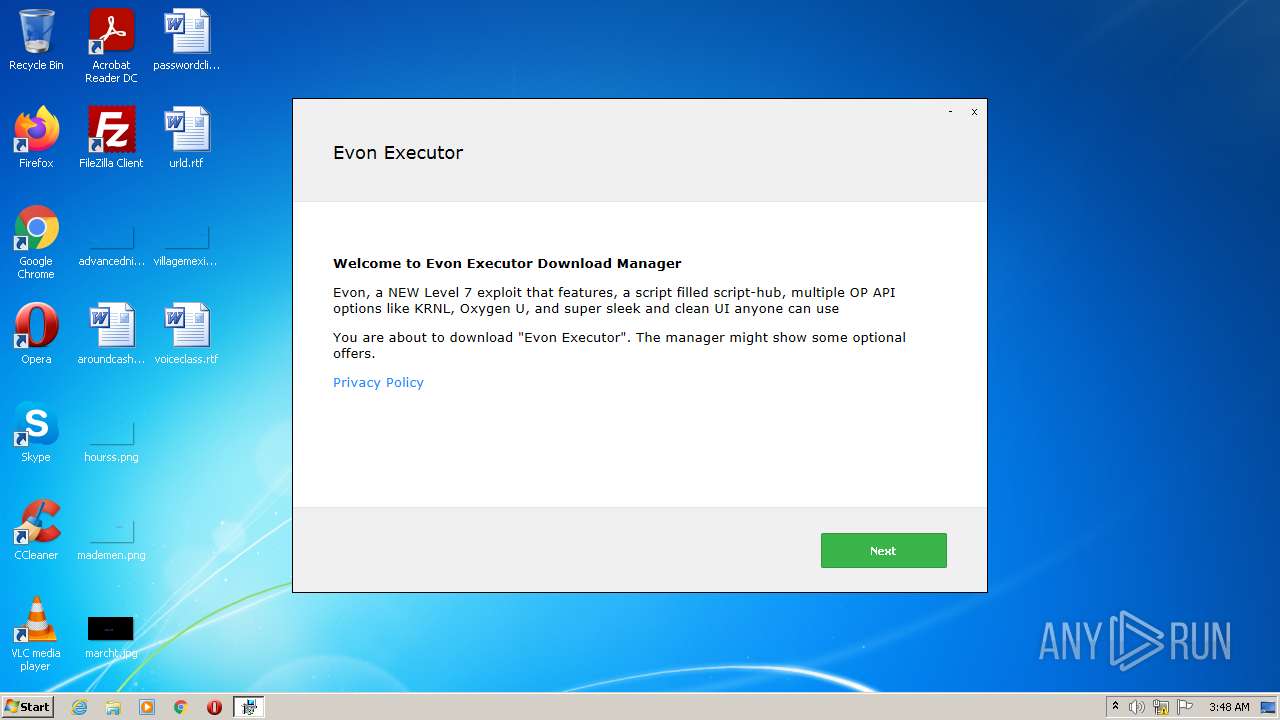
| File name: | Evon Executor_53841.exe |
| Full analysis: | https://app.any.run/tasks/c3f6075b-0b0a-466d-aa92-f3f83e13f219 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 03:47:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A15D8D3F50D25693F25FF8952C96EEC1 |
| SHA1: | B0D3C337F168A846EB17E0F44FB275F9941FD07C |
| SHA256: | 9F63A5E0E356E5F18940C01FDC5FA76CF0046A162E65B36B0D563CFE08035D40 |
| SSDEEP: | 196608:qQGQ4YVKf6i1GgJwrqNtr7G5RCrUL0n2mw:HN4co6RgJwrqN05GW0nP |
MALICIOUS
Application was dropped or rewritten from another process
- setup53841.exe (PID: 3908)
- GenericSetup.exe (PID: 3276)
- GenericSetup.exe (PID: 3968)
- setup53841.exe (PID: 3492)
Changes settings of System certificates
- GenericSetup.exe (PID: 3968)
Actions looks like stealing of personal data
- GenericSetup.exe (PID: 3968)
Loads dropped or rewritten executable
- GenericSetup.exe (PID: 3968)
- GenericSetup.exe (PID: 3276)
Drops executable file immediately after starts
- setup53841.exe (PID: 3908)
- setup53841.exe (PID: 3492)
SUSPICIOUS
Reads the computer name
- Evon Executor_53841.exe (PID: 3784)
- GenericSetup.exe (PID: 3968)
- GenericSetup.exe (PID: 3276)
Checks supported languages
- Evon Executor_53841.exe (PID: 3784)
- setup53841.exe (PID: 3908)
- GenericSetup.exe (PID: 3968)
- GenericSetup.exe (PID: 3276)
- setup53841.exe (PID: 3492)
Executable content was dropped or overwritten
- Evon Executor_53841.exe (PID: 3784)
- setup53841.exe (PID: 3908)
- setup53841.exe (PID: 3492)
Drops a file with a compile date too recent
- Evon Executor_53841.exe (PID: 3784)
- setup53841.exe (PID: 3908)
- setup53841.exe (PID: 3492)
Drops a file with too old compile date
- setup53841.exe (PID: 3908)
- setup53841.exe (PID: 3492)
Reads Environment values
- GenericSetup.exe (PID: 3968)
Reads Windows owner or organization settings
- GenericSetup.exe (PID: 3968)
Adds / modifies Windows certificates
- GenericSetup.exe (PID: 3968)
Drops a file that was compiled in debug mode
- setup53841.exe (PID: 3908)
- setup53841.exe (PID: 3492)
Reads the Windows organization settings
- GenericSetup.exe (PID: 3968)
Searches for installed software
- GenericSetup.exe (PID: 3968)
INFO
Reads settings of System Certificates
- Evon Executor_53841.exe (PID: 3784)
- GenericSetup.exe (PID: 3968)
Checks Windows Trust Settings
- Evon Executor_53841.exe (PID: 3784)
- GenericSetup.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x37d2dd |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4481024 |
| CodeSize: | 4227584 |
| LinkerVersion: | 14.22 |
| PEType: | PE32 |
| TimeStamp: | 2021:10:20 22:18:25+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Oct-2021 20:18:25 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Oct-2021 20:18:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0040803B | 0x00408200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63785 |
.rdata | 0x0040A000 | 0x00101A1A | 0x00101C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.59804 |
.data | 0x0050C000 | 0x0002A60C | 0x00023E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.80416 |
.rsrc | 0x00537000 | 0x002CF1F8 | 0x002CF200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.93575 |
.reloc | 0x00807000 | 0x0004A980 | 0x0004AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59482 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04264 | 562 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.73071 | 67624 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 2.77417 | 16936 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.65334 | 9640 | UNKNOWN | Dutch - Netherlands | RT_ICON |
5 | 2.82974 | 4264 | UNKNOWN | Dutch - Netherlands | RT_ICON |
6 | 4.49114 | 1128 | UNKNOWN | Dutch - Netherlands | RT_ICON |
101 | 7.98334 | 2842672 | UNKNOWN | Dutch - Netherlands | RT_RCDATA |
103 | 2.75463 | 90 | UNKNOWN | Dutch - Netherlands | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
44
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3276 | .\GenericSetup.exe hready | C:\Users\admin\AppData\Local\Temp\7zS4AD12264\GenericSetup.exe | — | setup53841.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Software Installation Exit code: 1 Version: 2.0.2.5023 Modules
| |||||||||||||||
| 3492 | C:\Users\admin\AppData\Local\setup53841.exe hready | C:\Users\admin\AppData\Local\setup53841.exe | Evon Executor_53841.exe | ||||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3552 | "C:\Users\admin\AppData\Local\Temp\Evon Executor_53841.exe" | C:\Users\admin\AppData\Local\Temp\Evon Executor_53841.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3784 | "C:\Users\admin\AppData\Local\Temp\Evon Executor_53841.exe" | C:\Users\admin\AppData\Local\Temp\Evon Executor_53841.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3908 | C:\Users\admin\AppData\Local\setup53841.exe hhwnd=459180 hreturntoinstaller hextras=id:8a088045139134a-FR-BCFQA | C:\Users\admin\AppData\Local\setup53841.exe | Evon Executor_53841.exe | ||||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3968 | .\GenericSetup.exe hhwnd=459180 hreturntoinstaller hextras=id:8a088045139134a-FR-BCFQA | C:\Users\admin\AppData\Local\Temp\7zS44F30034\GenericSetup.exe | setup53841.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 2.0.2.5023 Modules
| |||||||||||||||
Total events
17 204
Read events
17 128
Write events
76
Delete events
0
Modification events
| (PID) Process: | (3968) GenericSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) GenericSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) GenericSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) GenericSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3968) GenericSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3968) GenericSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8CF427FD790C3AD166068DE81E57EFBB932272D4 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000004BE2C99196650CF40E5A9392A00AFEB27F000000010000002C000000302A060A2B0601040182370A030406082B0601050507030506082B0601050507030606082B06010505070307090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F0000000100000020000000FDE5F2D9CE2026E1E10064C0A468C9F355B90ACF85BAF5CE6F52D4016837FD940300000001000000140000008CF427FD790C3AD166068DE81E57EFBB932272D41D0000000100000010000000521B5F4582C1DCAAE381B05E37CA2D341400000001000000140000006A72267AD01EEF7DE73B6951D46C8D9F901266AB0B000000010000001800000045006E00740072007500730074002E006E0065007400000062000000010000002000000043DF5774B03E7FEF5FE40D931A7BEDF1BB2E6B42738C4E6D3841103D3AA7F339190000000100000010000000FA46CE7CBB85CFB4310075313A09EE05530000000100000041000000303F3020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C07E000000010000000800000000C001B39667D6012000000001000000420400003082043E30820326A00302010202044A538C28300D06092A864886F70D01010B05003081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D204732301E170D3039303730373137323535345A170D3330313230373137353535345A3081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BA84B672DB9E0C6BE299E93001A776EA32B895411AC9DA614E5872CFFEF68279BF7361060AA527D8B35FD3454E1C72D64E32F2728A0FF78319D06A808000451EB0C7E79ABF1257271CA3682F0A87BD6A6B0E5E65F31C77D5D4858D7021B4B332E78BA2D5863902B1B8D247CEE4C949C43BA7DEFB547D57BEF0E86EC279B23A0B55E250981632135C2F7856C1C294B3F25AE4279A9F24D7C6ECD09B2582E3CCC2C445C58C977A066B2A119FA90A6E483B6FDBD4111942F78F07BFF5535F9C3EF4172CE669AC4E324C6277EAB7E8E5BB34BC198BAE9C51E7B77EB553B13322E56DCF703C1AFAE29B67B683F48DA5AF624C4DE058AC64341203F8B68D946324A4710203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604146A72267AD01EEF7DE73B6951D46C8D9F901266AB300D06092A864886F70D01010B05000382010100799F1D96C6B6793F228D87D3870304606A6B9A2E59897311AC43D1F513FF8D392BC0F2BD4F708CA92FEA17C40B549ED41B9698333CA8AD62A20076AB59696E061D7EC4B9448D98AF12D461DB0A194647F3EBF763C1400540A5D2B7F4B59A36BFA98876880455042B9C877F1A373C7E2DA51AD8D4895ECABDAC3D6CD86DAFD5F3760FCD3B8838229D6C939AC43DBF821B653FA60F5DAAFCE5B215CAB5ADC6BC3DD084E8EA0672B04D393278BF3E119C0BA49D9A21F3F09B0B3078DBC1DC8743FEBC639ACAC5C21CC9C78DFF3B125808E6B63DEC7A2C4EFB8396CE0C3C69875473A473C293FF5110AC155401D8FC05B189A17F74839A49D7DC4E7B8A486F8B45F6 | |||
| (PID) Process: | (3968) GenericSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8CF427FD790C3AD166068DE81E57EFBB932272D4 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800007E000000010000000800000000C001B39667D601530000000100000041000000303F3020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0190000000100000010000000FA46CE7CBB85CFB4310075313A09EE0562000000010000002000000043DF5774B03E7FEF5FE40D931A7BEDF1BB2E6B42738C4E6D3841103D3AA7F3390B000000010000001800000045006E00740072007500730074002E006E006500740000001400000001000000140000006A72267AD01EEF7DE73B6951D46C8D9F901266AB1D0000000100000010000000521B5F4582C1DCAAE381B05E37CA2D340300000001000000140000008CF427FD790C3AD166068DE81E57EFBB932272D40F0000000100000020000000FDE5F2D9CE2026E1E10064C0A468C9F355B90ACF85BAF5CE6F52D4016837FD94090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703087F000000010000002C000000302A060A2B0601040182370A030406082B0601050507030506082B0601050507030606082B060105050703070400000001000000100000004BE2C99196650CF40E5A9392A00AFEB22000000001000000420400003082043E30820326A00302010202044A538C28300D06092A864886F70D01010B05003081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D204732301E170D3039303730373137323535345A170D3330313230373137353535345A3081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BA84B672DB9E0C6BE299E93001A776EA32B895411AC9DA614E5872CFFEF68279BF7361060AA527D8B35FD3454E1C72D64E32F2728A0FF78319D06A808000451EB0C7E79ABF1257271CA3682F0A87BD6A6B0E5E65F31C77D5D4858D7021B4B332E78BA2D5863902B1B8D247CEE4C949C43BA7DEFB547D57BEF0E86EC279B23A0B55E250981632135C2F7856C1C294B3F25AE4279A9F24D7C6ECD09B2582E3CCC2C445C58C977A066B2A119FA90A6E483B6FDBD4111942F78F07BFF5535F9C3EF4172CE669AC4E324C6277EAB7E8E5BB34BC198BAE9C51E7B77EB553B13322E56DCF703C1AFAE29B67B683F48DA5AF624C4DE058AC64341203F8B68D946324A4710203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604146A72267AD01EEF7DE73B6951D46C8D9F901266AB300D06092A864886F70D01010B05000382010100799F1D96C6B6793F228D87D3870304606A6B9A2E59897311AC43D1F513FF8D392BC0F2BD4F708CA92FEA17C40B549ED41B9698333CA8AD62A20076AB59696E061D7EC4B9448D98AF12D461DB0A194647F3EBF763C1400540A5D2B7F4B59A36BFA98876880455042B9C877F1A373C7E2DA51AD8D4895ECABDAC3D6CD86DAFD5F3760FCD3B8838229D6C939AC43DBF821B653FA60F5DAAFCE5B215CAB5ADC6BC3DD084E8EA0672B04D393278BF3E119C0BA49D9A21F3F09B0B3078DBC1DC8743FEBC639ACAC5C21CC9C78DFF3B125808E6B63DEC7A2C4EFB8396CE0C3C69875473A473C293FF5110AC155401D8FC05B189A17F74839A49D7DC4E7B8A486F8B45F6 | |||
| (PID) Process: | (3784) Evon Executor_53841.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3784) Evon Executor_53841.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3784) Evon Executor_53841.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
35
Suspicious files
5
Text files
33
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\InstallingPage.html | html | |
MD5:29F74FBCCB8AE8E707CF96BA40DBFA9A | SHA256:F56BB8FE20B8BE18B877DFE0DD46AD3C717FC44797DB5EC904F1612F815DA120 | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\images\loader.gif | image | |
MD5:2B26F73D382AB69F3914A7D9FDA97B0F | SHA256:A6A0B05B1D5C52303DD3E9E2F9CDA1E688A490FBE84EA0D6E22A051AB6EFD643 | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\BundleConfig.json | binary | |
MD5:21AF643B9796542FE1DDB138E023C380 | SHA256:C111BF07221EE4D2A23710EDEB905DE157C68719E49C61D72770B832AD2EC7E5 | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\images\warning48x48.png | image | |
MD5:D3361CF0D689A1B34D84F483D60BA9C9 | SHA256:56739925AADA73F9489F9A6B72BFAAA92892B27D20F4D221380BA3EAE17F1442 | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\images\logo.png | image | |
MD5:990F9B45069F97D66C33B8CC0D64F8D4 | SHA256:BC58A9327ADD07C26FE55F34DE6B4AF0331DA55623055C06F7C04C73E5A922FA | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\style.css | text | |
MD5:7ACE08D87D4DED12ECA2241616DDDC63 | SHA256:1C4BD3408D3FDDC1EB11A860E9A2F607D00CB4CF09E2AF45DB9E4D3AADFE07E3 | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\OfferPage.html | html | |
MD5:5F29B47126C45D119442AD3B896F74EB | SHA256:4E85074502C0267E04B324CDBB46DF644E040513E94DD13C6625FB2E039C9A3F | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\tis\Log.tis | text | |
MD5:CEF7A21ACF607D44E160EAC5A21BDF67 | SHA256:73ED0BE73F408AB8F15F2DA73C839F86FEF46D0A269607330B28F9564FAE73C7 | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\Resources\tis\Config.tis | text | |
MD5:FB1C09FC31CE983ED99D8913BB9F1474 | SHA256:293959C3F8EBB87BFFE885CE2331F0B40AB5666F9D237BE4791ED4903CE17BF4 | |||
| 3908 | setup53841.exe | C:\Users\admin\AppData\Local\Temp\7zS44F30034\GenericSetup.exe.config | xml | |
MD5:FB0F6EC442C72190B9A27BDFD53563BB | SHA256:99C598E9B85A47F0FBDE66A7FED7EB896A15CA2AF869EBB2007B2A2CE64C14FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
13
DNS requests
8
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3784 | Evon Executor_53841.exe | GET | 200 | 35.190.60.70:80 | http://dlsft.com/callback/info.php?id=53841 | US | text | 211 b | malicious |
3784 | Evon Executor_53841.exe | POST | 200 | 35.190.60.70:80 | http://dlsft.com/callback/?channel=BCFQA&id=53841&action=started | US | compressed | 211 b | malicious |
3784 | Evon Executor_53841.exe | POST | 200 | 35.190.60.70:80 | http://dlsft.com/callback/geo/geo.php | US | text | 18 b | malicious |
3784 | Evon Executor_53841.exe | GET | 200 | 35.190.60.70:80 | http://dlsft.com/callback/offers.php | US | text | 17 b | malicious |
3784 | Evon Executor_53841.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3784 | Evon Executor_53841.exe | GET | 200 | 8.253.204.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fa67b7cec3d78c3d | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3784 | Evon Executor_53841.exe | 35.190.60.70:80 | dlsft.com | Google Inc. | US | whitelisted |
— | — | 35.190.60.70:80 | dlsft.com | Google Inc. | US | whitelisted |
3968 | GenericSetup.exe | 104.18.87.101:443 | flow.lavasoft.com | Cloudflare Inc | US | shared |
3968 | GenericSetup.exe | 104.16.235.79:443 | sos.adaware.com | Cloudflare Inc | US | shared |
3784 | Evon Executor_53841.exe | 188.114.96.22:443 | filedm.com | Cloudflare Inc | US | malicious |
3784 | Evon Executor_53841.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3784 | Evon Executor_53841.exe | 8.253.204.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dlsft.com |
| malicious |
www.google.com |
| malicious |
flow.lavasoft.com |
| whitelisted |
sos.adaware.com |
| whitelisted |
filedm.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
GenericSetup.exe | Error: File not found - genericsetup.wrappers.sciter:console.tis
|
GenericSetup.exe | at sciter:init-script.tis
|
GenericSetup.exe | |
GenericSetup.exe | |
GenericSetup.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|