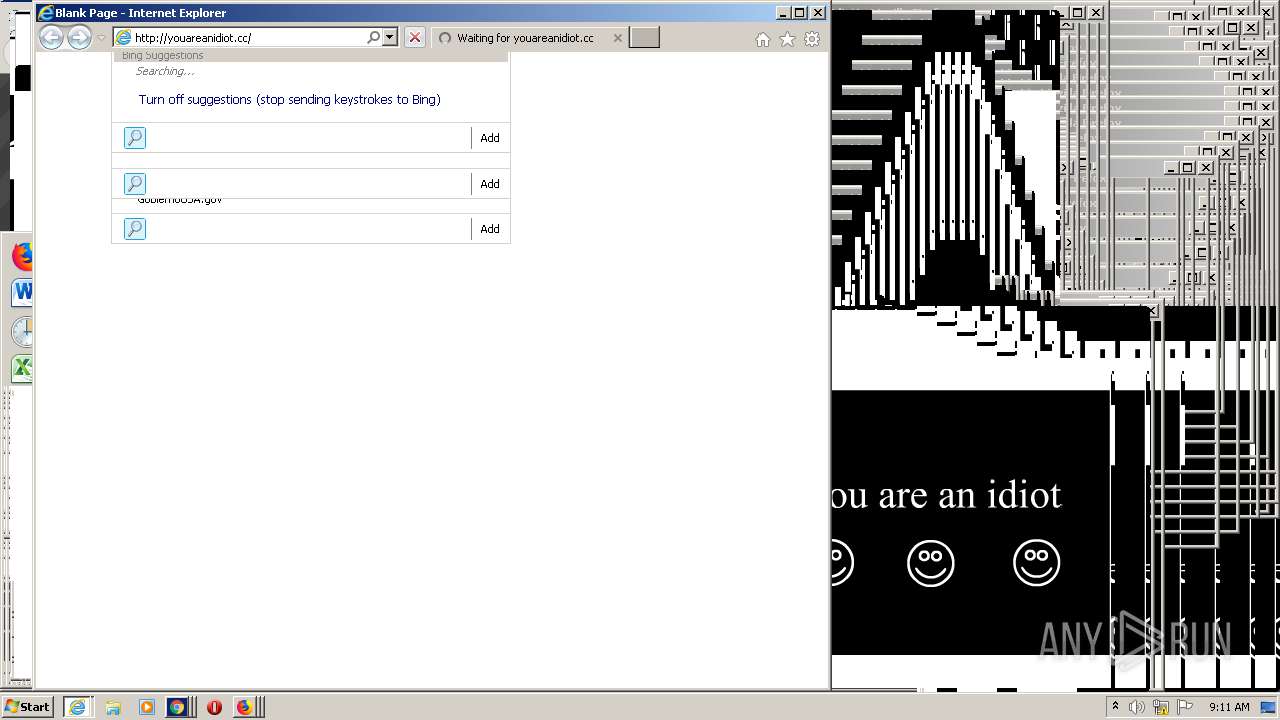
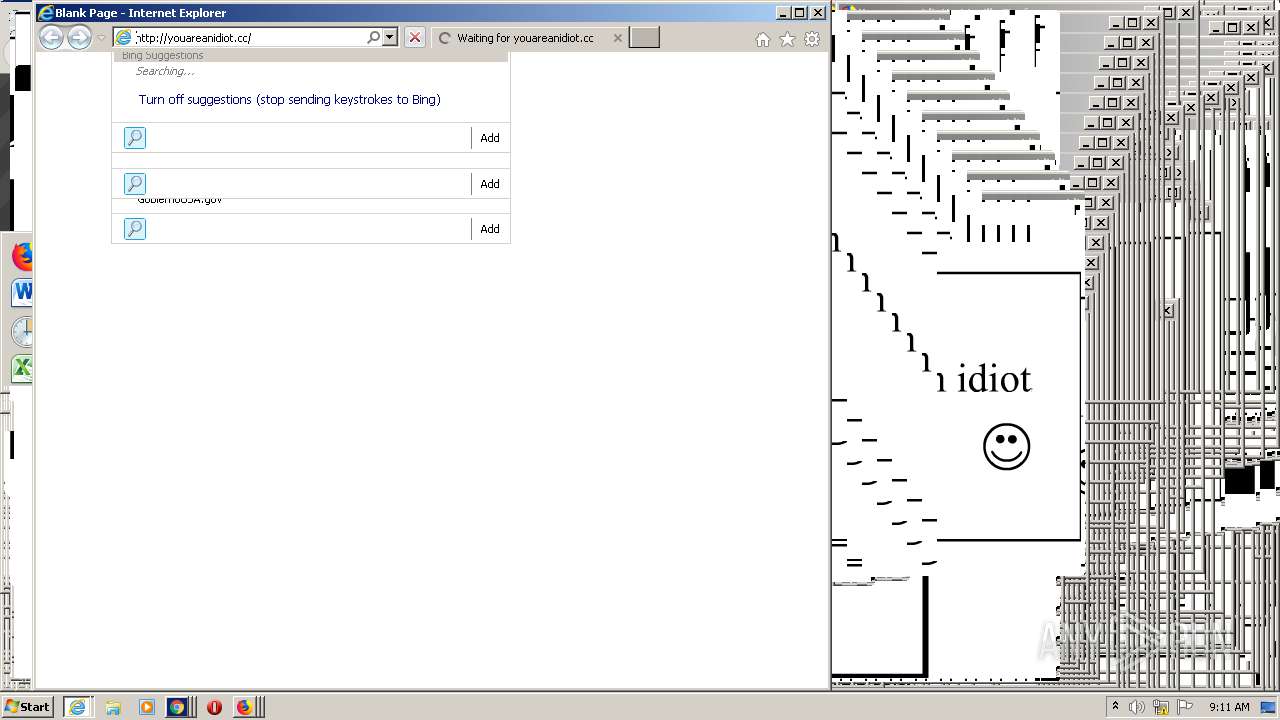
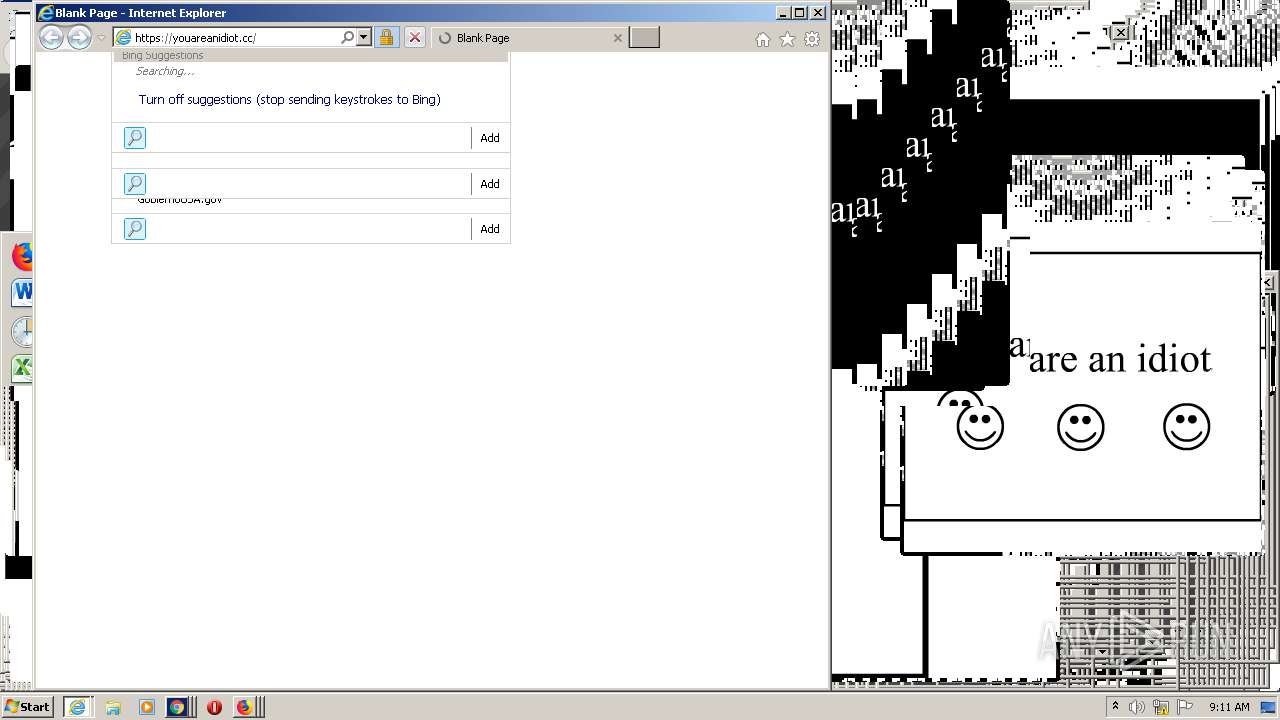
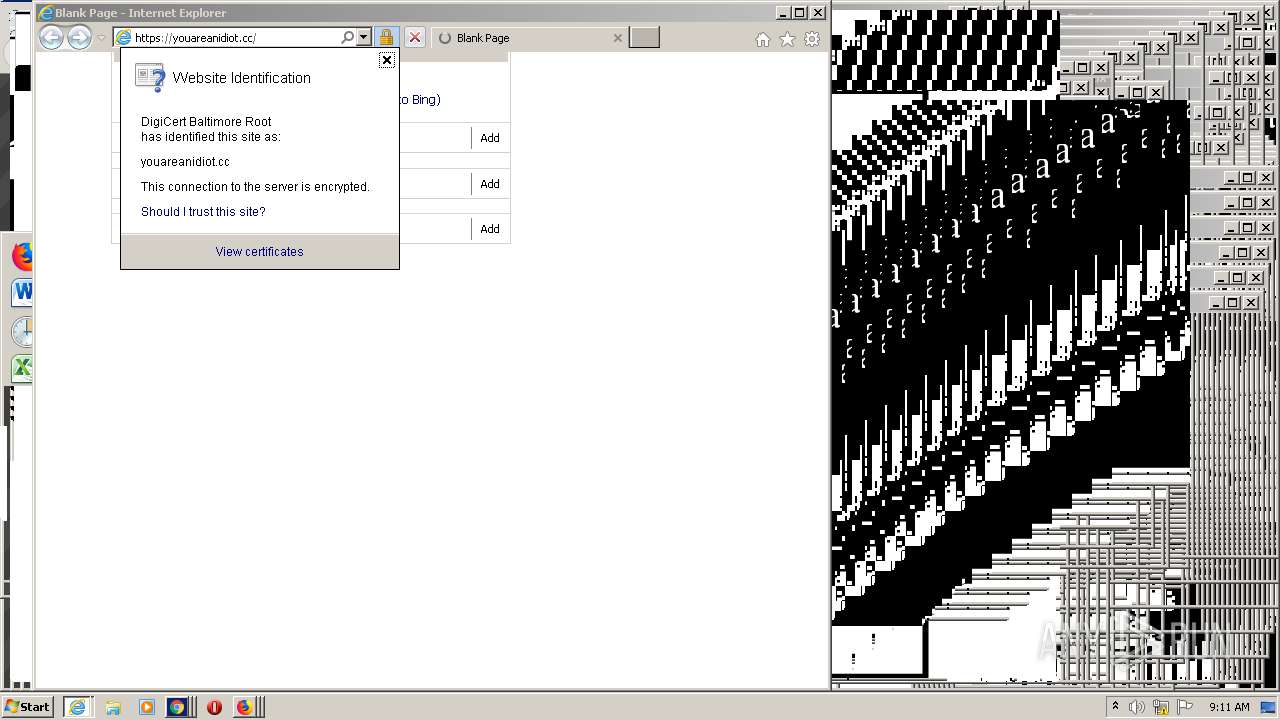
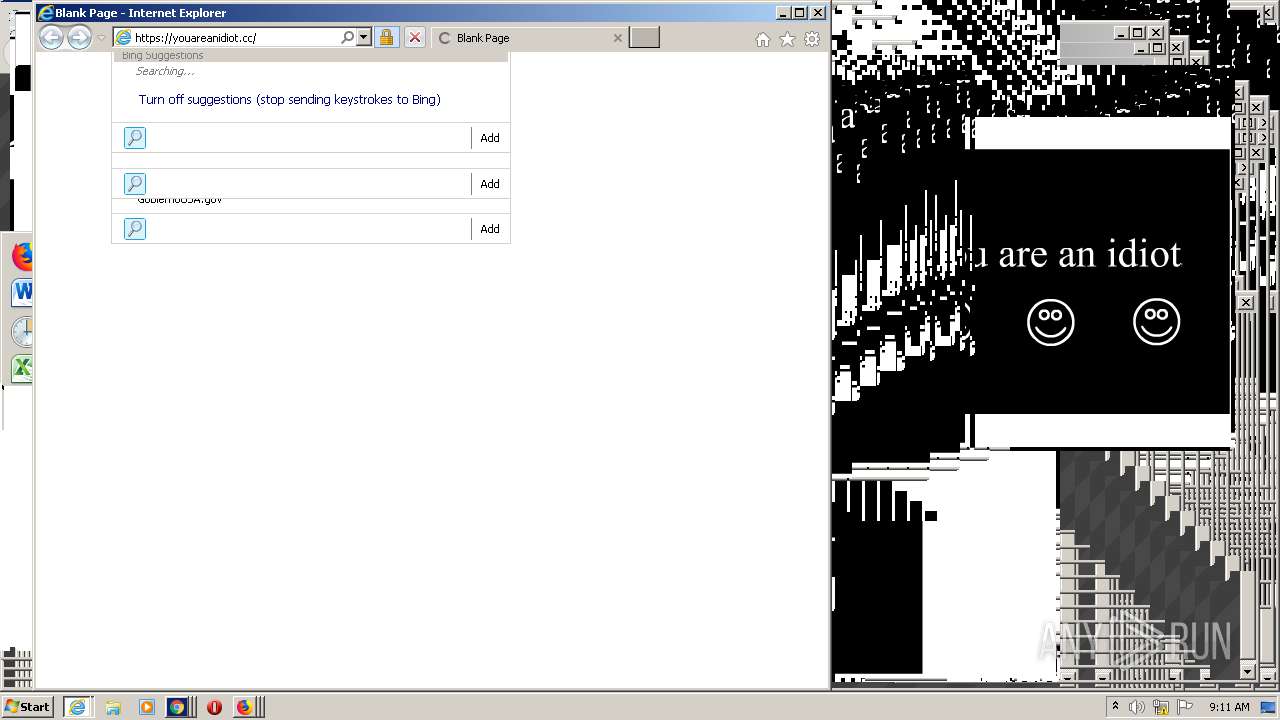
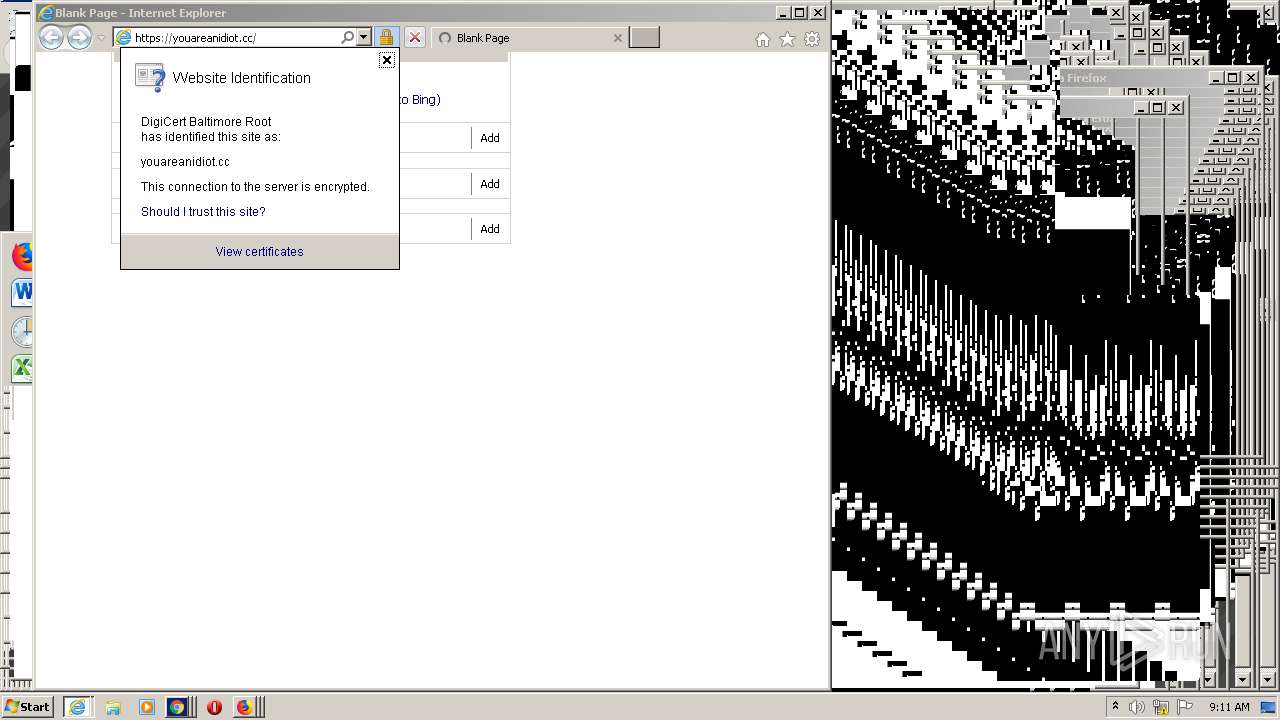
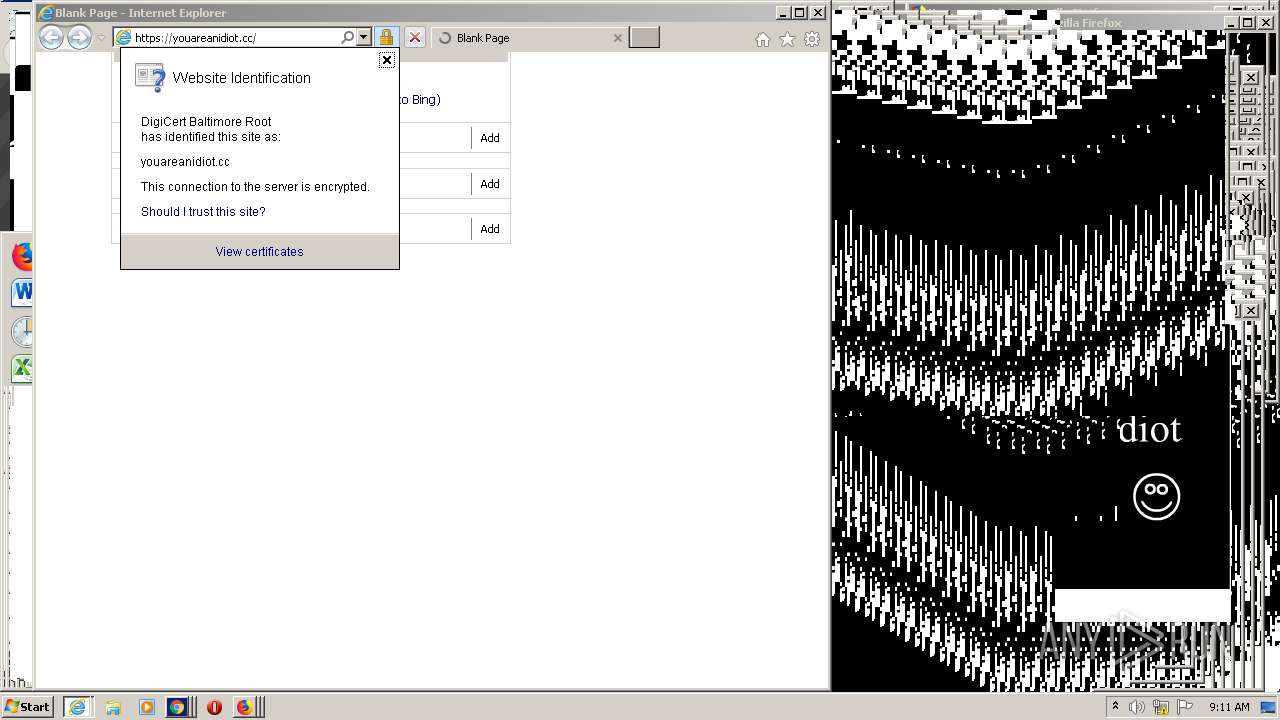
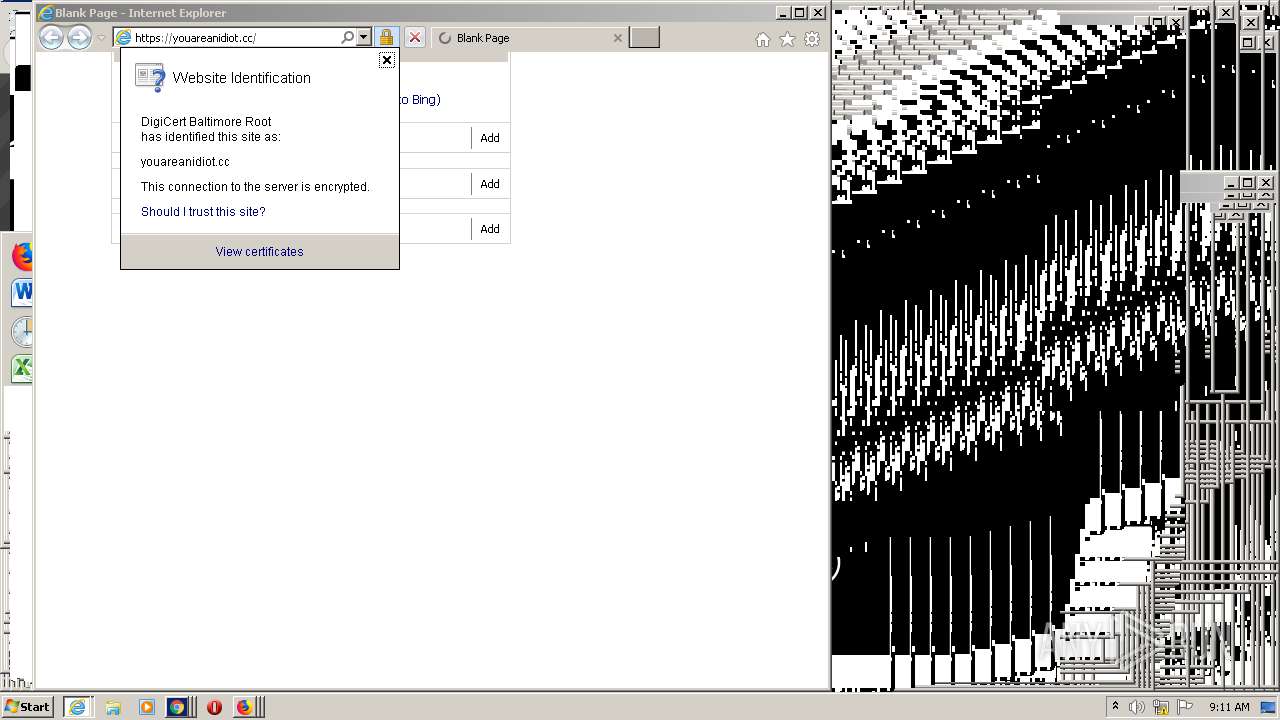
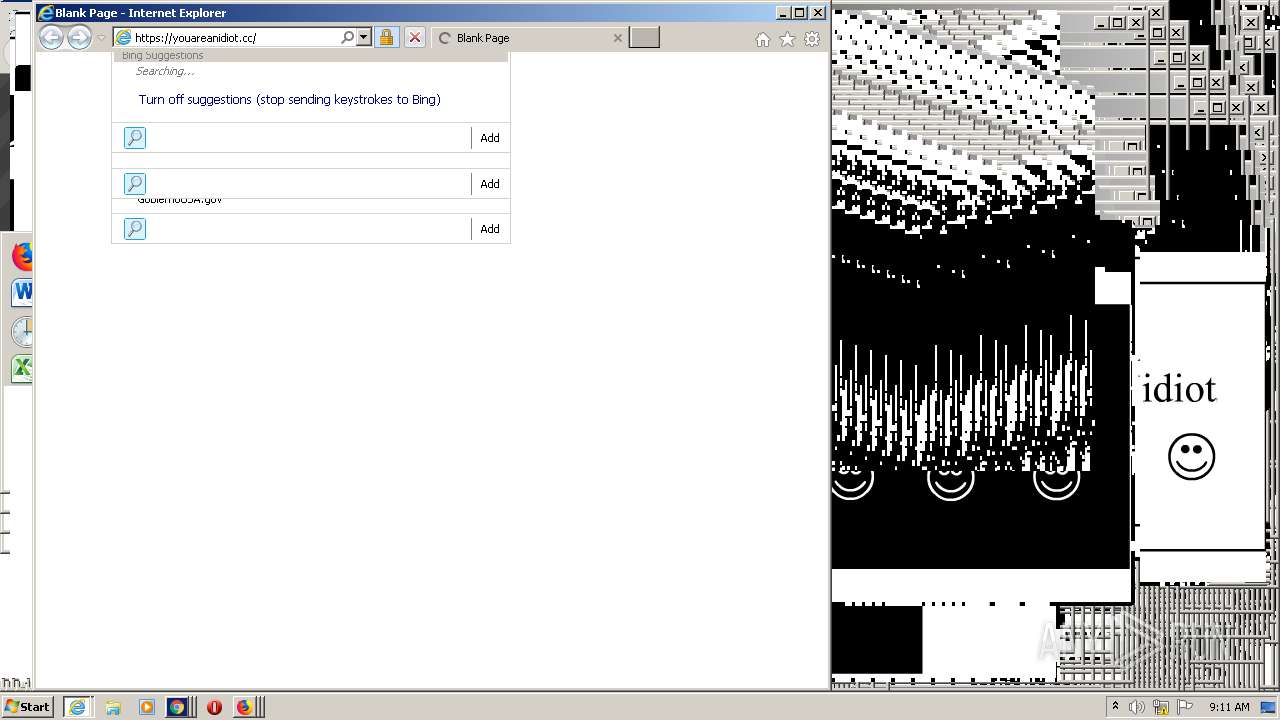
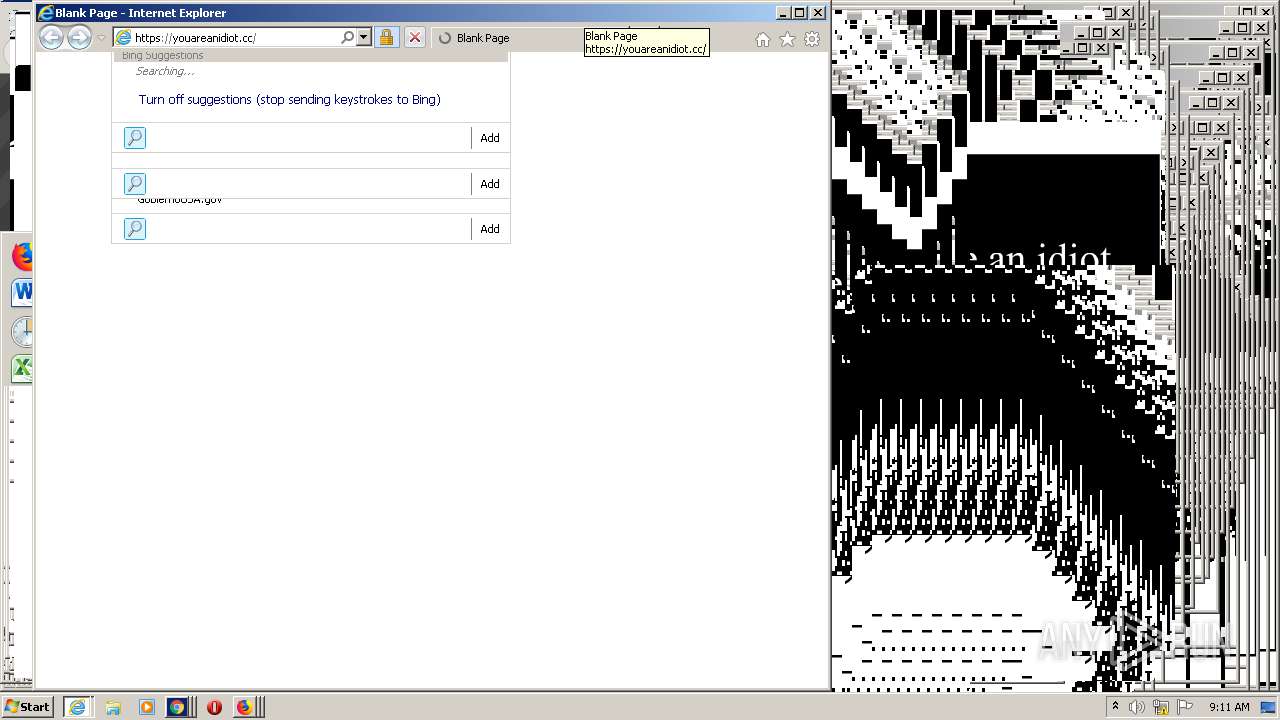
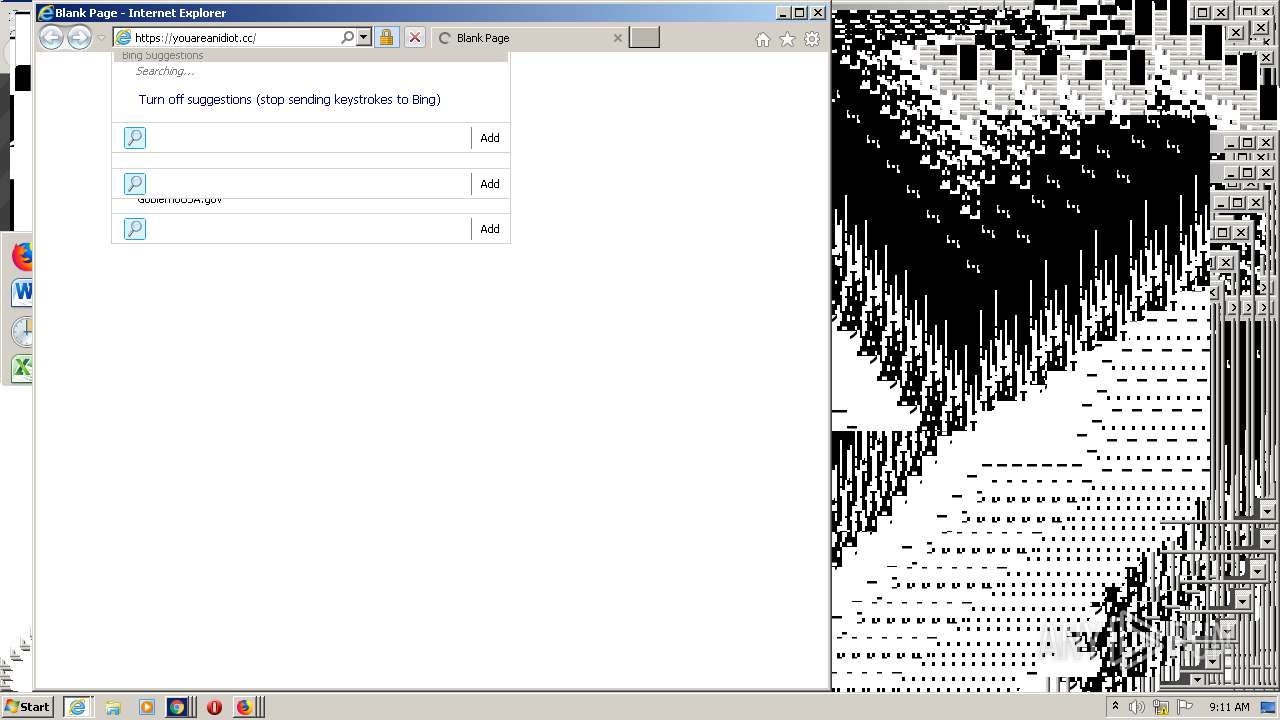
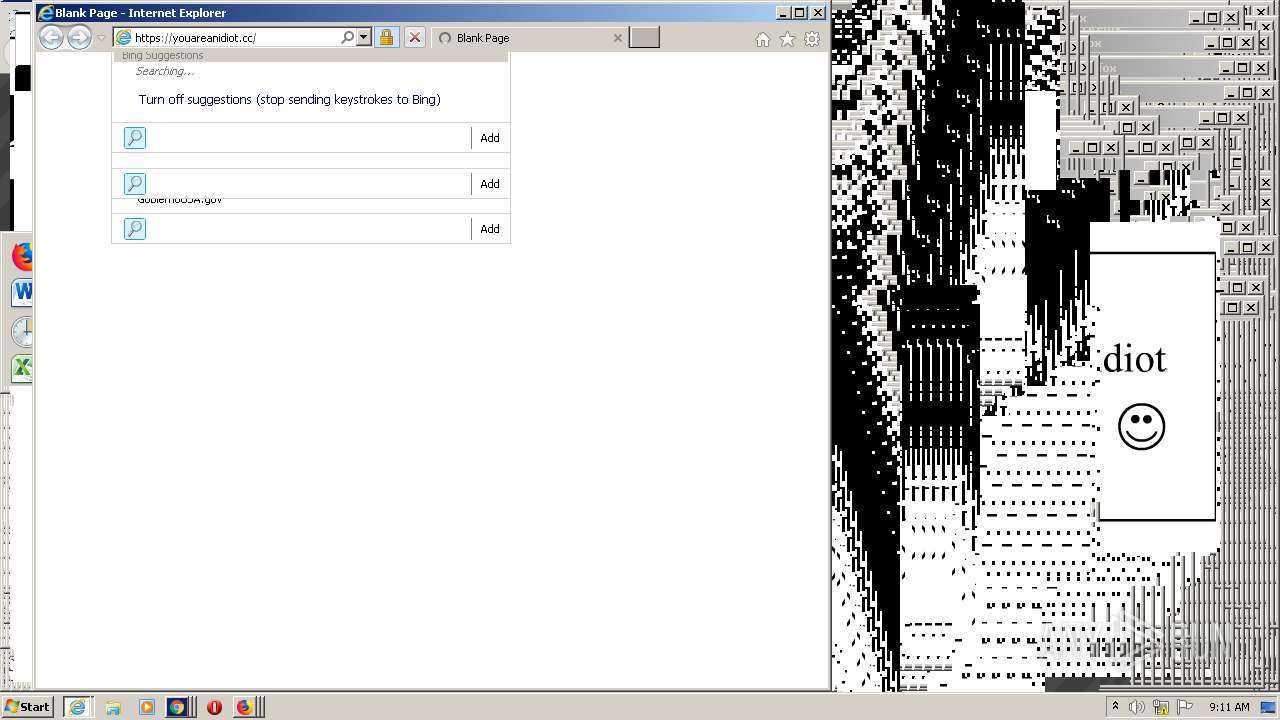
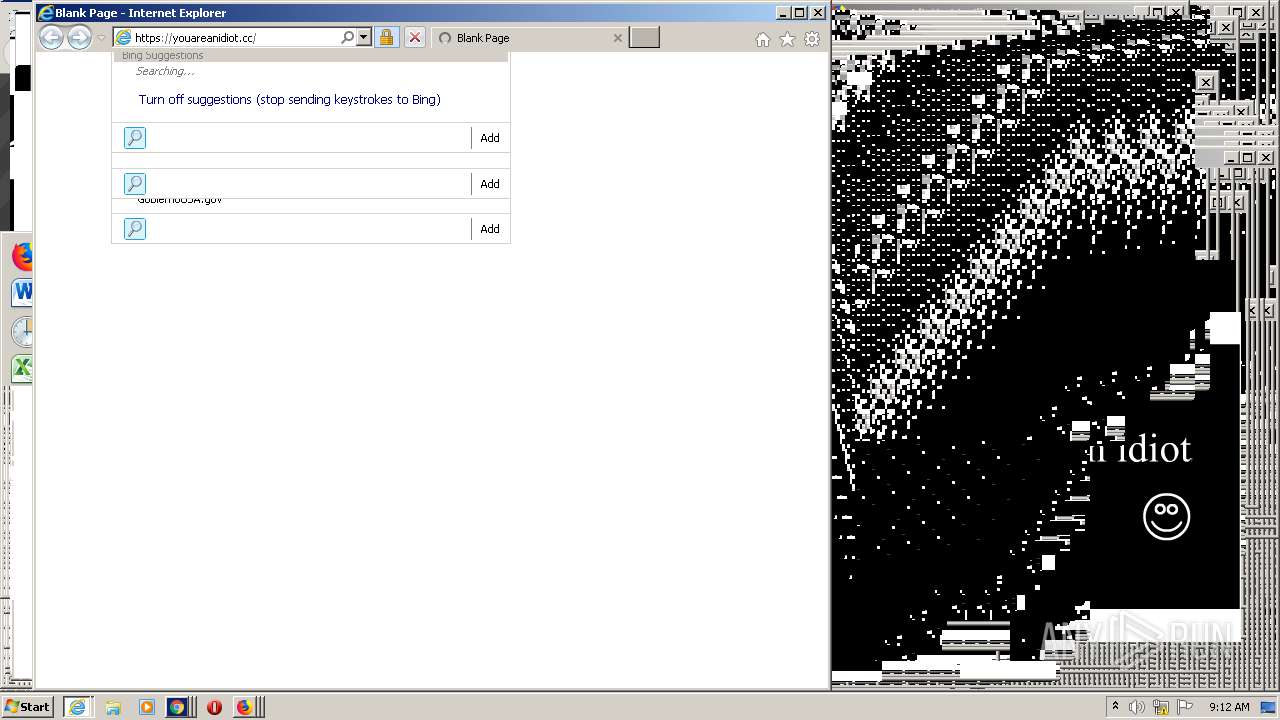
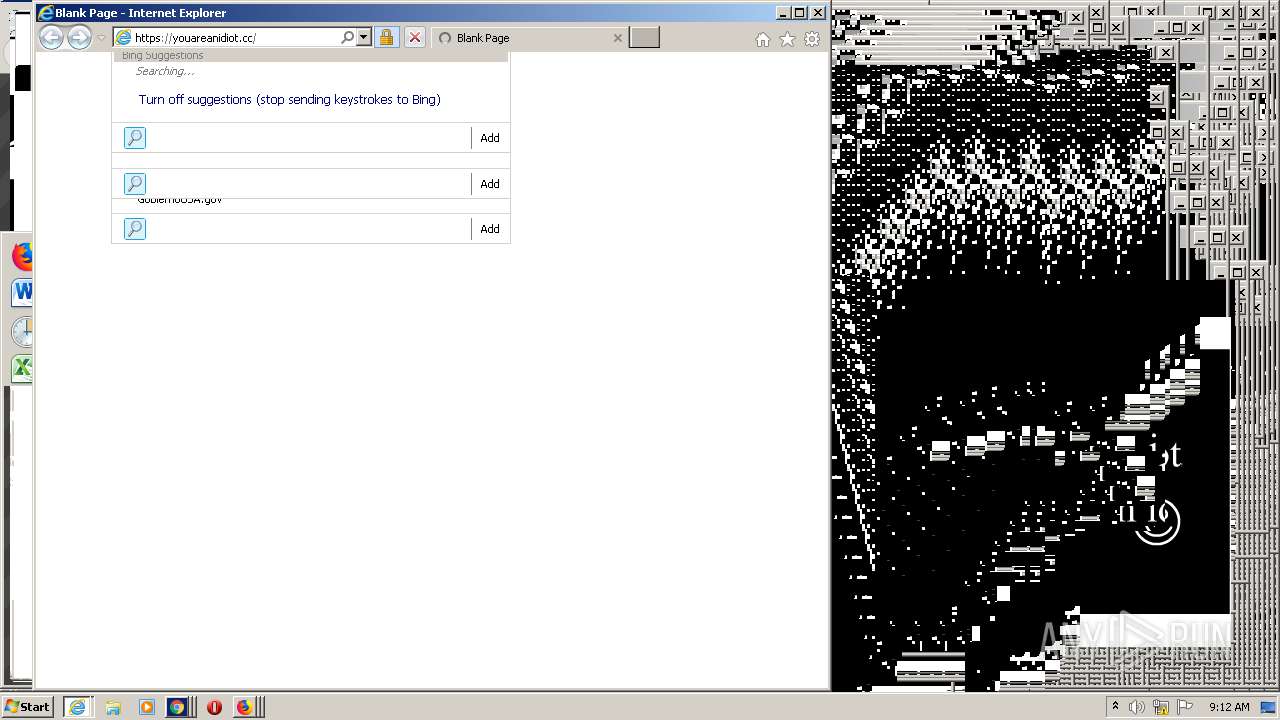
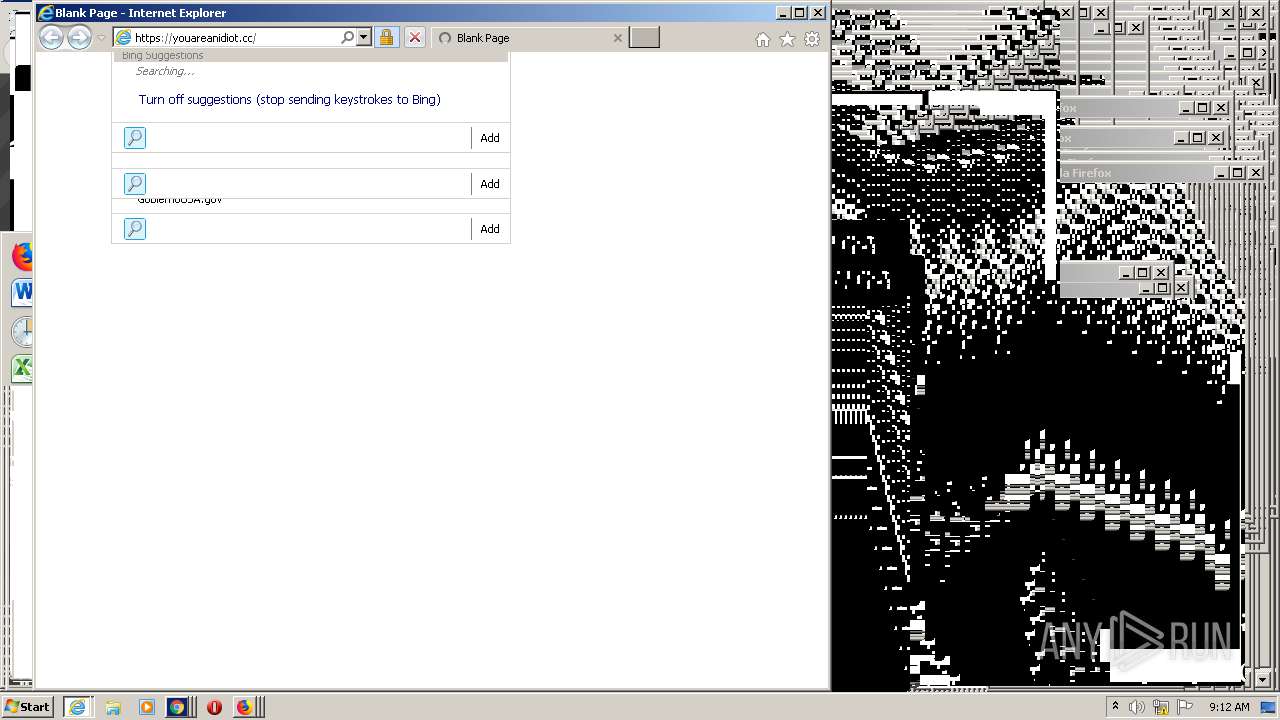
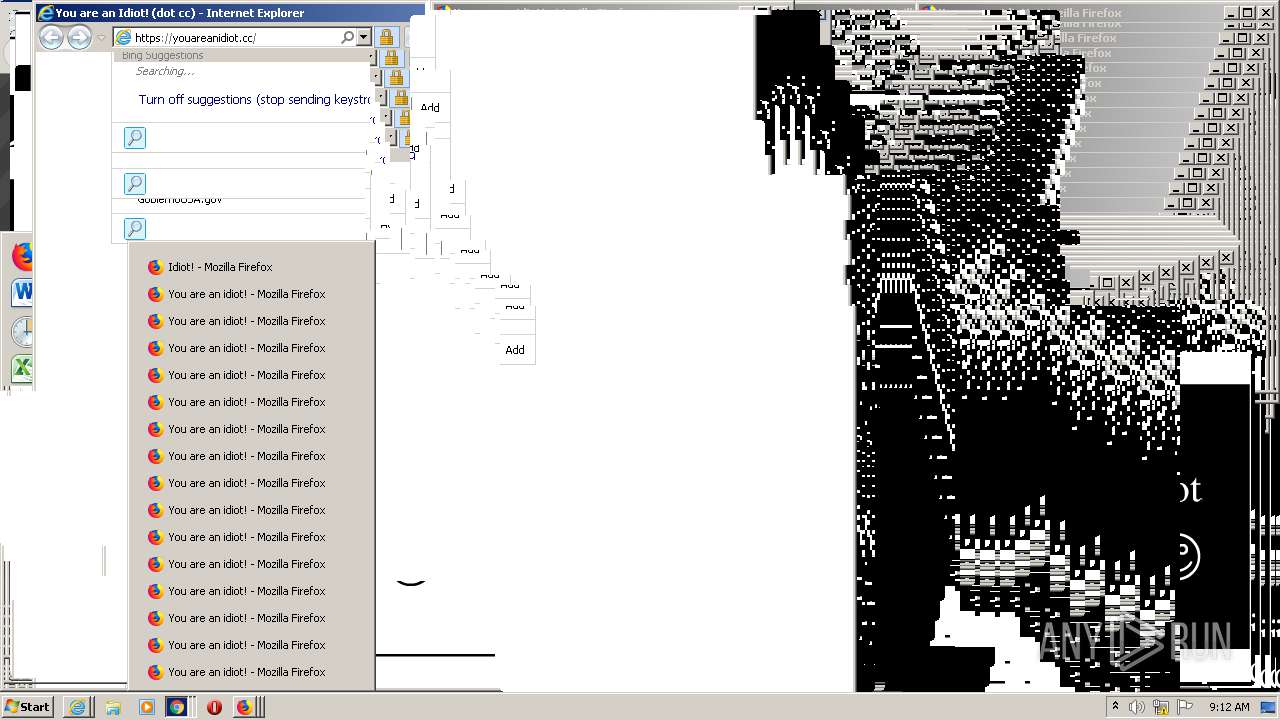
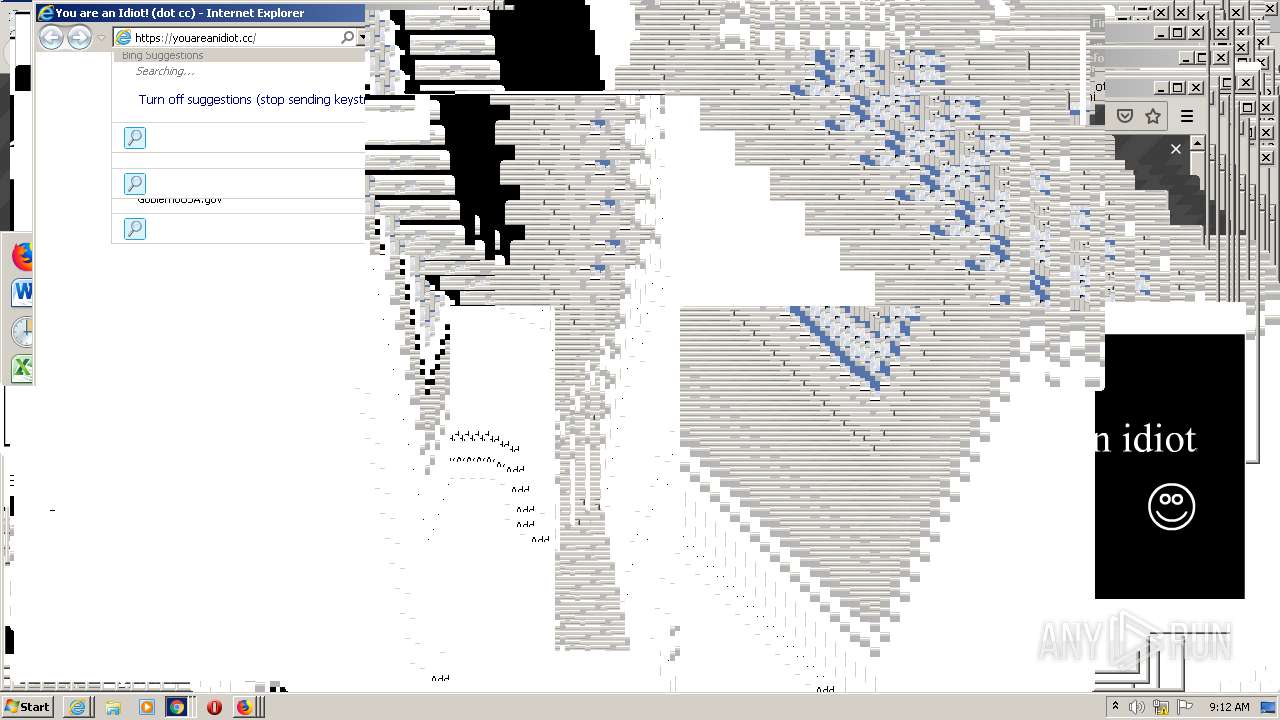
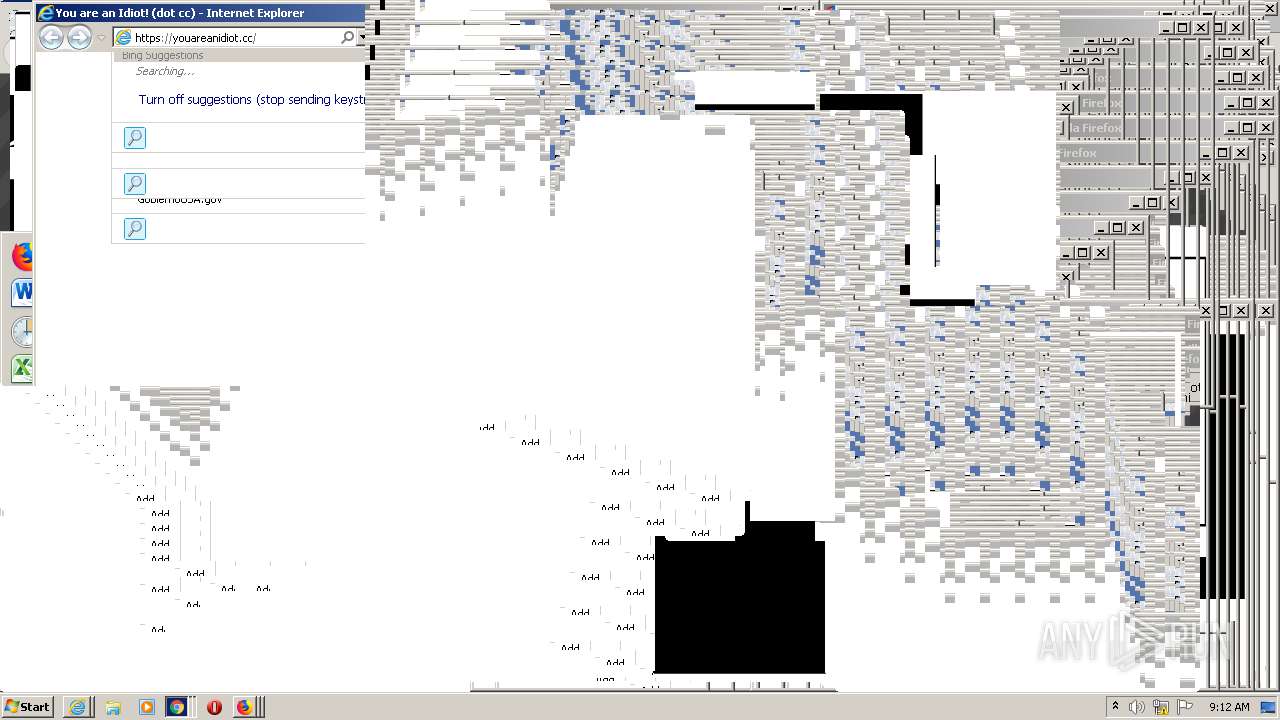
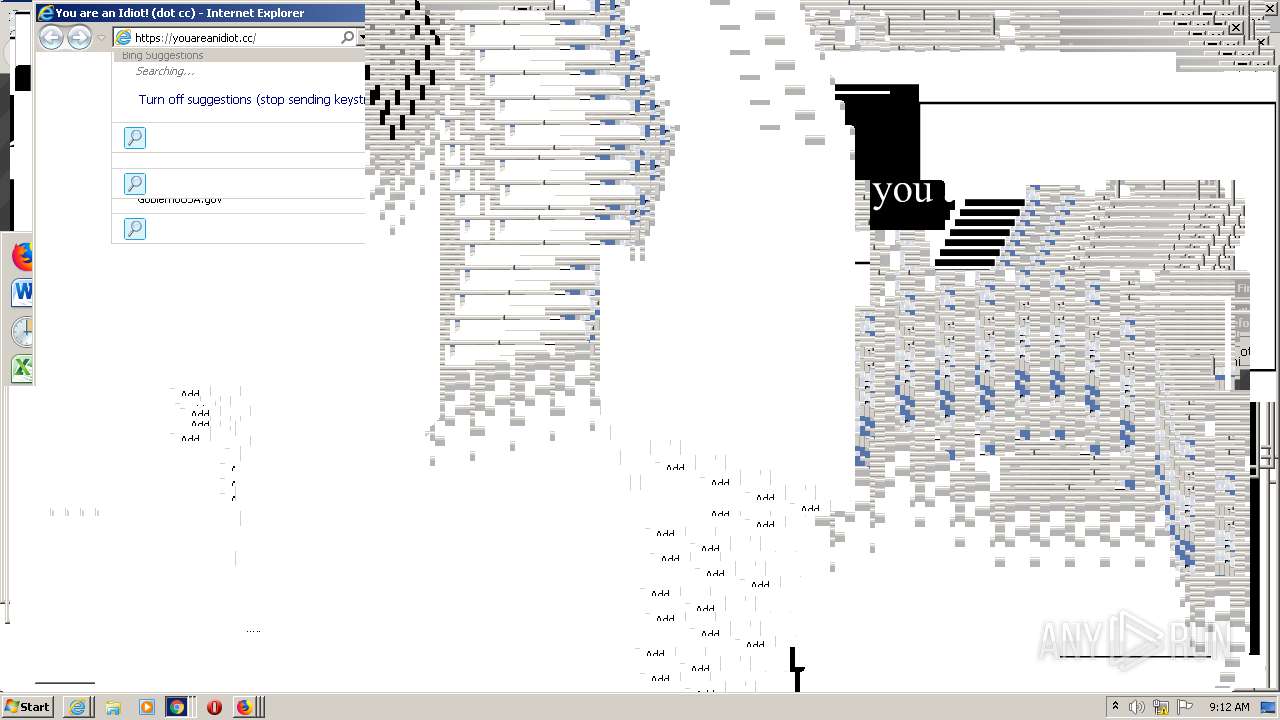
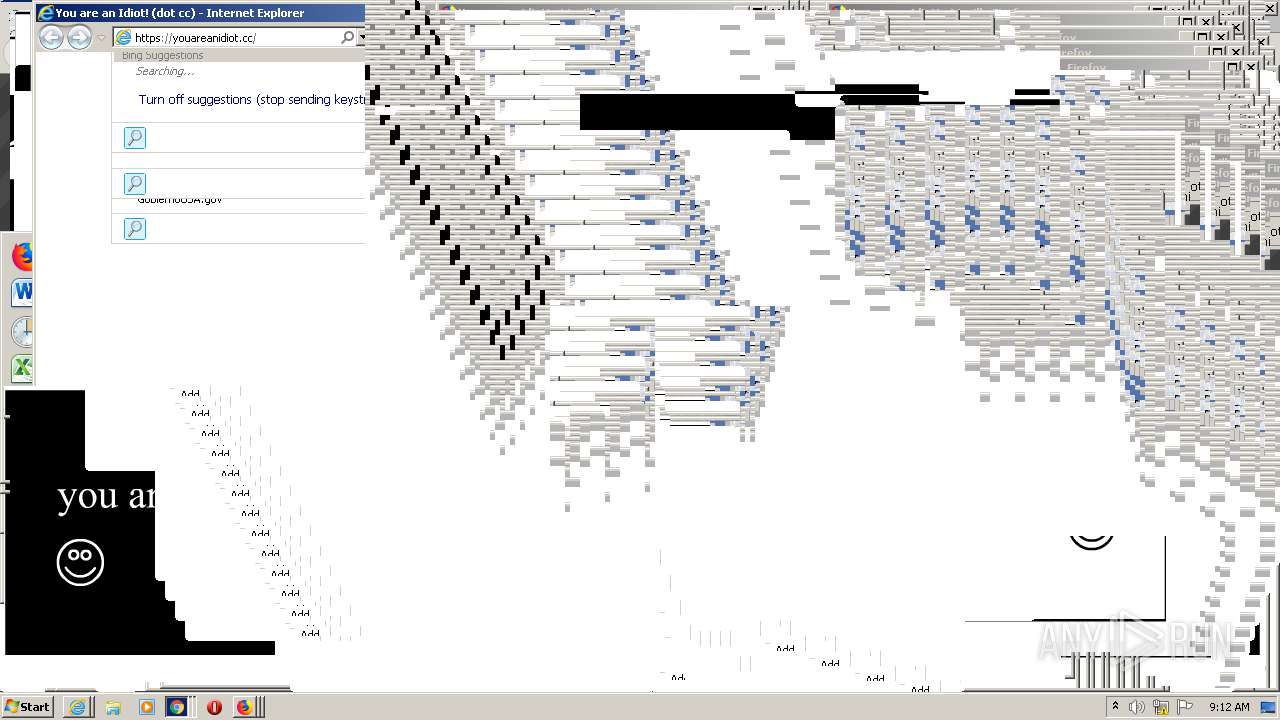
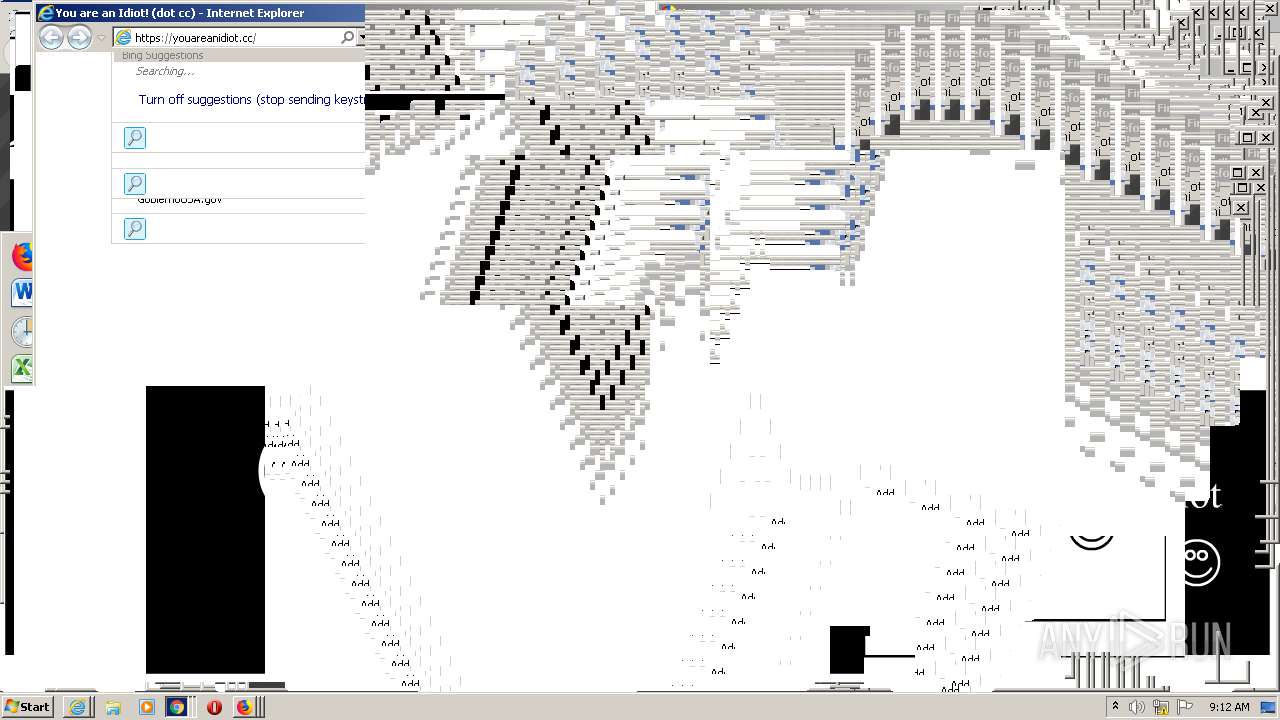
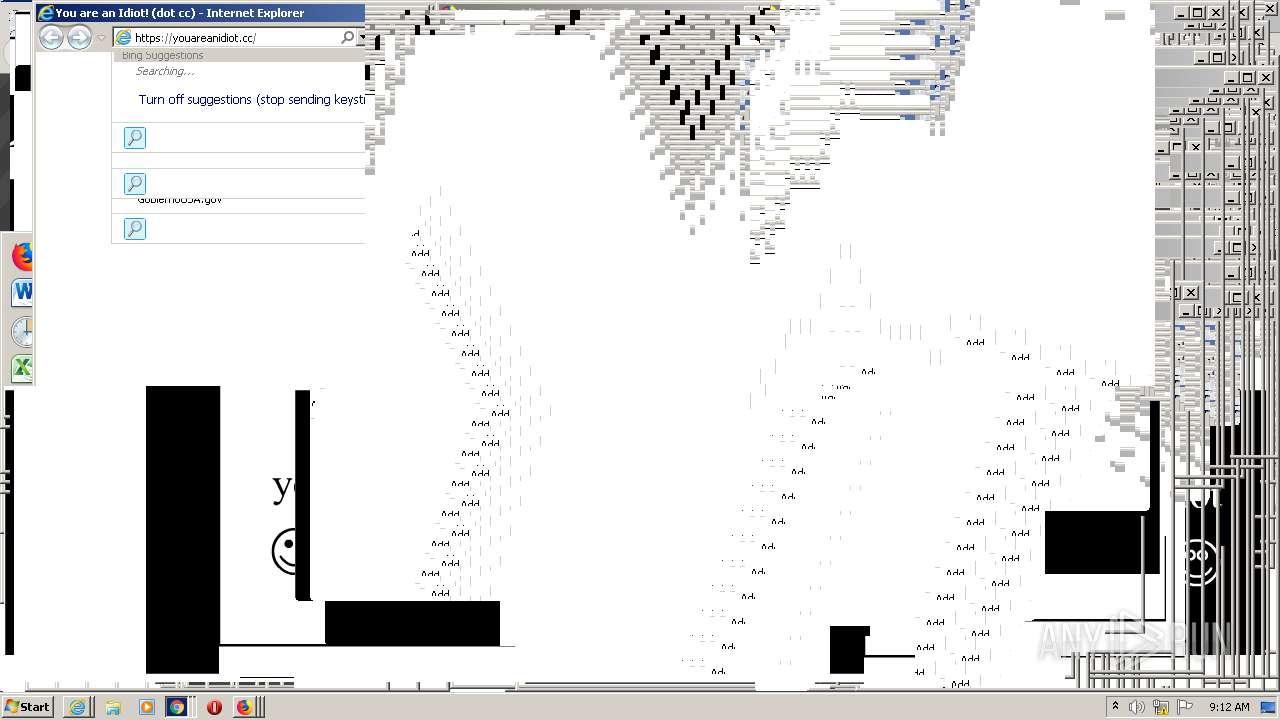
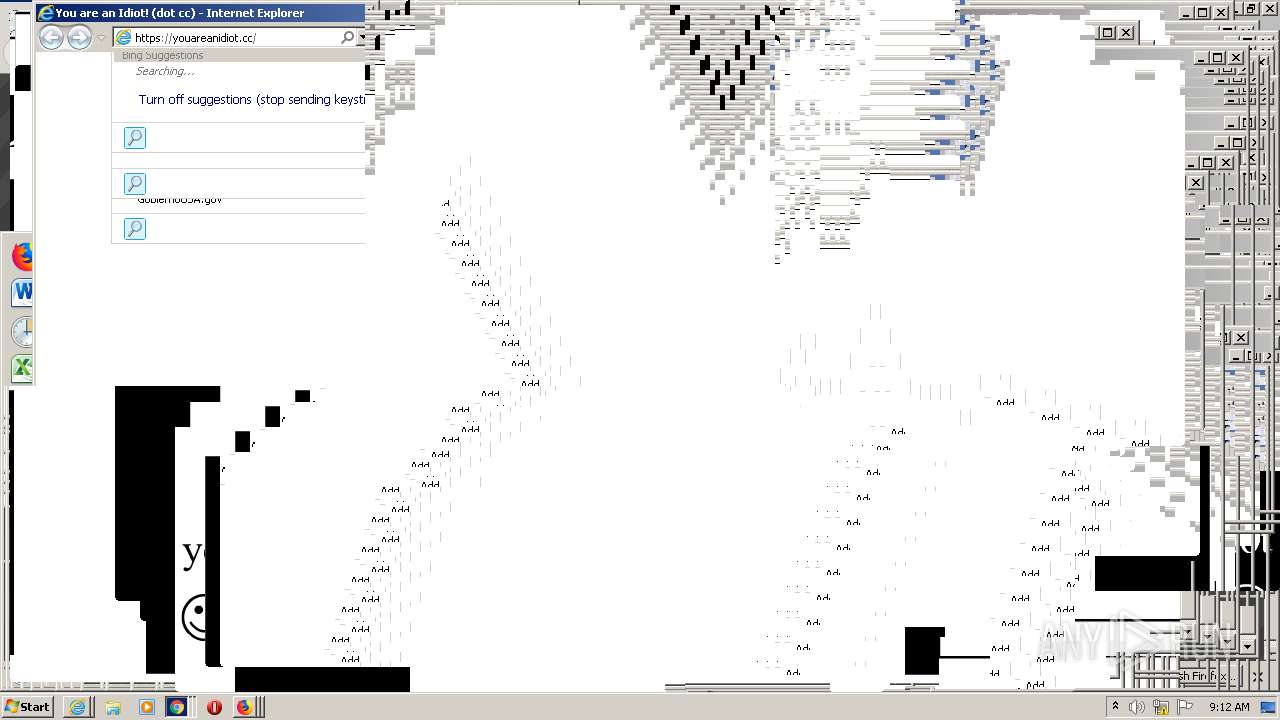
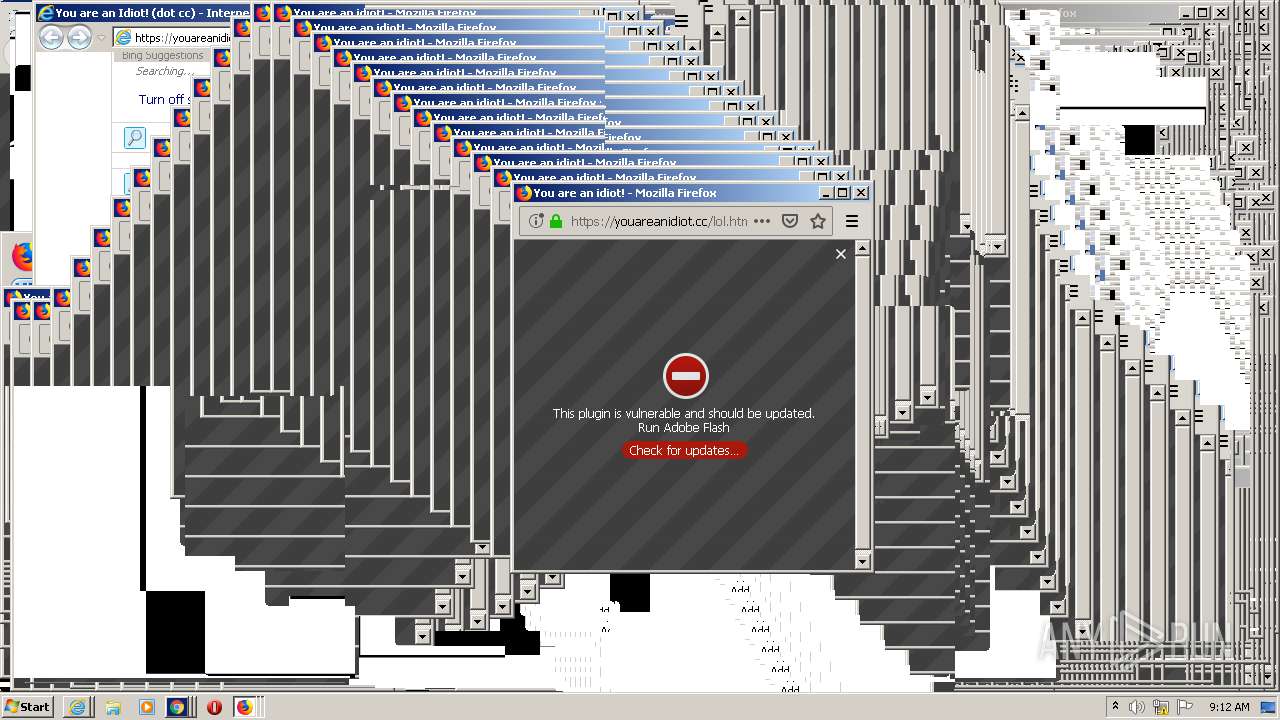
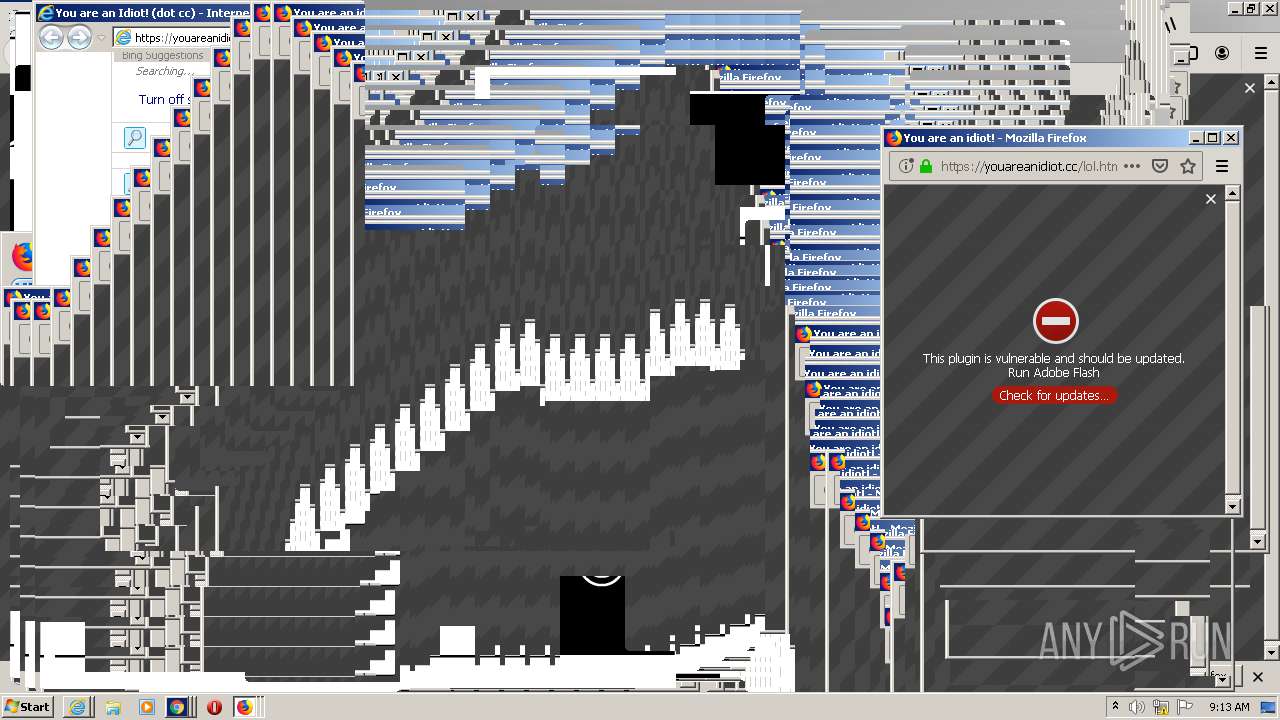
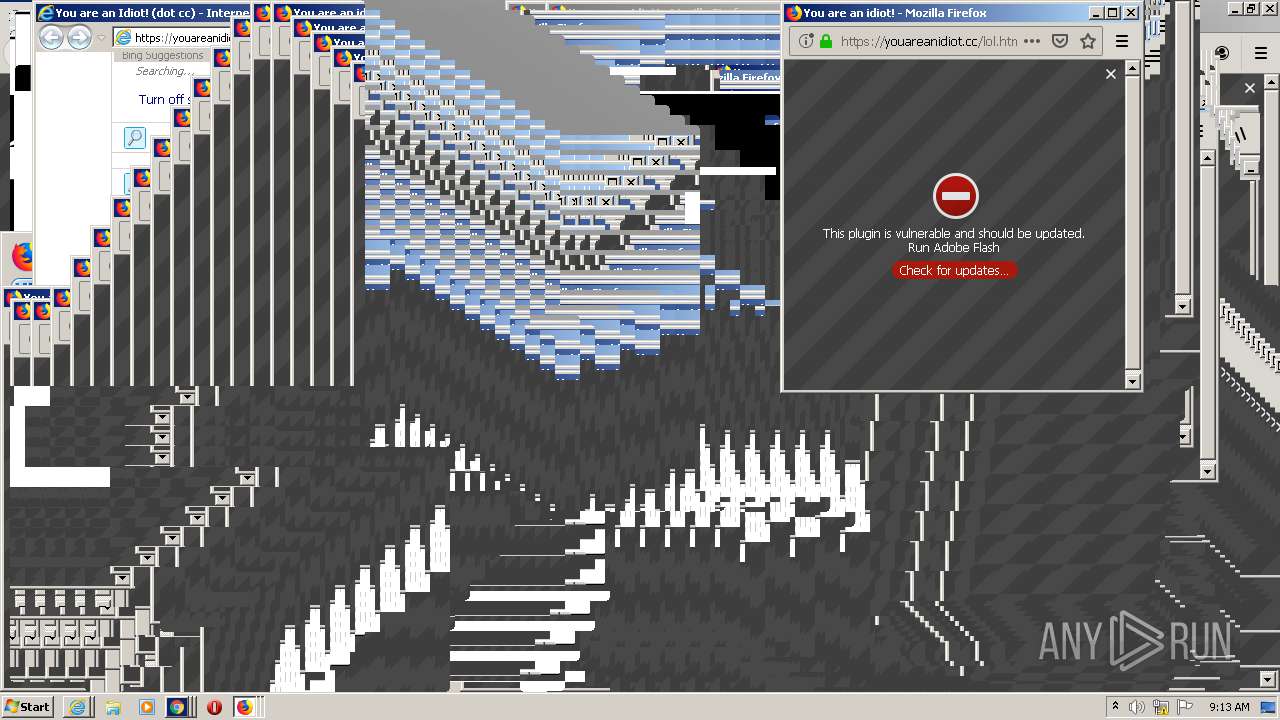
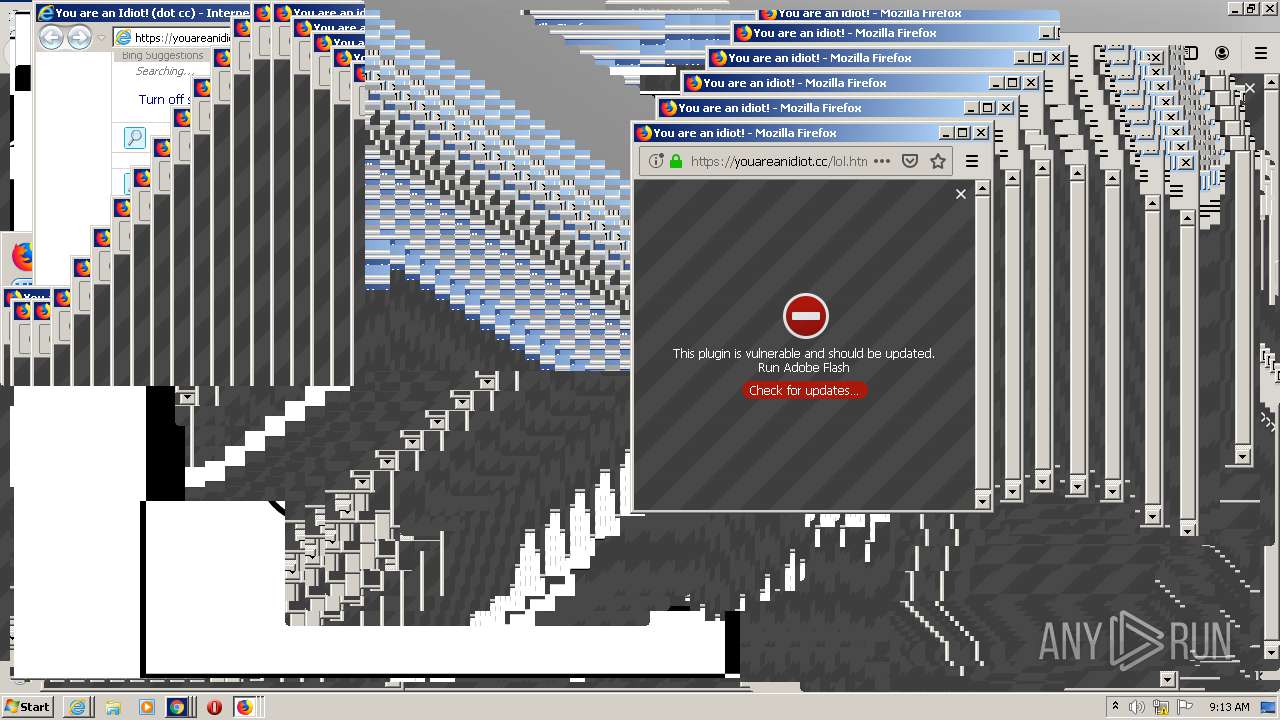
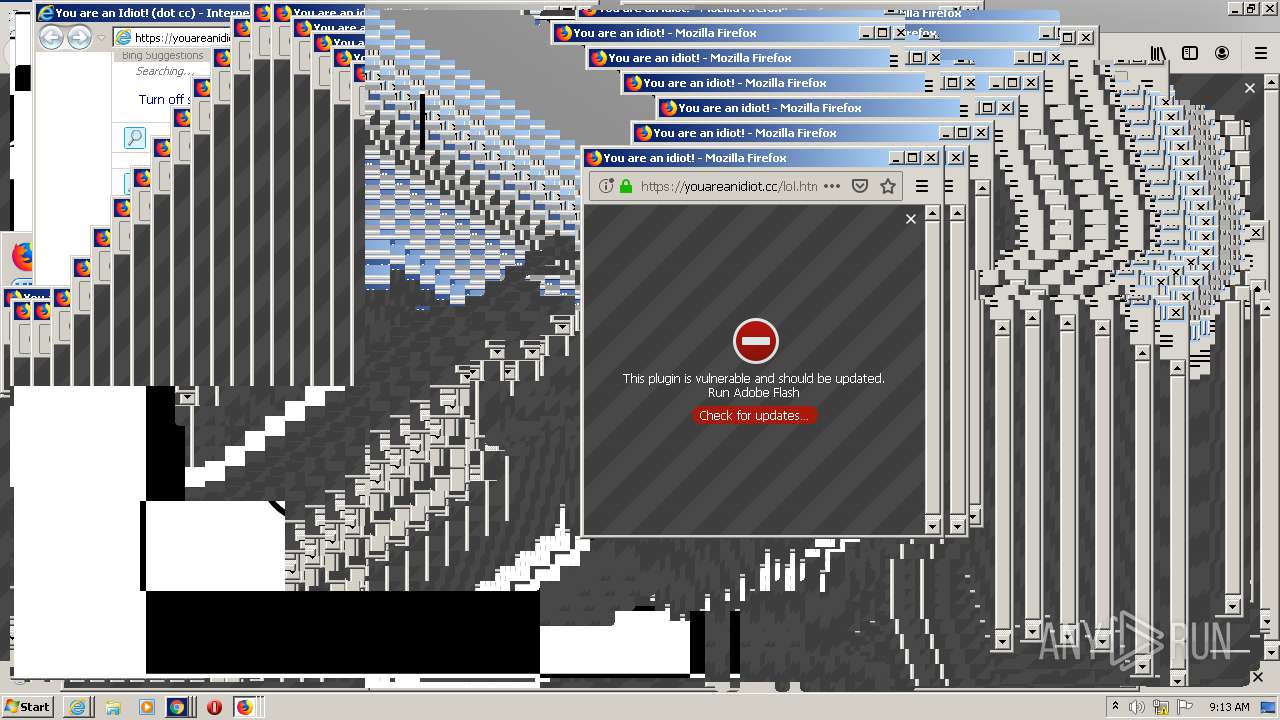
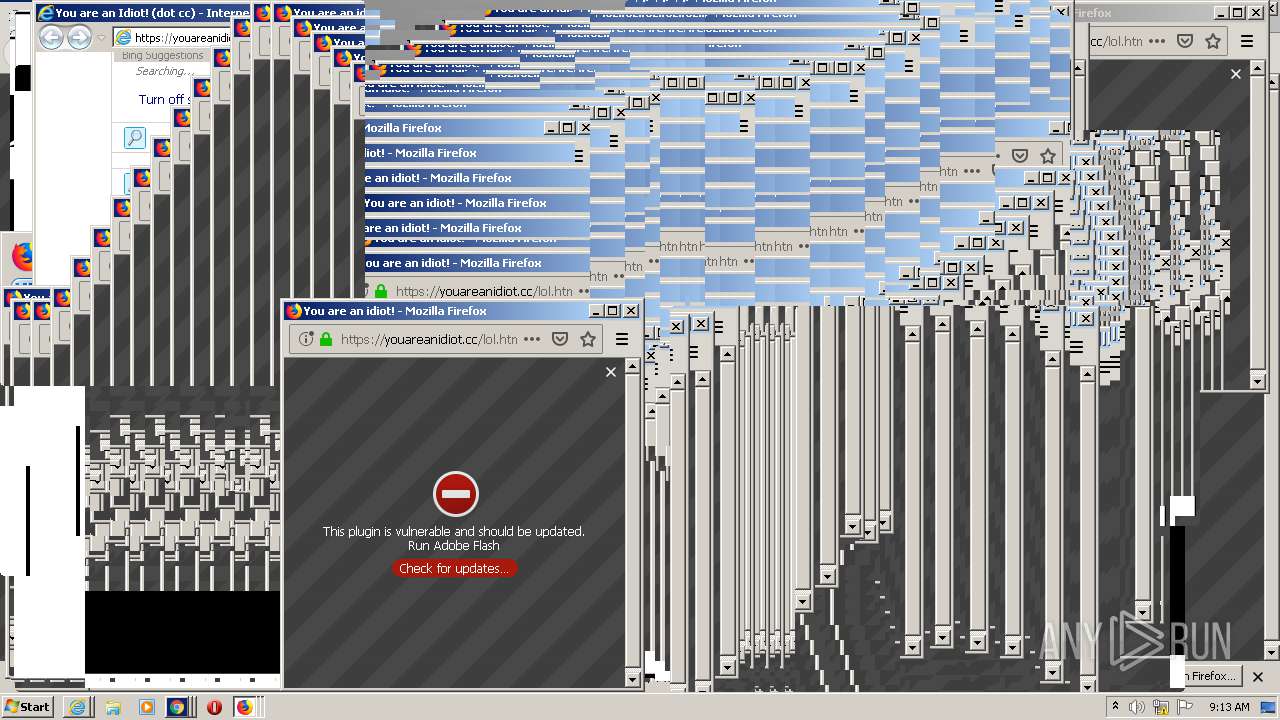
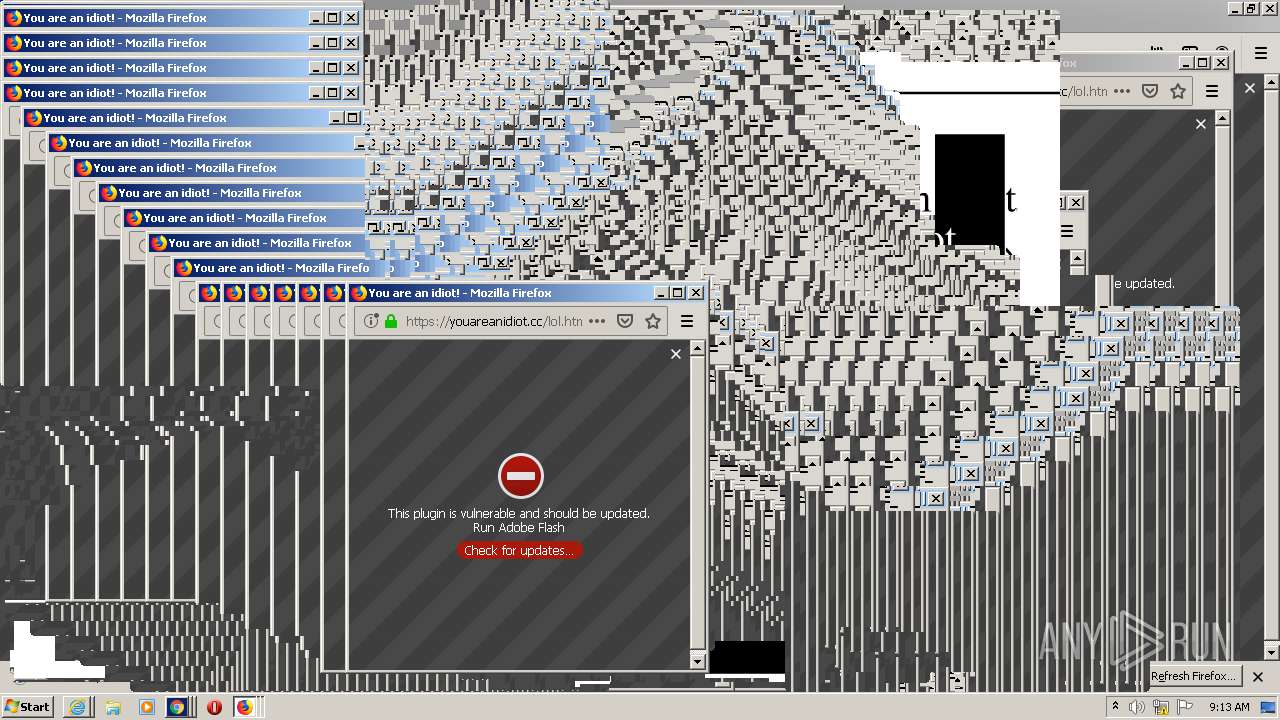
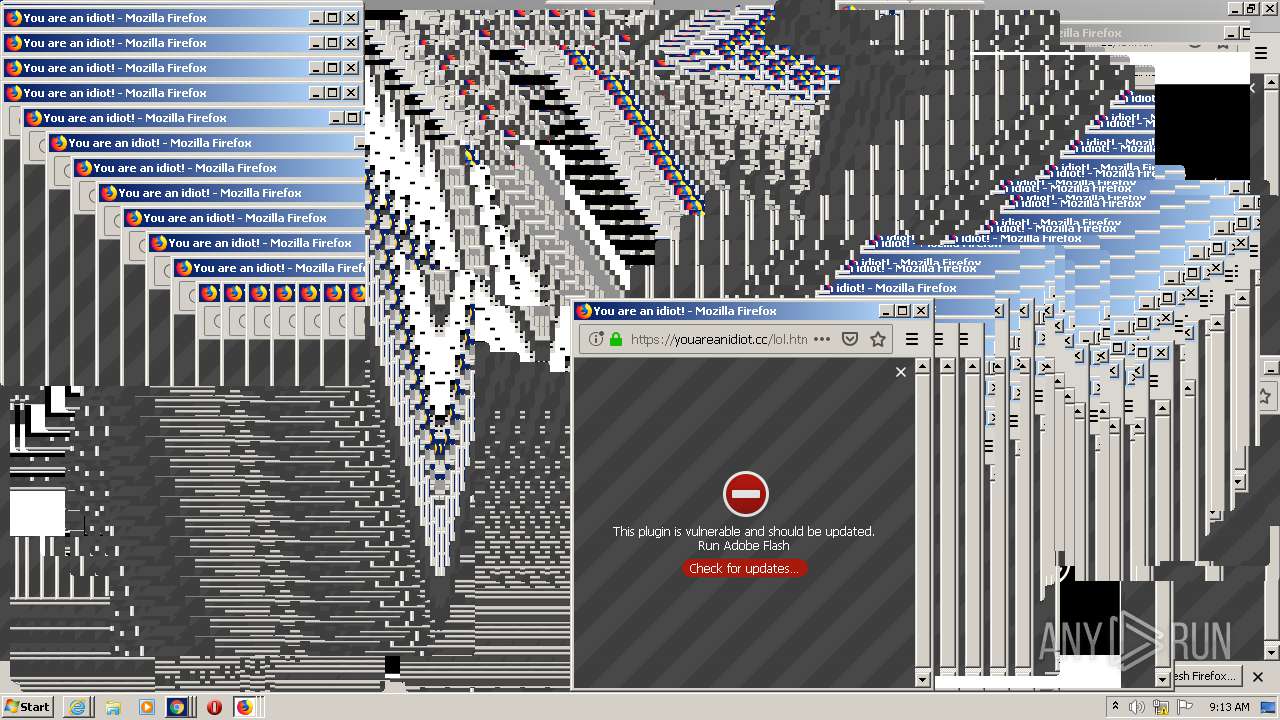
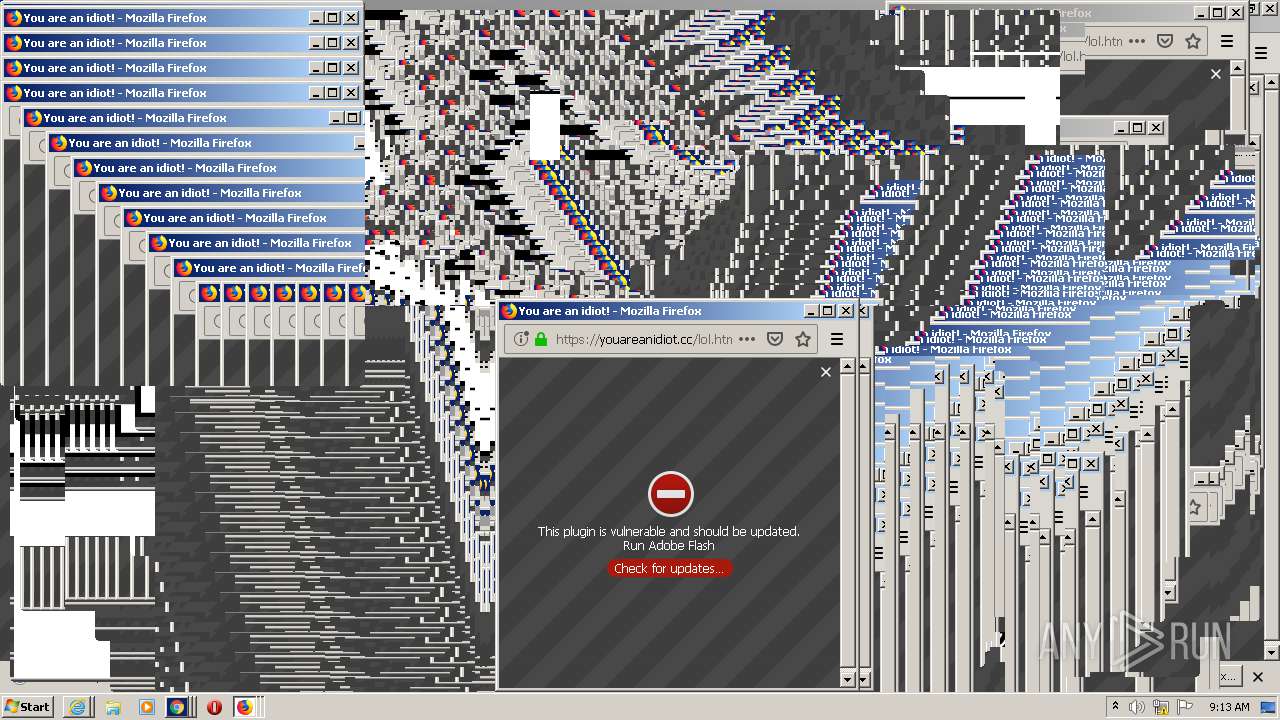
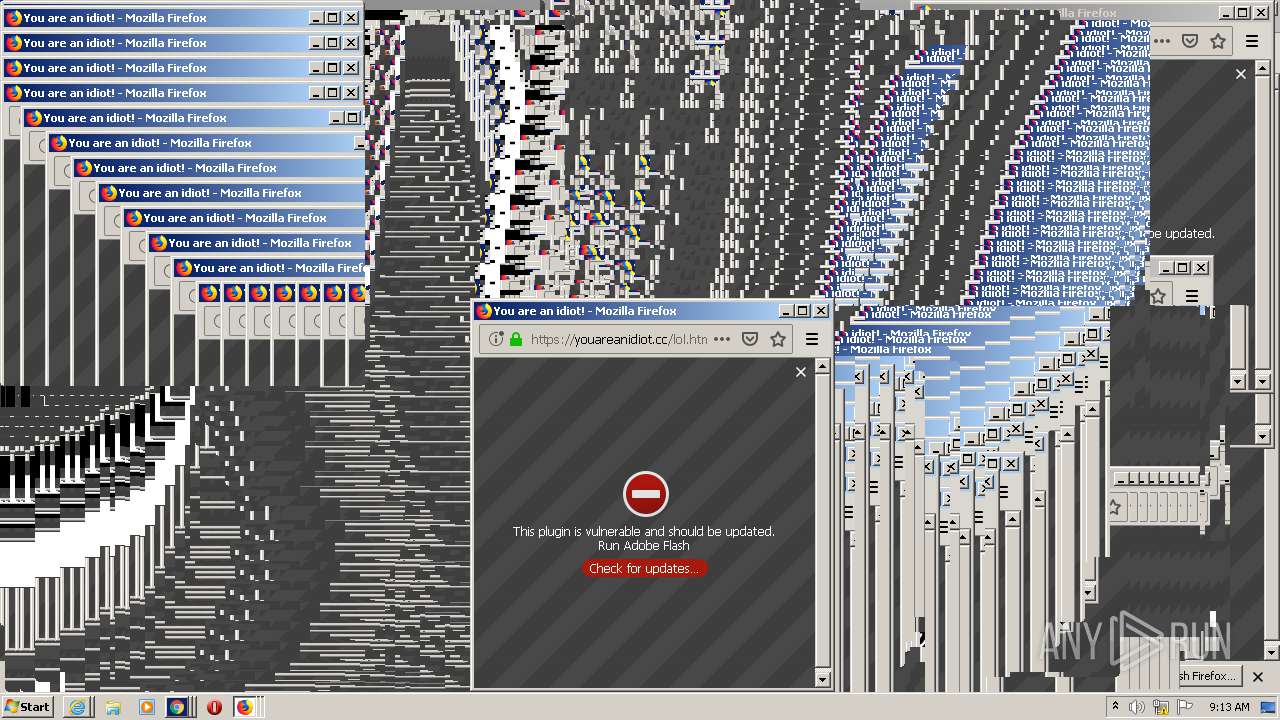
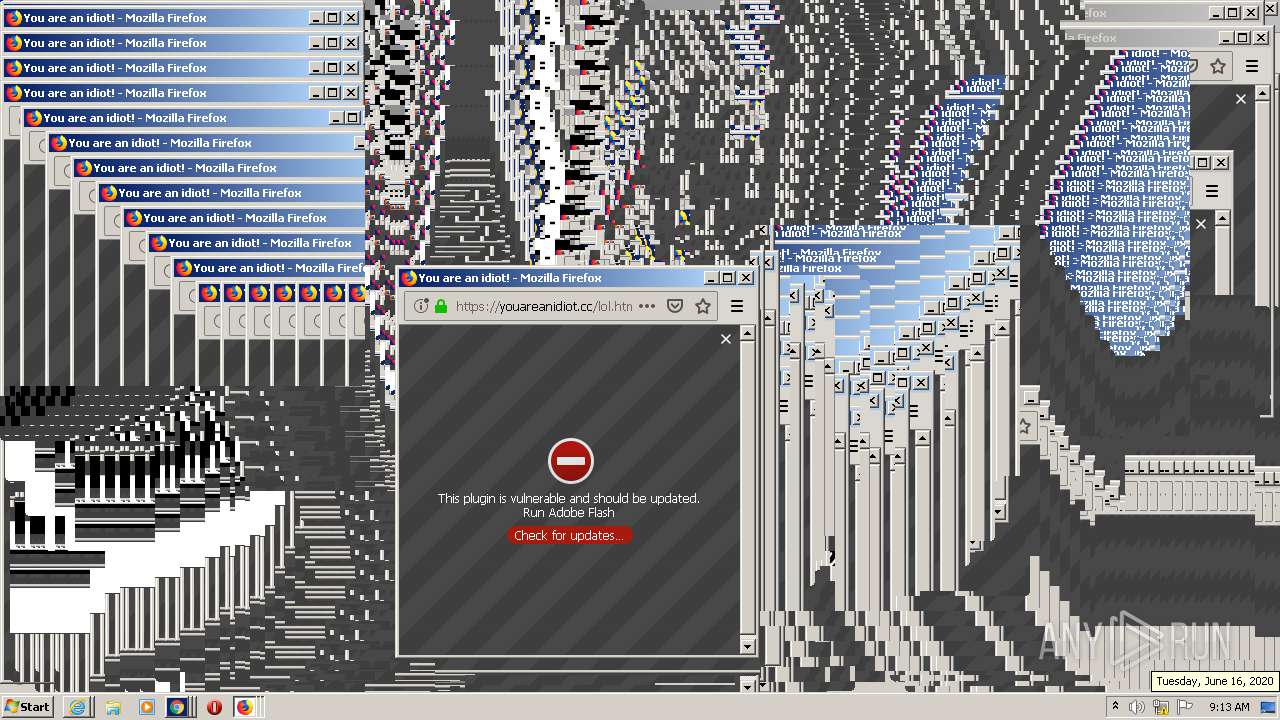
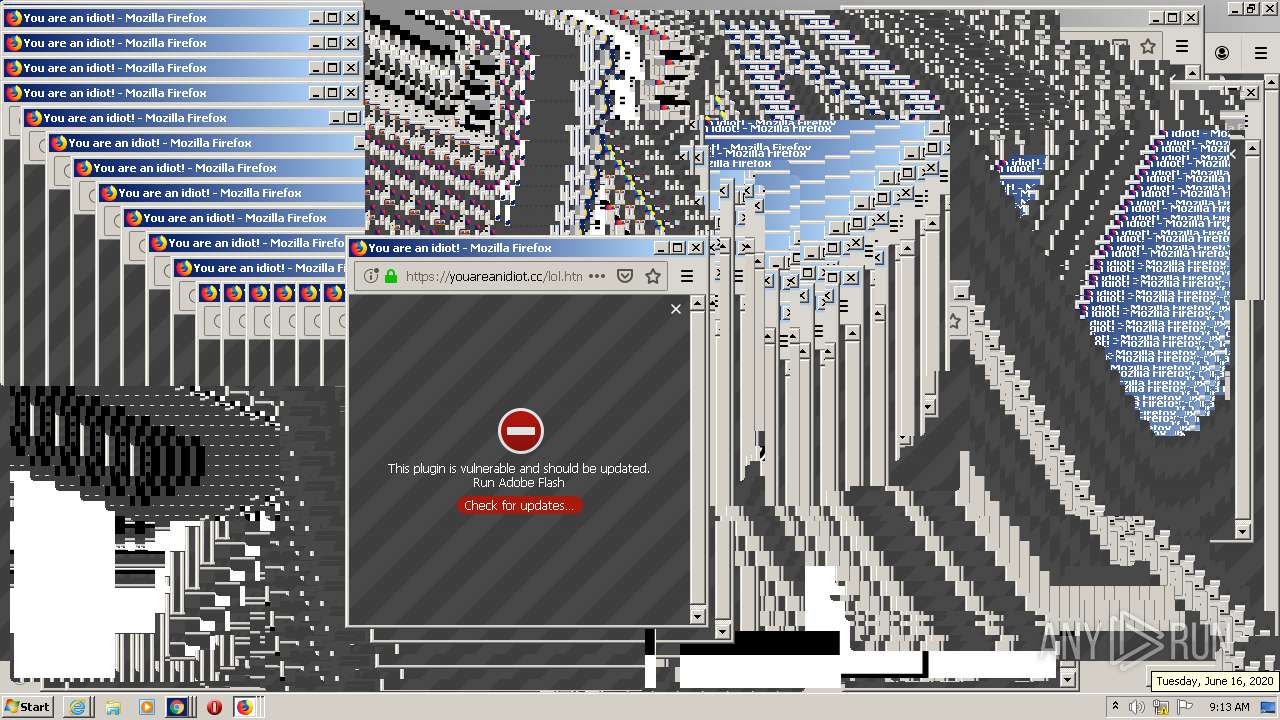
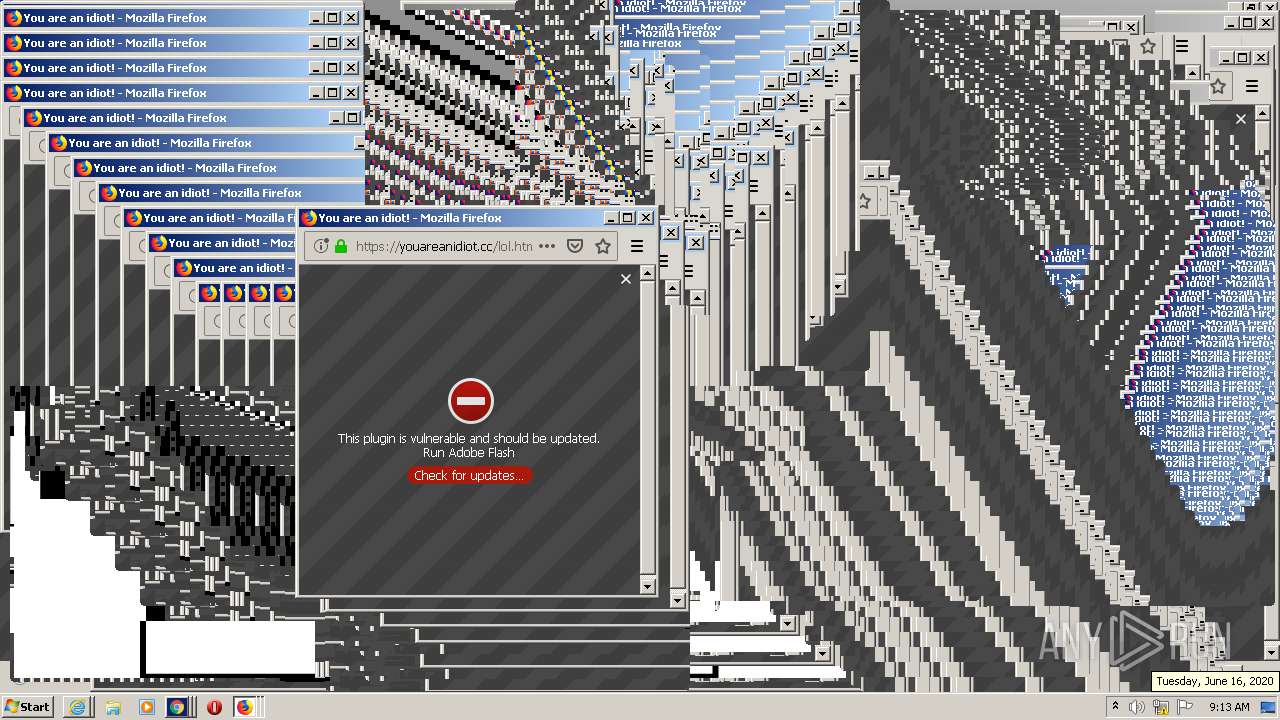
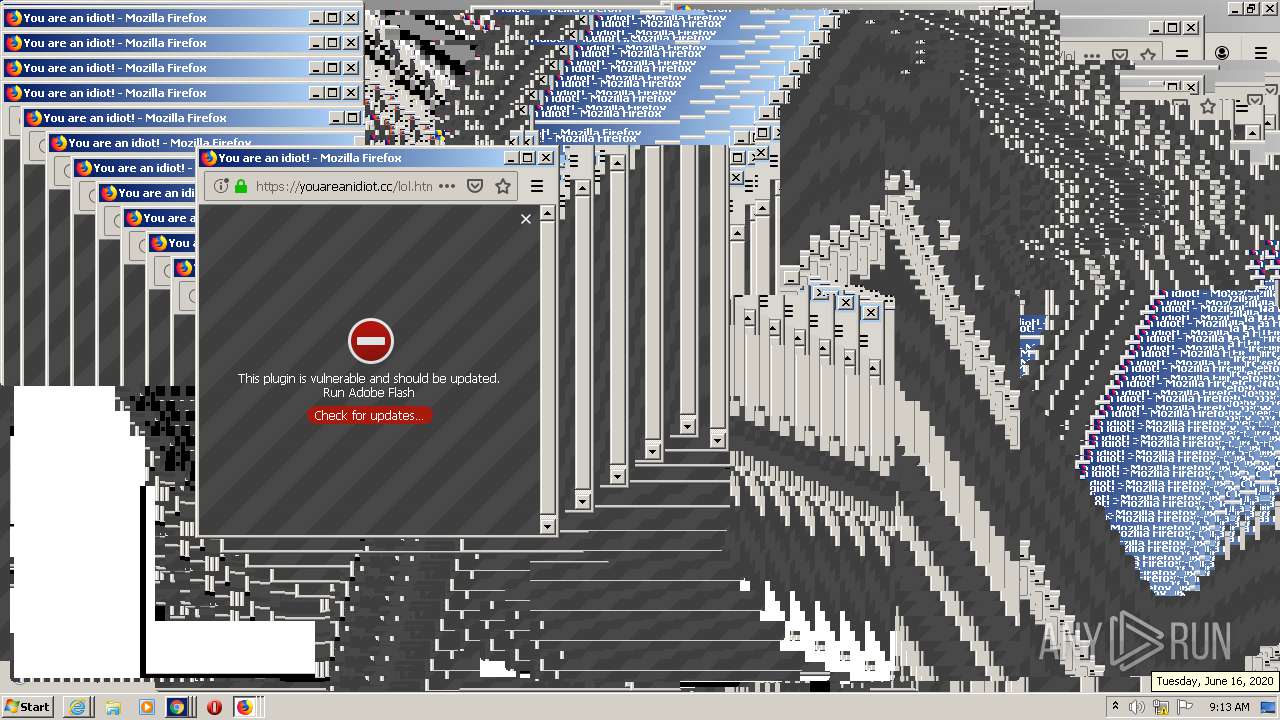
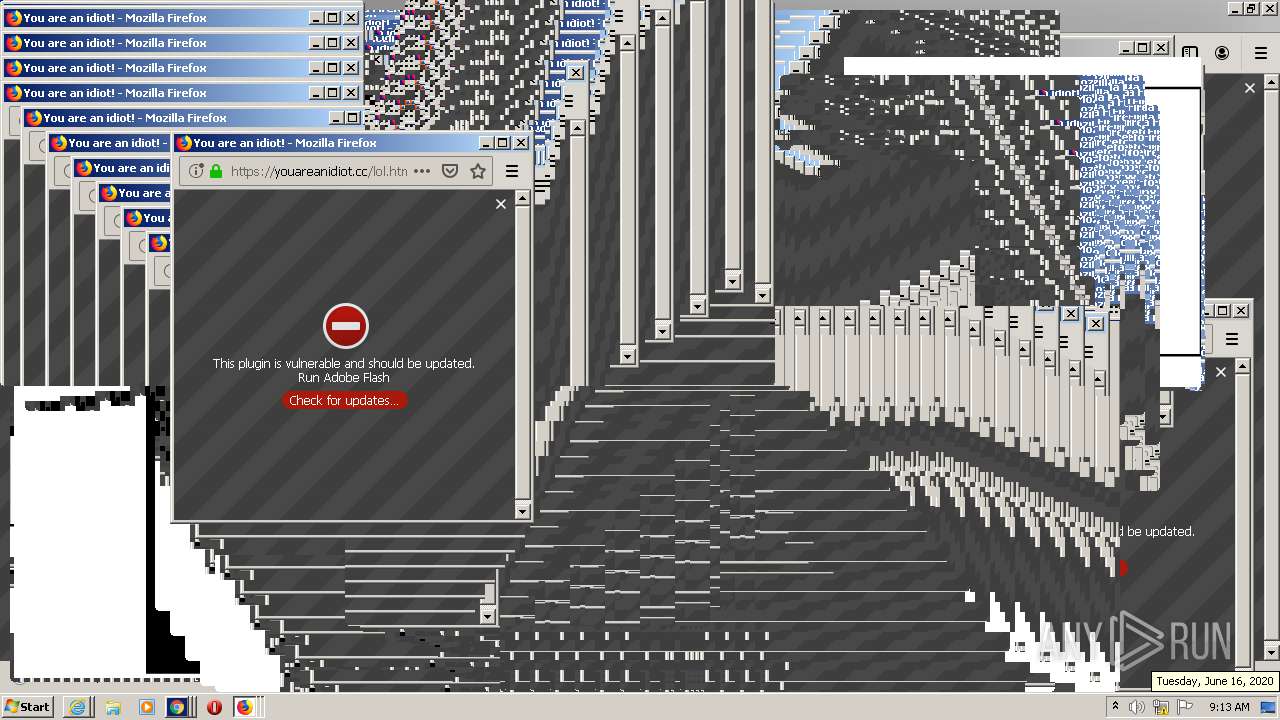
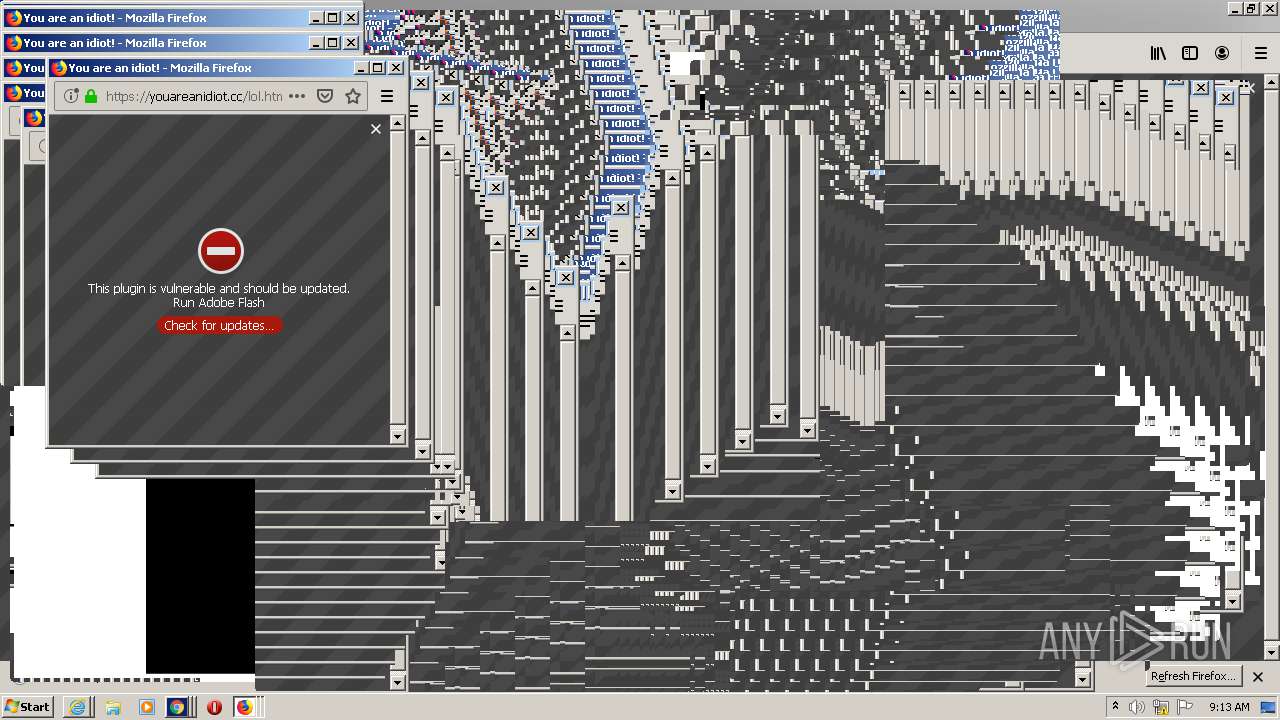
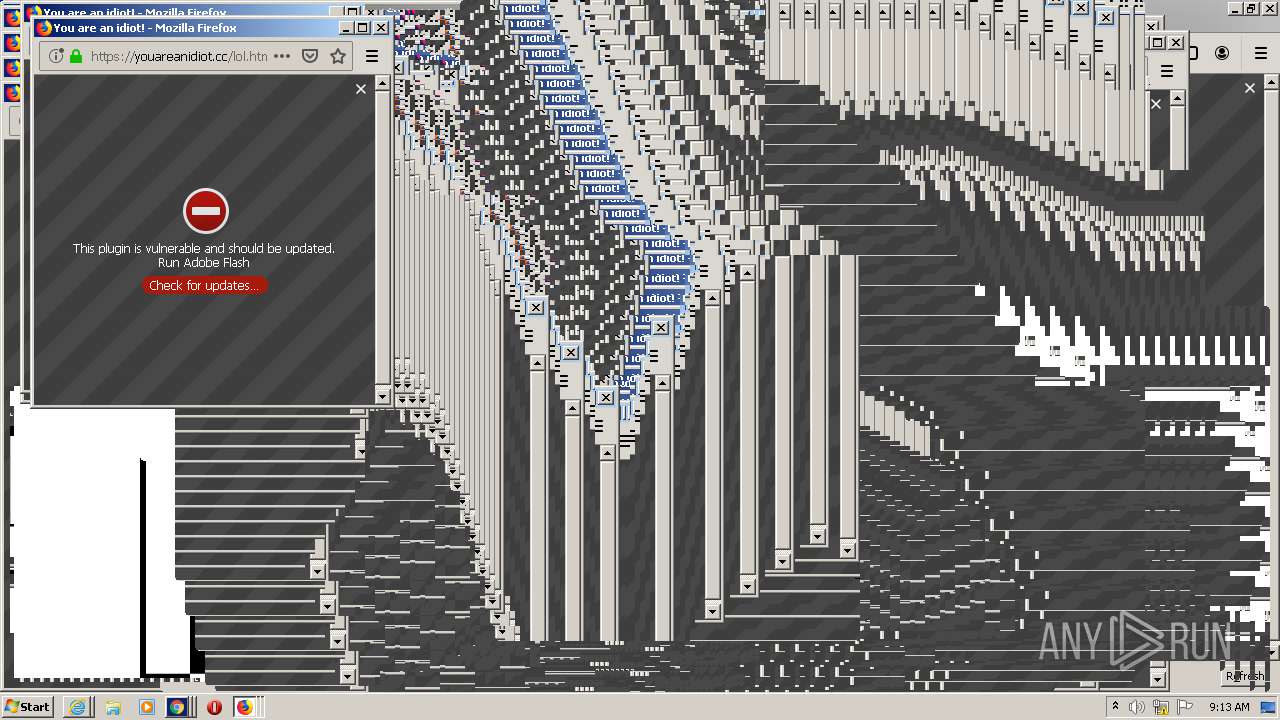
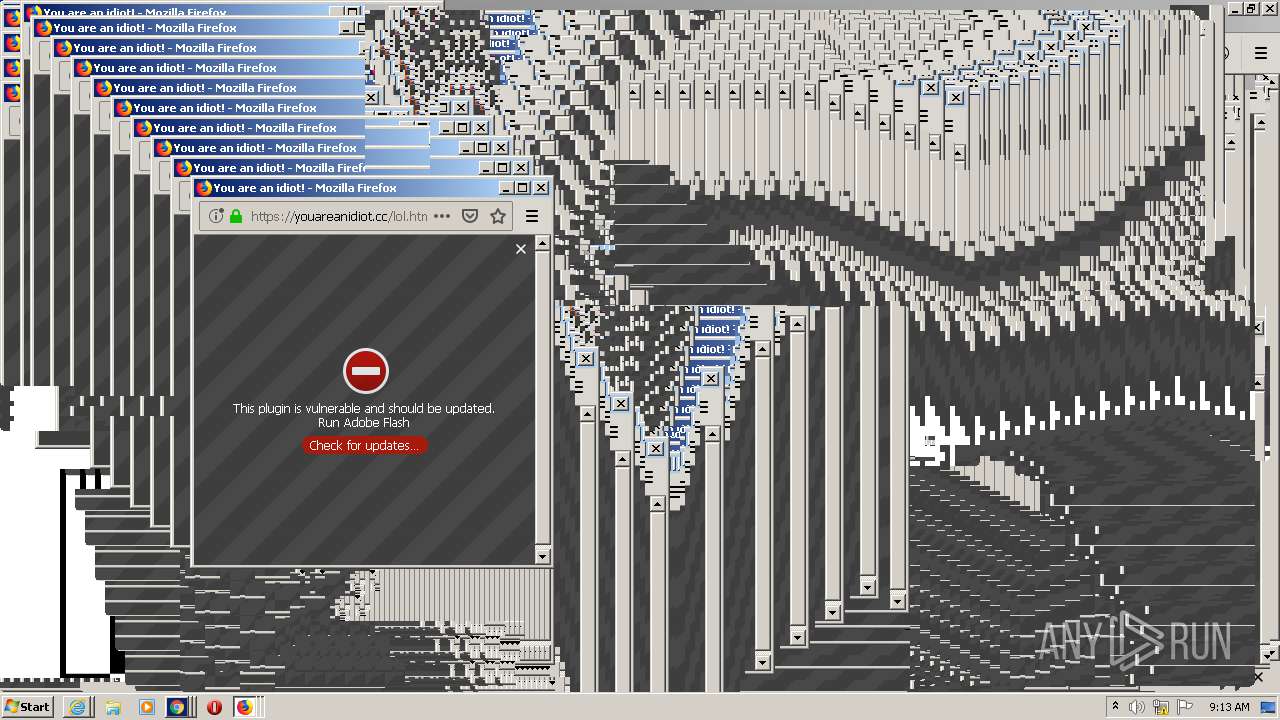
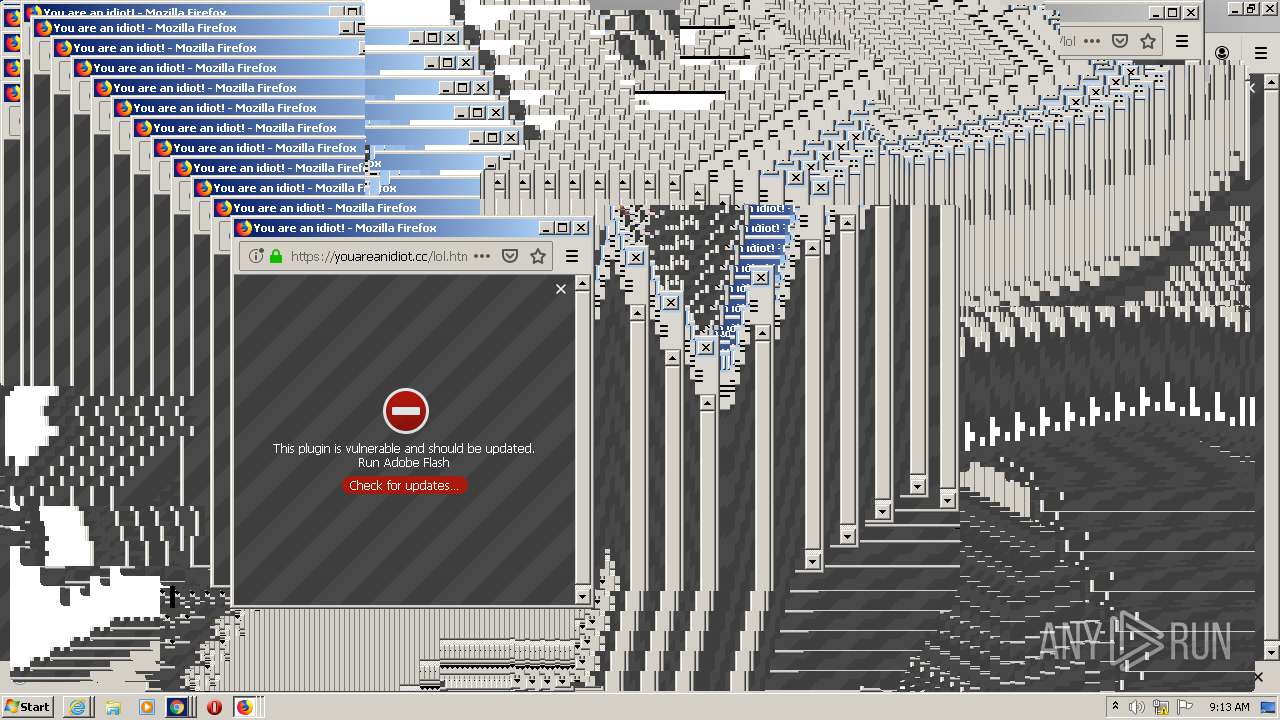
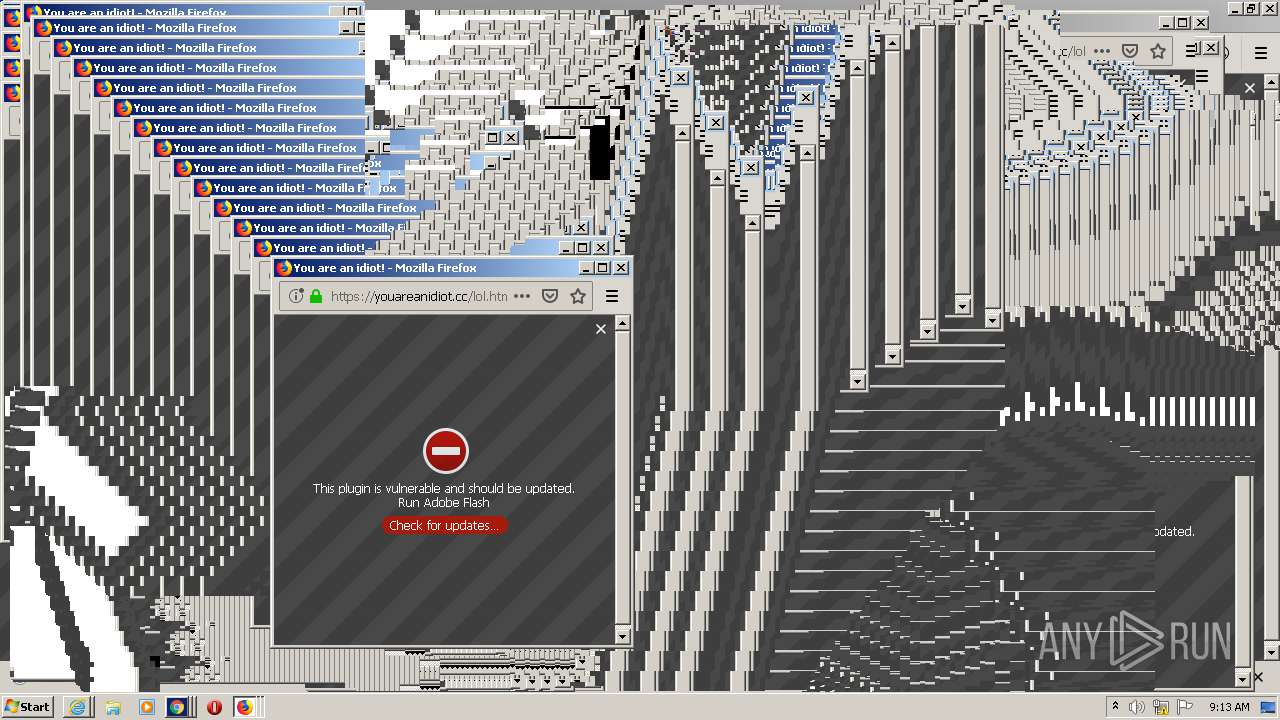
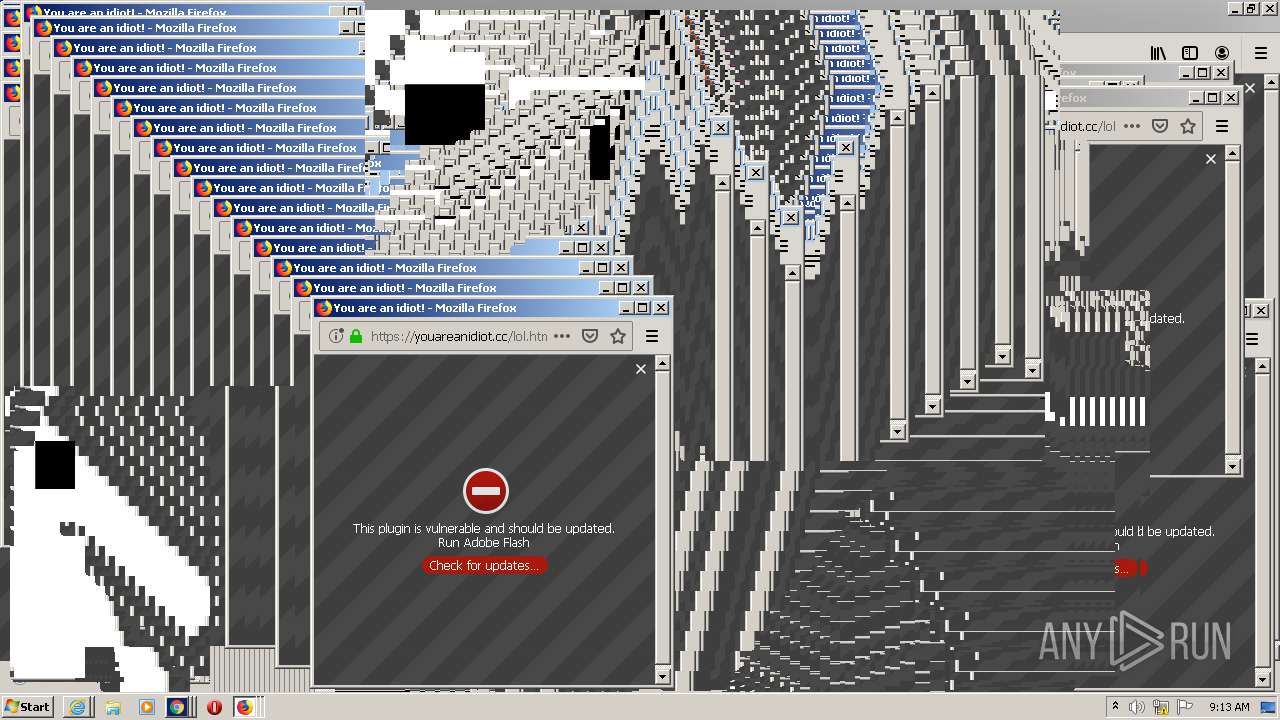
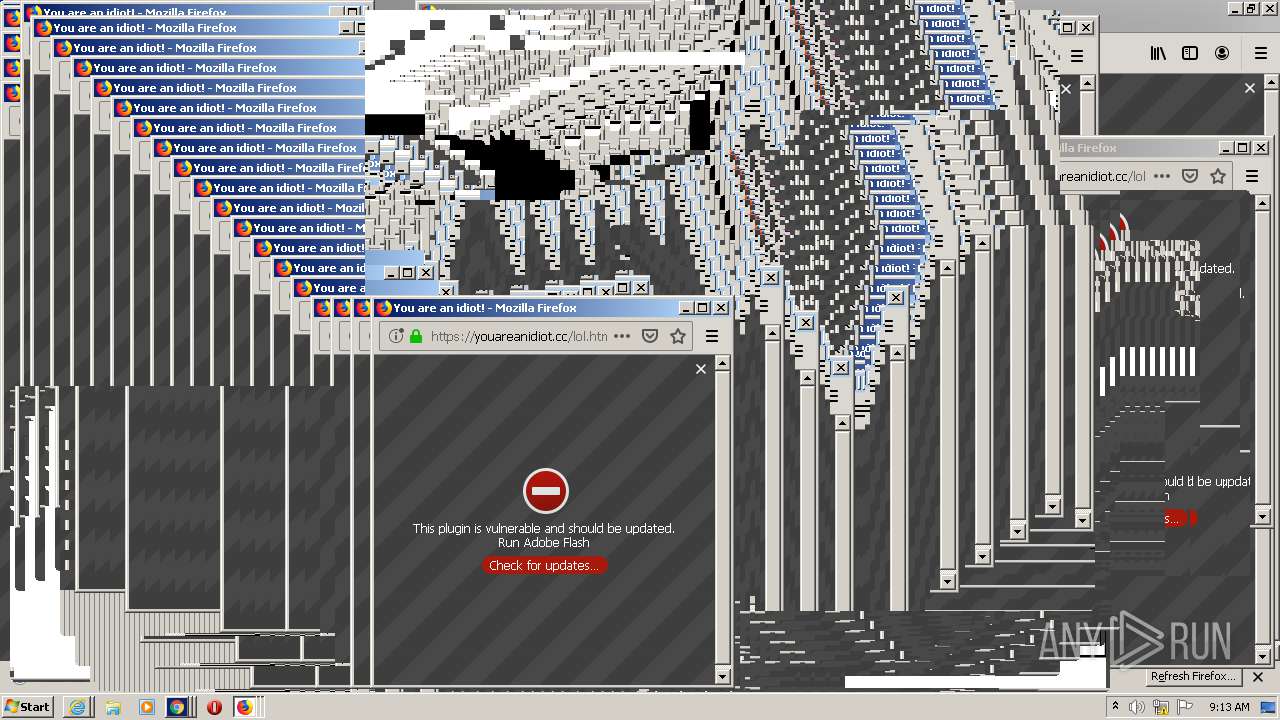
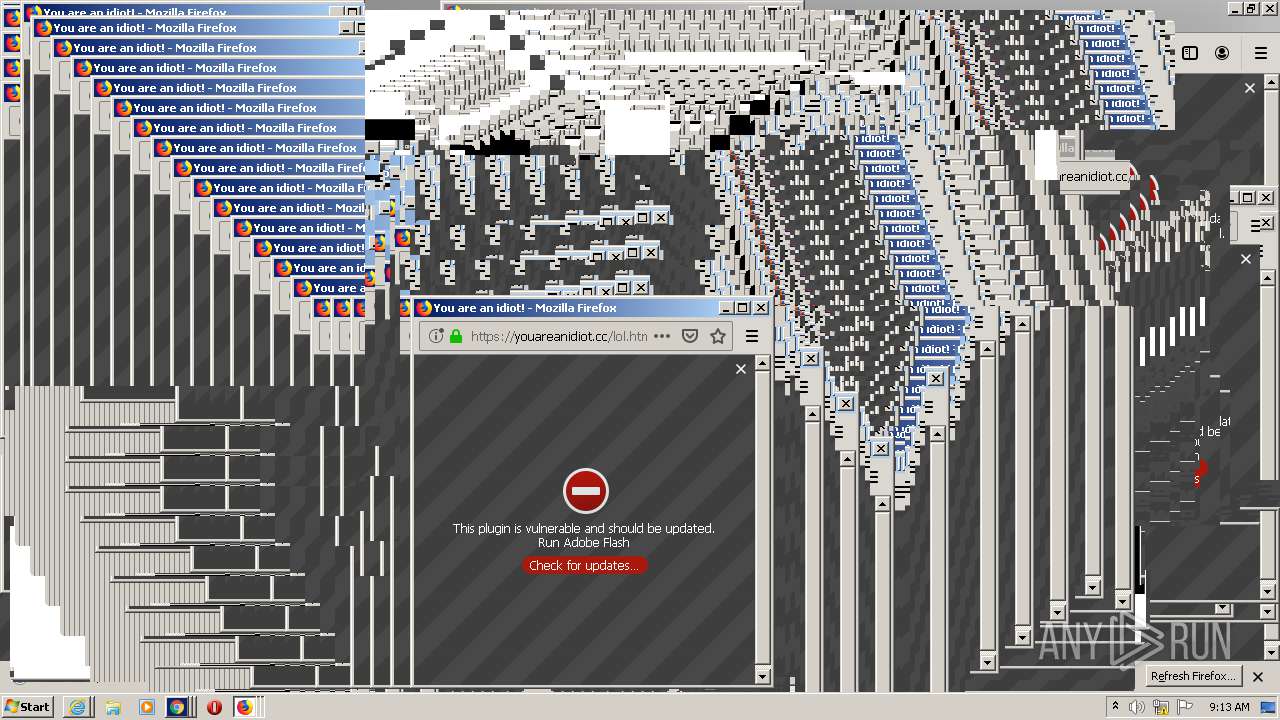
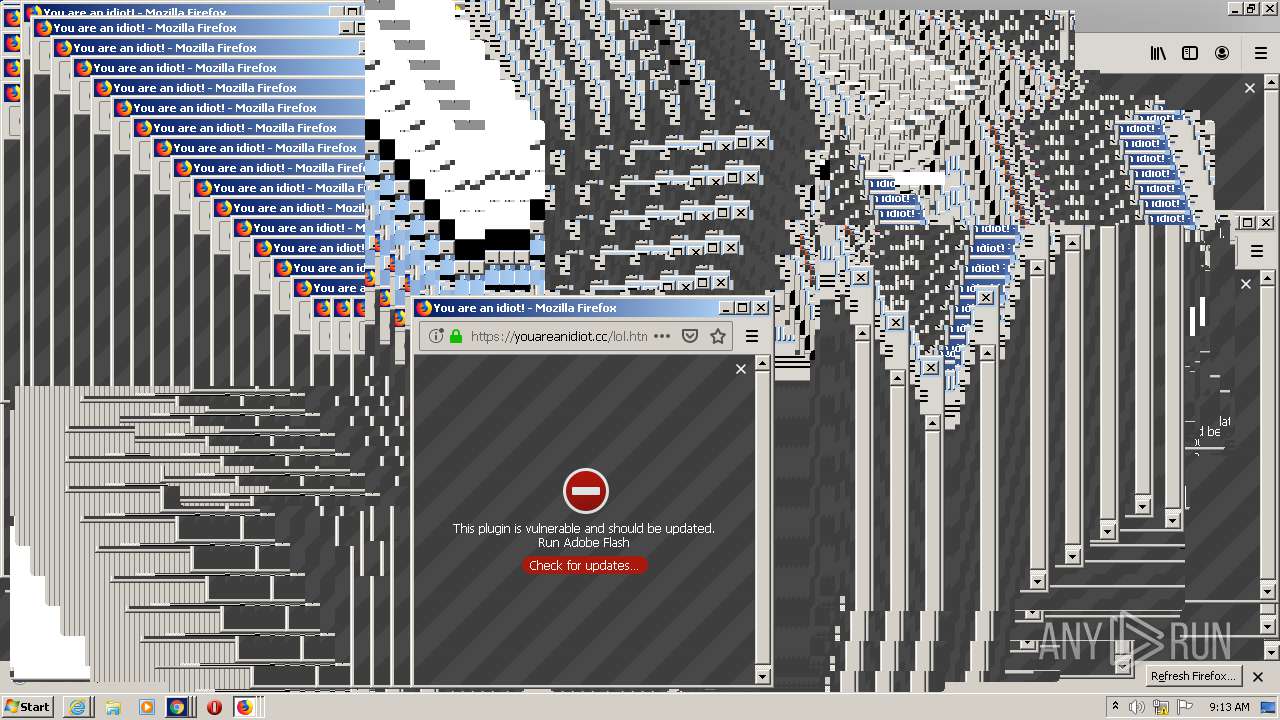
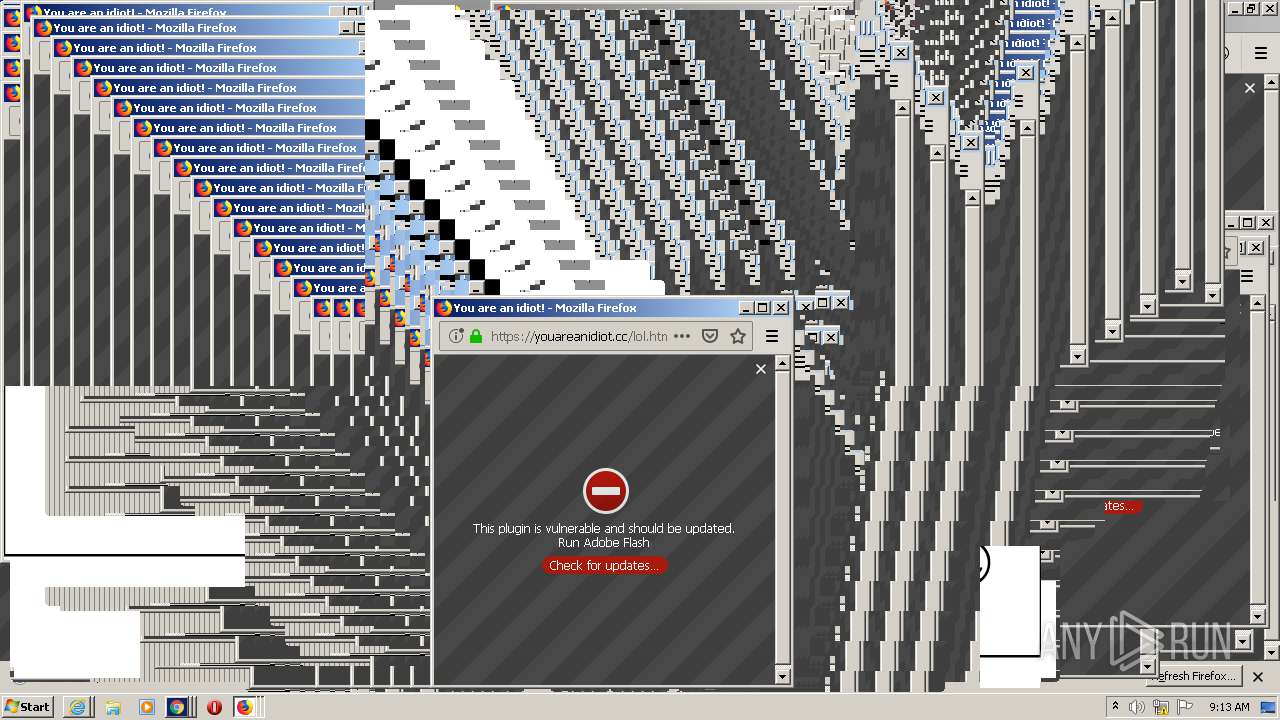
| URL: | https://youareanidiot.cc |
| Full analysis: | https://app.any.run/tasks/3c5b691b-2644-43f7-ade2-4e7edc4f30d5 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2020, 08:08:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F18F0C9C6DC4C9300E89D61335531E20 |
| SHA1: | FB03FE89D9656E664C8A1861AE21660B7C8EF1C6 |
| SHA256: | A02203723F398B47295C8F386FCF74DC40635D0FE6B795E0C1AD8D4CC88C47D5 |
| SSDEEP: | 3:N8uKpQGG:2ul |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2640)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1540)
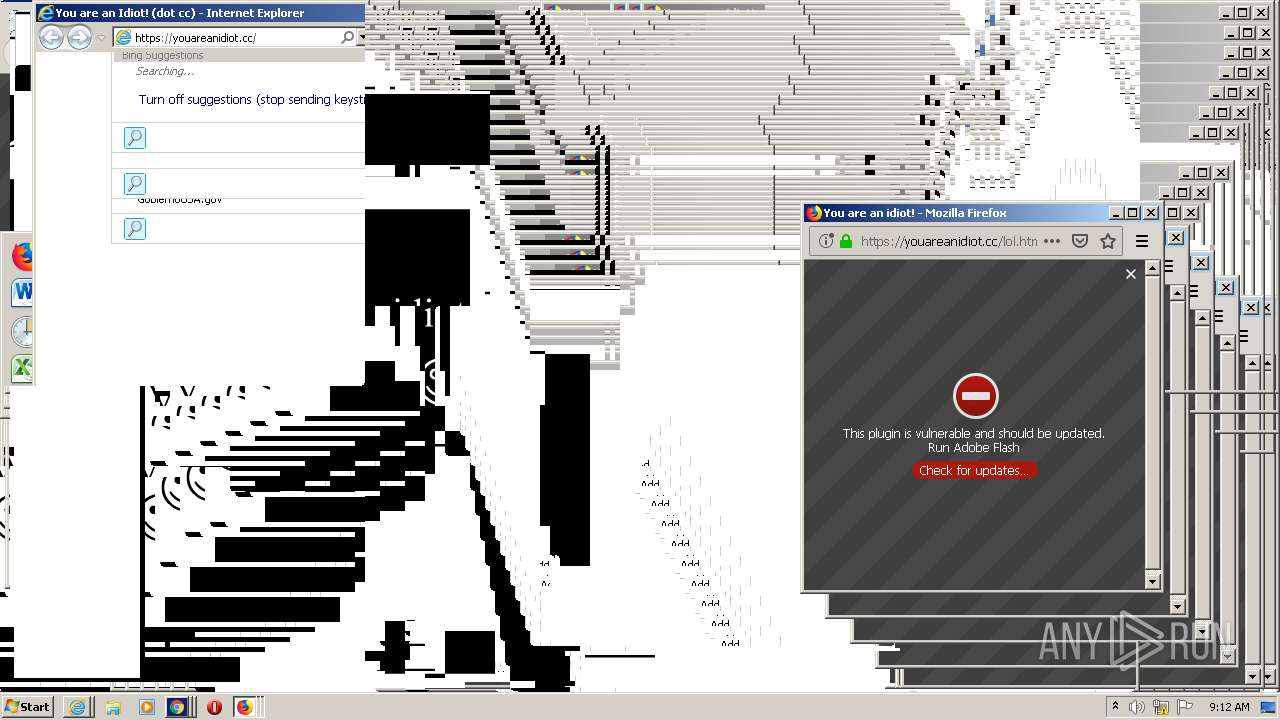
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4160)
INFO
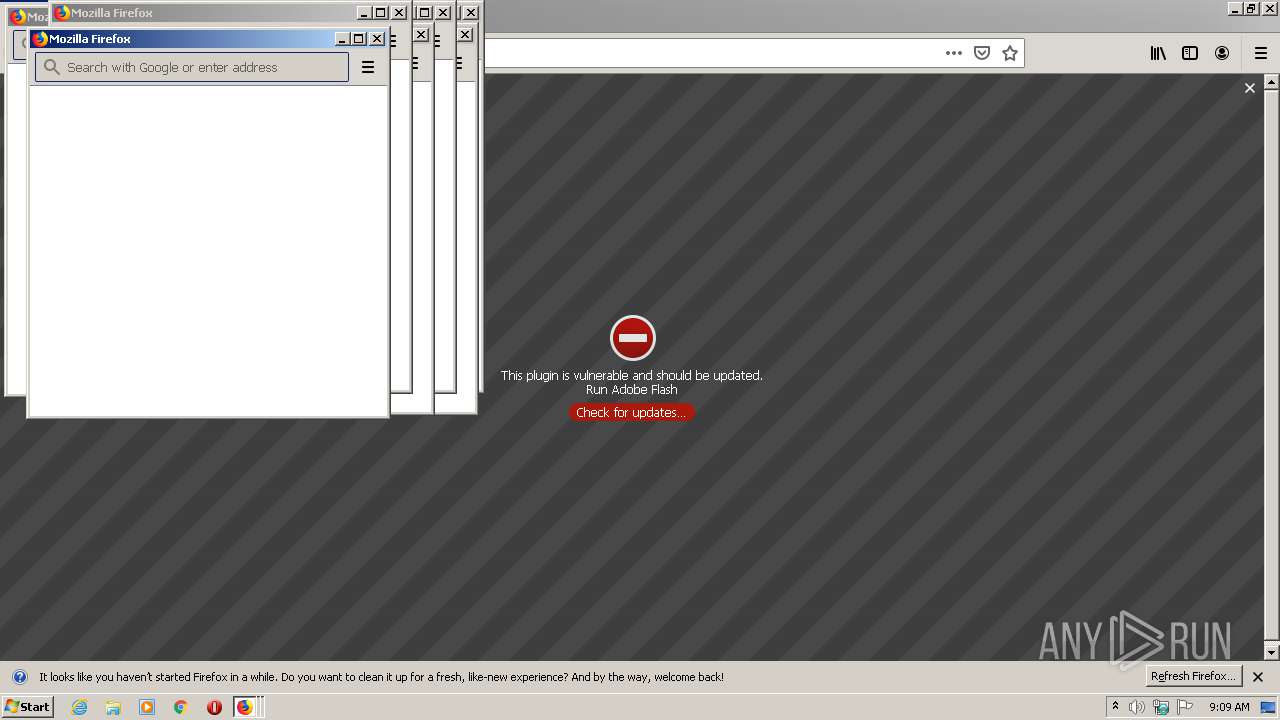
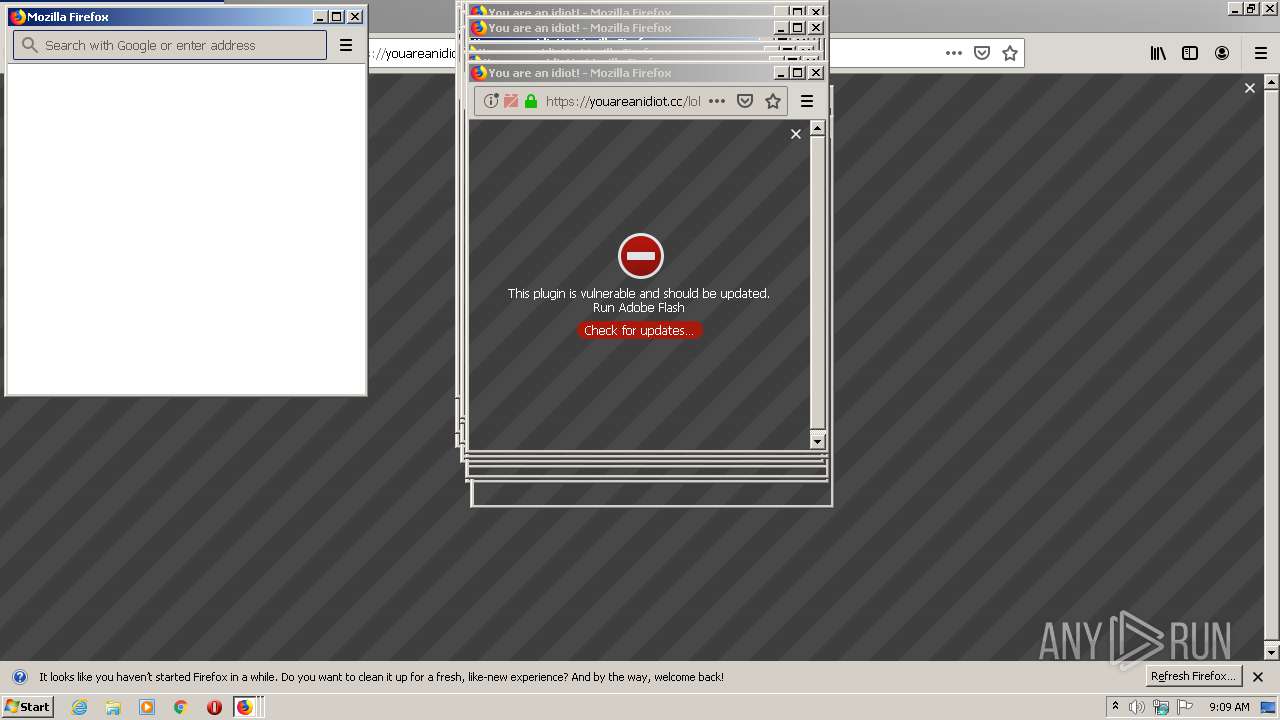
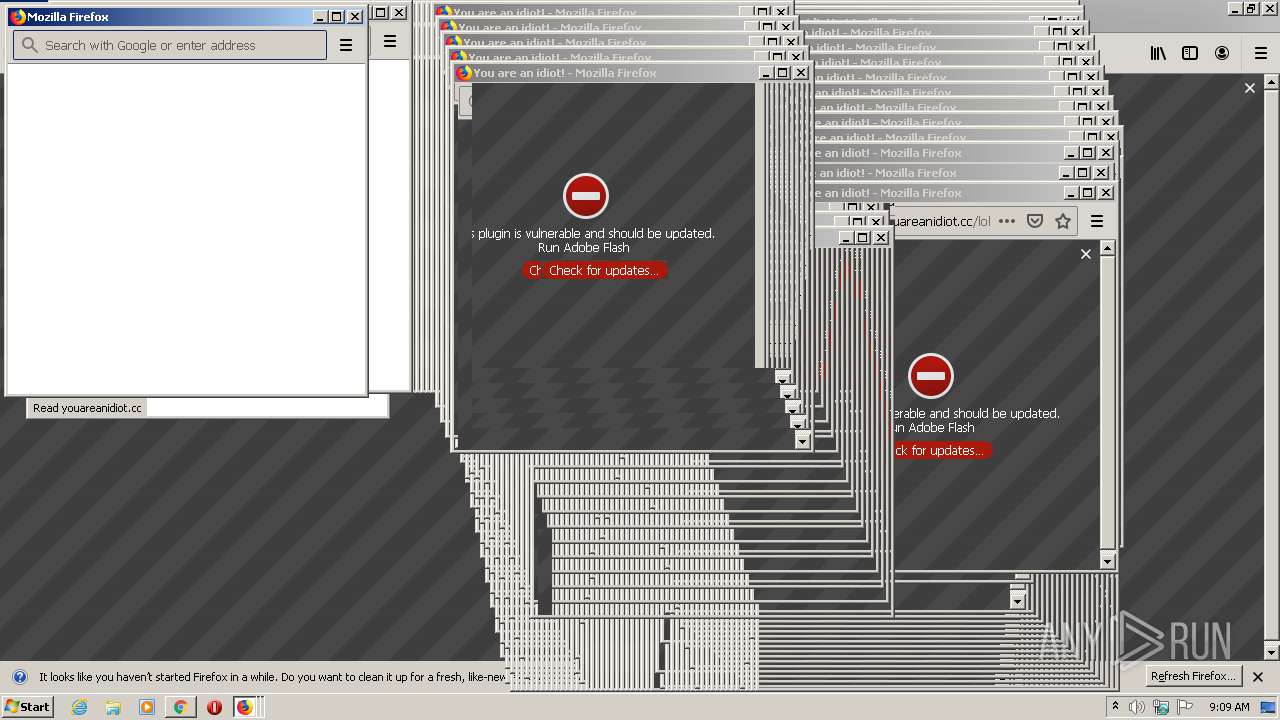
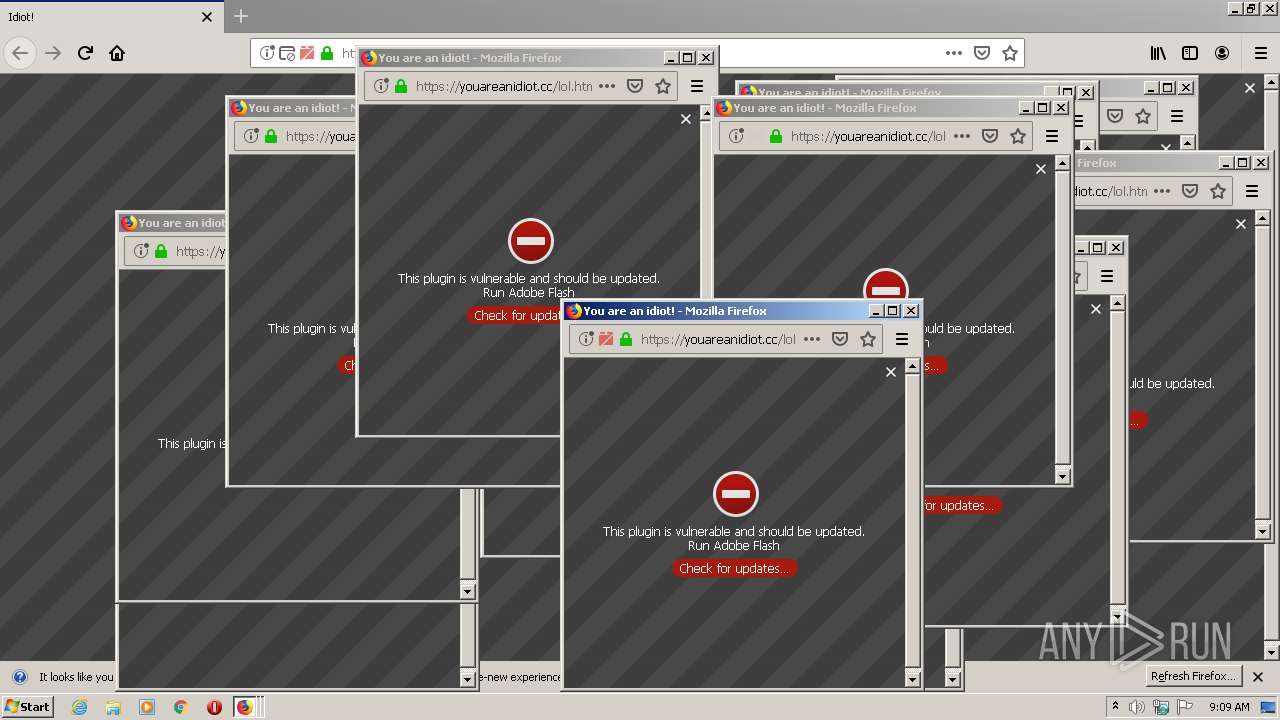
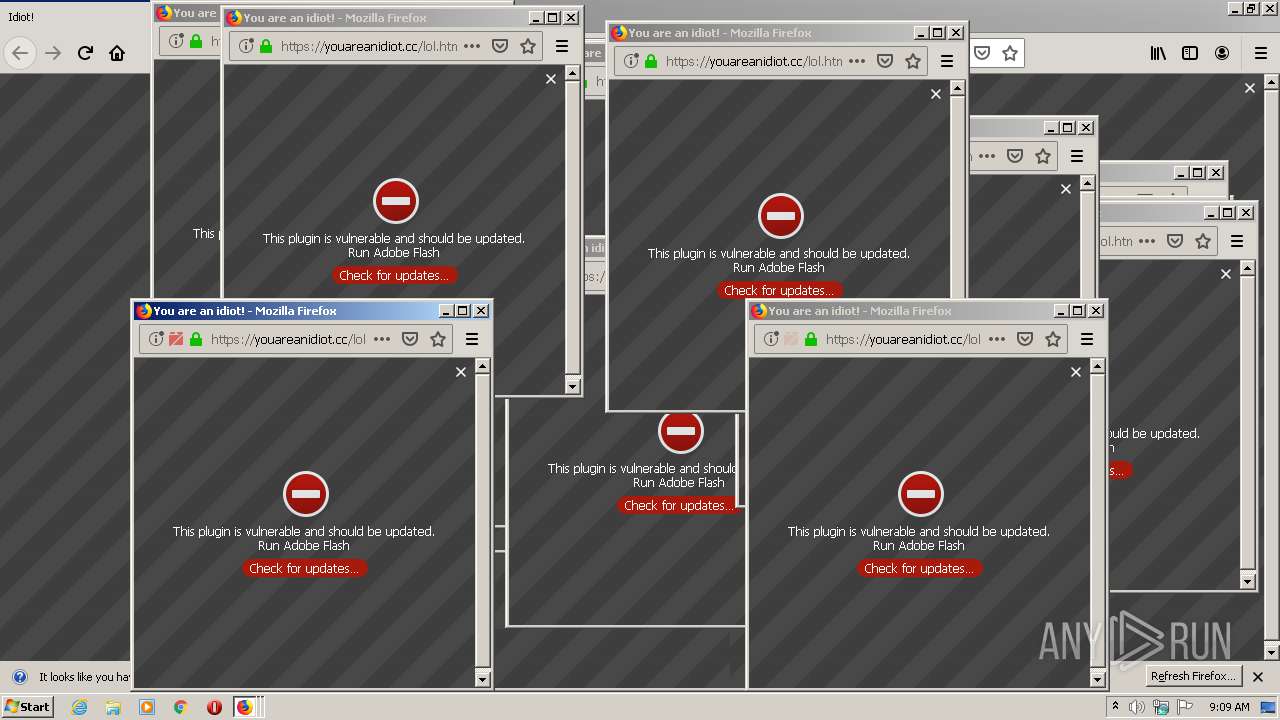
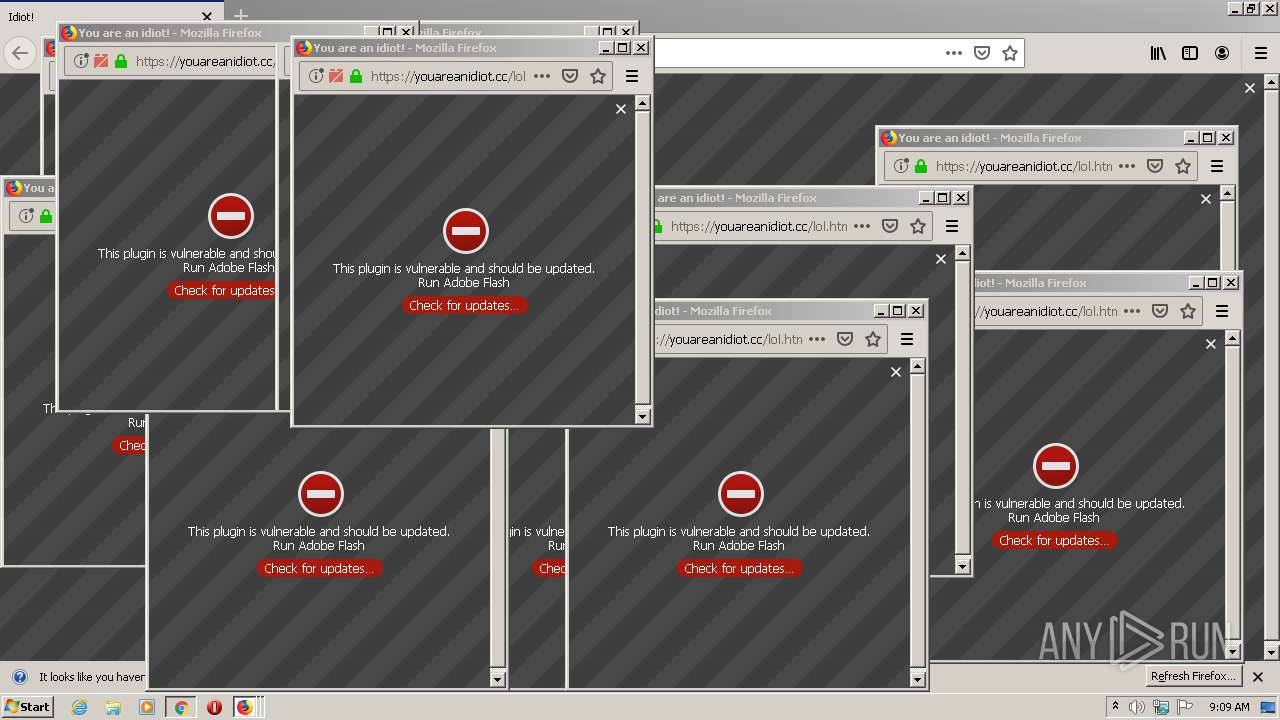
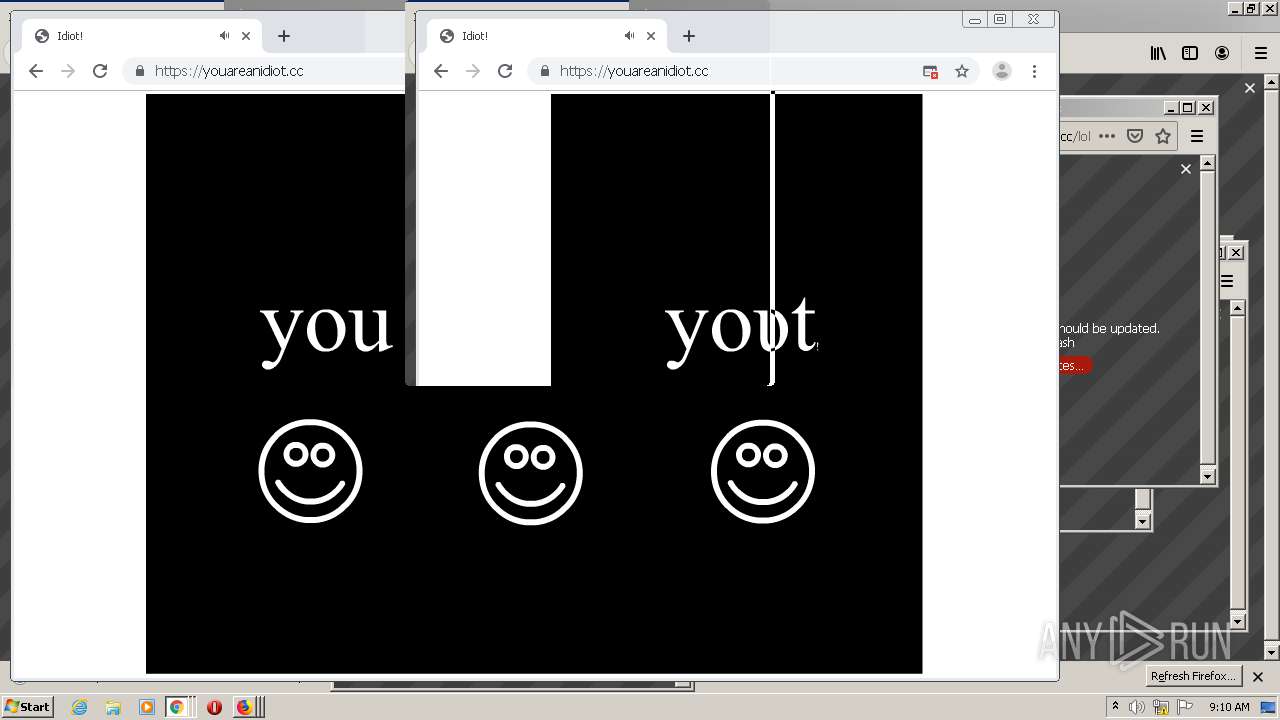
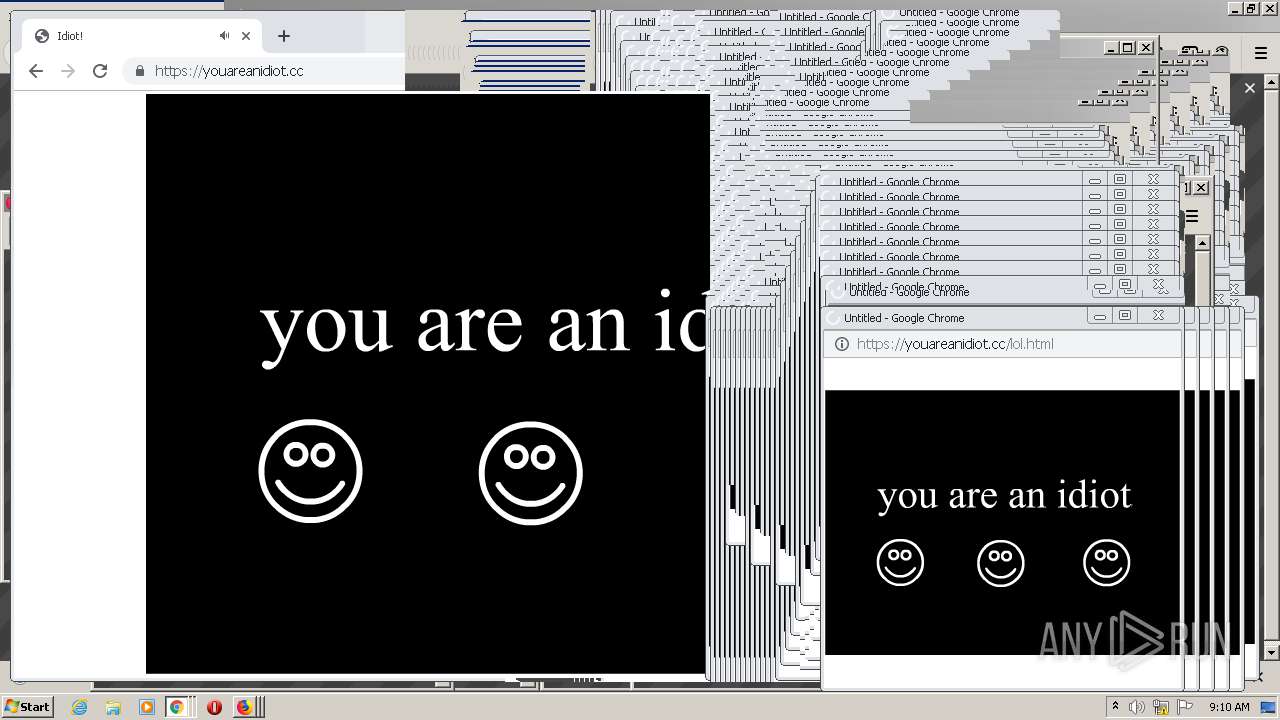
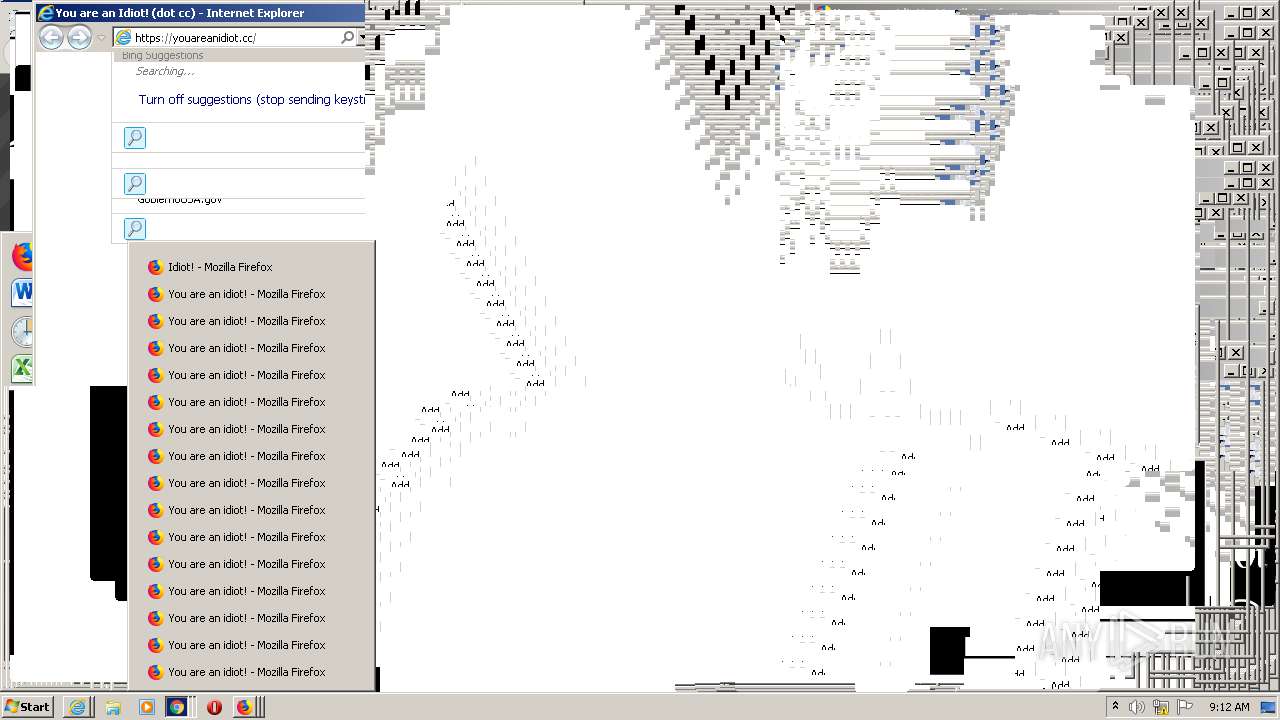
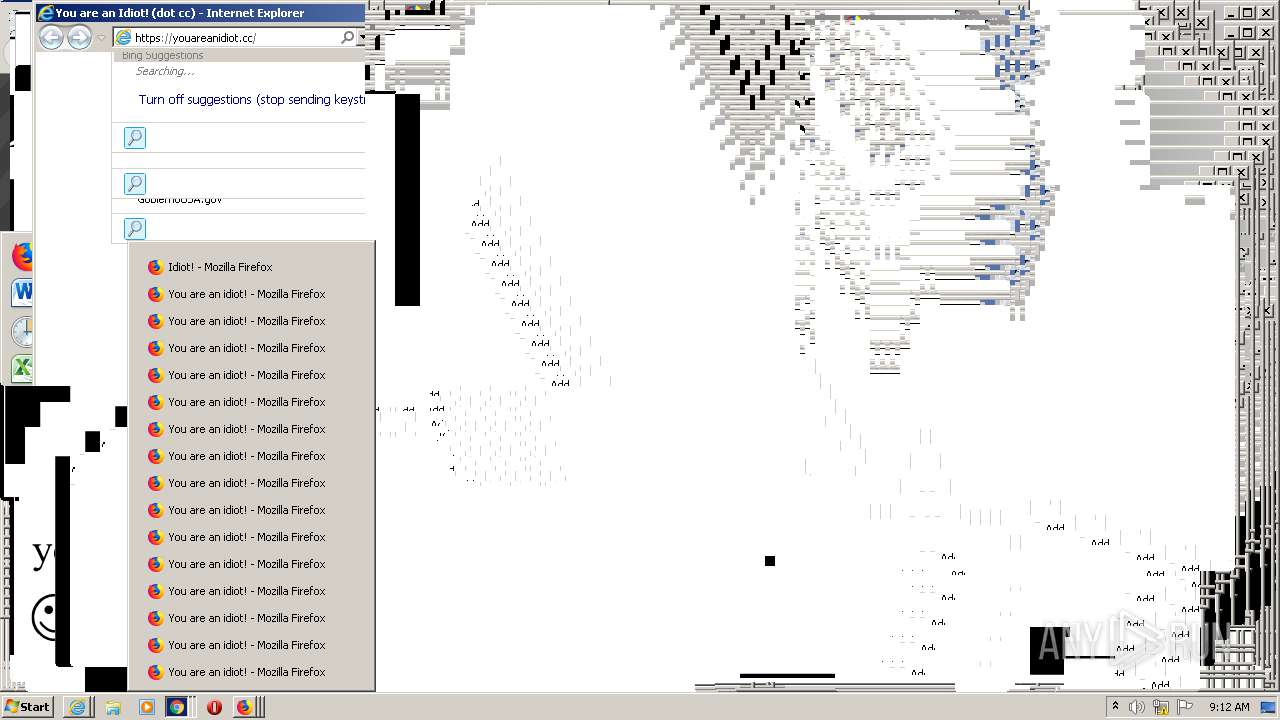
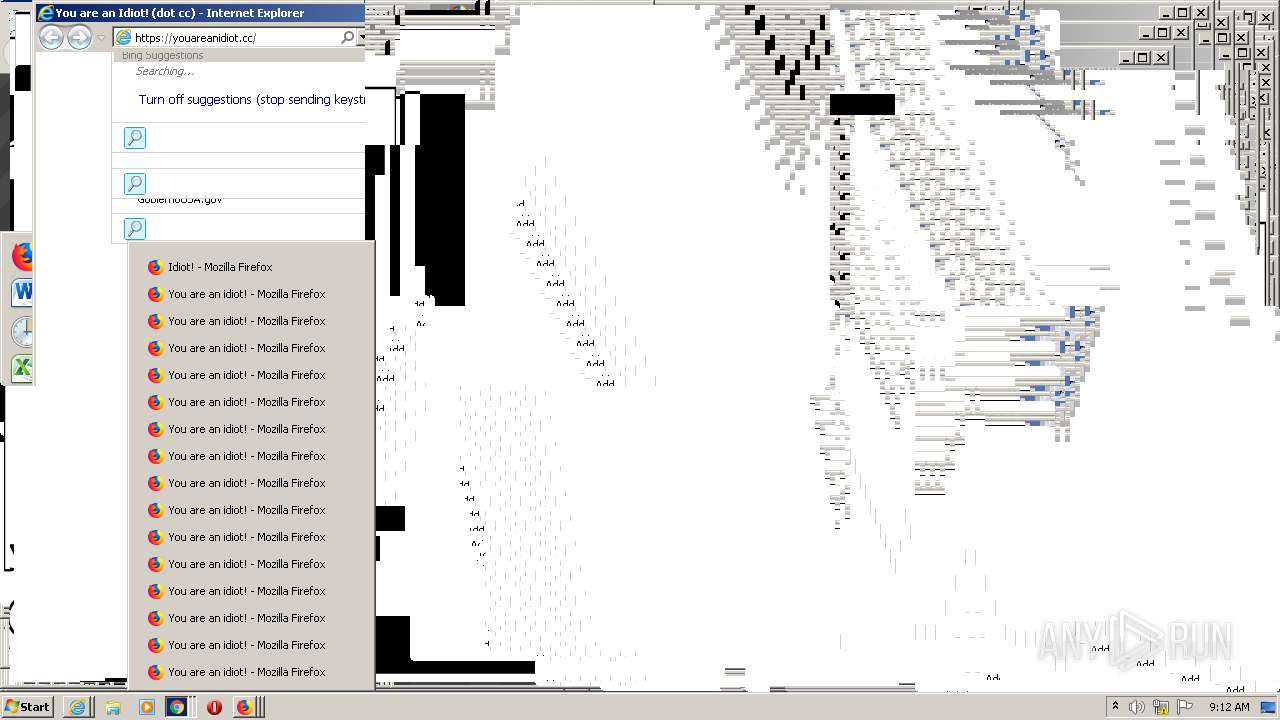
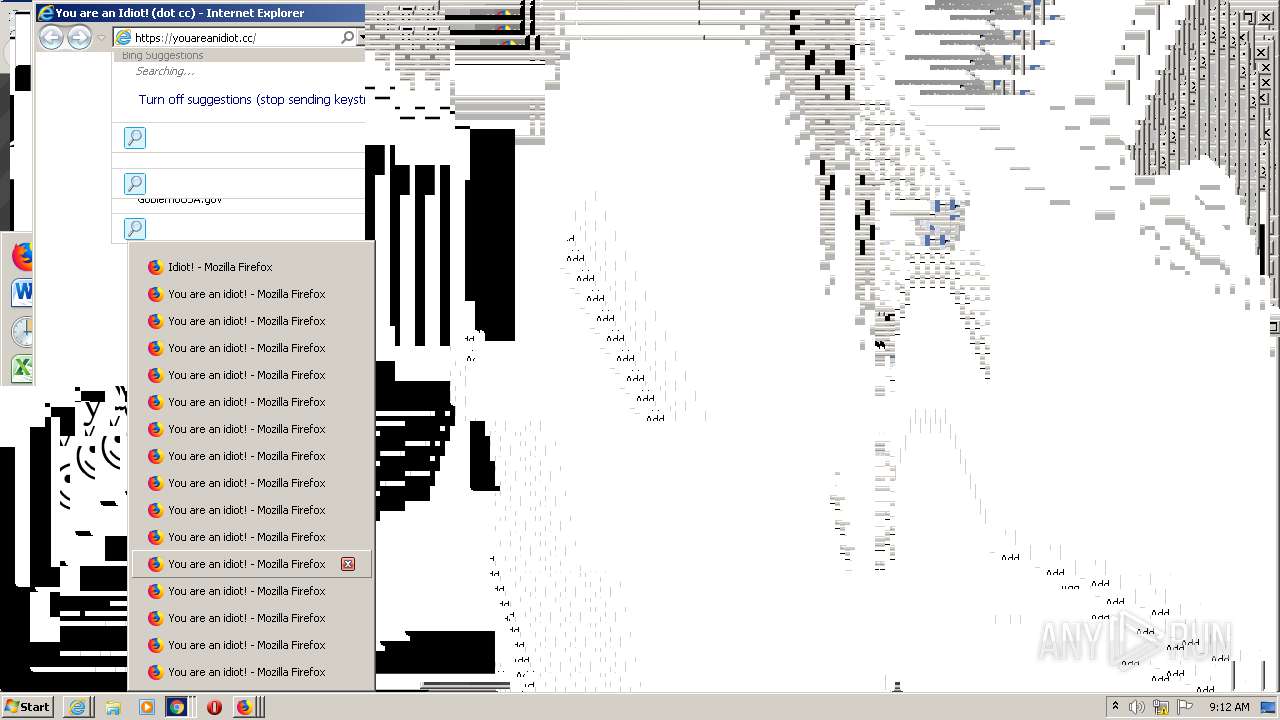
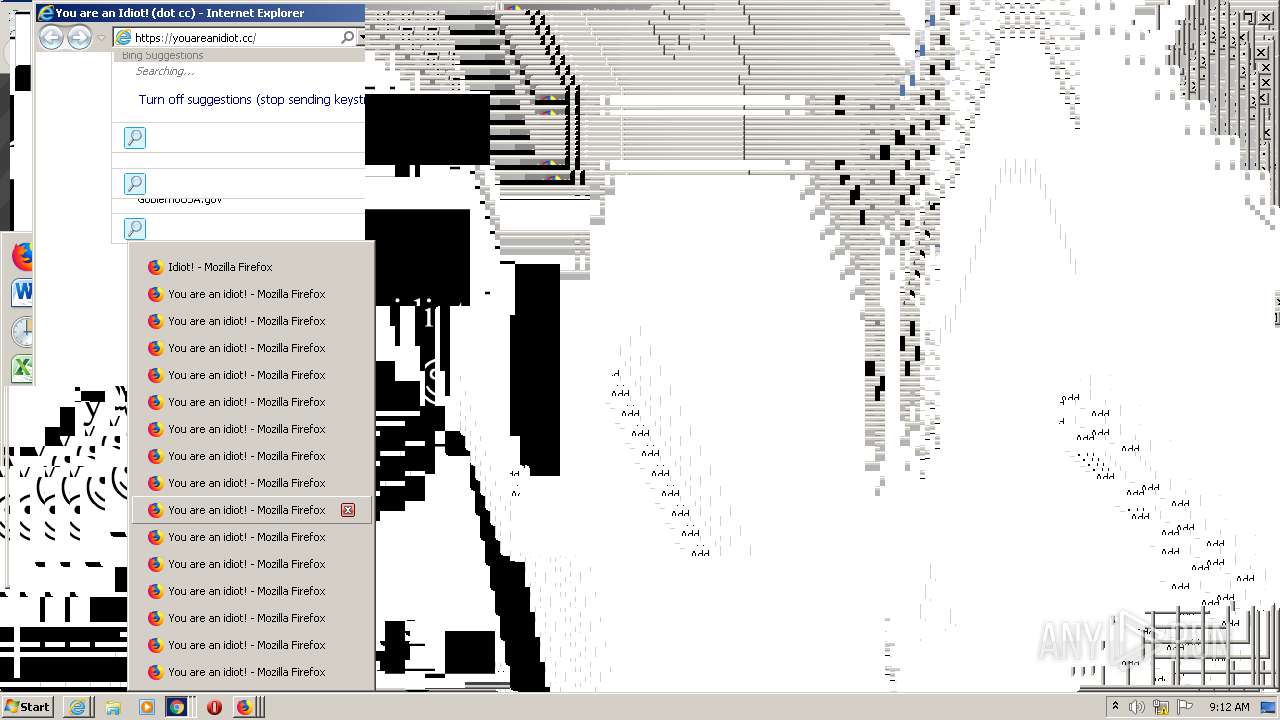
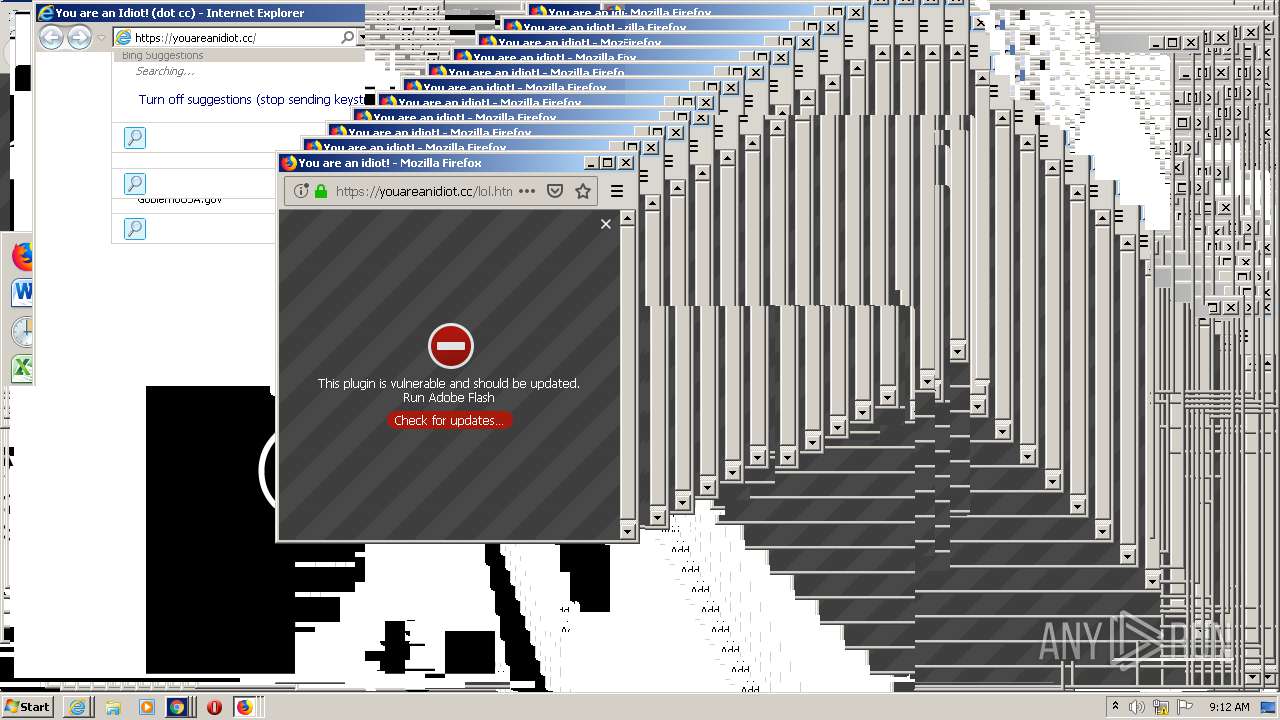
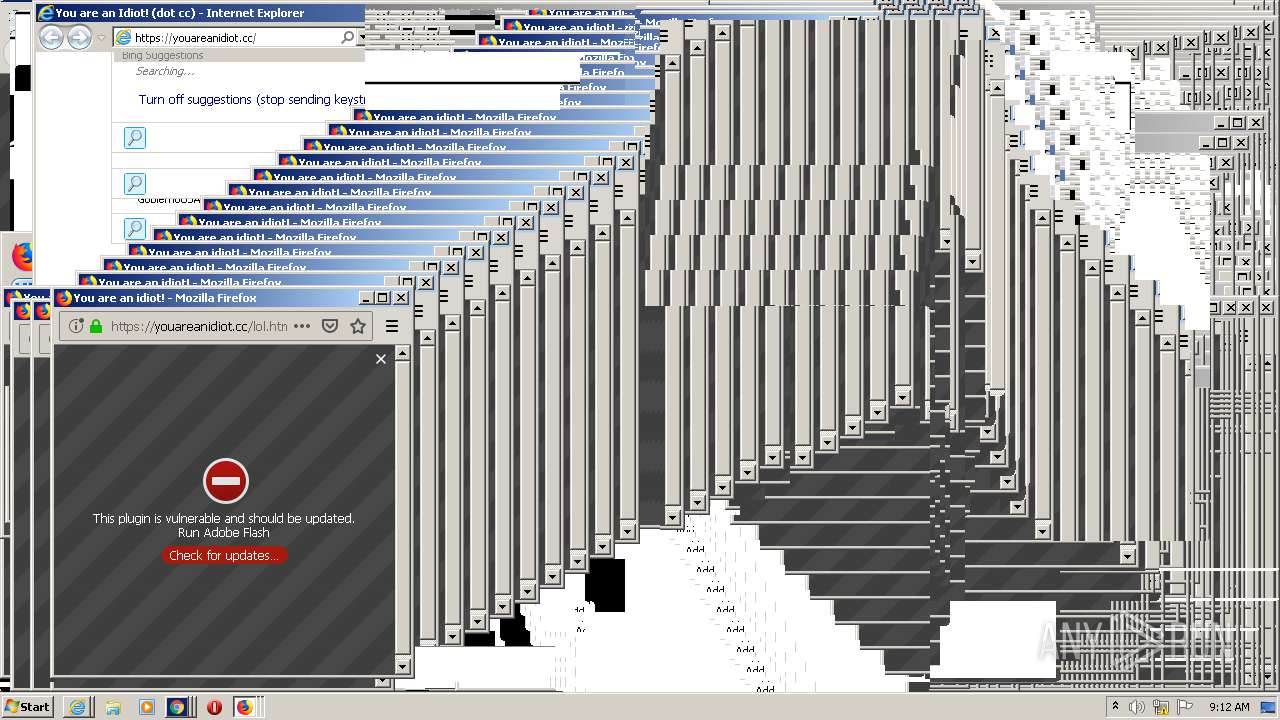
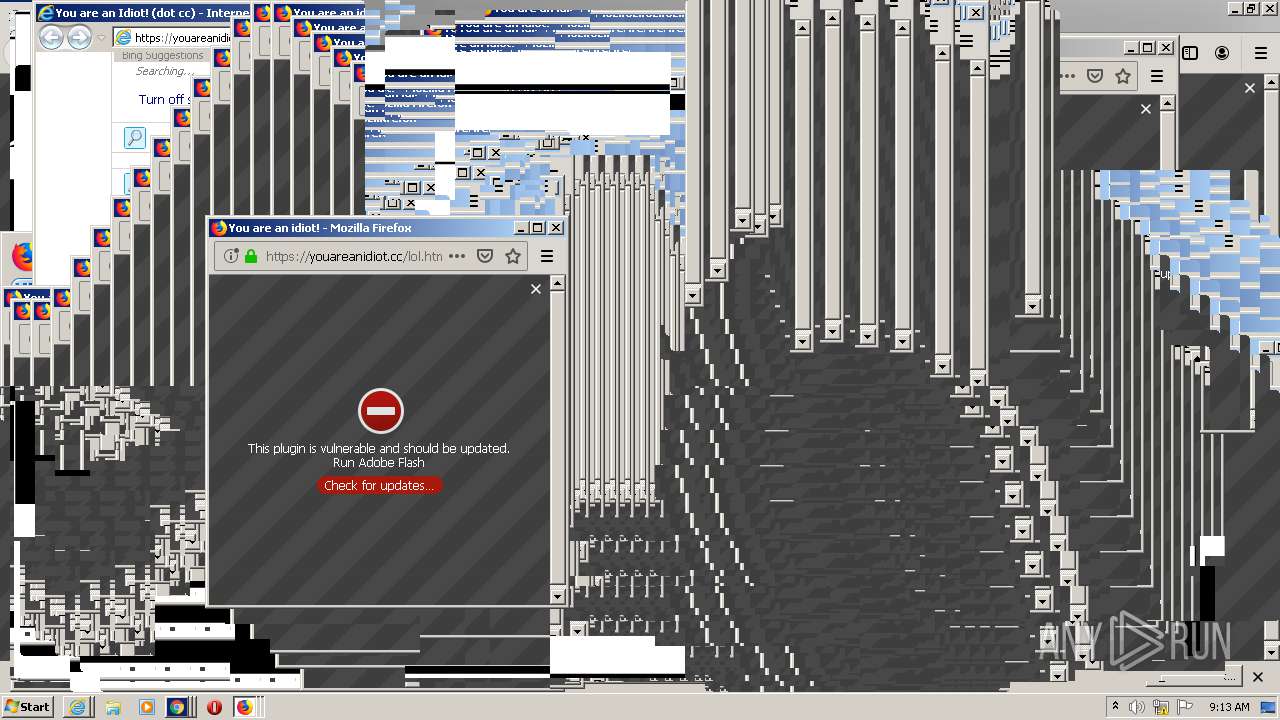
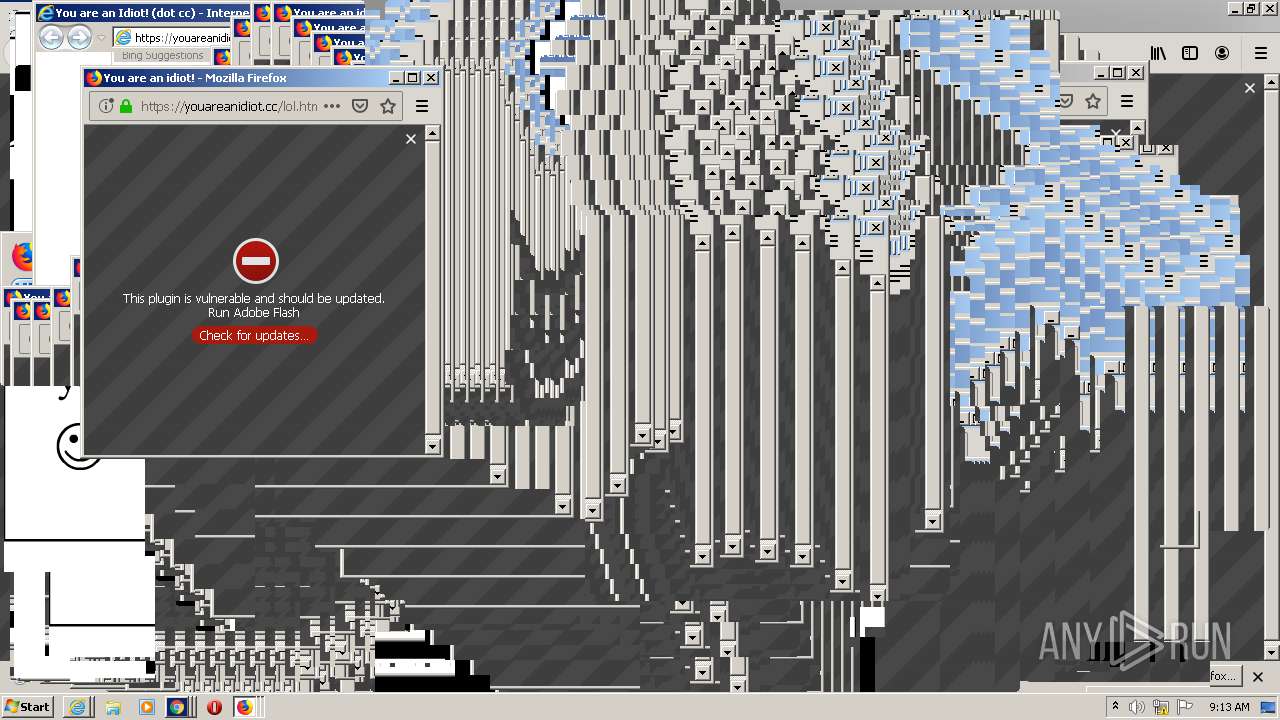
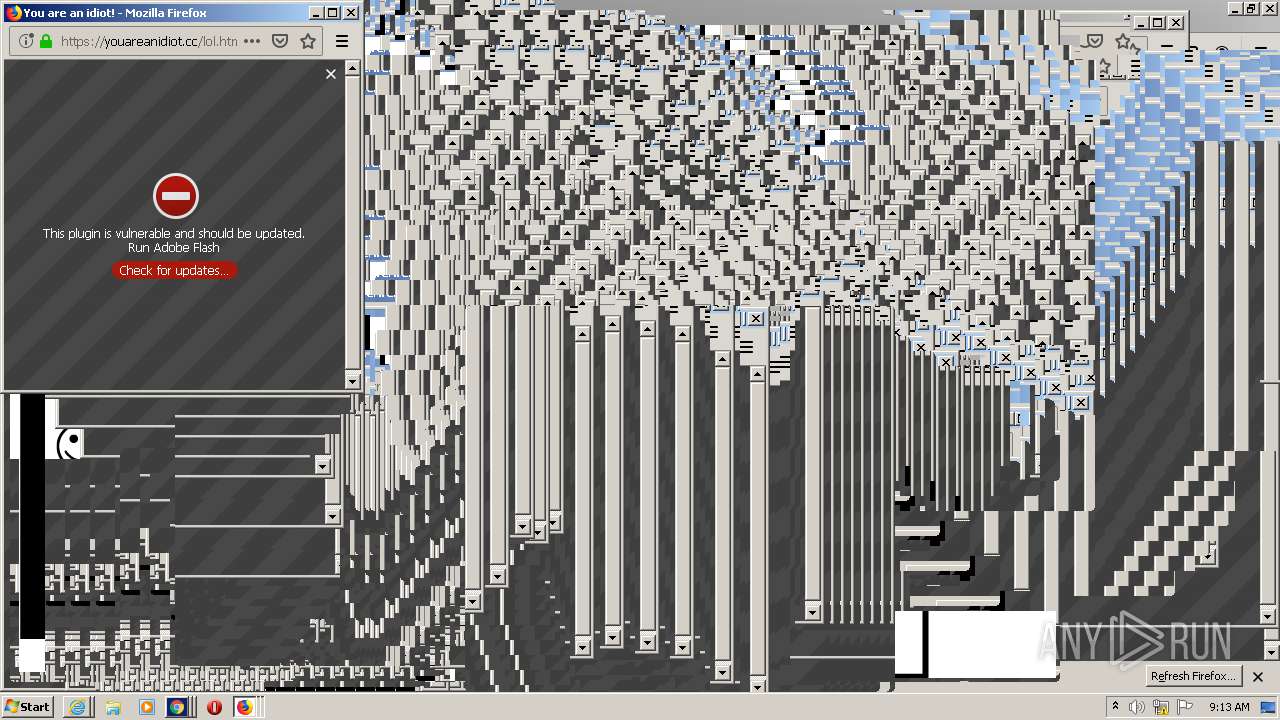
Application launched itself
- firefox.exe (PID: 2640)
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 2116)
- chrome.exe (PID: 1540)
Reads the hosts file
- chrome.exe (PID: 1088)
- chrome.exe (PID: 1540)
Manual execution by user
- chrome.exe (PID: 1540)
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 1820)
Reads Internet Cache Settings
- firefox.exe (PID: 2640)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 2320)
Reads CPU info
- firefox.exe (PID: 2640)
Changes internet zones settings
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 2116)
Creates files in the user directory
- firefox.exe (PID: 2640)
- iexplore.exe (PID: 2244)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4160)
Reads internet explorer settings
- iexplore.exe (PID: 2320)
- iexplore.exe (PID: 2244)
Reads settings of System Certificates
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 1820)
- chrome.exe (PID: 1088)
- iexplore.exe (PID: 2116)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 2116)
Changes settings of System certificates
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 2116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
46
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,17843242788190352914,4017634747251321535,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9597146917265402642 --mojo-platform-channel-handle=3068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2640.13.1417525532\1757940700" -childID 2 -isForBrowser -prefsHandle 2892 -prefMapHandle 2916 -prefsLen 5997 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2640 "\\.\pipe\gecko-crash-server-pipe.2640" 2928 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2640.20.1499660356\719925021" -childID 3 -isForBrowser -prefsHandle 3548 -prefMapHandle 3544 -prefsLen 7130 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2640 "\\.\pipe\gecko-crash-server-pipe.2640" 3556 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,17843242788190352914,4017634747251321535,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15828671799077641927 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2640.0.577537964\196218329" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2640 "\\.\pipe\gecko-crash-server-pipe.2640" 1176 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,17843242788190352914,4017634747251321535,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1453019210536070421 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=988,17843242788190352914,4017634747251321535,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=9594145076822452508 --mojo-platform-channel-handle=4180 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,17843242788190352914,4017634747251321535,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1573249898279154770 --mojo-platform-channel-handle=3004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,17843242788190352914,4017634747251321535,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17560139113165850339 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
10 213
Read events
2 570
Write events
5 187
Delete events
2 456
Modification events
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 9CF4E00300000000 | |||
| (PID) Process: | (2060) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 9BF4E00300000000 | |||
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
0
Suspicious files
144
Text files
288
Unknown types
121
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:DE9496ACA551ADE408EF6466A11833A1 | SHA256:8F9C7FDB3E0BC01024E43A8E242468FC4DD4F74C725E32A883571635203DC10A | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:5027177F513CDAE07DB2330E1DED5934 | SHA256:0C53F16051E738287A4612F68E296238087627E594CFD6DDFA1FECC2E998328B | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:6D378E0D40B6EACA22C8BCE899A1C5C1 | SHA256:ADA2467B2477ACEFF837AC7820C435AD1EBBE844B2DA31C7AB9AE8D010C7A639 | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:354459382F30B8994109C88659DFA1F3 | SHA256:E3E8E2B7E7EECA231620D83C70FA5A926E8B9CE74C51F595F71191DC0B50527E | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:4A1220FC03E11726F09E9981834345DB | SHA256:6AE7FC0FDBE217104F4034BF6A580A461106B50309ABCCFF6E309124DCA5EF39 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
81
DNS requests
92
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2640 | firefox.exe | POST | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
2640 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2640 | firefox.exe | GET | 200 | 2.16.107.8:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
1088 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
1088 | chrome.exe | GET | 200 | 173.194.137.72:80 | http://r3---sn-aigzrn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.217.117.161&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1592294892&mv=m&mvi=2&pl=27&shardbypass=yes | US | crx | 823 Kb | whitelisted |
2244 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=about%3Ablany&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2244 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=abou&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2244 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=youar&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2640 | firefox.exe | GET | 200 | 2.16.107.8:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2244 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=about%3Ablanyou&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | firefox.exe | 2.16.107.8:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
2640 | firefox.exe | 52.26.114.88:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2640 | firefox.exe | 104.28.24.163:443 | youareanidiot.cc | Cloudflare Inc | US | malicious |
2640 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2640 | firefox.exe | 143.204.202.128:443 | snippets.cdn.mozilla.net | — | US | malicious |
2640 | firefox.exe | 2.16.107.25:443 | shavar.services.mozilla.com | Akamai International B.V. | — | malicious |
2640 | firefox.exe | 13.224.198.117:443 | tracking-protection.cdn.mozilla.net | — | US | unknown |
1088 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1088 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
1088 | chrome.exe | 216.58.212.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
youareanidiot.cc |
| malicious |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |