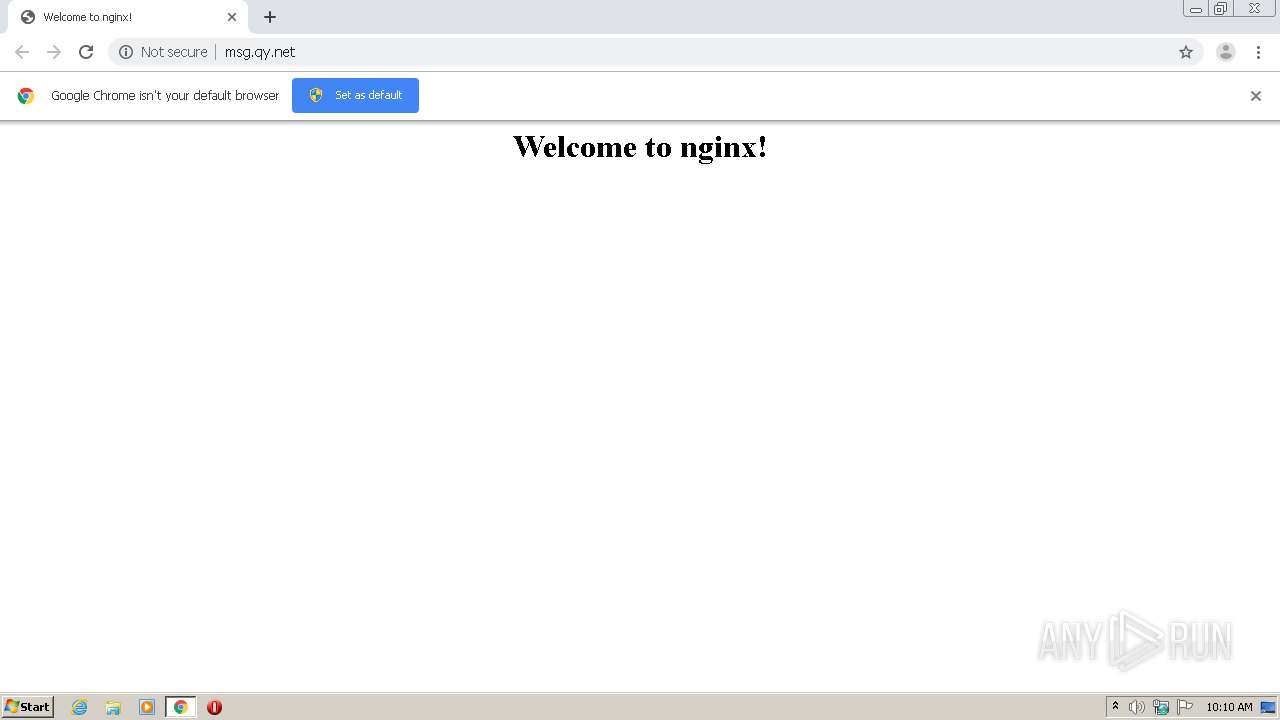
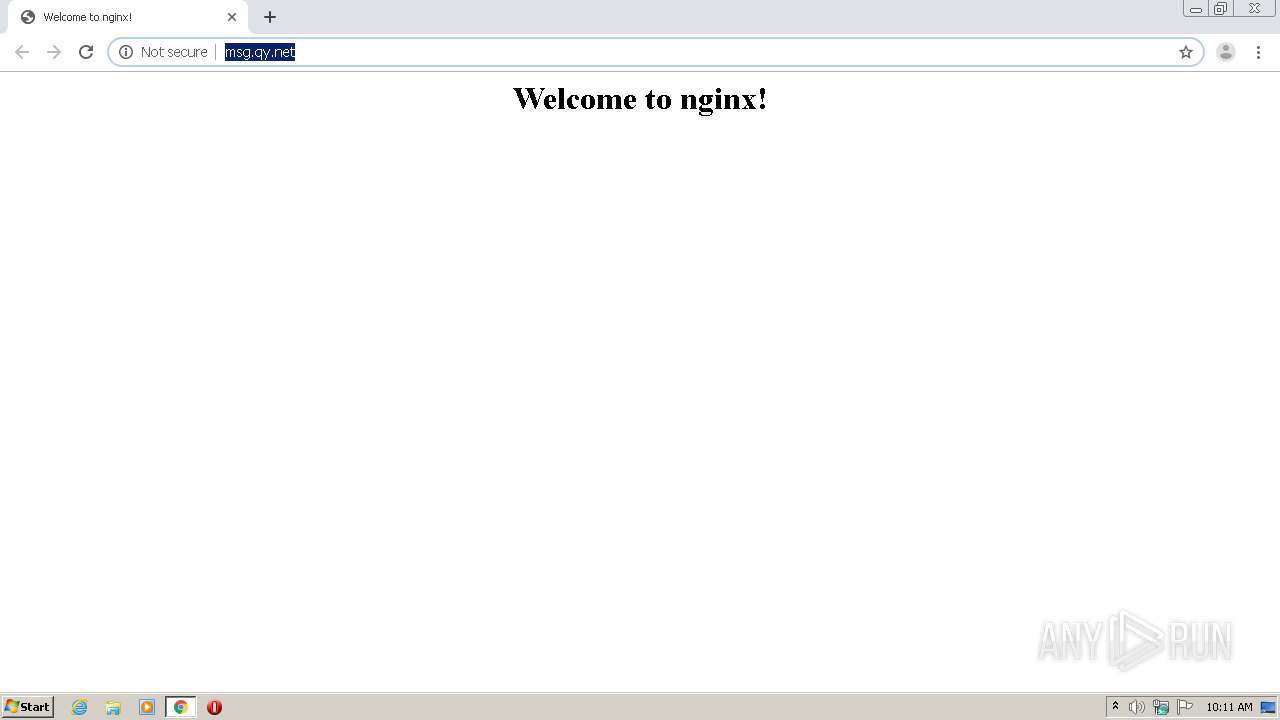
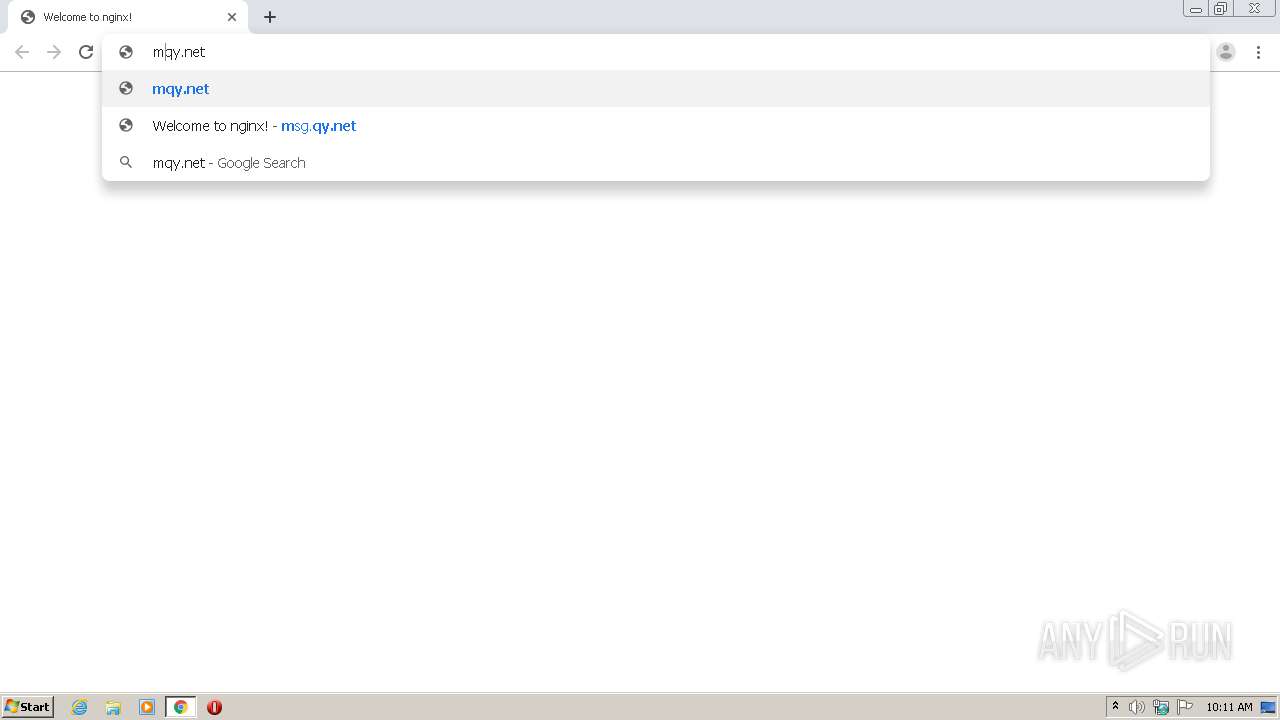
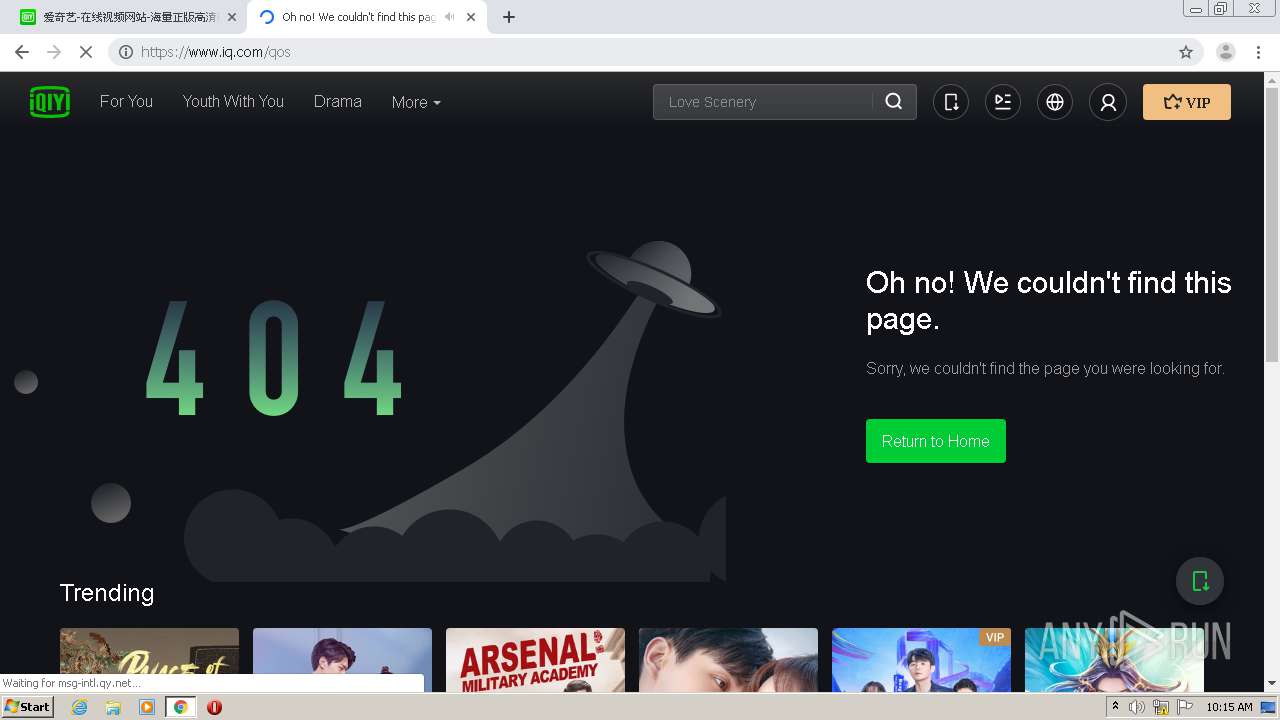
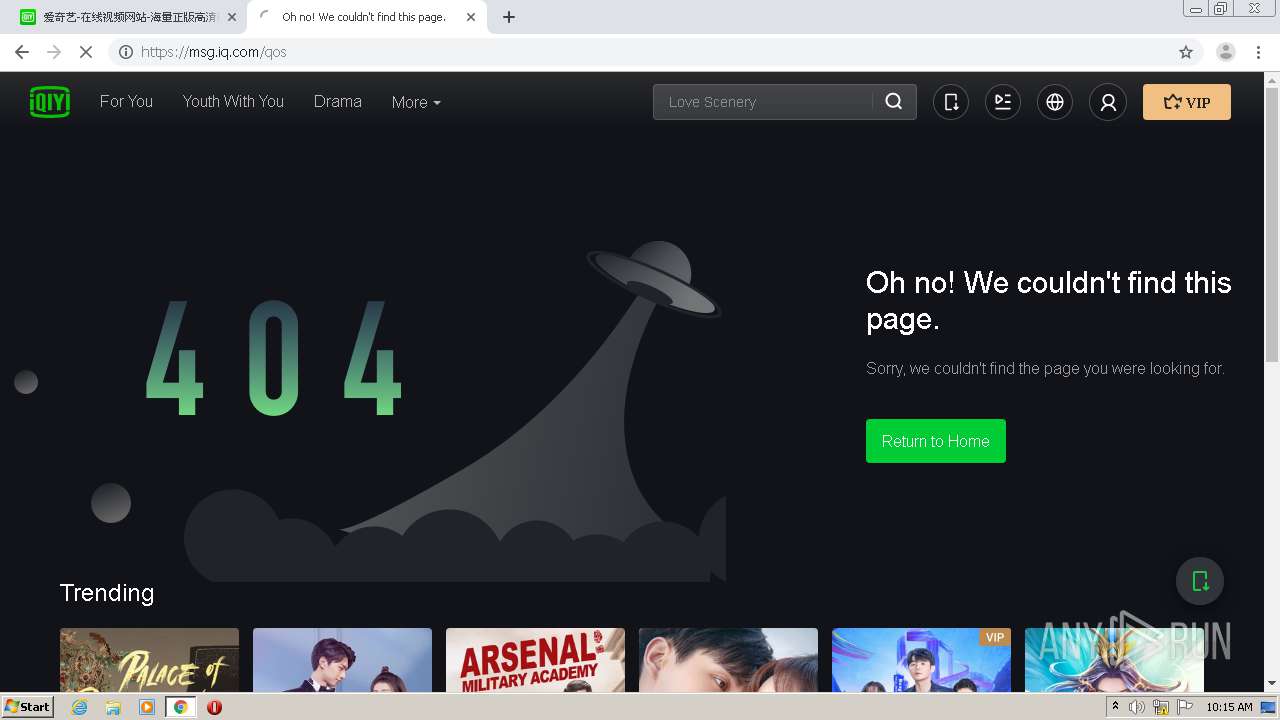
| URL: | http://msg.qy.net |
| Full analysis: | https://app.any.run/tasks/54cc4a63-6e00-4015-abb5-66ff7d88d56b |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2021, 09:10:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C25C09C2F8452AD9747CF943E88A69A6 |
| SHA1: | DD82FDEAFEC196115F50E8EC0DF48ABAA6DCDD9E |
| SHA256: | 9FE15273C9FE65983D6C7F51D1C631BB05FE3CBF3C6682450140943814B90DDA |
| SSDEEP: | 3:N1KTxN0n:CFi |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 992)
Reads the hosts file
- chrome.exe (PID: 992)
- chrome.exe (PID: 308)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9524104877481292803 --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15176080362335342351 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://msg.qy.net" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3367637463974814665 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9726949728391932641 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10027164833148717857 --mojo-platform-channel-handle=2008 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11556737295505538005 --mojo-platform-channel-handle=3528 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10065953179376448654 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3059964675074480209,9800750929595143850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16304211034414051465 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=920 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
663
Read events
591
Write events
69
Delete events
3
Modification events
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 992-13265111444021000 |
Value: 259 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
459
Text files
128
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6098F895-3E0.pma | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8edf26b7-5926-40a4-969a-57e3cc92ebfc.tmp | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF150a69.TMP | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF150a69.TMP | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF150de4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
142
DNS requests
118
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
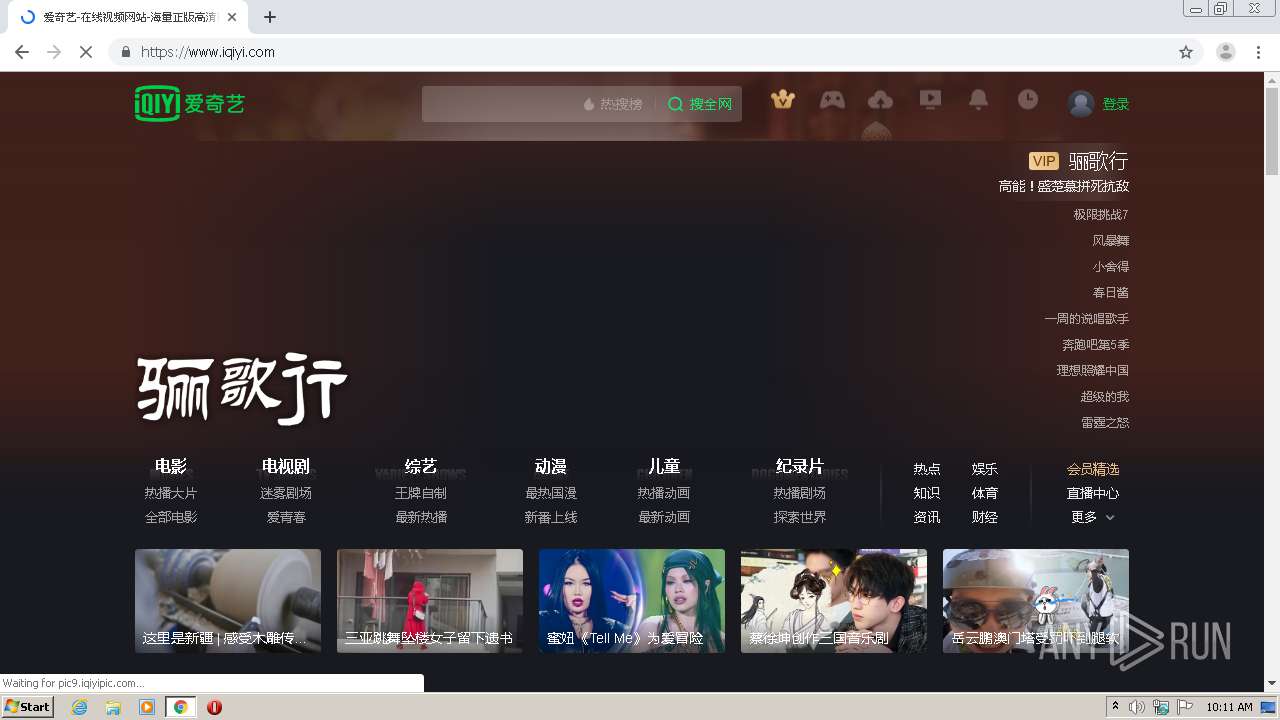
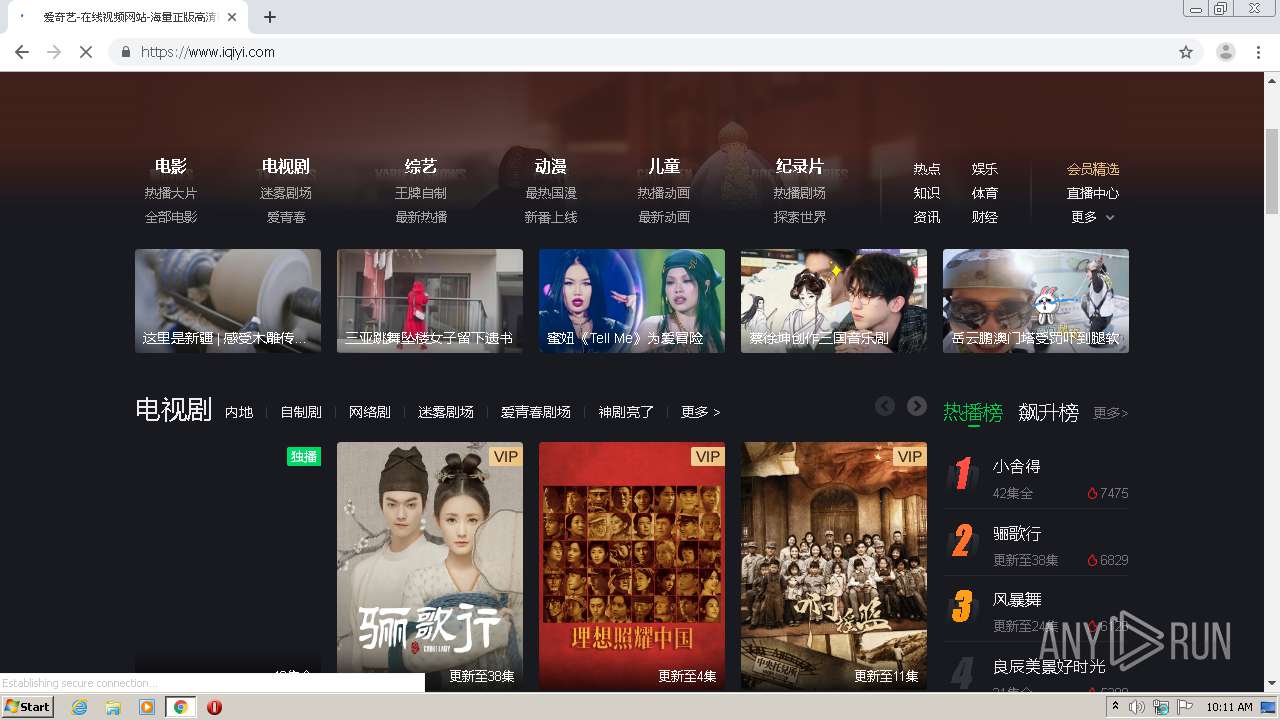
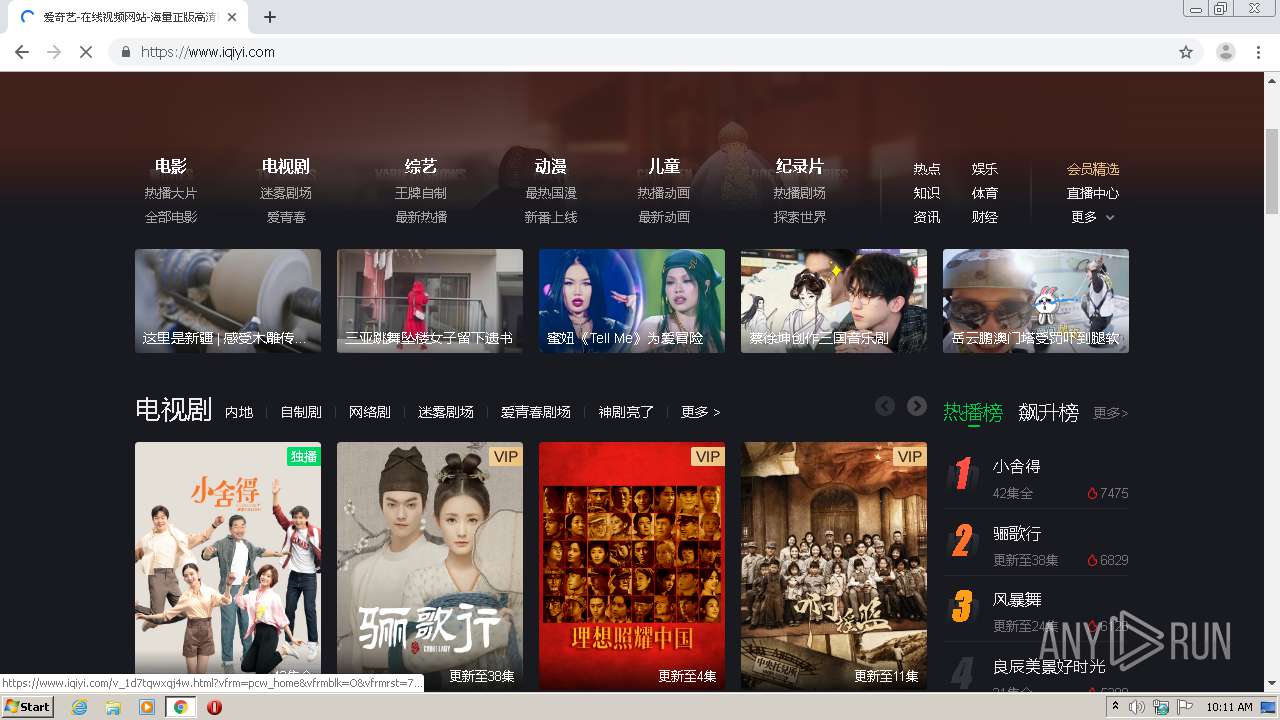
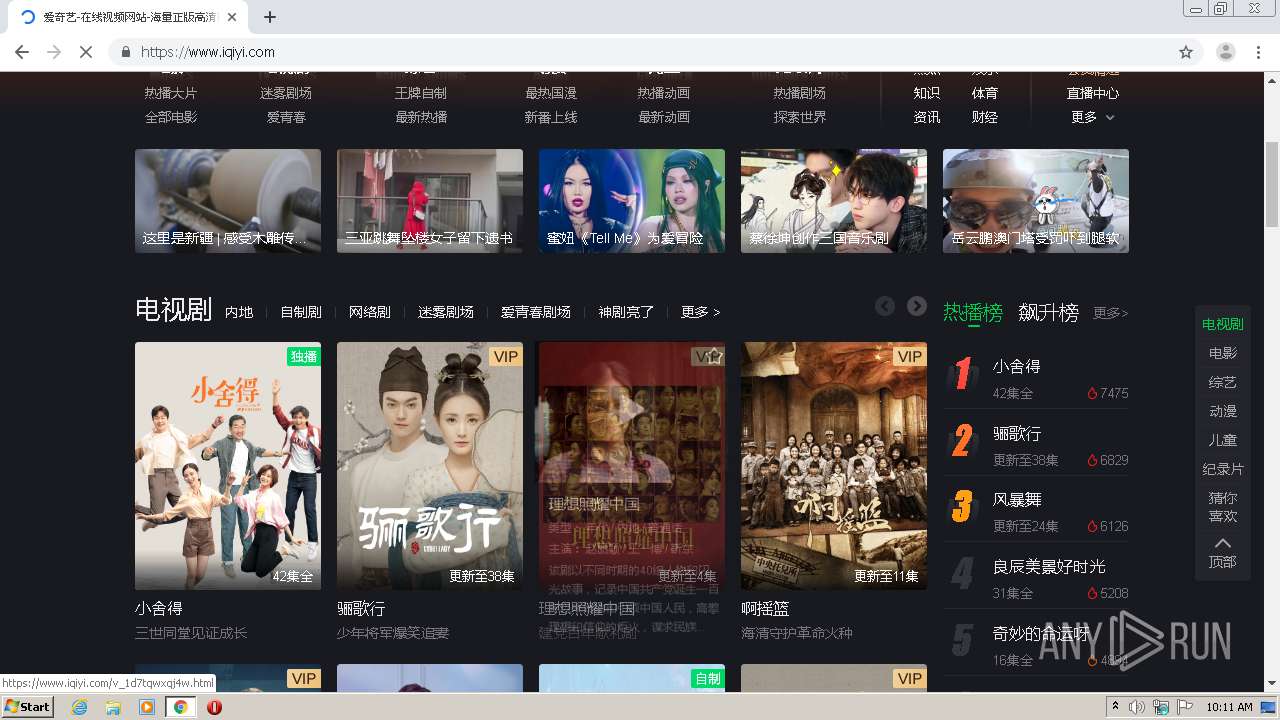
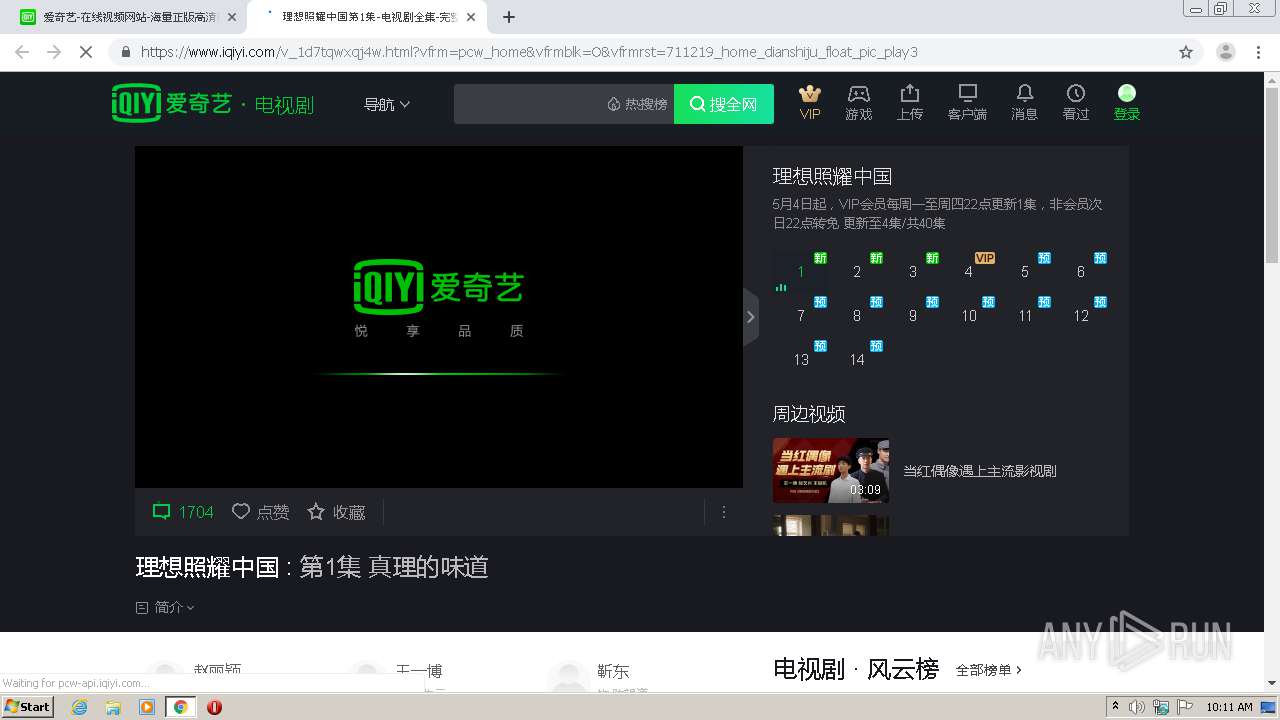
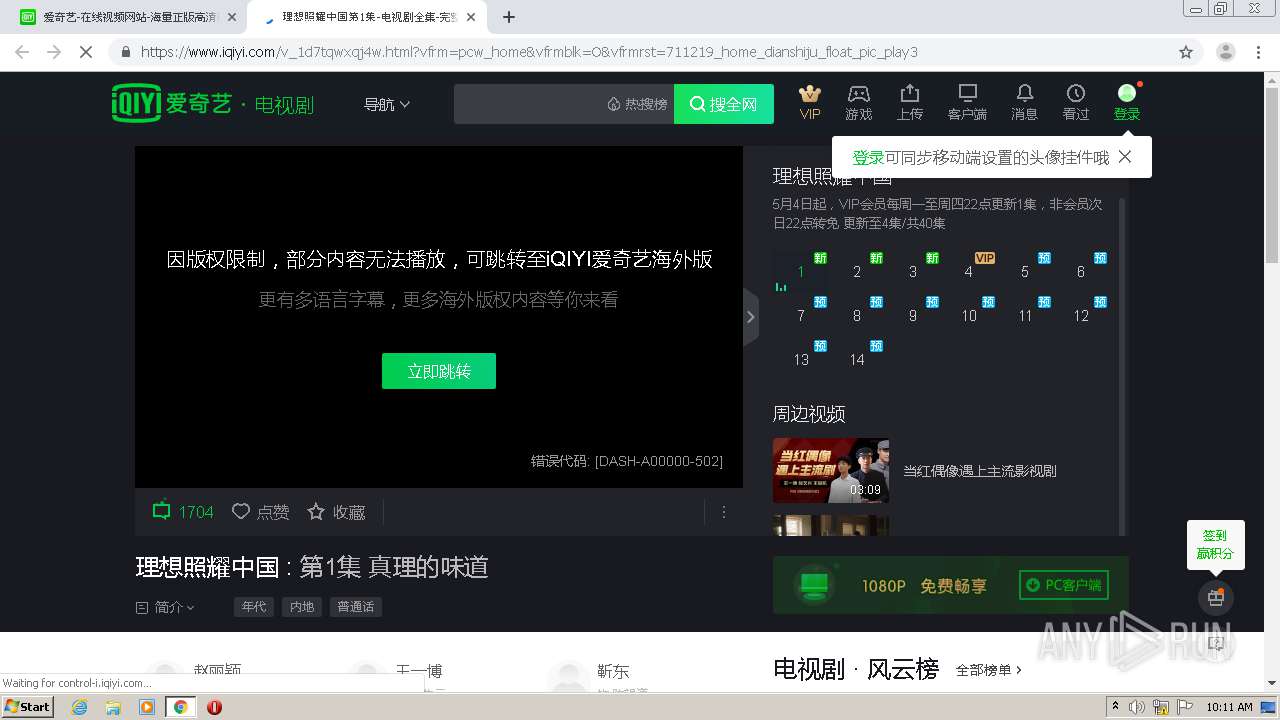
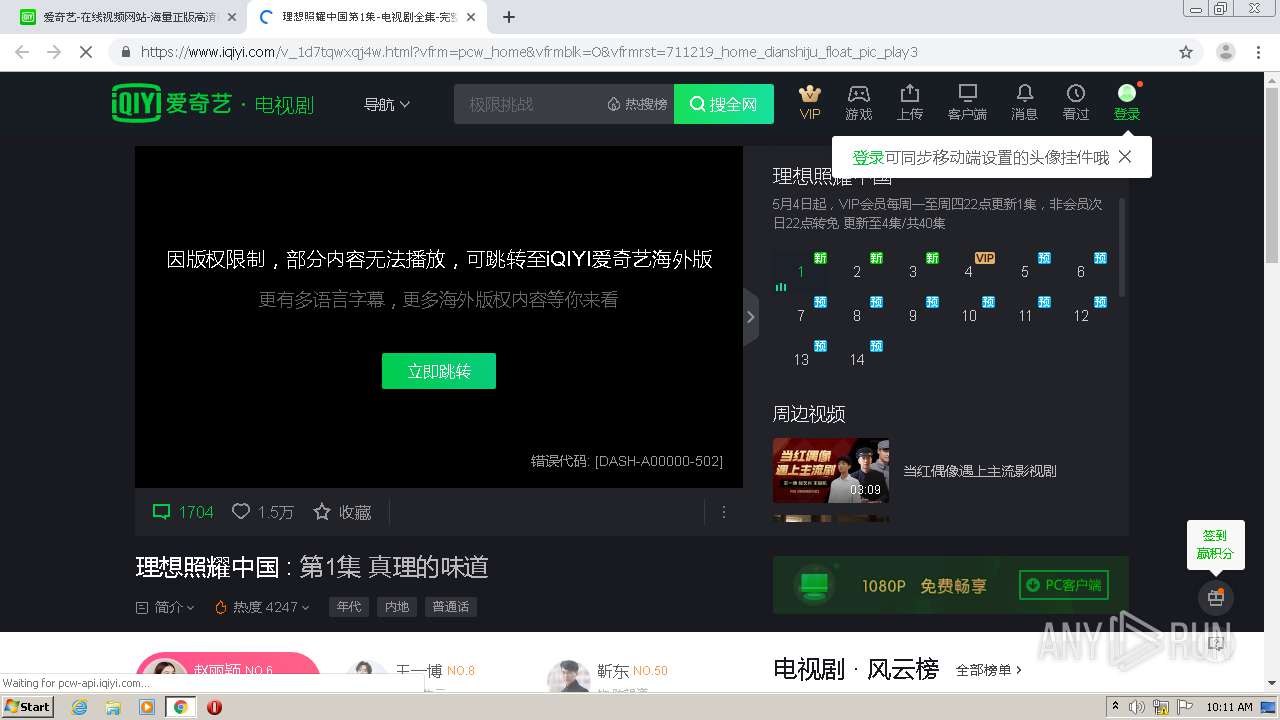
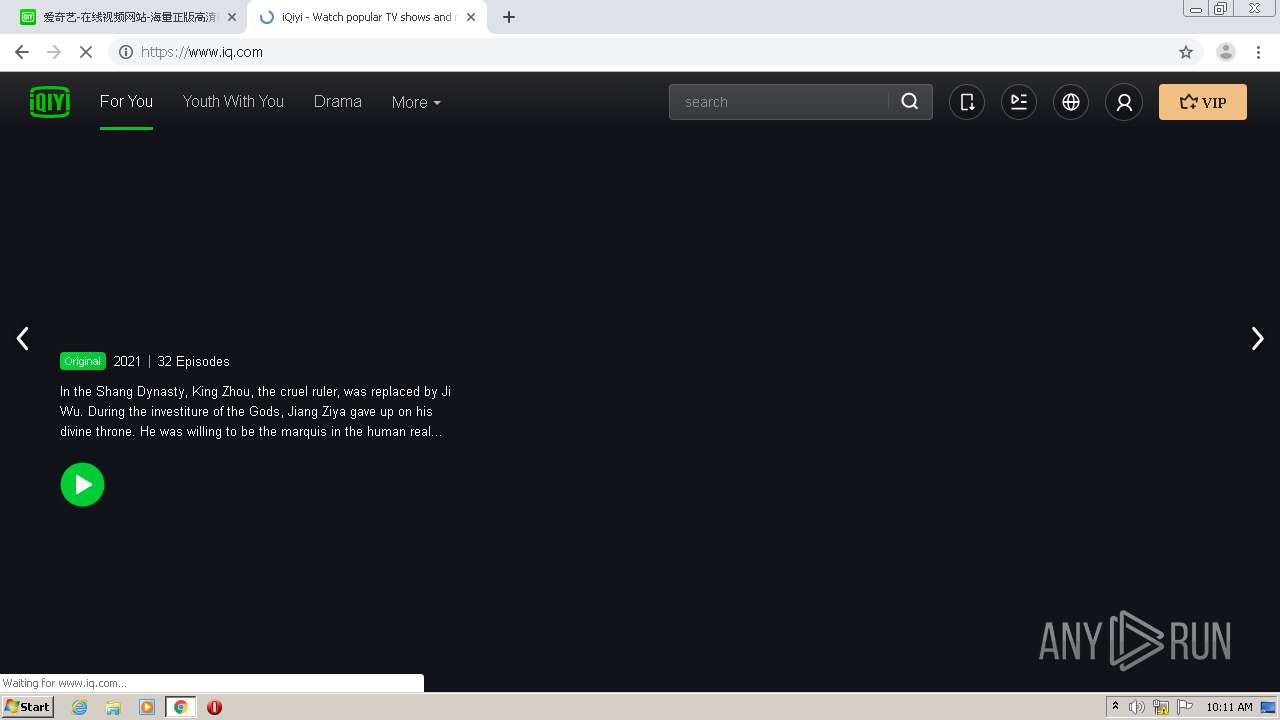
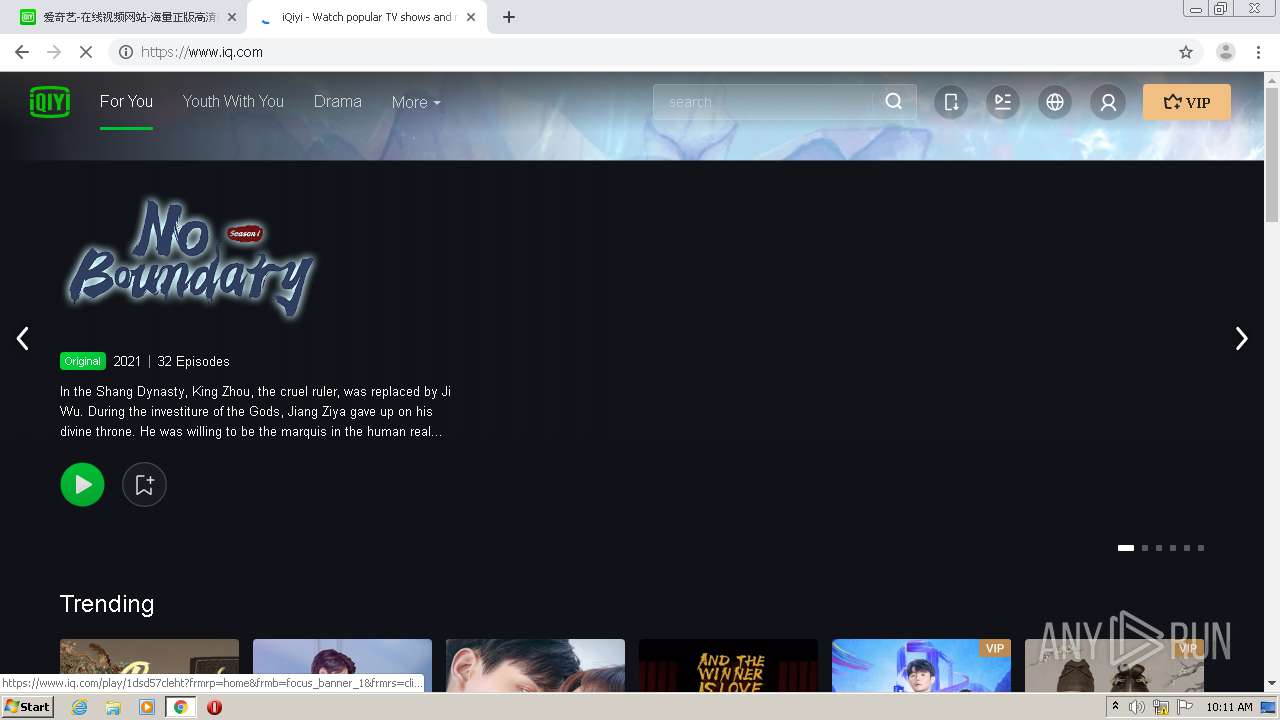
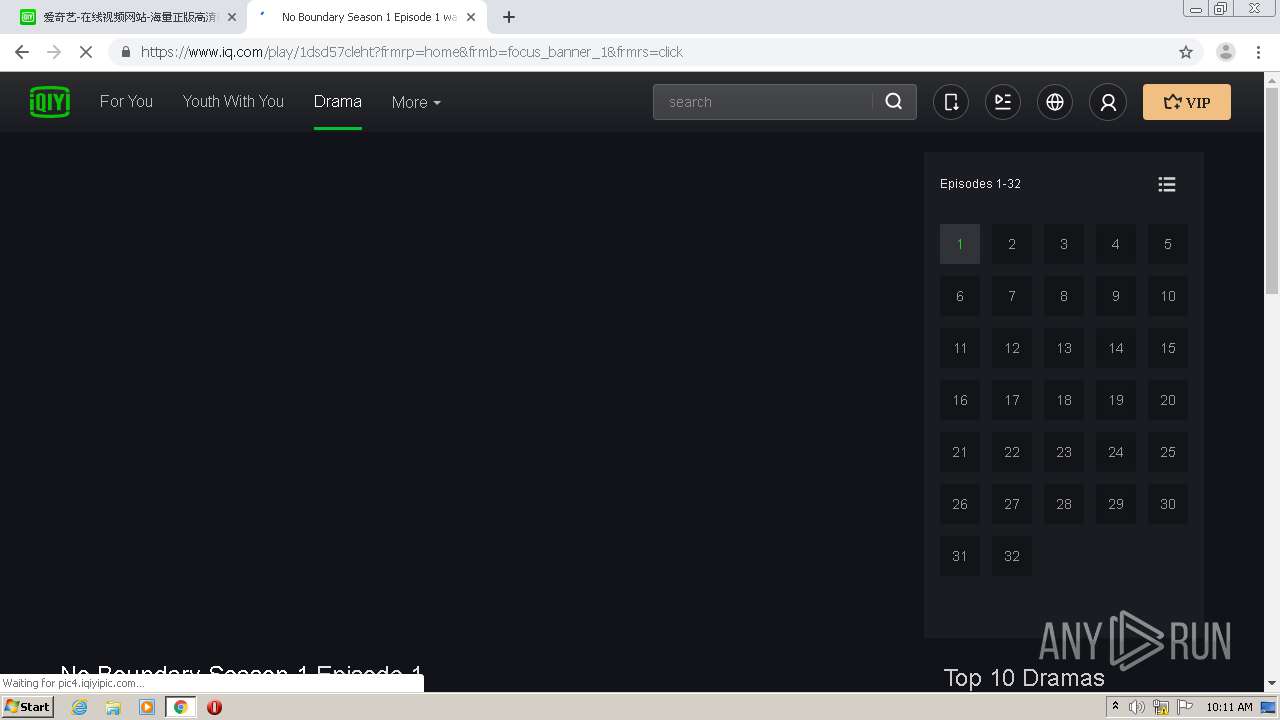
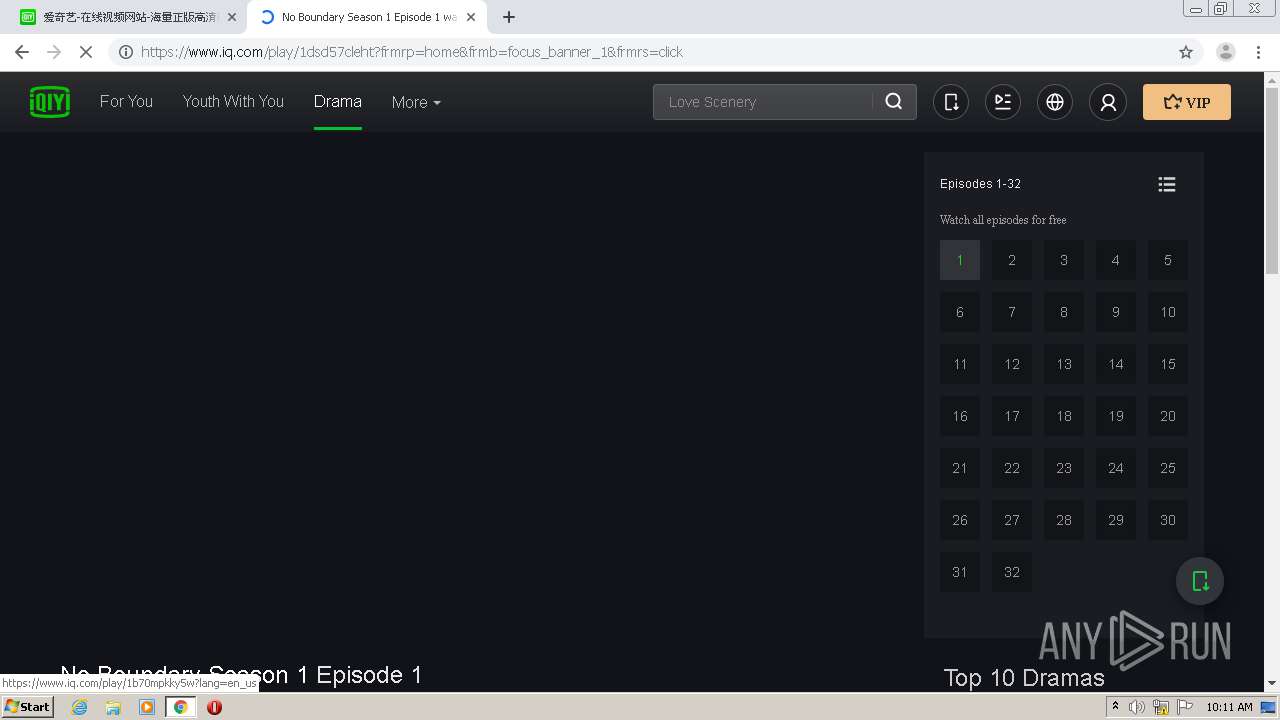
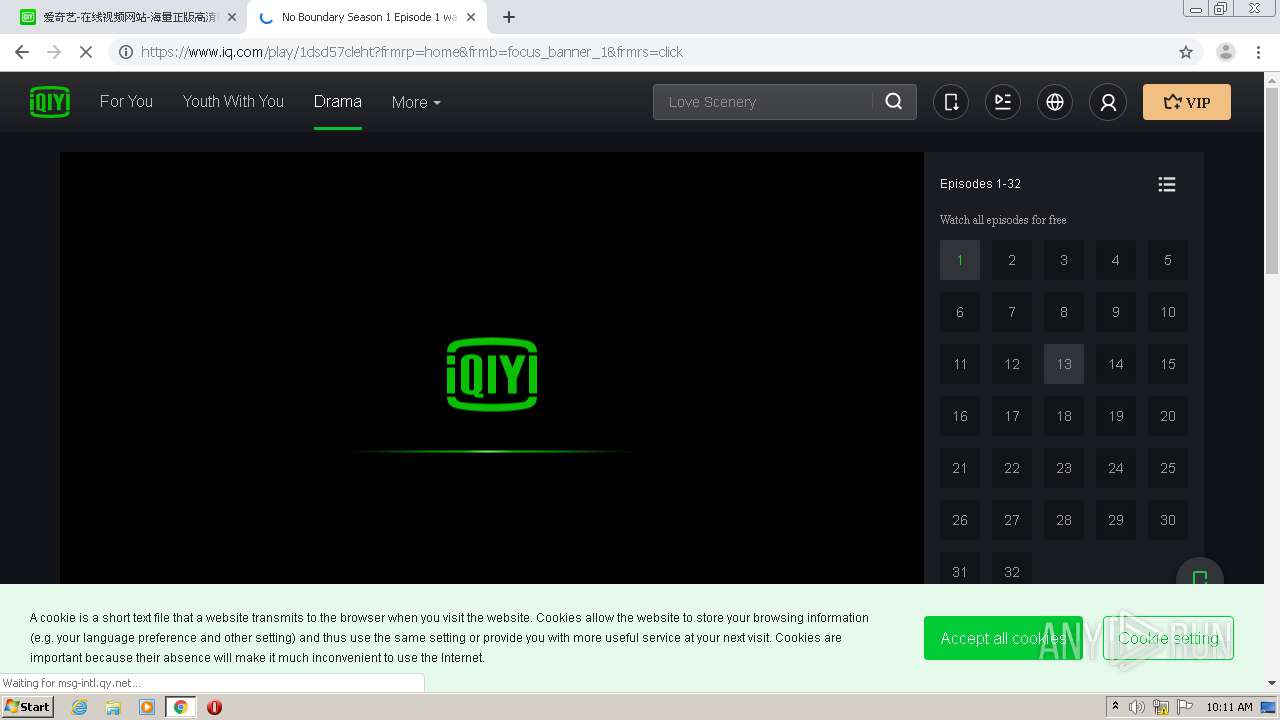
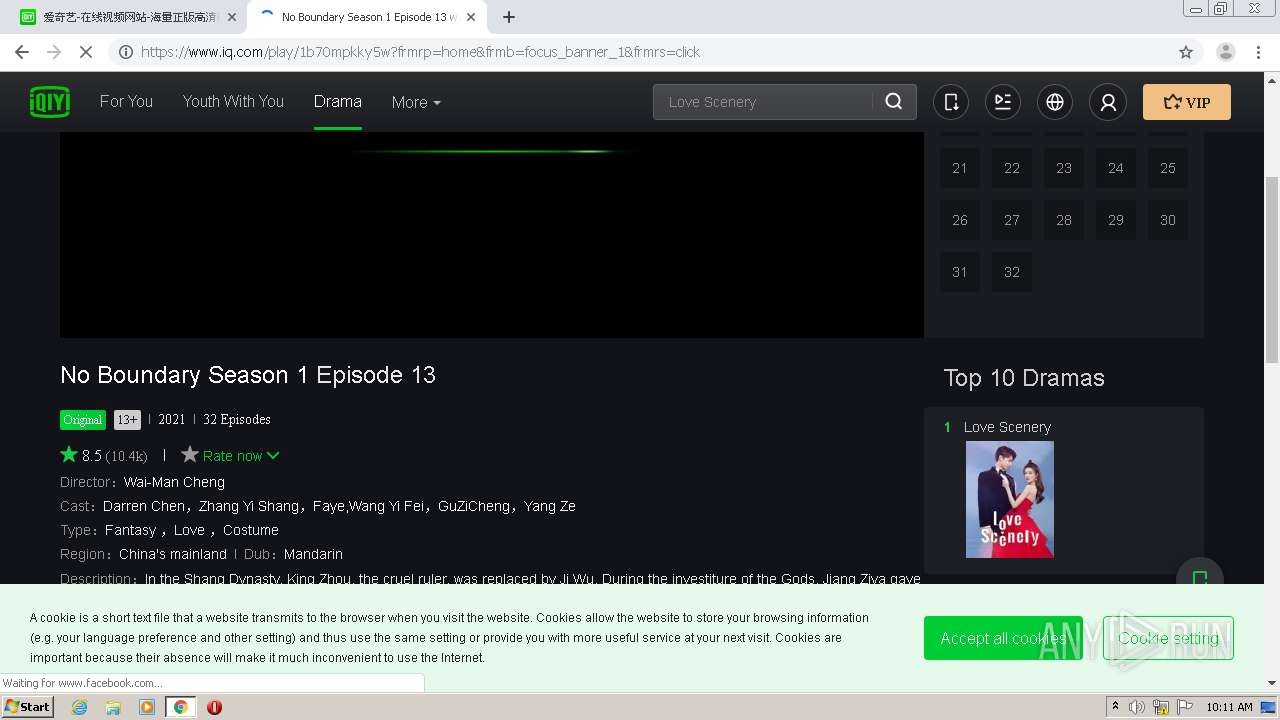
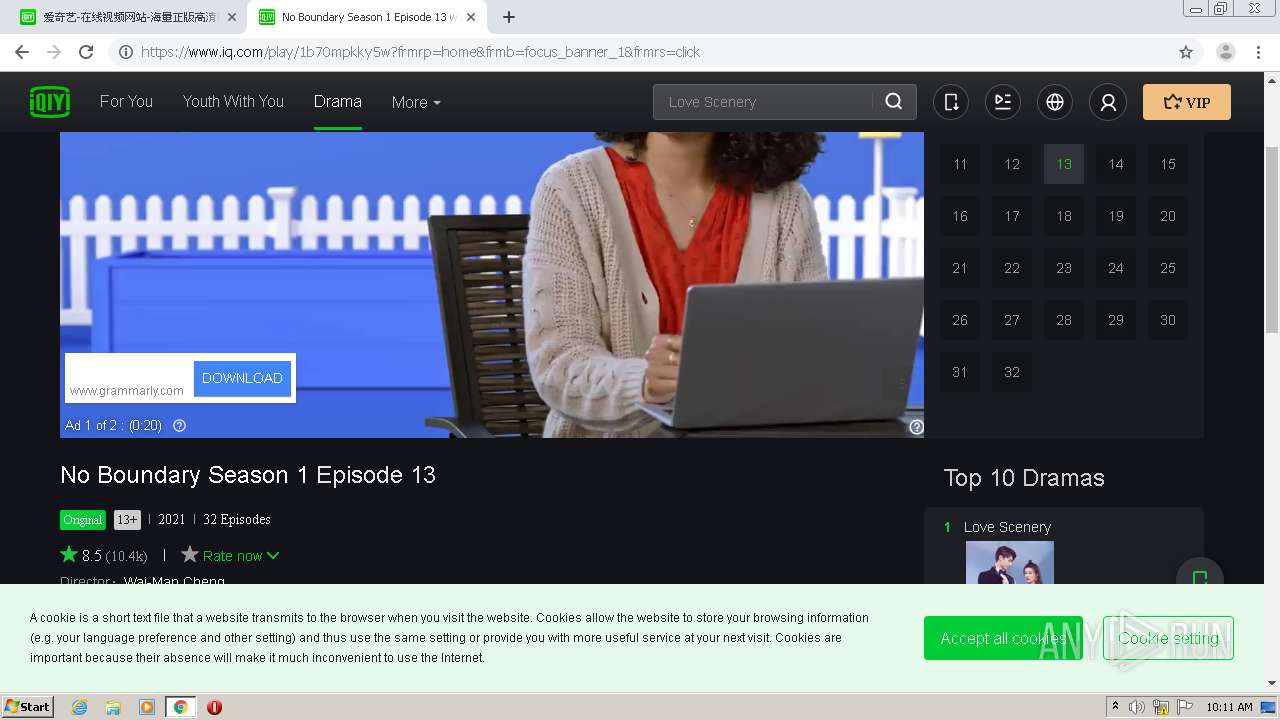
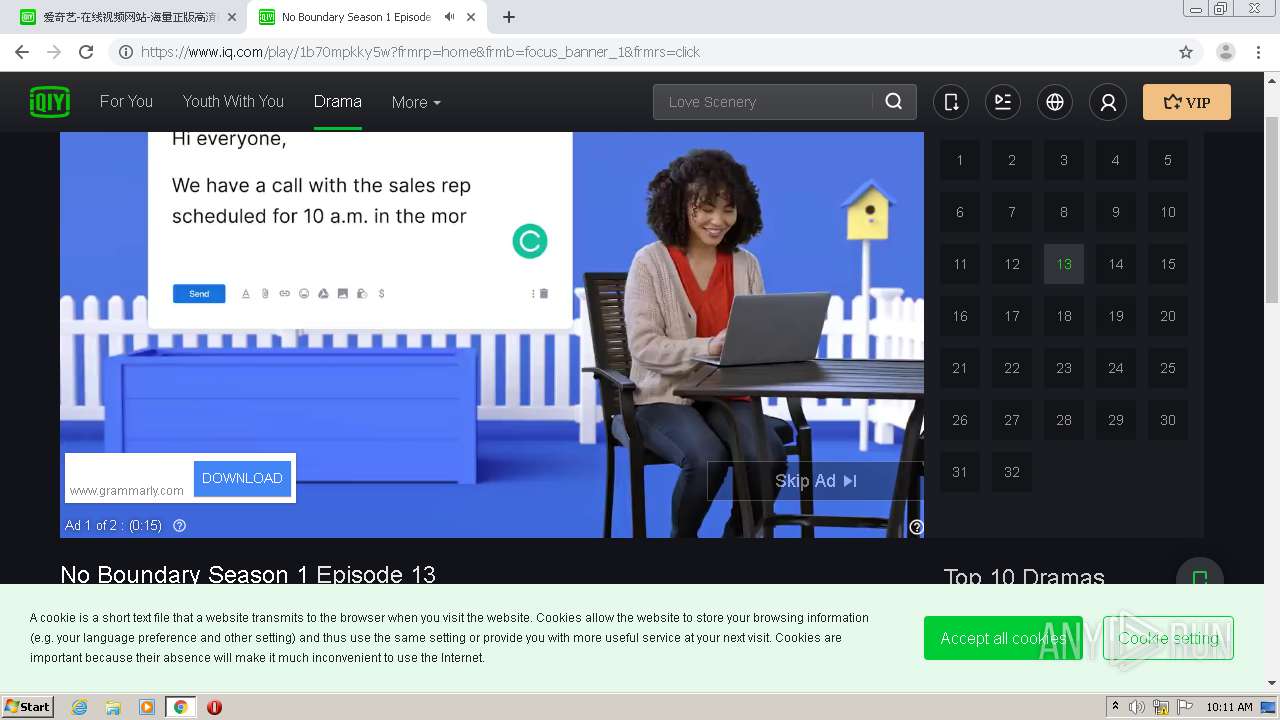
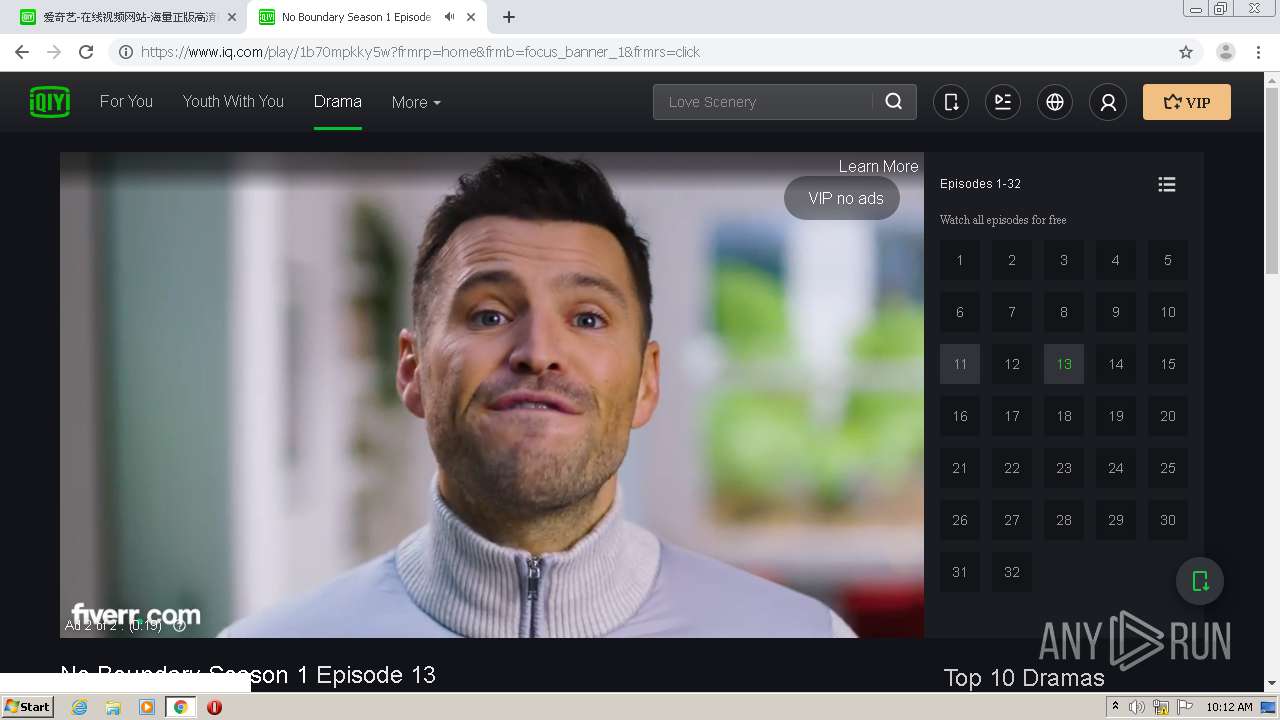
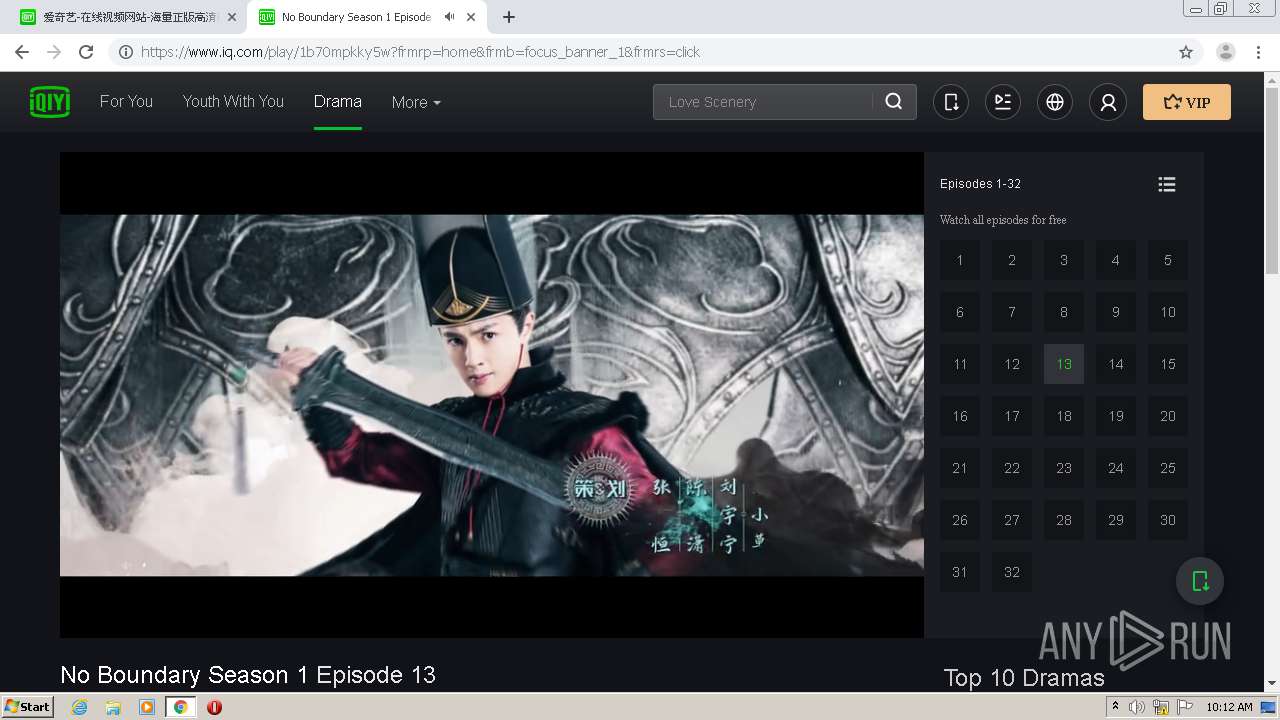
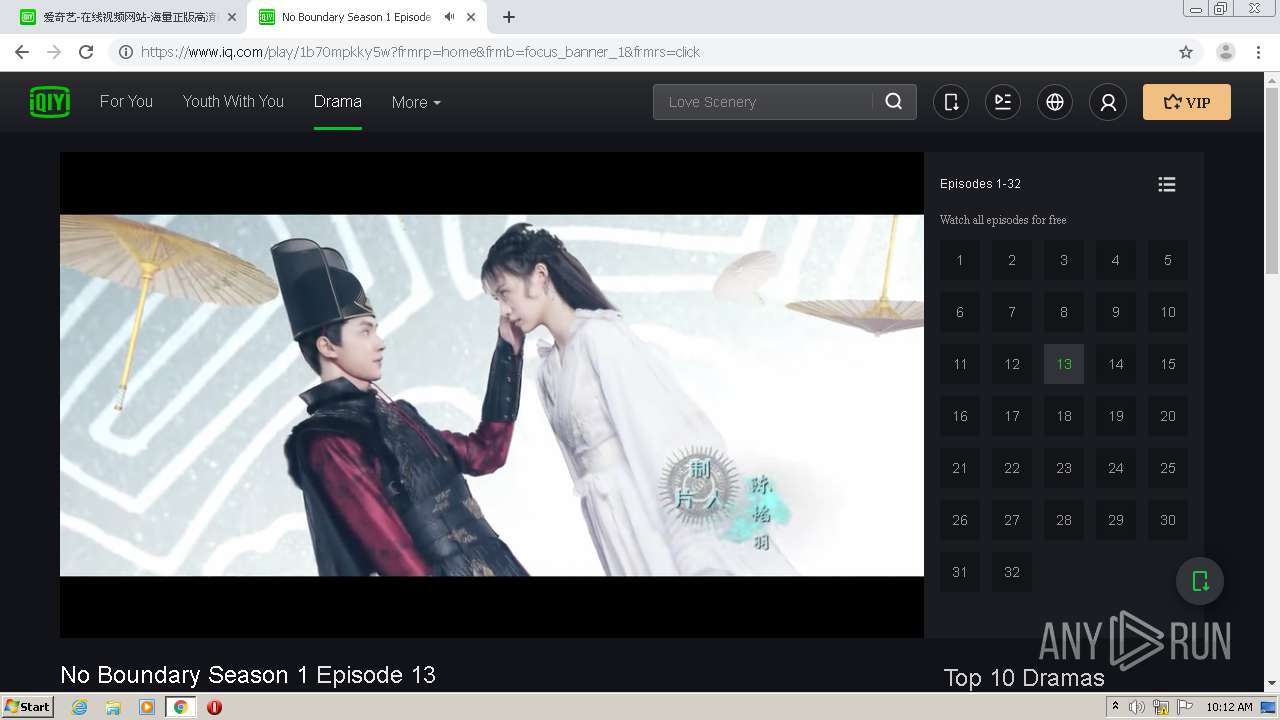
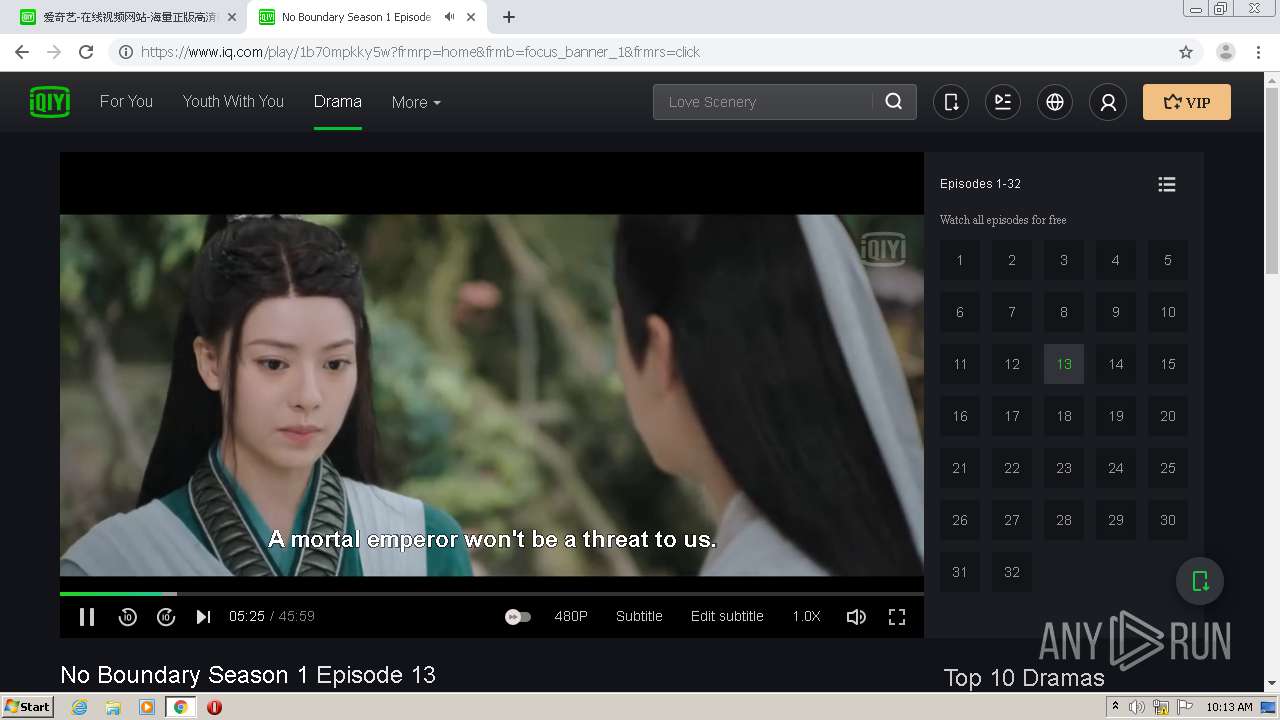
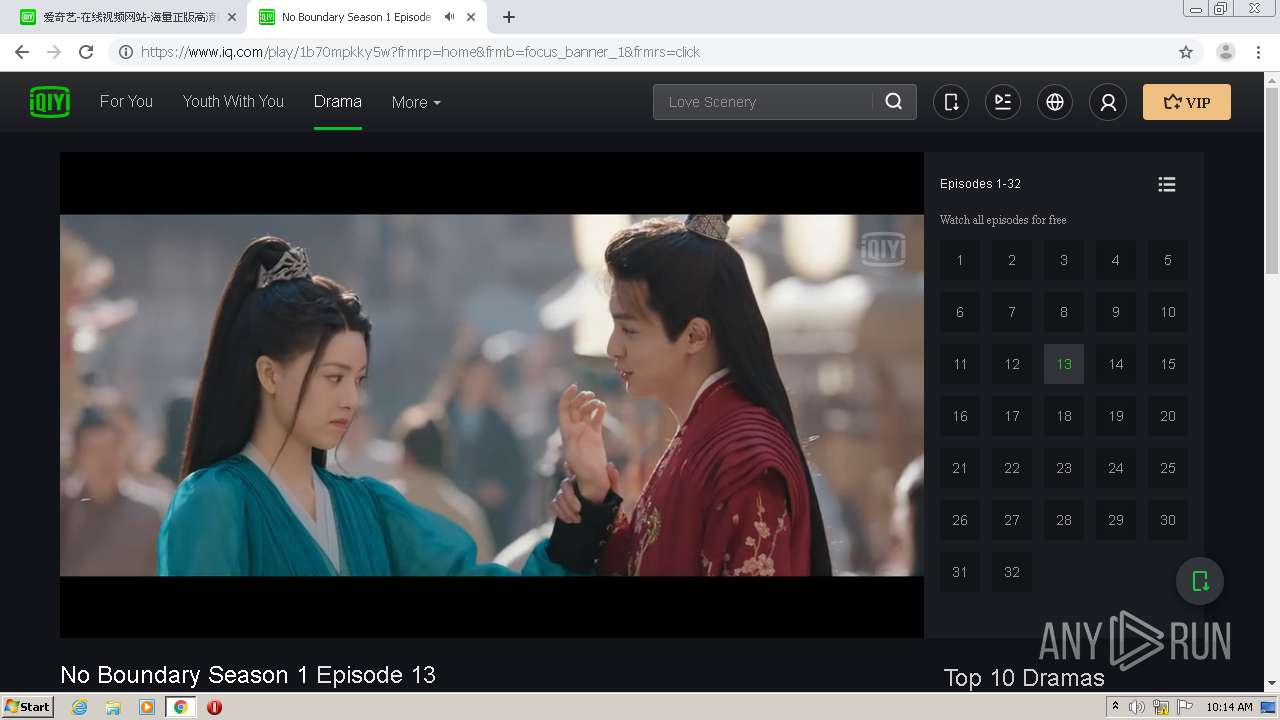
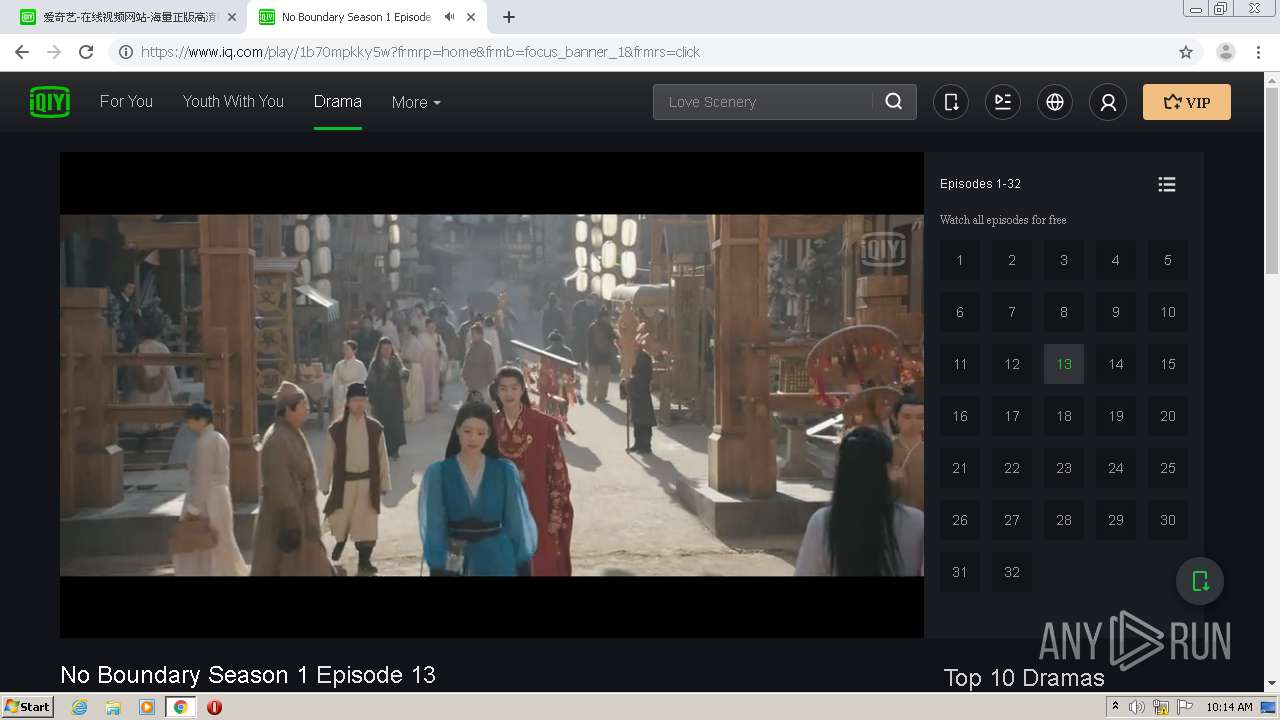
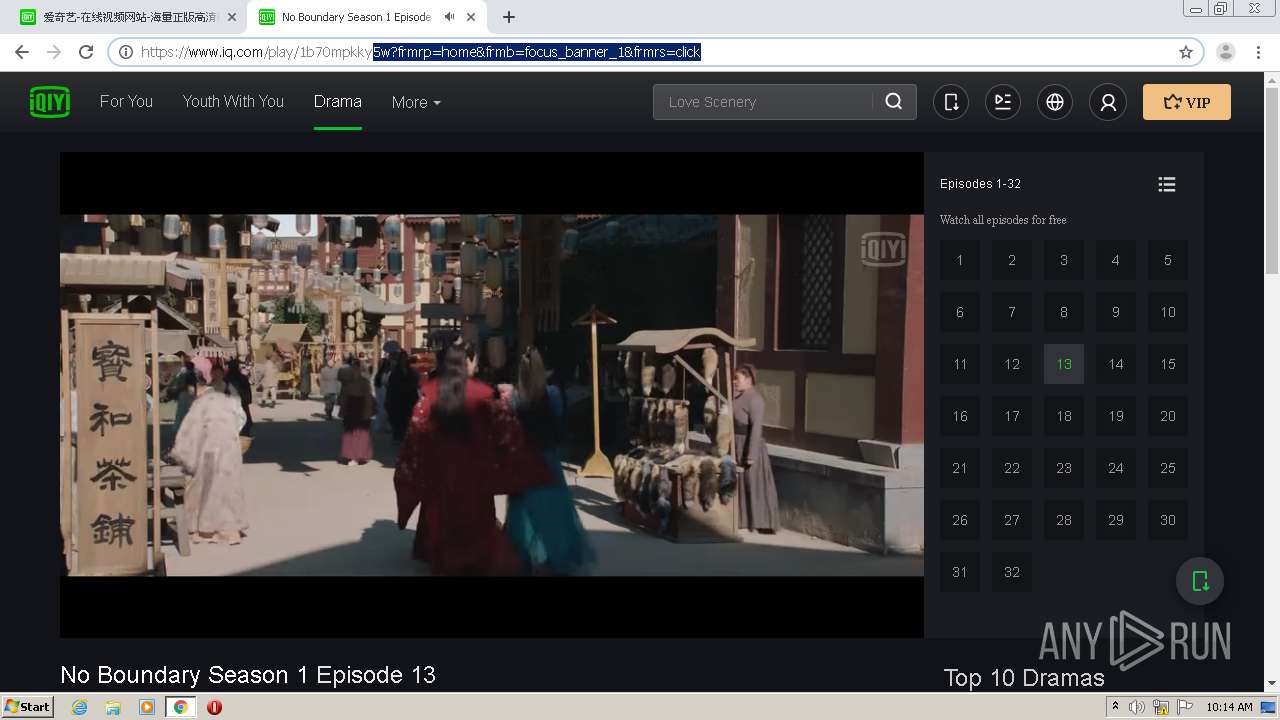
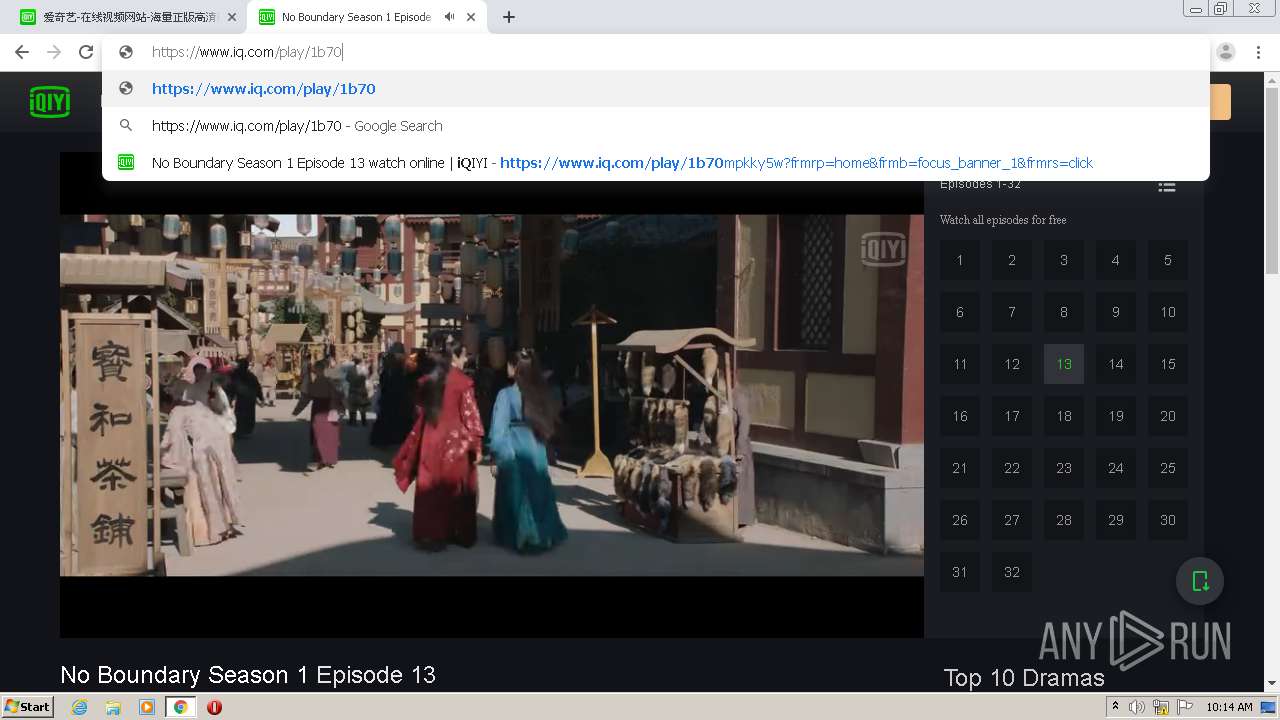
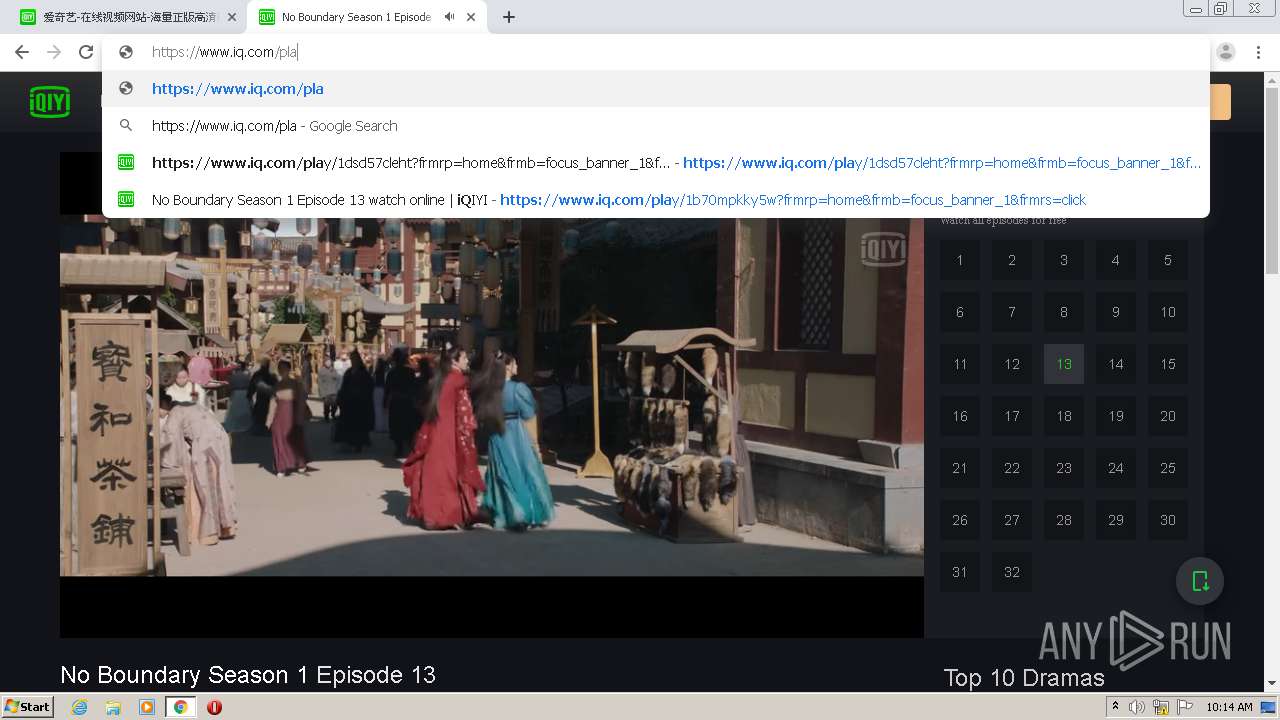
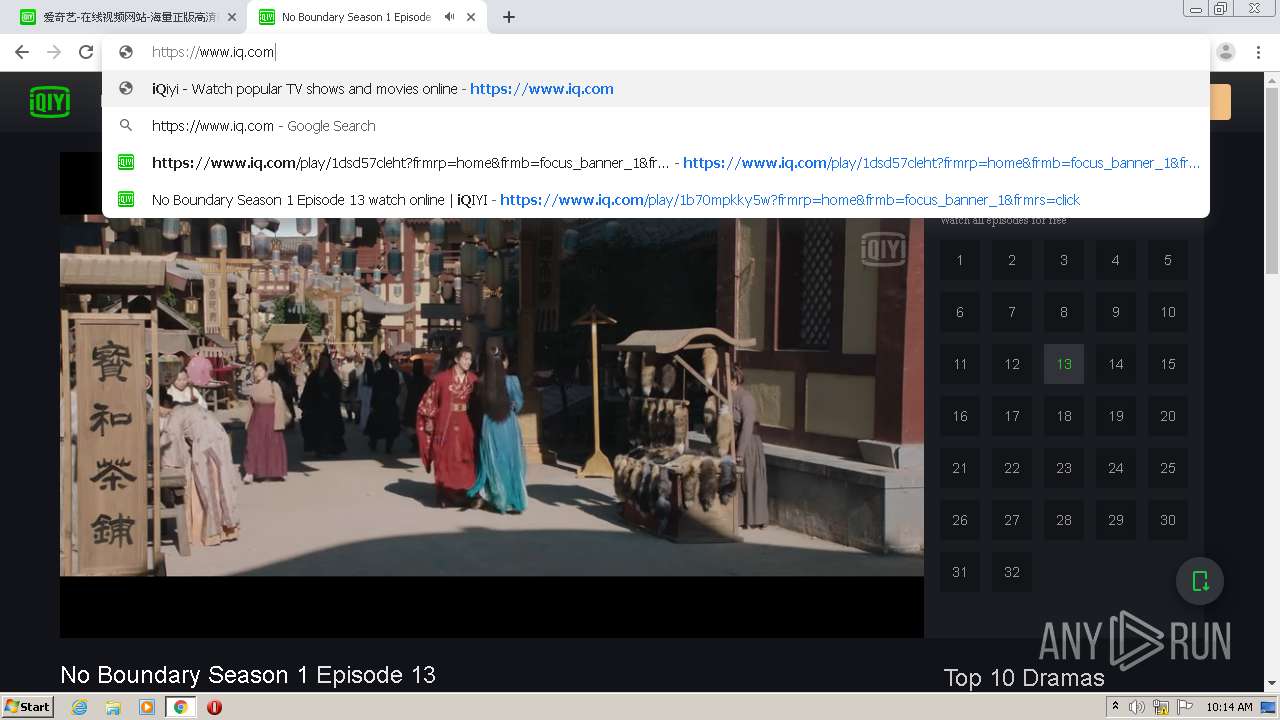
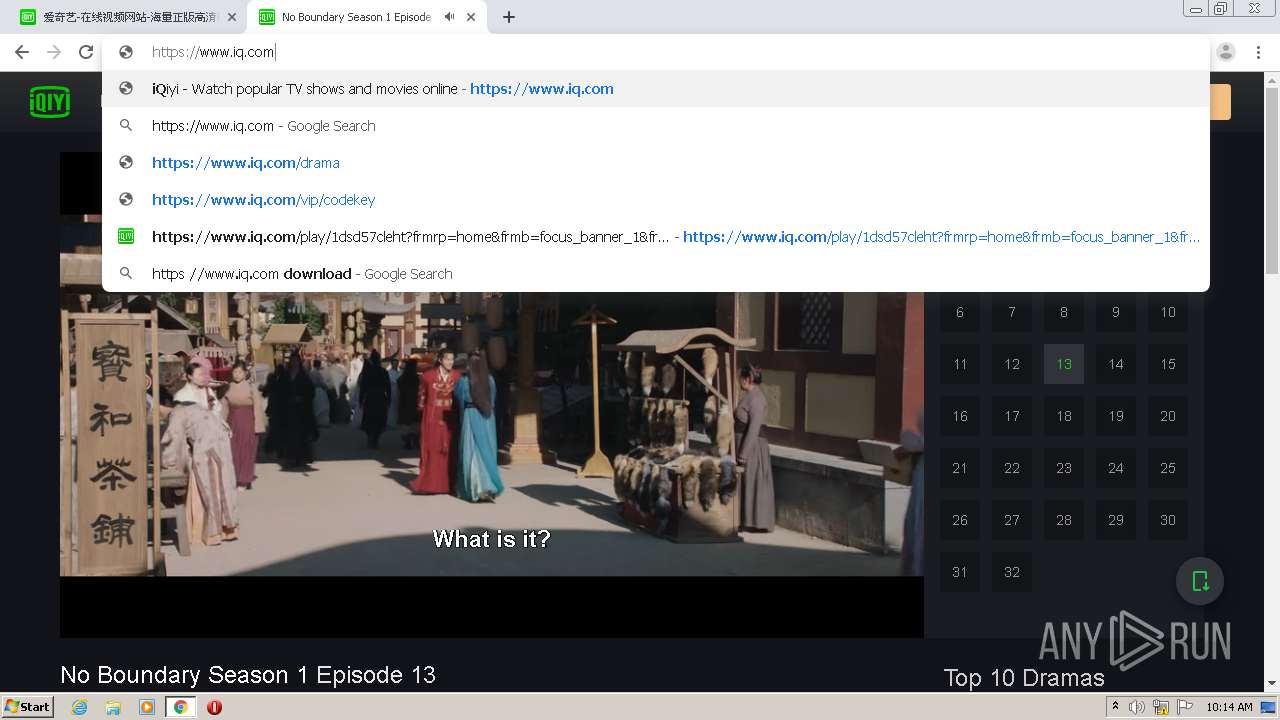
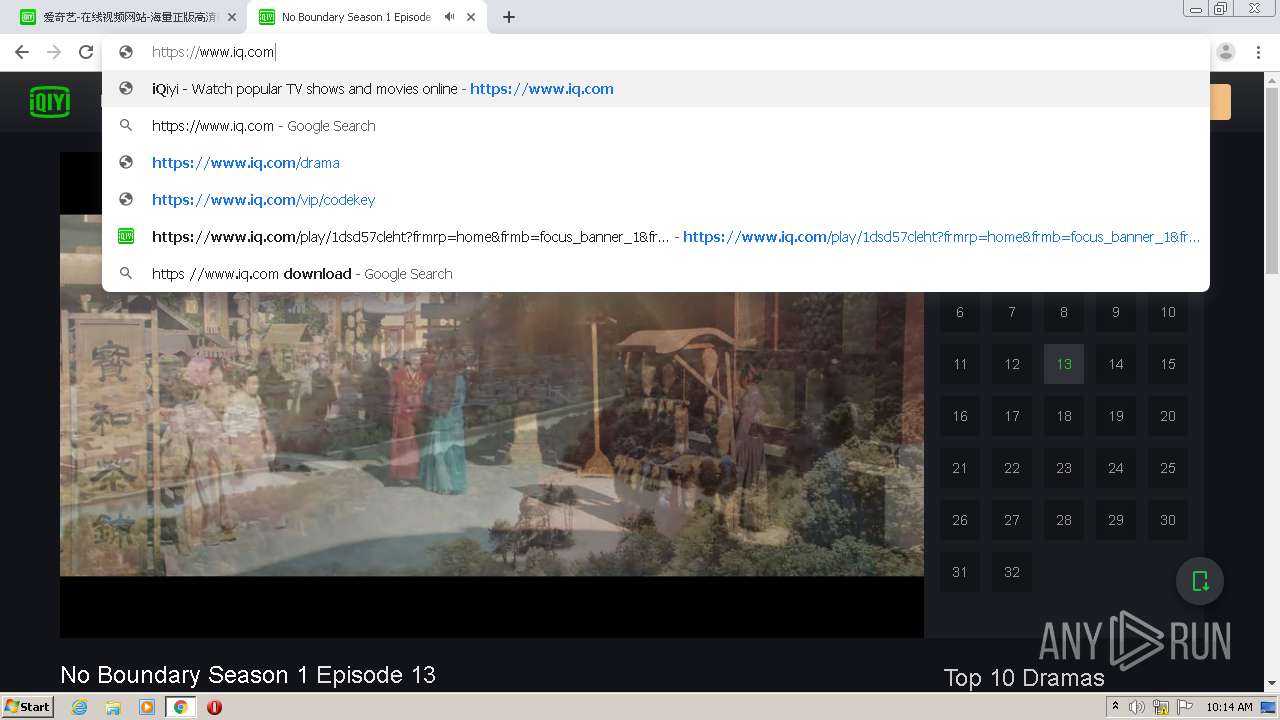
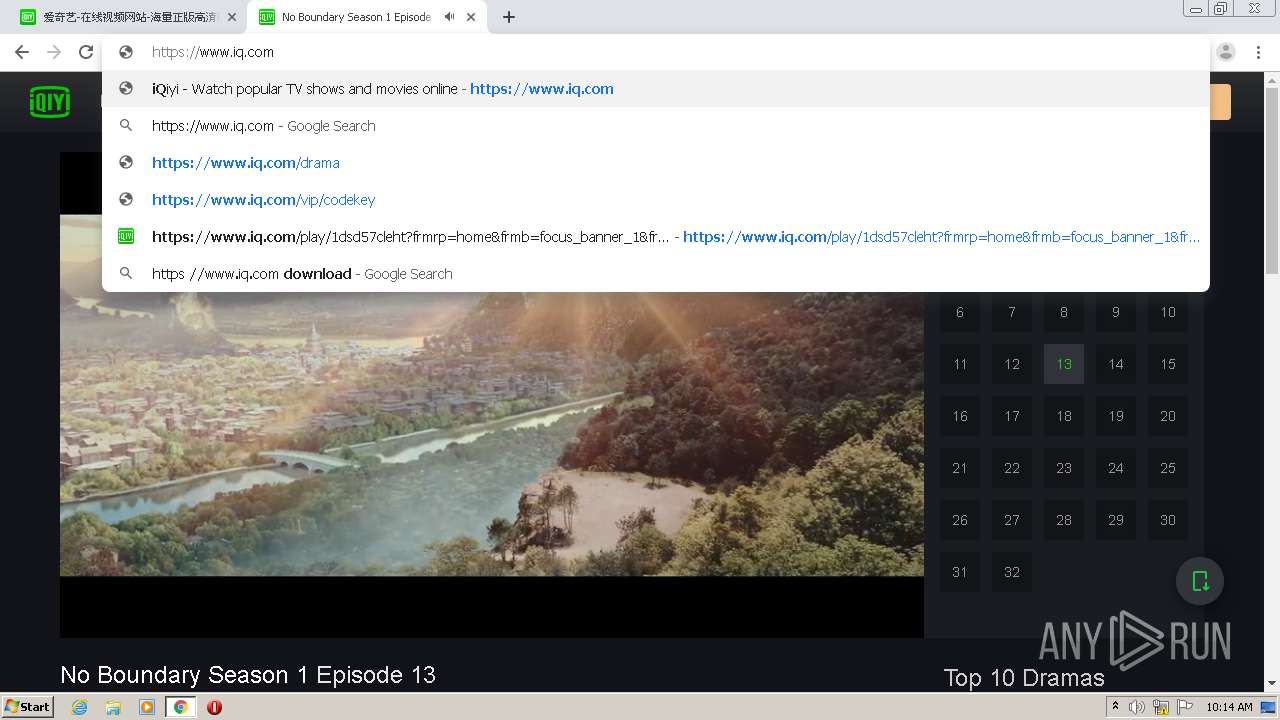
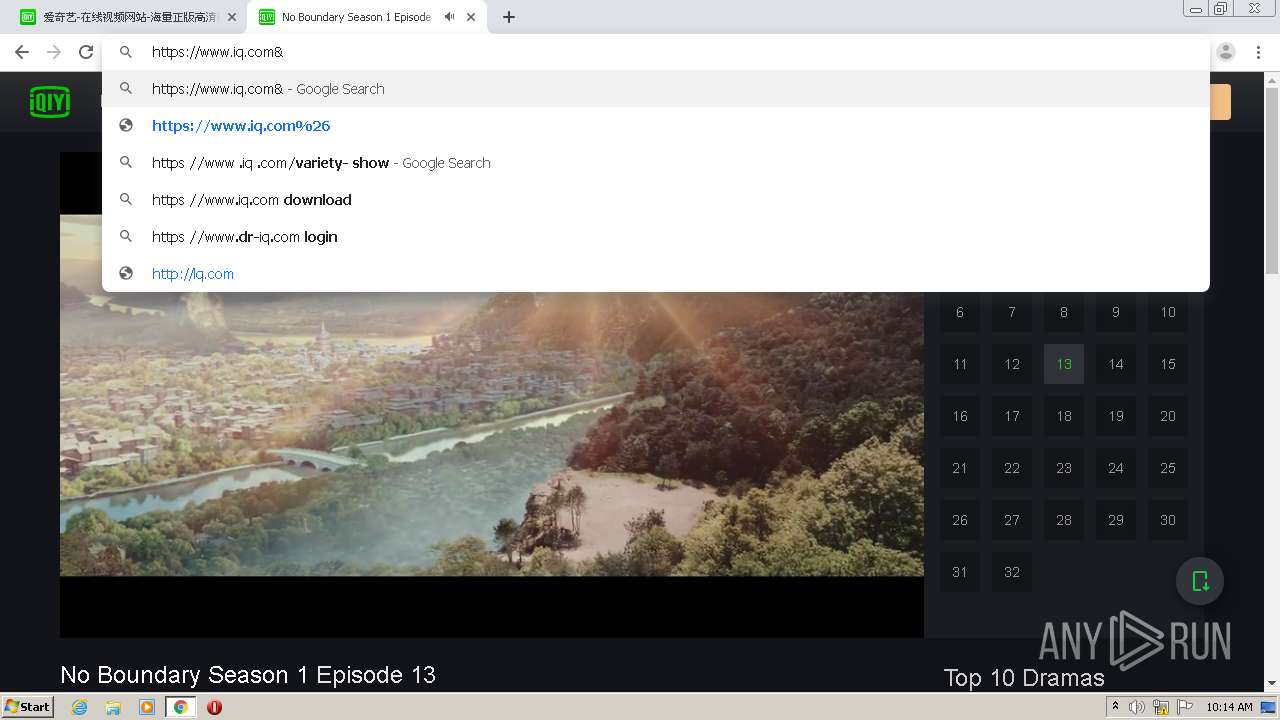
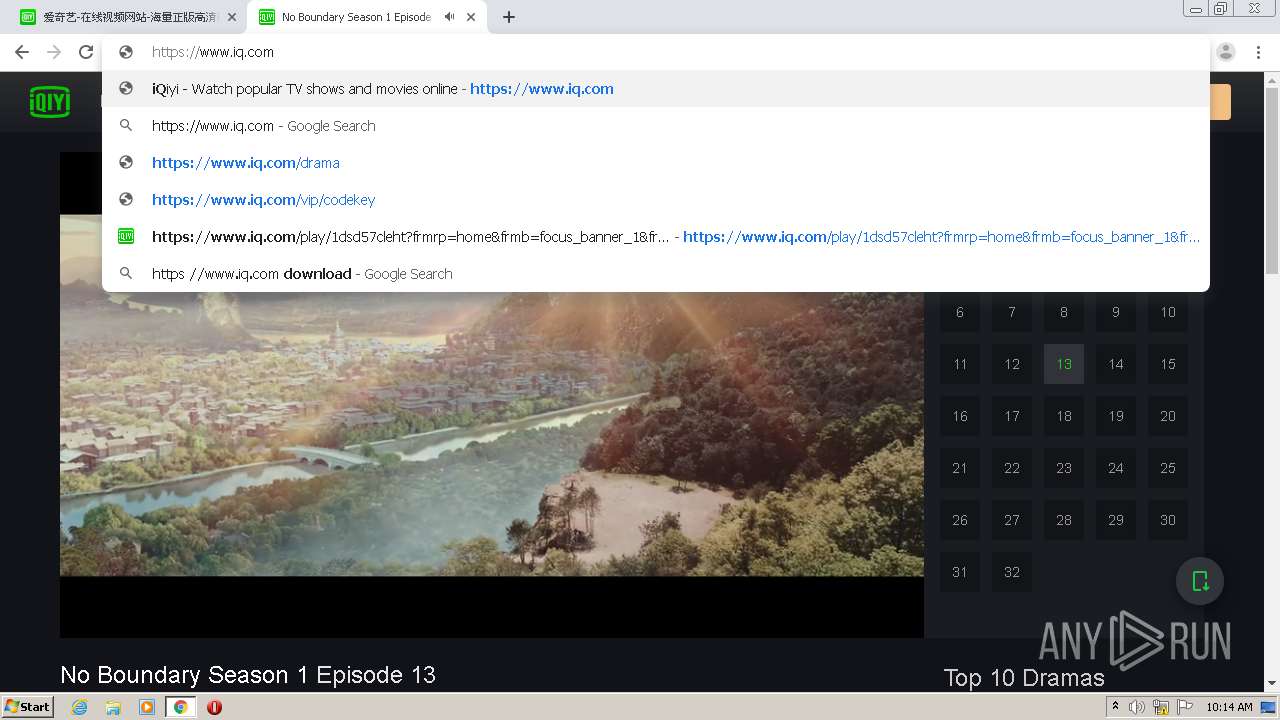
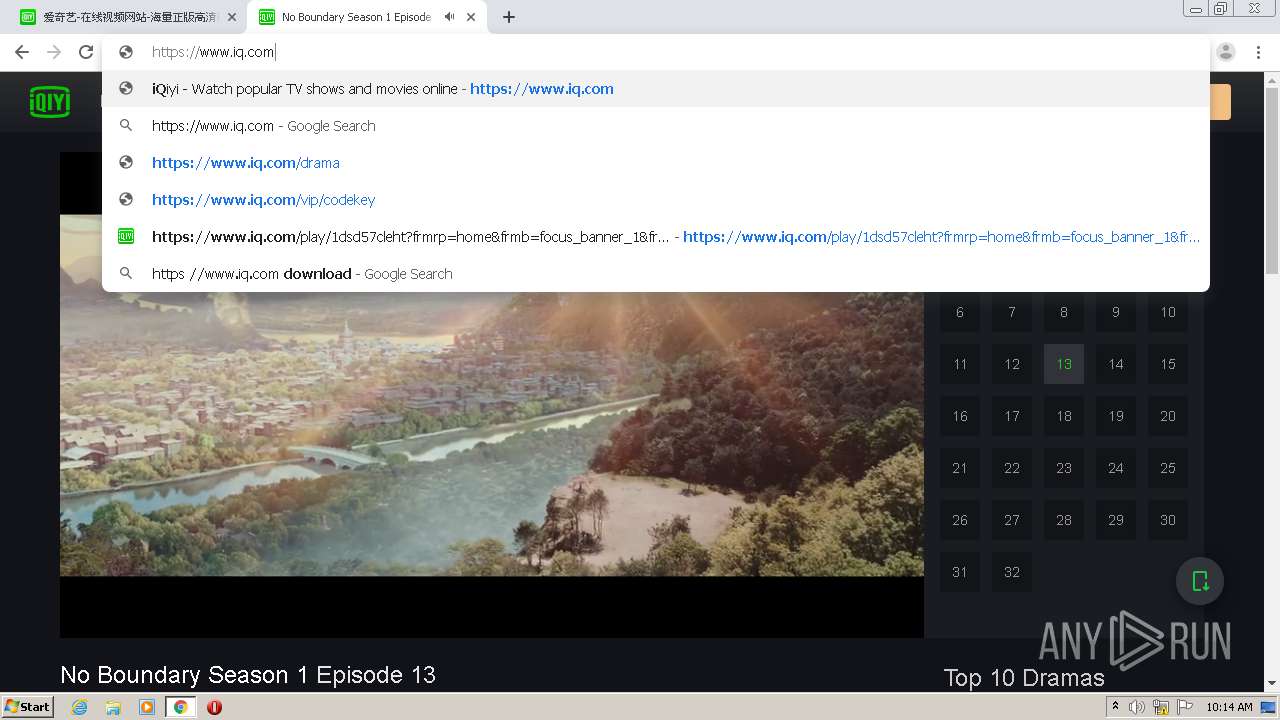
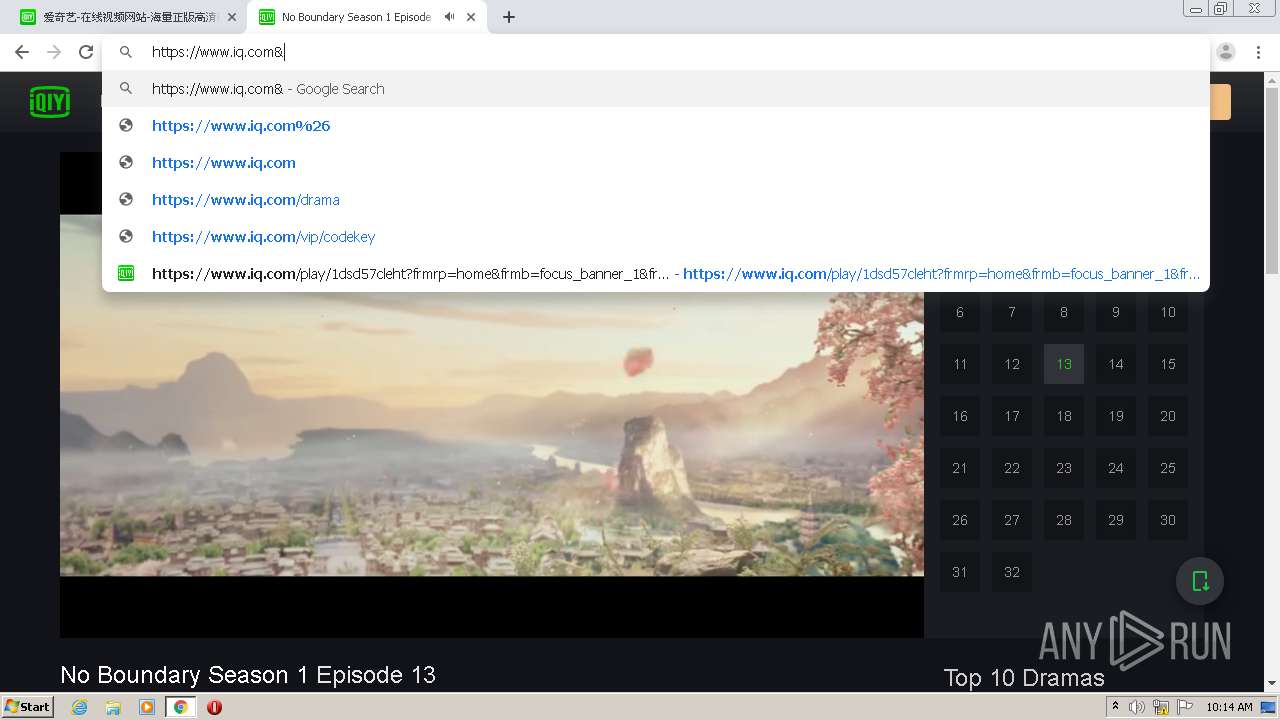
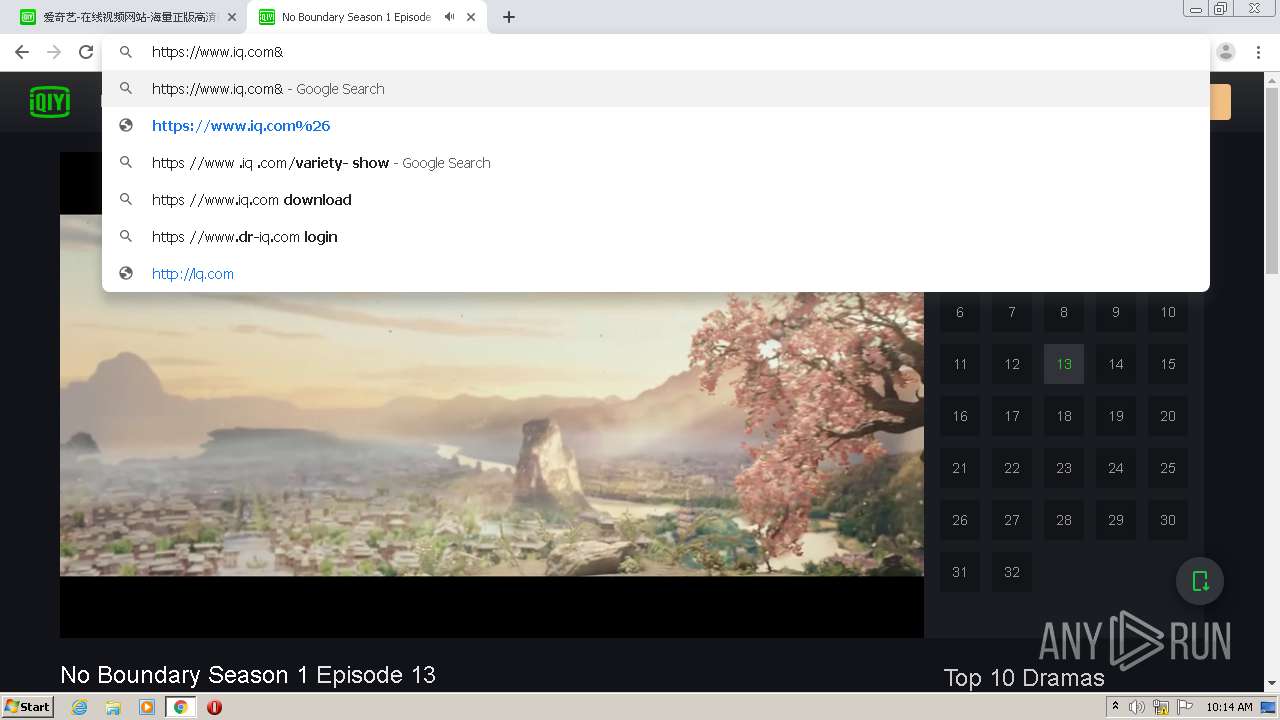
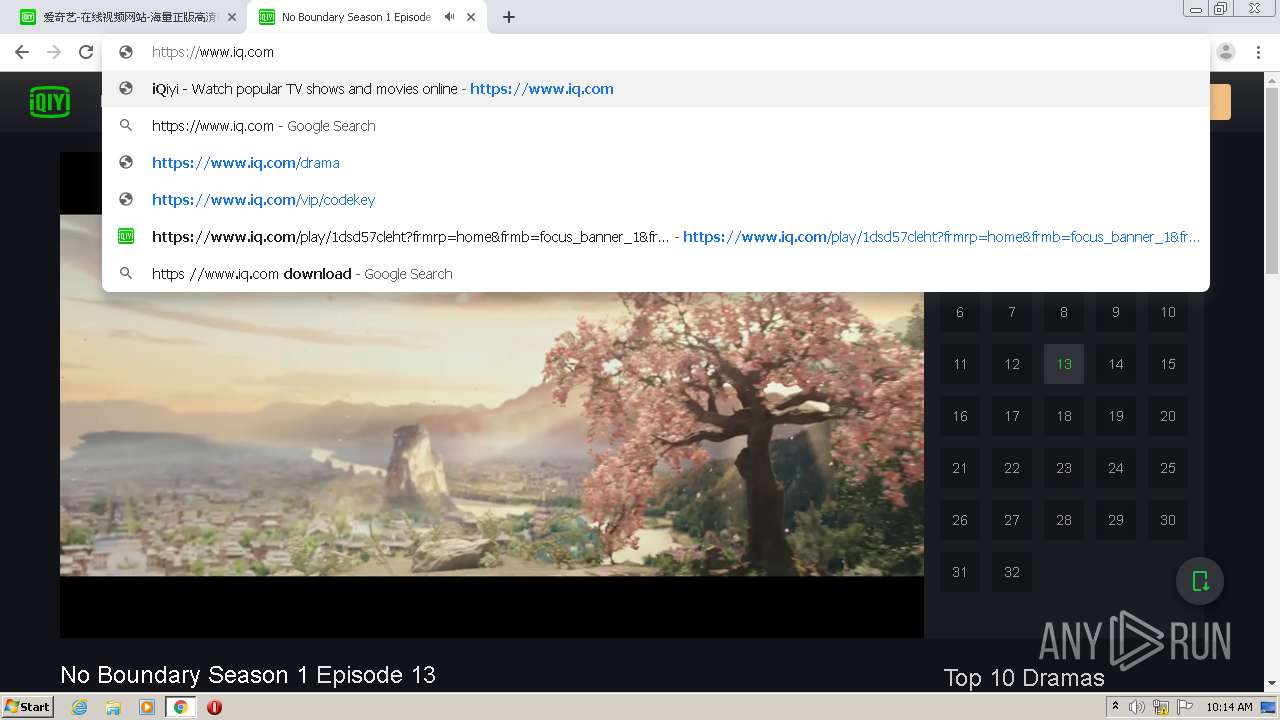
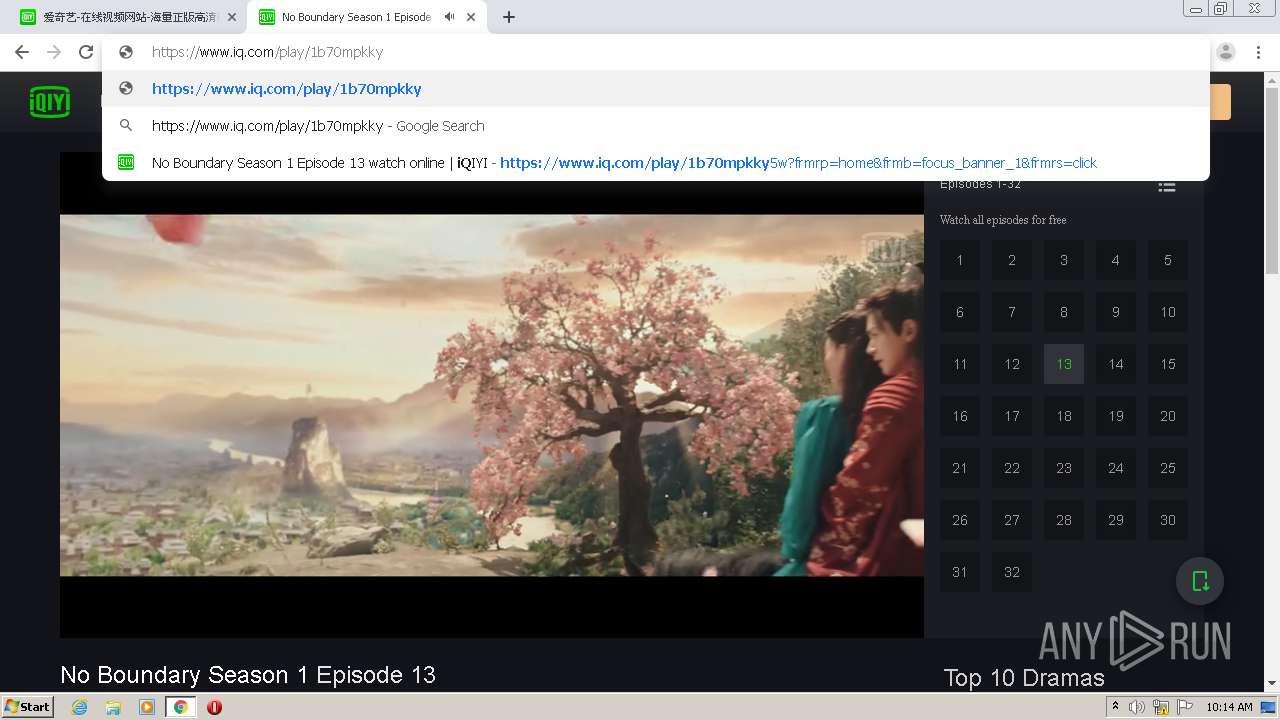
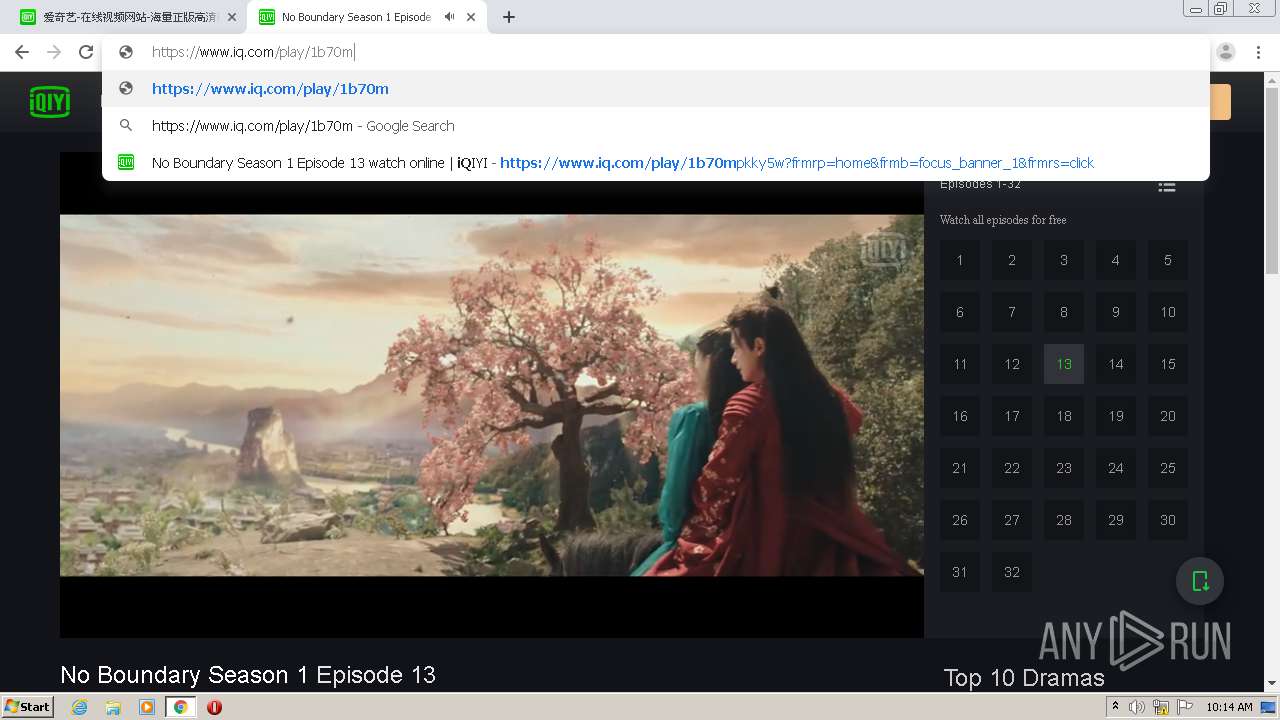
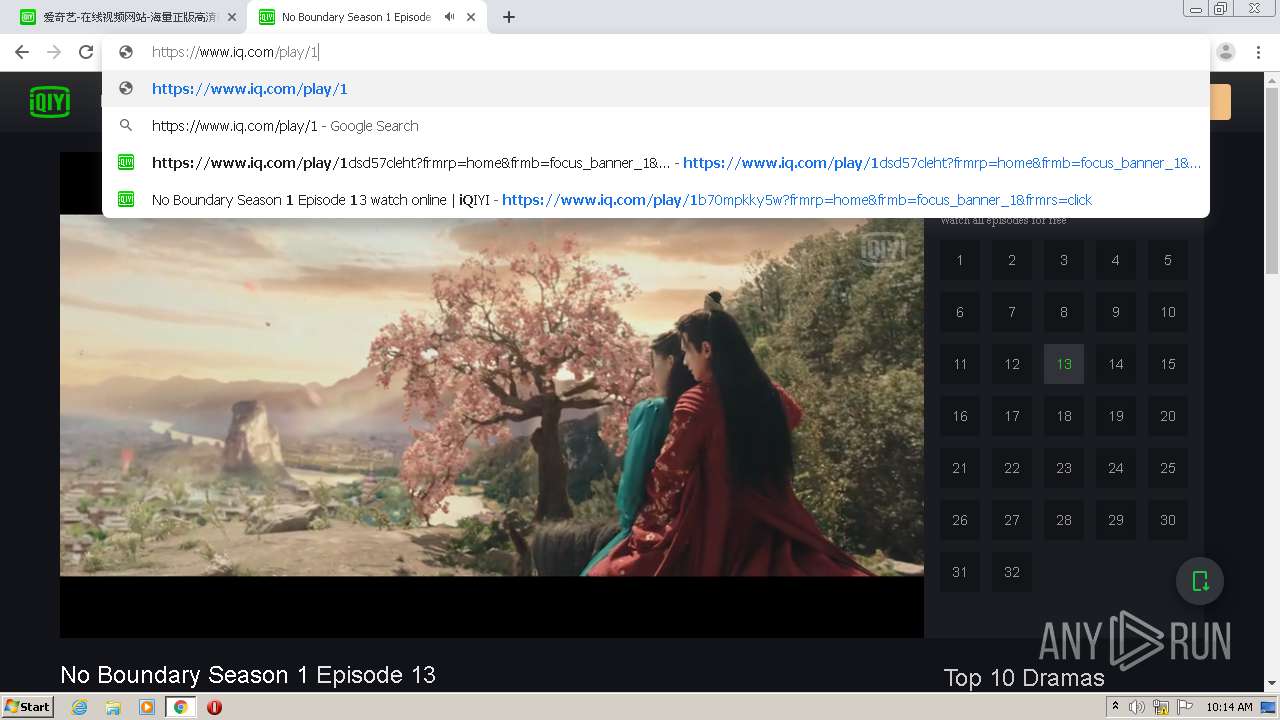
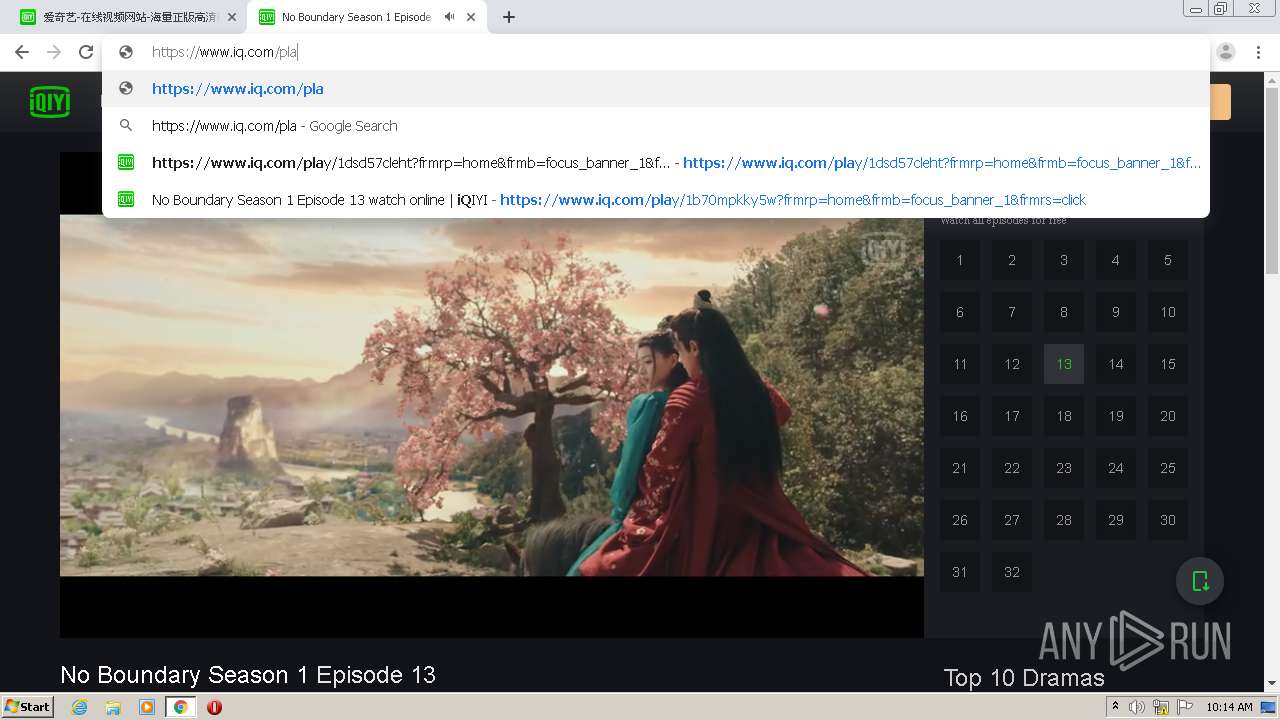
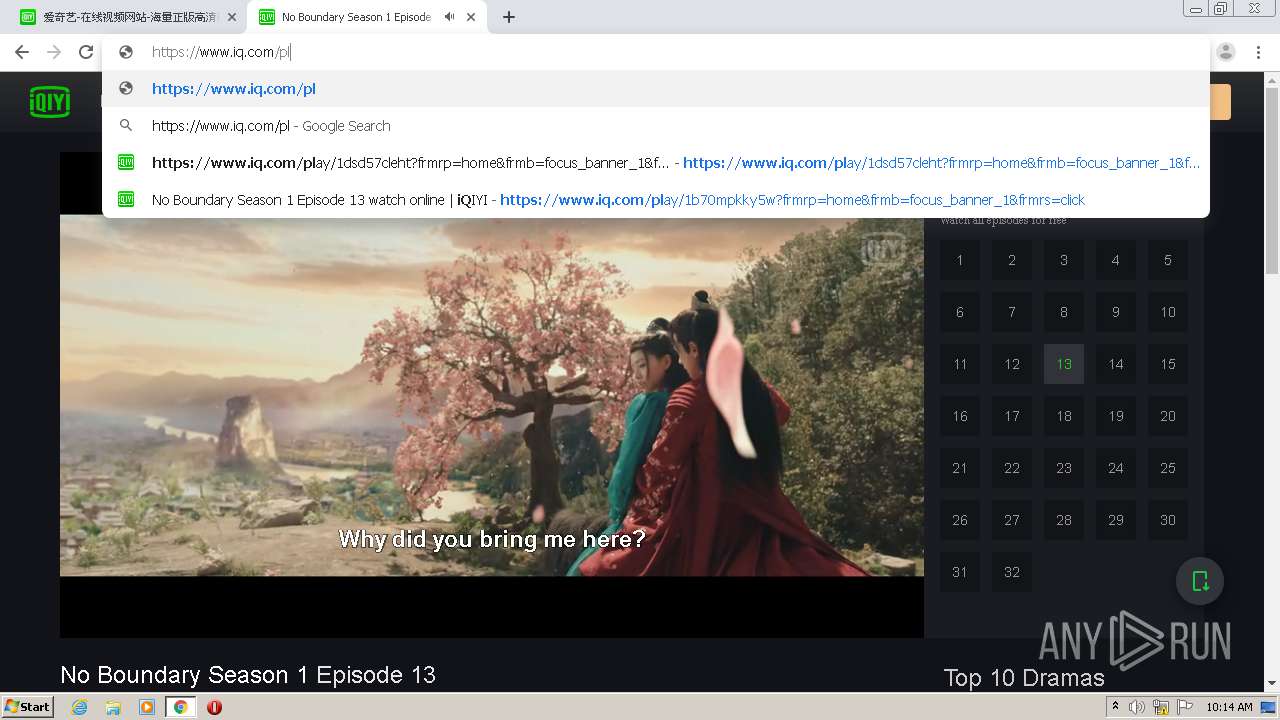
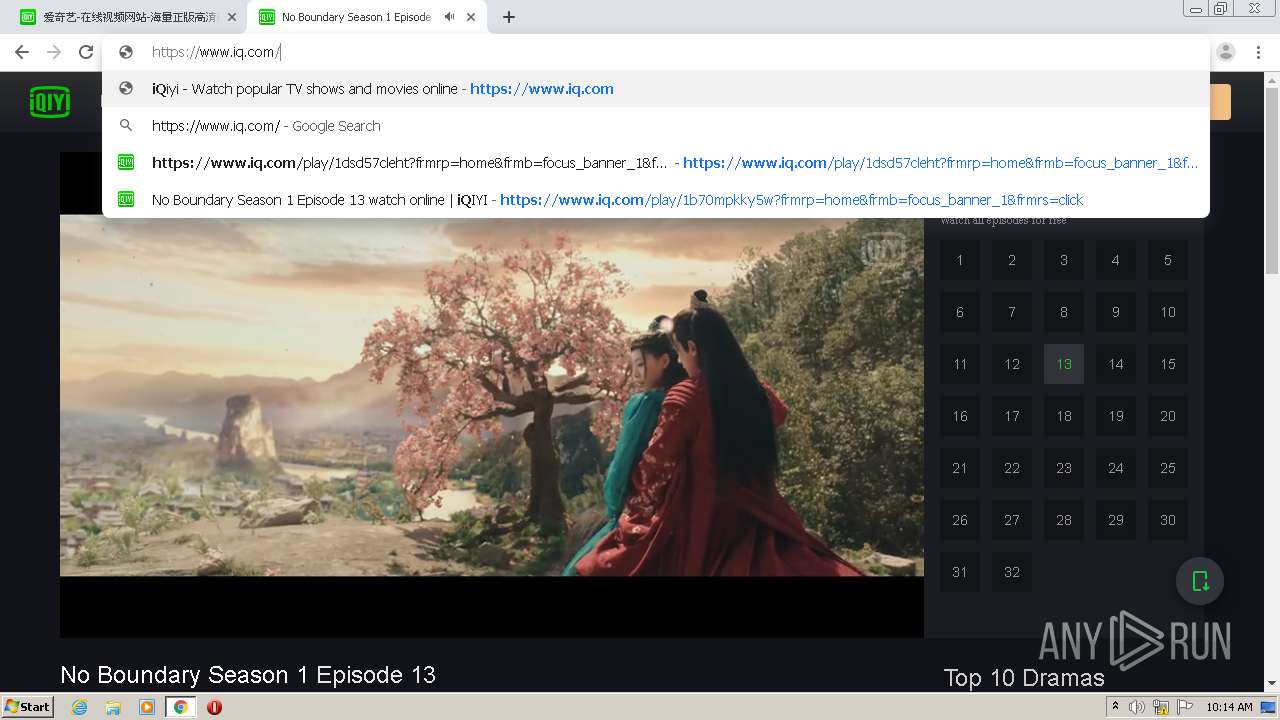
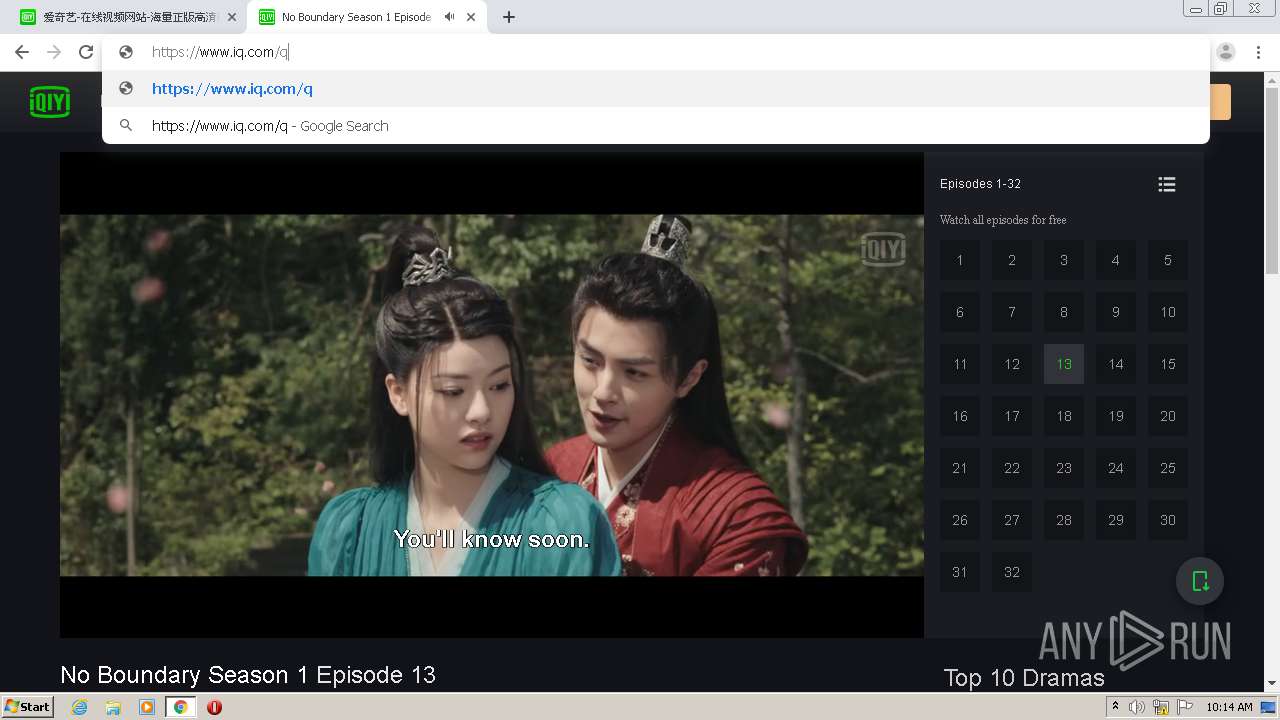
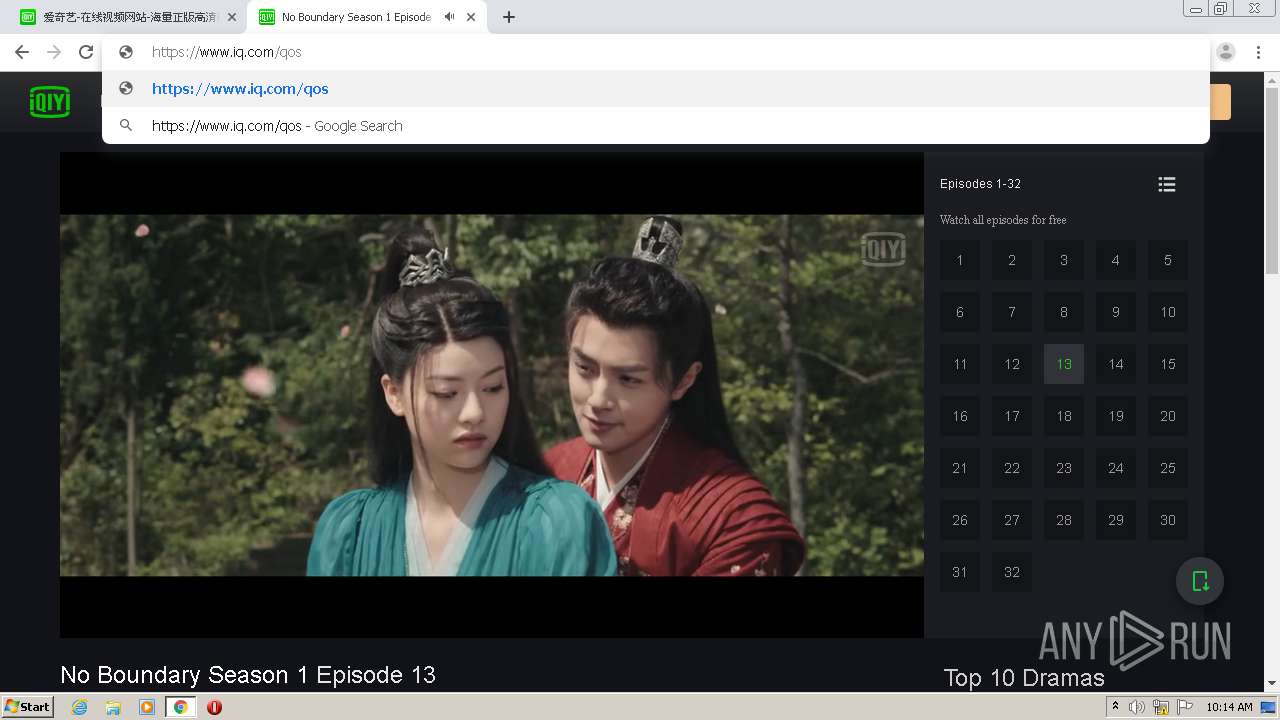
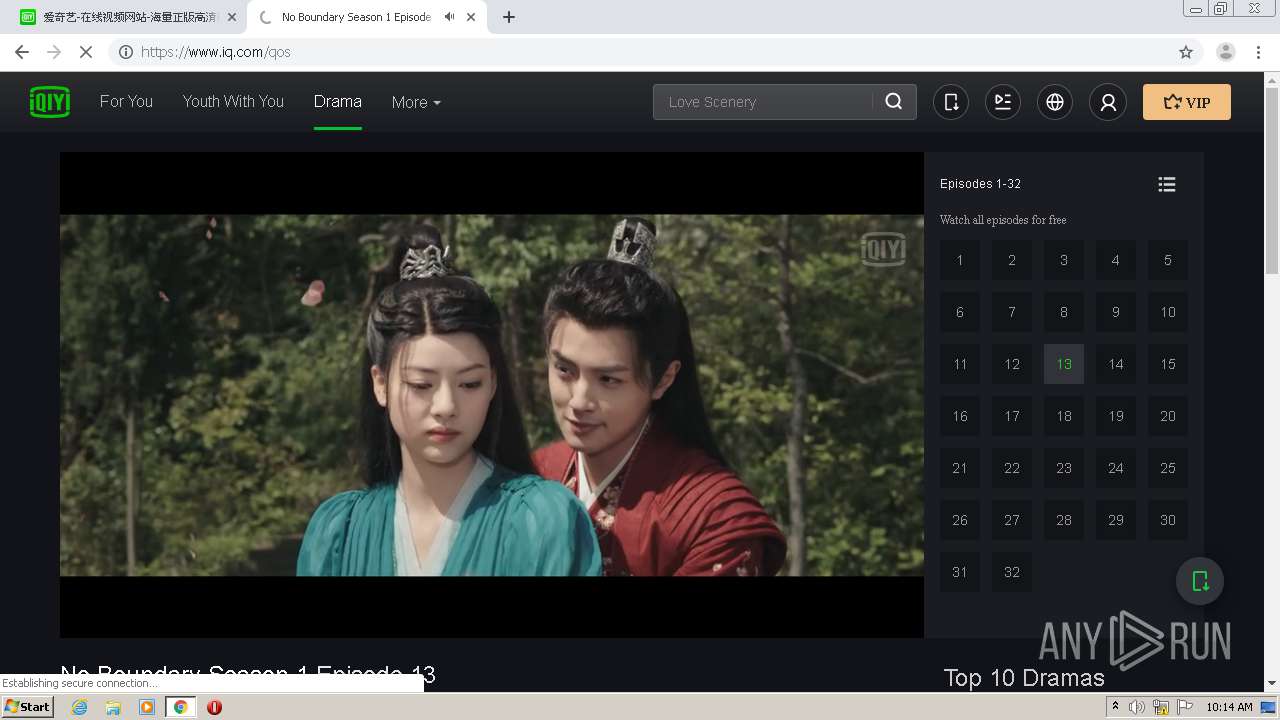
308 | chrome.exe | GET | 302 | 184.24.4.164:80 | http://www.iqiyi.com/ | US | — | — | suspicious |
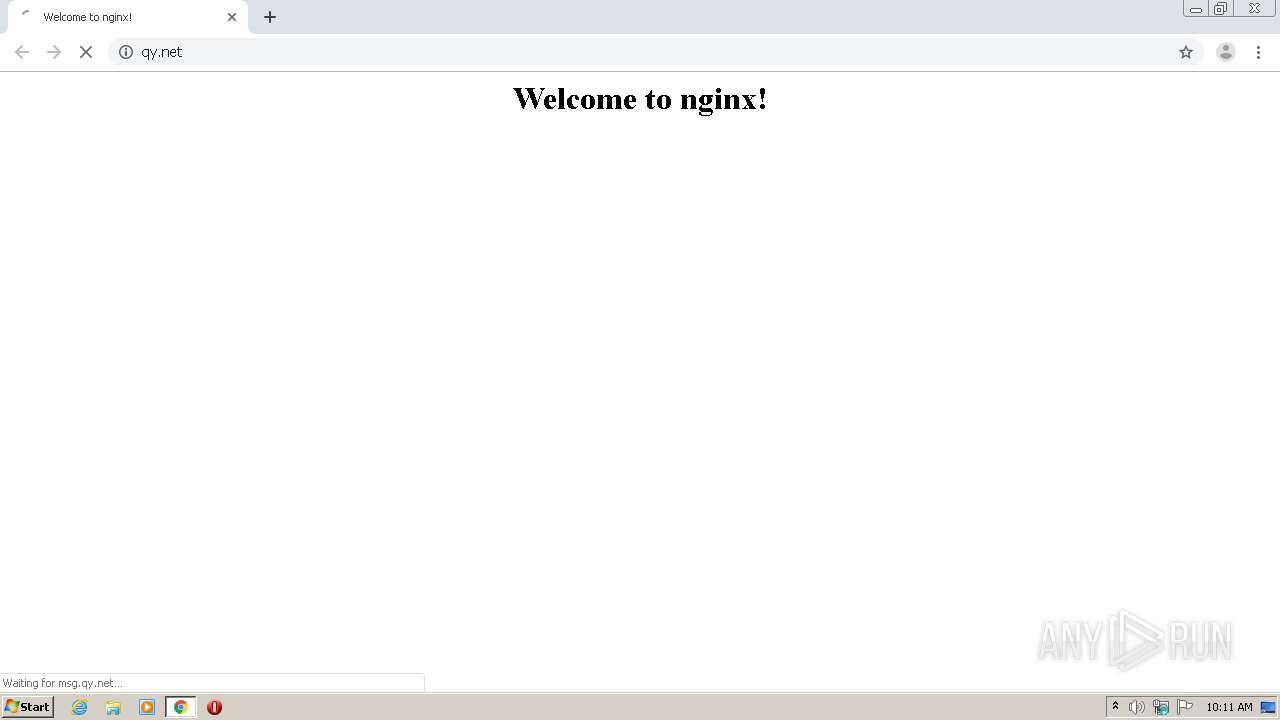
308 | chrome.exe | GET | 302 | 36.110.238.119:80 | http://qy.net/ | CN | html | 138 b | unknown |
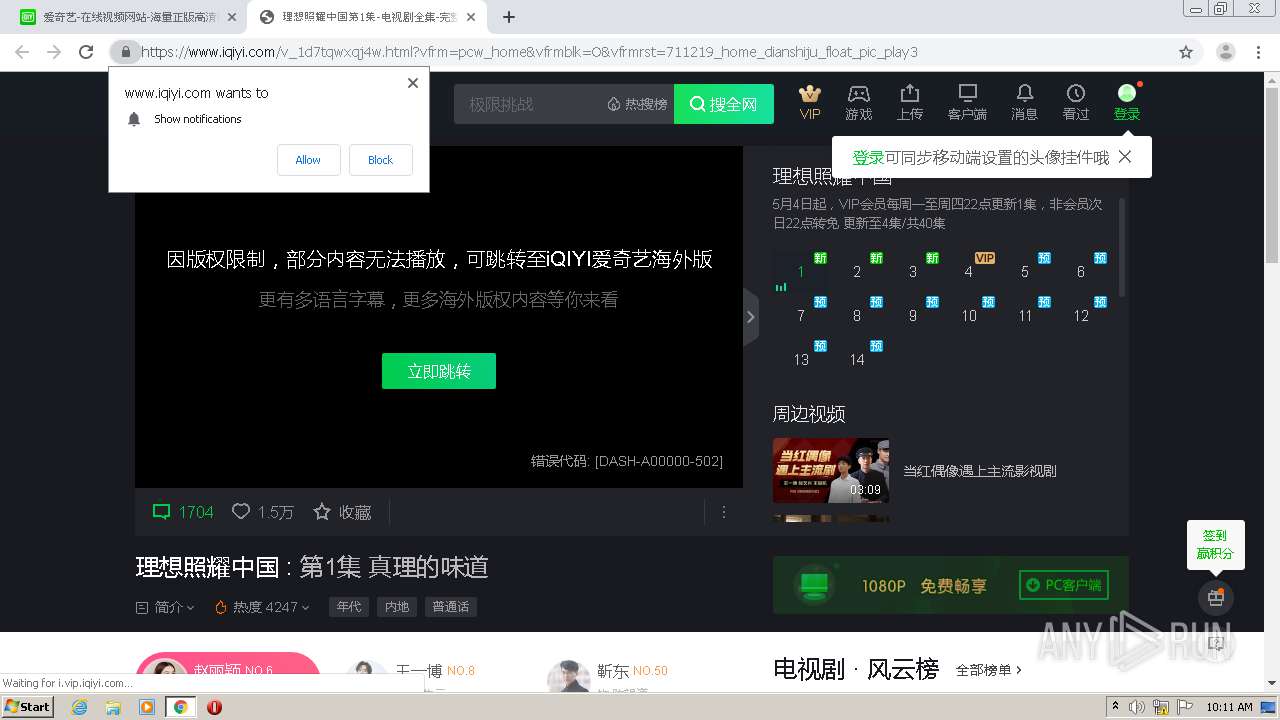
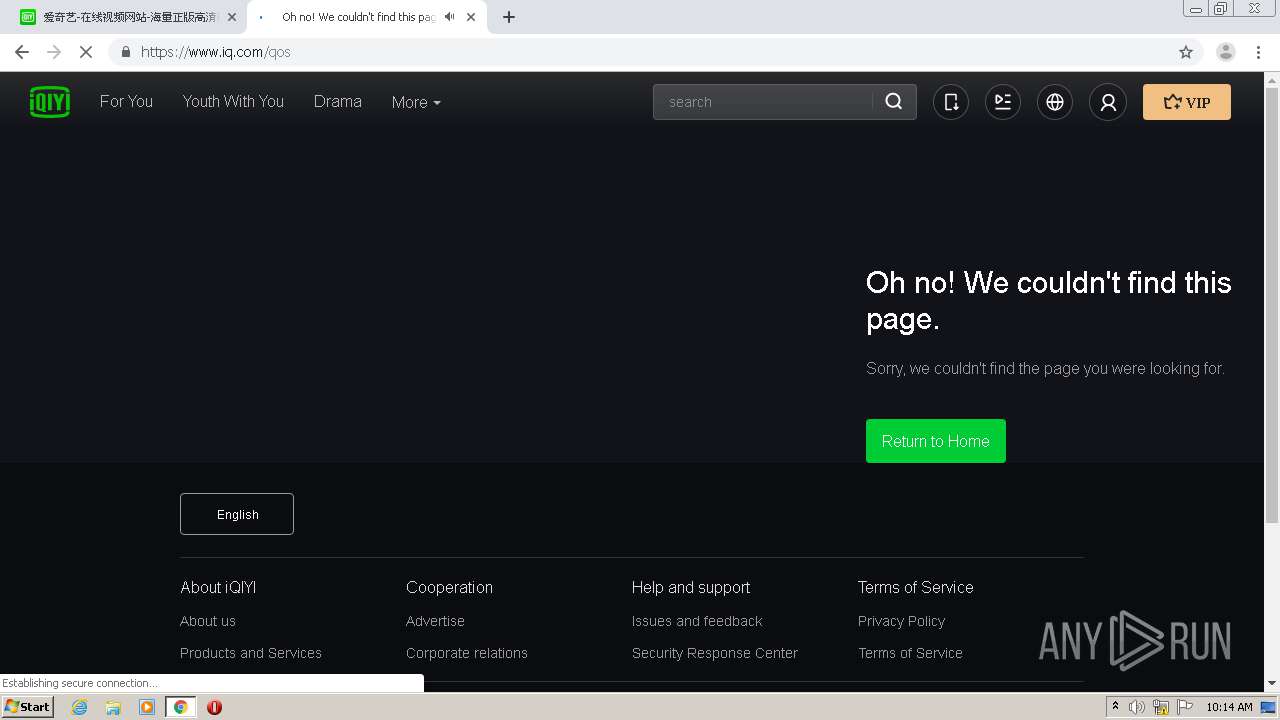
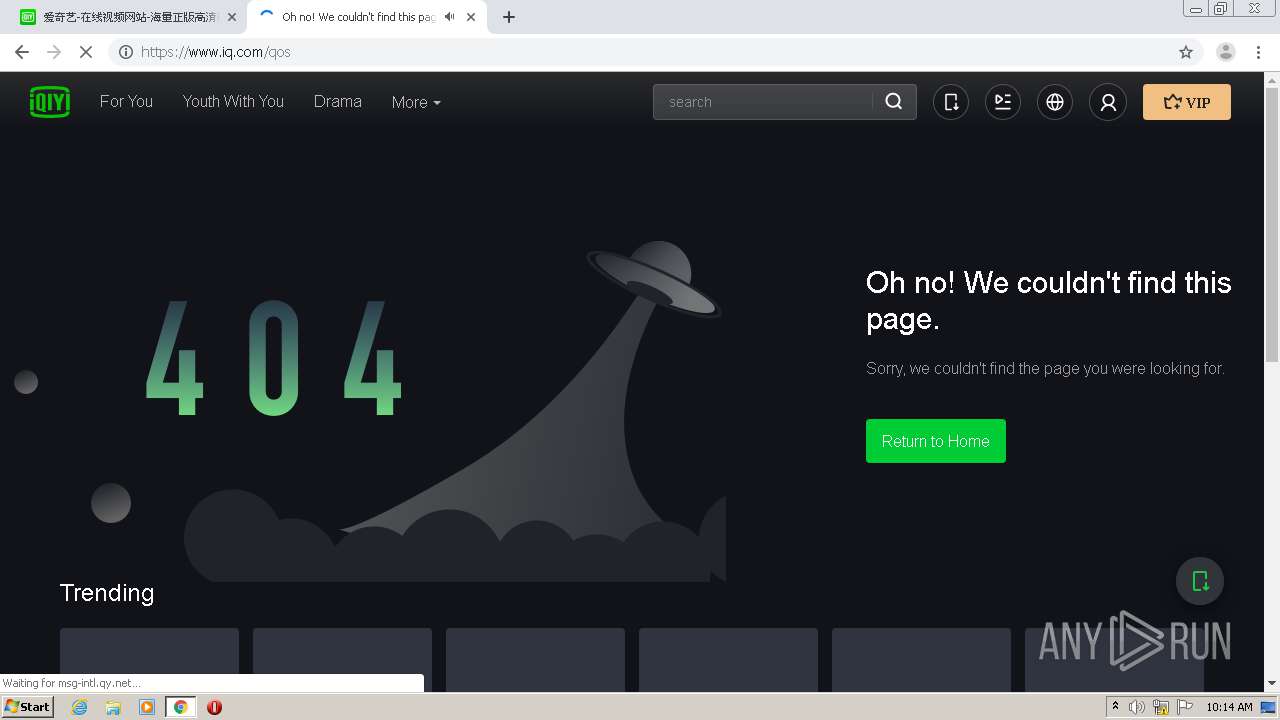
308 | chrome.exe | GET | 200 | 118.26.32.16:80 | http://msg.qy.net/ | CN | html | 151 b | suspicious |
308 | chrome.exe | GET | 200 | 118.26.32.16:80 | http://msg.qy.net/ | CN | html | 151 b | suspicious |
308 | chrome.exe | GET | 200 | 118.26.32.16:80 | http://msg.qy.net/favicon.ico | CN | html | 151 b | suspicious |
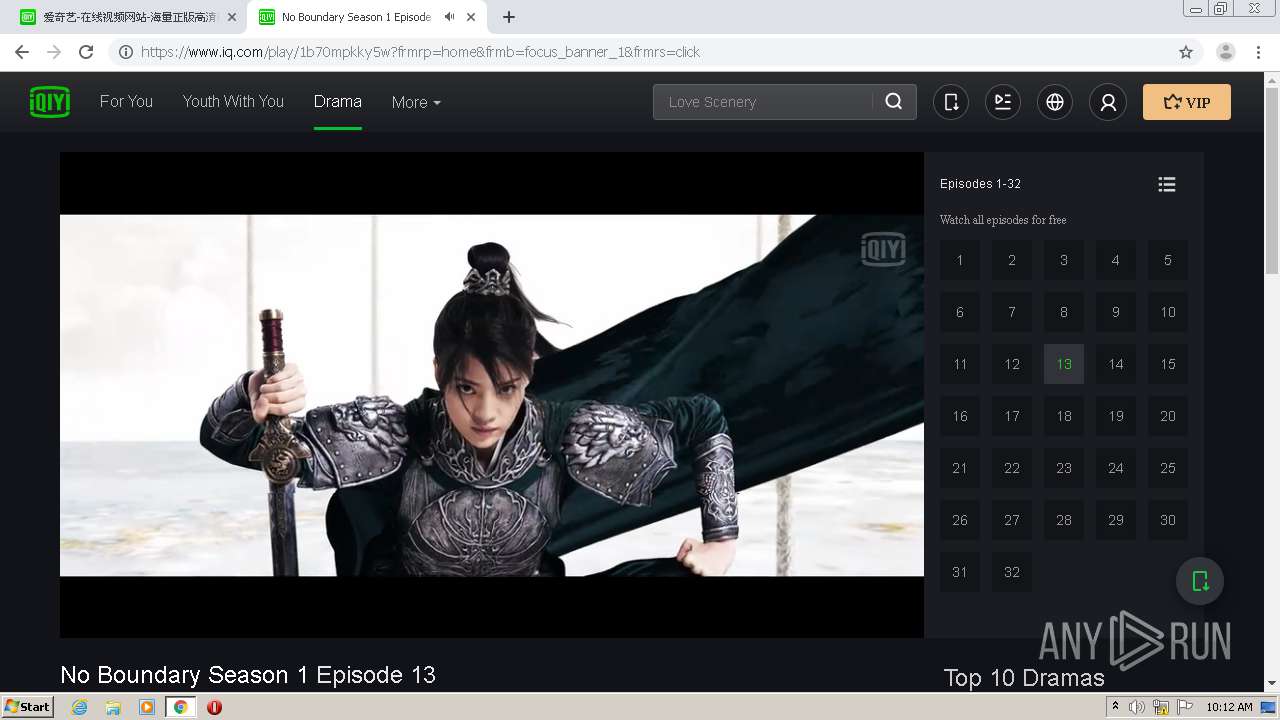
308 | chrome.exe | GET | 200 | 104.109.72.237:80 | http://www.iqiyipic.com/lequ/20210401/1920-vertical.png | NL | image | 5.03 Kb | suspicious |
308 | chrome.exe | GET | 200 | 118.26.32.16:80 | http://msg.qy.net/favicon.ico | CN | html | 151 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
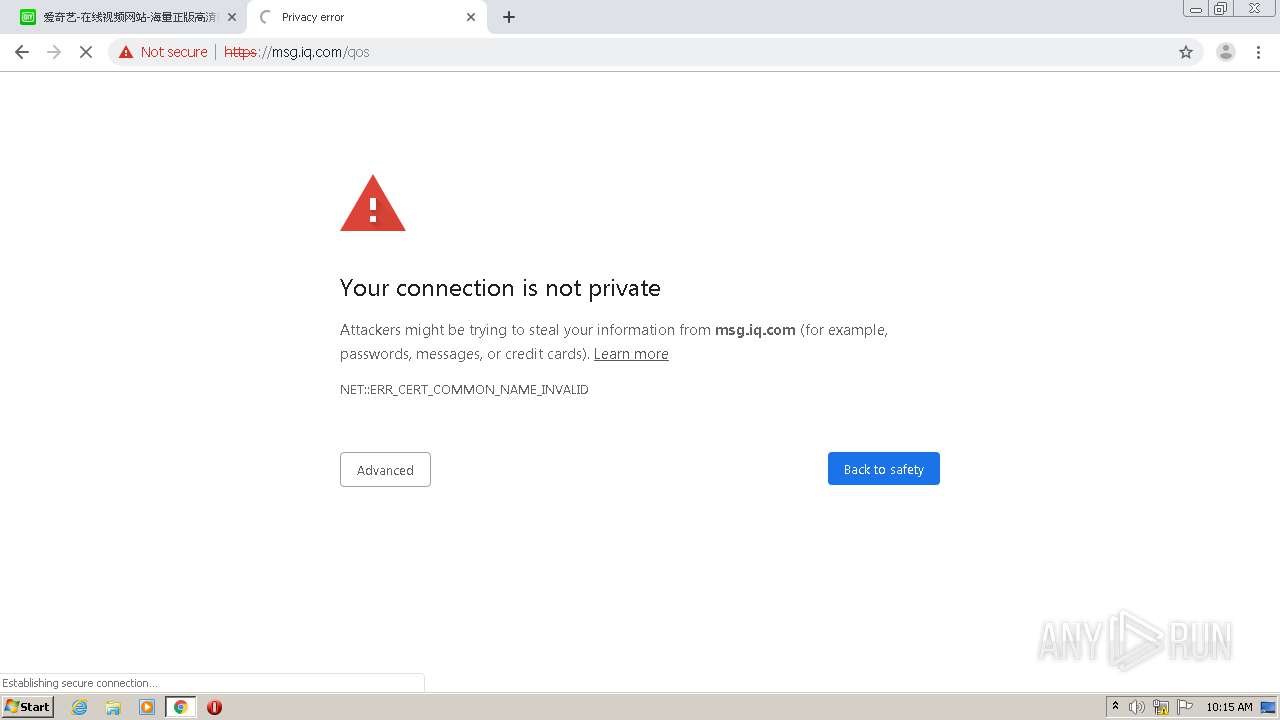
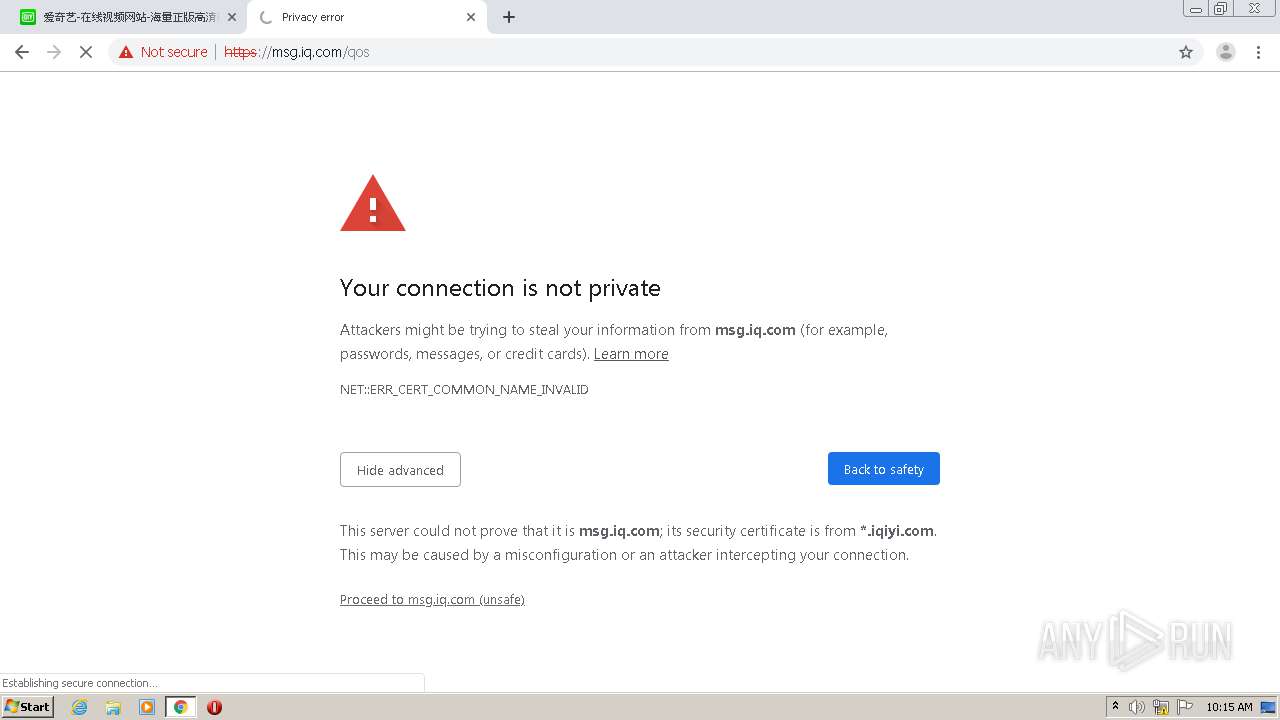
308 | chrome.exe | 118.26.32.16:80 | msg.qy.net | — | CN | malicious |
308 | chrome.exe | 104.109.72.237:443 | stc.iqiyipic.com | Akamai International B.V. | NL | unknown |
308 | chrome.exe | 184.24.4.164:443 | www.iqiyi.com | Bharti Airtel Ltd., Telemedia Services | US | unknown |
308 | chrome.exe | 184.24.4.169:443 | pic4.iqiyipic.com | Bharti Airtel Ltd., Telemedia Services | US | unknown |
308 | chrome.exe | 118.26.120.3:443 | pcw-api.iqiyi.com | — | CN | suspicious |
308 | chrome.exe | 119.188.176.48:443 | zz.bdstatic.com | CHINA UNICOM China169 Backbone | CN | unknown |
308 | chrome.exe | 216.58.212.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
308 | chrome.exe | 118.26.32.16:443 | msg.qy.net | — | CN | malicious |
308 | chrome.exe | 111.206.210.170:443 | datax.baidu.com | China Unicom Beijing Province Network | CN | unknown |
308 | chrome.exe | 103.235.46.39:443 | sp0.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
msg.qy.net |
| suspicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
qy.net |
| unknown |
www.iqiyi.com |
| suspicious |
stc.iqiyipic.com |
| unknown |
www.iqiyipic.com |
| suspicious |
pic0.iqiyipic.com |
| unknown |
static-s.iqiyi.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
308 | chrome.exe | Potentially Bad Traffic | ET INFO Unconfigured nginx Access |
308 | chrome.exe | Potentially Bad Traffic | ET INFO Unconfigured nginx Access |