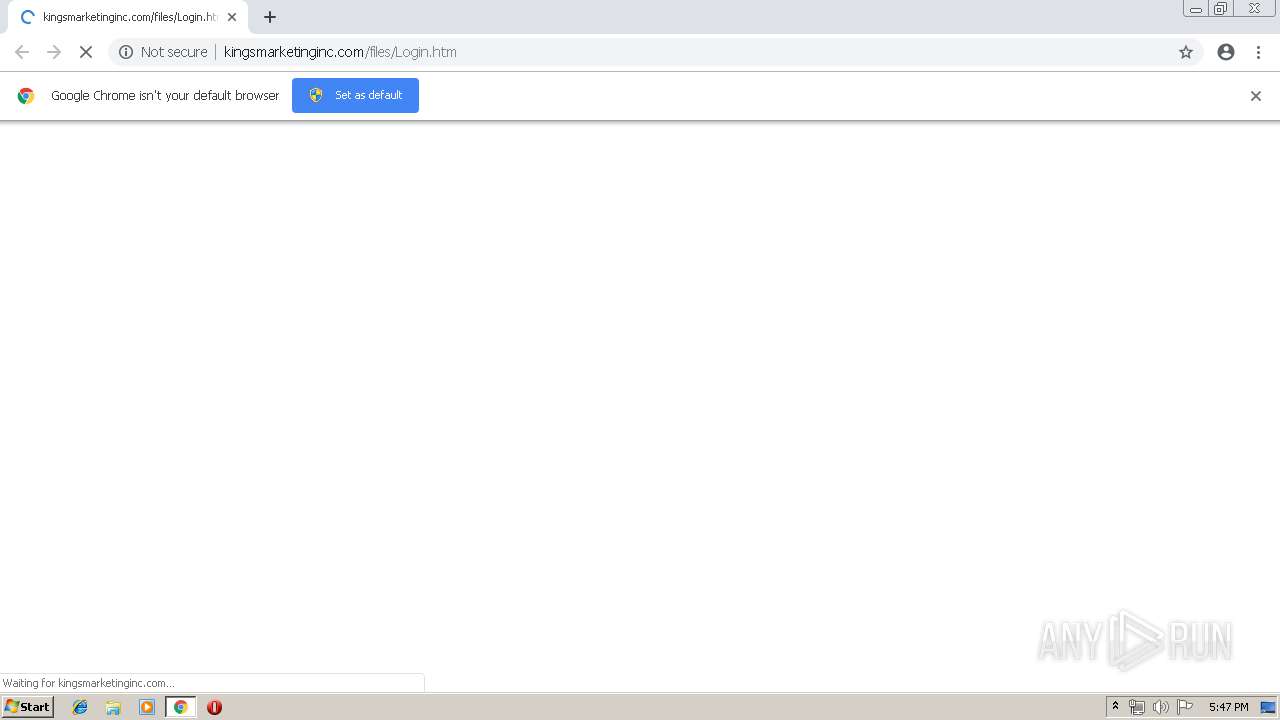
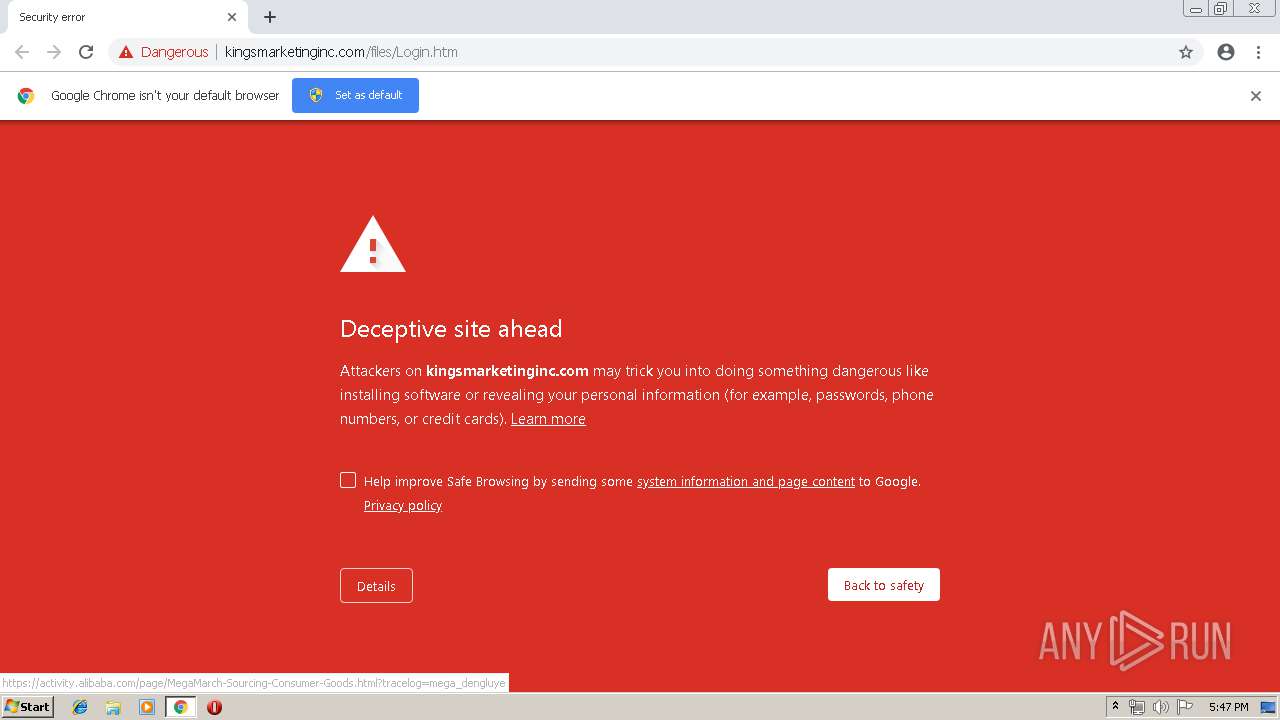
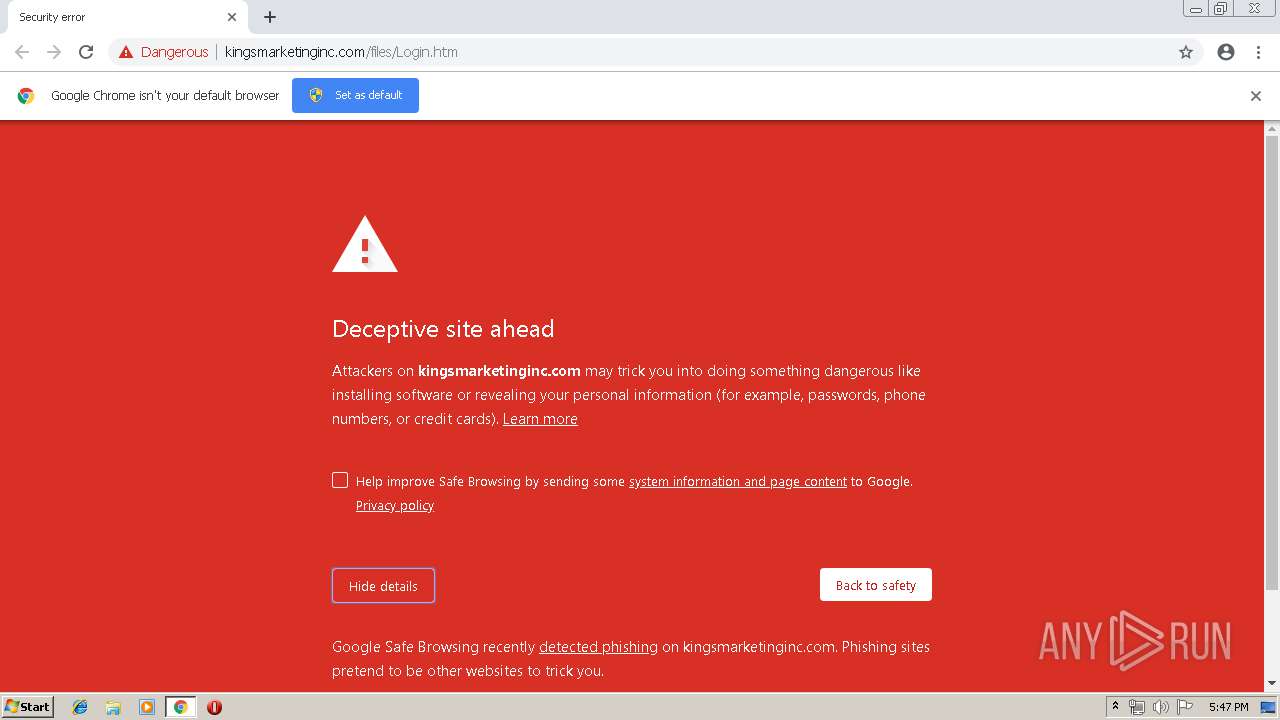
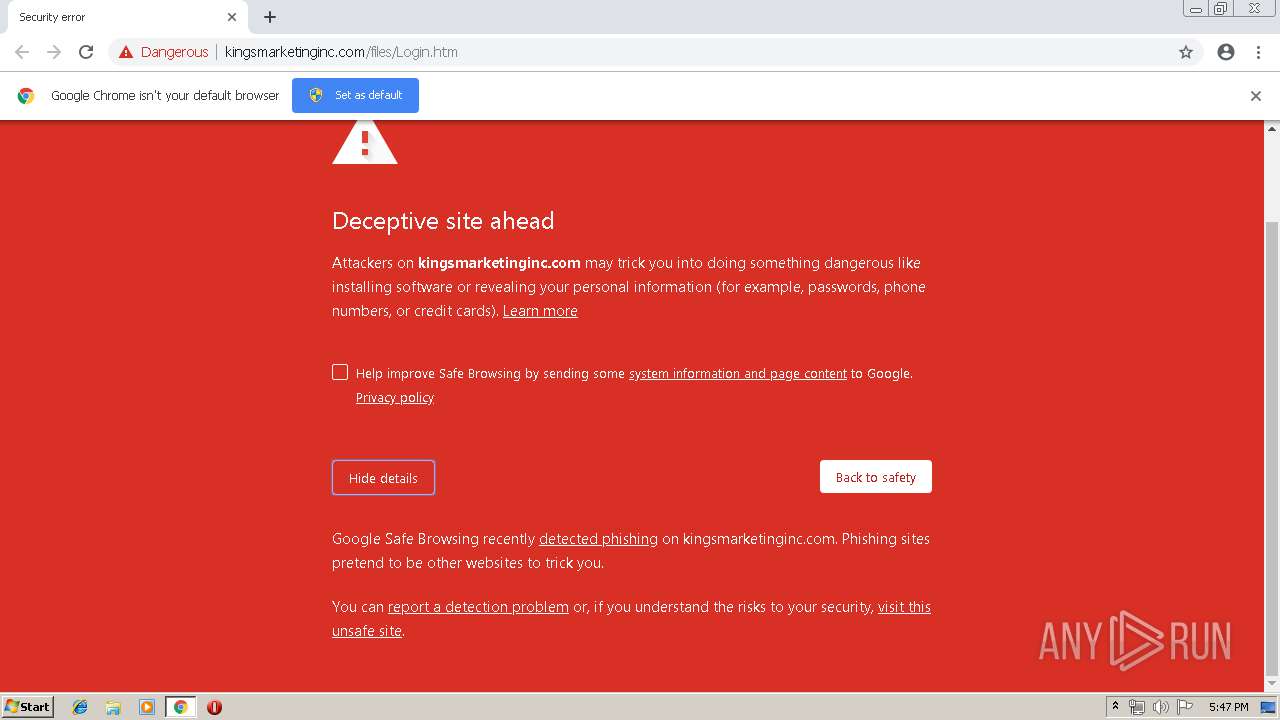
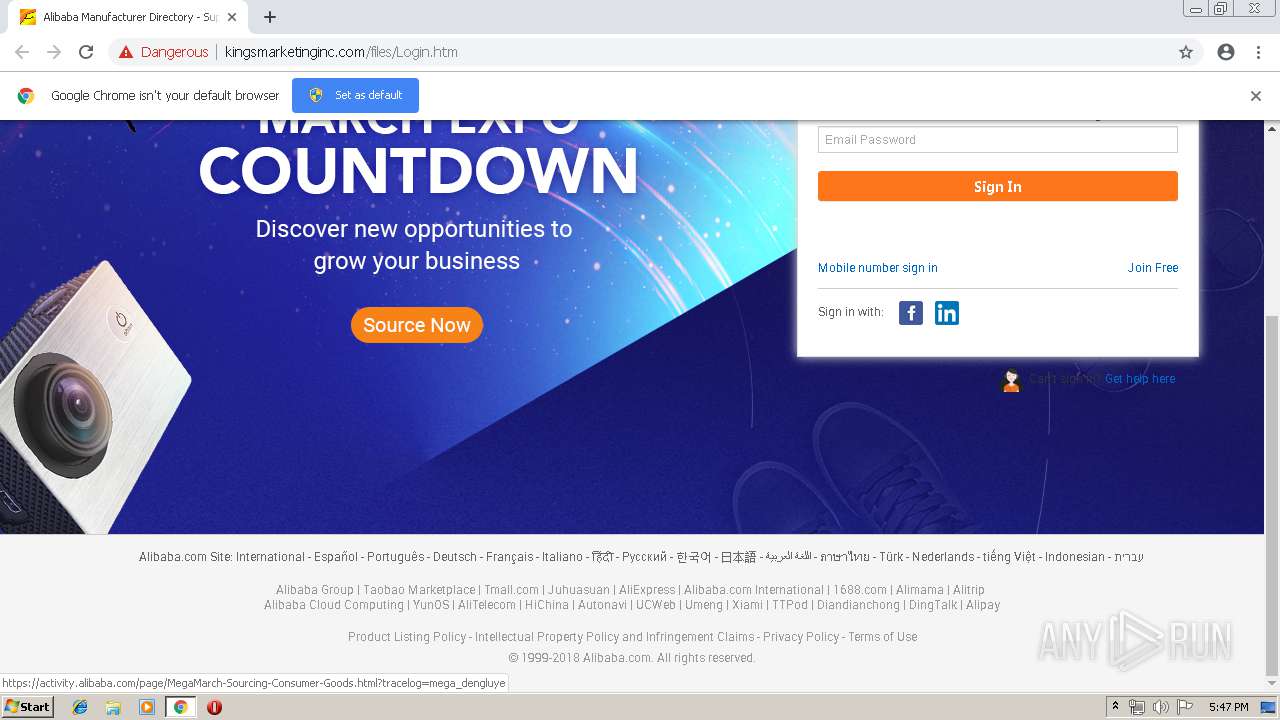
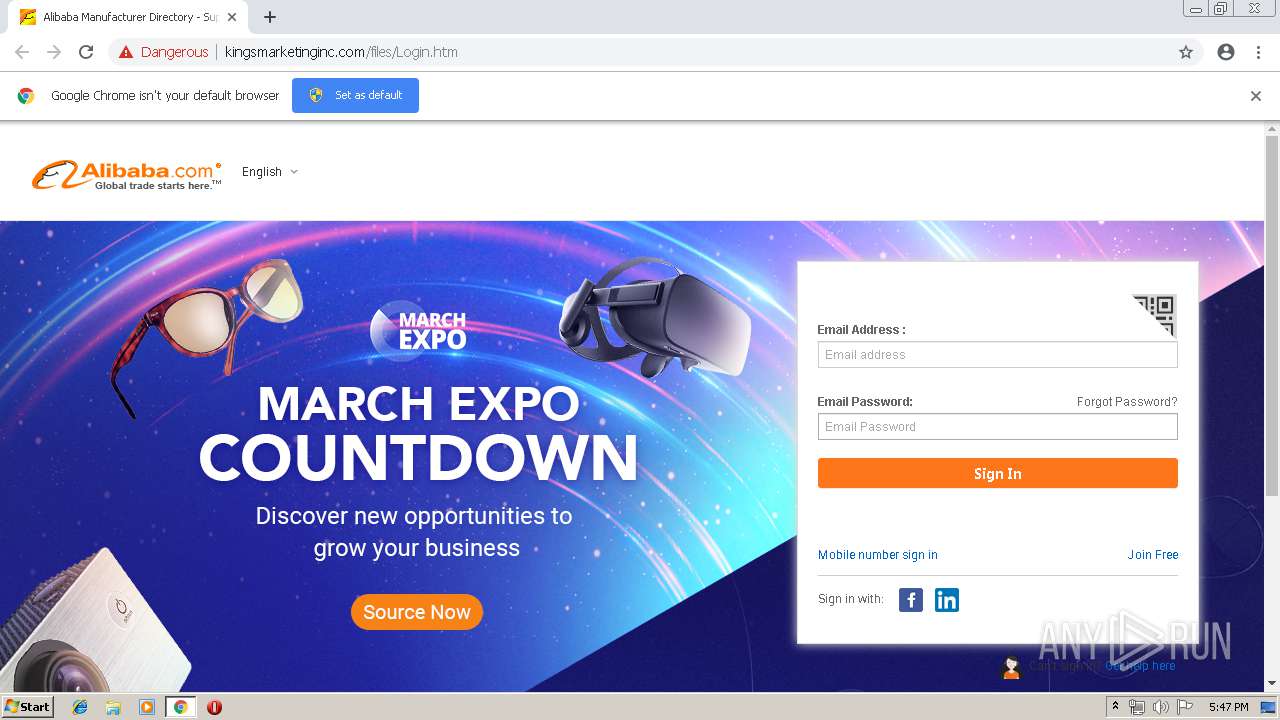
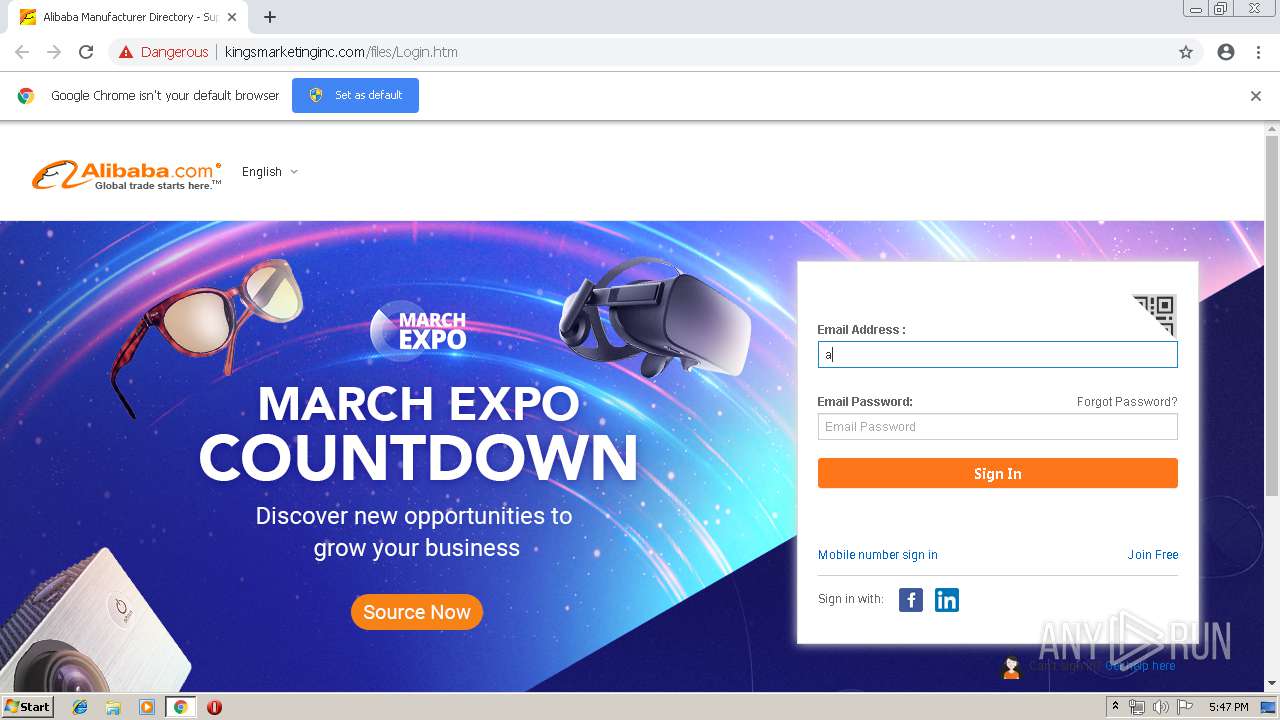
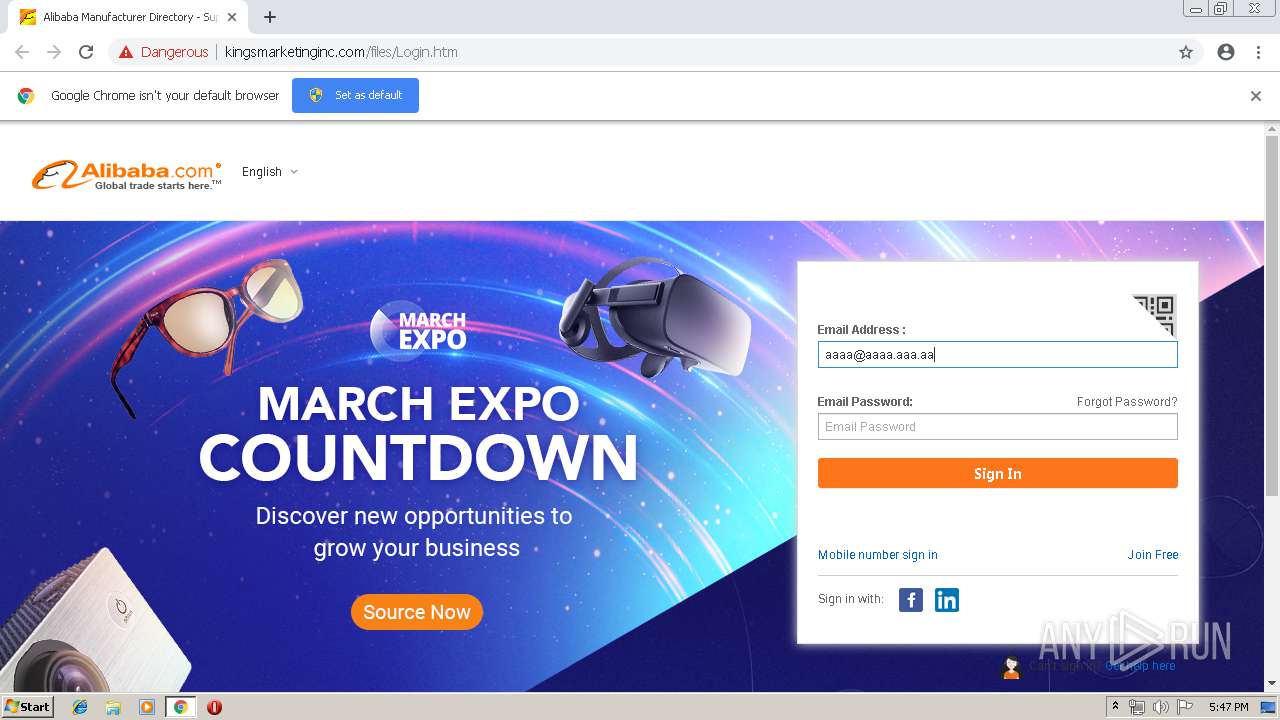
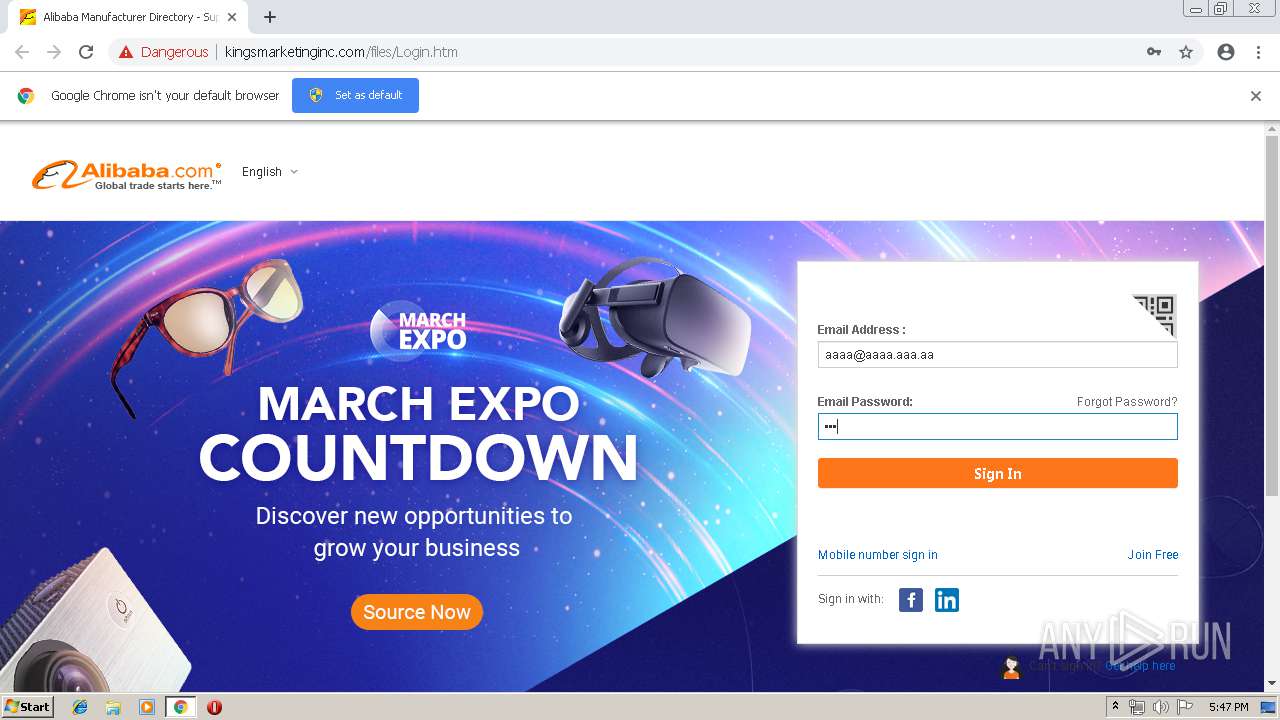
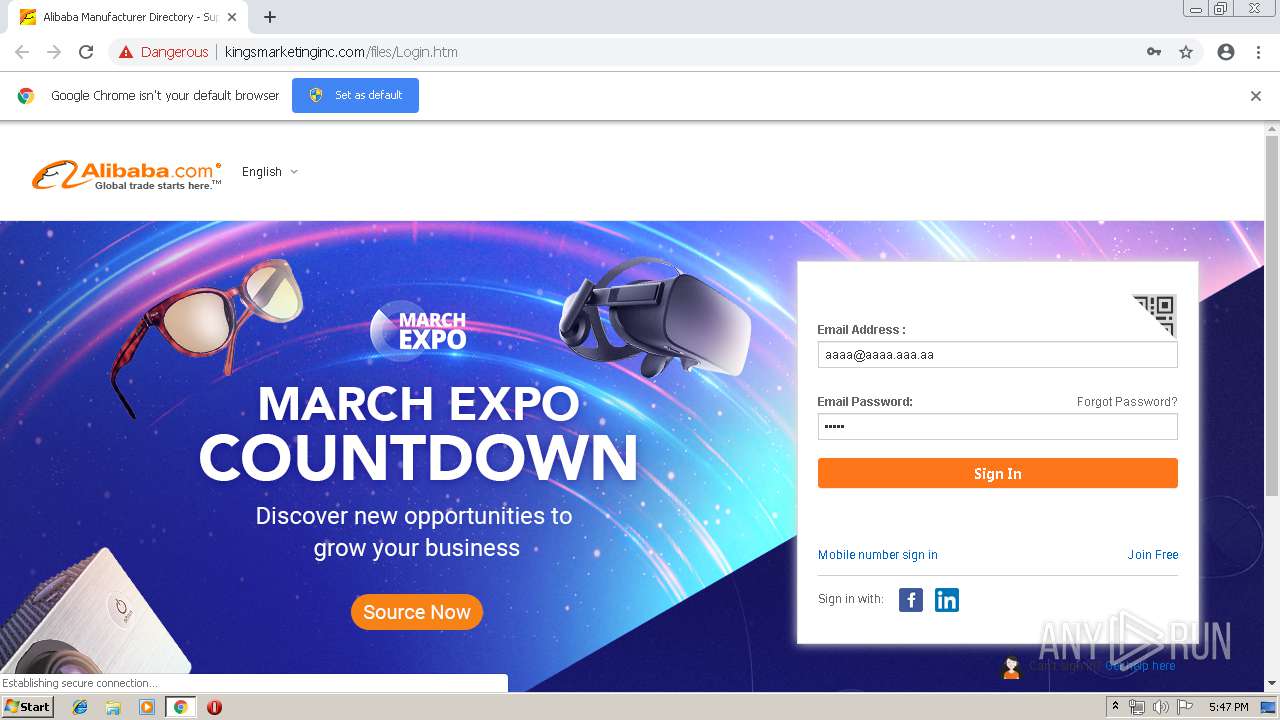
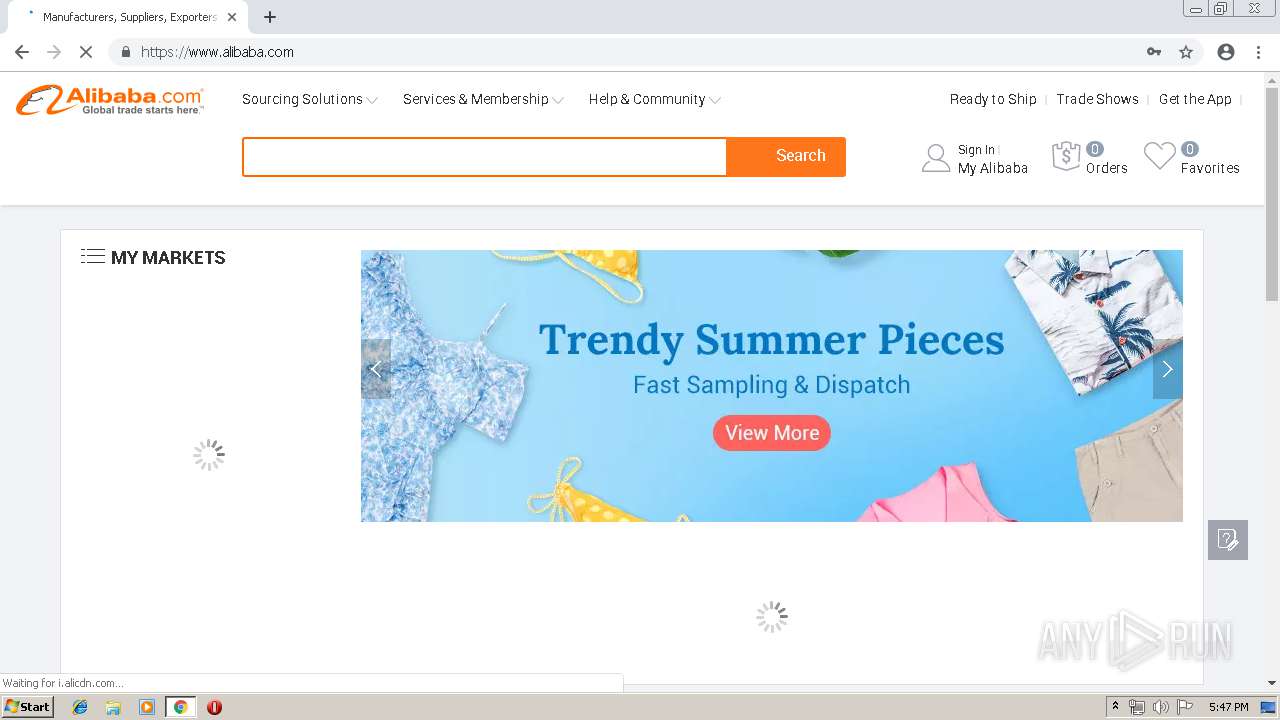
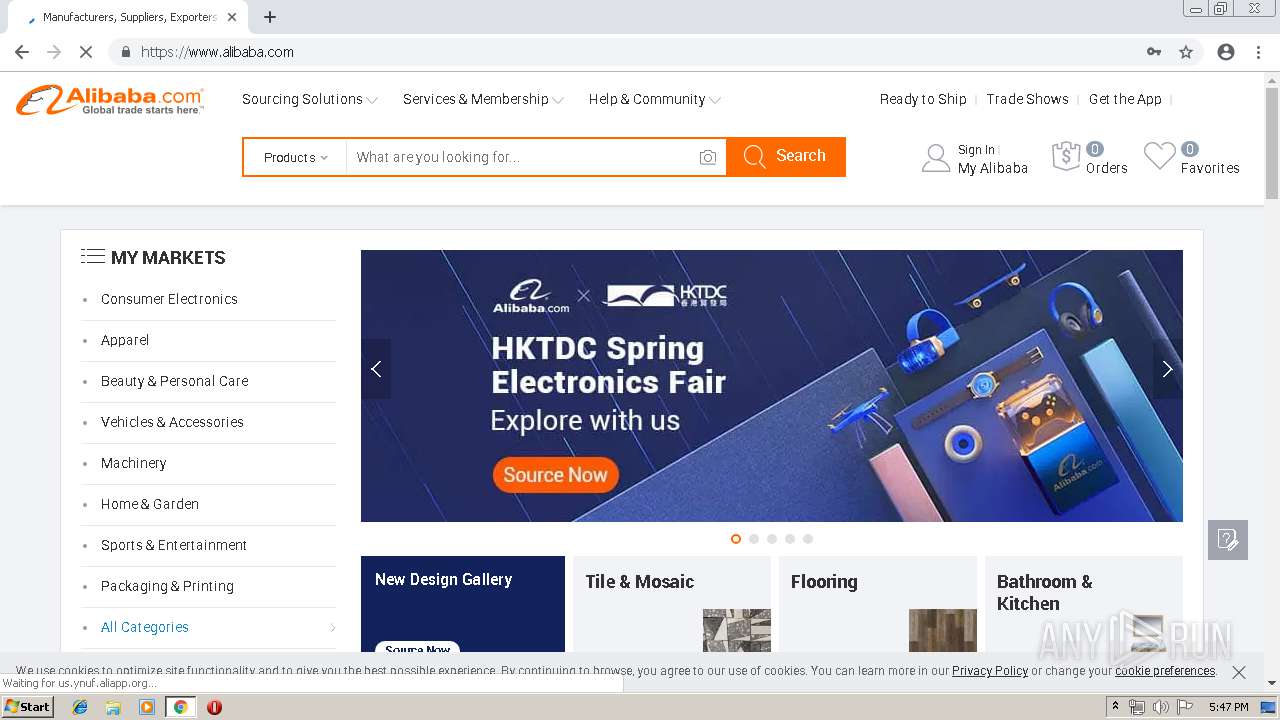
| URL: | http://kingsmarketinginc.com/files/Login.htm |
| Full analysis: | https://app.any.run/tasks/b5541568-880f-4b8b-a4a2-244712760ed7 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 16:46:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7D16546FAC51575F5D9EC2180026EAFA |
| SHA1: | DF59732BDFEB32B09A780214A9F485FB25FC3F8B |
| SHA256: | 9F2B6A5C83B824F6AE9F66AA2D2243D688DB623BE645B1270C492E76BBF7C66C |
| SSDEEP: | 3:N1KVMDJKCMLcOKkPrI:CmmNrI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2668)
INFO
Application launched itself
- chrome.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3107490494145967417 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11435179244490678824 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11435179244490678824 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6311025506232558313 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6311025506232558313 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=262009904494995069 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --service-pipe-token=7811494552140373710 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7811494552140373710 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13038927298797946973 --mojo-platform-channel-handle=2716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14585021511065589160 --mojo-platform-channel-handle=1480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa60f18,0x6fa60f28,0x6fa60f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4501675509431005086 --mojo-platform-channel-handle=3520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://kingsmarketinginc.com/files/Login.htm | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
590
Read events
490
Write events
95
Delete events
5
Modification events
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2668-13199734022318875 |
Value: 259 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2668-13199734022318875 |
Value: 259 | |||
Executable files
0
Suspicious files
106
Text files
141
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f8d65f94-9459-4954-b1dc-1e2e90f627da.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
61
DNS requests
124
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
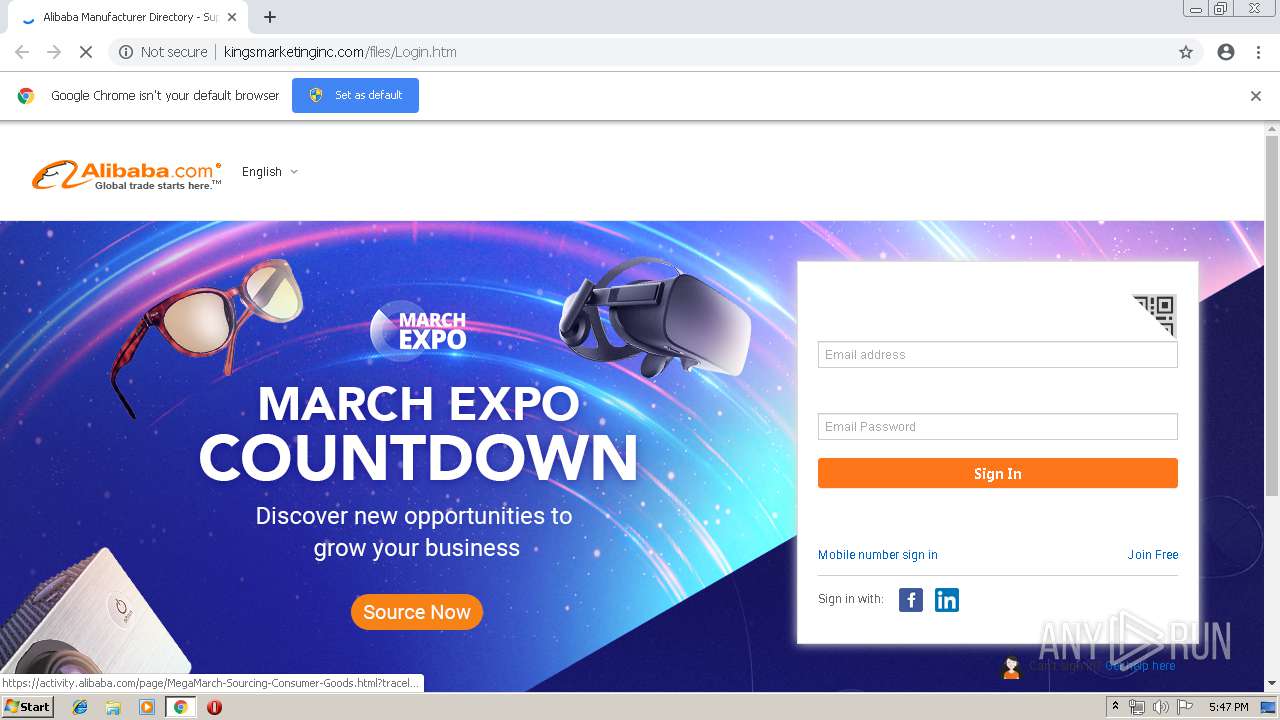
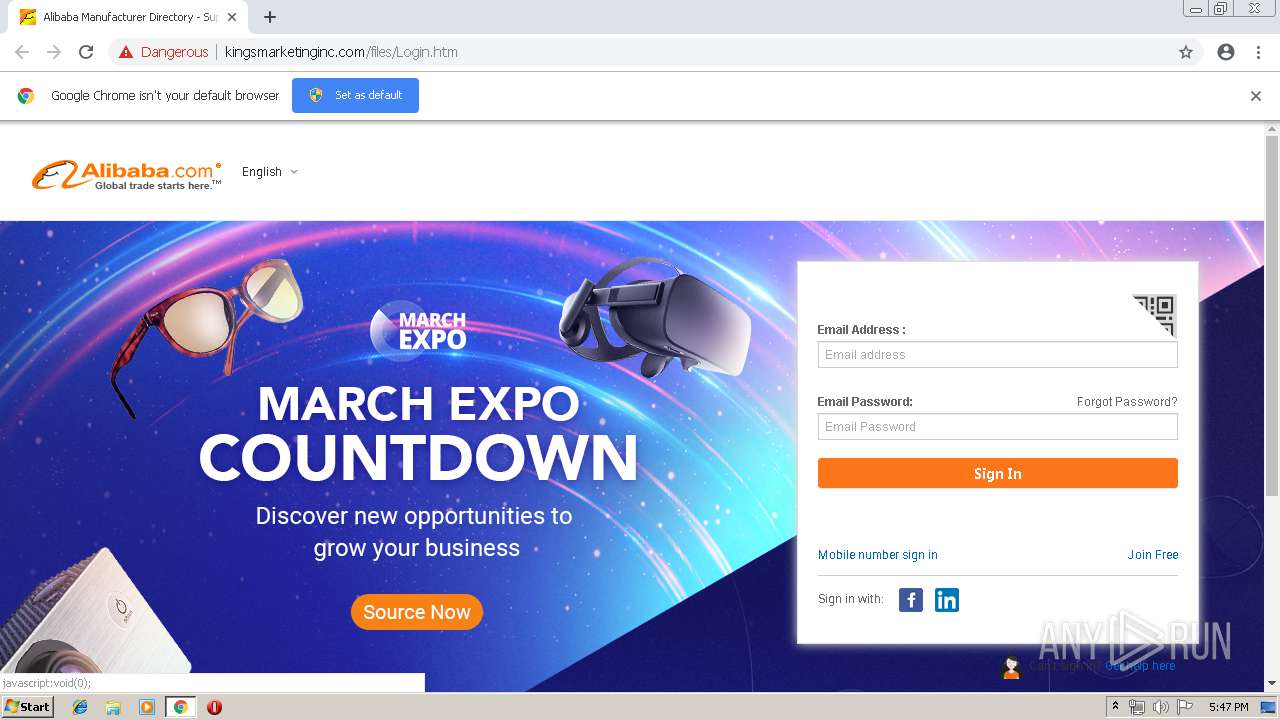
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/files/Login.htm | US | html | 5.48 Kb | suspicious |
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/files/images/login.htm | US | html | 10.5 Kb | suspicious |
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/files/images/TB1ROn8OpXXXXbZaXXXXXXXXXXX-32-31.png | US | image | 1.66 Kb | suspicious |
2236 | chrome.exe | GET | 301 | 198.11.132.198:80 | http://cmap.alibaba.com/ml.html?callback=landing8978252&cna=3bw9EfTyjFECASRKAo4n2aNT | US | html | 278 b | whitelisted |
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/files/images/footer.css | US | text | 1.77 Kb | suspicious |
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/sc-footer/20160321161740/src/1x.png | US | binary | 26 b | suspicious |
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/files/images/clear.png | US | image | 81 b | suspicious |
2236 | chrome.exe | GET | 200 | 198.11.136.21:80 | http://gj.mmstat.com/7.gif?logtype=1&title=&pre=&cache=39e072b&scr=1280x720&isbeta=5&spm-cnt=a2700.homelogin.0.0.MLj6Ac&aplus&userid=&ali_beacon_id=36.73.231.75.1488974567562.630904.4&ali_apache_id=36.73.231.75.1488974564603.407437.8&ali_apache_track=%22%22&ali_apache_tracktmp=&dmtrack_c=%7Baep_usuc_f%3D-%7Caeu_cid%3D-%7D&pageid=245175aa0ab9ea5b58c3db4716a1cbec903a7e1478&hn=enlogin010185234091.oc27&asid=AQAAAABH28NYrHNCZwAAAAAjYkbDBfffDA%3D%3D&dmtrack_b=%7Bifm%3D0%7Clogin%3D0%7D&p=1&o=win7&b=chrome73&s=1280x720&w=webkit&mx=360ee | US | image | 43 b | whitelisted |
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/files/images/data/uab.js | US | text | 357 b | suspicious |
2236 | chrome.exe | GET | 200 | 50.87.146.102:80 | http://kingsmarketinginc.com/files/images/data/nc.js | US | text | 33.4 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2236 | chrome.exe | 205.204.101.142:443 | activity.alibaba.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2236 | chrome.exe | 50.87.146.102:80 | kingsmarketinginc.com | Unified Layer | US | suspicious |
2236 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2236 | chrome.exe | 104.111.216.213:443 | u.alicdn.com | Akamai International B.V. | NL | whitelisted |
2236 | chrome.exe | 198.11.132.198:80 | cmap.alibaba.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2236 | chrome.exe | 198.11.132.6:443 | stylessl.aliunicorn.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2236 | chrome.exe | 198.11.136.21:80 | gj.mmstat.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2236 | chrome.exe | 198.11.132.198:443 | cmap.alibaba.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2236 | chrome.exe | 195.27.31.250:443 | gw.alicdn.com | CW Vodafone Group PLC | DE | unknown |
2236 | chrome.exe | 104.111.216.213:80 | u.alicdn.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
kingsmarketinginc.com |
| suspicious |
accounts.google.com |
| shared |
stylessl.aliunicorn.com |
| unknown |
cmap.alibaba.com |
| whitelisted |
u.alicdn.com |
| whitelisted |
img.alicdn.com |
| whitelisted |
gj.mmstat.com |
| whitelisted |
activity.alibaba.com |
| whitelisted |
aliqin.tmall.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2236 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Alibaba Phishing Landing - Title over non SSL |
2236 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2236 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2236 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2236 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2236 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2236 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2236 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2236 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |