| File name: | OInstall.exe |
| Full analysis: | https://app.any.run/tasks/575b5bc5-4572-4a0f-9c46-383c7590cb83 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2019, 06:36:44 |
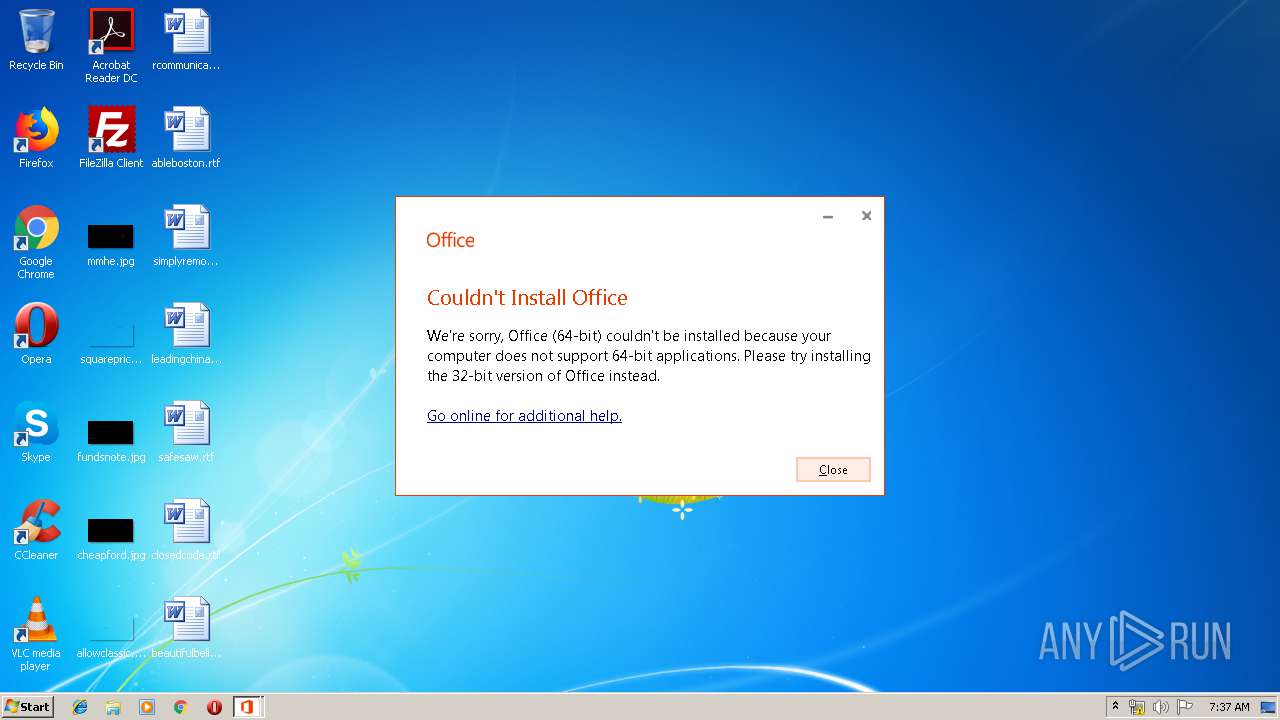
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | CB6E2C13B9548E4864EAA610EBCE96A3 |
| SHA1: | 02B0F88785DED01C75A3EAF4288AEB0BE48D143E |
| SHA256: | 9F46B1F0AA822B65F98744F91414E033C9248021A9F472FA23AE8A81B26B8FAE |
| SSDEEP: | 196608:vHKNxawqBBz0yVnn6z77vv1JQOE5LlpiFi8oULkWZlftsc1ZMihDOnc6ACqcq2tf:vExEBBV96z77vvf3kioGkmBD7wnc6Ad2 |
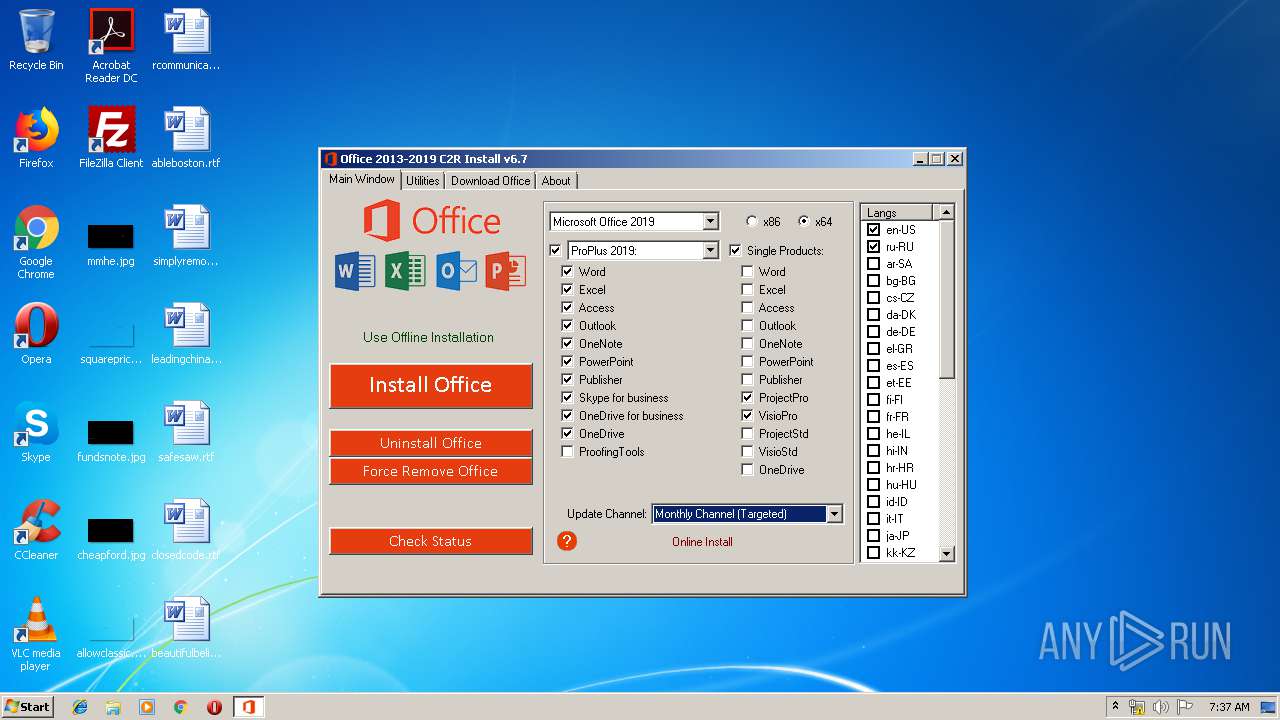
MALICIOUS
Application was dropped or rewritten from another process
- setup.exe (PID: 2108)
- files.dat (PID: 2572)
Changes settings of System certificates
- setup.exe (PID: 2108)
SUSPICIOUS
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 3940)
Starts application with an unusual extension
- cmd.exe (PID: 2348)
Executable content was dropped or overwritten
- files.dat (PID: 2572)
- OInstall.exe (PID: 3940)
Adds / modifies Windows certificates
- setup.exe (PID: 2108)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2940)
- cmd.exe (PID: 4056)
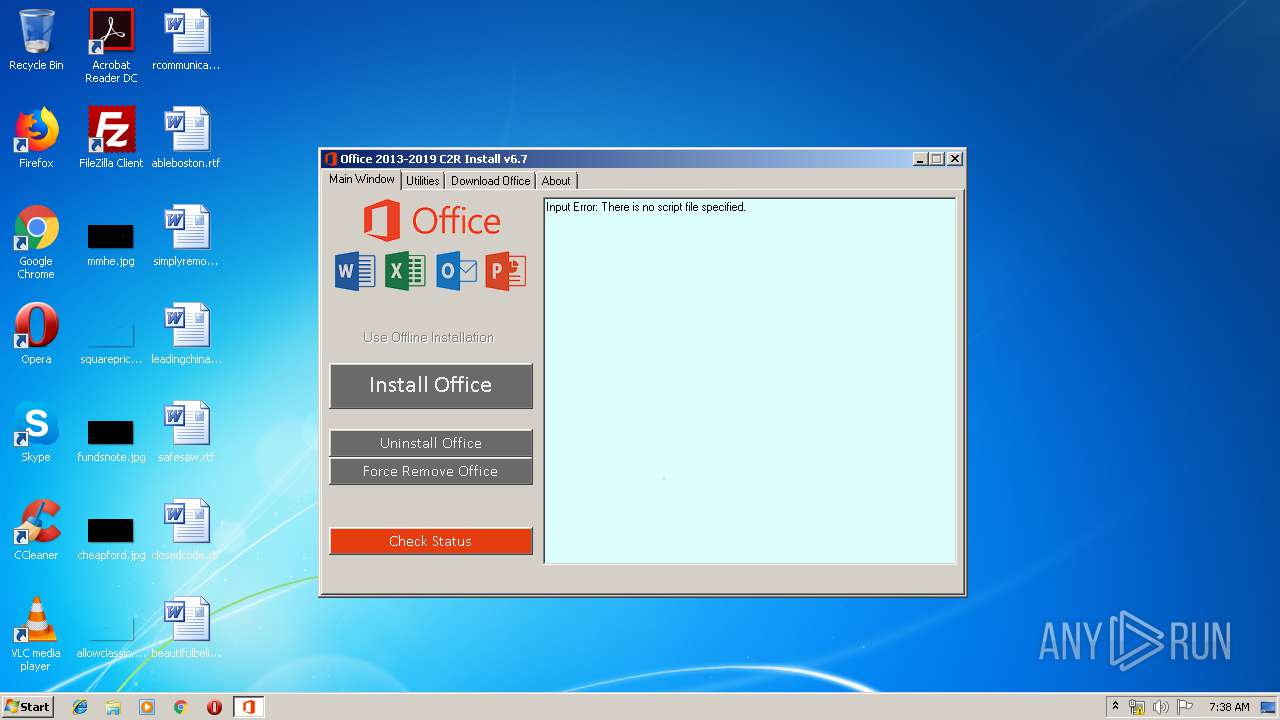
Executes scripts
- cmd.exe (PID: 2996)
INFO
Reads Microsoft Office registry keys
- reg.exe (PID: 2068)
Reads settings of System Certificates
- setup.exe (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:25 07:02:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 10174464 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 9658368 |
| EntryPoint: | 0x12eace0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
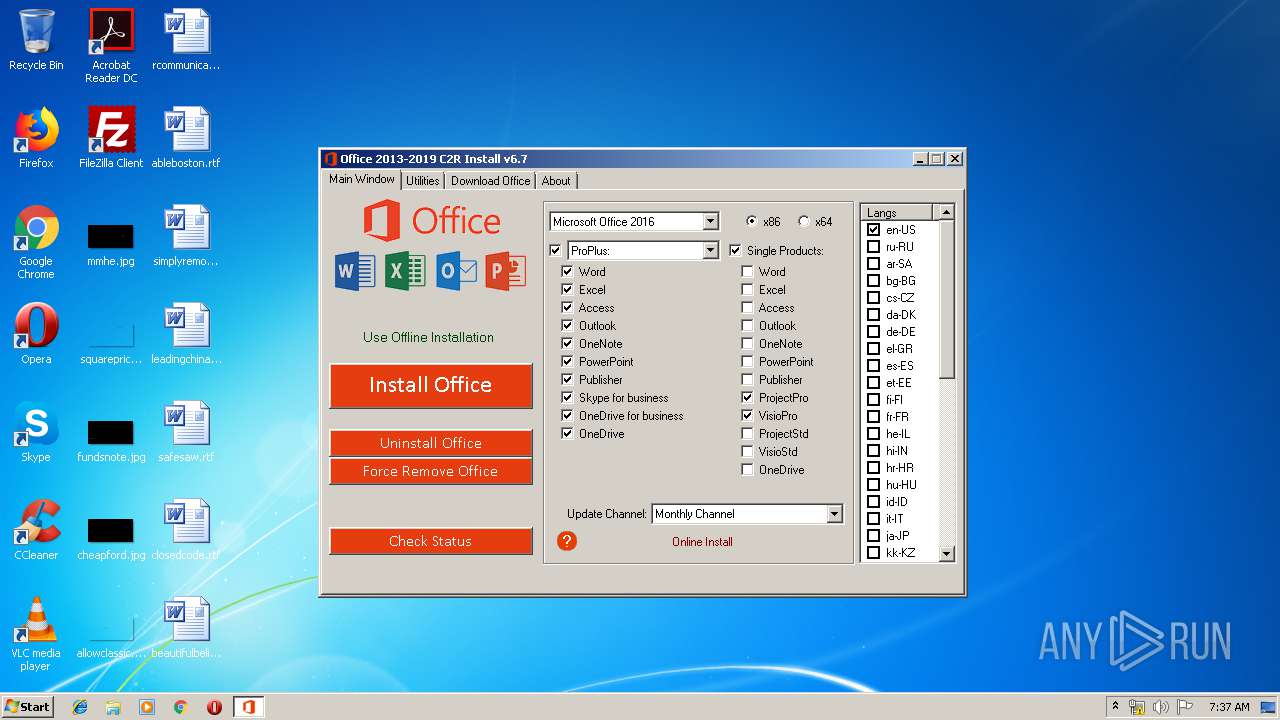
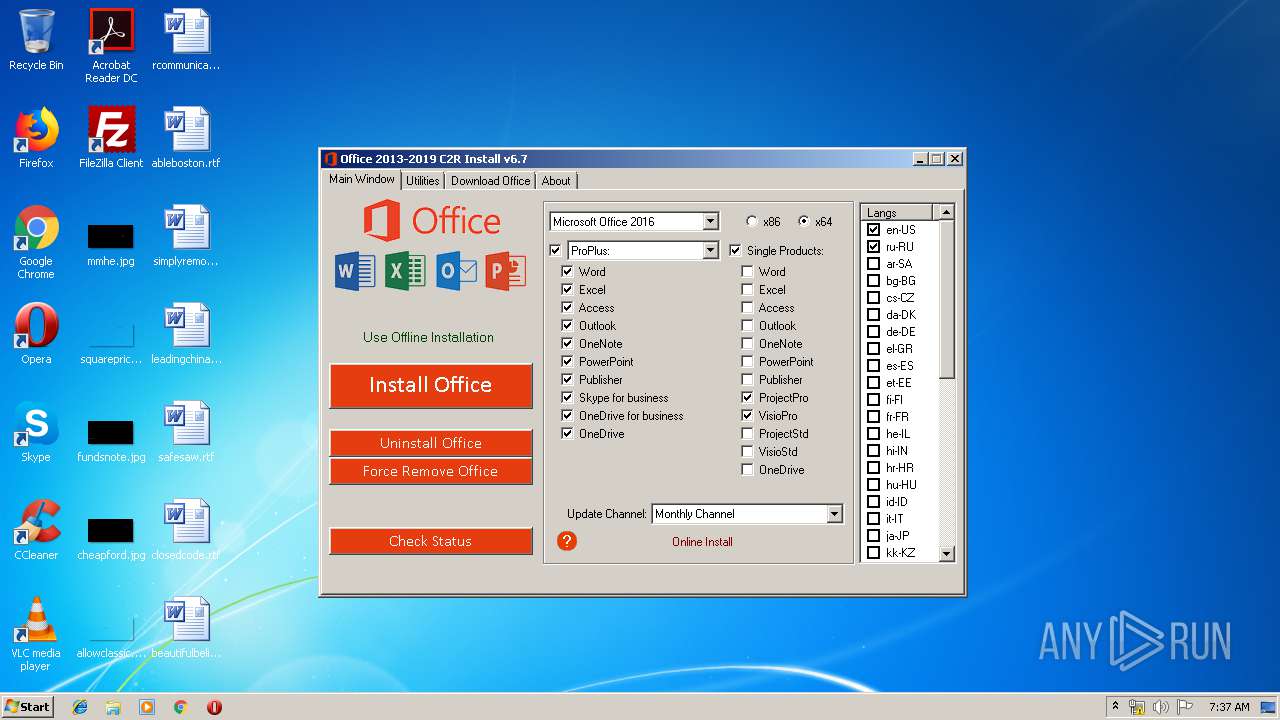
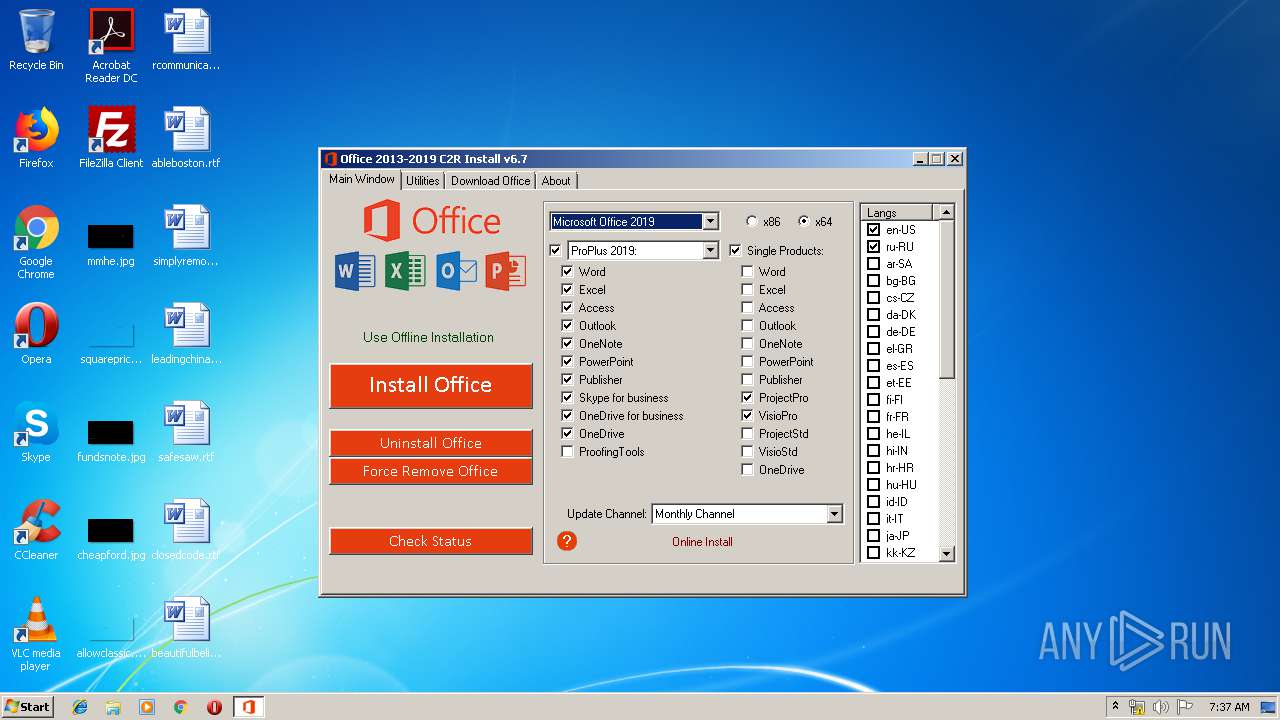
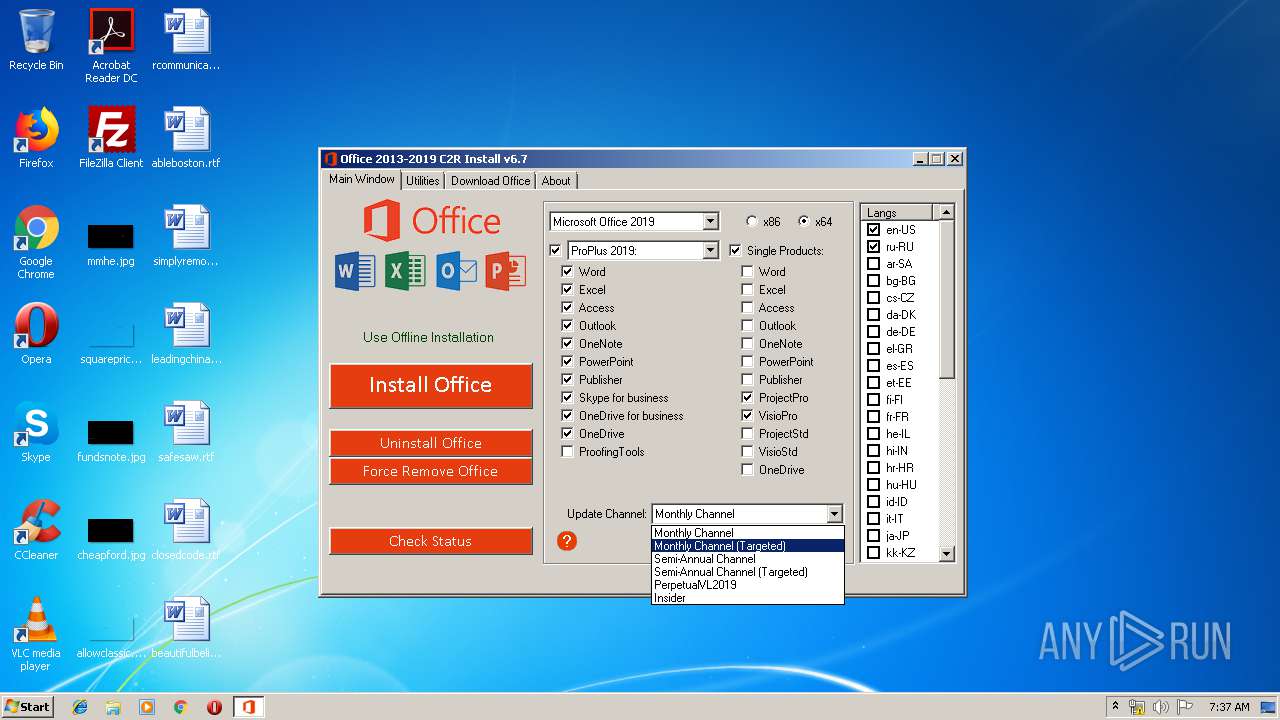
| FileVersionNumber: | 6.7.0.0 |
| ProductVersionNumber: | 6.7.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
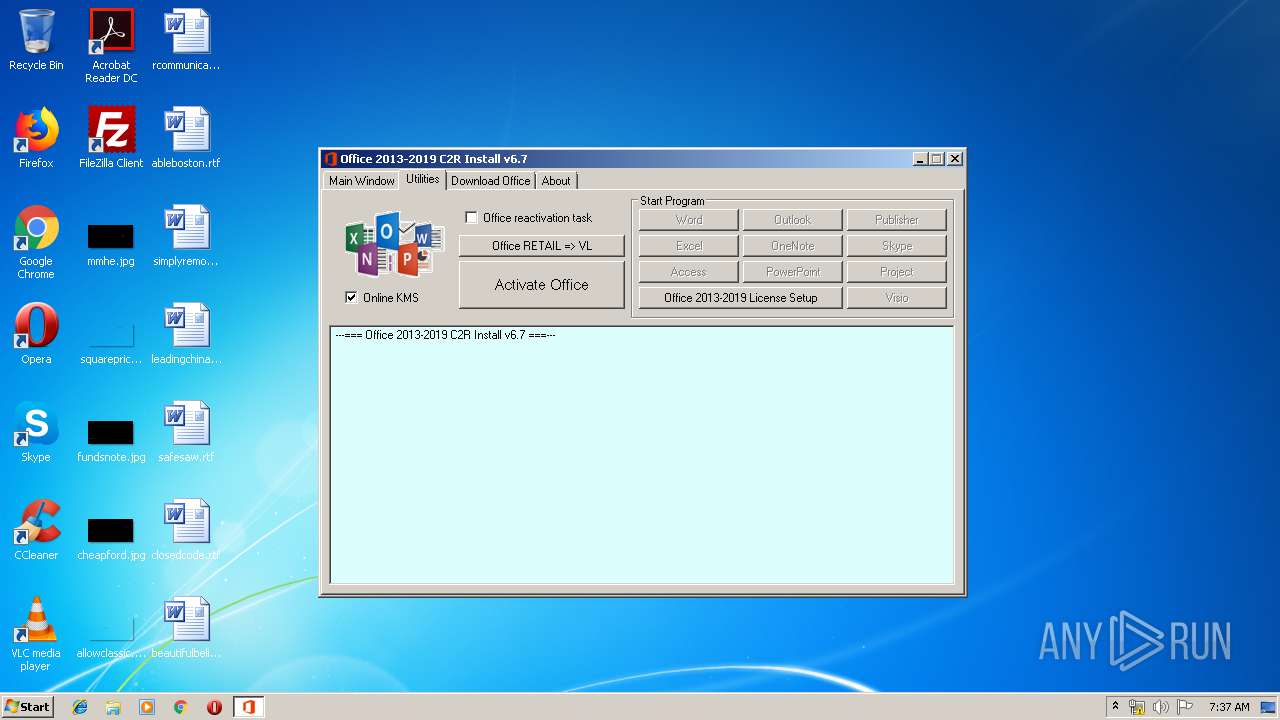
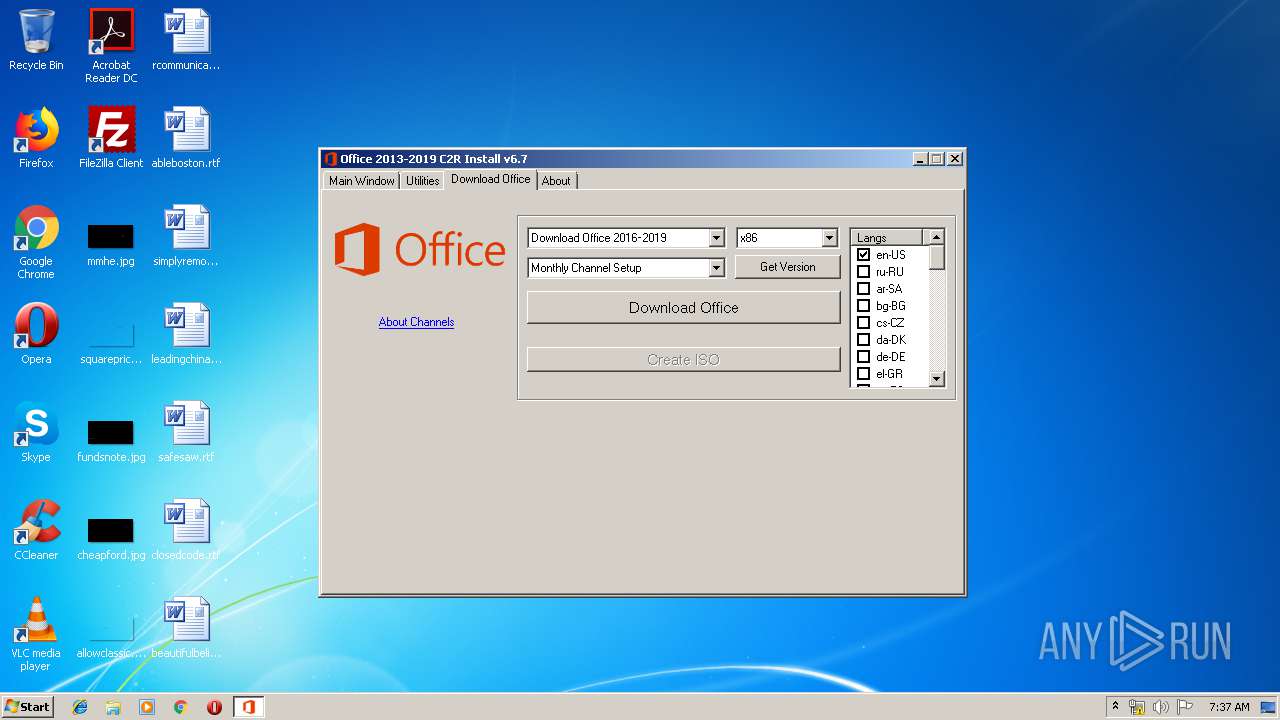
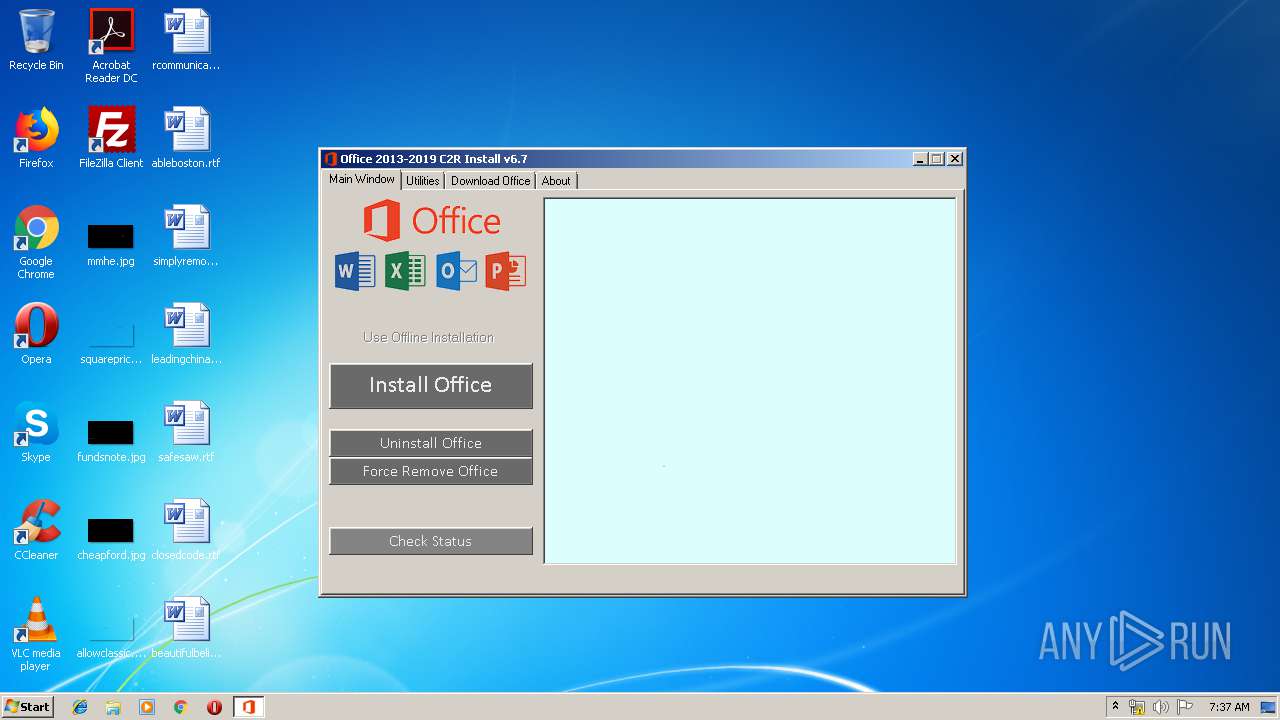
| ProductName: | Office 2013-2016 C2R Install |
| FileDescription: | Office 2013-2016 C2R Install |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Apr-2019 05:02:44 |
| Detected languages: |
|
| ProductName: | Office 2013-2016 C2R Install |
| FileDescription: | Office 2013-2016 C2R Install |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Apr-2019 05:02:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00936000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00937000 | 0x009B4000 | 0x009B4000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89369 |
.rsrc | 0x012EB000 | 0x00016000 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.96496 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94291 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
53
Monitored processes
13
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2068 | REG QUERY HKLM\Software\Microsoft\Office /s /v Path /reg:64 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | C:\Users\admin\AppData\Local\Temp\files\Setup.exe /configure Configure.xml | C:\Users\admin\AppData\Local\Temp\files\setup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Exit code: 1603 Version: 16.0.11617.33601 Modules
| |||||||||||||||
| 2348 | "C:\Windows\System32\cmd.exe" /D /c files.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2548 | REG QUERY HKLM\Software\WOW6432Node\Microsoft\Office /s /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | files.dat -y -pkmsauto | C:\Users\admin\AppData\Local\Temp\files\files.dat | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 2760 | "C:\Windows\System32\cmd.exe" /D /c copy C:\Windows\system32\Tasks\OInstall "C:\Windows\Temp\OInstall.tmp" /Y | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2940 | "C:\Windows\System32\cmd.exe" /c REG QUERY HKLM\Software\Microsoft\Office /s /v Path /reg:64 | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2996 | "C:\Windows\System32\cmd.exe" /D /c cscript.exe "" /dstatus //NoLogo | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\AppData\Local\Temp\OInstall.exe" | C:\Users\admin\AppData\Local\Temp\OInstall.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Office 2013-2016 C2R Install Exit code: 3221226540 Modules
| |||||||||||||||
| 3636 | "C:\Windows\System32\cmd.exe" /D /c C:\Users\admin\AppData\Local\Temp\files\Setup.exe /configure Configure.xml | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1603 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
213
Read events
142
Write events
71
Delete events
0
Modification events
| (PID) Process: | (3940) OInstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\Experiment\officeclicktorun |
| Operation: | write | Name: | FirstSessionTriggered |
Value: 1 | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | UIFallbackLanguages |
Value: x-none | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | HelpLanguageTag |
Value: en-US | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreviousPreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordMailChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | XLChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (2108) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PPTChangeInstallLanguage |
Value: No | |||
Executable files
6
Suspicious files
8
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R30881168-DA4A-4089-8DC5-E975E3018D51\v64_16.0.11727.20210.cab | — | |
MD5:— | SHA256:— | |||
| 2108 | setup.exe | C:\Users\admin\AppData\Local\Temp\Cab33D9.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | setup.exe | C:\Users\admin\AppData\Local\Temp\Tar33DA.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R30881168-DA4A-4089-8DC5-E975E3018D51OfficeC2RB3F4B8BD-E1B1-482F-BBBB-20DD6D2C67B0\v64.hash | — | |
MD5:— | SHA256:— | |||
| 2108 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R30881168-DA4A-4089-8DC5-E975E3018D51OfficeC2RB3F4B8BD-E1B1-482F-BBBB-20DD6D2C67B0\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 2108 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R30881168-DA4A-4089-8DC5-E975E3018D51\v64.hash | — | |
MD5:— | SHA256:— | |||
| 2108 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R30881168-DA4A-4089-8DC5-E975E3018D51\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 3940 | OInstall.exe | C:\Users\admin\AppData\Local\Temp\files\setup.exe | executable | |
MD5:5B51ECE9852B92CFD1D3946D5940EED5 | SHA256:4F5C5CBCBF63115D0FA4F79988F80B9753B1C43D5A2B2C1DD1A6597EA9038E6E | |||
| 2108 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F90F18257CBB4D84216AC1E1F3BB2C76 | binary | |
MD5:— | SHA256:— | |||
| 2108 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\696F3DE637E6DE85B458996D49D759AD | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2108 | setup.exe | HEAD | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.11727.20210.cab | unknown | — | — | whitelisted |
2108 | setup.exe | HEAD | 200 | 2.16.186.83:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.11727.20210.cab | unknown | — | — | whitelisted |
2108 | setup.exe | HEAD | 200 | 2.16.186.83:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.11727.20210.cab | unknown | — | — | whitelisted |
2108 | setup.exe | HEAD | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.11727.20210.cab | unknown | — | — | whitelisted |
2108 | setup.exe | GET | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.11727.20210.cab | unknown | — | — | whitelisted |
2108 | setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
2108 | setup.exe | GET | 200 | 2.16.186.83:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.11727.20210.cab | unknown | compressed | 17.0 Kb | whitelisted |
2108 | setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/Microsoft%20Code%20Signing%20PCA(2).crl | unknown | der | 555 b | whitelisted |
2108 | setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
2108 | setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2108 | setup.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
2108 | setup.exe | 52.109.88.44:443 | mrodevicemgr.officeapps.live.com | Microsoft Corporation | NL | whitelisted |
2108 | setup.exe | 2.18.232.120:80 | officecdn.microsoft.com | Akamai International B.V. | — | whitelisted |
2108 | setup.exe | 2.16.186.83:80 | officecdn.microsoft.com.edgesuite.net | Akamai International B.V. | — | whitelisted |
2108 | setup.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
mrodevicemgr.officeapps.live.com |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
officecdn.microsoft.com.edgesuite.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |