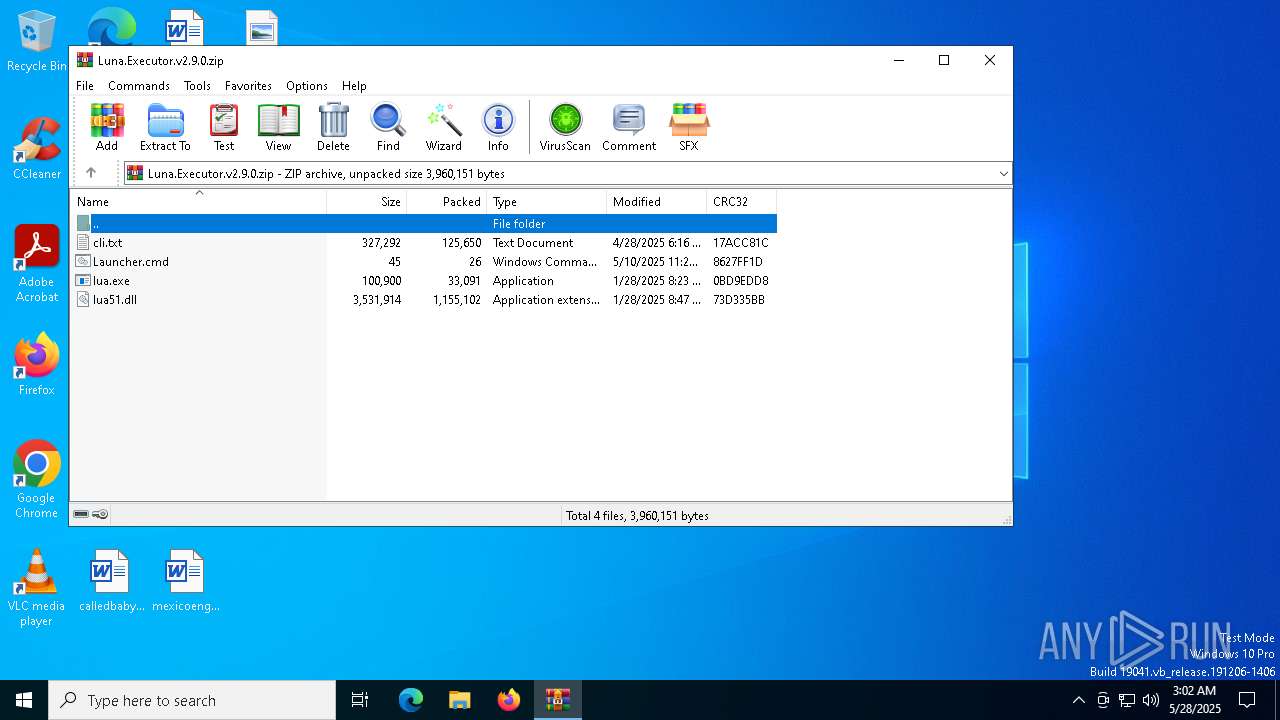
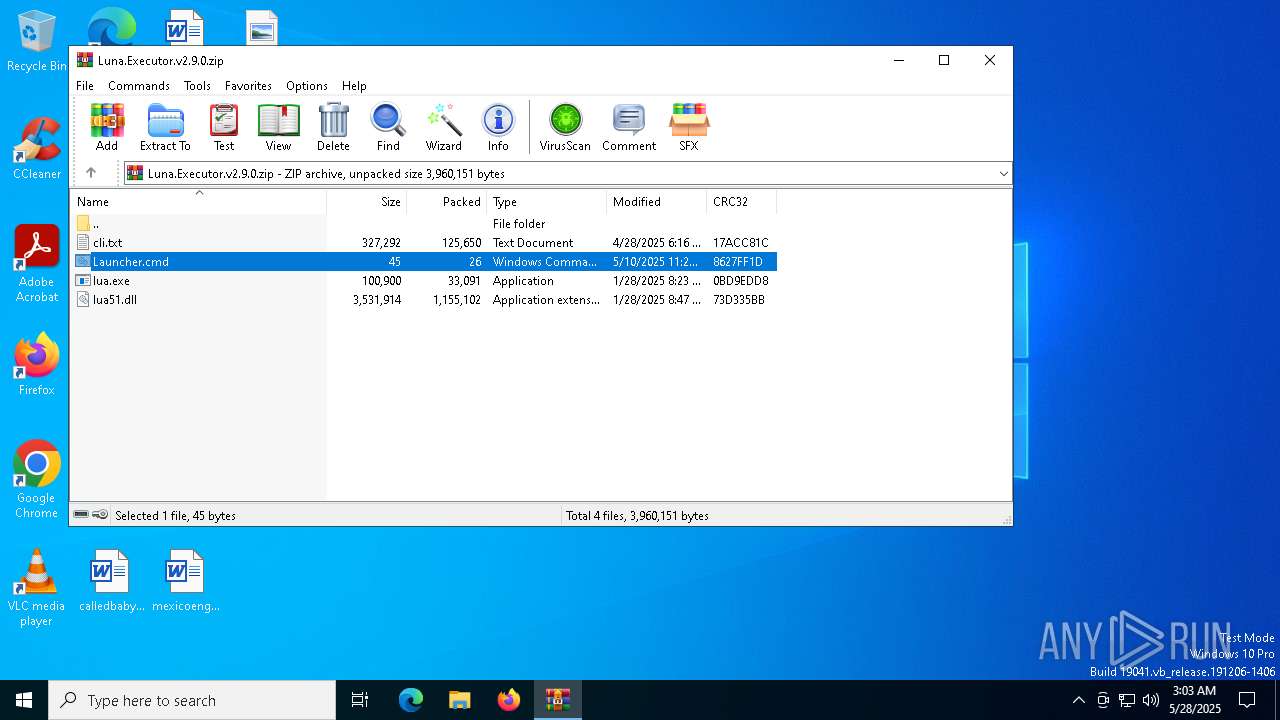
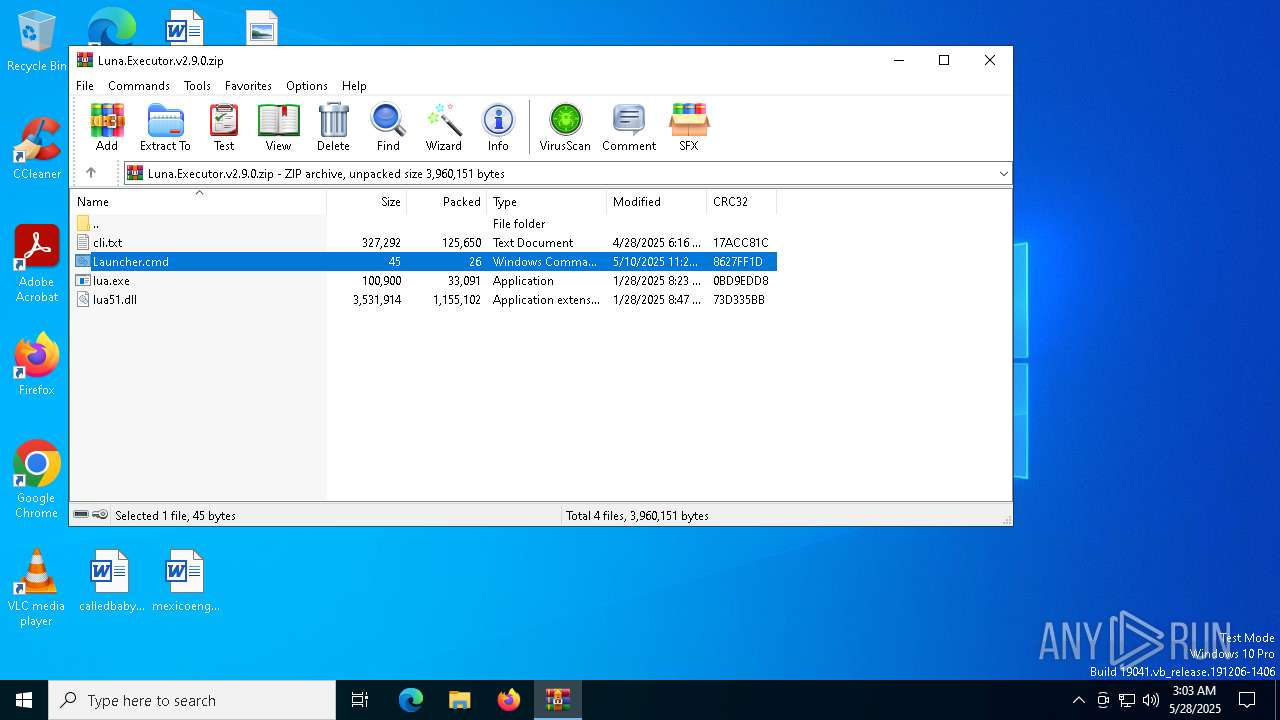
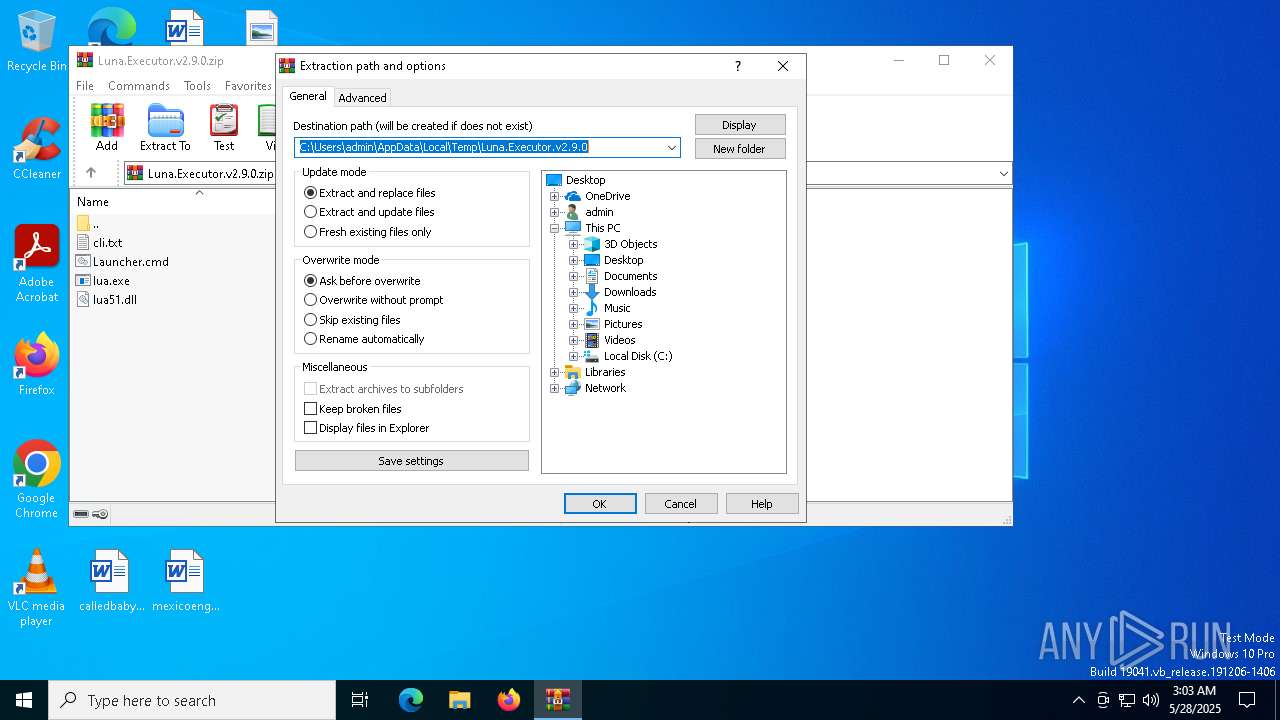
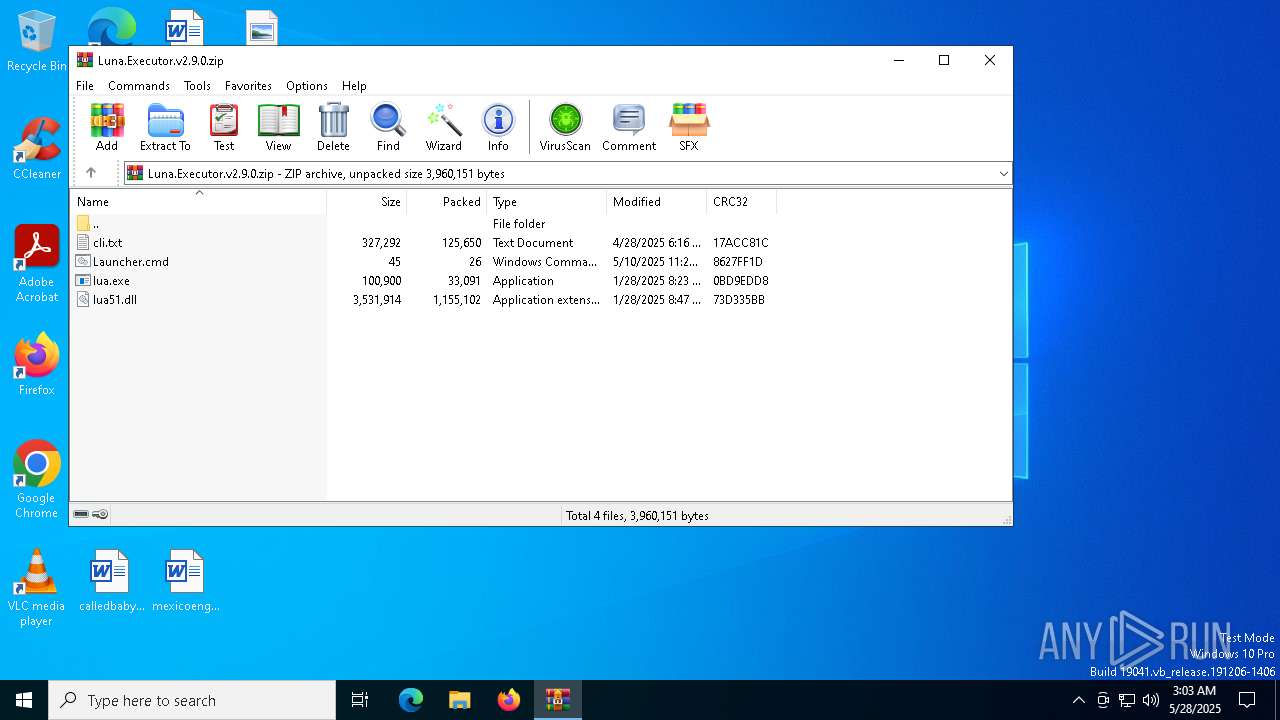
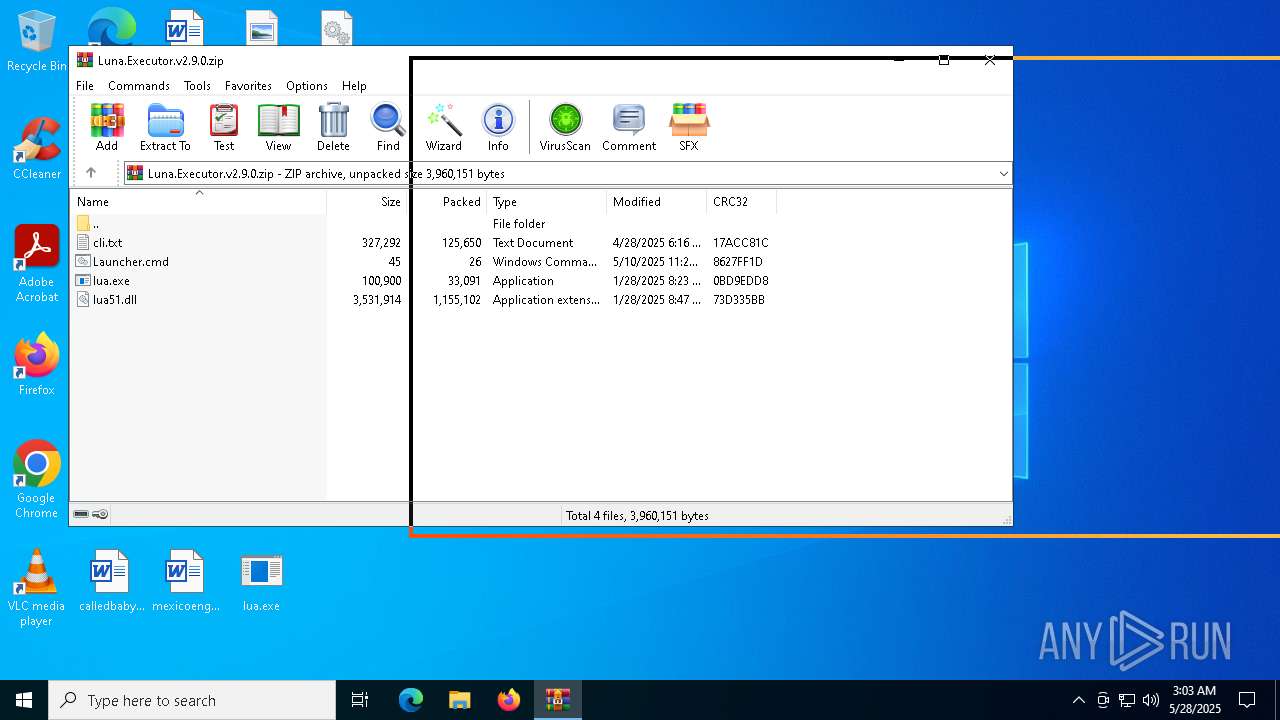
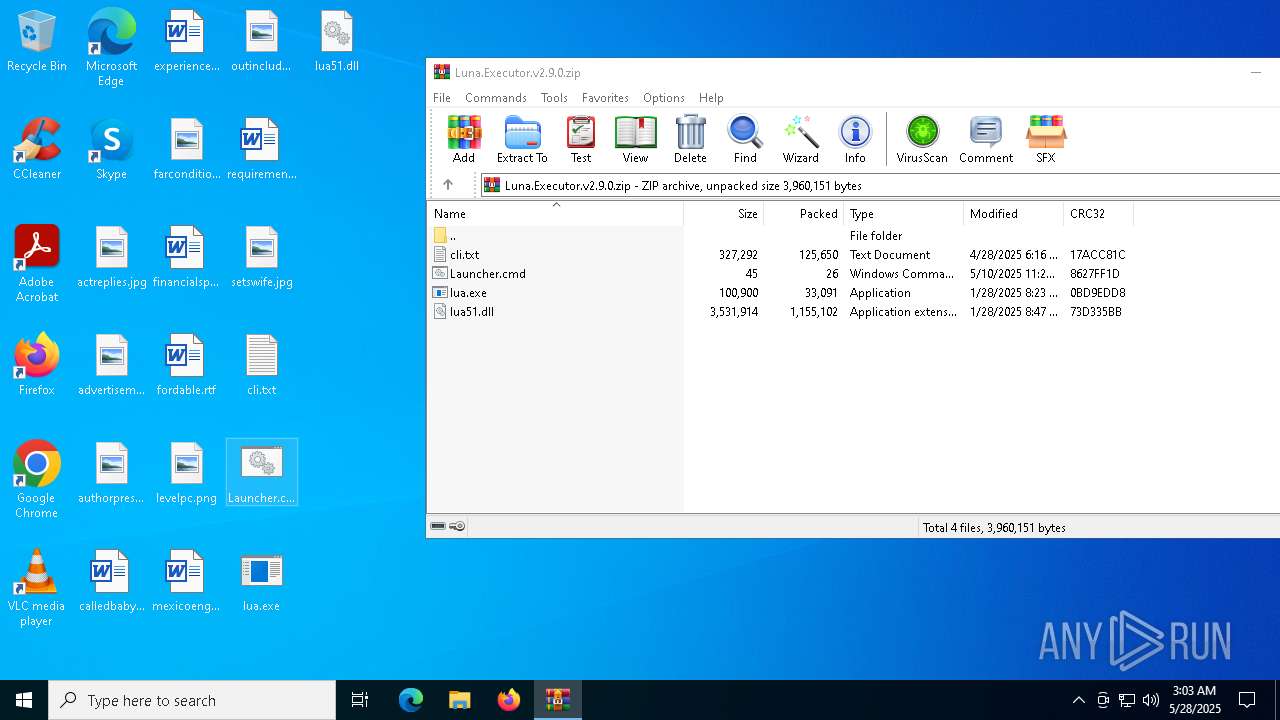
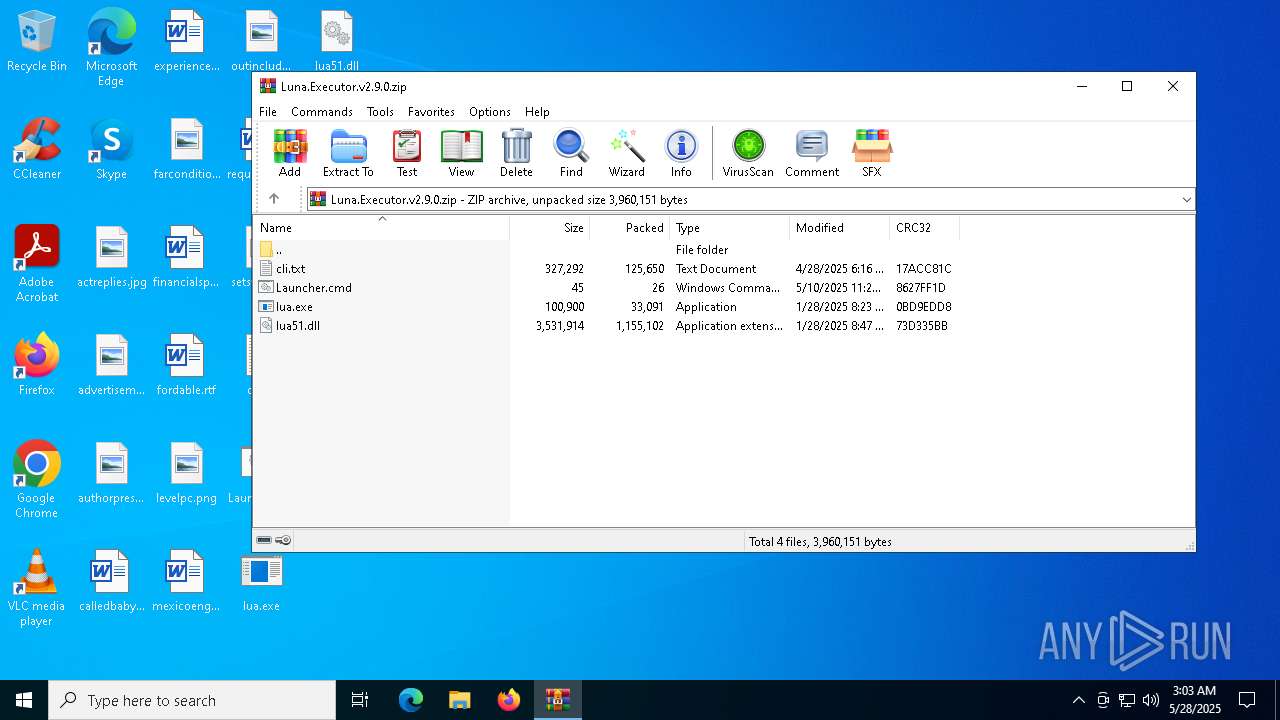
| File name: | Luna.Executor.v2.9.0.zip |
| Full analysis: | https://app.any.run/tasks/f1f40917-250c-4518-bd90-a472faf487ce |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 03:02:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 17AB262E32599B8F4156B5DE37B5D3AF |
| SHA1: | BEE8B80595FA020CB812CB09690196C993019B13 |
| SHA256: | 9FB7556D6FE8A04122464C476F6AD13B42592A08DF2BEFF667F0662DD821AC40 |
| SSDEEP: | 49152:prIeYbmgCLygT+yceMJgcMqbavus3NdOFVooJO4SJhz9a02sgpHqA0vCMYSRi6Hq:dBva3yIJ3euYdOPJSJh6pHqA2VYSnHe3 |
MALICIOUS
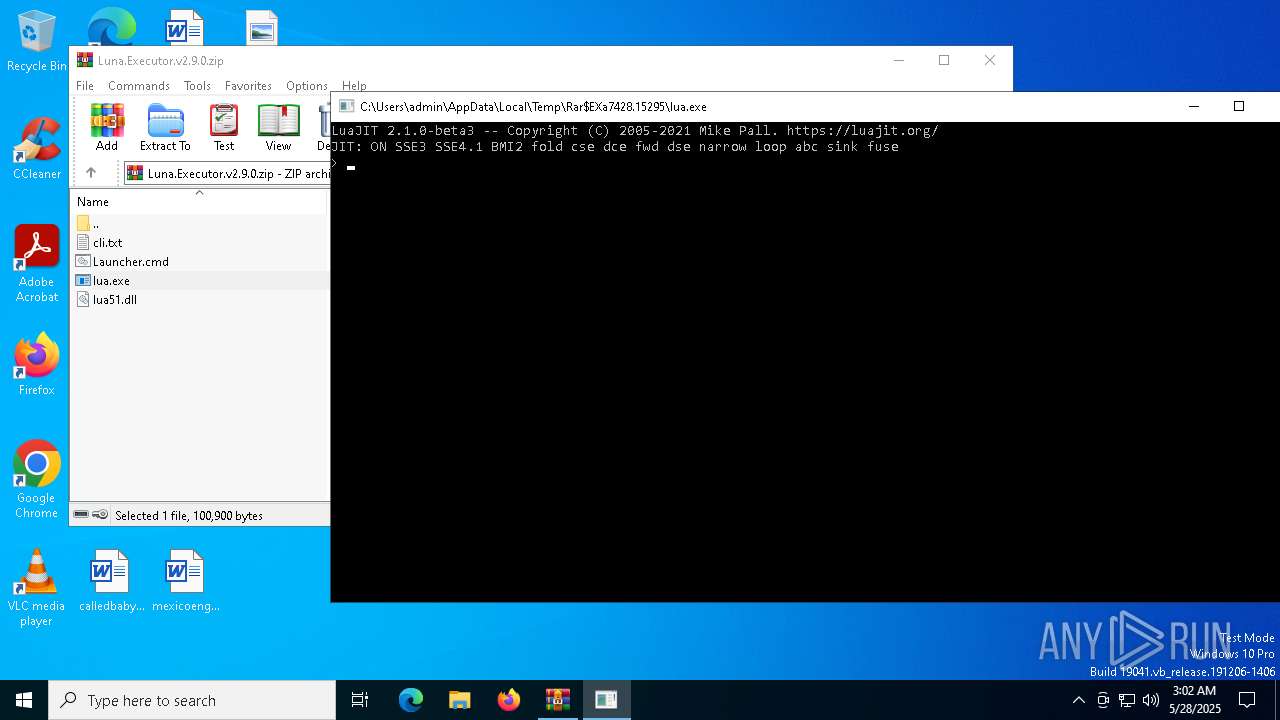
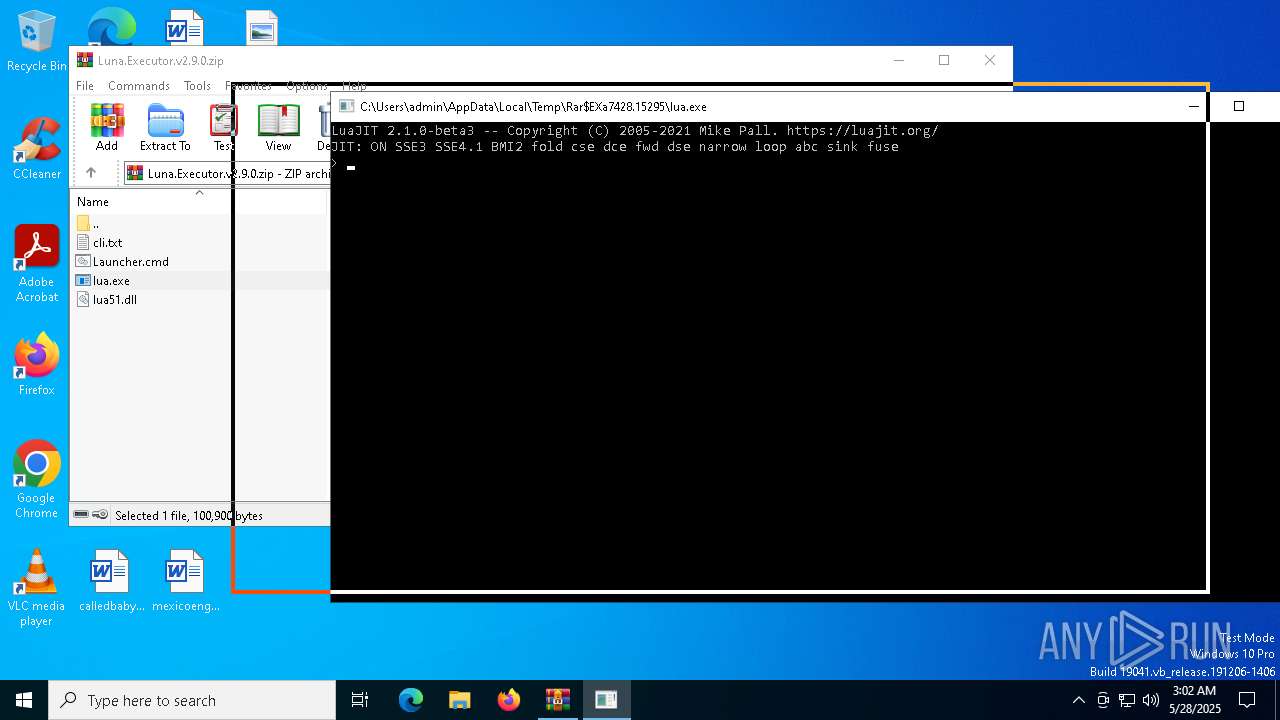
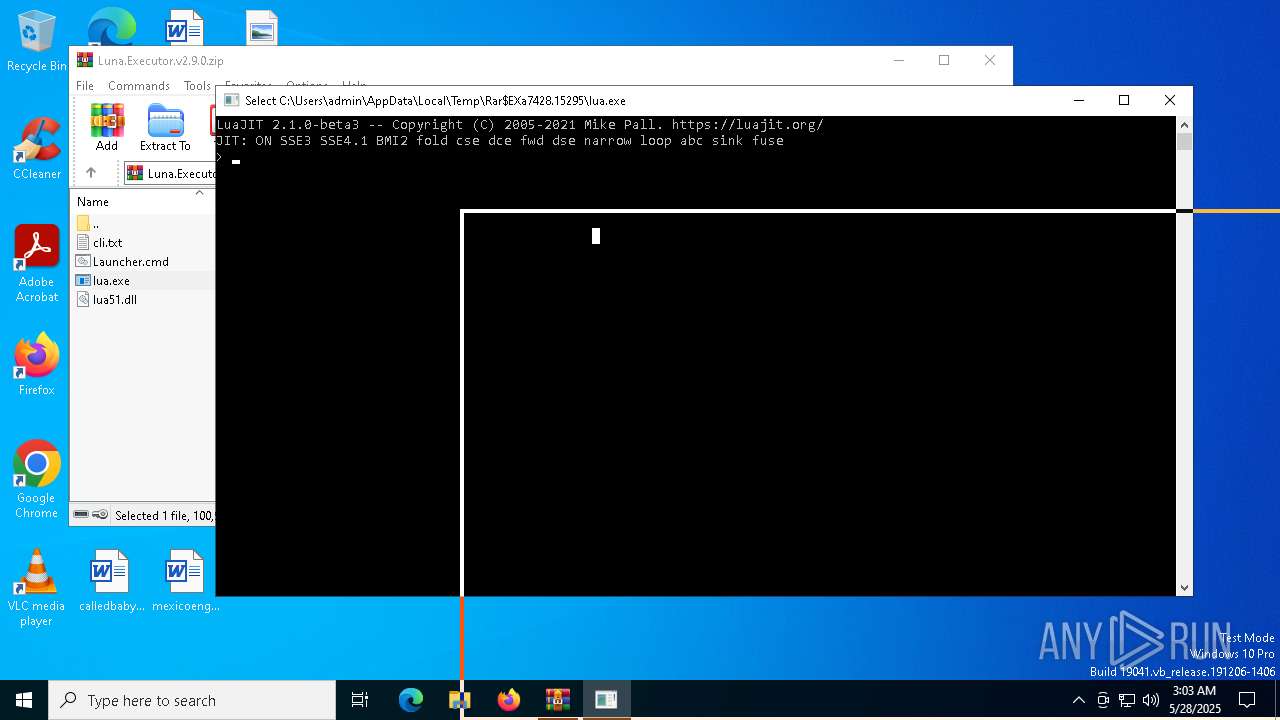
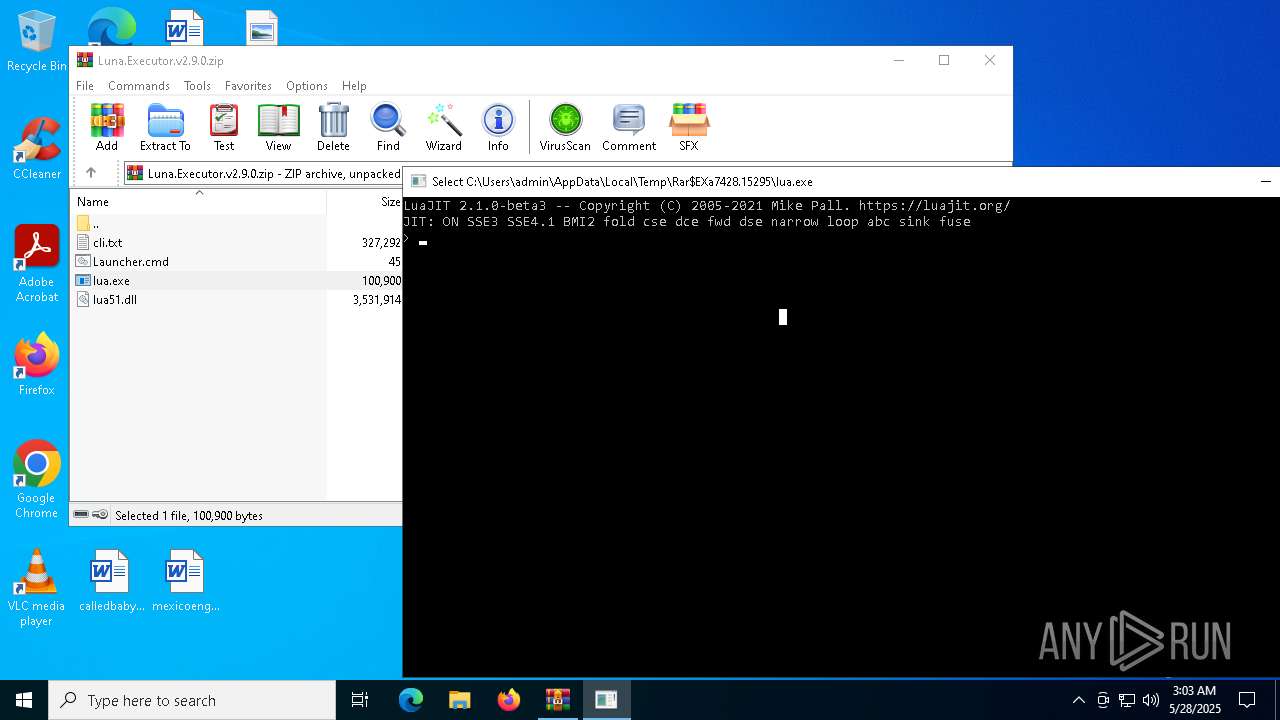
Generic archive extractor
- WinRAR.exe (PID: 7428)
GENERIC has been found (auto)
- WinRAR.exe (PID: 7428)
SUSPICIOUS
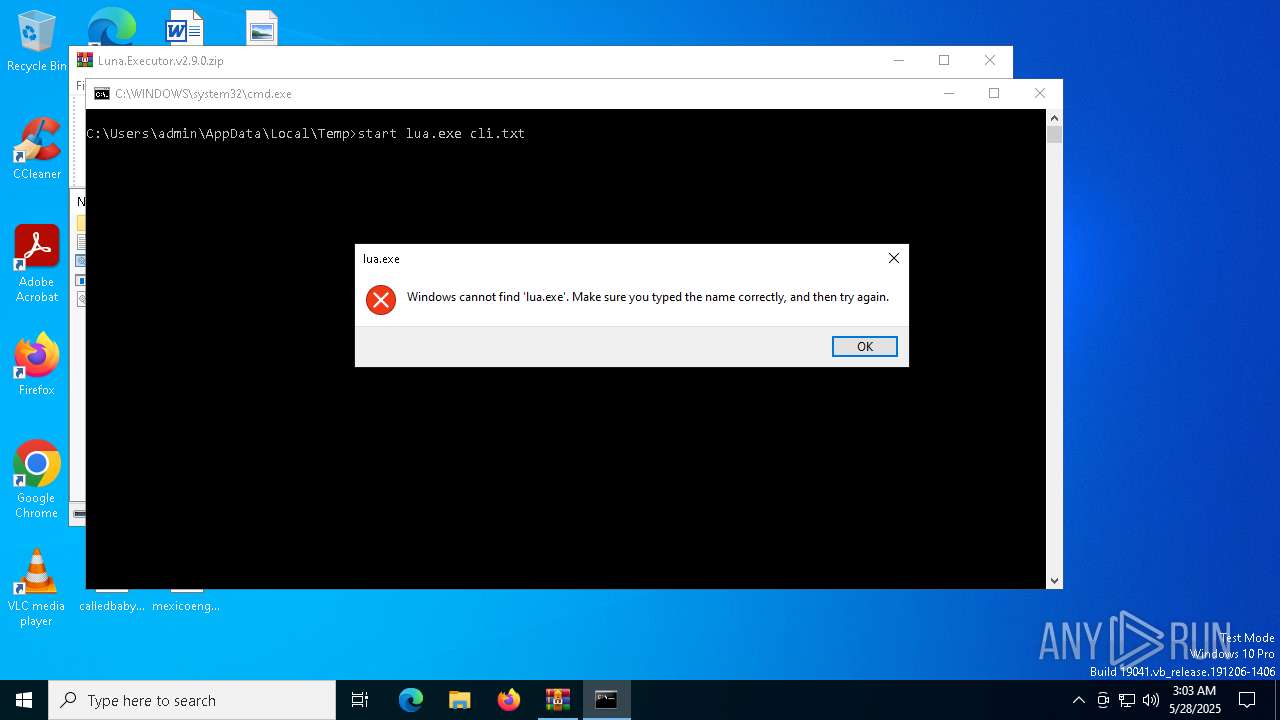
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7428)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7428)
- lua.exe (PID: 7548)
Executing commands from ".cmd" file
- WinRAR.exe (PID: 7428)
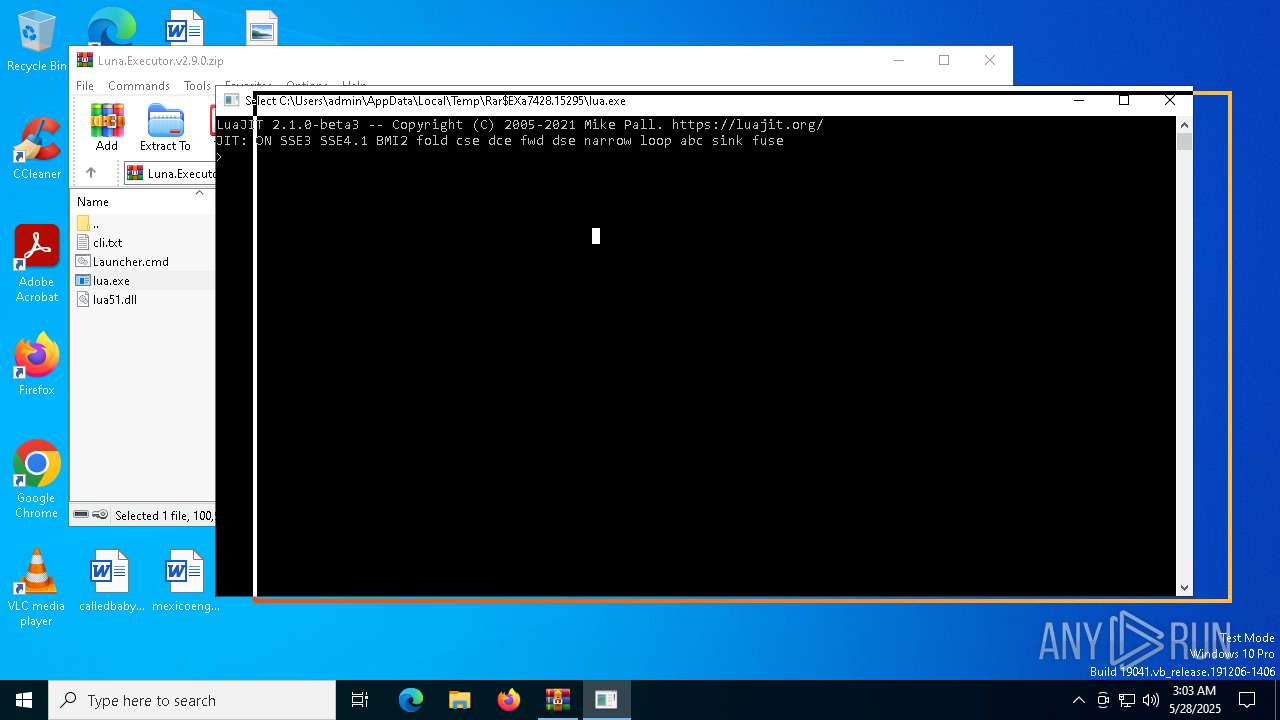
Checks for external IP
- svchost.exe (PID: 2196)
- lua.exe (PID: 7548)
Connects to the server without a host name
- lua.exe (PID: 7548)
INFO
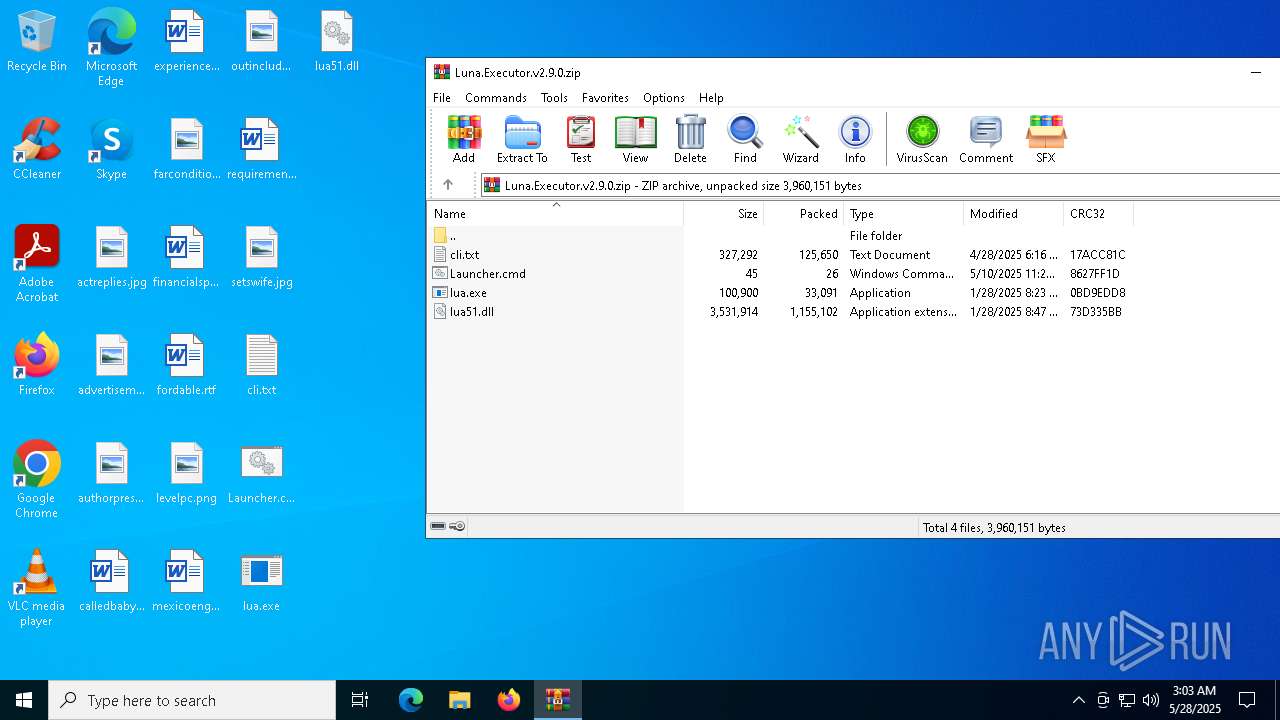
