| File name: | Warblade 1.33.exe |
| Full analysis: | https://app.any.run/tasks/67e5f1aa-b7db-425a-805b-e5e9e8a55101 |
| Verdict: | Malicious activity |
| Analysis date: | June 07, 2024, 21:08:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 57E51C317F240B559FA2A17DFD7FA8DA |
| SHA1: | 2AF7E4997DD922FA00A43B9E89FF9A192E634C88 |
| SHA256: | 9F600958FE7473902738950BB5A599A935230F82DB56CB2265CD22D8F2D17654 |
| SSDEEP: | 98304:OJIHJv8TyaDP0Nlso/WA6zRcrsYFlw4P5O2CRmeJ8WcMpJsd912F+6wufcrCzieQ:0l8LkUIDkZZGYHmd95aOZWKKPxRT |
MALICIOUS
Drops the executable file immediately after the start
- Warblade 1.33.exe (PID: 3992)
- Warblade 1.33.exe (PID: 864)
- Warblade 1.33.tmp (PID: 1116)
SUSPICIOUS
Executable content was dropped or overwritten
- Warblade 1.33.exe (PID: 864)
- Warblade 1.33.tmp (PID: 1116)
- Warblade 1.33.exe (PID: 3992)
Process drops legitimate windows executable
- Warblade 1.33.tmp (PID: 1116)
Reads the Windows owner or organization settings
- Warblade 1.33.tmp (PID: 1116)
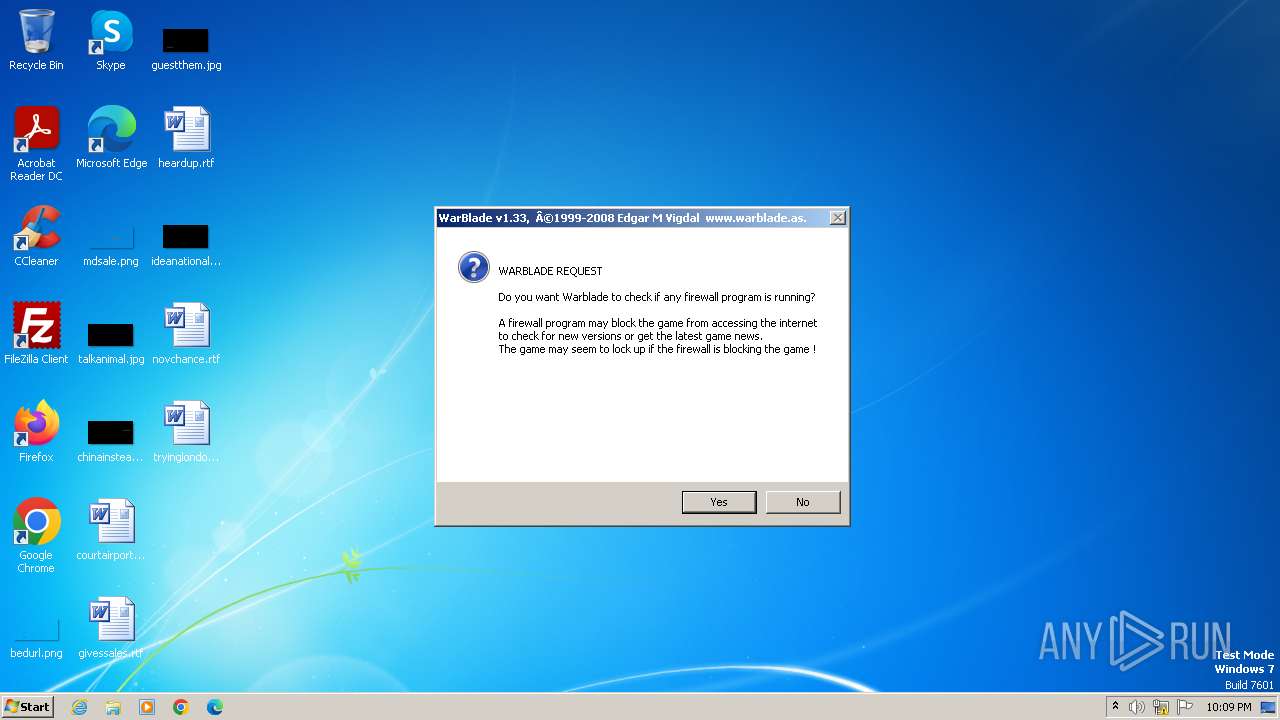
Reads security settings of Internet Explorer
- warblade.exe (PID: 2028)
Reads the Internet Settings
- warblade.exe (PID: 2028)
INFO
Checks supported languages
- Warblade 1.33.exe (PID: 3992)
- Warblade 1.33.exe (PID: 864)
- Warblade 1.33.tmp (PID: 4008)
- Warblade 1.33.tmp (PID: 1116)
- warblade.exe (PID: 2028)
Create files in a temporary directory
- Warblade 1.33.exe (PID: 3992)
- Warblade 1.33.exe (PID: 864)
- Warblade 1.33.tmp (PID: 1116)
Reads the computer name
- Warblade 1.33.tmp (PID: 4008)
- Warblade 1.33.tmp (PID: 1116)
- warblade.exe (PID: 2028)
Creates a software uninstall entry
- Warblade 1.33.tmp (PID: 1116)
Creates files in the program directory
- Warblade 1.33.tmp (PID: 1116)
Reads the machine GUID from the registry
- warblade.exe (PID: 2028)
Checks proxy server information
- warblade.exe (PID: 2028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (60) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (22.7) |
| .exe | | | Win32 Executable Delphi generic (7.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.6) |
| .exe | | | Win32 Executable (generic) (2.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37376 |
| InitializedDataSize: | 19968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9a58 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
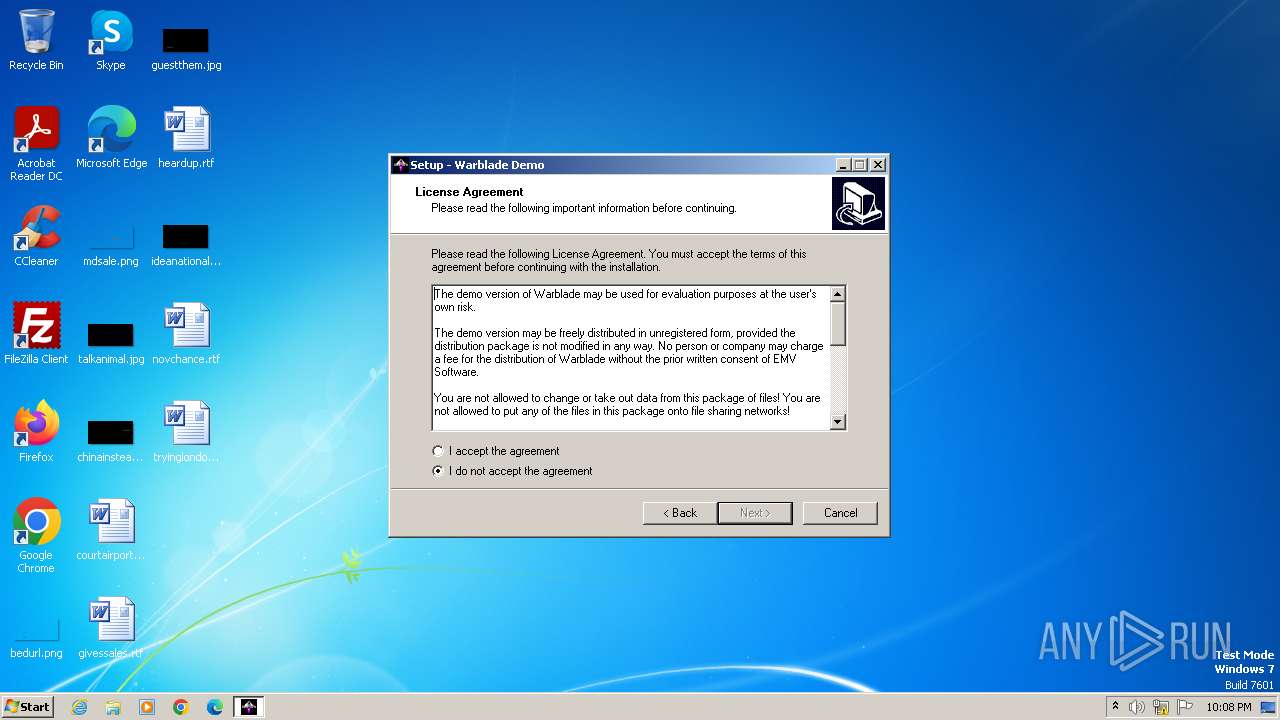
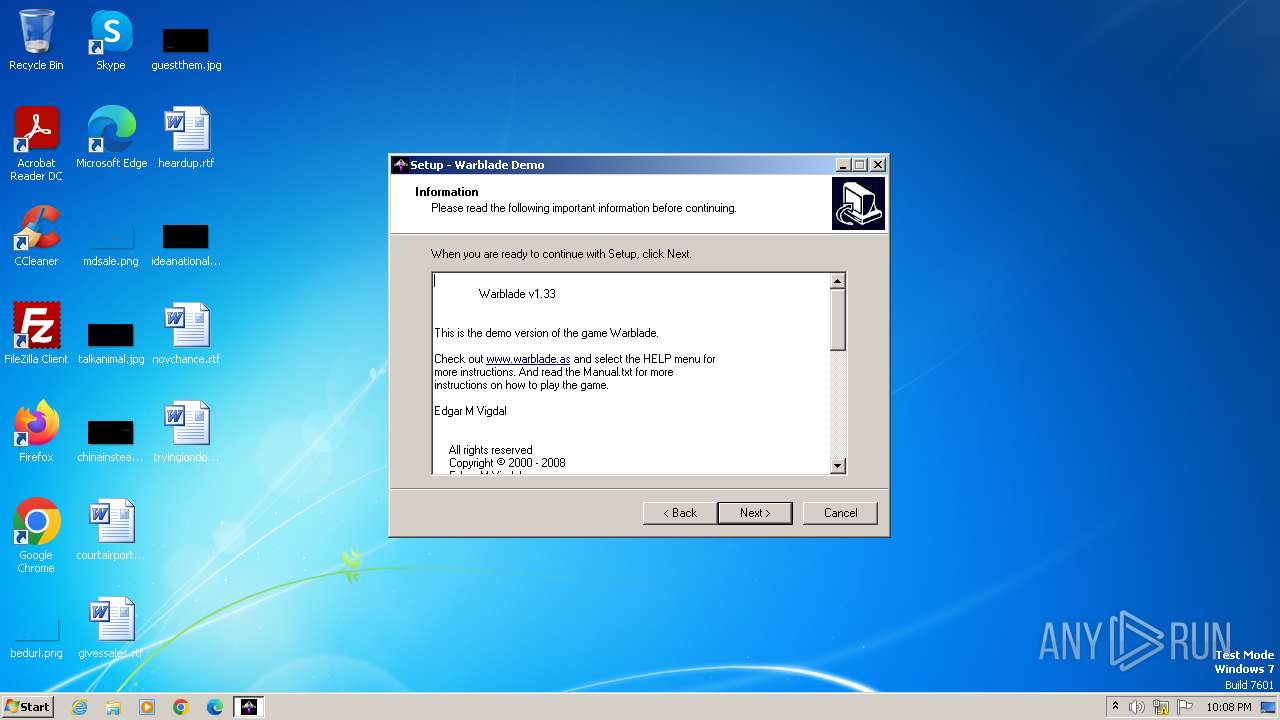
| CompanyName: | EMV Software |
| FileDescription: | Warblade Demo Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Warblade Demo |
| ProductVersion: |
Total processes
40
Monitored processes
5
Malicious processes
4
Suspicious processes
1
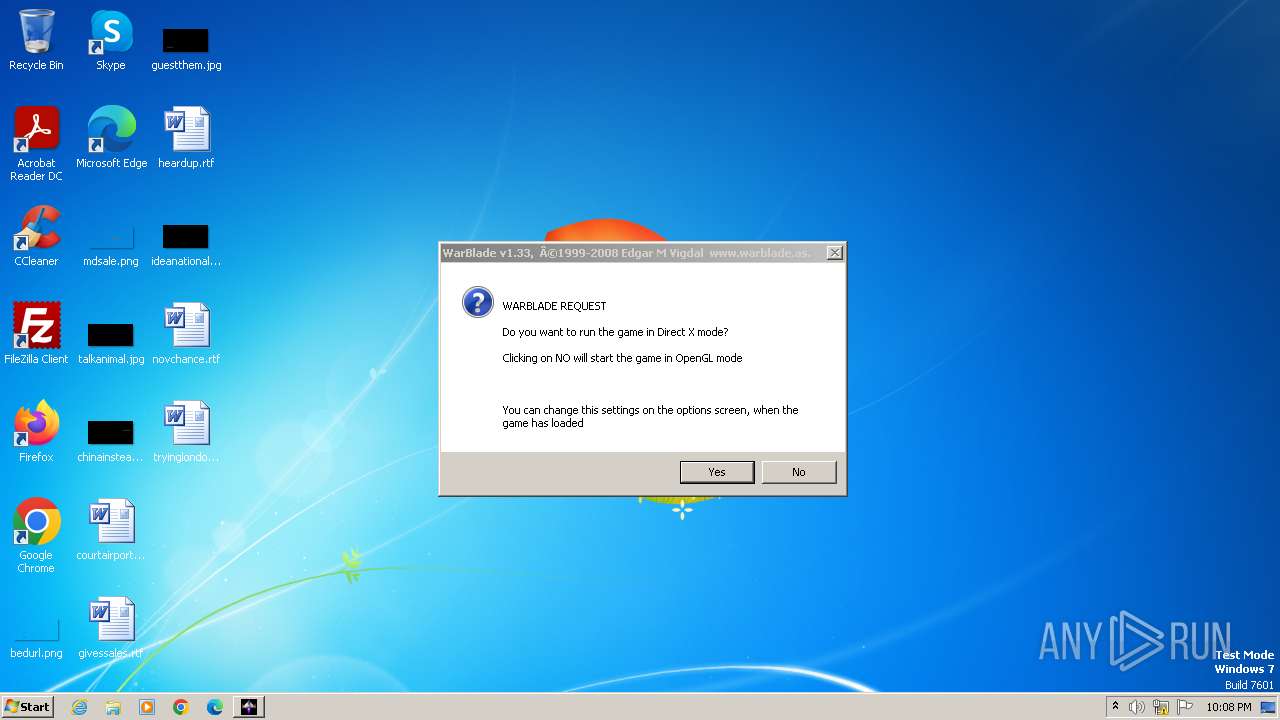
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Users\admin\AppData\Local\Temp\Warblade 1.33.exe" /SPAWNWND=$20134 /NOTIFYWND=$30138 | C:\Users\admin\AppData\Local\Temp\Warblade 1.33.exe | Warblade 1.33.tmp | ||||||||||||
User: admin Company: EMV Software Integrity Level: HIGH Description: Warblade Demo Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\AppData\Local\Temp\is-MOAV4.tmp\Warblade 1.33.tmp" /SL5="$30130,14925863,58368,C:\Users\admin\AppData\Local\Temp\Warblade 1.33.exe" /SPAWNWND=$20134 /NOTIFYWND=$30138 | C:\Users\admin\AppData\Local\Temp\is-MOAV4.tmp\Warblade 1.33.tmp | Warblade 1.33.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
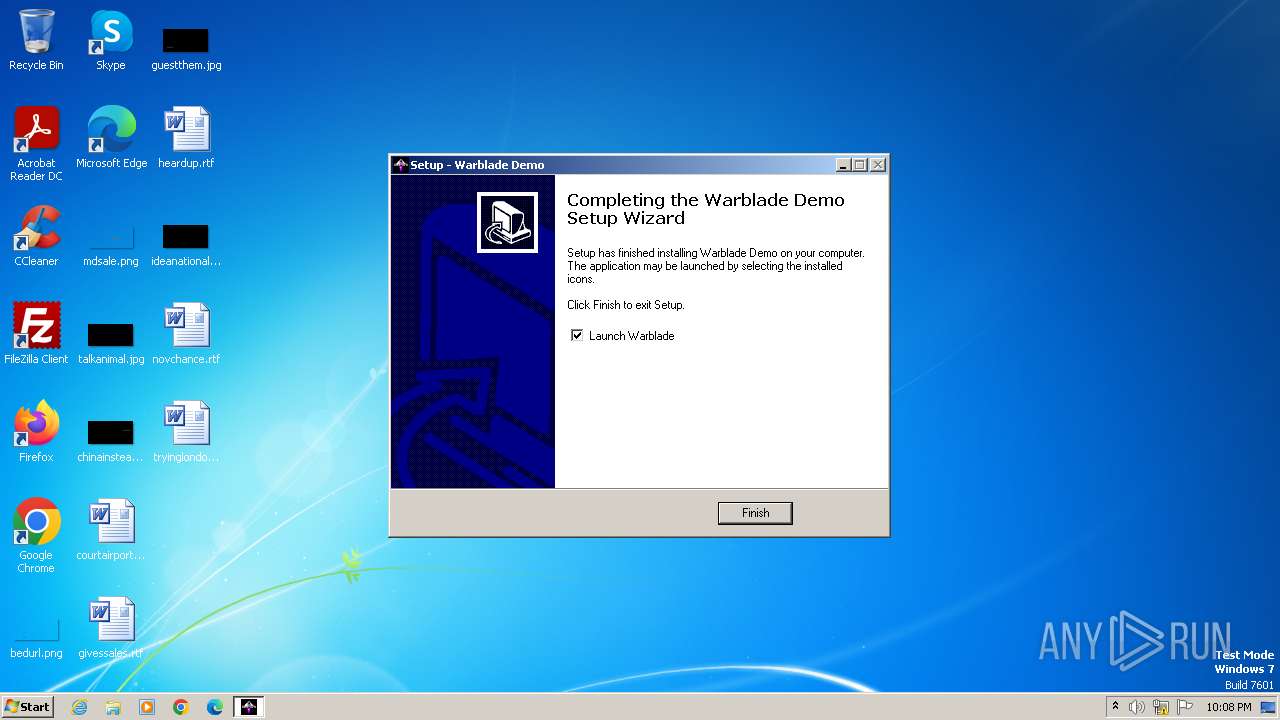
| 2028 | "C:\Program Files\Warblade Demo\warblade.exe" | C:\Program Files\Warblade Demo\warblade.exe | Warblade 1.33.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\Warblade 1.33.exe" | C:\Users\admin\AppData\Local\Temp\Warblade 1.33.exe | explorer.exe | ||||||||||||
User: admin Company: EMV Software Integrity Level: MEDIUM Description: Warblade Demo Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\AppData\Local\Temp\is-83TBA.tmp\Warblade 1.33.tmp" /SL5="$30138,14925863,58368,C:\Users\admin\AppData\Local\Temp\Warblade 1.33.exe" | C:\Users\admin\AppData\Local\Temp\is-83TBA.tmp\Warblade 1.33.tmp | — | Warblade 1.33.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
Total events
5 765
Read events
5 722
Write events
37
Delete events
6
Modification events
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.2.3 | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Warblade Demo | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Warblade Demo\ | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Warblade Demo | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: desktopicon,quicklaunchicon | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | DisplayName |
Value: Warblade Demo | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Warblade Demo\unins000.exe" | |||
| (PID) Process: | (1116) Warblade 1.33.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Warblade Demo_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Warblade Demo\unins000.exe" /SILENT | |||
Executable files
10
Suspicious files
244
Text files
16
Unknown types
82
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\data\is-T34HU.tmp | — | |
MD5:— | SHA256:— | |||
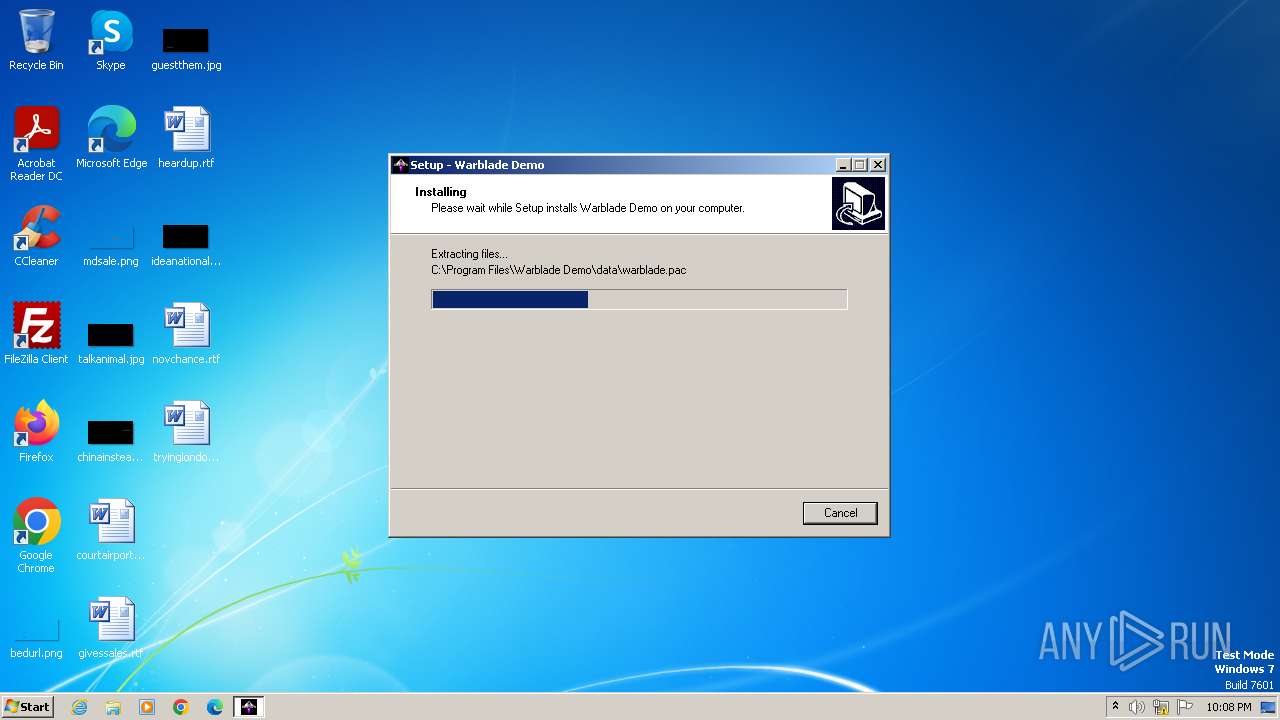
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\data\warblade.pac | — | |
MD5:— | SHA256:— | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\warblade.exe | executable | |
MD5:7CE5625BF2D46C1CD125CCA39E1549EA | SHA256:5D1ACB95C3CF22C2CE68A86E0A3E4A679EB1D070F4CBE1147753BACDB235282A | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\warblade.ico | image | |
MD5:6F1DA2CE56A4BBF334F7D4417C0FE67D | SHA256:7EA4BB9D30BD683FD59A7AB25F7471DB93BB122741813F0AC9753F7DB616C70F | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\unins000.exe | executable | |
MD5:859A40B0605716E69A9BD8E9BC37415E | SHA256:1501253C25BC66EABDF46058711F1312CA2998CF923C4782159AE6B1AA251F03 | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\is-BIQJQ.tmp | text | |
MD5:A08B88974C5970414D2D1E71E9267AA6 | SHA256:918BF0A0F507CF00CE9F9693D6E87F4B9DDC62EF00BCC800621EBAB5DE427C47 | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\is-2262B.tmp | executable | |
MD5:7CE5625BF2D46C1CD125CCA39E1549EA | SHA256:5D1ACB95C3CF22C2CE68A86E0A3E4A679EB1D070F4CBE1147753BACDB235282A | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\Important new version notes_V1.33_Eng.txt | text | |
MD5:0AB958BEFBE69F76B1F4FCDE436E45F0 | SHA256:1EA14A1BACA528A658790FB21DDC7D0006DDCF6A13C1426DE15F0E98AEEEF5B4 | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\is-I7FQ7.tmp | image | |
MD5:6F1DA2CE56A4BBF334F7D4417C0FE67D | SHA256:7EA4BB9D30BD683FD59A7AB25F7471DB93BB122741813F0AC9753F7DB616C70F | |||
| 1116 | Warblade 1.33.tmp | C:\Program Files\Warblade Demo\license.txt | text | |
MD5:C6534B9961551F8D6A9CA0C0FE478AE4 | SHA256:E558D8B67788A03CB351E2210C8078F8397FBE416C729F35966E78CA42A13F1E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
2028 | warblade.exe | 79.170.80.190:80 | www.warblade.as | Sognenett AS | NO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.warblade.as |
| unknown |
dns.msftncsi.com |
| shared |