| File name: | rms.exe |
| Full analysis: | https://app.any.run/tasks/78efce3f-ed15-41de-8e1f-b6e143ebe2b1 |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 07:52:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 7B7ADE39381DFB51B337D93BBADA1309 |
| SHA1: | FDBD8E8BD4969D00880E3CDFFEE39E510EA0098A |
| SHA256: | 9FC7C6E7B082D8CB837C736E7D21FAEC5298257C66FEA00908F7347A4B22D56D |
| SSDEEP: | 98304:HKF7KQF1iEaGzM038RzYf0ML2x5tTDaLclizt5CW:HS7KQrLM/RzYI7Da4It |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- rms.exe (PID: 3724)
Creates files in the program directory
- rms.exe (PID: 3724)
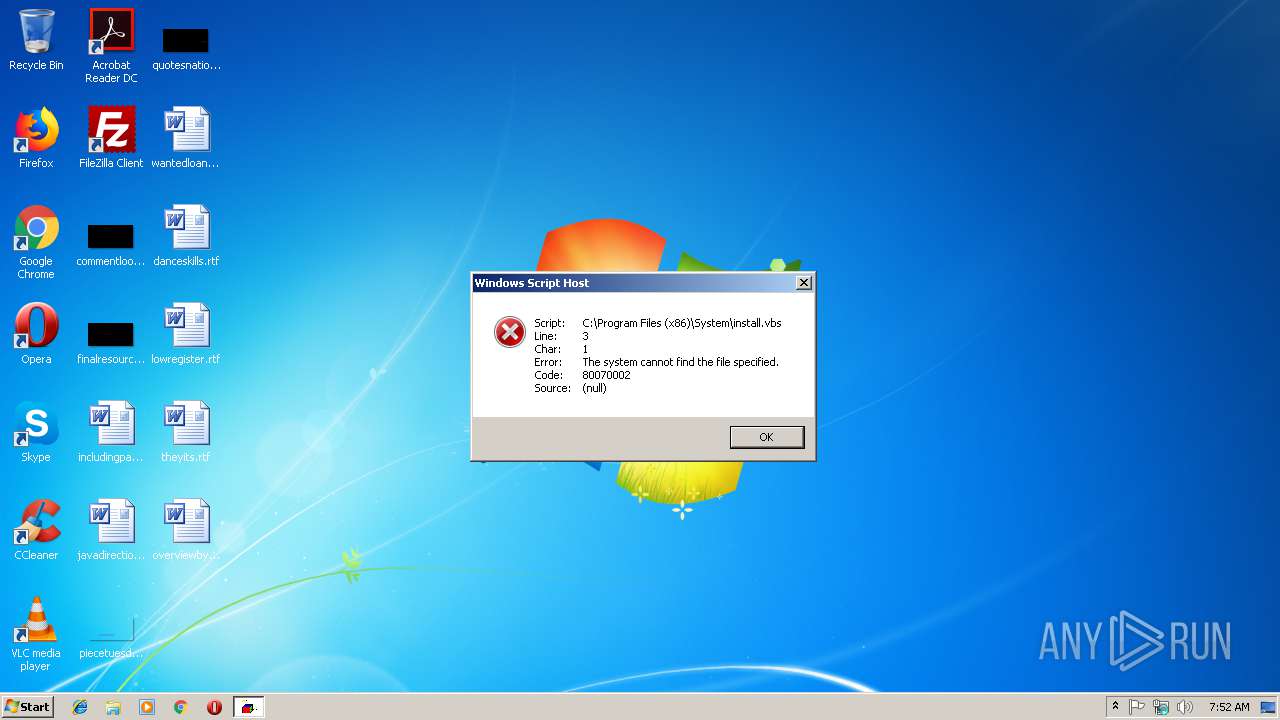
Executes scripts
- rms.exe (PID: 3724)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:12:02 11:07:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165376 |
| InitializedDataSize: | 35328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d5db |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Dec-2014 10:07:30 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Dec-2014 10:07:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002859A | 0x00028600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72265 |
.rdata | 0x0002A000 | 0x00004FD3 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38632 |
.data | 0x0002F000 | 0x00021428 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.46654 |
.rsrc | 0x00051000 | 0x00002218 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.38124 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.96849 | 830 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.74776 | 476 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11 | 3.88515 | 1086 | Latin 1 / Western European | UNKNOWN | RT_STRING |
12 | 3.68258 | 356 | Latin 1 / Western European | UNKNOWN | RT_STRING |
13 | 3.54875 | 228 | Latin 1 / Western European | UNKNOWN | RT_STRING |
14 | 3.52809 | 250 | Latin 1 / Western European | UNKNOWN | RT_STRING |
15 | 3.30562 | 186 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
35
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2872 | "C:\Windows\System32\WScript.exe" "C:\Program Files (x86)\System\install.vbs" | C:\Windows\System32\WScript.exe | — | rms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\AppData\Local\Temp\rms.exe" | C:\Users\admin\AppData\Local\Temp\rms.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 3724 | "C:\Users\admin\AppData\Local\Temp\rms.exe" | C:\Users\admin\AppData\Local\Temp\rms.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
80
Read events
76
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3724) rms.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3724) rms.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3724 | rms.exe | C:\Program Files (x86)\System\regedit.reg | text | |
MD5:— | SHA256:— | |||
| 3724 | rms.exe | C:\Program Files (x86)\System\install.vbs | text | |
MD5:— | SHA256:— | |||
| 3724 | rms.exe | C:\Program Files (x86)\System\rfusclient.exe | executable | |
MD5:B8667A1E84567FCF7821BCEFB6A444AF | SHA256:DC9D875E659421A51ADDD8E8A362C926369E84320AB0C5D8BBB1E4D12D372FC9 | |||
| 3724 | rms.exe | C:\Program Files (x86)\System\rutserv.exe | executable | |
MD5:37A8802017A212BB7F5255ABC7857969 | SHA256:1699B9B4FC1724F9B0918B57CA58C453829A3935EFD89BD4E9FA66B5E9F2B8A6 | |||
| 3724 | rms.exe | C:\Program Files (x86)\System\vp8decoder.dll | executable | |
MD5:88318158527985702F61D169434A4940 | SHA256:4C04D7968A9FE9D9258968D3A722263334BBF5F8AF972F206A71F17FA293AA74 | |||
| 3724 | rms.exe | C:\Program Files (x86)\System\vp8encoder.dll | executable | |
MD5:6298C0AF3D1D563834A218A9CC9F54BD | SHA256:81AF82019D9F45A697A8CA1788F2C5C0205AF9892EFD94879DEDF4BC06DB4172 | |||
| 3724 | rms.exe | C:\Program Files (x86)\System\mailsend.exe | executable | |
MD5:AC23B87F8EC60DDD3F555556F89A6AF8 | SHA256:80A1D0A15066C7AF67CF5377E59E450C2A96018505236F8F3352173282B27AE4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report