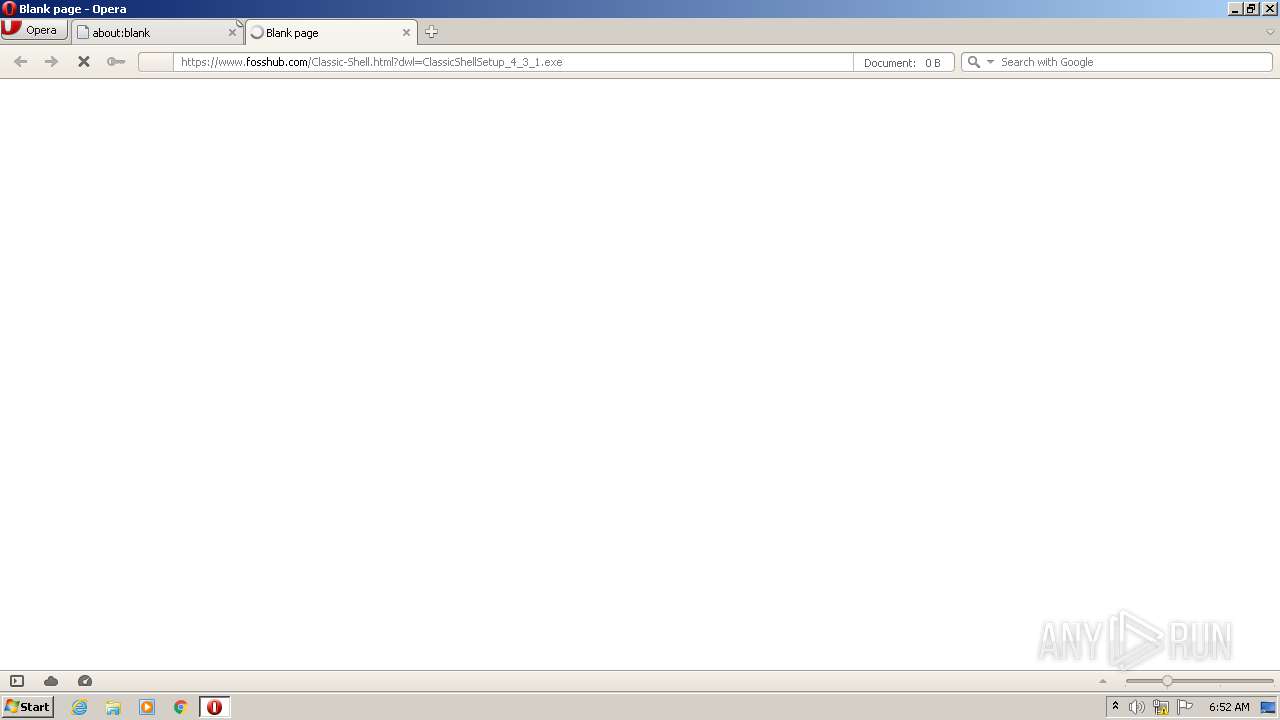
| URL: | https://www.fosshub.com/Classic-Shell.html?dwl=ClassicShellSetup_4_3_1.exe |
| Full analysis: | https://app.any.run/tasks/06bf5245-11eb-4fb2-8d49-58336d58f3f4 |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2020, 06:51:56 |
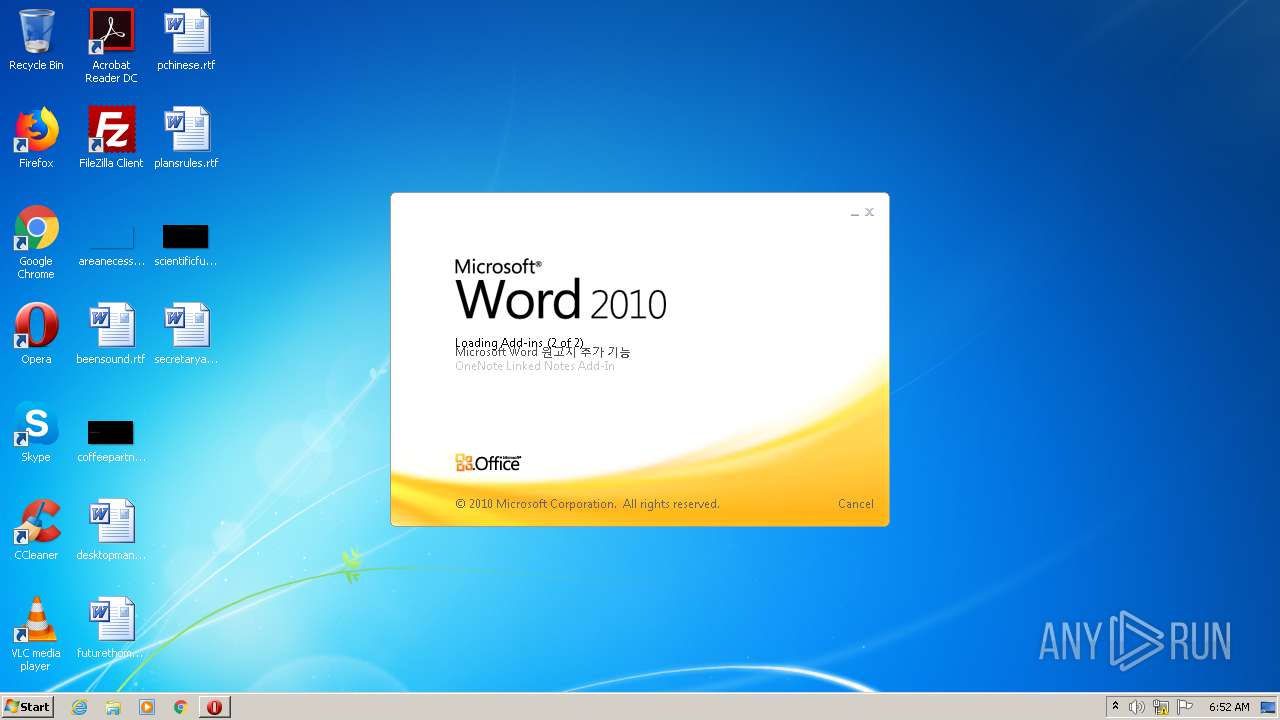
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 947C972ABF6CAE9396C7173F9E7DC536 |
| SHA1: | 133A2C6E1EDAF65973E344E184BC2766E98470D1 |
| SHA256: | 9F5BD816D9731EA424C8C7ECEC928F632DB268EEACB76A58AE34F79B230D9640 |
| SSDEEP: | 3:N8DSLWWKS/QNBSsZW0QxzC:2OLWWzKksZWvC |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2600)
Creates files in the user directory
- WINWORD.EXE (PID: 2600)
- opera.exe (PID: 2312)
- firefox.exe (PID: 2480)
Application launched itself
- firefox.exe (PID: 2480)
- firefox.exe (PID: 3108)
- chrome.exe (PID: 2824)
Manual execution by user
- firefox.exe (PID: 3108)
- chrome.exe (PID: 2824)
- WINWORD.EXE (PID: 2600)
Creates files in the program directory
- firefox.exe (PID: 2480)
Reads CPU info
- firefox.exe (PID: 2480)
Reads the hosts file
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,1360545802547966788,781205323496608987,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17416708060856836635 --mojo-platform-channel-handle=2808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2480.0.1862177500\612795035" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2480 "\\.\pipe\gecko-crash-server-pipe.2480" 1148 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2480.20.1812222936\1590154570" -childID 3 -isForBrowser -prefsHandle 3640 -prefMapHandle 3656 -prefsLen 6718 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2480 "\\.\pipe\gecko-crash-server-pipe.2480" 3672 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3020 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Opera\opera.exe" "https://www.fosshub.com/Classic-Shell.html?dwl=ClassicShellSetup_4_3_1.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,1360545802547966788,781205323496608987,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7108826289352700734 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x592ba9d0,0x592ba9e0,0x592ba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
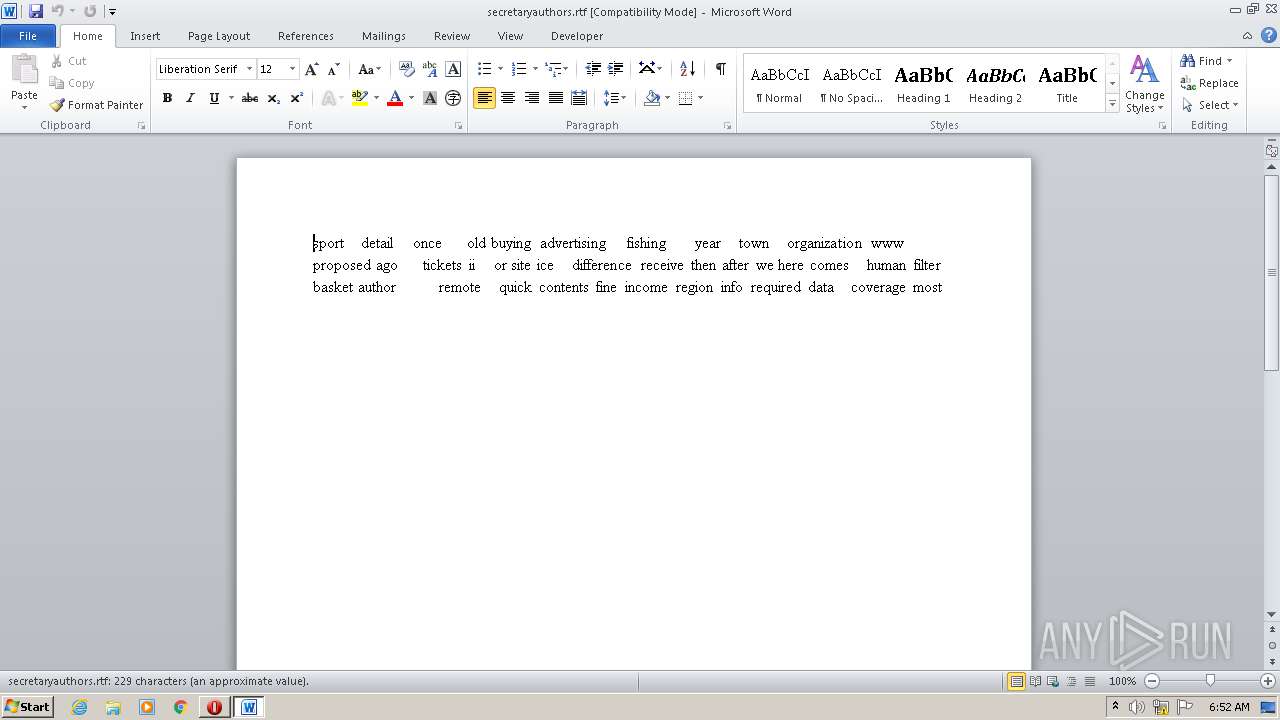
| 2600 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\secretaryauthors.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2480.3.409059075\114923897" -childID 1 -isForBrowser -prefsHandle 1732 -prefMapHandle 1728 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2480 "\\.\pipe\gecko-crash-server-pipe.2480" 1752 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
1 619
Read events
878
Write events
597
Delete events
144
Modification events
| (PID) Process: | (2312) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "https://www.fosshub.com/Classic-Shell.html?dwl=ClassicShellSetup_4_3_1.exe" | |||
| (PID) Process: | (2312) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !6# |
Value: 21362300280A0000010000000000000000000000 | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
Executable files
0
Suspicious files
102
Text files
87
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprD6F2.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprD6F3.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprD752.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EF3088YYTGBZ7L1ZE2DW.temp | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 2600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFE12.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr180.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\https%3A%2F%2Fwww.fosshub.com%2Fmedia%2Ffavicon%2Ffavicon-32x32.png | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\https%3A%2F%2Fwww.fosshub.com%2Fmedia%2Ffavicon%2Fandroid-chrome-192x192.png | — | |
MD5:— | SHA256:— | |||
| 2312 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\https%3A%2F%2Fwww.fosshub.com%2Fmedia%2Ffavicon%2Ffavicon.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
50
DNS requests
74
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2312 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.30 Kb | whitelisted |
2312 | opera.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDoZTy4rmFzYAIAAAAAgFS4 | US | der | 472 b | whitelisted |
2312 | opera.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQC8nOEuy2BgAwgAAAAAYtcC | US | der | 472 b | whitelisted |
2312 | opera.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDOGlA3rPWk4gIAAAAAgFRa | US | der | 472 b | whitelisted |
2312 | opera.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCTUSQbvrzbawgAAAAAYtax | US | der | 472 b | whitelisted |
2480 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2480 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
2480 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2480 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2480 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2312 | opera.exe | 185.26.182.118:443 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
2312 | opera.exe | 104.20.136.9:443 | www.fosshub.com | Cloudflare Inc | US | shared |
2312 | opera.exe | 185.26.182.94:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
2312 | opera.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2480 | firefox.exe | 52.41.230.109:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2312 | opera.exe | 172.217.23.104:443 | ssl.google-analytics.com | Google Inc. | US | suspicious |
2480 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
2480 | firefox.exe | 54.213.218.169:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2480 | firefox.exe | 143.204.215.89:443 | snippets.cdn.mozilla.net | — | US | malicious |
2312 | opera.exe | 216.58.212.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.fosshub.com |
| malicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |