| File name: | 553d21ec9c4e8a08d072e50f3ae0afe1.exe |
| Full analysis: | https://app.any.run/tasks/48d74232-32be-4755-857d-709334e024bc |
| Verdict: | Malicious activity |
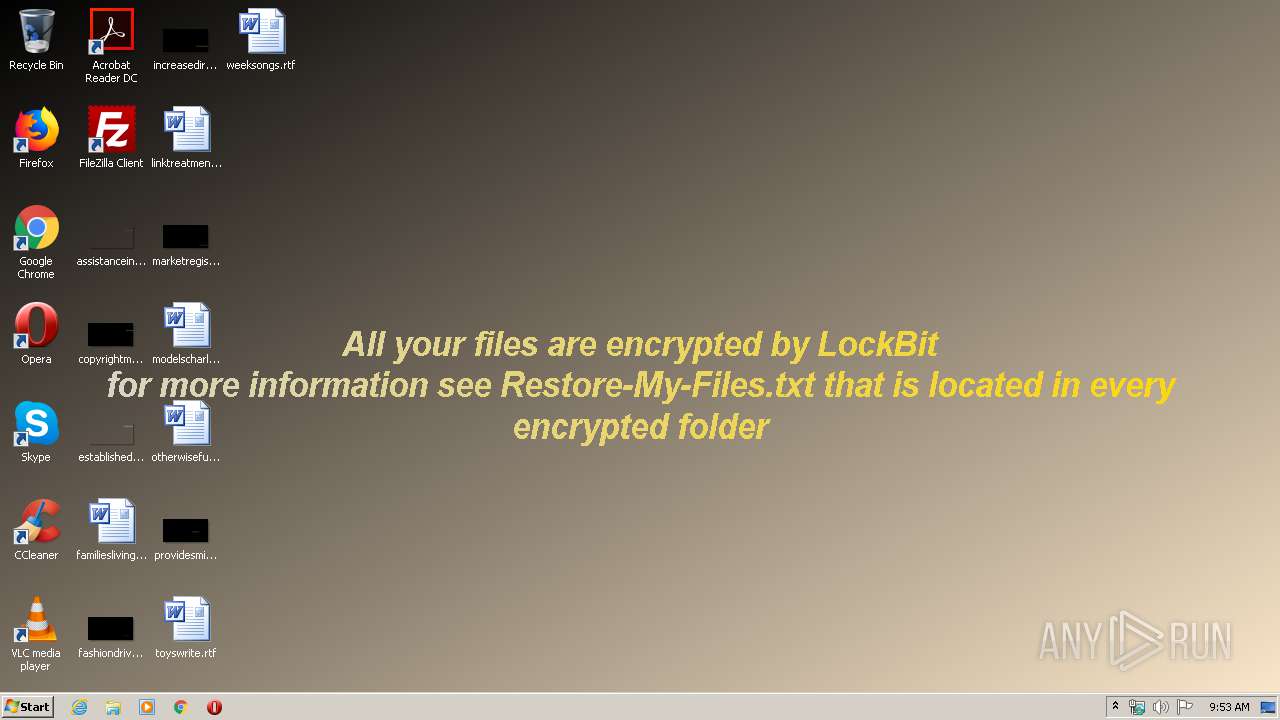
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | March 31, 2020, 08:52:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 553D21EC9C4E8A08D072E50F3AE0AFE1 |
| SHA1: | D3ED3BAB0119C38CF0BE0E7039A3A501C0978E75 |
| SHA256: | A0085DA4A920E92D8F59FEFA6F25551655CA911382B5E34DF76A9333AC8B7214 |
| SSDEEP: | 3072:pm3/OyVPX/1jTCAR4fsp0Vb2xosM89QJ49cqO2DDHMqqD/Tx0Hv/:pq/1VP1OyysNmJyXsqqD/ls/ |
MALICIOUS
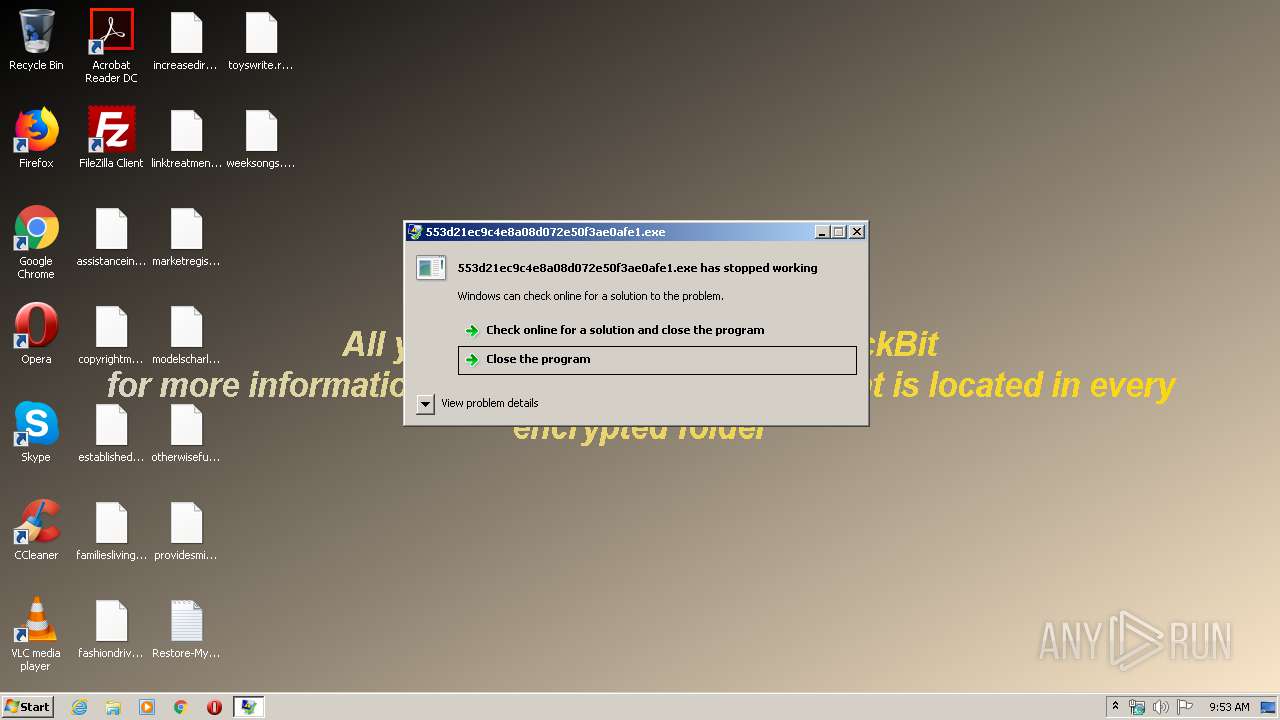
LOCKBIT was detected
- 553d21ec9c4e8a08d072e50f3ae0afe1.exe (PID: 2480)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 2784)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 2556)
Deletes shadow copies
- cmd.exe (PID: 2672)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 2836)
Loads the Task Scheduler COM API
- wbengine.exe (PID: 3772)
Changes the autorun value in the registry
- 553d21ec9c4e8a08d072e50f3ae0afe1.exe (PID: 2480)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2804)
- DllHost.exe (PID: 3336)
- vdsldr.exe (PID: 880)
Starts CMD.EXE for commands execution
- 553d21ec9c4e8a08d072e50f3ae0afe1.exe (PID: 2480)
Uses WEVTUTIL.EXE to clean Windows Eventlog
- cmd.exe (PID: 3560)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 3964)
- cmd.exe (PID: 1084)
- cmd.exe (PID: 2540)
Executed as Windows Service
- wbengine.exe (PID: 3772)
- vds.exe (PID: 1724)
- vssvc.exe (PID: 2852)
Low-level read access rights to disk partition
- vds.exe (PID: 1724)
- wbengine.exe (PID: 3772)
Creates files in the Windows directory
- wbadmin.exe (PID: 2128)
Creates files in the program directory
- 553d21ec9c4e8a08d072e50f3ae0afe1.exe (PID: 2480)
INFO
Dropped object may contain Bitcoin addresses
- 553d21ec9c4e8a08d072e50f3ae0afe1.exe (PID: 2480)
Dropped object may contain TOR URL's
- 553d21ec9c4e8a08d072e50f3ae0afe1.exe (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:17 06:58:42+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 126464 |
| InitializedDataSize: | 35328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b160 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Feb-2020 05:58:42 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Feb-2020 05:58:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001EDCB | 0x0001EE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36479 |
.rdata | 0x00020000 | 0x0000642A | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.95283 |
.data | 0x00027000 | 0x00002350 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.60241 |
Imports
ADVAPI32.dll |
CRYPT32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
NETAPI32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WS2_32.dll |
Total processes
110
Monitored processes
50
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | /c wbadmin DELETE SYSTEMSTATEBACKUP -deleteOldest | C:\Windows\system32\cmd.exe | — | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294967293 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 348 | /c wmic SHADOWCOPY /nointeractive | C:\Windows\system32\cmd.exe | — | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 44124 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 880 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | /c wevtutil cl application | C:\Windows\system32\cmd.exe | — | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1440 | /c wevtutil cl security | C:\Windows\system32\cmd.exe | — | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1488 | wmic SHADOWCOPY /nointeractive | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 44124 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | "C:\Users\admin\AppData\Local\Temp\553d21ec9c4e8a08d072e50f3ae0afe1.exe" | C:\Users\admin\AppData\Local\Temp\553d21ec9c4e8a08d072e50f3ae0afe1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1724 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | vssadmin Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | wbadmin DELETE SYSTEMSTATEBACKUP -deleteOldest | C:\Windows\system32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
925
Read events
907
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2804) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ICM\Calibration |
| Operation: | write | Name: | DisplayCalibrator |
Value: C:\Users\admin\AppData\Local\Temp\553d21ec9c4e8a08d072e50f3ae0afe1.exe | |||
| (PID) Process: | (3336) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3336) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2480) 553d21ec9c4e8a08d072e50f3ae0afe1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | XO1XADpO01 |
Value: "C:\Users\admin\AppData\Local\Temp\553d21ec9c4e8a08d072e50f3ae0afe1.exe" | |||
| (PID) Process: | (2480) 553d21ec9c4e8a08d072e50f3ae0afe1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2480) 553d21ec9c4e8a08d072e50f3ae0afe1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2480) 553d21ec9c4e8a08d072e50f3ae0afe1.exe | Key: | HKEY_CURRENT_USER\Software\LockBit |
| Operation: | write | Name: | full |
Value: 80B8209C20CAAB6605D29782719EE41810ECEF86A158900CC8FE49AEE8E4D7E22935DBFCE4A1E3E14469F10D04B7E6E5BEEFBA87FFDA604969B054EF62419811FCBE6429DEE17FACE556A46F14C29EFF29FCCE4A1050015A40B394A3A72C409CBEEBCD707E581ED22C431AA80E66B04BD8B53D0BF071898615F2230CCFBC465CD4D109FC048EB41610604EB4D03FD48812A8D7E827E466CA26A74EFE78B5FC990A538DDAC4174E2FA4A679122E6FCE5BB22B244AD21C0DD755844429007F9324FAF989A9B41F5D144CB137B1433972073C9F98559B363D3A6E7CE0D9B1334F2FCACCE68F59B14098D8078518BE635F3C0948A6765AF995FC28A4B3735D997D2F4EECE438A8BBD2856CA6DD6BE981AF6394AE6F6AFF1160EC6A80C9FCC82A3AAFA01D711961B445B4C424466F2A8FB5BE700E4CC230EC1C9122C5ECC1A15A0F5143F9727E940A7F78A638C5A122FE48EE045D6E9D236711C7B87CEC615886300478921BF9B19EA9487DF4B0322D327ED9E6E1CD502E23EC901D1789E2EFCCFFA3227C6E70706B05332876153B399F9D70CD25B90CFDAA788297C4590E48BC353B46135EC5AF743F8F51BA1F76DA9B0574F23739F158158A061EB1FAE9A3E6AE2436624C5128B06E8819D17B78F67E3392D5D99D88BE0ADBD627A13830CF3F8923D75F41FE15625023FB9D62F8D870CA7502C556BCEC44498BEEC017AE57EC871F00EF66FE1626929810CBC24BBF998536FA20C75A099369F770E39C2A8F1F1AA758AA31E68225551FBC409D956D54018899F2CB791F31BC3F5E727226FCB8374B263CE7EBD8DD5E8BF2749A7D811D1740708EB0352478D245159CE2561DB78348D8A34742B583179D925EC1A2EB818F0B9C27ED24A1A1F9B9B1E7CF22D6A01846CACFEFF445AD61AA9A1524184AC40C6645D10CC98D7FA9CF202983B2ECBC014EA00A9BBA6DA99943D726C976E7E5A143960516C743DEB650EA9B05F091E209271ADC5DED231205E0FB856F85A64EAF90D3EDC69BBEB2F297761BC4D1961A4D375266DFB046053DE8F2EE40DF812F18B6C776BE185AD06452ACB1B240672E537C559FA10126E0412B5024122033C3363BEA38410BA1072F462AEAC3EC70A309FAB999EA6647E890A4582CE7B9772940DB5CB310DB348B696BF2B2BDA40B459A091251C49EFCCC6459E1D78E347DC44200BE05CCB9DFA9D0CA8A54D1FF136C621EA7603B02C888B2FB06A04CD6EFCEE745BBDAFF914357EDCE87EB6FEBF7079F6D742154F3C4E5F531419FD4A347AC3DDA3042F620D773775DD9731EBE9E0CC42E63135FF1FB681B01387467C5B21CD55ED099EACB719ECEF87E879E961C9B6A3B5CF49F5D336F6A3525C2658BB53F3D805CE1B15ABB0578759619A61884A3FCAAEADD60201E173B6FCBA572741F2DE3241E0FA19595E45C6FFE9C8848AD491BC21DB11C79806005C7FA48E4F0B85AFAE2701DFD48DF85949C39A2E4C5B76D87C9339BD8BE37DF71CDE85824A50573C66581C3FF2E2BD0B588007A9B7AD8D2C5BE1873EEA76AB818099FB9ED7146CE2A7412FA5031079FAC463E0AA0B48B78AA3EE675085CDF7551BD5D41653F17D889853B38DB1F7F485244A5F37DEC3778A541E1F76457EED04C3C933DB4D1E83932F69404871CCBC435B9F7393A818FAB4231FE0553DB78E0A91003E84B42EB75E7BADDA7599B785322E8858EE58740A2E26427A38A7358B4E92A449157DE91346C53A71AFA7B2BCD76BDFF282E0A64D1D261755C72C80E8F3F5089AA2BB8E2FD90D0D6079FCA2809A3066694915525CF87D7 | |||
| (PID) Process: | (2480) 553d21ec9c4e8a08d072e50f3ae0afe1.exe | Key: | HKEY_CURRENT_USER\Software\LockBit |
| Operation: | write | Name: | Public |
Value: E9B343B8BA155E5BF4633FB2B09A912D6A8EFC7D6B7BC6890FA7FEC223195D4E4A229501021B7663B119CD5E7DAFFC0173C89C2544CE570AC82BEFBBB0803DF8E381DC0D963262880634EB259FA53F6D1B95CF39EB4CAEAA9237684AC6B3C7D9DDECA1DE1337C430F10B80C197AD76AEF718573E661B1D12E7A72599E32D72A6739FED22FCEC39B4326AF3F882CE78191B4A35D4F8F3FDB9F1FCF6A8BCC19EDCB3754C0CD7973A8FD2BF768B78FF57C78930B523832C625769A701AE9580678AA6A6146529B62CE998D368DB6501F2DC64CE3A894B999D5F7C07966E03BB8F9B0C82041FC32CC11A5B441A6D3F2D7100292967BD7BA6A605D06A2534CECC1AD5010001 | |||
| (PID) Process: | (3560) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\16000009 |
| Operation: | write | Name: | Element |
Value: 00 | |||
| (PID) Process: | (3824) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\250000e0 |
| Operation: | write | Name: | Element |
Value: 0100000000000000 | |||
Executable files
0
Suspicious files
3 036
Text files
360
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Restore-My-Files.txt | text | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Leame.htm.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Benioku.htm.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Lisezmoi.htm.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\LueMinut.htm.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\CAT\Combine_R_RHP.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Llegiu-me.htm.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Restore-My-Files.txt | text | |
MD5:— | SHA256:— | |||
| 2480 | 553d21ec9c4e8a08d072e50f3ae0afe1.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\1494870C-9912-C184-4CC9-B401-A53F4D8DE290.pdf.lockbit | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report