| File name: | worm.exe |
| Full analysis: | https://app.any.run/tasks/4ca365ca-804b-4fd4-b6cd-841bdd35cca9 |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2024, 03:44:08 |
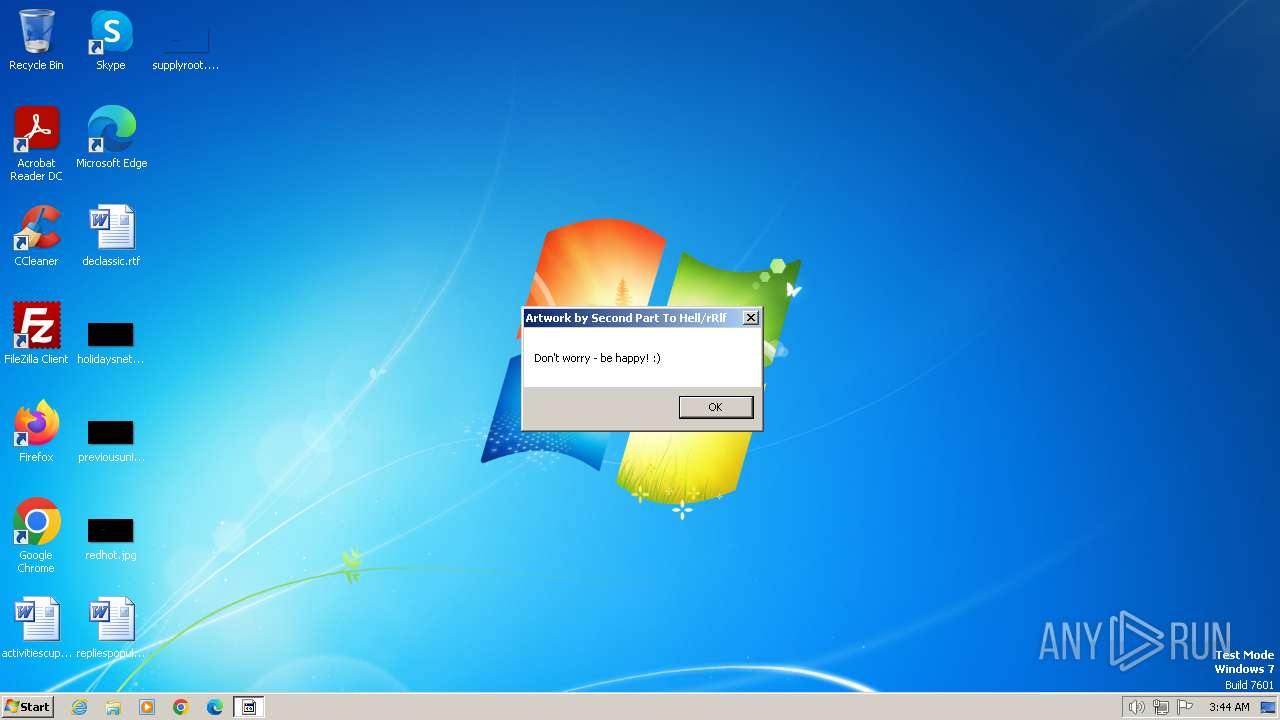
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F68872773A88652541BD8D6CA9BDA058 |
| SHA1: | C8AC1B977D771C89ED7152F0DAEDB6A3E8B69B24 |
| SHA256: | 9FD30BDA0EDF3B10B326703303FA15995A688D200582822EF49422EBAC87B7F7 |
| SSDEEP: | 48:ZvtQeJNRBDfUm8m0Zqaeo9bffS9lQ1eQC/g5eK09EHQfQFZduyvMstkf:Z1HnxffuZDBWQ1kK09gPFZwyEN |
MALICIOUS
Drops the executable file immediately after the start
- worm.exe (PID: 3240)
SUSPICIOUS
Reads the Internet Settings
- worm.exe (PID: 3240)
Reads security settings of Internet Explorer
- worm.exe (PID: 3240)
Checks Windows Trust Settings
- worm.exe (PID: 3240)
Reads settings of System Certificates
- worm.exe (PID: 3240)
INFO
Checks supported languages
- worm.exe (PID: 3240)
Reads the computer name
- worm.exe (PID: 3240)
Checks proxy server information
- worm.exe (PID: 3240)
Reads the machine GUID from the registry
- worm.exe (PID: 3240)
Creates files or folders in the user directory
- worm.exe (PID: 3240)
Reads the software policy settings
- worm.exe (PID: 3240)
Create files in a temporary directory
- worm.exe (PID: 3240)
Application launched itself
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 2328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.7) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.4) |
| .exe | | | DOS Executable Generic (23.4) |
| .vxd | | | VXD Driver (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:05:21 11:36:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 1.56 |
| CodeSize: | - |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2000 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2328 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3848 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3848 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3240 | "C:\Users\admin\AppData\Local\Temp\worm.exe" | C:\Users\admin\AppData\Local\Temp\worm.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
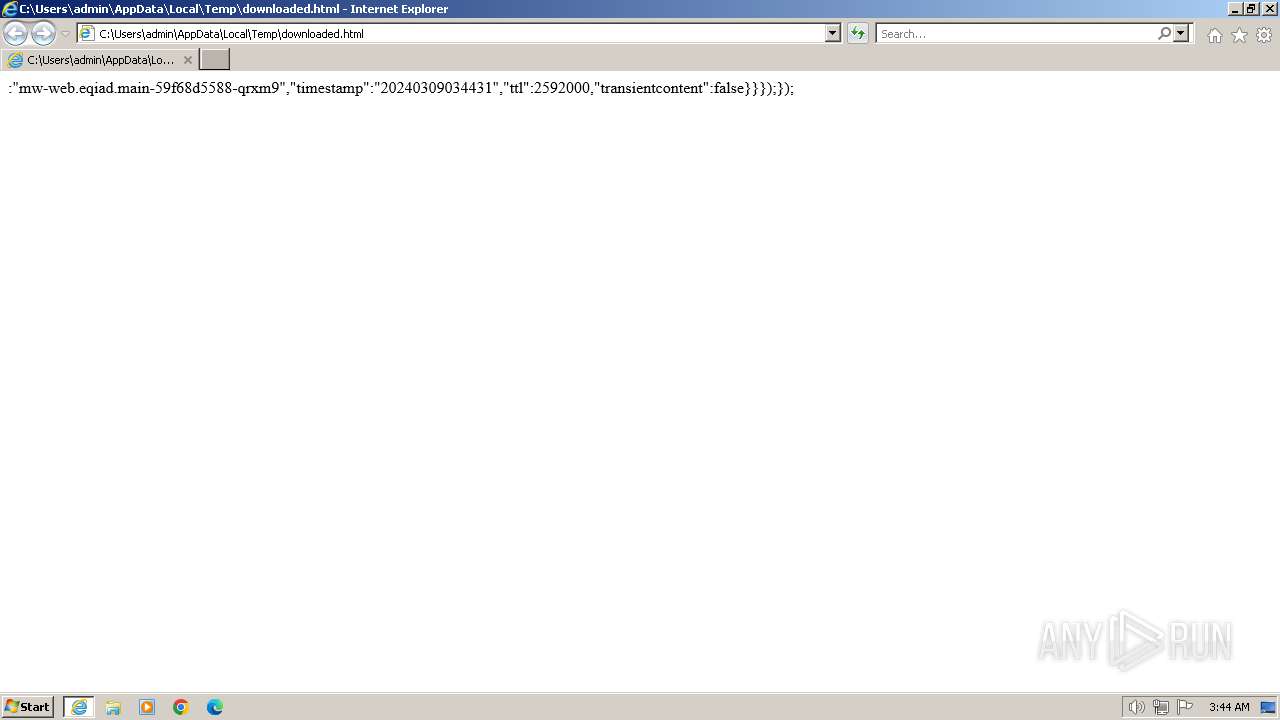
| 3848 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\downloaded.html" | C:\Program Files\Internet Explorer\iexplore.exe | worm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 508
Read events
15 274
Write events
174
Delete events
60
Modification events
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3240) worm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
11
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | worm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:F92C752410E237945C3248B0E32F6DFA | SHA256:E06688C3D82469D09C9E6732A793BE42B2A3F3F6C85AE43EF4D528AE56A1F545 | |||
| 3240 | worm.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\4M6PSHSP.txt | text | |
MD5:3275BE8A1A202DA3976F8C4F0C11B71E | SHA256:C56598C56FC33791E8186DEACC163FA21529AC2A0416AA10AC6993ECCC098955 | |||
| 3240 | worm.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\933937VR.txt | text | |
MD5:2C942AF860D5D6D02DC5ABA0F60275A8 | SHA256:0E0D555F4F4FAAAAB3675ECFA95916B0DAED2EE55E26B251289FABEA3AB255EE | |||
| 3240 | worm.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\index[1].htm | html | |
MD5:FCB10DB018F33216F9E3E6D362D930EF | SHA256:94C10E4DD922D1364F1E1DB52688918D9064834CB91426C53641E8218C7D995A | |||
| 3240 | worm.exe | C:\Users\admin\AppData\Local\Temp\downloaded.html | html | |
MD5:9186B495DF6D9283AC4142D52780A276 | SHA256:25F18F9C410D57F37BAEACABC6E7F66BCA9135AF571EA3072A81F197D432E7D1 | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:F6EC1D937D4A8101AF345EC2BD9E78BE | SHA256:F2503C7083D83E068FD6EA91CB0C48F22038CA2FD1C8E1DEDBCF833E0D436E85 | |||
| 3240 | worm.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\BUS3616X.txt | text | |
MD5:51032DA07AFBF75ED1CE042411539AF6 | SHA256:AFF6B934A8D3830EC30F8B016473764F64741971C8615DA7698A50AA97C701CF | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:85138C7C671DDB9E362B57C978C26999 | SHA256:4FDF6020175B0C4ED9086AE4593DB6BDDE2C42A63C548A4BE16B4795E4D5DB93 | |||
| 3240 | worm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:6BAF0F2646BB299C04008DE03FDFC73B | SHA256:E496E9E23E26B1774C181AD85C9961C7CFB5A2402278C0EC89CB9B035D60B048 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
16
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3240 | worm.exe | GET | 301 | 185.15.59.224:80 | http://en.wikipedia.org/wiki/Special:Random | unknown | — | — | unknown |
3240 | worm.exe | GET | 304 | 92.123.133.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c41d92d6b09abc02 | unknown | — | — | unknown |
3240 | worm.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | binary | 471 b | unknown |
3240 | worm.exe | GET | 301 | 185.15.59.224:80 | http://en.wikipedia.org/w/index.php?title=Piechota_wybraniecka&action=edit | unknown | — | — | unknown |
3848 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
1080 | svchost.exe | GET | 200 | 92.123.133.35:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0754c686571bd23f | unknown | compressed | 67.5 Kb | unknown |
1080 | svchost.exe | GET | 304 | 92.123.133.35:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?624d1ab720bef5f8 | unknown | compressed | 67.5 Kb | unknown |
3848 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3240 | worm.exe | 185.15.59.224:80 | en.wikipedia.org | WIKIMEDIA | US | unknown |
3240 | worm.exe | 185.15.59.224:443 | en.wikipedia.org | WIKIMEDIA | US | unknown |
3240 | worm.exe | 92.123.133.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3240 | worm.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3848 | iexplore.exe | 2.19.80.27:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3848 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 92.123.133.35:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
en.wikipedia.org |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |