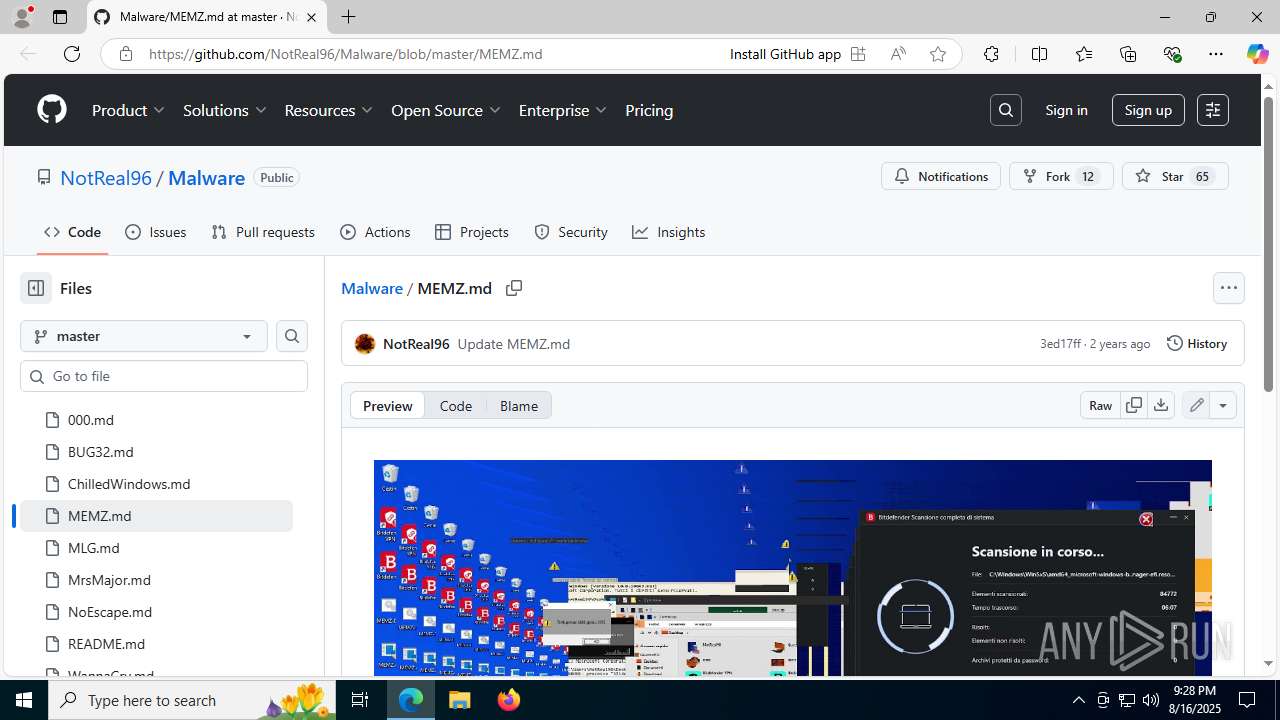
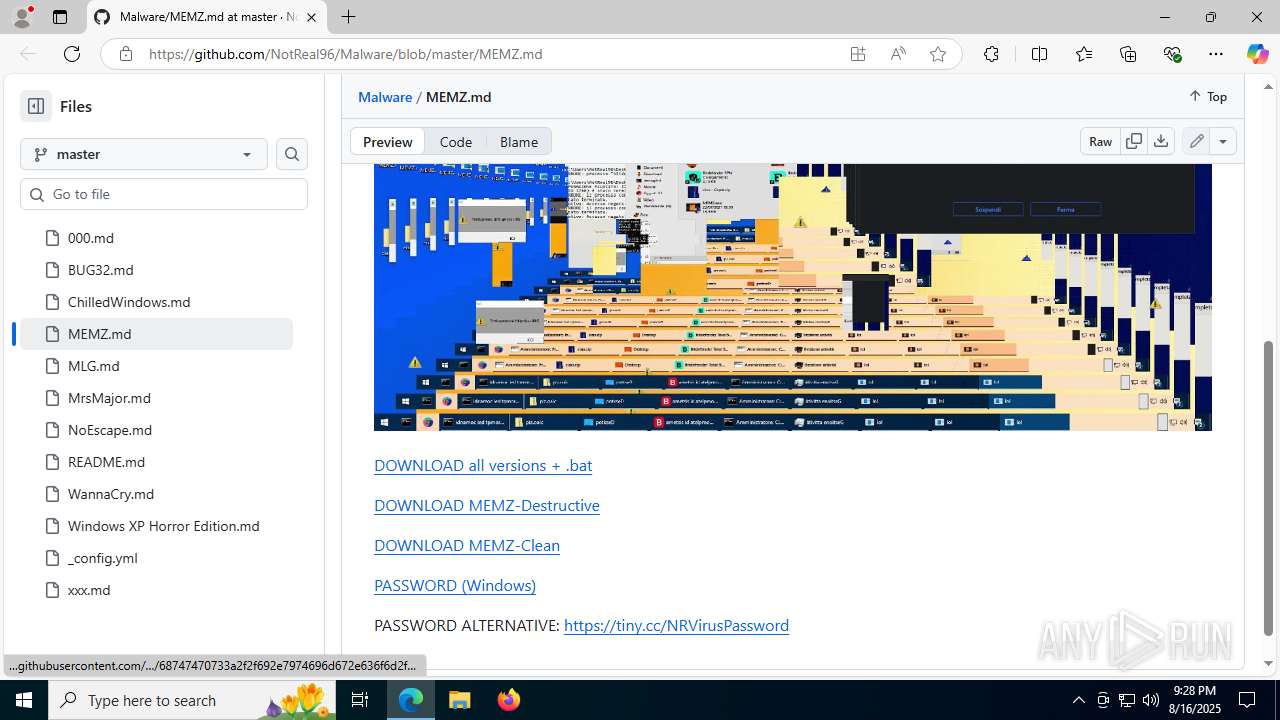
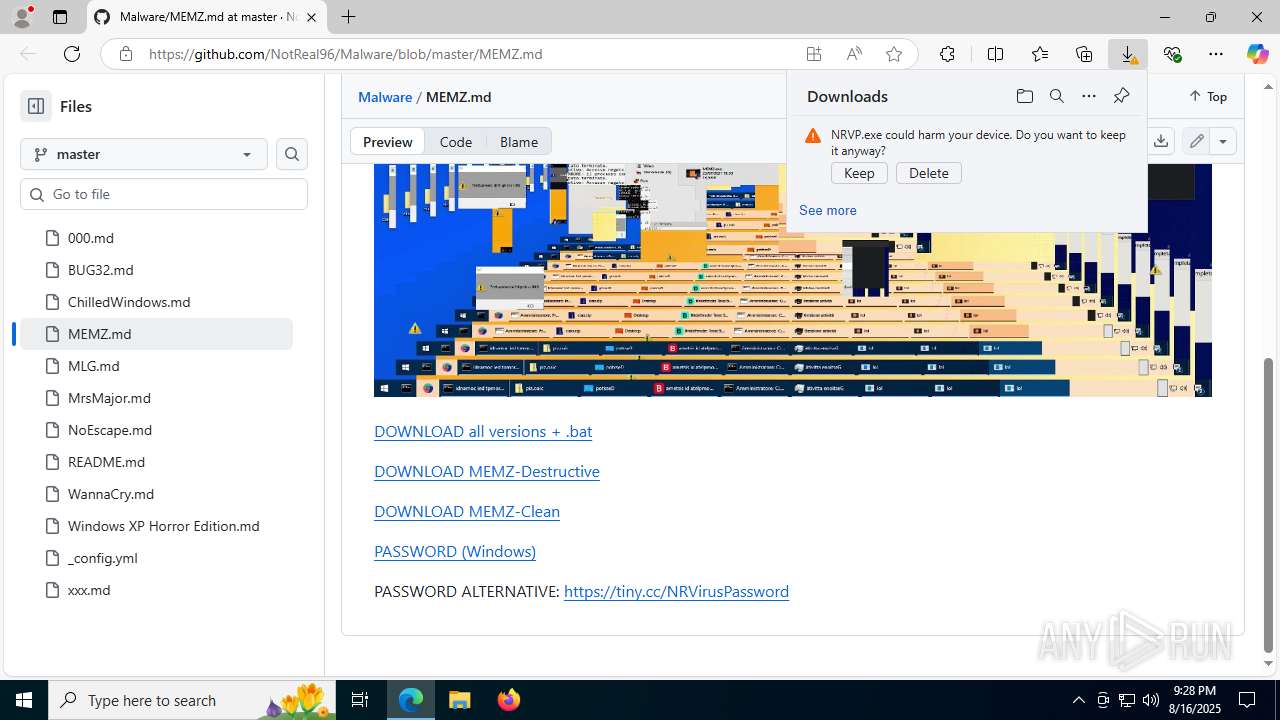
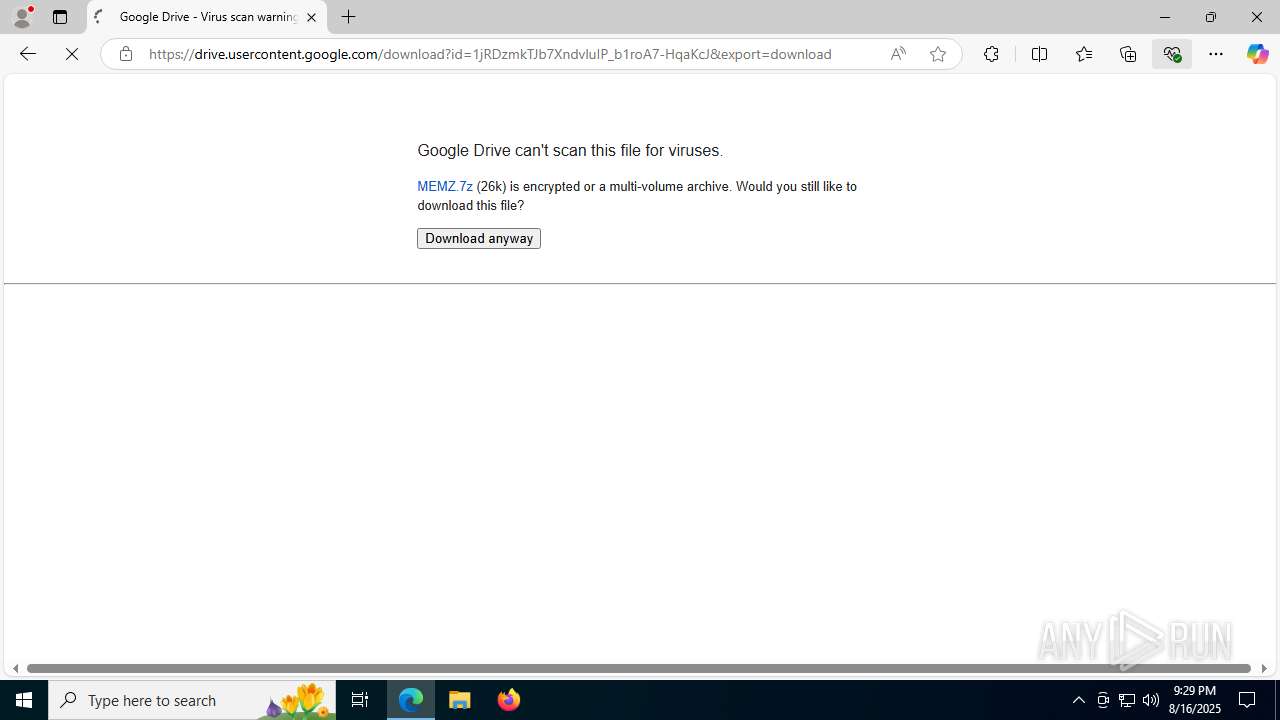
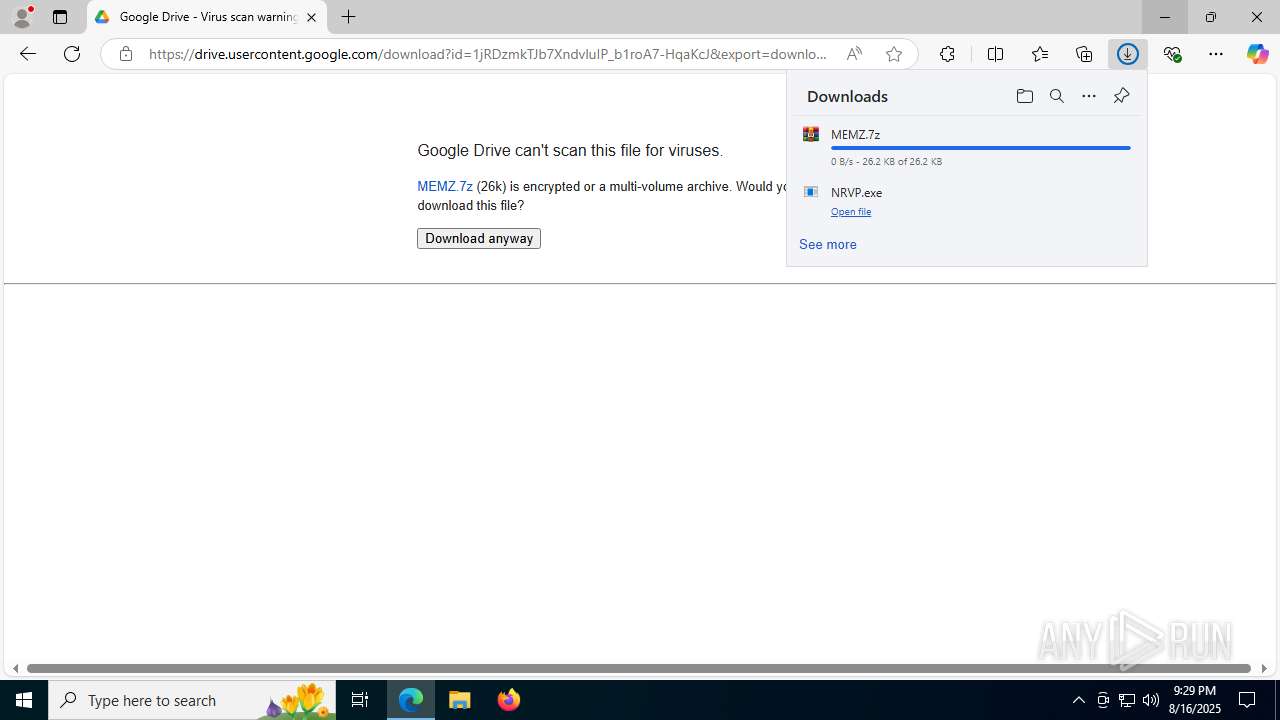
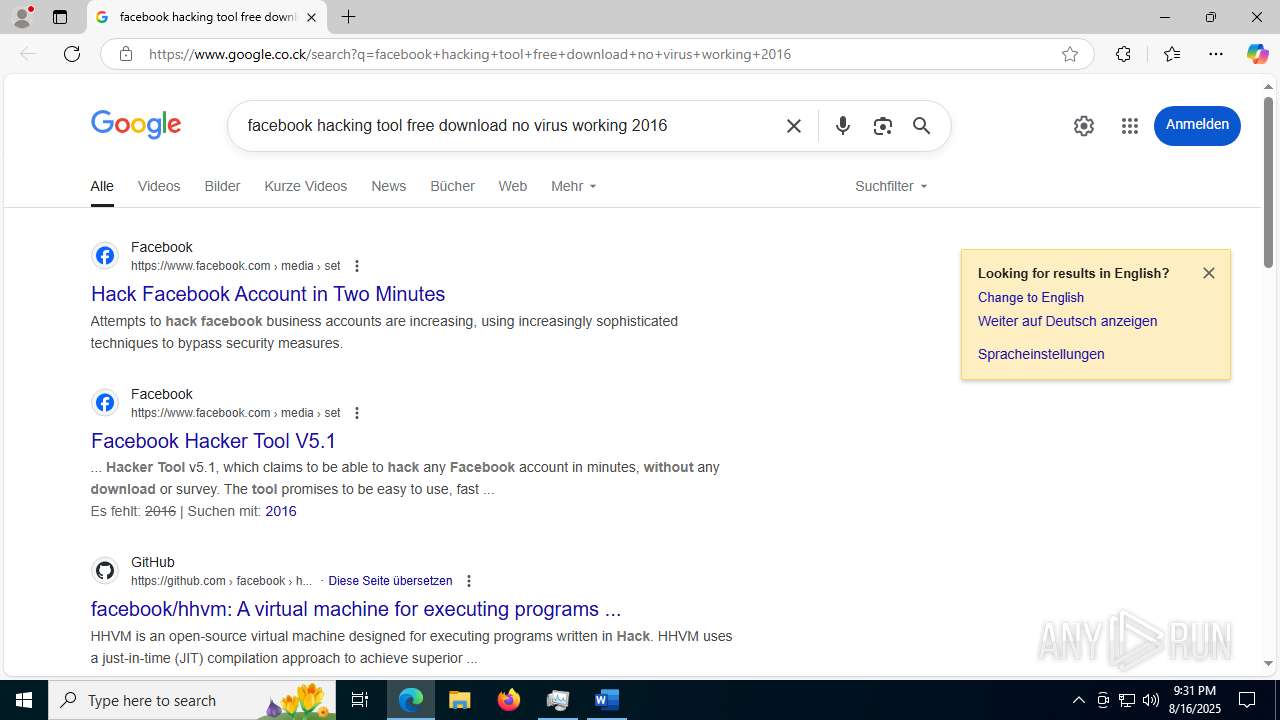
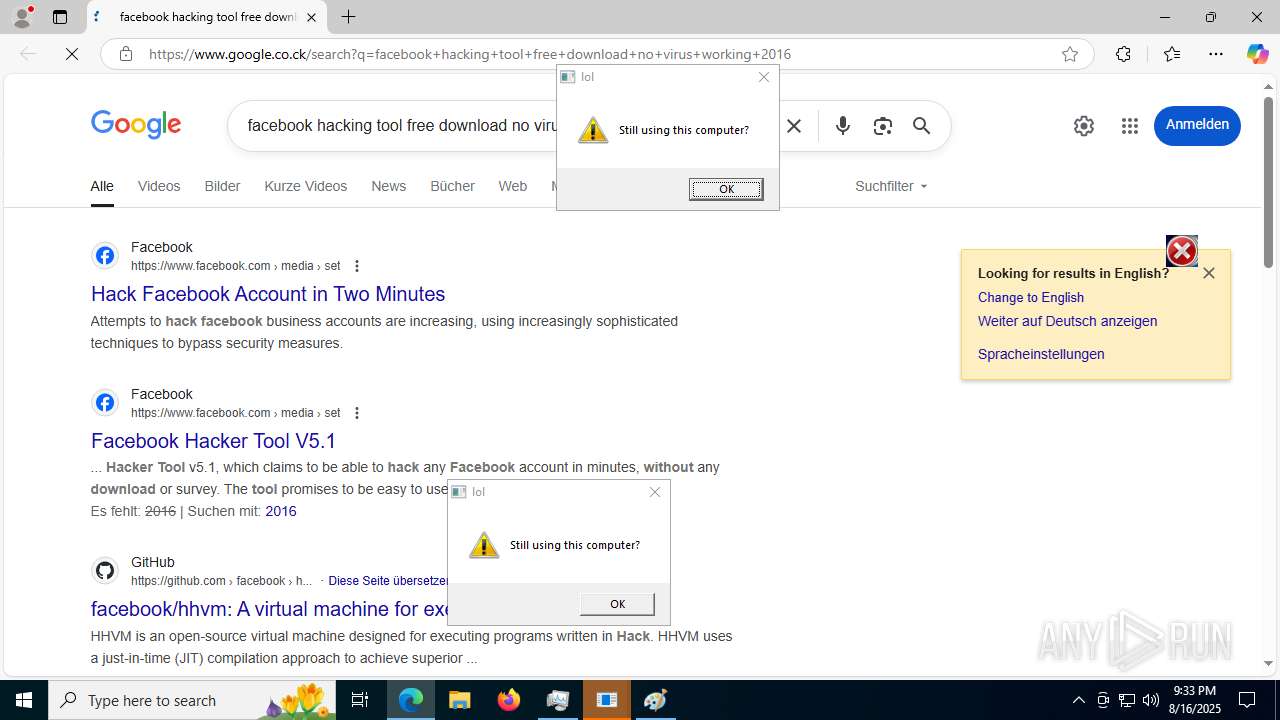
| URL: | https://github.com/NotReal96/Malware/blob/master/MEMZ.md |
| Full analysis: | https://app.any.run/tasks/3da25cb8-b9a6-4a3e-aec1-d5992d589975 |
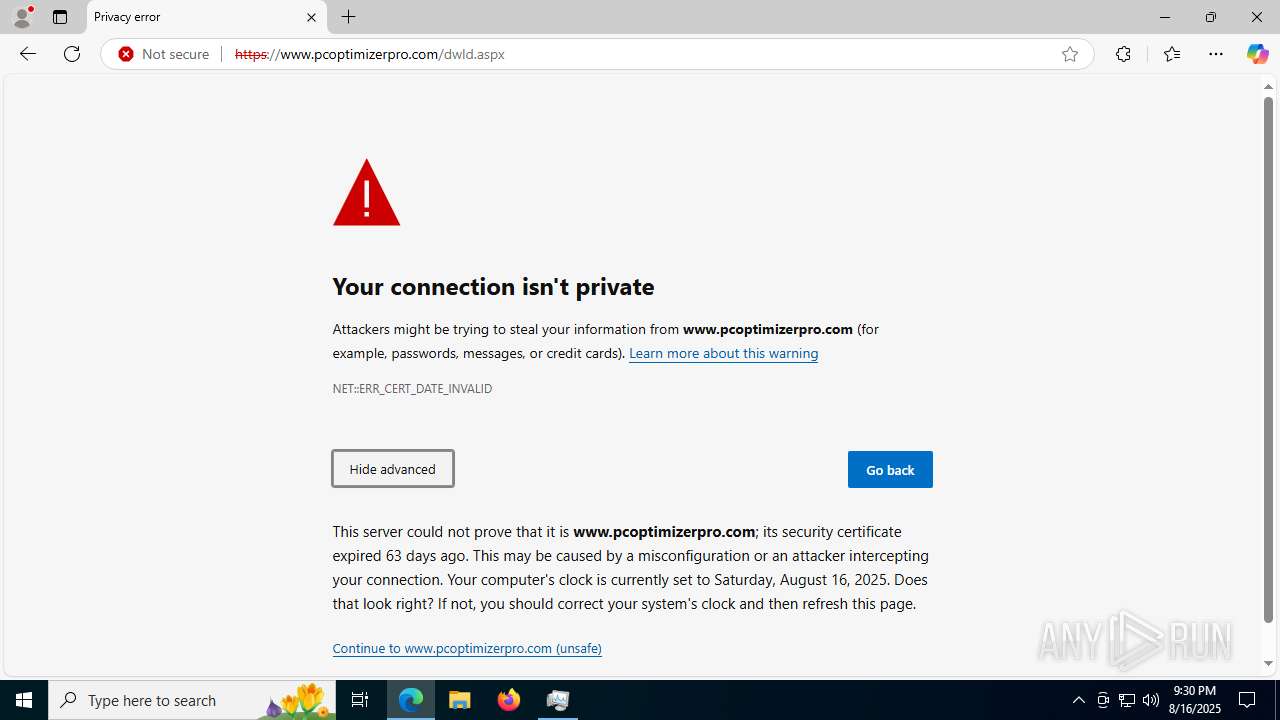
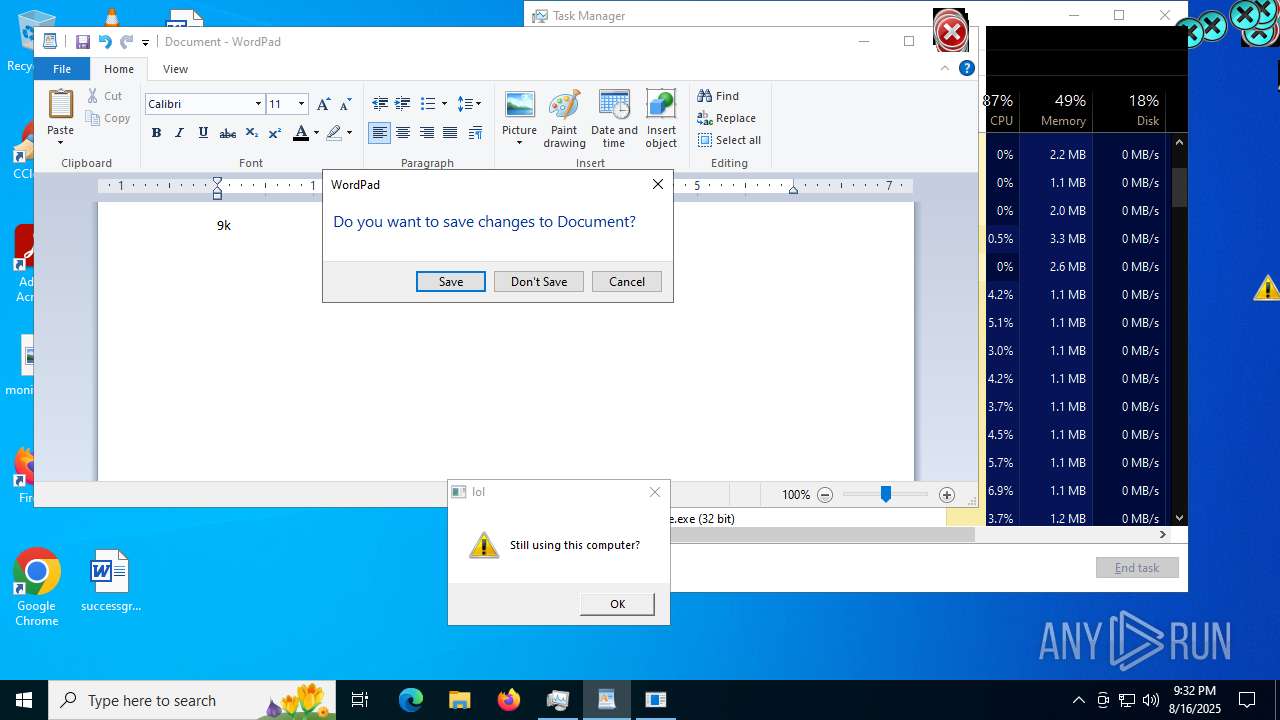
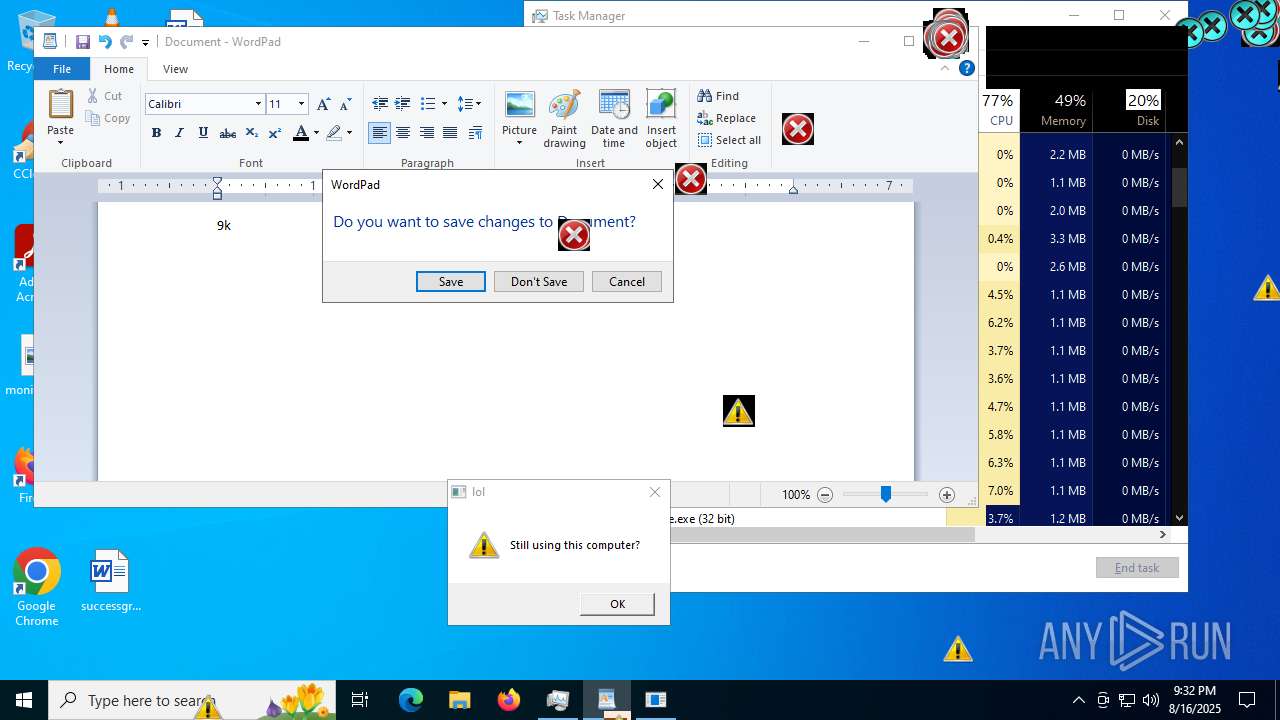
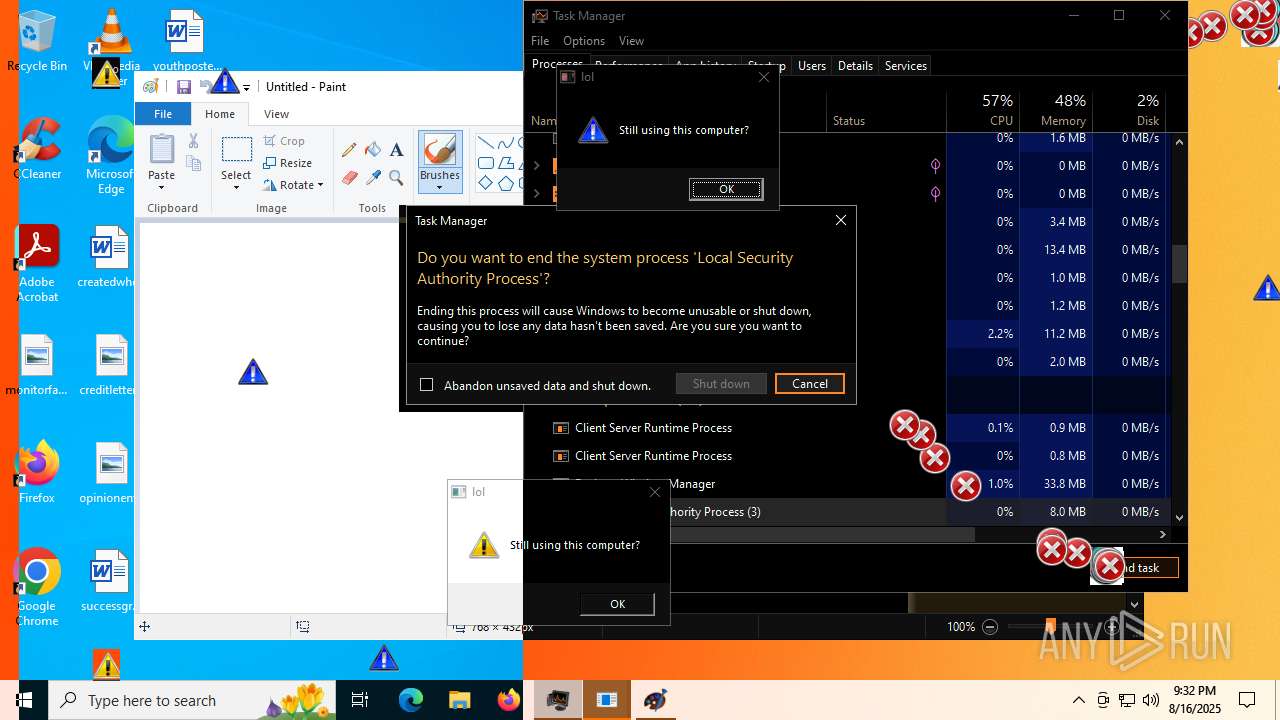
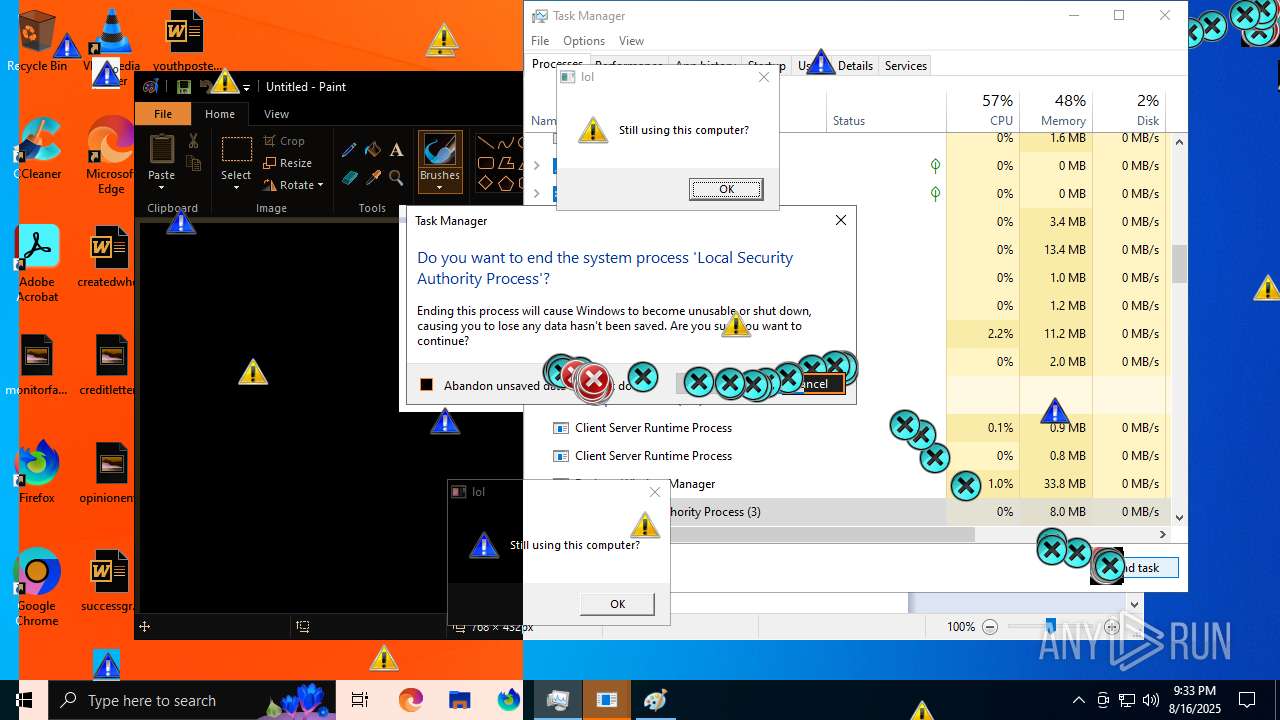
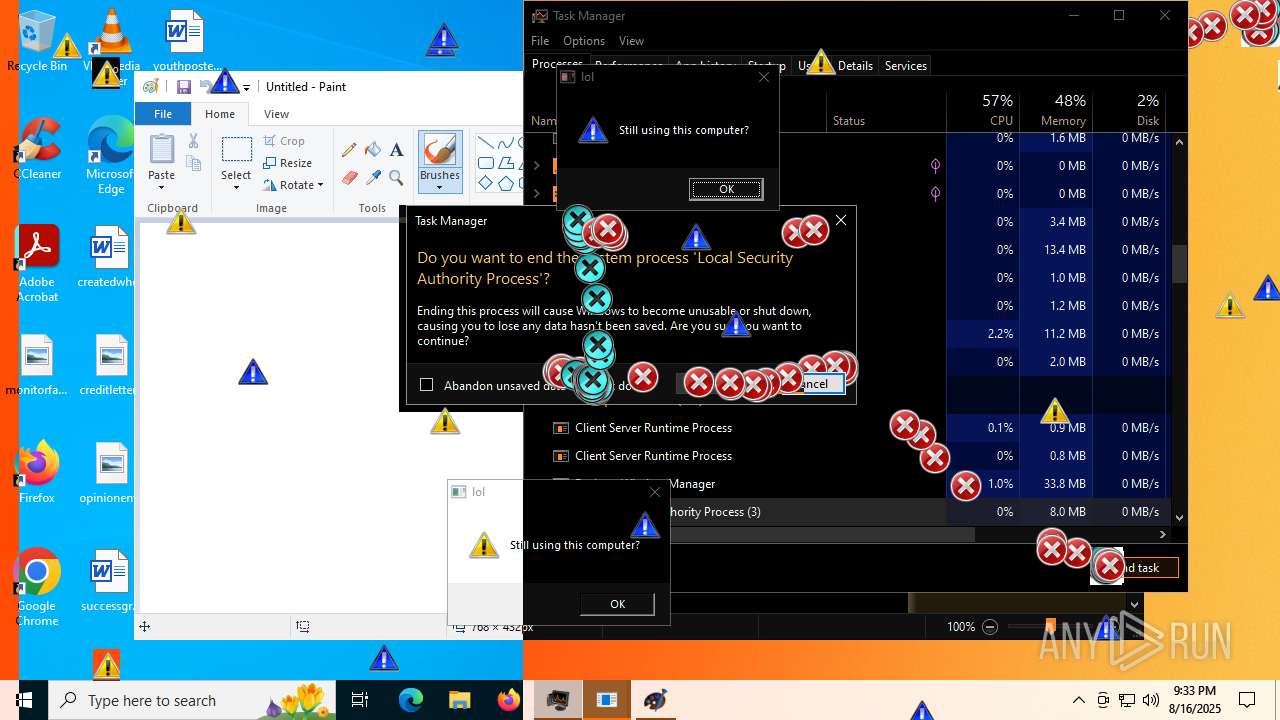
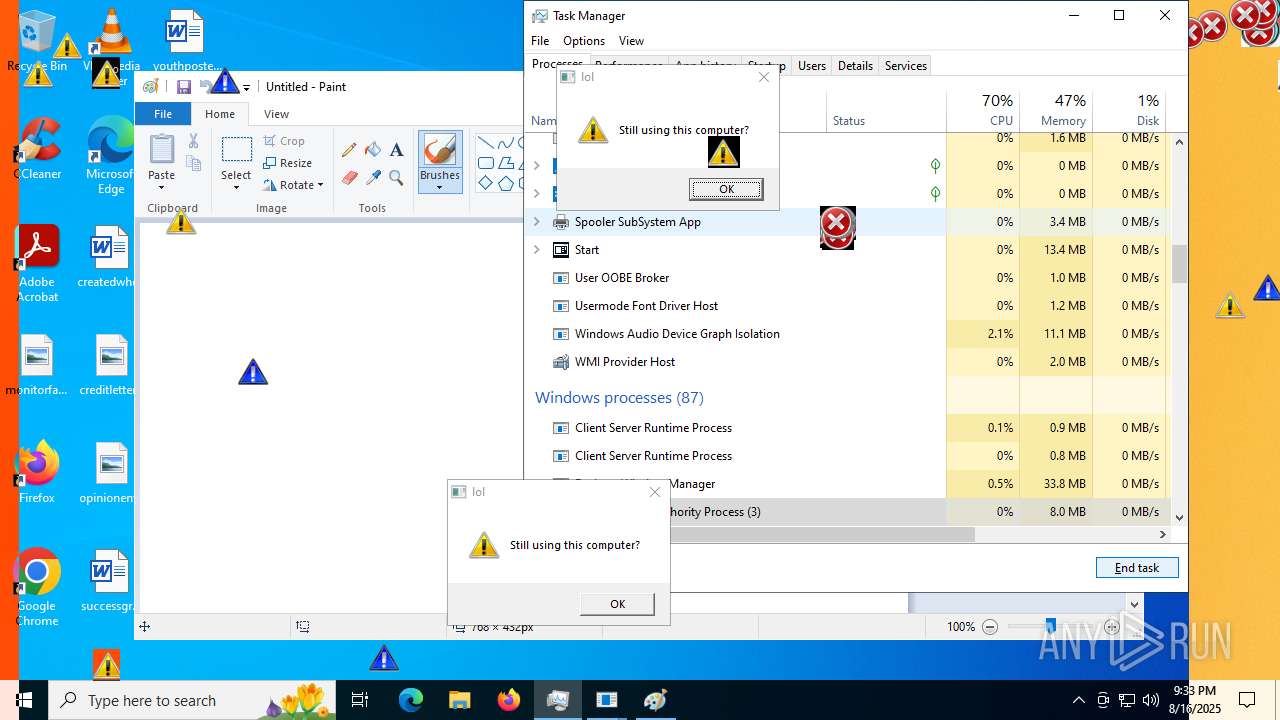
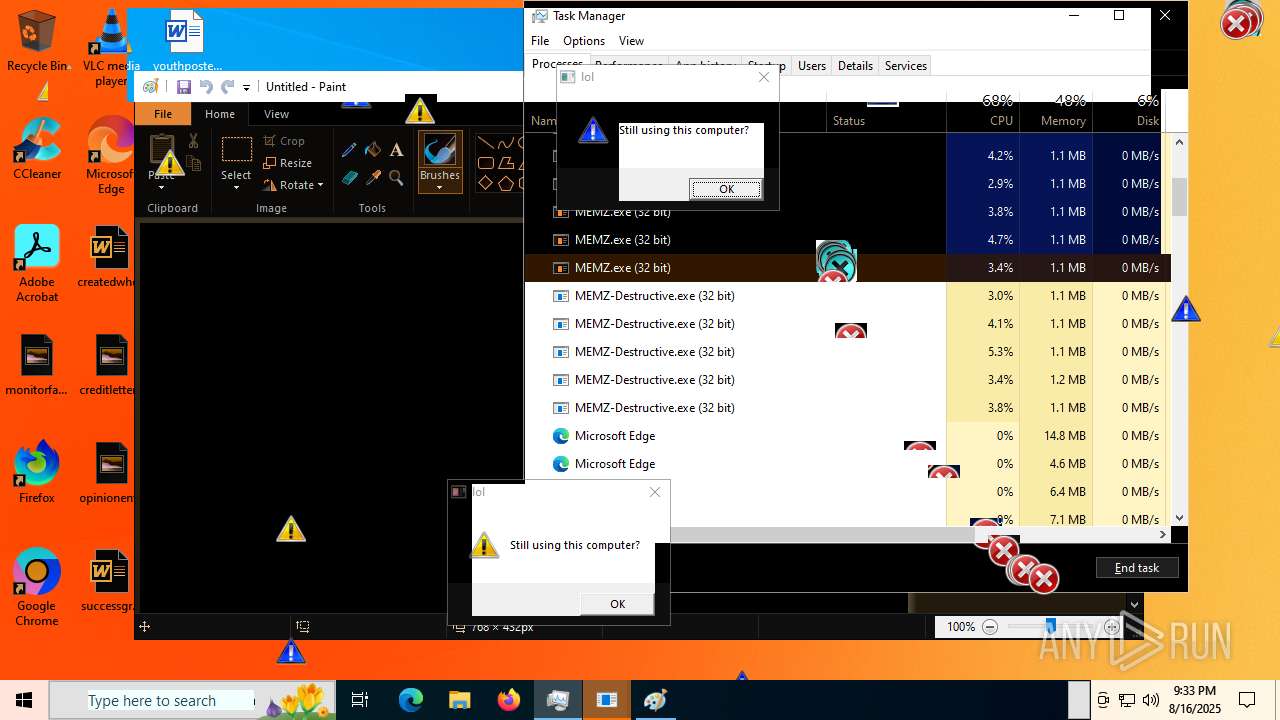
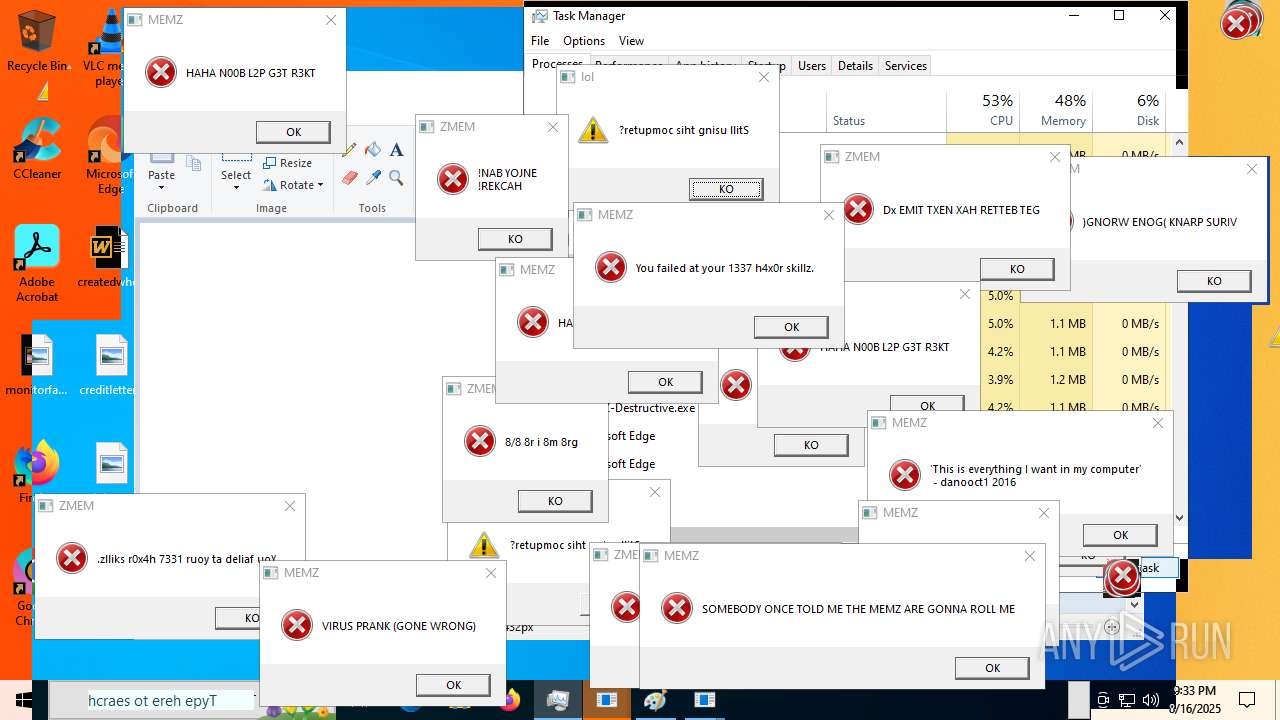
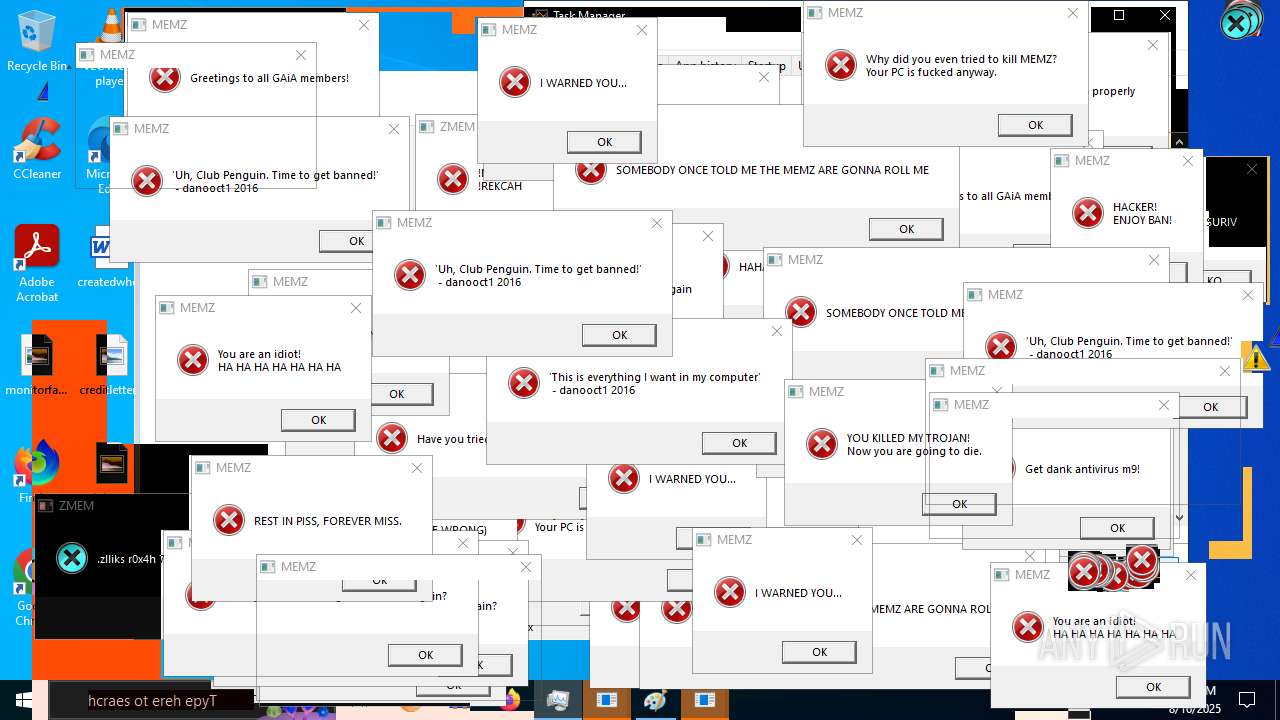
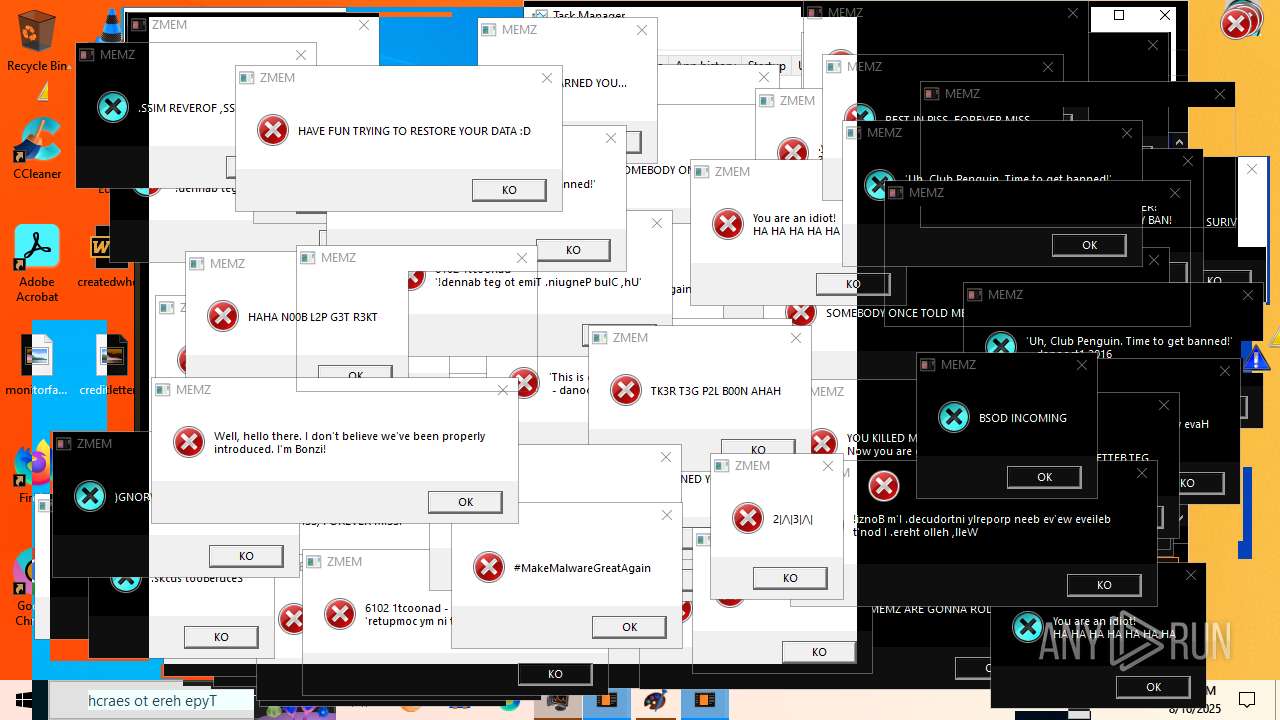
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2025, 21:28:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7B98E23787D1CB31E553364CFBE821FC |
| SHA1: | C7205240927086FB8A169BFB6BD558F574BBD831 |
| SHA256: | 9F3F8616682572644FB209B3D876C3D8569B6AFB5C118FAF820A160CED0973A4 |
| SSDEEP: | 3:N8tEduR3AESTocEJcTEHBQn:2uYR3Ax+6 |
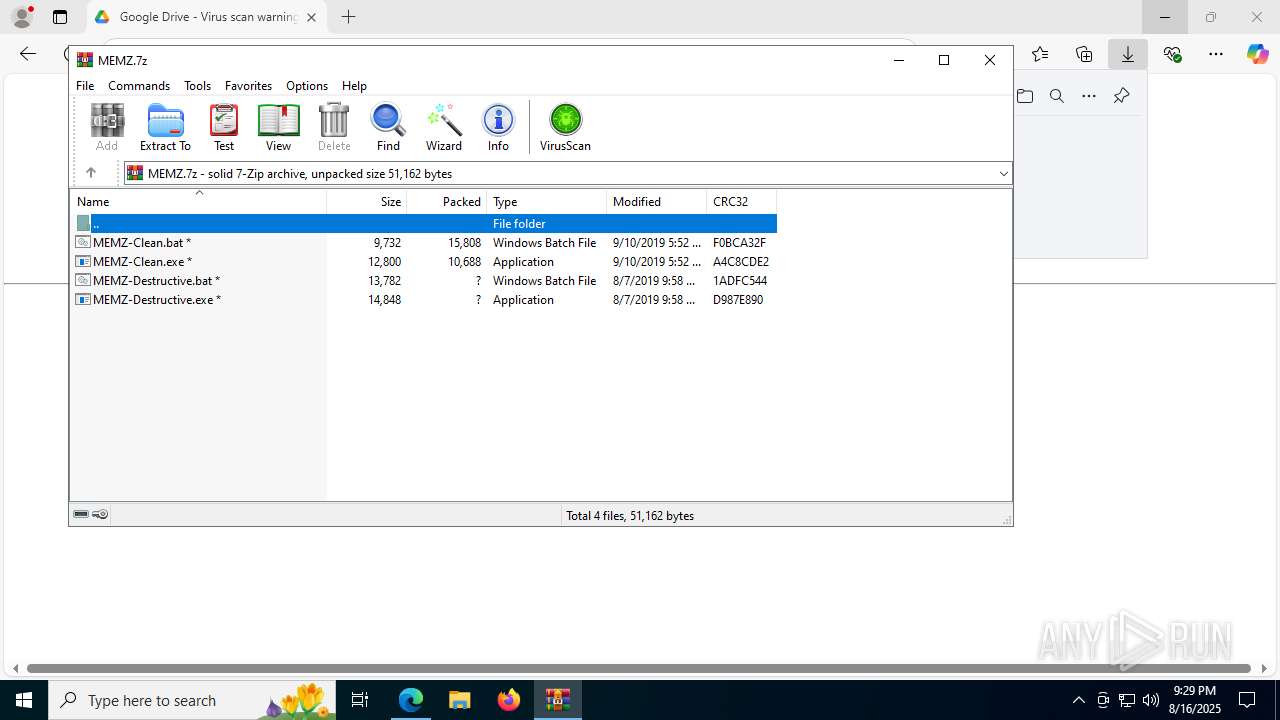
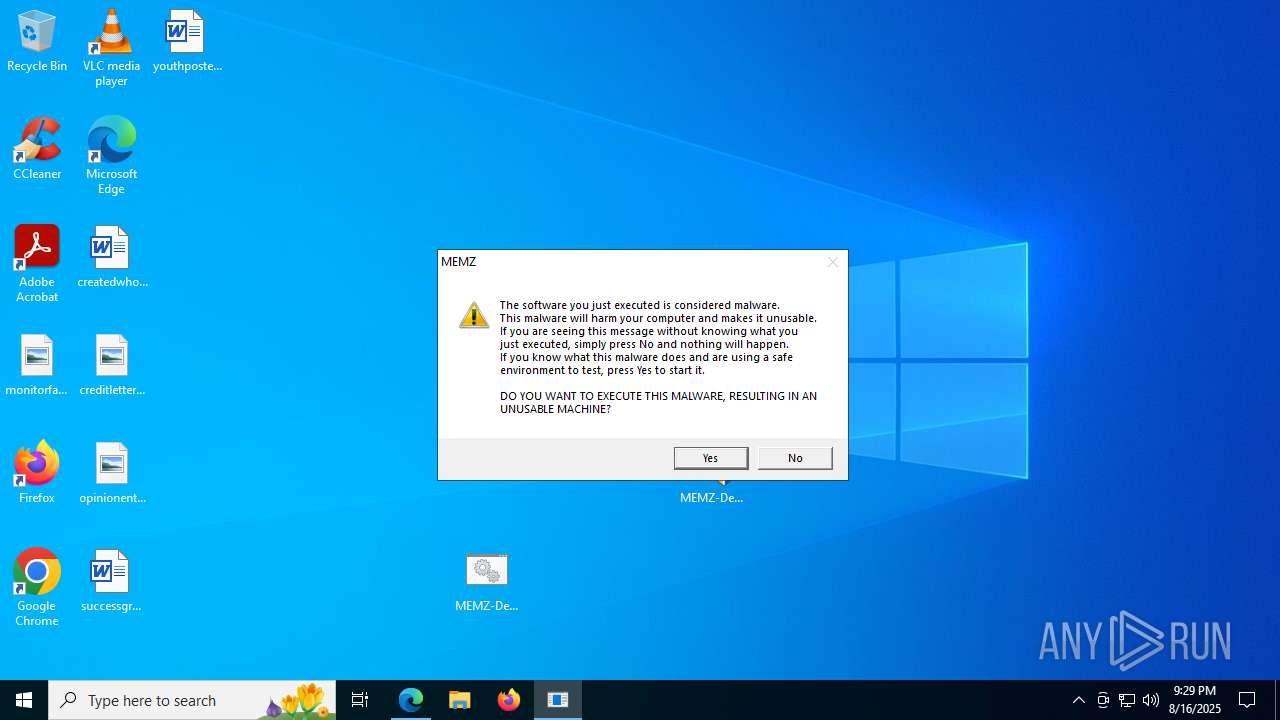
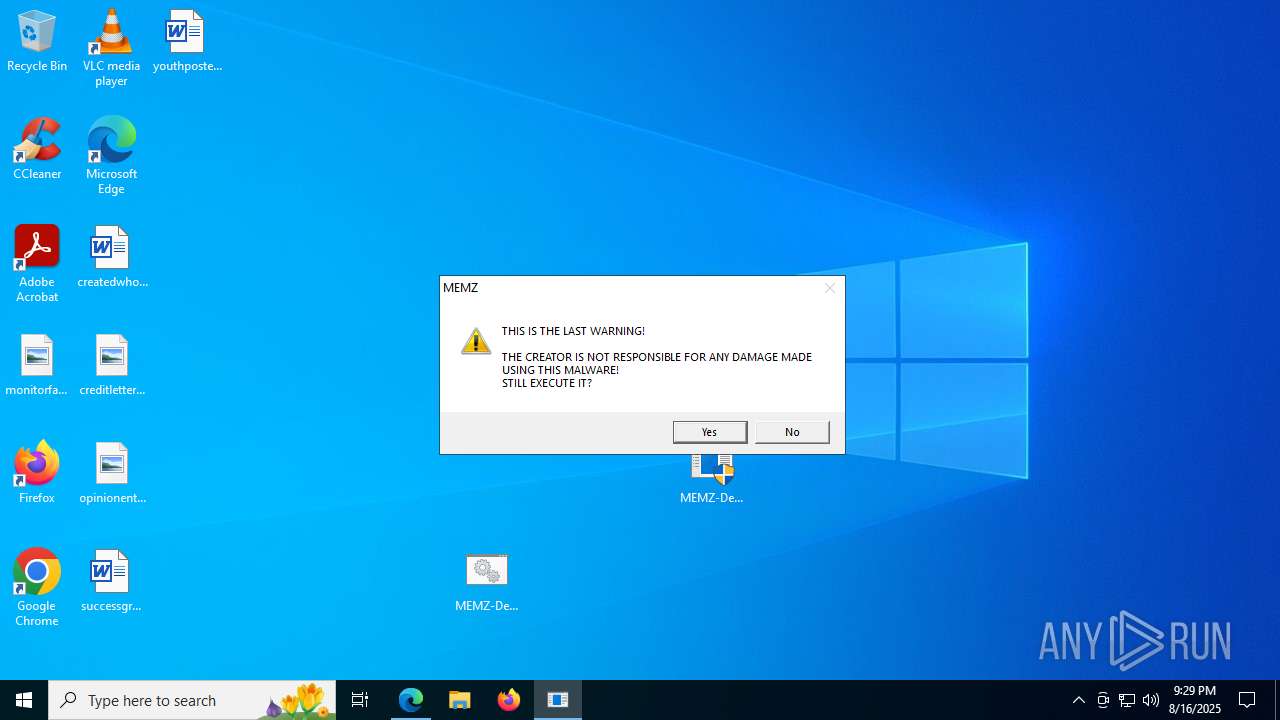
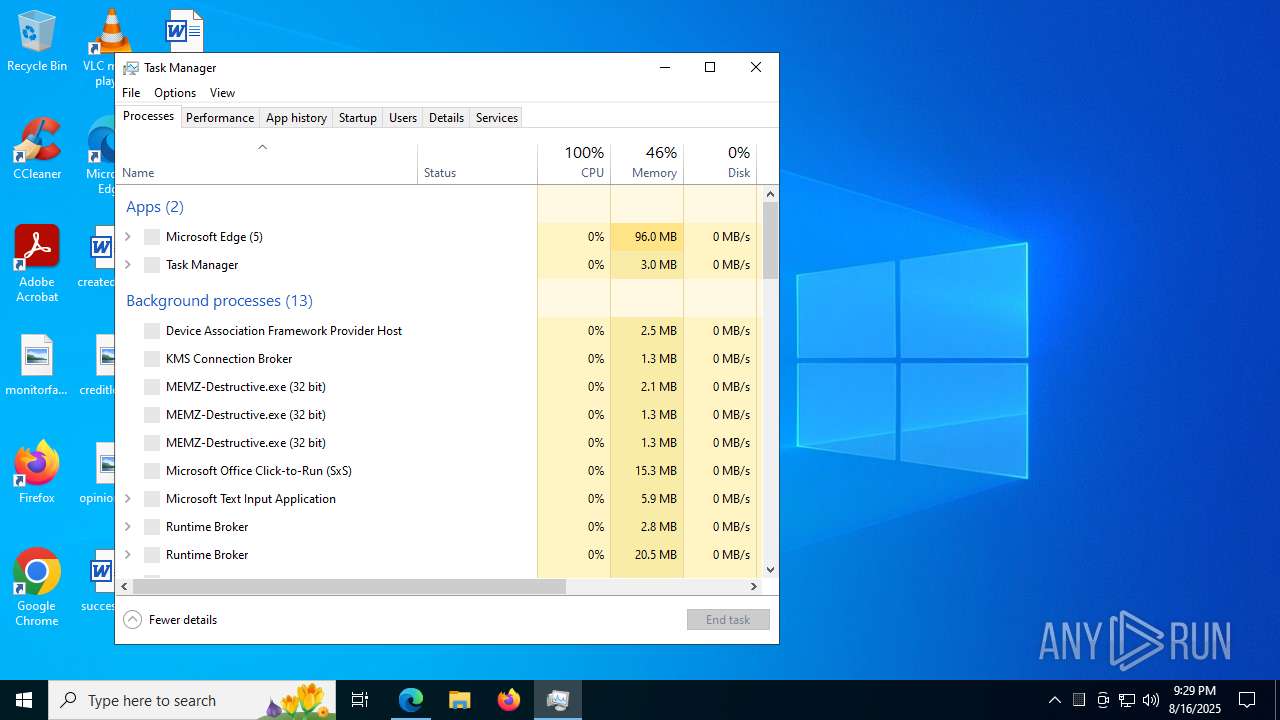
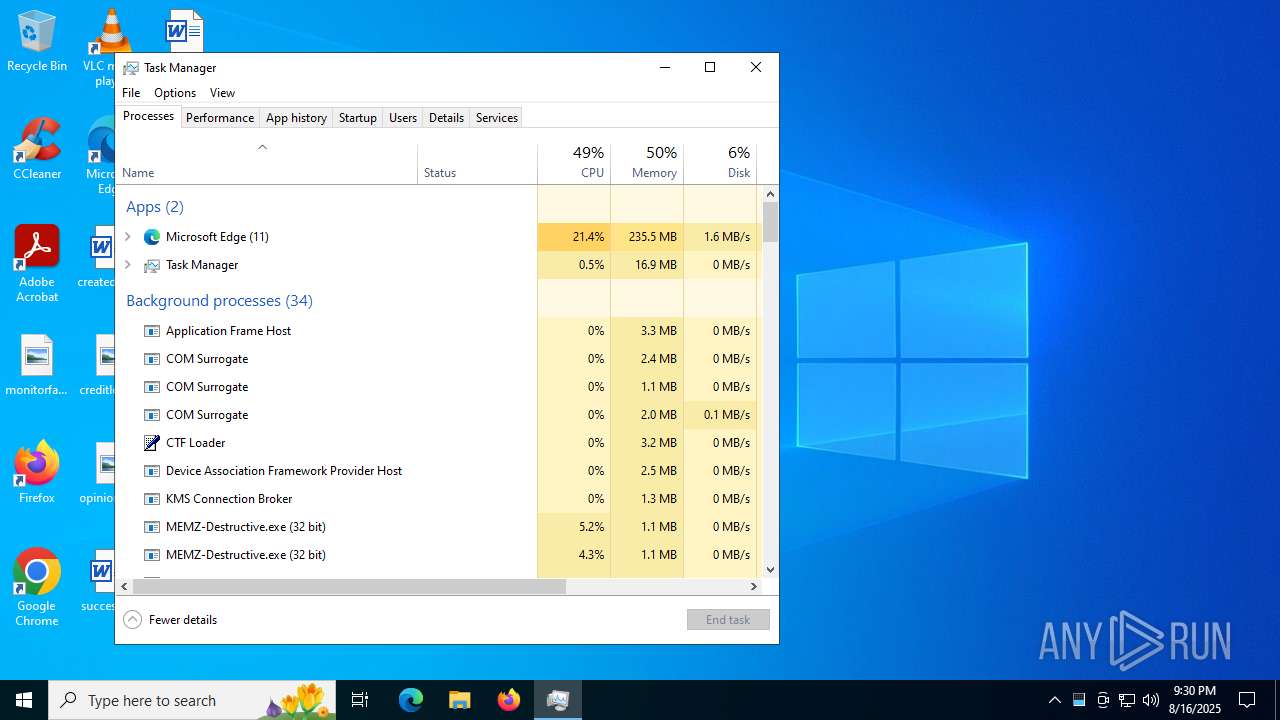
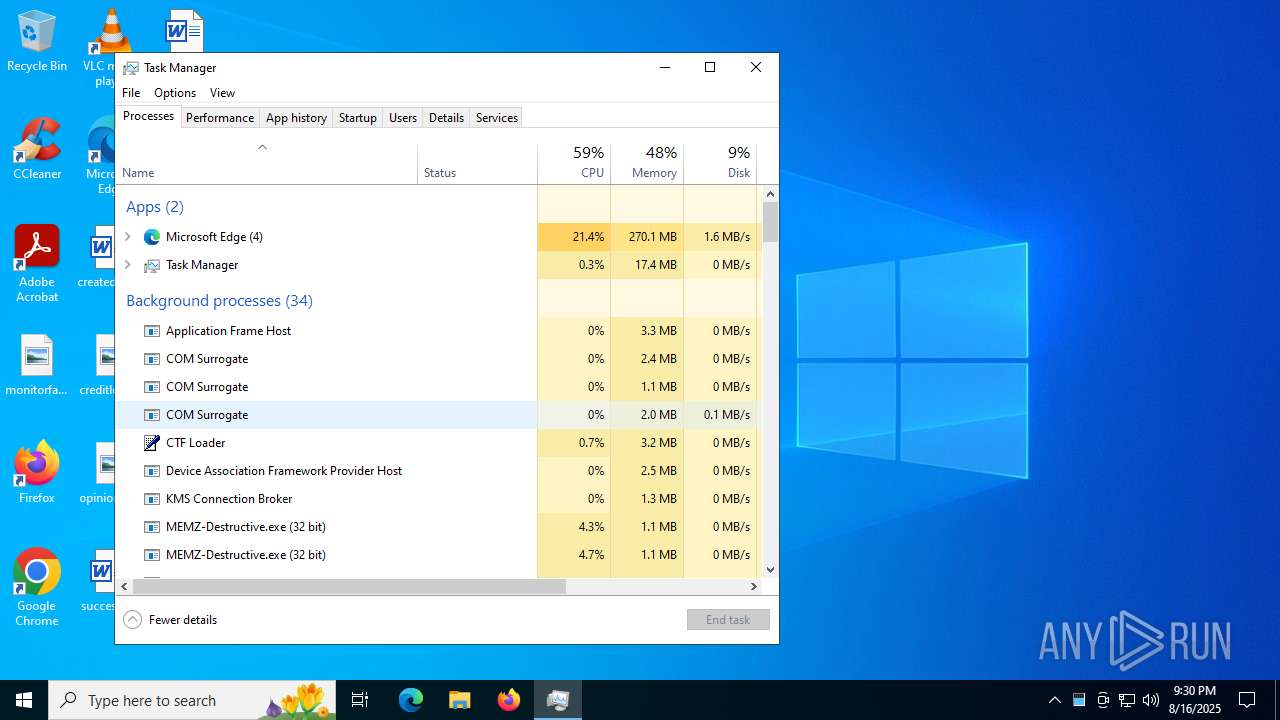
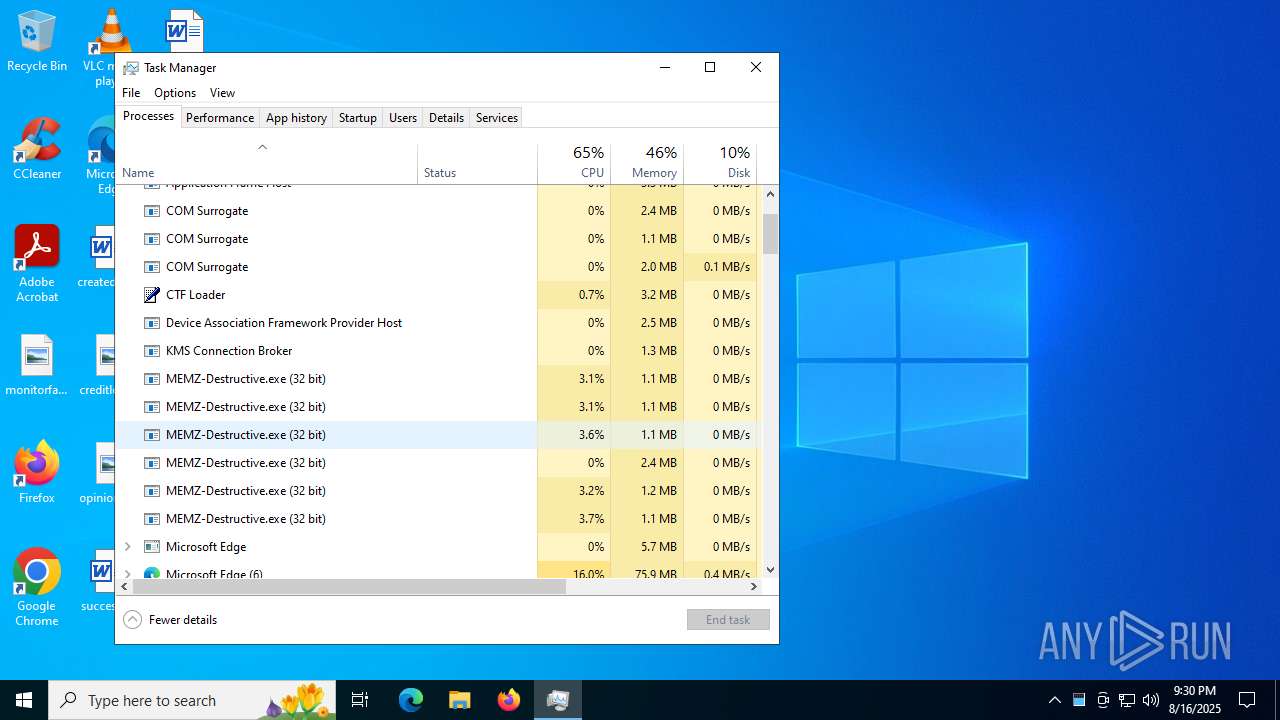
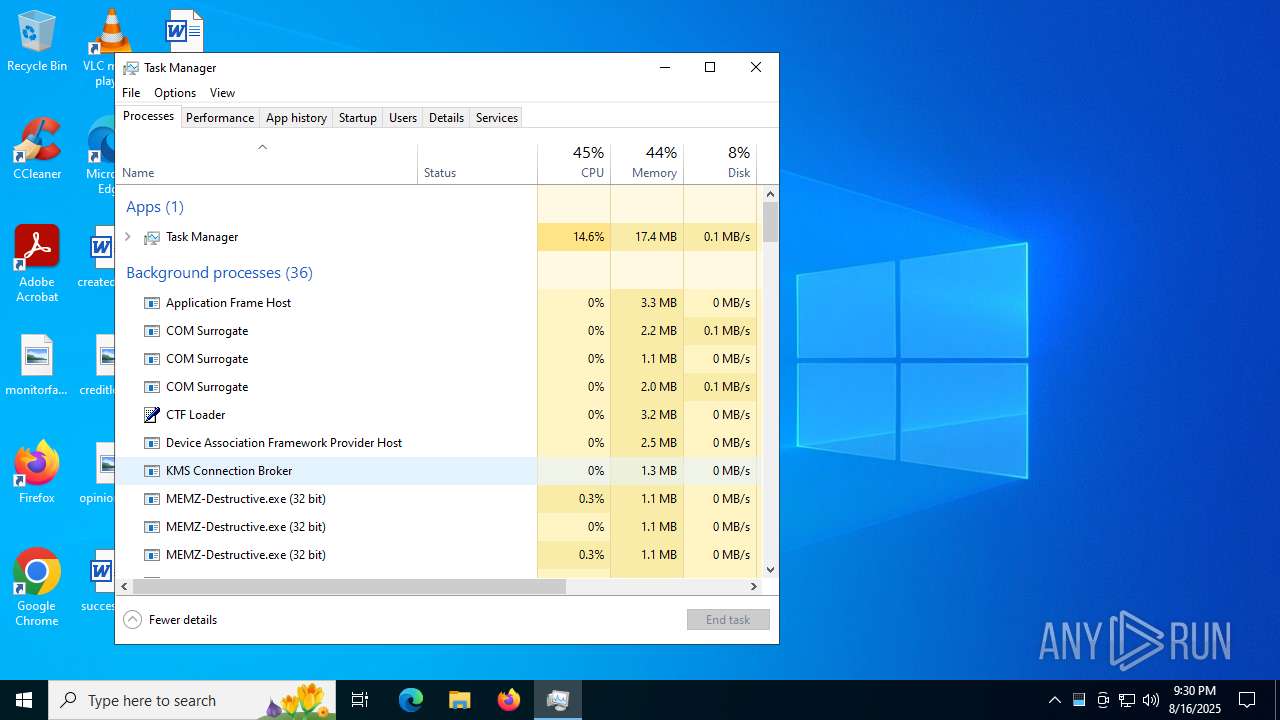
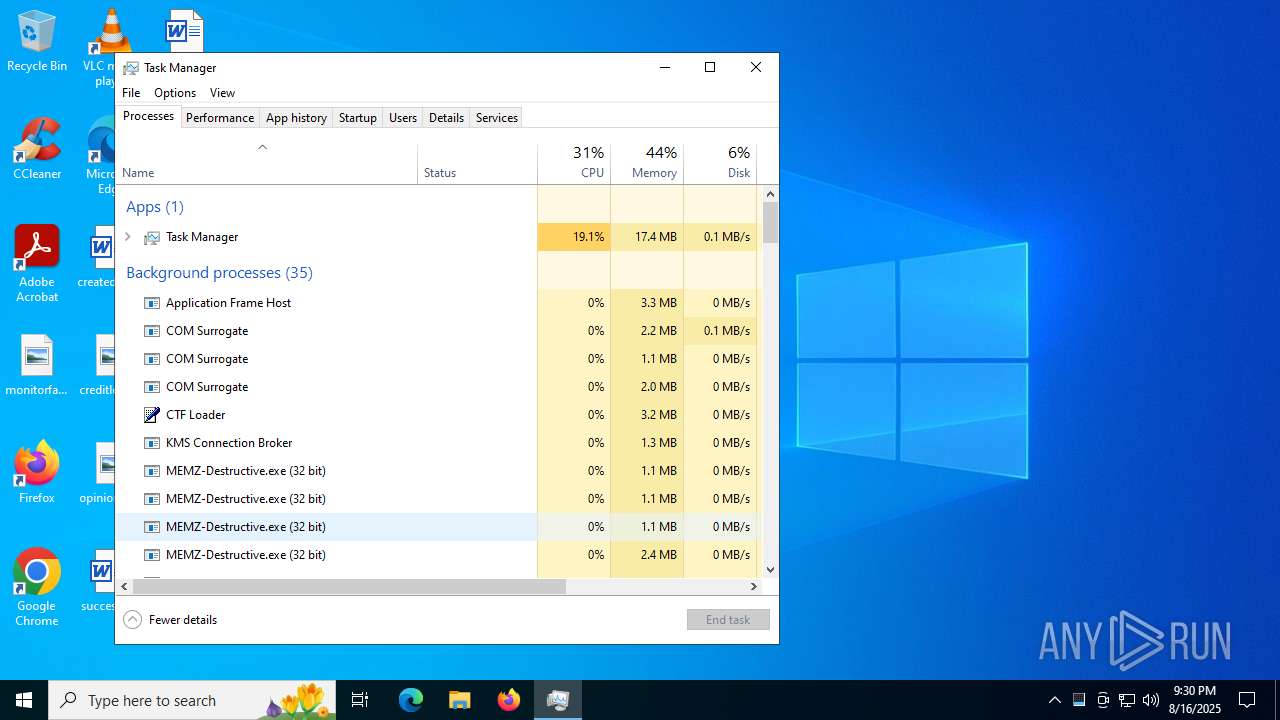
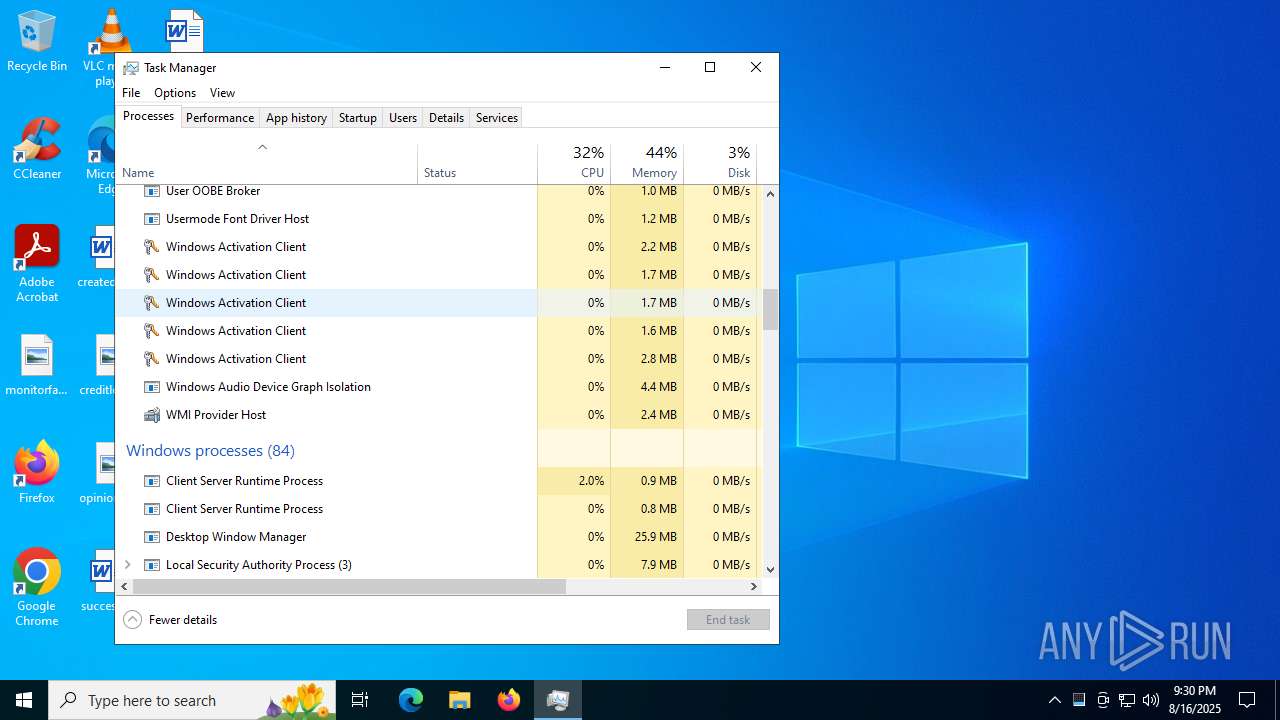
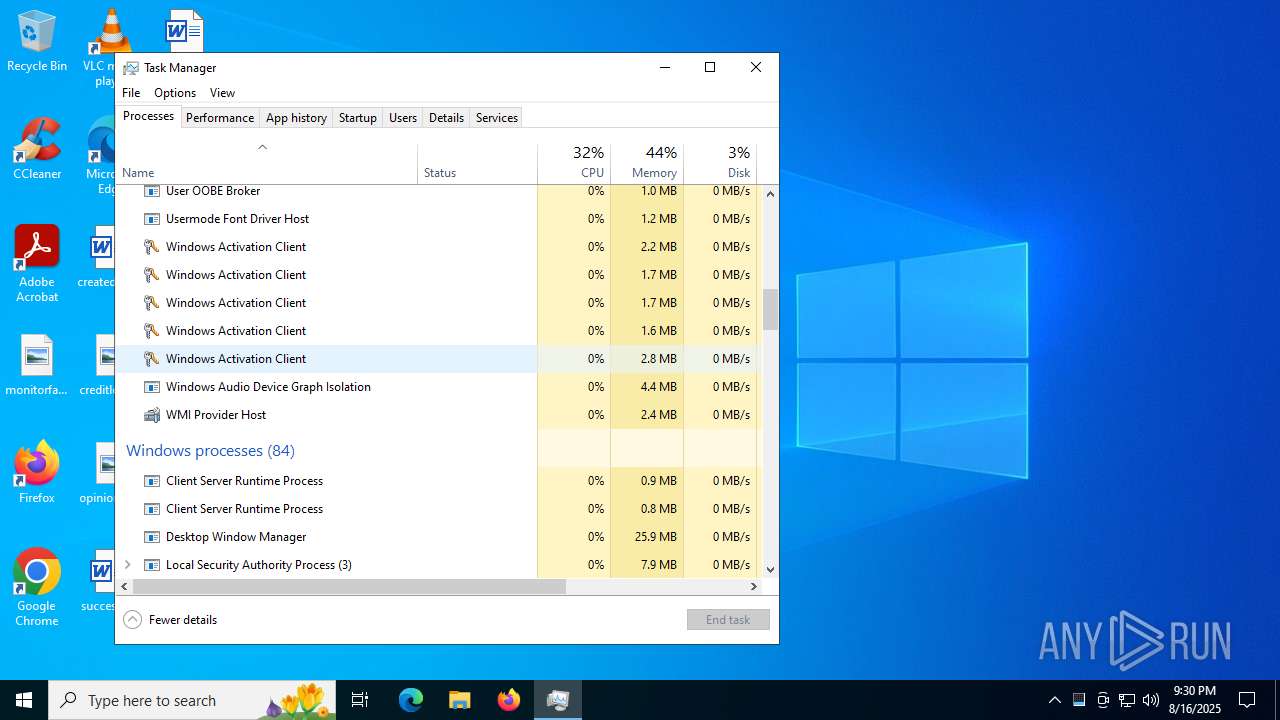
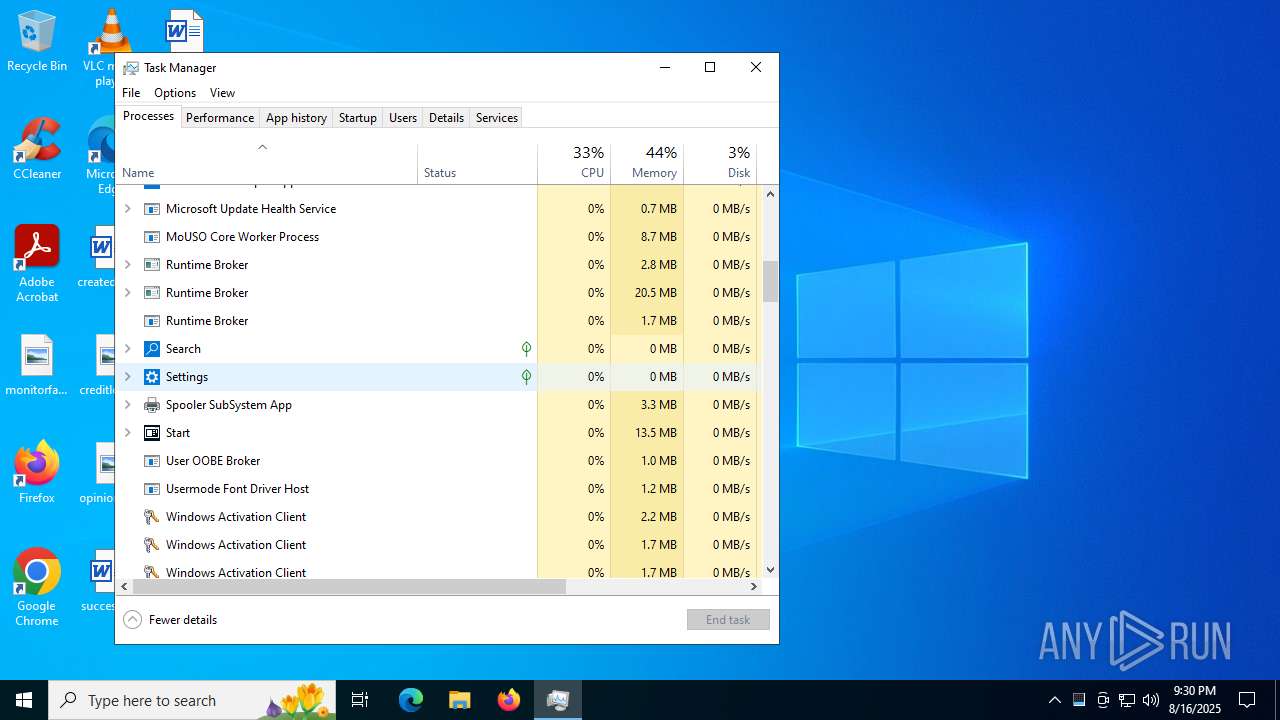
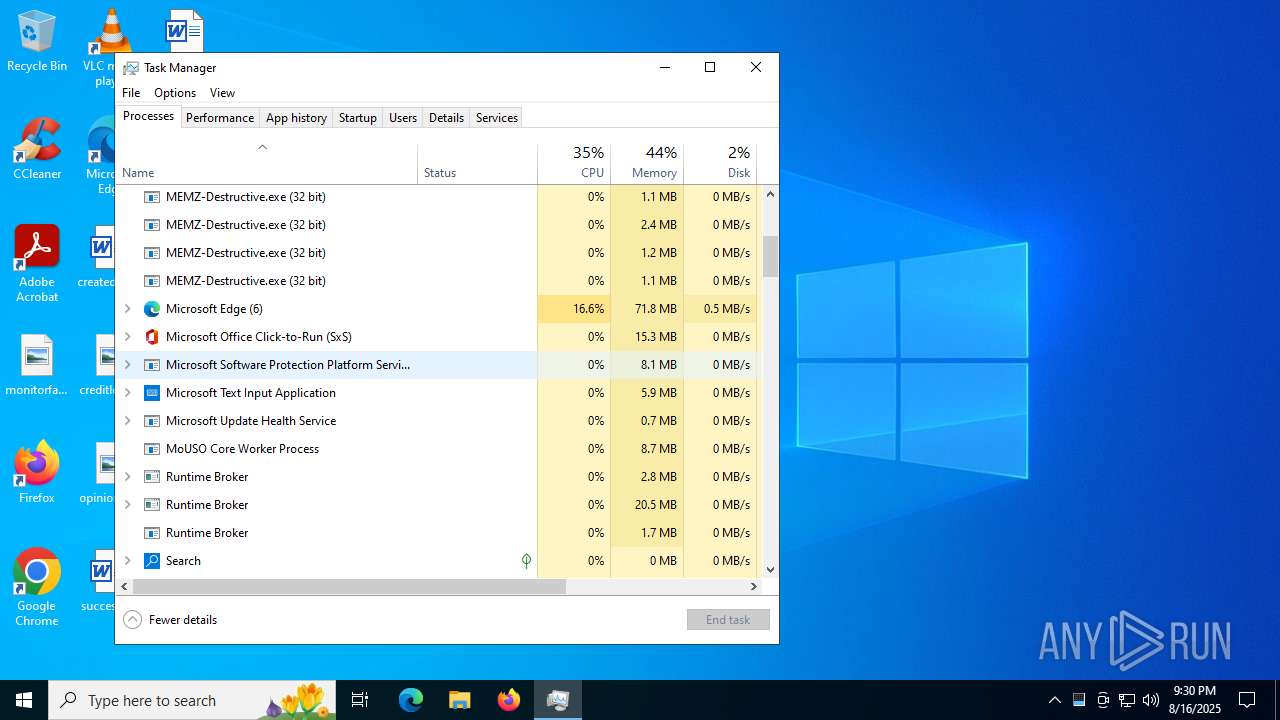
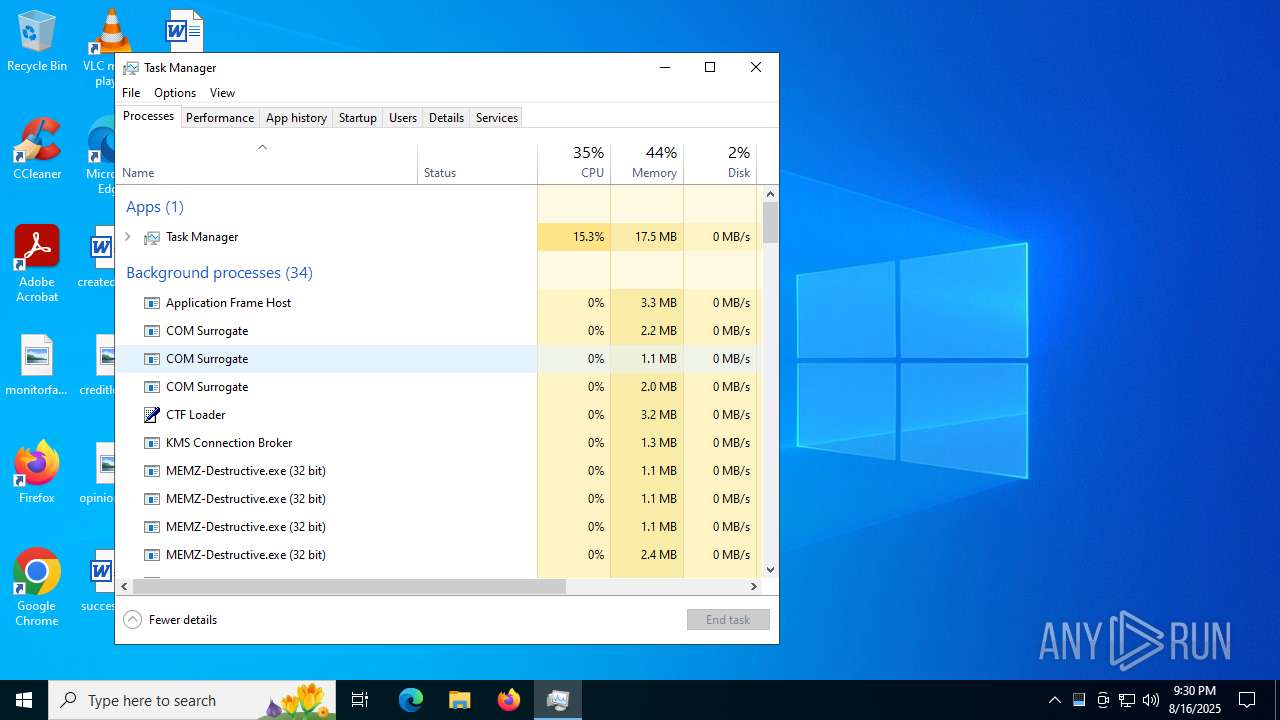
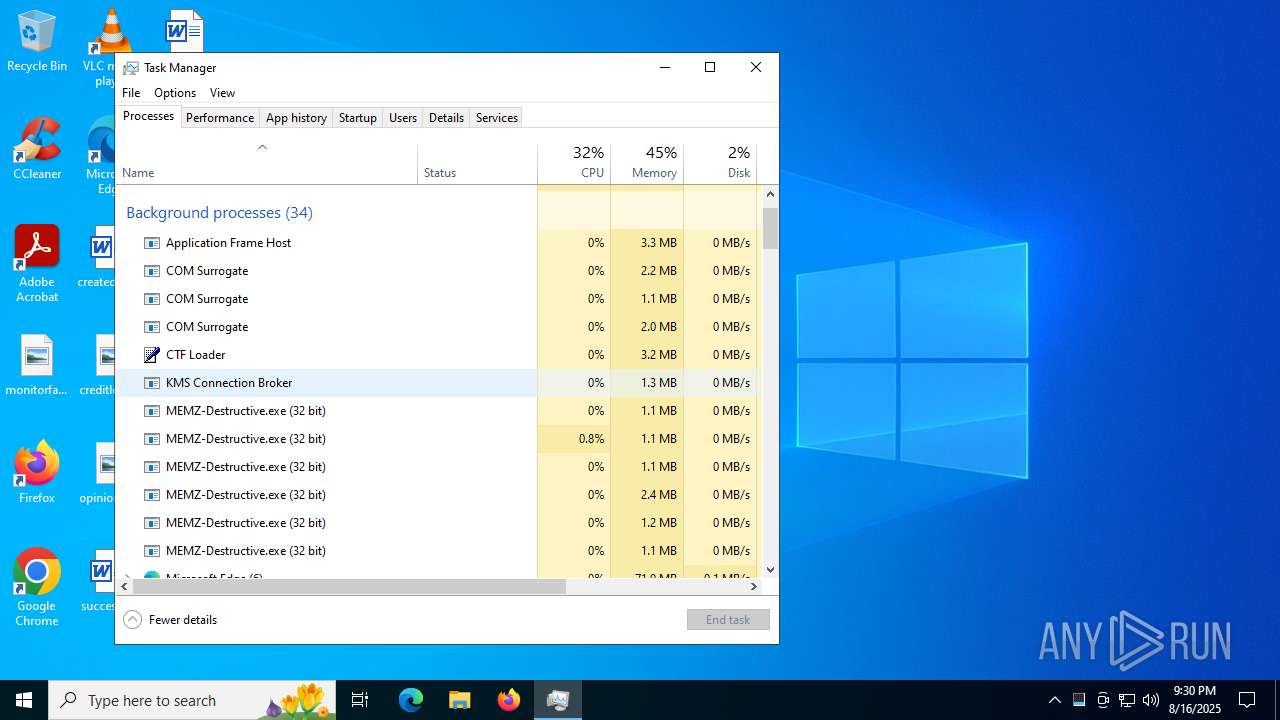
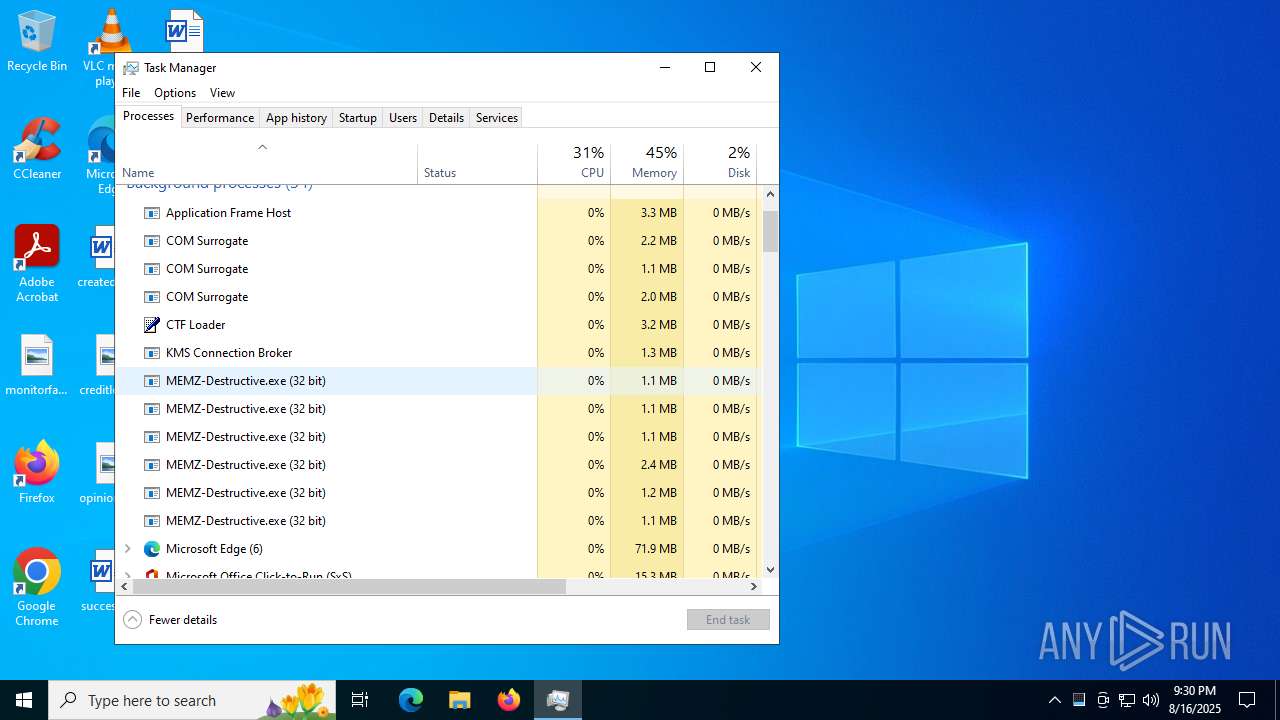
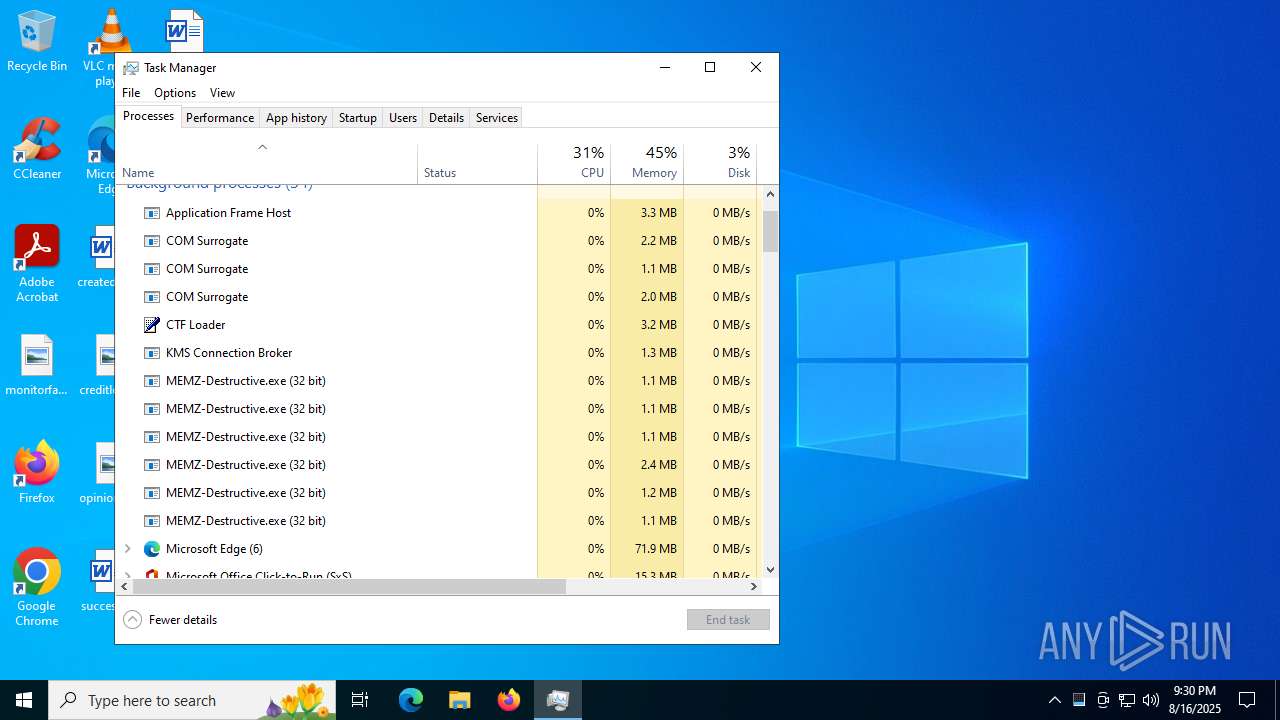
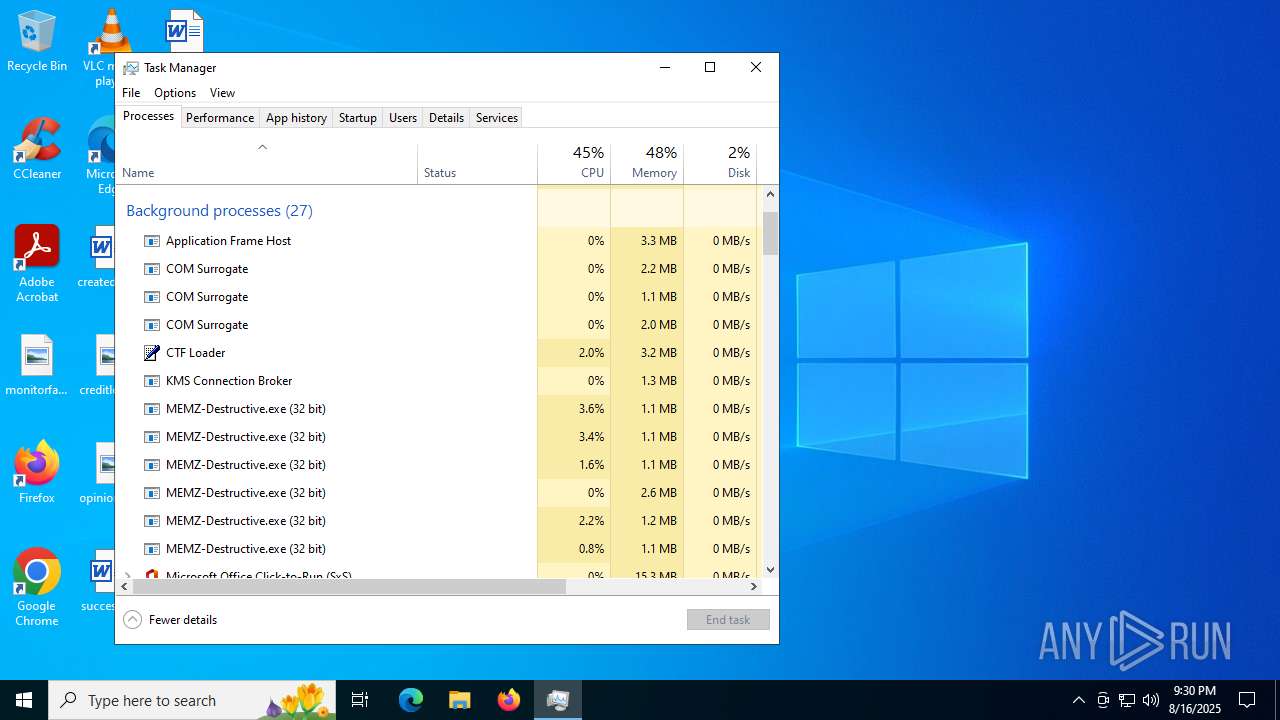
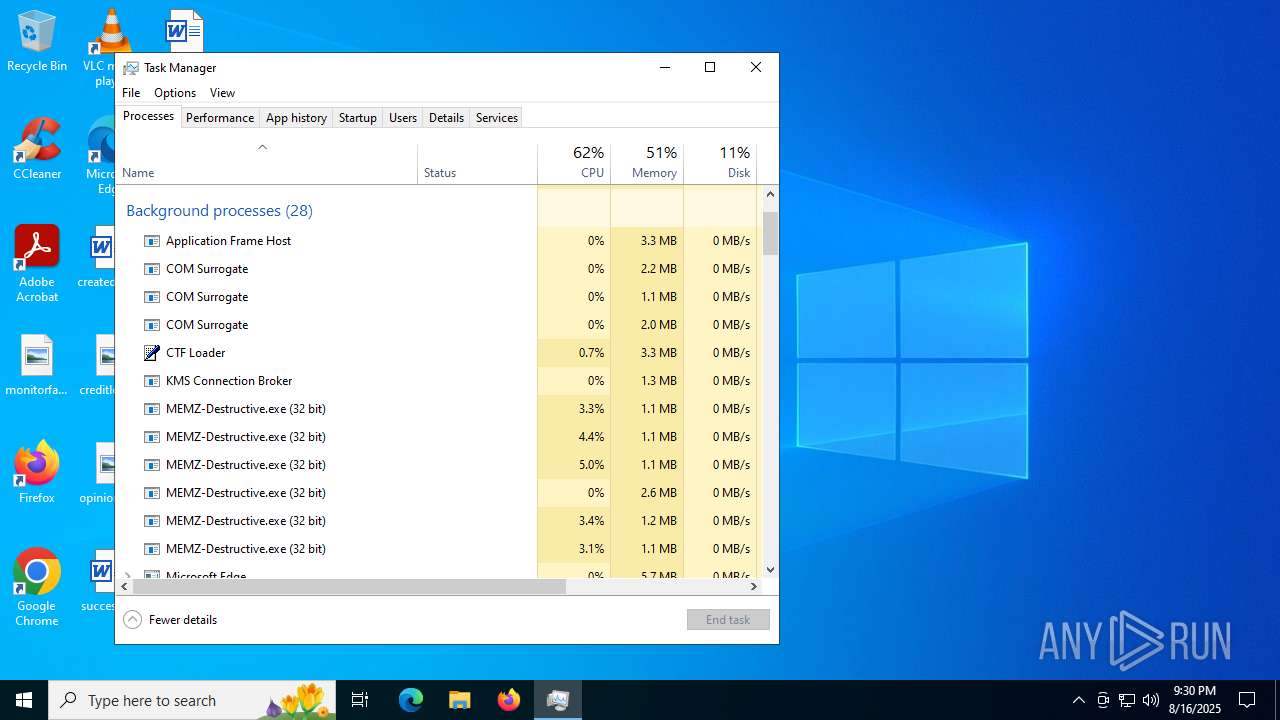
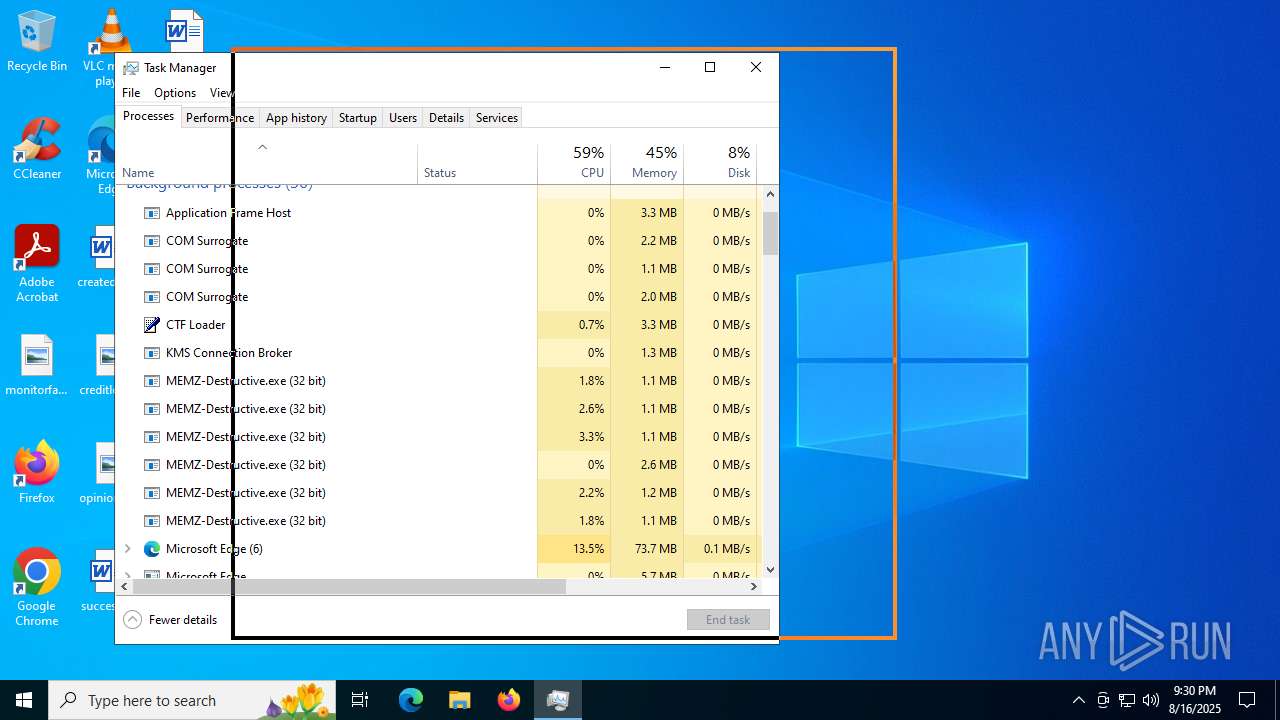
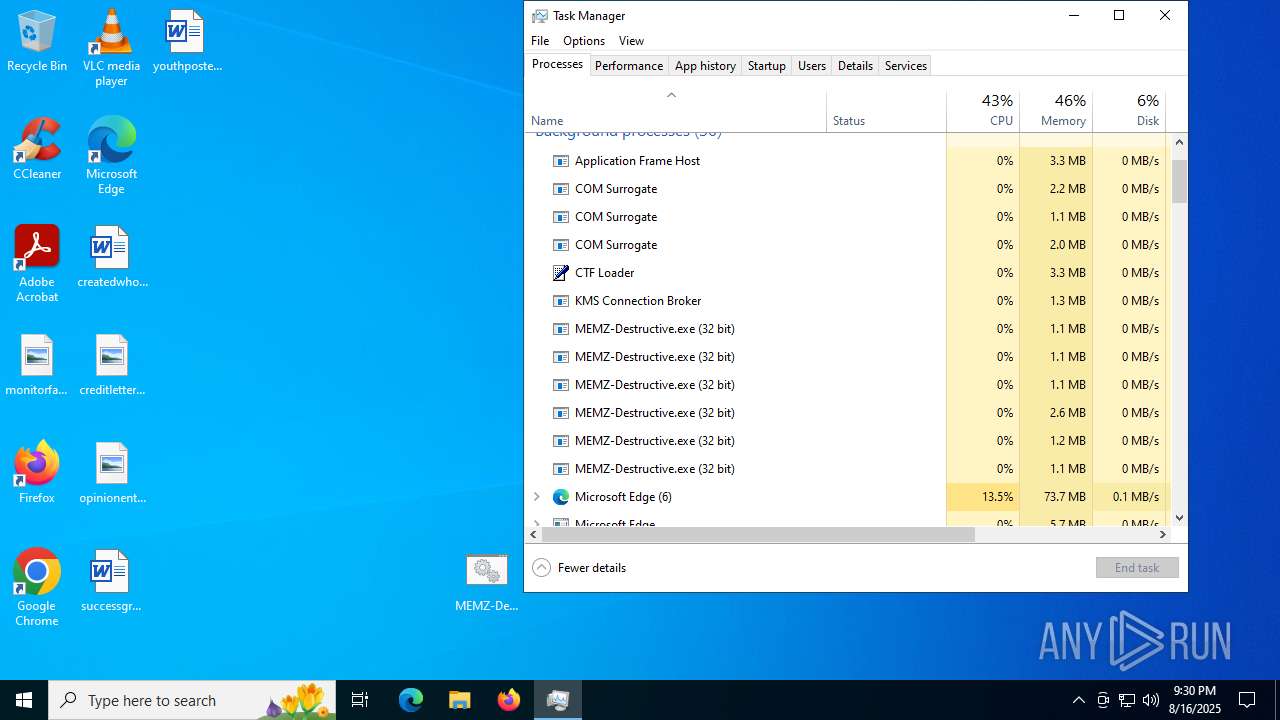
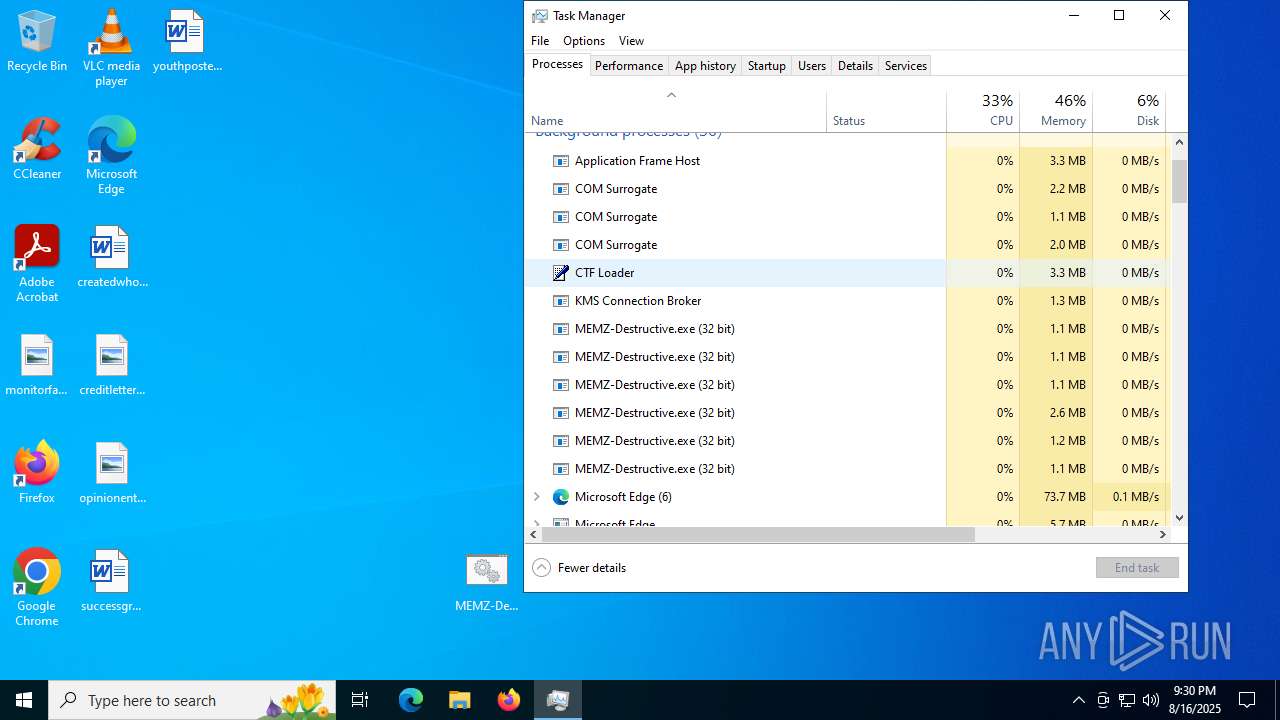
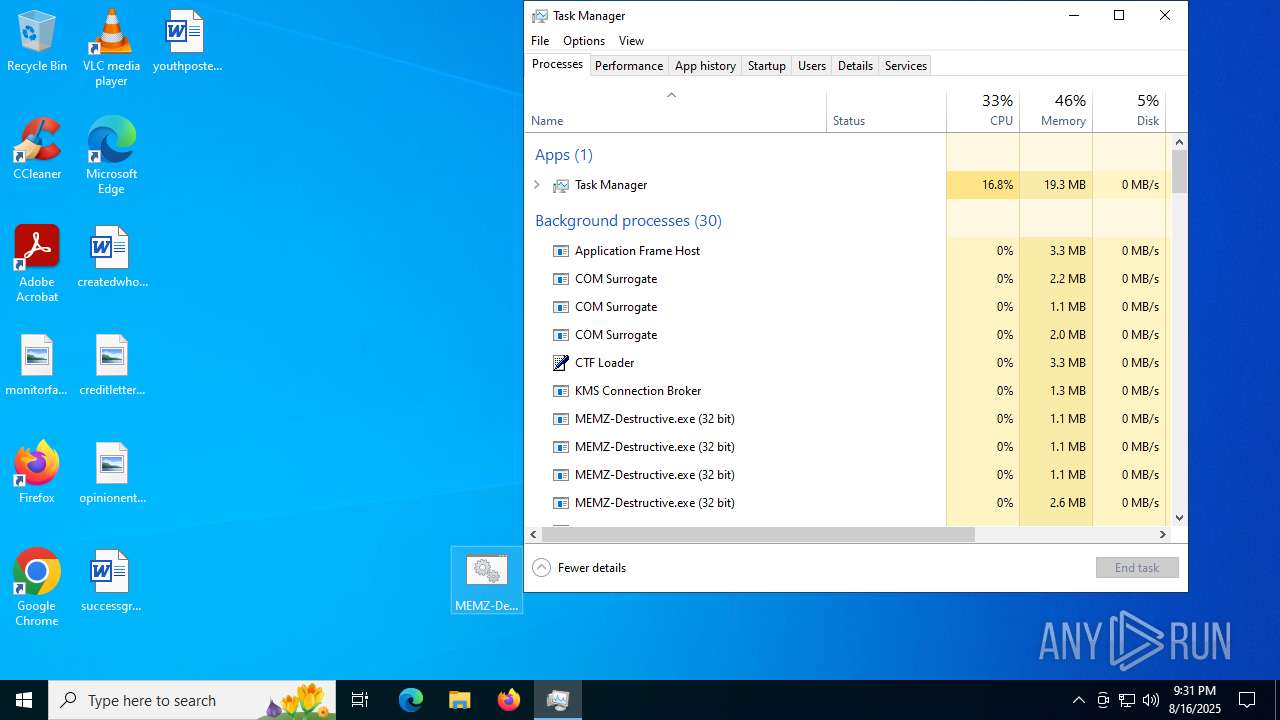
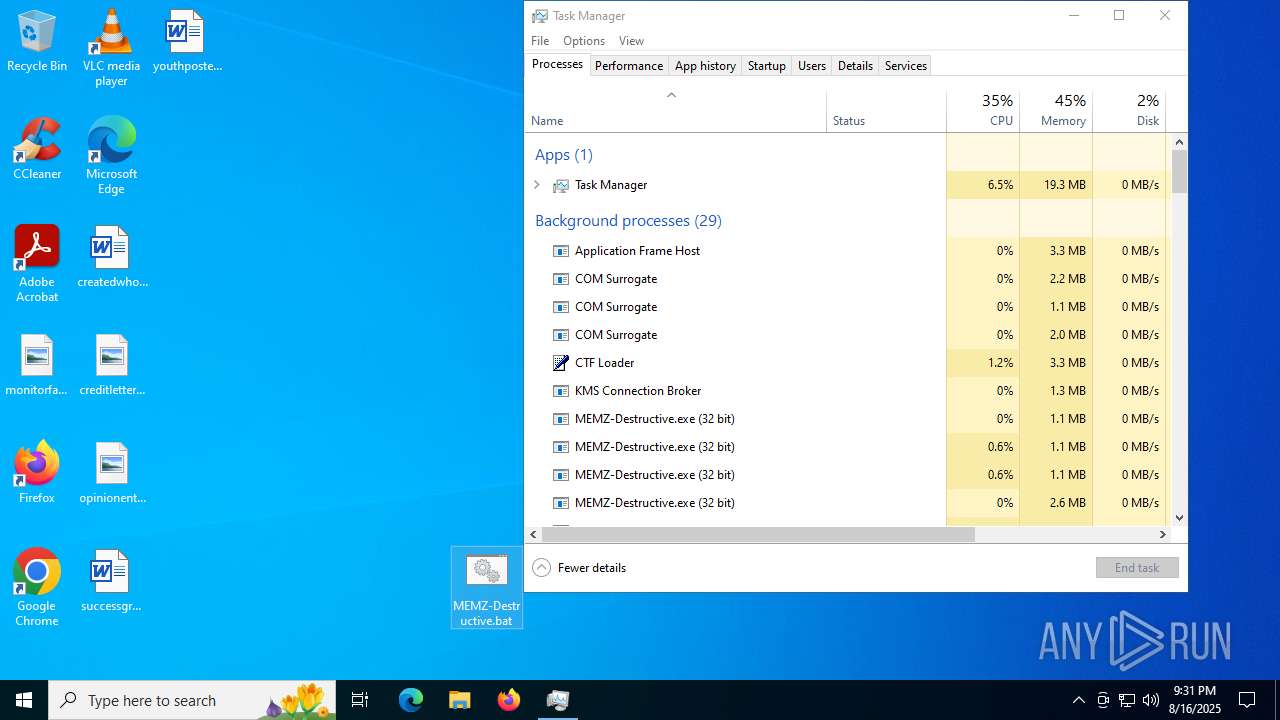
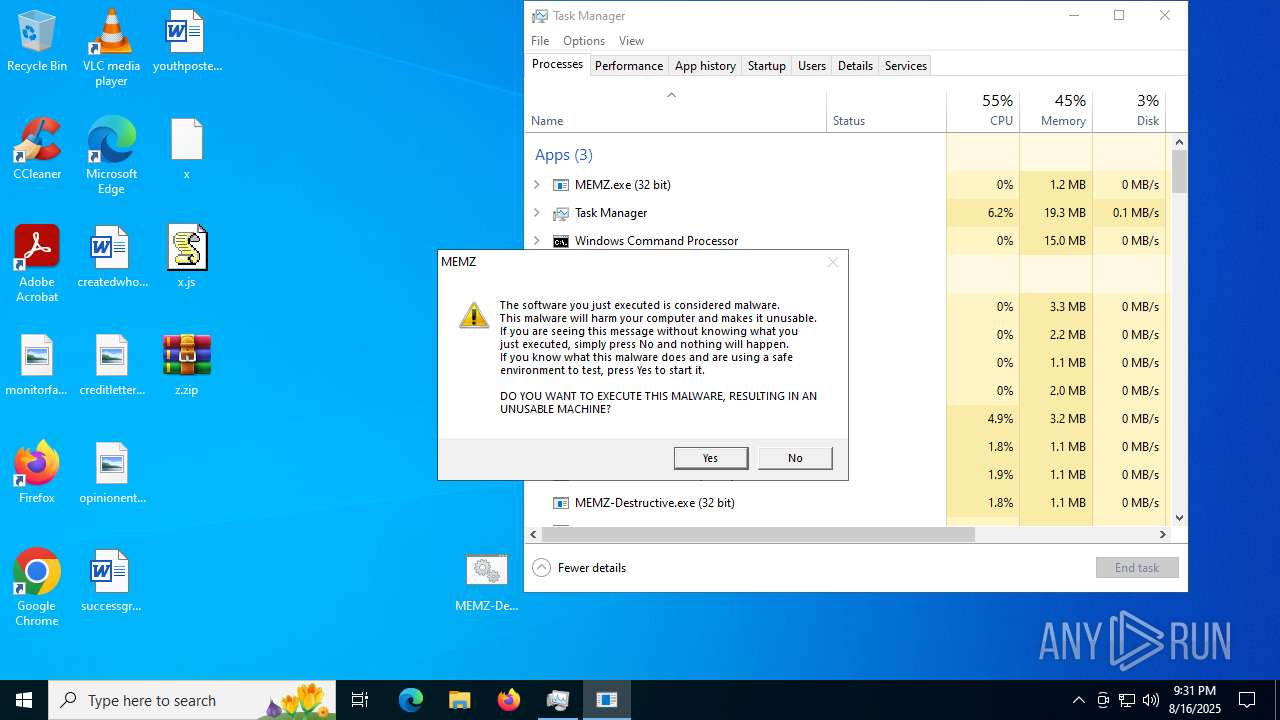
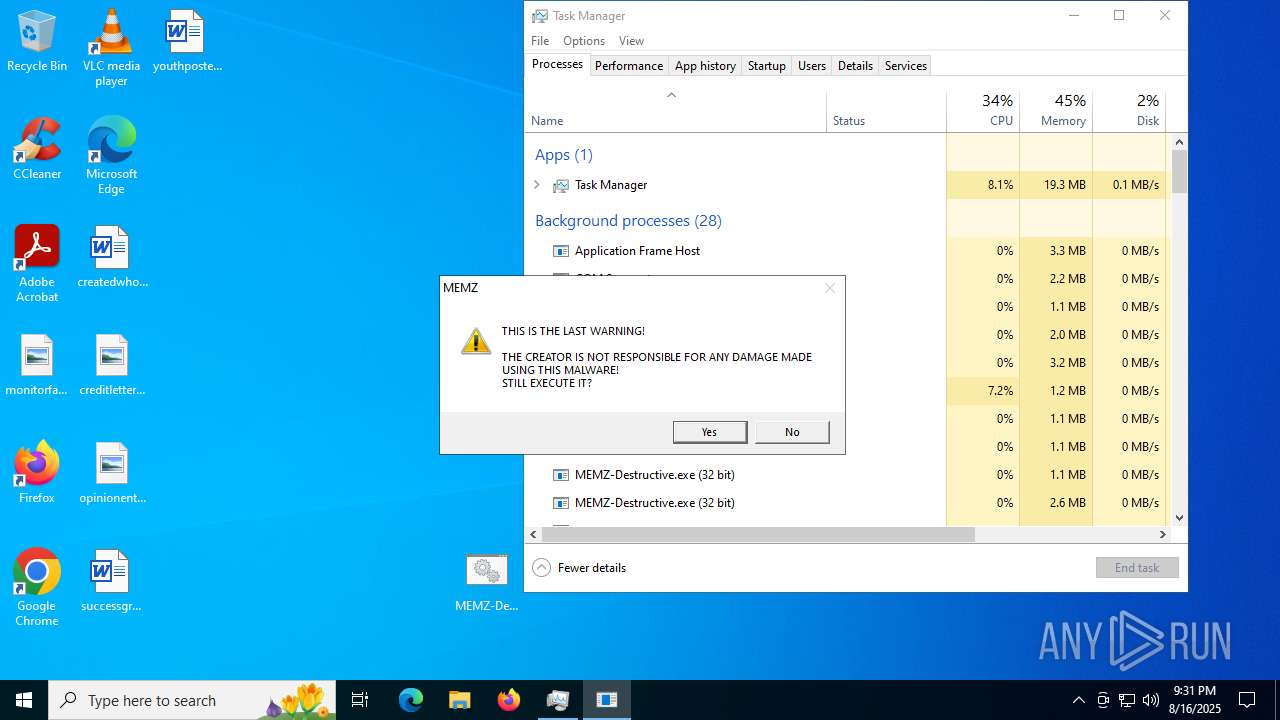
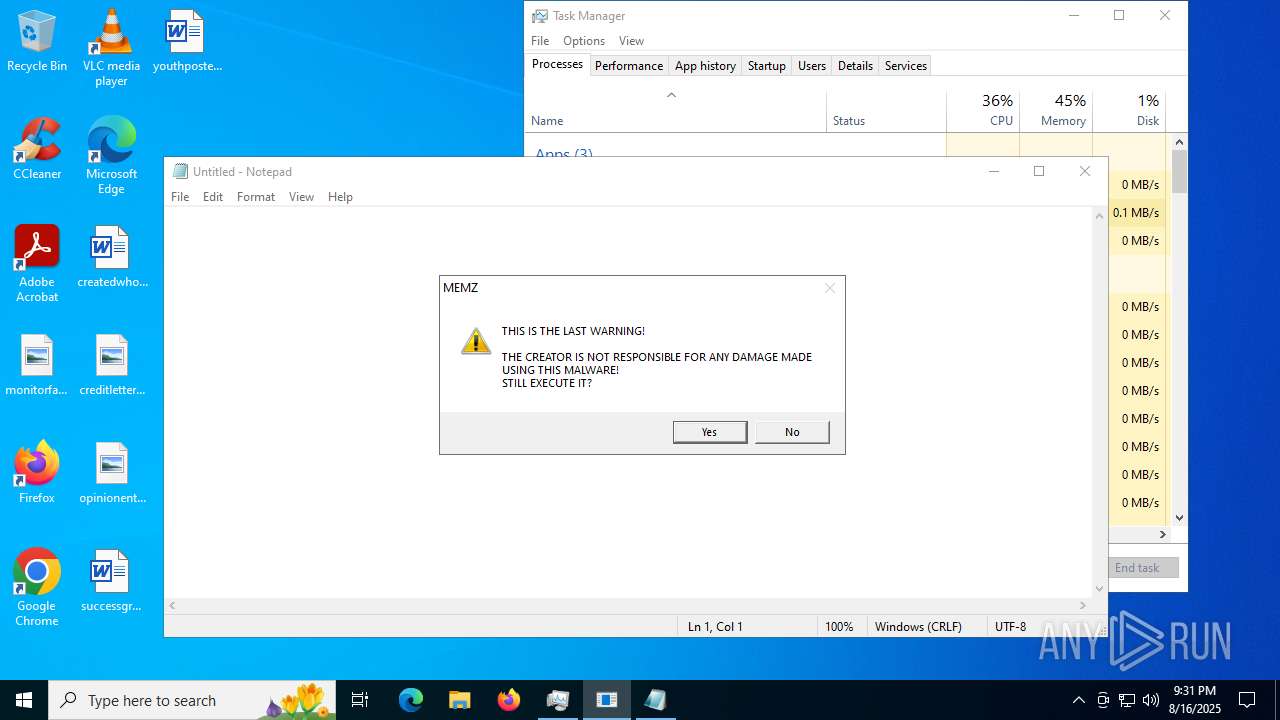
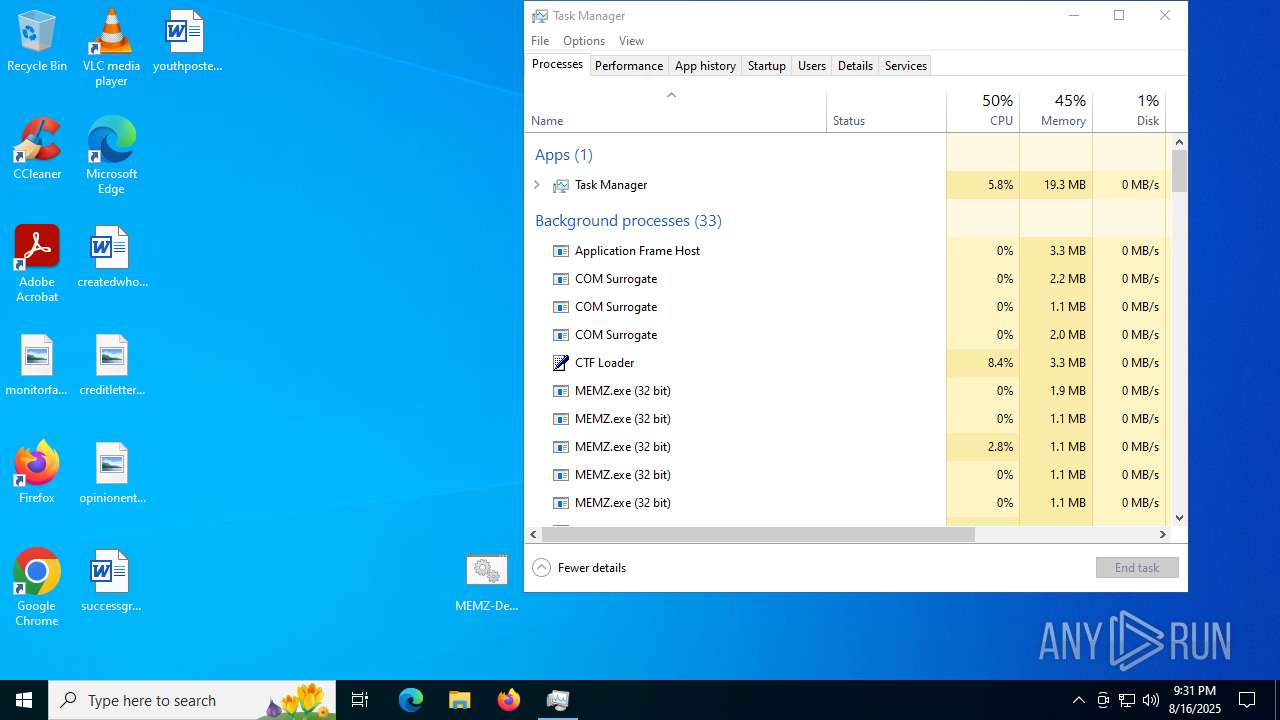
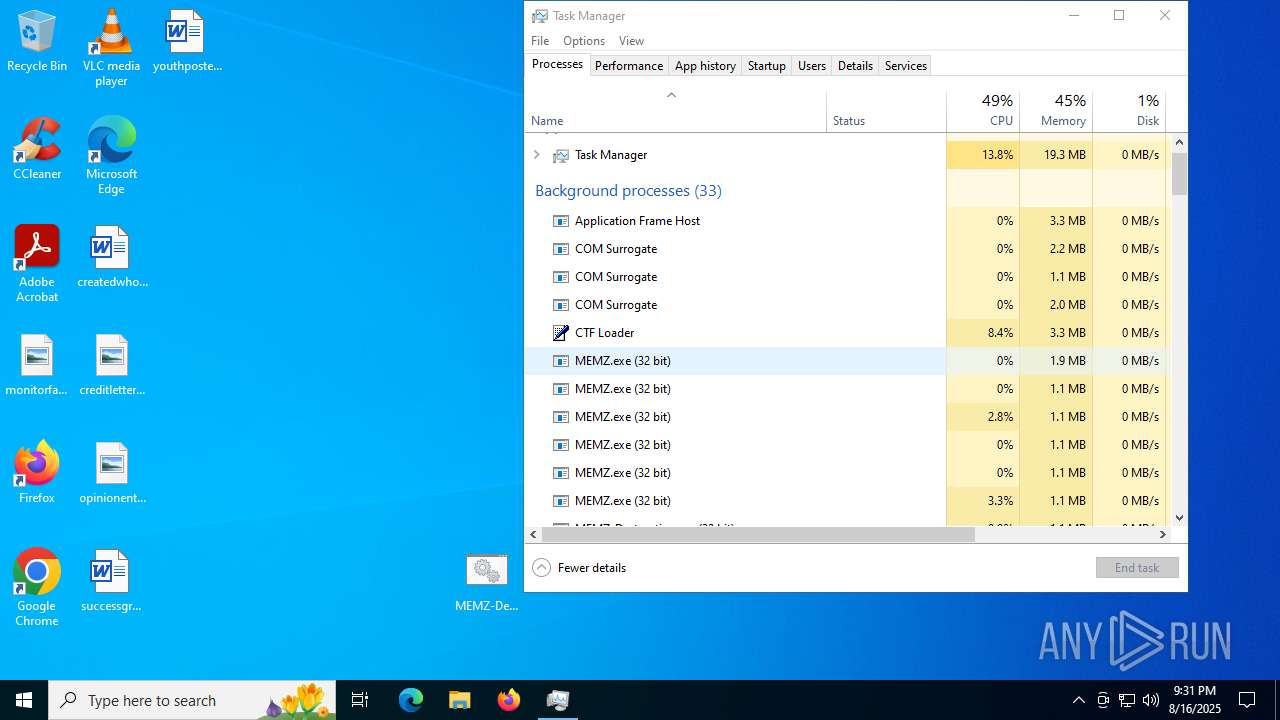
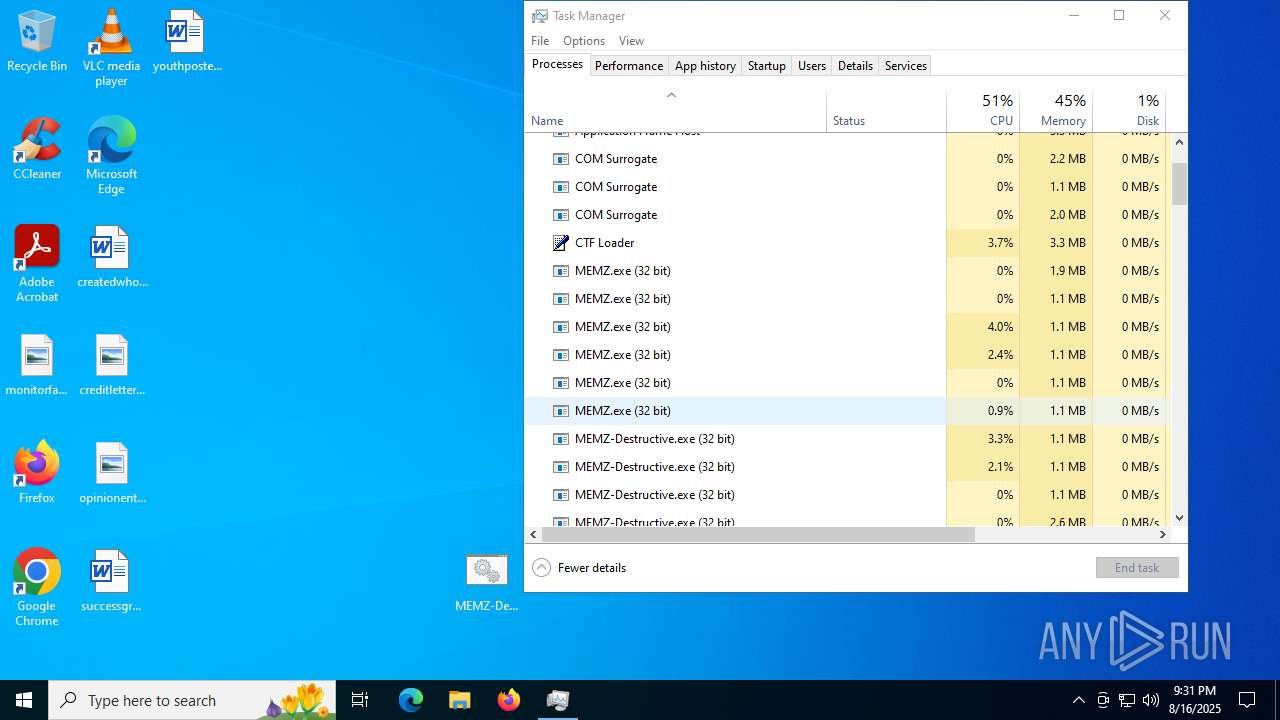
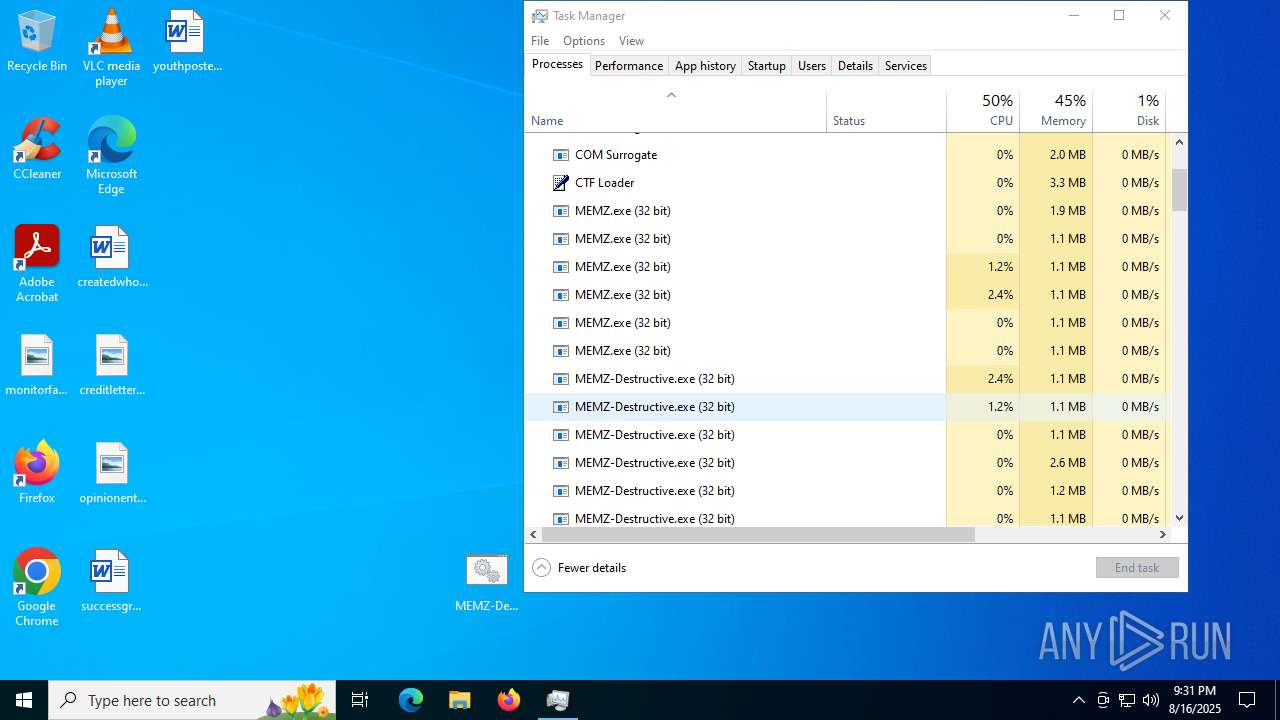
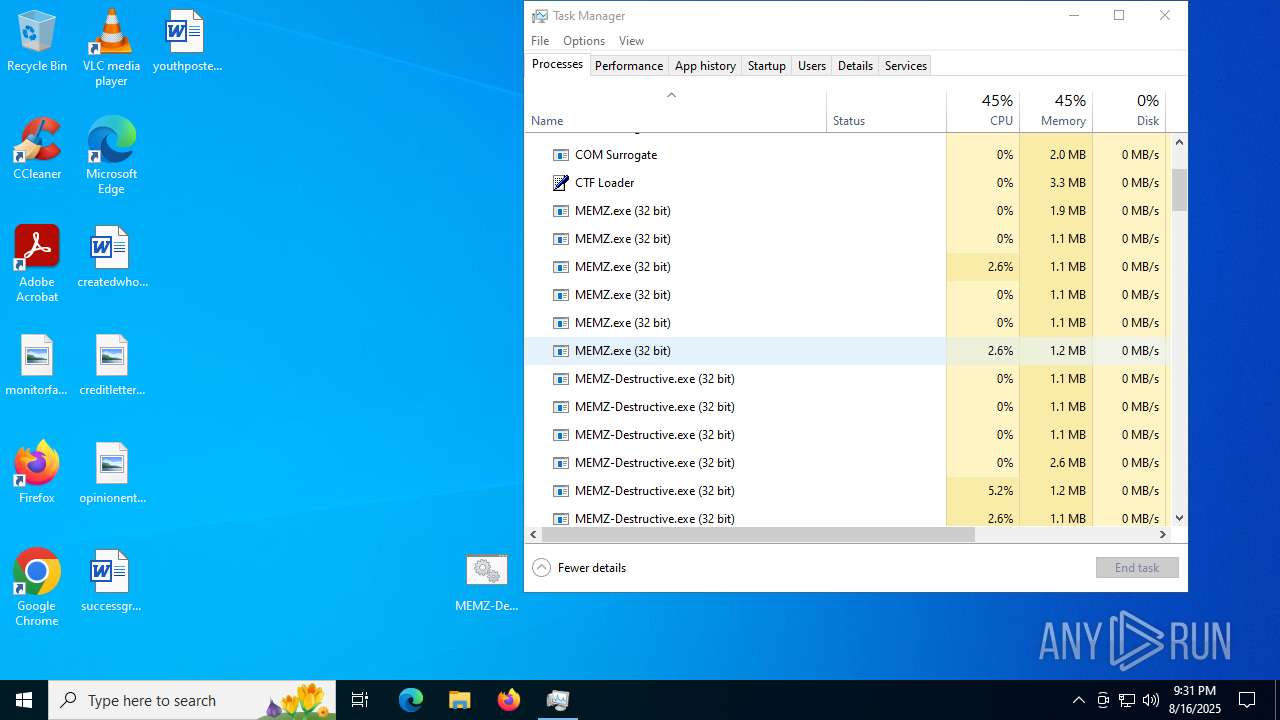
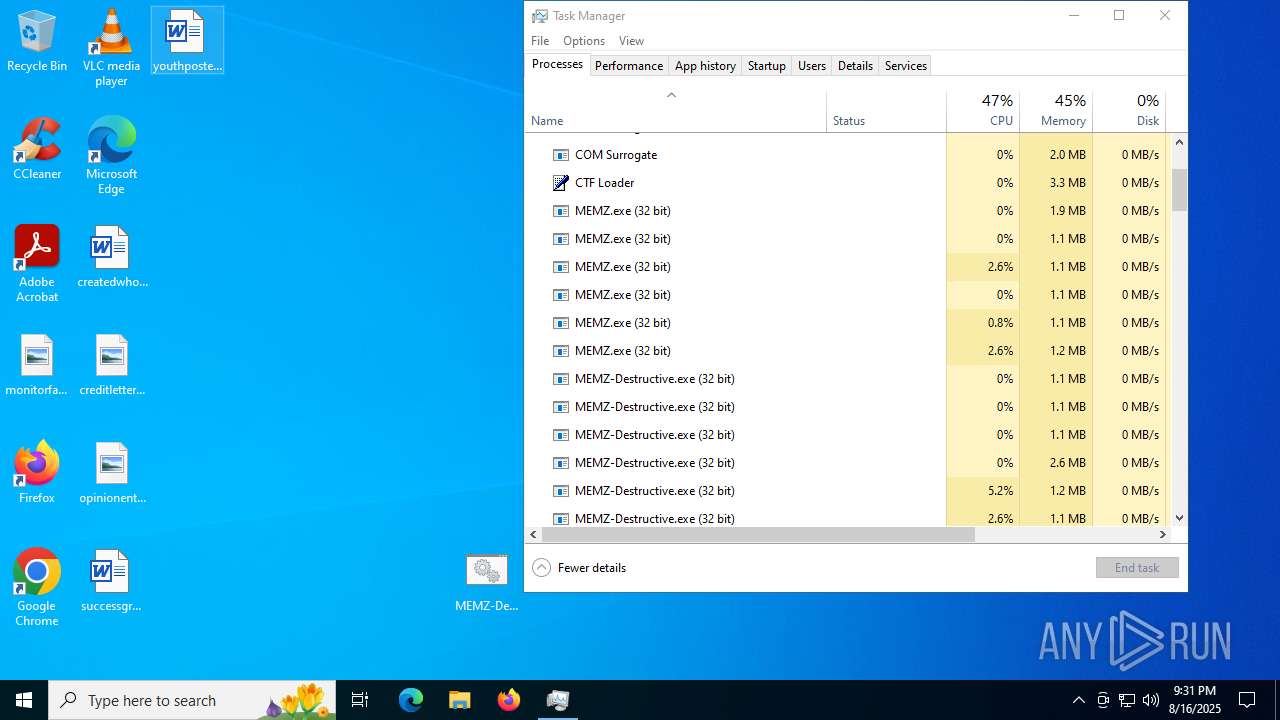
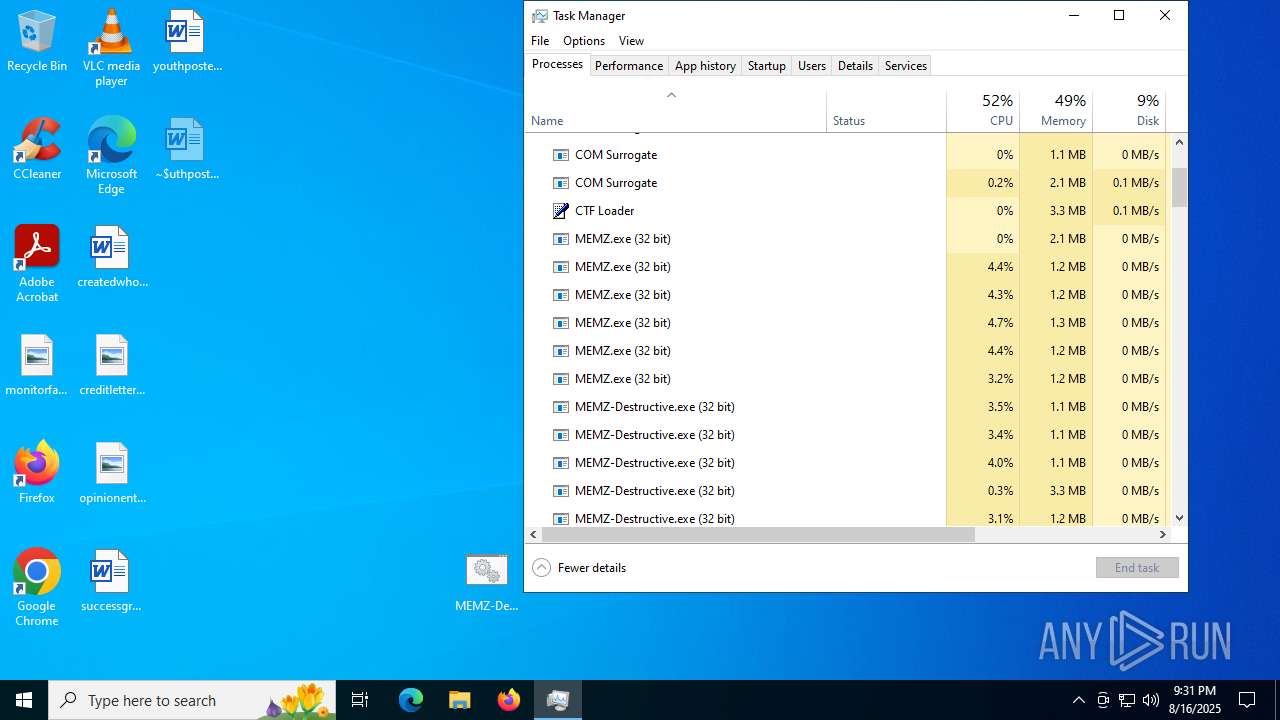
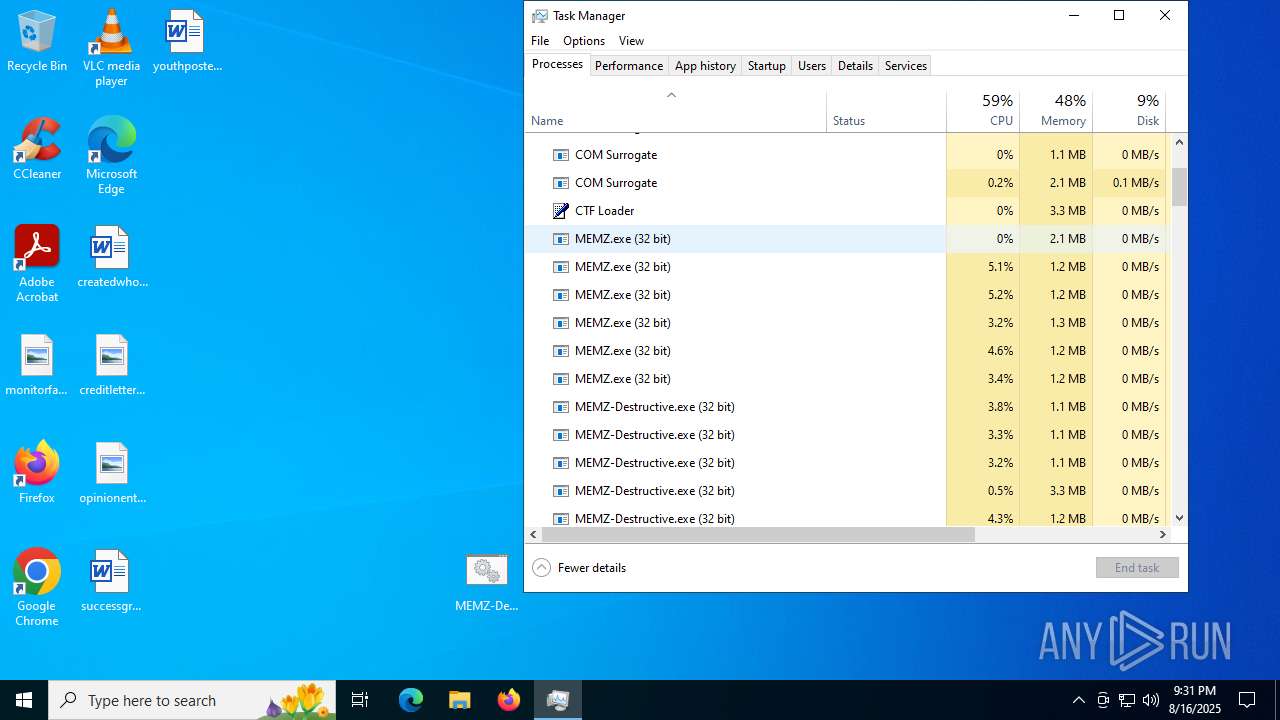
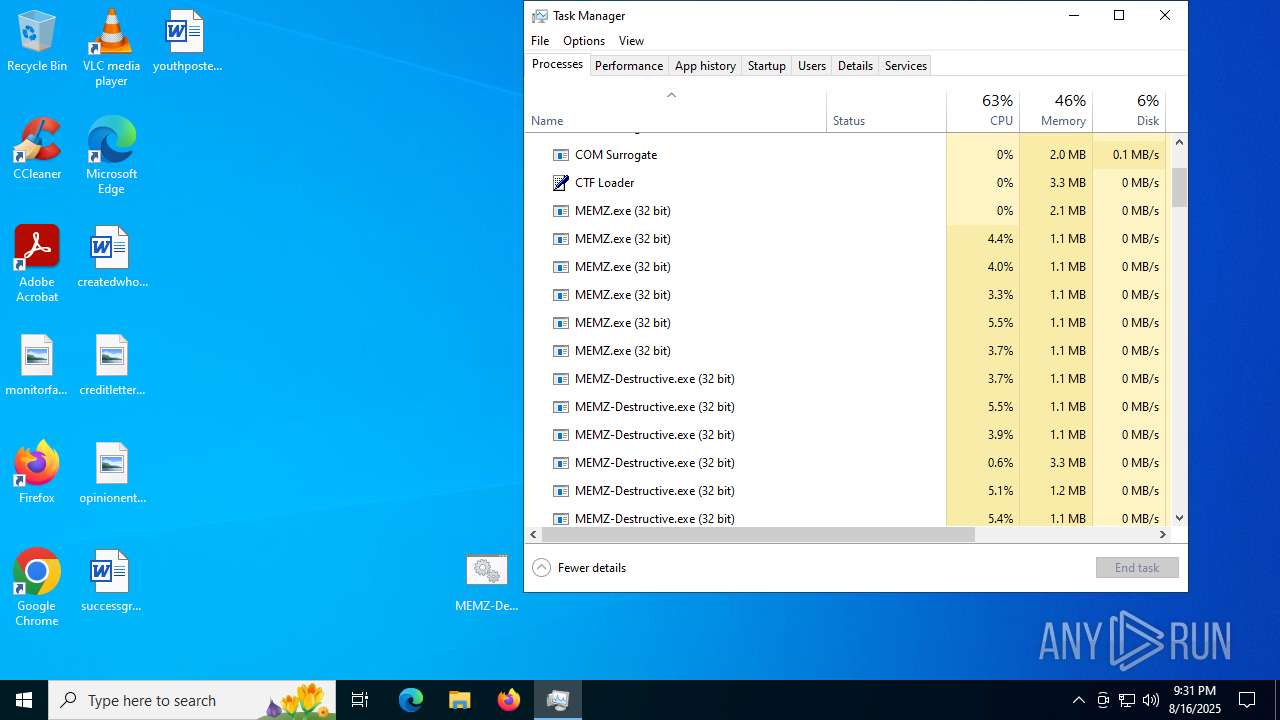
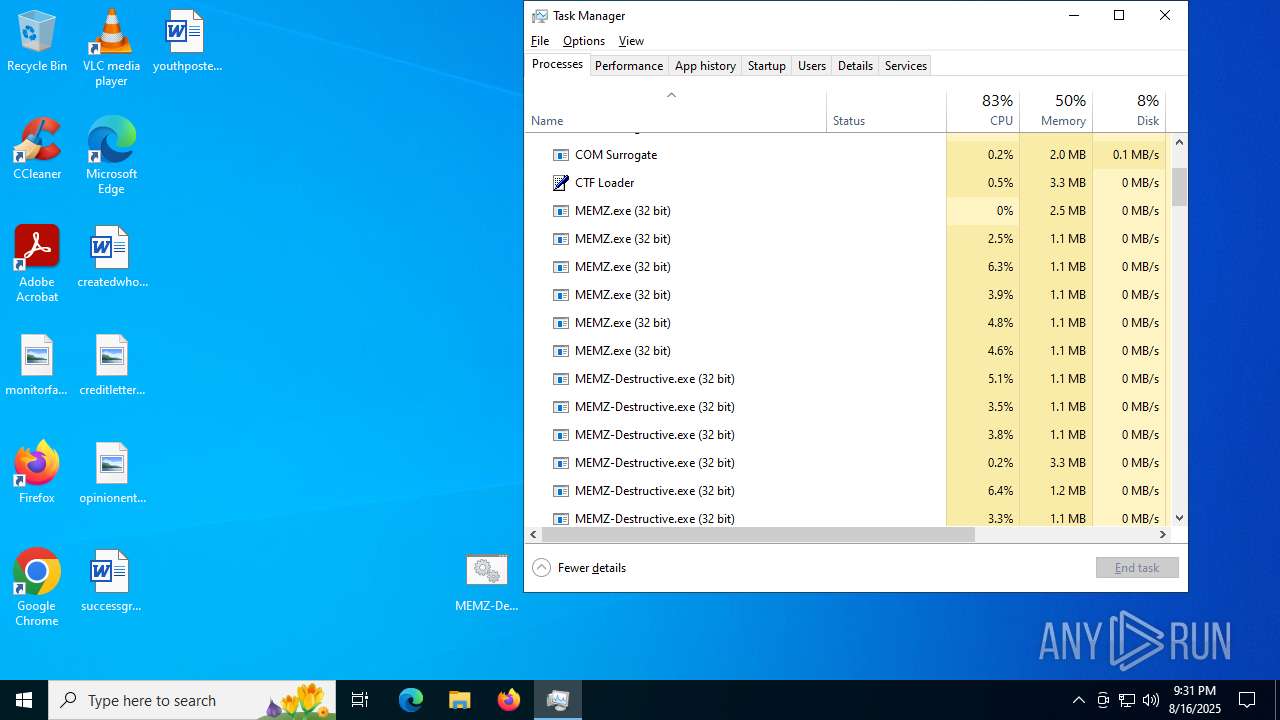
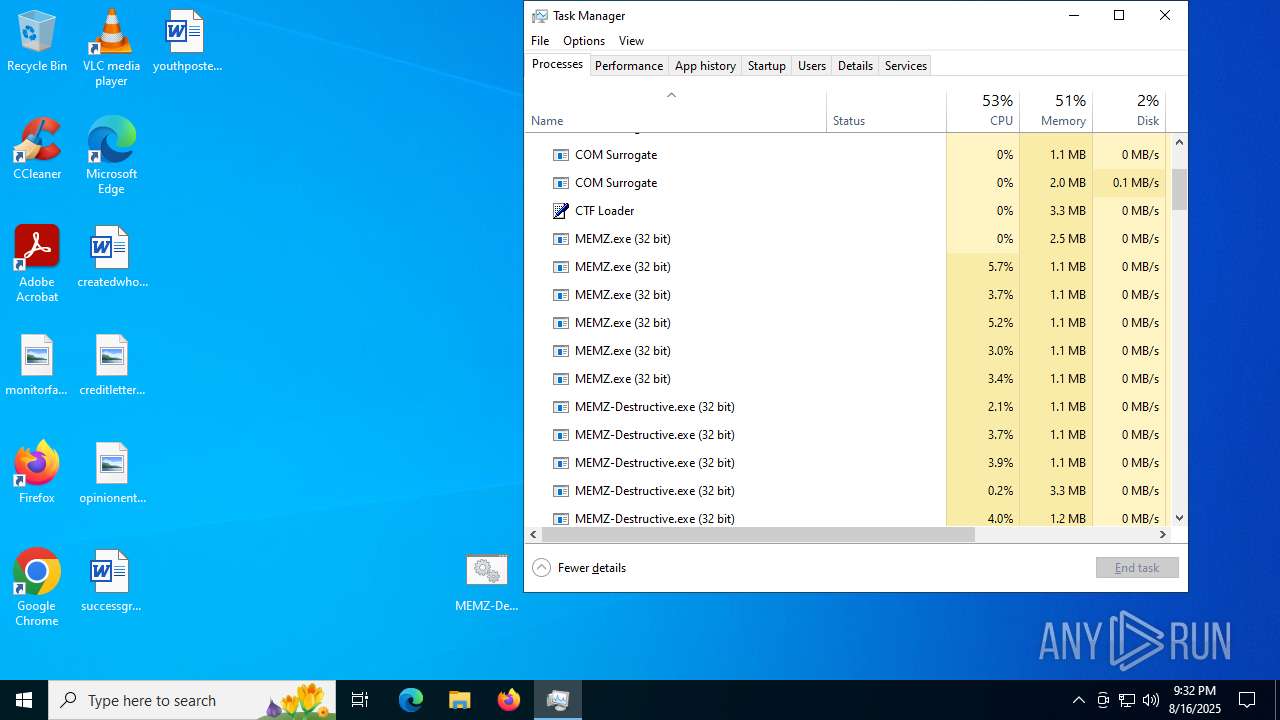
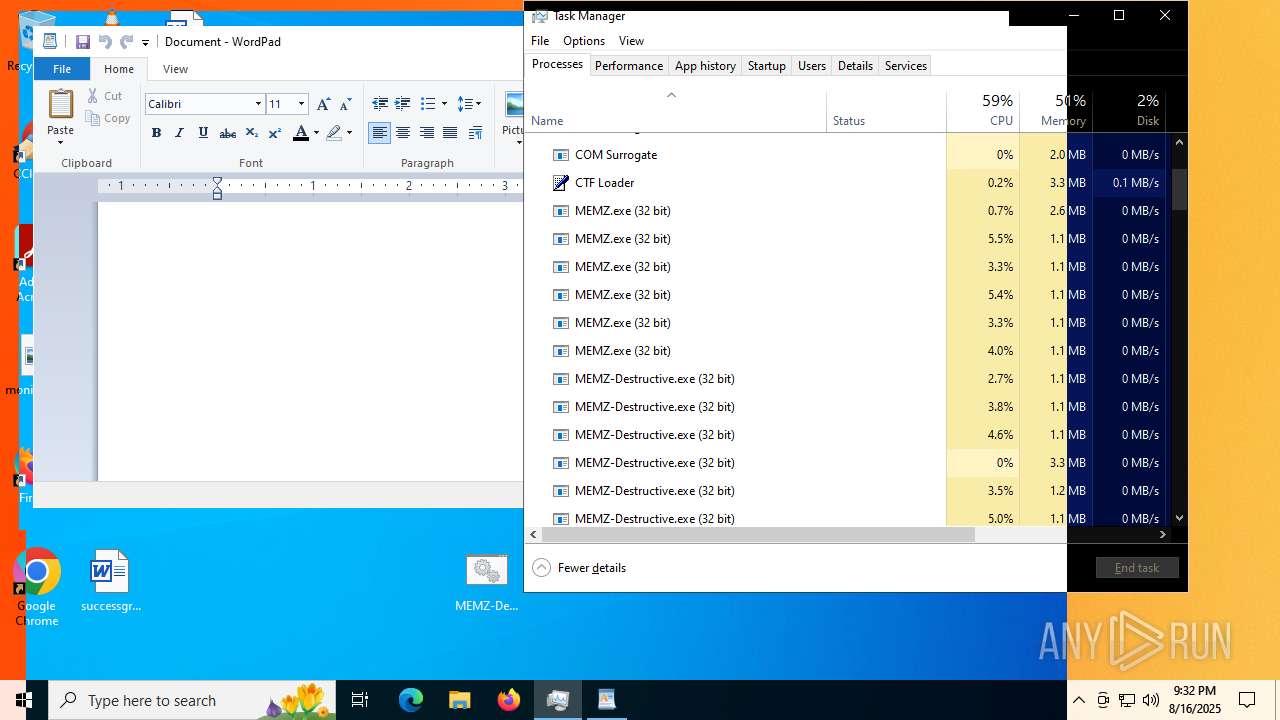
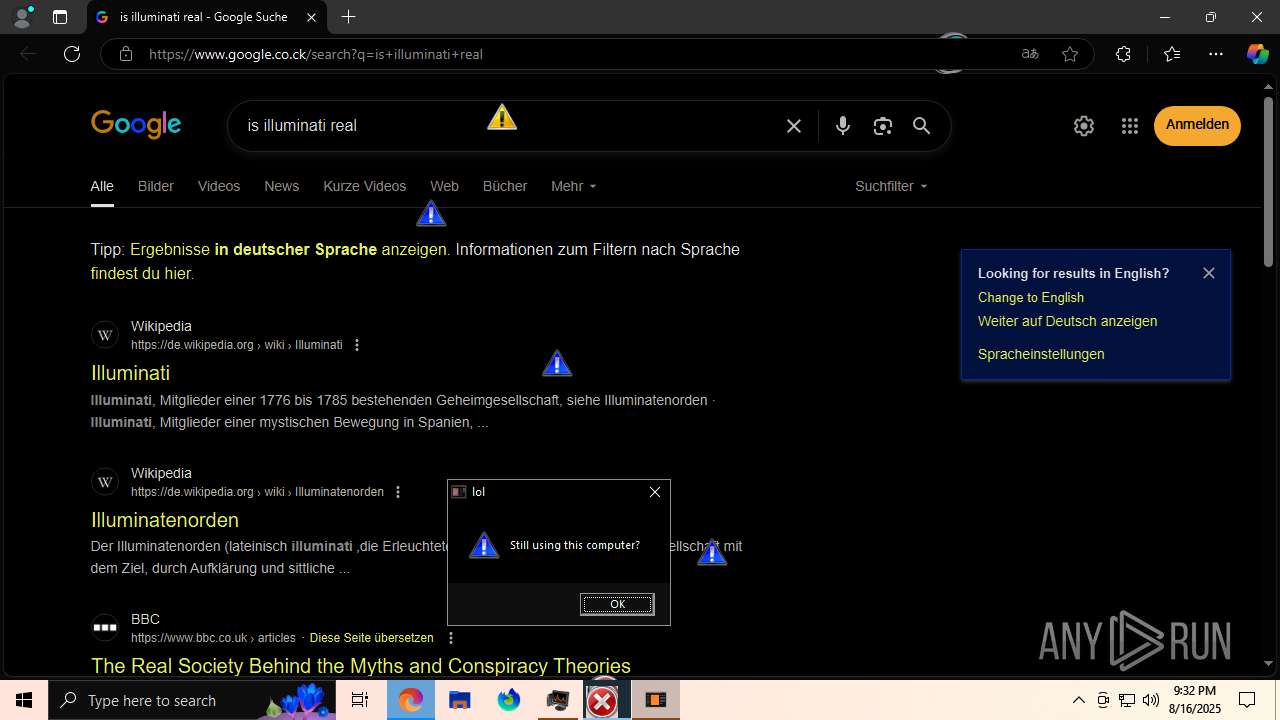
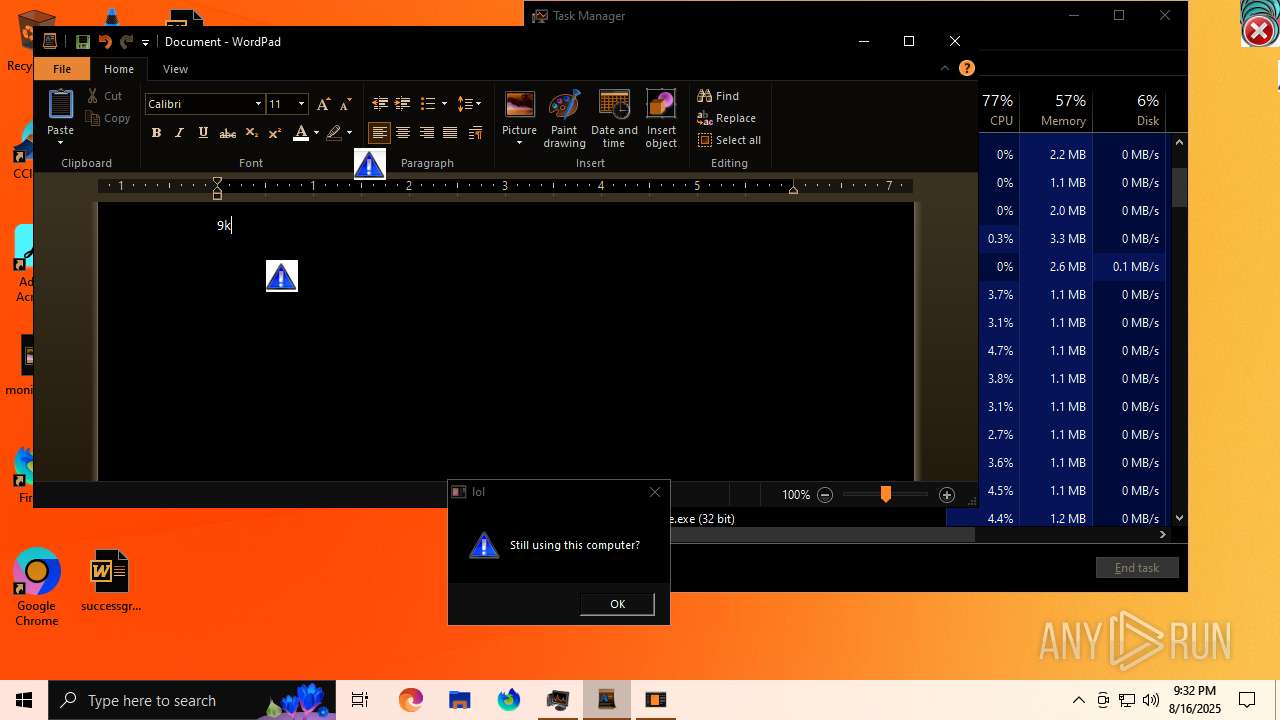
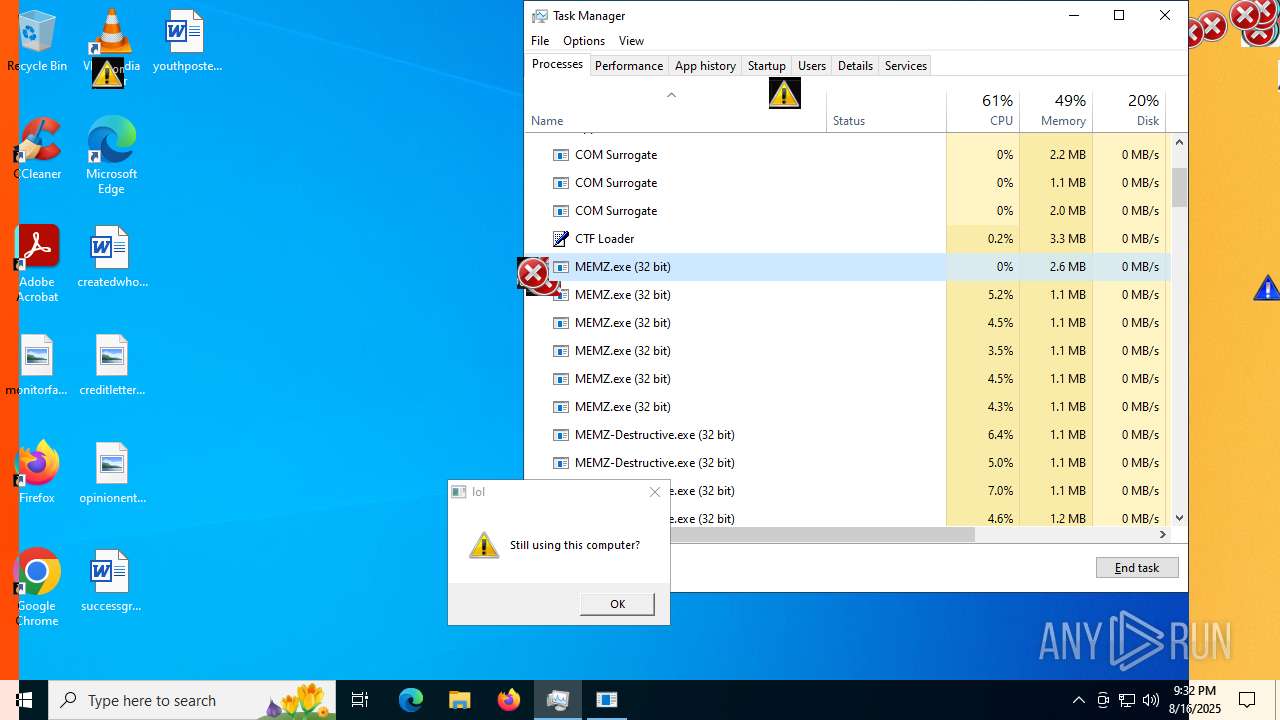
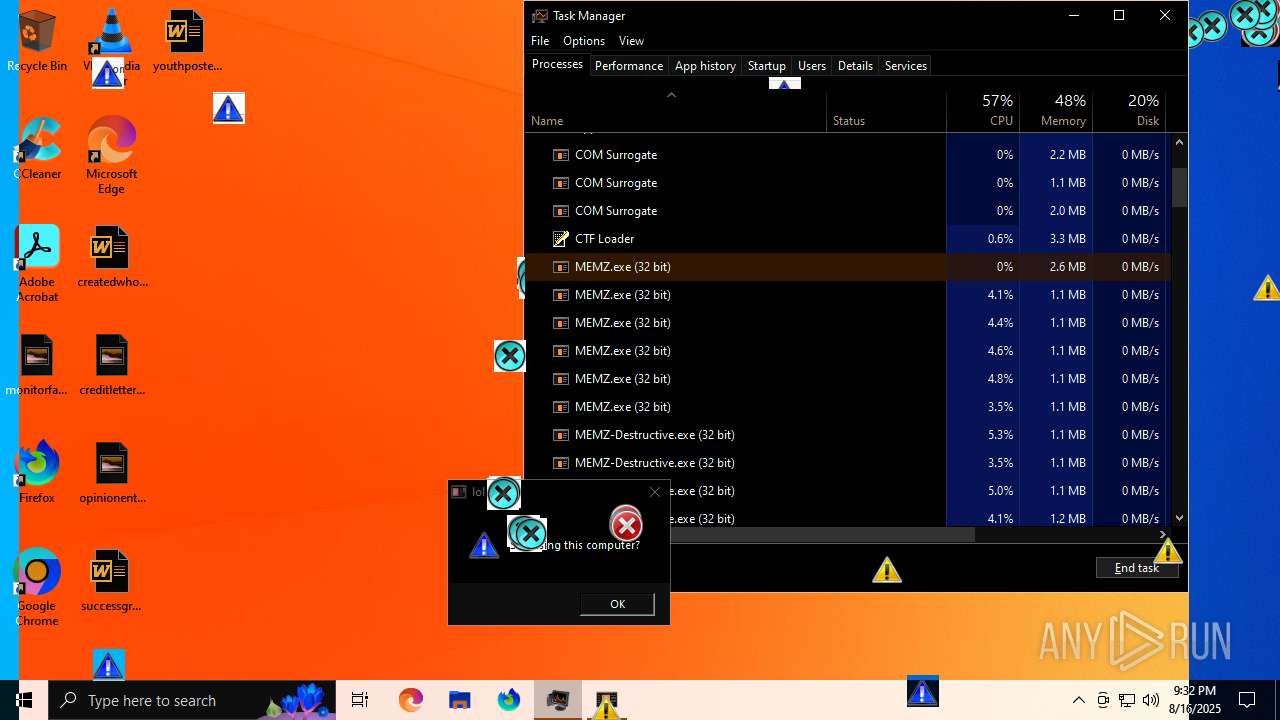
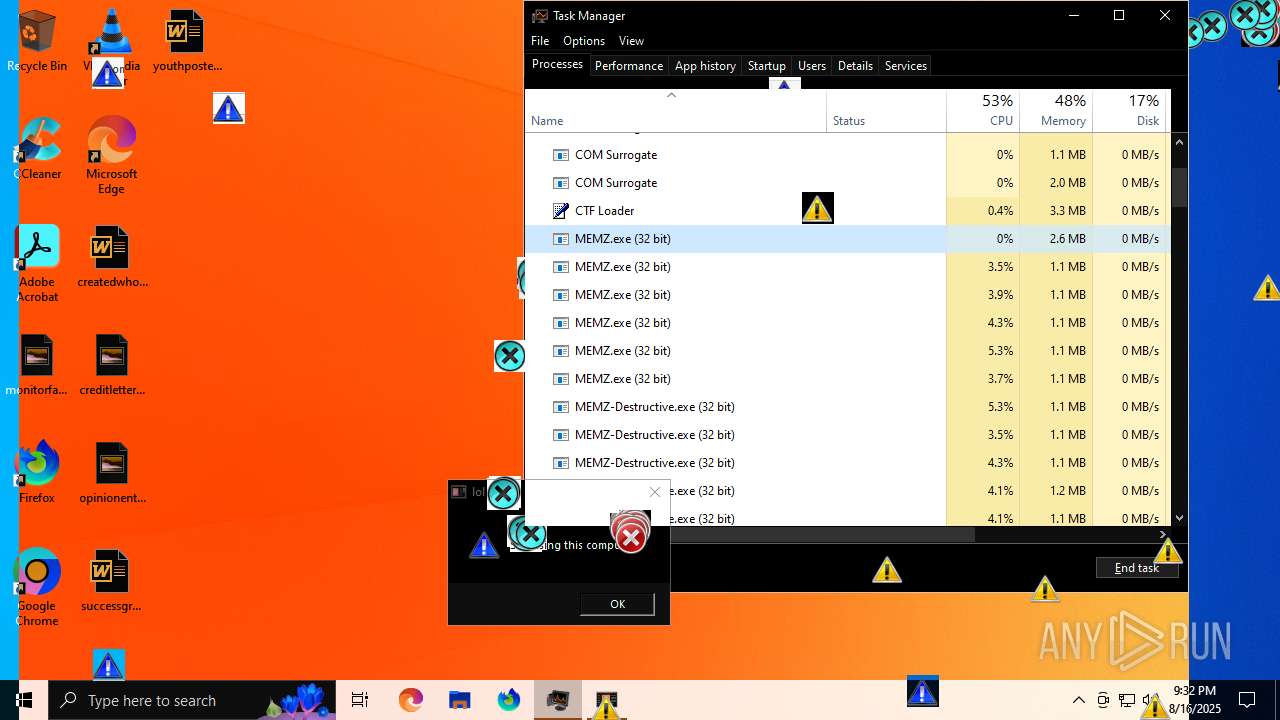
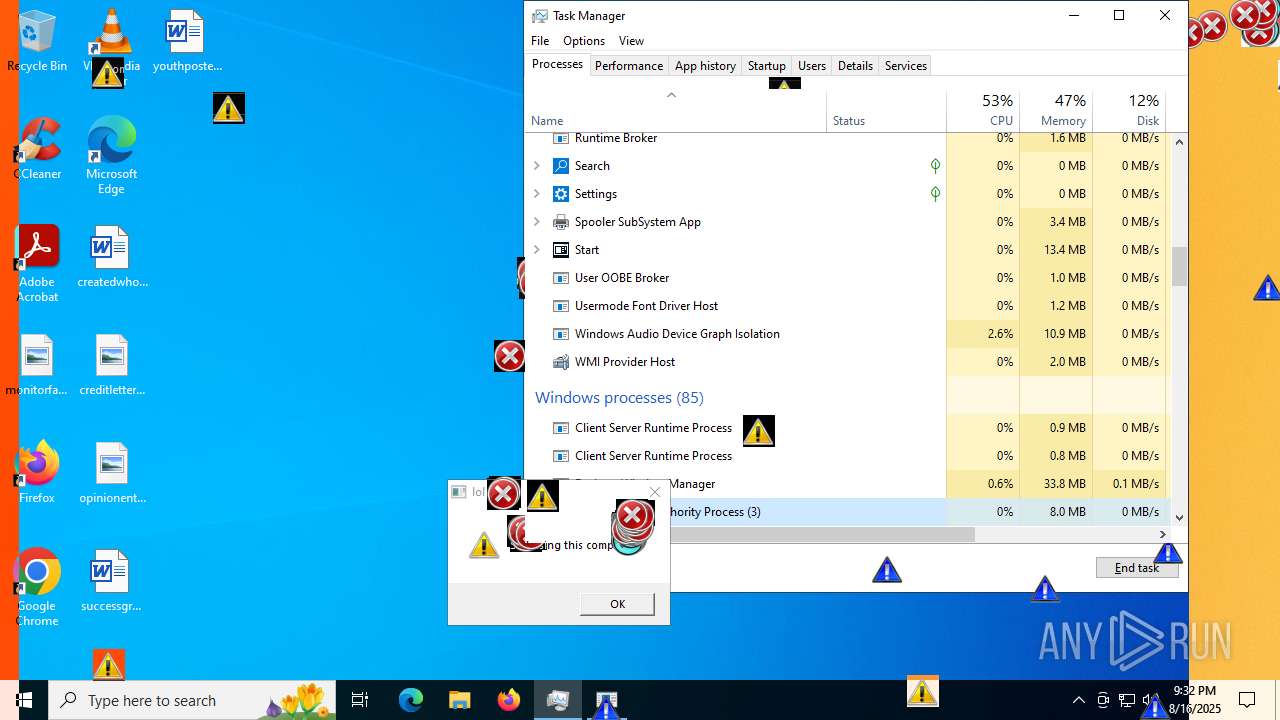
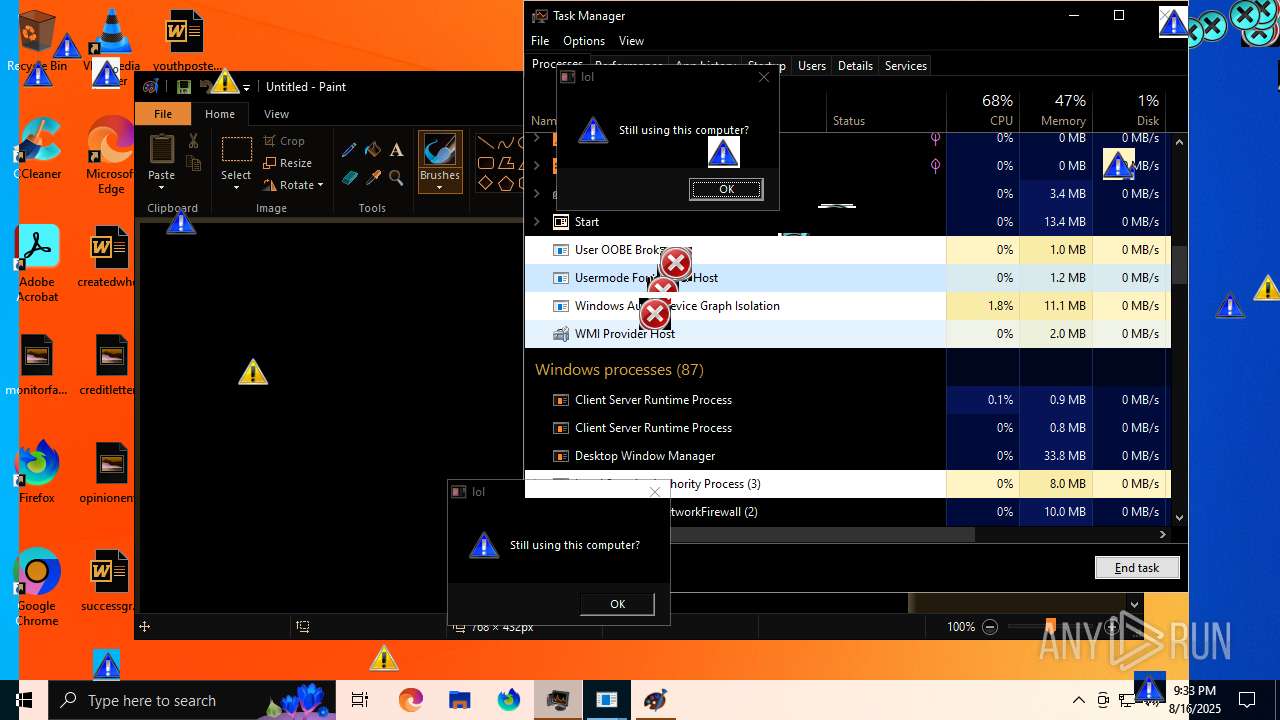
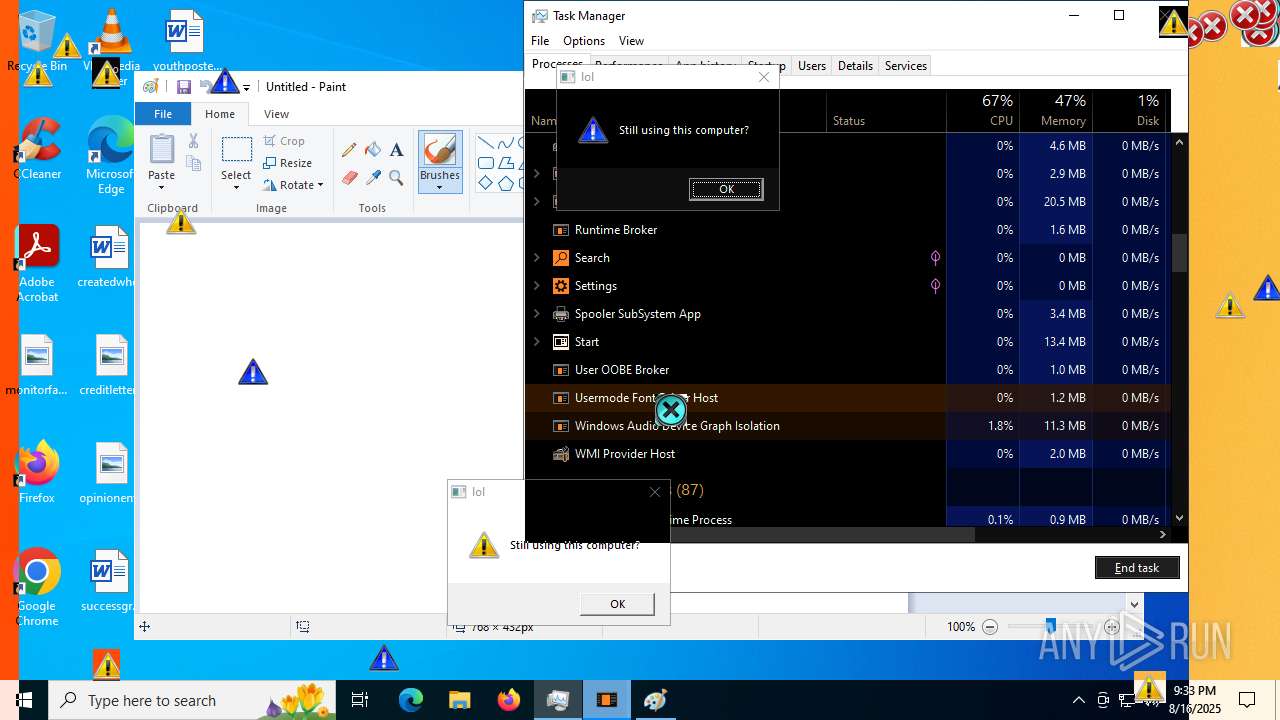
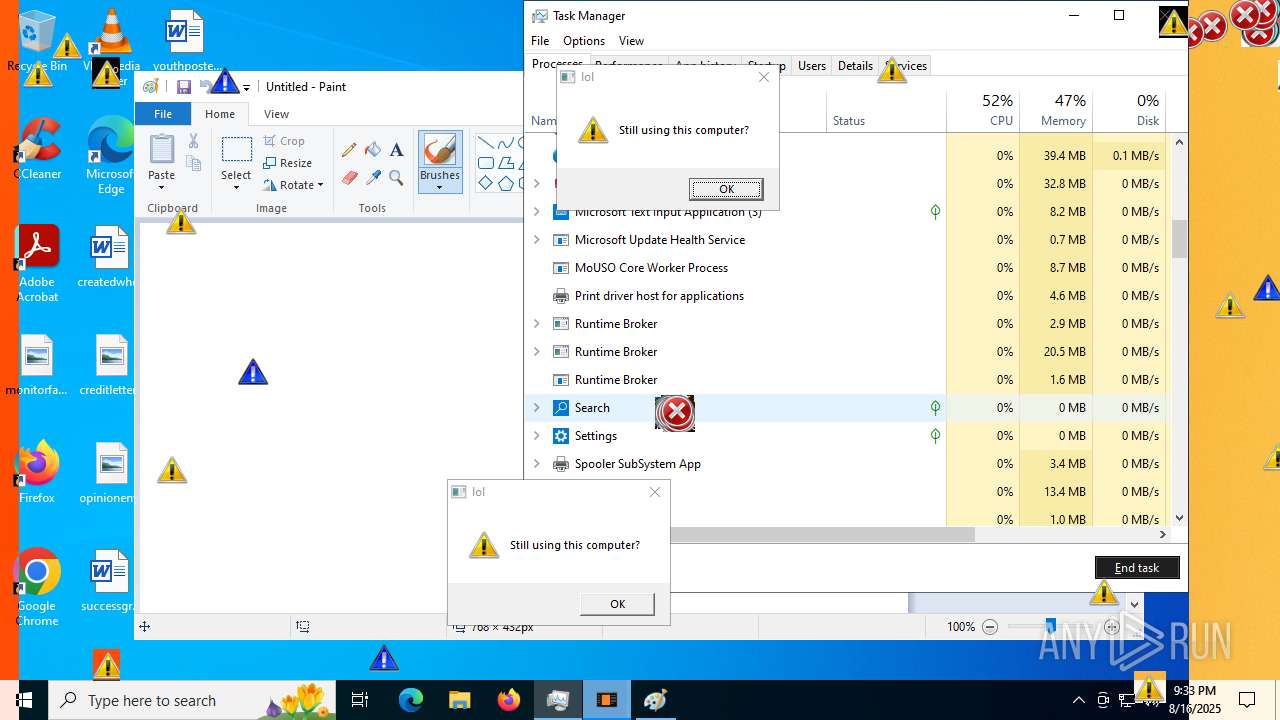
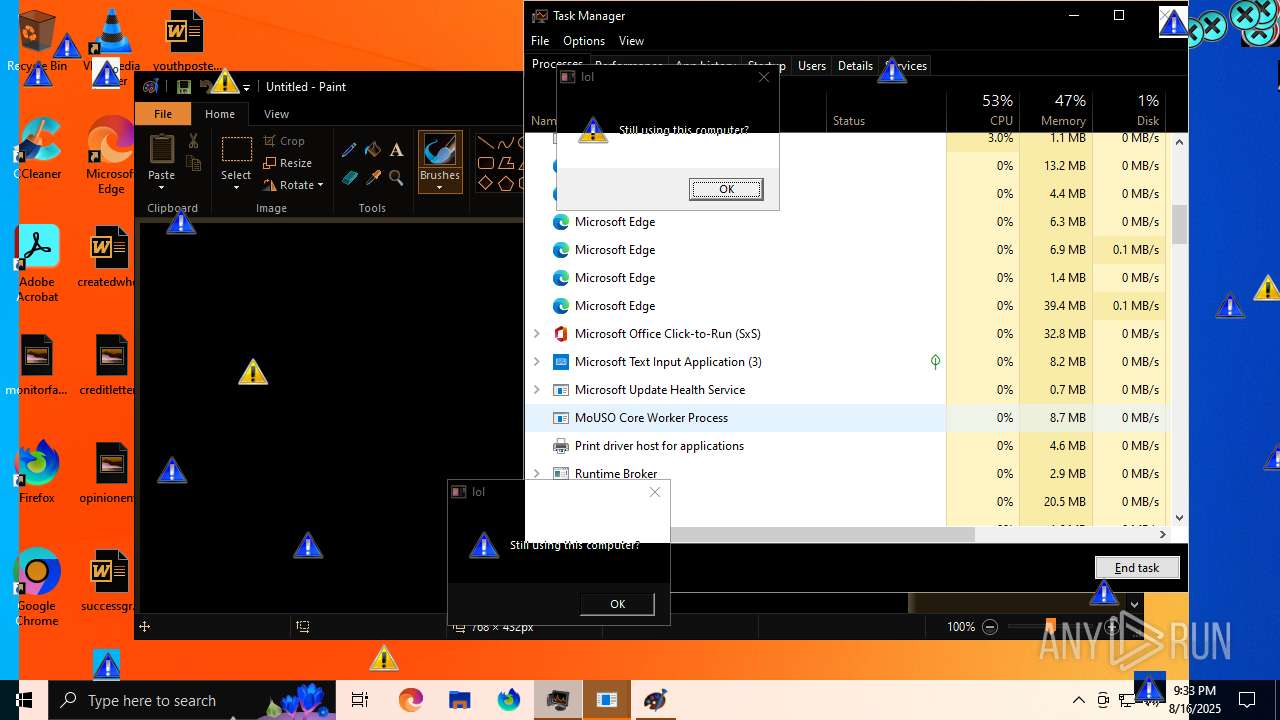
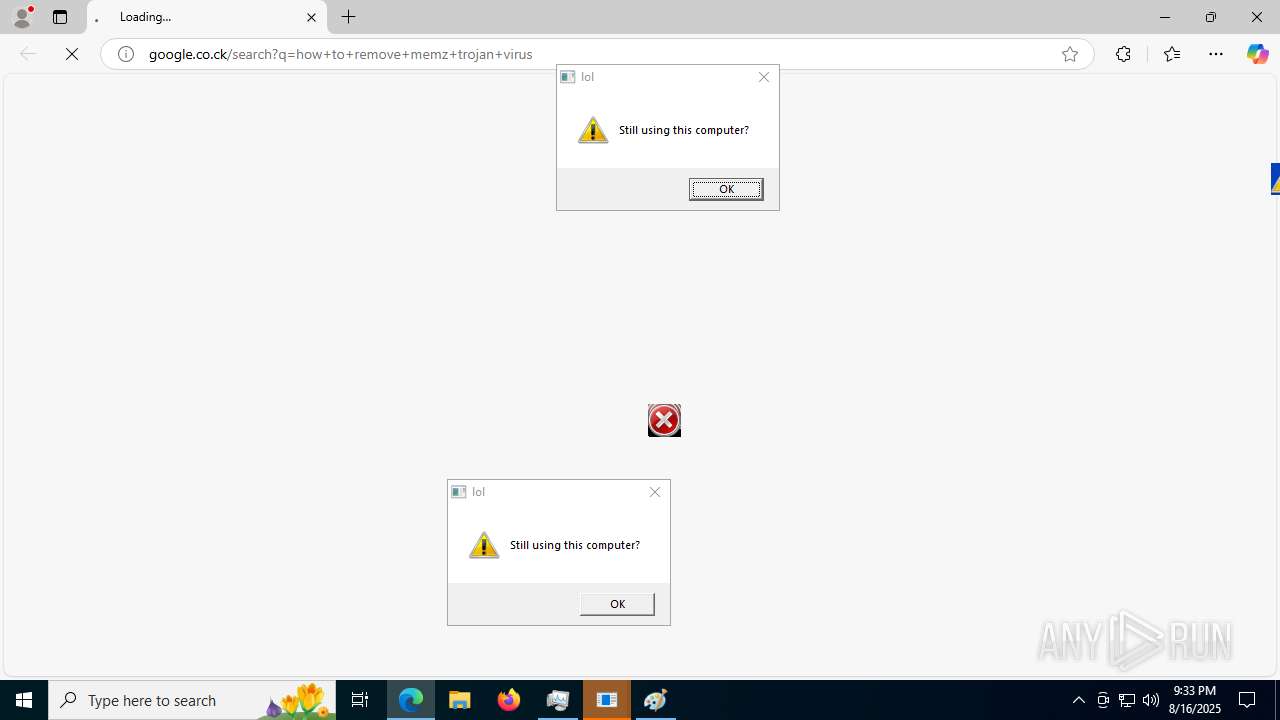
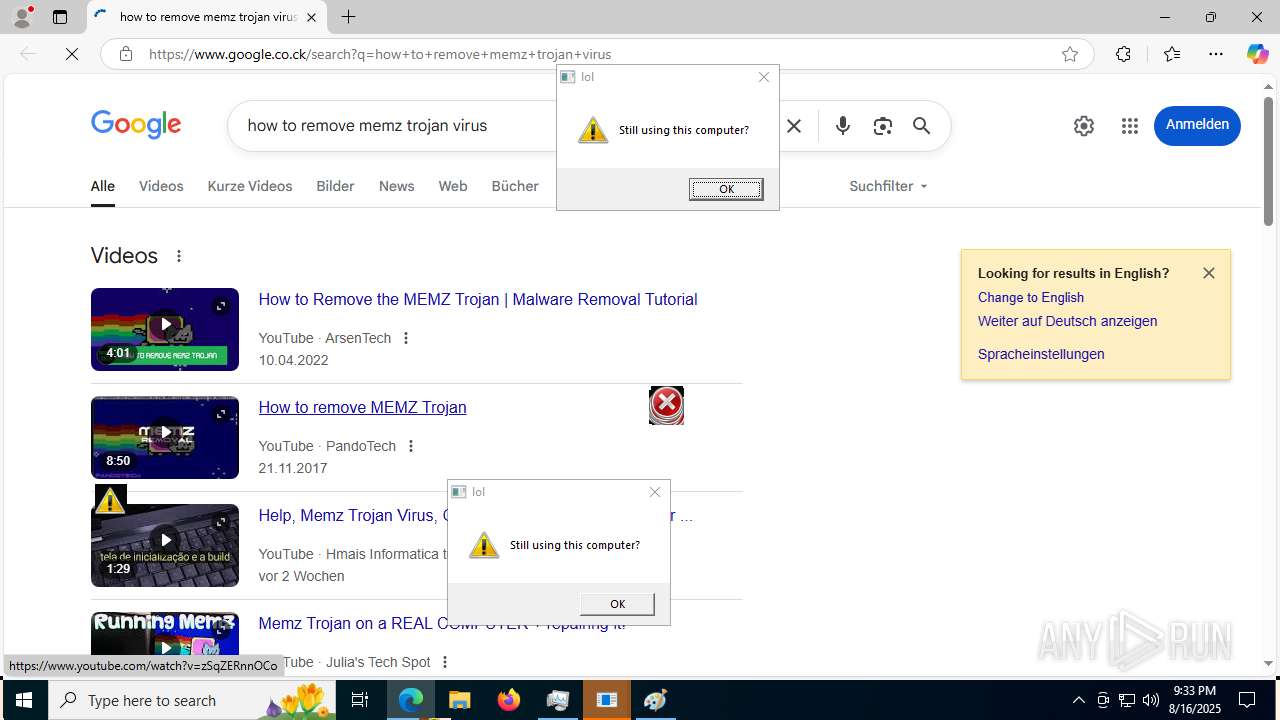
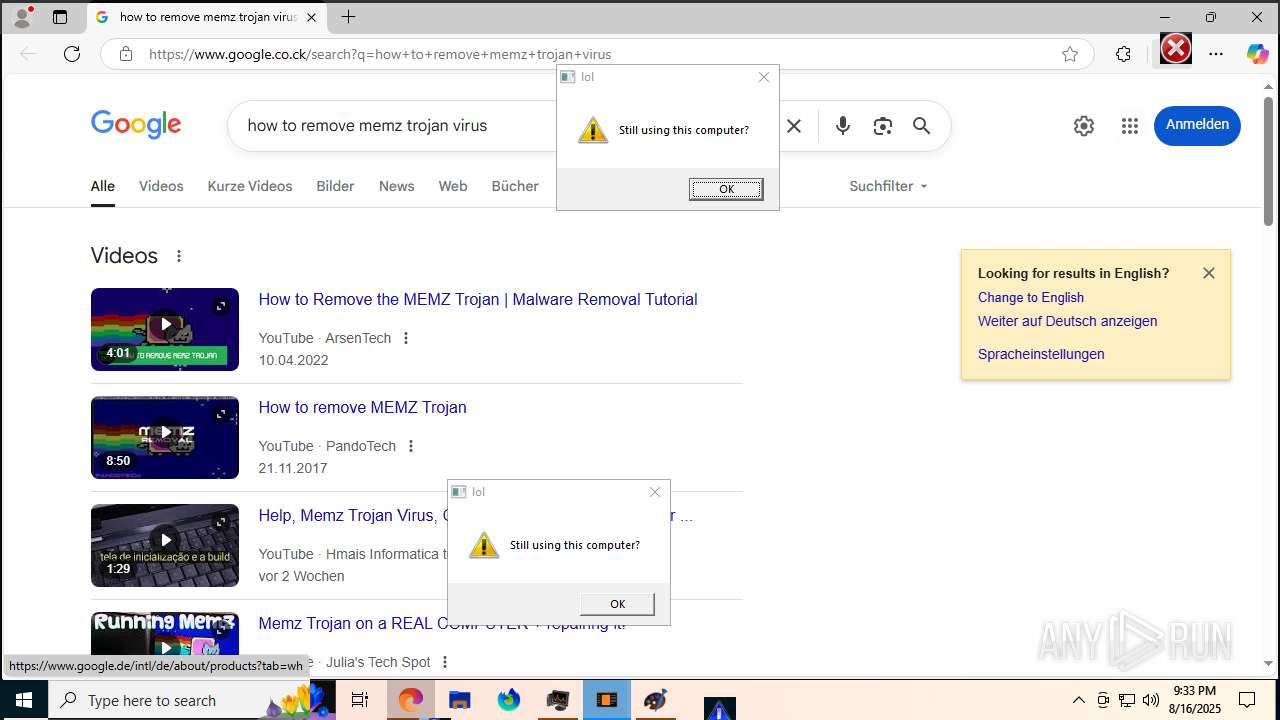
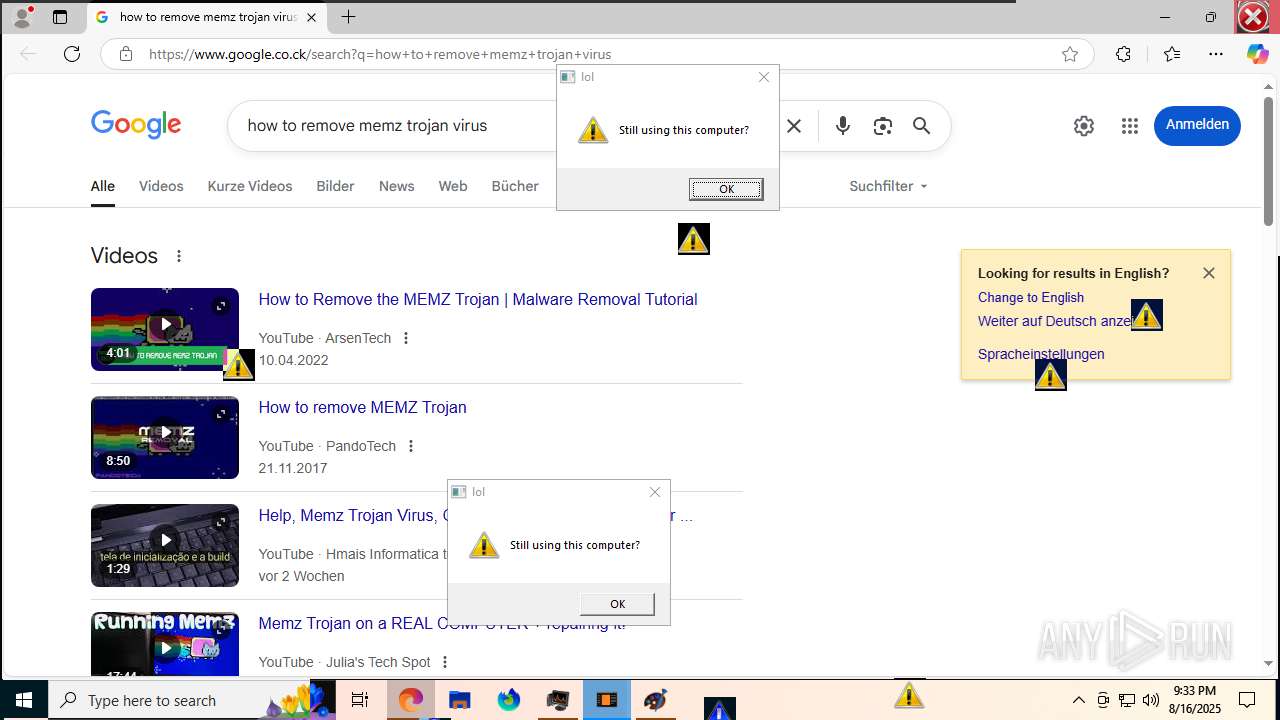
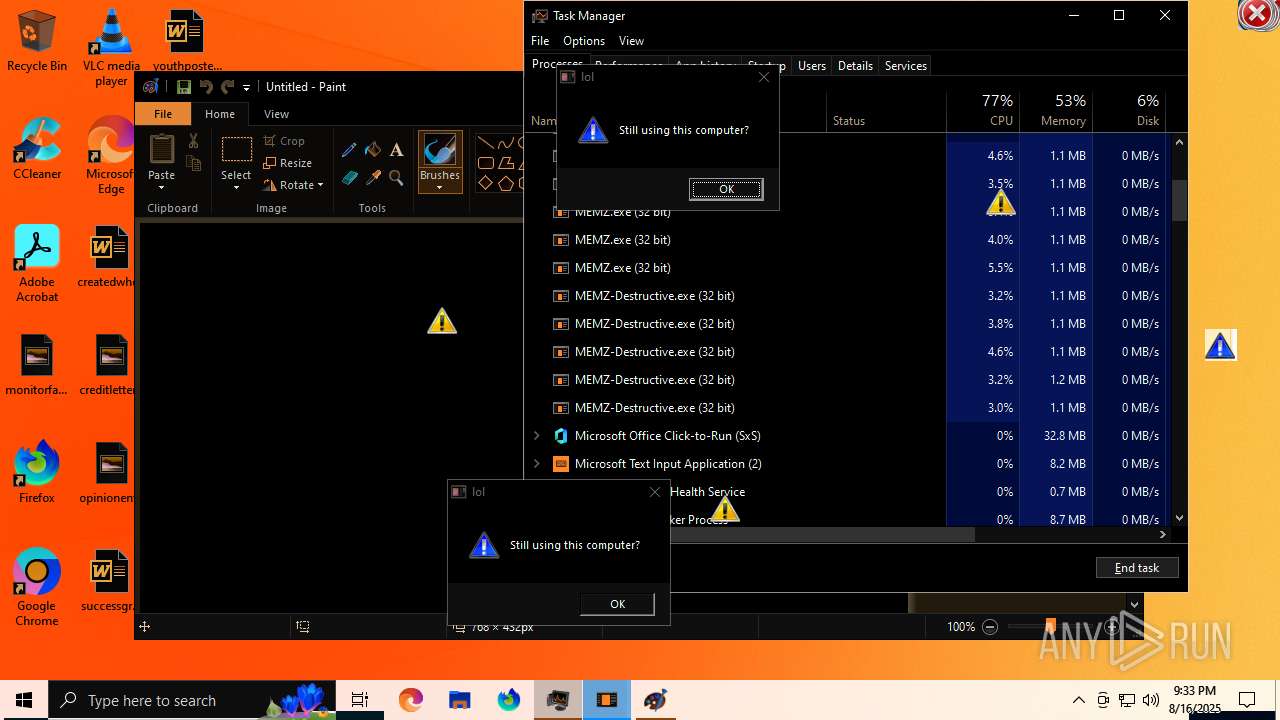
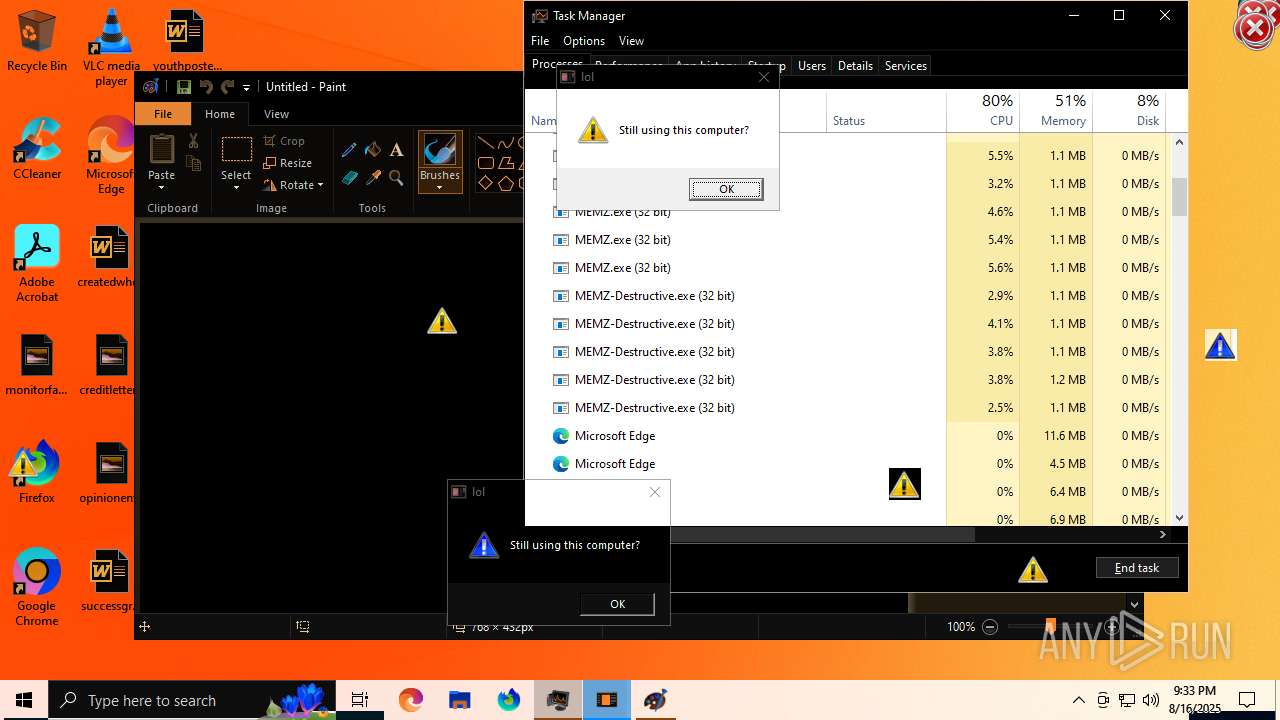
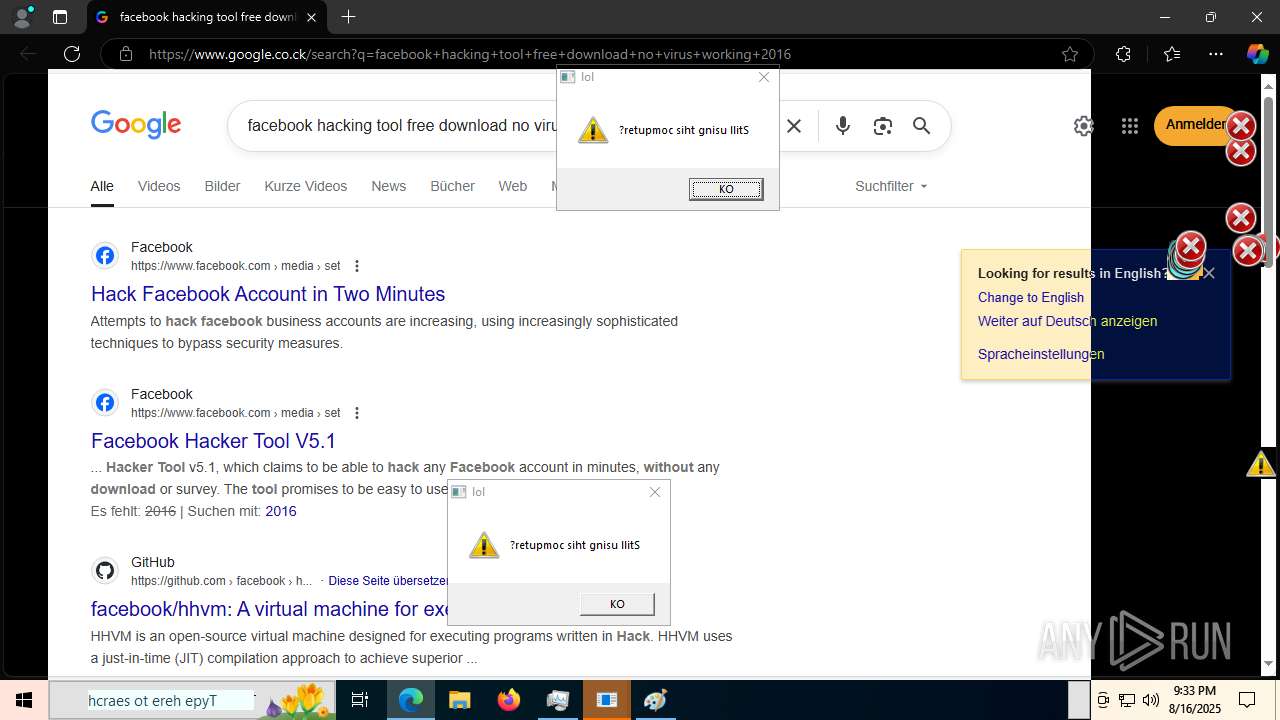
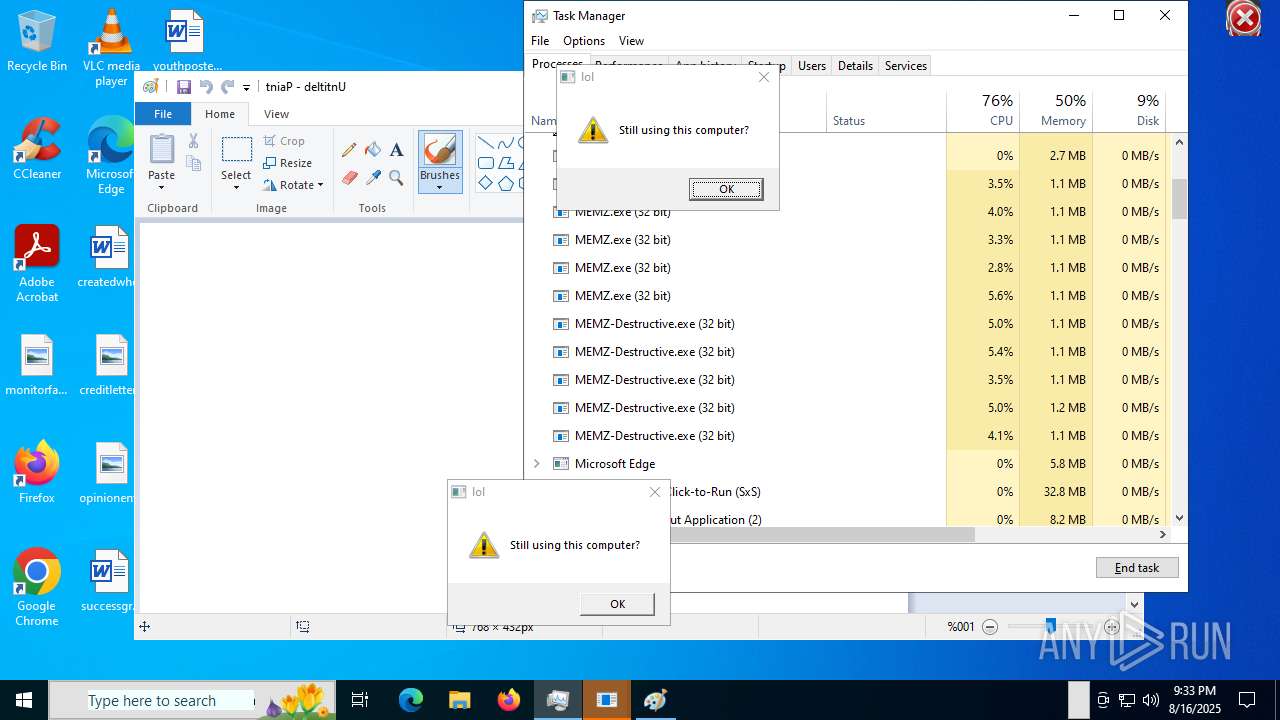
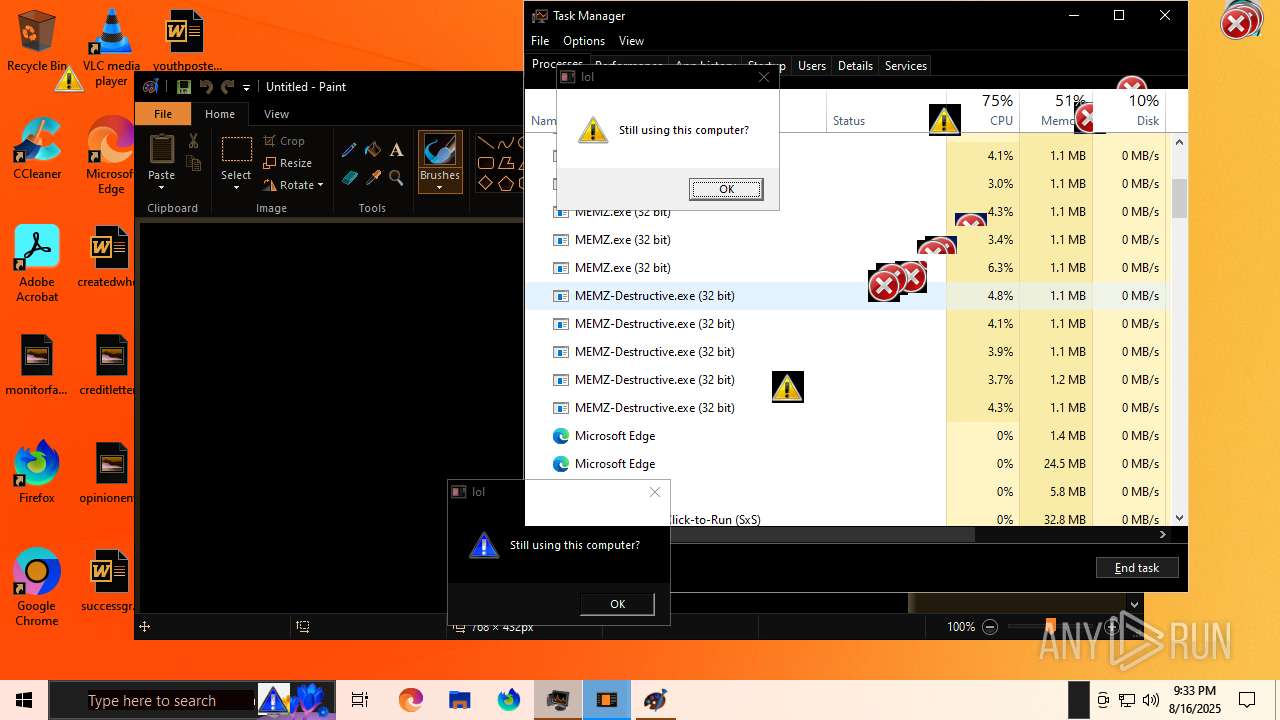
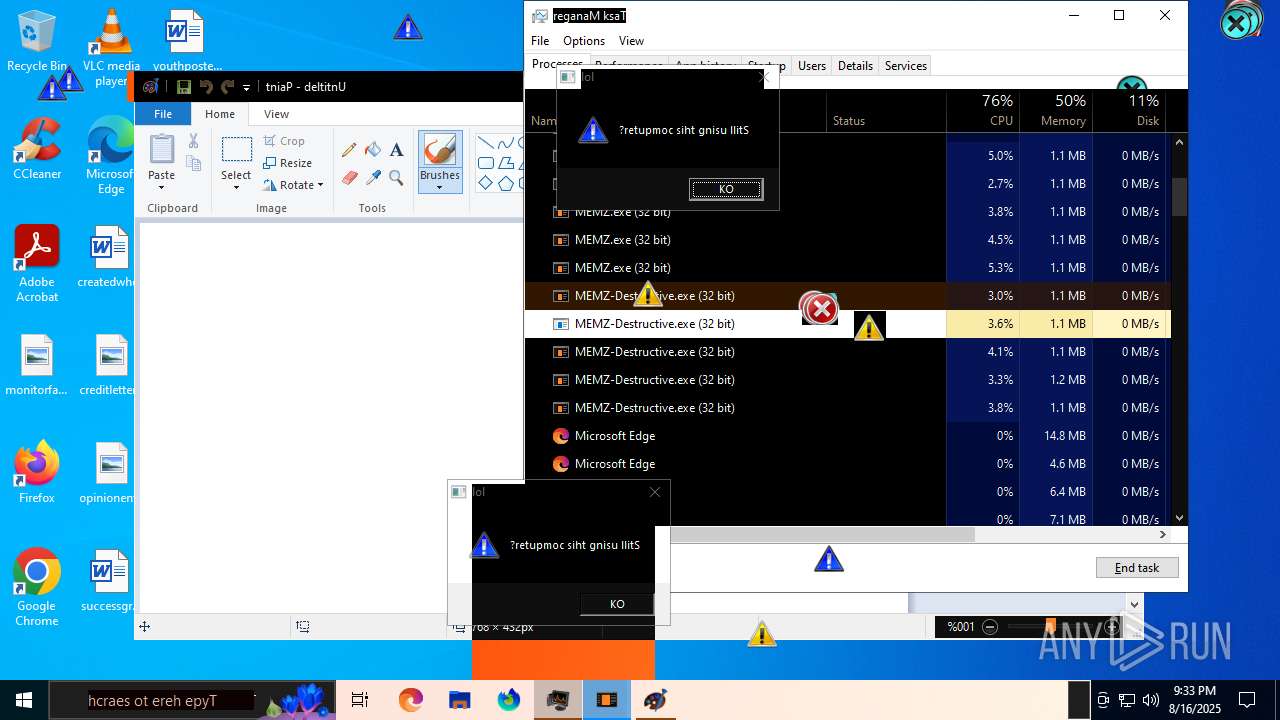
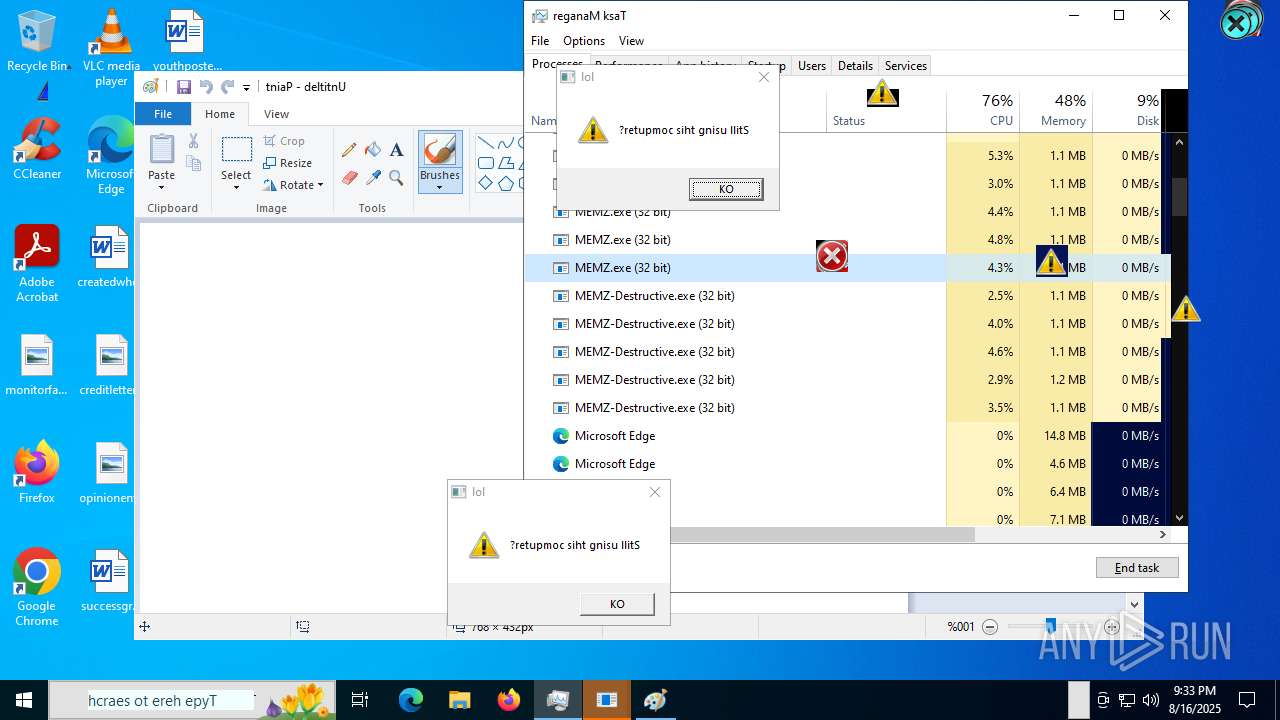
MALICIOUS
MEMZ has been detected (YARA)
- MEMZ-Destructive.exe (PID: 7796)
- MEMZ-Destructive.exe (PID: 3852)
- MEMZ-Destructive.exe (PID: 7700)
- MEMZ-Destructive.exe (PID: 7676)
- MEMZ-Destructive.exe (PID: 7716)
- MEMZ-Destructive.exe (PID: 7848)
- MEMZ.exe (PID: 2668)
- MEMZ.exe (PID: 1216)
- MEMZ.exe (PID: 3800)
- MEMZ.exe (PID: 2648)
- MEMZ.exe (PID: 3620)
- MEMZ.exe (PID: 6868)
- MEMZ.exe (PID: 6452)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- cscript.exe (PID: 420)
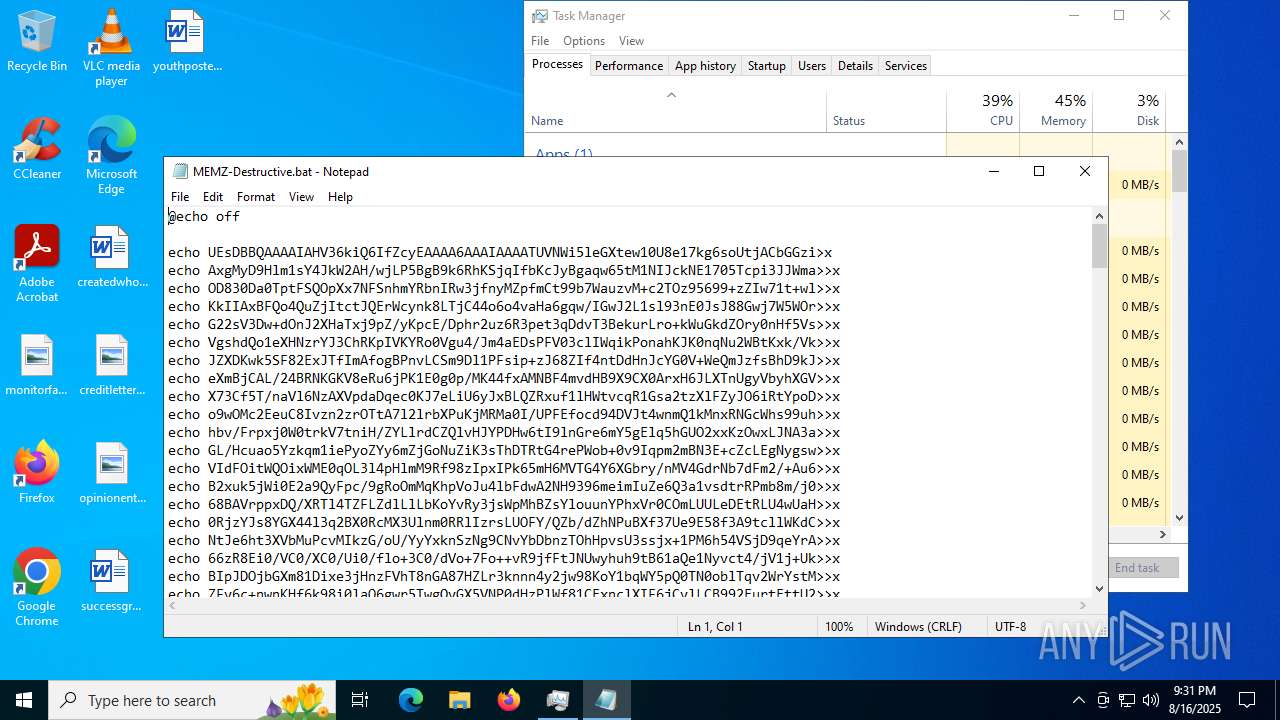
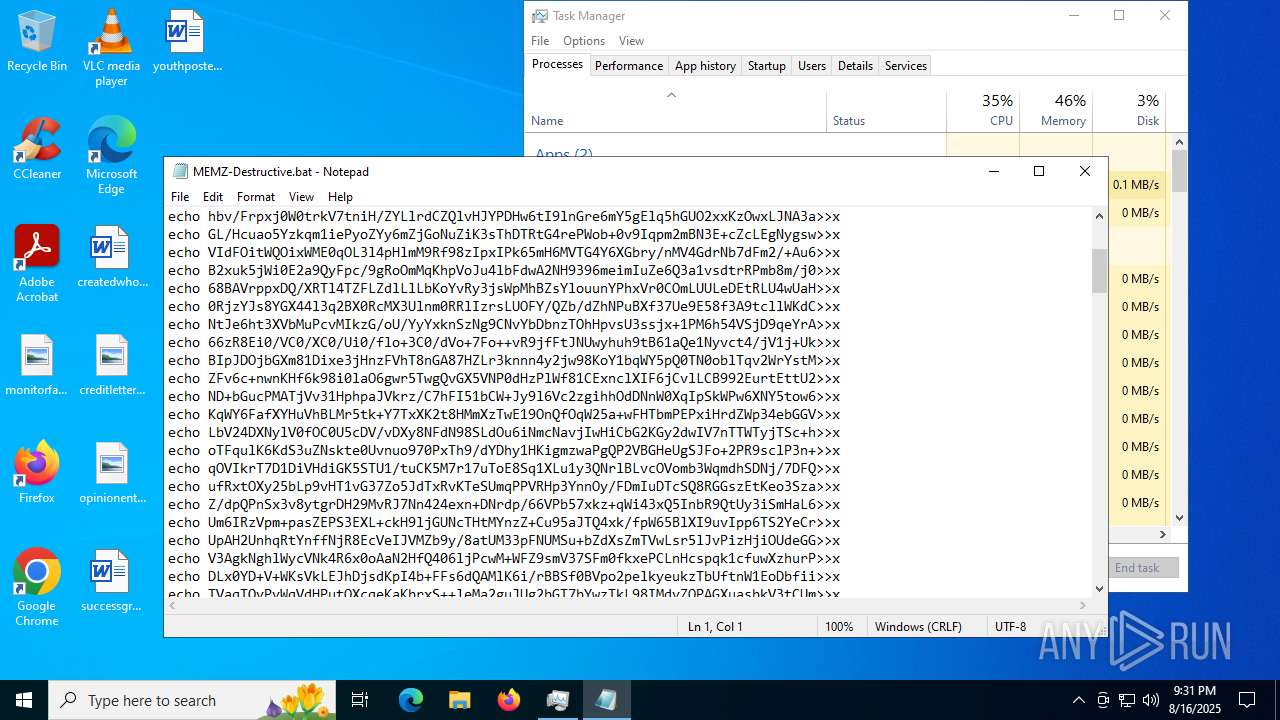
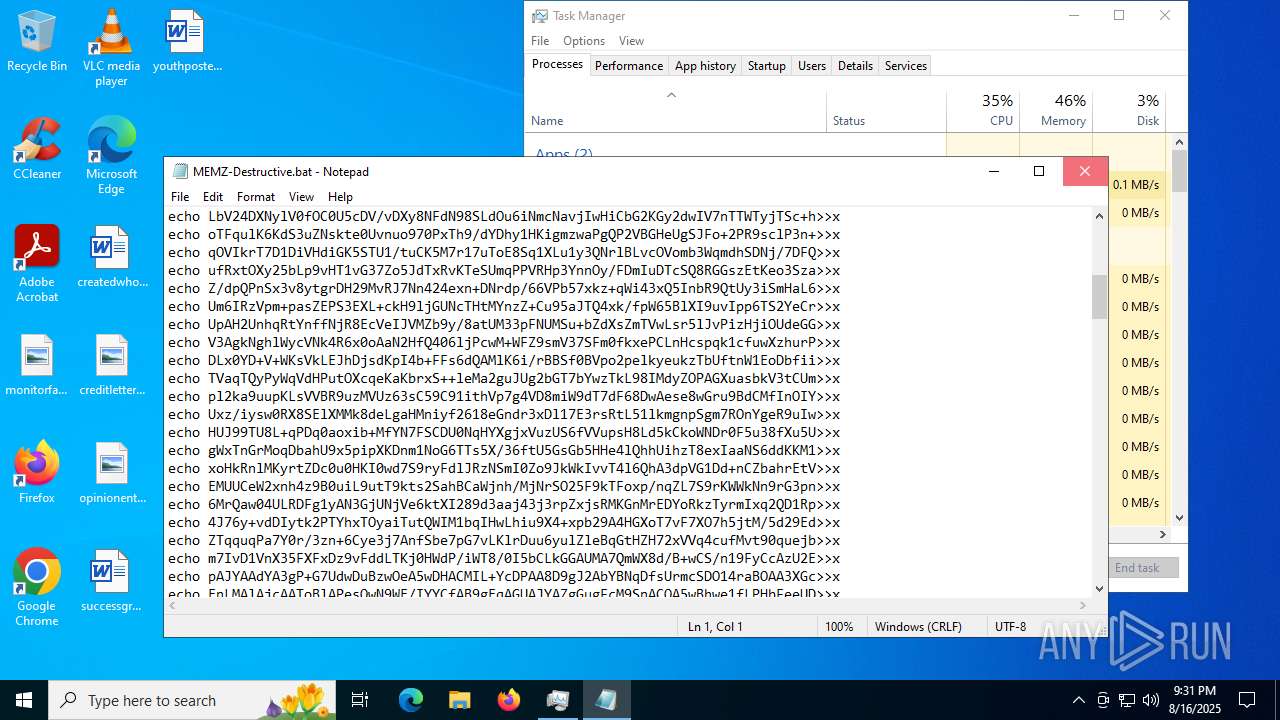
Uses base64 encoding (SCRIPT)
- cscript.exe (PID: 420)
SUSPICIOUS
Reads Internet Explorer settings
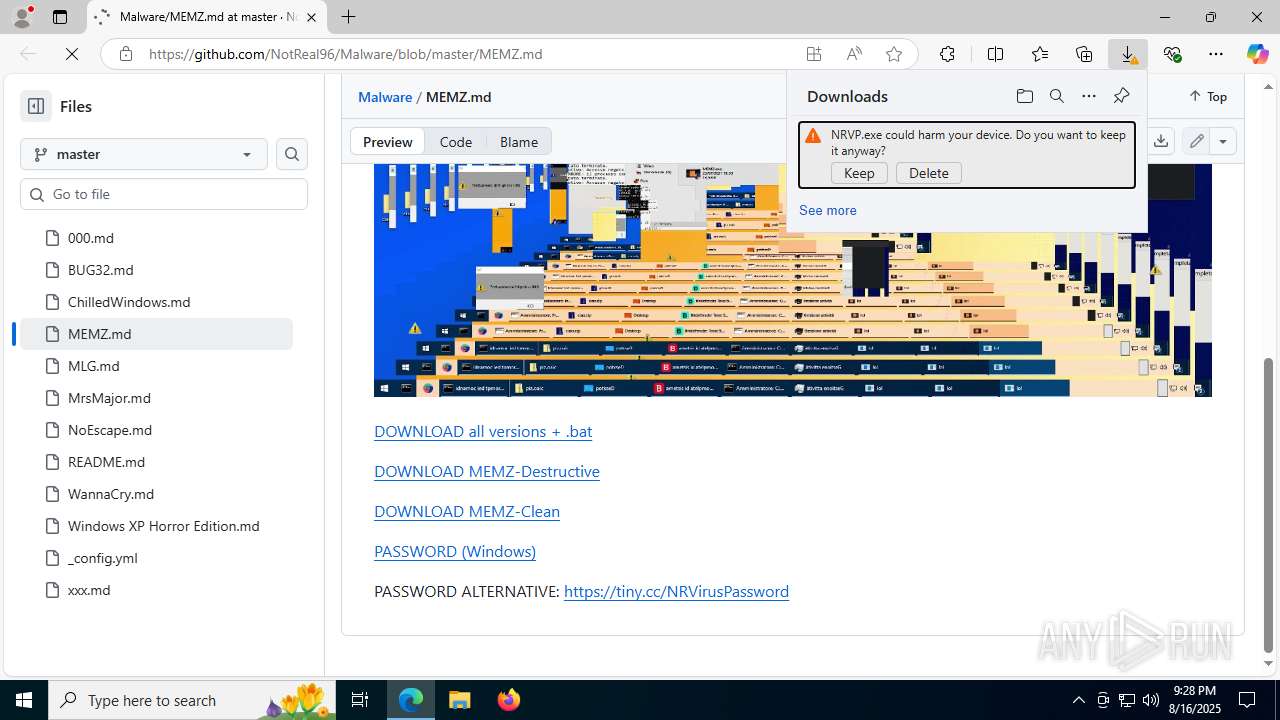
- NRVP.exe (PID: 7964)
Reads Microsoft Outlook installation path
- NRVP.exe (PID: 7964)
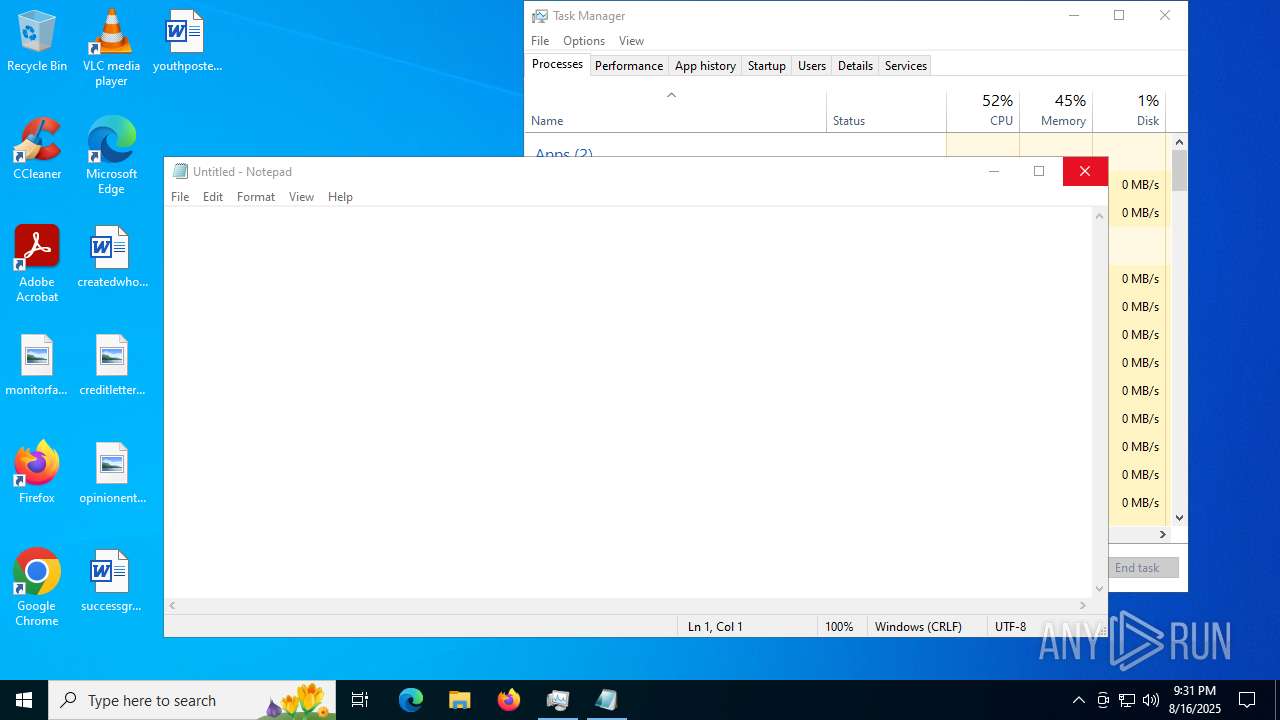
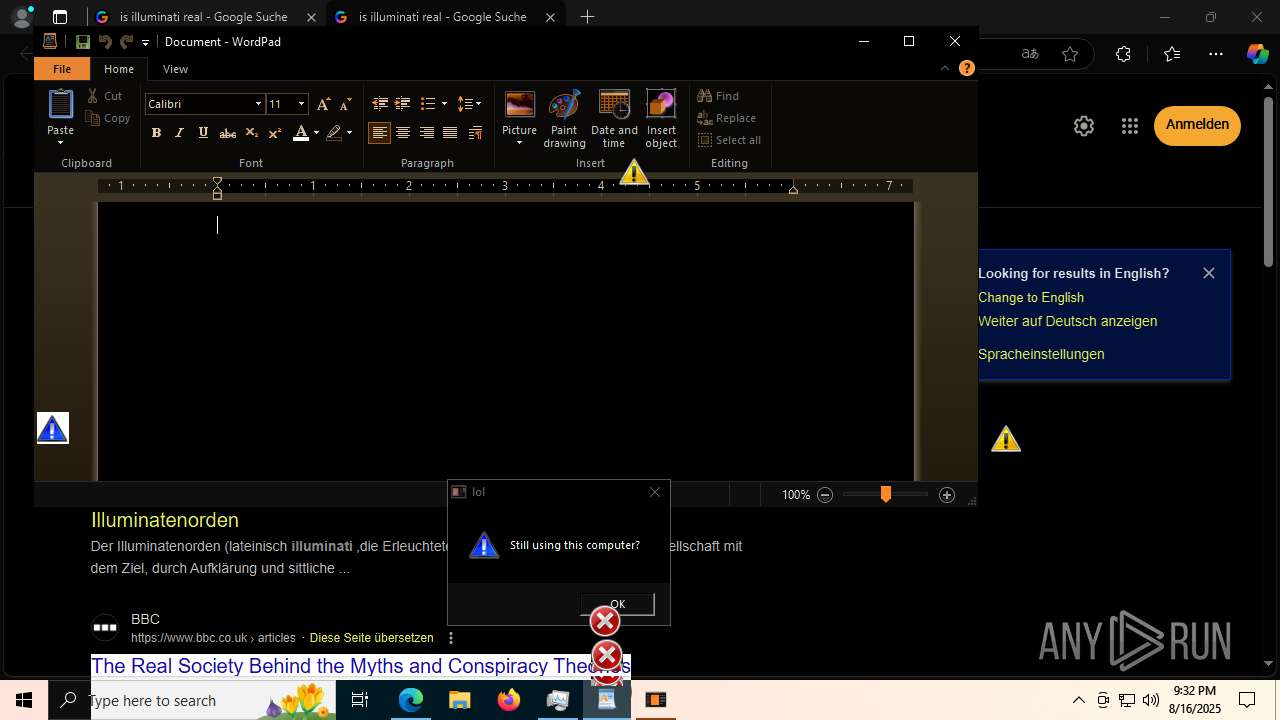
Application launched itself
- MEMZ-Destructive.exe (PID: 7932)
- MEMZ.exe (PID: 2668)
Reads security settings of Internet Explorer
- NRVP.exe (PID: 7964)
- MEMZ-Destructive.exe (PID: 7848)
- MEMZ.exe (PID: 2668)
- MEMZ-Destructive.exe (PID: 7932)
- MEMZ.exe (PID: 1216)
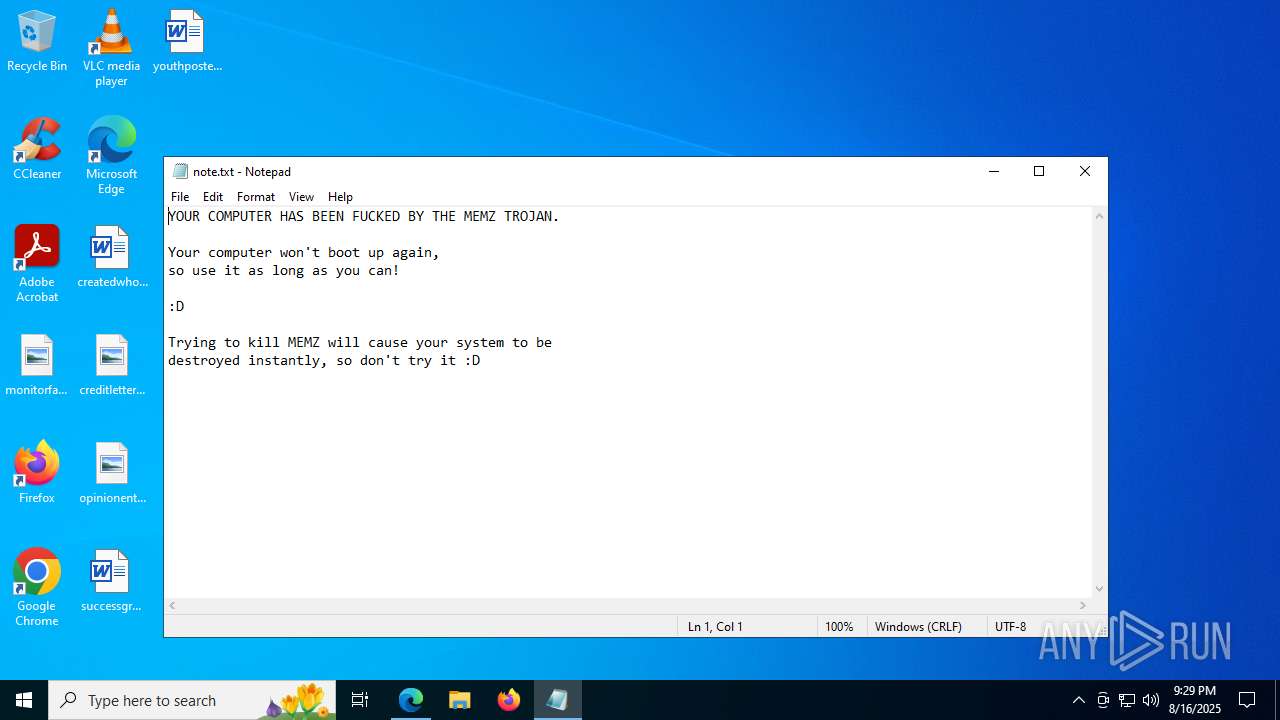
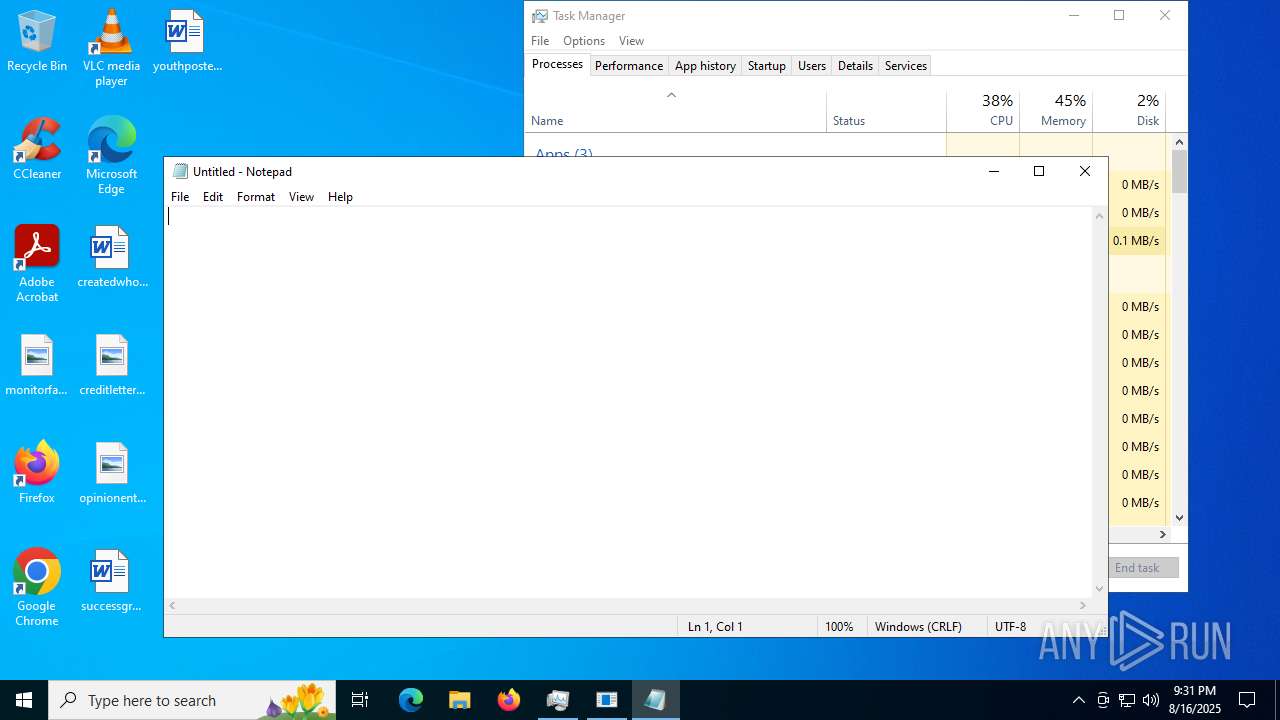
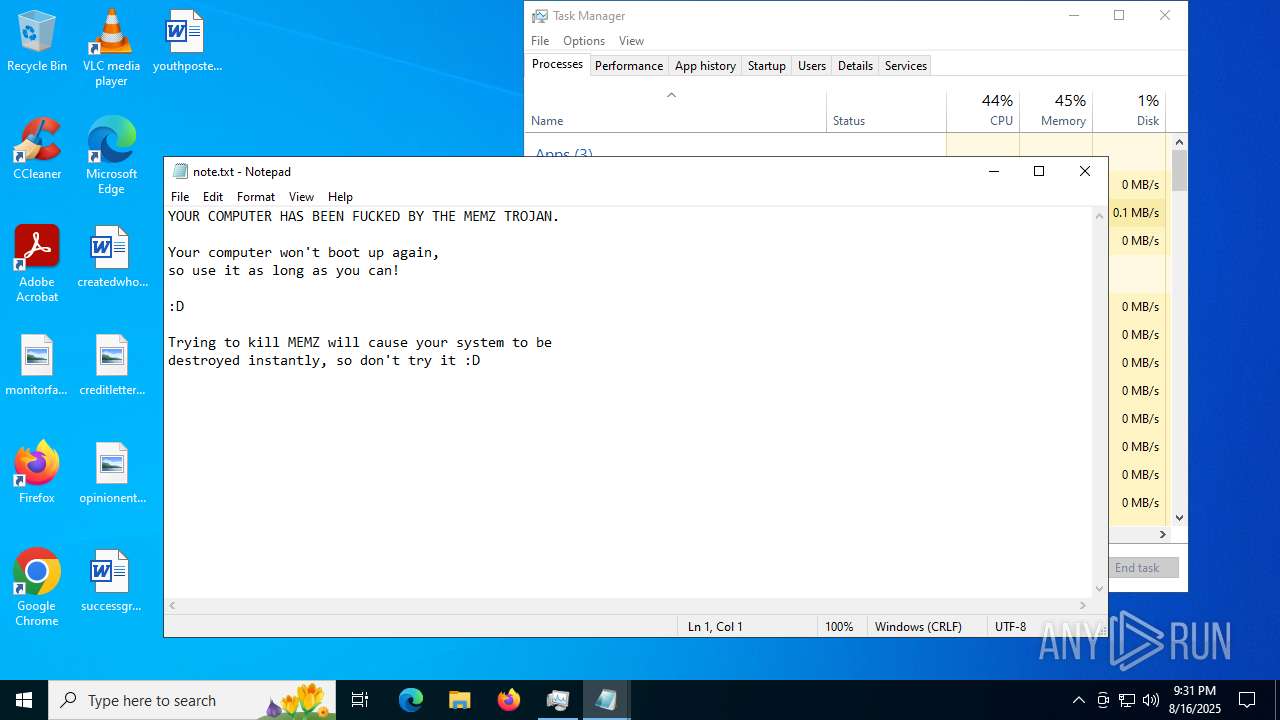
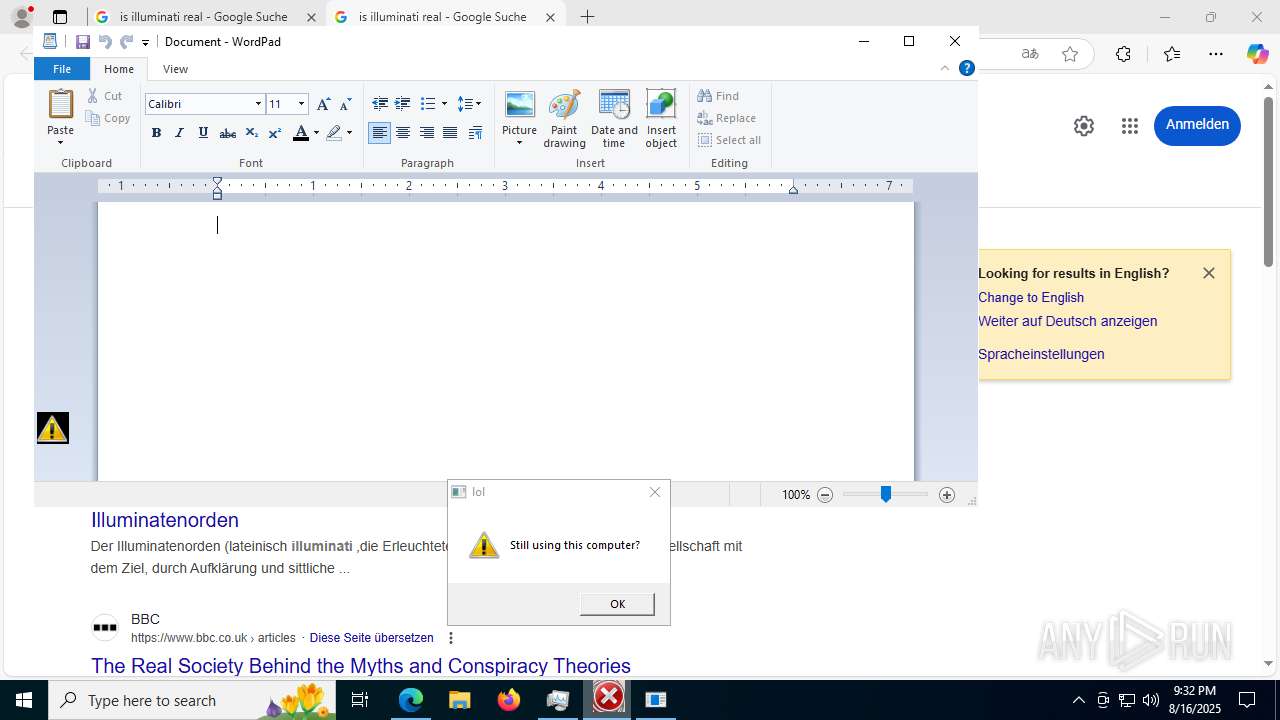
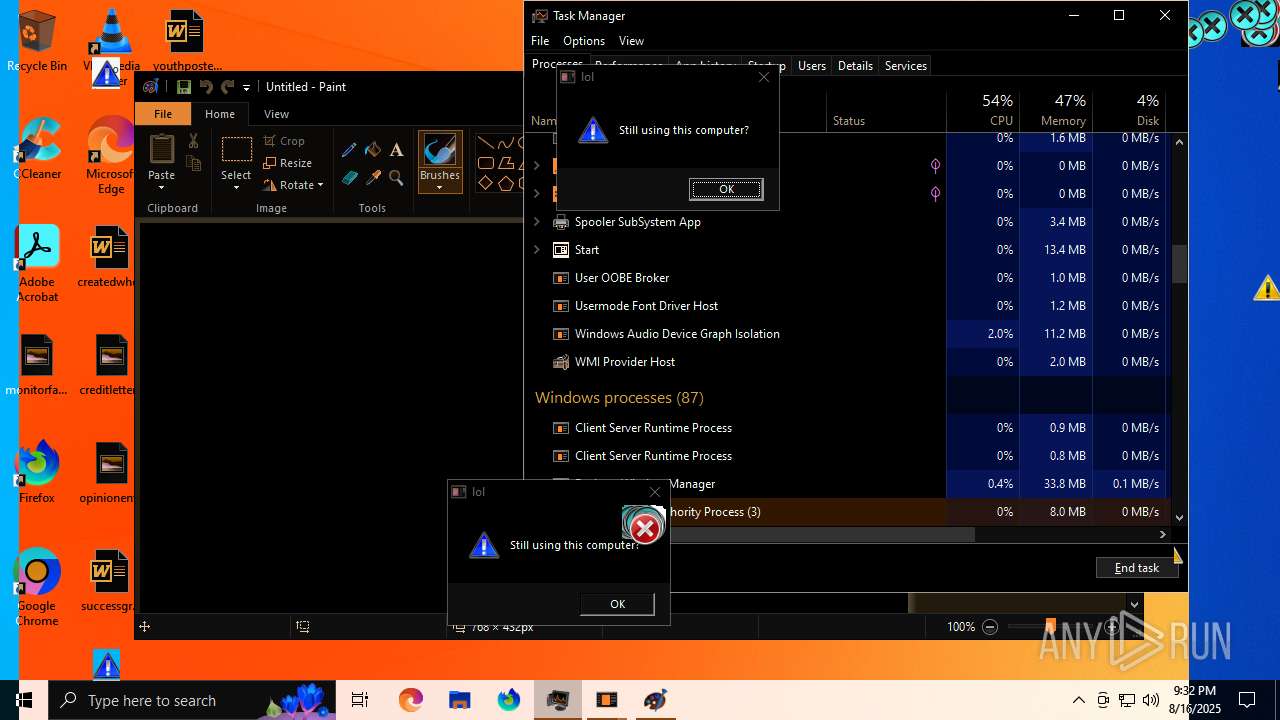
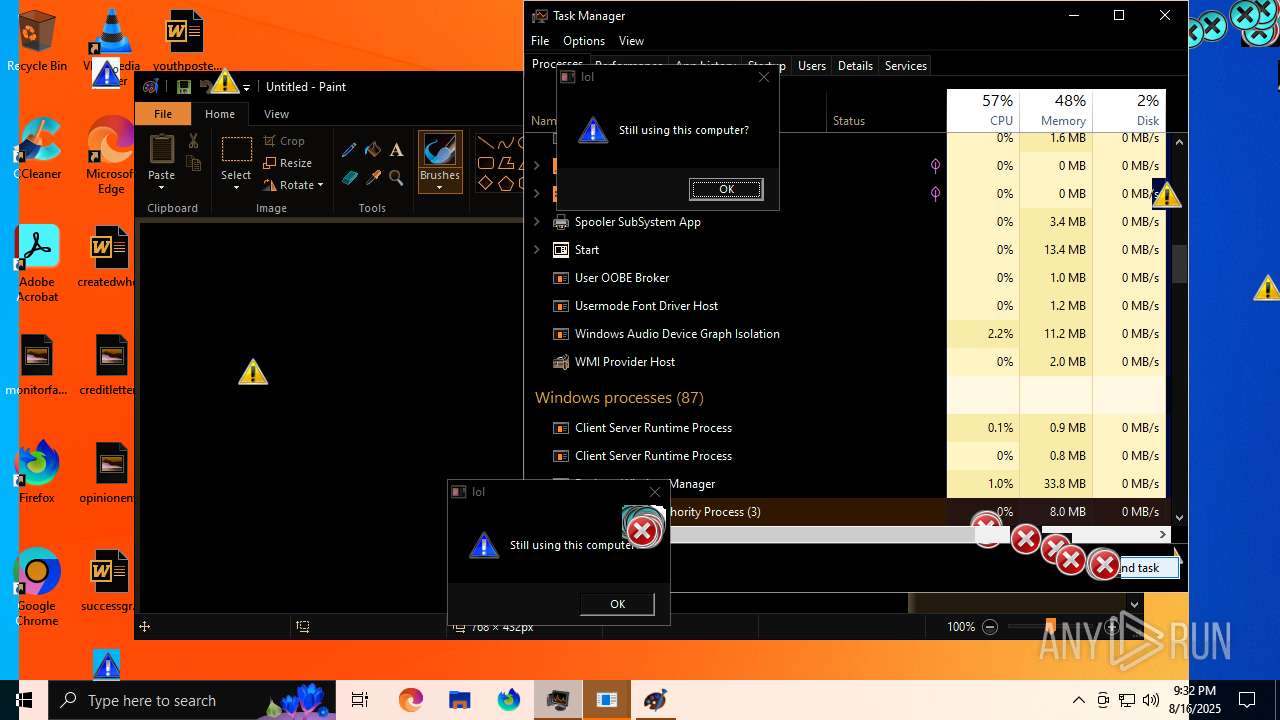
Start notepad (likely ransomware note)
- MEMZ-Destructive.exe (PID: 7848)
- MEMZ.exe (PID: 1216)
Creates file in the systems drive root
- MEMZ-Destructive.exe (PID: 7848)
- notepad.exe (PID: 8144)
- MEMZ.exe (PID: 1216)
- notepad.exe (PID: 8096)
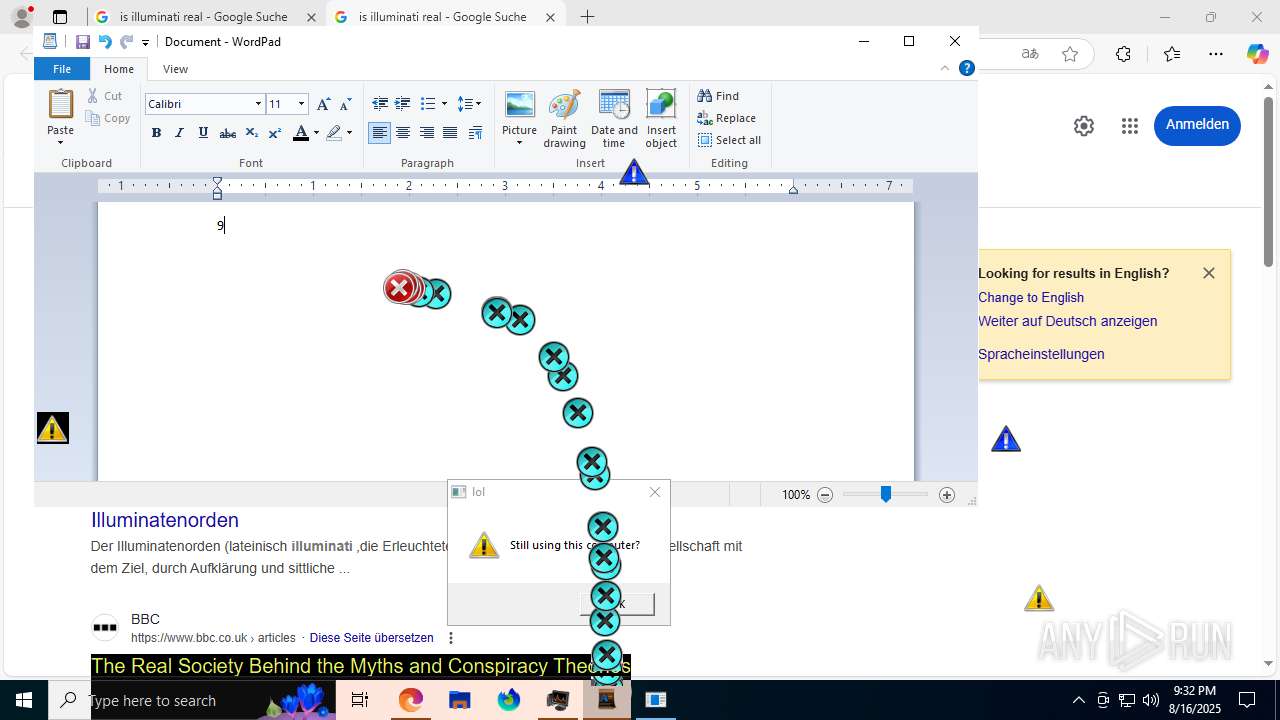
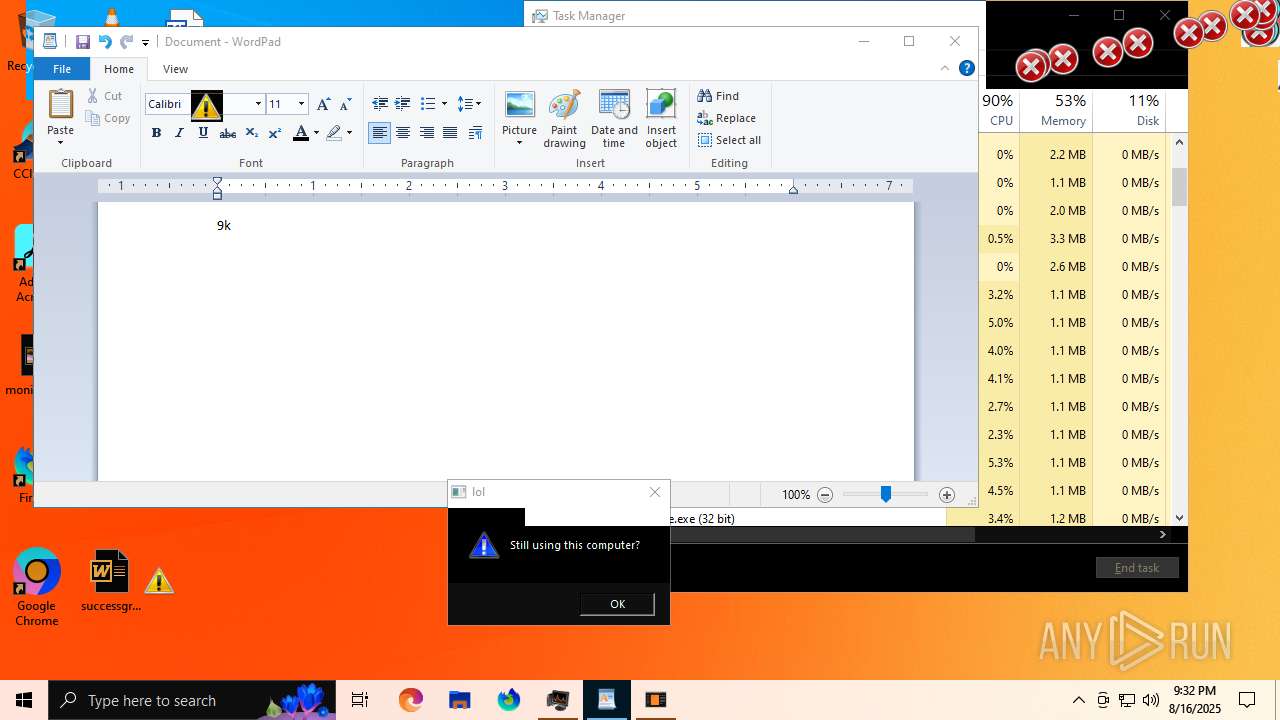
There is functionality for taking screenshot (YARA)
- MEMZ-Destructive.exe (PID: 7796)
- MEMZ-Destructive.exe (PID: 3852)
- MEMZ-Destructive.exe (PID: 7676)
- MEMZ-Destructive.exe (PID: 7716)
- MEMZ-Destructive.exe (PID: 7700)
- MEMZ-Destructive.exe (PID: 7848)
- MEMZ.exe (PID: 6868)
- MEMZ.exe (PID: 1216)
- MEMZ.exe (PID: 3800)
- MEMZ.exe (PID: 2648)
- MEMZ.exe (PID: 3620)
- MEMZ.exe (PID: 6452)
- MEMZ.exe (PID: 2668)
The process executes JS scripts
- cmd.exe (PID: 7184)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 420)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 420)
Creates XML DOM element (SCRIPT)
- cscript.exe (PID: 420)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 420)
Script creates XML DOM node (SCRIPT)
- cscript.exe (PID: 420)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 420)
Creates a Folder object (SCRIPT)
- cscript.exe (PID: 420)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 420)
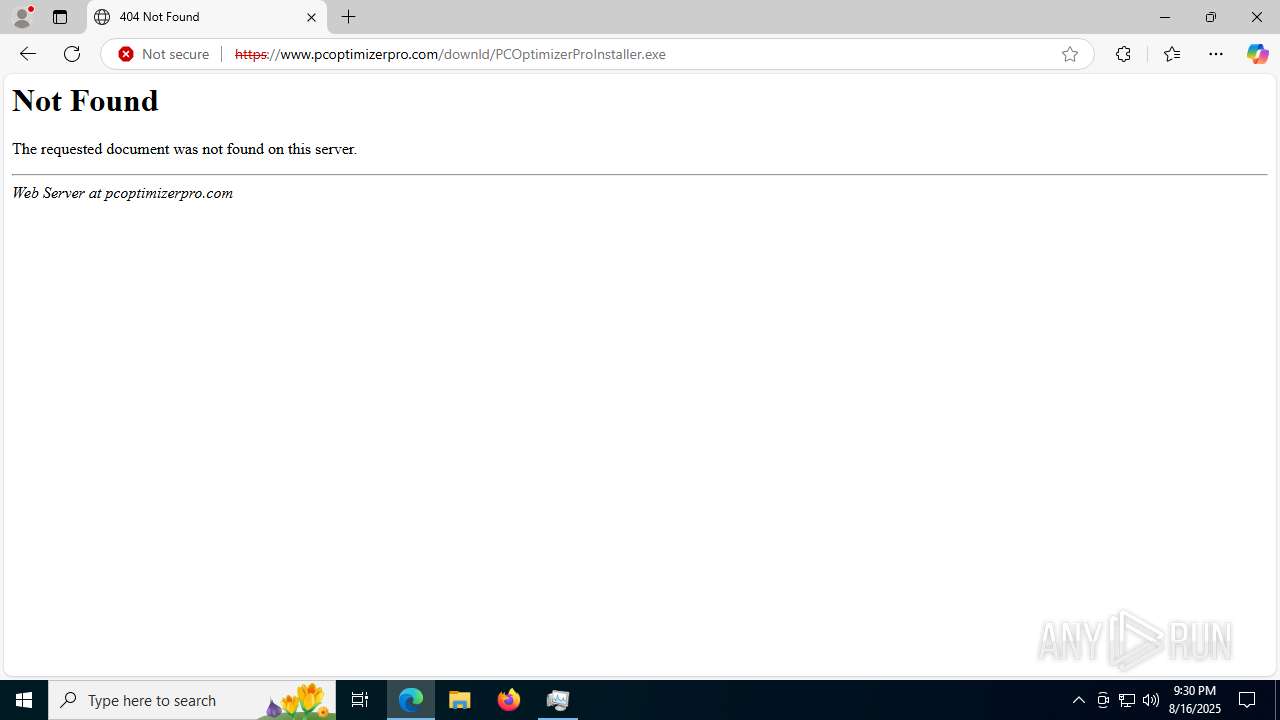
Executable content was dropped or overwritten
- cscript.exe (PID: 420)
INFO
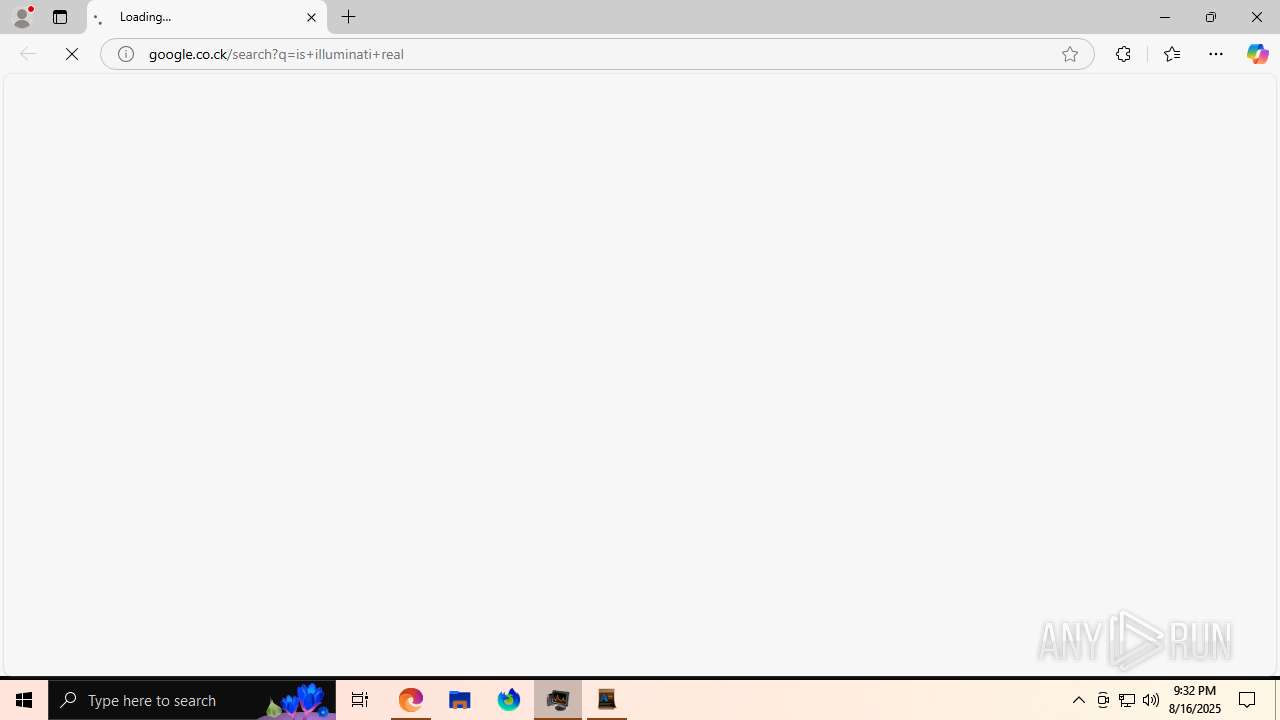
Application launched itself
- msedge.exe (PID: 6472)
- msedge.exe (PID: 3960)
- msedge.exe (PID: 7328)
- msedge.exe (PID: 1816)
- msedge.exe (PID: 5716)
- msedge.exe (PID: 4540)
- msedge.exe (PID: 7884)
- msedge.exe (PID: 6620)
- msedge.exe (PID: 4052)
- msedge.exe (PID: 1040)
- msedge.exe (PID: 7316)
- msedge.exe (PID: 2808)
- msedge.exe (PID: 2580)
- msedge.exe (PID: 1632)
- msedge.exe (PID: 3092)
- msedge.exe (PID: 6428)
- msedge.exe (PID: 5400)
- msedge.exe (PID: 1844)
- msedge.exe (PID: 5468)
- msedge.exe (PID: 7480)
- msedge.exe (PID: 7616)
Checks supported languages
- NRVP.exe (PID: 7964)
- identity_helper.exe (PID: 7660)
- MEMZ-Destructive.exe (PID: 7796)
- MEMZ-Destructive.exe (PID: 7848)
- MEMZ-Destructive.exe (PID: 3852)
- MEMZ-Destructive.exe (PID: 7716)
- MEMZ-Destructive.exe (PID: 7676)
- MEMZ-Destructive.exe (PID: 7700)
- identity_helper.exe (PID: 7372)
- identity_helper.exe (PID: 2996)
- identity_helper.exe (PID: 3572)
- MEMZ.exe (PID: 2668)
- MEMZ.exe (PID: 3800)
- MEMZ.exe (PID: 6868)
- MEMZ.exe (PID: 6452)
- MEMZ-Destructive.exe (PID: 7932)
- MEMZ.exe (PID: 2648)
- MEMZ.exe (PID: 3620)
- MEMZ.exe (PID: 1216)
- wordpad.exe (PID: 6200)
- identity_helper.exe (PID: 7420)
- identity_helper.exe (PID: 6160)
- identity_helper.exe (PID: 7408)
- identity_helper.exe (PID: 8024)
- identity_helper.exe (PID: 2428)
- identity_helper.exe (PID: 6788)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6472)
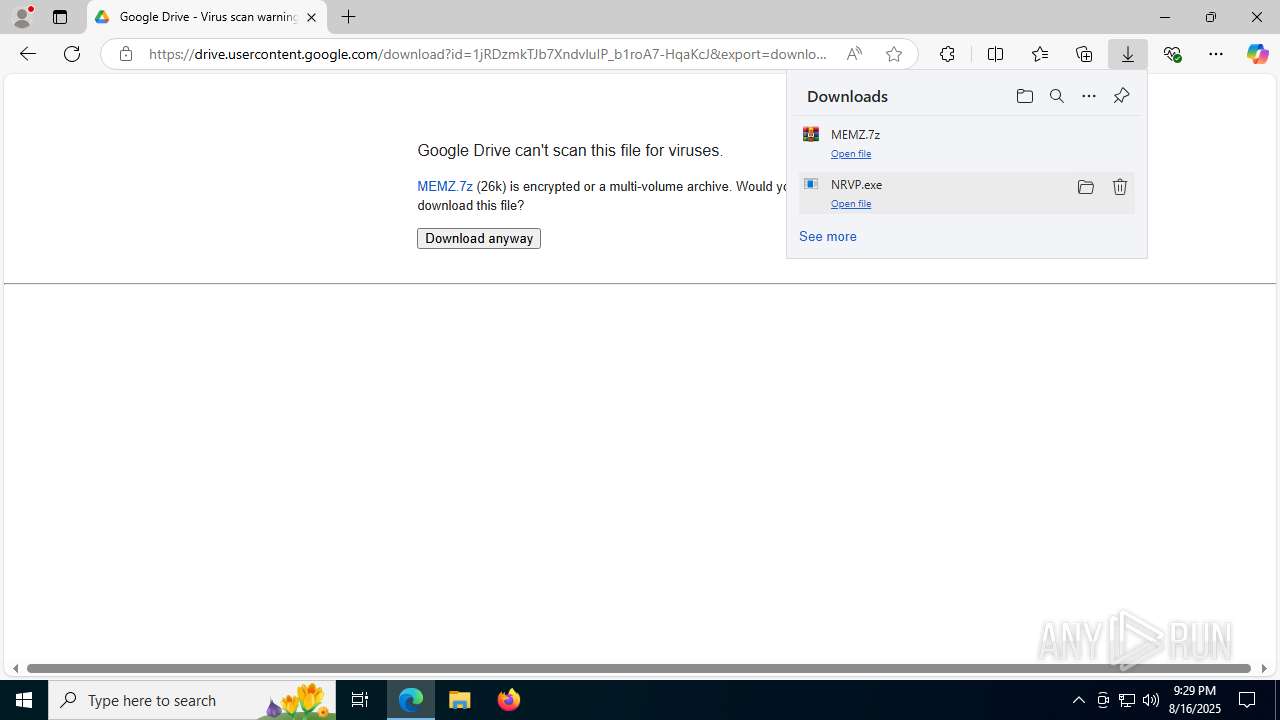
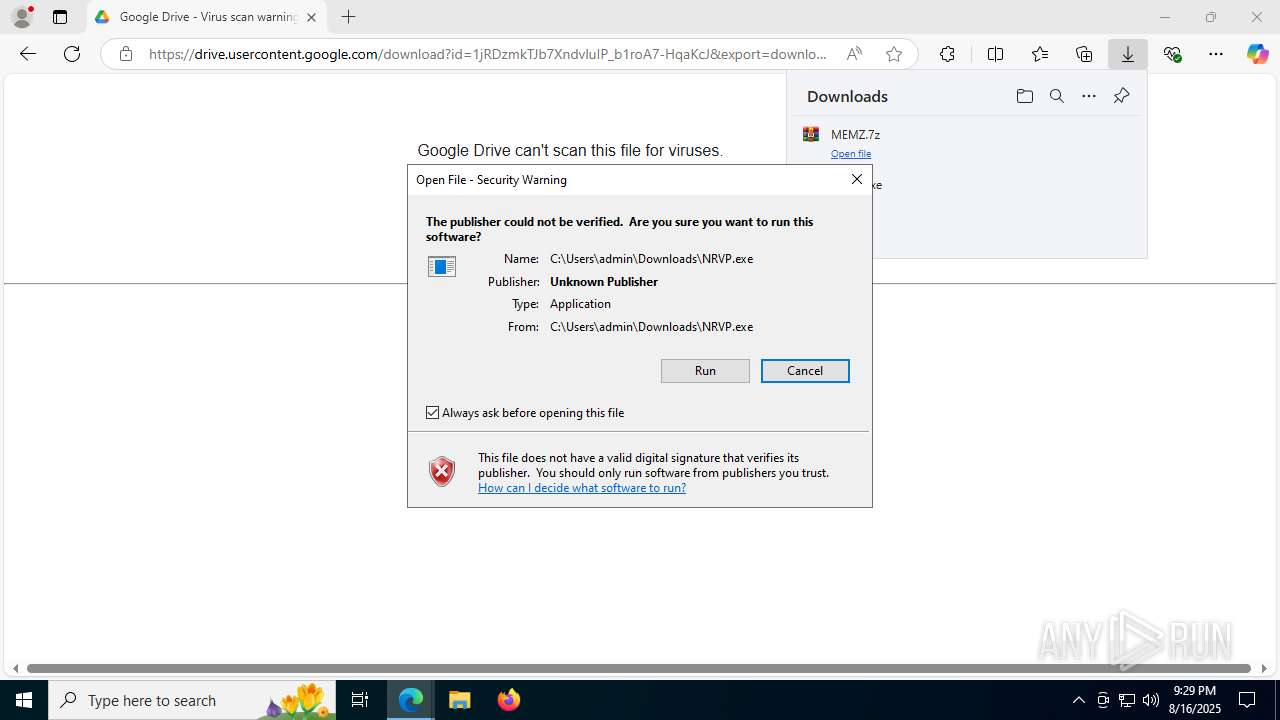
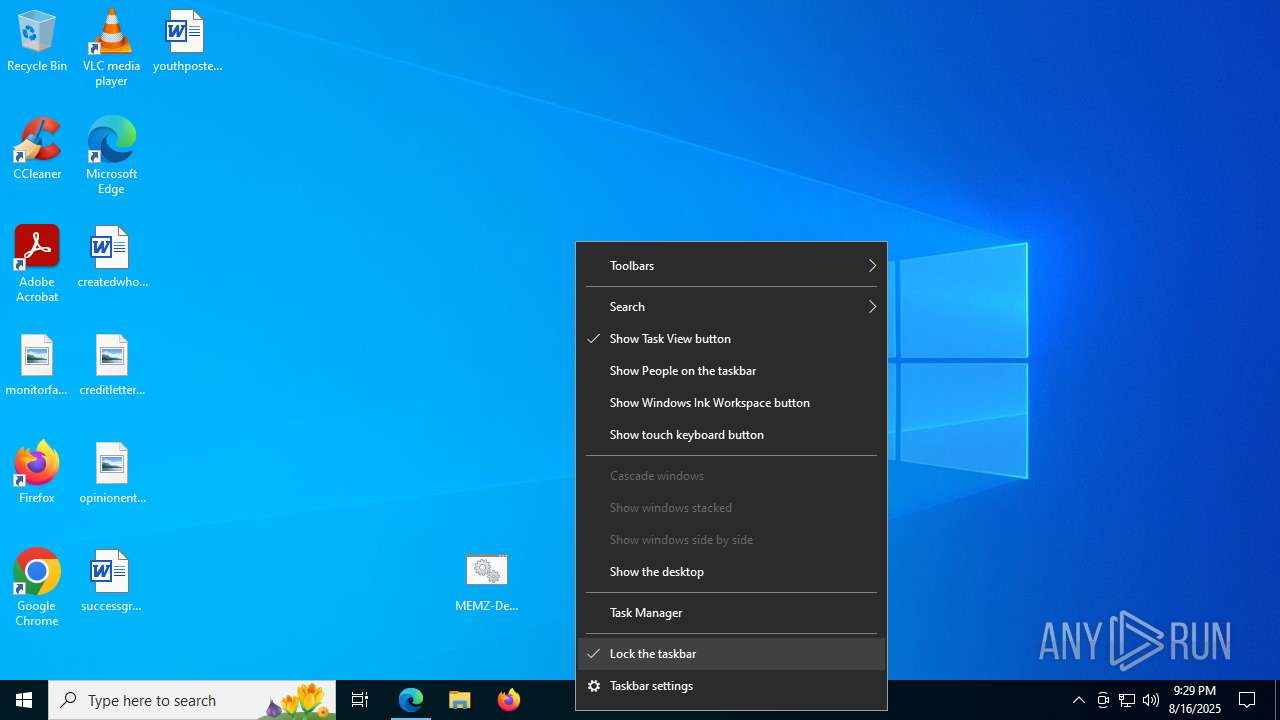
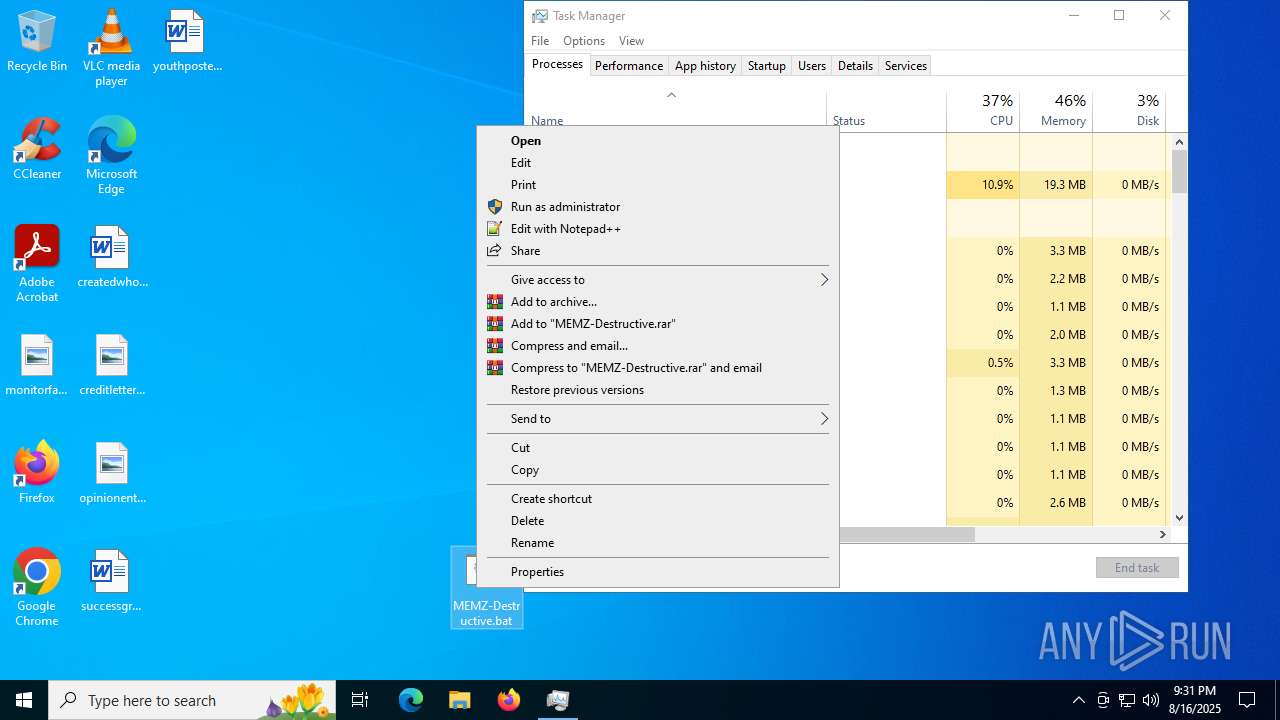
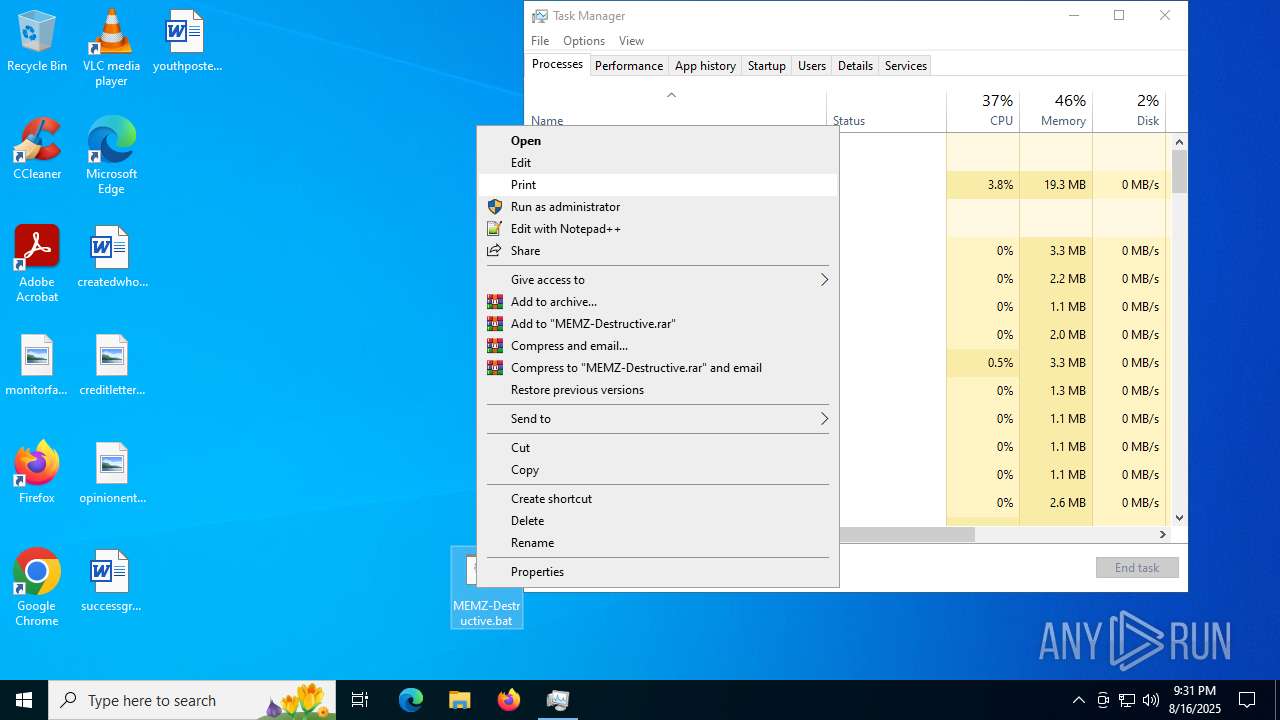
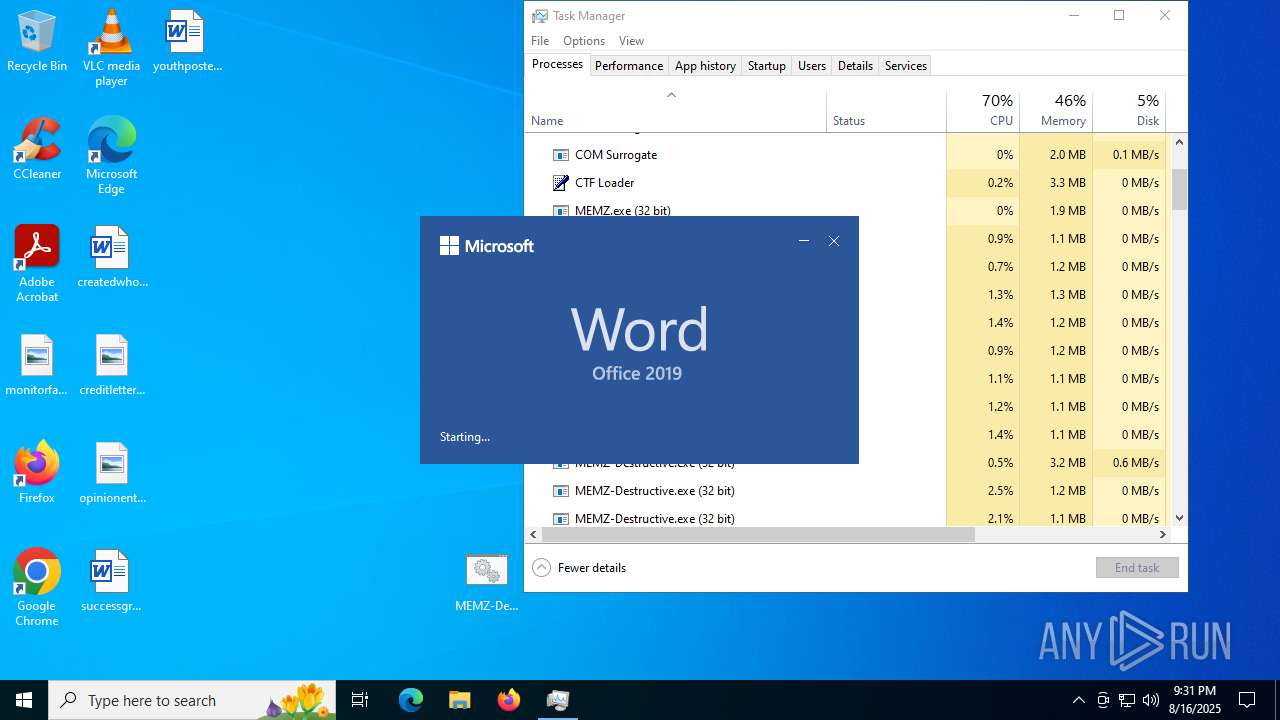
Manual execution by a user
- MEMZ-Destructive.exe (PID: 7748)
- MEMZ-Destructive.exe (PID: 7932)
- Taskmgr.exe (PID: 8080)
- Taskmgr.exe (PID: 7132)
- notepad.exe (PID: 4264)
- cmd.exe (PID: 7184)
- WINWORD.EXE (PID: 2168)
Reads the computer name
- MEMZ-Destructive.exe (PID: 7932)
- identity_helper.exe (PID: 7660)
- NRVP.exe (PID: 7964)
- MEMZ-Destructive.exe (PID: 7848)
- identity_helper.exe (PID: 7372)
- identity_helper.exe (PID: 2996)
- identity_helper.exe (PID: 3572)
- MEMZ.exe (PID: 2668)
- MEMZ.exe (PID: 1216)
- identity_helper.exe (PID: 7408)
- identity_helper.exe (PID: 6160)
- identity_helper.exe (PID: 7420)
- wordpad.exe (PID: 6200)
- identity_helper.exe (PID: 8024)
- identity_helper.exe (PID: 2428)
- MEMZ.exe (PID: 6452)
- MEMZ.exe (PID: 6868)
- MEMZ.exe (PID: 2648)
- MEMZ.exe (PID: 3620)
- identity_helper.exe (PID: 6788)
The sample compiled with english language support
- msedge.exe (PID: 6472)
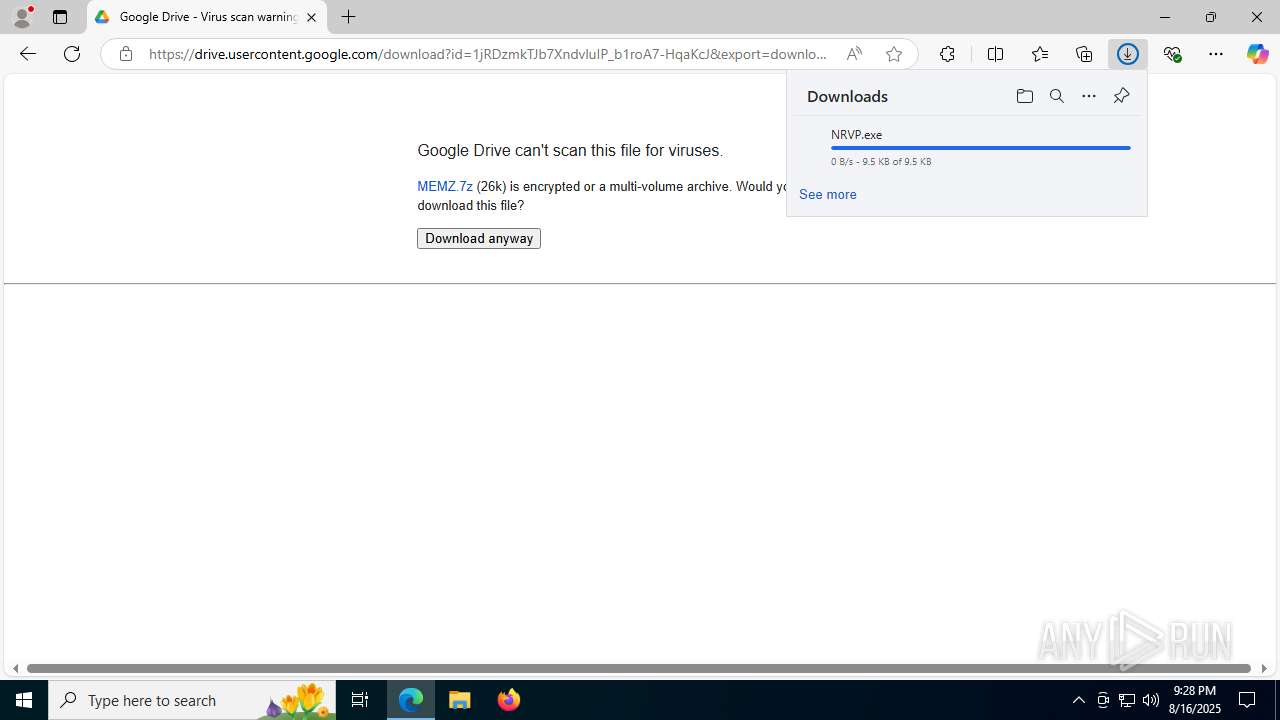
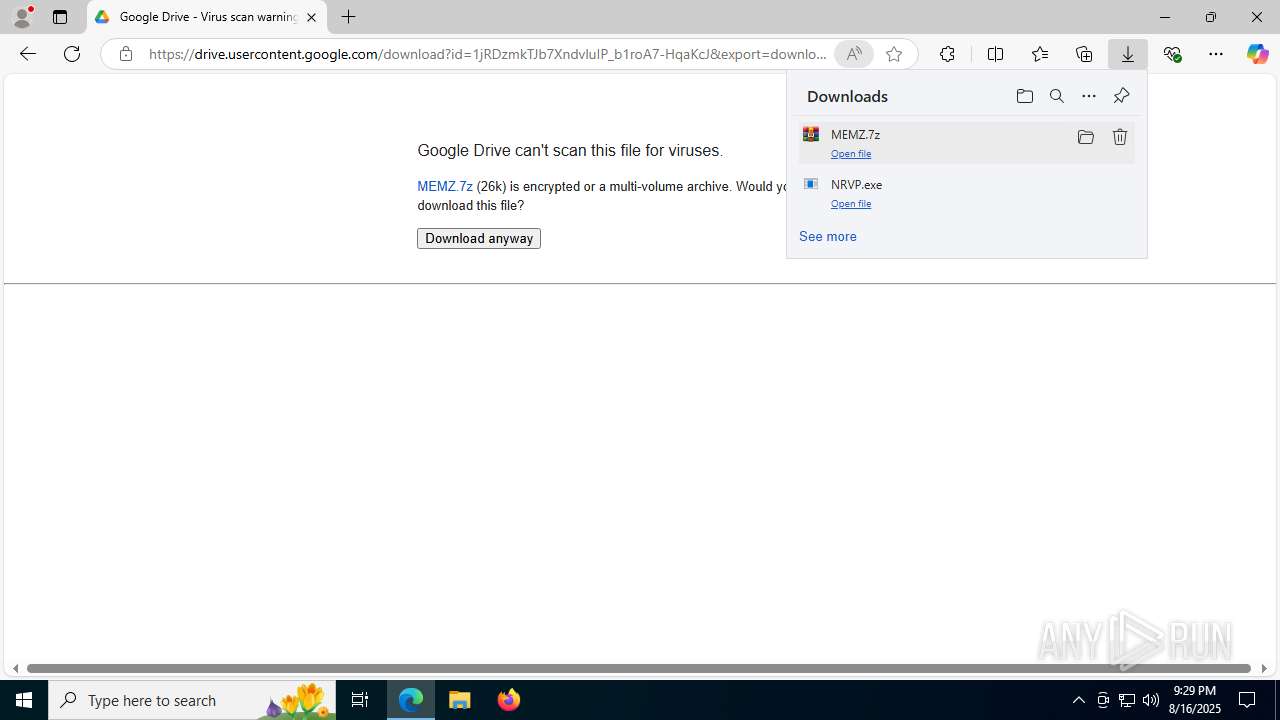
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7440)
- msedge.exe (PID: 6472)
Reads Environment values
- identity_helper.exe (PID: 7660)
- identity_helper.exe (PID: 2996)
- identity_helper.exe (PID: 3572)
- identity_helper.exe (PID: 7372)
- identity_helper.exe (PID: 7408)
- identity_helper.exe (PID: 6160)
- identity_helper.exe (PID: 7420)
- identity_helper.exe (PID: 8024)
- identity_helper.exe (PID: 2428)
- identity_helper.exe (PID: 6788)
Launching a file from the Downloads directory
- msedge.exe (PID: 6472)
Checks proxy server information
- NRVP.exe (PID: 7964)
- slui.exe (PID: 2804)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8144)
- Taskmgr.exe (PID: 7132)
- notepad.exe (PID: 4264)
- cscript.exe (PID: 420)
- notepad.exe (PID: 8096)
- splwow64.exe (PID: 7332)
Process checks computer location settings
- MEMZ-Destructive.exe (PID: 7848)
- MEMZ-Destructive.exe (PID: 7932)
- MEMZ.exe (PID: 2668)
- MEMZ.exe (PID: 1216)
Reads the machine GUID from the registry
- MEMZ-Destructive.exe (PID: 7848)
- MEMZ.exe (PID: 1216)
- MEMZ.exe (PID: 6868)
- MEMZ.exe (PID: 2648)
- MEMZ.exe (PID: 6452)
- MEMZ.exe (PID: 3620)
Reads the software policy settings
- slui.exe (PID: 2804)
Creates files or folders in the user directory
- cscript.exe (PID: 420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
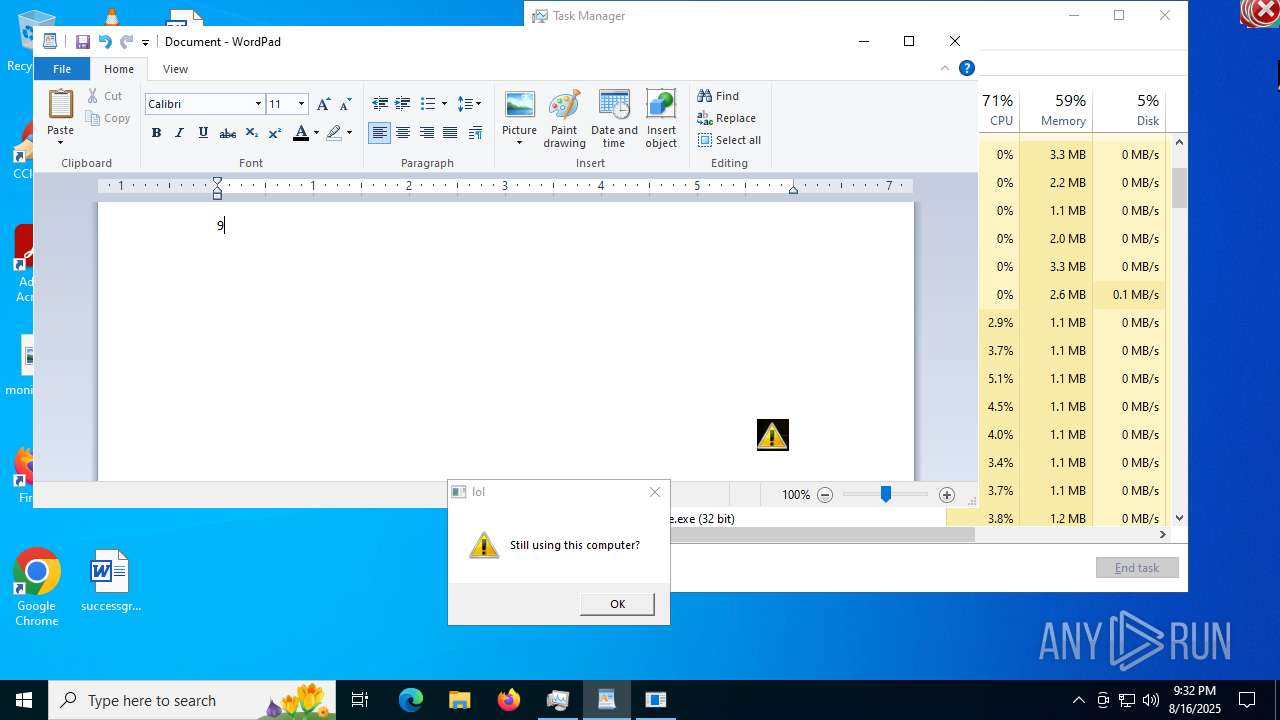
Total processes
382
Monitored processes
222
Malicious processes
16
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=5380,i,12898217080089854484,8020450012752467986,262144 --variations-seed-version --mojo-platform-channel-handle=5336 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 420 | cscript x.js | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --always-read-main-dll --field-trial-handle=6140,i,3116375462400096496,2090579248435179675,262144 --variations-seed-version --mojo-platform-channel-handle=5216 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2304,i,12216858201648086856,17885201900076769728,262144 --variations-seed-version --mojo-platform-channel-handle=2296 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=6072,i,7067083971777556600,14850320666043633392,262144 --variations-seed-version --mojo-platform-channel-handle=5680 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 952 | "C:\Windows\System32\mspaint.exe" | C:\Windows\SysWOW64\mspaint.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Paint Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2180,i,1176119551497168989,10303568947680322887,262144 --variations-seed-version --mojo-platform-channel-handle=2548 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4648,i,12216858201648086856,17885201900076769728,262144 --variations-seed-version --mojo-platform-channel-handle=4768 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "D0899128-88CA-4CBF-A3C4-C03DFE028DB7" "F02A1F13-BE91-43AD-92DD-5D3D1035F6FC" "2168" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
Total events
53 208
Read events
52 674
Write events
506
Delete events
28
Modification events
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 749CAA79189B2F00 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590632 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FF7D6A7E-E3A7-4D8C-B87C-9017E37DE10C} | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590632 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {23B2C601-771A-4C93-93F1-0EB688BB6C8C} | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590632 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {41FEC58C-092E-474B-8058-1ED74FA3CF3E} | |||
Executable files
44
Suspicious files
1 057
Text files
411
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d8c7.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d8c7.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d8c7.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d8c7.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d8e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
460
DNS requests
491
Threats
131
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.1.250.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5884 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:lFn4fMWsABHKNsPbuzE8YD0QF122lw6xxpJQvCG8W7Q&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5644 | svchost.exe | GET | 200 | 104.78.173.167:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4844 | svchost.exe | GET | 206 | 62.115.253.208:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755916477&P2=404&P3=2&P4=clk8OlYfg6CCXeNmiDVrXydTWest9TeFtYuWfwO4VBZPvHFlxLEuqdgtbifUDWOk%2bKn5P6fE4je4xQjQ5eV4mw%3d%3d | unknown | — | — | whitelisted |
4844 | svchost.exe | GET | 200 | 62.115.253.208:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1755909279&P2=404&P3=2&P4=XdBlya0N8W9LeoyHY7cQNp8MZ0wLeENeRWoENiy1RQWy0CVYFqXwj5IS1fWT8bMtzaOLEM1qACwnAkoTih5%2fNA%3d%3d | unknown | — | — | whitelisted |
4844 | svchost.exe | GET | 206 | 62.115.253.208:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755916477&P2=404&P3=2&P4=clk8OlYfg6CCXeNmiDVrXydTWest9TeFtYuWfwO4VBZPvHFlxLEuqdgtbifUDWOk%2bKn5P6fE4je4xQjQ5eV4mw%3d%3d | unknown | — | — | whitelisted |
2464 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://zerossl.crt.sectigo.com/ZeroSSLRSADomainSecureSiteCA.crt | unknown | — | — | whitelisted |
2464 | msedge.exe | GET | 204 | 150.171.74.11:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | unknown | — | — | whitelisted |
7896 | backgroundTaskHost.exe | GET | 200 | 23.10.239.251:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 62.115.253.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5432 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5884 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5884 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5884 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5884 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
5884 | msedge.exe | 62.115.253.98:443 | copilot.microsoft.com | Telia Company AB | ES | whitelisted |
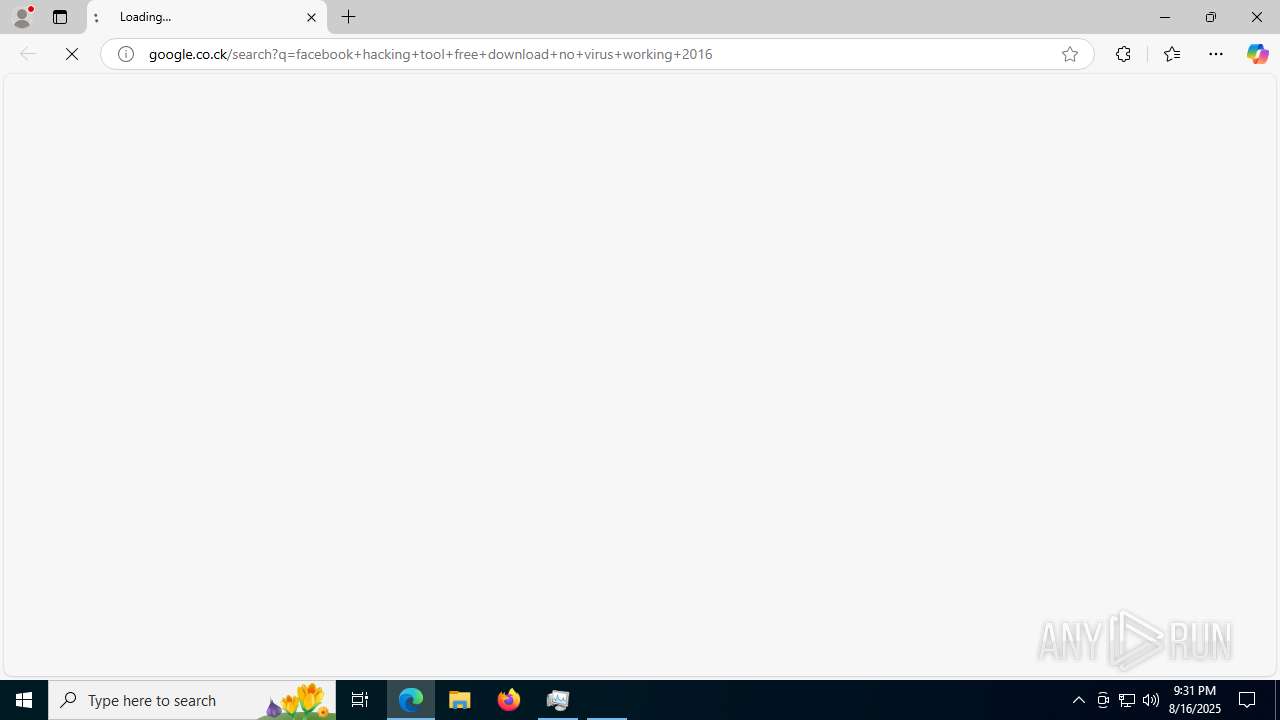
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
www.bing.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5884 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2464 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2464 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2464 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2464 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2464 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|