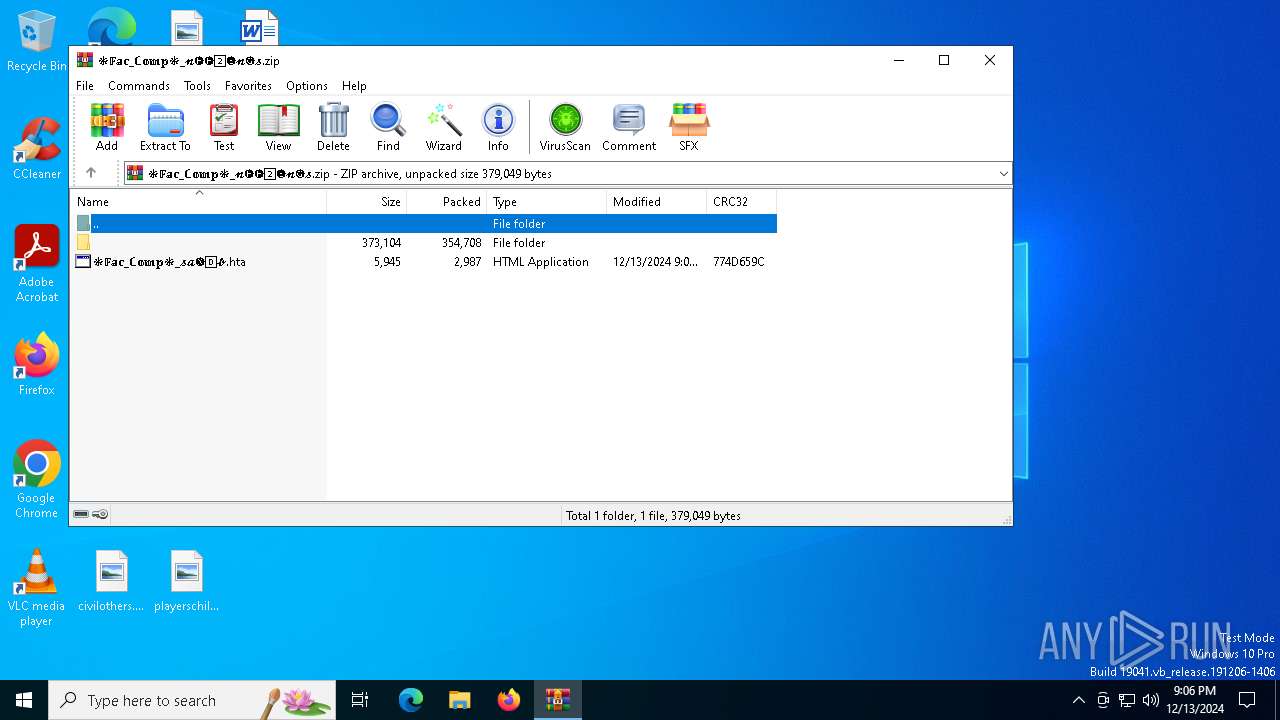
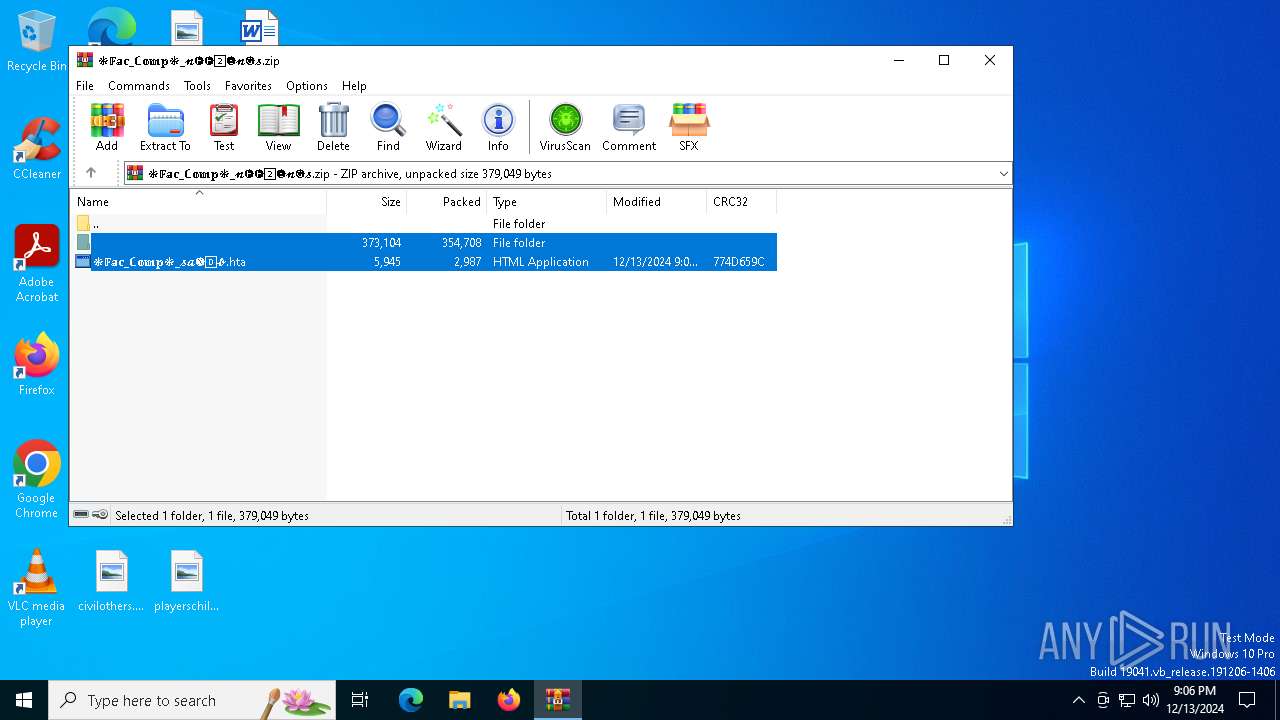
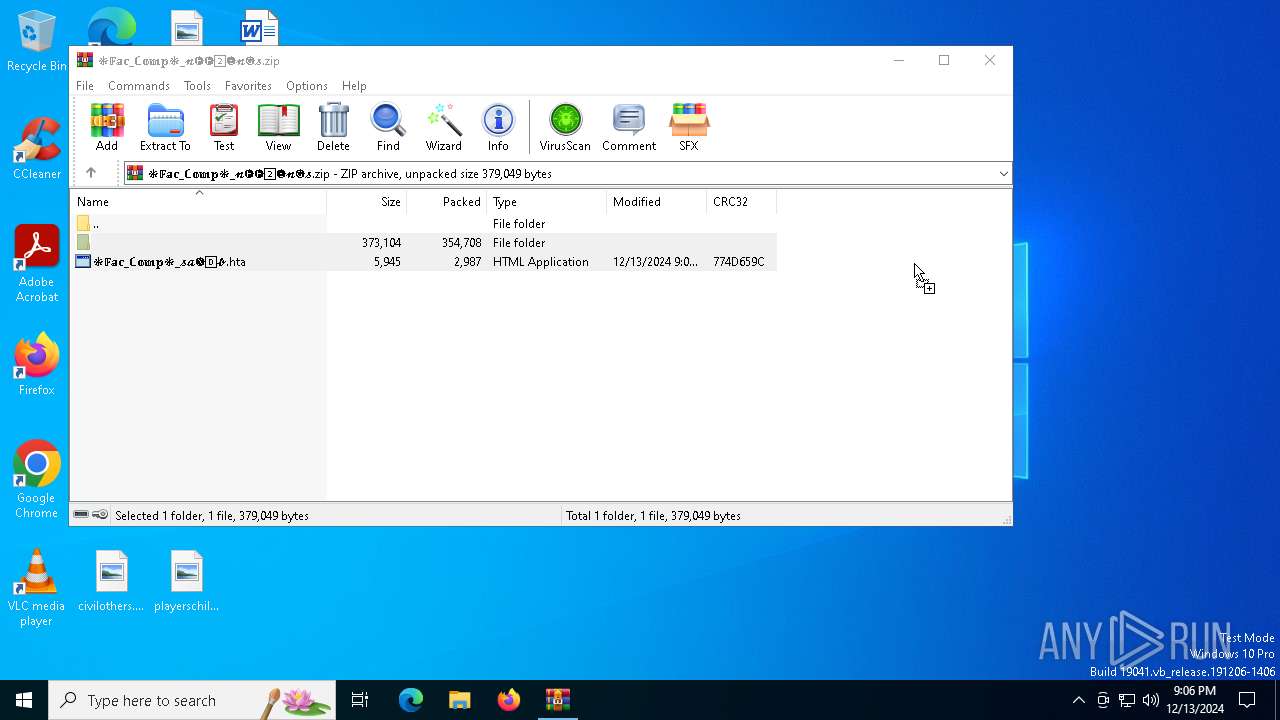
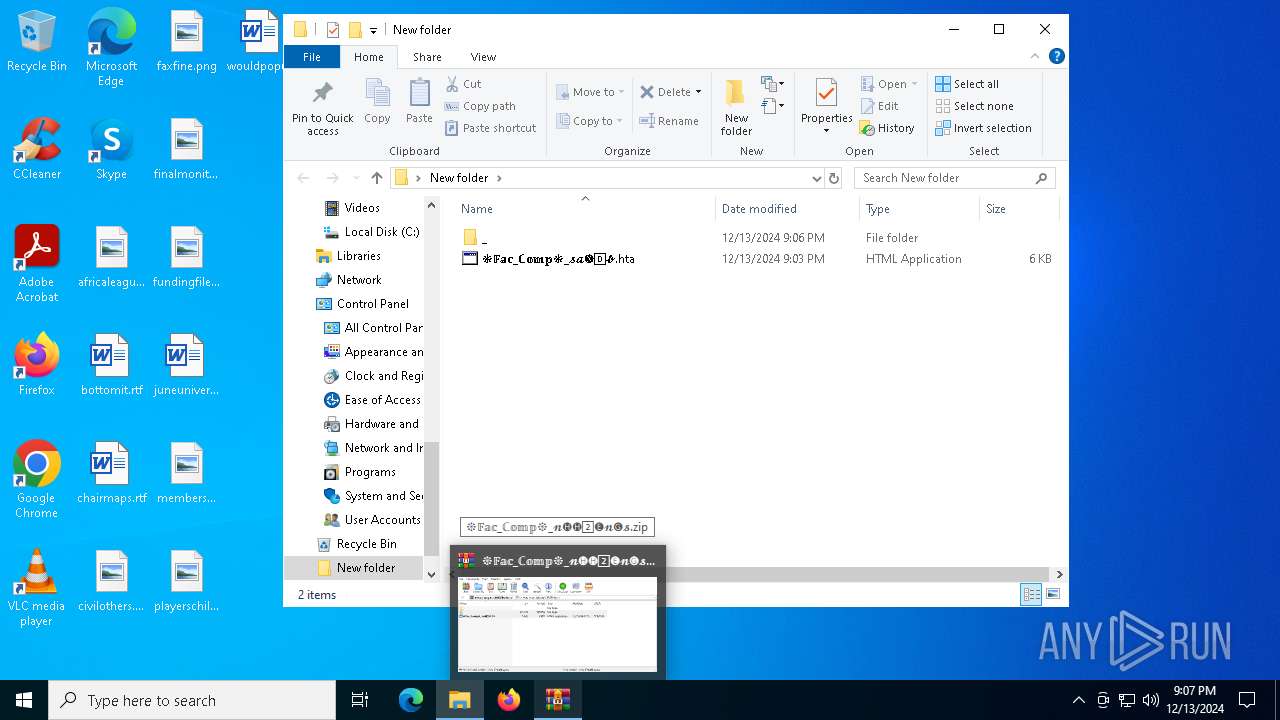
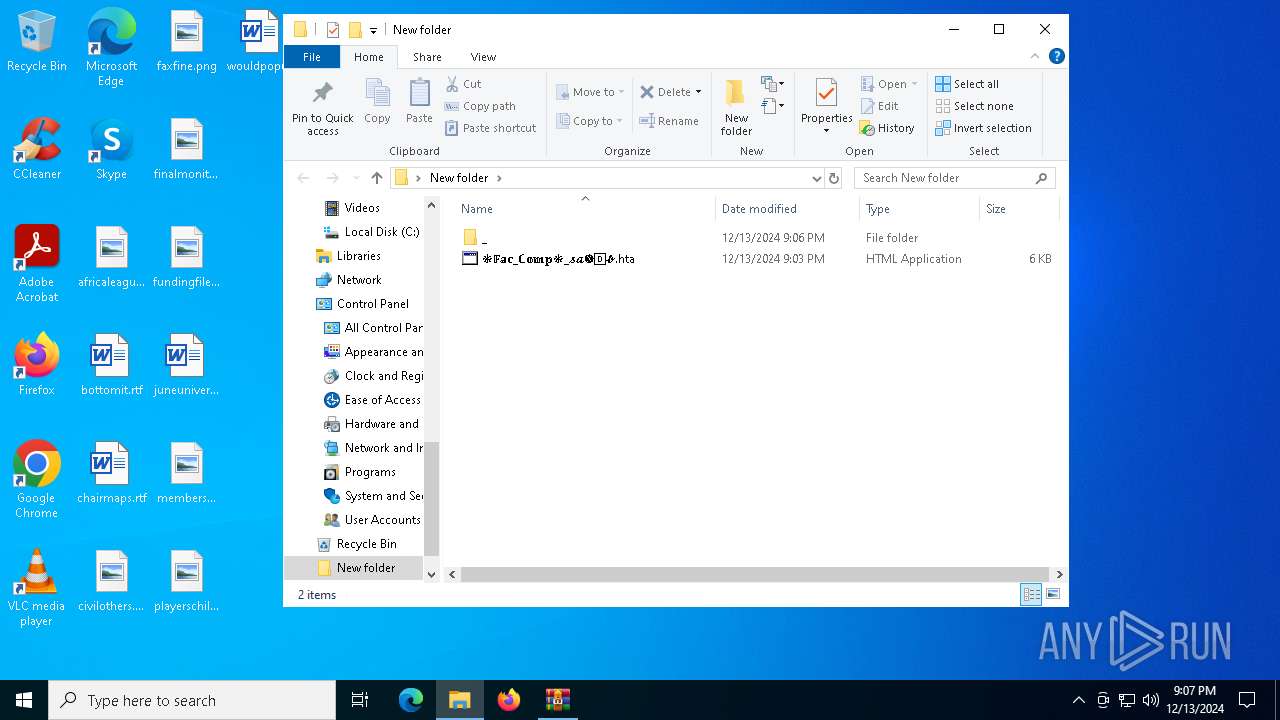
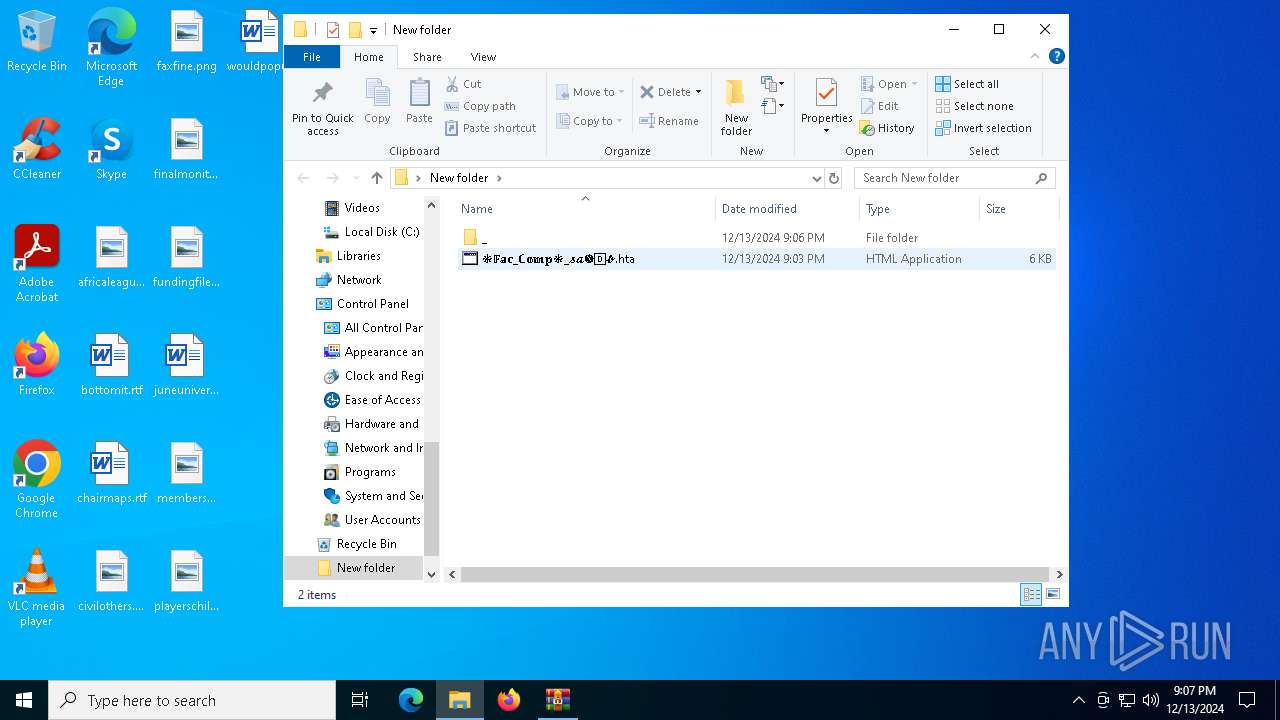
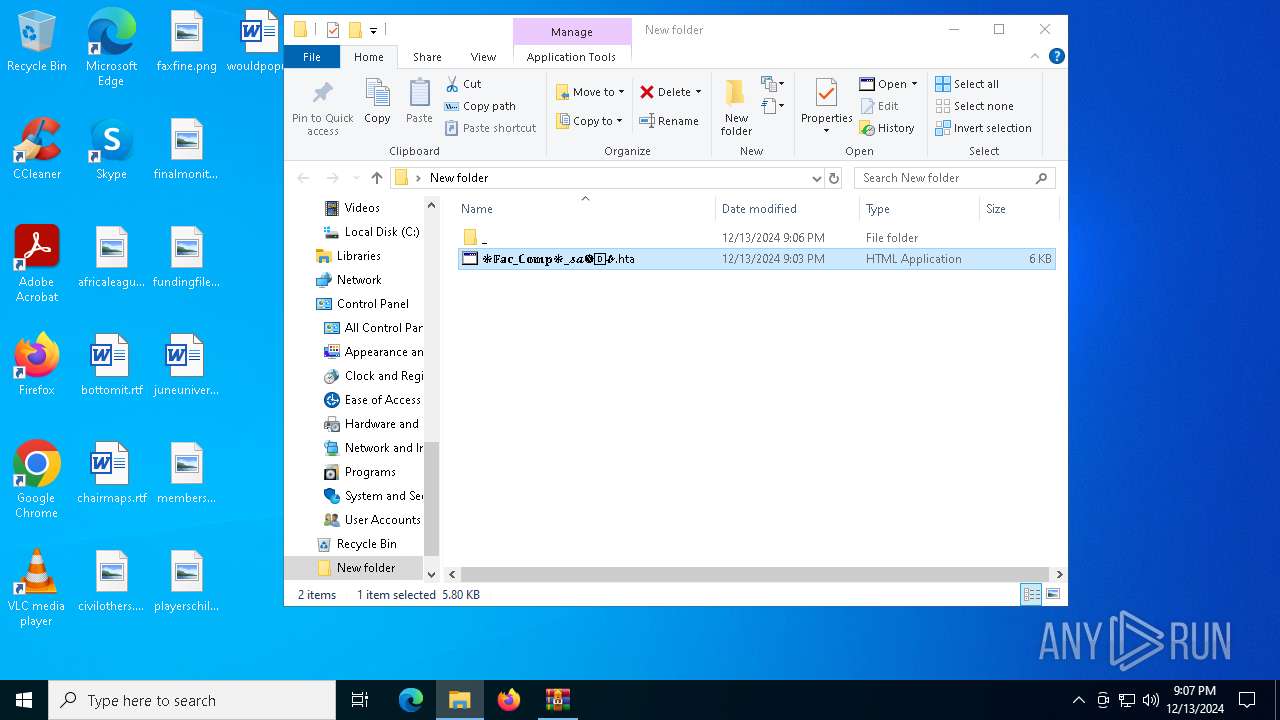
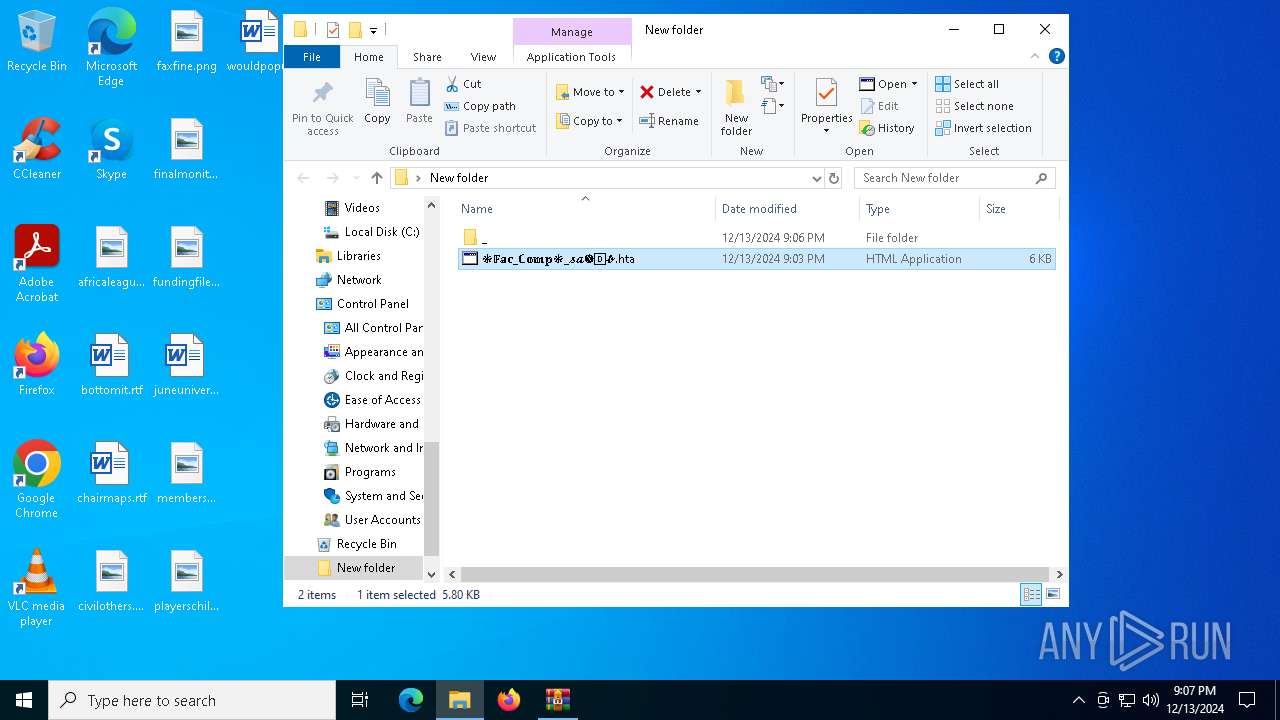
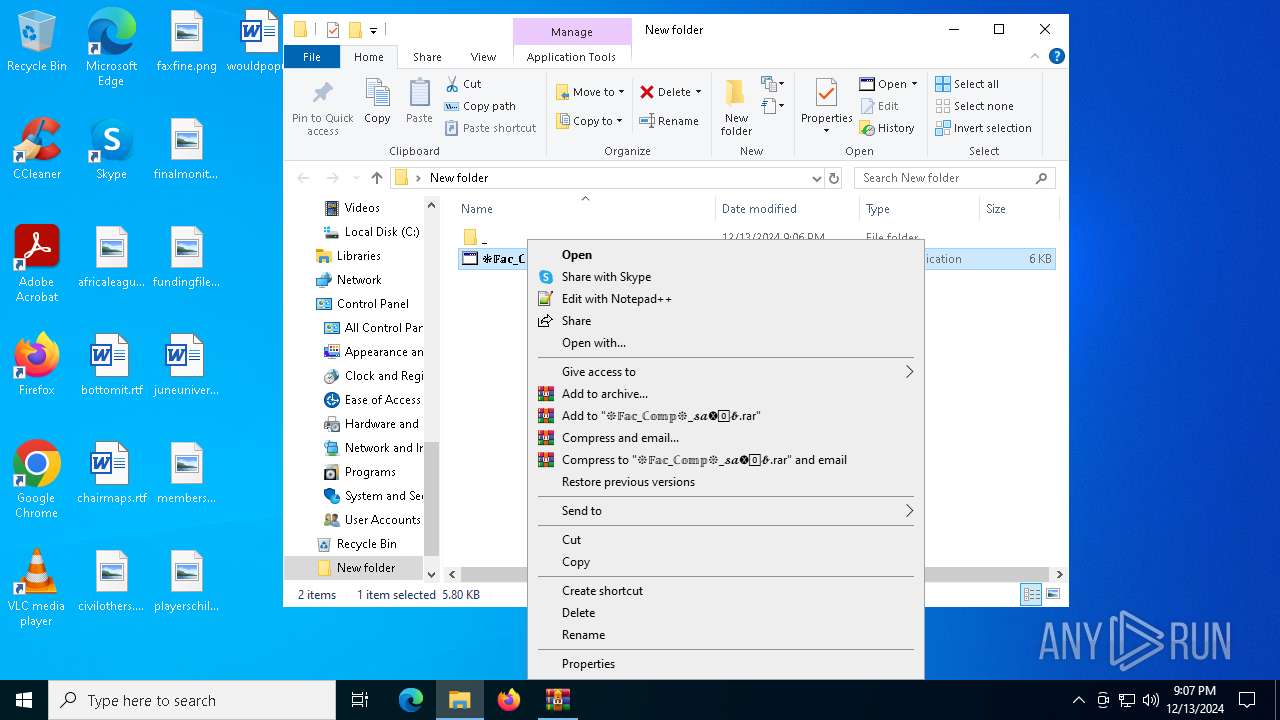
| File name: | ❉𝔽𝕒𝕔_ℂ𝕠𝕞𝕡❉_𝓷🅗🅗2⃣🅔𝓷🅖𝓼.zip |
| Full analysis: | https://app.any.run/tasks/08a0b57e-622e-4485-841a-1cf22528ba12 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 21:06:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 080A44193C88985E90AD22DAFF3A6AD4 |
| SHA1: | DCDFD310BCC9130D719DE8BEC7DF4ADFC8C3BD94 |
| SHA256: | A016020D5D5E923D111262A371C4EA3DE759E5AF11AB7D1EBA91F415627180E8 |
| SSDEEP: | 12288:hUkgpWgALGPWHC0BbCz0lVYzpjNSeJWD8EmvBFdWdJvri:ekgpxALGPWHC0BbCzGVajNSeJWD8dvB/ |
MALICIOUS
Accesses environment variables (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Gets username (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Checks whether a specified folder exists (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
SUSPICIOUS
Accesses computer name via WMI (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Gets computer name (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Accesses current user name via WMI (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Executes WMI query (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Accesses language version of the operating system installed via WMI (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Reads security settings of Internet Explorer
- notepad++.exe (PID: 6184)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 6424)
- mshta.exe (PID: 5460)
- mshta.exe (PID: 6884)
Reads Internet Explorer settings
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
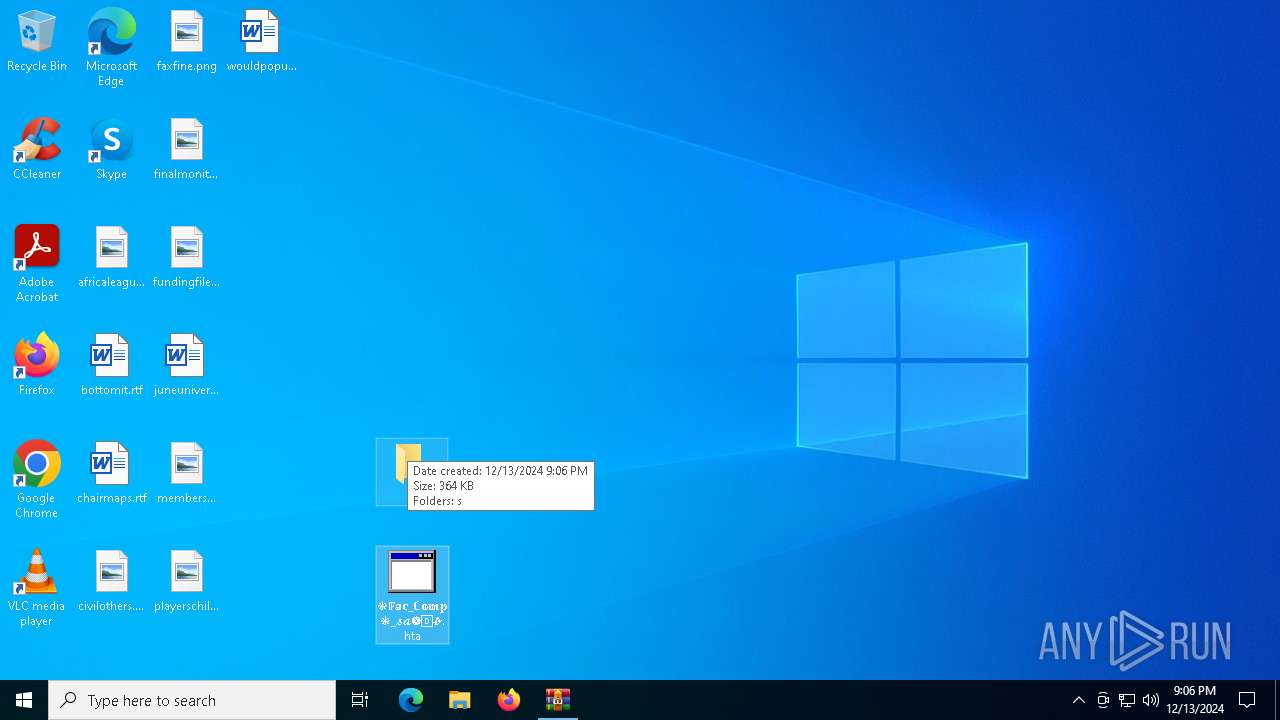
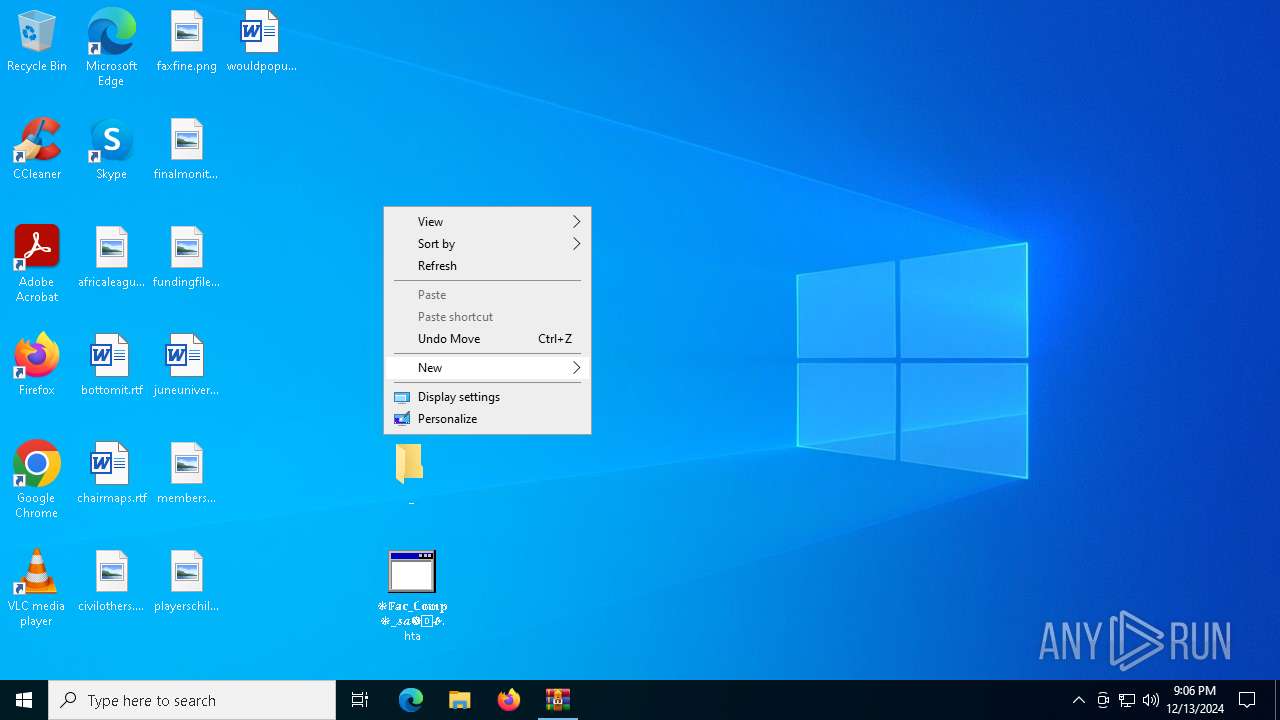
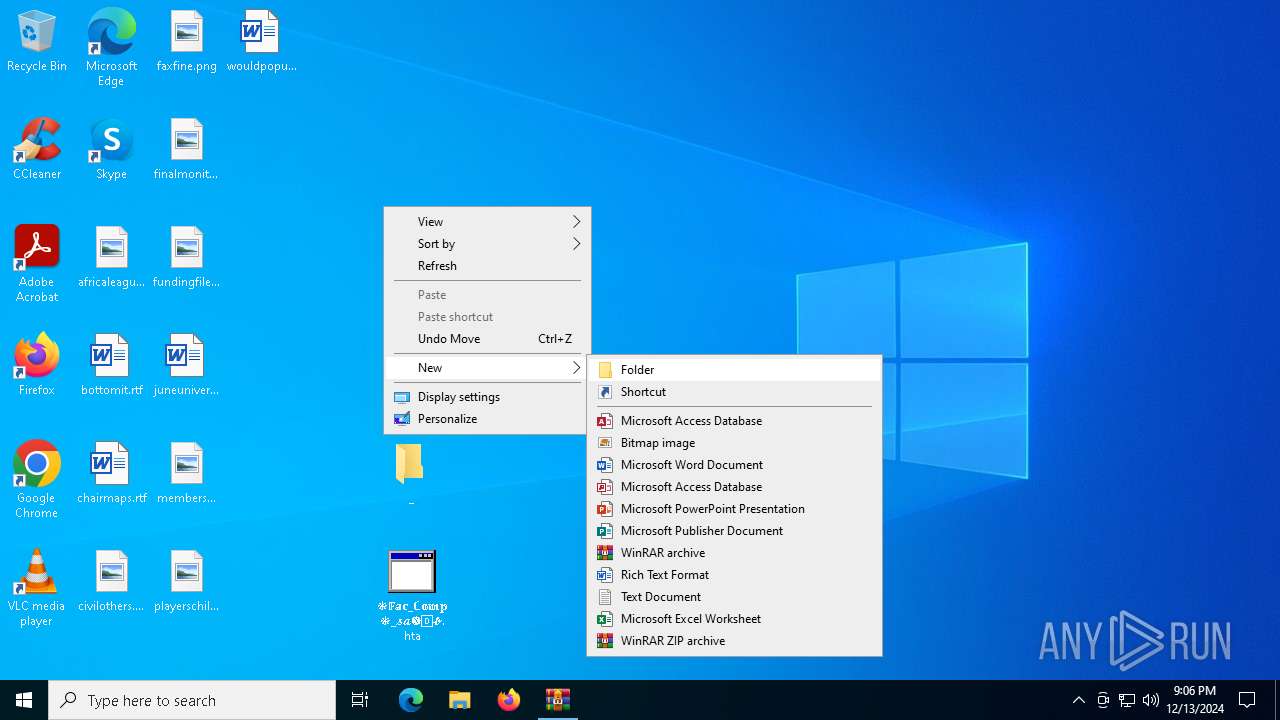
Manual execution by a user
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
- notepad++.exe (PID: 6184)
The sample compiled with english language support
- WinRAR.exe (PID: 6424)
- msedge.exe (PID: 7108)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6424)
- msedge.exe (PID: 7108)
Checks proxy server information
- mshta.exe (PID: 6884)
- mshta.exe (PID: 5460)
Sends debugging messages
- notepad++.exe (PID: 6184)
Application launched itself
- msedge.exe (PID: 2040)
Checks supported languages
- identity_helper.exe (PID: 1220)
Reads the computer name
- identity_helper.exe (PID: 1220)
Reads Environment values
- identity_helper.exe (PID: 1220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:13 21:03:44 |
| ZipCRC: | 0xdcbf5db0 |
| ZipCompressedSize: | 354708 |
| ZipUncompressedSize: | 373104 |
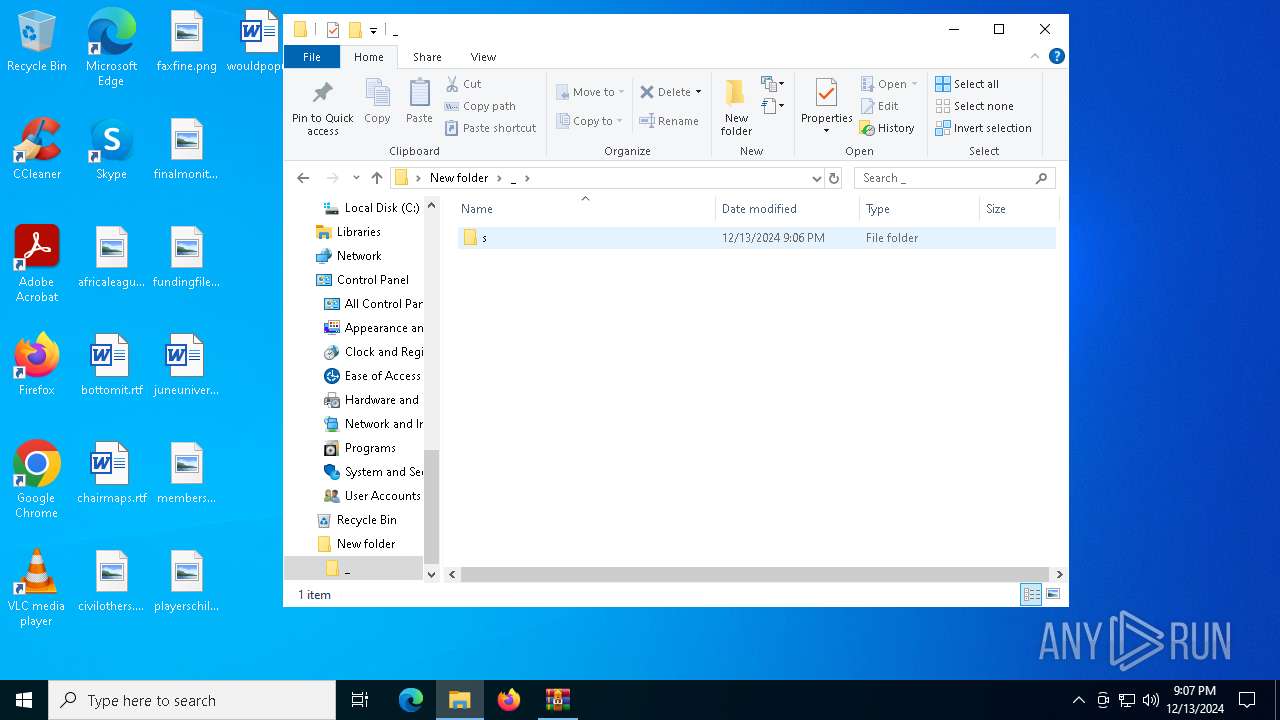
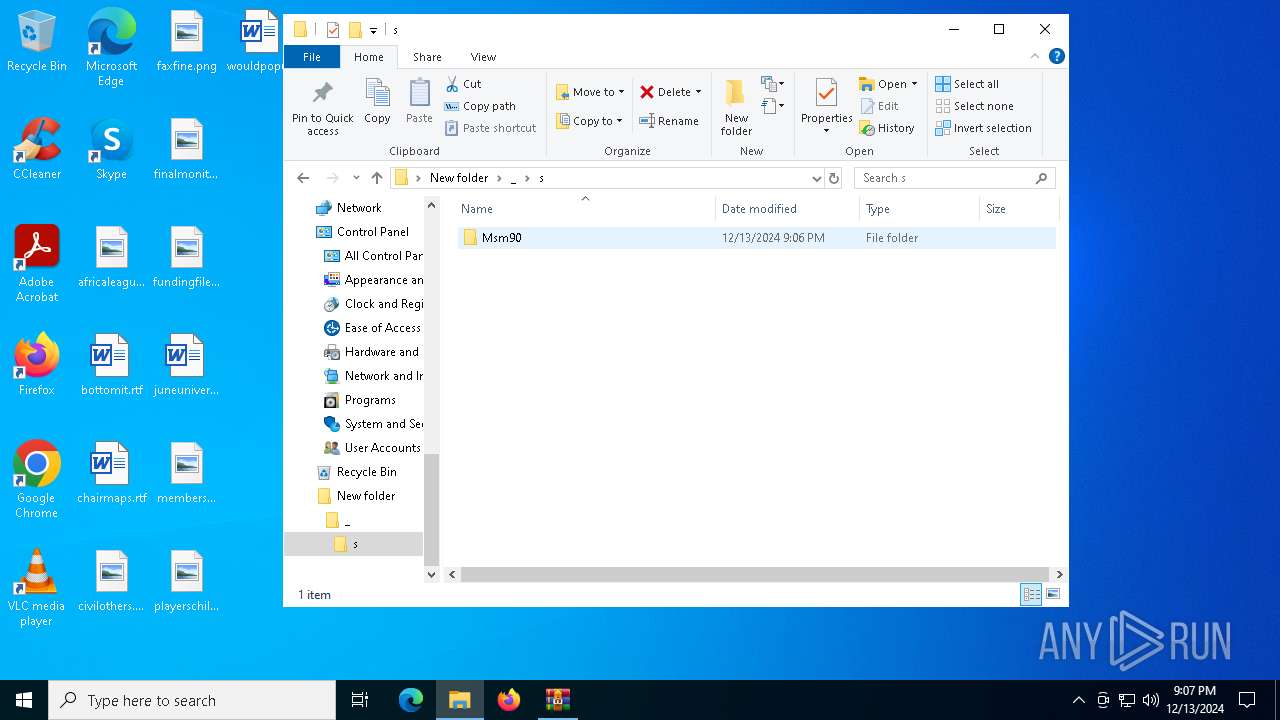
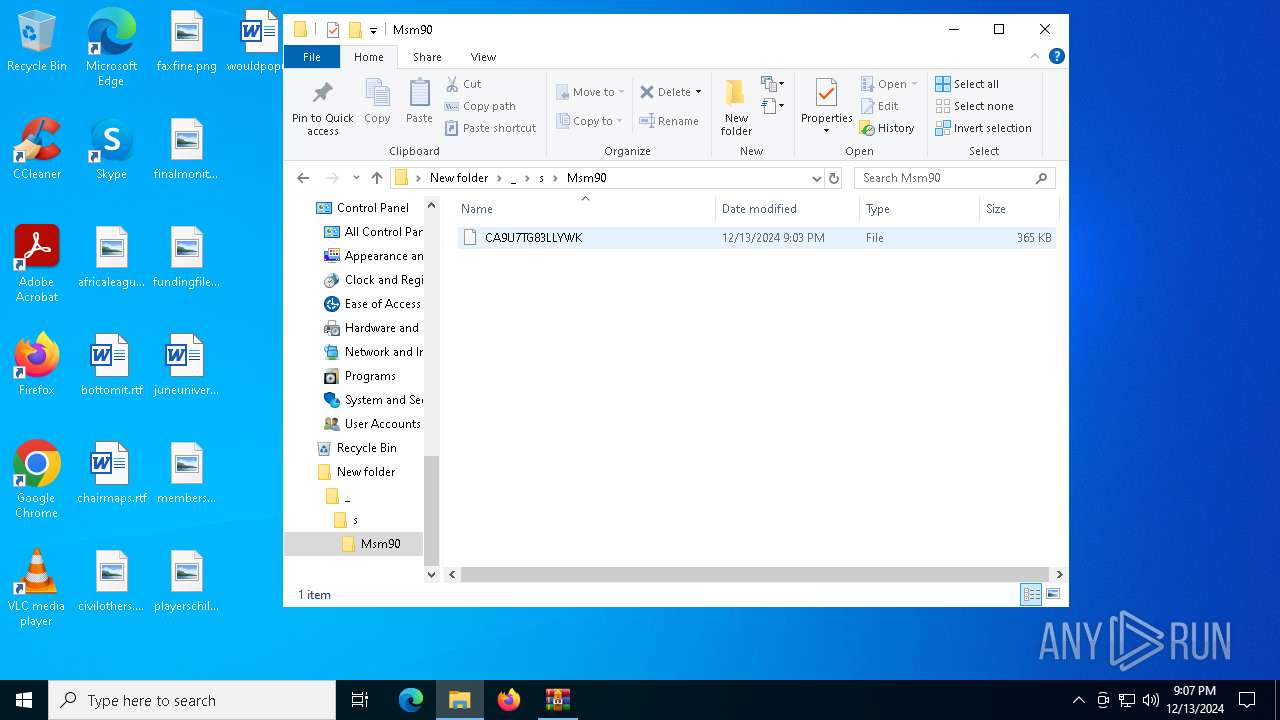
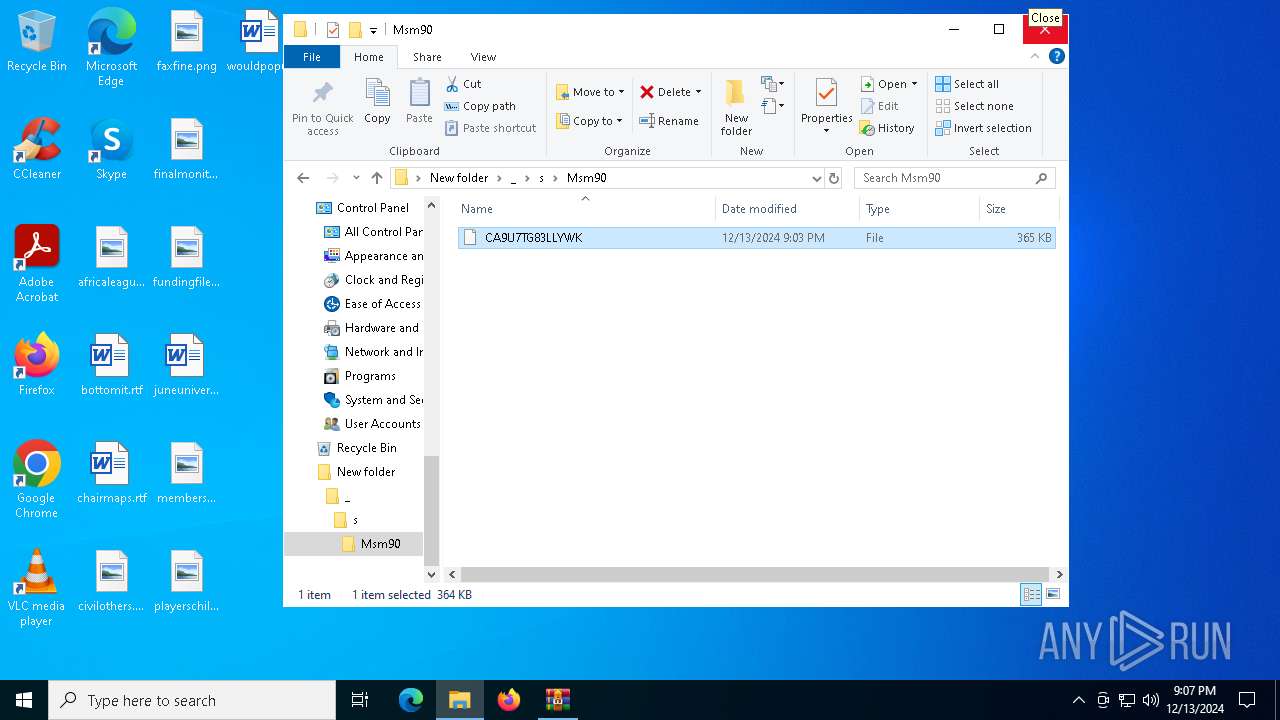
| ZipFileName: | /\s/Msm90/ CA9U7TG83LLYWK |
Total processes
182
Monitored processes
59
