| URL: | http://91.196.149.97:81/ridi.exe |
| Full analysis: | https://app.any.run/tasks/47a64f1f-1da8-4a36-aff1-4b16c367a663 |
| Verdict: | Malicious activity |
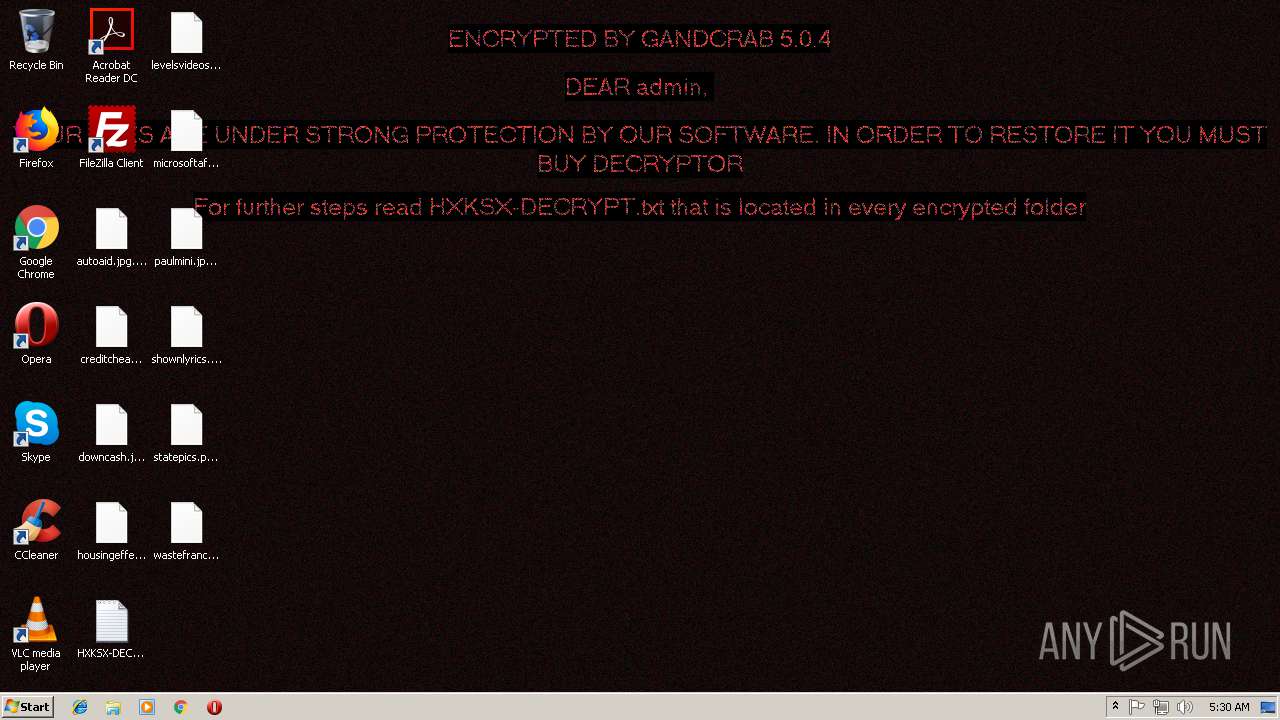
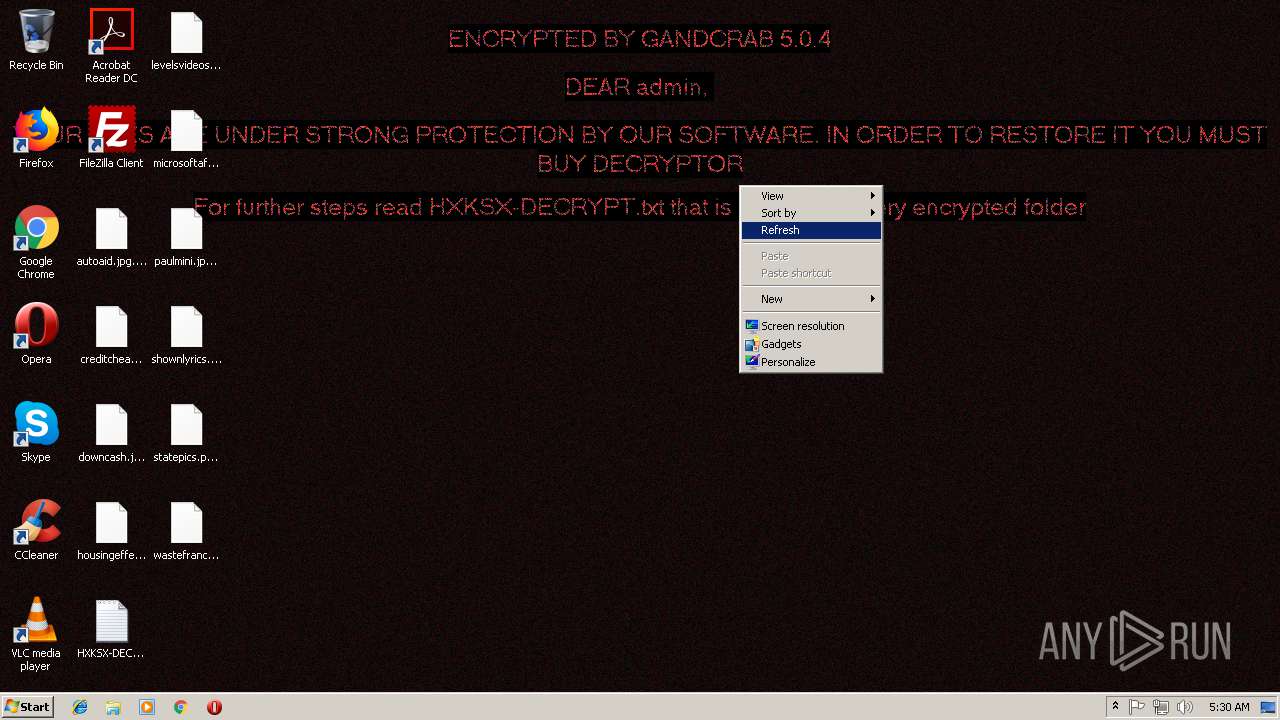
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | December 06, 2018, 05:29:58 |
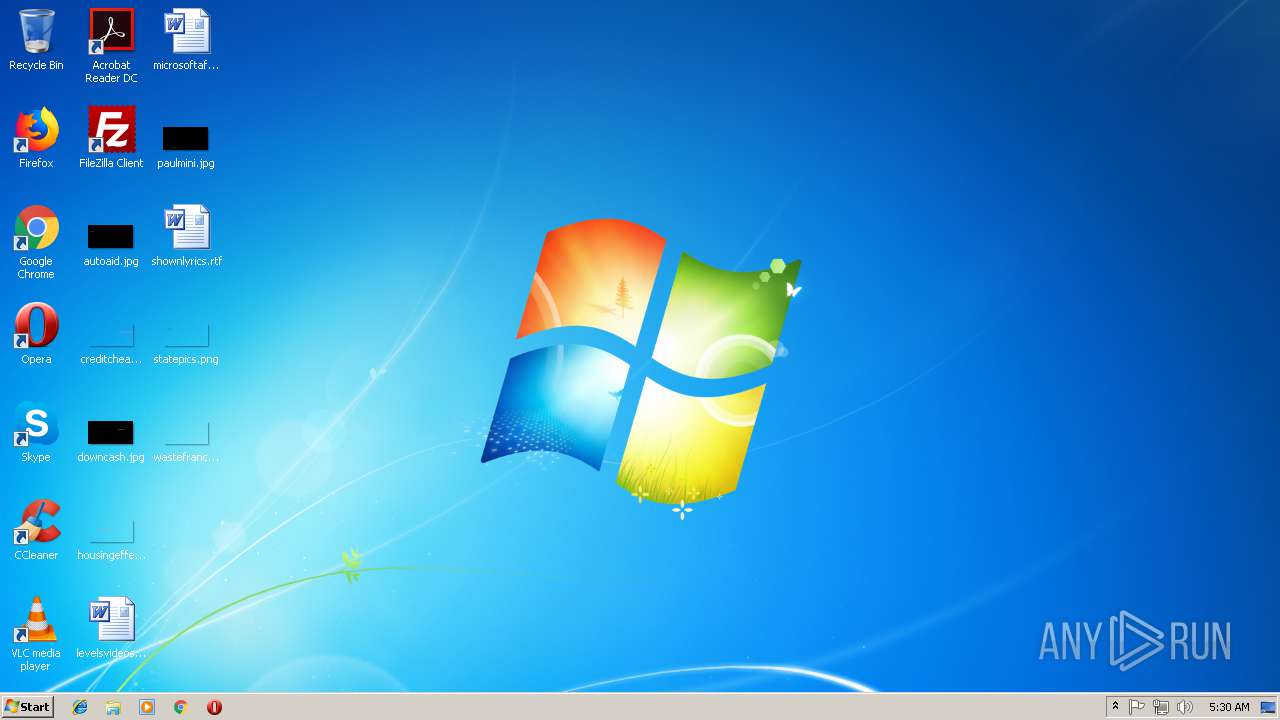
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3F27B4137D61909E7E9AAFD3F15F80E6 |
| SHA1: | 2C629ECB3F21B0D87F0AB974ACA545C3F510937E |
| SHA256: | 9FAA3ABC087B2017899D5248AA650833151B94241F5DAC1D0647A62A4DB4B8DA |
| SSDEEP: | 3:N1K0K+NwMJ:C0HN3 |
MALICIOUS
Application was dropped or rewritten from another process
- ridi[1].exe (PID: 3872)
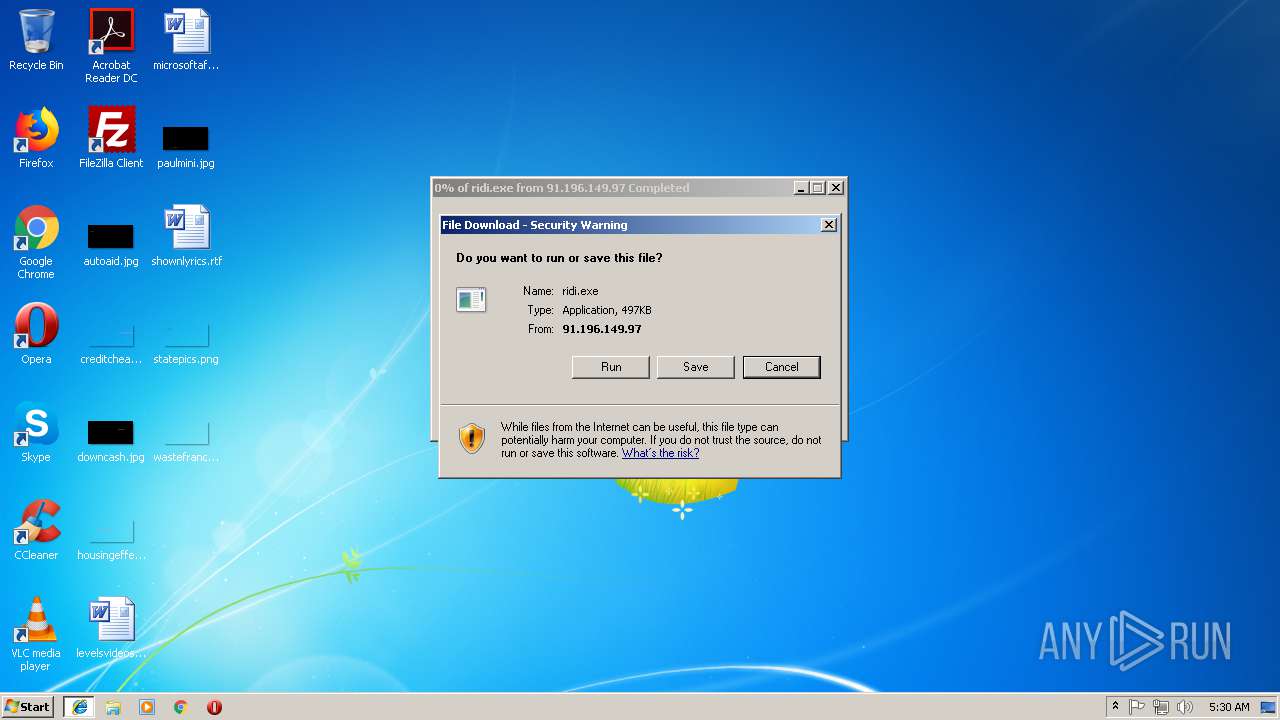
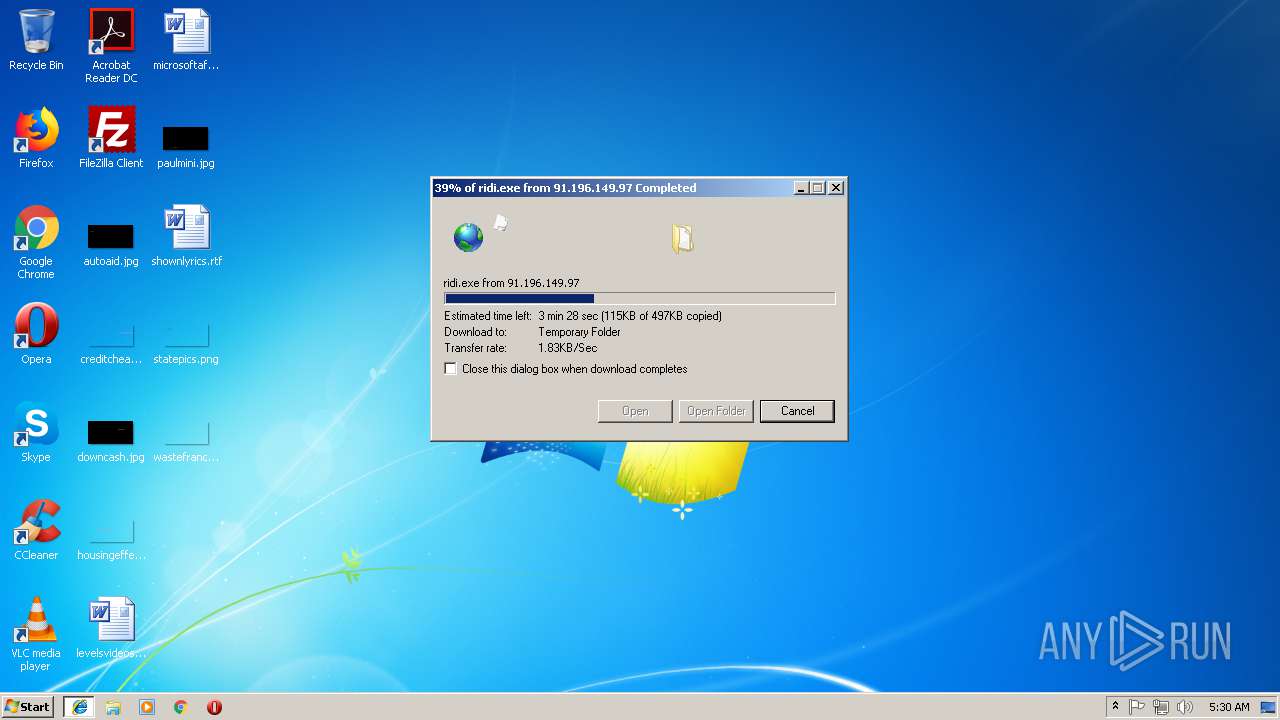
Downloads executable files from the Internet
- iexplore.exe (PID: 3764)
Actions looks like stealing of personal data
- ridi[1].exe (PID: 3872)
GandCrab keys found
- ridi[1].exe (PID: 3872)
Dropped file may contain instructions of ransomware
- ridi[1].exe (PID: 3872)
Writes file to Word startup folder
- ridi[1].exe (PID: 3872)
Deletes shadow copies
- ridi[1].exe (PID: 3872)
Renames files like Ransomware
- ridi[1].exe (PID: 3872)
Connects to CnC server
- ridi[1].exe (PID: 3872)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3484)
- iexplore.exe (PID: 3764)
Creates files like Ransomware instruction
- ridi[1].exe (PID: 3872)
Reads the cookies of Mozilla Firefox
- ridi[1].exe (PID: 3872)
Creates files in the user directory
- ridi[1].exe (PID: 3872)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3484)
Reads Internet Cache Settings
- iexplore.exe (PID: 3484)
- iexplore.exe (PID: 3764)
Connects to unusual port
- iexplore.exe (PID: 3764)
Dropped object may contain TOR URL's
- ridi[1].exe (PID: 3872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | ridi[1].exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3484 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\ridi[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\ridi[1].exe | iexplore.exe | ||||||||||||
User: admin Company: Delivery Hero Integrity Level: MEDIUM Description: Datarowview Privilege Transmitting Exit code: 0 Version: 7.6.3.3 Modules
| |||||||||||||||
Total events
770
Read events
687
Write events
79
Delete events
4
Modification events
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {01BEE863-F918-11E8-834A-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C000400060005001E000F00C701 | |||
Executable files
2
Suspicious files
282
Text files
234
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF38E52253EF69DC0A.TMP | — | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCF6133C275DF7DDD.TMP | — | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{01BEE863-F918-11E8-834A-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3872 | ridi[1].exe | C:\Users\admin\AppData\Local\Temp\11507584 | — | |
MD5:— | SHA256:— | |||
| 3872 | ridi[1].exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{01BEE864-F918-11E8-834A-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\ridi[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3872 | ridi[1].exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
188
DNS requests
87
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | ridi[1].exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
3872 | ridi[1].exe | GET | 302 | 192.185.159.253:80 | http://www.pizcam.com/ | US | — | — | malicious |
3872 | ridi[1].exe | GET | — | 212.59.186.61:80 | http://www.hotelweisshorn.com/ | CH | — | — | malicious |
3872 | ridi[1].exe | GET | 301 | 104.24.22.22:80 | http://www.belvedere-locarno.com/ | US | — | — | shared |
3872 | ridi[1].exe | GET | 301 | 83.166.138.7:80 | http://www.whitepod.com/ | CH | — | — | whitelisted |
3872 | ridi[1].exe | GET | 301 | 80.244.187.247:80 | http://www.hotelfarinet.com/ | GB | — | — | malicious |
3872 | ridi[1].exe | GET | — | 217.26.53.37:80 | http://www.hrk-ramoz.com/ | CH | — | — | malicious |
3872 | ridi[1].exe | GET | 301 | 83.138.82.107:80 | http://www.swisswellness.com/ | DE | — | — | whitelisted |
3764 | iexplore.exe | GET | 200 | 91.196.149.97:81 | http://91.196.149.97:81/ridi.exe | UA | executable | 497 Kb | suspicious |
3872 | ridi[1].exe | GET | 200 | 74.220.215.73:80 | http://www.bizziniinfissi.com/ | US | html | 6.96 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3872 | ridi[1].exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
3872 | ridi[1].exe | 138.201.162.99:443 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
3872 | ridi[1].exe | 192.185.159.253:80 | www.pizcam.com | CyrusOne LLC | US | malicious |
3872 | ridi[1].exe | 192.185.159.253:443 | www.pizcam.com | CyrusOne LLC | US | malicious |
3484 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3764 | iexplore.exe | 91.196.149.97:81 | — | Maximum-Net LLC | UA | suspicious |
3872 | ridi[1].exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3872 | ridi[1].exe | 83.166.138.7:80 | www.whitepod.com | Infomaniak Network SA | CH | malicious |
3872 | ridi[1].exe | 212.59.186.61:80 | www.hotelweisshorn.com | green.ch AG | CH | malicious |
3872 | ridi[1].exe | 83.166.138.7:443 | www.whitepod.com | Infomaniak Network SA | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
www.whitepod.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3764 | iexplore.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3764 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3872 | ridi[1].exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
3872 | ridi[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3872 | ridi[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3872 | ridi[1].exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
3872 | ridi[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3872 | ridi[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3872 | ridi[1].exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3872 | ridi[1].exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |