| File name: | MC5 Trainer v5.5.EXE |
| Full analysis: | https://app.any.run/tasks/cdbe98aa-91e9-4f63-ac5a-dae2a5de10e9 |
| Verdict: | No threats detected |
| Analysis date: | March 18, 2018, 08:52:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 69F1039A651698D071D1B1F3D083CF80 |
| SHA1: | F4620684106BDD2949BA042232AA029058176868 |
| SHA256: | 9F9A7AA1C45B22A78689870656947F3FC1B8CE02790B73854C3E00C653FEE1F4 |
| SSDEEP: | 98304:9mrEsT06tT7VAab4Ft8A+U9BQA3Ib8gCDwzG+FtcOKmg0Skpn9wHwb7PfsQUWKje:9sg69h7b4f8Hw3Ib8bEKA9n9wETEQUW/ |
MALICIOUS
Application was dropped or rewritten from another process
- MC5 Trainer v5.5.EXE (PID: 3720)
- MC5 Trainer v5.5.EXE (PID: 4064)
Changes internet zones settings
- iexplore.exe (PID: 4020)
Application loaded dropped or rewritten executable
- MC5 Trainer v5.5.EXE (PID: 4064)
SUSPICIOUS
Application launched itself
- iexplore.exe (PID: 4020)
Creates files in the user directory
- MC5 Trainer v5.5.EXE (PID: 4064)
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 4020)
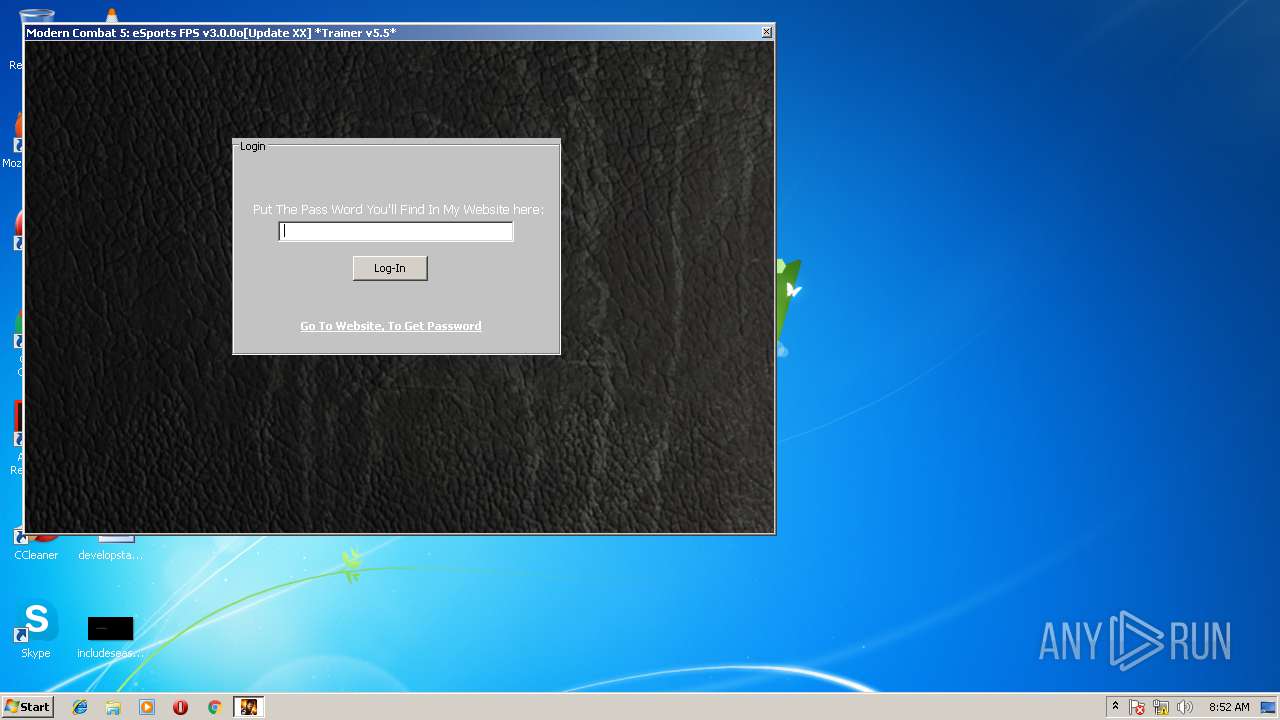
Starts Internet Explorer
- MC5 Trainer v5.5.EXE (PID: 4064)
- iexplore.exe (PID: 4020)
INFO
Dropped object may contain URL's
- MC5 Trainer v5.5.EXE (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:28 16:45:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 36352 |
| InitializedDataSize: | 5802496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x15eb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Jun-2013 14:45:44 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-Jun-2013 14:45:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008D54 | 0x00008E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56215 |
.rdata | 0x0000A000 | 0x00002114 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.44357 |
.data | 0x0000D000 | 0x00002ADC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.1026 |
.rsrc | 0x00010000 | 0x005847B0 | 0x00584800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.991 |
.reloc | 0x00595000 | 0x00000EEA | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.32883 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.77792 | 357 | Latin 1 / Western European | English - United States | RT_MANIFEST |
101 | 7.92981 | 4118 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
ARCHIVE | 7.99836 | 5408856 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
DECOMPRESSOR | 6.11488 | 194048 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
40
Monitored processes
6
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2228 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4020 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\MC5 Trainer v5.5.EXE" | C:\Users\admin\AppData\Local\Temp\MC5 Trainer v5.5.EXE | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3252 | "C:\Users\admin\AppData\Local\Temp\MC5 Trainer v5.5.EXE" | C:\Users\admin\AppData\Local\Temp\MC5 Trainer v5.5.EXE | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3720 | "C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\MC5 Trainer v5.5.EXE" -ORIGIN:"C:\Users\admin\AppData\Local\Temp\" | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\MC5 Trainer v5.5.EXE | MC5 Trainer v5.5.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4020 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | — | MC5 Trainer v5.5.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4064 | "C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\MC5 Trainer v5.5.EXE" "C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\CET_TRAINER.CETRAINER" "-ORIGIN:C:\Users\admin\AppData\Local\Temp\" | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\MC5 Trainer v5.5.EXE | MC5 Trainer v5.5.EXE | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Exit code: 0 Version: 6.7.0.5198 Modules
| |||||||||||||||
Total events
347
Read events
269
Write events
78
Delete events
0
Modification events
| (PID) Process: | (4064) MC5 Trainer v5.5.EXE | Key: | HKEY_CURRENT_USER\Software\Cheat Engine\Window Positions 96 |
| Operation: | write | Name: | AdvancedOptions Position |
Value: C0000000000100003B0200002F010000 | |||
| (PID) Process: | (4064) MC5 Trainer v5.5.EXE | Key: | HKEY_CURRENT_USER\Software\Cheat Engine\Window Positions 96 |
| Operation: | write | Name: | frmAutoInject Position |
Value: AE010000E5020000AF0100004B010000 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B000000090000000000000000000000000000000400000000000000108E82C8479FD301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A8640B0000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\AdminActive |
| Operation: | write | Name: | {D00DBCCF-2A89-11E8-943E-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (4020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
Executable files
6
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3252 | MC5 Trainer v5.5.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\CET_Archive.dat | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3720 | MC5 Trainer v5.5.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\CET_TRAINER.CETRAINER | binary | |
MD5:— | SHA256:— | |||
| 3252 | MC5 Trainer v5.5.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\MC5 Trainer v5.5.EXE | executable | |
MD5:A65C29111A4CF5A7FDD5A9D79F77BCAB | SHA256:DAB3003436B6861AE220CC5FDCB97970FC05AFDF114C2F91E46EED627CE3D6AF | |||
| 3720 | MC5 Trainer v5.5.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\defines.lua | text | |
MD5:AF18263191D6F3FE55AF8BD455A947BD | SHA256:A71D5867A2C1A25DFE7649549449024128DD5540A492DA76856E150FDBE07FEB | |||
| 3720 | MC5 Trainer v5.5.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\lua53-32.dll | executable | |
MD5:9B8D650FFC6FFF2CFE67A7E5C020CCFB | SHA256:59B9F3FA57C1B7FDD3312F864C20EAEE76BA9FCB7BB8D2542060D3533CED12C2 | |||
| 3720 | MC5 Trainer v5.5.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\MC5 Trainer v5.5.EXE | executable | |
MD5:CAA9D29F5B5751A94A179328AAF7CC6F | SHA256:76892D1A377BF7A010D77E3C7B26E42369BA12AD066C3DB71F05E361343E9AED | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Feeds Cache\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3720 | MC5 Trainer v5.5.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9524.tmp\extracted\DotNetDataCollector64.exe | executable | |
MD5:8D59B498EB8311EDD5C29F3930F4789B | SHA256:D26EA9B41F172C146633D2E4FAC8C50A4B0C6BB343A37CF5FB3C17598BB49971 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 195.20.34.135:80 | http://kobra.gq/ | NL | — | — | suspicious |
— | — | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 195.20.34.135:80 | kobra.gq | Verotel International B.V. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
kobra.gq |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
Process | Message |
|---|---|
MC5 Trainer v5.5.EXE | sizeof fxstate = 512 |
MC5 Trainer v5.5.EXE | sizeof fxstate = 512 |
MC5 Trainer v5.5.EXE | TSymhandler.create |
MC5 Trainer v5.5.EXE | TSymhandler.create 1 |
MC5 Trainer v5.5.EXE | TSymhandler.create 2 |
MC5 Trainer v5.5.EXE | TSymhandler.create 3 |
MC5 Trainer v5.5.EXE | TSymbolListHandler.create 1 |
MC5 Trainer v5.5.EXE | TSymbolListHandler.create 2 |
MC5 Trainer v5.5.EXE | TSymbolListHandler.create exit |
MC5 Trainer v5.5.EXE | TSymhandler.create exit |