Malicious processes
2
Suspicious processes
0
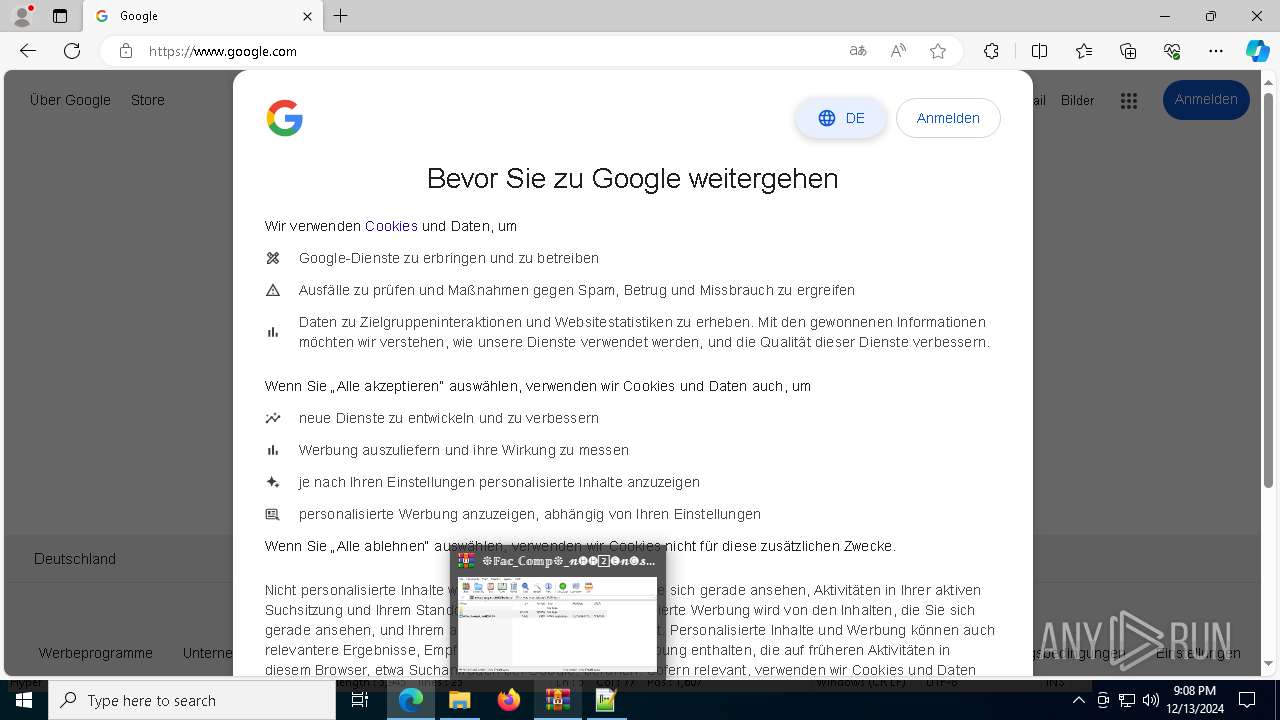
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6476 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4420 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1220 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6176 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1292 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5692 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4612 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3604 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5304 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
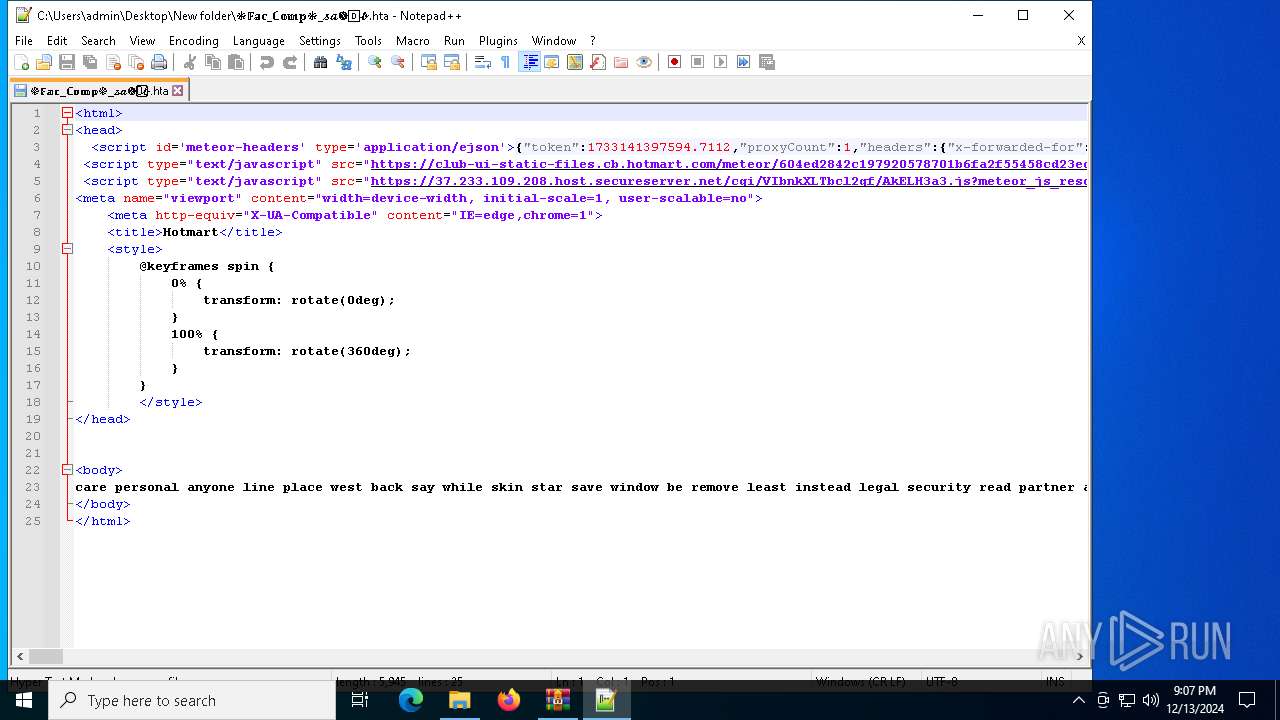
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://37.233.109.208.host.secureserver.net/cgi/VIbnkXLTbcl2gf/AkELH3a3.js?meteor_js_resource=true | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | notepad++.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5608 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6604 --field-trial-handle=2488,i,5615379144880863693,11748894011444692538,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
8 503
Read events
8 463
Write events
40
Delete events
0
Modification events
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\❉𝔽𝕒𝕔_ℂ𝕠𝕞𝕡❉_𝓷🅗🅗2⃣🅔𝓷🅖𝓼.zip | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6884) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6884) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
6
Suspicious files
401
Text files
110
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
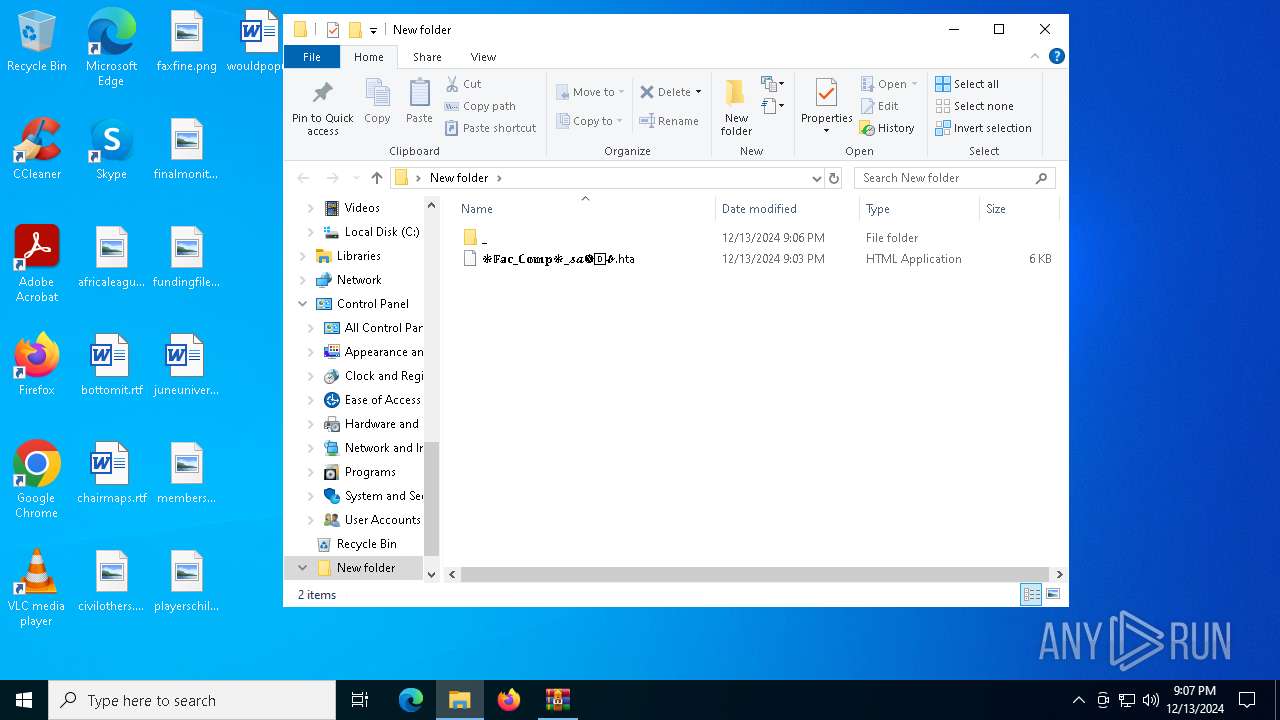
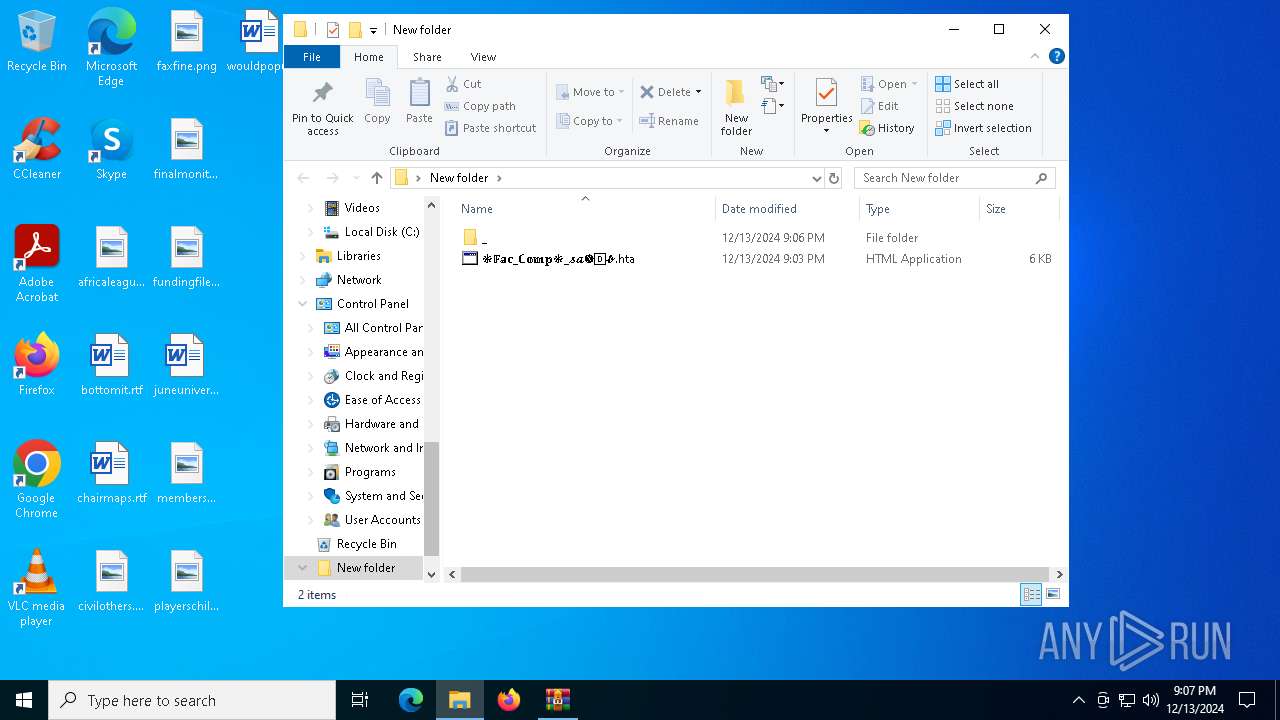
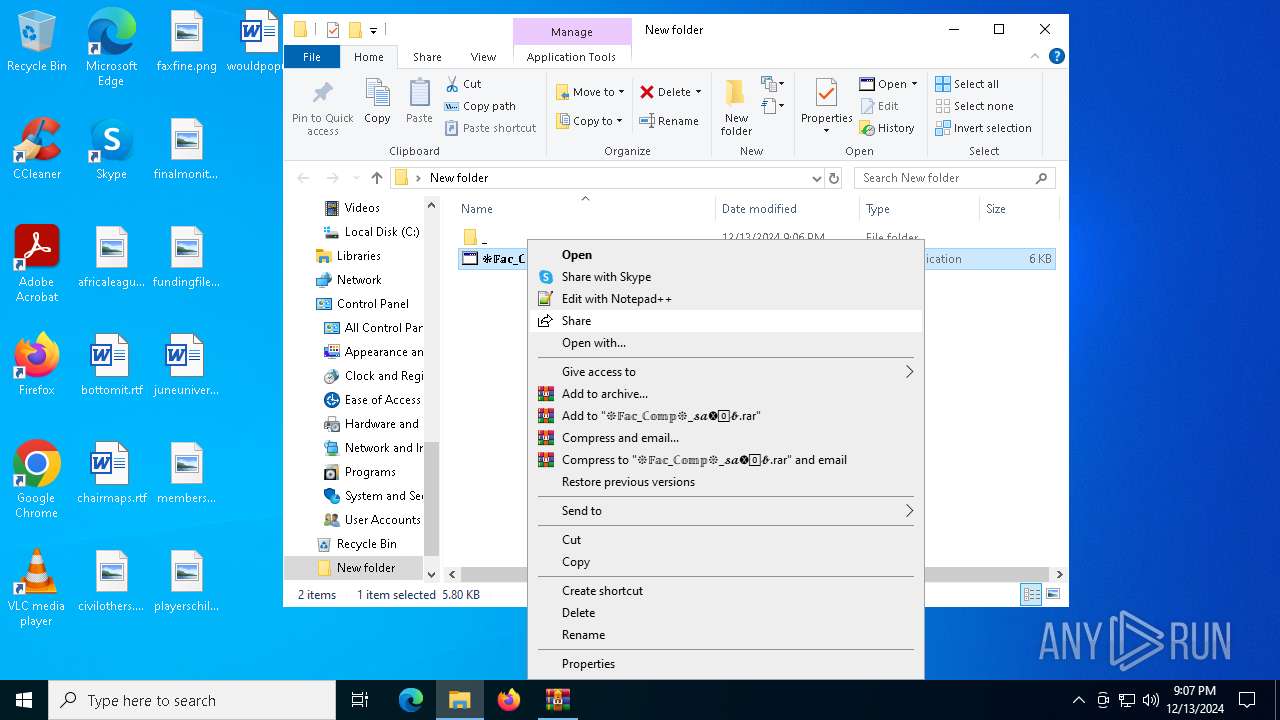
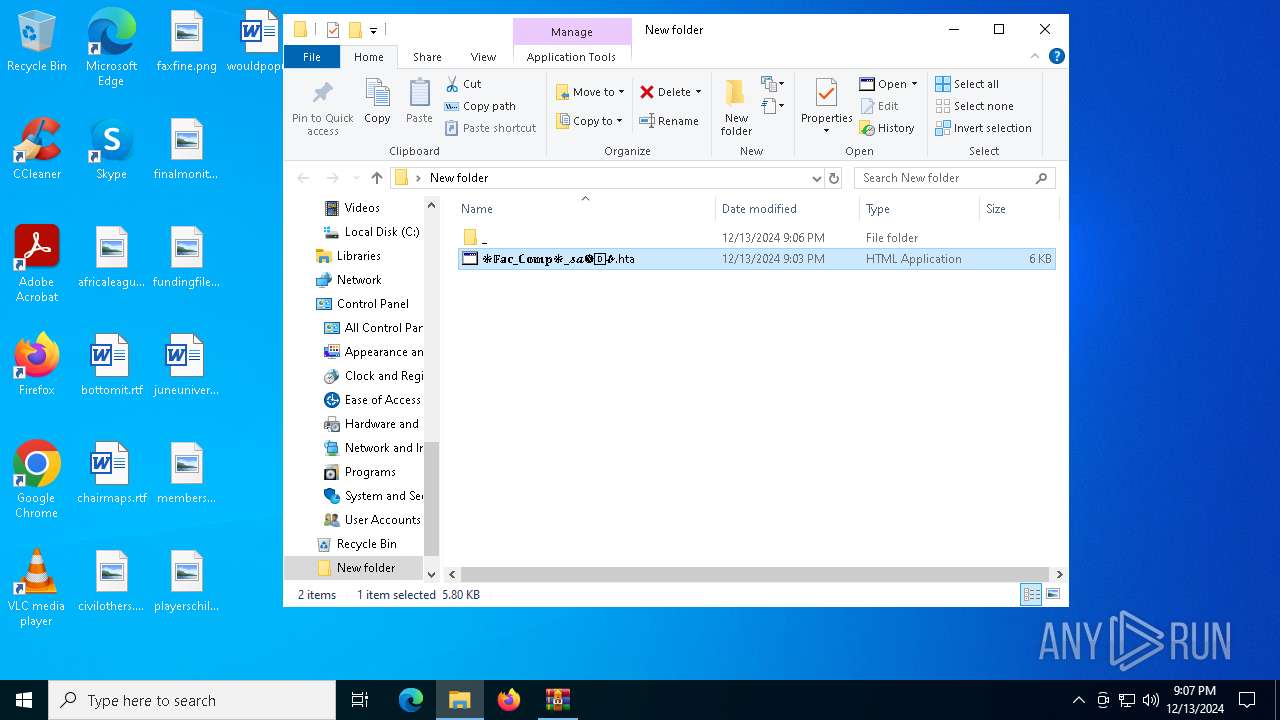
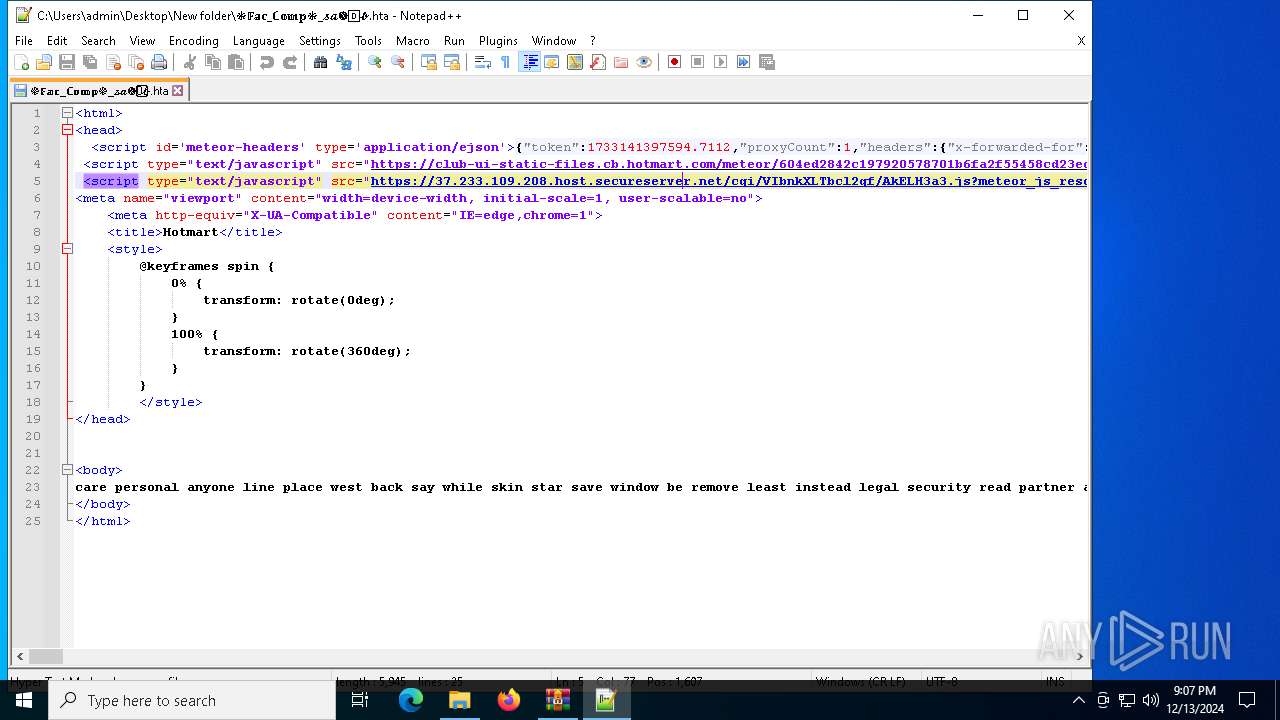
| 6424 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6424.31113\❉𝔽𝕒𝕔_ℂ𝕠𝕞𝕡❉_𝓼𝓪🅧0⃣𝓫.hta | html | |
MD5:7B1D05E8AB2188CD1259886EE6BF0A0A | SHA256:AF8D757F5FC7AD3887C0A2BDF99A8C7388D693854E58B7DB6CAC8652BED0F23C | |||
