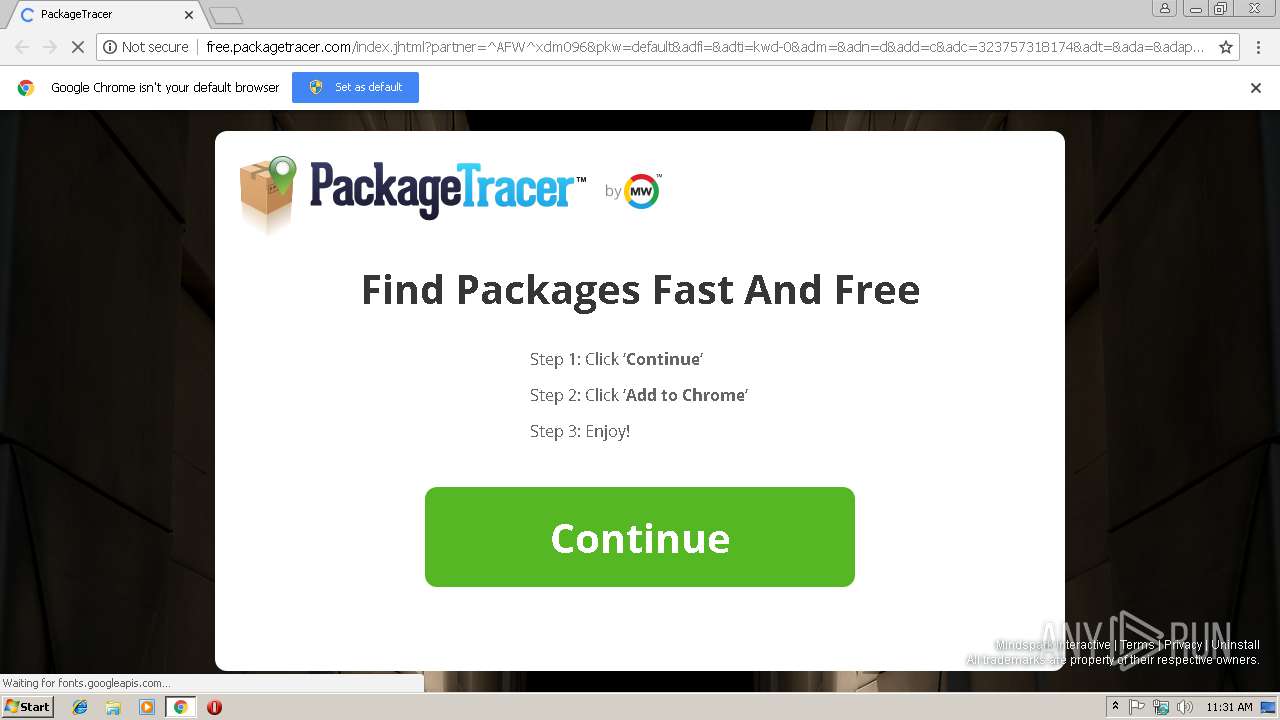
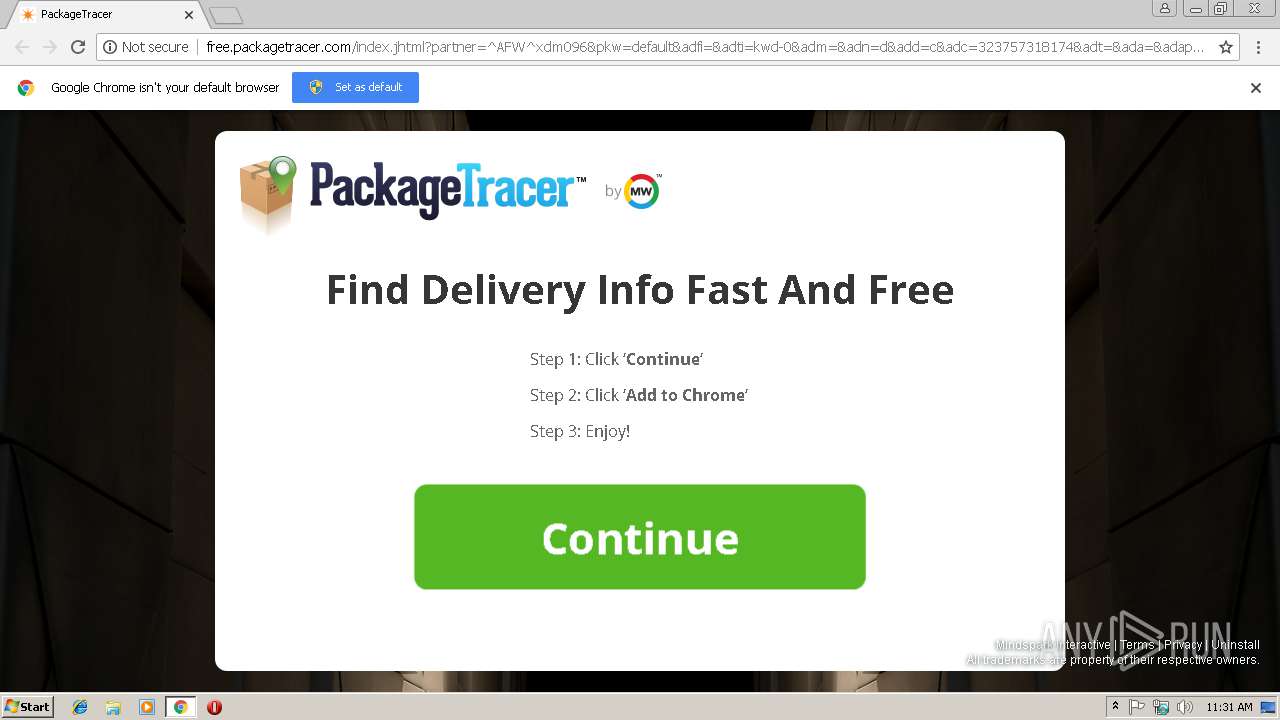
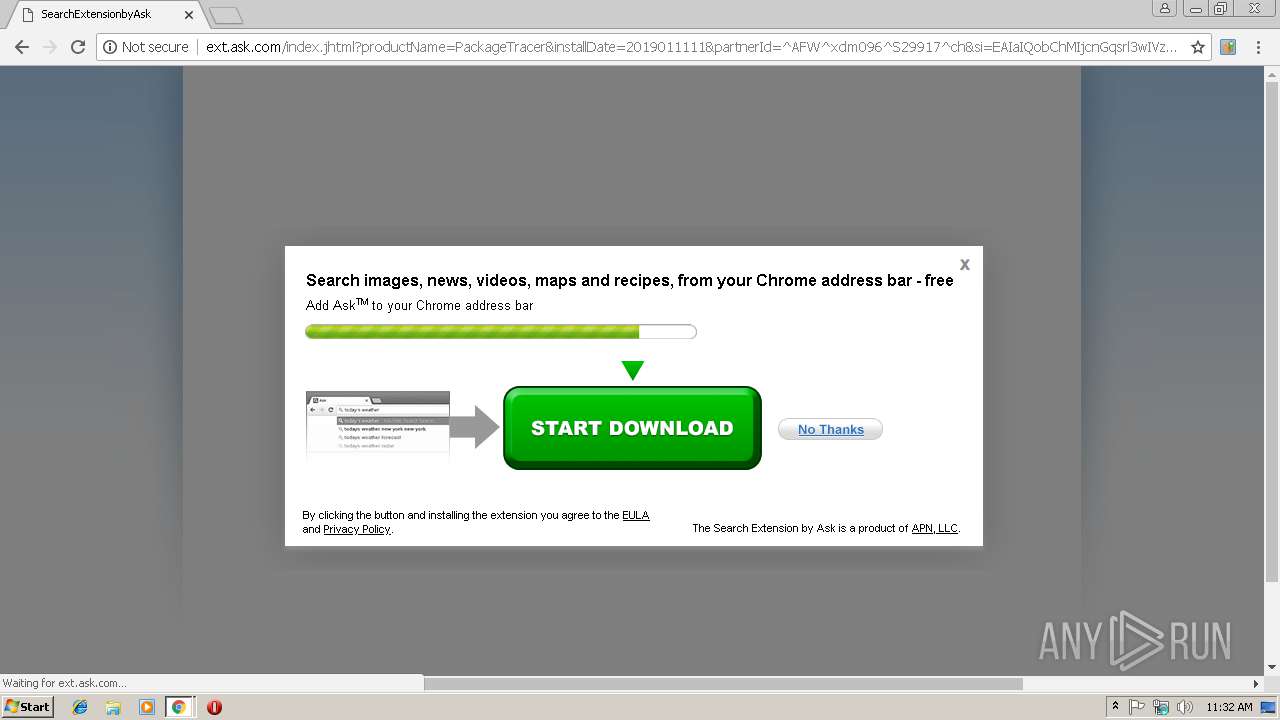
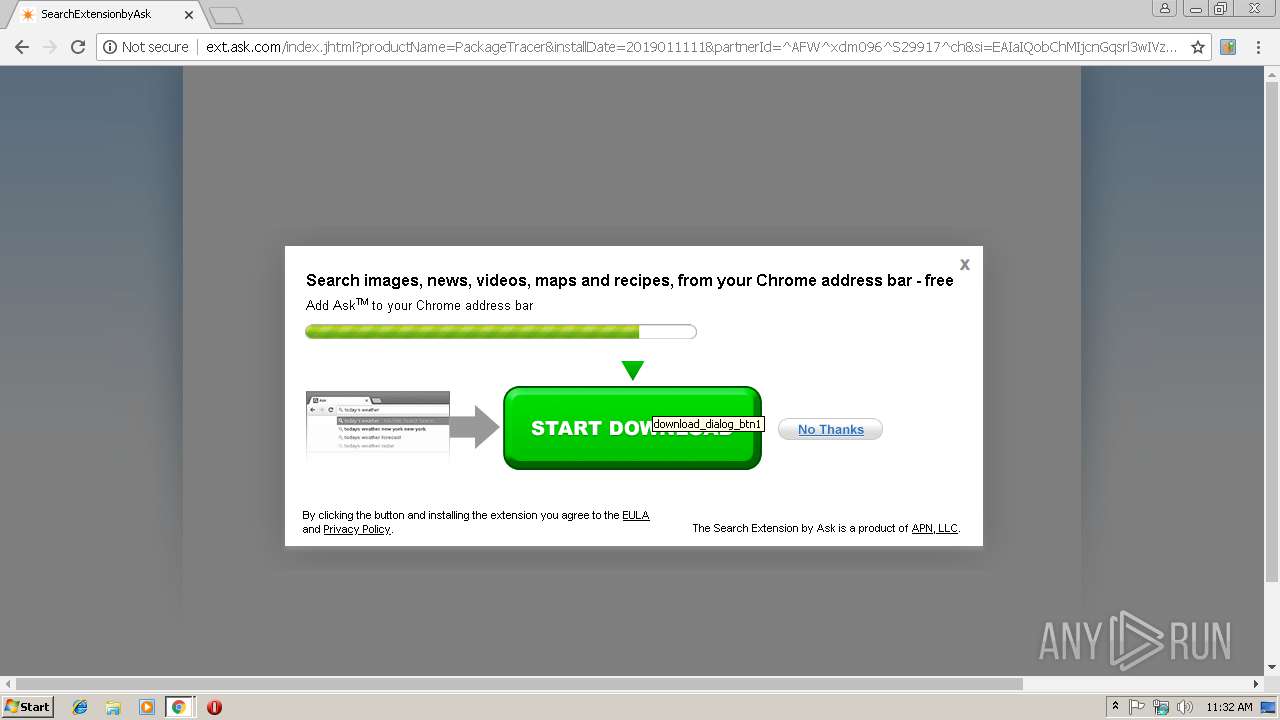
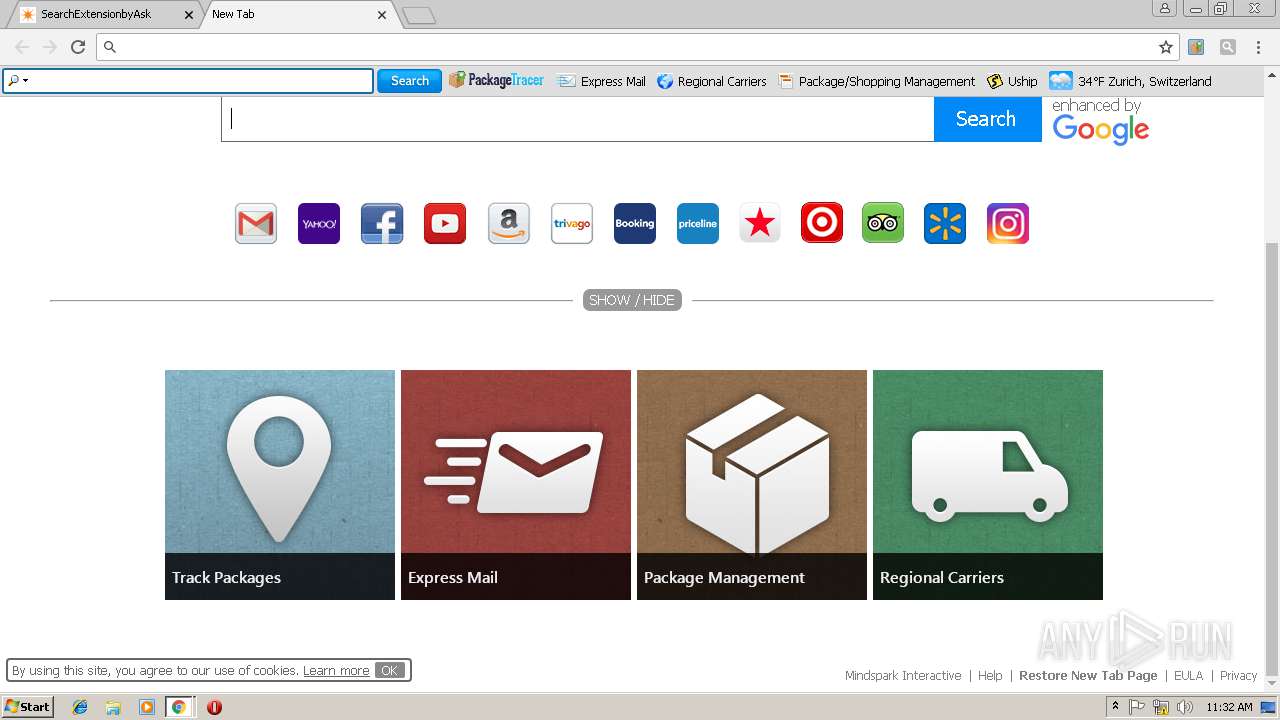
| URL: | http://free.packagetracer.com/index.jhtml?partner=^AFW^xdm096&pkw=default&adfi=&adti=kwd-0&adm=&adn=d&add=c&adc=323757318174&adt=&ada=&adap=none&adp=www.sejda.com&gclid=EAIaIQobChMIjcnGqsrl3wIVzoVoCh0Lqg5QEAEYASAAEgLqr_D_BwE |
| Full analysis: | https://app.any.run/tasks/de1d0809-5004-4e3a-8e83-778490b616dc |
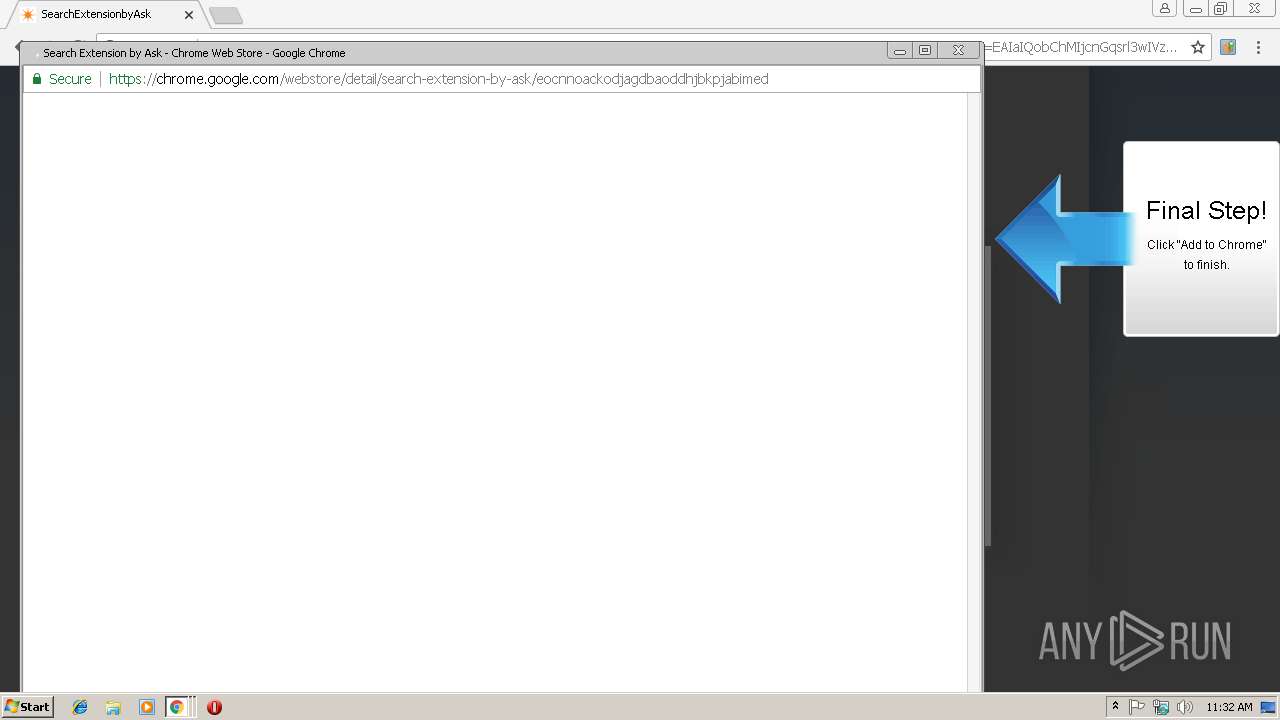
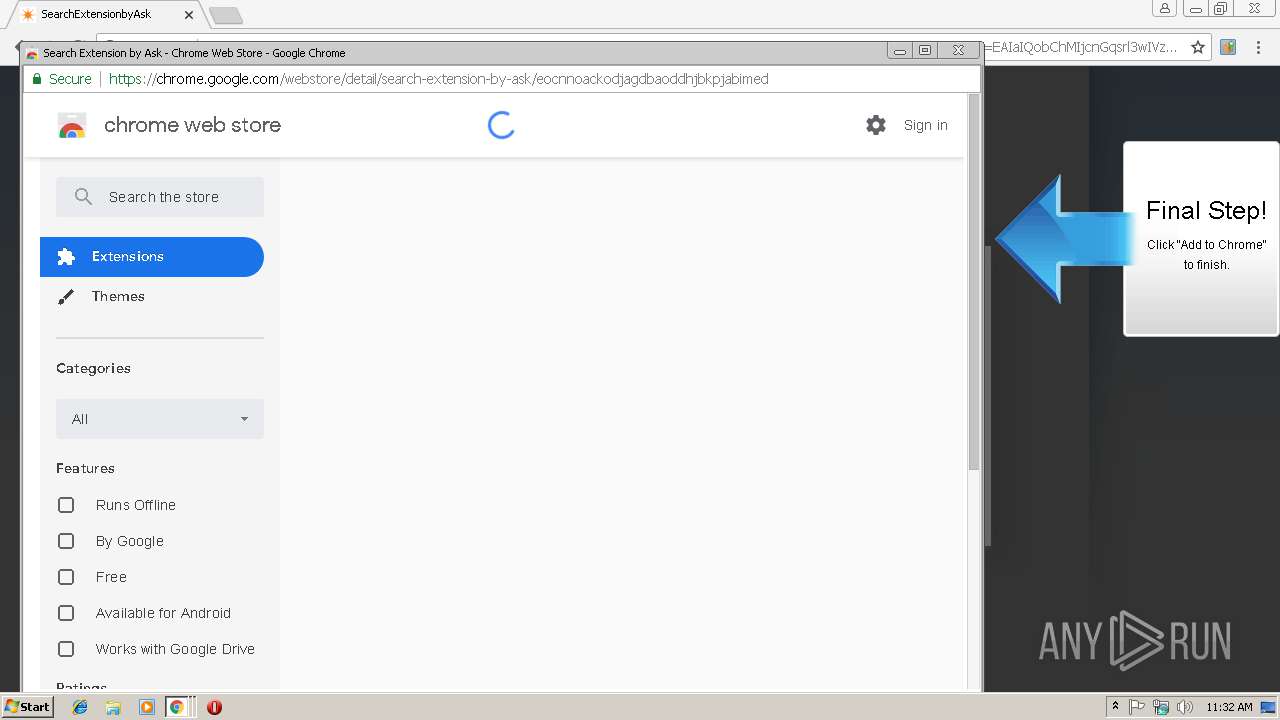
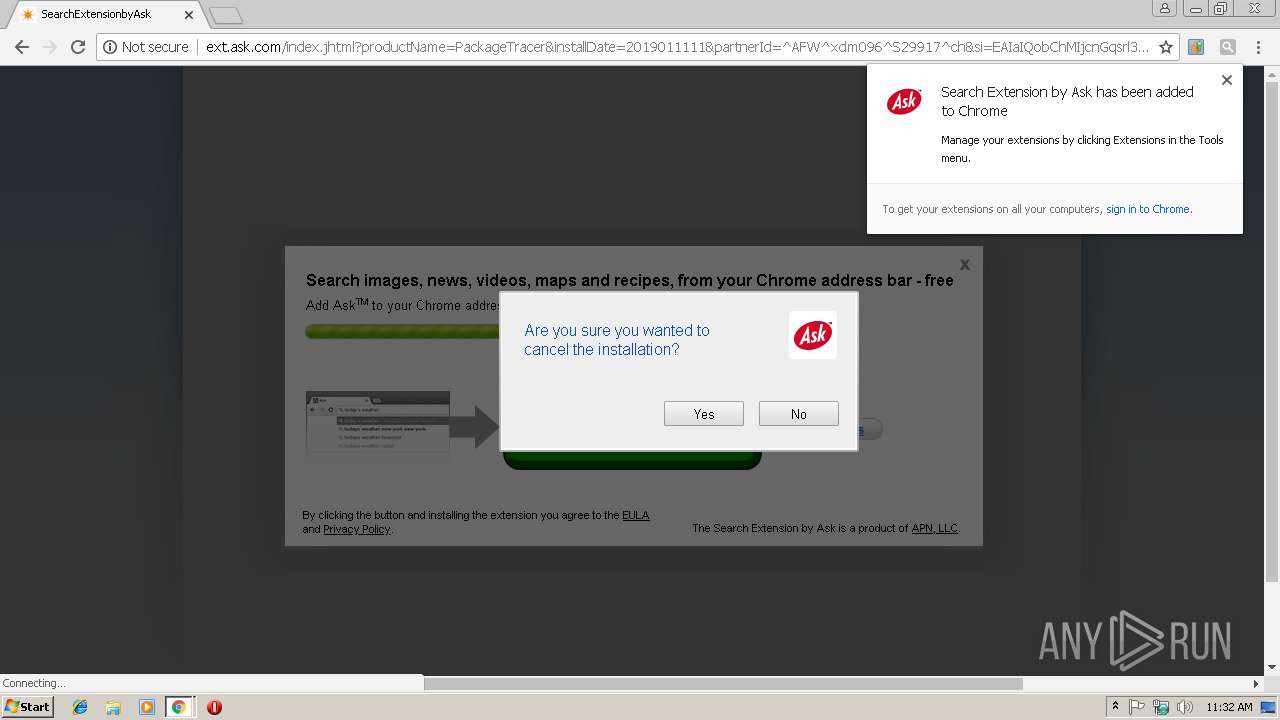
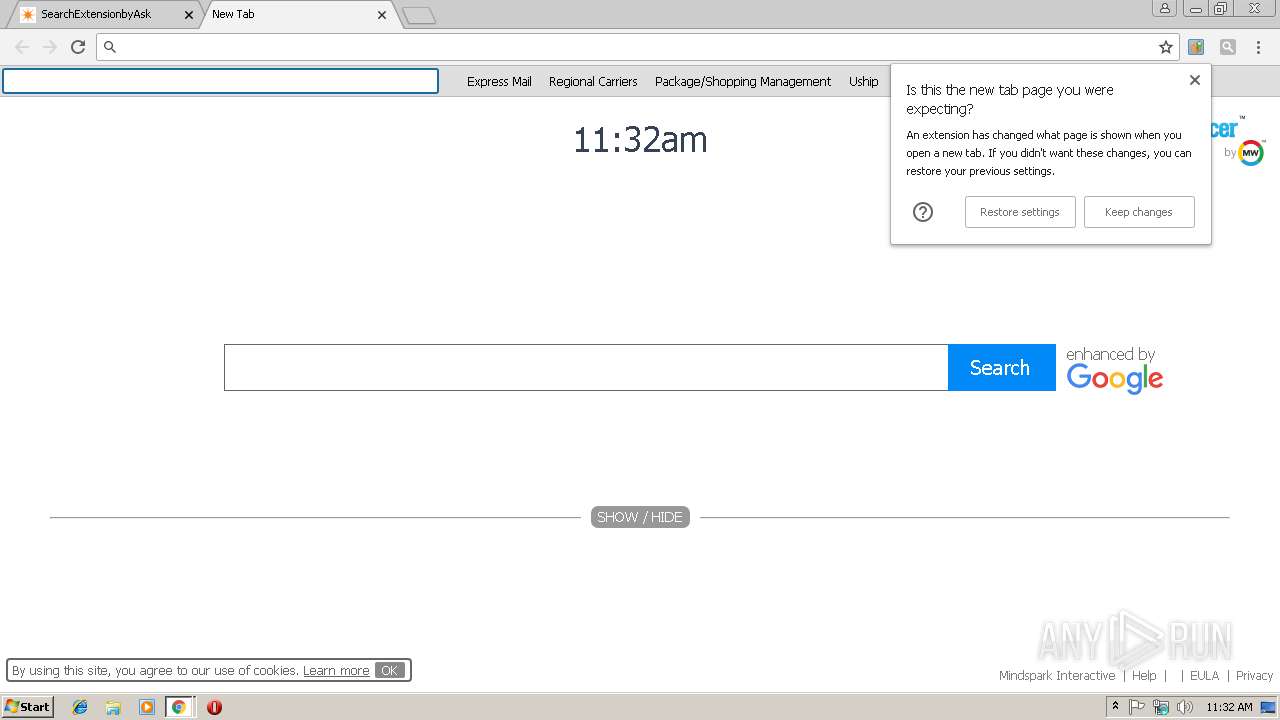
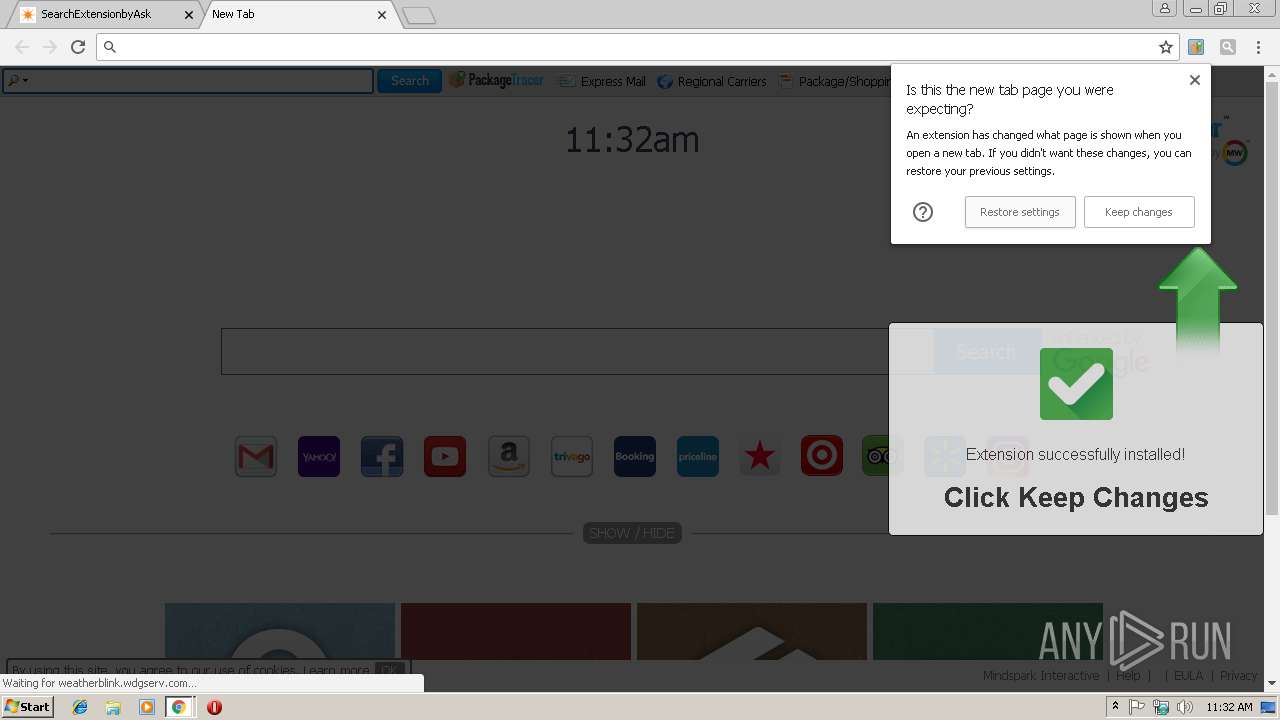
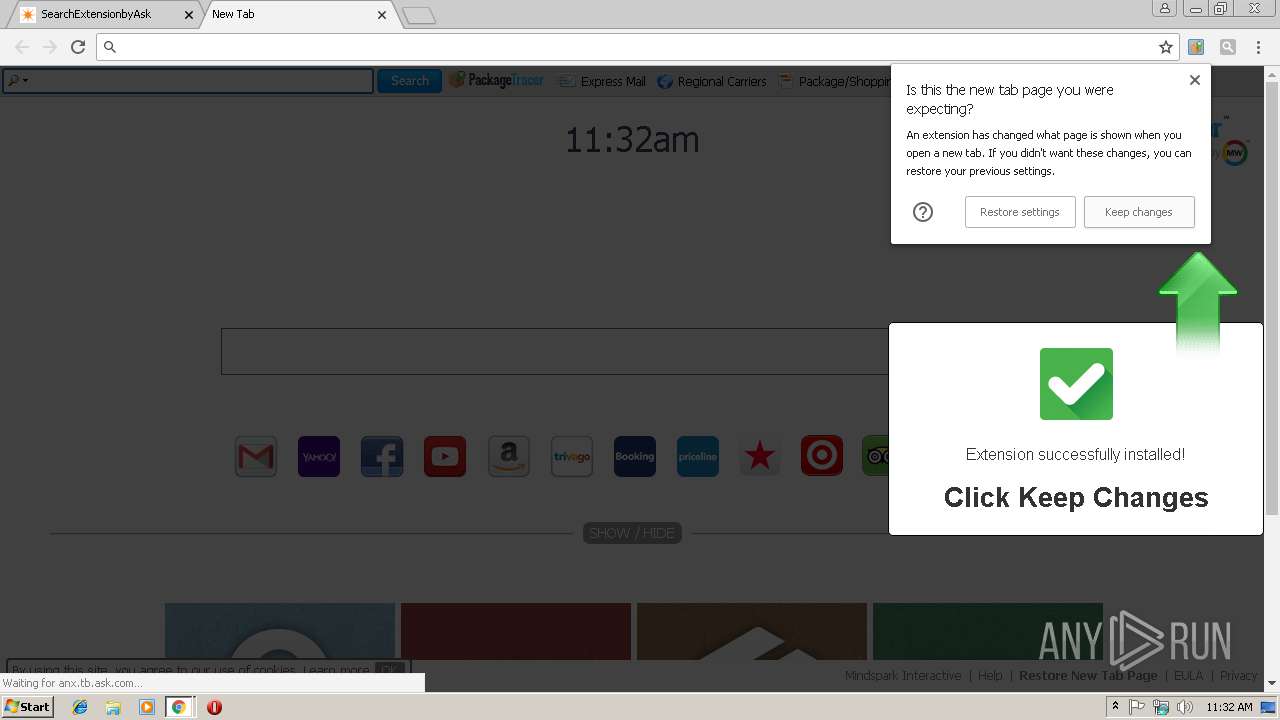
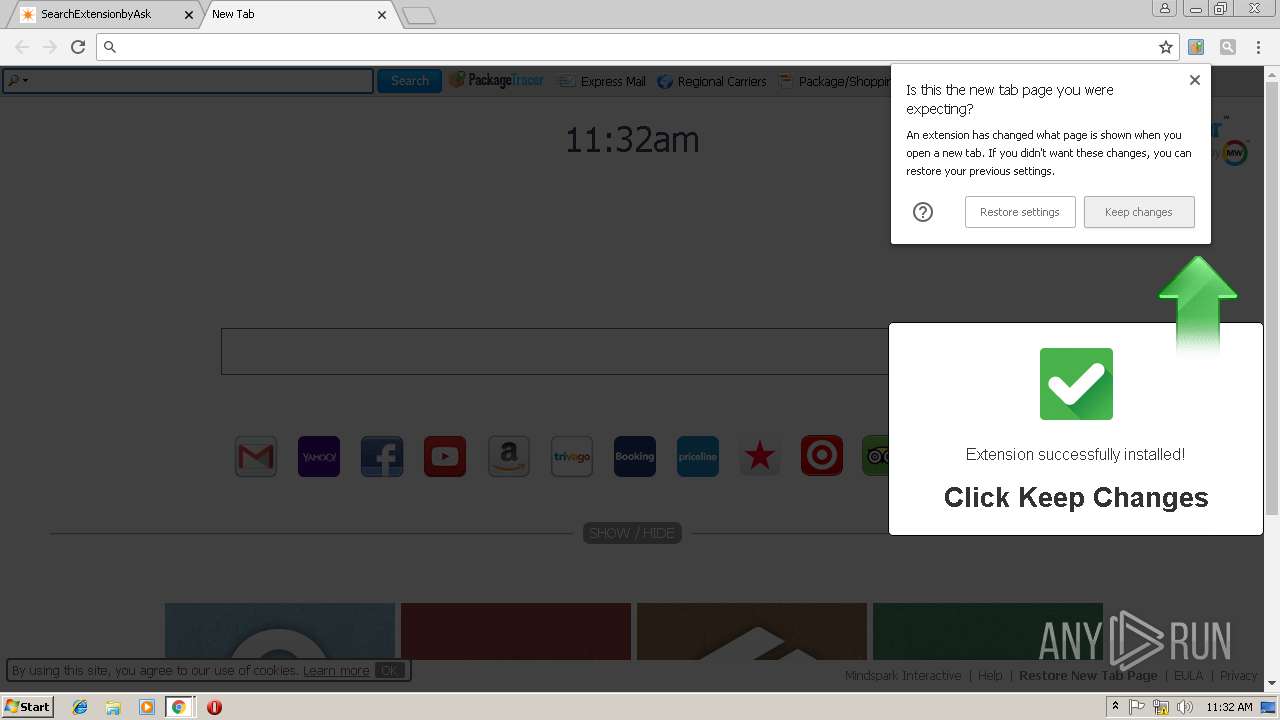
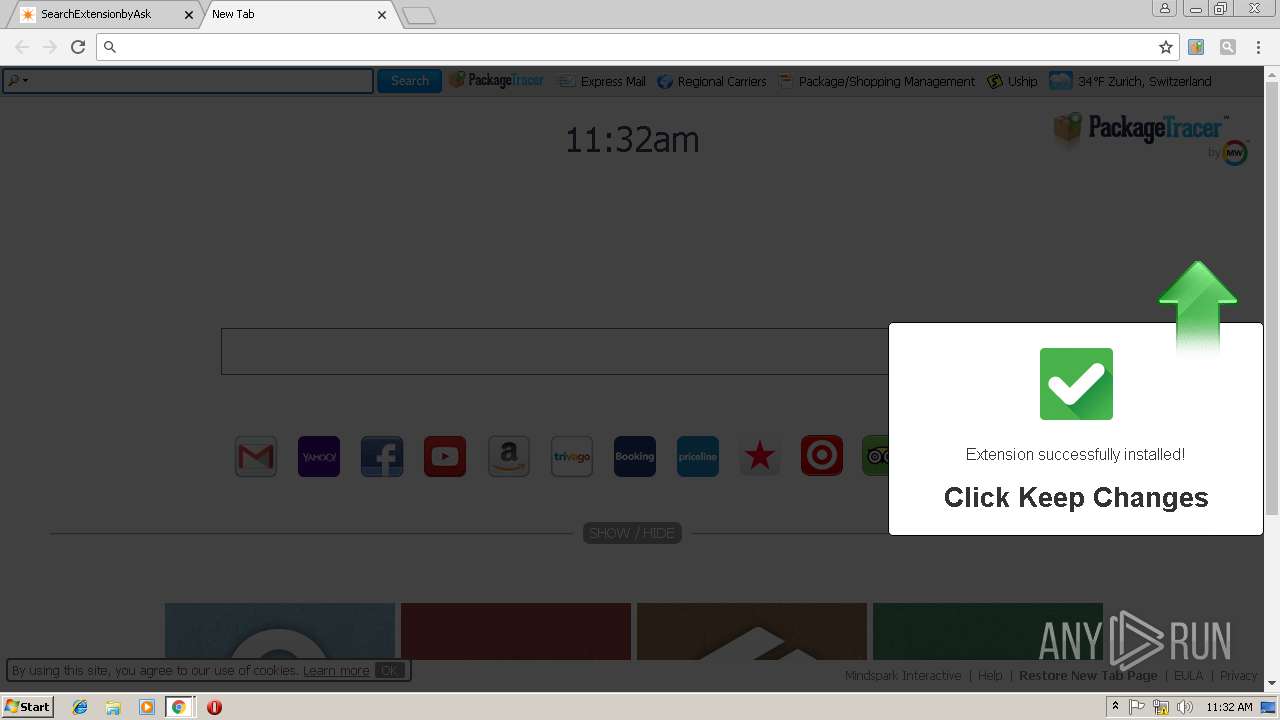
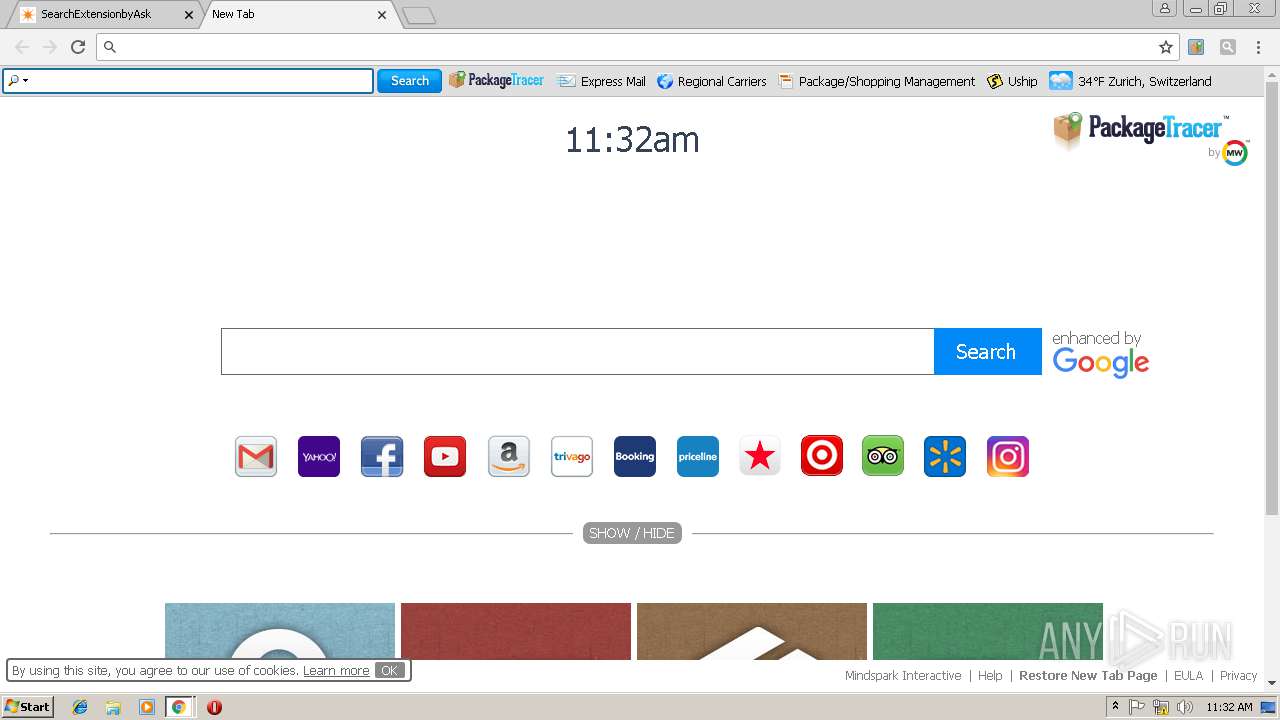
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 11:31:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8CF11F07E7E8646DE1F776FE262C12A1 |
