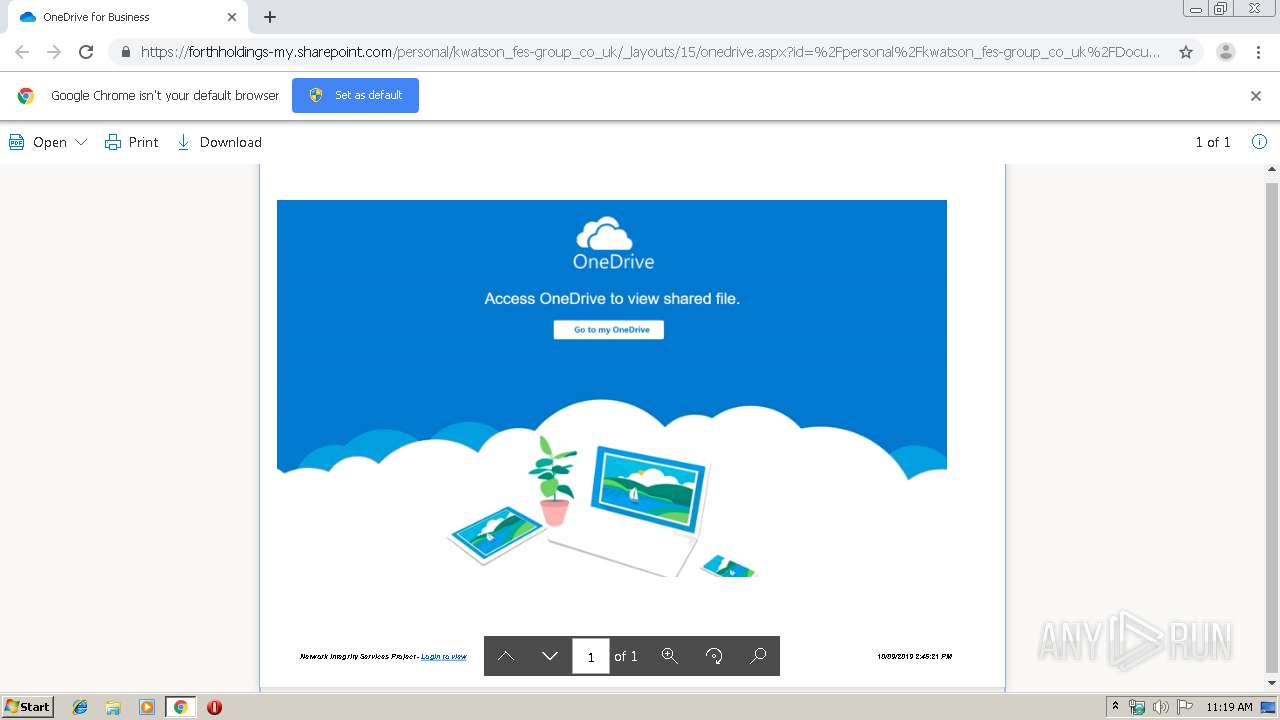
| URL: | https://forthholdings-my.sharepoint.com/:b:/g/personal/kwatson_fes-group_co_uk/EYO_640f-LBIpaEQ_9Lu2IoB0J9BNl2vnxEnjyr-BIX0cA?e=lHto1N |
| Full analysis: | https://app.any.run/tasks/c0c5e6e0-db33-4fdc-a972-ffeaee501eec |
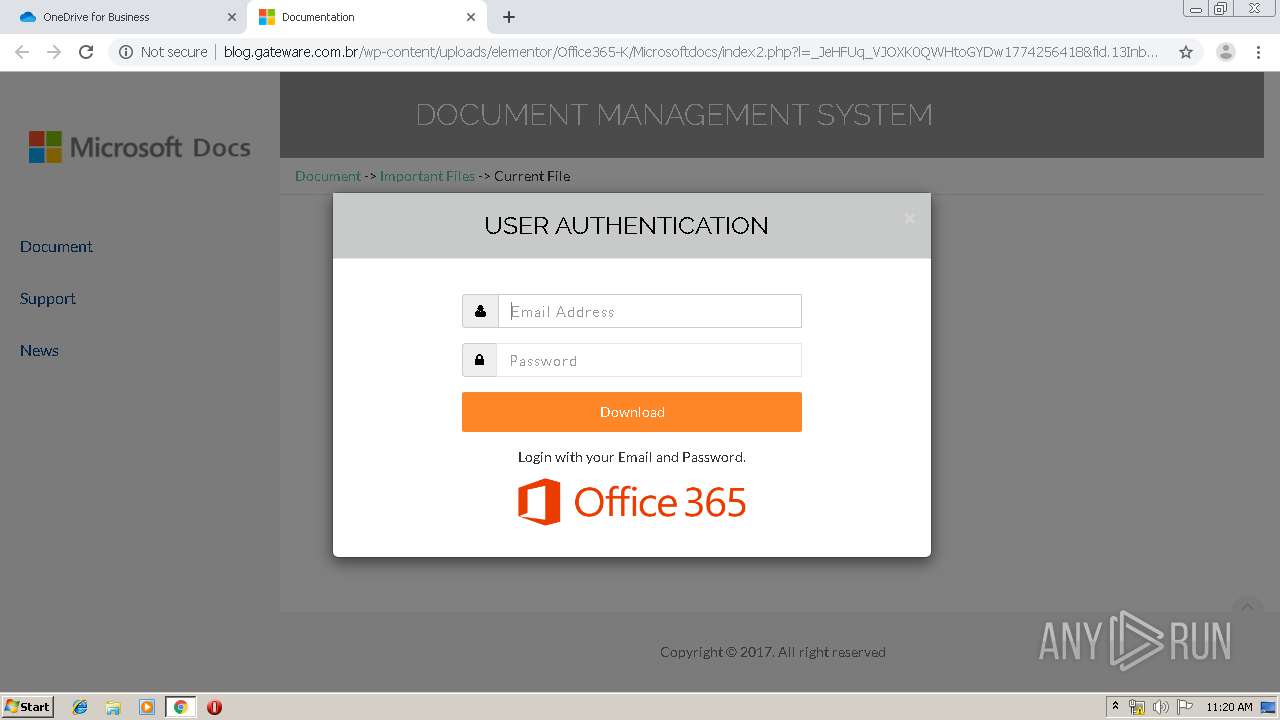
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 10:18:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E0F6E526FA74A34F5FF6BE4F23D7C96E |
| SHA1: | C01E91A9373CD84E67F2AACB7D5A8AB7EC5EDA06 |
| SHA256: | 9F4E7B9B3F54A1AC7B8BAE3129E7F3B633F4ECE813ED7E762A08F8101ED418CB |
| SSDEEP: | 3:N8aZyKVd+ArL5BKqGSOhNL6DzfKQGKKg76TvI2663craea/tRPr:2IVd+AfzriFpvZV/e0zr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2912)
INFO
Reads the hosts file
- chrome.exe (PID: 2912)
- chrome.exe (PID: 2340)
Application launched itself
- chrome.exe (PID: 2912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17697763239407184694 --mojo-platform-channel-handle=4280 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14980701971147236026 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11663402250395884641 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3544431498128836136 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6873992013391575158 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8427301411977817700 --mojo-platform-channel-handle=3716 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10708289360670945759 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15655292681297394658 --mojo-platform-channel-handle=3012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16526348491793987200 --mojo-platform-channel-handle=3956 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16342001267465117073,16580130140610266700,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5832890517966562068 --mojo-platform-channel-handle=3824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
610
Read events
521
Write events
84
Delete events
5
Modification events
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2912-13212670737577250 |
Value: 259 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
78
Text files
200
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\659c6d30-bcef-45a3-bf65-e9fc076b74df.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF16b02a.TMP | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF16b02a.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
37
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
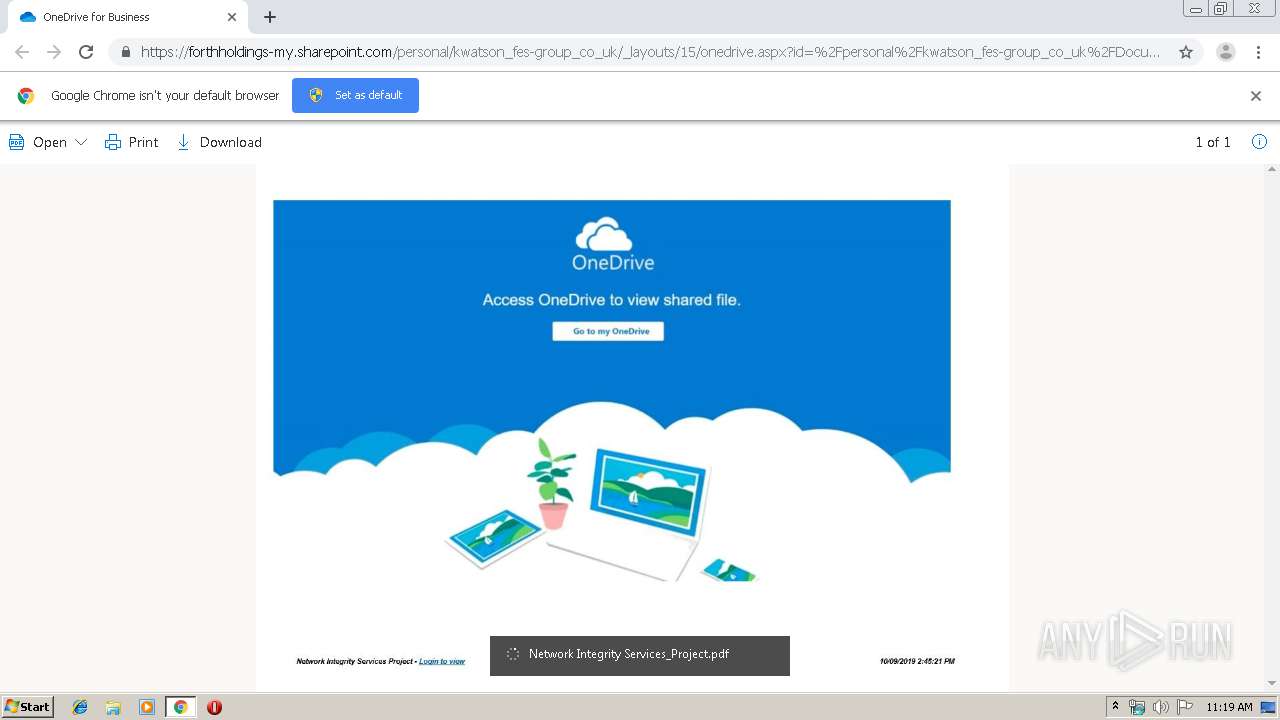
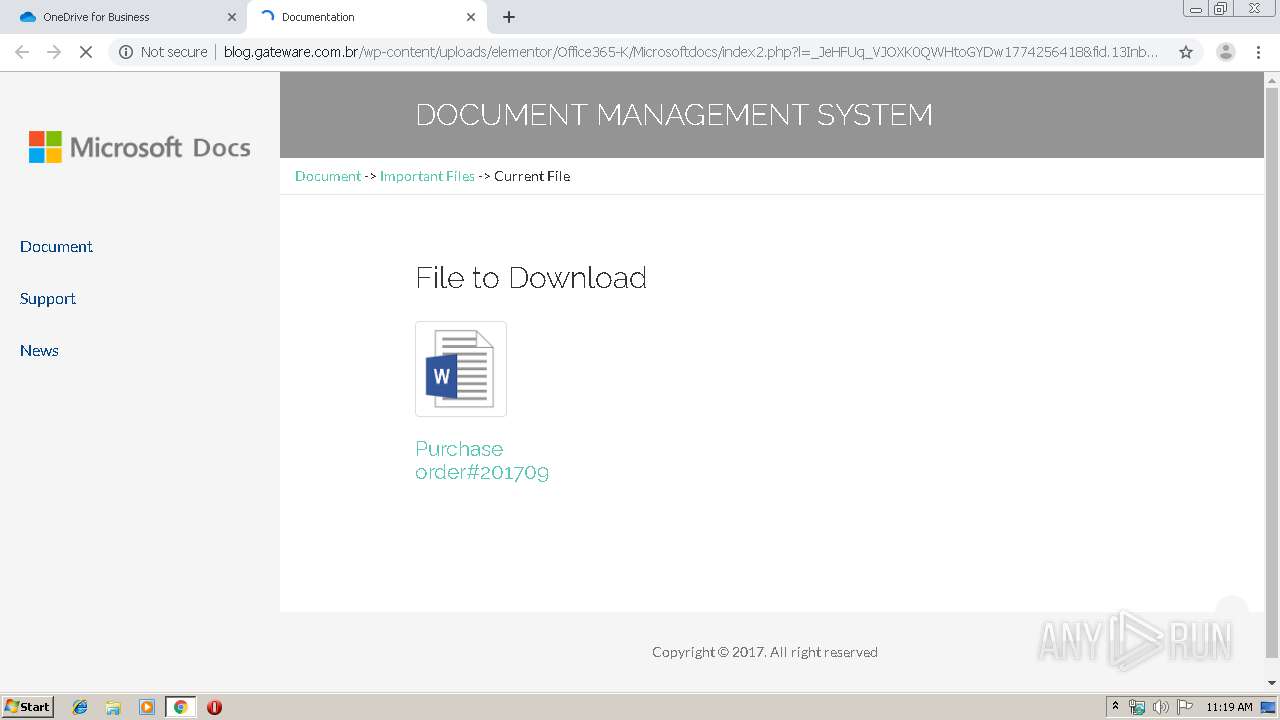
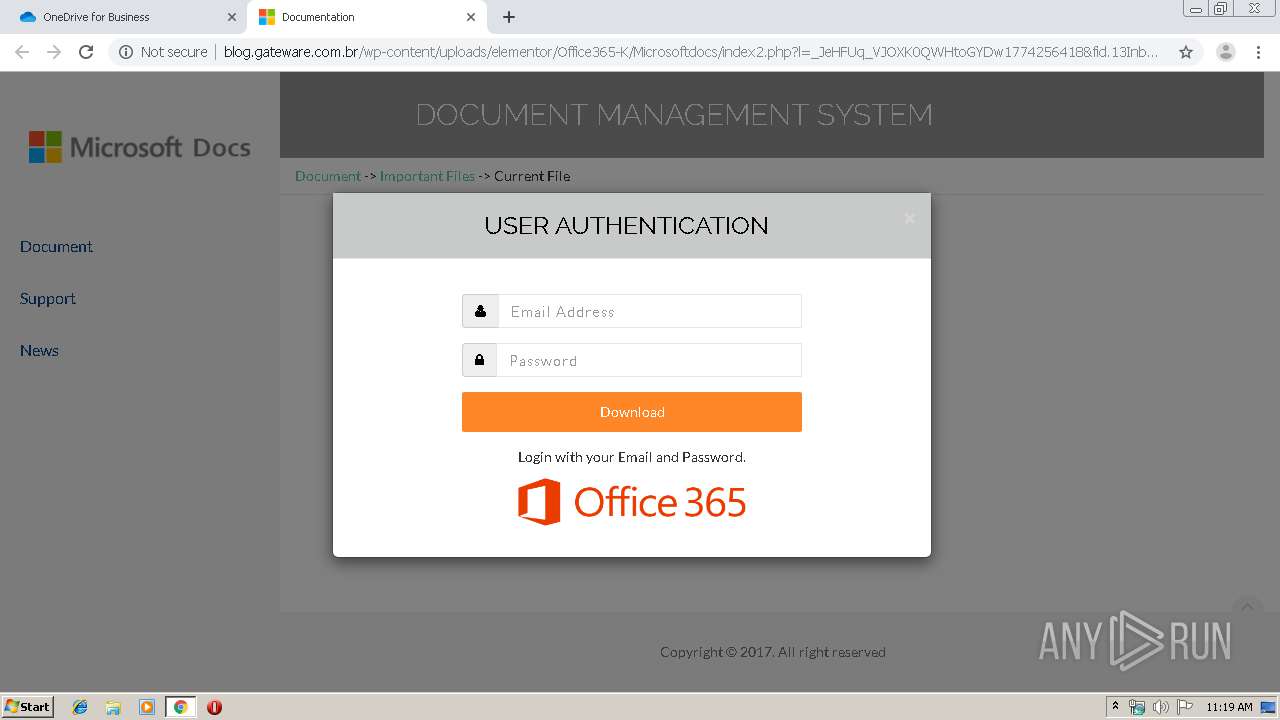
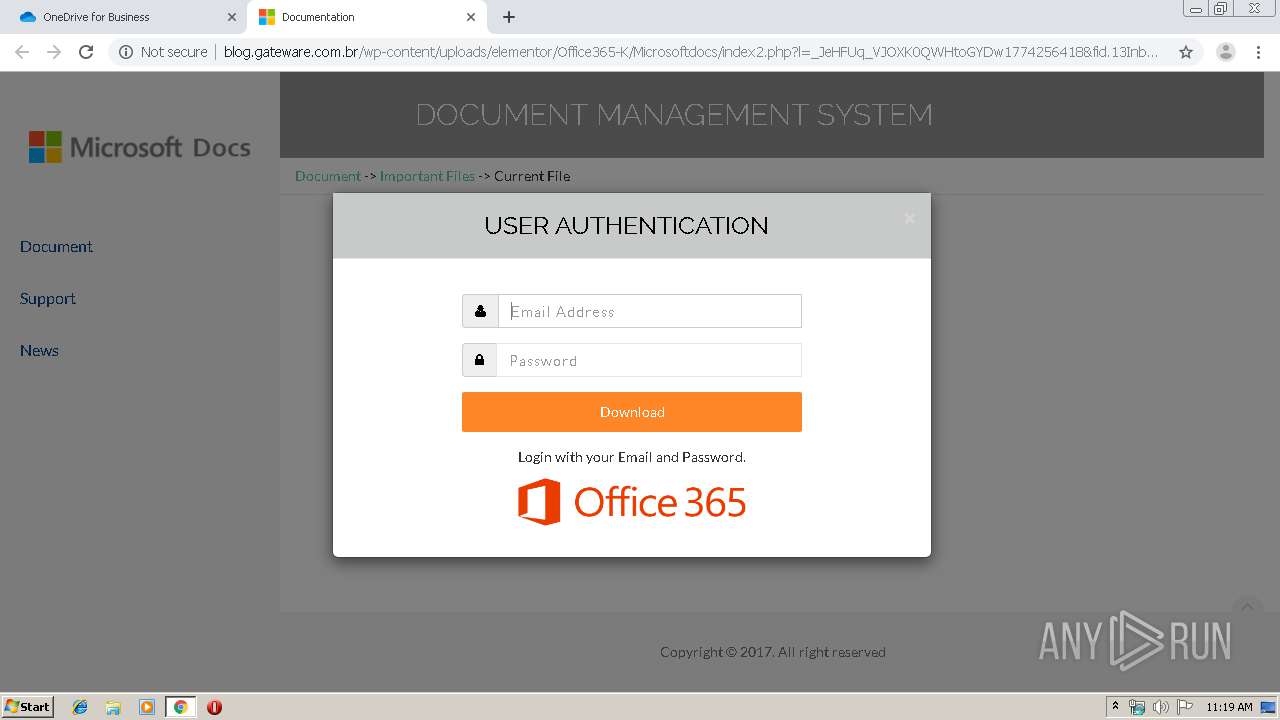
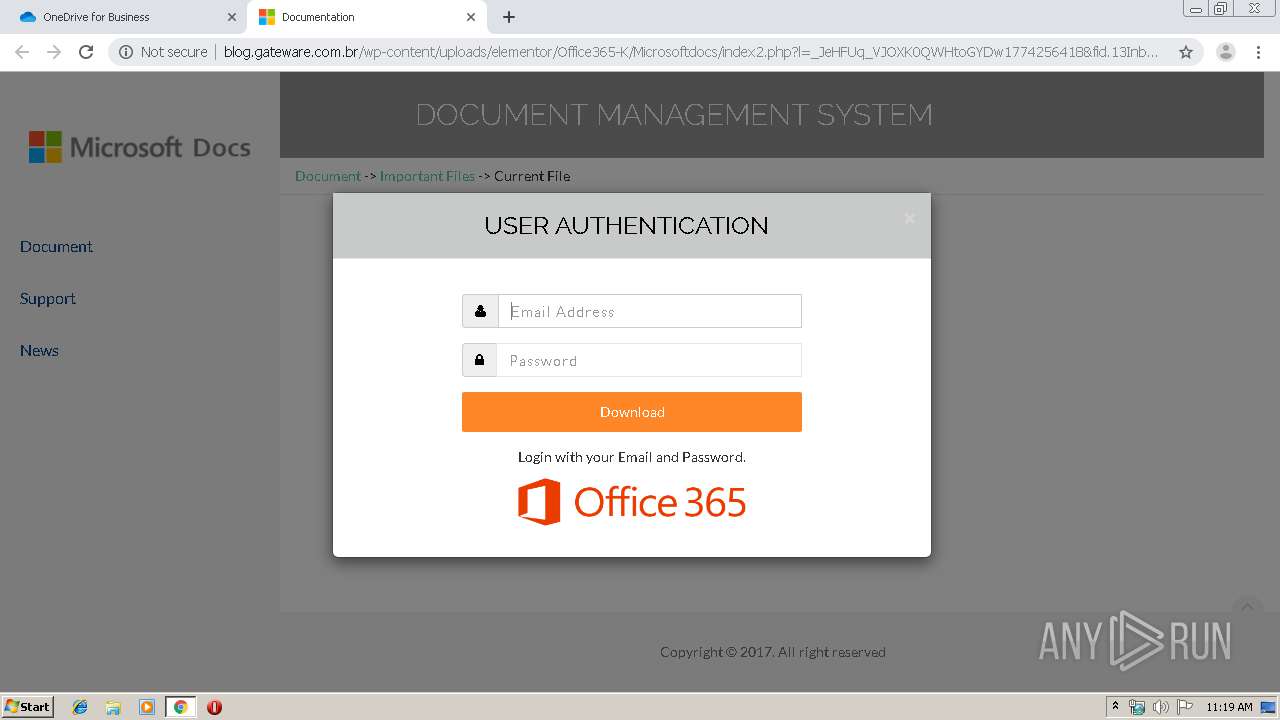
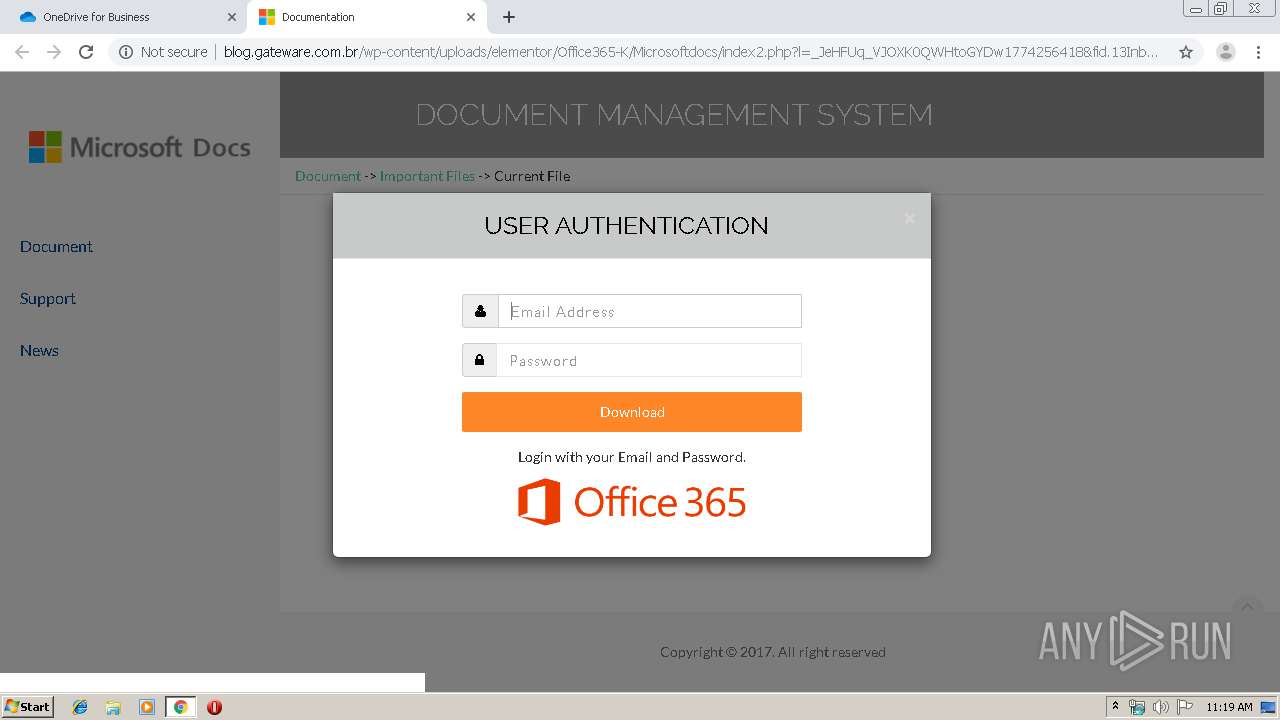
2340 | chrome.exe | GET | 200 | 191.243.140.106:80 | http://blog.gateware.com.br/wp-content/uploads/elementor/Office365-K/Microsoftdocs/index2.php?l=_JeHFUq_VJOXK0QWHtoGYDw1774256418&fid.13InboxLight.aspxn.1774256418&fid.125289964252813InboxLight99642_Product-email&email= | BR | html | 1.79 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 191.243.140.106:80 | http://blog.gateware.com.br/wp-content/uploads/elementor/Office365-K/Microsoftdocs/assets/js/custom.js | BR | text | 1.01 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 216.58.207.42:80 | http://fonts.googleapis.com/css?family=Raleway:100,300,400,500%7CLato:300,400 | US | text | 579 b | whitelisted |
2340 | chrome.exe | GET | 200 | 191.243.140.106:80 | http://blog.gateware.com.br/wp-content/uploads/elementor/Office365-K/Microsoftdocs/assets/img/word.png | BR | image | 7.09 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 191.243.140.106:80 | http://blog.gateware.com.br/wp-content/uploads/elementor/Office365-K/Microsoftdocs/assets/css/theDocs.all.min.css | BR | text | 35.7 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 191.243.140.106:80 | http://blog.gateware.com.br/wp-content/uploads/elementor/Office365-K/Microsoftdocs/assets/fonts/fontawesome-webfont5b62.html?v=4.6.3 | BR | woff2 | 70.2 Kb | suspicious |
2340 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2340 | chrome.exe | GET | 200 | 191.243.140.106:80 | http://blog.gateware.com.br/wp-content/uploads/elementor/Office365-K/Microsoftdocs/assets/img/favicon.png | BR | image | 15.7 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 216.58.206.3:80 | http://fonts.gstatic.com/s/raleway/v14/1Ptrg8zYS_SKggPNwIYqWqZPAA.woff2 | US | woff2 | 20.3 Kb | whitelisted |
2340 | chrome.exe | GET | 200 | 216.58.206.3:80 | http://fonts.gstatic.com/s/lato/v16/S6uyw4BMUTPHjx4wXg.woff2 | US | woff2 | 22.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2340 | chrome.exe | 2.16.186.40:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
2340 | chrome.exe | 2.19.34.64:443 | static2.sharepointonline.com | Akamai International B.V. | — | whitelisted |
2340 | chrome.exe | 13.107.136.9:443 | forthholdings-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
2340 | chrome.exe | 13.107.136.13:443 | ukwest1-mediap.svc.ms | Microsoft Corporation | US | suspicious |
2340 | chrome.exe | 216.58.207.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2340 | chrome.exe | 52.114.88.28:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | GB | unknown |
2340 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2340 | chrome.exe | 216.58.206.3:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2340 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
forthholdings-my.sharepoint.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
spoprod-a.akamaihd.net |
| whitelisted |
static2.sharepointonline.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
ukwest1-mediap.svc.ms |
| suspicious |
www.google.com |
| malicious |
clients1.google.com |
| whitelisted |
blog.gateware.com.br |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2340 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Document Phishing Landing 2018-08-30 |
2 ETPRO signatures available at the full report