| 6424 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6424.31113\_\s\Msm90\ CA9U7TG83LLYWK | executable | |
MD5:B28B54B38F5CD12BDB8139006CF4E840 | SHA256:764D6E3DDB8A9D9AFE701E05FFE5A3E5F807A069FC1EEB4EE8B164A0A211CFC3 | |||
| 6884 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3DFCA46E00FFA4795C72A41375F159D3 | SHA256:DCBA1A505396539BAC40A7253C9F5DCCF06CBB79957E21D56305E1FC3AF5F40E | |||
| 6884 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\cid[1].htm | xml | |
MD5:E07F5838B0A1AC6C388CE3066D27DF8F | SHA256:FA9AC1EFF0D8BFCD949BE9A0D4049D0E775DF6A955F12AF7612A5BC56FE829A4 | |||
| 6884 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3F31858D3C5AF811791DCCEE0B3F72C8 | binary | |
MD5:F3BF516C2F27848FD7D3F8F905E4B7DC | SHA256:4C0CAB43677271B748F4F784213A48ED232486AAFAD0EB632188D2A2923BD8AE | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1491ce.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1491de.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1491de.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
95
DNS requests
93
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6200 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2892 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
444 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555338&P2=404&P3=2&P4=CqXMn5S%2b69JA5T4LhNVJspgpptIlIRQ2UrQ75gNuXKZSEcXqQVizqZw1ijisczYS%2fyEa6AciTUbrRU%2b4lupcYw%3d%3d | unknown | — | — | whitelisted |
444 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555338&P2=404&P3=2&P4=CqXMn5S%2b69JA5T4LhNVJspgpptIlIRQ2UrQ75gNuXKZSEcXqQVizqZw1ijisczYS%2fyEa6AciTUbrRU%2b4lupcYw%3d%3d | unknown | — | — | whitelisted |
6884 | mshta.exe | GET | 200 | 2.16.202.121:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgPieppUddNlEt5PgIEXQIXD4w%3D%3D | unknown | — | — | whitelisted |
6200 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6688 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
444 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555338&P2=404&P3=2&P4=CqXMn5S%2b69JA5T4LhNVJspgpptIlIRQ2UrQ75gNuXKZSEcXqQVizqZw1ijisczYS%2fyEa6AciTUbrRU%2b4lupcYw%3d%3d | unknown | — | — | whitelisted |
444 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555338&P2=404&P3=2&P4=CqXMn5S%2b69JA5T4LhNVJspgpptIlIRQ2UrQ75gNuXKZSEcXqQVizqZw1ijisczYS%2fyEa6AciTUbrRU%2b4lupcYw%3d%3d | unknown | — | — | whitelisted |
444 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555338&P2=404&P3=2&P4=CqXMn5S%2b69JA5T4LhNVJspgpptIlIRQ2UrQ75gNuXKZSEcXqQVizqZw1ijisczYS%2fyEa6AciTUbrRU%2b4lupcYw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4872 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1356 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1356 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1356 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
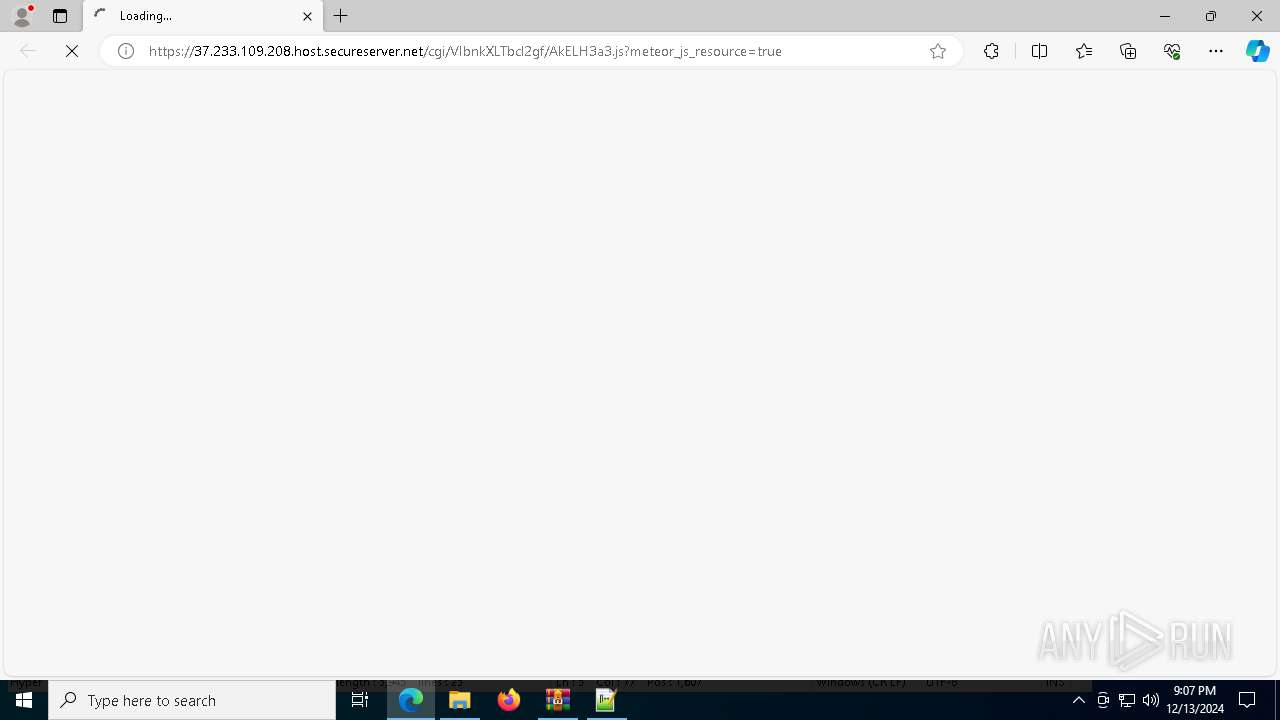
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
club-ui-static-files.cb.hotmart.com |
| unknown |
37.233.109.208.host.secureserver.net |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|