| SHA1: | 36DC127BD36303099CEF154497B189E078CF3819 |
| SHA256: | 9F88178EEA86BCE2D635448AA3C835F8A650D3F8E89CDE5EB3FE1FFDD5050741 |
| SSDEEP: | 6:CYrrNUGYKaBUUuXPdBJn4yY9sgH6lGuEGmhNp+LYfaN/1Tg:Nr6KahuXPdBJ4y9gH6hcxfaN5g |
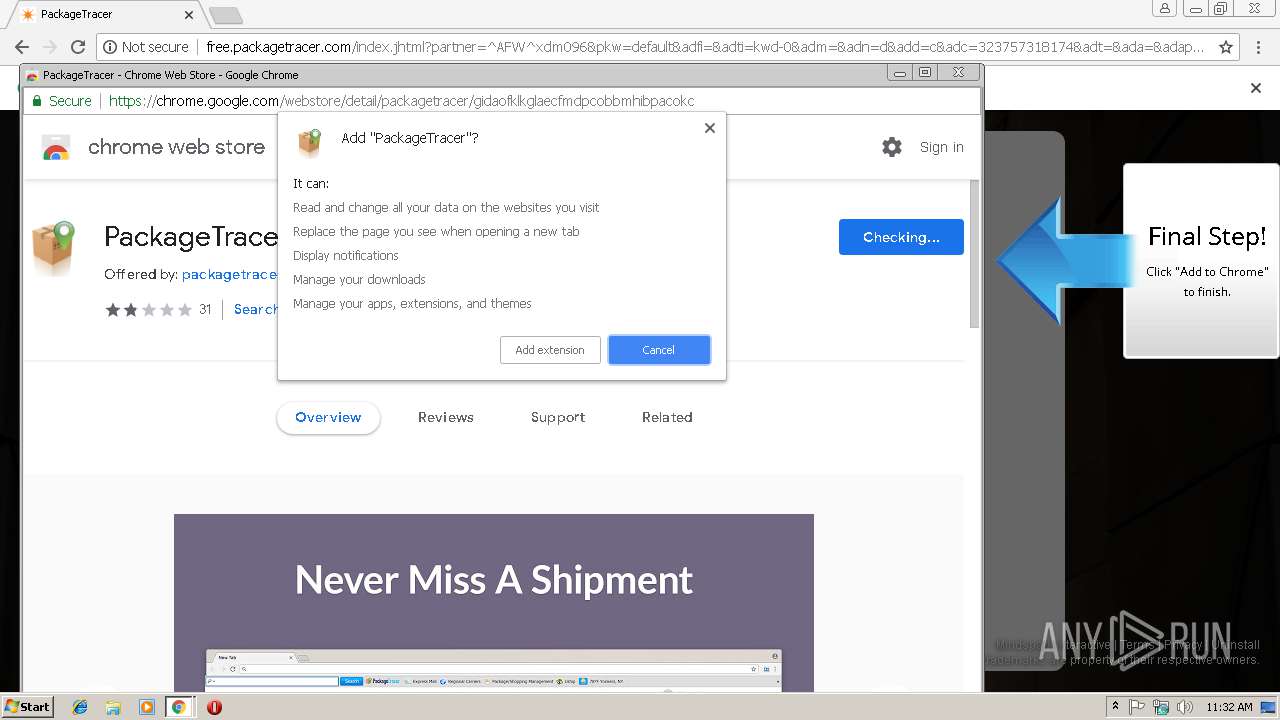
MALICIOUS
No malicious indicators.SUSPICIOUS
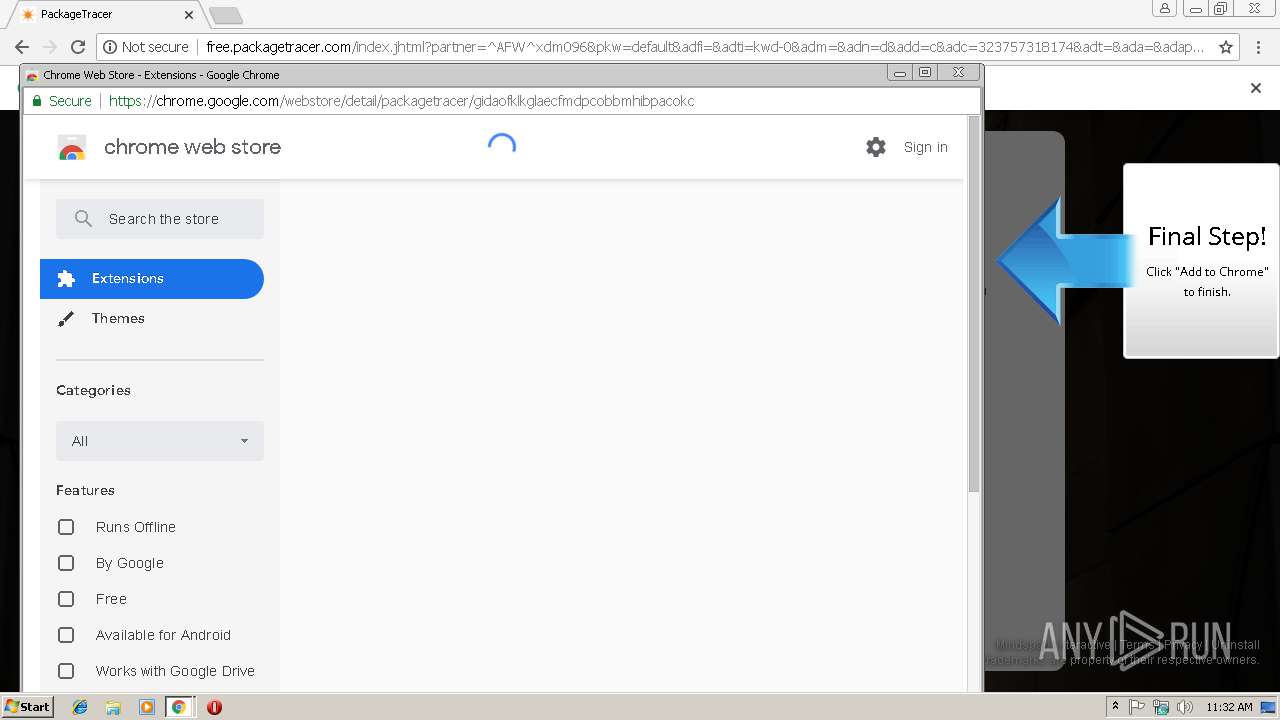
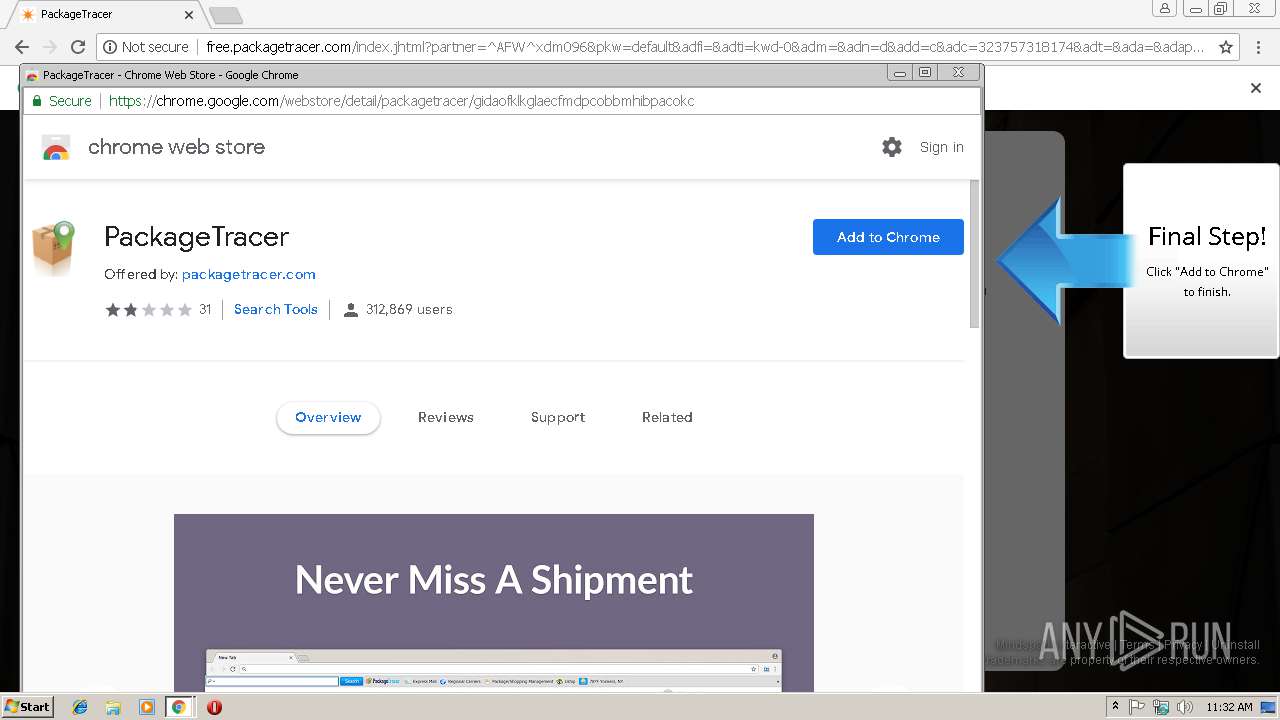
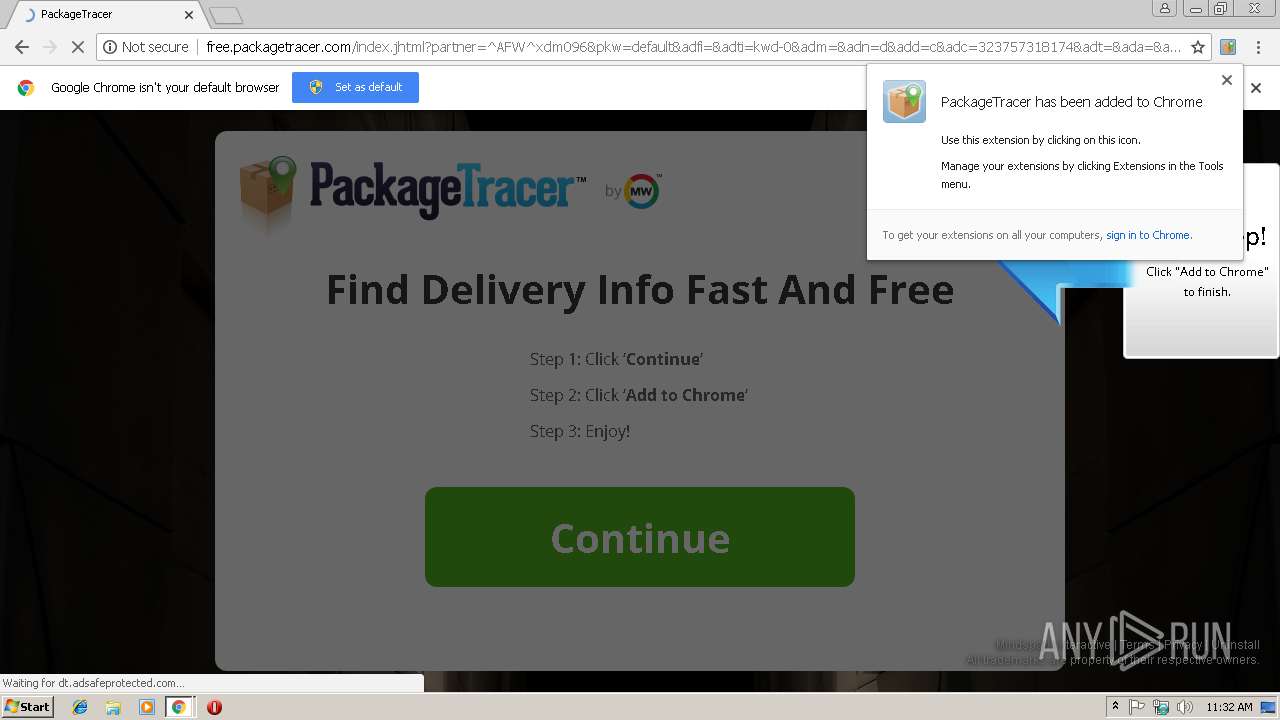
Modifies files in Chrome extension folder
- chrome.exe (PID: 2876)
INFO
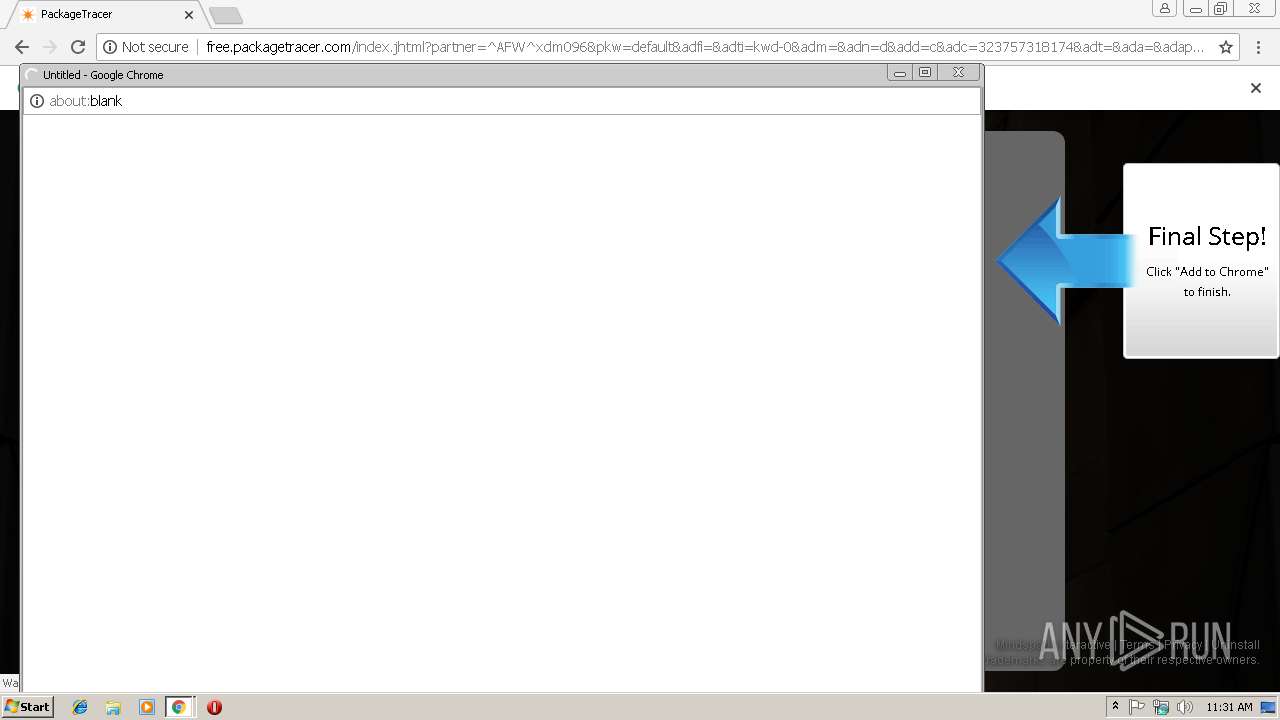
Application launched itself
- chrome.exe (PID: 2876)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2876)
Reads settings of System Certificates
- chrome.exe (PID: 2876)
Reads Internet Cache Settings
- chrome.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
32
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=94A8CF984C7E8DBDD5ABBDEAB8C52BF5 --mojo-platform-channel-handle=6096 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D671C63E4E581707ED42B4434E249087 --mojo-platform-channel-handle=3840 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7A21705F2805C9B82A028B93C228C78F --mojo-platform-channel-handle=5300 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=70ECCD4D85175859762E9932349F0A49 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=70ECCD4D85175859762E9932349F0A49 --renderer-client-id=7 --mojo-platform-channel-handle=4016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=EA6F28BC7BC4669481400703424E3AB7 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=EA6F28BC7BC4669481400703424E3AB7 --renderer-client-id=28 --mojo-platform-channel-handle=6276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=FCFD5431C7334B24A7654C4BF27B59E0 --mojo-platform-channel-handle=4300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0DB00C3224C4222B1E7B843CA7563DF7 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0DB00C3224C4222B1E7B843CA7563DF7 --renderer-client-id=26 --mojo-platform-channel-handle=4820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8C744F3B2E2776B844668D64B65739B2 --mojo-platform-channel-handle=5744 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=503030840B2A23C44802639FB795348A --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=503030840B2A23C44802639FB795348A --renderer-client-id=15 --mojo-platform-channel-handle=5300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
687
Read events
582
Write events
100
Delete events
5
Modification events
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2876-13191679894034750 |
Value: 259 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
162
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198c38.TMP | — | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\74802bb0-60c3-48cc-b75f-0942b928756a.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e25be6ea-76d3-41b2-bdc2-456902fdc345.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model~RF199001.TMP | binary | |
MD5:— | SHA256:— | |||
| 2876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
119
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2876 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://free.packagetracer.com/anemone.jhtml?anxuu=B2916FB8-259F-4887-B966-B3959F3BD3BD&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe15.dub.jabodo.com&anxu=http%3A%2F%2Ffree.packagetracer.com%2Findex.jhtml&anxl=en-US&anxlv=1547206296322&anxsq=3&present=false&anxe=ToolbarDetect&anxr=587197709 | IE | — | — | whitelisted |
2876 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://free.packagetracer.com/anemone.jhtml?anxuu=B2916FB8-259F-4887-B966-B3959F3BD3BD&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe15.dub.jabodo.com&anxu=http%3A%2F%2Ffree.packagetracer.com%2Findex.jhtml&anxl=en-US&anxlv=1547206296347&anxsq=4&page=SplashPage&action=userconnection&downLink=1.55&effectiveType=4g&anxe=DLPInfo&anxr=302230856 | IE | — | — | whitelisted |
2876 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://free.packagetracer.com/anemone.jhtml?anxuu=B2916FB8-259F-4887-B966-B3959F3BD3BD&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe15.dub.jabodo.com&anxu=http%3A%2F%2Ffree.packagetracer.com%2Findex.jhtml&anxl=en-US&anxlv=1547206297670&anxsq=6&label=download_main_btn1&type=INPUT&anxe=UIControl&anxr=249811768 | IE | — | — | whitelisted |
2876 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://free.packagetracer.com/anemone.jhtml?anxuu=B2916FB8-259F-4887-B966-B3959F3BD3BD&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe15.dub.jabodo.com&anxu=http%3A%2F%2Ffree.packagetracer.com%2Findex.jhtml&anxl=en-US&anxlv=1547206318818&anxsq=7&anxe=SplashLandingClicked&anxr=1655569452 | IE | — | — | whitelisted |
2876 | chrome.exe | GET | 200 | 74.113.235.138:80 | http://packagetracer.dl.myway.com/localStorage.jhtml | IE | html | 2.20 Kb | whitelisted |
2876 | chrome.exe | GET | 200 | 74.113.235.138:80 | http://free.packagetracer.com/index.jhtml?partner=^AFW^xdm096&pkw=default&adfi=&adti=kwd-0&adm=&adn=d&add=c&adc=323757318174&adt=&ada=&adap=none&adp=www.sejda.com&gclid=EAIaIQobChMIjcnGqsrl3wIVzoVoCh0Lqg5QEAEYASAAEgLqr_D_BwE | IE | html | 43.5 Kb | whitelisted |
2876 | chrome.exe | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/ttdetect-2/prd/ttDetectUtil.js | unknown | text | 3.81 Kb | whitelisted |
2876 | chrome.exe | GET | 200 | 74.113.235.138:80 | http://packagetracer.dl.tb.ask.com/localStorage.jhtml | IE | html | 2.20 Kb | whitelisted |
2876 | chrome.exe | GET | 200 | 2.18.232.251:80 | http://ak.imgfarm.com/images/download/symantec/nortonseal.gif | unknown | image | 2.83 Kb | whitelisted |
2876 | chrome.exe | GET | 204 | 74.113.235.138:80 | http://free.packagetracer.com/anemone.jhtml?anxuu=B2916FB8-259F-4887-B966-B3959F3BD3BD&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe15.dub.jabodo.com&anxu=http%3A%2F%2Ffree.packagetracer.com%2Findex.jhtml&anxl=en-US&anxlv=1547206296306&anxrd=none&anxrp=-&anxrk=-&anxrm=-&anxrb=-&anxrc=-&anxrs=-&anxsq=1&anxi=29D802AA-DFC7-4D2C-96AB-9E79F7558D61&anxe=backFill&anxr=752657607 | IE | compressed | 43.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
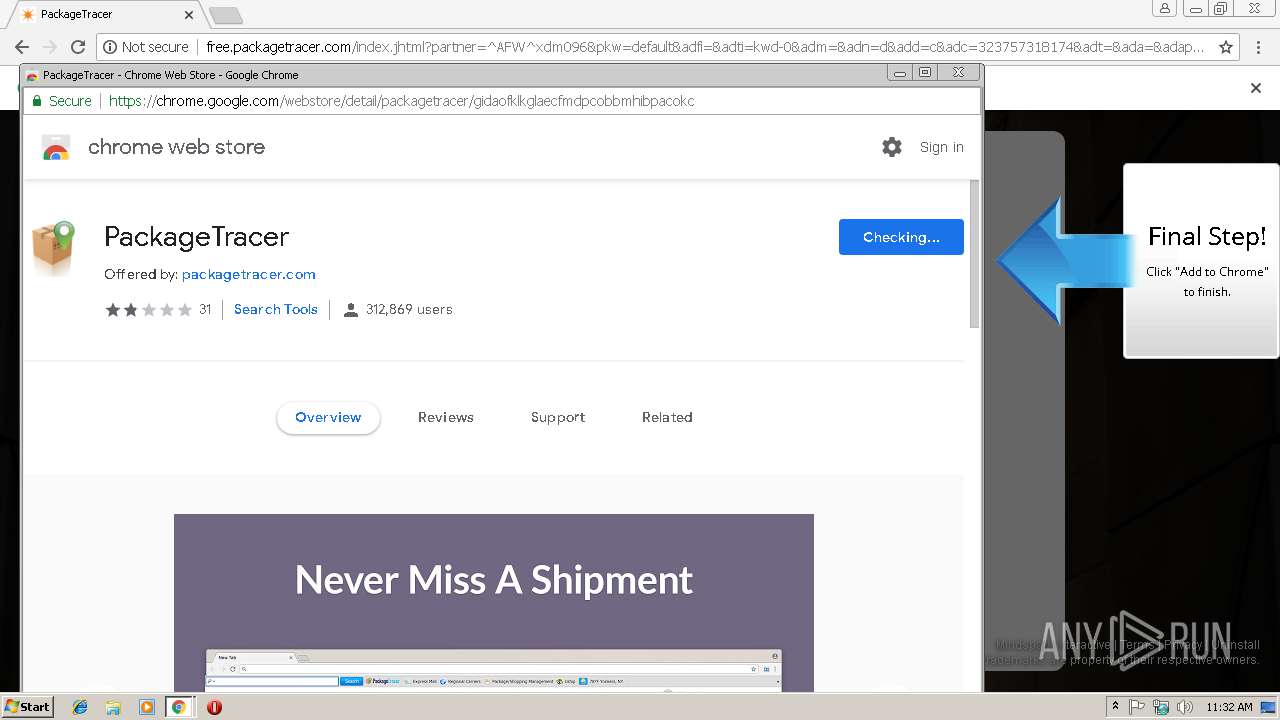
2876 | chrome.exe | 74.113.235.138:80 | free.packagetracer.com | Mindspark Interactive Network, Inc. | IE | malicious |
2876 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2876 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2876 | chrome.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2876 | chrome.exe | 2.18.232.251:80 | ak.staticimgfarm.com | Akamai International B.V. | — | whitelisted |
2876 | chrome.exe | 2.18.232.251:443 | ak.staticimgfarm.com | Akamai International B.V. | — | whitelisted |
2876 | chrome.exe | 54.194.184.41:80 | insight.adsrvr.org | Amazon.com, Inc. | IE | unknown |
2876 | chrome.exe | 69.172.216.55:443 | pixel.adsafeprotected.com | Integral Ad Science, Inc. | US | unknown |
2876 | chrome.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2876 | chrome.exe | 172.217.16.130:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
free.packagetracer.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
packagetracer.dl.tb.ask.com |
| whitelisted |