| File name: | wps_lid.lid-e8M7cwwtRpZi.exe |
| Full analysis: | https://app.any.run/tasks/fbb2bf0b-0927-4d52-b738-611fd28b12f4 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2025, 16:17:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 24BDD69ADCAEE407F4F7C75737438DCE |
| SHA1: | E4DC8EDE51D65253802EC51972ADED07DBF2E7DD |
| SHA256: | 9FF03B3178FEB91FFB13C96080578ECB33831FCBD7712A6072D1FBA04E2F98ED |
| SSDEEP: | 98304:Oes0MWJAepmDJabqp+Euc0bgUbspkX538WOpWA1jNKO+bkNa1Z2BwtQBS10W9bde:Rrb6aAnqCMG |
MALICIOUS
Drops known malicious document
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
SUSPICIOUS
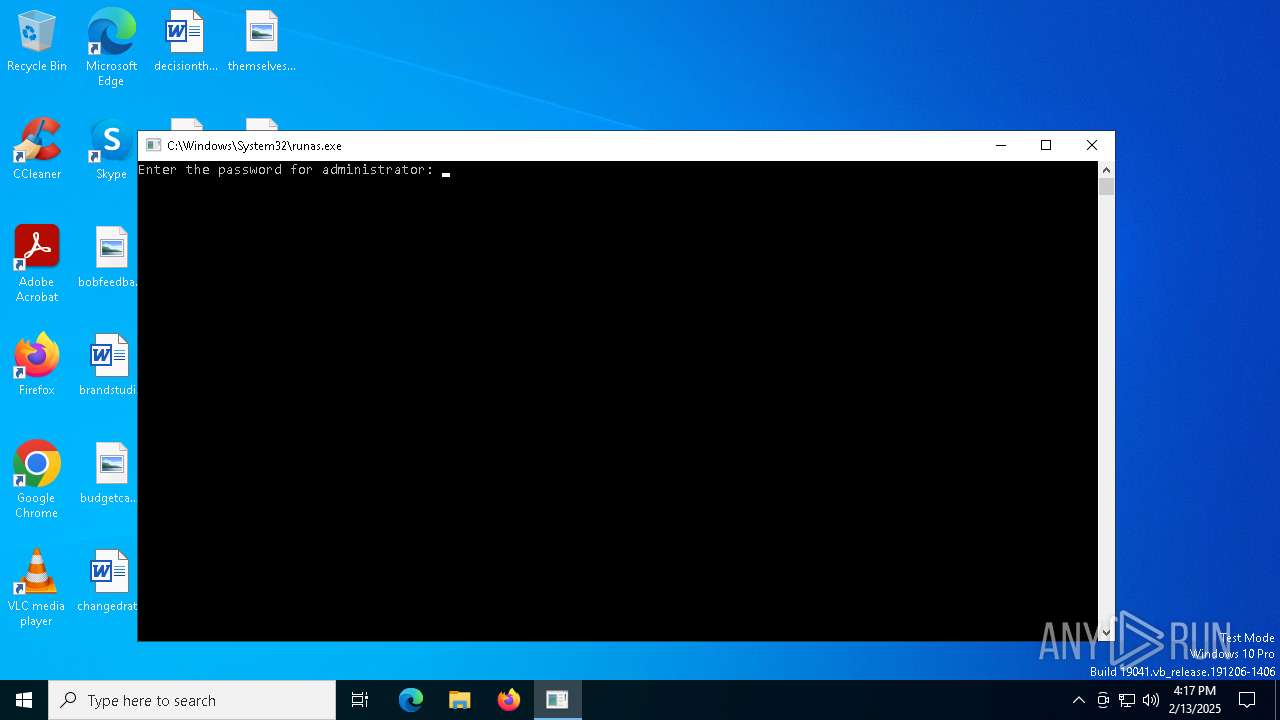
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 6300)
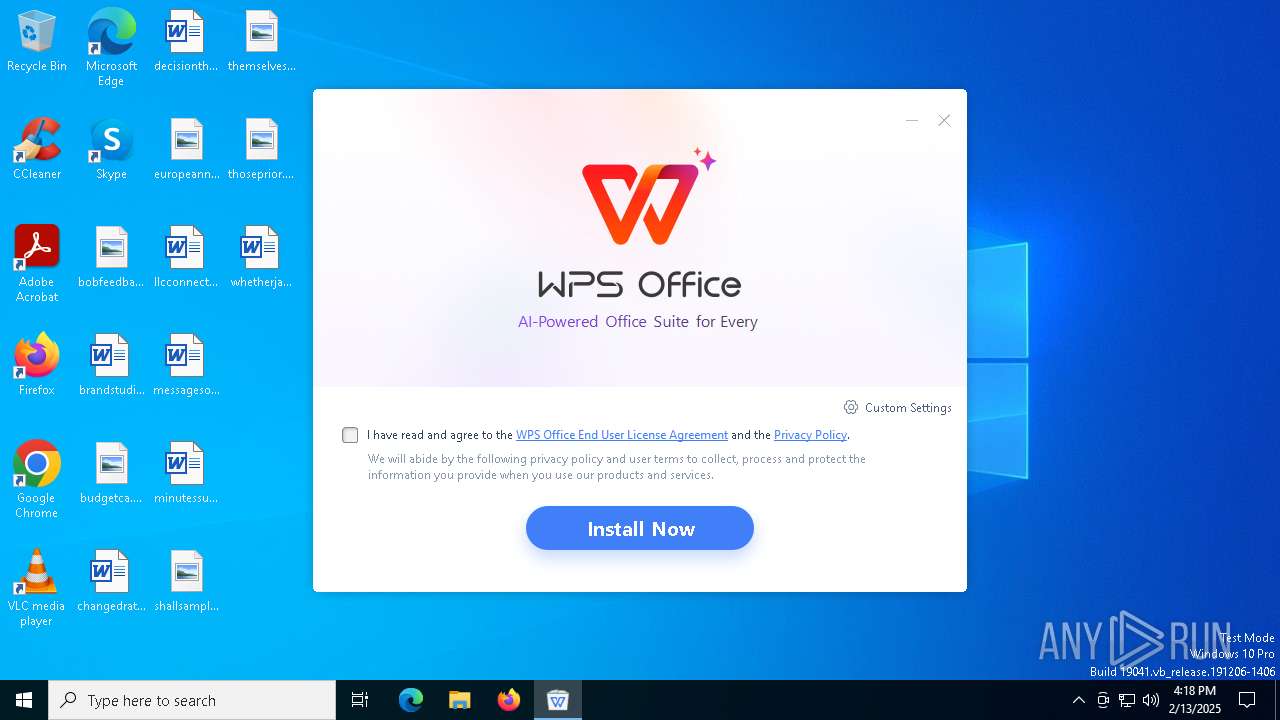
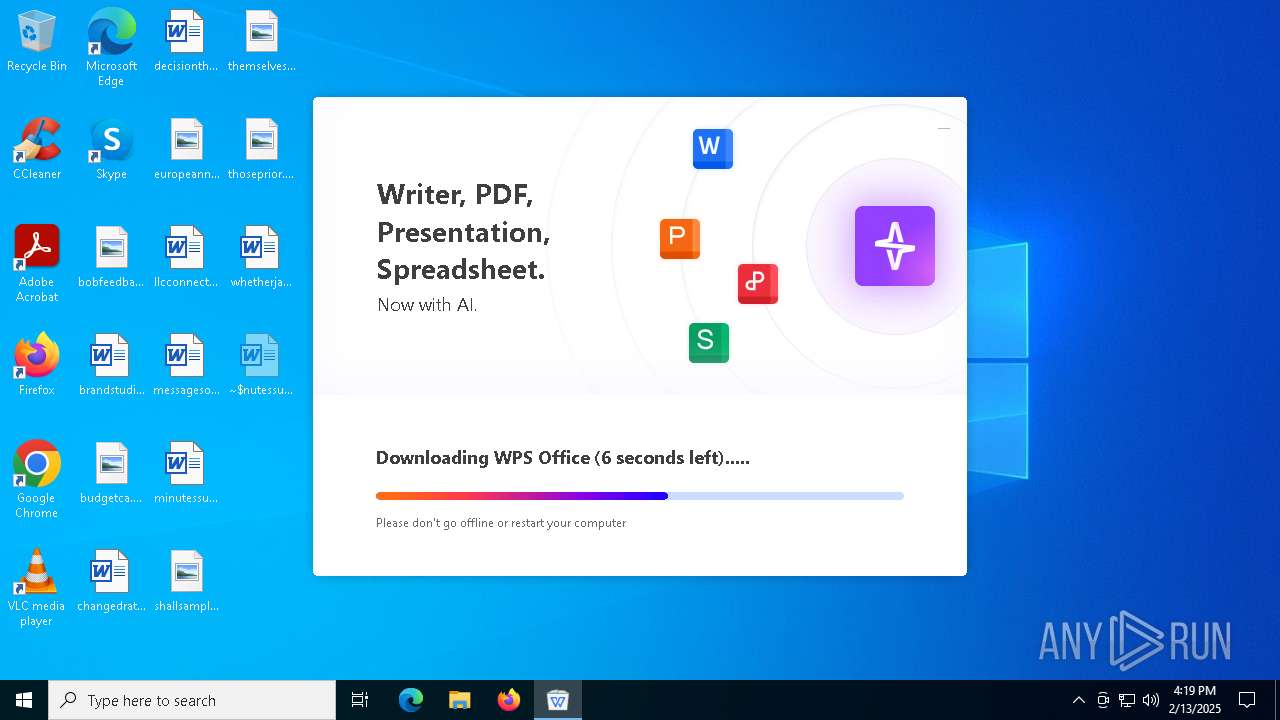
WPS mutex has been found
- wps_lid.lid-e8M7cwwtRpZi.exe (PID: 6948)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 556)
Process drops legitimate windows executable
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
Executable content was dropped or overwritten
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
The process drops C-runtime libraries
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
Reads security settings of Internet Explorer
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
Checks Windows Trust Settings
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
There is functionality for taking screenshot (YARA)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
Write to the desktop.ini file (may be used to cloak folders)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
INFO
Process checks computer location settings
- wps_lid.lid-e8M7cwwtRpZi.exe (PID: 6948)
Reads the machine GUID from the registry
- wps_lid.lid-e8M7cwwtRpZi.exe (PID: 6948)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 556)
Checks supported languages
- wps_lid.lid-e8M7cwwtRpZi.exe (PID: 6948)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 556)
Reads the software policy settings
- wps_lid.lid-e8M7cwwtRpZi.exe (PID: 6948)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 556)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
Create files in a temporary directory
- wps_lid.lid-e8M7cwwtRpZi.exe (PID: 6948)
Reads the computer name
- wps_lid.lid-e8M7cwwtRpZi.exe (PID: 6948)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 556)
Manual execution by a user
- WINWORD.EXE (PID: 3420)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 556)
The sample compiled with english language support
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
Creates files or folders in the user directory
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 556)
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
The sample compiled with japanese language support
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
The sample compiled with chinese language support
- b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe (PID: 6864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:02:11 03:45:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 4097024 |
| InitializedDataSize: | 1440768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x277f35 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.9.0.19236 |
| ProductVersionNumber: | 12.9.0.19236 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
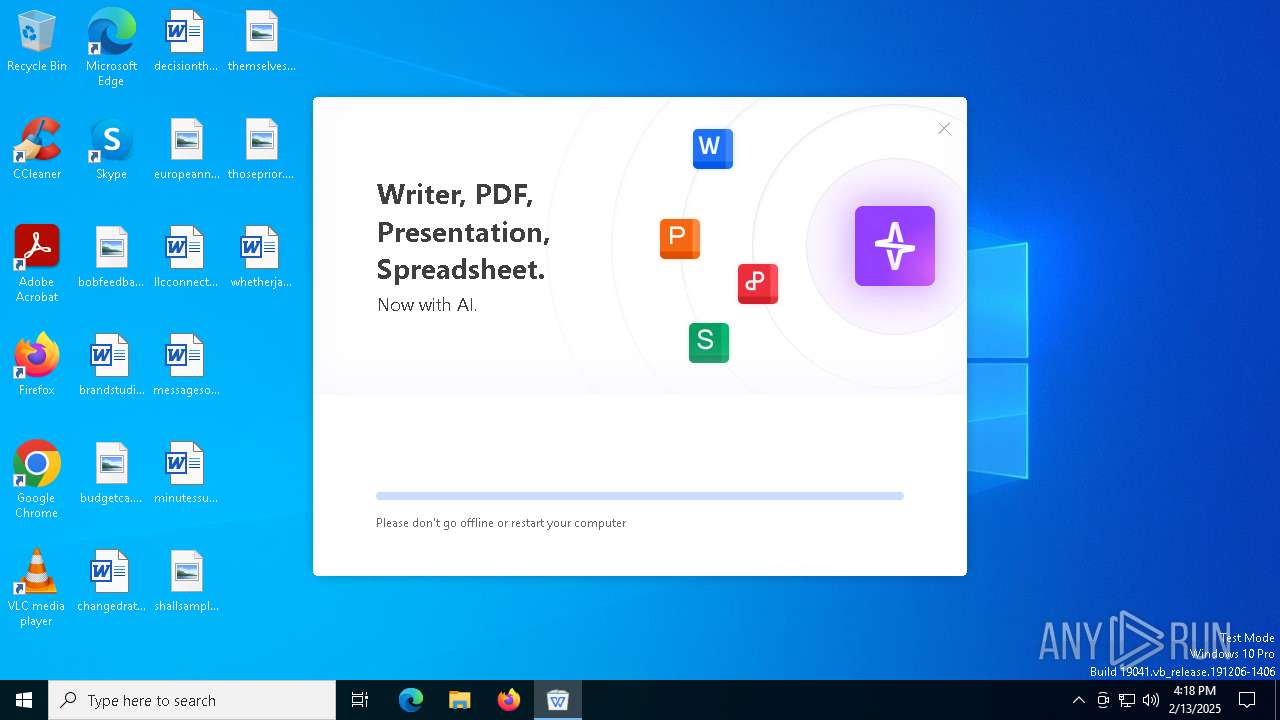
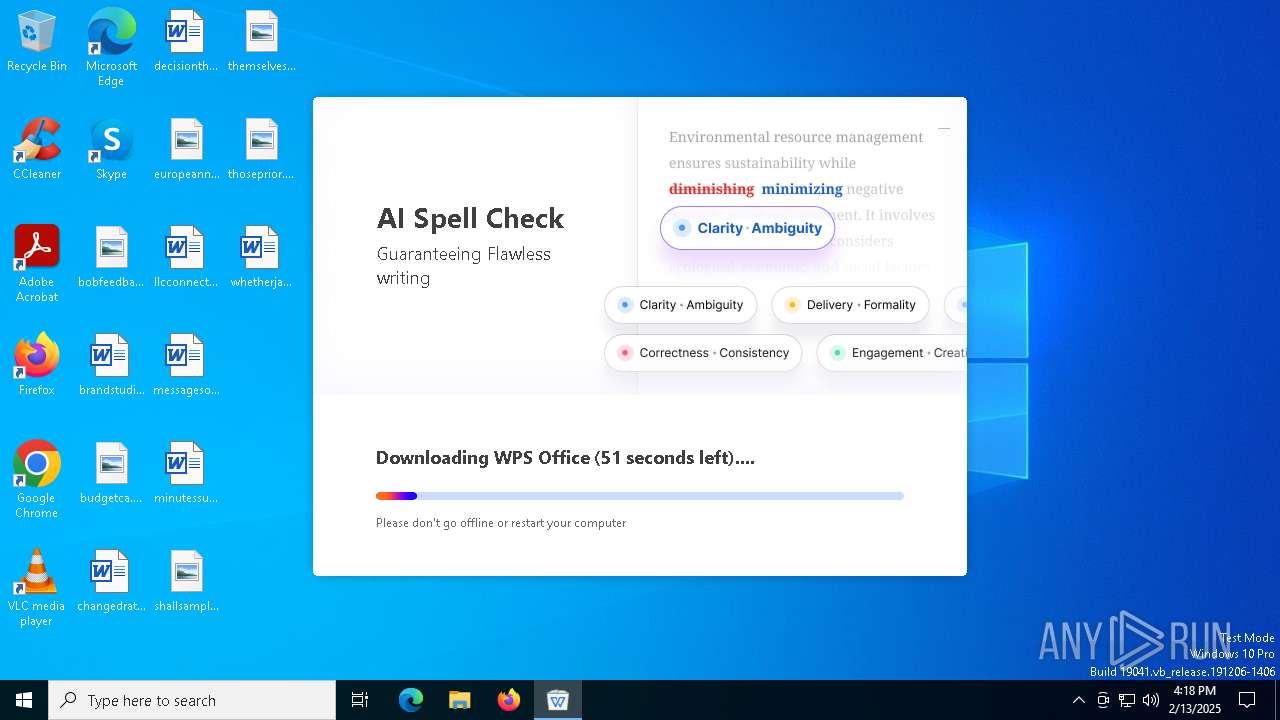
| FileDescription: | WPS Office Setup |
| FileVersion: | 12,9,0,19236 |
| InternalName: | konlinesetup_xa |
| LegalCopyright: | Copyright©2024 Kingsoft Corporation. All rights reserved. |
| OriginalFileName: | konlinesetup_xa.exe |
| ProductName: | WPS Office |
| ProductVersion: | 12,9,0,19236 |
| MIMEType: | - |
Total processes
140
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Users\admin\AppData\Local\Temp\wps_download\b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe" -downpower -installCallByOnlineSetup -defaultOpen -defaultOpenPdf -asso_pic_setup -createIcons -pinTaskbar -curlangofinstalledproduct="en_US" -D="C:\Users\Administrator\AppData\Local\Kingsoft\WPS Office" -enableSetupMuiPkg="C:\Users\Administrator\AppData\Local\Kingsoft\WPS Office" -appdata="C:\Users\Administrator\AppData\Roaming" -msgwndname=wpssetup_message_14BEE9 -curinstalltemppath=C:\Users\ADMINI~1\AppData\Local\Temp\wps\~14a873\ | C:\Users\admin\AppData\Local\Temp\wps_download\b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | explorer.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Install Application Version: 12,2,0,19805 Modules
| |||||||||||||||
| 3420 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\minutessuccessful.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 6300 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\AppData\Local\Temp\wps_lid.lid-e8M7cwwtRpZi.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6308 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6844 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "7B12A392-6B1A-4459-91FA-FC628E71B1A7" "5C112F86-1134-454D-91E4-016F9F3232C2" "3420" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
| 6864 | C:\Users\admin\AppData\Local\Temp\wps_download\b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe -installCallByOnlineSetup -defaultOpen -defaultOpenPdf -asso_pic_setup -createIcons -pinTaskbar -curlangofinstalledproduct=en_US -D="C:\Users\Administrator\AppData\Local\Kingsoft\WPS Office" -enableSetupMuiPkg -appdata="C:\Users\Administrator\AppData\Roaming" | C:\Users\admin\AppData\Local\Temp\wps_download\b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | wps_lid.lid-e8M7cwwtRpZi.exe | ||||||||||||
User: Administrator Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: HIGH Description: WPS Install Application Version: 12,2,0,19805 Modules
| |||||||||||||||
| 6948 | C:\Users\admin\AppData\Local\Temp\wps_lid.lid-e8M7cwwtRpZi.exe | C:\Users\admin\AppData\Local\Temp\wps_lid.lid-e8M7cwwtRpZi.exe | runas.exe | ||||||||||||
User: Administrator Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: HIGH Description: WPS Office Setup Version: 12,9,0,19236 Modules
| |||||||||||||||
Total events
21 268
Read events
20 957
Write events
284
Delete events
27
Modification events
| (PID) Process: | (6948) wps_lid.lid-e8M7cwwtRpZi.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | infoGuid |
Value: CA9F0AA16C6E4200ABDADED488C569B3 | |||
| (PID) Process: | (6948) wps_lid.lid-e8M7cwwtRpZi.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | infoHdid |
Value: 1cf1645444bdcdc4ee428c47695eccce | |||
| (PID) Process: | (6948) wps_lid.lid-e8M7cwwtRpZi.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | onlinesetup_penetrate_id_type |
Value: web | |||
| (PID) Process: | (6948) wps_lid.lid-e8M7cwwtRpZi.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | onlinesetup_penetrate_id |
Value: lid-e8M7cwwtRpZi | |||
| (PID) Process: | (6948) wps_lid.lid-e8M7cwwtRpZi.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Kingsoft\Office\6.0\plugins\kdcsdk |
| Operation: | write | Name: | countrycode |
Value: FR | |||
| (PID) Process: | (6948) wps_lid.lid-e8M7cwwtRpZi.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Kingsoft\Office\6.0\plugins\kdcsdk |
| Operation: | write | Name: | lastupdatecountrycode |
Value: 1739463493658 | |||
| (PID) Process: | (6948) wps_lid.lid-e8M7cwwtRpZi.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Kingsoft\Office\6.0\plugins\kdcsdk |
| Operation: | write | Name: | lastUpdateDeviceInfoDate |
Value: 2025/2/13 | |||
| (PID) Process: | (3420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (3420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\3420 |
| Operation: | write | Name: | 0 |
Value: 0B0E1059F5AF9B062D594EB9BB9FC671A98C8A230046F9C0C1F7AFC6DFED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511DC1AD2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (3420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %,% |
Value: 252C25005C0D00000100000000000000C951FCFE327EDB0100000000 | |||
Executable files
87
Suspicious files
836
Text files
2 415
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:F4E1AF947E4592CAF962F9328A9A4513 | SHA256:445BFEBC99ADBB3B882DB2BF78A83E414D27D5CEB69EF8C708AFDEE52A910284 | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\975002BC.tmp | binary | |
MD5:EF1FA8818BBB17FAEC3C7350D622F2D9 | SHA256:12379444D12FCDEC499D96DD46FFBB3B05EACDD868C461037BC38E753F9BF334 | |||
| 3420 | WINWORD.EXE | C:\Users\admin\Desktop\~$nutessuccessful.rtf | binary | |
MD5:6B41154A003D34B03E6A57E6A93814DC | SHA256:624744A2EADCE68A5A6FC84899CD0DAFBB3AD4AB262108FBD2F644C7EC448F1E | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json | binary | |
MD5:6AEF15731097626AE527CCB4C4734C45 | SHA256:2A0583E779455A0BE3247564DB3C40087B3C42CD1ECB3E00242DFF0D9B7932A1 | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\minutessuccessful.rtf.LNK | binary | |
MD5:D4486435FC277FC7CC517B6C3BC2ACD0 | SHA256:E6C019445F2A168BBC49F4D818CC206308DF64B4F55ACFC479E2C2C6537DE285 | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:6AEF15731097626AE527CCB4C4734C45 | SHA256:2A0583E779455A0BE3247564DB3C40087B3C42CD1ECB3E00242DFF0D9B7932A1 | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:07C7D0DB7E2EEED0FB9116D28B95D567 | SHA256:8BC843BA584FC3C7E15C4C82F91327DA0E6409968BF7D31D1731A92ACBBF1D2A | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:5EB54CFEACF229B4D5ADDDE846BC635A | SHA256:1A30DEDD503AAD9D170517D75960F6414E83344941B64E9C86F5BE3A357E11F5 | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Diagnostics\WINWORD\App1739463543029266300_9BAFF559-2D06-4E59-B9BB-9FC671A98C8A.log | — | |
MD5:— | SHA256:— | |||
| 3420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
53
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3280 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6444 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3280 | svchost.exe | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5556 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5556 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3420 | WINWORD.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 92.123.104.16:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3280 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5968 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
api.wps.com |
| whitelisted |
wdl1.pcfg.cache.wpscdn.com |
| unknown |
Threats
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | [kscreen] isElide:0 switchRec:0 switchRecElide:1 |
b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | QLayout: Attempting to add QLayout "" to QWidget "m_BrandAreaWidget", which already has a layout
|
b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | QLayout: Attempting to add QLayout "" to QWidget "", which already has a layout
|
b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
b0e3565535fc6099fe4f4c9bfb777a13-15_setup_XA_mui_Free.exe.601.1139.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|