| File name: | Test.exe |
| Full analysis: | https://app.any.run/tasks/35269764-aedd-4e22-8e1f-a4ffdf277592 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 19:37:00 |
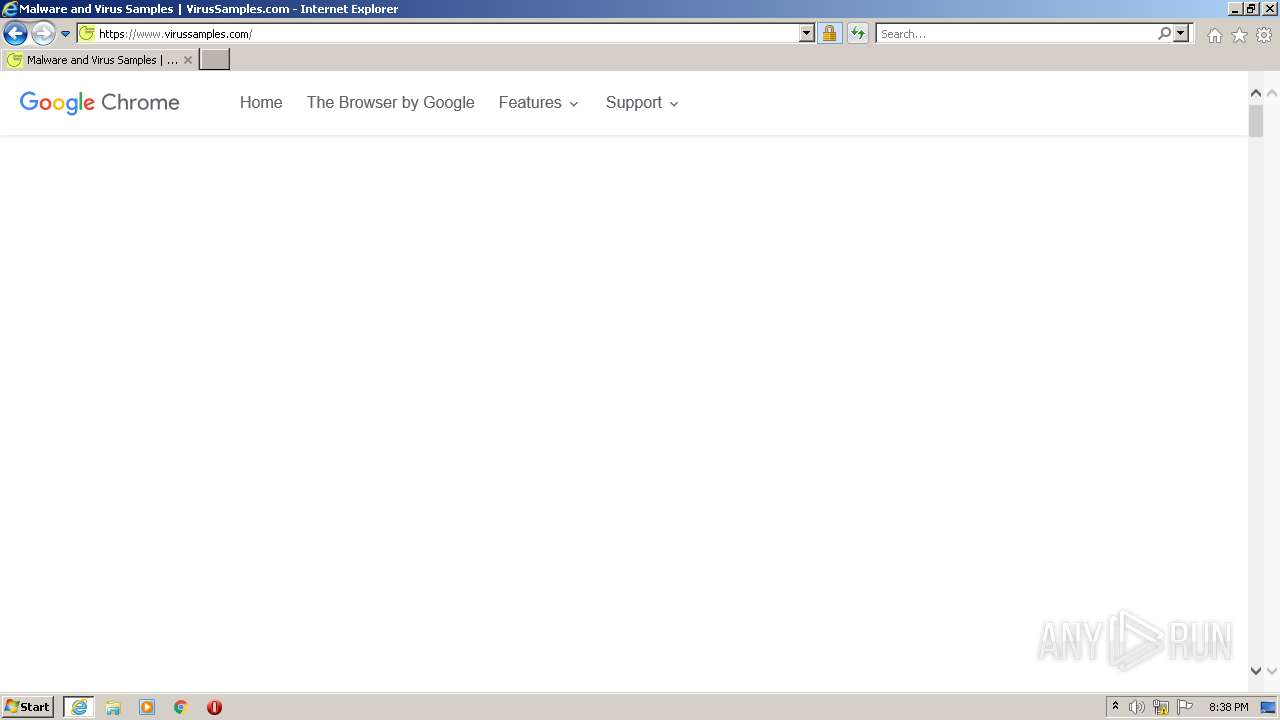
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-python |
| File info: | Python script, ASCII text executable, with CRLF line terminators |
| MD5: | 9809F6DB1527EFDE1B69144D77CEA5F1 |
| SHA1: | 8759FED55C7442769D02E26952DC94452EB9231A |
| SHA256: | 9FA547EF7A4085FDB6289B0B16BF14018C0FA9A4E391132BD8C1D0017CE0D2BD |
| SSDEEP: | 48:TfEaXjWkgXsJcellNLLOfWukWSWwojzLTejzu+aQ:TfEazTg8cel3LLX4DjzLK9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 444)
- iexplore.exe (PID: 3716)
INFO
Manual execution by user
- opera.exe (PID: 2708)
- iexplore.exe (PID: 3716)
Reads the computer name
- opera.exe (PID: 2708)
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 444)
Check for Java to be installed
- opera.exe (PID: 2708)
Creates files in the user directory
- opera.exe (PID: 2708)
- iexplore.exe (PID: 444)
- iexplore.exe (PID: 3716)
Checks supported languages
- iexplore.exe (PID: 3716)
- ntvdm.exe (PID: 2468)
- opera.exe (PID: 2708)
- iexplore.exe (PID: 444)
Changes internet zones settings
- iexplore.exe (PID: 3716)
Reads the date of Windows installation
- opera.exe (PID: 2708)
- iexplore.exe (PID: 3716)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2708)
Checks Windows Trust Settings
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 444)
Application launched itself
- iexplore.exe (PID: 3716)
Reads settings of System Certificates
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 444)
Changes settings of System certificates
- iexplore.exe (PID: 3716)
Reads internet explorer settings
- iexplore.exe (PID: 444)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3716 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2468 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3716 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
30 343
Read events
30 043
Write events
292
Delete events
8
Modification events
| (PID) Process: | (2708) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (2708) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 195849376 | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960769 | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 496008751 | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960769 | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
65
Text files
305
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr9BB5.tmp | text | |
MD5:— | SHA256:— | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr9C04.tmp | xml | |
MD5:— | SHA256:— | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8PX5BOBYEGKVLQA9P7DB.temp | binary | |
MD5:— | SHA256:— | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | xml | |
MD5:— | SHA256:— | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2468 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs446D.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 2708 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opicacrt6.dat | binary | |
MD5:82F1A2B1176A5ECC457D32301E2AD833 | SHA256:A783052804DD4C232BE2ED3DC00C430CB67A20370890E235562ED2B27B5A602E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
115
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2708 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
444 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
444 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
444 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ae838bfaba23bdca | US | compressed | 60.0 Kb | whitelisted |
444 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDwQ9JNOs3IcArkp%2FBu7NbU | US | der | 472 b | whitelisted |
444 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDExSUZ712qmxLhqE9UUaDV | US | der | 472 b | whitelisted |
444 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
444 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e640db0a88f0110c | US | compressed | 60.0 Kb | whitelisted |
444 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCL0Jr%2Bbx9ShZBIWzZ25V2m | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2708 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
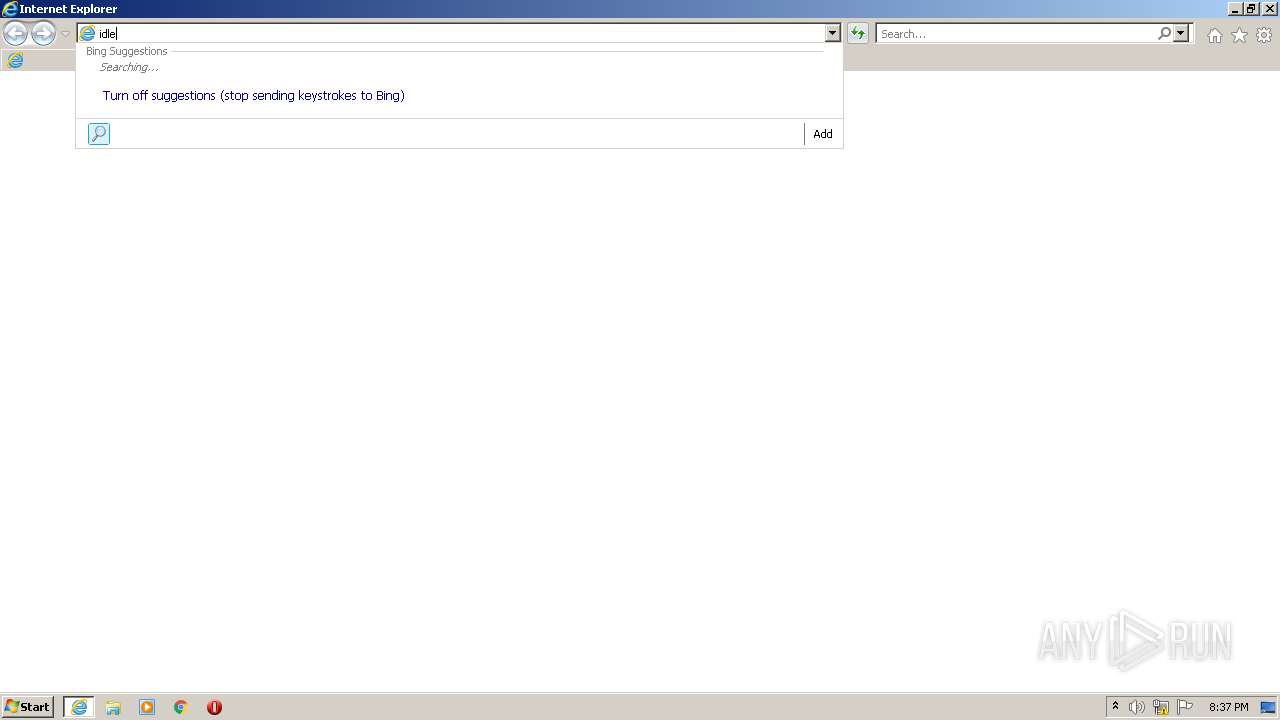
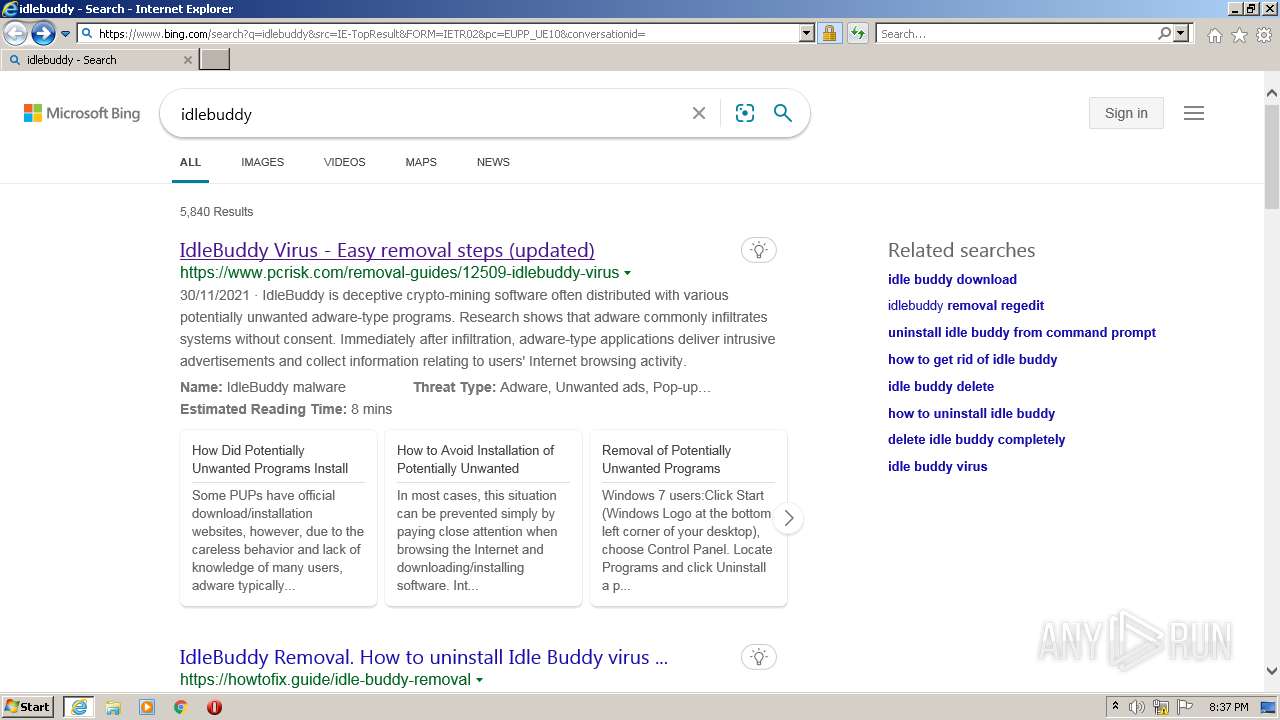
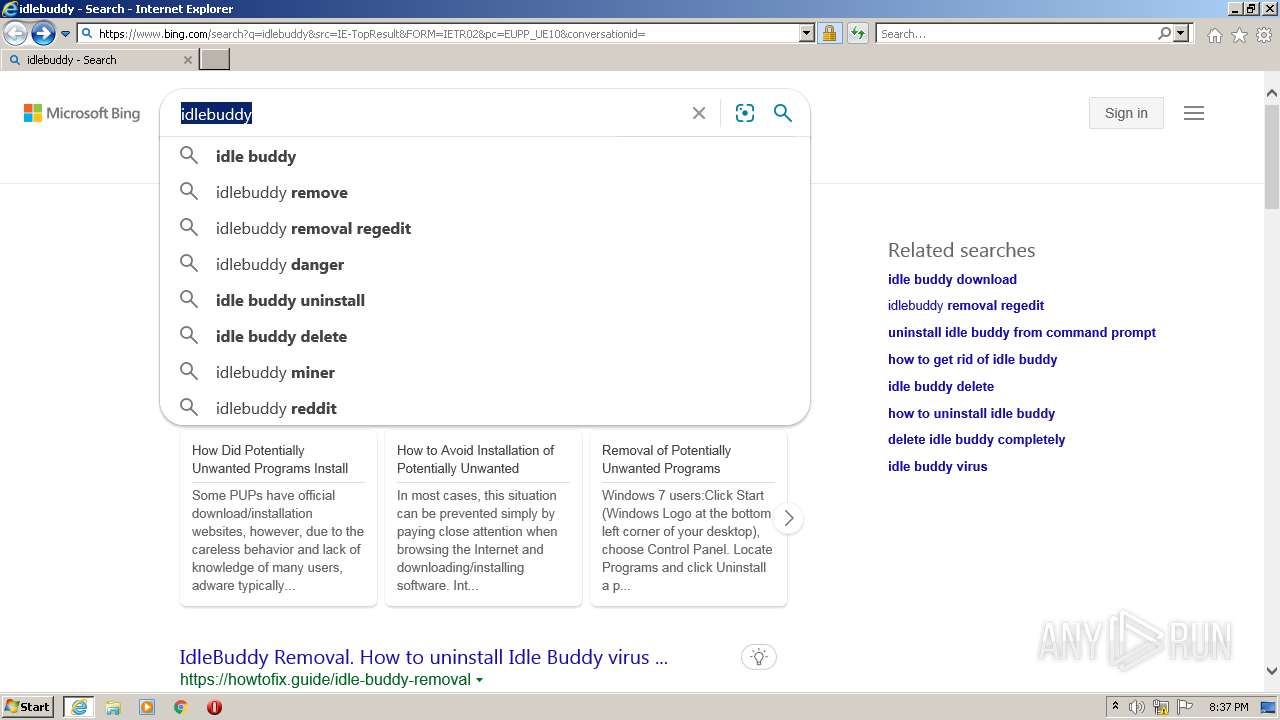
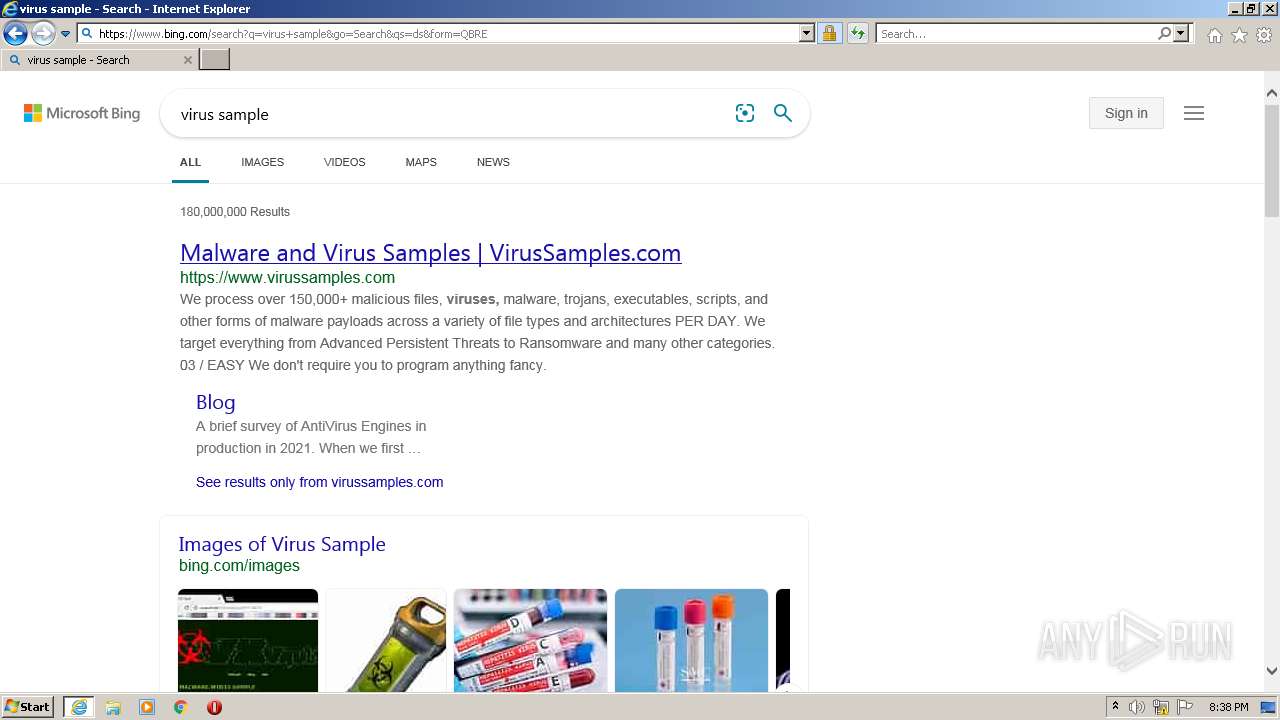
3716 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2708 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3716 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3716 | iexplore.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
444 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
444 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
444 | iexplore.exe | 40.126.32.134:443 | login.microsoftonline.com | Microsoft Corporation | US | whitelisted |
444 | iexplore.exe | 40.126.32.136:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
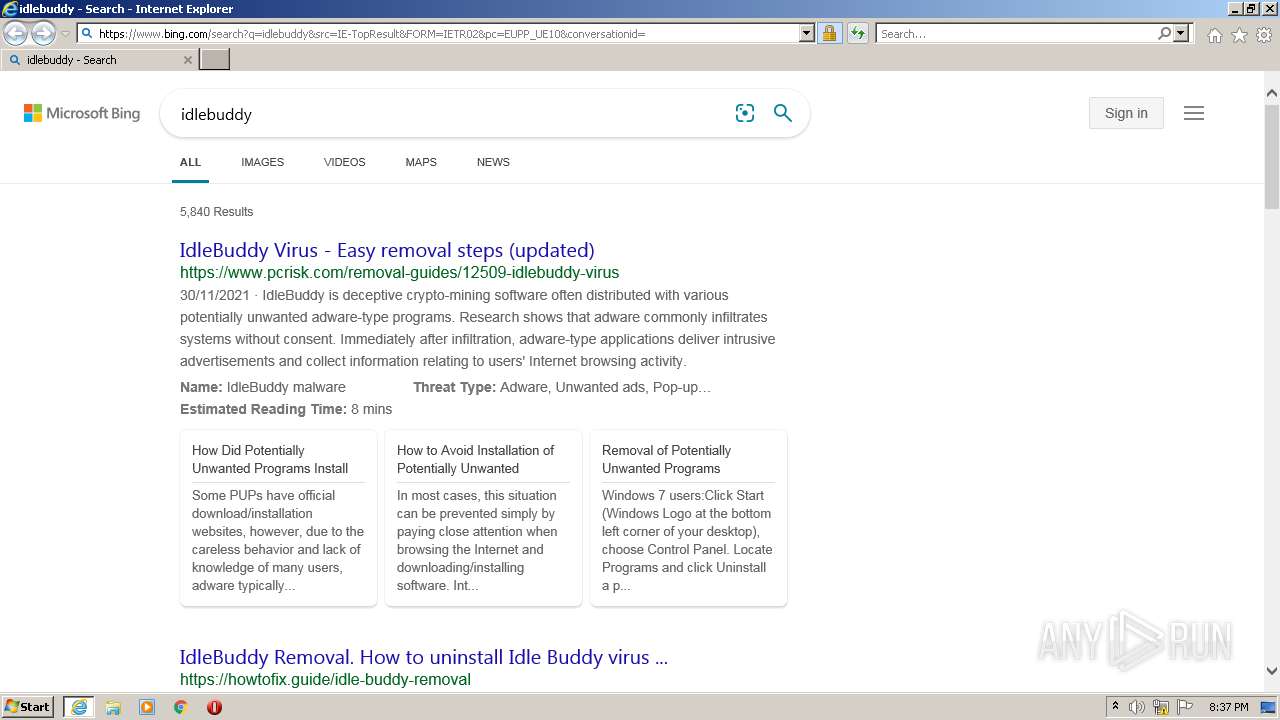
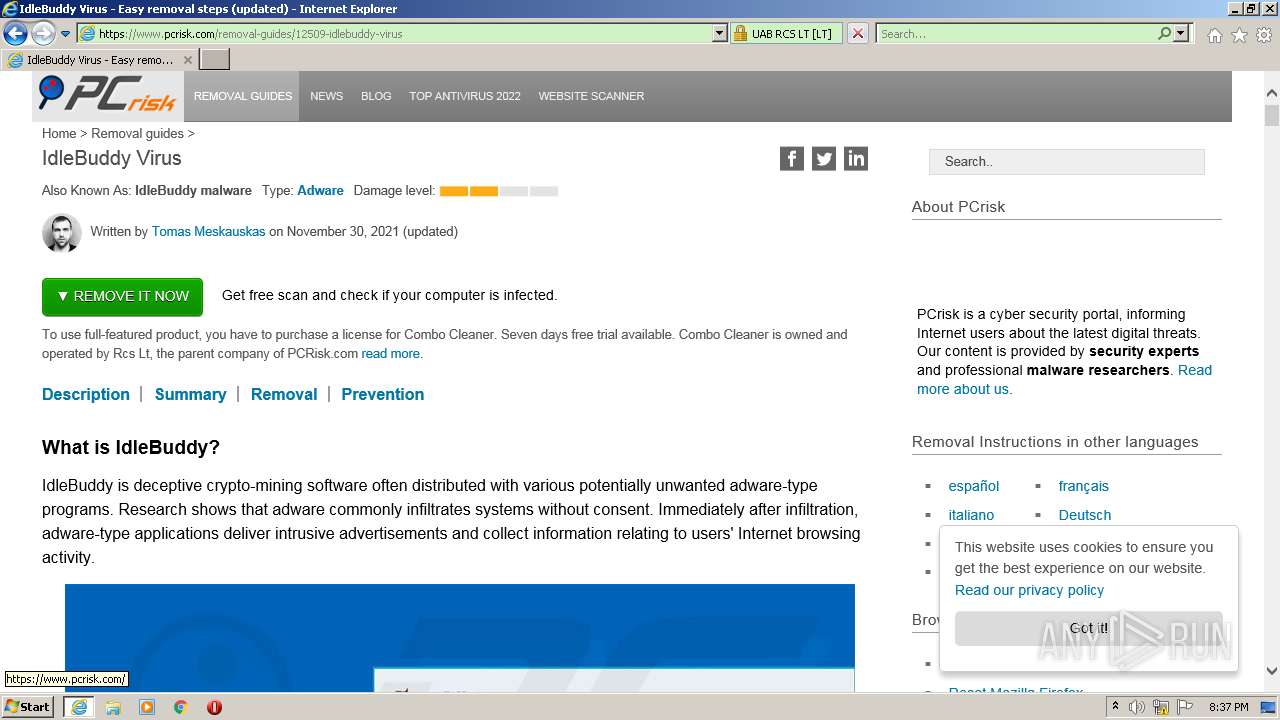
444 | iexplore.exe | 172.66.43.223:443 | www.pcrisk.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.youtube.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
www.pcrisk.com |
| unknown |