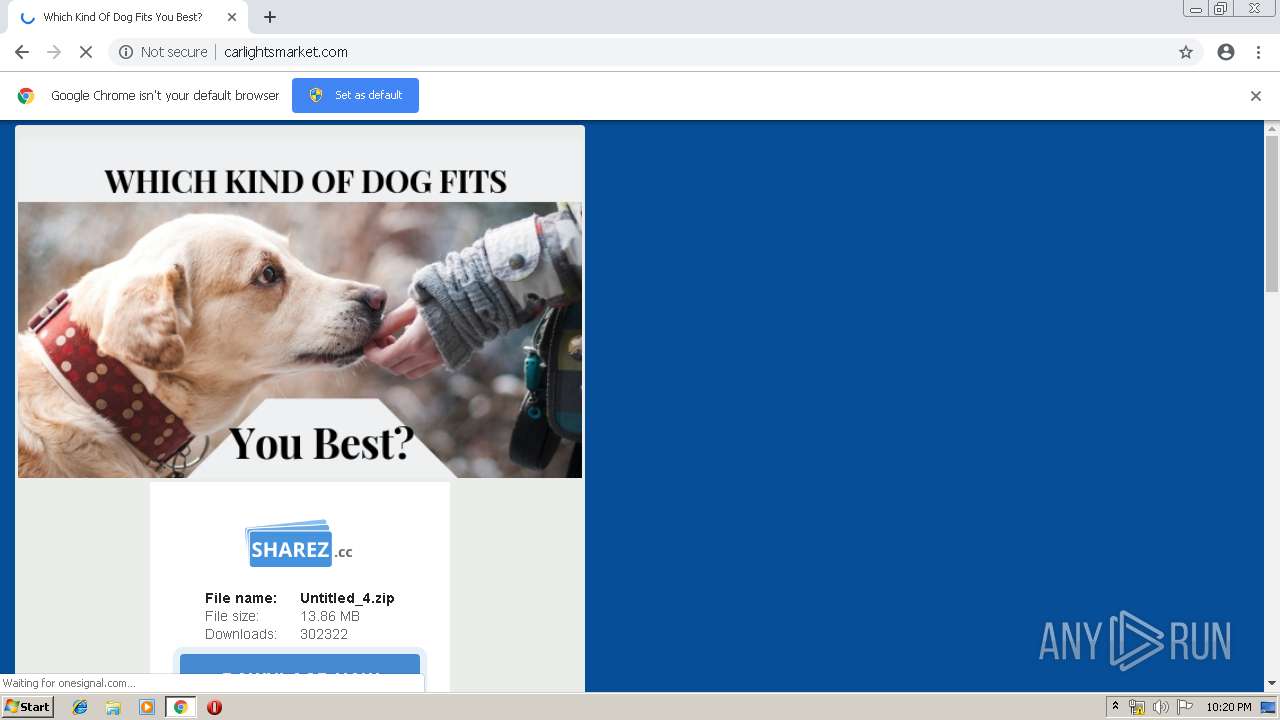
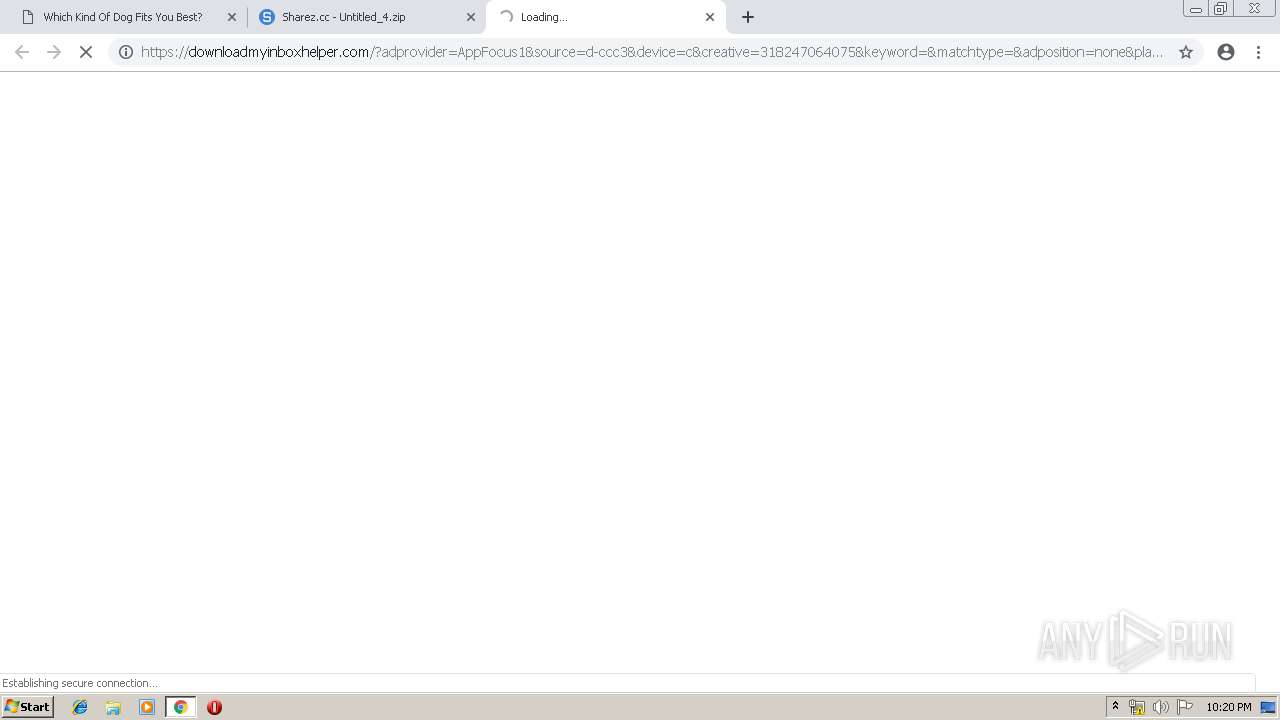
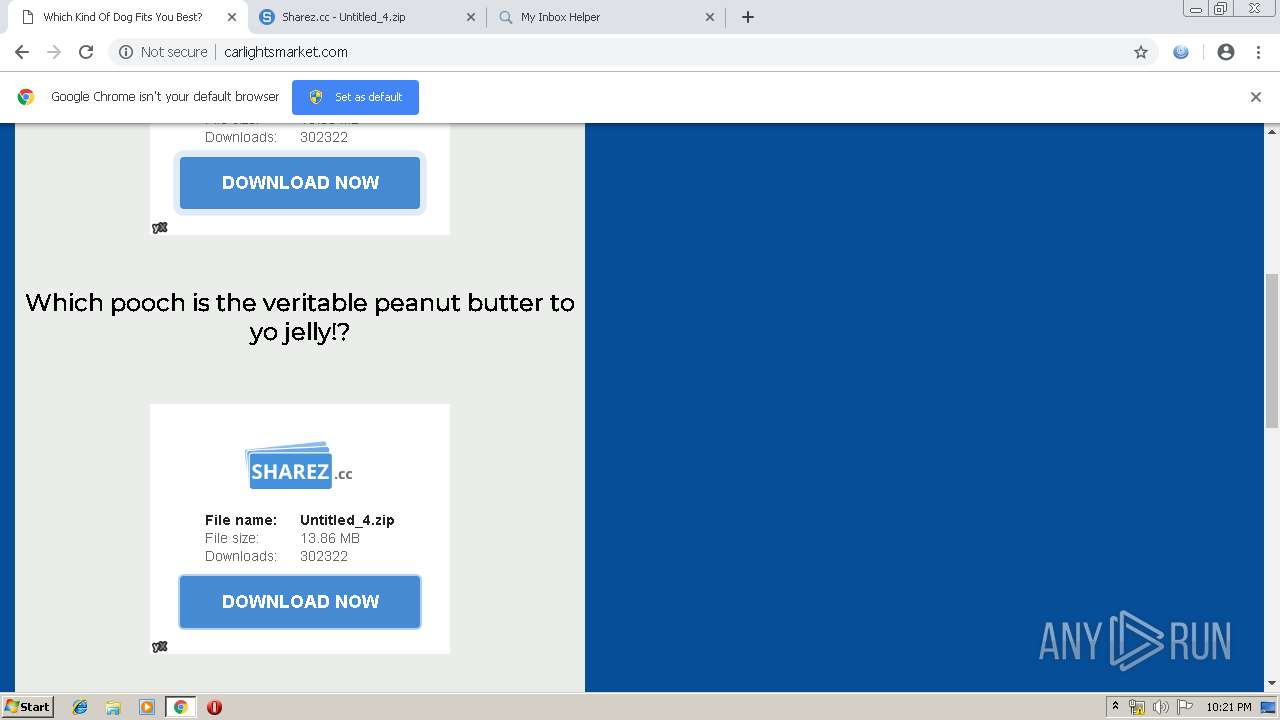
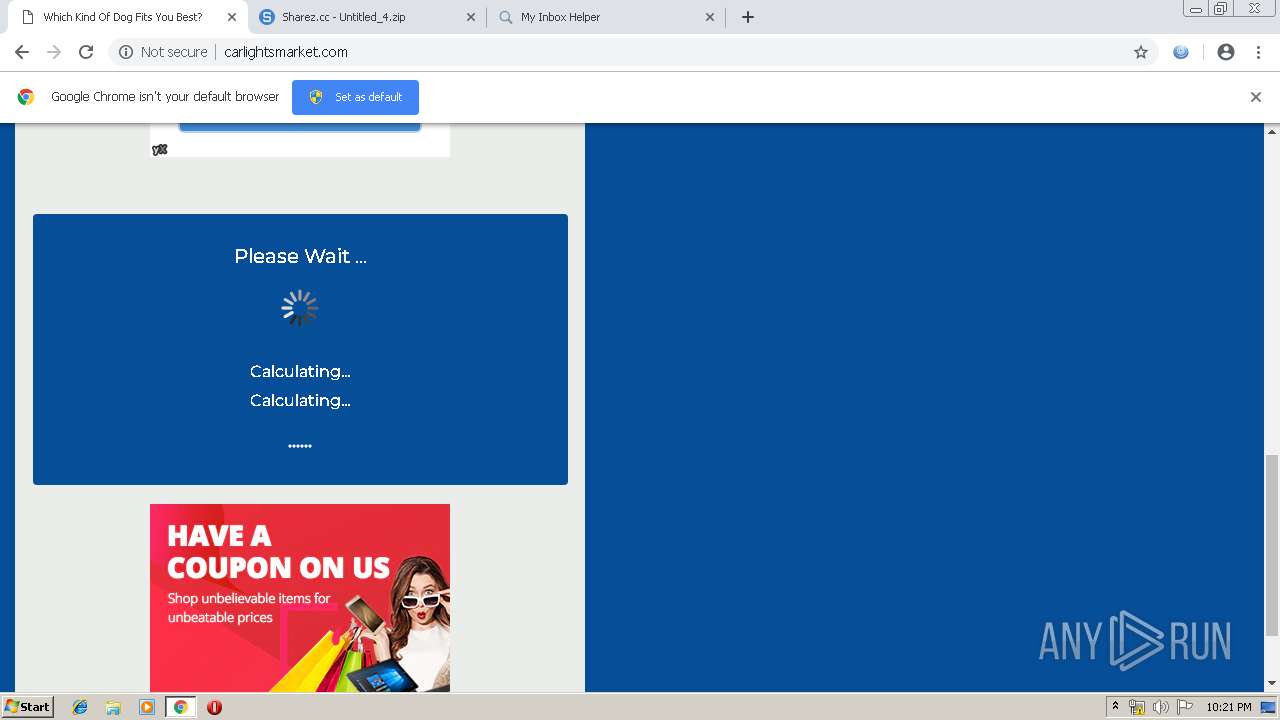
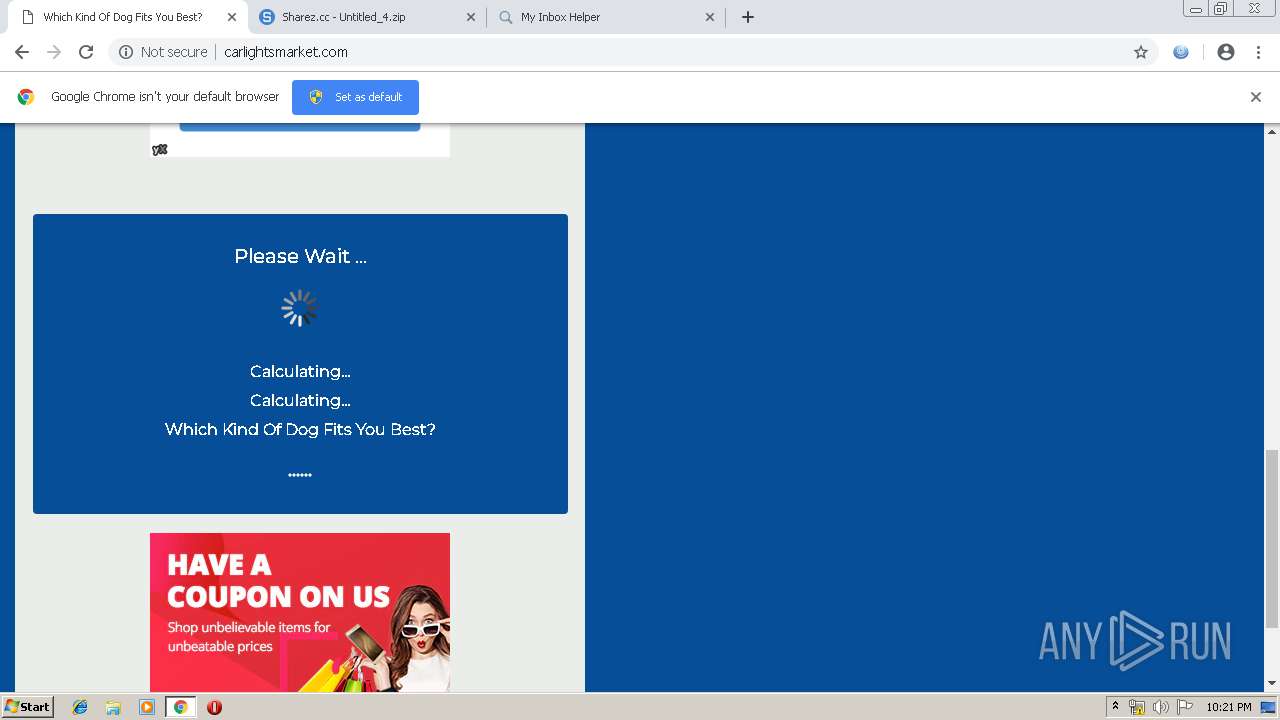
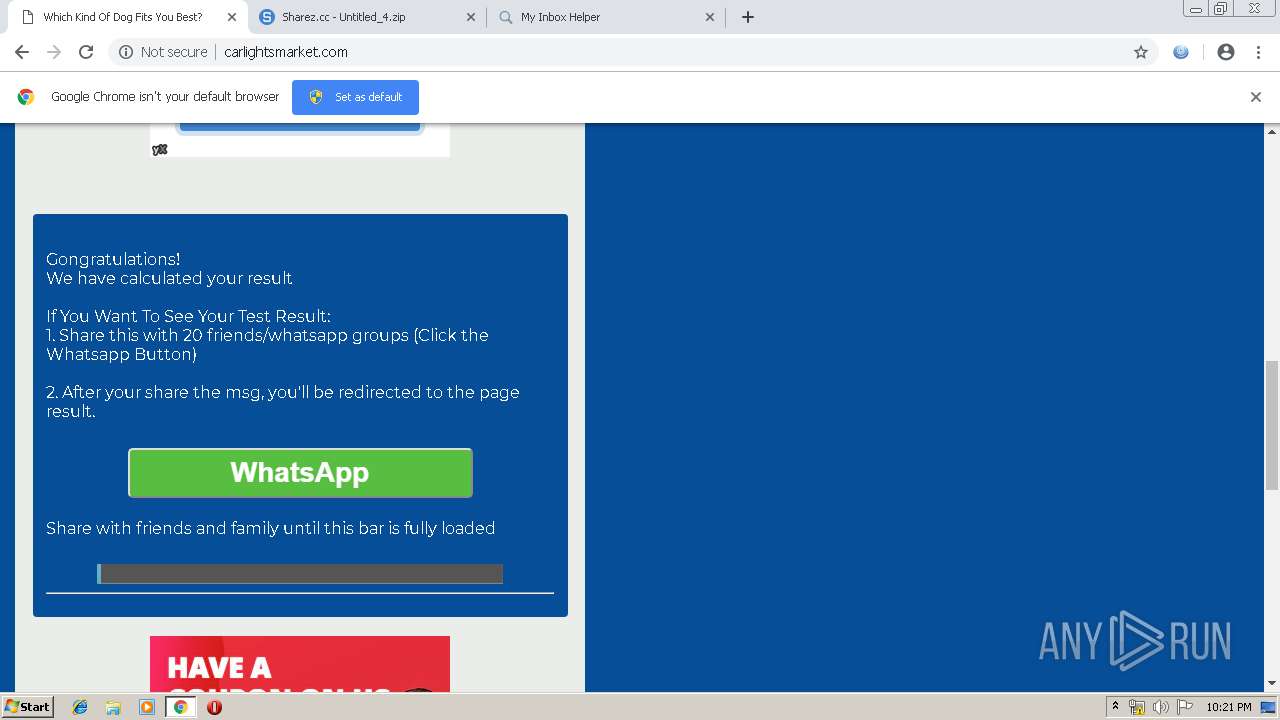
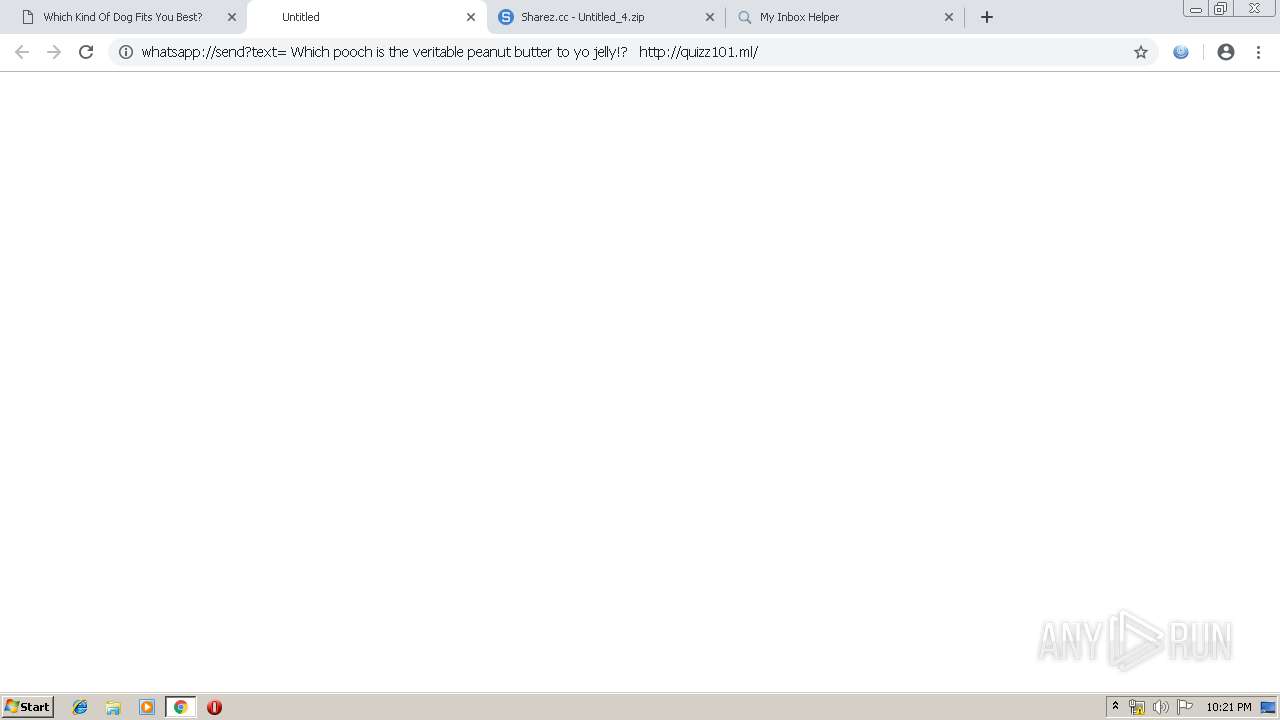
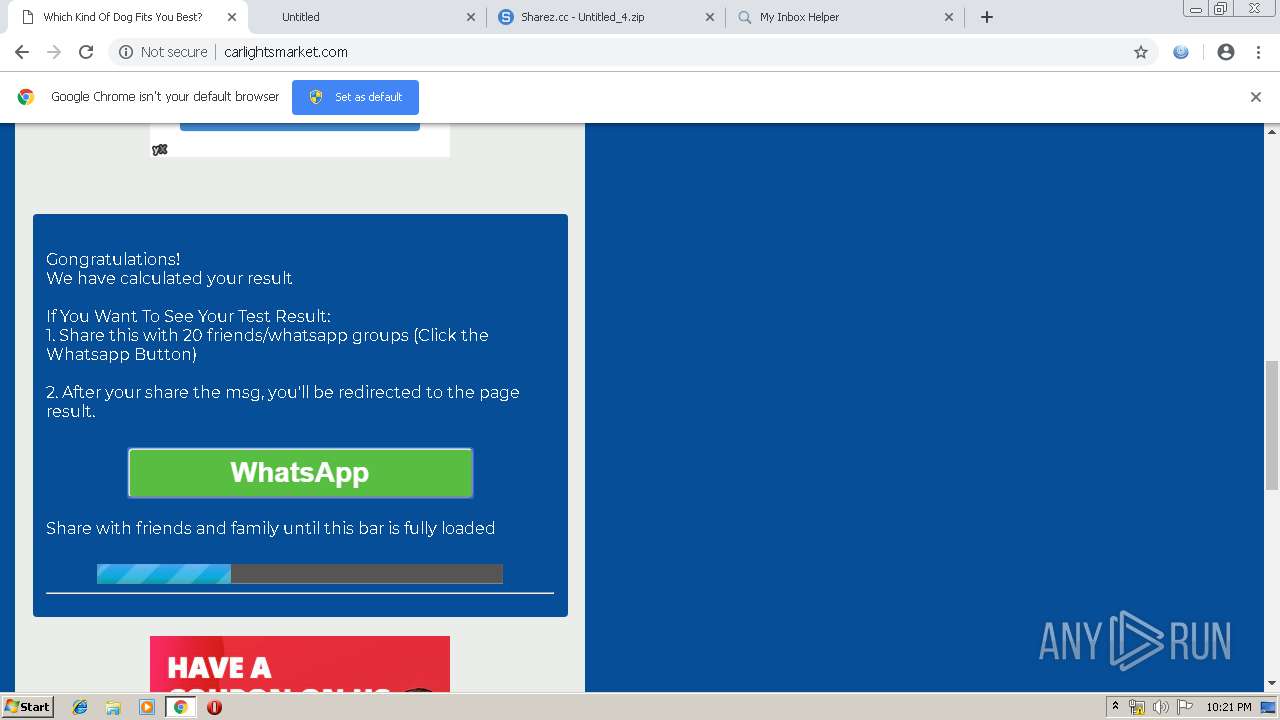
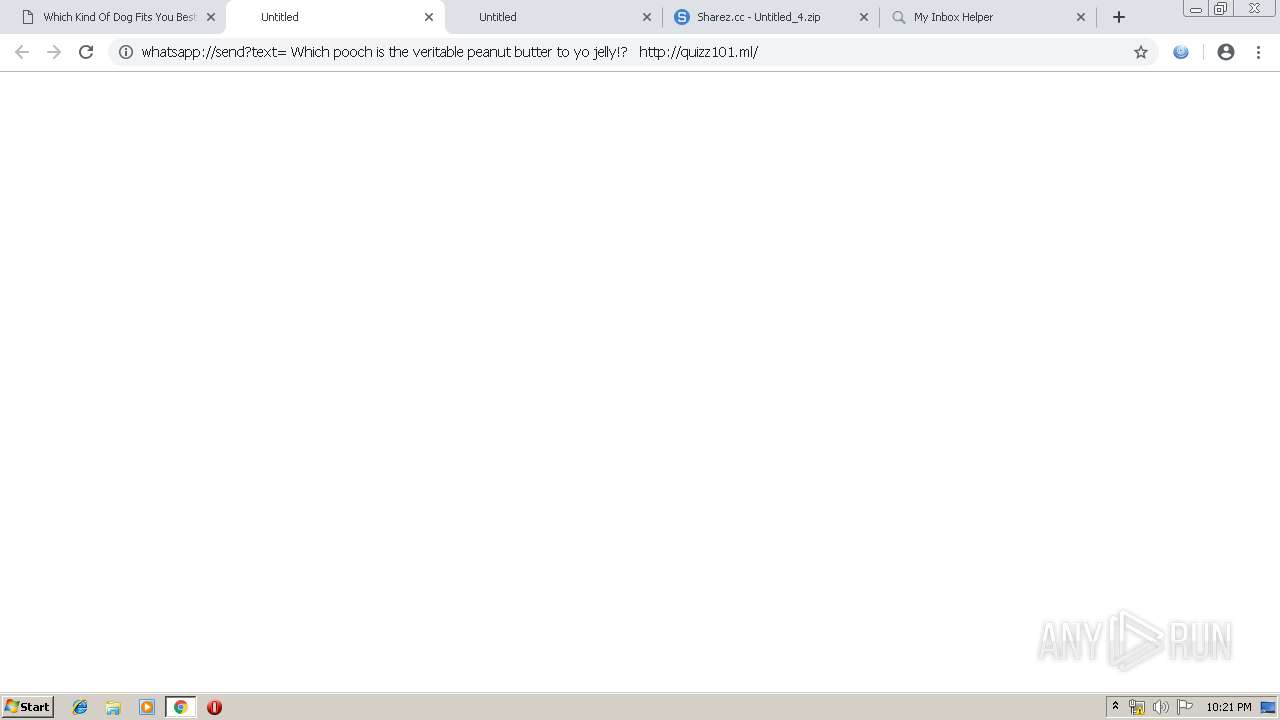
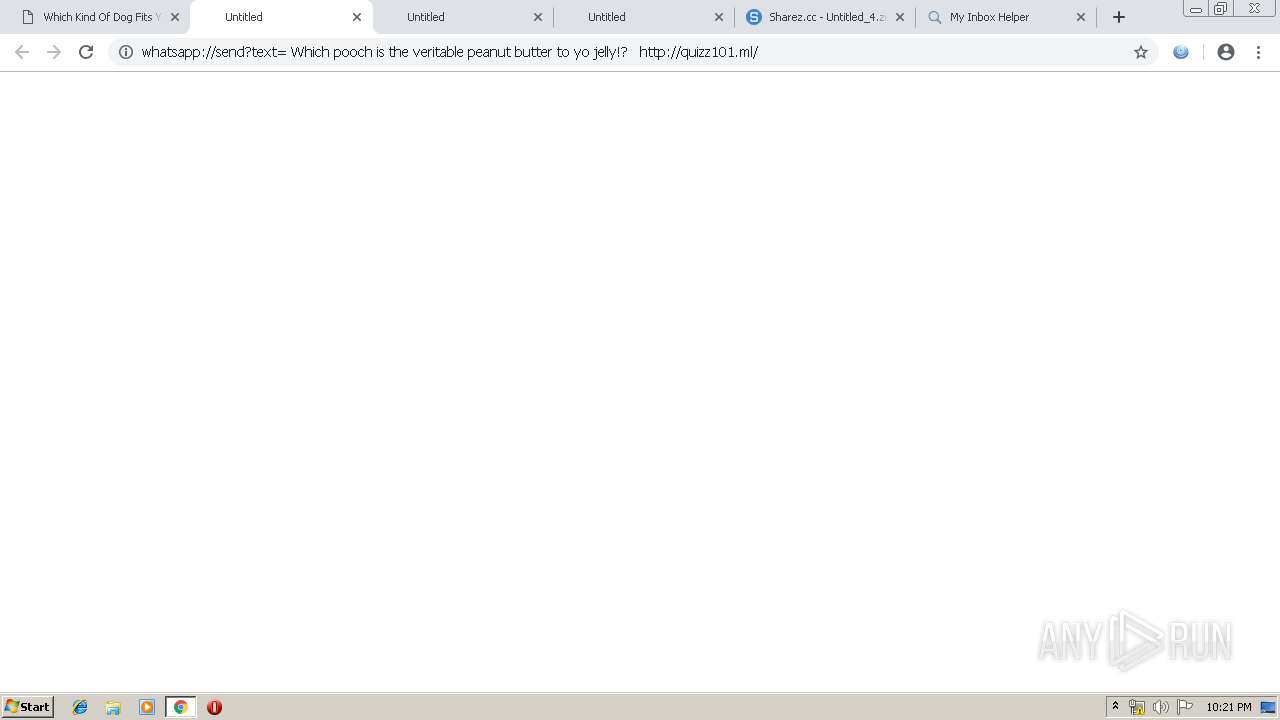
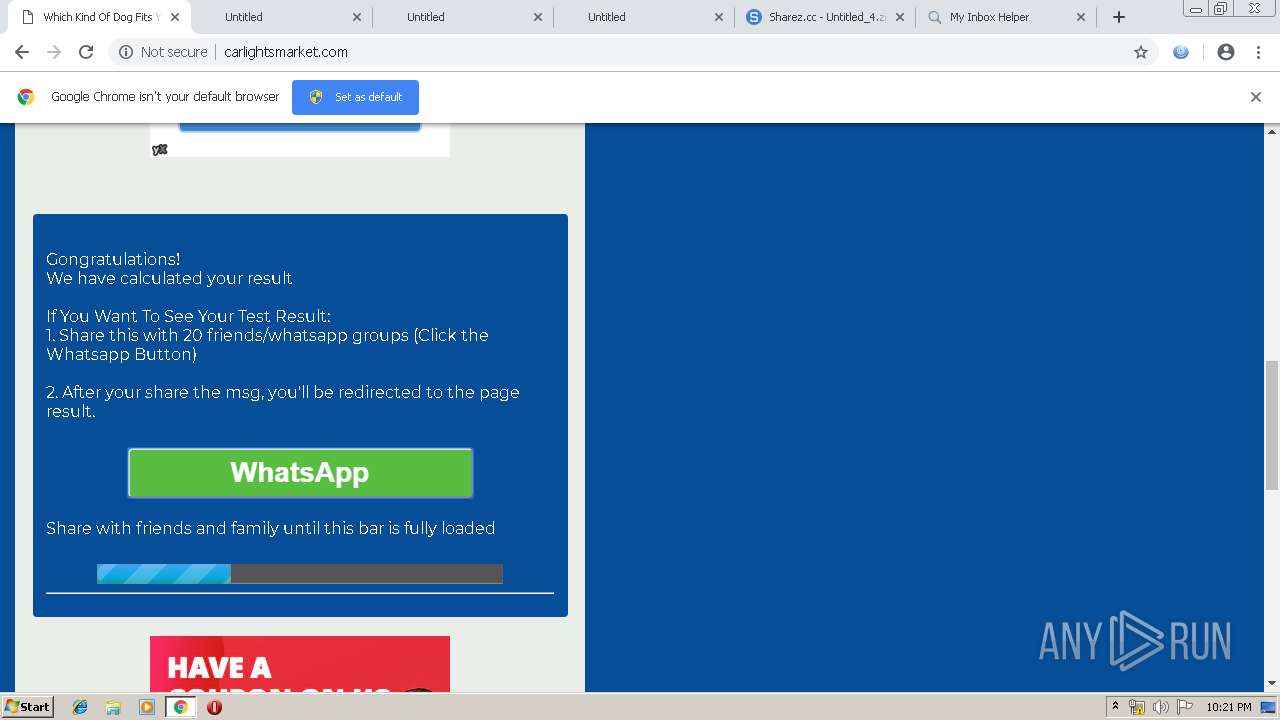
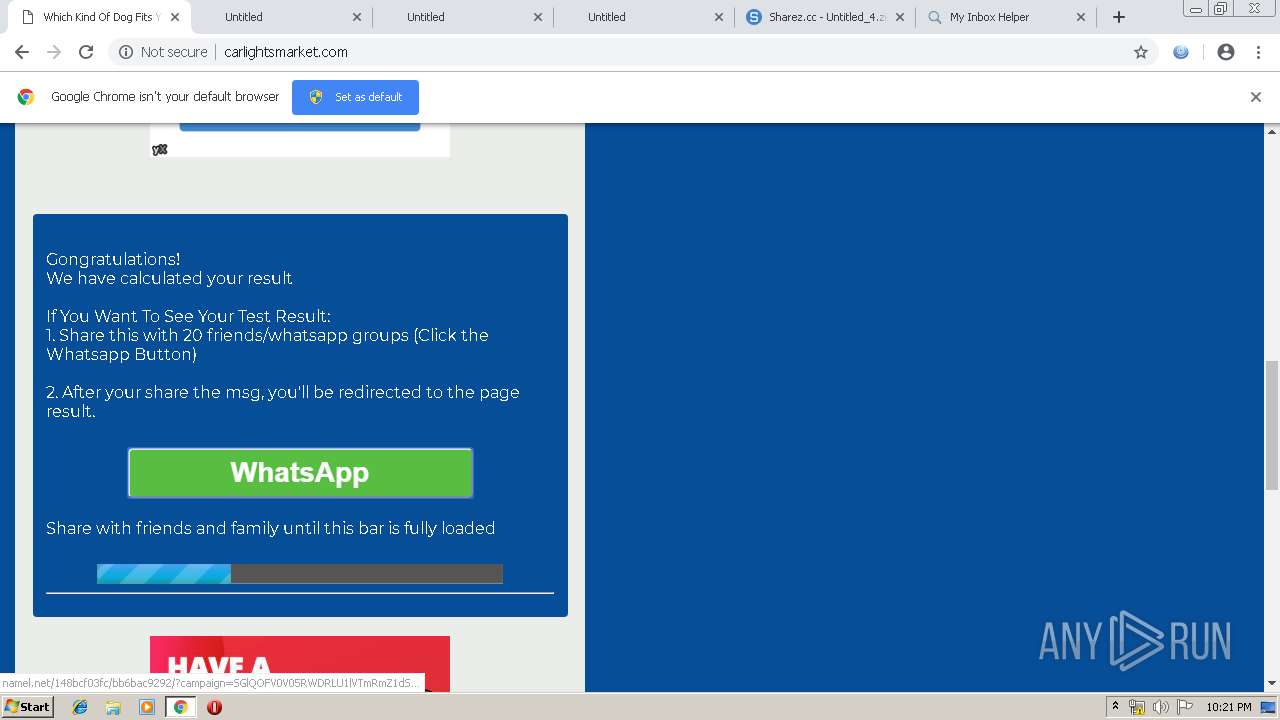
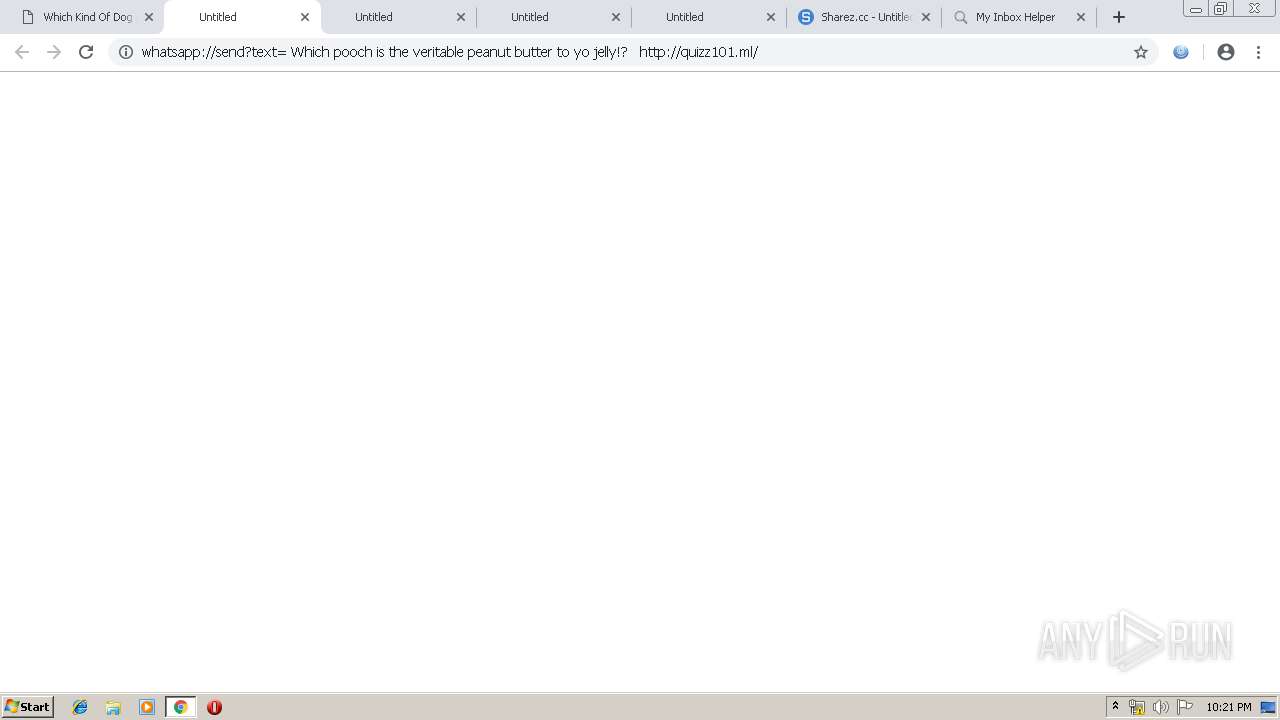
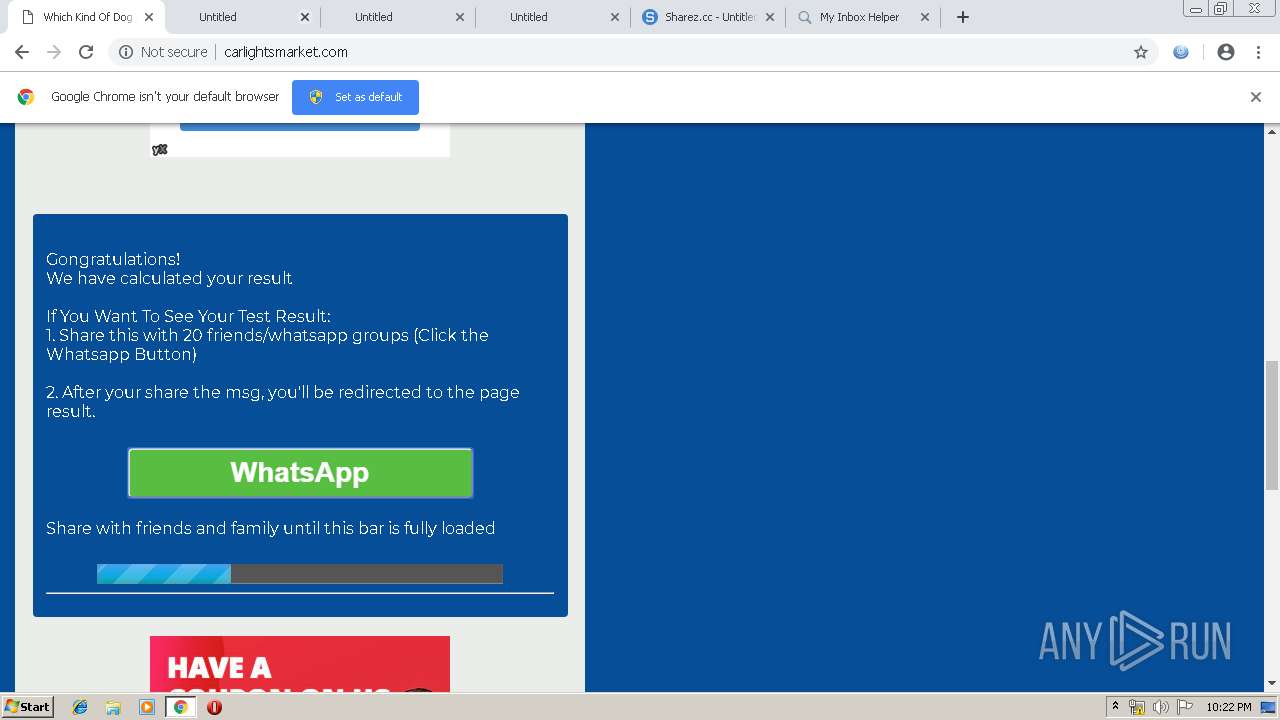
| URL: | http://carlightsmarket.com/ |
| Full analysis: | https://app.any.run/tasks/cf47440c-7a2a-49e1-bb11-6492936c44f4 |
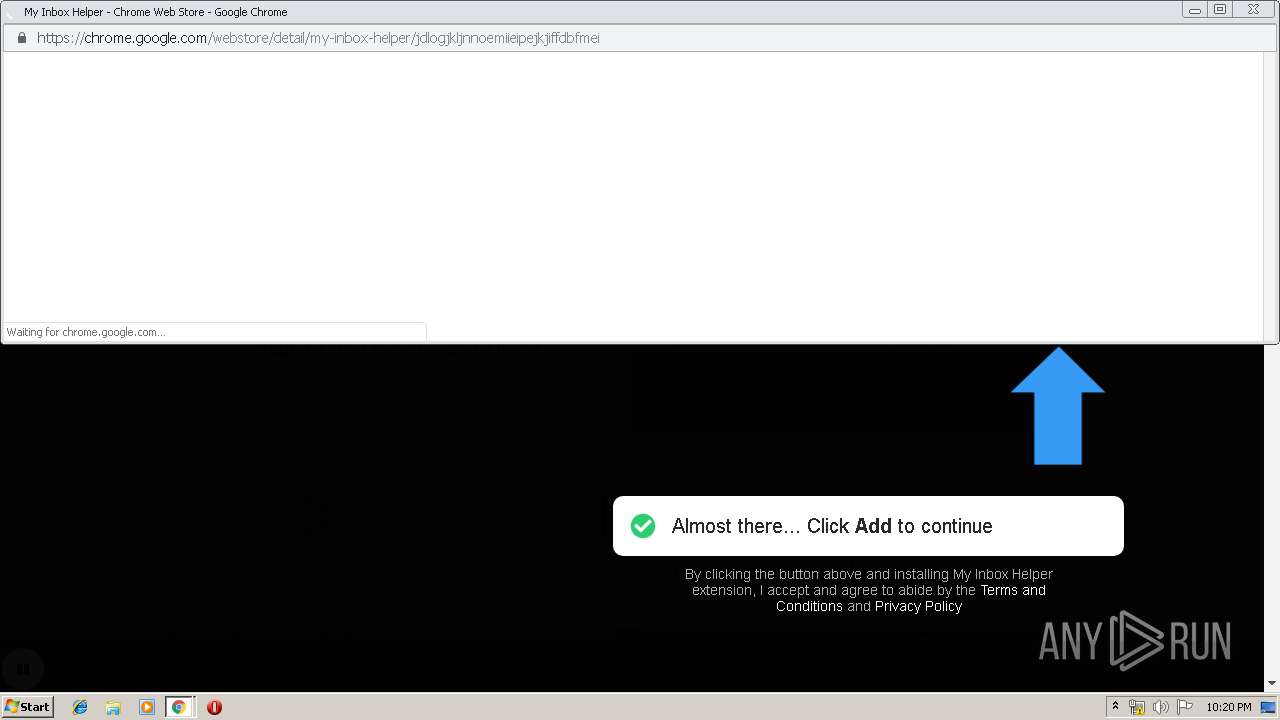
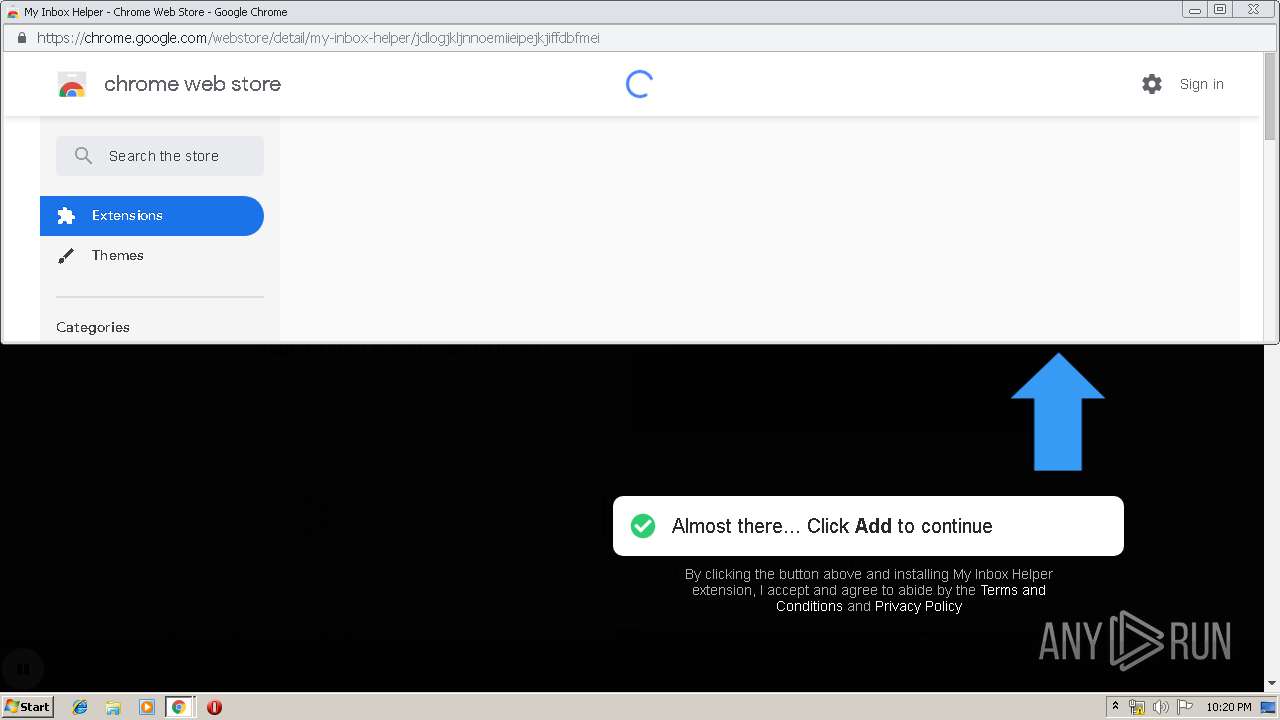
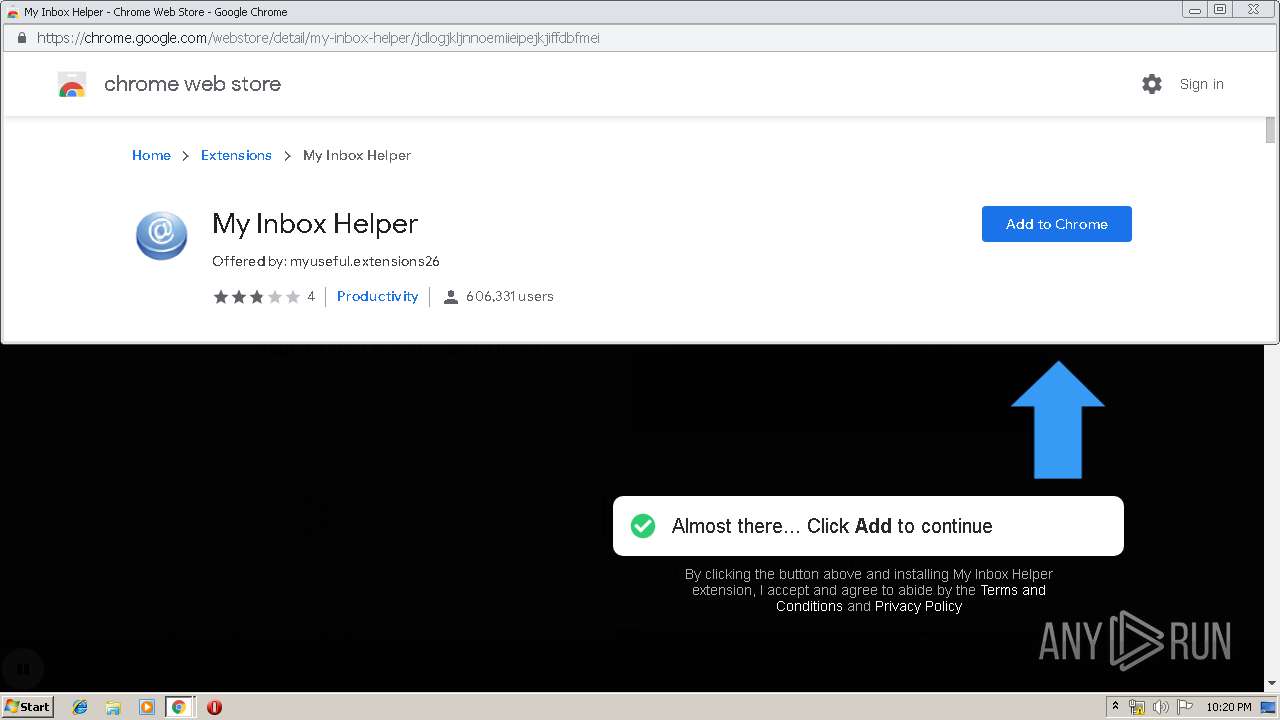
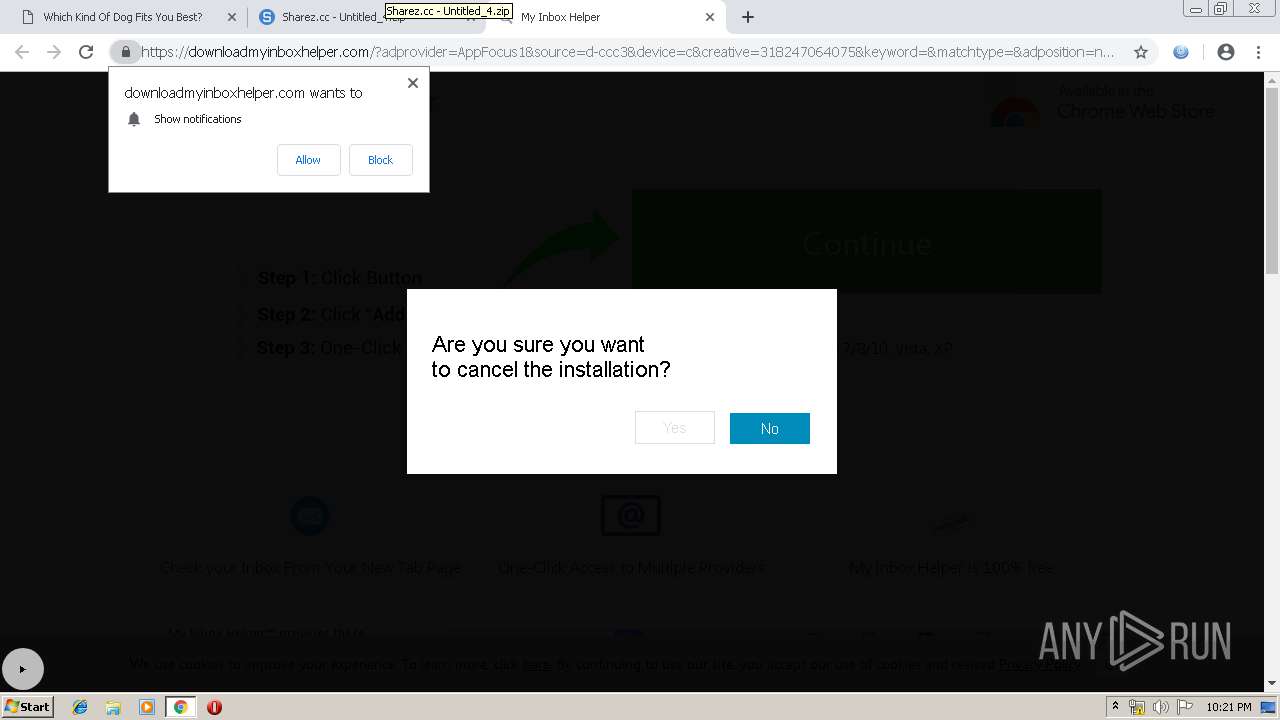
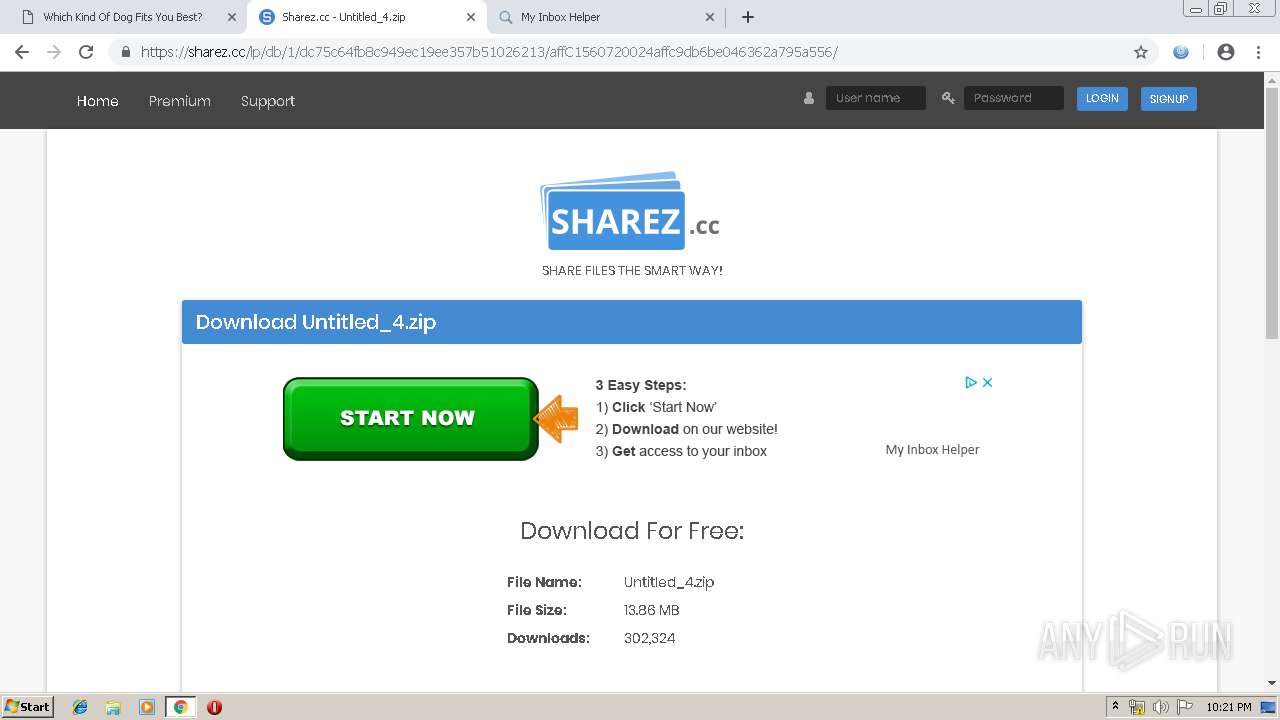
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 21:19:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D0FB2361897BB13D7AACE27F17D89DD5 |
| SHA1: | F70E6A6795EE3EE3AE3E8DE084C8CFAFE2492688 |
| SHA256: | 9FE66FA24A39B4EC06E5D04F5EE1791169530DB2AE60C1D3CA7D1C151312AB98 |
| SSDEEP: | 3:N1KdEZM+WIGRt:CGy+P2 |
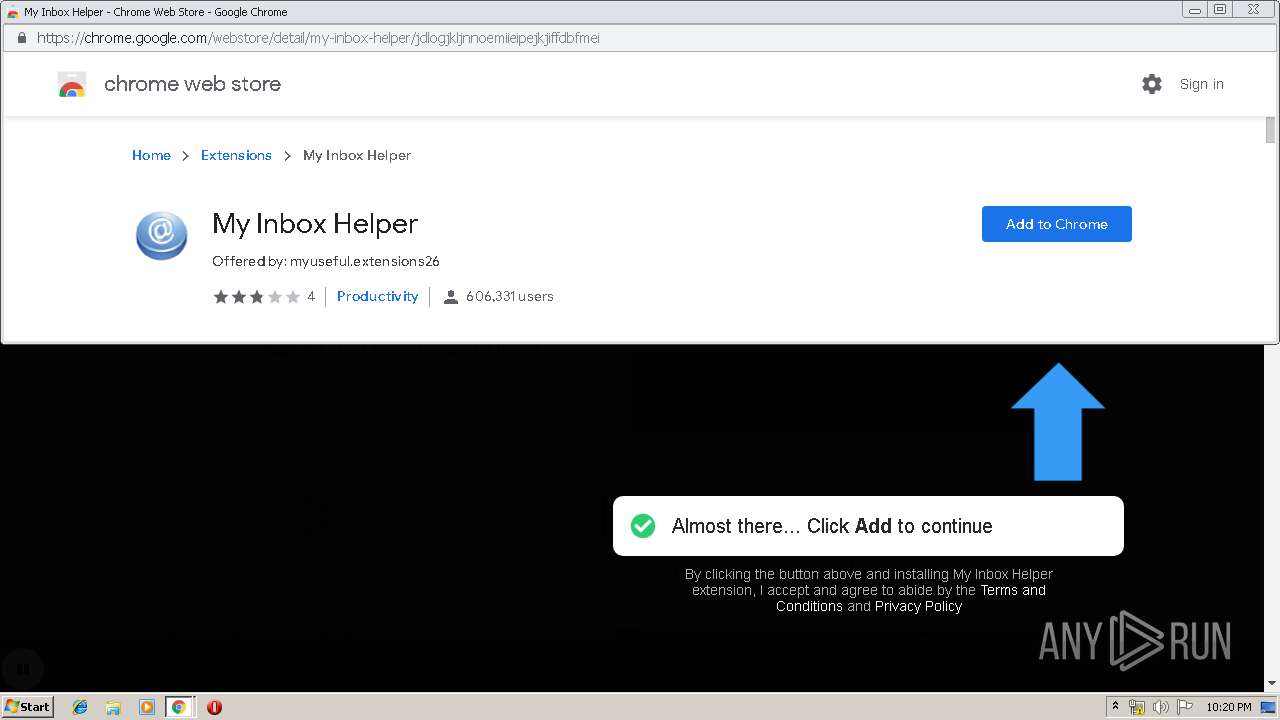
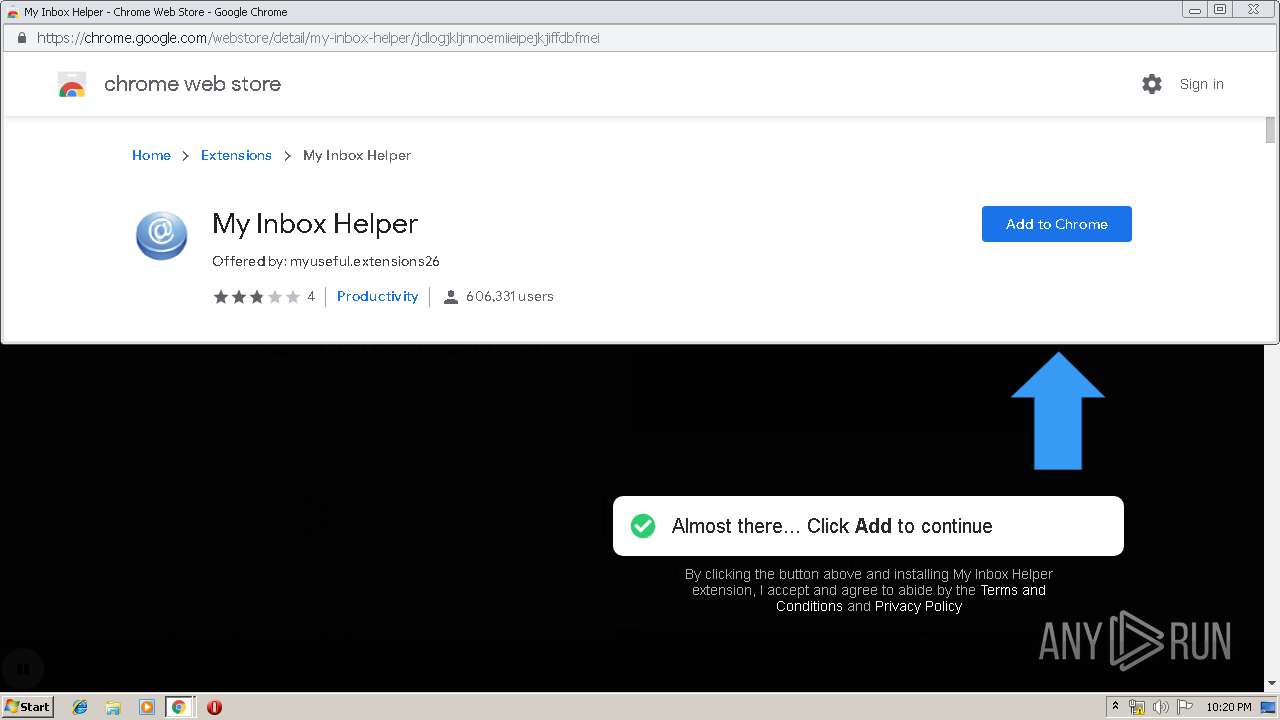
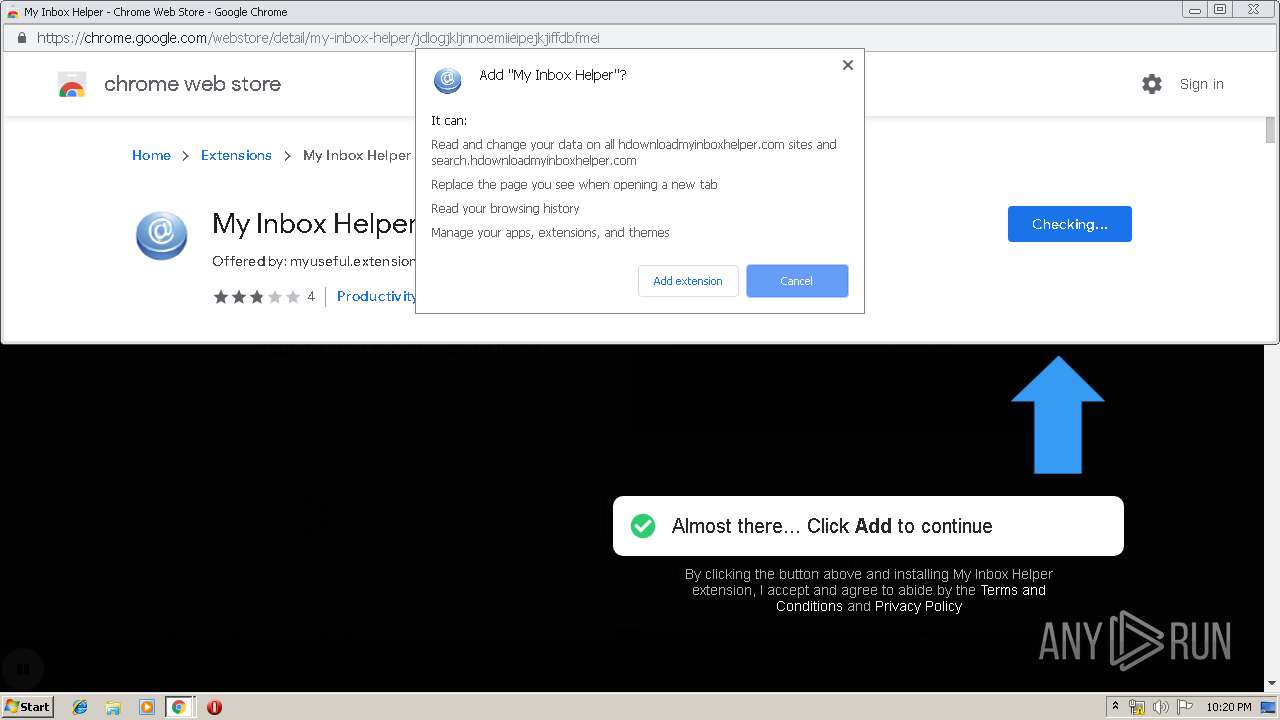
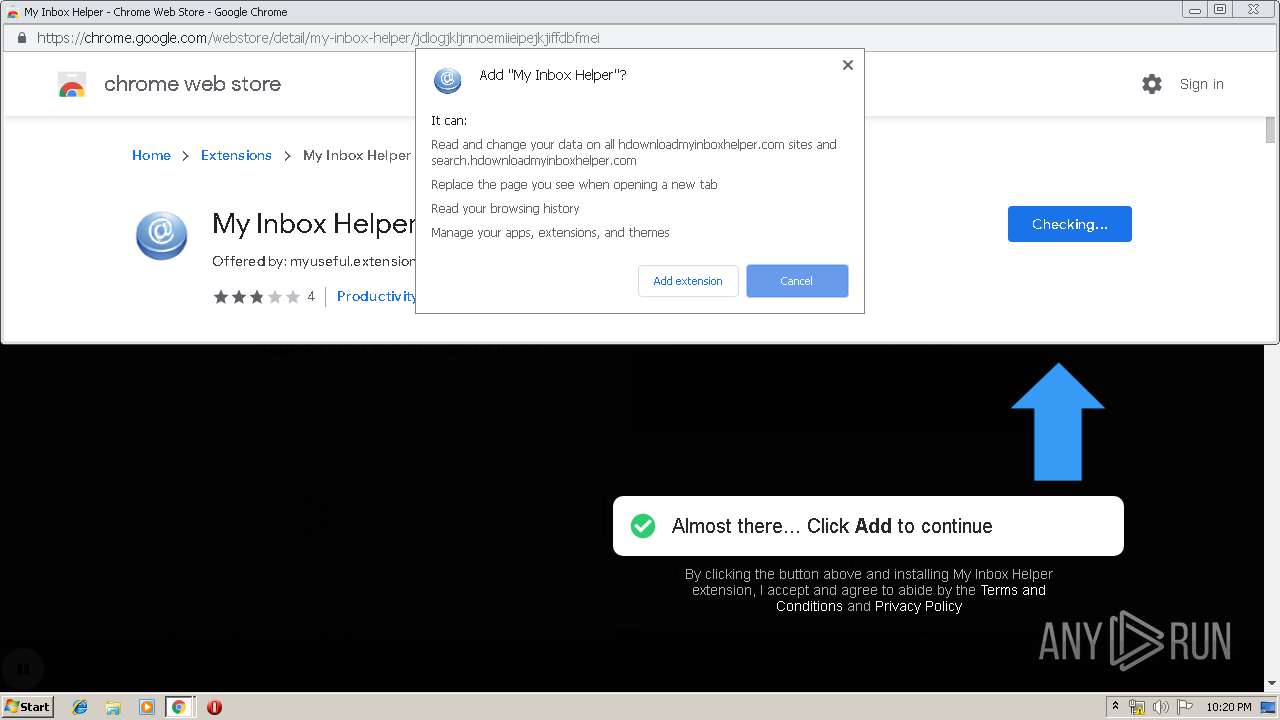
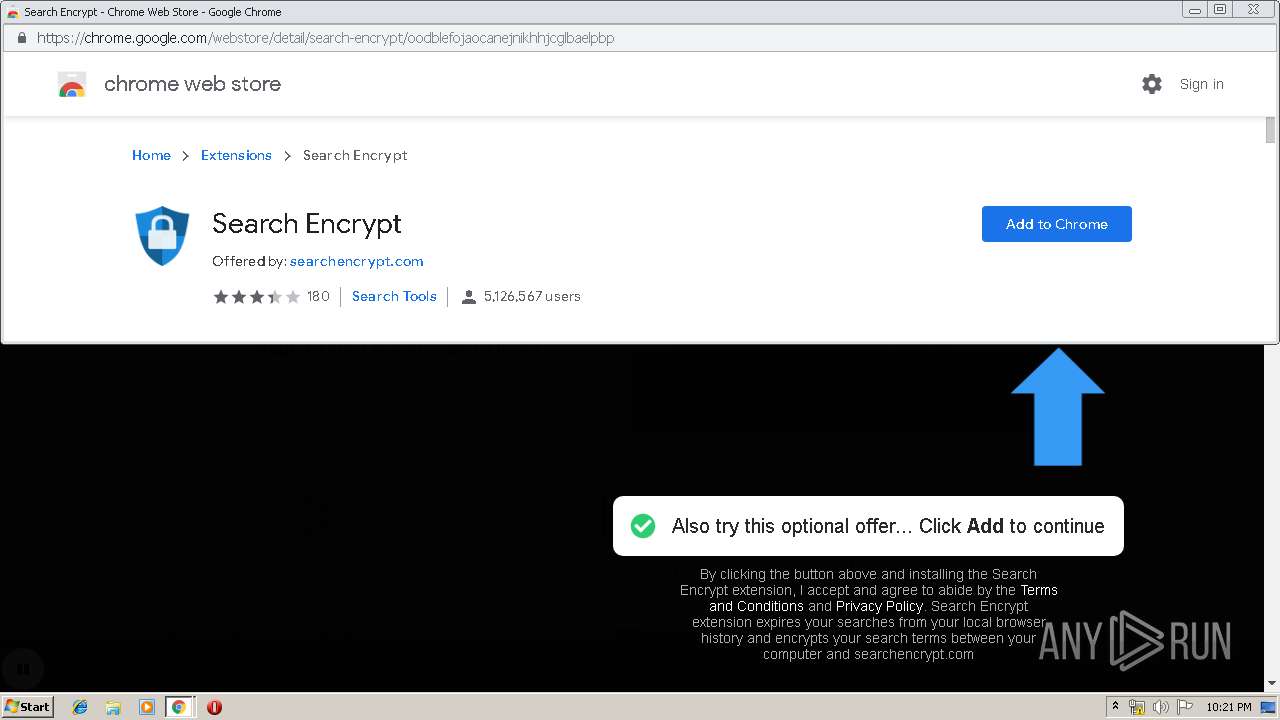
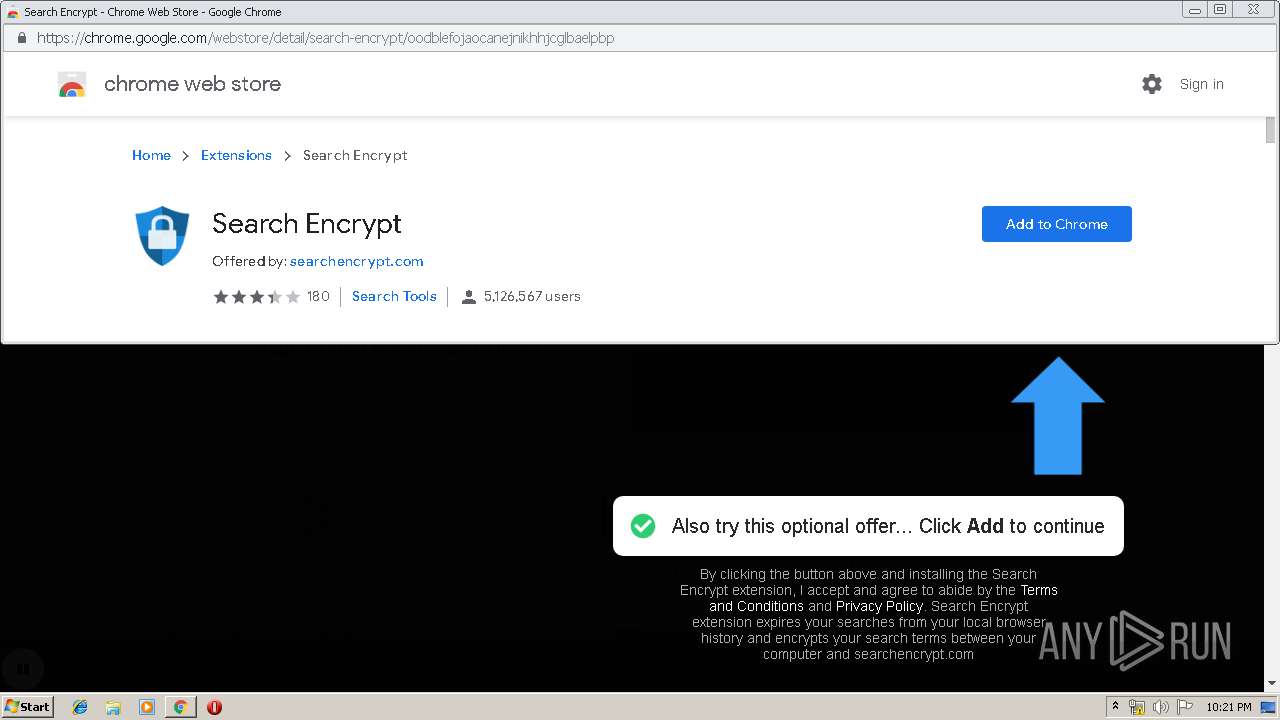
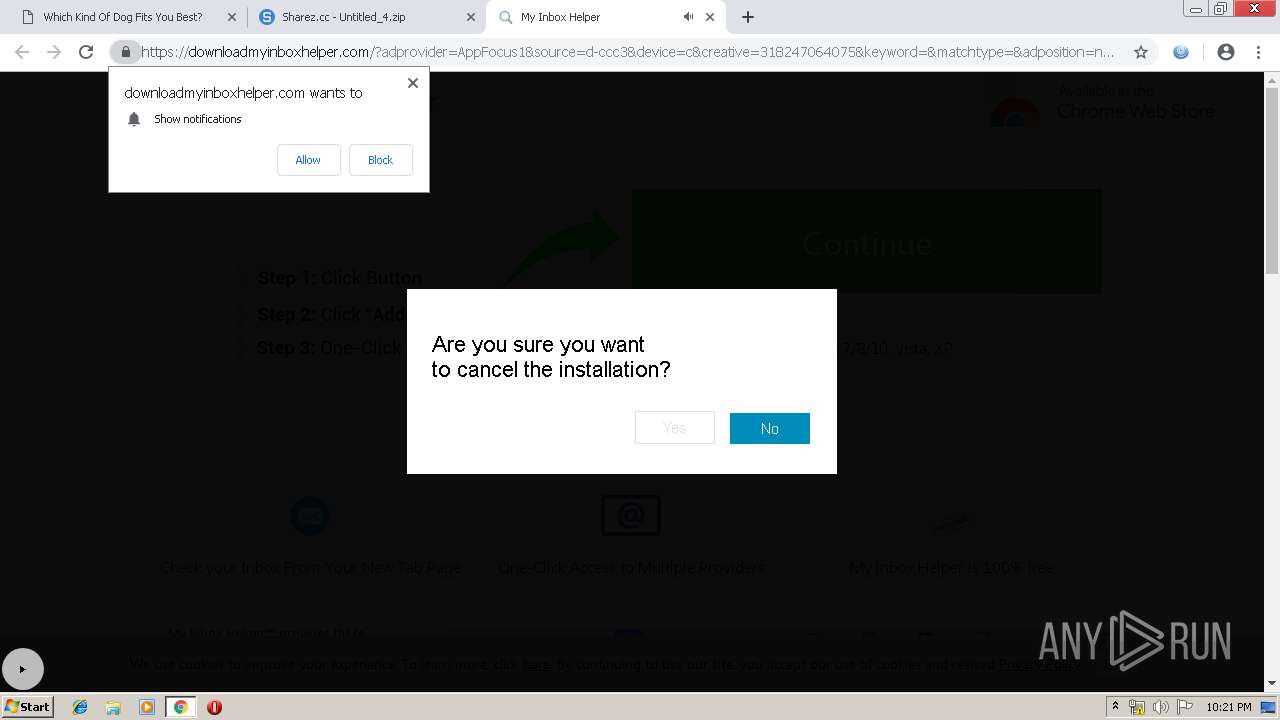
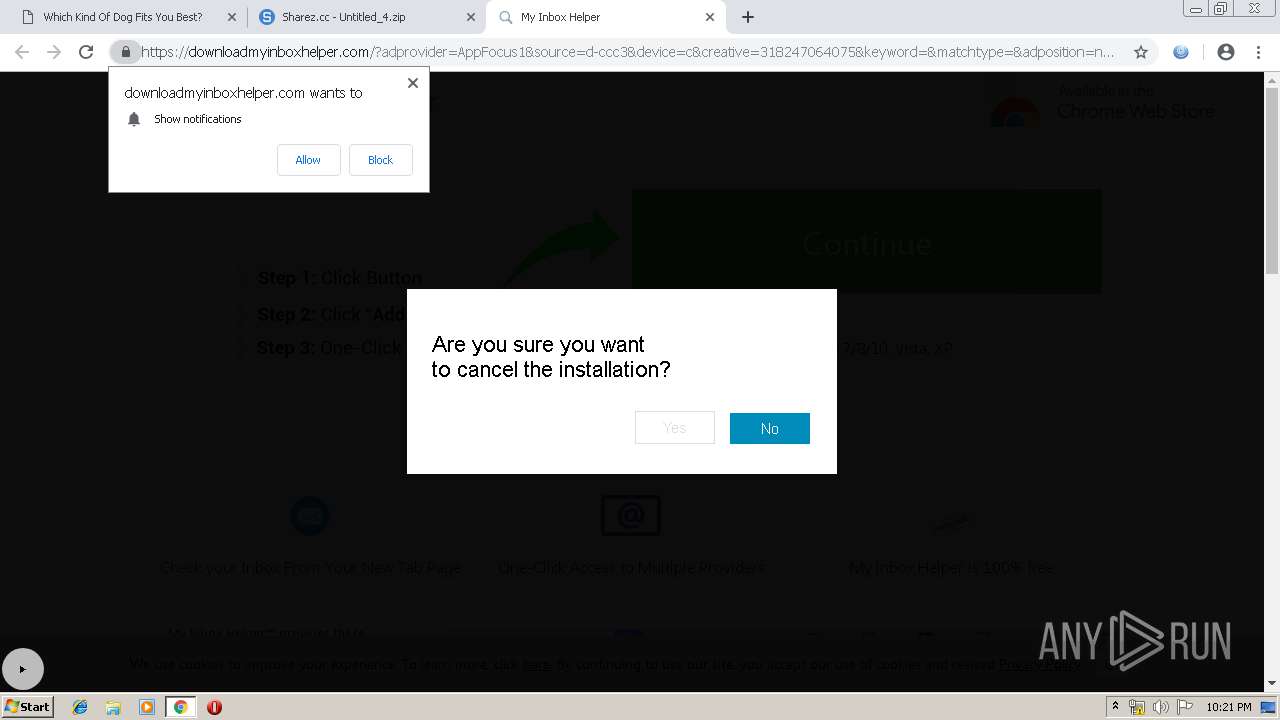
MALICIOUS
No malicious indicators.SUSPICIOUS
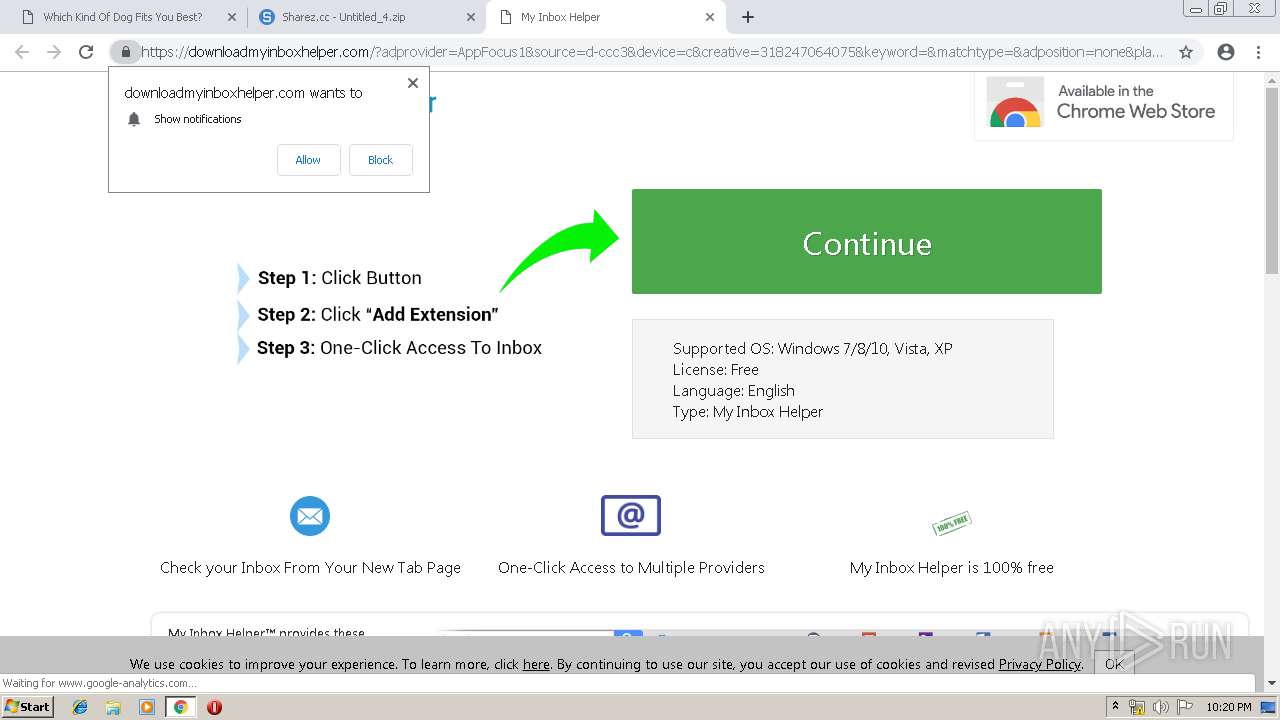
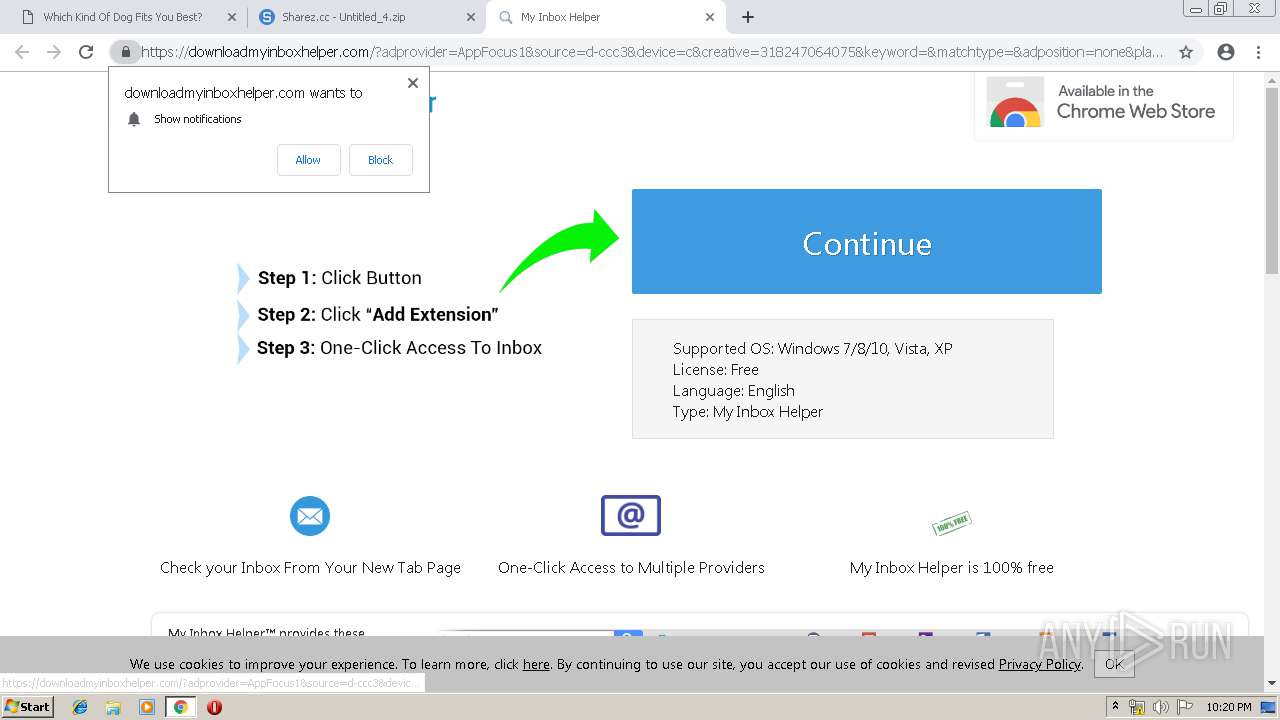
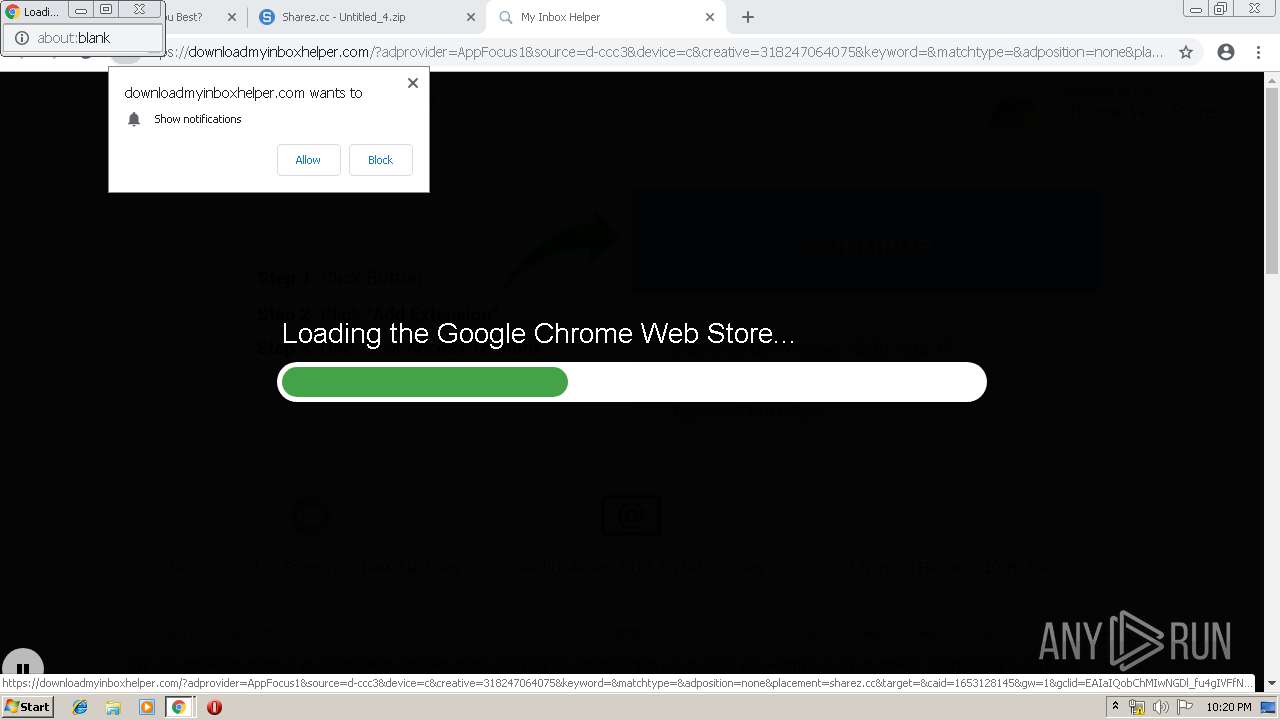
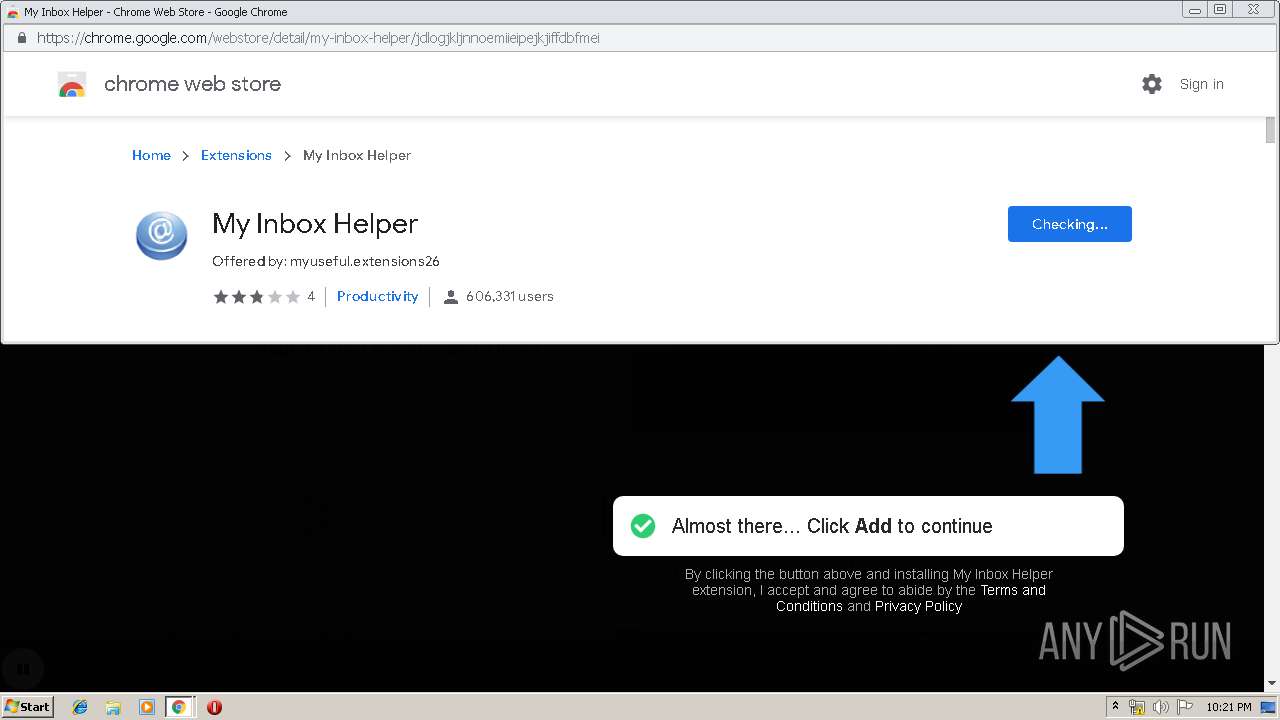
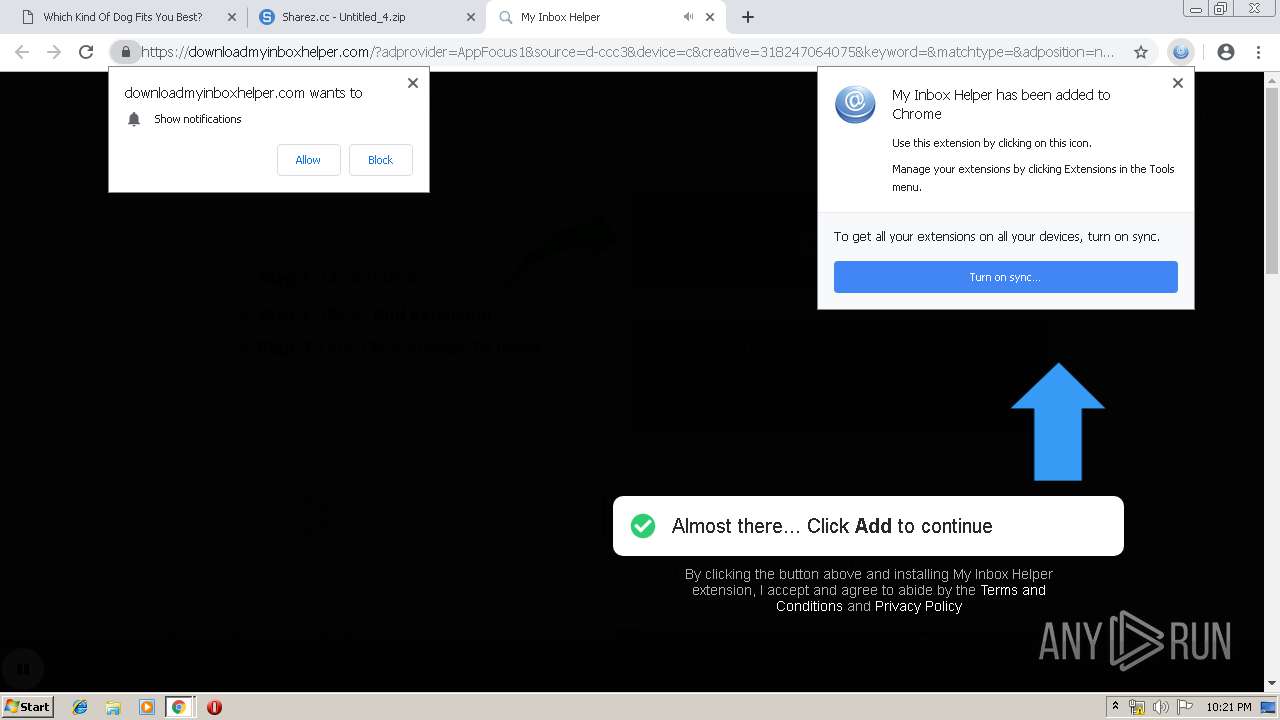
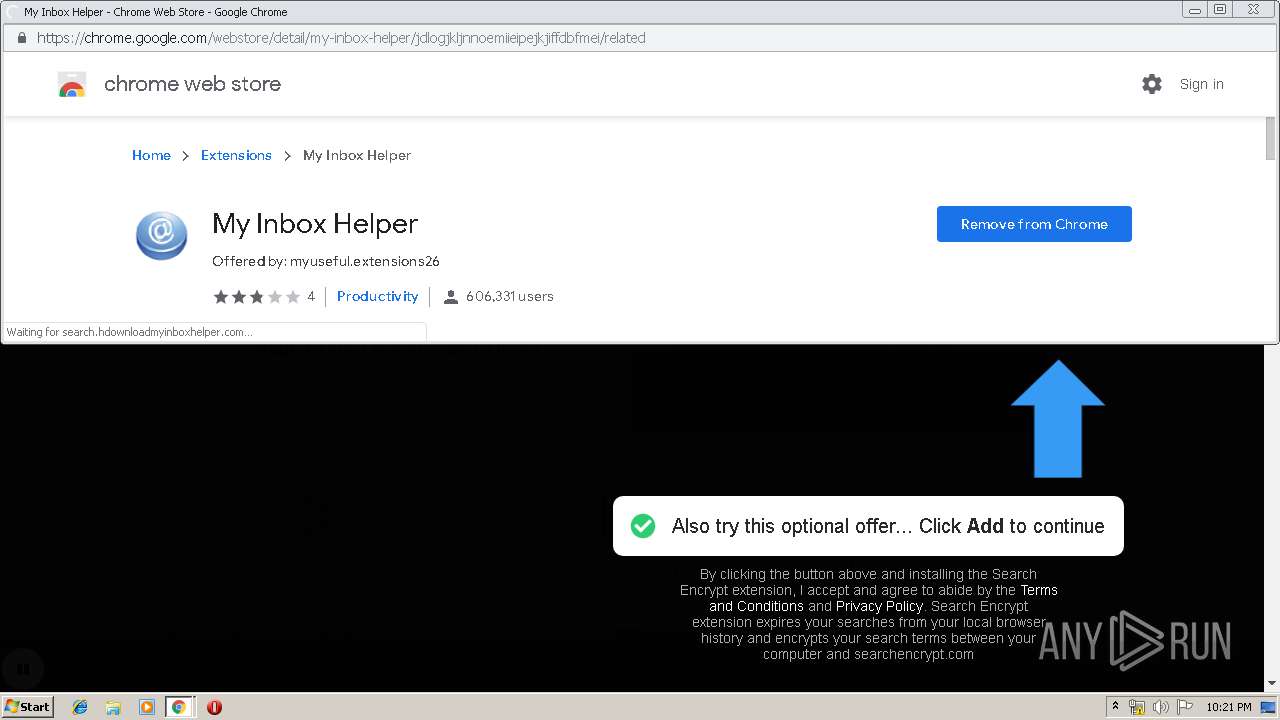
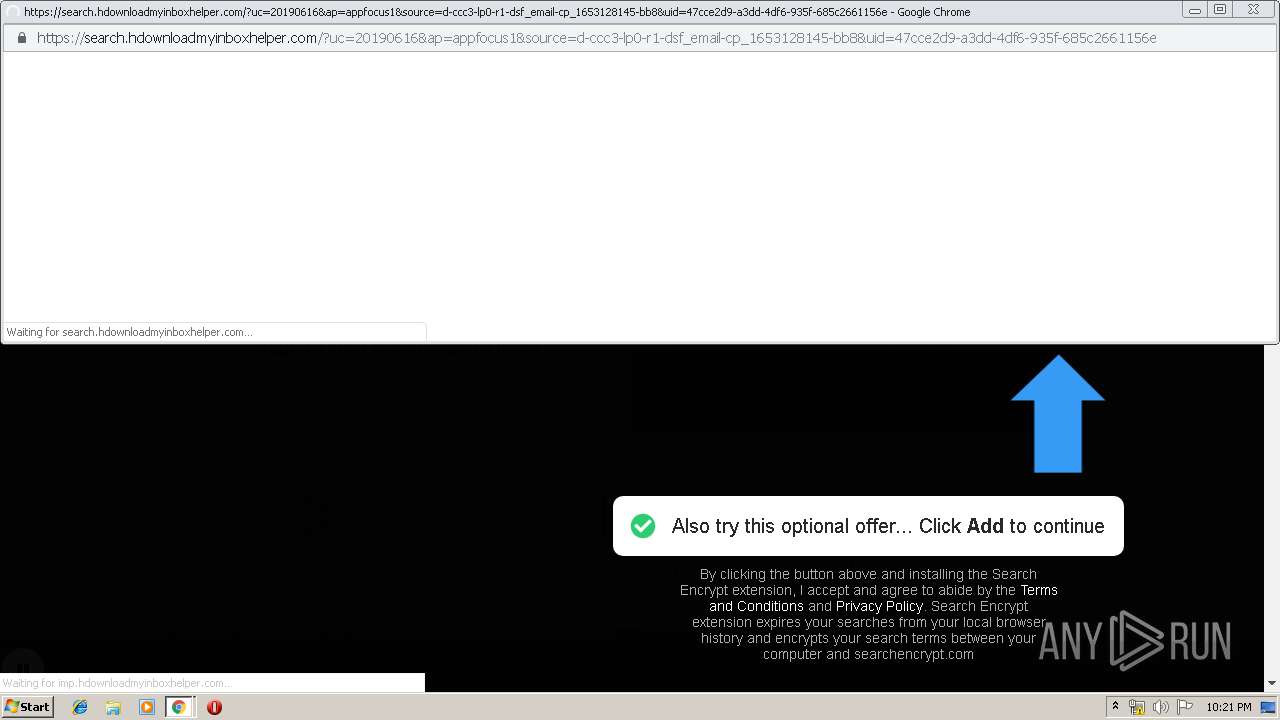
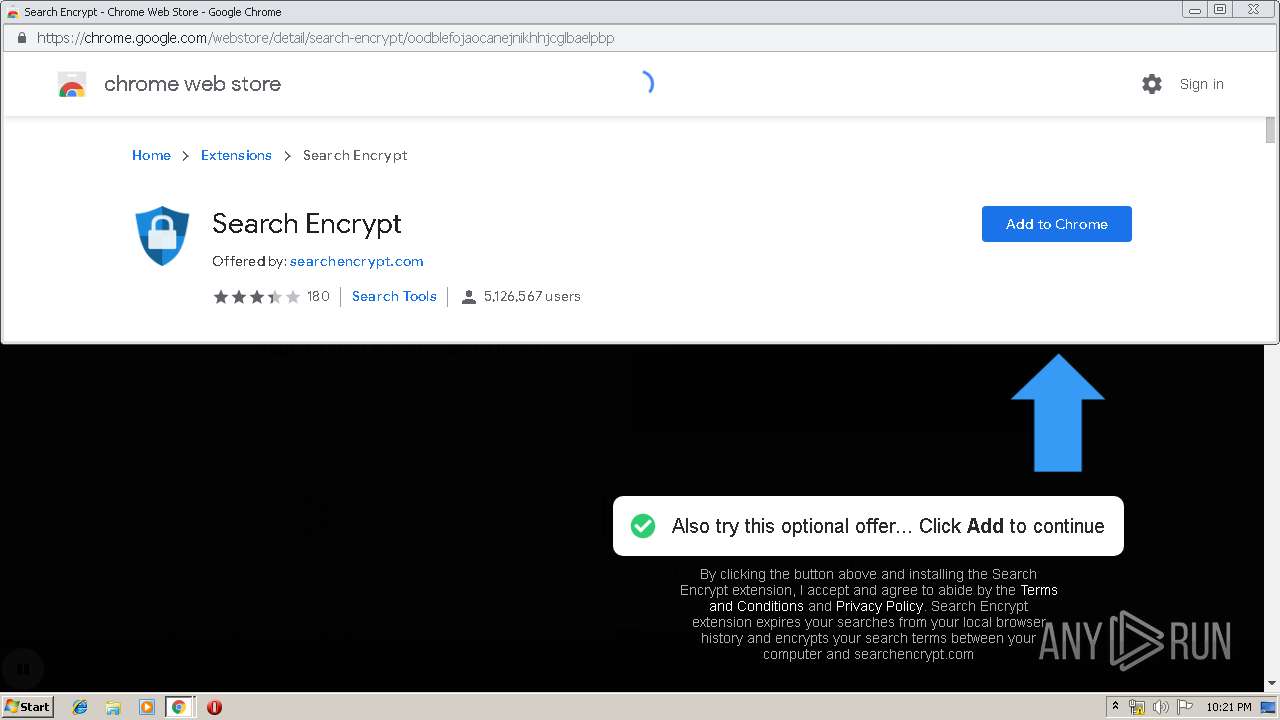
Modifies files in Chrome extension folder
- chrome.exe (PID: 3200)
INFO
Application launched itself
- chrome.exe (PID: 3200)
Reads Internet Cache Settings
- chrome.exe (PID: 3200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
46
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4404891881009356446 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4404891881009356446 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4877859821187672319 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4877859821187672319 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5905106572982912785 --mojo-platform-channel-handle=2064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2230476789234263690 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2230476789234263690 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=364795654114082658 --mojo-platform-channel-handle=5444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9711333530215289052 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4542304316705339040 --mojo-platform-channel-handle=5772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7193291798926775370 --mojo-platform-channel-handle=7596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7430331652486034902 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7430331652486034902 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,5903697395064375182,14290619191741862077,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9196392555071888464 --mojo-platform-channel-handle=5452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
699
Read events
579
Write events
115
Delete events
5
Modification events
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3200-13205193614612125 |
Value: 259 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3200-13205193614612125 |
Value: 259 | |||
Executable files
0
Suspicious files
119
Text files
249
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\056fb818-612c-43ae-812d-b424f820f57e.tmp | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
128
DNS requests
64
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3200 | chrome.exe | GET | — | 185.66.200.216:80 | http://ylx-1.com/bnr.php?section=Quiz&pub=266853&format=300x250&ga=g | SK | — | — | unknown |
3200 | chrome.exe | GET | — | 185.66.200.216:80 | http://ylx-1.com/bnr_xload.php?section=Quiz&pub=266853&format=300x250&ga=g&xt=156072001750665&xtt=1548458 | SK | — | — | unknown |
3200 | chrome.exe | GET | — | 167.86.95.96:80 | http://carlightsmarket.com/img/piplovi.png | US | — | — | unknown |
3200 | chrome.exe | GET | 200 | 167.86.95.96:80 | http://carlightsmarket.com/ | US | xml | 37.2 Kb | unknown |
3200 | chrome.exe | GET | 200 | 185.66.200.216:80 | http://ylx-1.com/bnr.php?section=Quiz&pub=266853&format=300x250&ga=g | SK | text | 276 b | unknown |
3200 | chrome.exe | GET | 200 | 185.66.200.216:80 | http://ylx-1.com/show.php?u78041560720018=true&ad=673873&f=300x250&a=395578&cri=0&s=NGFkYjNjY2E3YjIyNmIwZjUxMzcxYjVlNzgwZjU5ZWM=&u=266853&si=735117336&di=32054504&ci=16&h=cf358e7ea301ed4fa6157bf71d5c3683&cc=GB&useAf=loaded_string_273537baa324cb68f7373ff393ac7e55239a5_2241891_1560720018.1842_19756&ar=aHR0cDovL2NhcmxpZ2h0c21hcmtldC5jb20v | SK | html | 857 b | unknown |
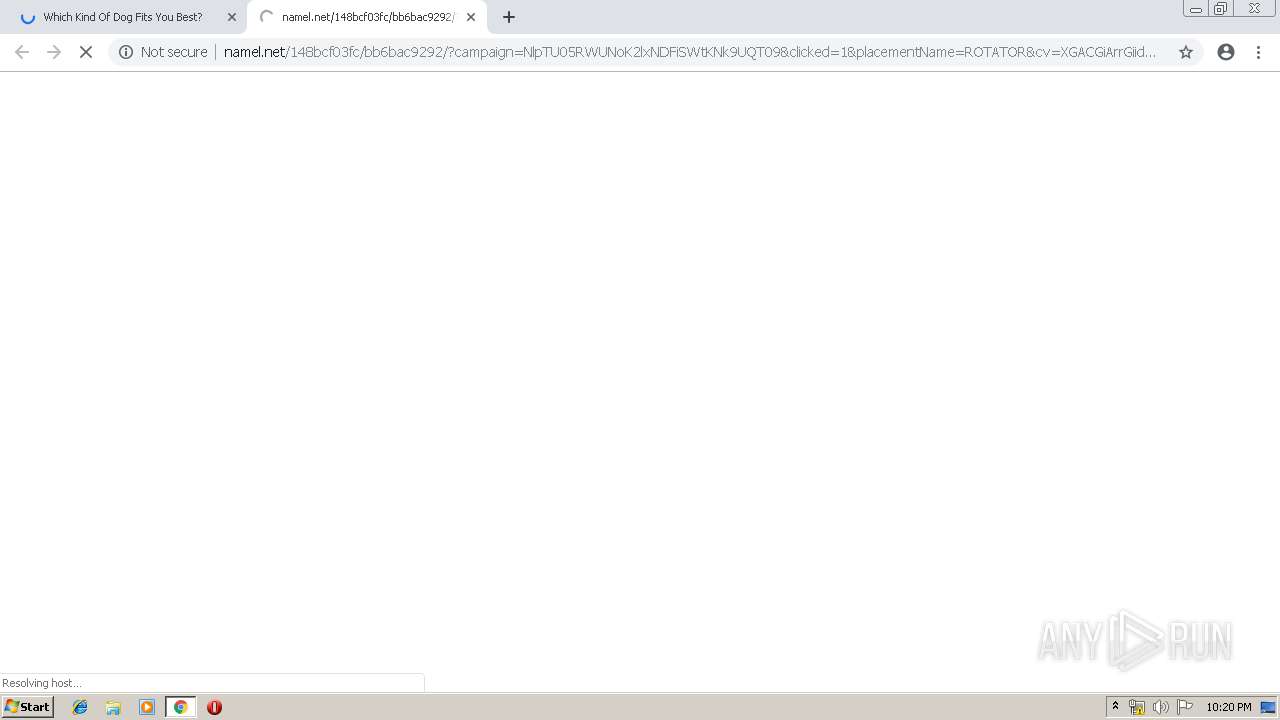
3200 | chrome.exe | GET | 200 | 185.66.201.34:80 | http://namel.net/148bcf03fc/bb6bac9292/?placementName=ROTATOR&type=n&cv=XGACGiArrGiidCikAAGjCxCrxkNrdkNZZNkkCrCZijCCrixCGiCrCrGCx&adApiR=loaded_string_273537baa324cb68f7373ff393ac7e55239a5_2241891_1560720018.1842_19756&refferer=2622481356_aHR0cDovL2NhcmxpZ2h0c21hcmtldC5jb20v&width=300&height=250&yxDom=eWx4LTEuY29t_d2e782c6bee242762e705a45bd0be41c | SK | text | 1.18 Kb | suspicious |
3200 | chrome.exe | GET | 200 | 185.66.201.34:80 | http://namel.net/148bcf03fc/bb6bac9292/?placementName=ROTATOR&type=n&cv=XGACGiArrGiidCikAAGjCxCrxkNrdkNZZNkkCrCZijCCrixCGiCrCrGCx&adApiR=loaded_string_223847baa324cb68f7373ff393ac7e55239a5_2241891_1560720018.3101_47199&refferer=2622481356_aHR0cDovL2NhcmxpZ2h0c21hcmtldC5jb20v&width=300&height=250&yxDom=eWx4LTEuY29t_d2e782c6bee242762e705a45bd0be41c | SK | text | 1.18 Kb | suspicious |
3200 | chrome.exe | GET | 404 | 167.86.95.96:80 | http://carlightsmarket.com/img/iks.png | US | html | 328 b | unknown |
3200 | chrome.exe | GET | 200 | 185.66.200.216:80 | http://ylx-1.com/show.php?u59741560720018=true&ad=673873&f=300x250&a=395578&cri=0&s=NGFkYjNjY2E3YjIyNmIwZjUxMzcxYjVlNzgwZjU5ZWM=&u=266853&si=735117336&di=32054504&ci=16&h=601b4a915ae12940ed38519fef208708&cc=GB&useAf=loaded_string_223847baa324cb68f7373ff393ac7e55239a5_2241891_1560720018.3101_47199&ar=aHR0cDovL2NhcmxpZ2h0c21hcmtldC5jb20v | SK | html | 857 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3200 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3200 | chrome.exe | 167.86.95.96:80 | carlightsmarket.com | Arapahoe School District #6 | US | unknown |
3200 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3200 | chrome.exe | 104.16.204.165:443 | cdn.onesignal.com | Cloudflare Inc | US | shared |
3200 | chrome.exe | 172.217.22.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3200 | chrome.exe | 151.101.38.2:443 | media.giphy.com | Fastly | US | unknown |
3200 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3200 | chrome.exe | 151.101.36.193:443 | i.imgur.com | Fastly | US | unknown |
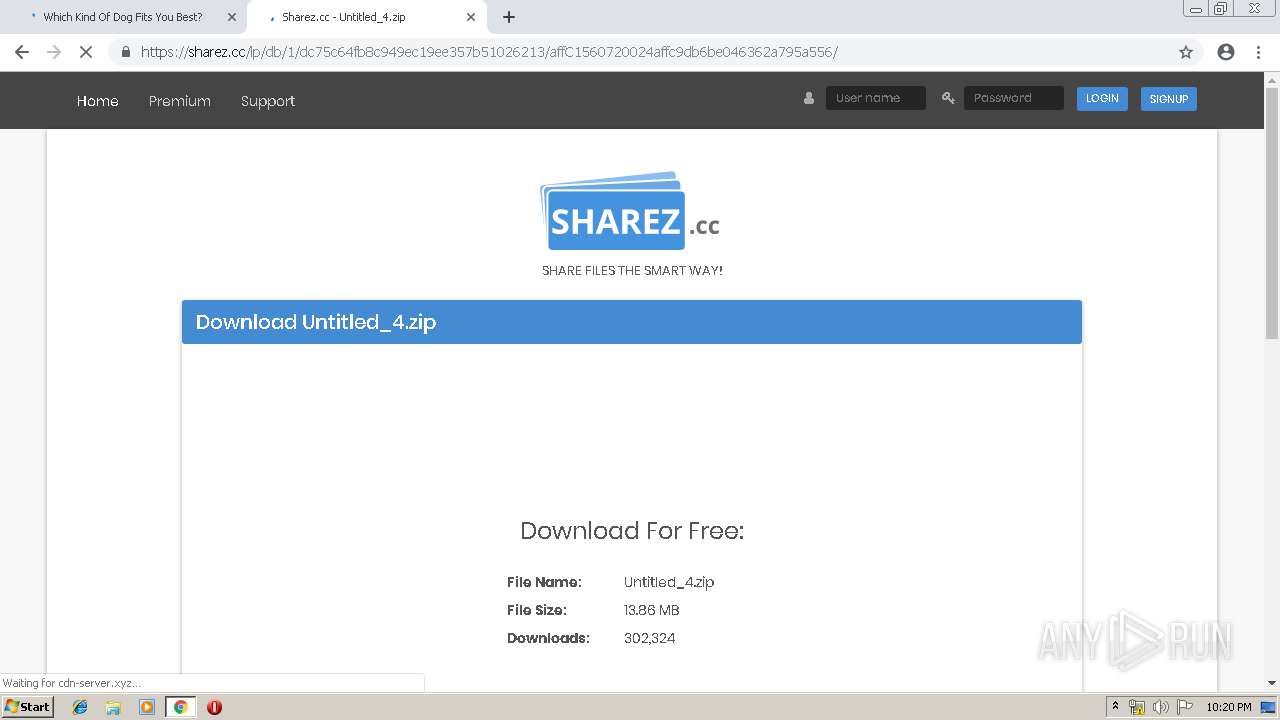
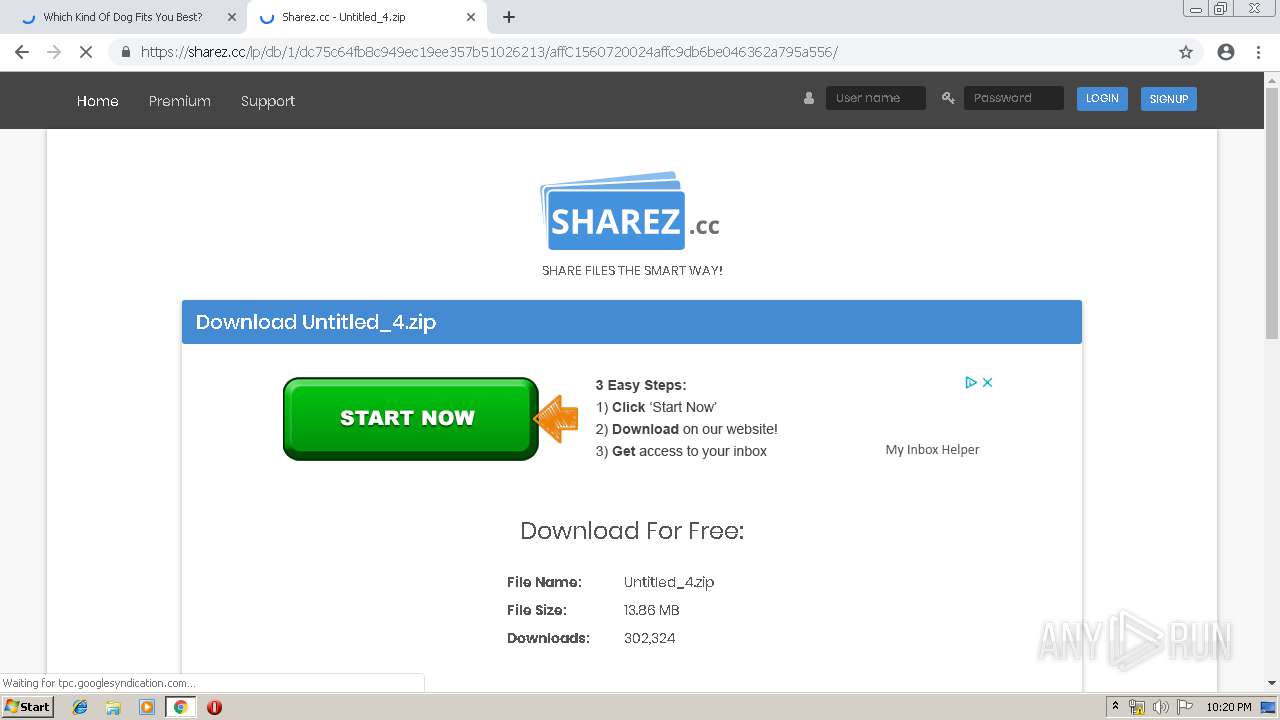
3200 | chrome.exe | 185.66.200.159:443 | sharez.cc | skHosting.eu s.r.o. | SK | unknown |
3200 | chrome.exe | 185.66.200.127:80 | ylx-i.advertica-cdn2.com | skHosting.eu s.r.o. | SK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
carlightsmarket.com |
| unknown |
accounts.google.com |
| shared |
cdn.onesignal.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ylx-1.com |
| unknown |
ylx-4.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
media.giphy.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3200 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |