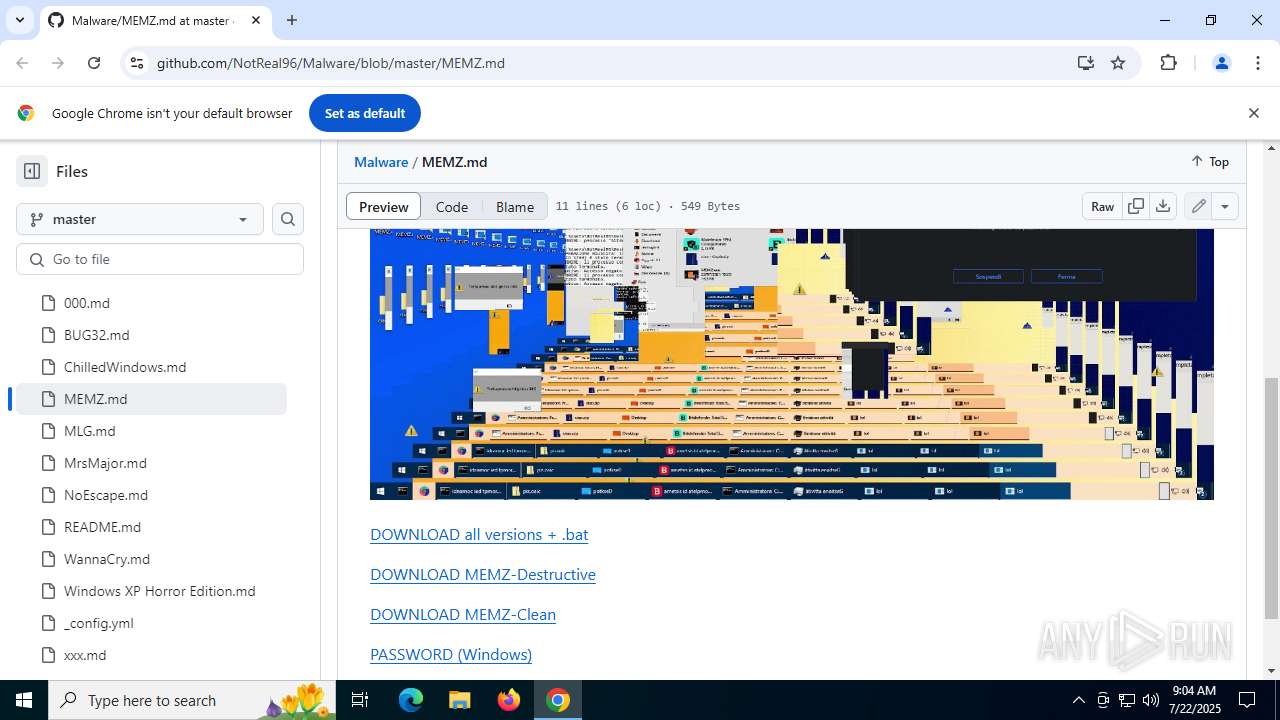
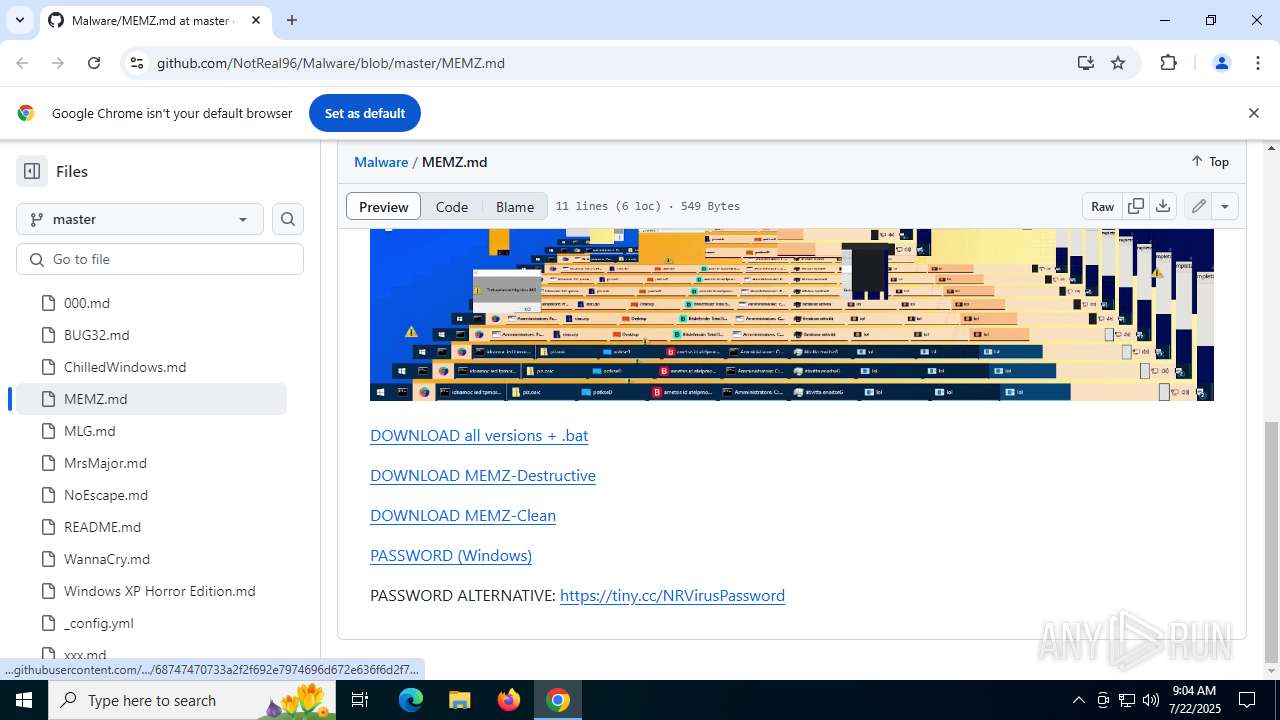
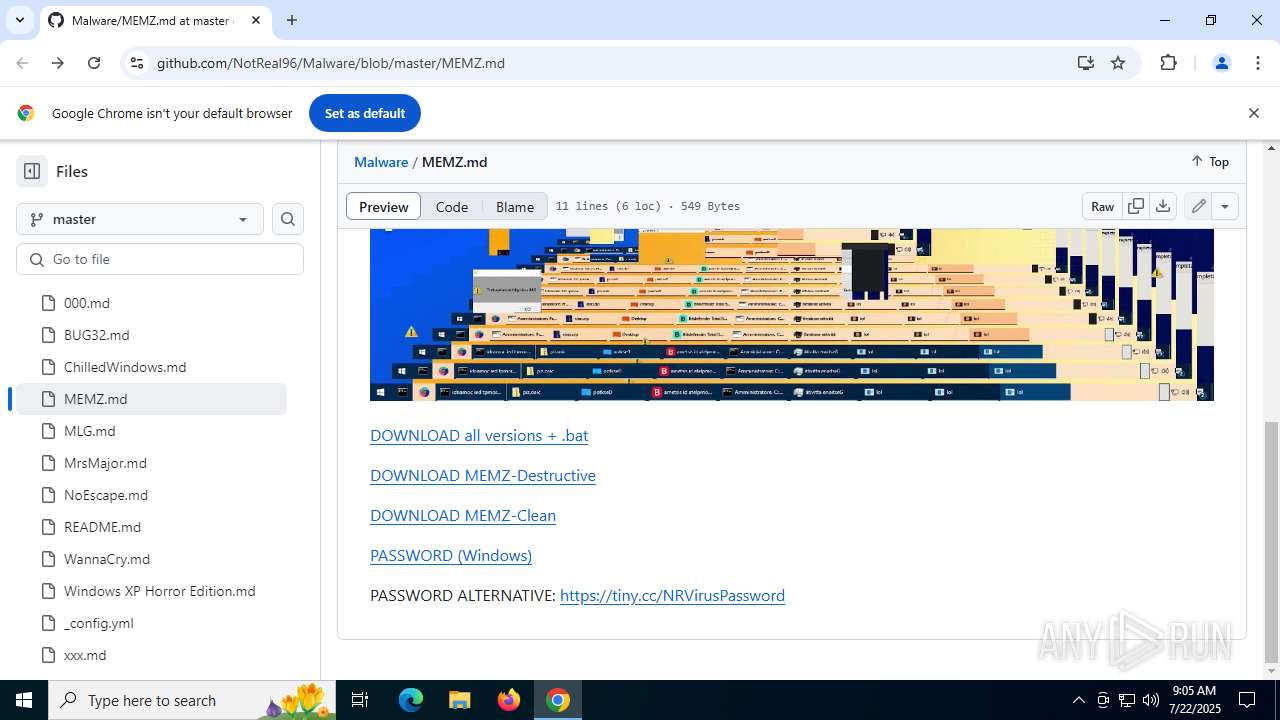
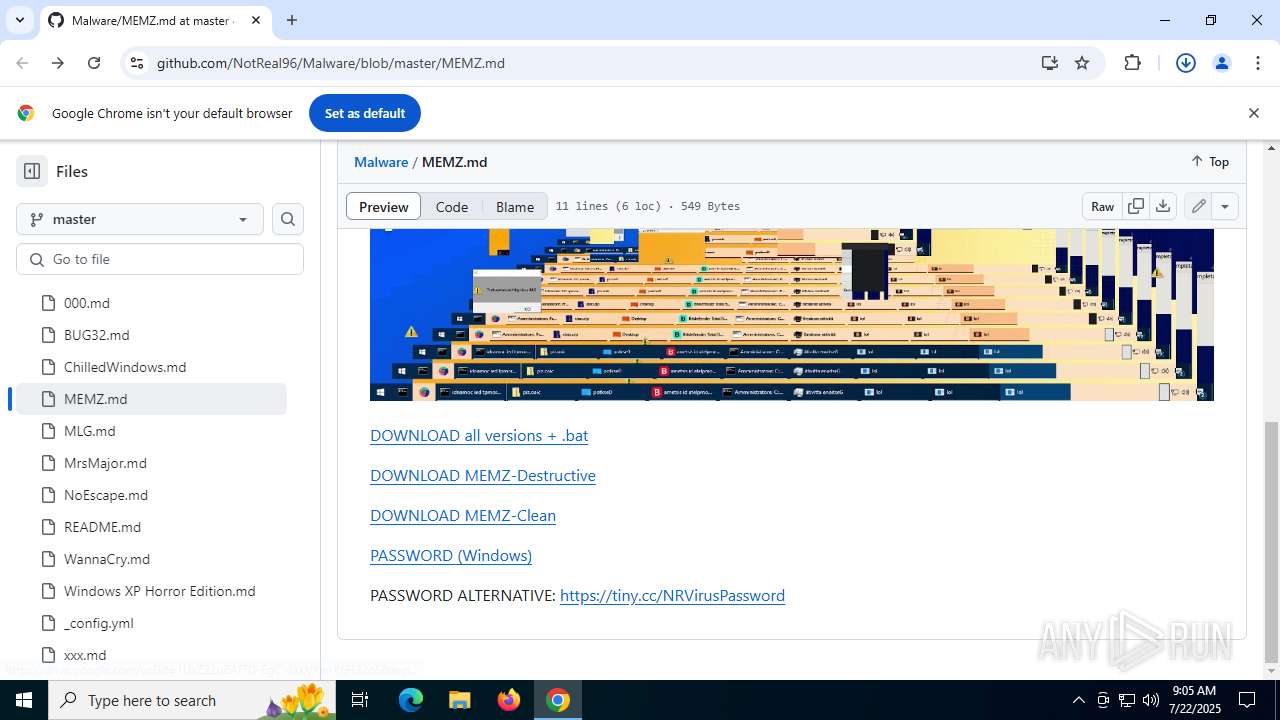
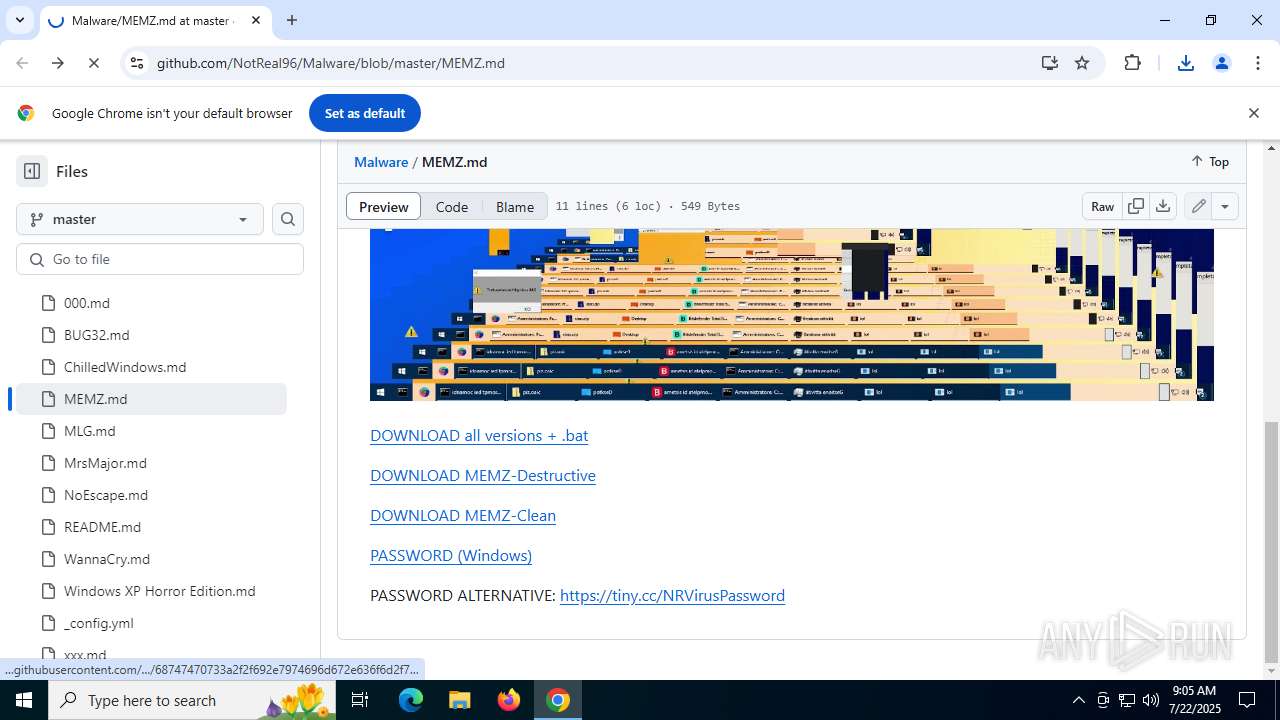
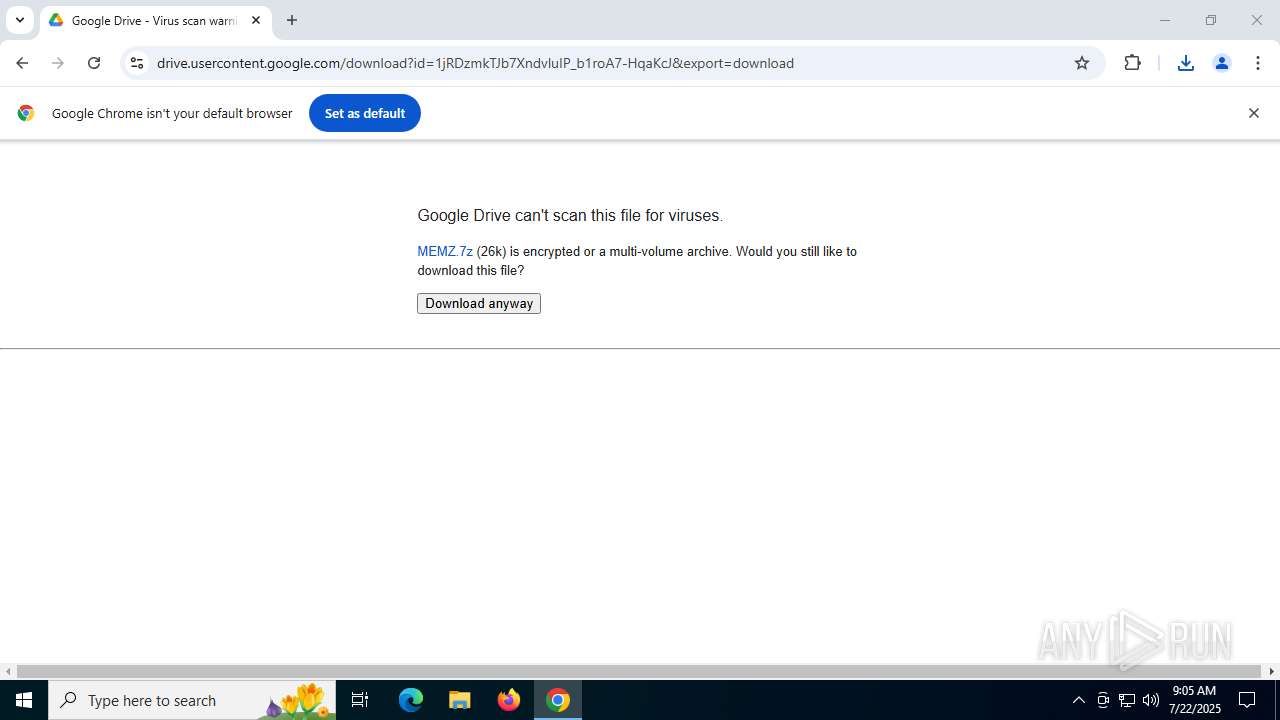
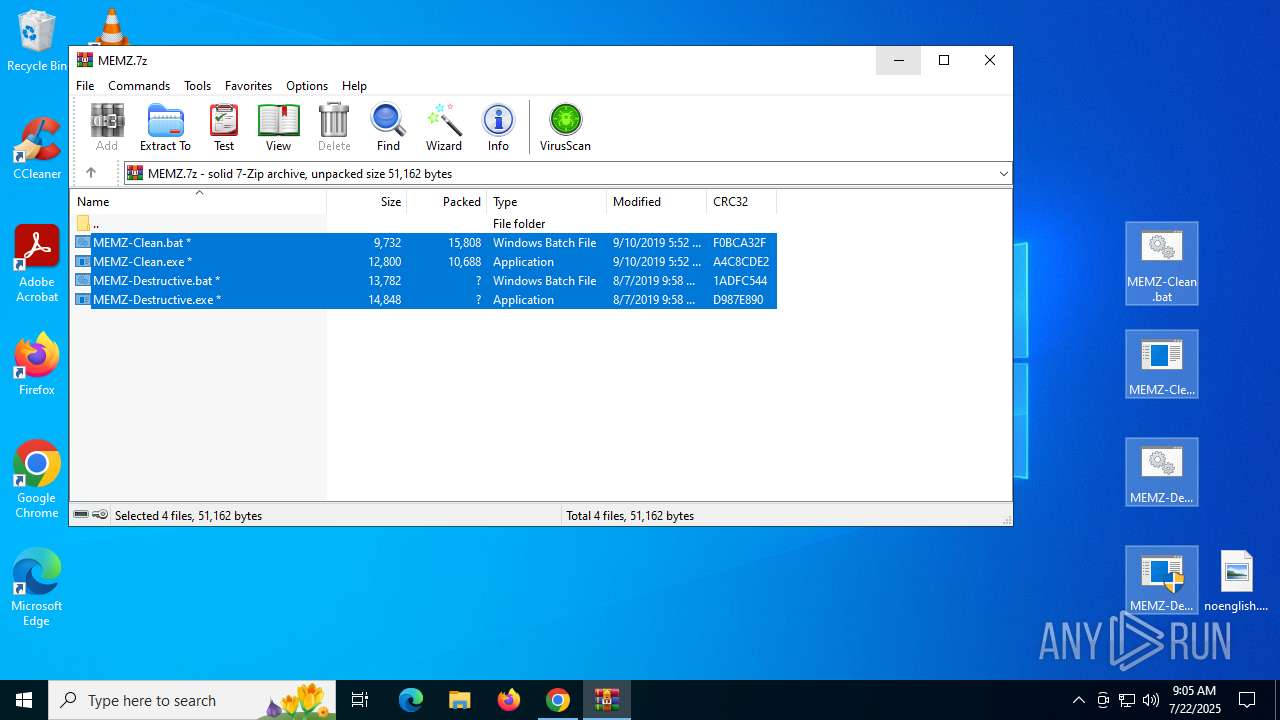
| URL: | https://github.com/NotReal96/Malware/blob/master/MEMZ.md |
| Full analysis: | https://app.any.run/tasks/32364bf7-d622-41f9-b785-c4046d5bfabc |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2025, 09:04:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
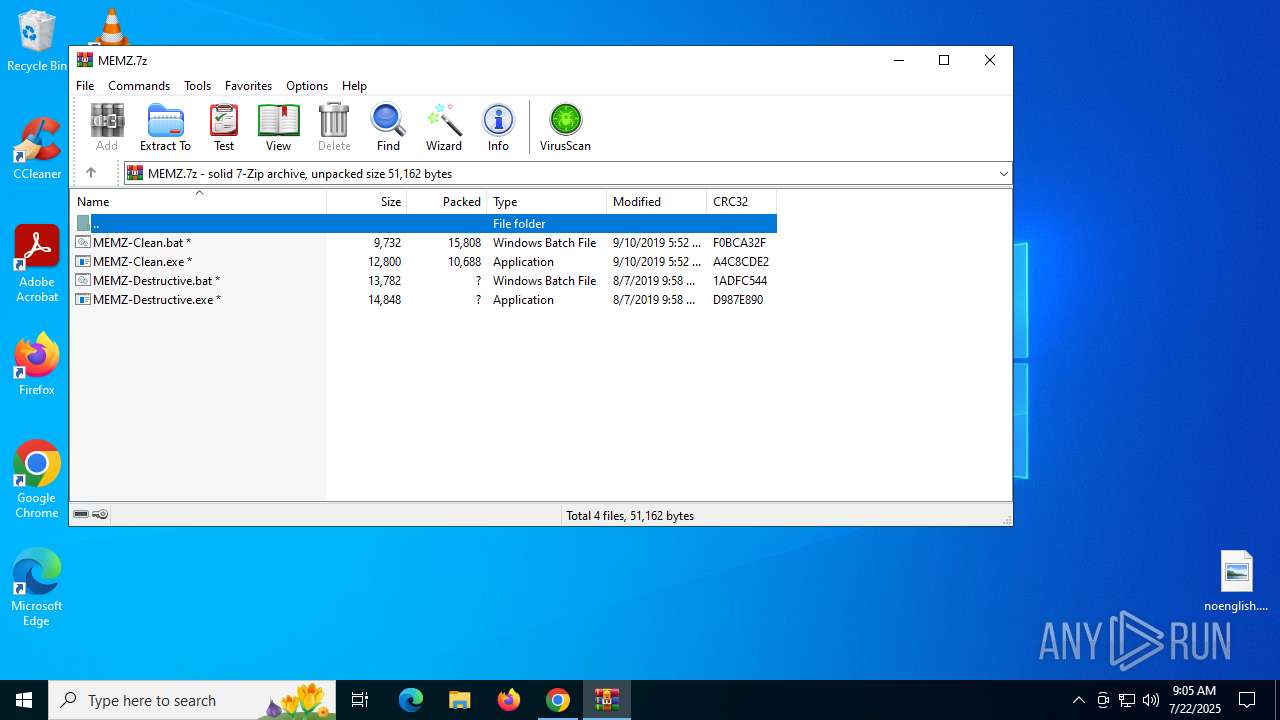
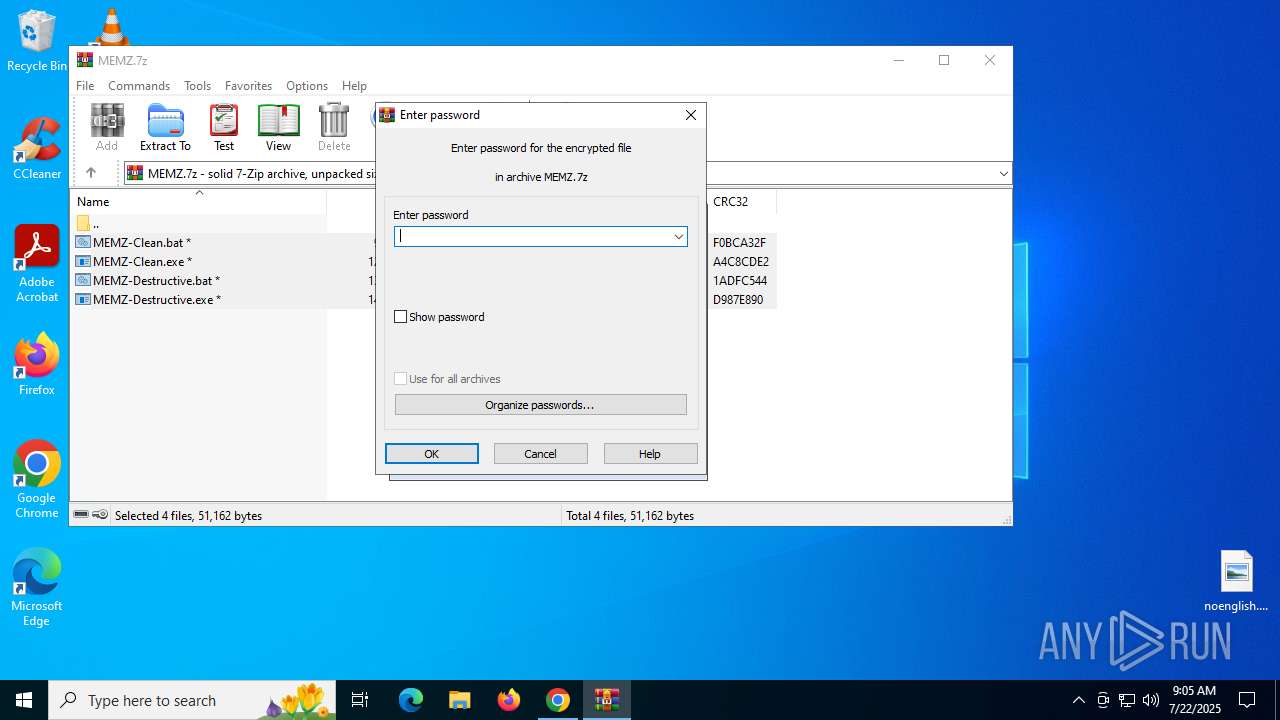
| MD5: | 7B98E23787D1CB31E553364CFBE821FC |
| SHA1: | C7205240927086FB8A169BFB6BD558F574BBD831 |
| SHA256: | 9F3F8616682572644FB209B3D876C3D8569B6AFB5C118FAF820A160CED0973A4 |
| SSDEEP: | 3:N8tEduR3AESTocEJcTEHBQn:2uYR3Ax+6 |
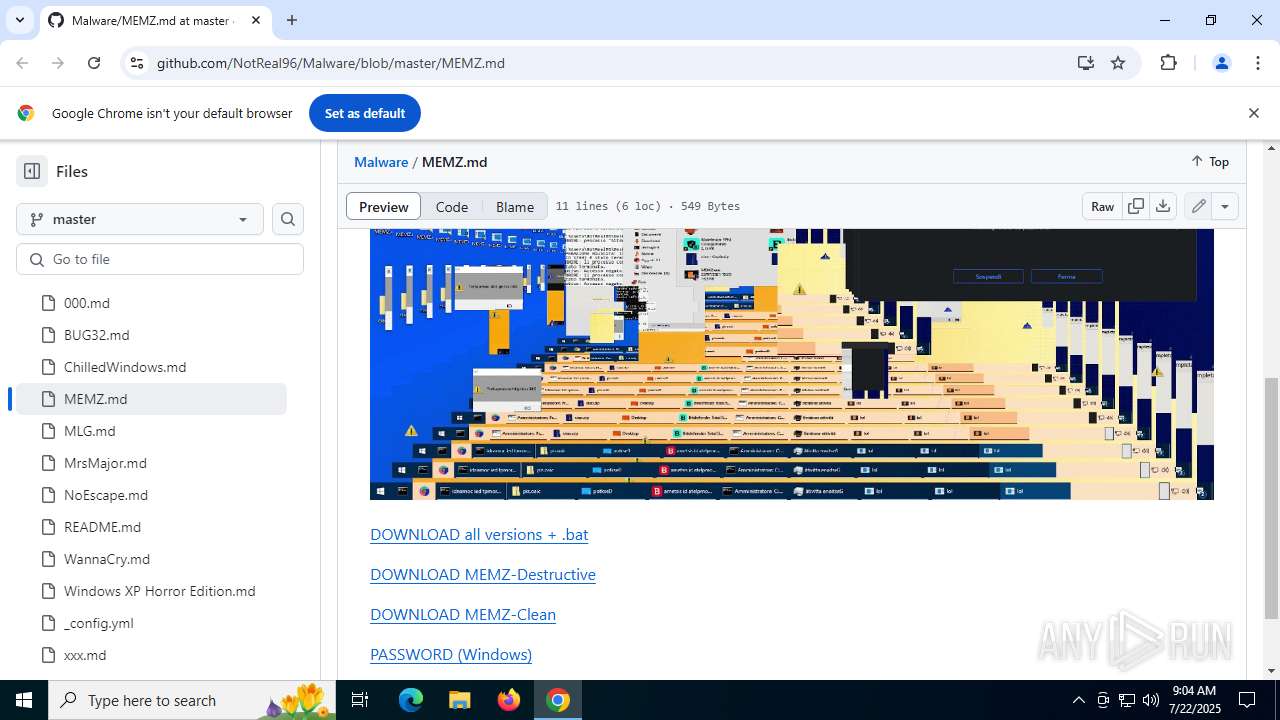
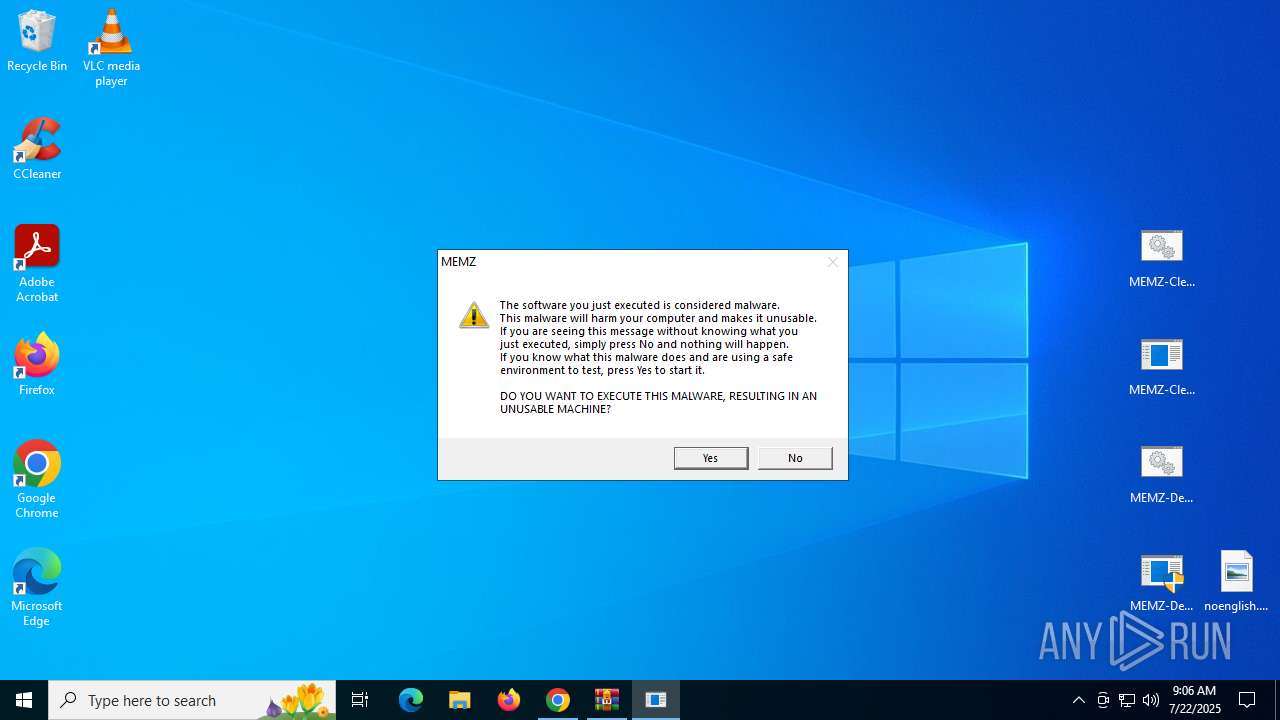
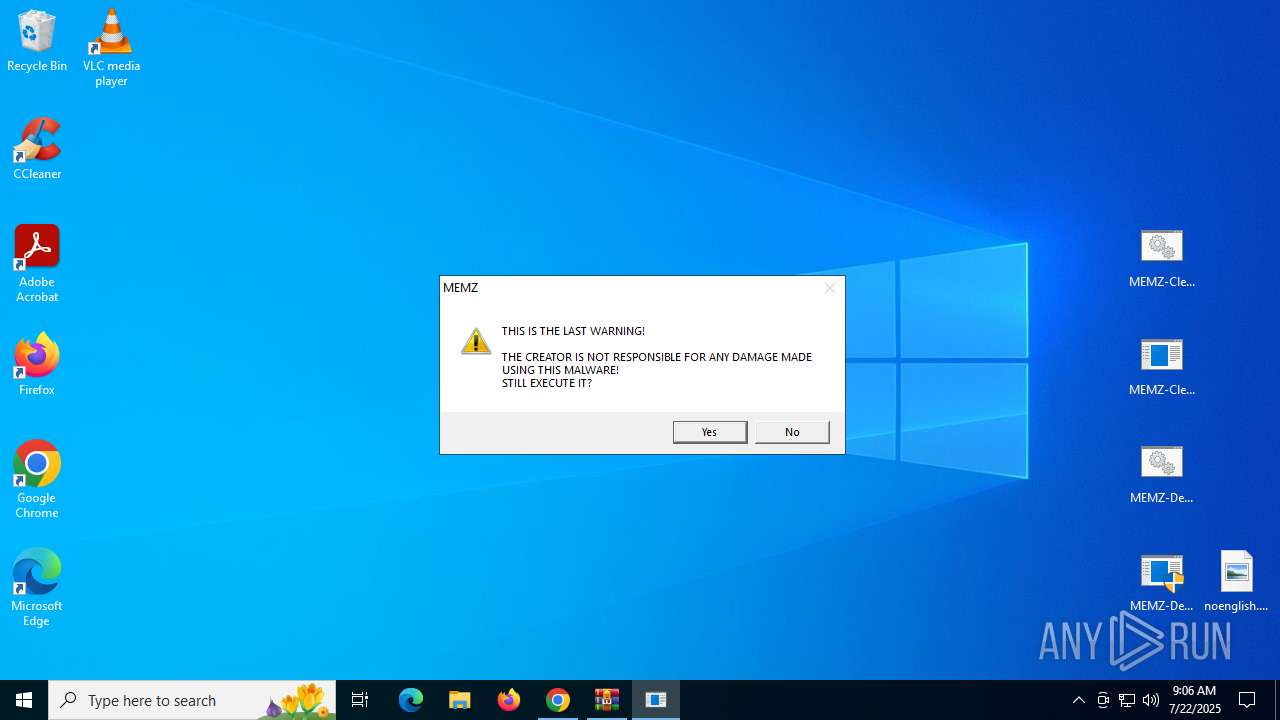
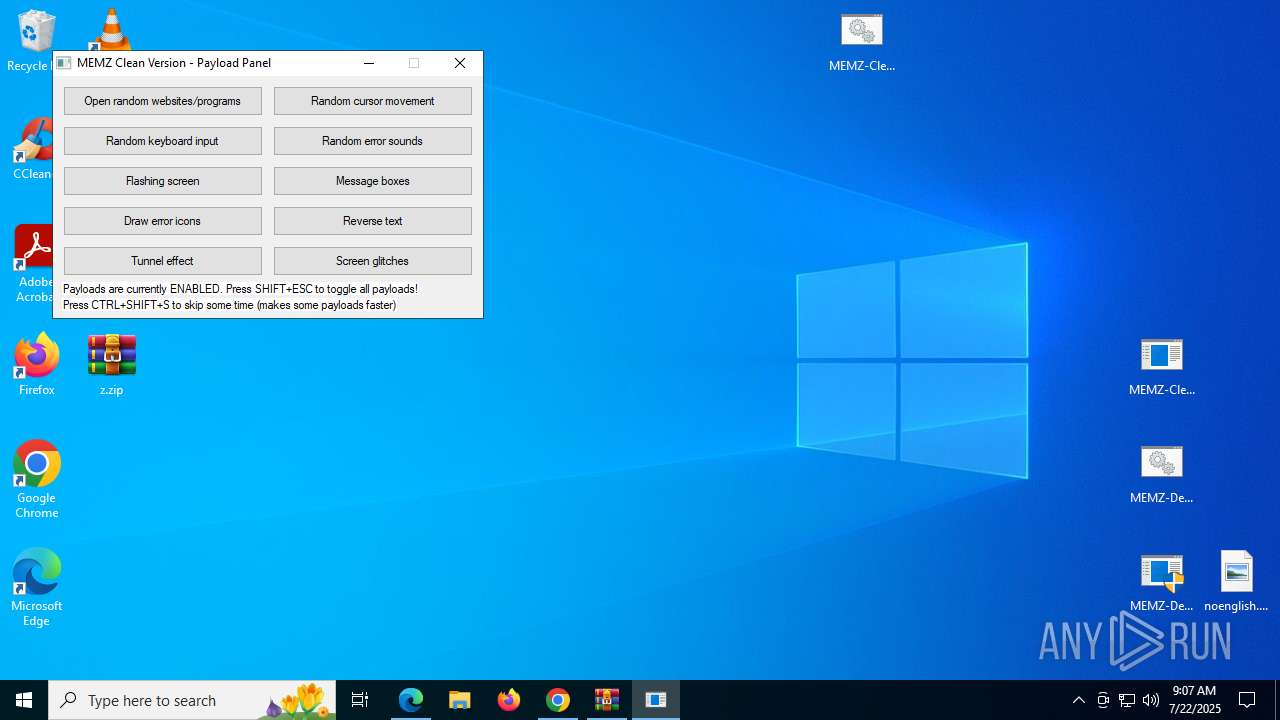
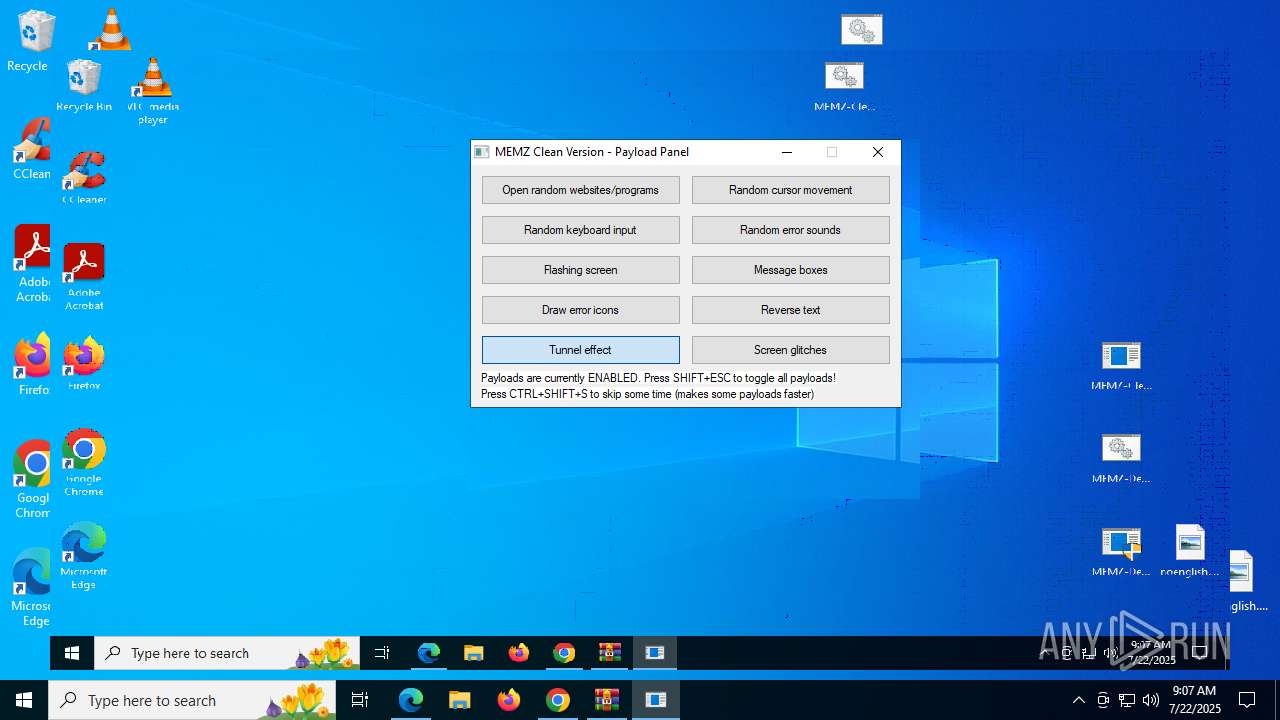
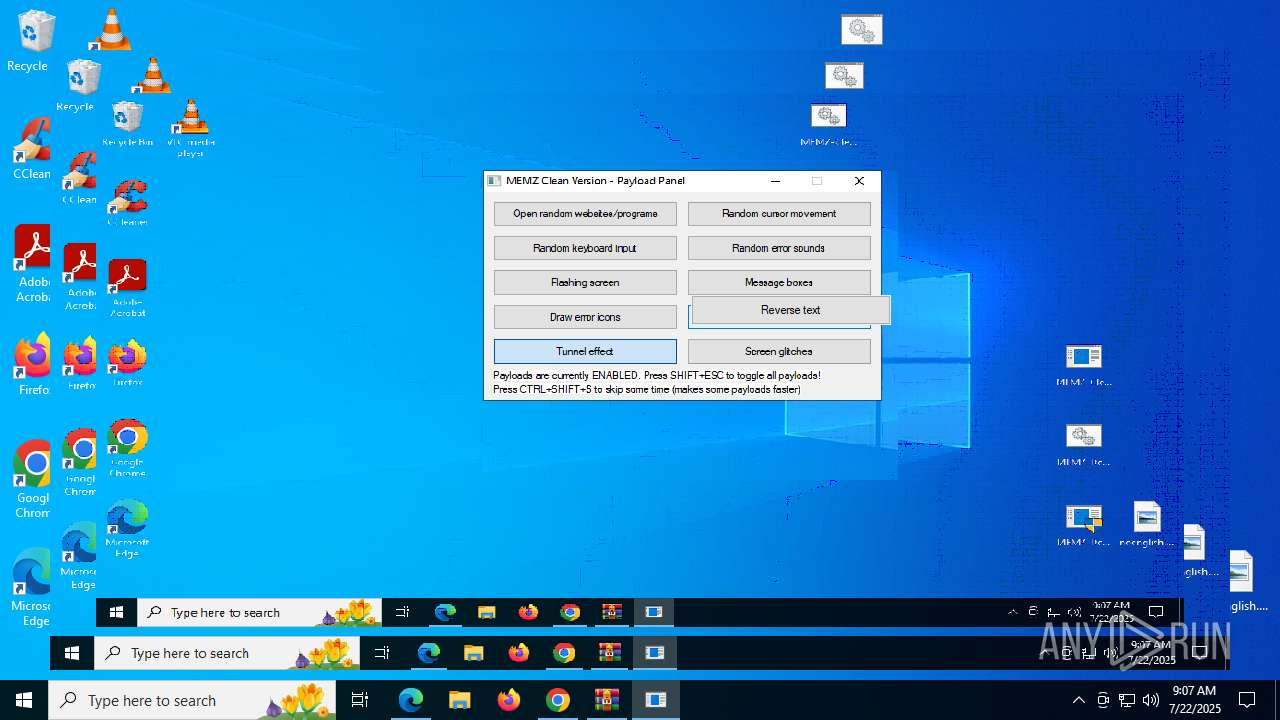
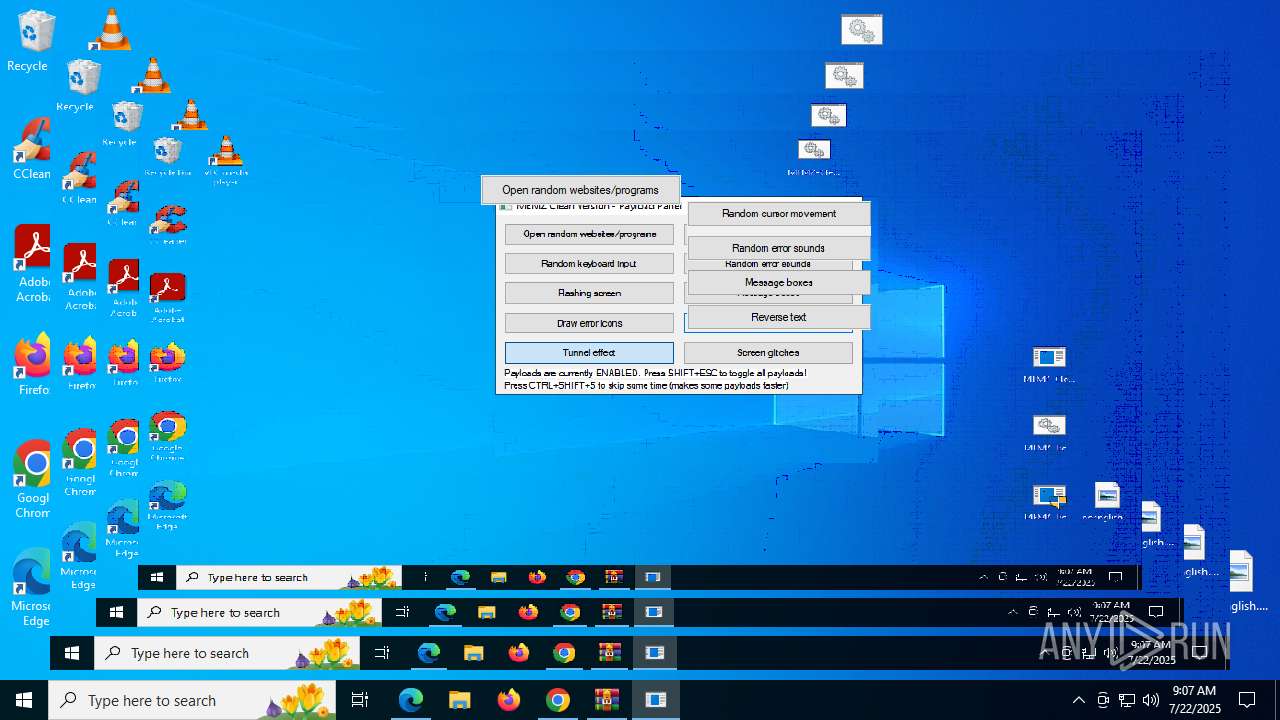
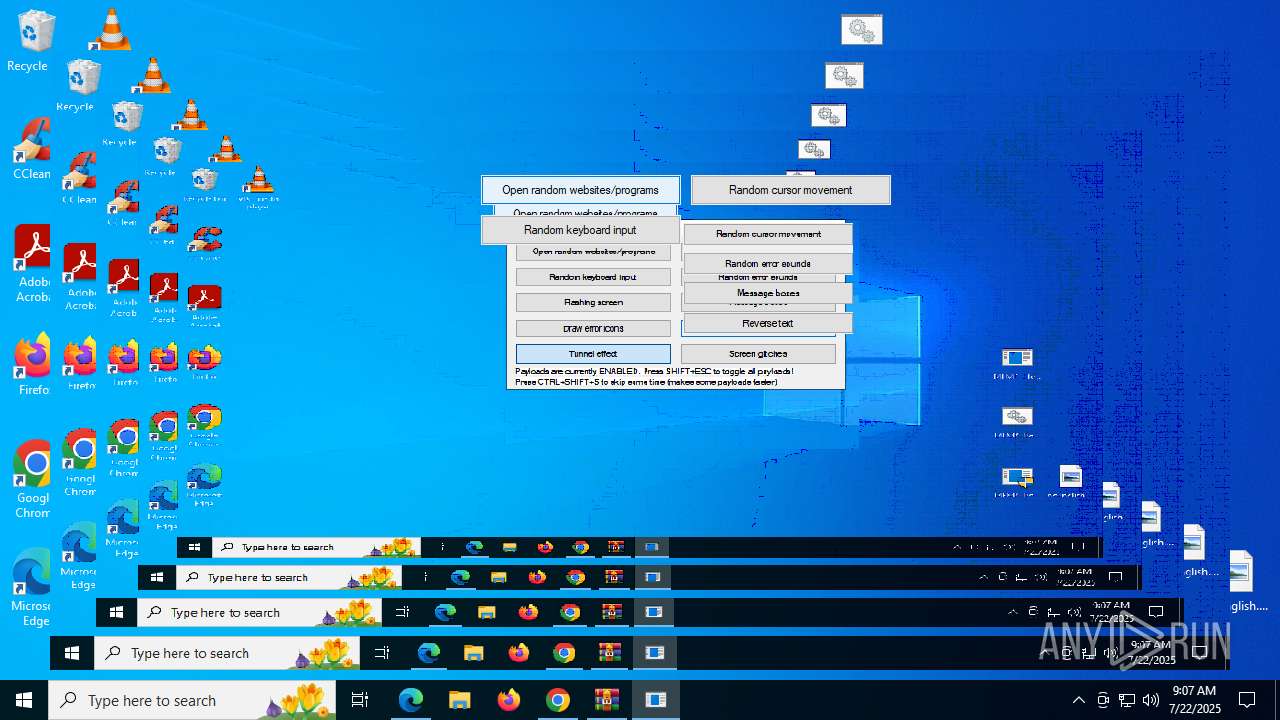
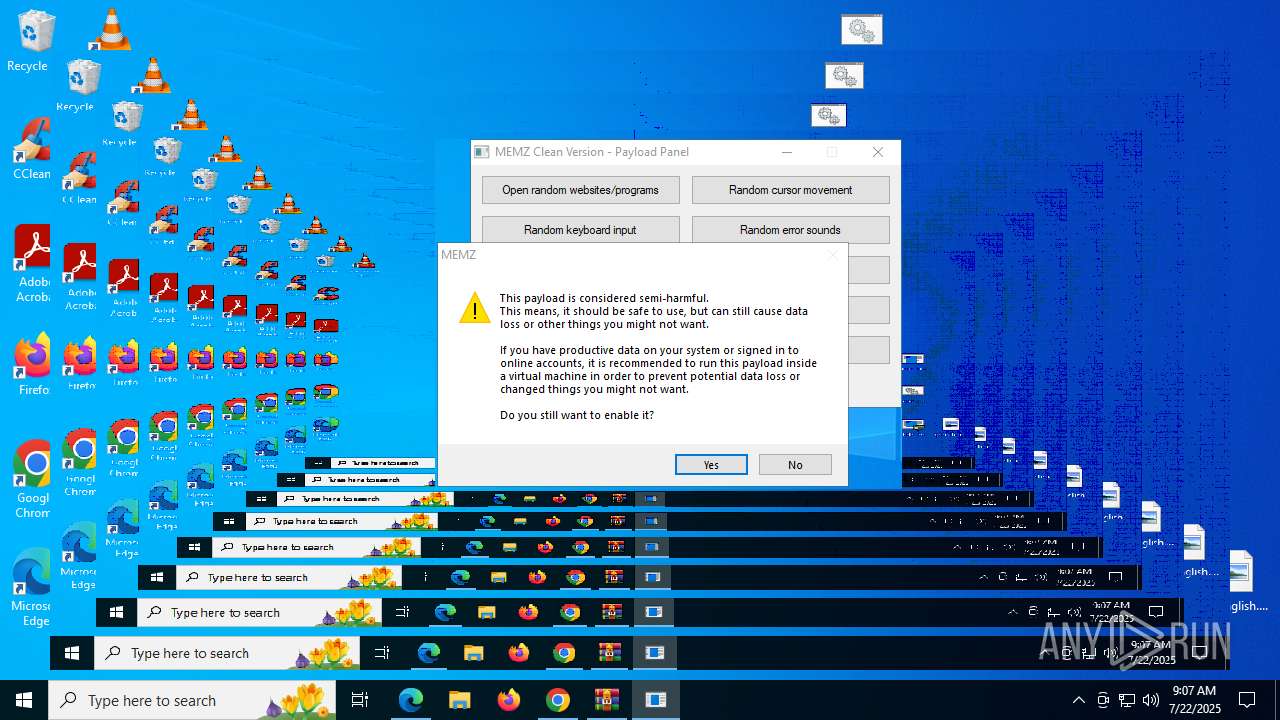
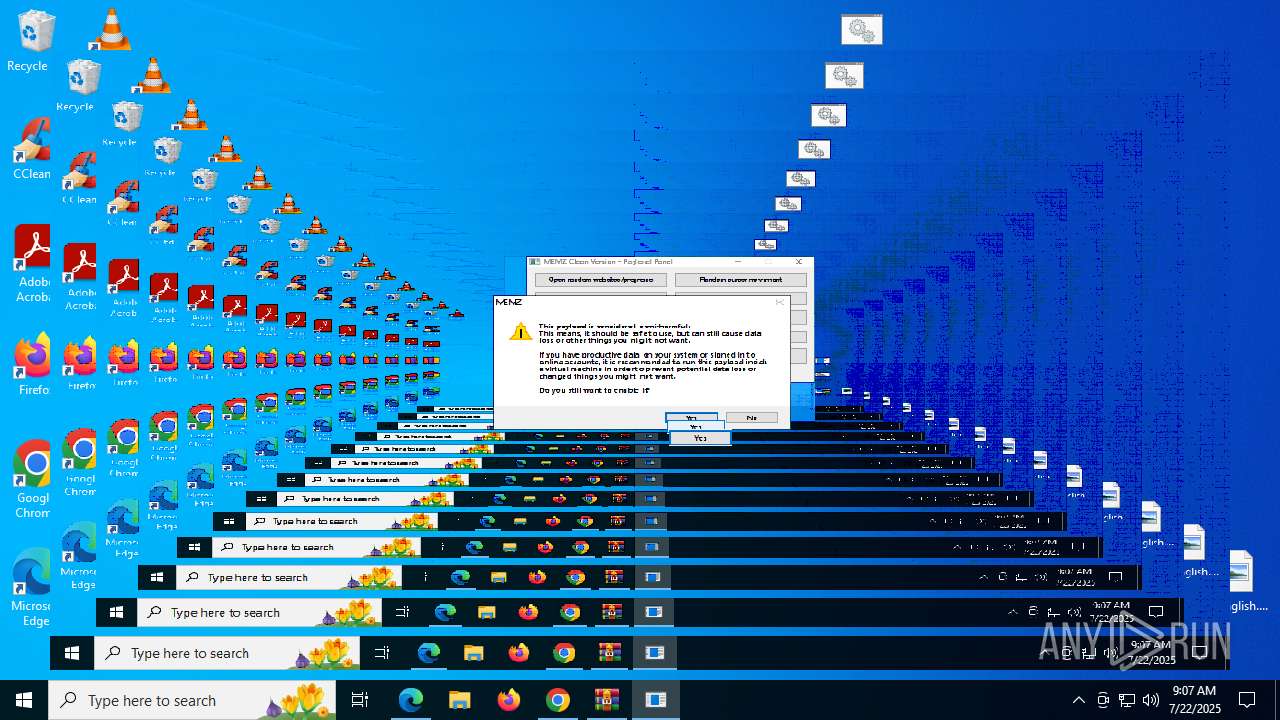
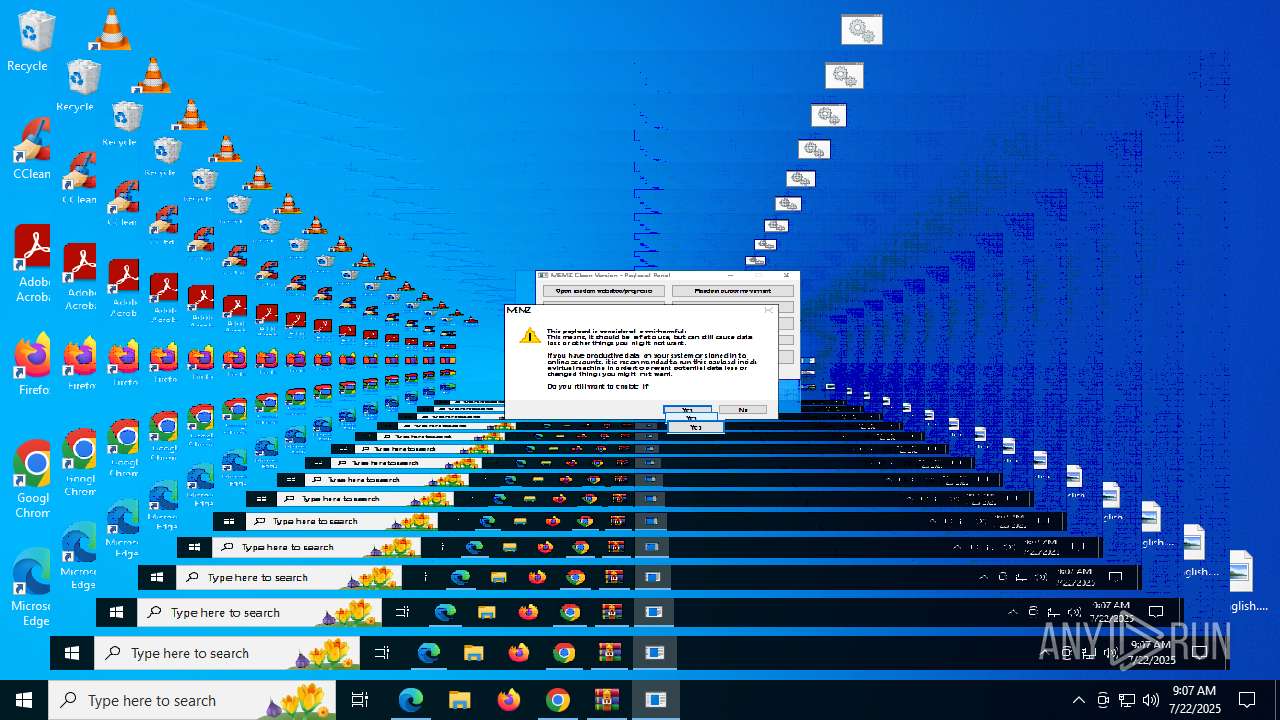
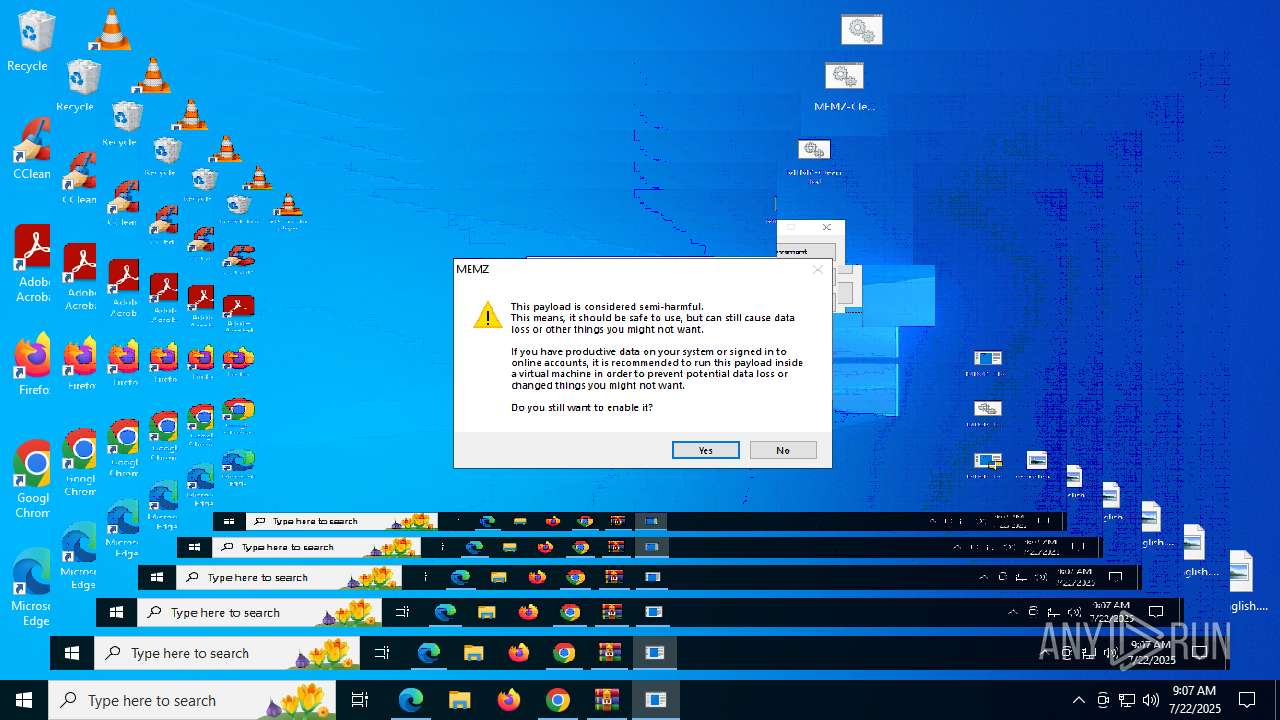
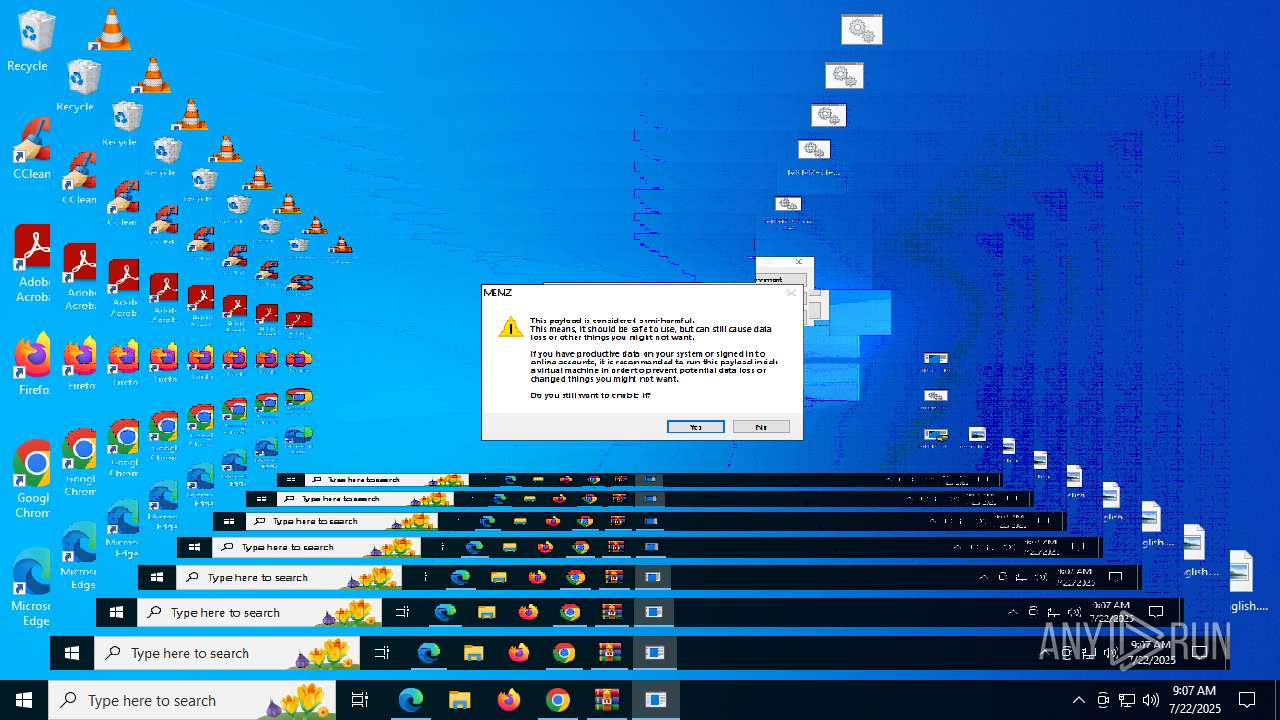
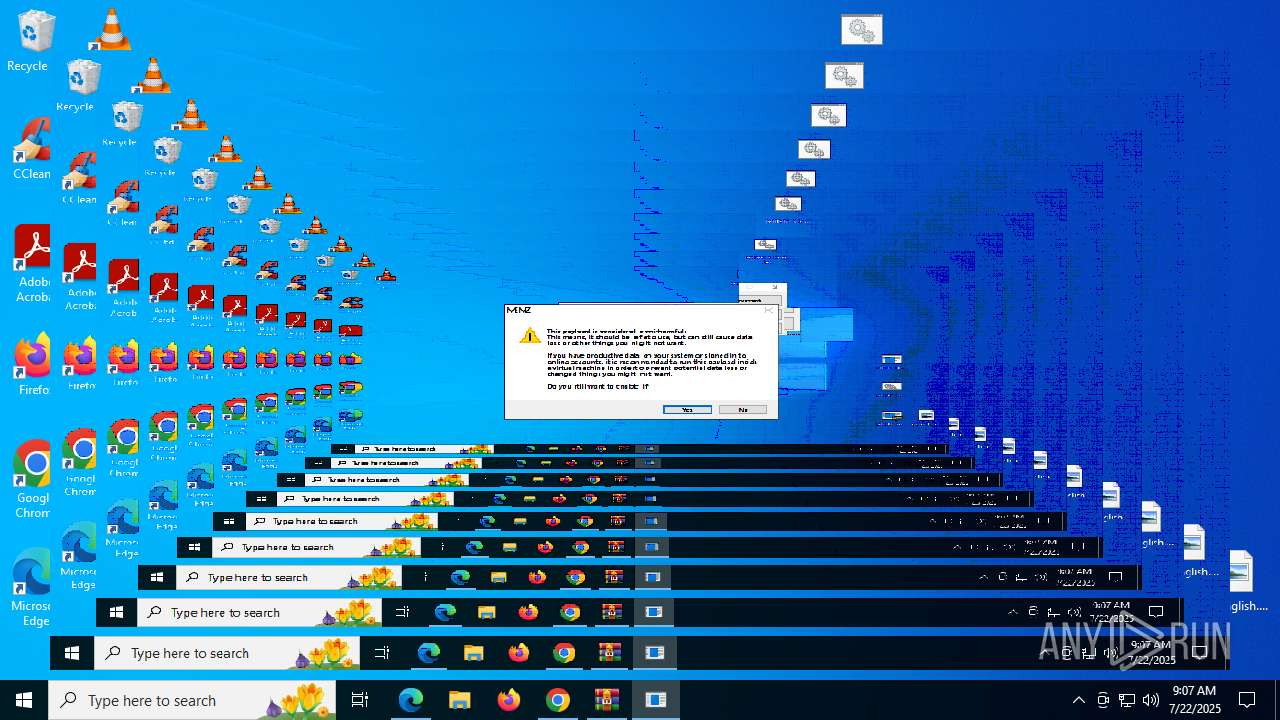
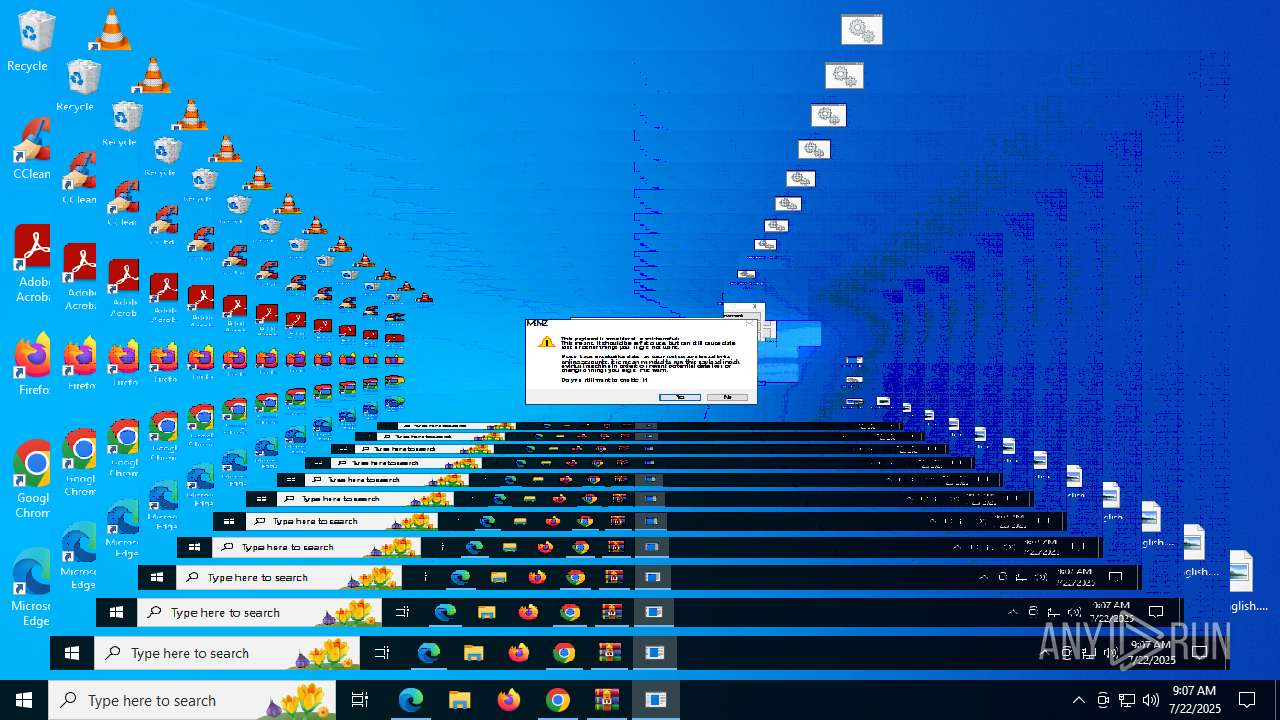
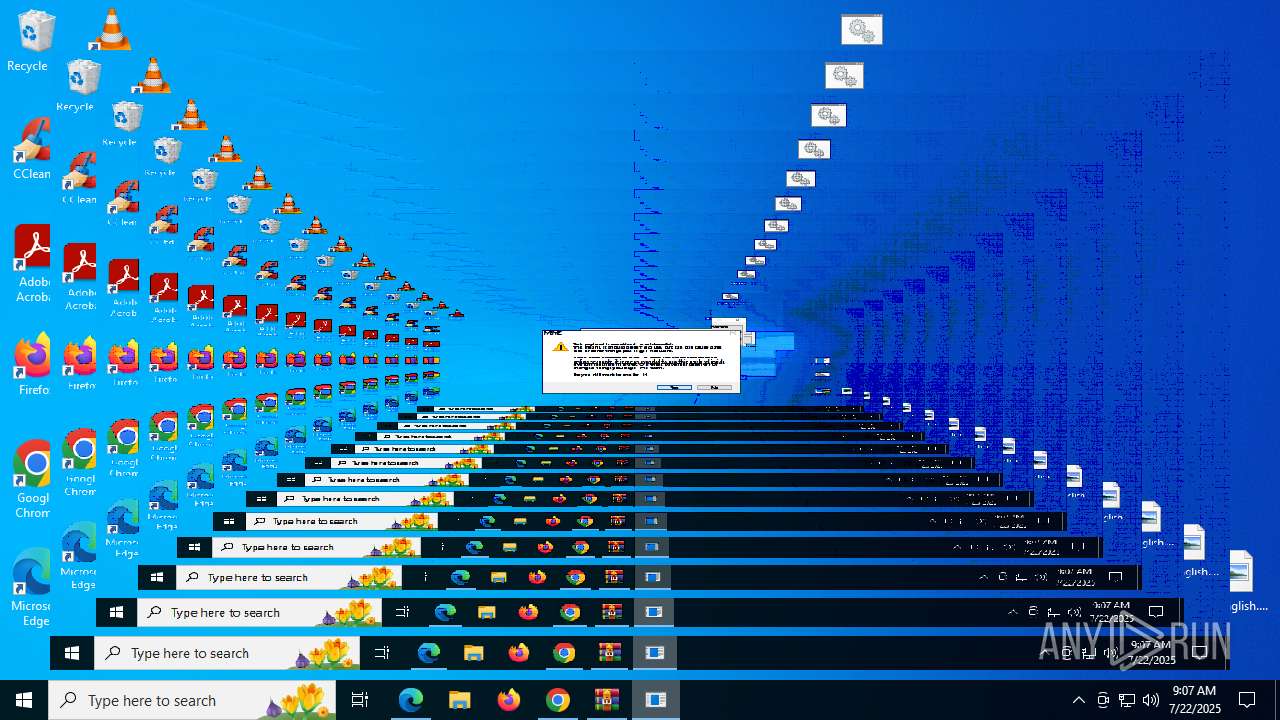
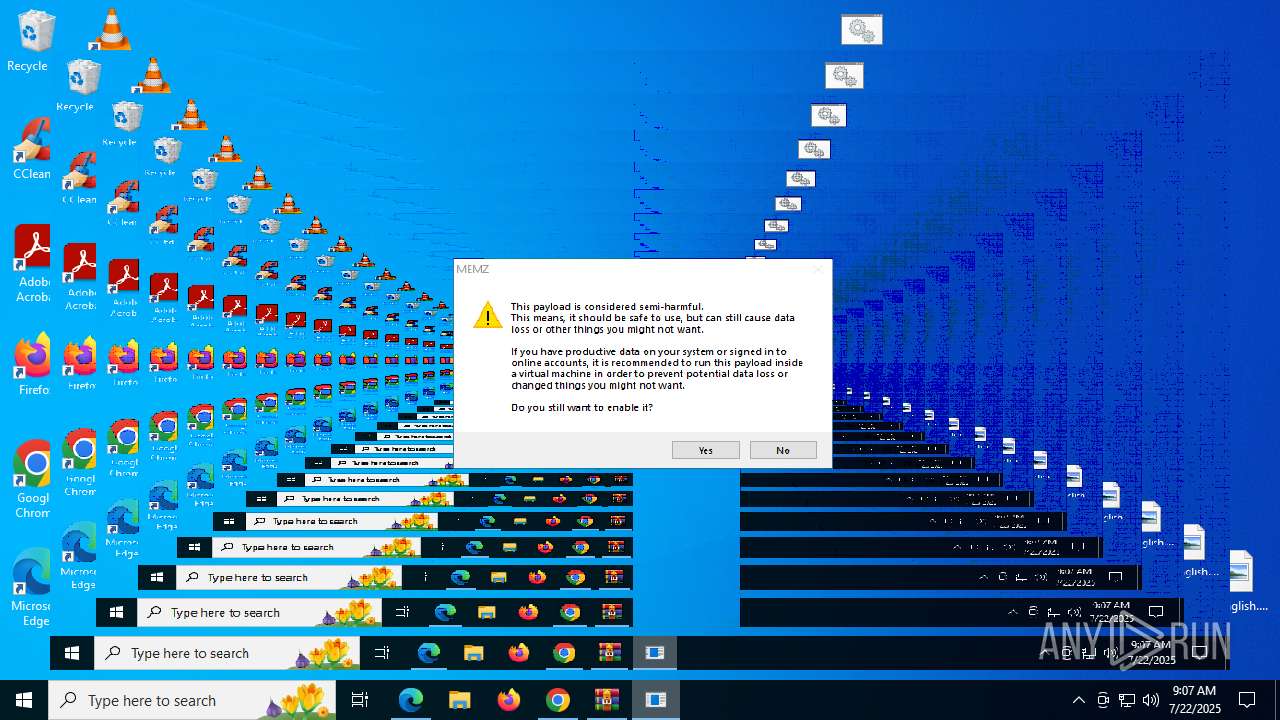
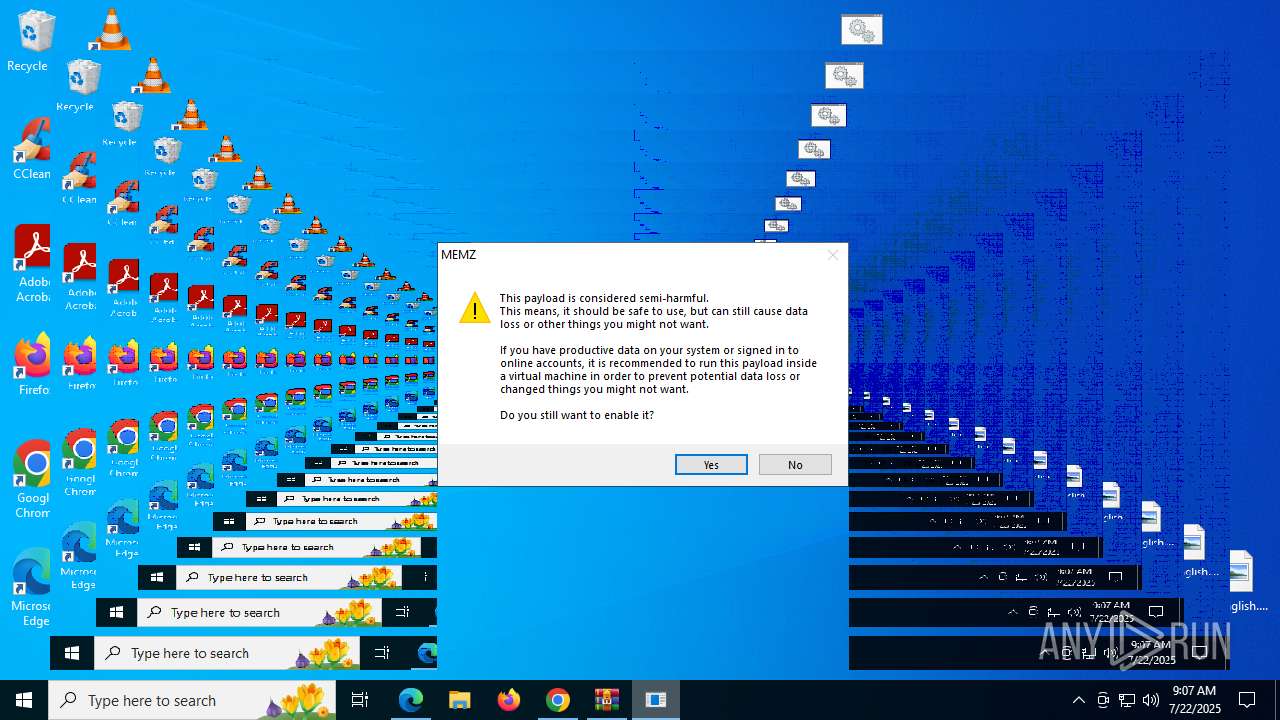
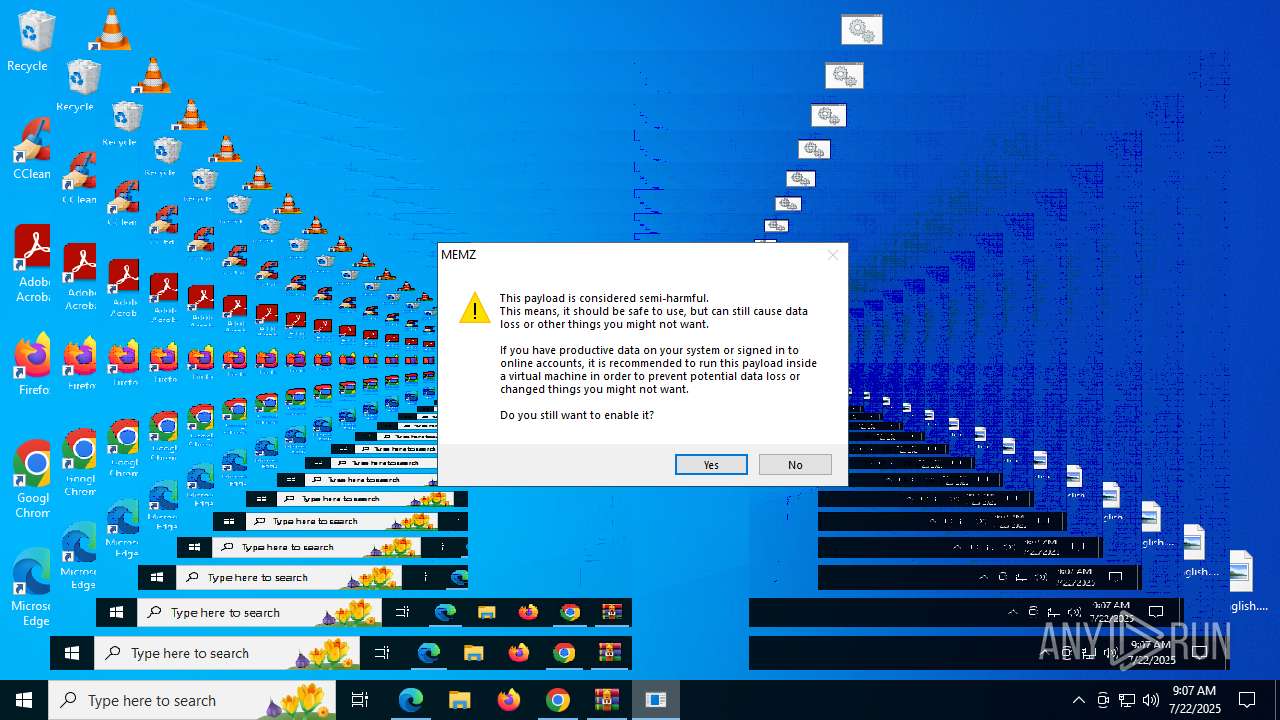
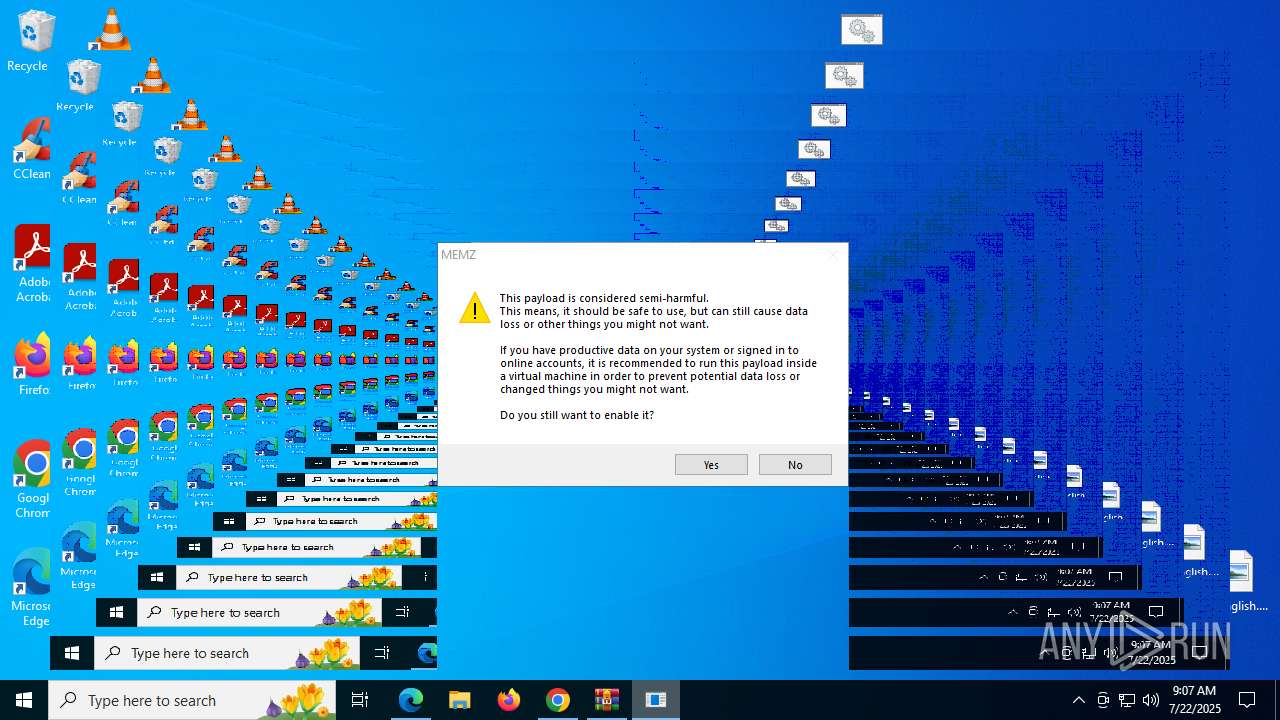
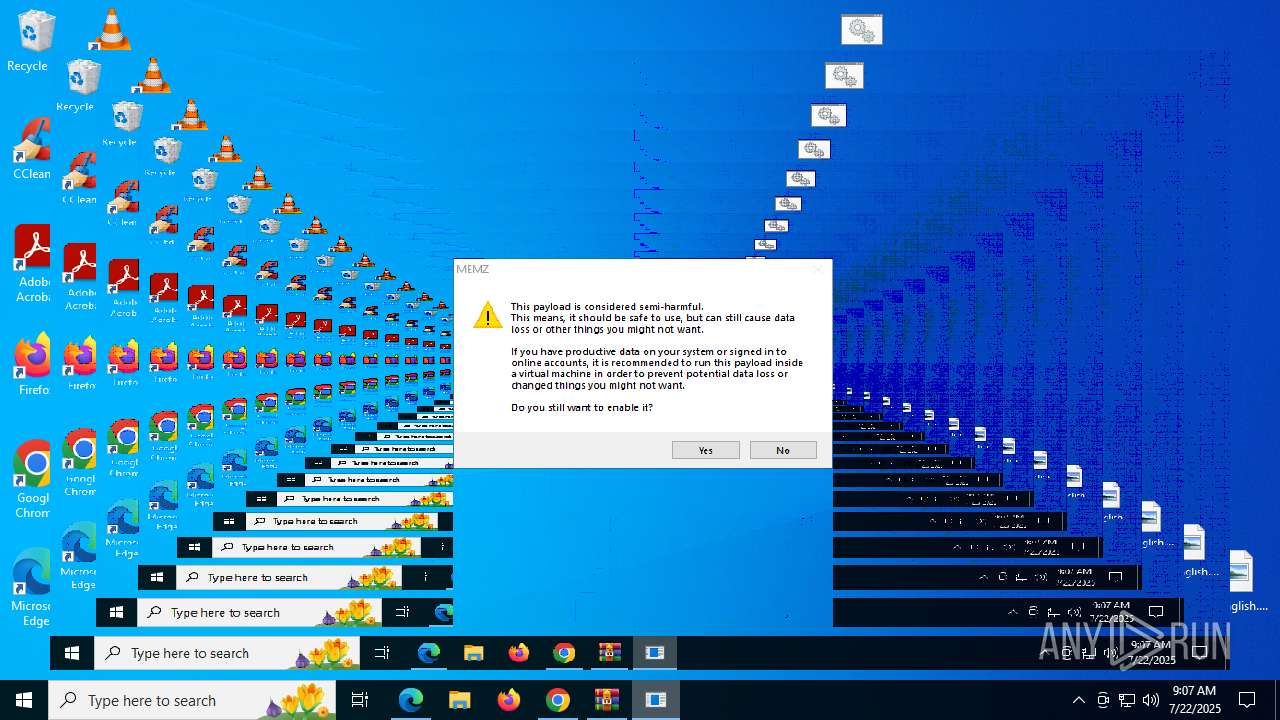
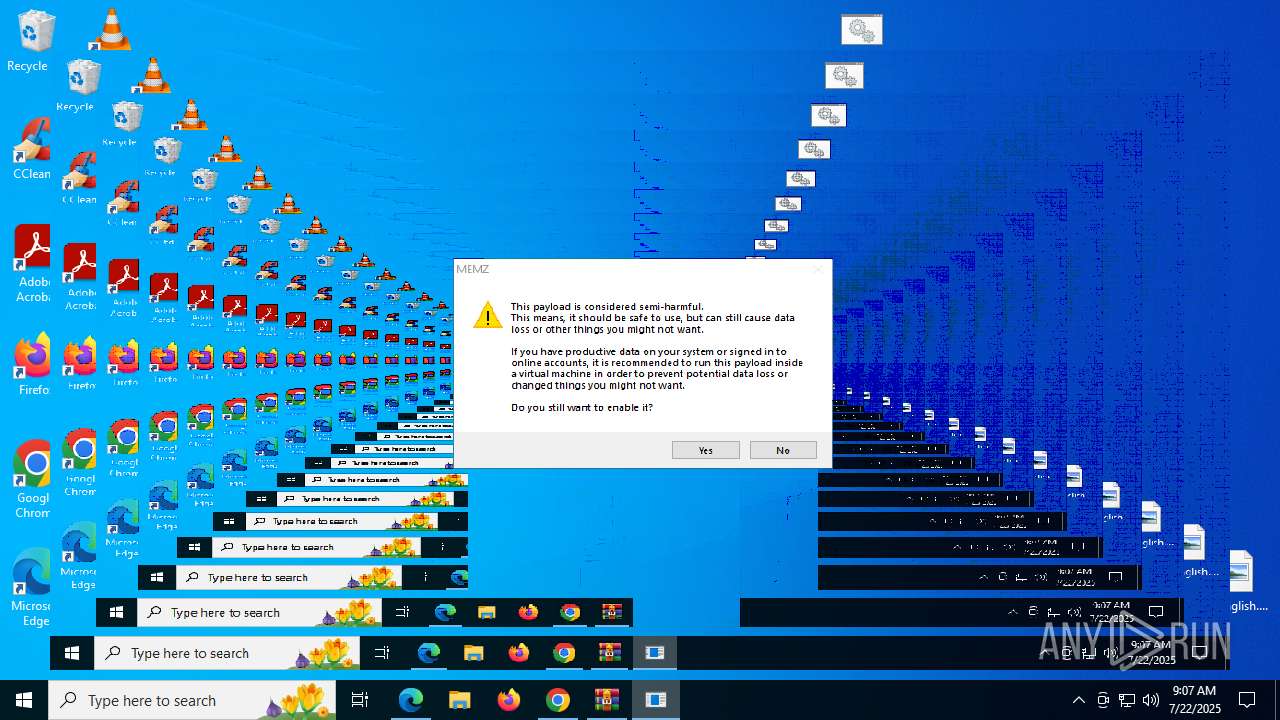
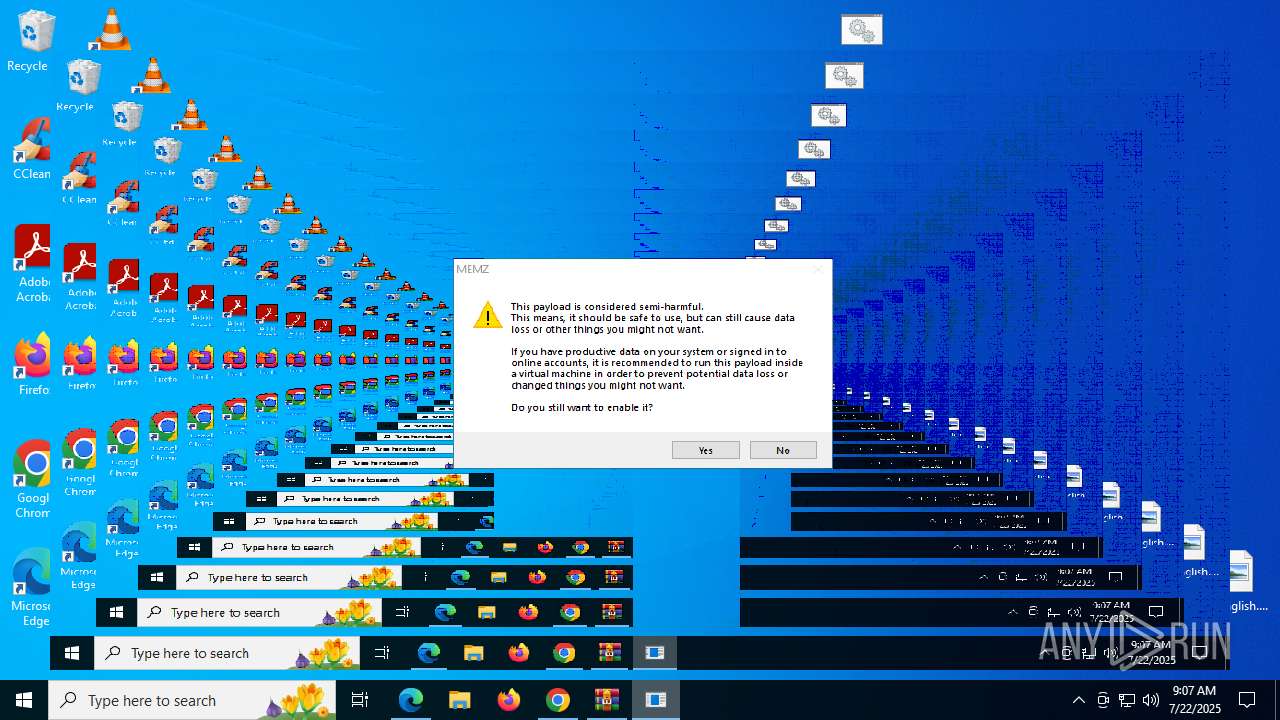
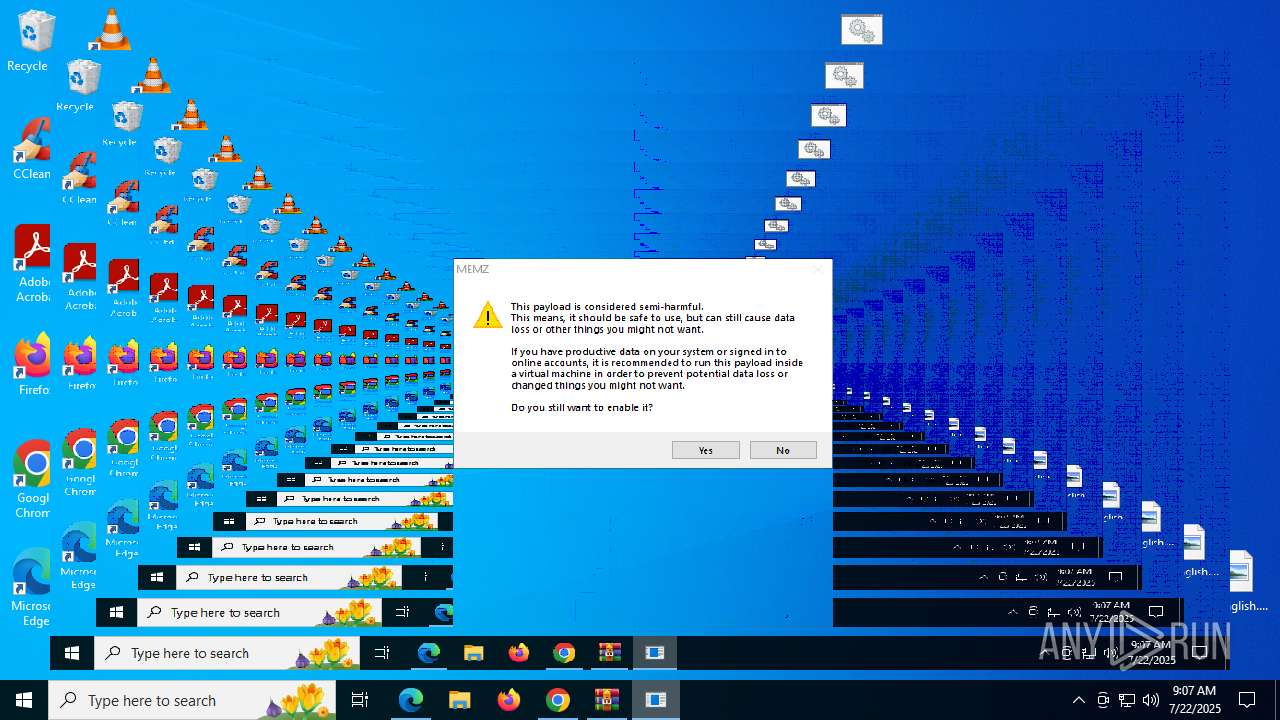
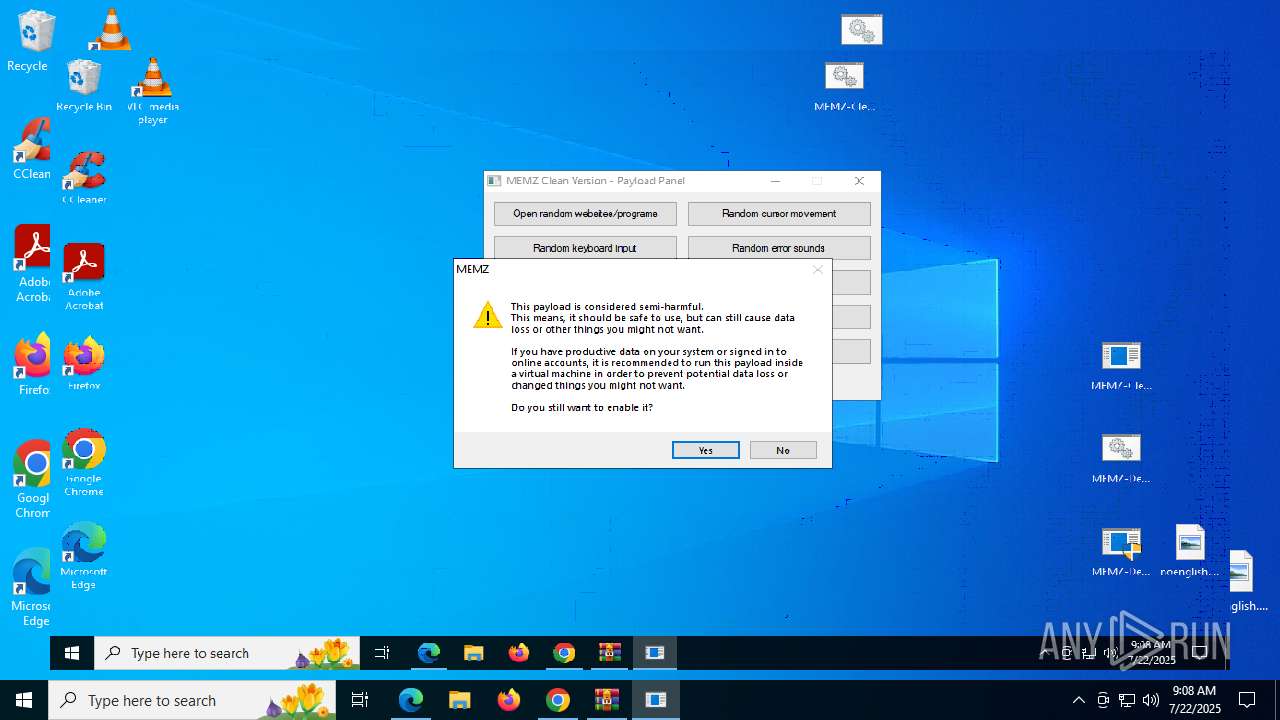
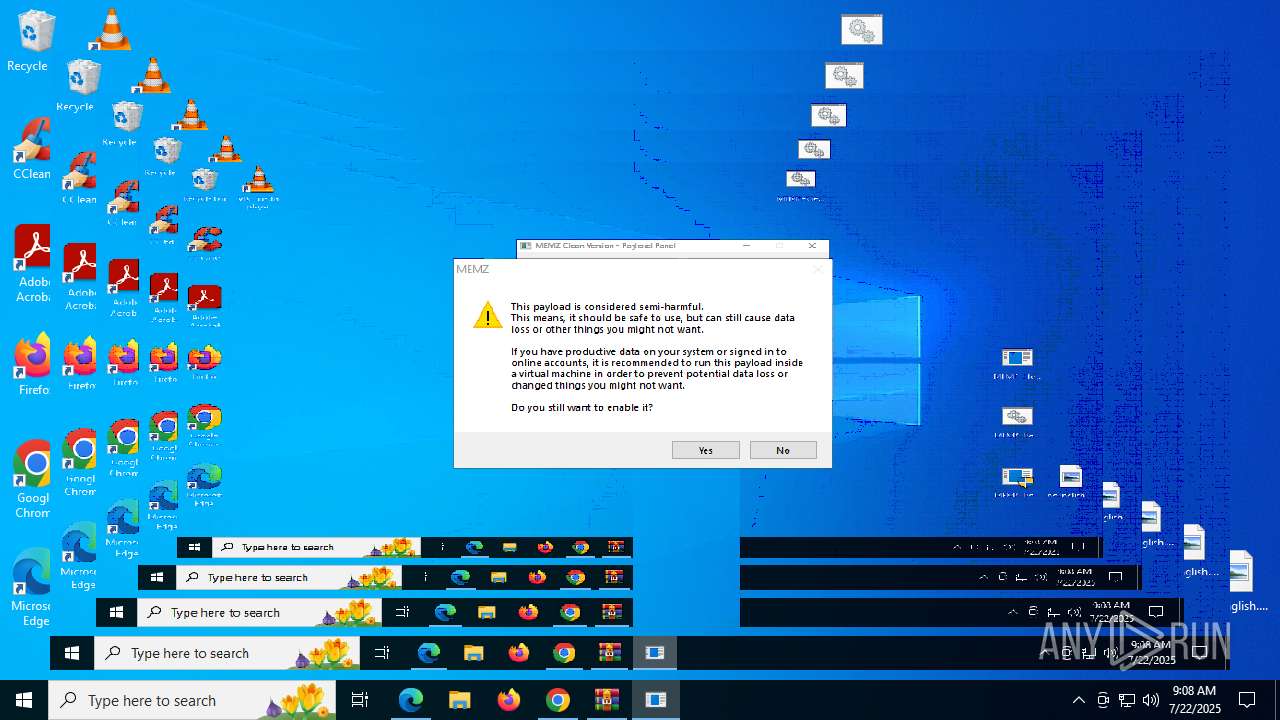
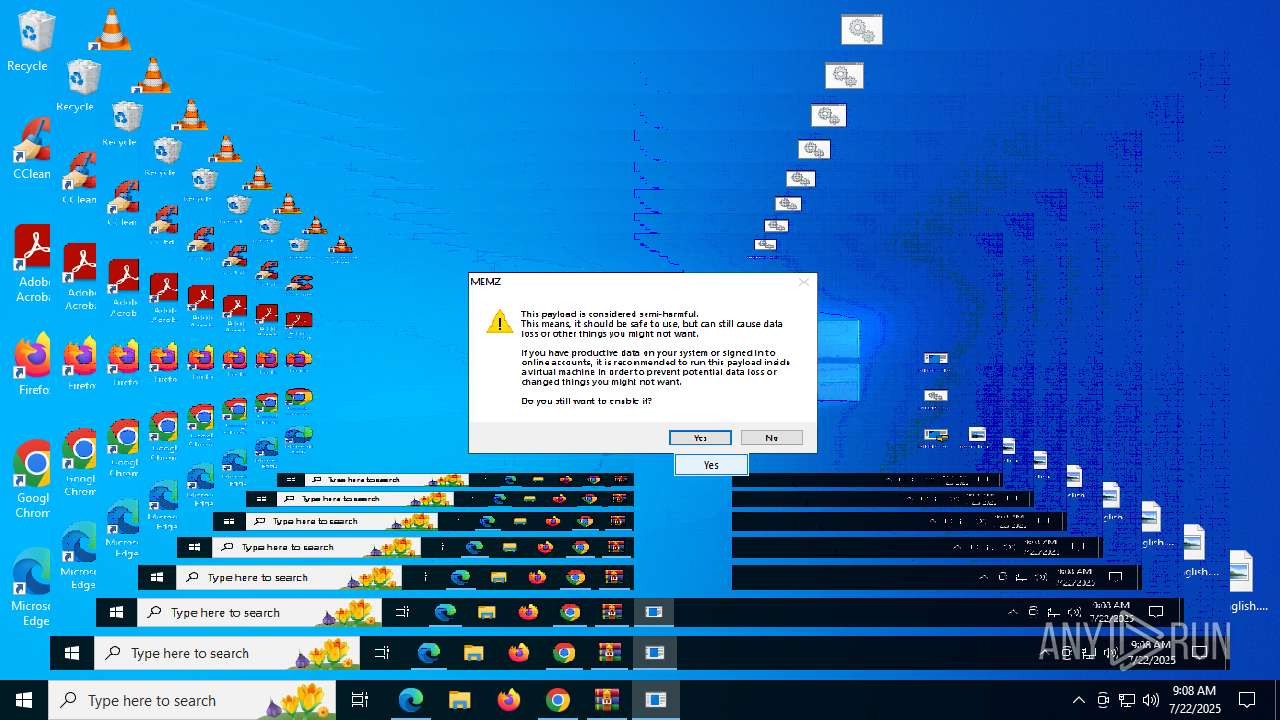
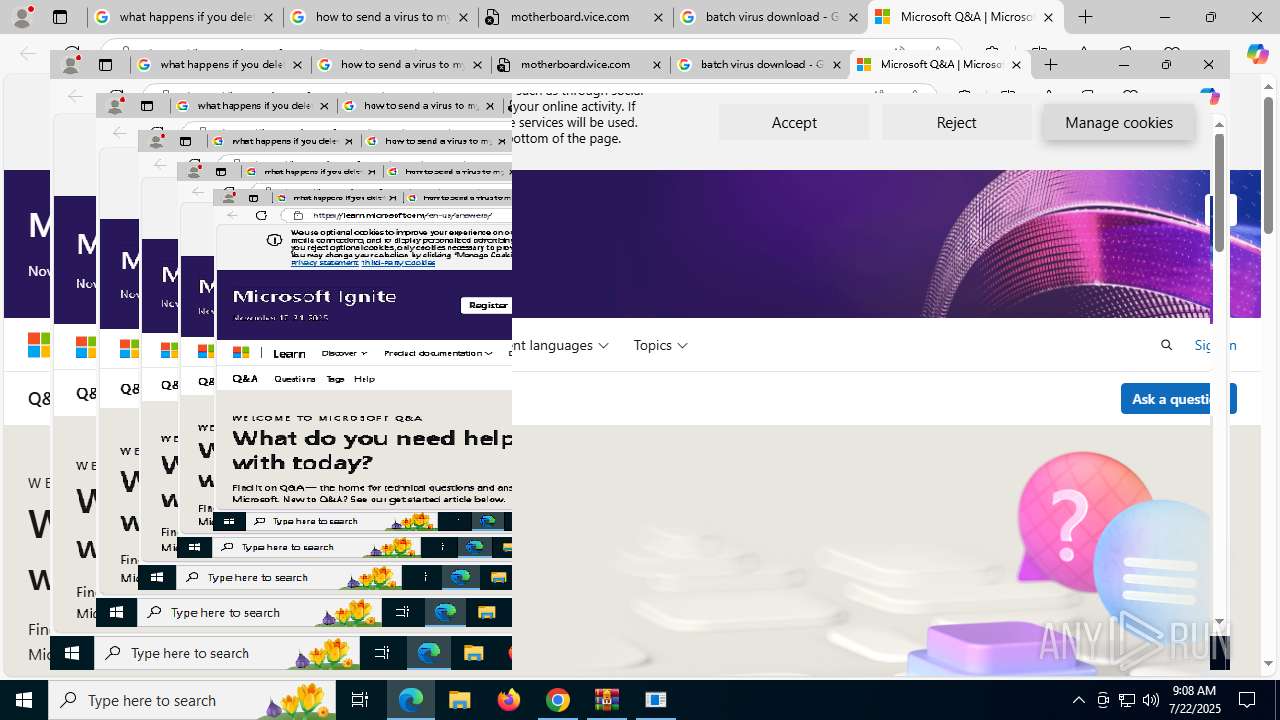
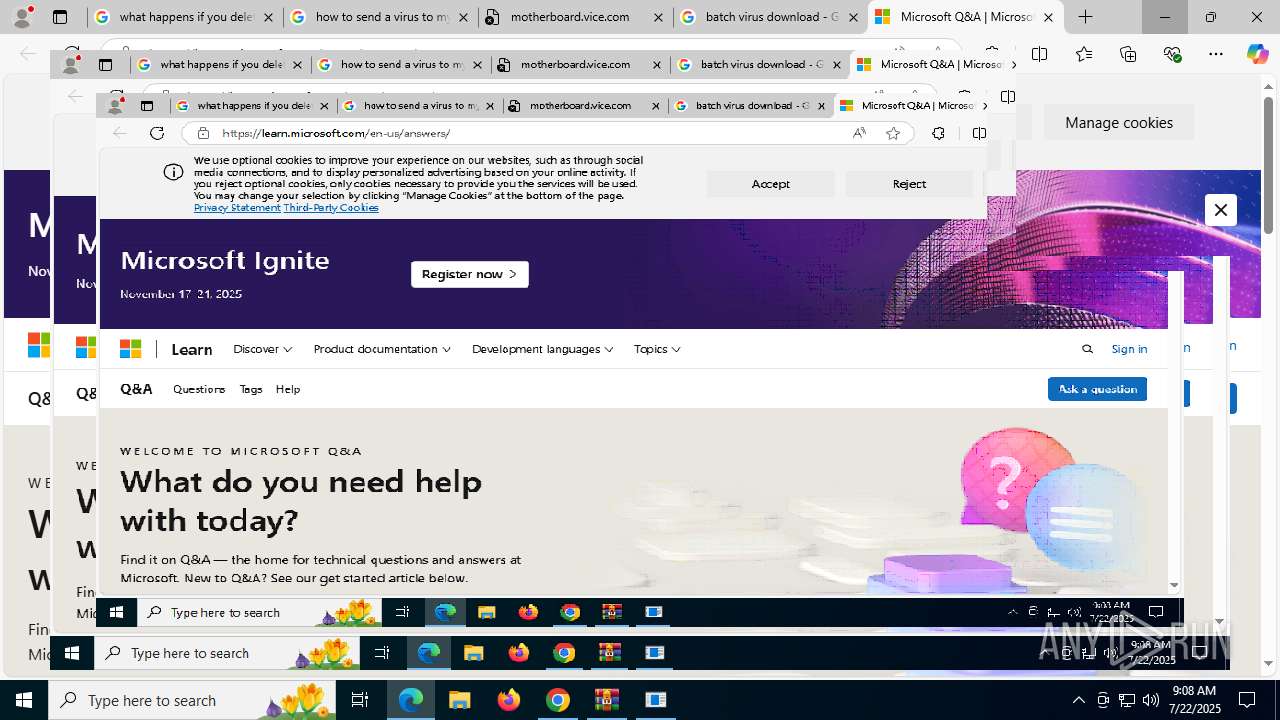
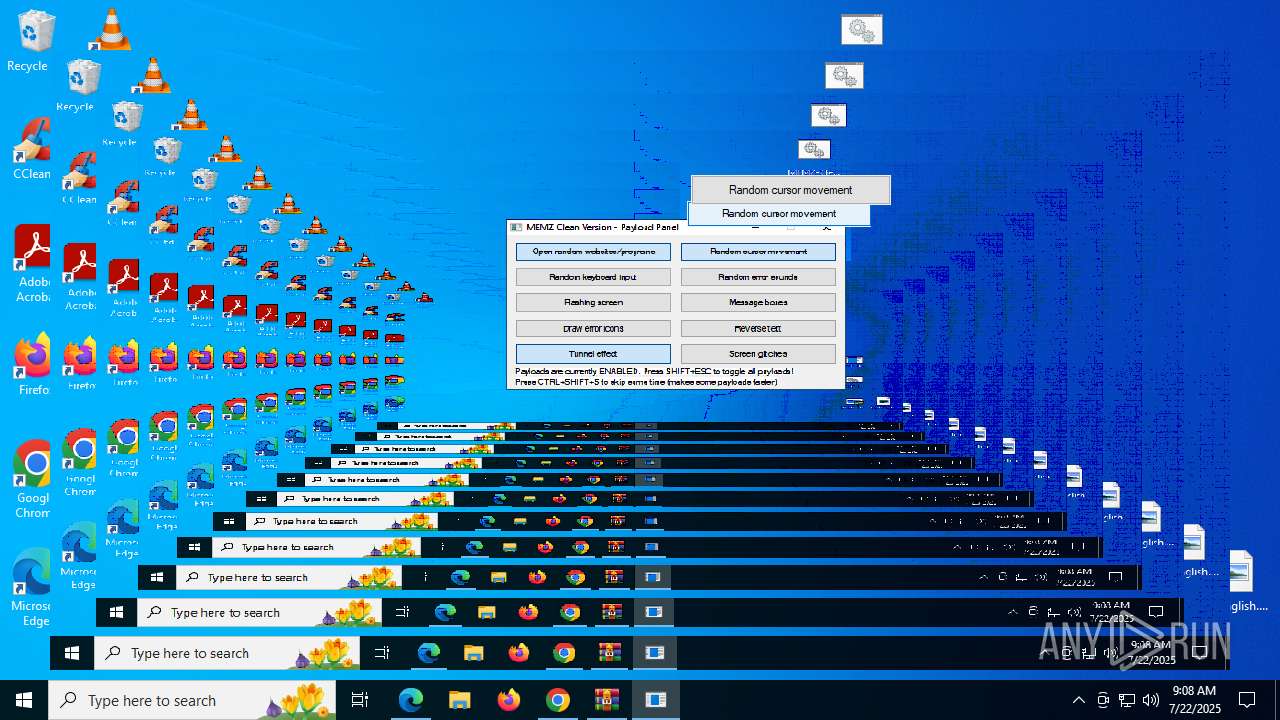
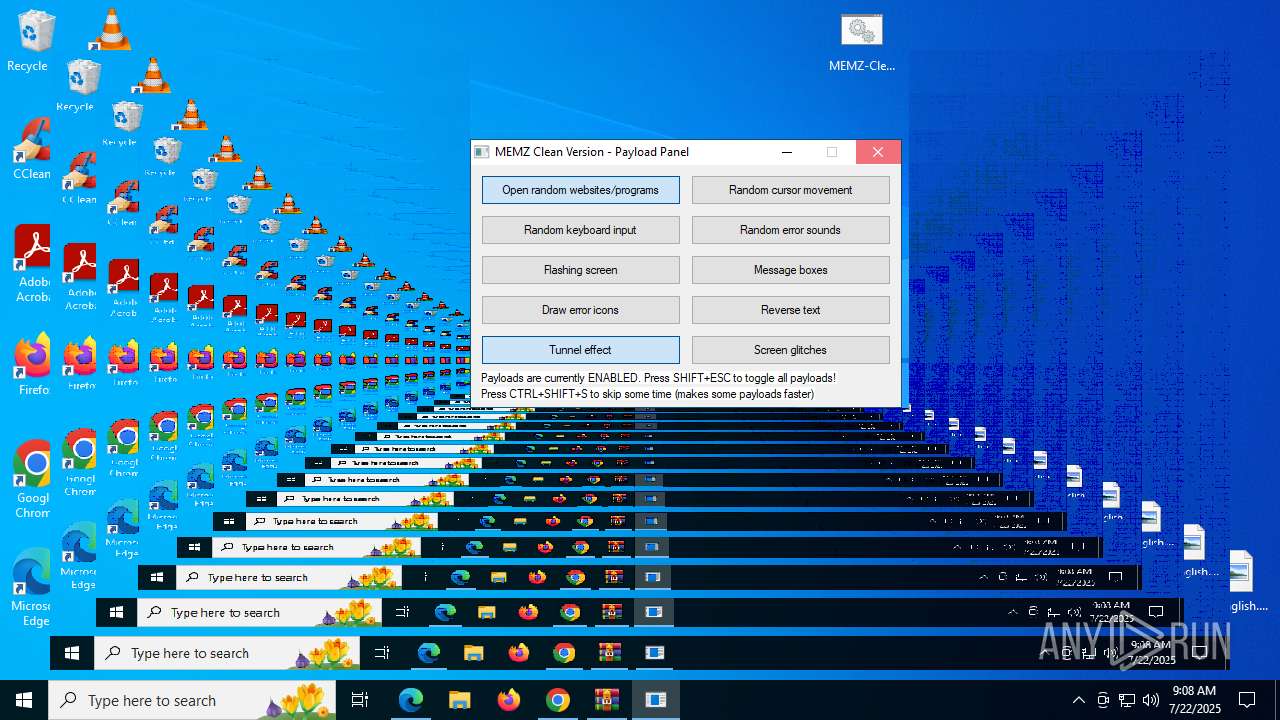
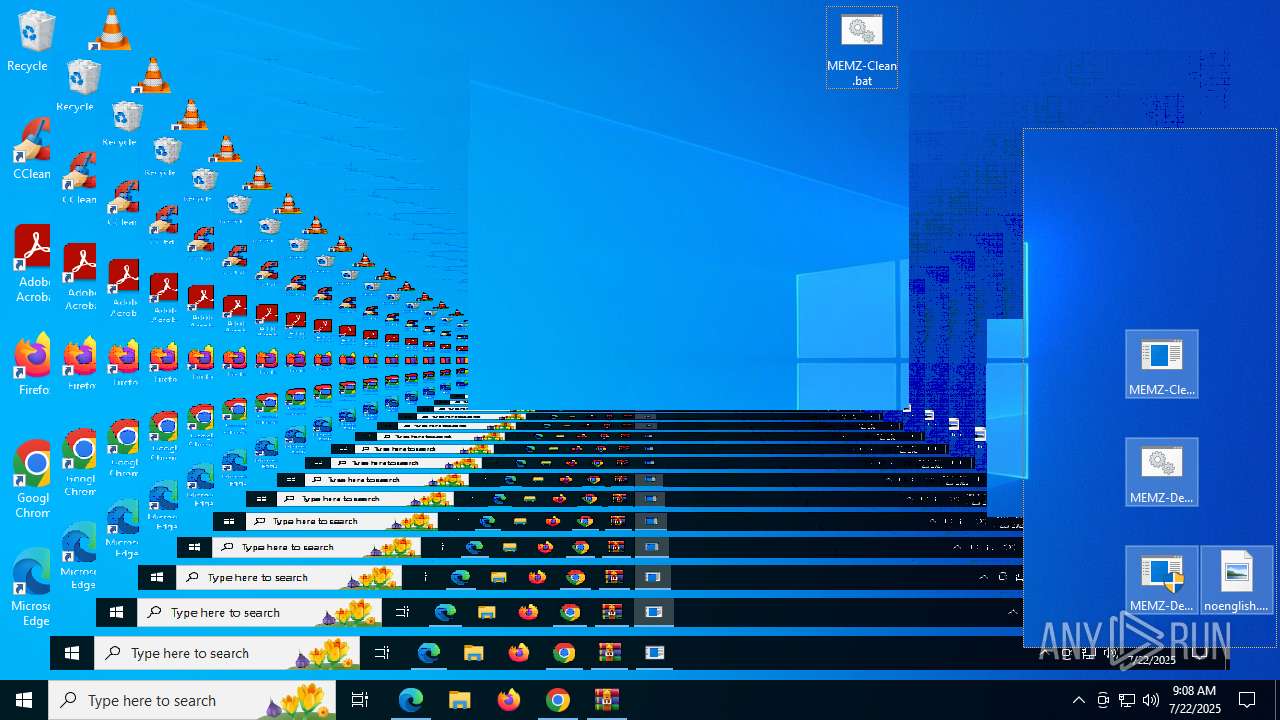
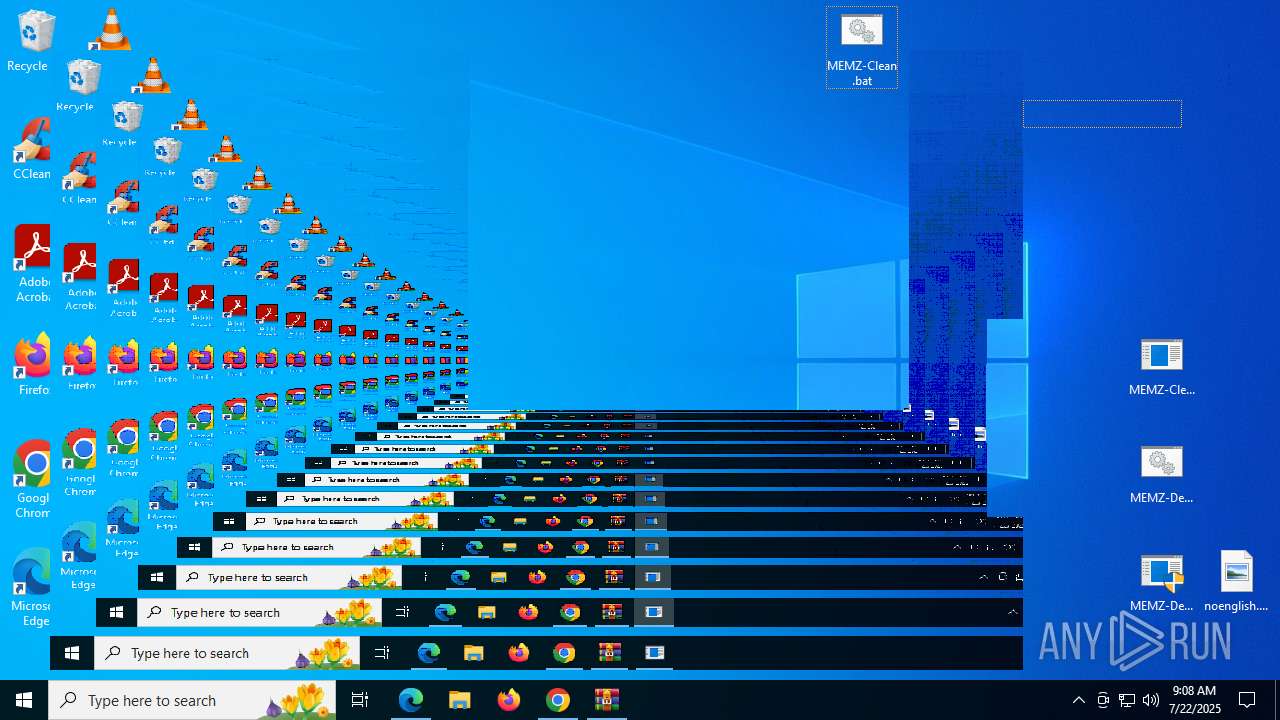
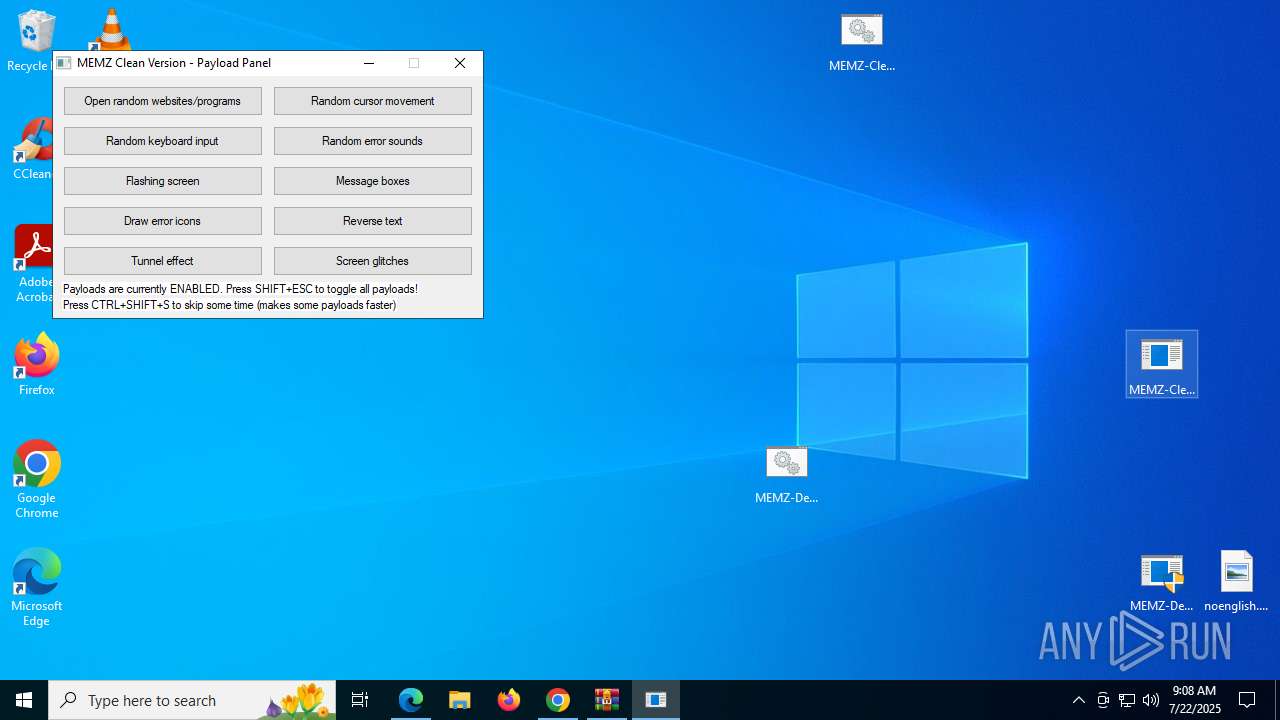
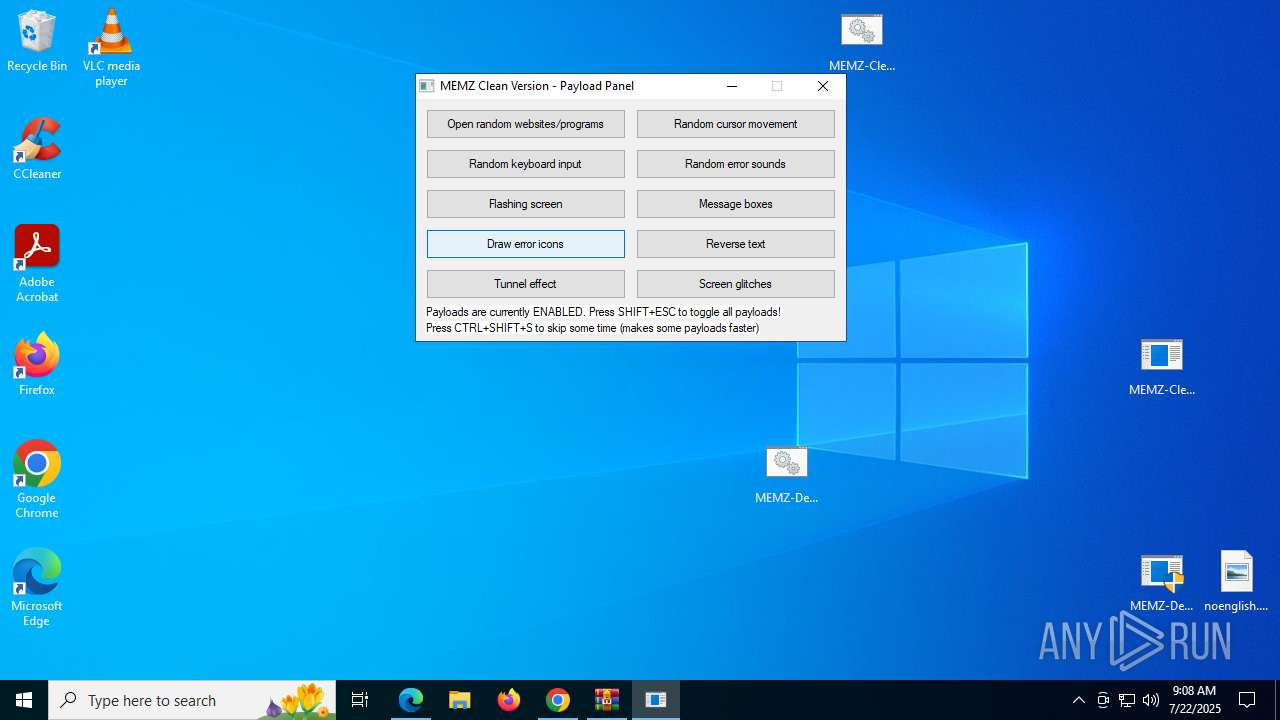
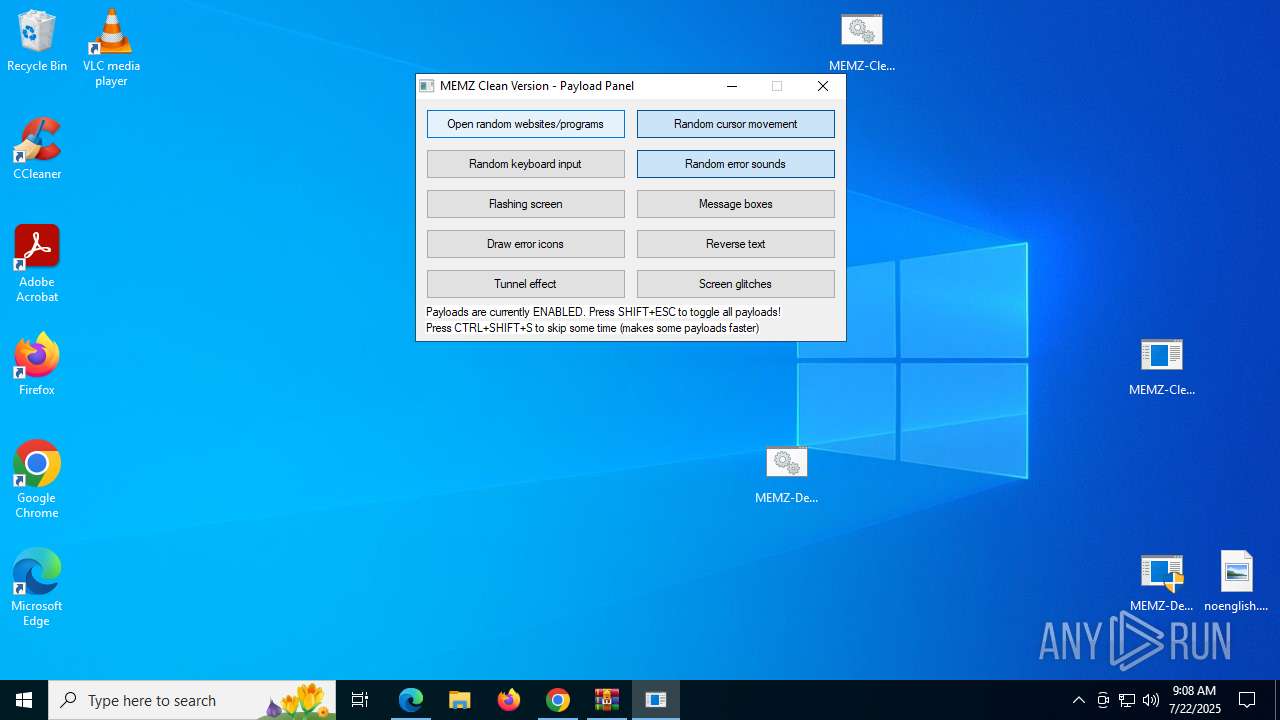
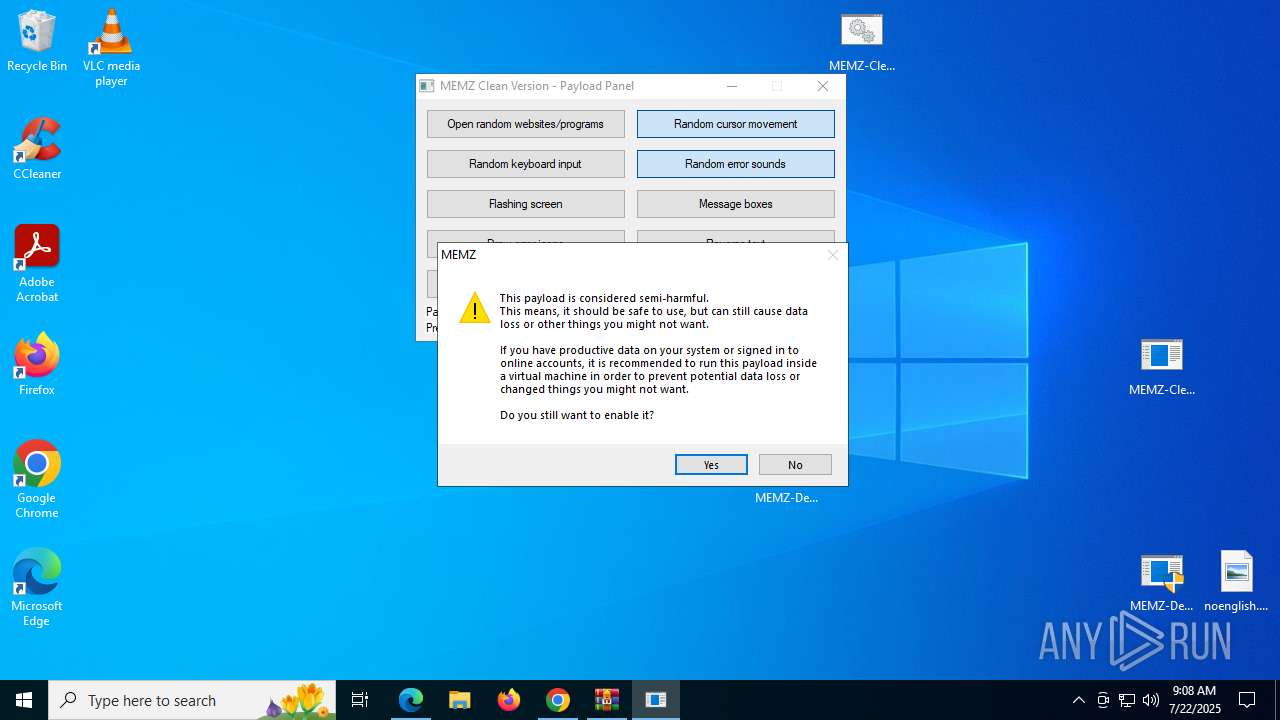
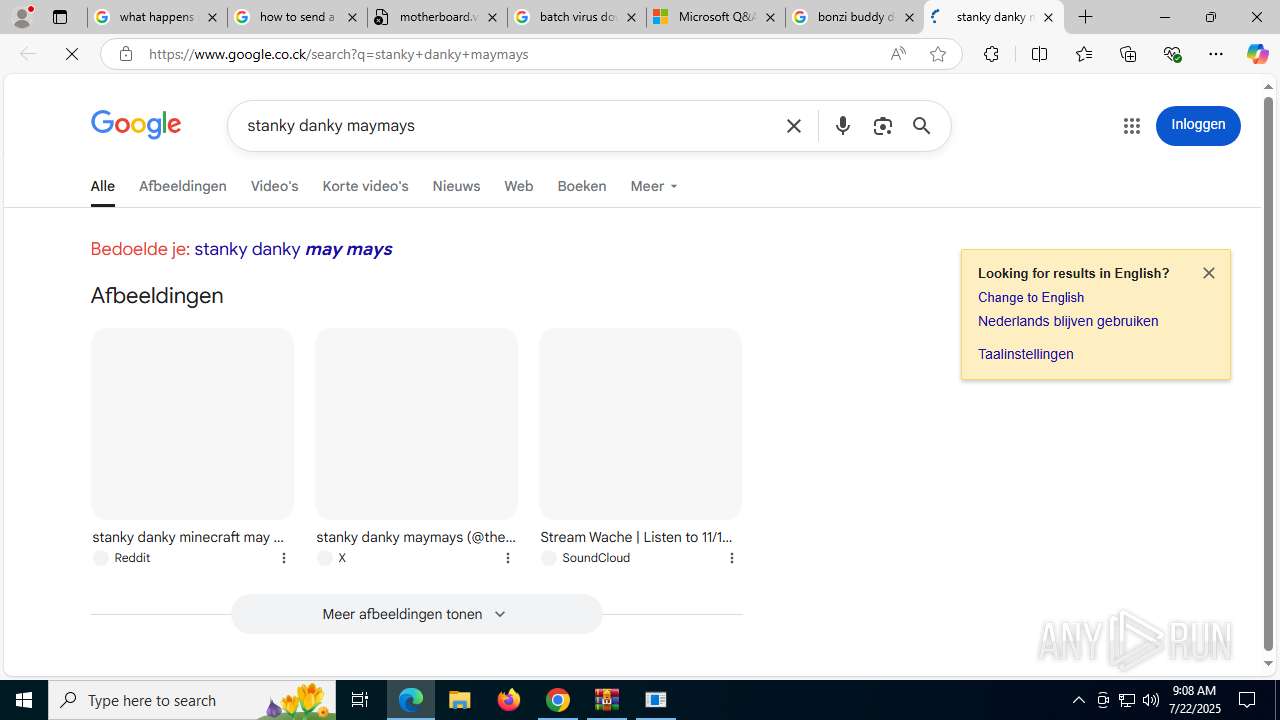
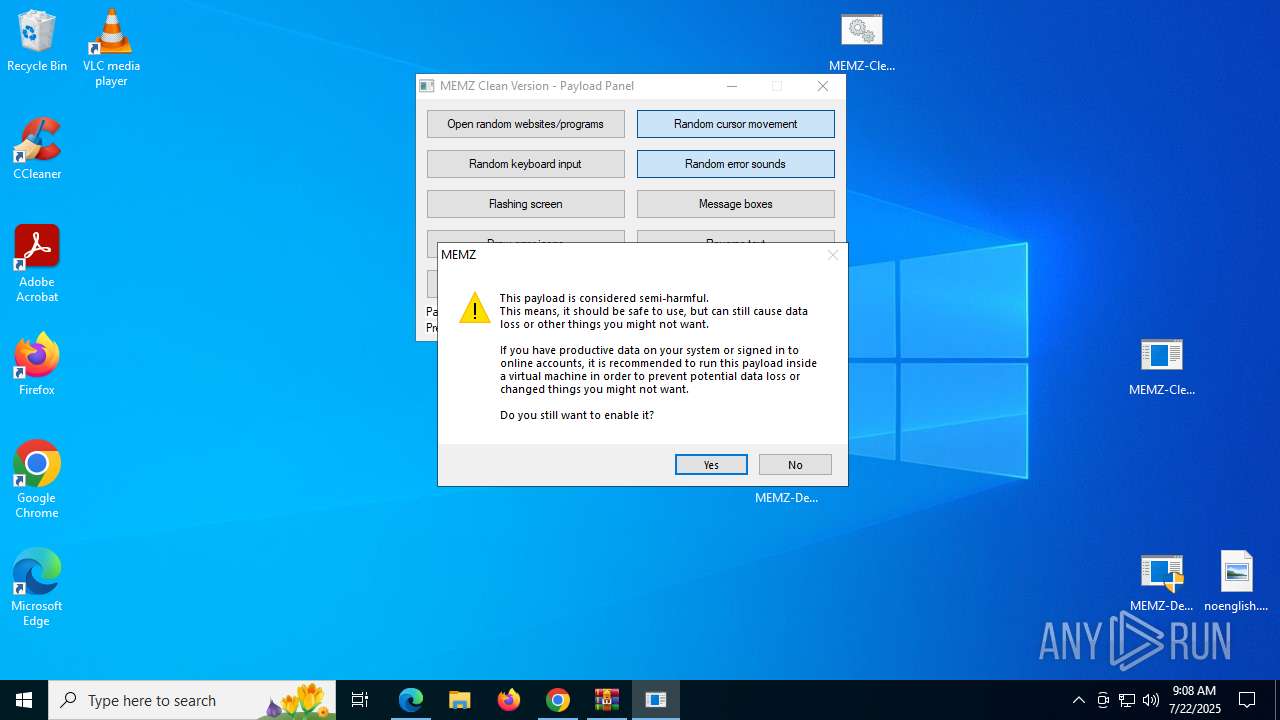
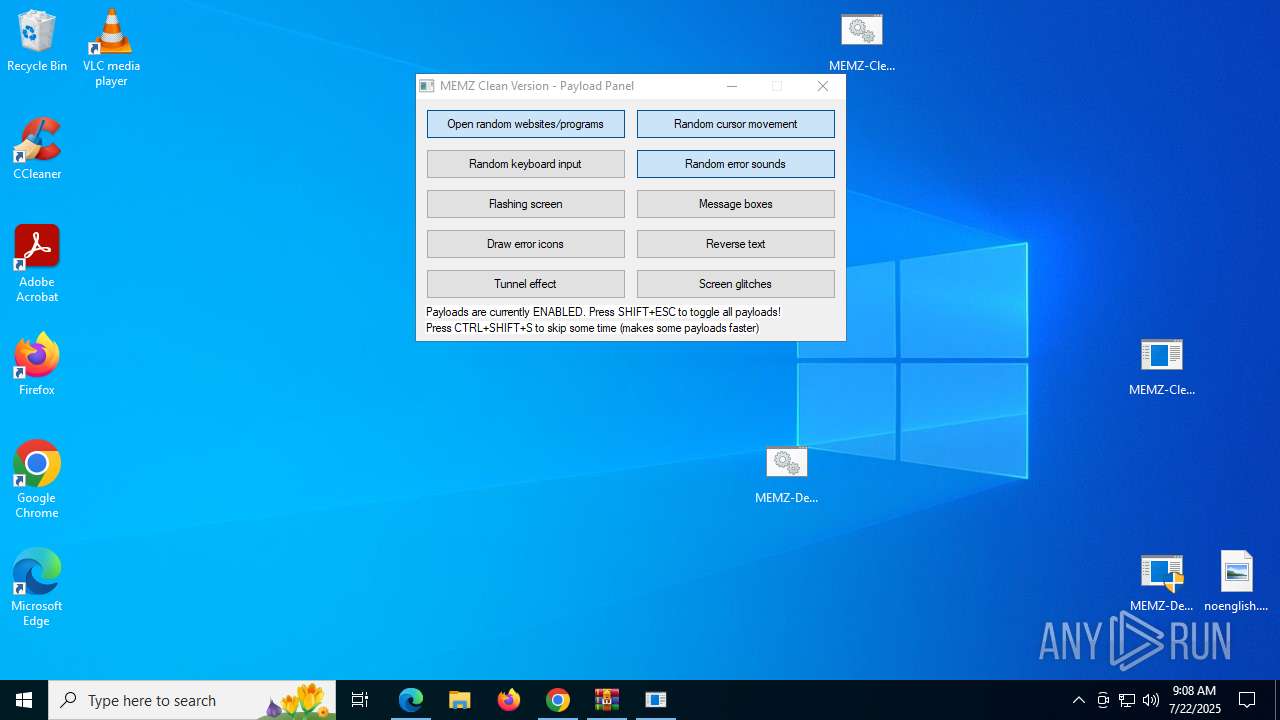
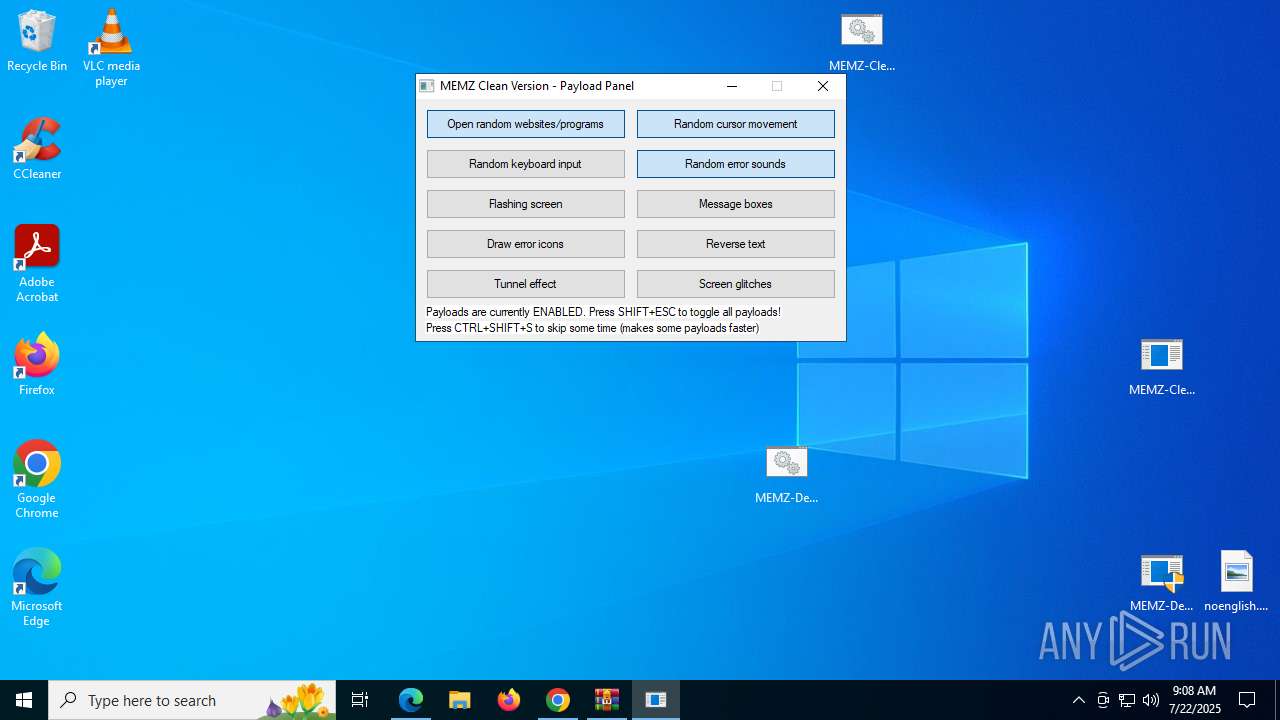
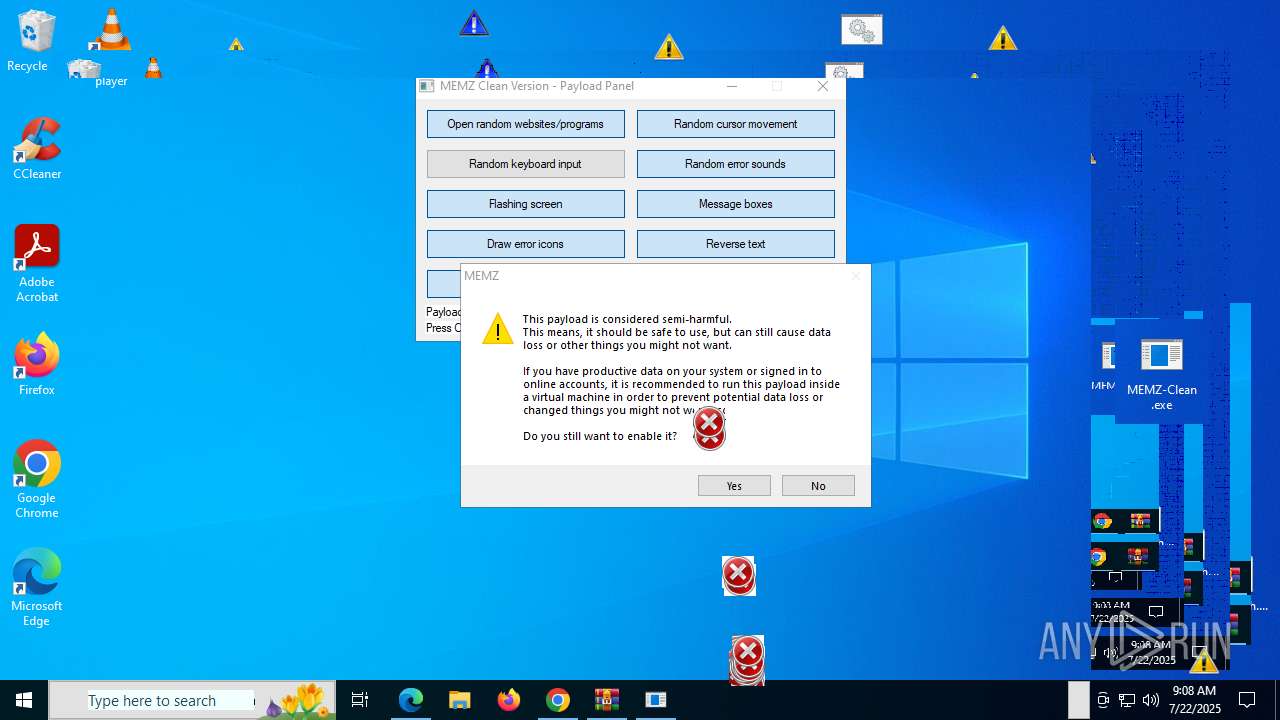
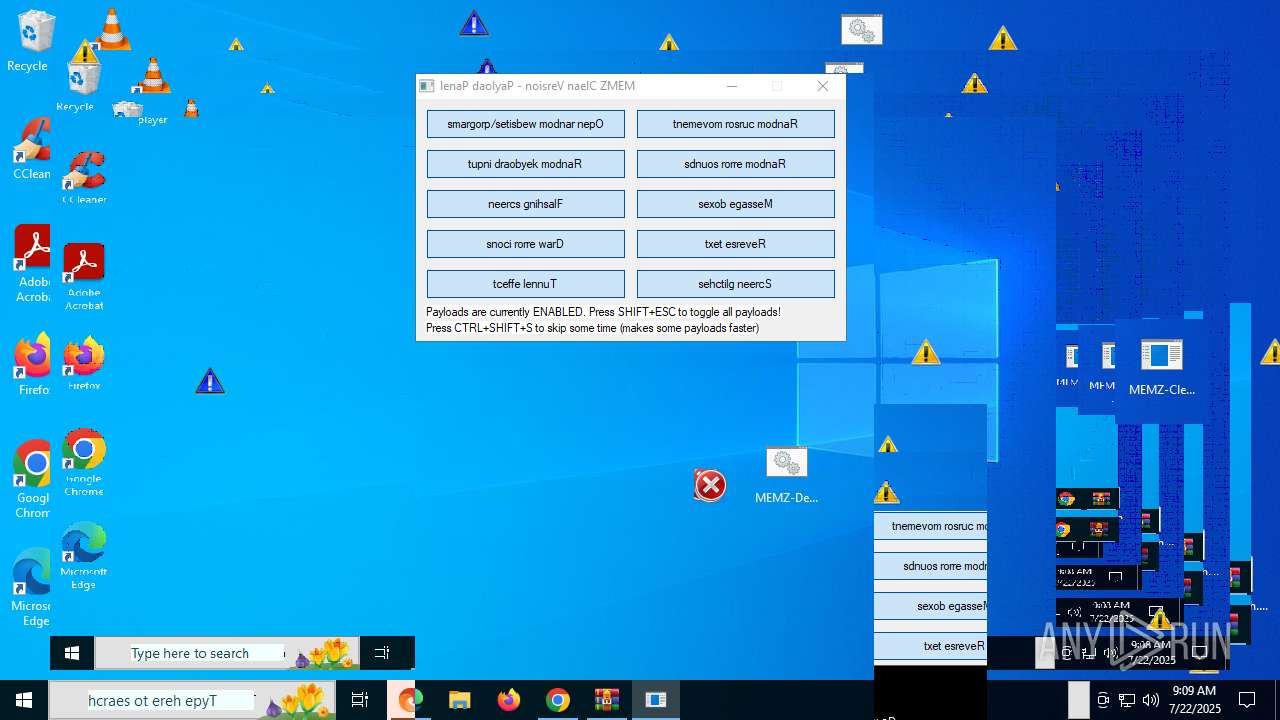
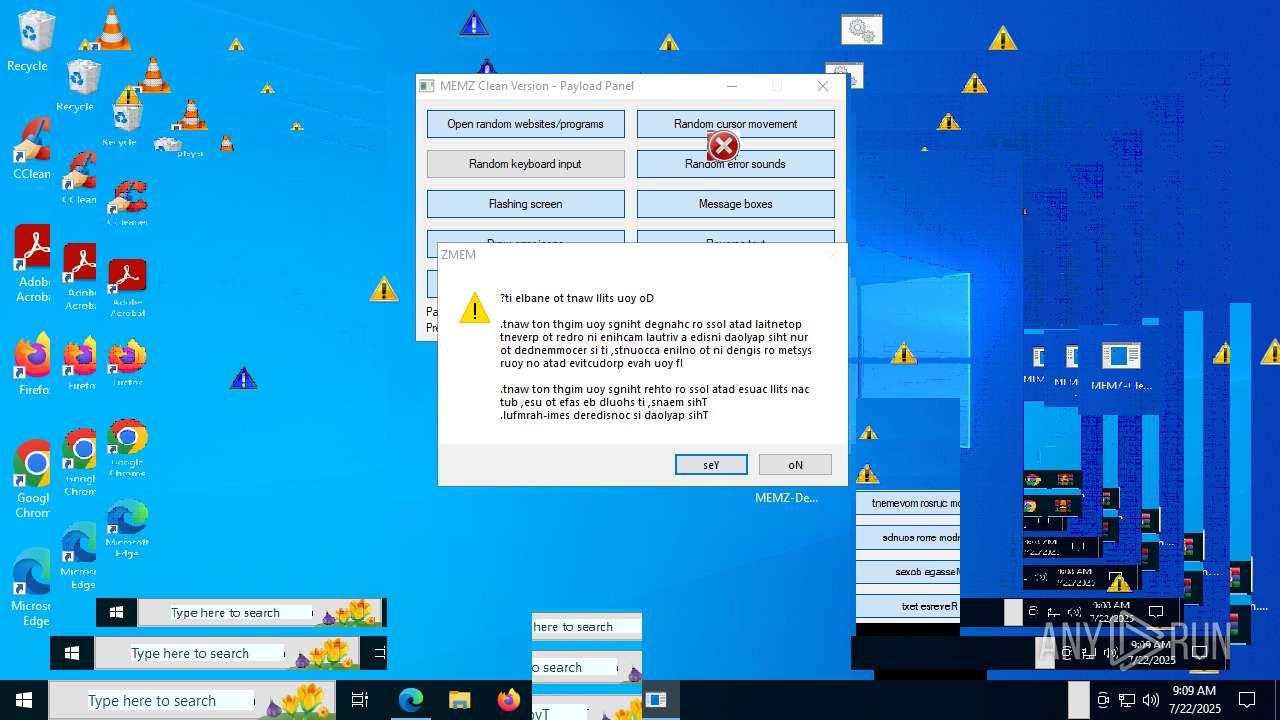
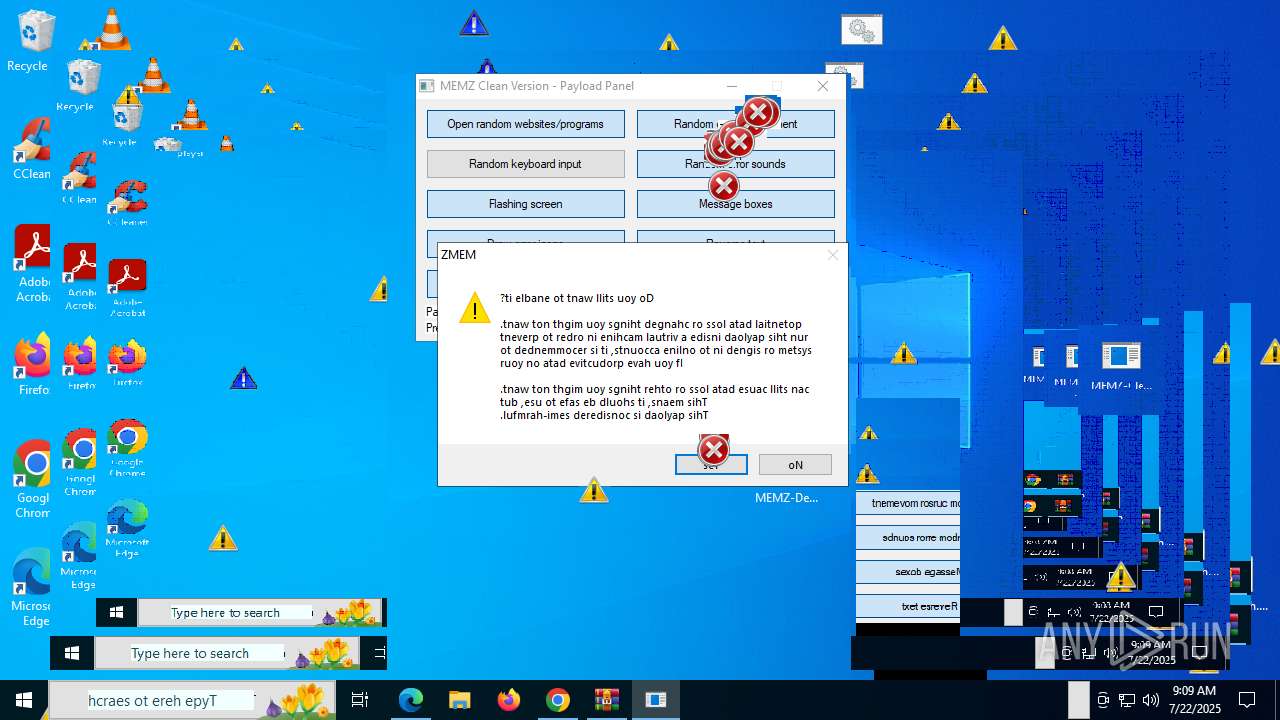
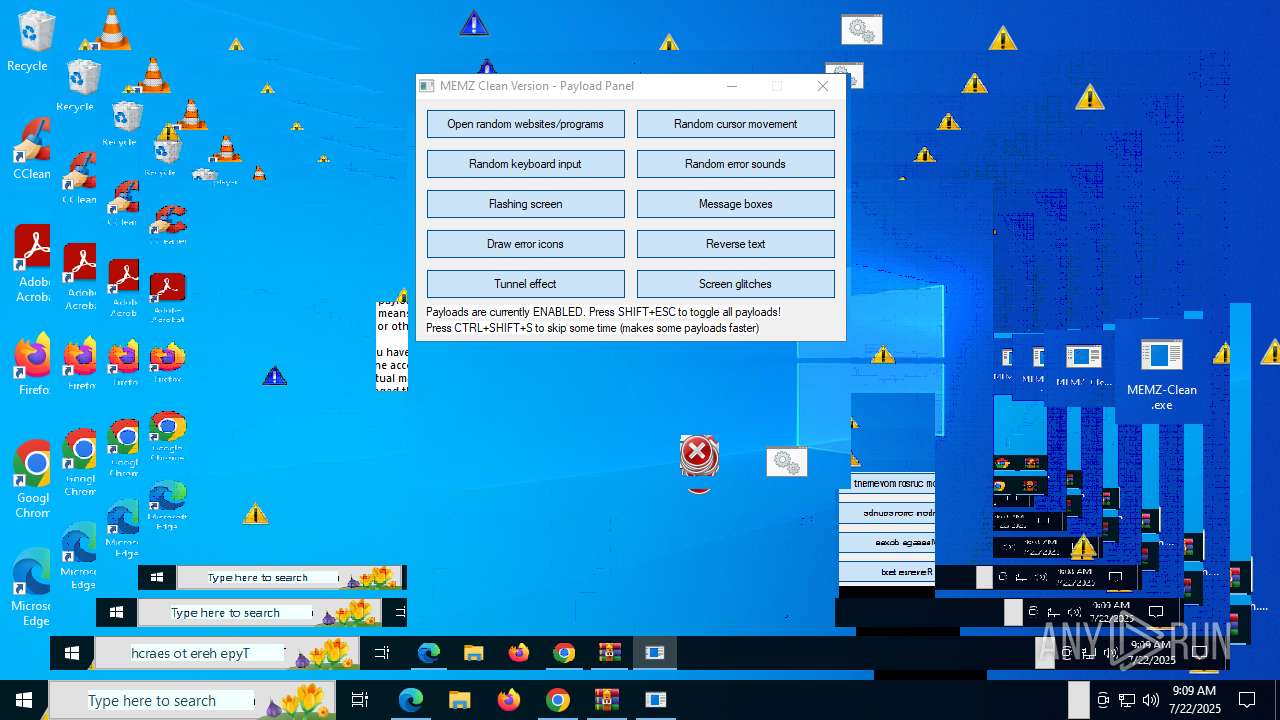
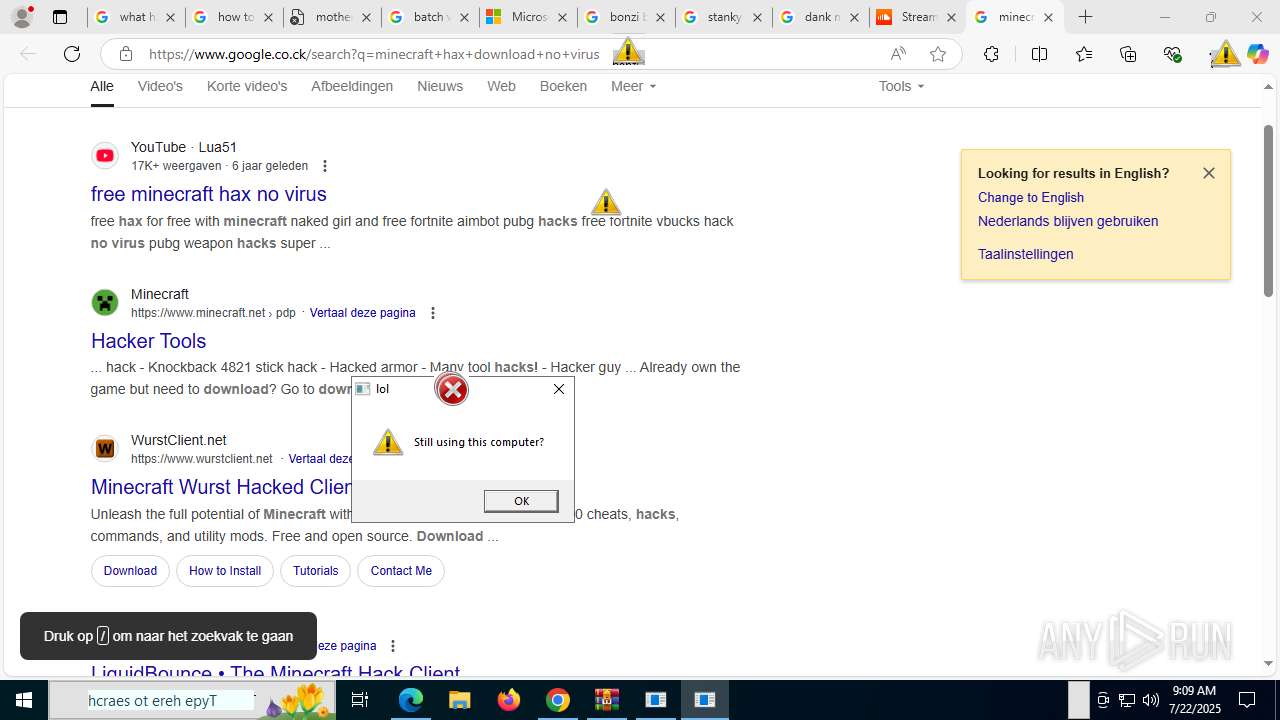
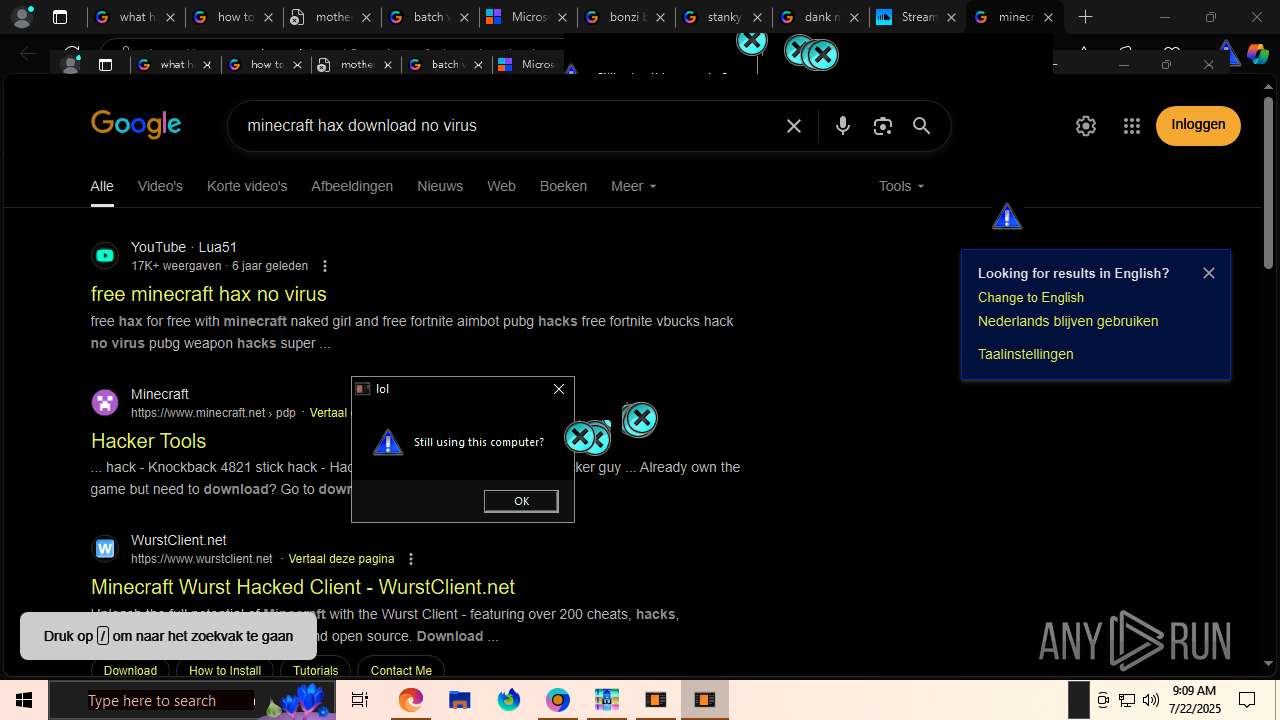
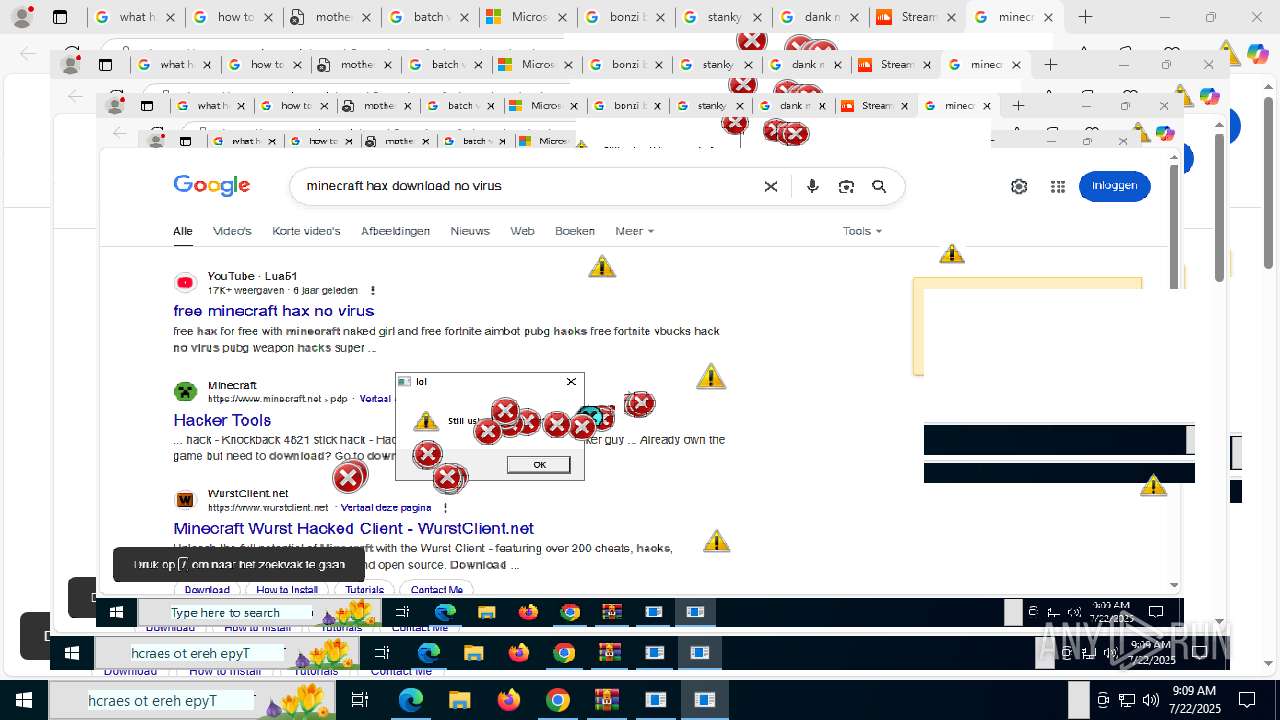
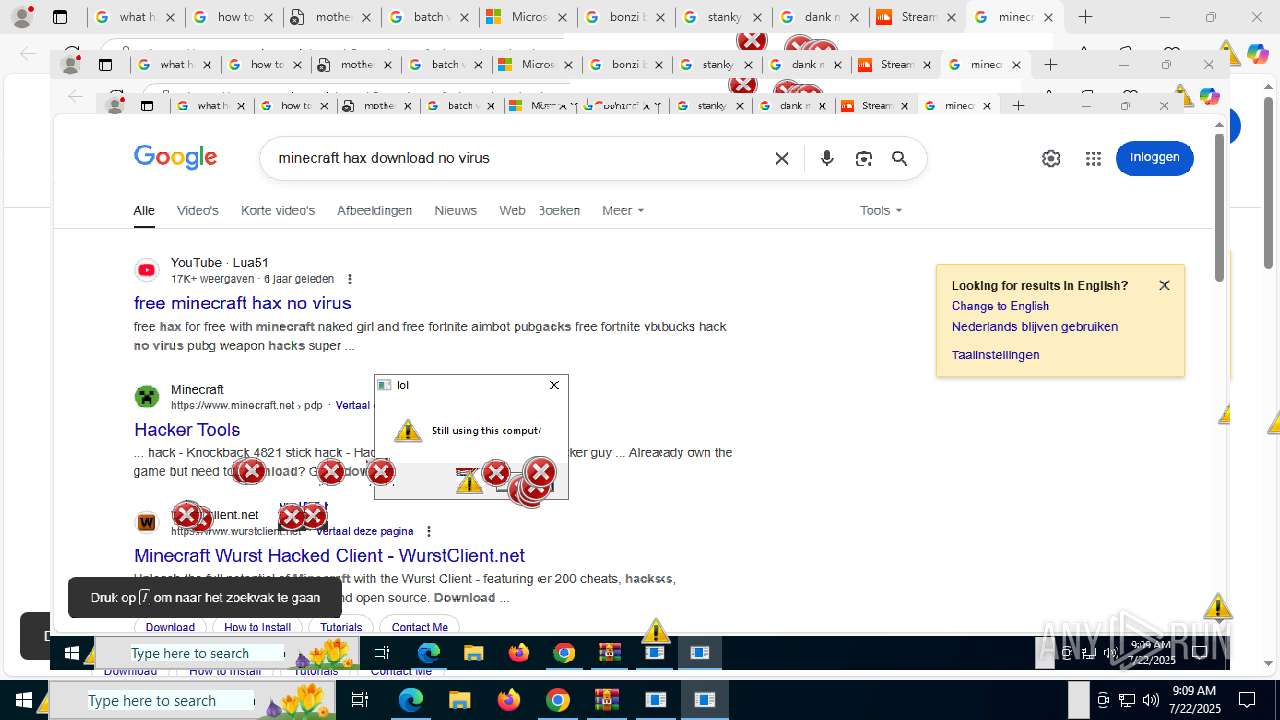
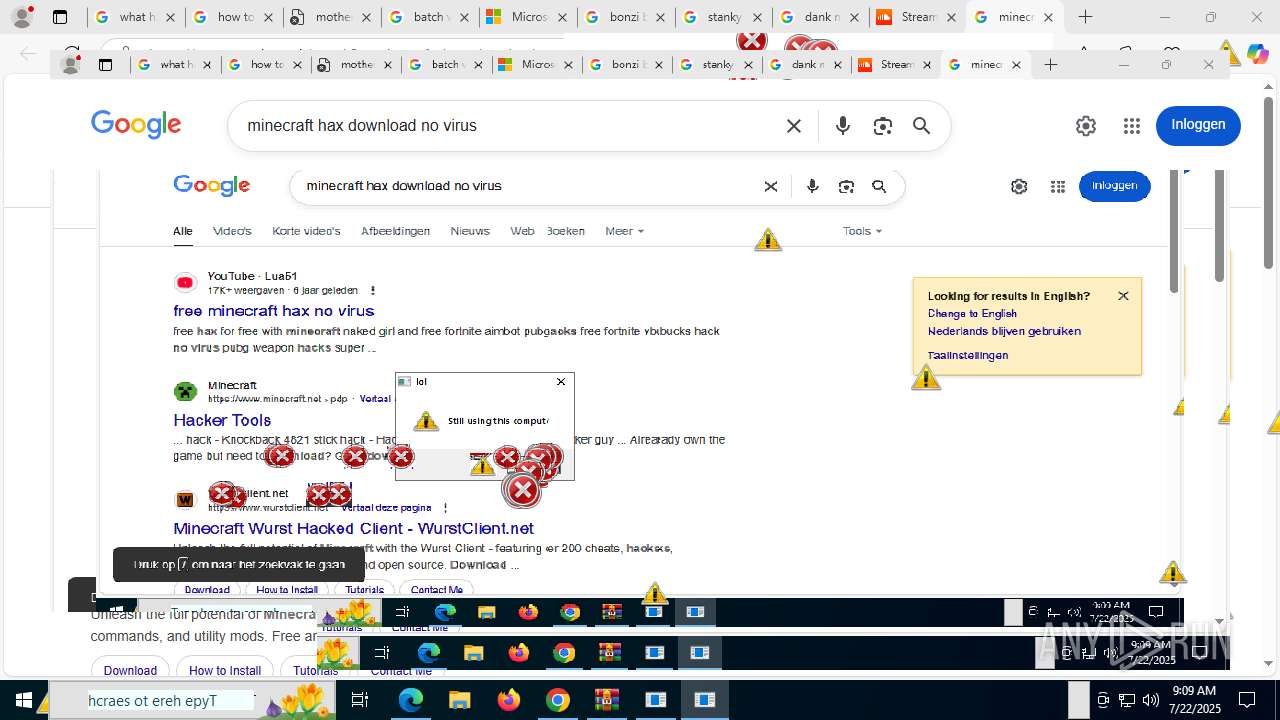
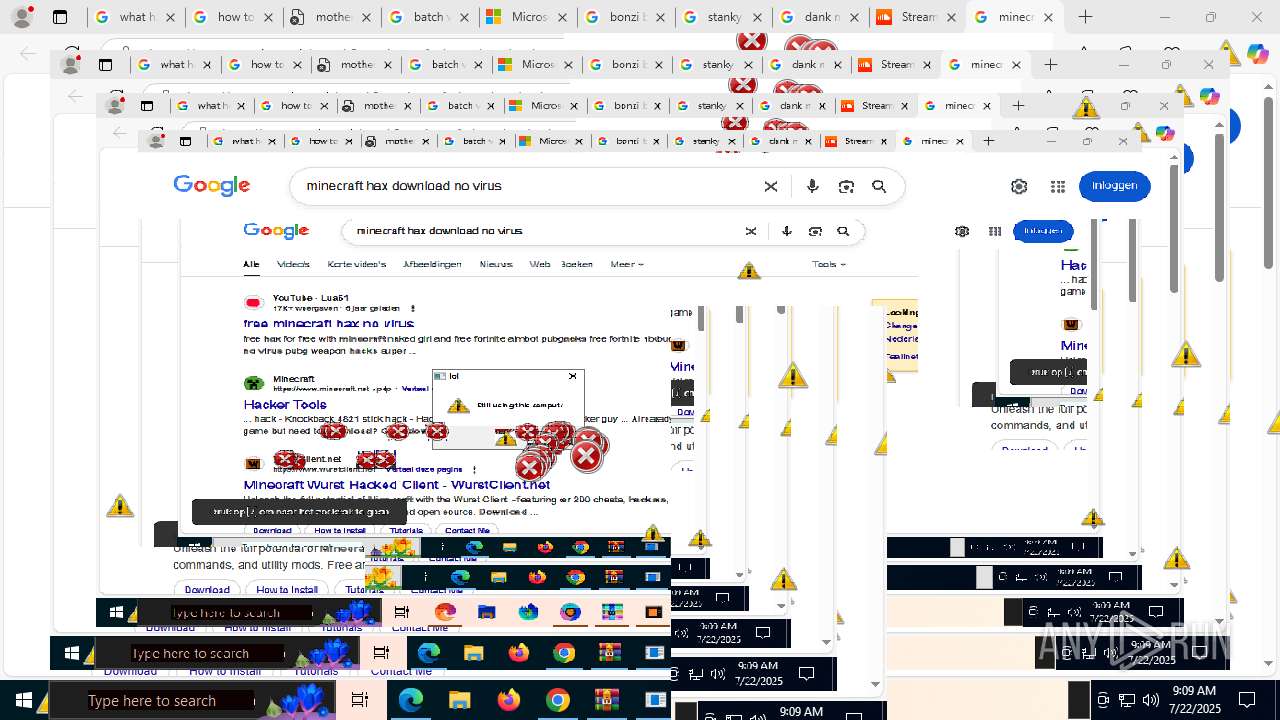
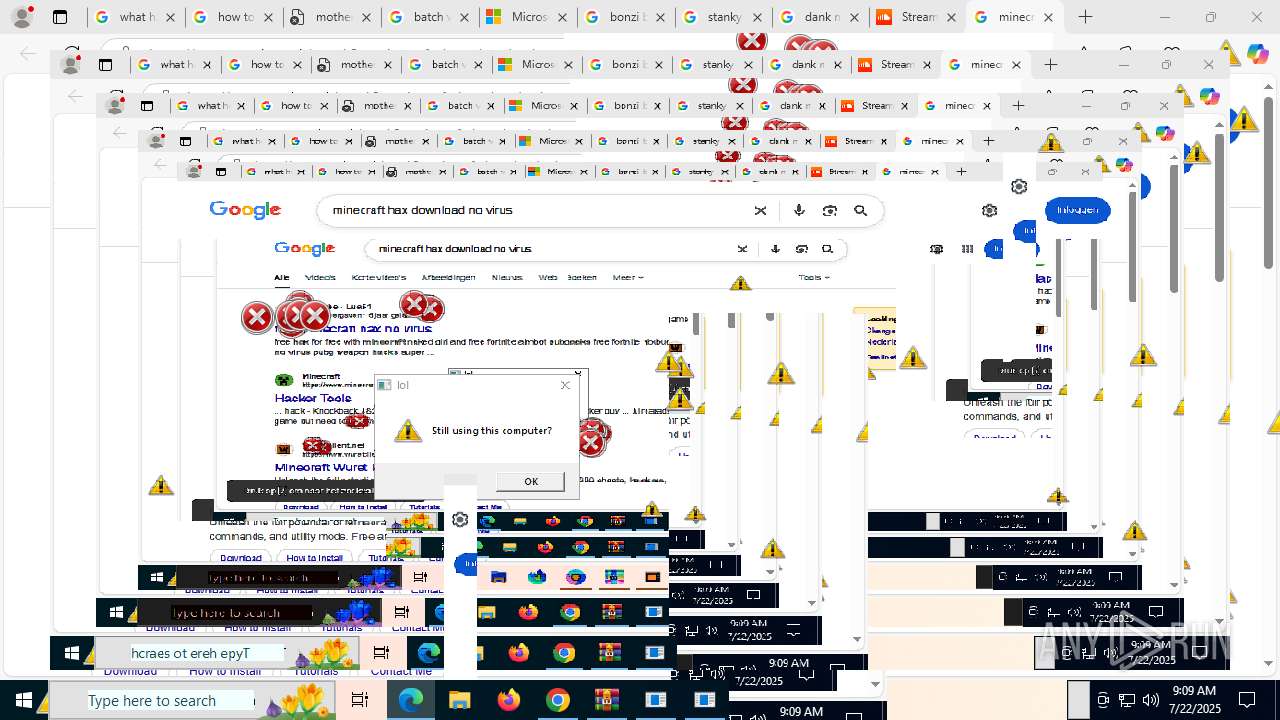
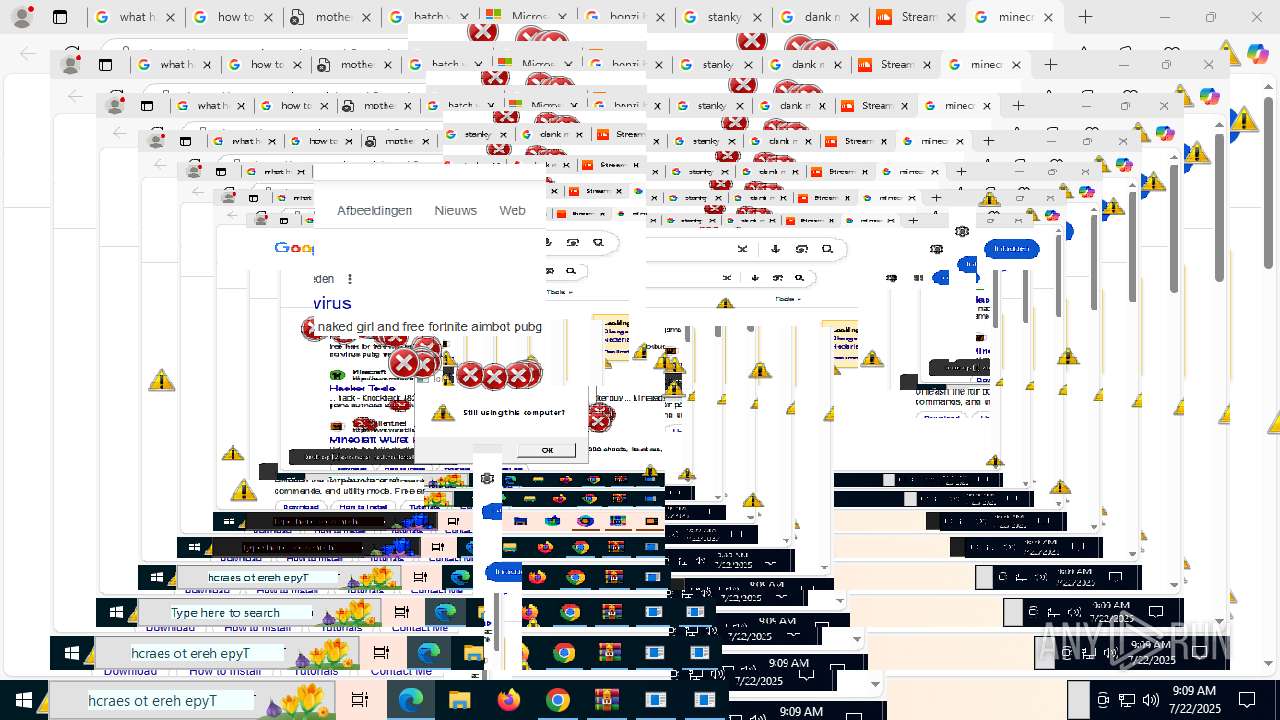
MALICIOUS
MEMZ has been detected (YARA)
- MEMZ-Destructive.exe (PID: 4192)
- MEMZ-Destructive.exe (PID: 6544)
- MEMZ-Destructive.exe (PID: 1440)
- MEMZ-Destructive.exe (PID: 1704)
- MEMZ-Destructive.exe (PID: 6488)
- MEMZ-Destructive.exe (PID: 3628)
Uses base64 encoding (SCRIPT)
- cscript.exe (PID: 7960)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- cscript.exe (PID: 7960)
SUSPICIOUS
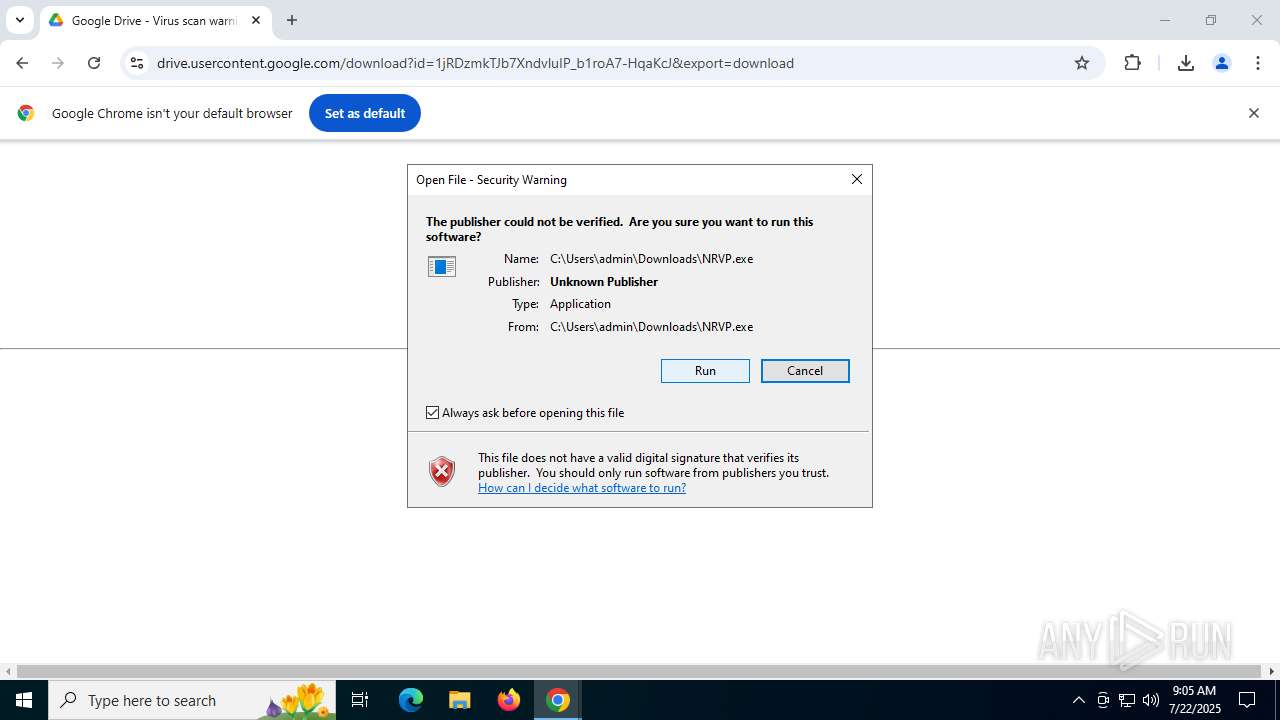
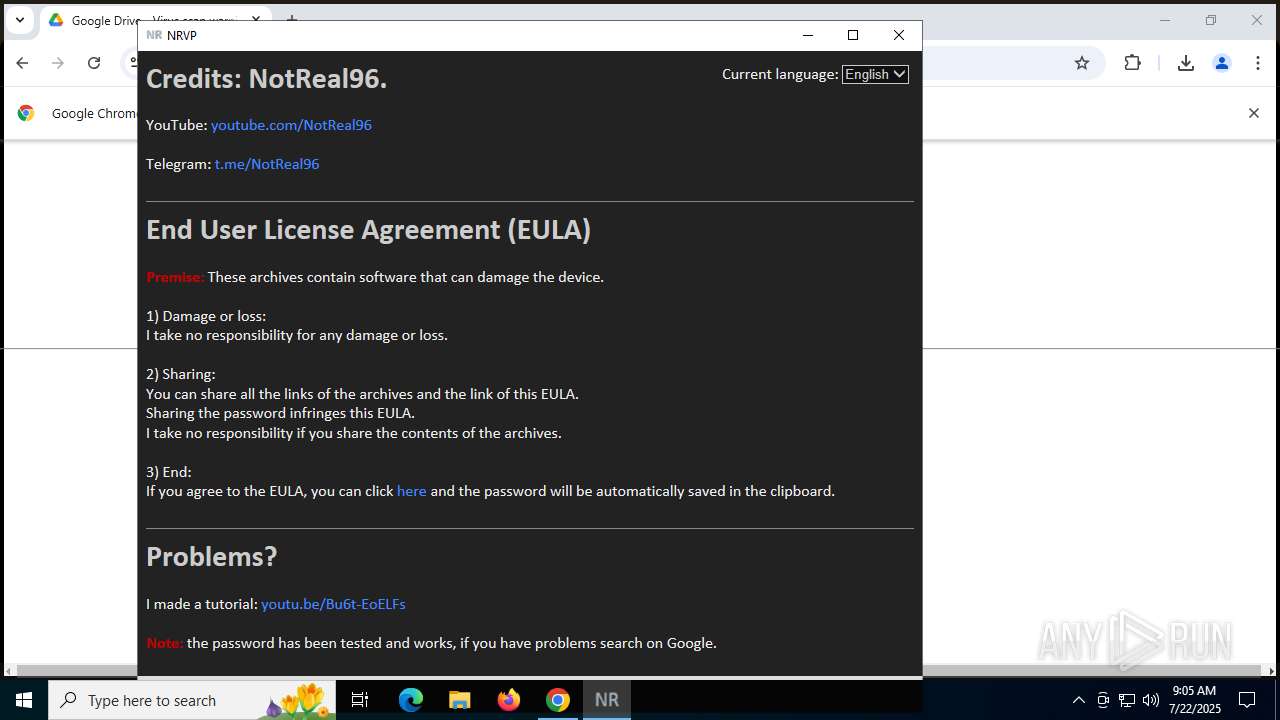
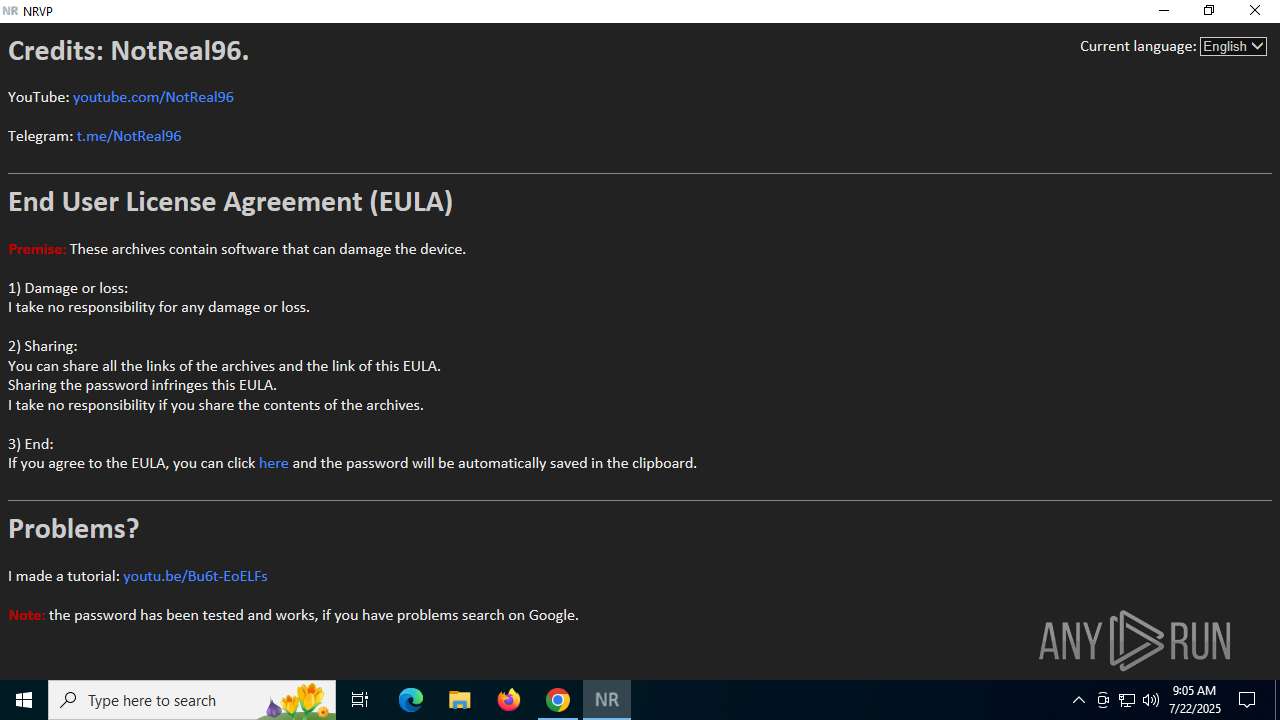
Reads Internet Explorer settings
- NRVP.exe (PID: 3732)
Reads Microsoft Outlook installation path
- NRVP.exe (PID: 3732)
Reads security settings of Internet Explorer
- NRVP.exe (PID: 3732)
- MEMZ-Destructive.exe (PID: 4748)
- MEMZ-Destructive.exe (PID: 6488)
- MEMZ.exe (PID: 8032)
- MEMZ-Clean.exe (PID: 8940)
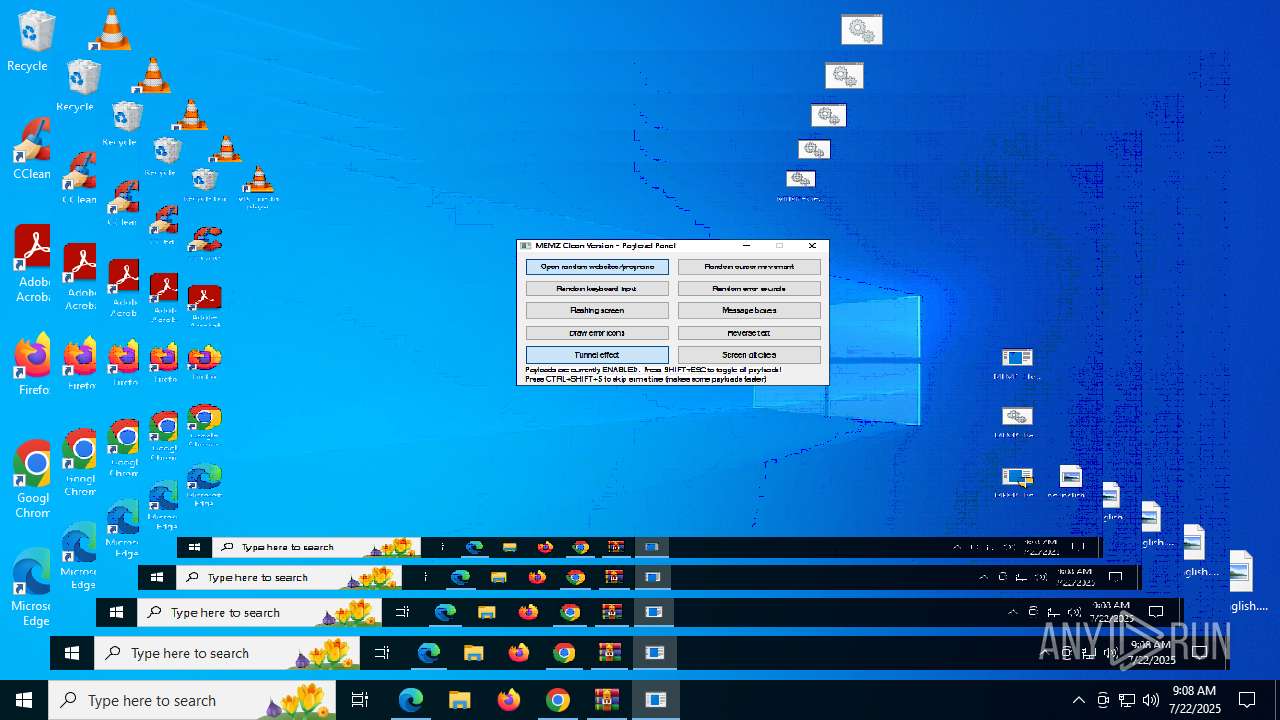
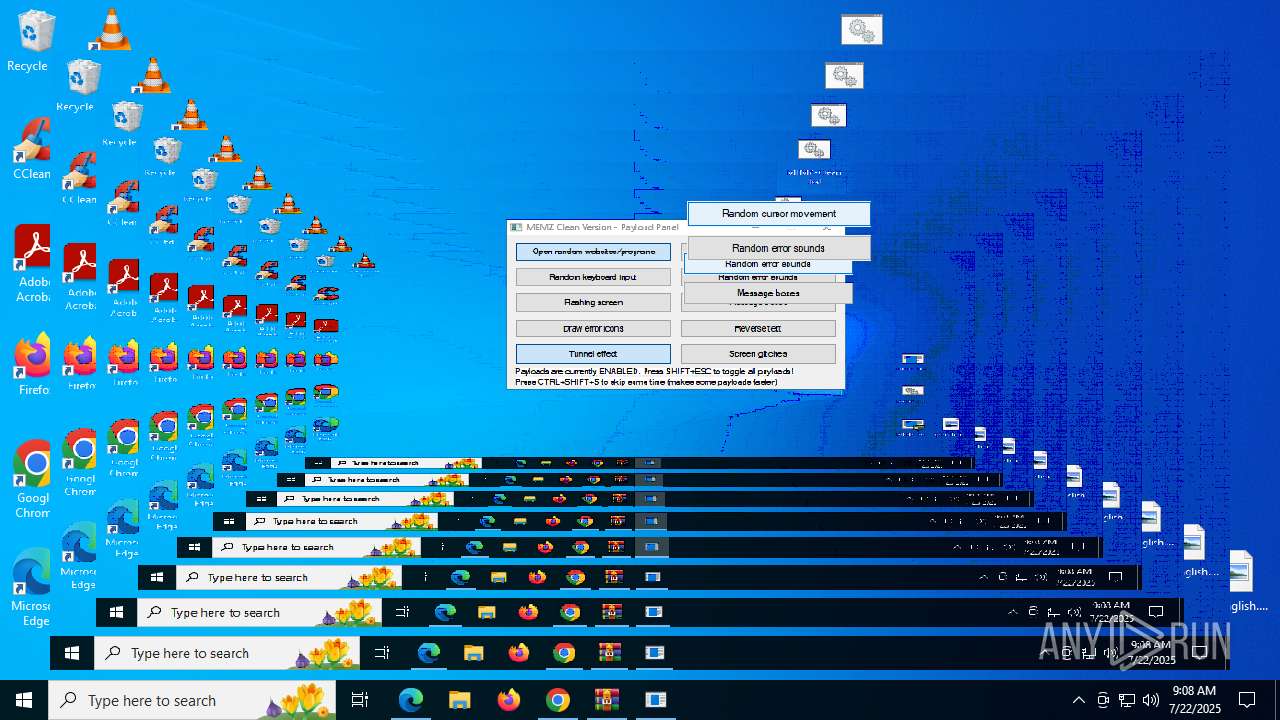
Application launched itself
- MEMZ-Destructive.exe (PID: 4748)
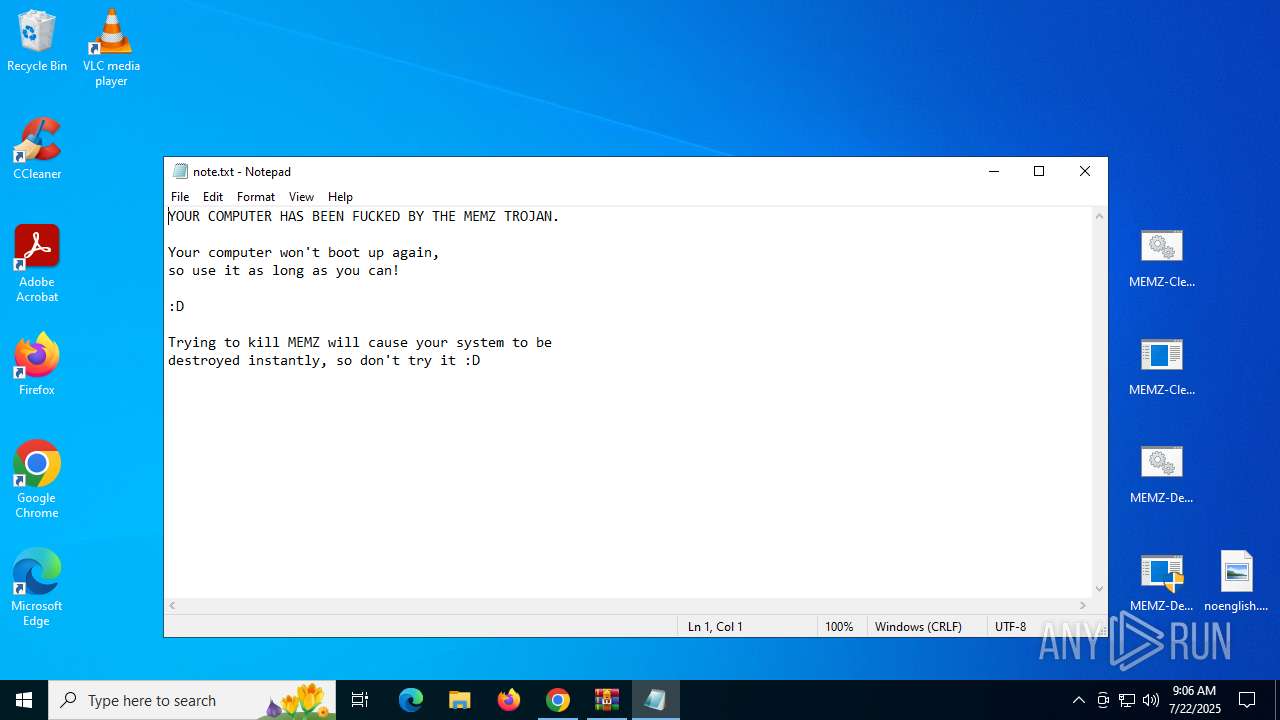
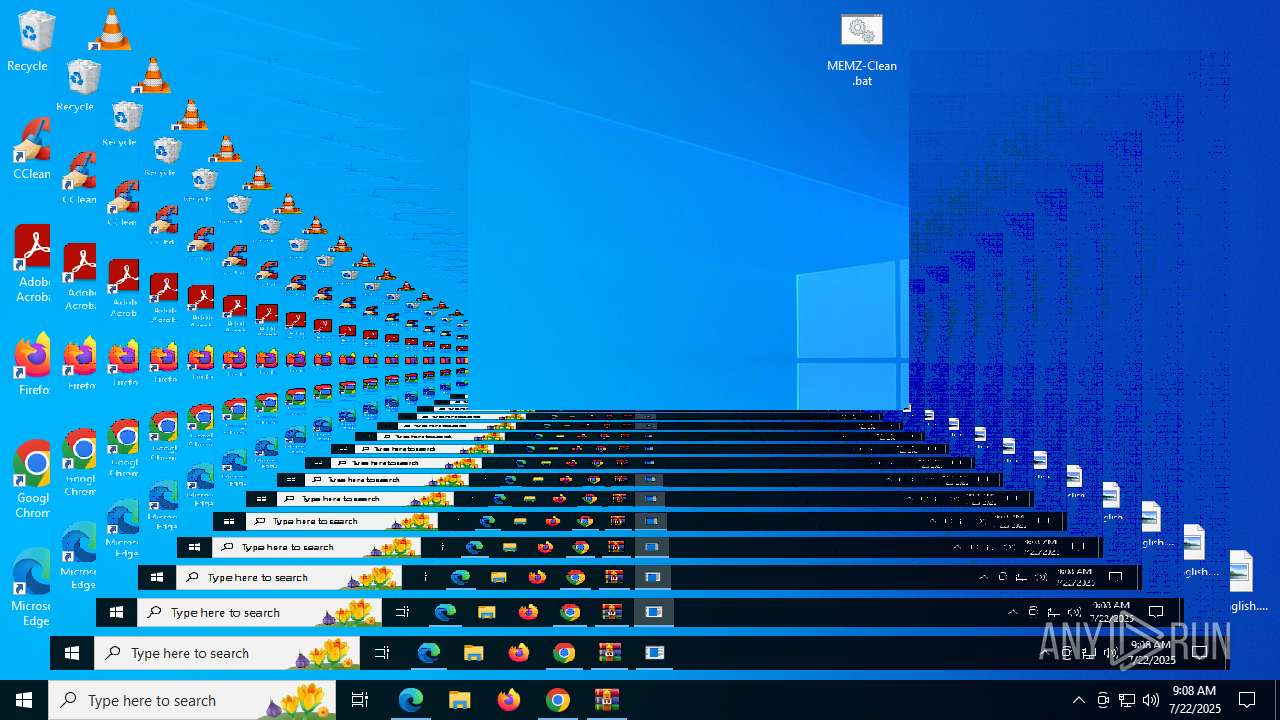
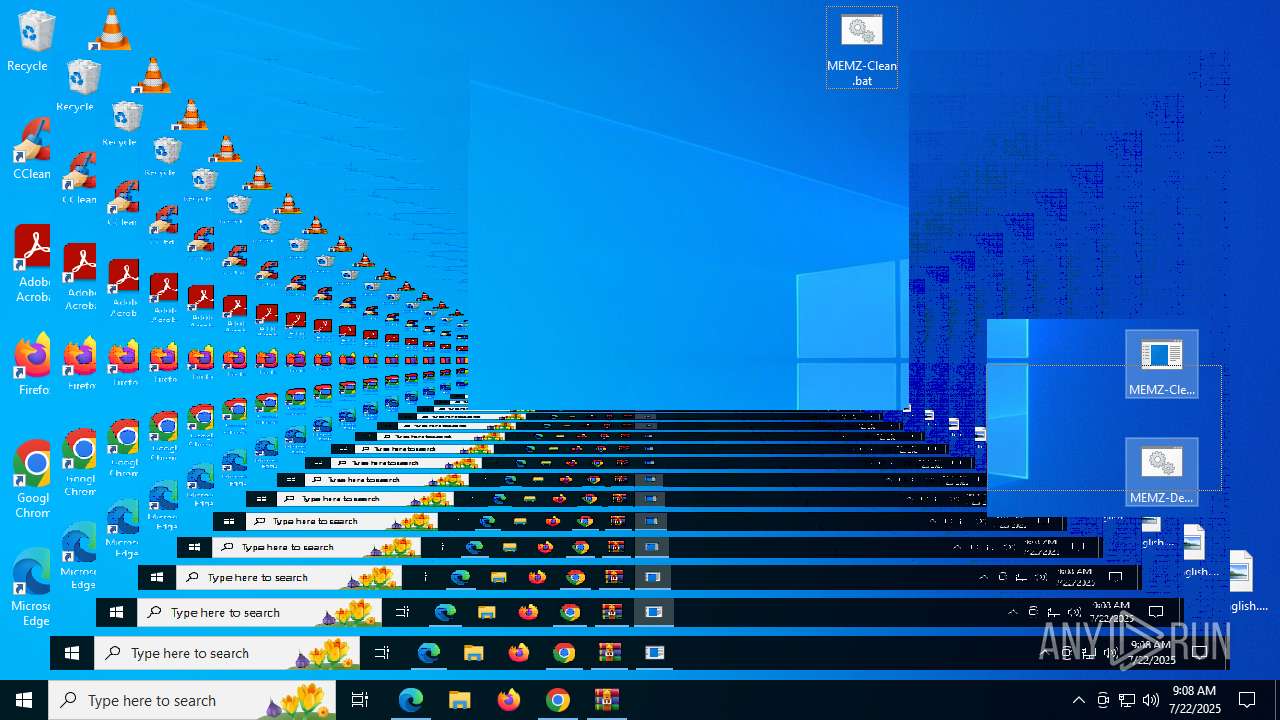
Creates file in the systems drive root
- MEMZ-Destructive.exe (PID: 6488)
- notepad.exe (PID: 7104)
Start notepad (likely ransomware note)
- MEMZ-Destructive.exe (PID: 6488)
There is functionality for taking screenshot (YARA)
- MEMZ-Destructive.exe (PID: 4192)
- MEMZ-Destructive.exe (PID: 3628)
- MEMZ-Destructive.exe (PID: 6544)
- MEMZ-Destructive.exe (PID: 1704)
- MEMZ-Destructive.exe (PID: 6488)
- MEMZ-Destructive.exe (PID: 1440)
- MEMZ.exe (PID: 8032)
The process executes JS scripts
- cmd.exe (PID: 7896)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 7960)
Creates XML DOM element (SCRIPT)
- cscript.exe (PID: 7960)
Script creates XML DOM node (SCRIPT)
- cscript.exe (PID: 7960)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 7960)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 7960)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 7960)
Creates a Folder object (SCRIPT)
- cscript.exe (PID: 7960)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 7960)
Executable content was dropped or overwritten
- cscript.exe (PID: 7960)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 8832)
INFO
Reads the computer name
- NRVP.exe (PID: 3732)
- MEMZ-Destructive.exe (PID: 4748)
- MEMZ-Destructive.exe (PID: 6488)
- identity_helper.exe (PID: 7676)
- MEMZ.exe (PID: 8032)
- MEMZ-Clean.exe (PID: 8940)
Checks supported languages
- NRVP.exe (PID: 3732)
- MEMZ-Destructive.exe (PID: 4748)
- MEMZ-Destructive.exe (PID: 3628)
- MEMZ-Destructive.exe (PID: 4192)
- MEMZ-Destructive.exe (PID: 6488)
- MEMZ-Destructive.exe (PID: 1440)
- MEMZ-Destructive.exe (PID: 6544)
- MEMZ-Destructive.exe (PID: 1704)
- identity_helper.exe (PID: 7676)
- MEMZ.exe (PID: 8032)
- MEMZ-Clean.exe (PID: 8940)
Reads Microsoft Office registry keys
- chrome.exe (PID: 2972)
Checks proxy server information
- NRVP.exe (PID: 3732)
- slui.exe (PID: 6292)
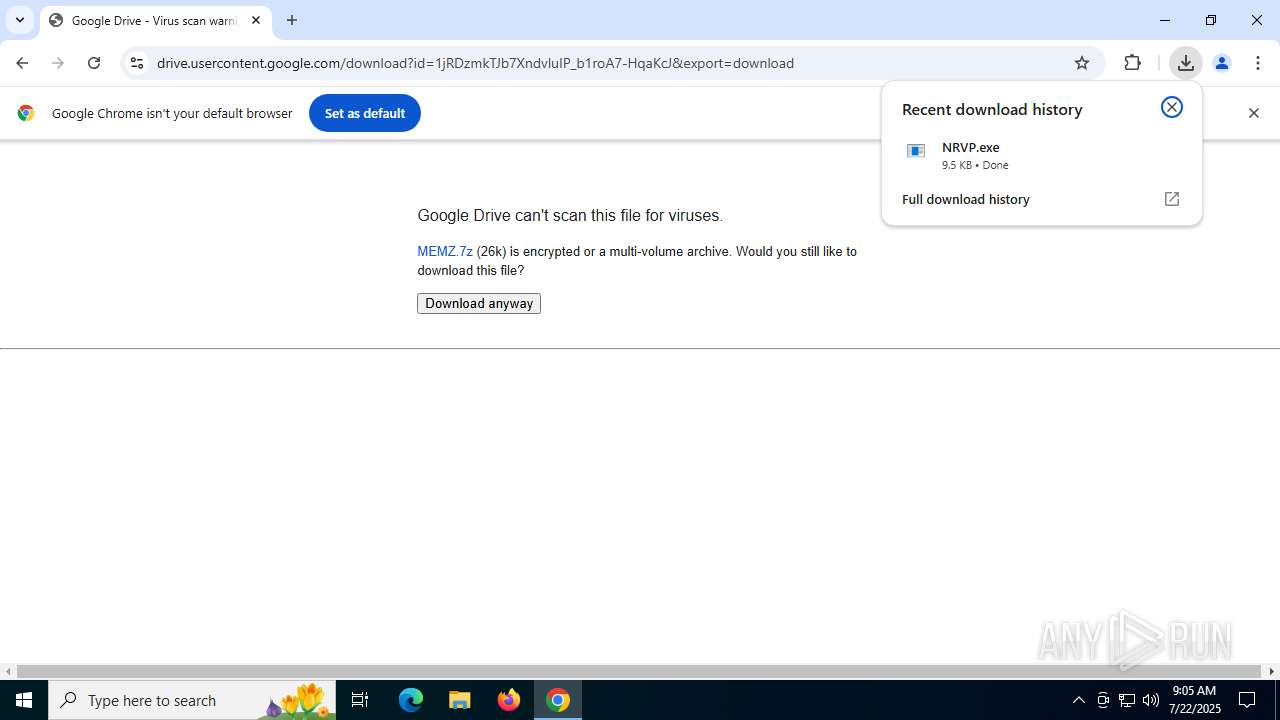
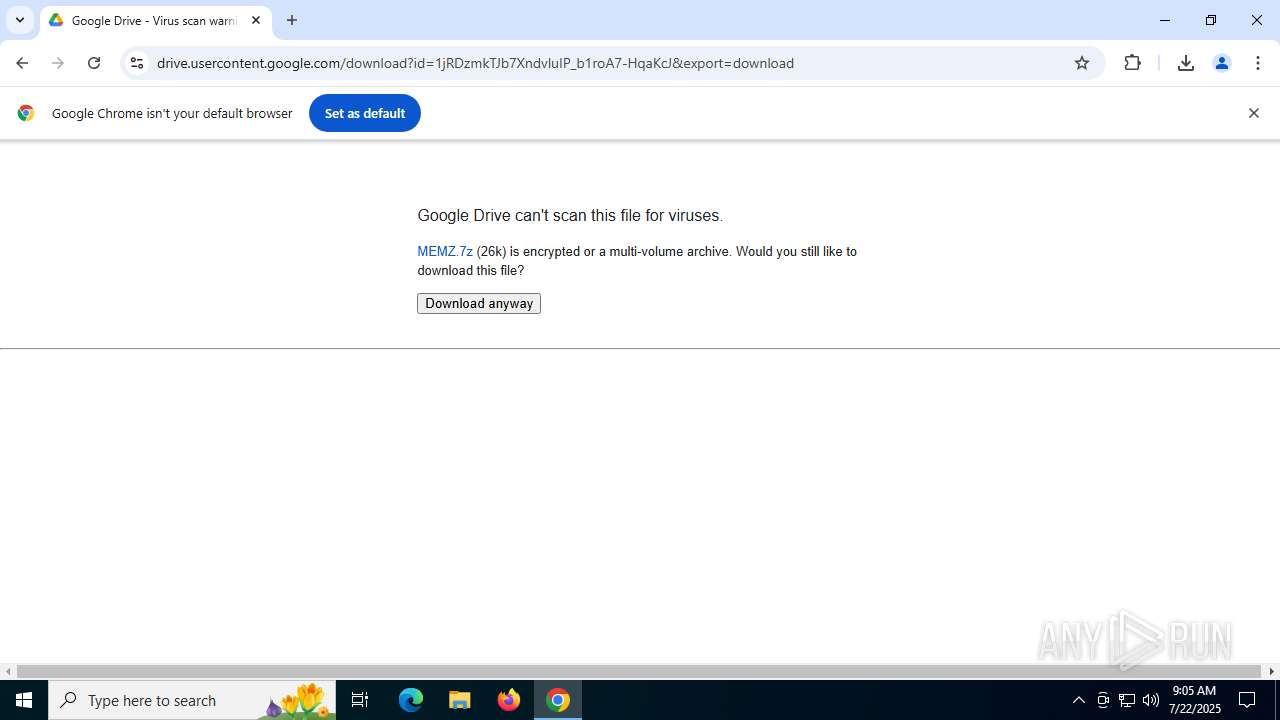
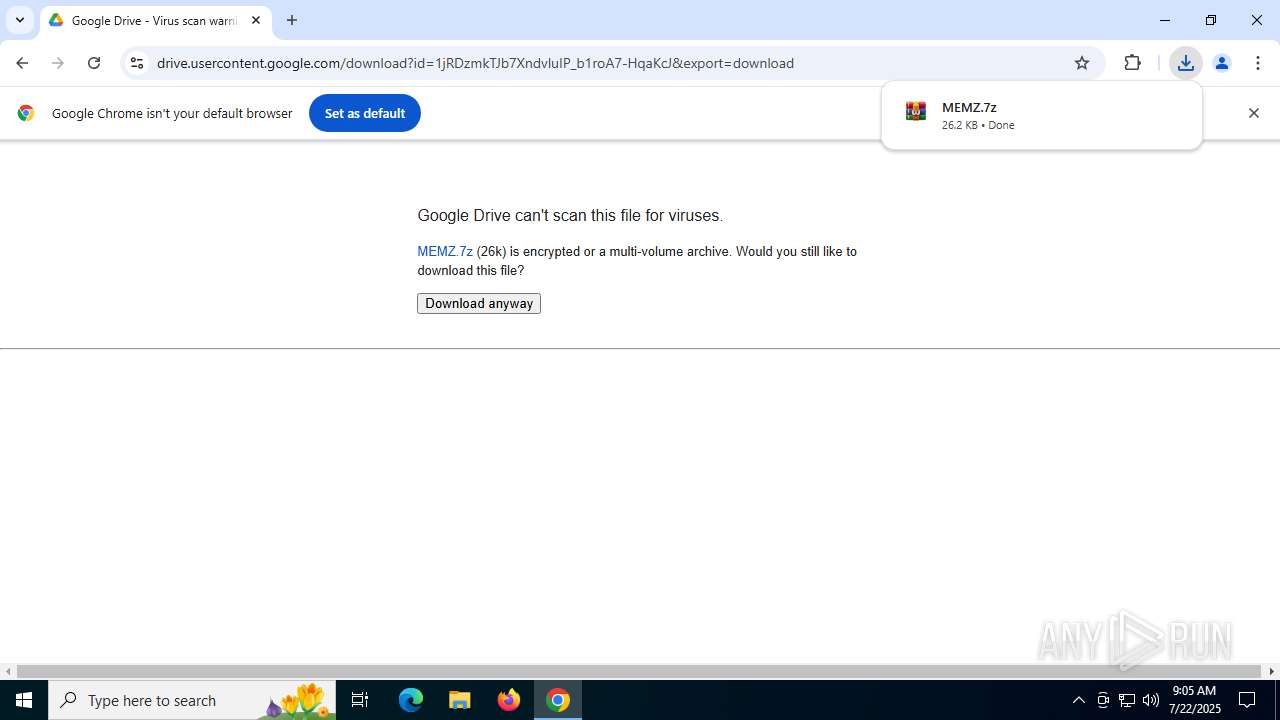
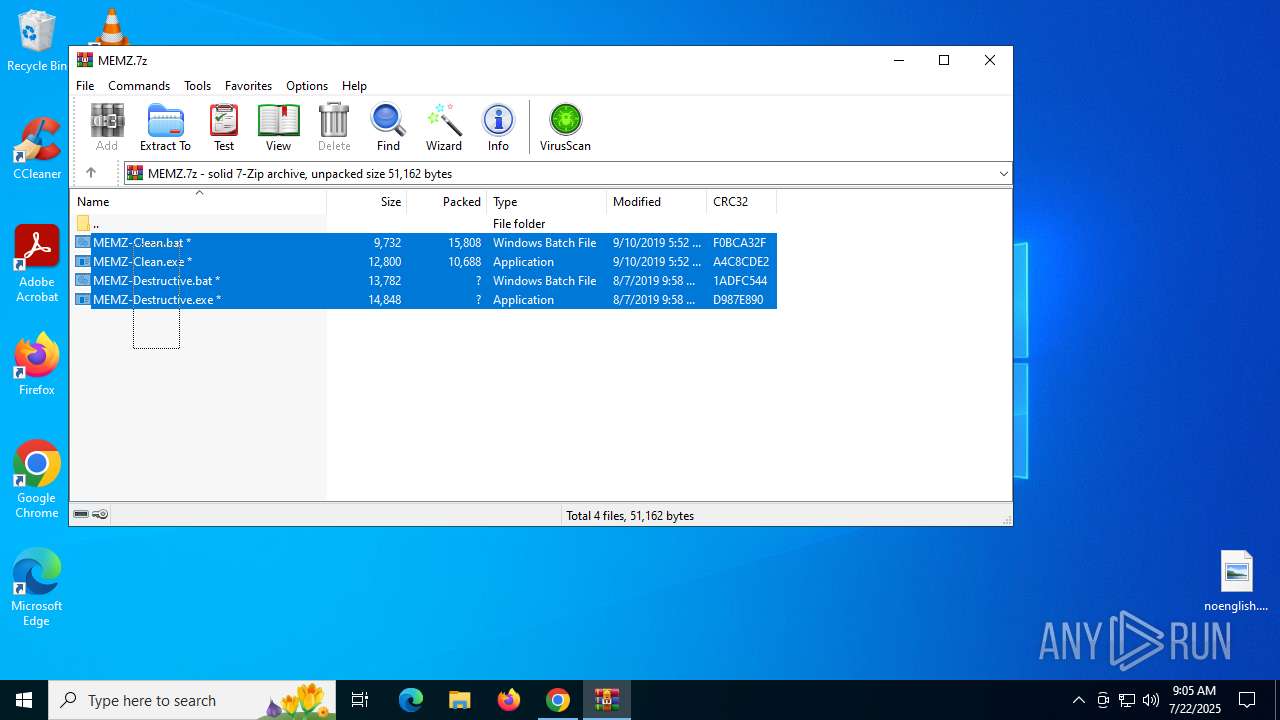
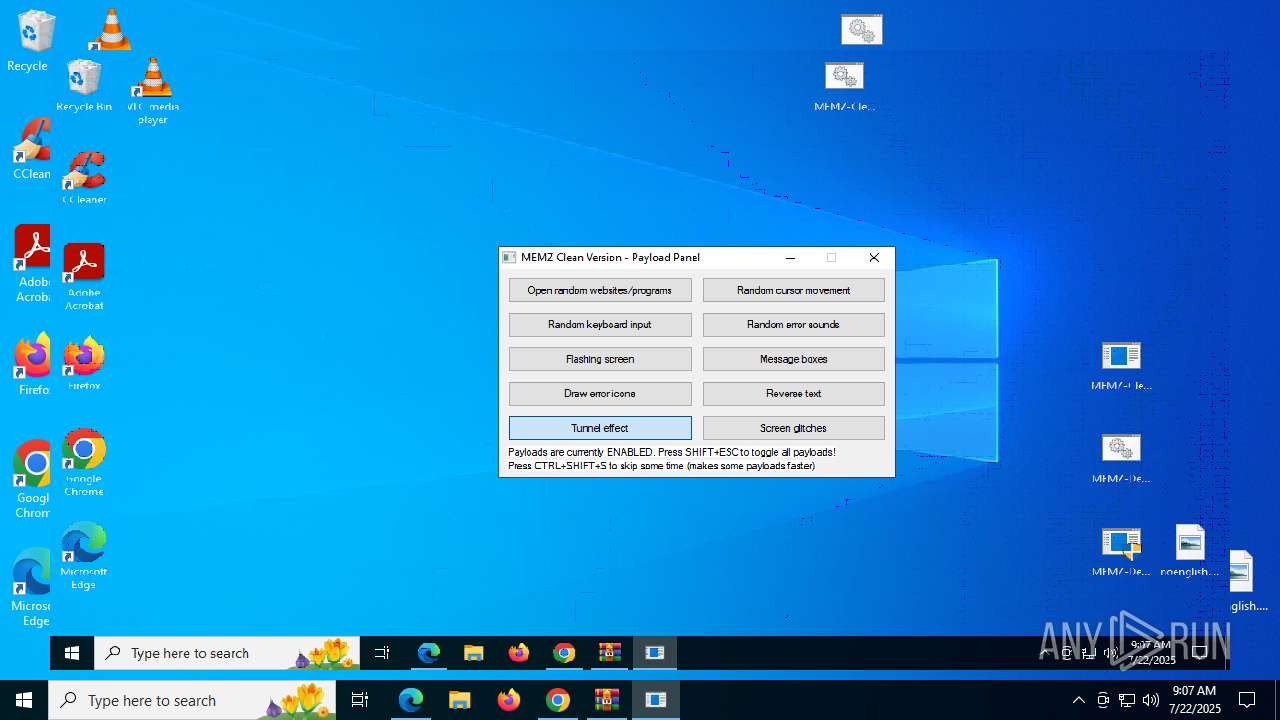
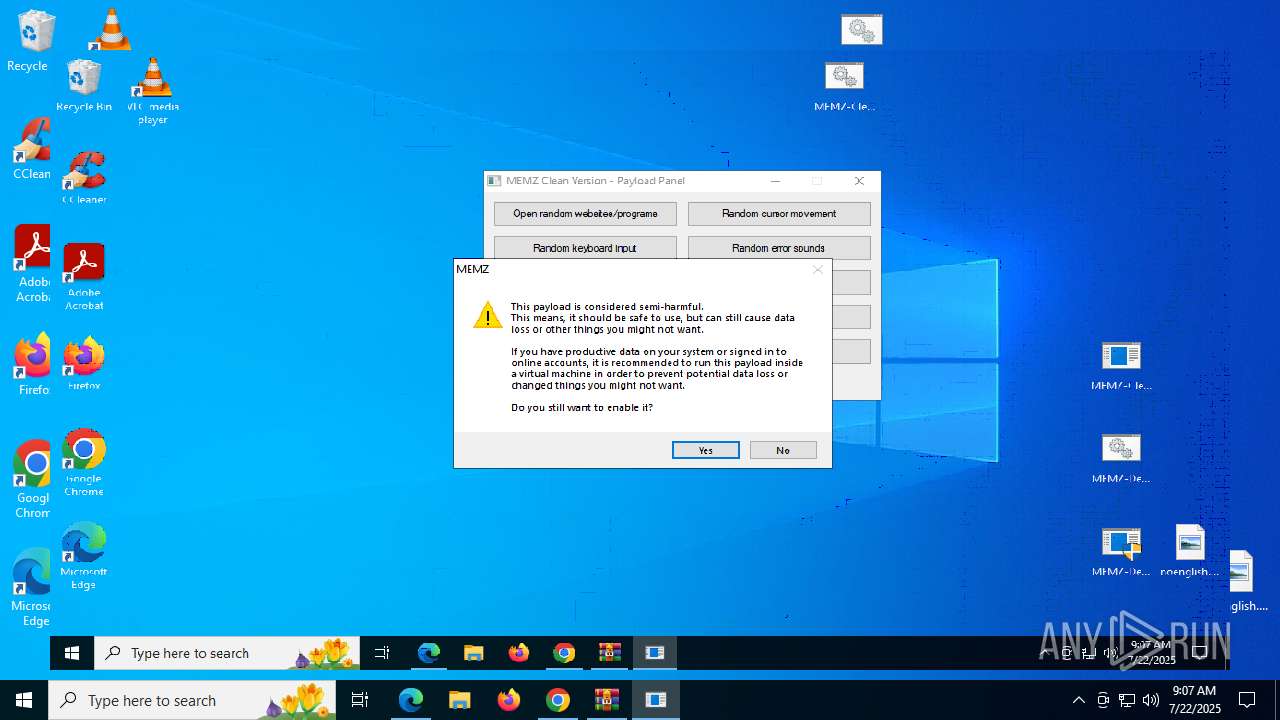
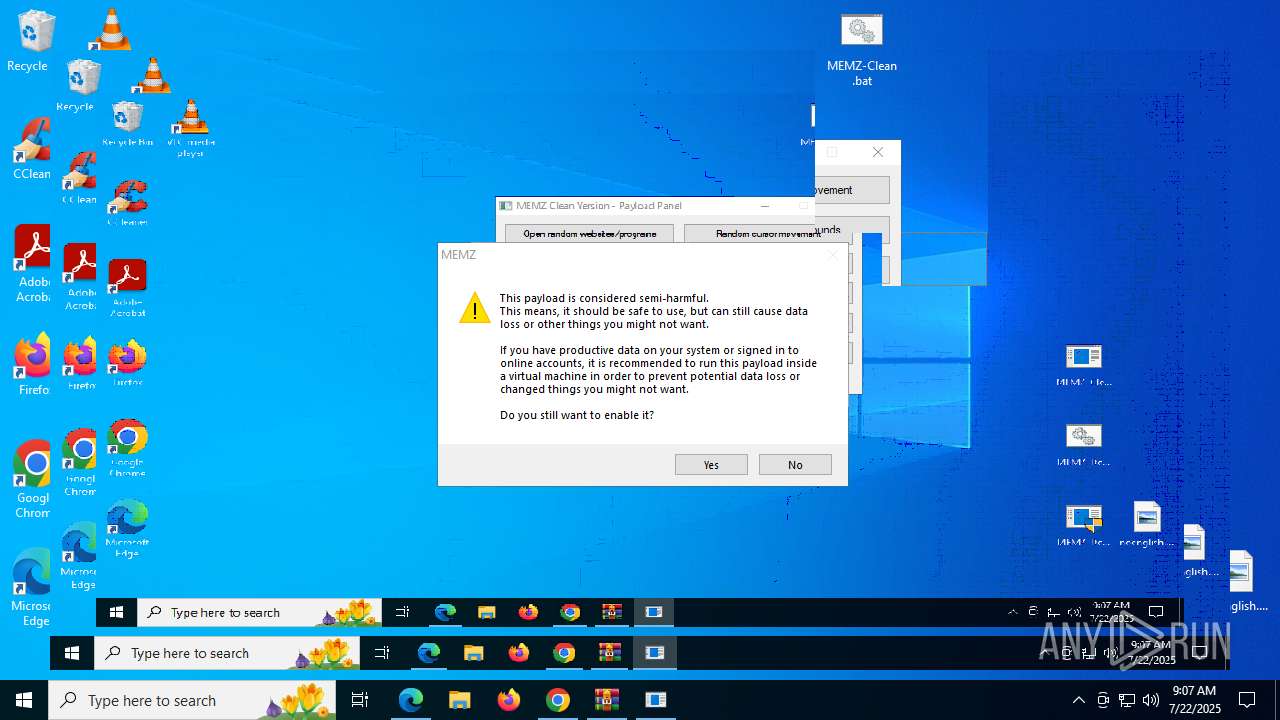
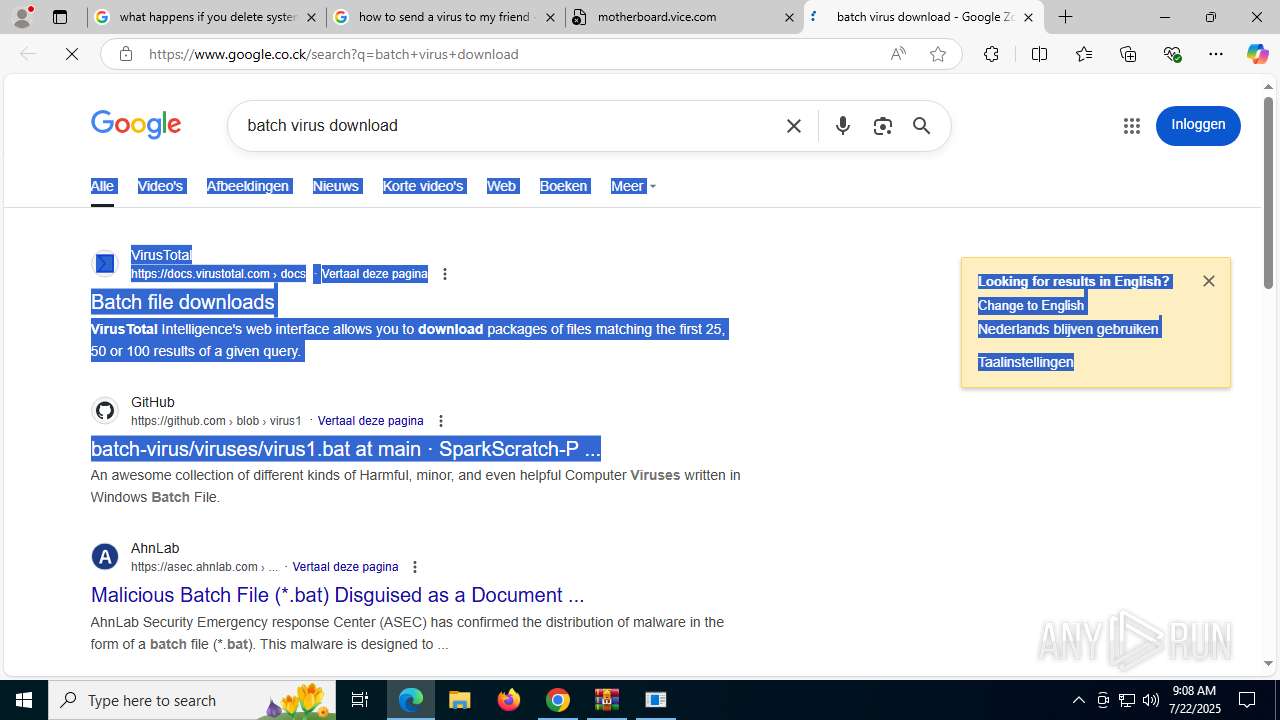
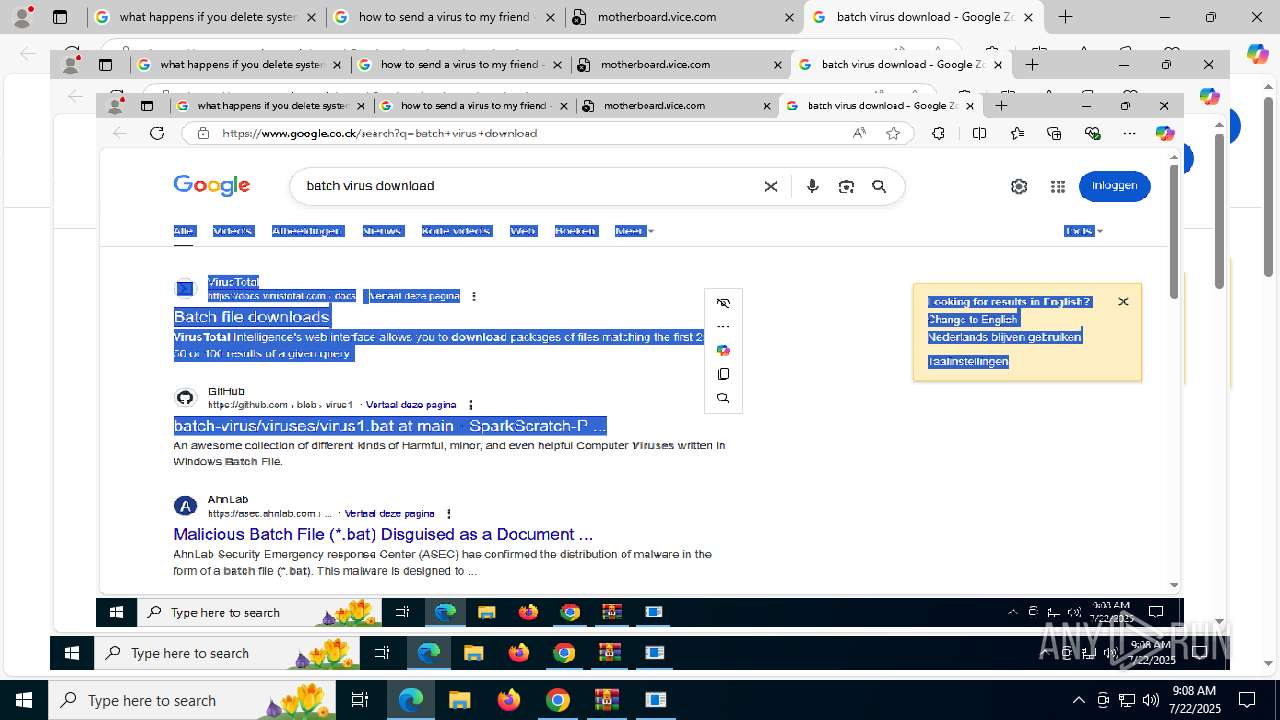
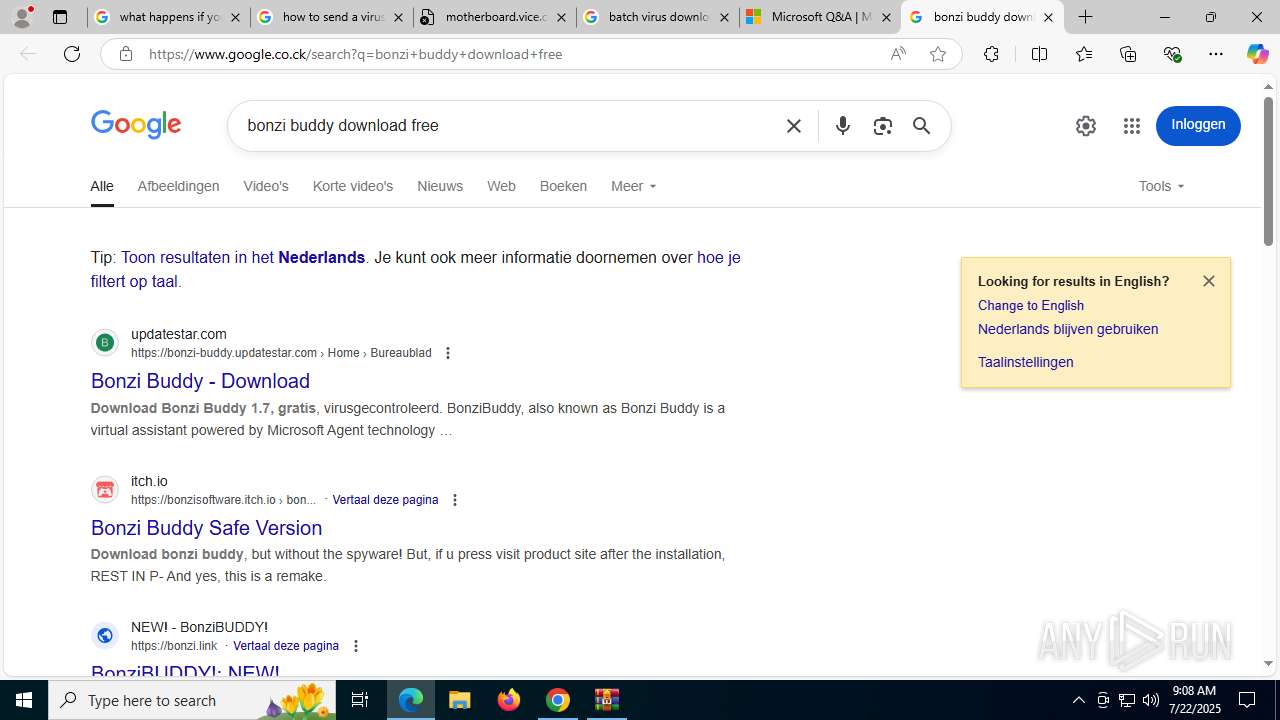
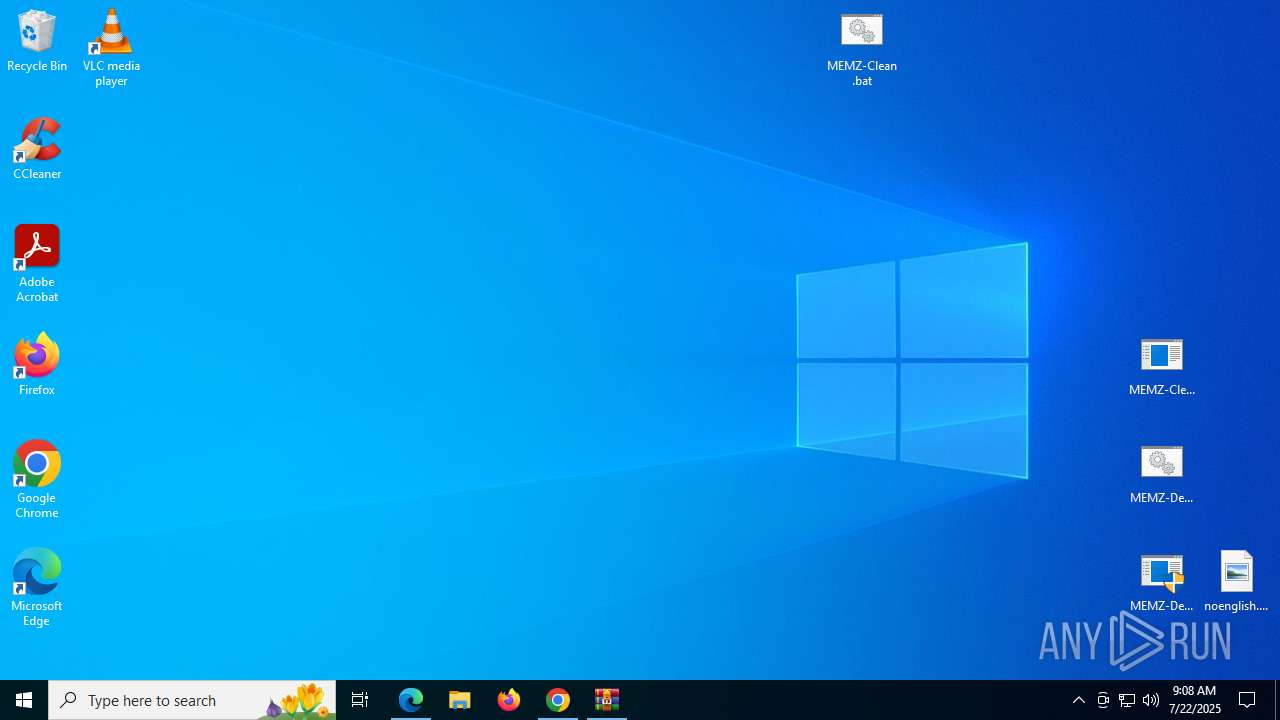
Manual execution by a user
- MEMZ-Destructive.exe (PID: 3588)
- MEMZ-Destructive.exe (PID: 4748)
- msedge.exe (PID: 3480)
- cmd.exe (PID: 7896)
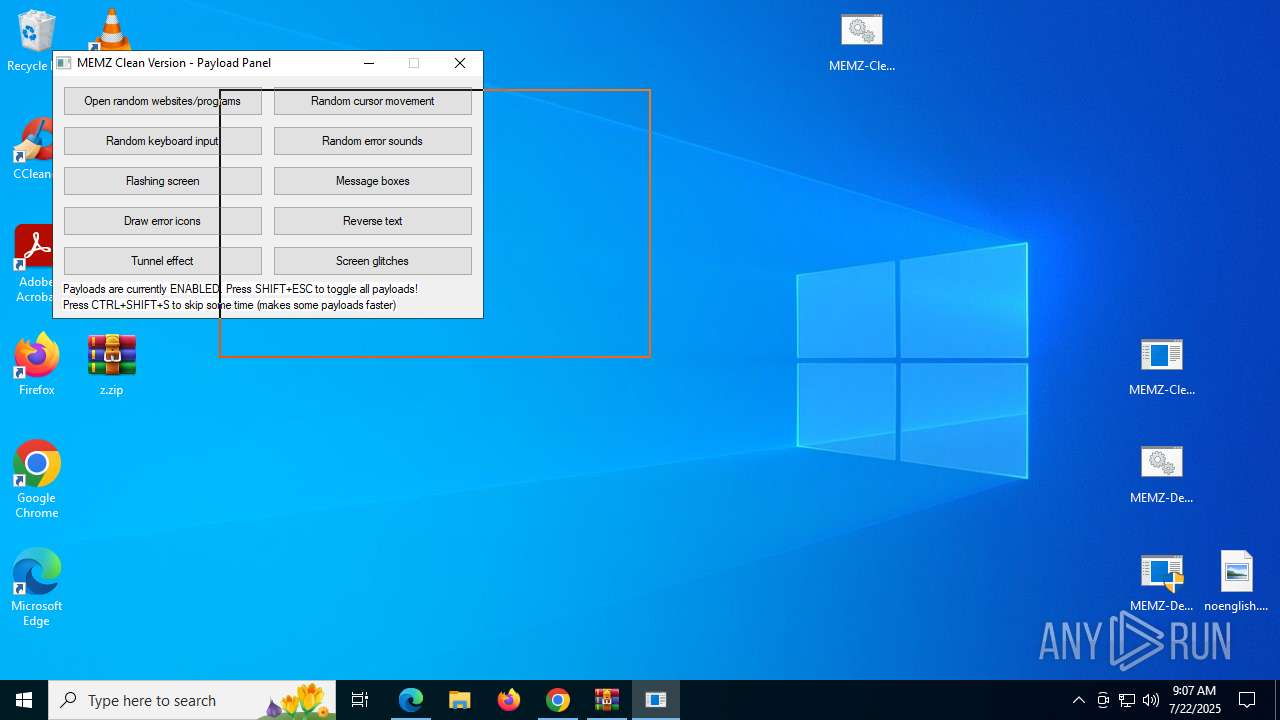
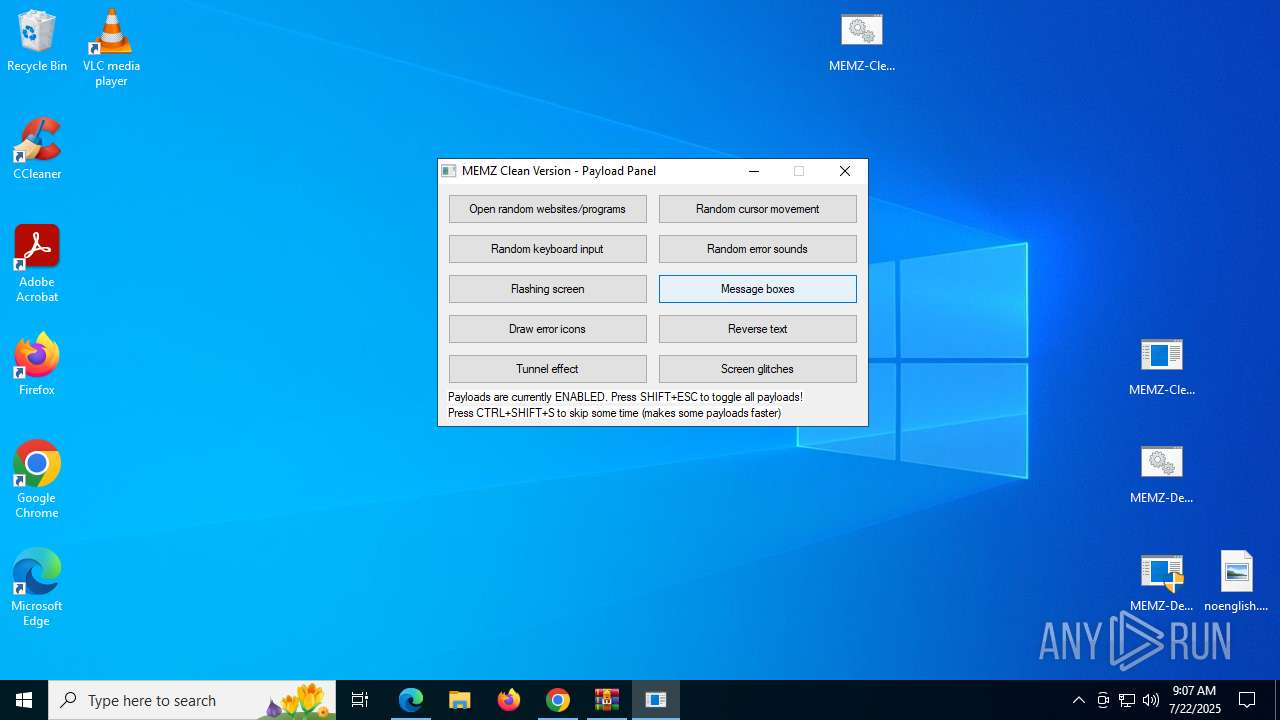
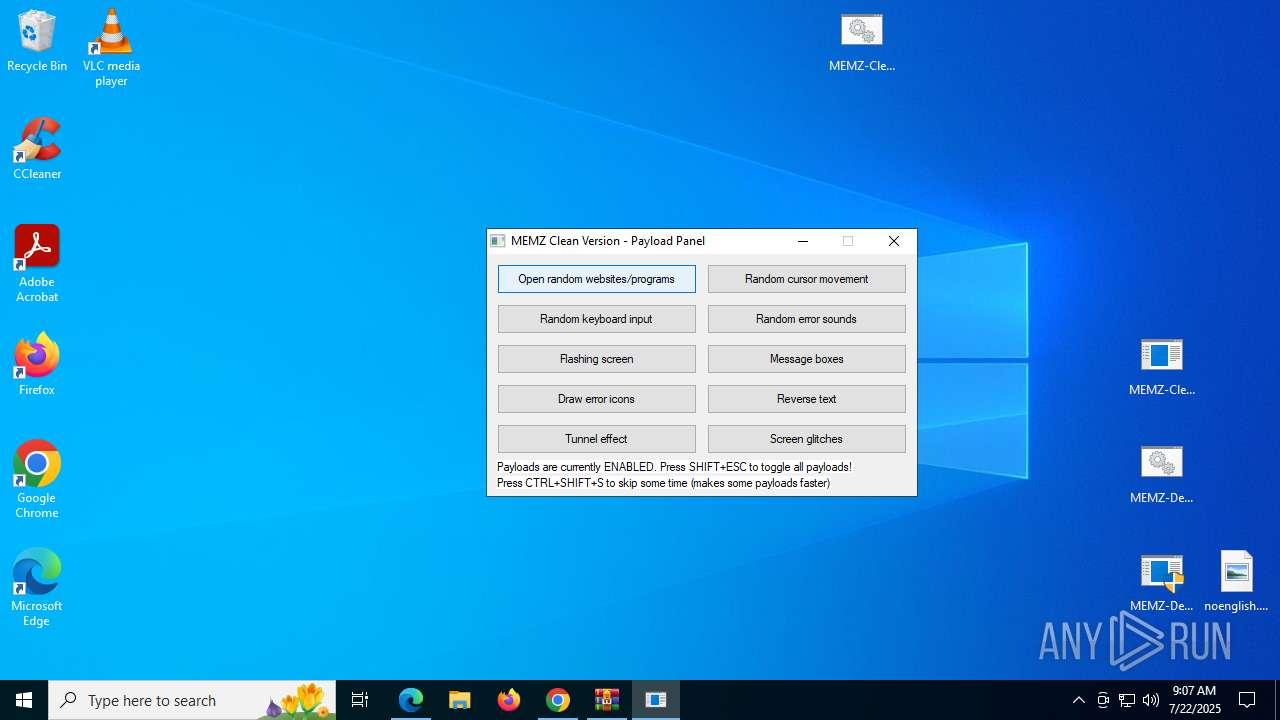
- MEMZ-Clean.exe (PID: 8940)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6664)
- chrome.exe (PID: 2972)
Process checks computer location settings
- MEMZ-Destructive.exe (PID: 4748)
- MEMZ-Destructive.exe (PID: 6488)
The sample compiled with english language support
- chrome.exe (PID: 2972)
Application launched itself
- chrome.exe (PID: 2972)
- msedge.exe (PID: 6288)
- msedge.exe (PID: 2212)
- msedge.exe (PID: 3480)
- msedge.exe (PID: 8136)
- msedge.exe (PID: 7824)
- msedge.exe (PID: 5296)
- msedge.exe (PID: 7768)
- msedge.exe (PID: 8404)
- msedge.exe (PID: 8096)
- msedge.exe (PID: 8788)
- msedge.exe (PID: 9076)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7104)
- cscript.exe (PID: 7960)
Reads the software policy settings
- slui.exe (PID: 6292)
Reads the machine GUID from the registry
- MEMZ-Destructive.exe (PID: 6488)
- MEMZ.exe (PID: 8032)
- MEMZ-Clean.exe (PID: 8940)
Reads Environment values
- identity_helper.exe (PID: 7676)
Creates files or folders in the user directory
- cscript.exe (PID: 7960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
276
Monitored processes
122
Malicious processes
9
Suspicious processes
1
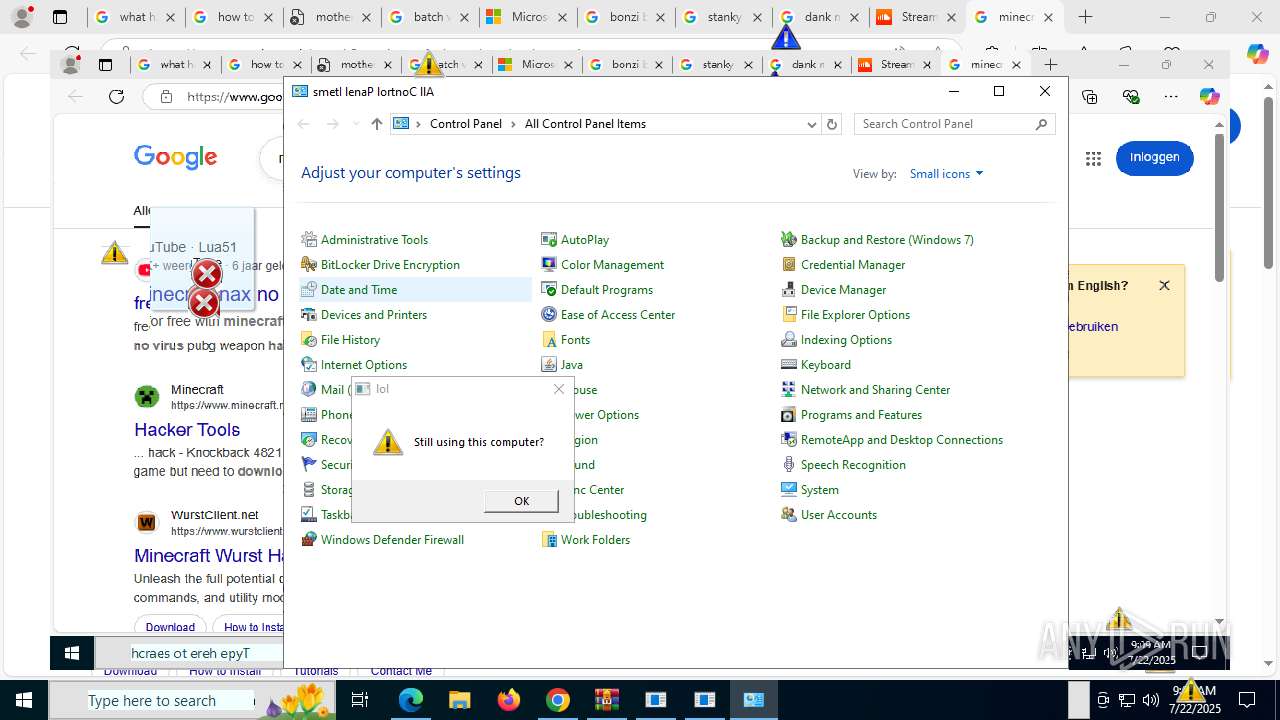
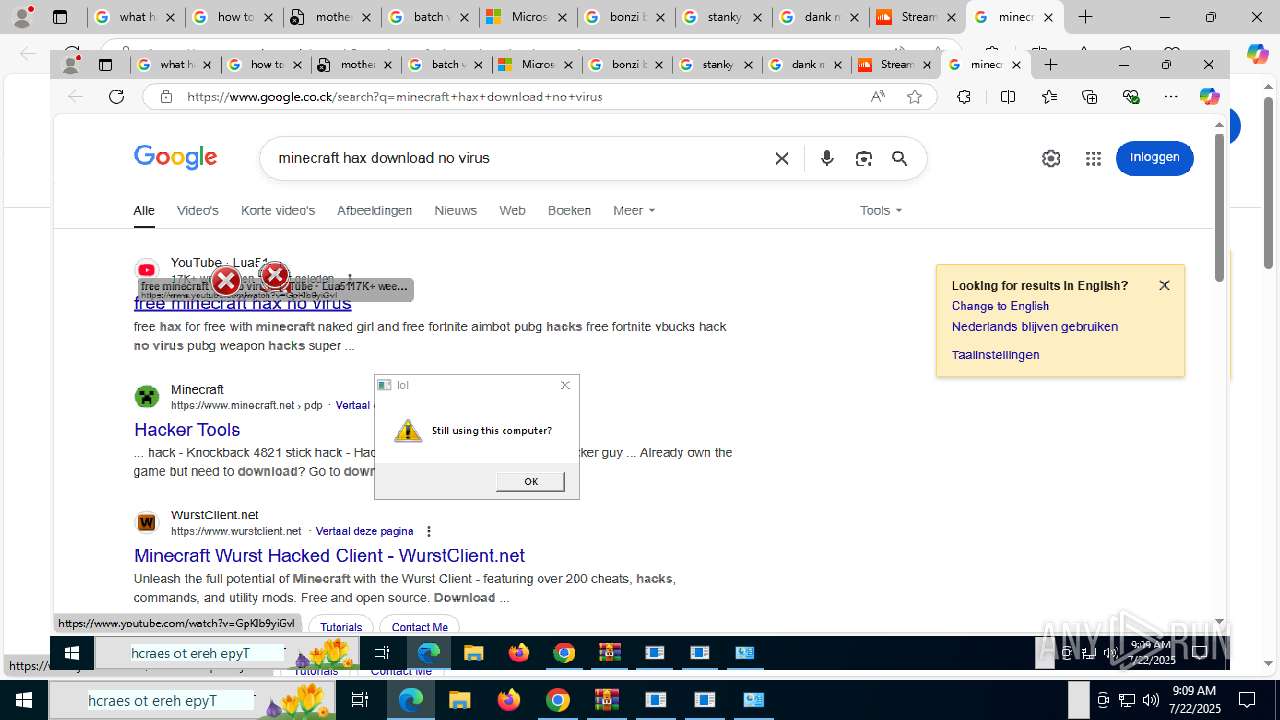
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2688,i,10241003419976248511,11512609533040558404,262144 --variations-seed-version --mojo-platform-channel-handle=2724 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=3468,i,12844266587819180192,17809698020104242445,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4896 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2384,i,10241003419976248511,11512609533040558404,262144 --variations-seed-version --mojo-platform-channel-handle=2376 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6232,i,10241003419976248511,11512609533040558404,262144 --variations-seed-version --mojo-platform-channel-handle=6720 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5104,i,12844266587819180192,17809698020104242445,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --always-read-main-dll --field-trial-handle=6868,i,10241003419976248511,11512609533040558404,262144 --variations-seed-version --mojo-platform-channel-handle=6916 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=38 --always-read-main-dll --field-trial-handle=7996,i,10241003419976248511,11512609533040558404,262144 --variations-seed-version --mojo-platform-channel-handle=7576 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --field-trial-handle=5744,i,12844266587819180192,17809698020104242445,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1440 | "C:\Users\admin\Desktop\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\Desktop\MEMZ-Destructive.exe | MEMZ-Destructive.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1704 | "C:\Users\admin\Desktop\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\Desktop\MEMZ-Destructive.exe | MEMZ-Destructive.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
24 178
Read events
23 994
Write events
176
Delete events
8
Modification events
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3732) NRVP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3732) NRVP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3732) NRVP.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
7
Suspicious files
796
Text files
107
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d750.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18d750.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18d760.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF18d76f.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18d76f.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
318
DNS requests
404
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7916 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7512 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753357322&P2=404&P3=2&P4=H47JzYJe9GnMDHDIA2Y9BD2CKxcnEkkaObRWL%2bLHfa7%2bT7I%2fjyi%2bQqt9mzvCvuaprdlf7M3eD8ydDM20Bo%2fANg%3d%3d | unknown | — | — | whitelisted |
7512 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1753360924&P2=404&P3=2&P4=JPaTxIuT2ltpcXSo45ZJLCAH3K8qDQmn6jt1E5krrQEFfjS44Zu6nlsPxZACWvASQR1xLn9wEUqOIUzPEOOCaw%3d%3d | unknown | — | — | whitelisted |
7512 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753357322&P2=404&P3=2&P4=H47JzYJe9GnMDHDIA2Y9BD2CKxcnEkkaObRWL%2bLHfa7%2bT7I%2fjyi%2bQqt9mzvCvuaprdlf7M3eD8ydDM20Bo%2fANg%3d%3d | unknown | — | — | whitelisted |
3656 | chrome.exe | GET | 200 | 172.217.18.14:80 | http://clients2.google.com/time/1/current?cup2key=8:xWcFmi2TY9N9DNmG232fEAMhMGcIc9iJjLp5Qag6RZs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1872 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
828 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3656 | chrome.exe | 142.250.186.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
3656 | chrome.exe | 172.217.18.14:80 | clients2.google.com | GOOGLE | US | whitelisted |
3656 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
3656 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3656 | chrome.exe | 185.199.109.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
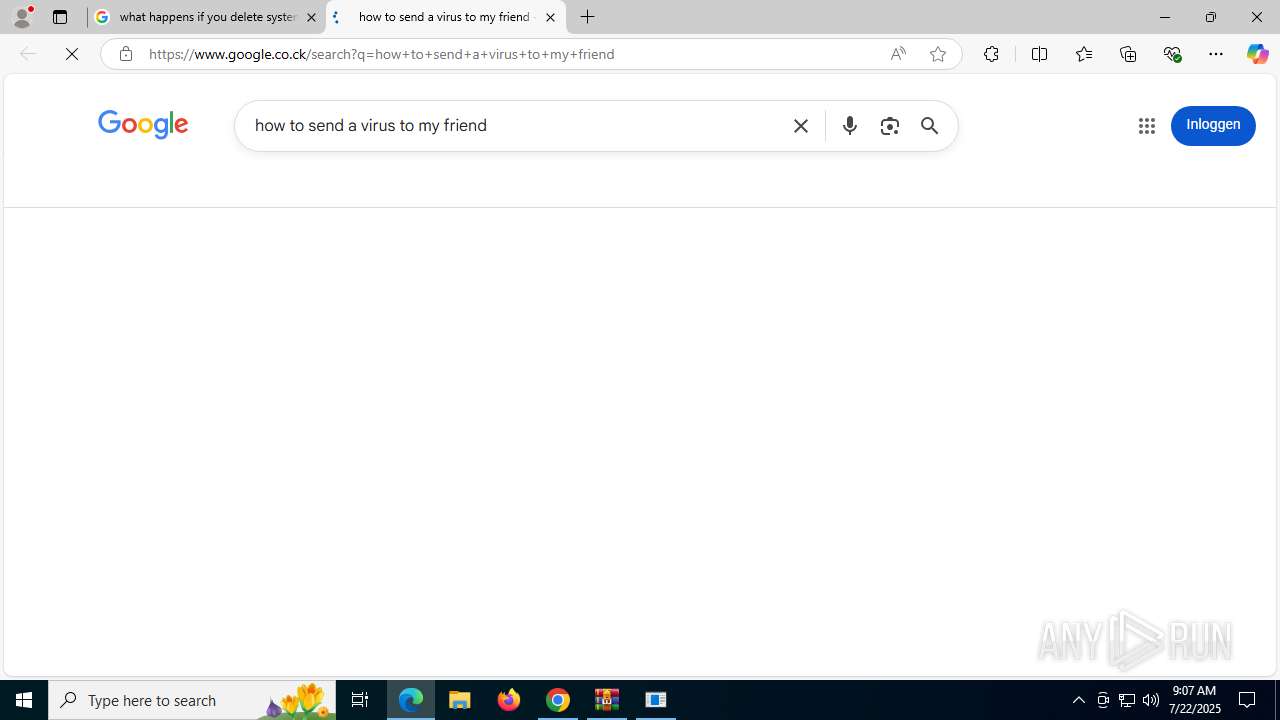
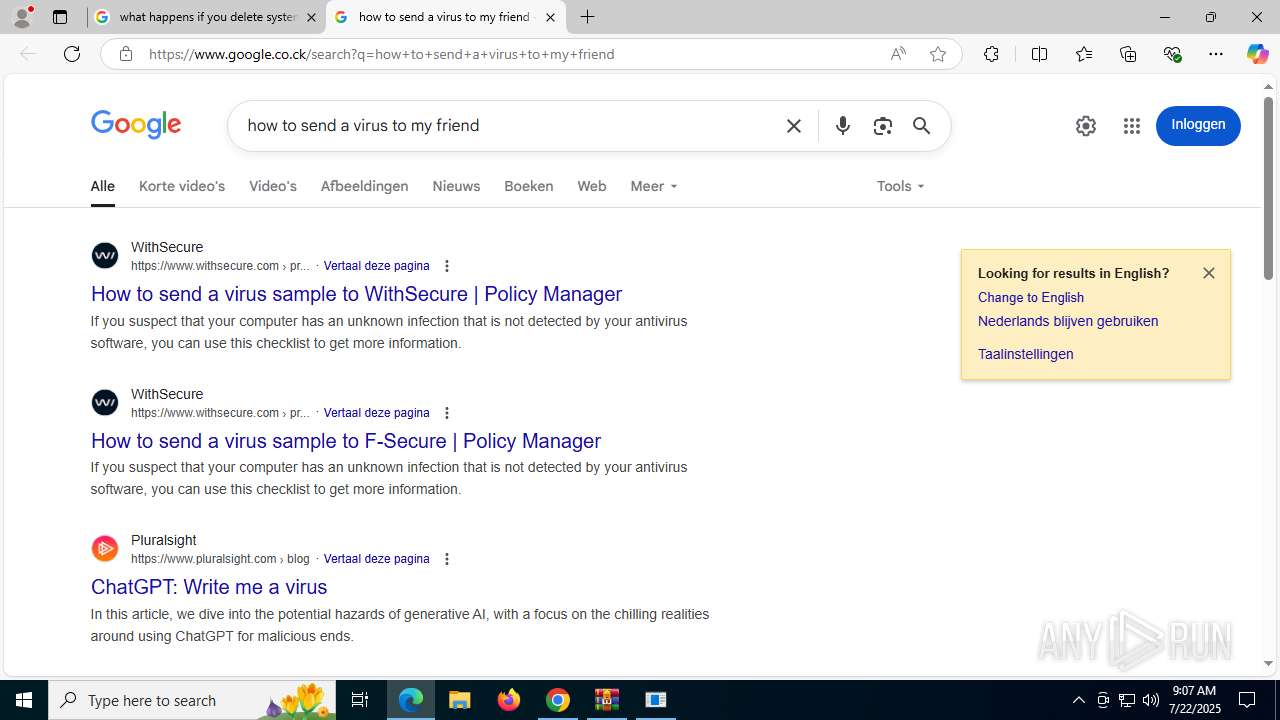
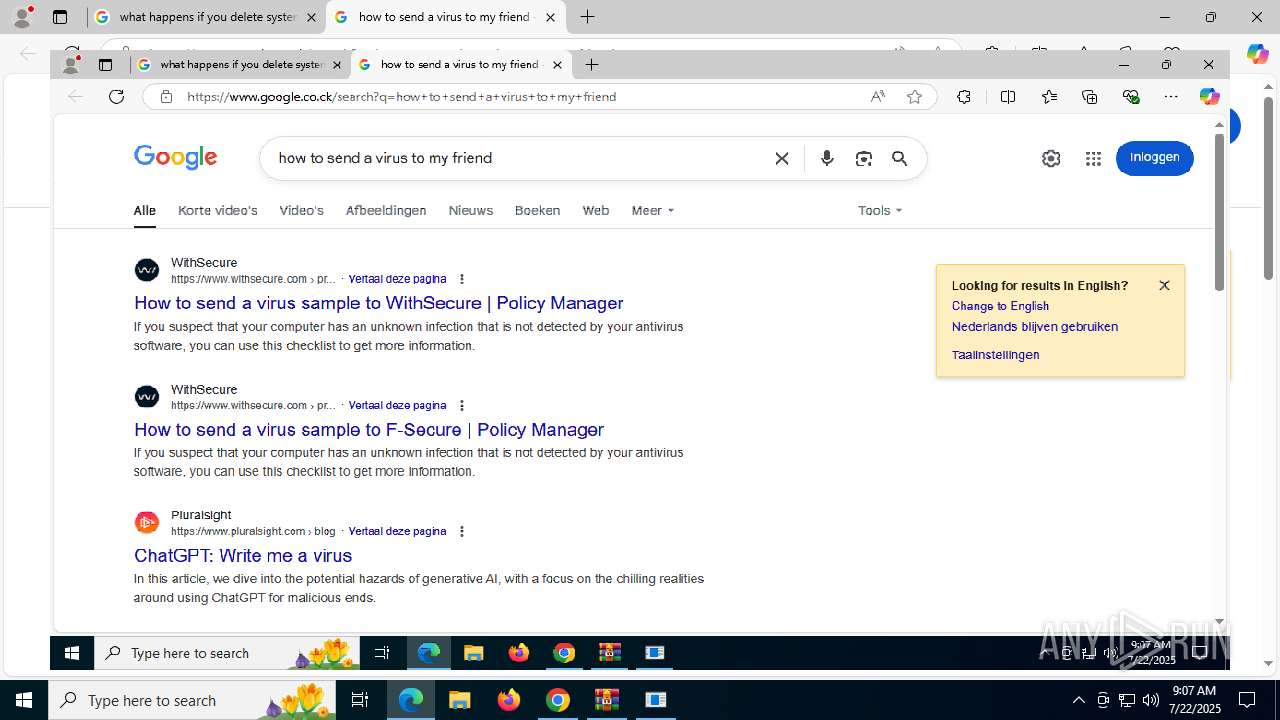
3656 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3656 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3656 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (tiny .cc) |
3656 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (tiny .cc) |
3656 | chrome.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (tiny .cc) |
3656 | chrome.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (tiny .cc) |