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7428)
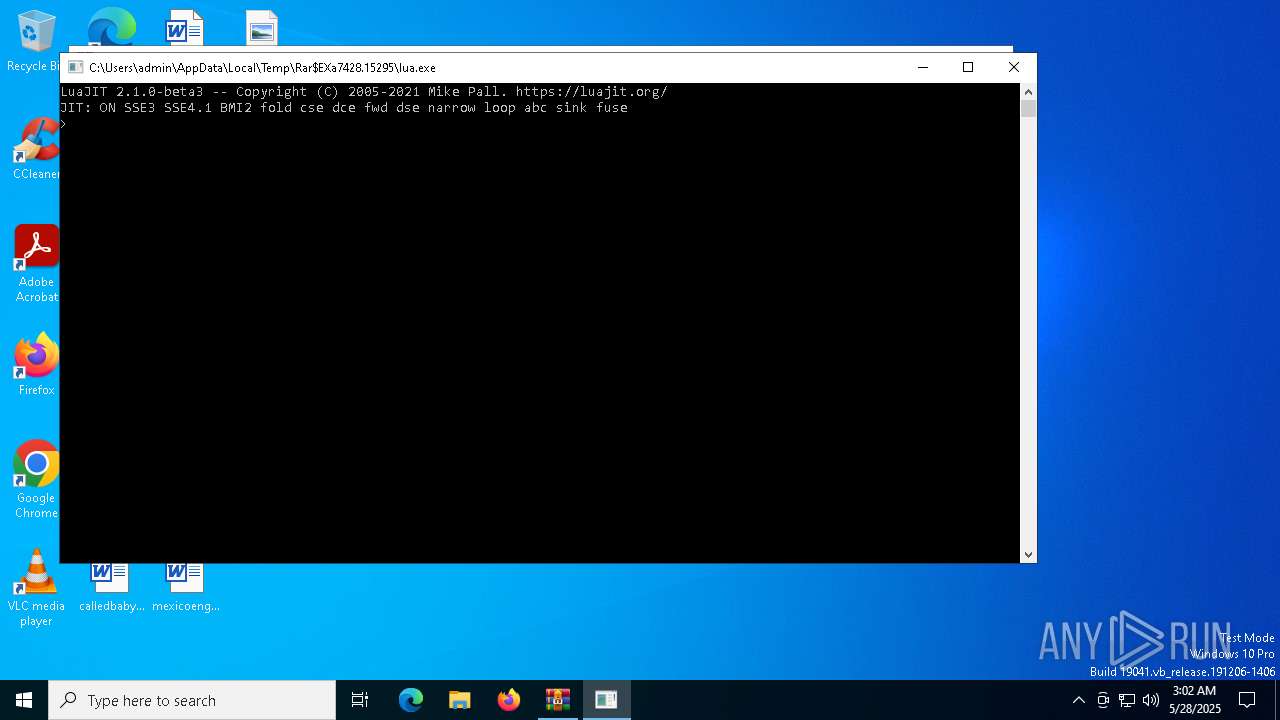
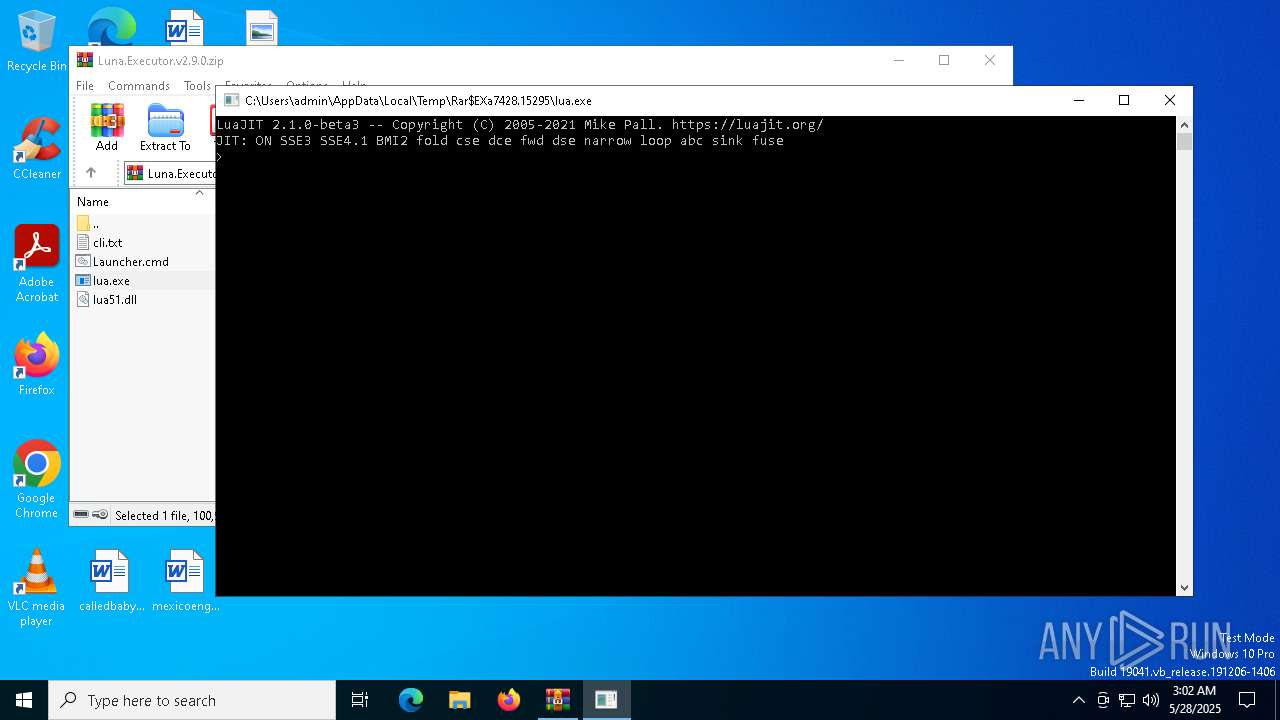
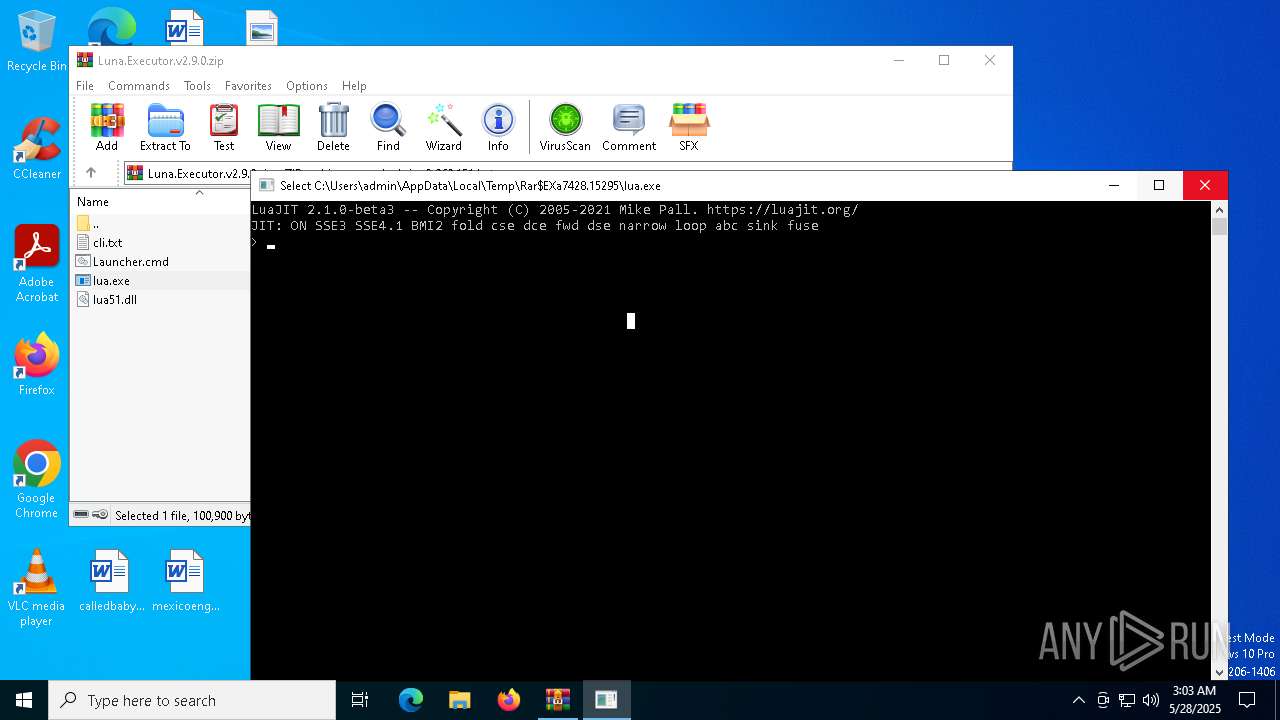
The process uses Lua
- lua.exe (PID: 7712)
Checks supported languages
- lua.exe (PID: 7712)
- lua.exe (PID: 7548)
Reads the software policy settings
- slui.exe (PID: 7640)
- lua.exe (PID: 7548)
- slui.exe (PID: 3156)
Manual execution by a user
- cmd.exe (PID: 7372)
Reads the computer name
- lua.exe (PID: 7548)
Checks proxy server information
- lua.exe (PID: 7548)
- slui.exe (PID: 3156)
Creates files or folders in the user directory
- lua.exe (PID: 7548)
Reads the machine GUID from the registry
- lua.exe (PID: 7548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
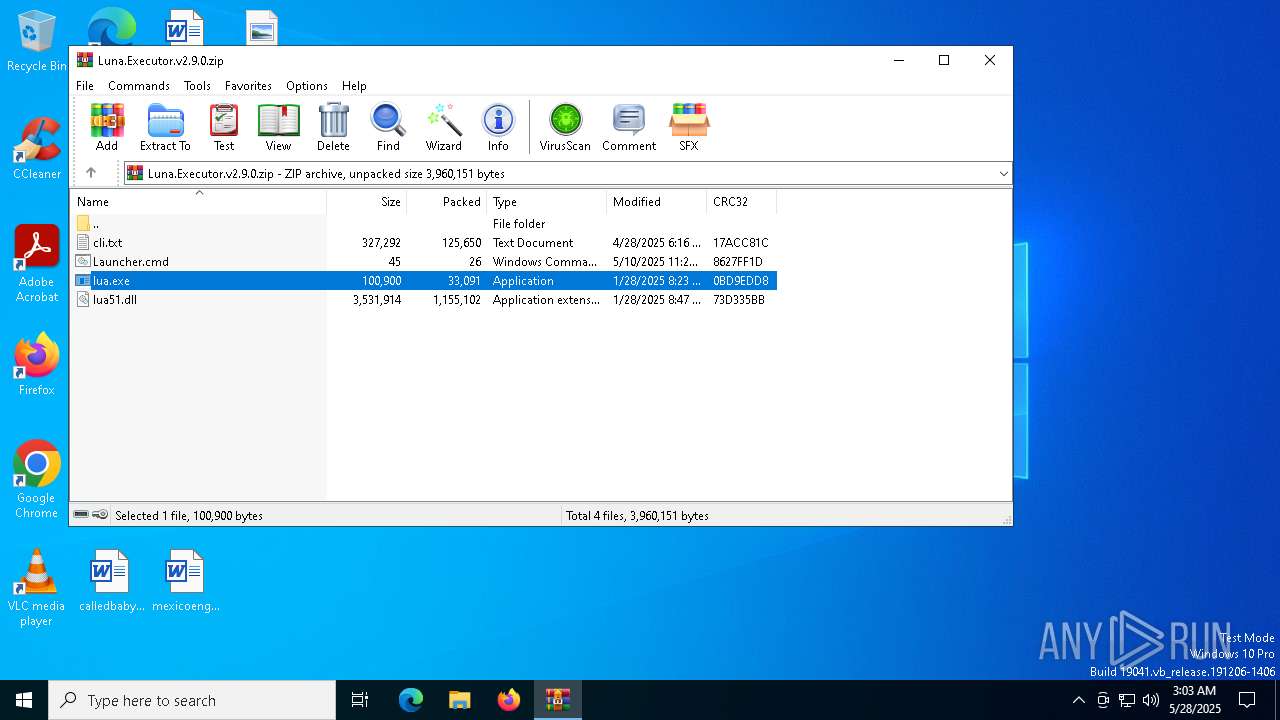
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:28 11:16:44 |
| ZipCRC: | 0x17acc81c |
| ZipCompressedSize: | 125650 |
| ZipUncompressedSize: | 327292 |
| ZipFileName: | cli.txt |
Total processes
142
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa7428.19665\Launcher.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3156 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | lua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7336 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7372 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Launcher.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
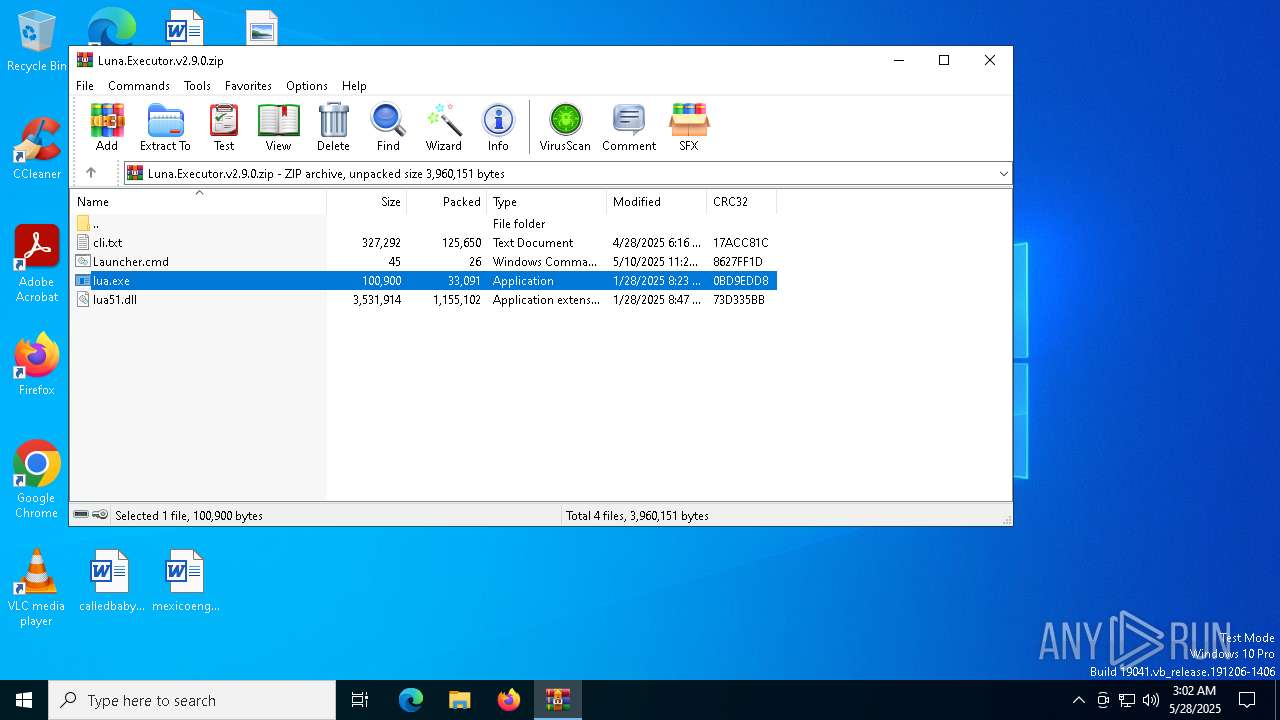
| 7428 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Luna.Executor.v2.9.0.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7548 | lua.exe cli.txt | C:\Users\admin\Desktop\lua.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7604 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 920
Read events
4 883
Write events
24
Delete events
13
Modification events
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Luna.Executor.v2.9.0.zip | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
4
Suspicious files
9
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7428 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7428.15295\cli.txt | text | |
MD5:BD48378E8370372F1C59E404BCB5C840 | SHA256:5FF619A187668B9FBF6426A4F3804F52900C7E0B2A9F3E8E140DEB00FB9F1829 | |||
| 7548 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:5CD7E29B56F19969C86746C699B45B58 | SHA256:072006AF86EF3E0A7F544AD3559B4B8EBC367E7DC71BCE23C5BFD28E0C678F54 | |||
| 7428 | WinRAR.exe | C:\Users\admin\Desktop\lua.exe | executable | |
MD5:00F60EE3FF2DEE681B5D7D442009B2C2 | SHA256:5343326FB0B4F79C32276F08FFCC36BD88CDE23AA19962BD1E8D8B80F5D33953 | |||
| 7428 | WinRAR.exe | C:\Users\admin\Desktop\cli.txt | text | |
MD5:BD48378E8370372F1C59E404BCB5C840 | SHA256:5FF619A187668B9FBF6426A4F3804F52900C7E0B2A9F3E8E140DEB00FB9F1829 | |||
| 7428 | WinRAR.exe | C:\Users\admin\Desktop\lua51.dll | executable | |
MD5:4EBD617A3AD9A9619172BD14A902A400 | SHA256:C7A657AF5455812FB215A8888B7E3FD8FA1BA27672A3ED9021EB6004EFF271AC | |||
| 7548 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:1E4AB04AD4FA6DCE95A68FC343B4C9ED | SHA256:7D280F8733B3F9C06AF12D93DD7704E2E905841FDB879E974A8ED680BDDCA23A | |||
| 7548 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:C22301B5245B697AA0D960E7D3A2D560 | SHA256:8E63BB9D833DDFF90DB225799A6B20821540B2A10AB3764EE07767259765DA0E | |||
| 7548 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\45266914391285466AEA1EA8BECBA90A_AFA50D4C705D6DE2B3101866B18F3B18 | binary | |
MD5:E24841BE45D5386A5BF706B722EED490 | SHA256:7B774C3533D7B2C1BF8F05CC90EF5DFF3CCF08C94446B7B91320D860F7FD605A | |||
| 7548 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:8B0FA6B0E76C66C453349861C992818F | SHA256:4B94B9671A3528B2ED180D9722B0ADAB1870ABB60647F62947E7994BC7787B09 | |||
| 7548 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:7C46225F9D82EC8CE0581C30C0C996D1 | SHA256:07B6F48D248D07CDCE80D690F7F47A25B2564ACEB93BE4C7DE49E9A6D58B3F27 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
30
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7548 | lua.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
7548 | lua.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7548 | lua.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7548 | lua.exe | GET | 200 | 172.217.16.195:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
7548 | lua.exe | GET | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr1/syE/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQwHTUyHgfAxFi3r4z8dPC7p%2BvIYAQUZmlJ1N4qnJEDz4kOJLgOMANuiC4CEQCzIZwUD2fxGg1YekhLZbuP | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1600 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5796 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7548 | lua.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |