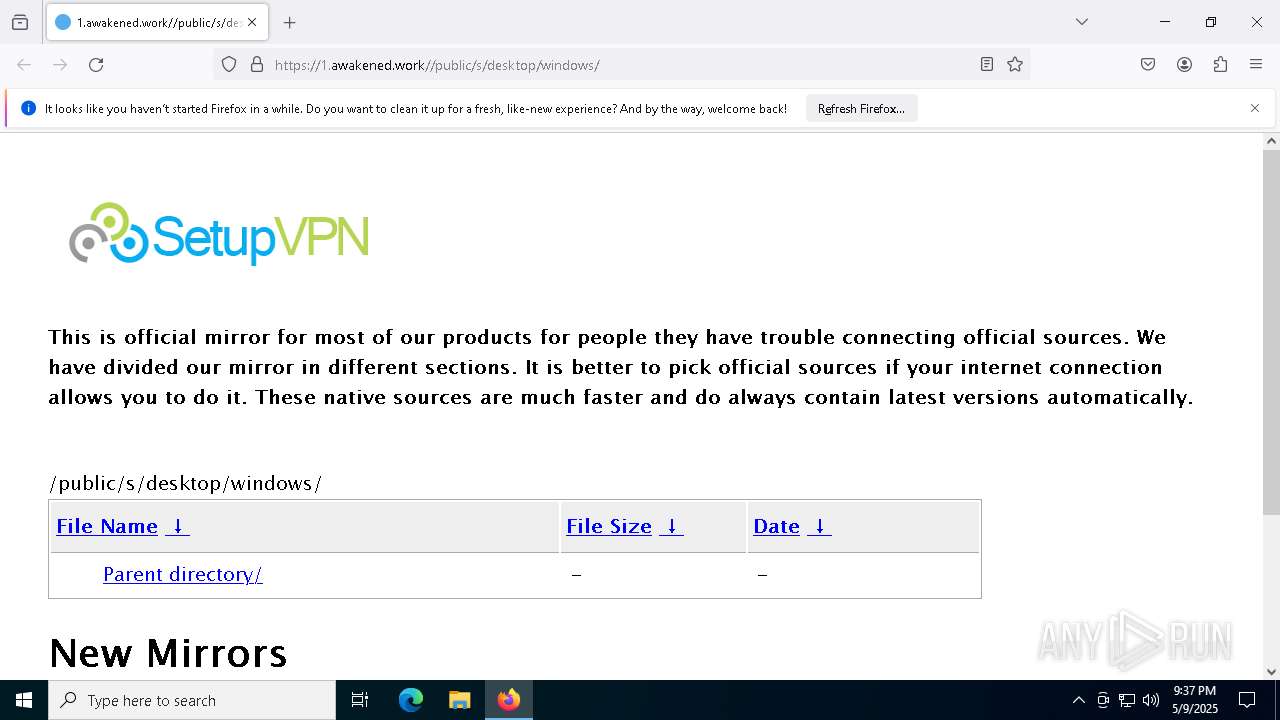
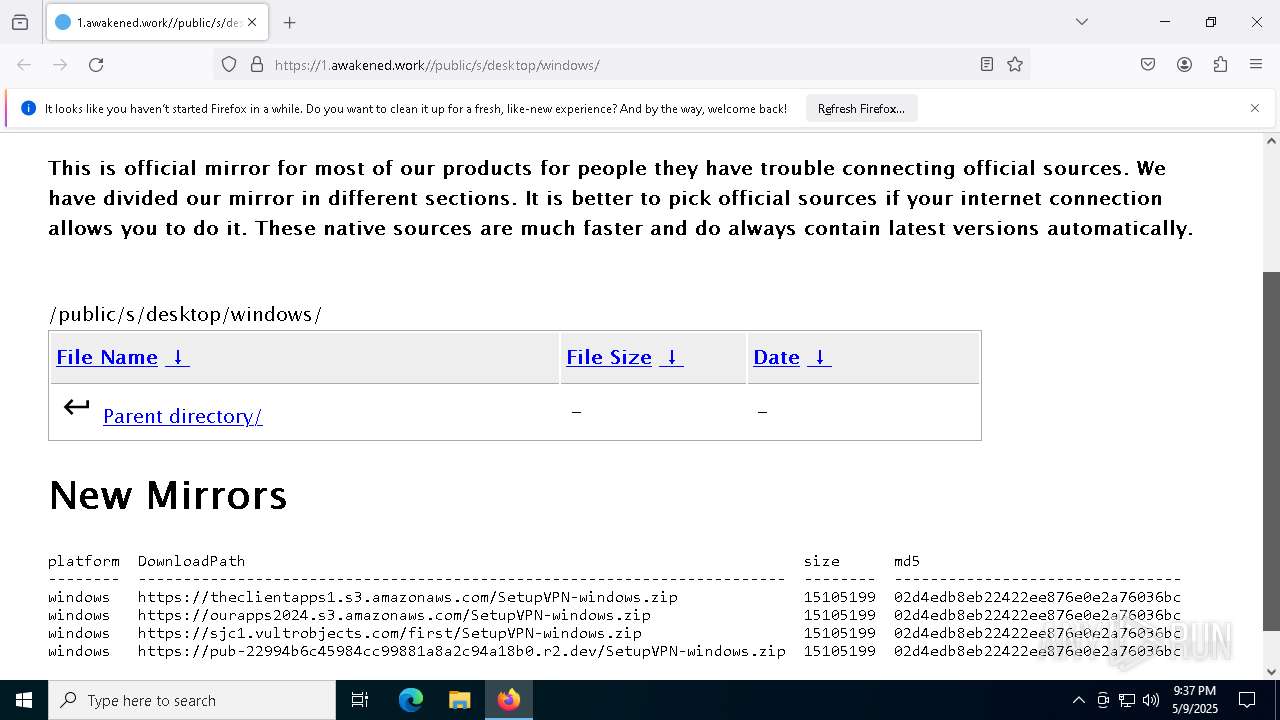
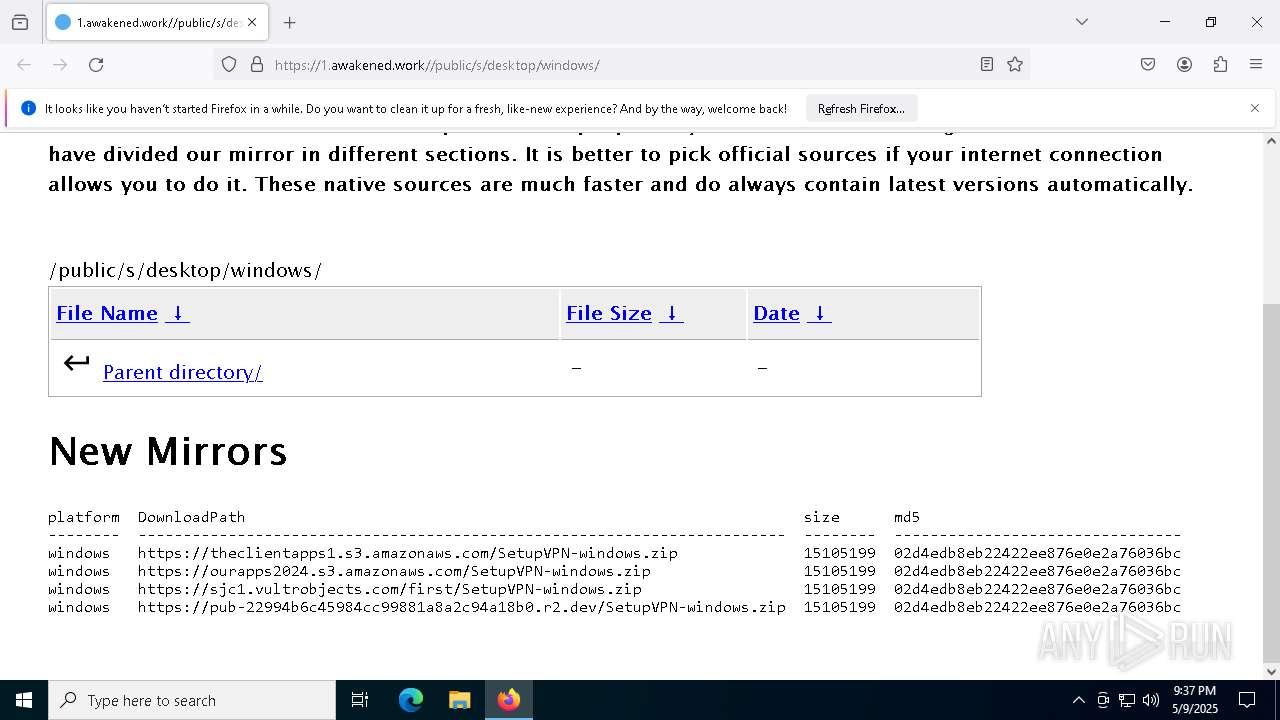
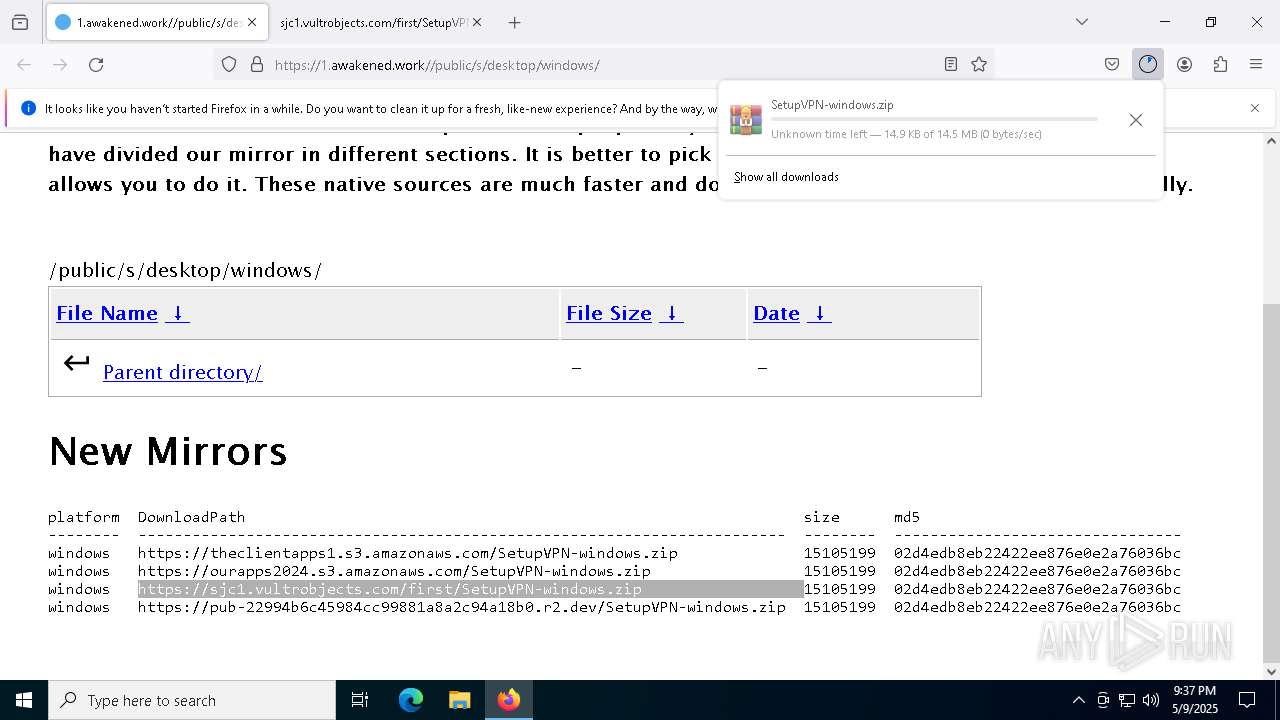
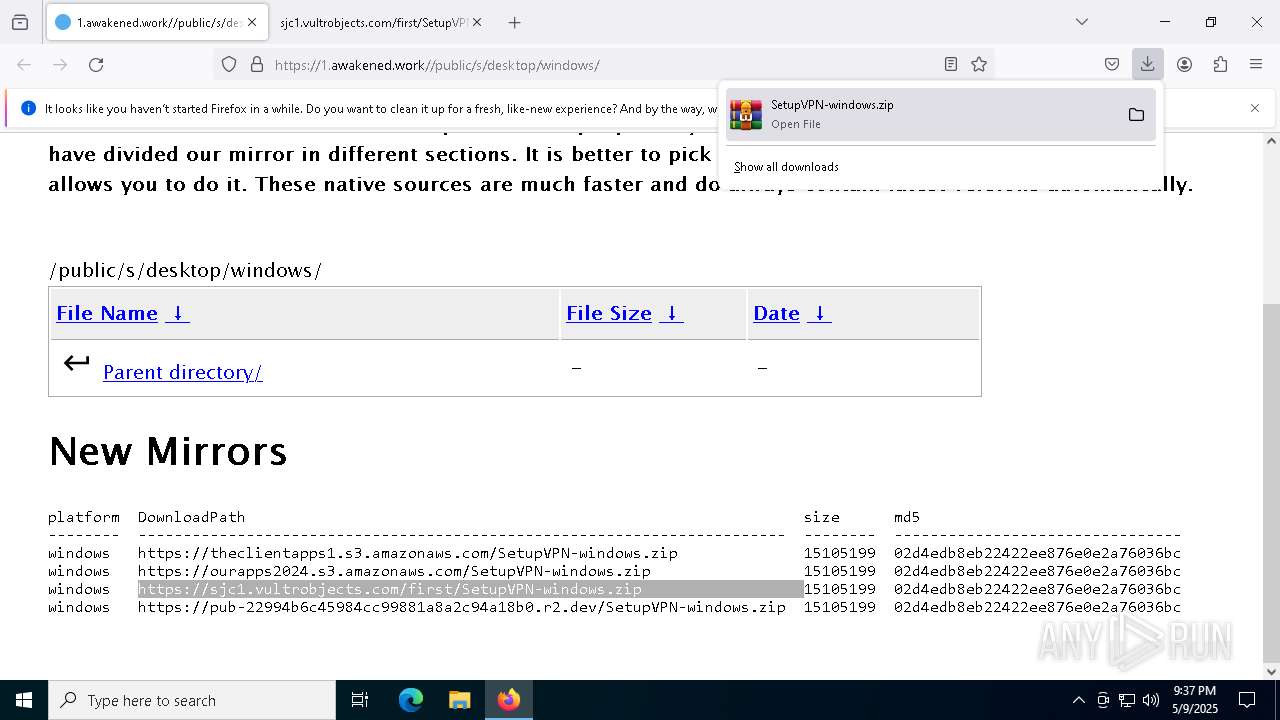
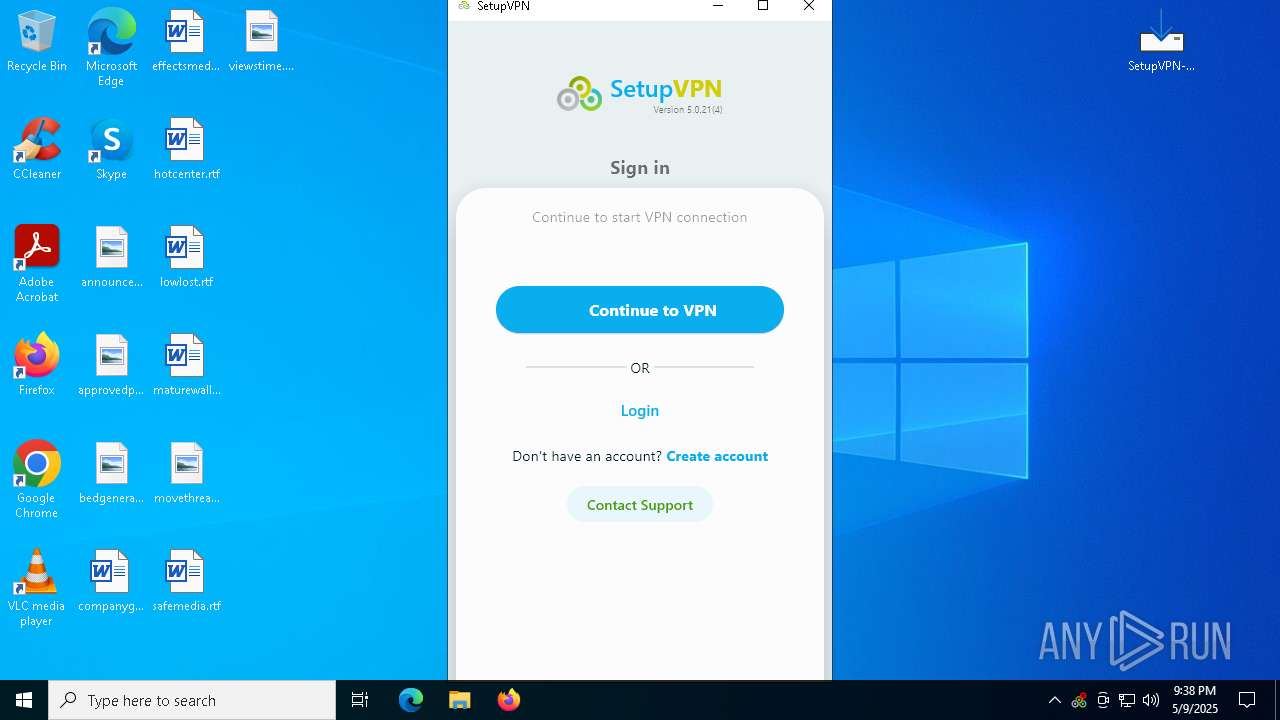
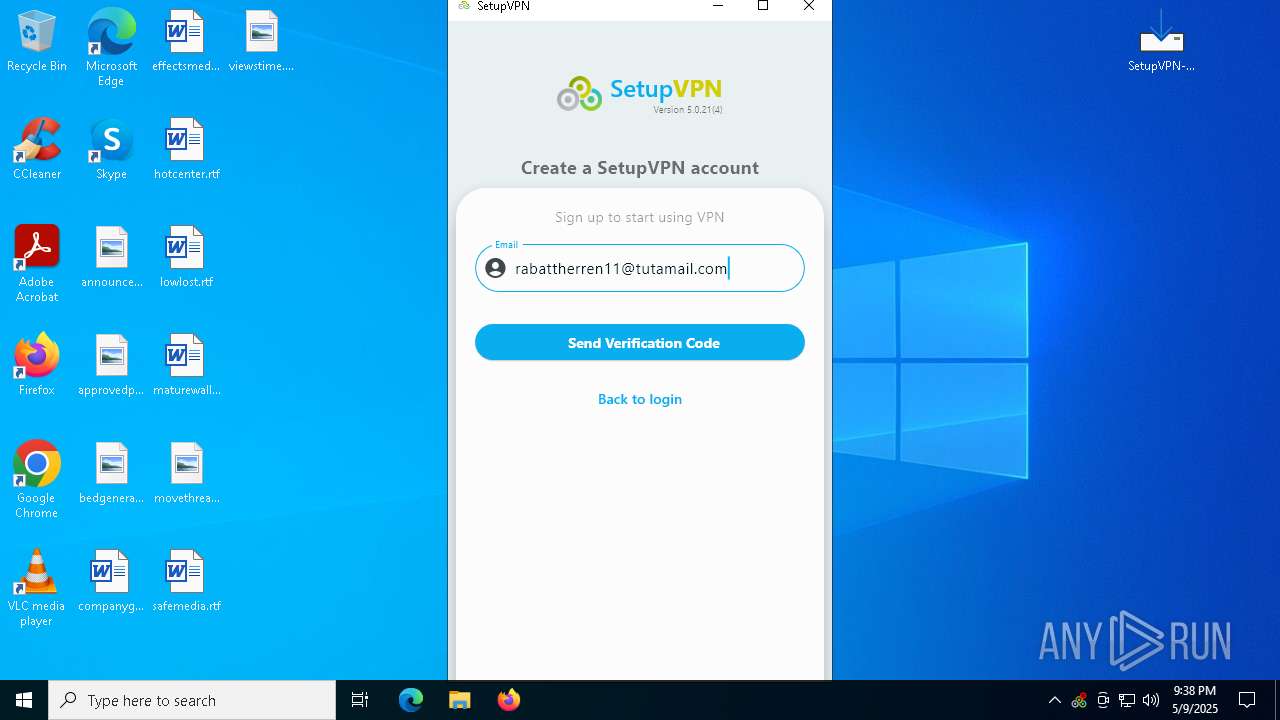
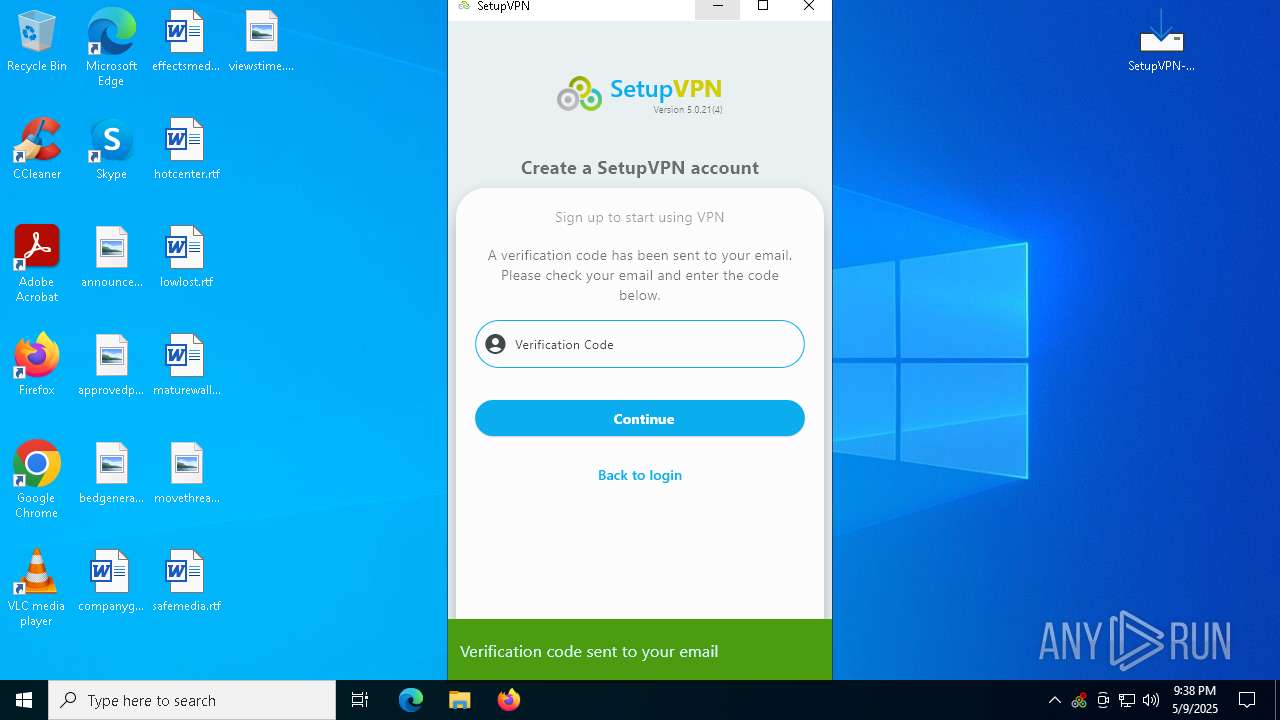
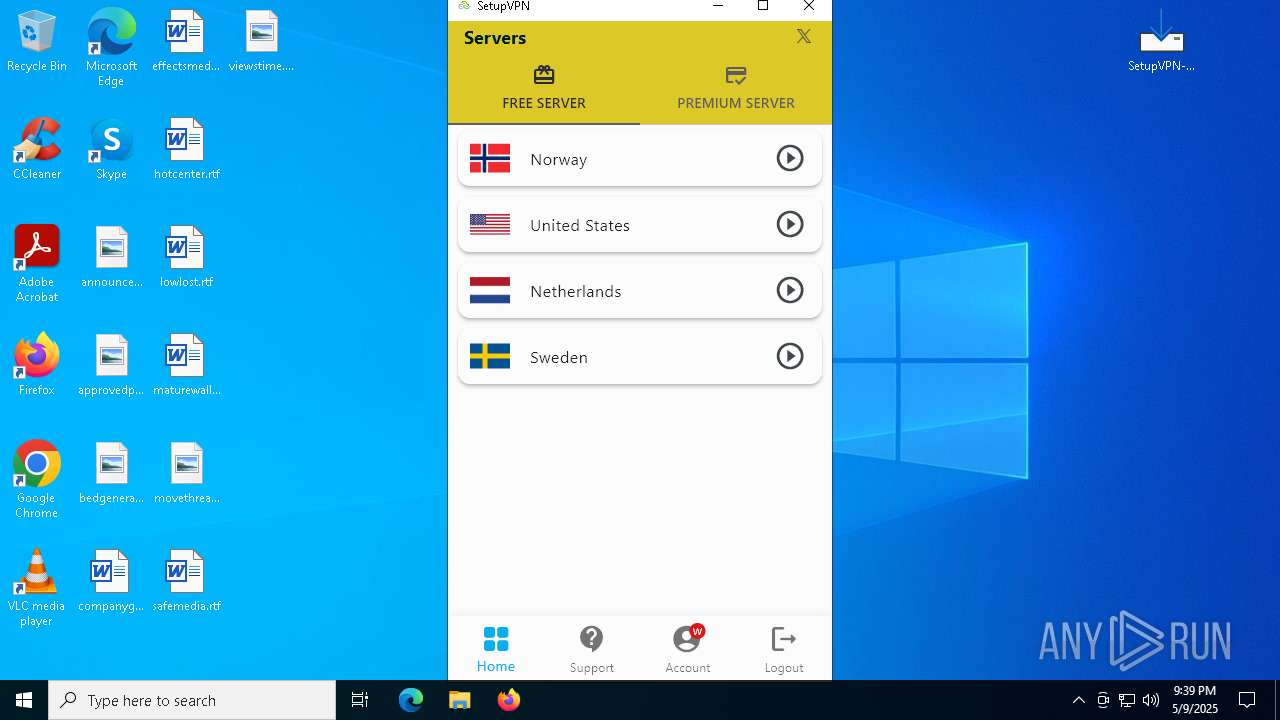
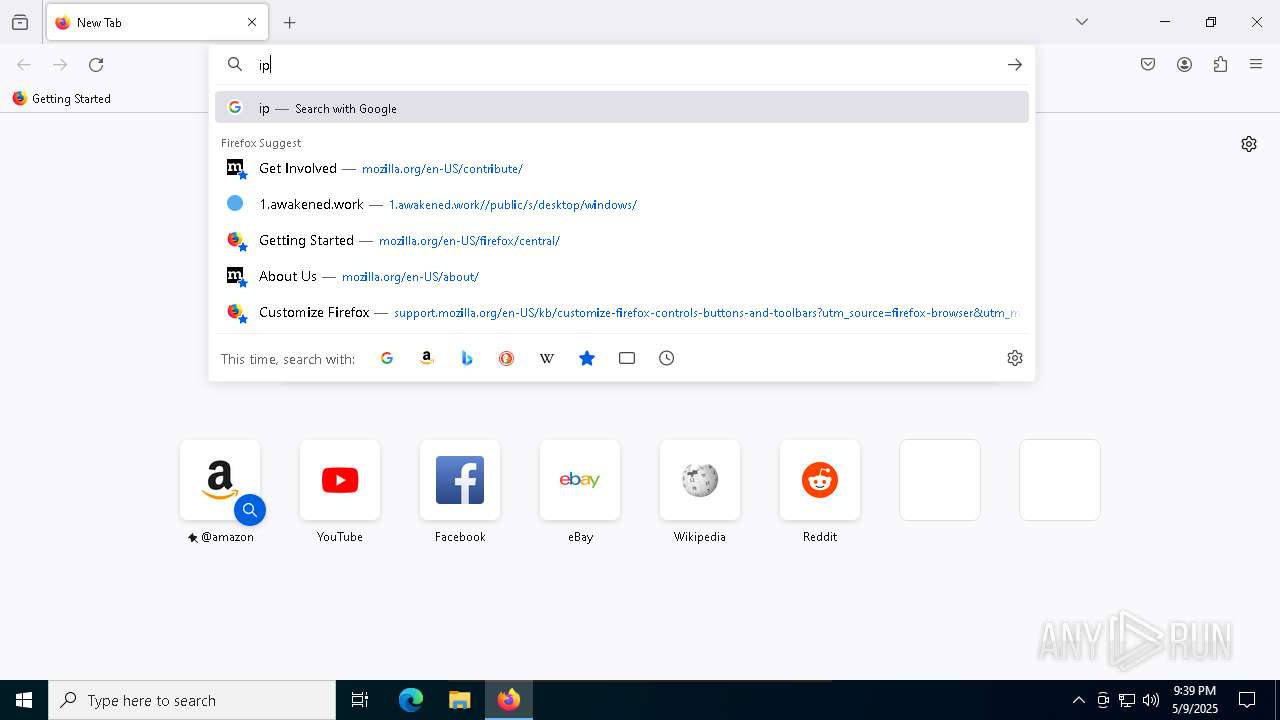
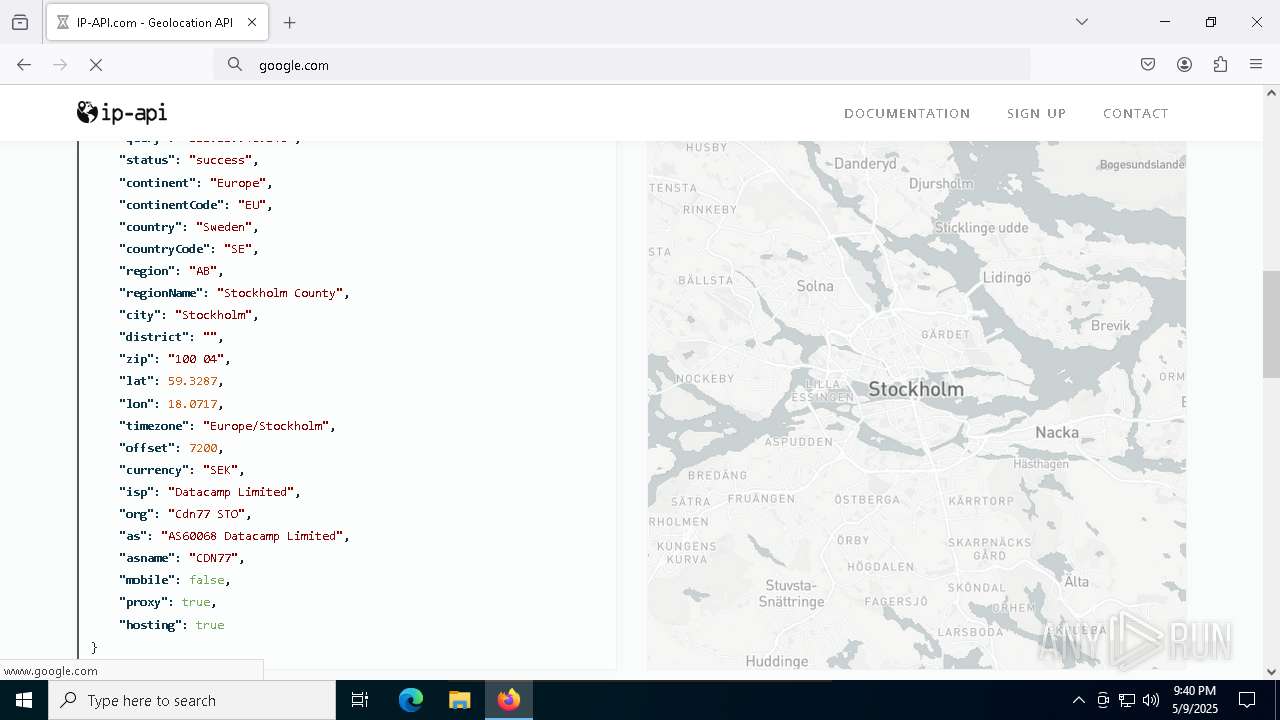
| URL: | https://1.awakened.work//public/s/desktop/windows/ |
| Full analysis: | https://app.any.run/tasks/140a161d-505f-42b9-a1cf-c6ae74eb7ec2 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2025, 21:37:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 51EBF3C518A0D528B1258A440DF5DE23 |
| SHA1: | BF30E8C059D6658FC3CFBAAE89850BEB5000B436 |
| SHA256: | A021930CE44D1F6672F7E05D5EA2238A7EF0218FB189448EA7593674A96271DE |
| SSDEEP: | 3:N8gESnA0/XNCIKVKSM9:2gU01CIOM |
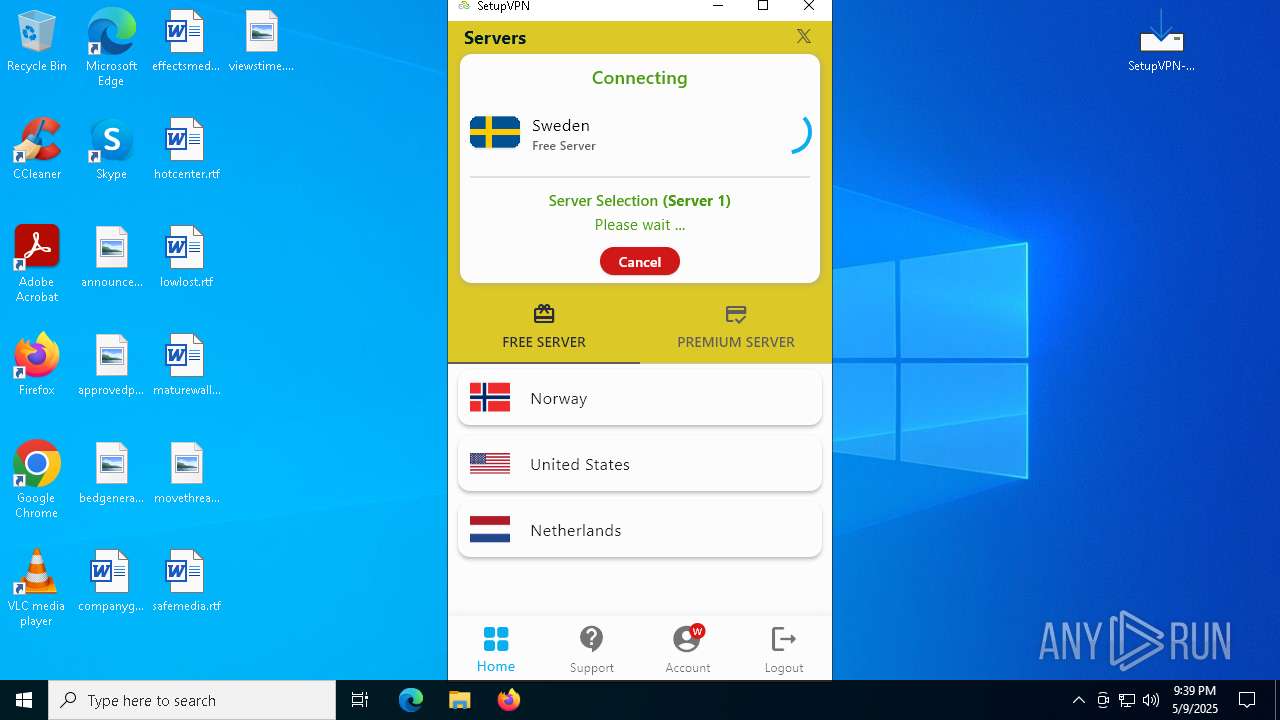
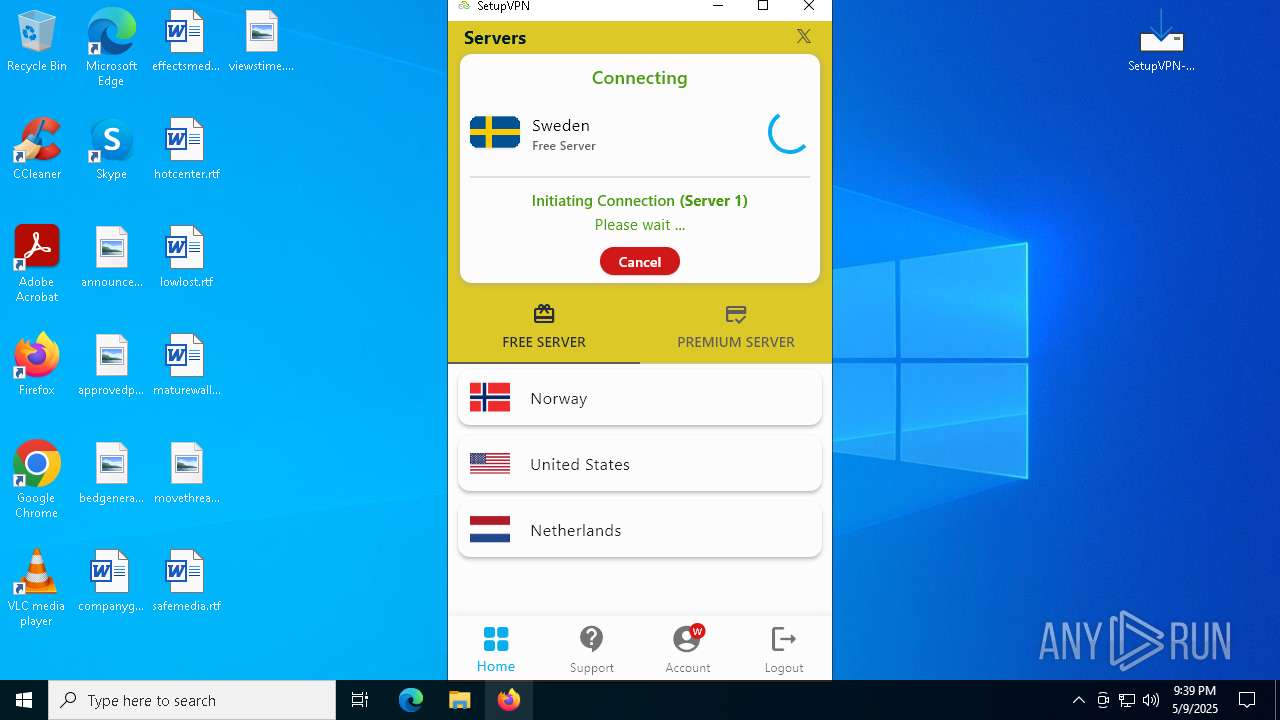
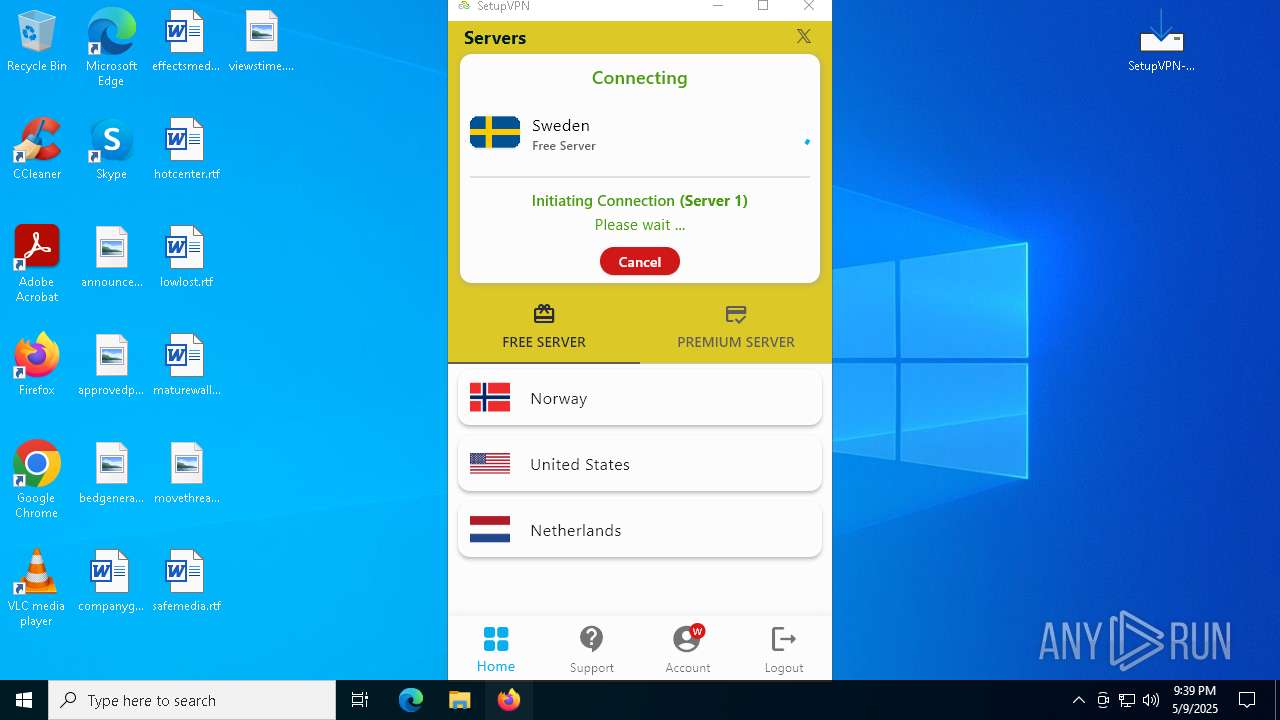
MALICIOUS
Executing a file with an untrusted certificate
- SetupVPN-5.0.21+4.exe (PID: 7996)
- SetupVPNService.exe (PID: 4220)
- SetupVPN.exe (PID: 7592)
- tun2socks.exe (PID: 684)
- smartdnsblock_sv.exe (PID: 7896)
- SetupVPN-5.0.21+4.exe (PID: 3180)
- tun2socks.exe (PID: 7620)
- smartdnsblock_sv.exe (PID: 7256)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
Starts NET.EXE for service management
- net.exe (PID: 780)
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- net.exe (PID: 7608)
- cmd.exe (PID: 7872)
- net.exe (PID: 7404)
Uses Task Scheduler to run other applications
- SetupVPN-5.0.21+4.tmp (PID: 5508)
SUSPICIOUS
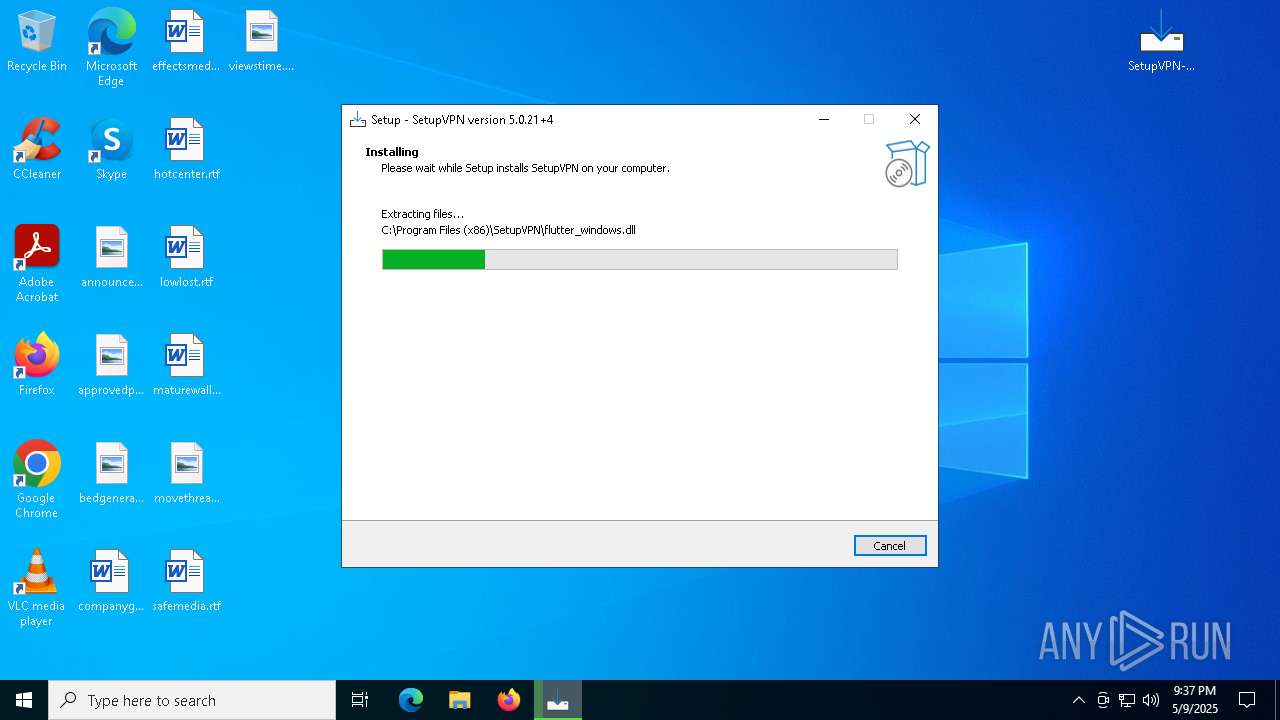
Executable content was dropped or overwritten
- SetupVPN-5.0.21+4.exe (PID: 7996)
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- tapinstall.exe (PID: 5400)
- drvinst.exe (PID: 7348)
- drvinst.exe (PID: 4896)
- SetupVPN-5.0.21+4.exe (PID: 3180)
Reads security settings of Internet Explorer
- SetupVPN-5.0.21+4.tmp (PID: 2152)
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- tapinstall.exe (PID: 5400)
Reads the Windows owner or organization settings
- SetupVPN-5.0.21+4.tmp (PID: 5508)
Uses TASKKILL.EXE to kill process
- SetupVPN-5.0.21+4.tmp (PID: 5508)
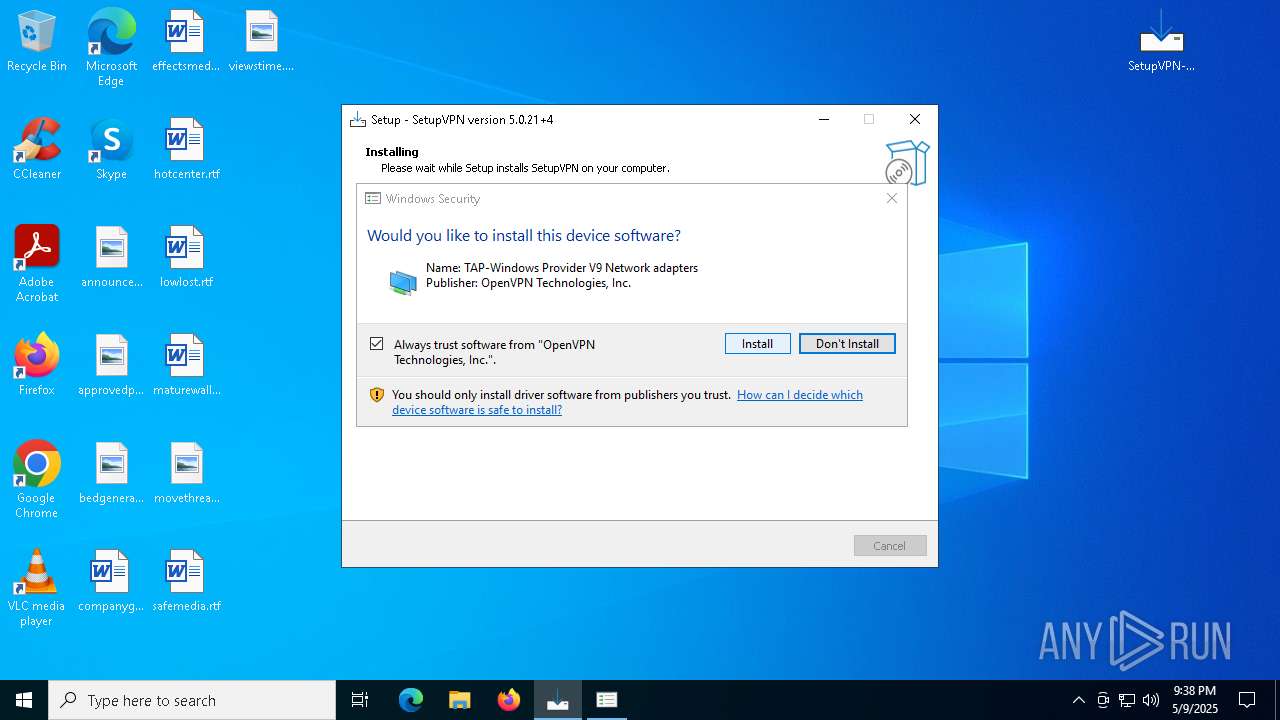
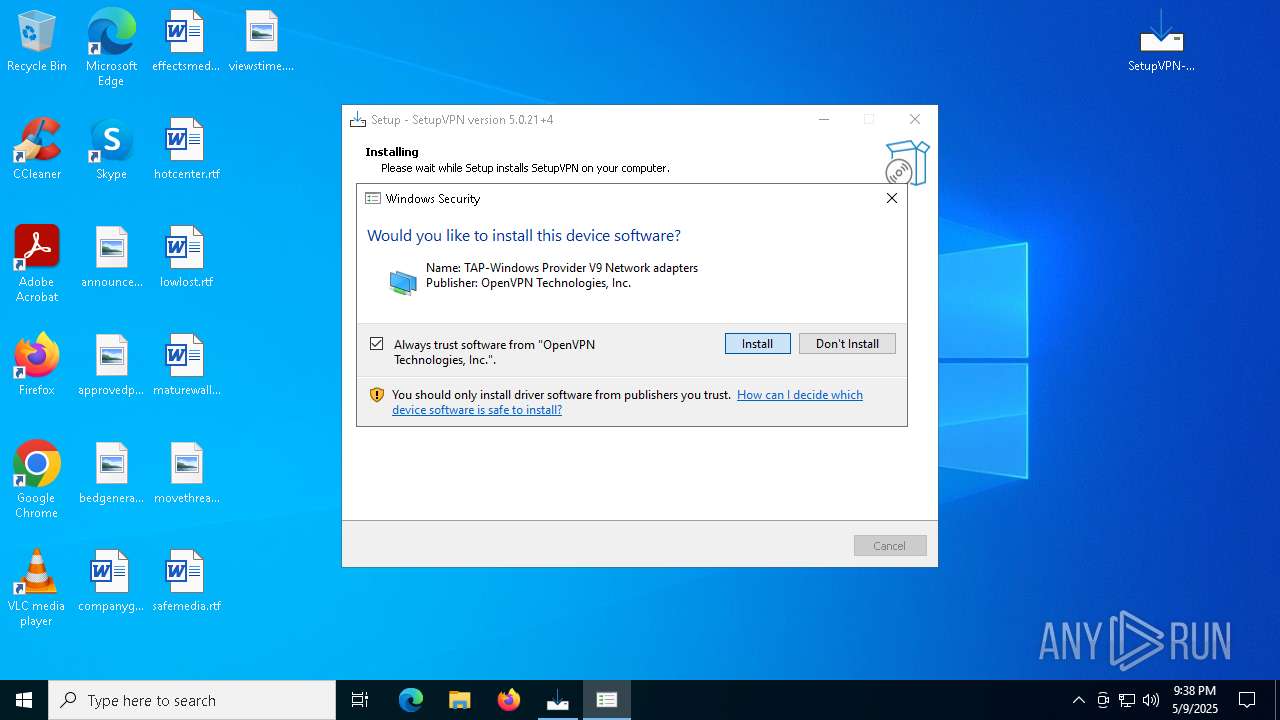
Drops a system driver (possible attempt to evade defenses)
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- tapinstall.exe (PID: 5400)
- drvinst.exe (PID: 7348)
- drvinst.exe (PID: 4896)
The process drops C-runtime libraries
- SetupVPN-5.0.21+4.tmp (PID: 5508)
Creates a new Windows service
- sc.exe (PID: 7300)
Windows service management via SC.EXE
- sc.exe (PID: 7756)
- sc.exe (PID: 900)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7860)
- SetupVPNService.exe (PID: 4220)
- tun2socks.exe (PID: 684)
- tun2socks.exe (PID: 7620)
Process drops legitimate windows executable
- SetupVPN-5.0.21+4.tmp (PID: 5508)
Starts CMD.EXE for commands execution
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- cmd.exe (PID: 7860)
- smartdnsblock_sv.exe (PID: 7896)
- smartdnsblock_sv.exe (PID: 7256)
Executing commands from a ".bat" file
- SetupVPN-5.0.21+4.tmp (PID: 5508)
Executes as Windows Service
- SetupVPNService.exe (PID: 4220)
Creates files in the driver directory
- drvinst.exe (PID: 7348)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7860)
Application launched itself
- cmd.exe (PID: 7860)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7860)
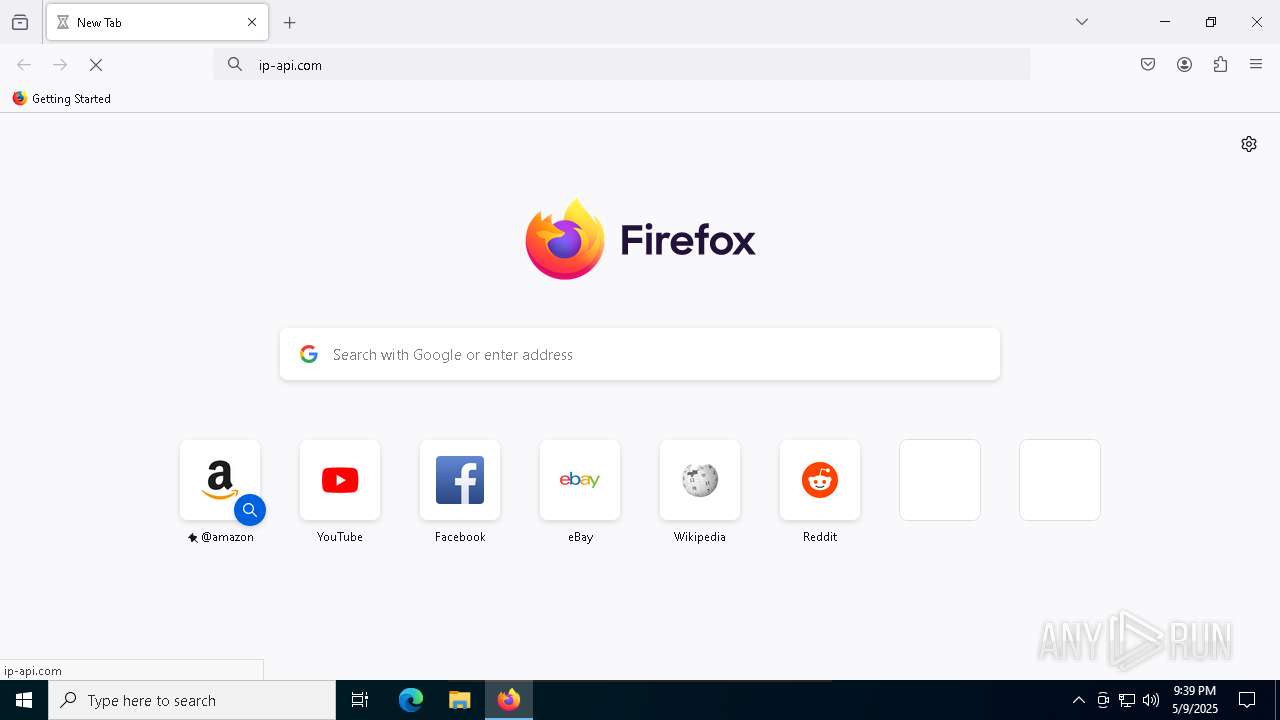
Process uses powershell cmdlet to discover network configuration
- cmd.exe (PID: 7860)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7860)
Get information on the list of running processes
- SetupVPN.exe (PID: 7592)
Uses ROUTE.EXE to modify routing table
- SetupVPNService.exe (PID: 4220)
Connects to unusual port
- SetupVPN.exe (PID: 7592)
- tun2socks.exe (PID: 7620)
Connects to SMTP port
- tun2socks.exe (PID: 684)
INFO
Application launched itself
- firefox.exe (PID: 4152)
- firefox.exe (PID: 864)
- firefox.exe (PID: 3884)
- firefox.exe (PID: 5772)
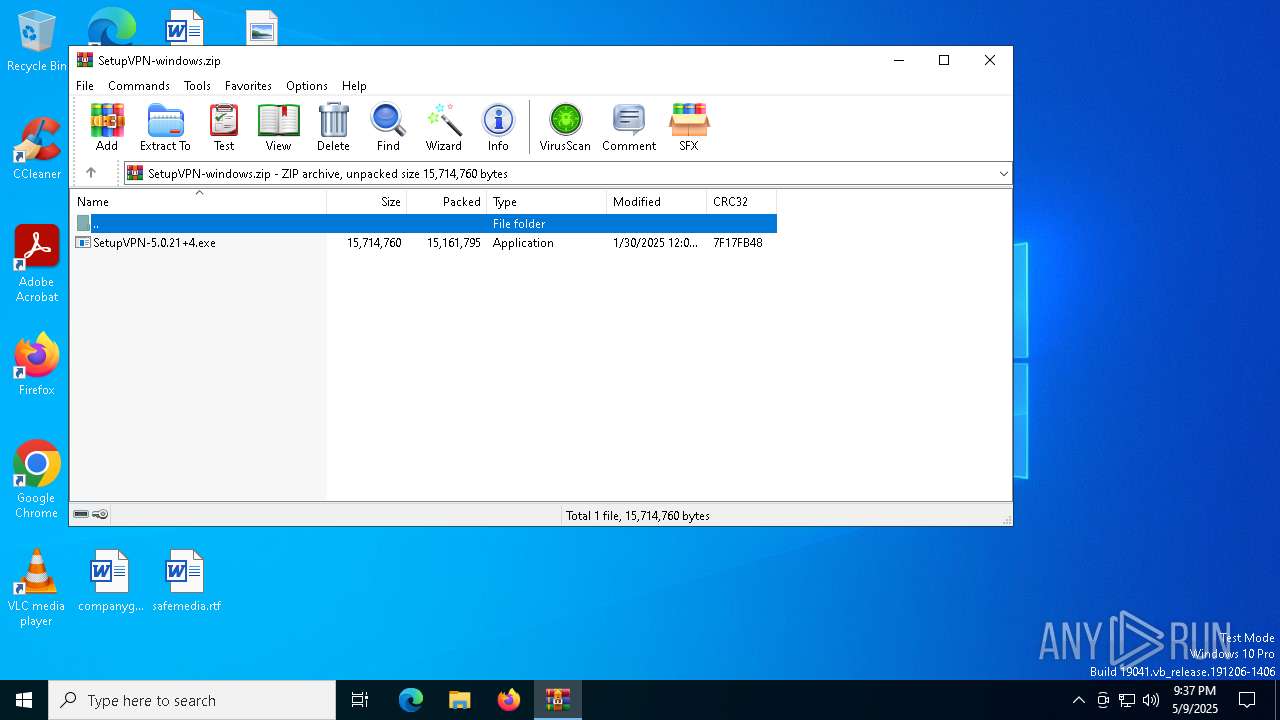
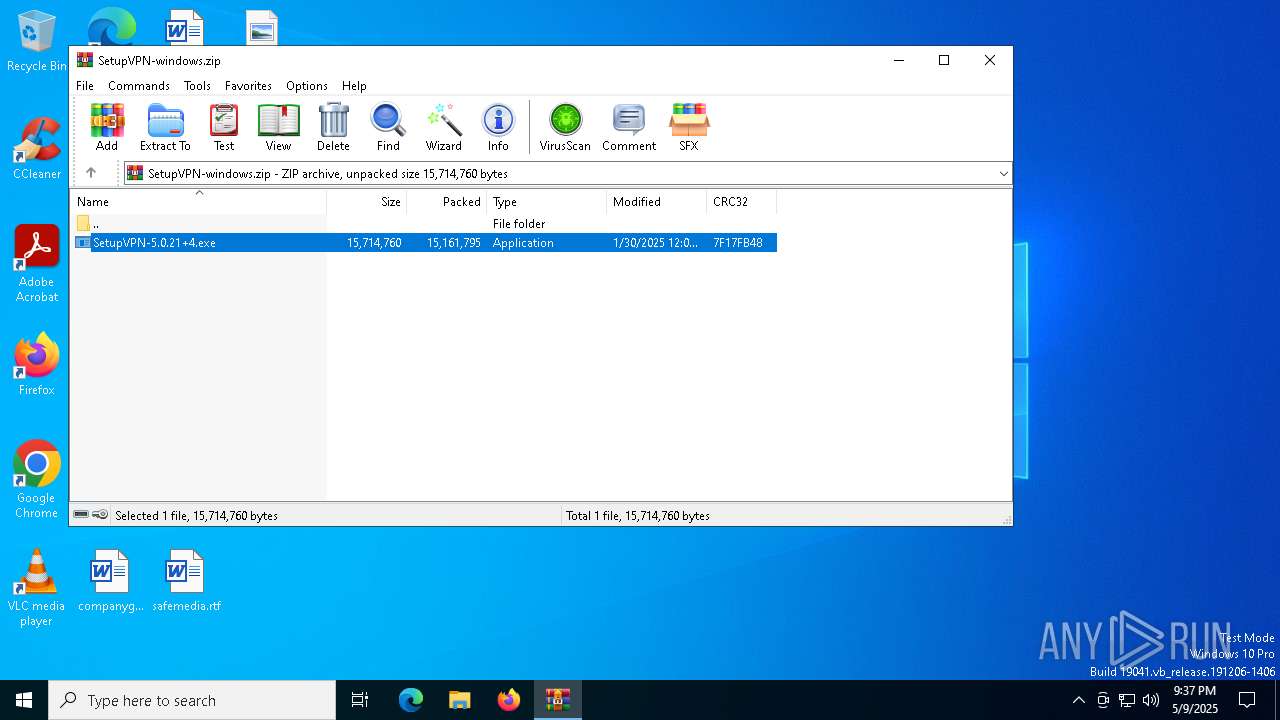
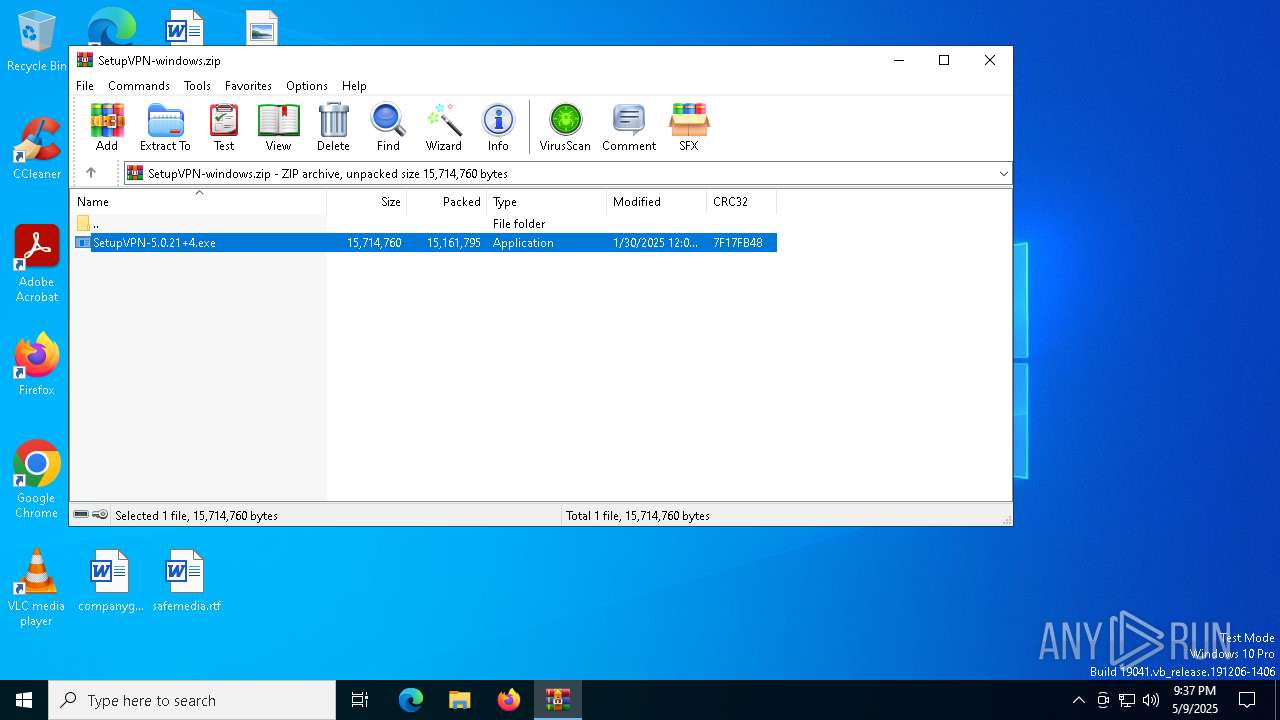
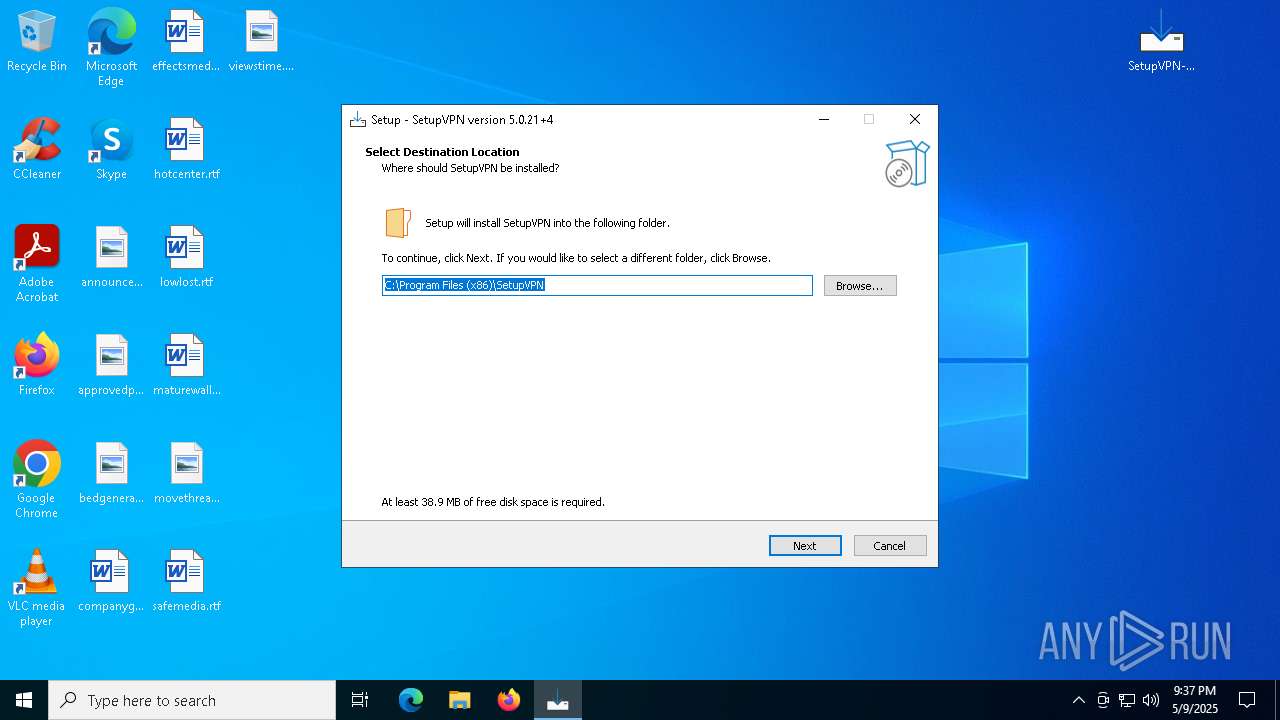
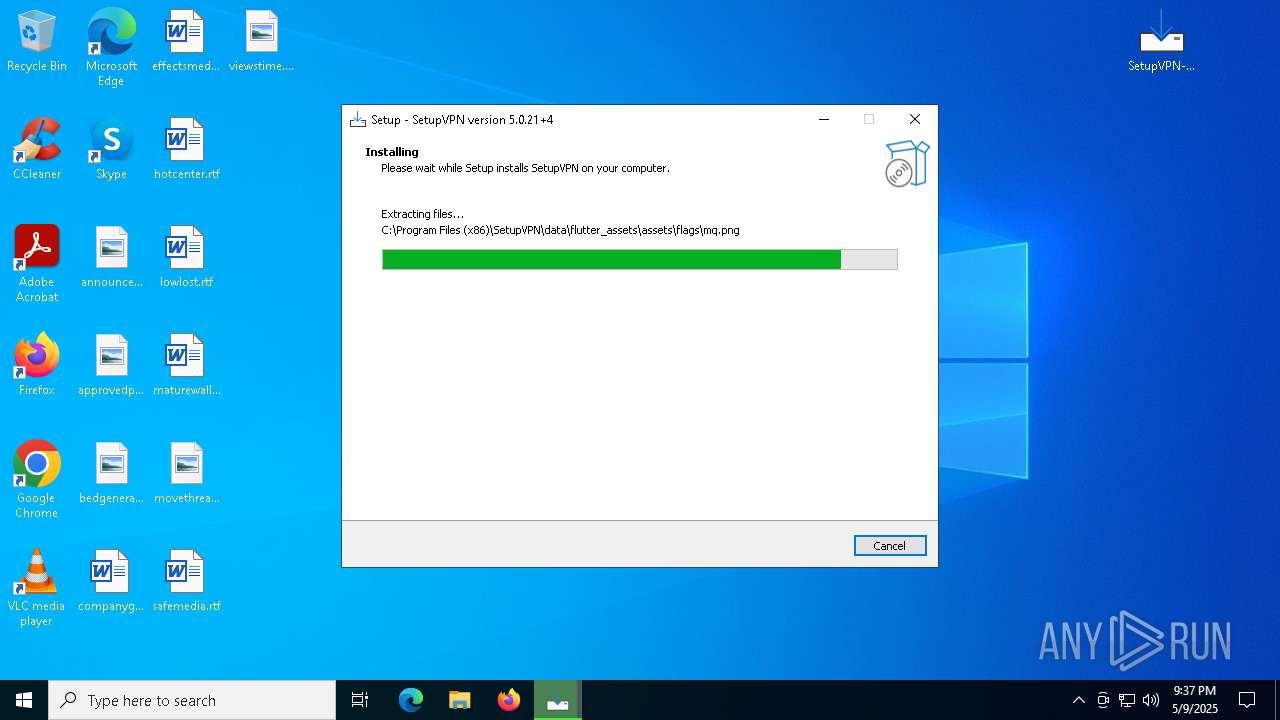
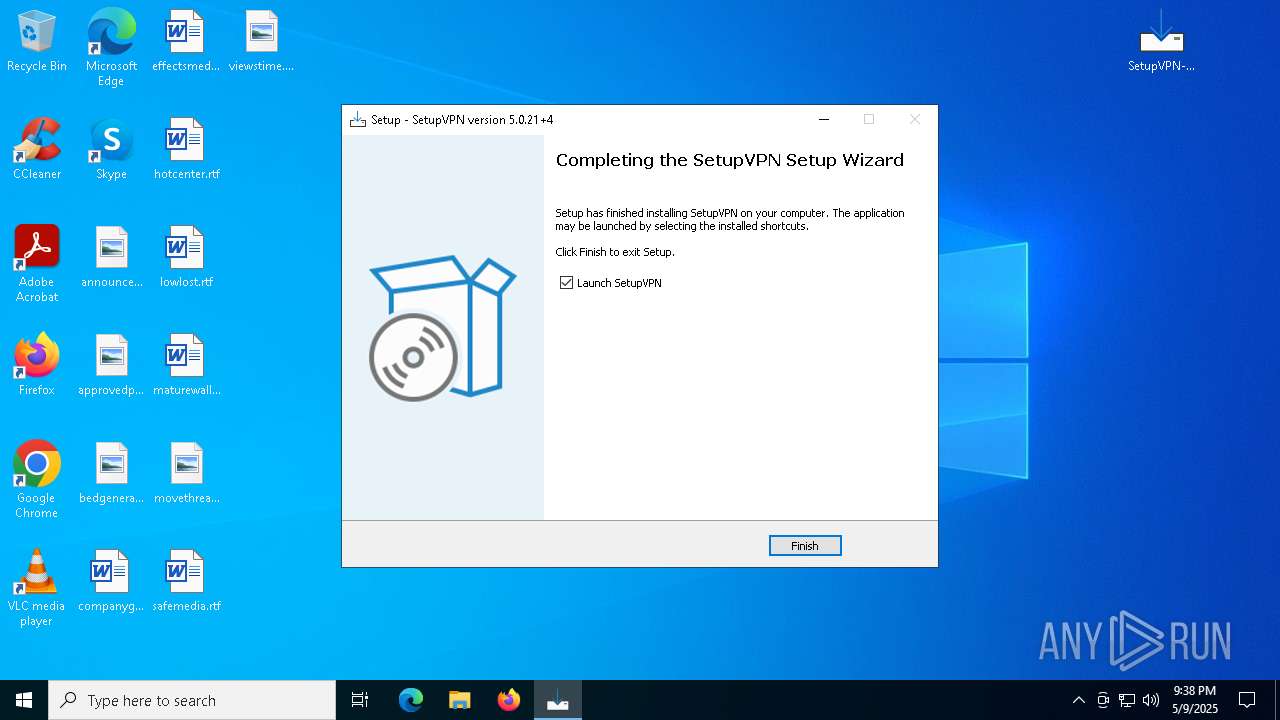
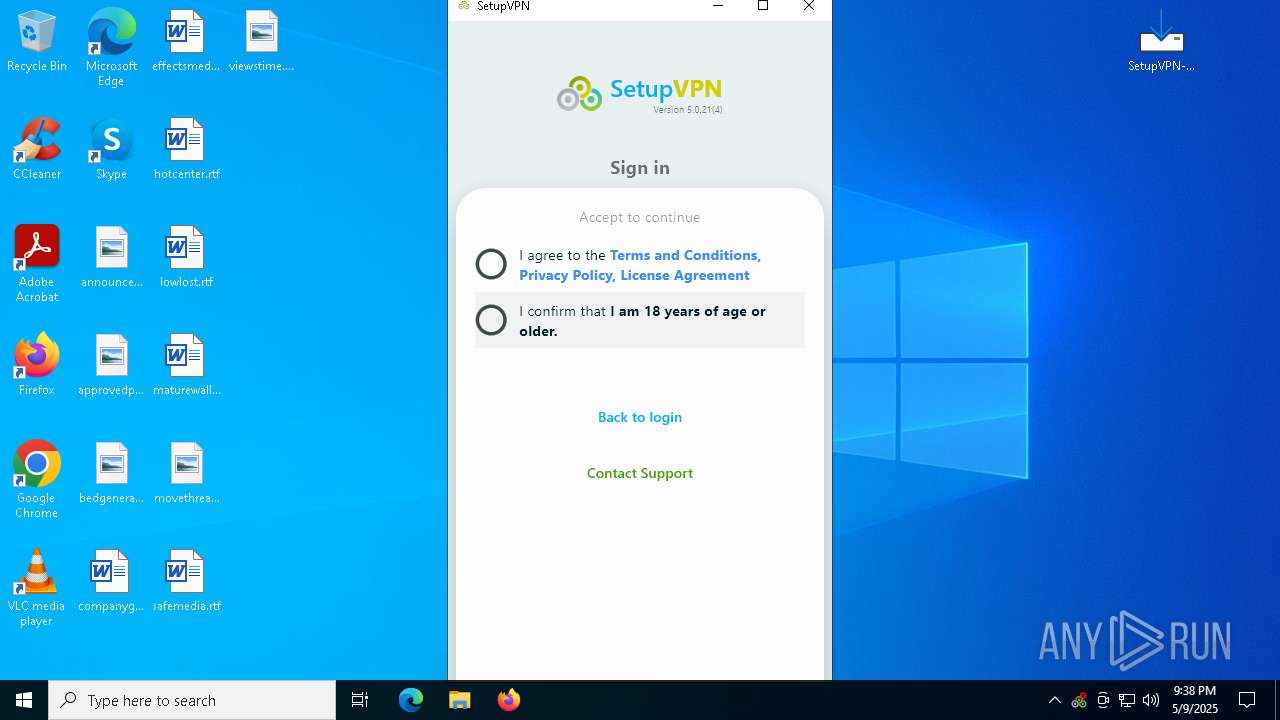
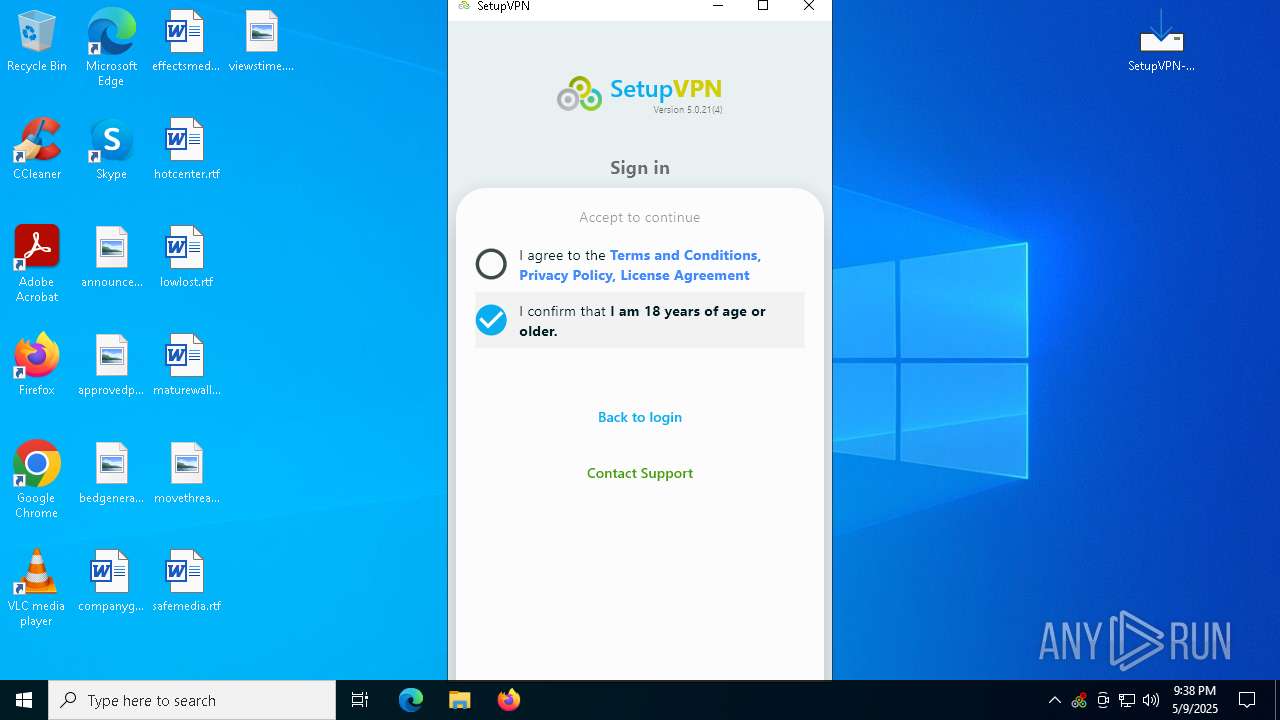
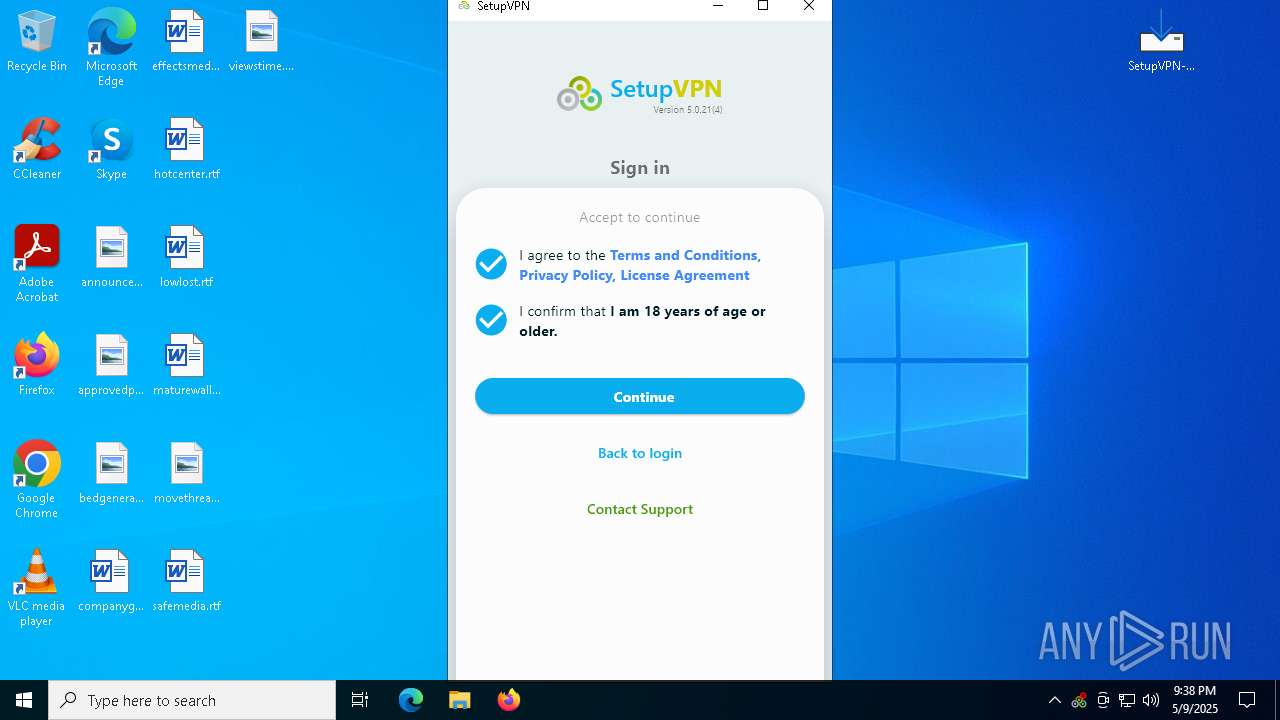
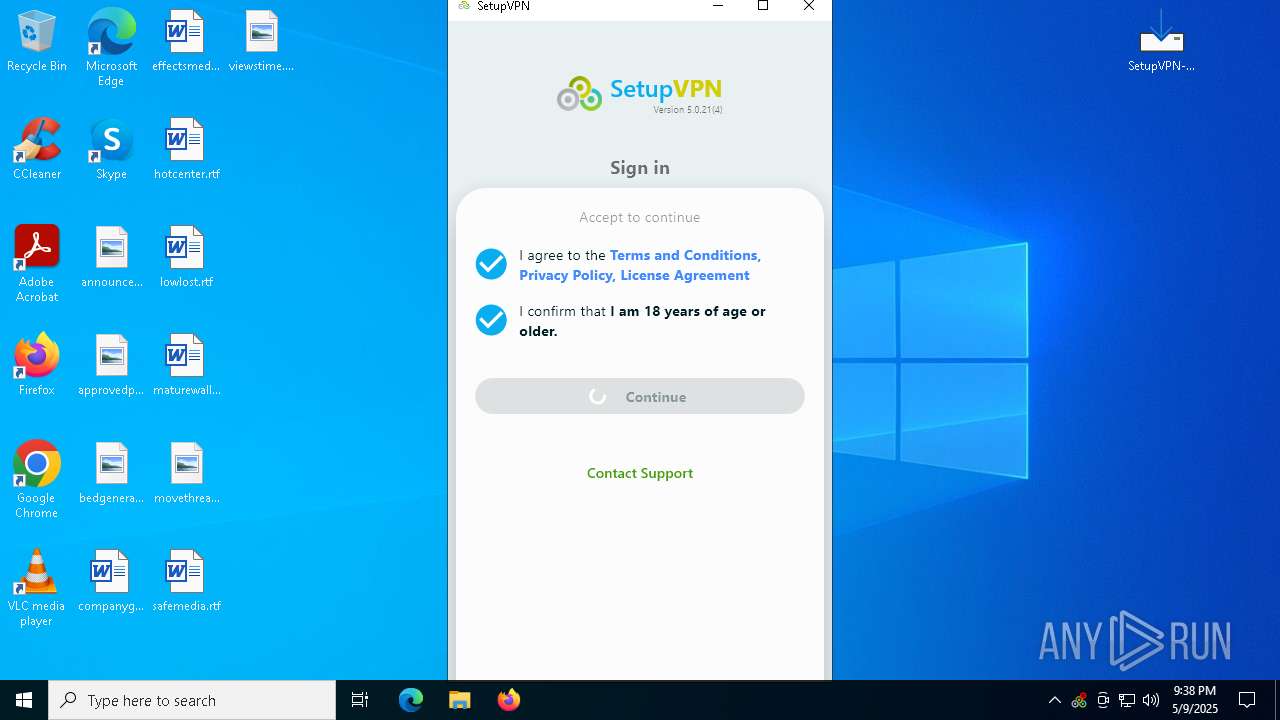
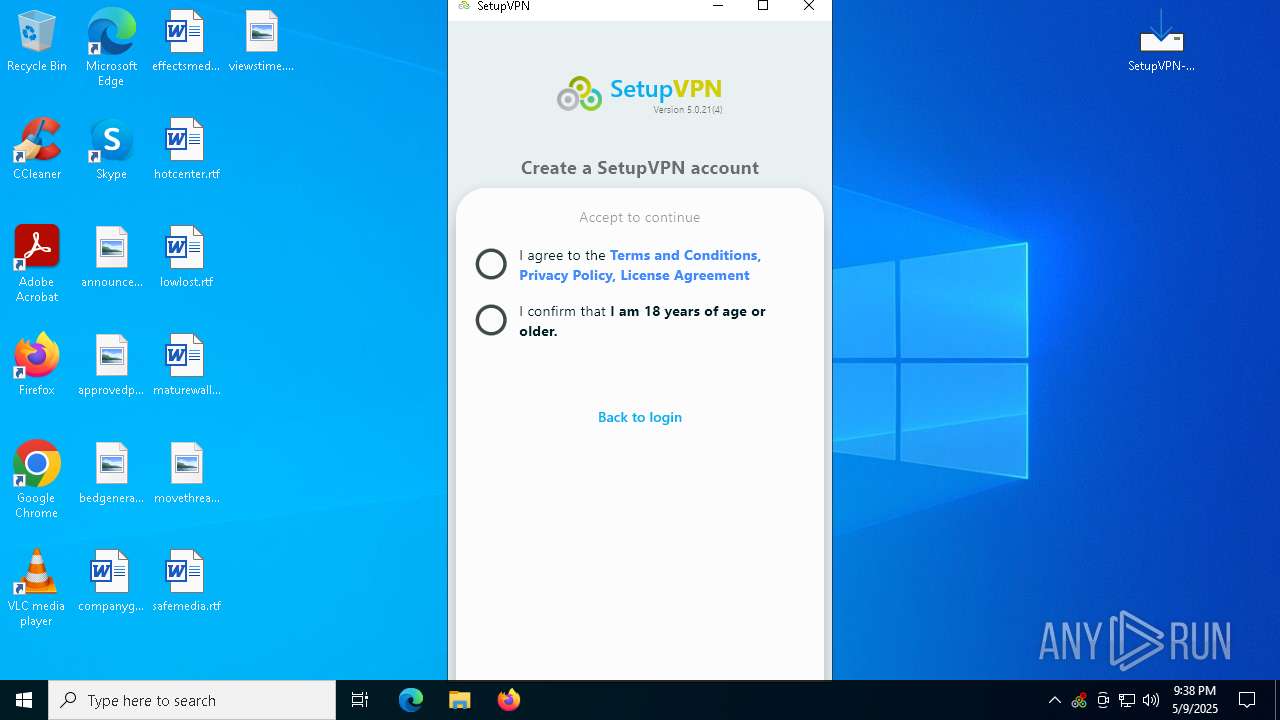
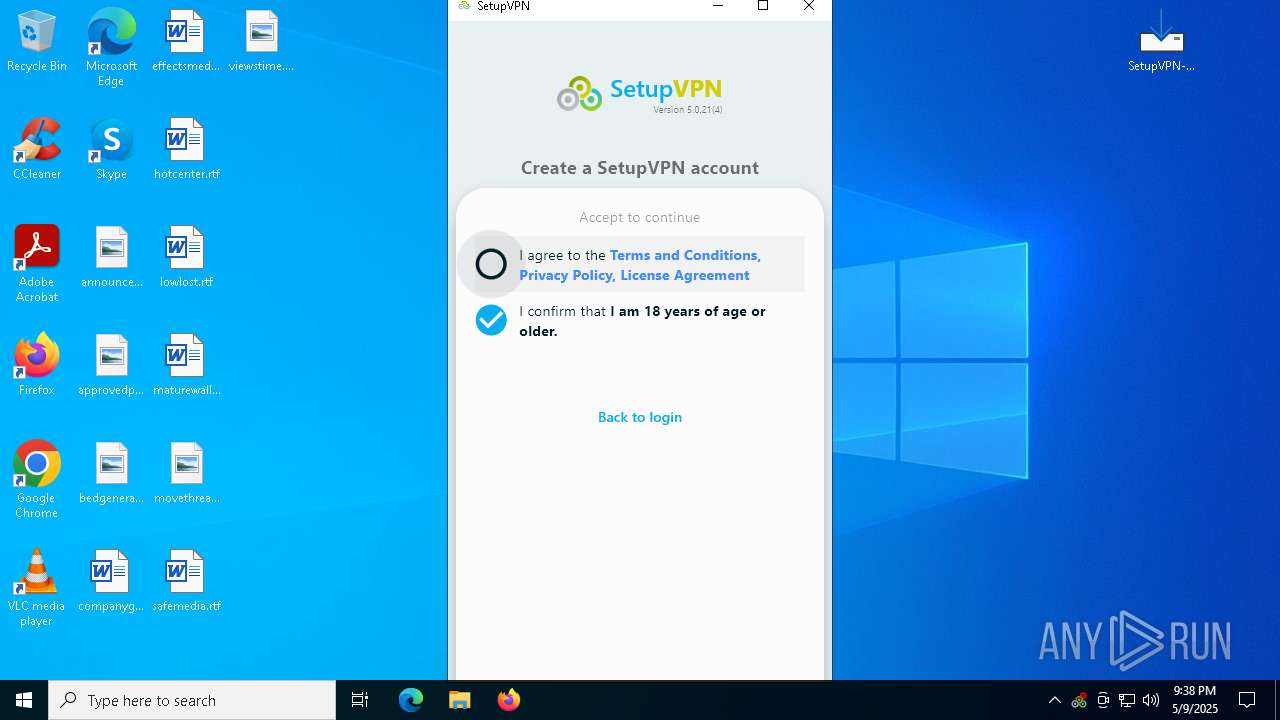
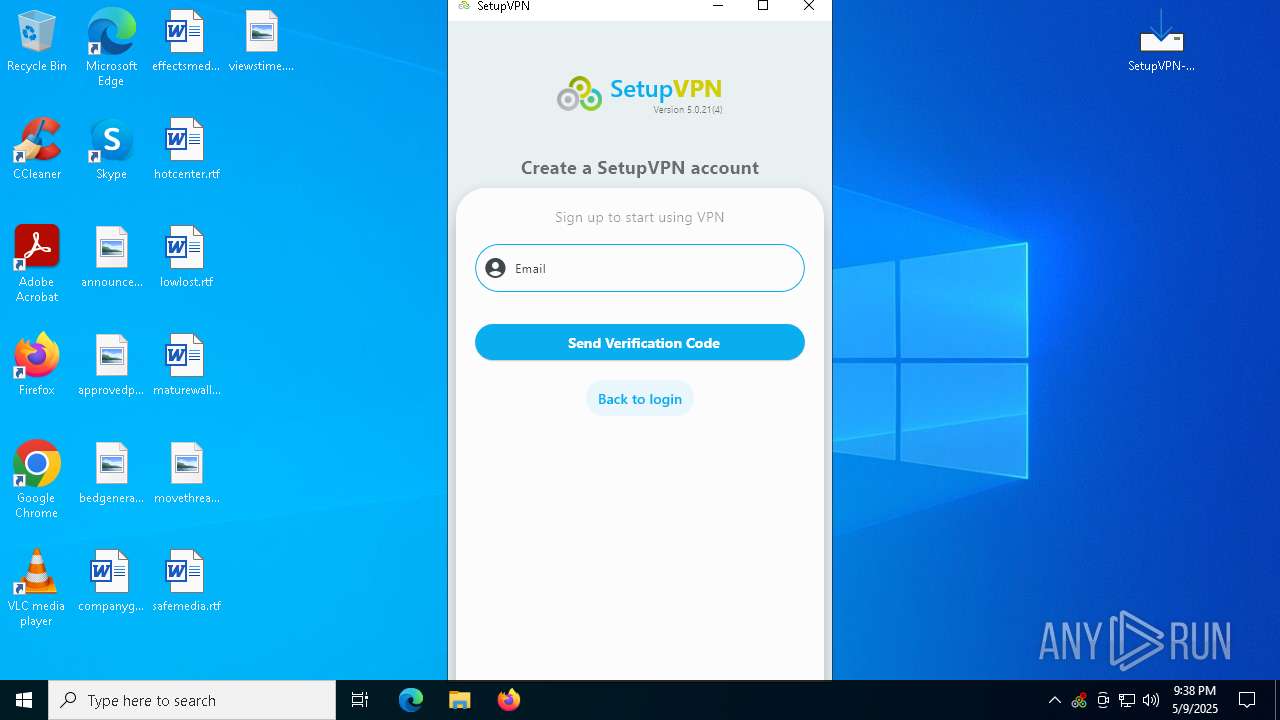
Manual execution by a user
- SetupVPN-5.0.21+4.exe (PID: 7996)
- WinRAR.exe (PID: 7636)
- firefox.exe (PID: 3884)
Reads the computer name
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- SetupVPNService.exe (PID: 4220)
- tapinstall.exe (PID: 5400)
- SetupVPN-5.0.21+4.tmp (PID: 2152)
Checks supported languages
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- SetupVPN-5.0.21+4.exe (PID: 7996)
- SetupVPN-5.0.21+4.tmp (PID: 2152)
- SetupVPNService.exe (PID: 4220)
- tapinstall.exe (PID: 5400)
- drvinst.exe (PID: 7348)
- SetupVPN-5.0.21+4.exe (PID: 3180)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7636)
Create files in a temporary directory
- SetupVPN-5.0.21+4.exe (PID: 7996)
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- tapinstall.exe (PID: 5400)
- SetupVPN-5.0.21+4.exe (PID: 3180)
Creates files in the program directory
- SetupVPN-5.0.21+4.tmp (PID: 5508)
The sample compiled with english language support
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- tapinstall.exe (PID: 5400)
- drvinst.exe (PID: 7348)
- drvinst.exe (PID: 4896)
Detects InnoSetup installer (YARA)
- SetupVPN-5.0.21+4.exe (PID: 7996)
- SetupVPN-5.0.21+4.tmp (PID: 2152)
- SetupVPN-5.0.21+4.exe (PID: 3180)
- SetupVPN-5.0.21+4.tmp (PID: 5508)
Compiled with Borland Delphi (YARA)
- SetupVPN-5.0.21+4.exe (PID: 7996)
- SetupVPN-5.0.21+4.tmp (PID: 2152)
- SetupVPN-5.0.21+4.exe (PID: 3180)
- SetupVPN-5.0.21+4.tmp (PID: 5508)
Creates a software uninstall entry
- SetupVPN-5.0.21+4.tmp (PID: 5508)
Process checks computer location settings
- SetupVPN-5.0.21+4.tmp (PID: 5508)
- SetupVPN-5.0.21+4.tmp (PID: 2152)
Disables trace logs
- netsh.exe (PID: 7652)
Reads the software policy settings
- tapinstall.exe (PID: 5400)
- drvinst.exe (PID: 7348)
Reads the machine GUID from the registry
- tapinstall.exe (PID: 5400)
- drvinst.exe (PID: 7348)
Modifies an existing route via ROUTE.EXE
- ROUTE.EXE (PID: 7900)
- ROUTE.EXE (PID: 6112)
- ROUTE.EXE (PID: 6136)
- ROUTE.EXE (PID: 7280)
- ROUTE.EXE (PID: 3332)
- ROUTE.EXE (PID: 4996)
- ROUTE.EXE (PID: 1088)
- ROUTE.EXE (PID: 6752)
- ROUTE.EXE (PID: 896)
- ROUTE.EXE (PID: 7672)
- ROUTE.EXE (PID: 1020)
- ROUTE.EXE (PID: 7396)
- ROUTE.EXE (PID: 5360)
- ROUTE.EXE (PID: 6944)
- ROUTE.EXE (PID: 7848)
- ROUTE.EXE (PID: 7588)
- ROUTE.EXE (PID: 2772)
- ROUTE.EXE (PID: 8120)
- ROUTE.EXE (PID: 3956)
- ROUTE.EXE (PID: 6960)
- ROUTE.EXE (PID: 8100)
- ROUTE.EXE (PID: 5800)
- ROUTE.EXE (PID: 8040)
- ROUTE.EXE (PID: 7272)
- ROUTE.EXE (PID: 7360)
- ROUTE.EXE (PID: 8148)
- ROUTE.EXE (PID: 4012)
- ROUTE.EXE (PID: 8012)
- ROUTE.EXE (PID: 7252)
- ROUTE.EXE (PID: 3032)
- ROUTE.EXE (PID: 7432)
- ROUTE.EXE (PID: 7436)
- ROUTE.EXE (PID: 1852)
- ROUTE.EXE (PID: 732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
375
Monitored processes
236
Malicious processes
12
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=NetworkAvailable | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | netsh interface ip set dnsservers SetupVPN static address=1.1.1.1 | C:\Windows\SysWOW64\netsh.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
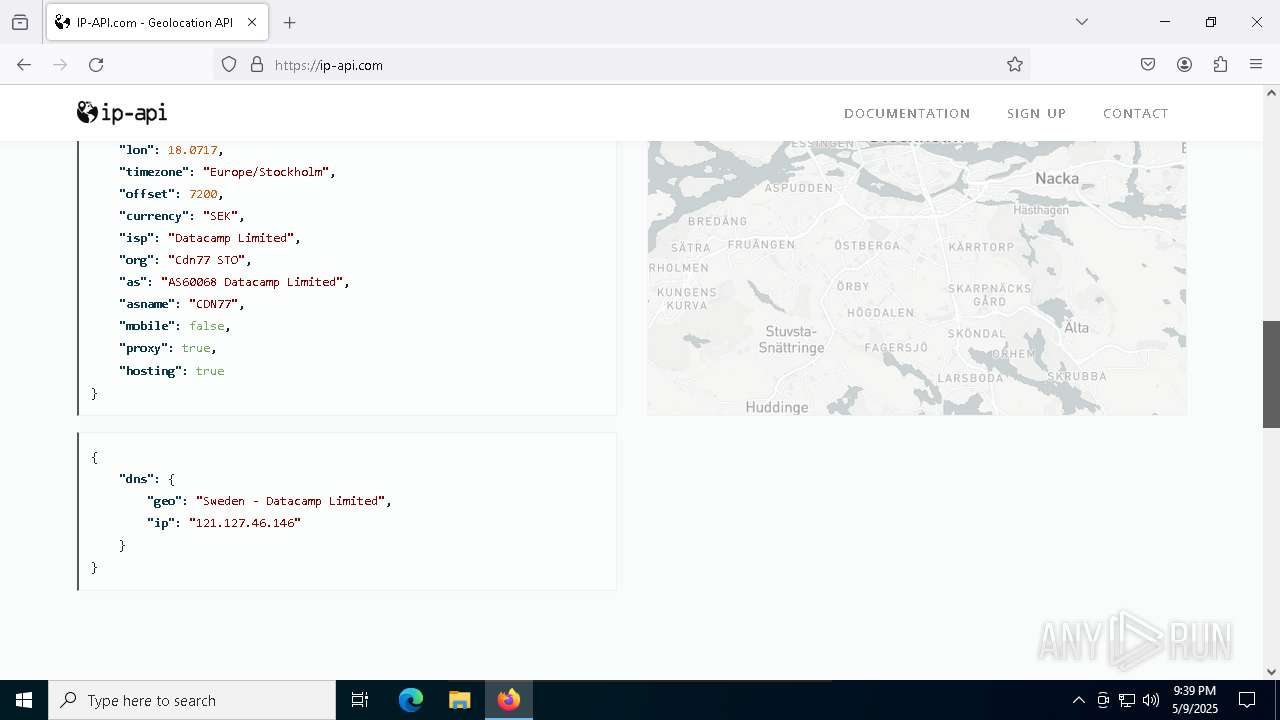
| 684 | "C:\Program Files (x86)\SetupVPN\tun2socks\tun2socks.exe" -tunName SetupVPN -tunDNS 54.81.22.119 -proxyHost 121.127.46.146 -proxyPort 587 -proxyPassword b446b9ee -dnsFallback -tunGw 172.16.9.1 -tunAddr 172.16.9.2 | C:\Program Files (x86)\SetupVPN\tun2socks\tun2socks.exe | SetupVPN.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "route" change 203.0.113.0/24 192.168.100.2 if 14 | C:\Windows\SysWOW64\ROUTE.EXE | — | SetupVPNService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: TCP/IP Route Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "netsh" interface ipv6 add route fc00::/7 interface=1 metric=0 store=active | C:\Windows\SysWOW64\netsh.exe | — | SetupVPNService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "net" stop SetupVPNService | C:\Windows\SysWOW64\net.exe | — | SetupVPN-5.0.21+4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | smartdnsblock_sv.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://1.awakened.work//public/s/desktop/windows/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
112 013
Read events
111 899
Write events
106
Delete events
8
Modification events
| (PID) Process: | (4152) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\SetupVPN-windows.zip | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
54
Suspicious files
268
Text files
560
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4152 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:8684C30CD509452564DD0486E9A108D1 | SHA256:3AA76C2F87BC61500FC2C336F4817C22CE2EF89CC7443B56375FF0D0975D5EB0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
211
DNS requests
194
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4152 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4152 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
4152 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
4152 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
4152 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
4152 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
4152 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
4152 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
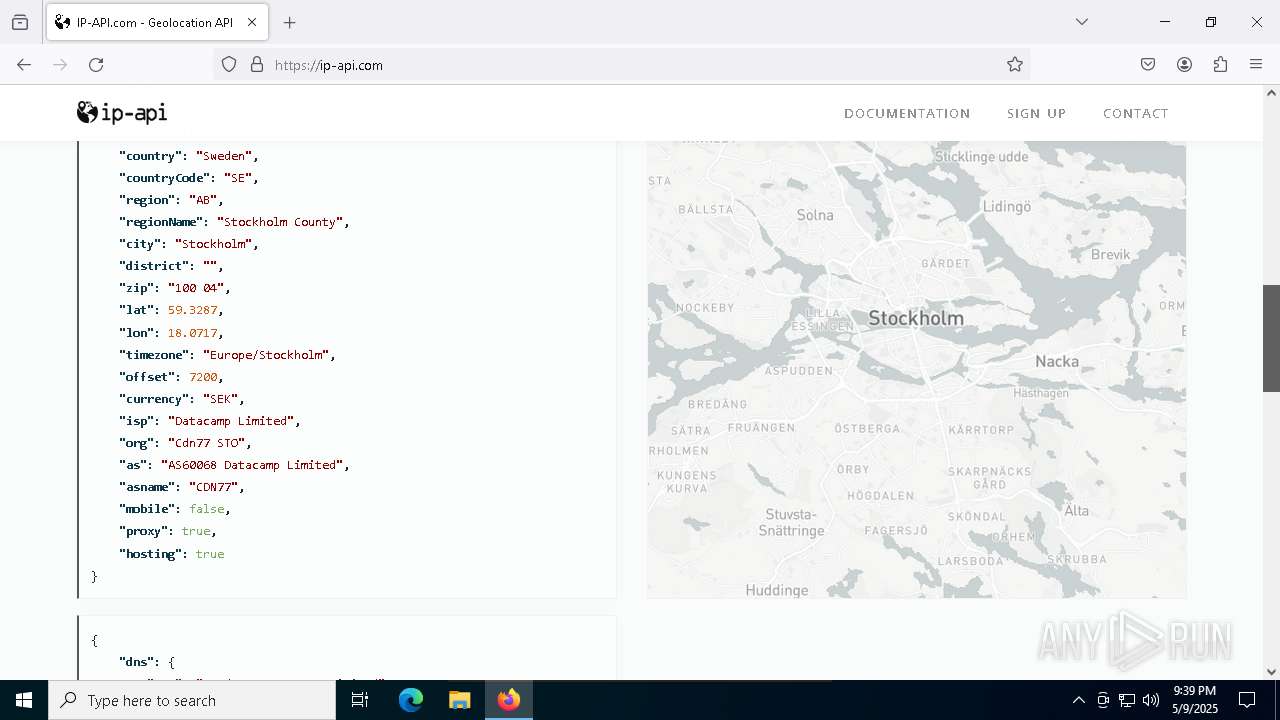
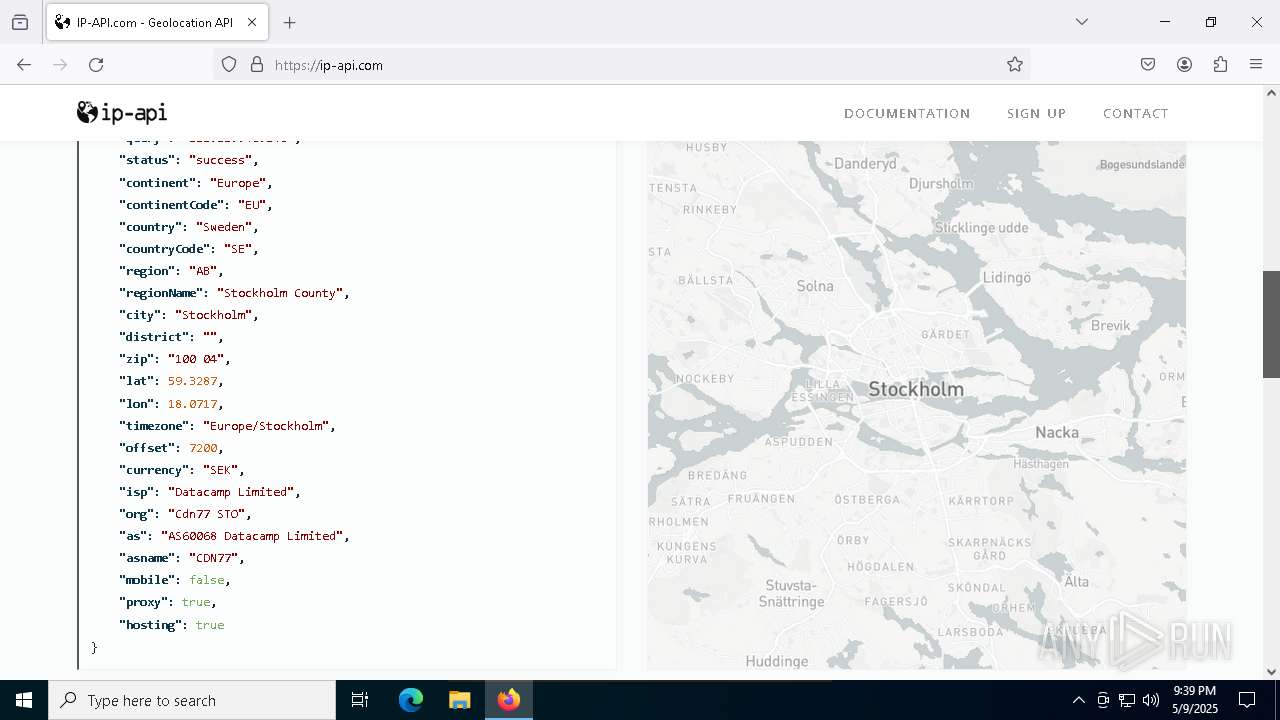
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.190:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4152 | firefox.exe | 104.21.112.1:443 | 1.awakened.work | CLOUDFLARENET | — | unknown |
4152 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
4152 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
4152 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
4152 | firefox.exe | 184.24.77.56:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
1.awakened.work |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
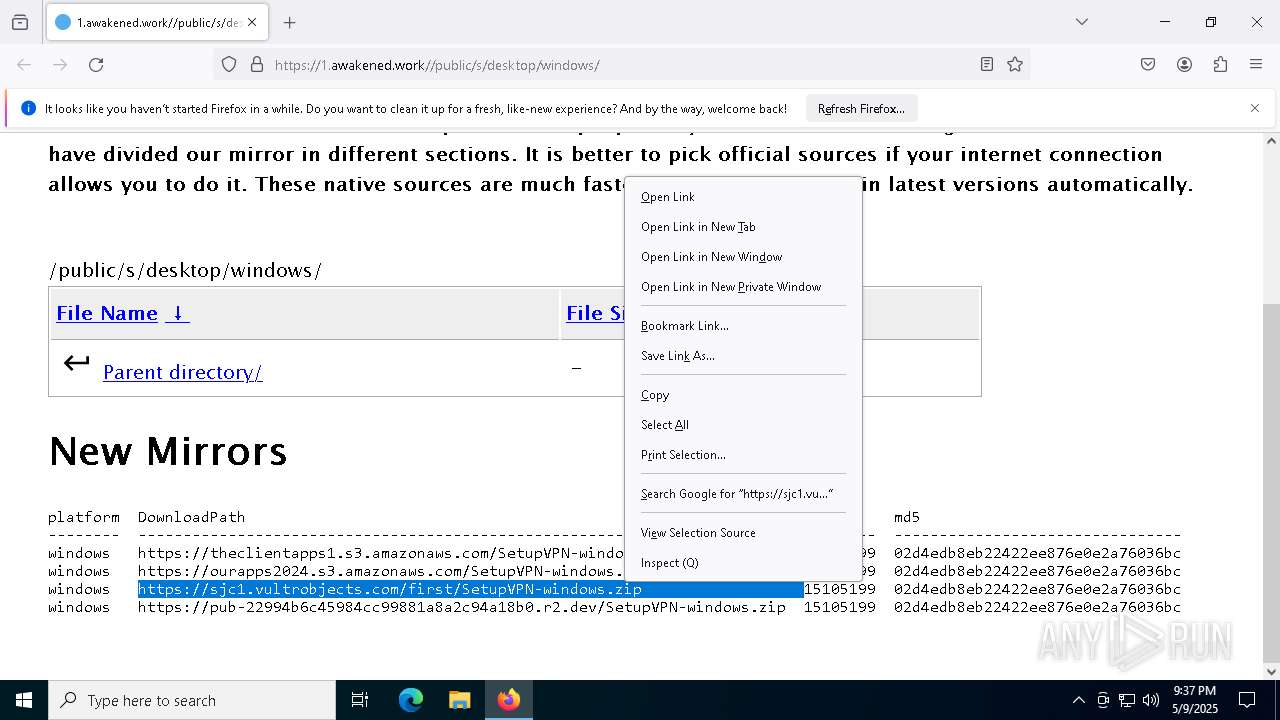
2196 | svchost.exe | Misc activity | ET INFO Vultr CDN/Object Storage Domain in DNS Lookup (vultrobjects .com) |
4152 | firefox.exe | Misc activity | ET INFO Observed Suspicious Domain (vultrobjects .com in TLS SNI) |
2196 | svchost.exe | Misc activity | ET INFO Vultr CDN/Object Storage Domain in DNS Lookup (vultrobjects .com) |
2196 | svchost.exe | Misc activity | ET INFO Vultr CDN/Object Storage Domain in DNS Lookup (vultrobjects .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (vultrobjects .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (vultrobjects .com) |
4152 | firefox.exe | Misc activity | ET INFO Observed Suspicious Domain (vultrobjects .com in TLS SNI) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (vultrobjects .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |