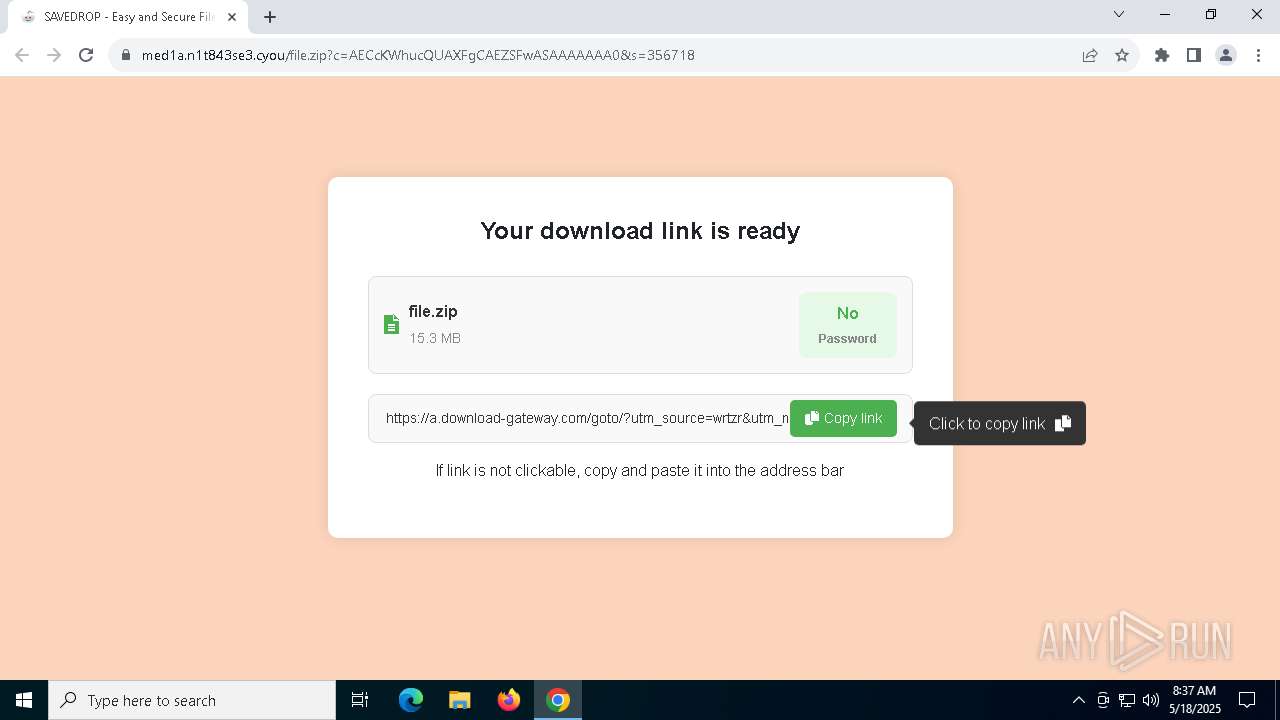
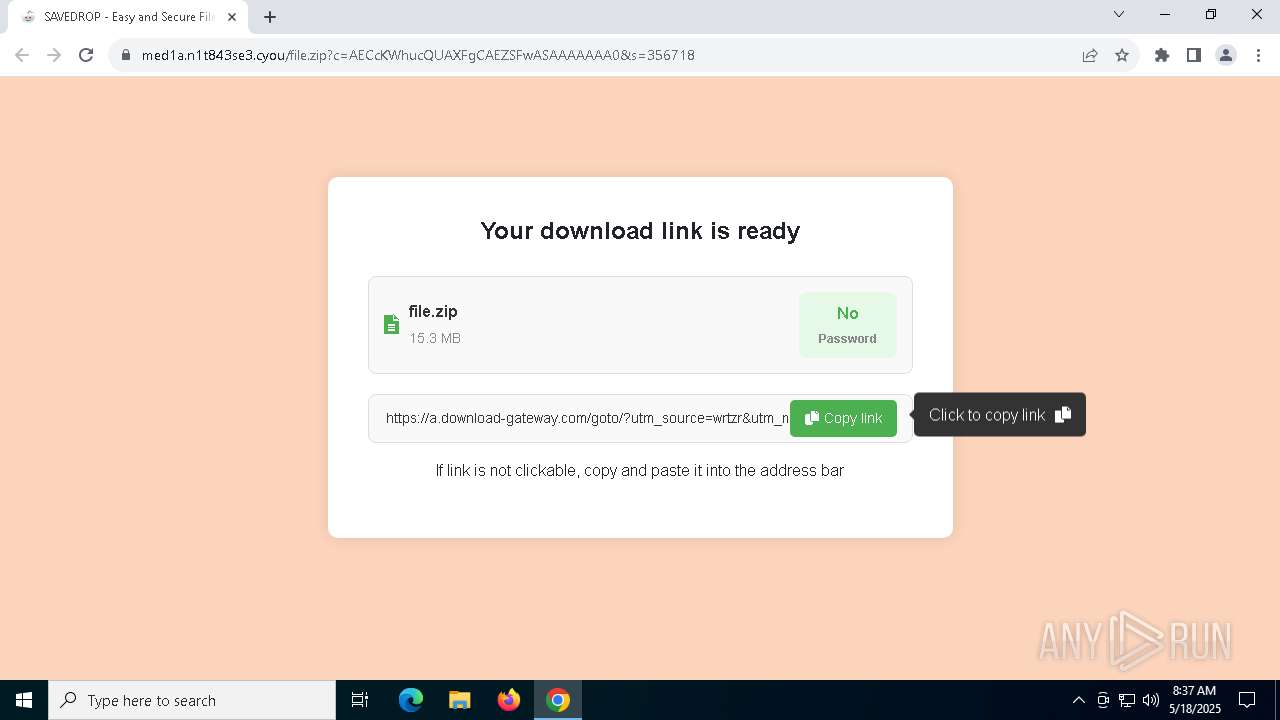
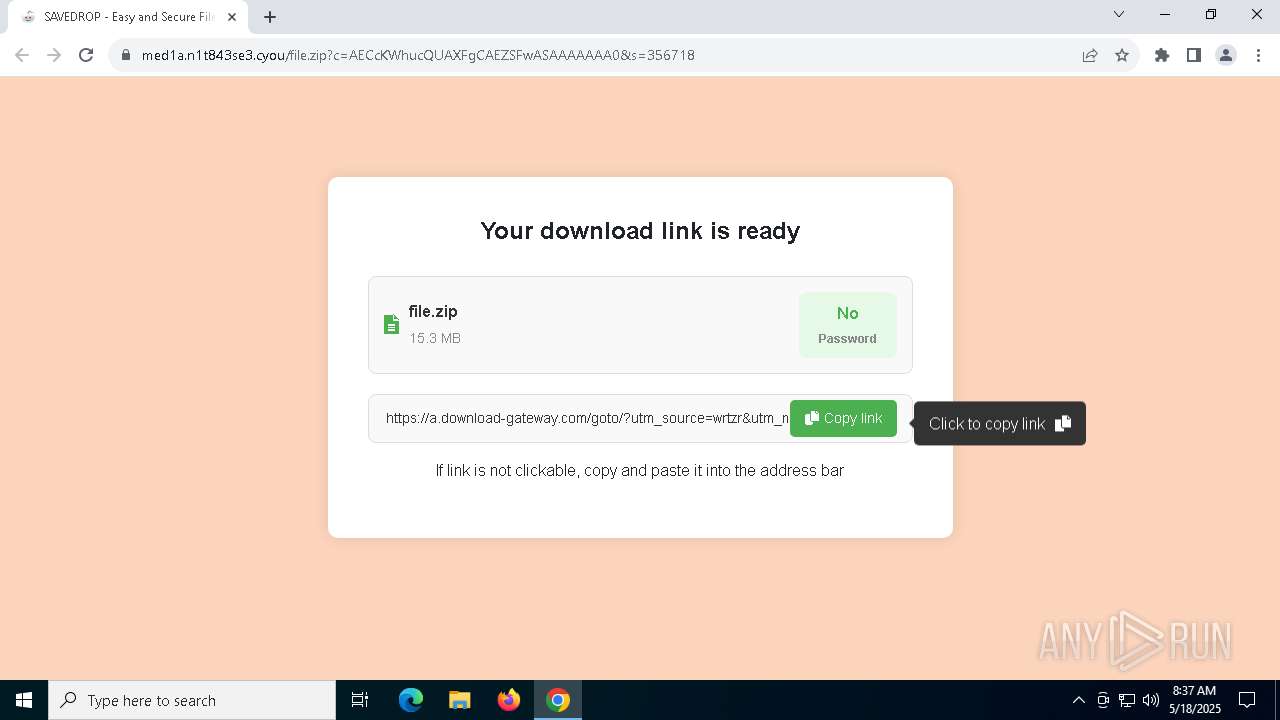
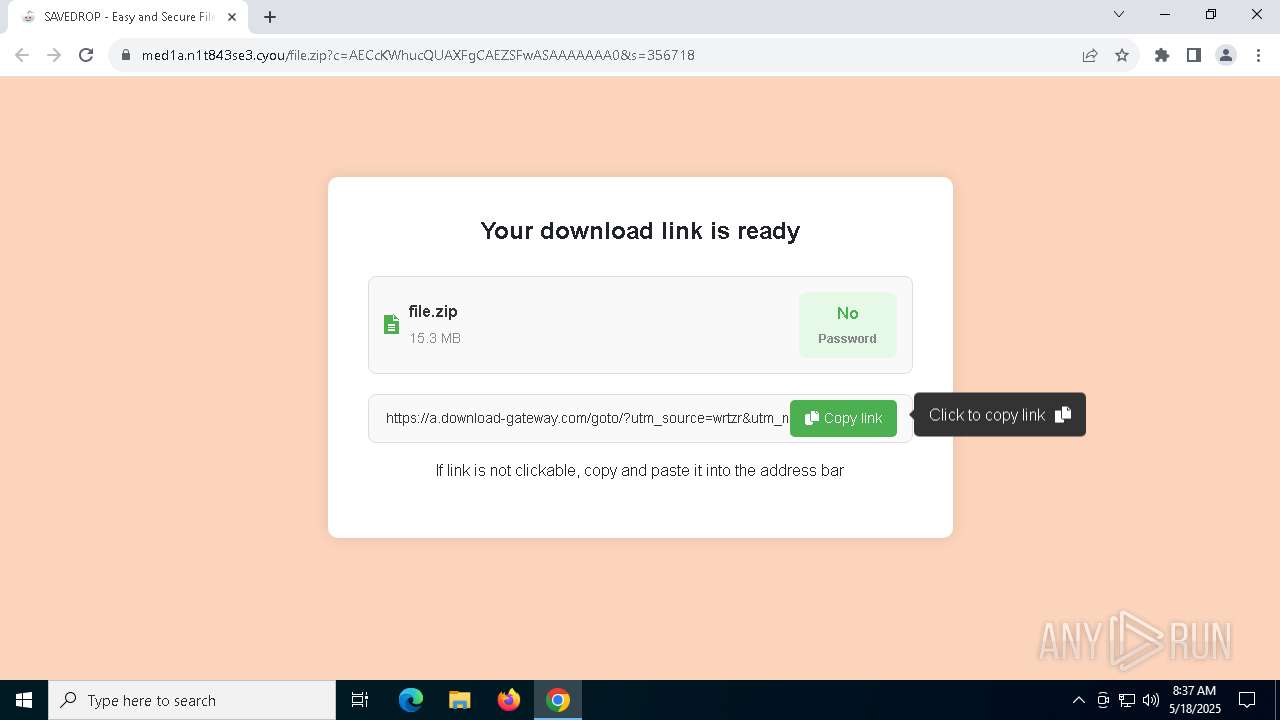
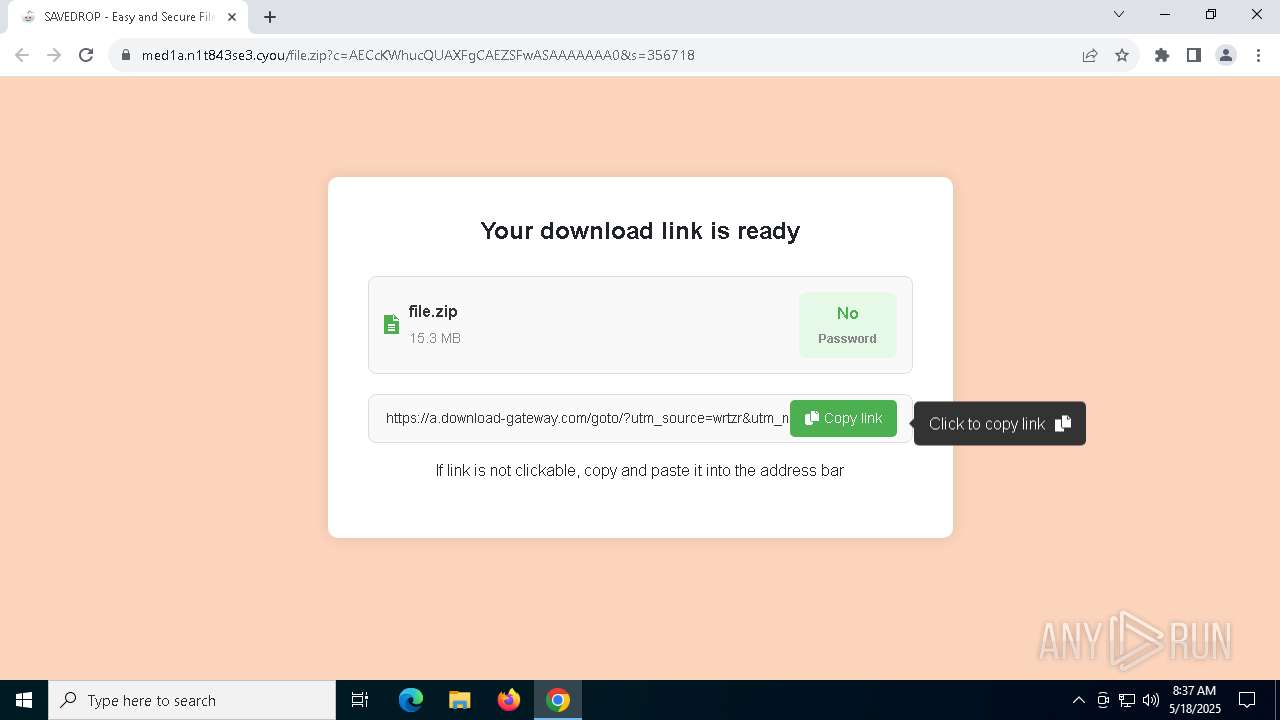
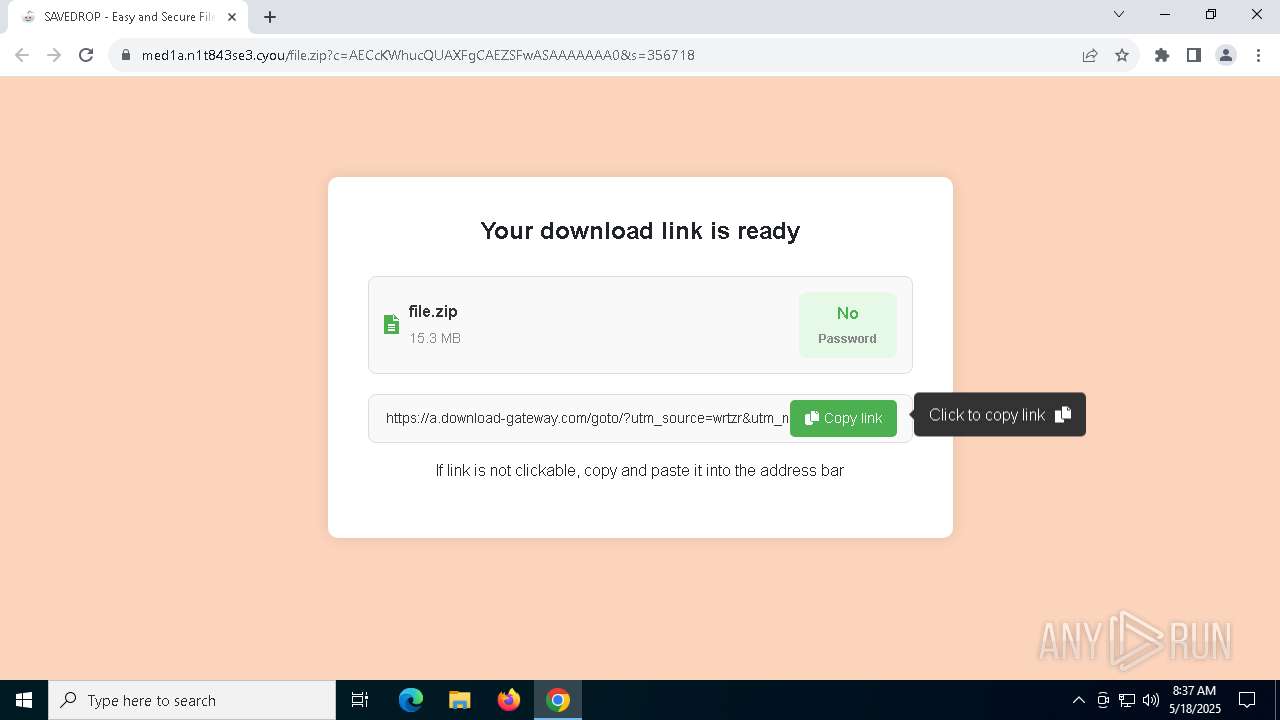
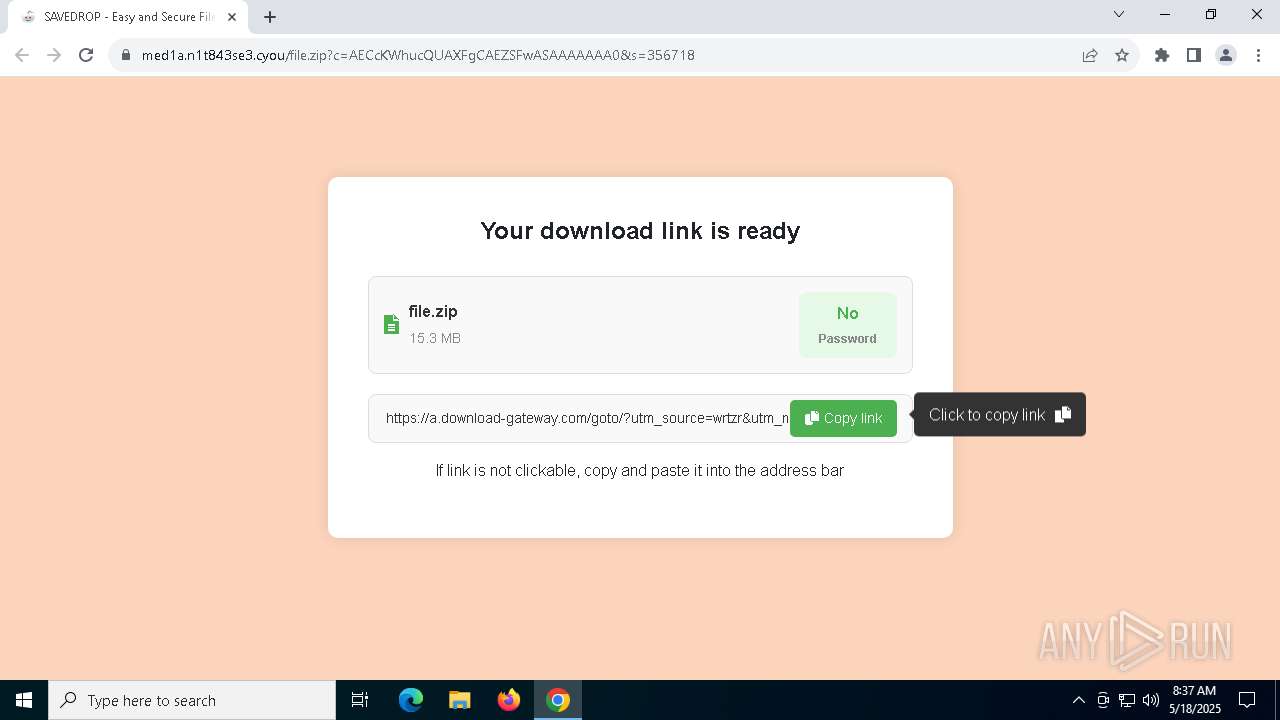
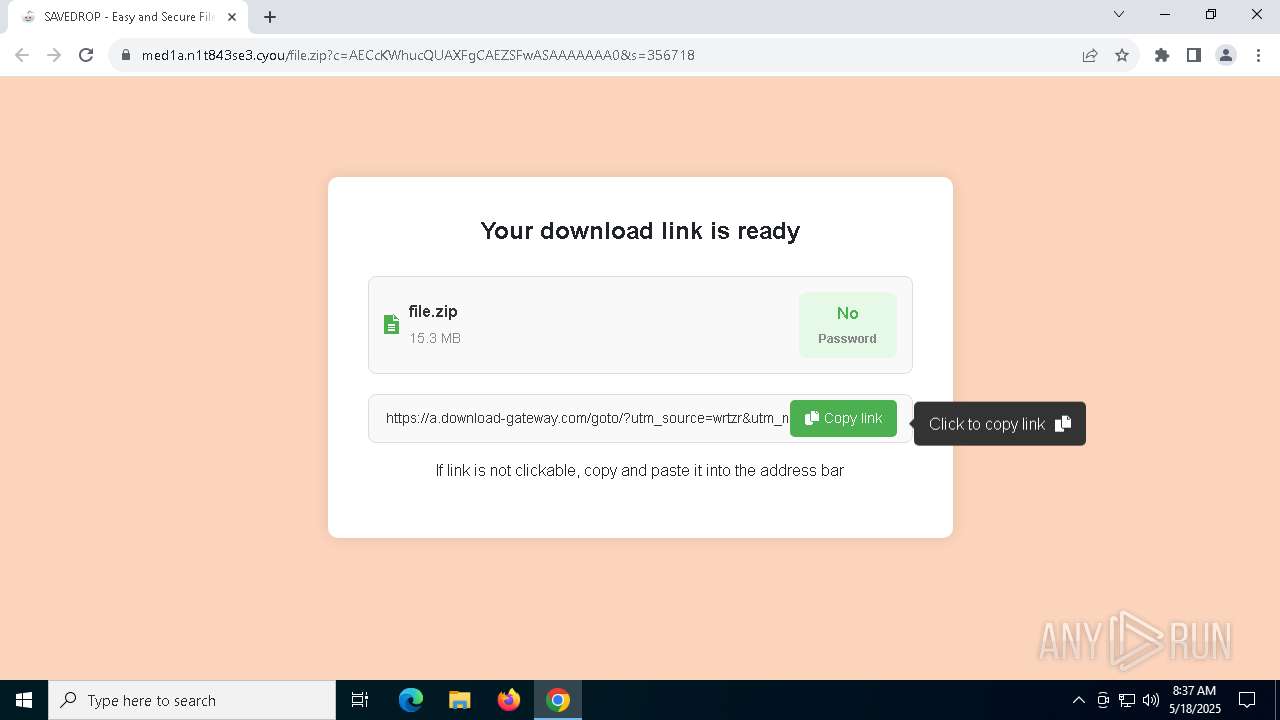
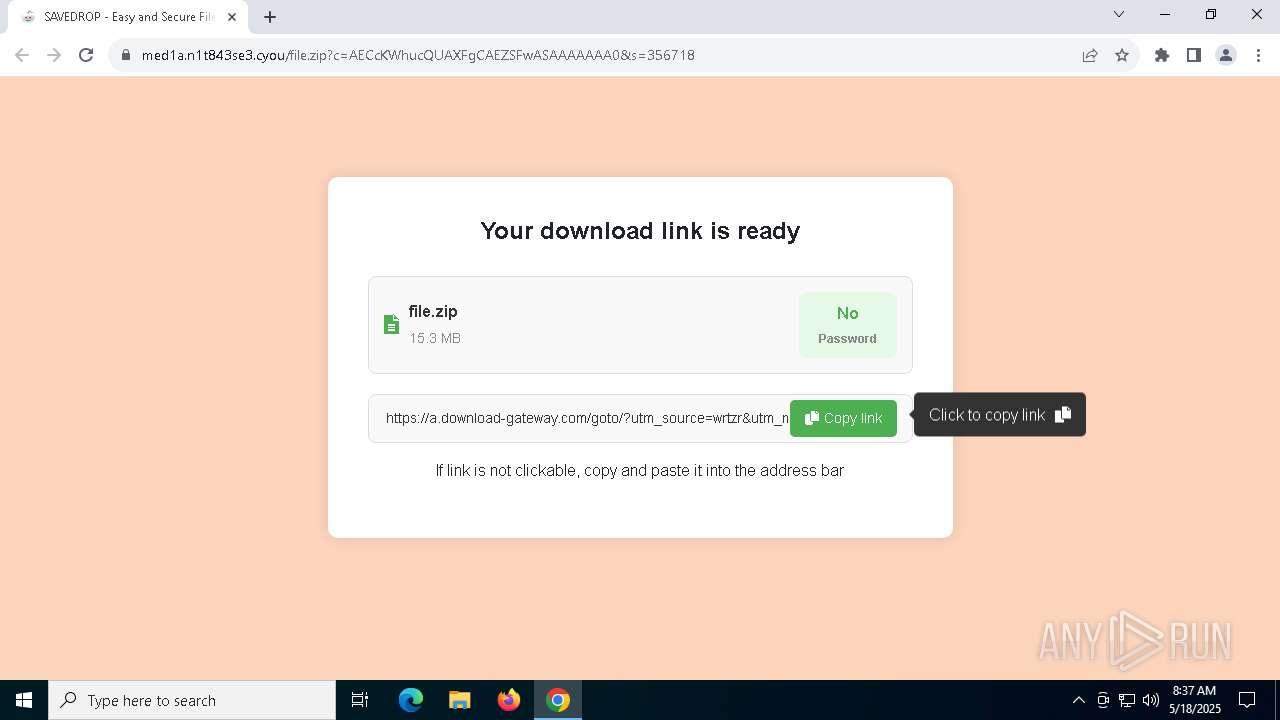
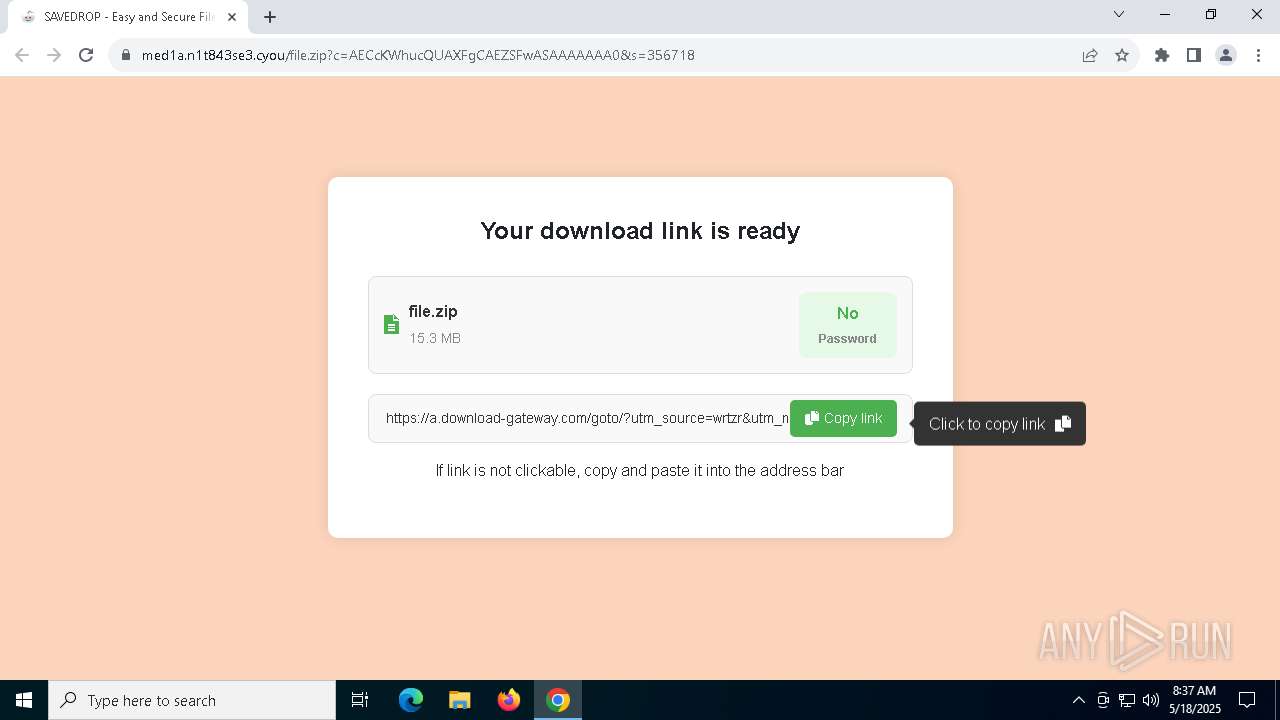
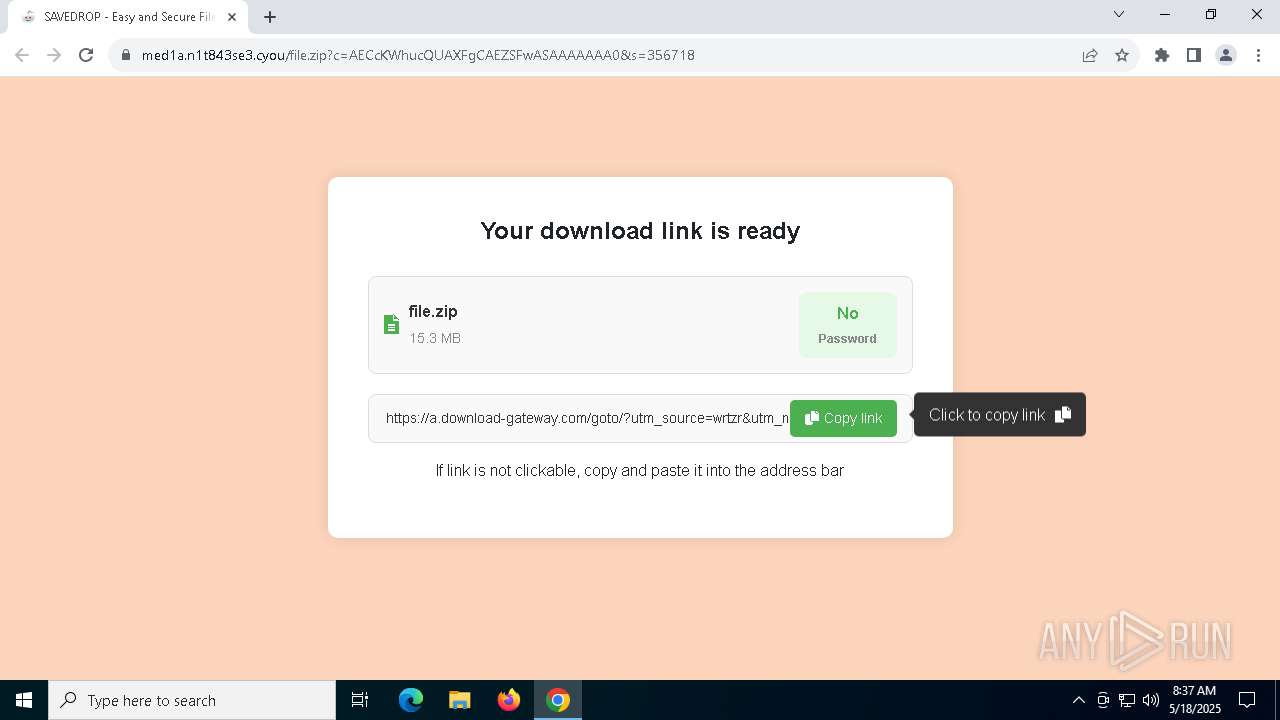
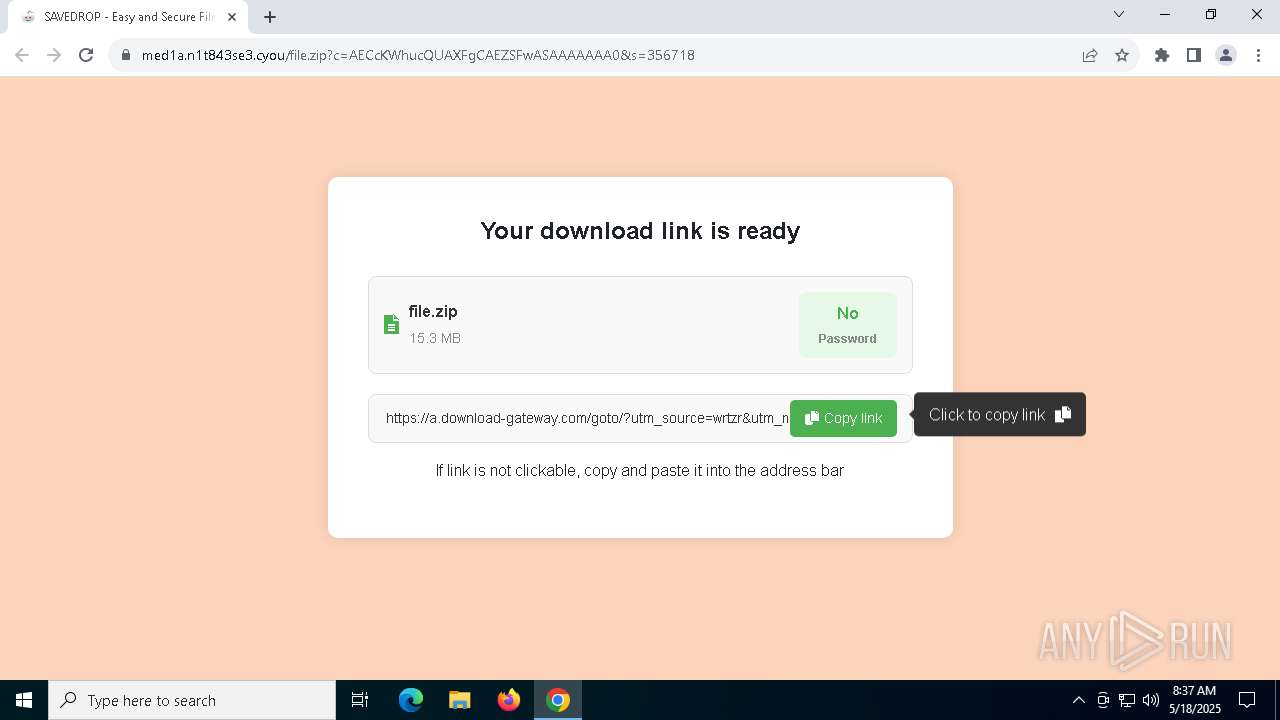
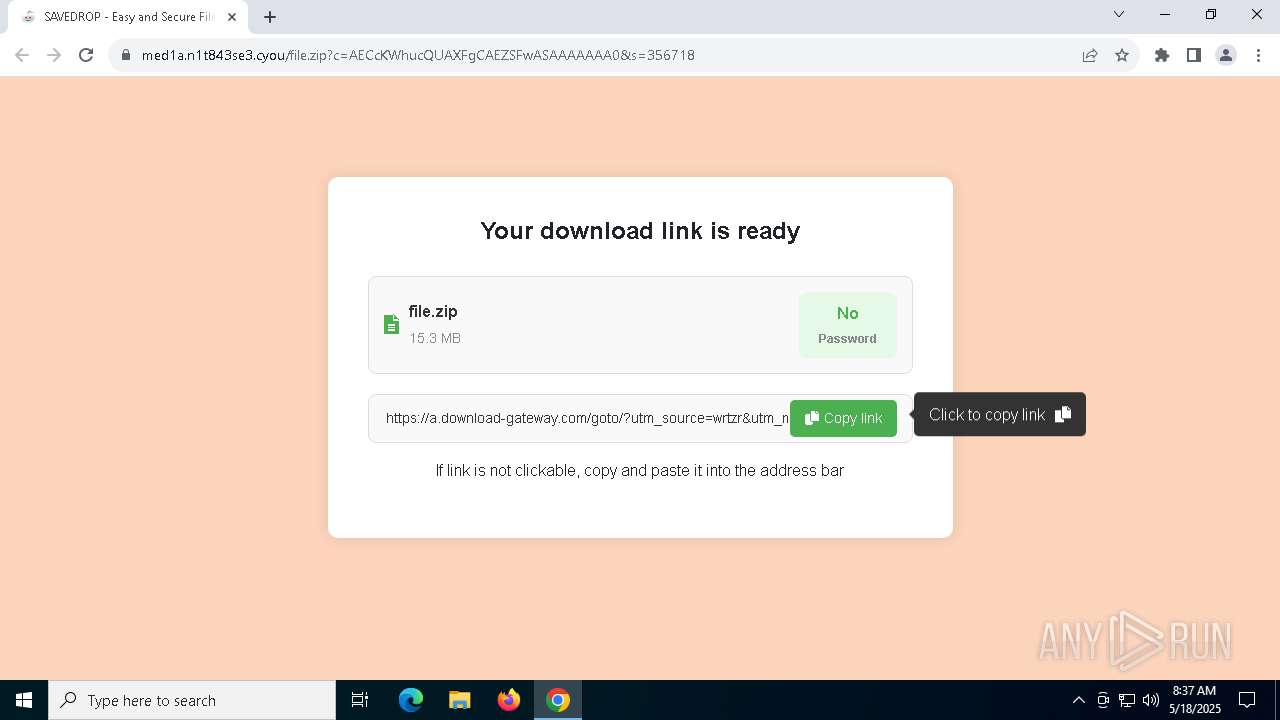
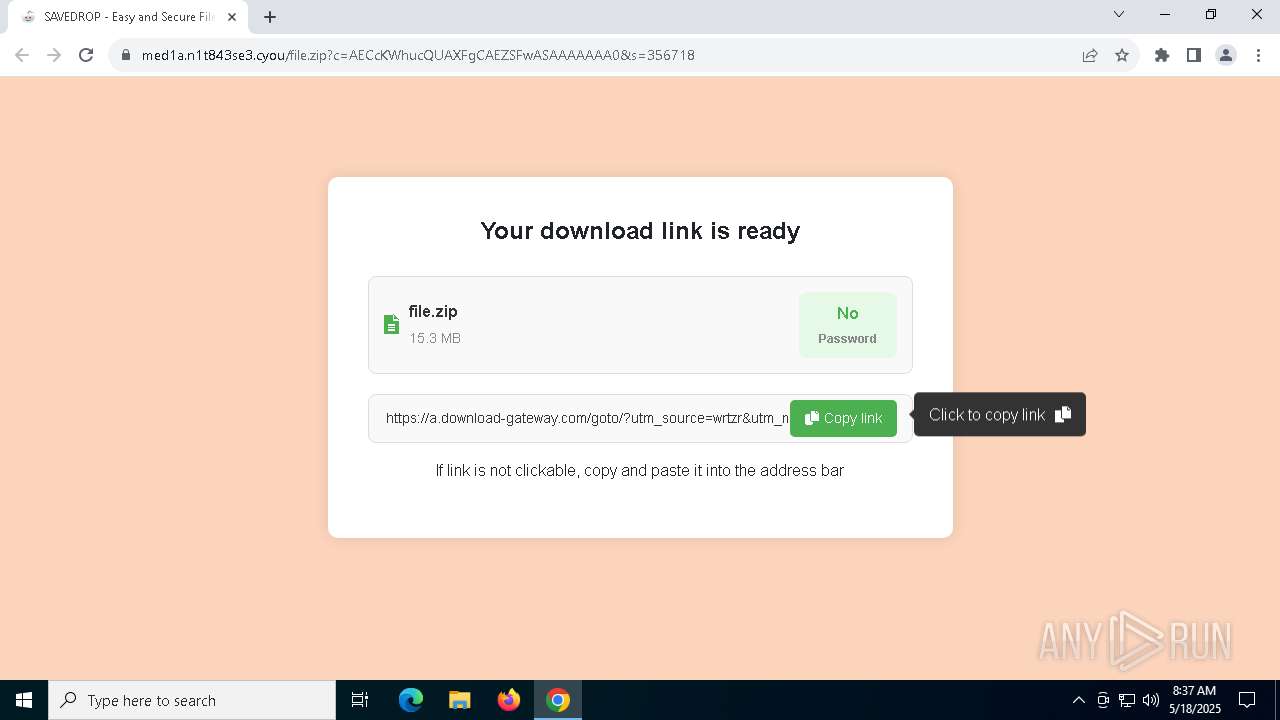
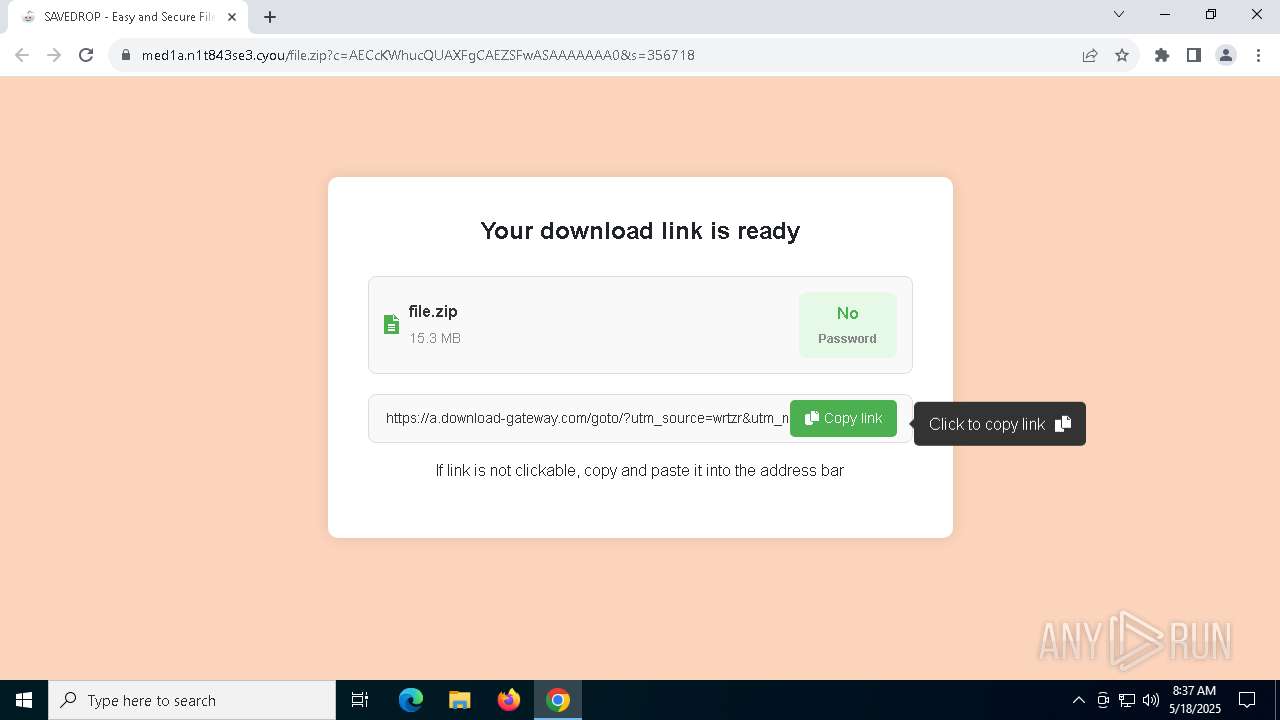
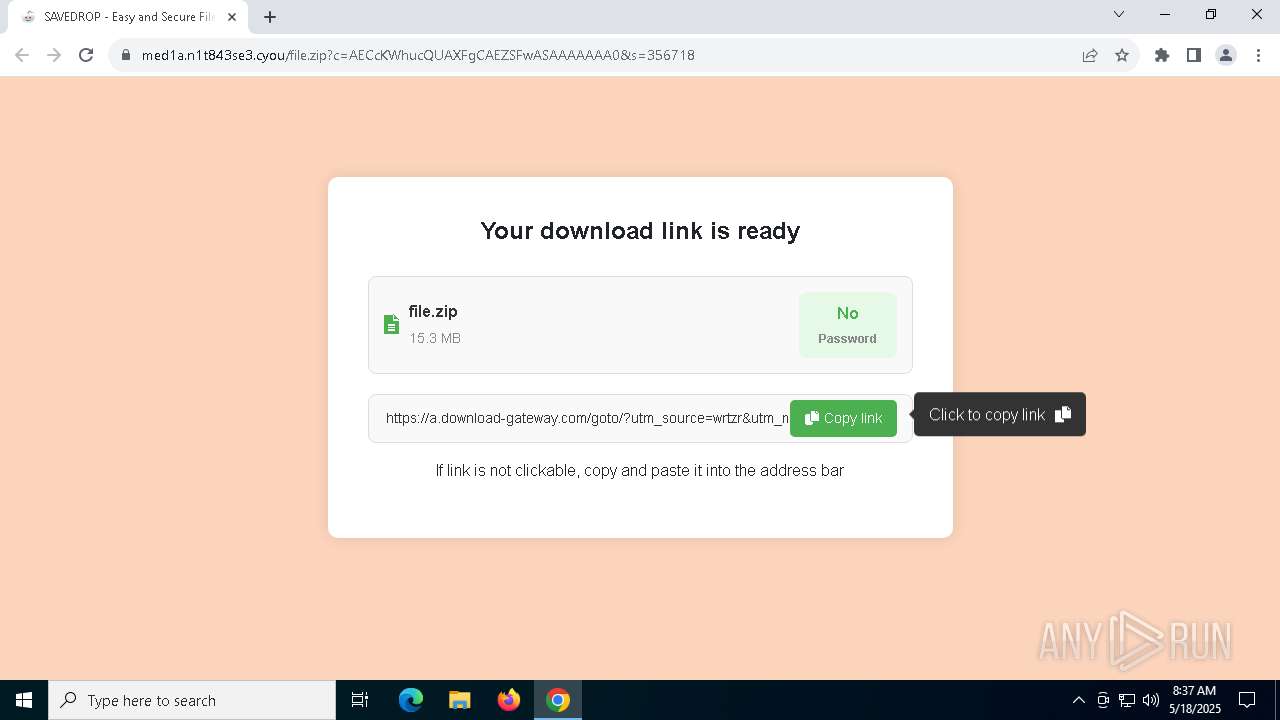
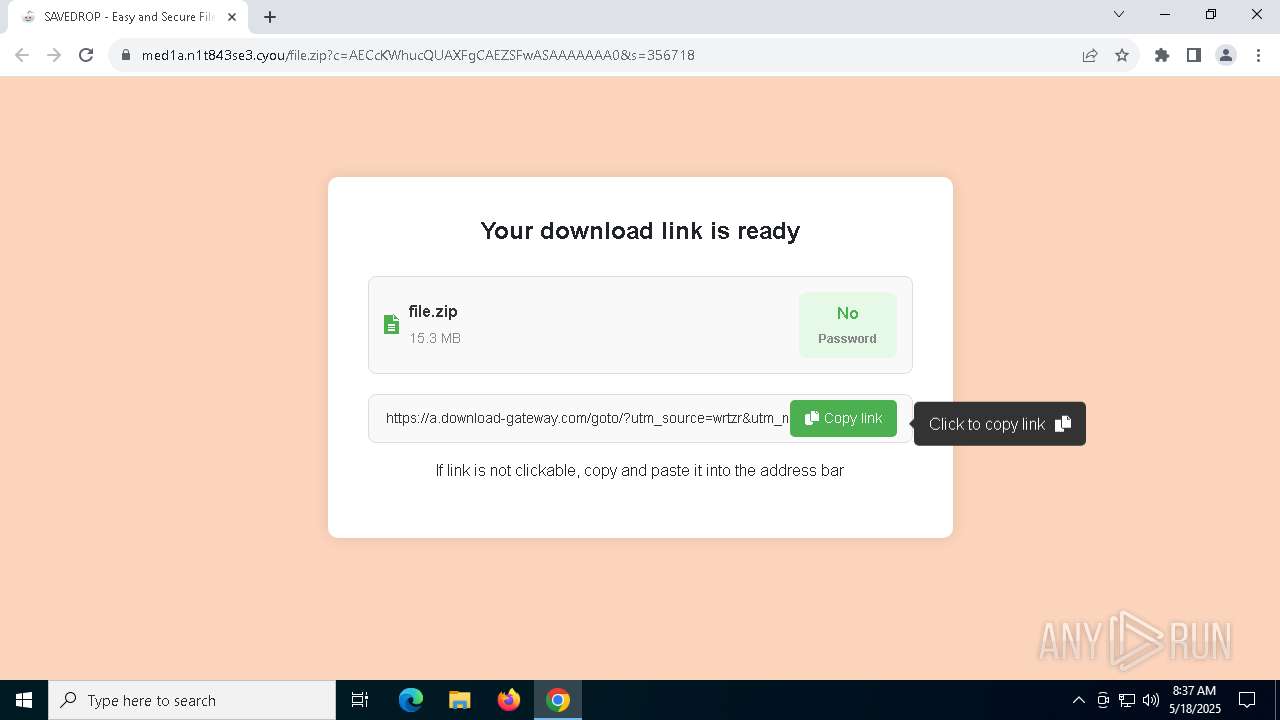
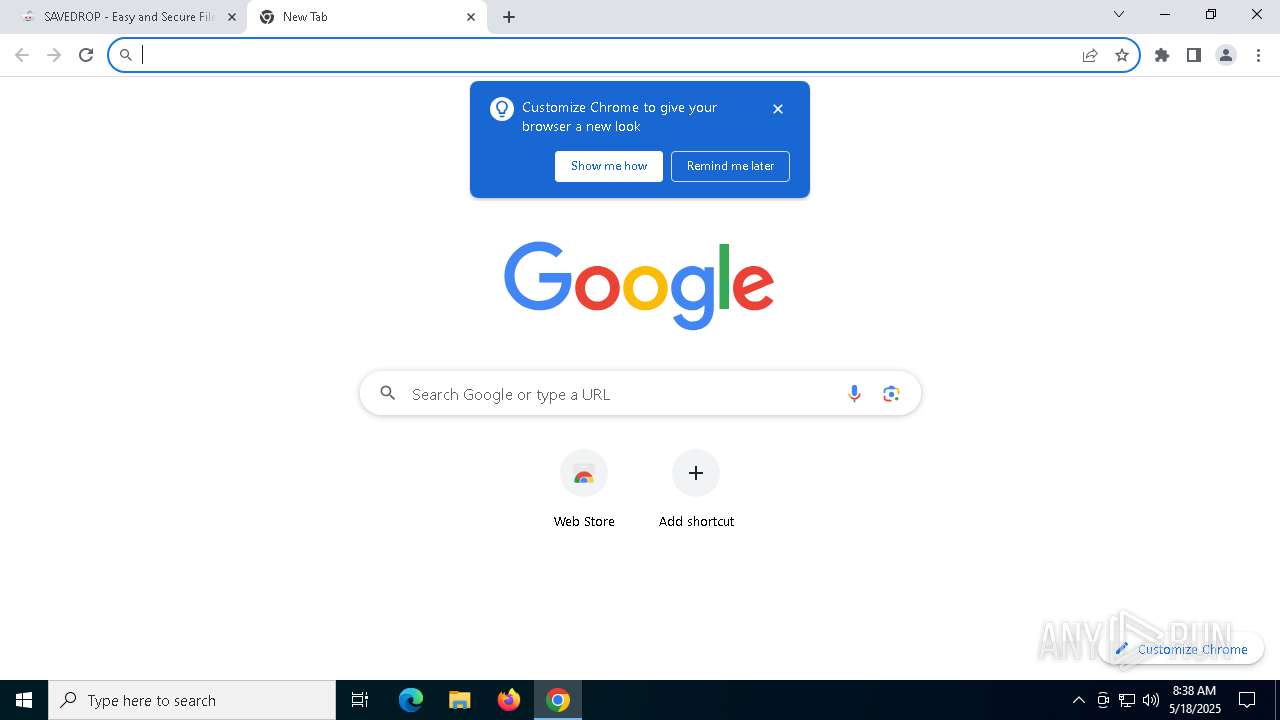
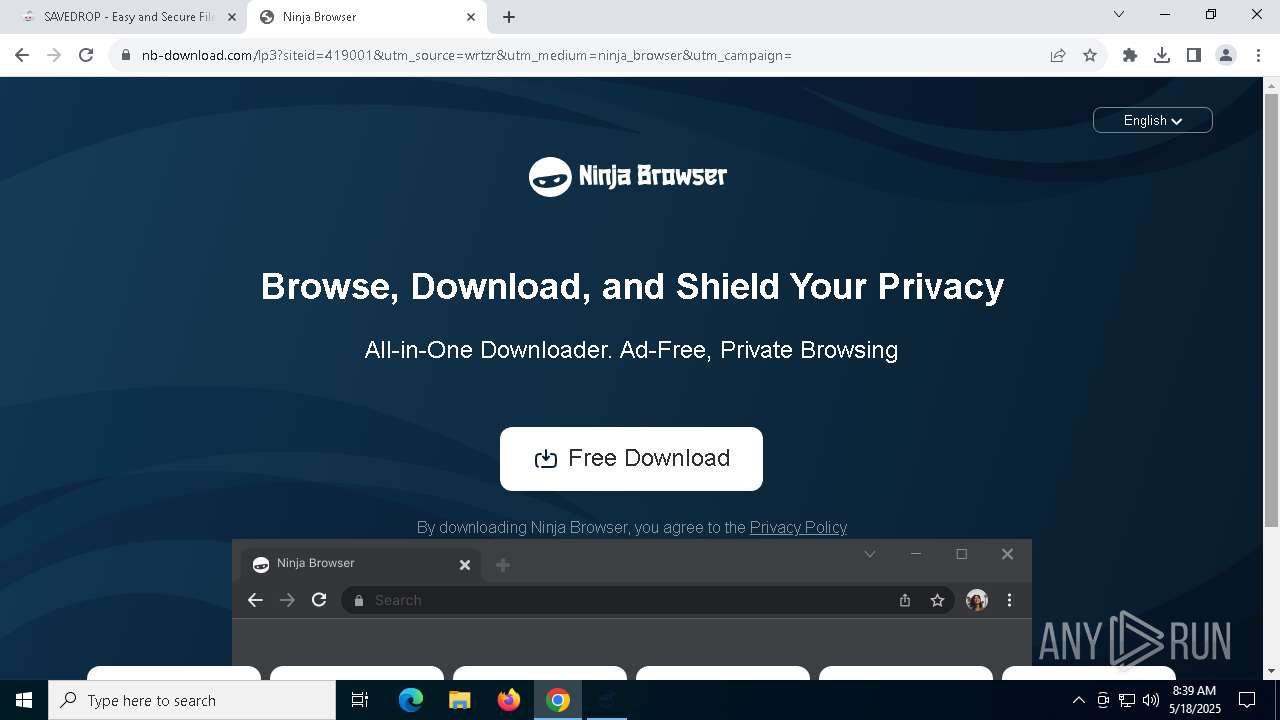
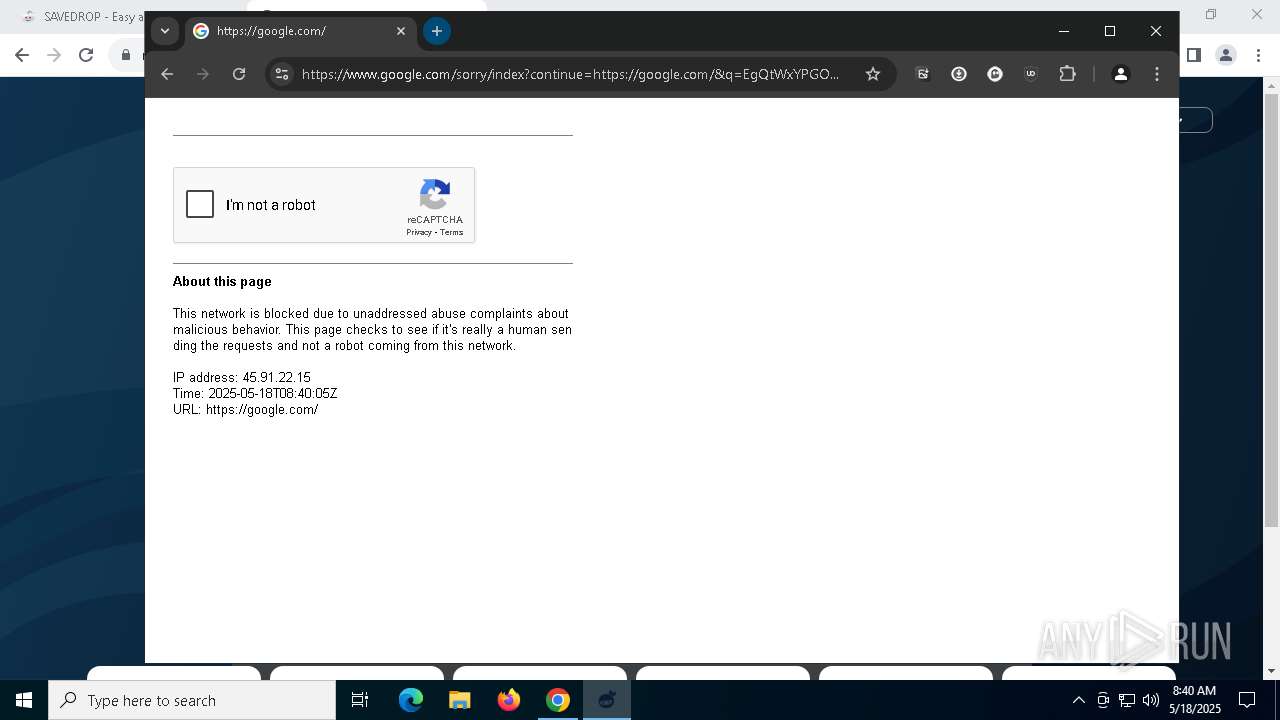
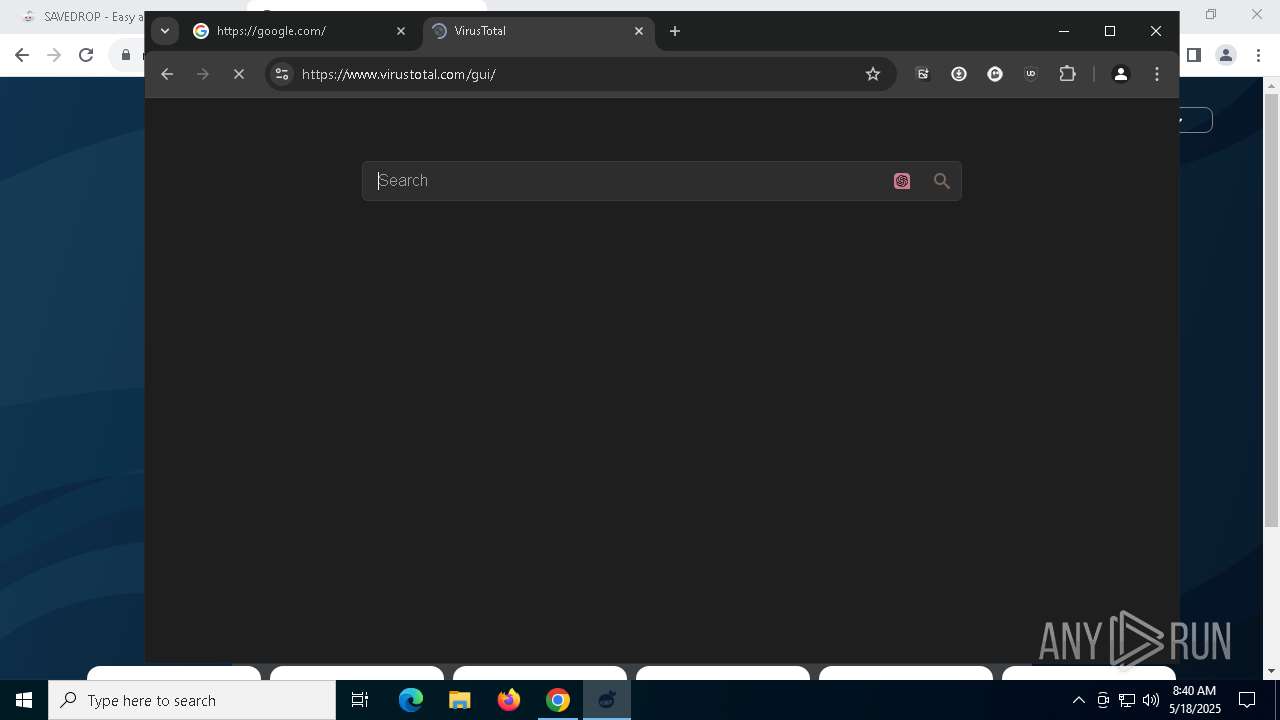
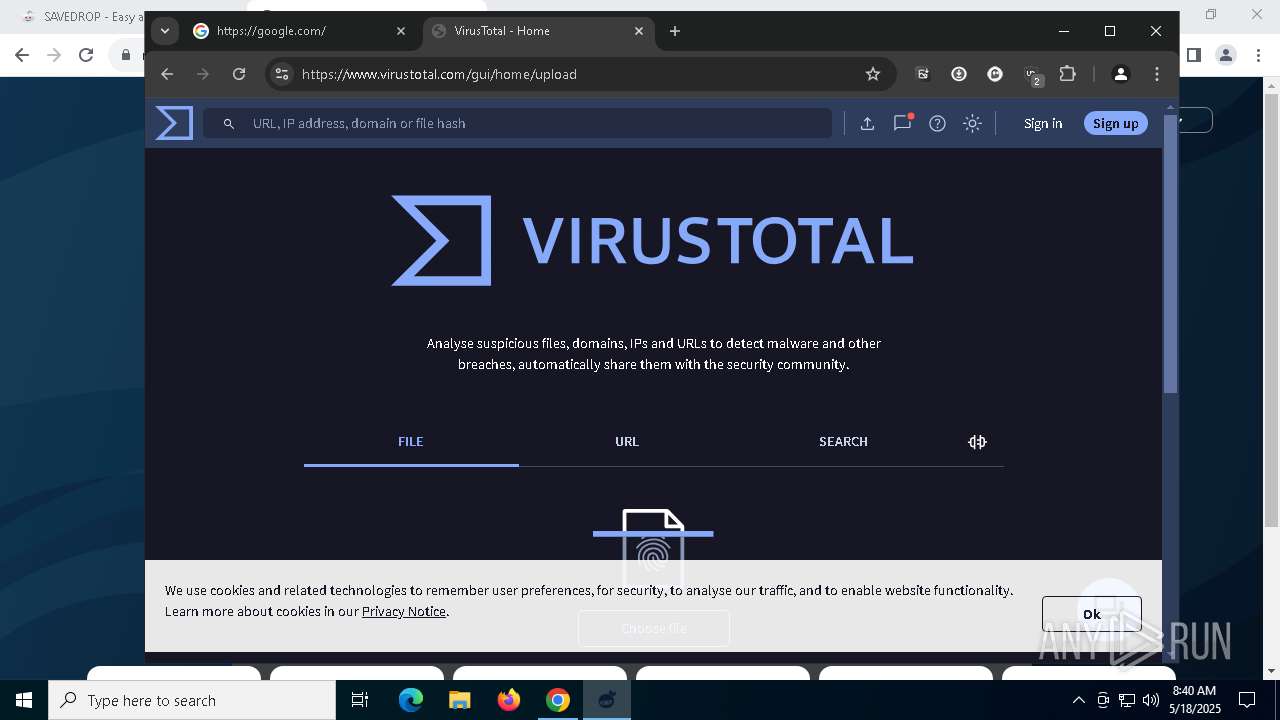
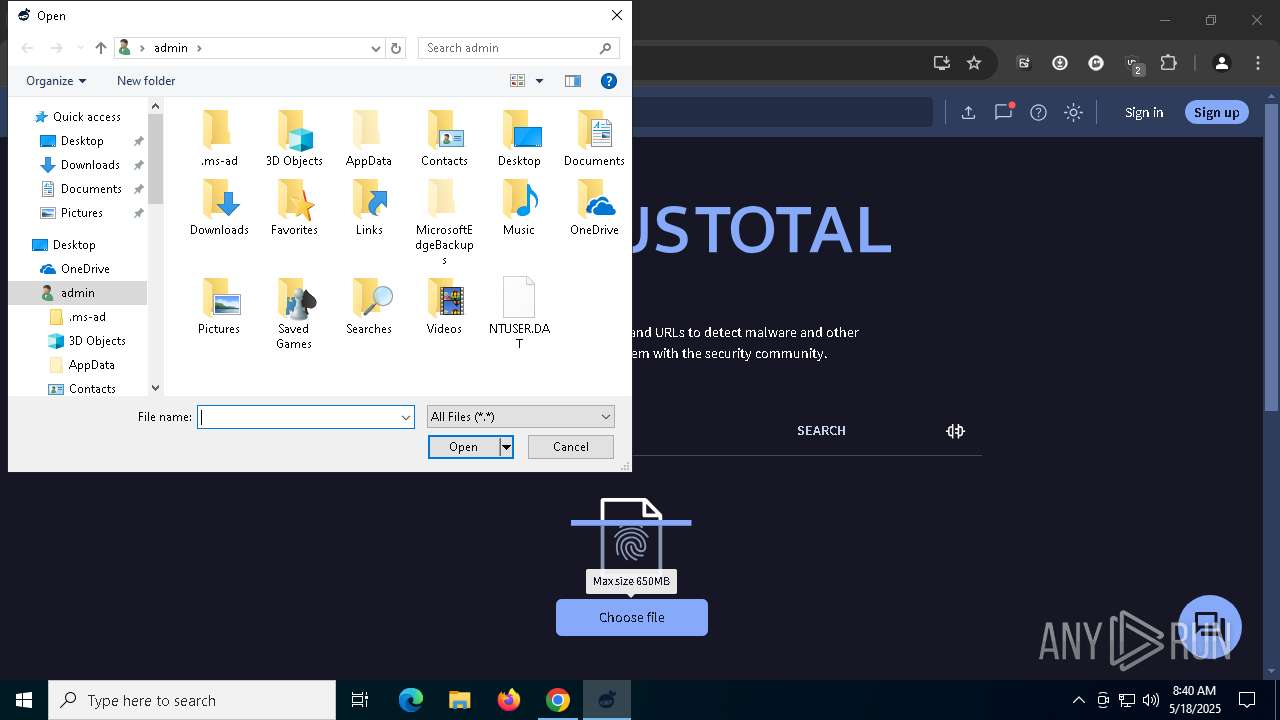
| URL: | https://thetotoro.com/wg8hn5?cost=0.000009¤cy=usd&external_id=947617804096643838&creative_id=23653299&ad_campaign_id=9410814&source=6969766 |
| Full analysis: | https://app.any.run/tasks/cd0f6a33-e638-45ba-843f-565cfa1819c0 |
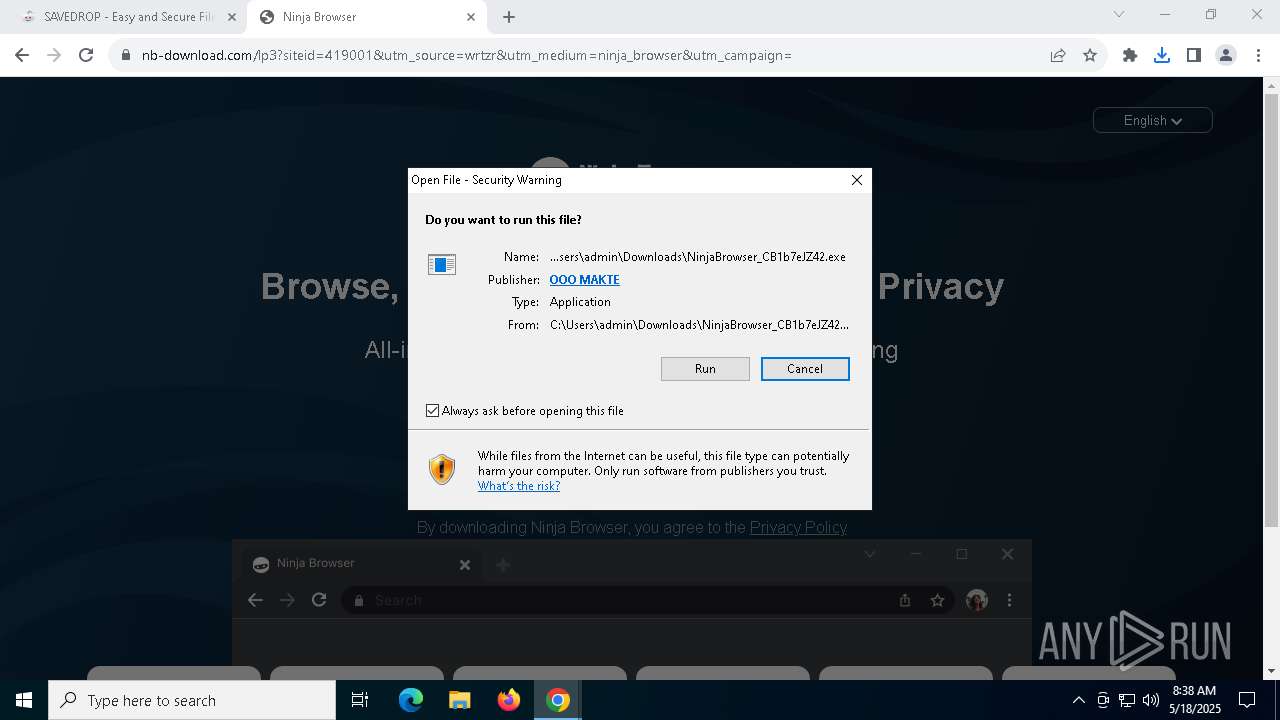
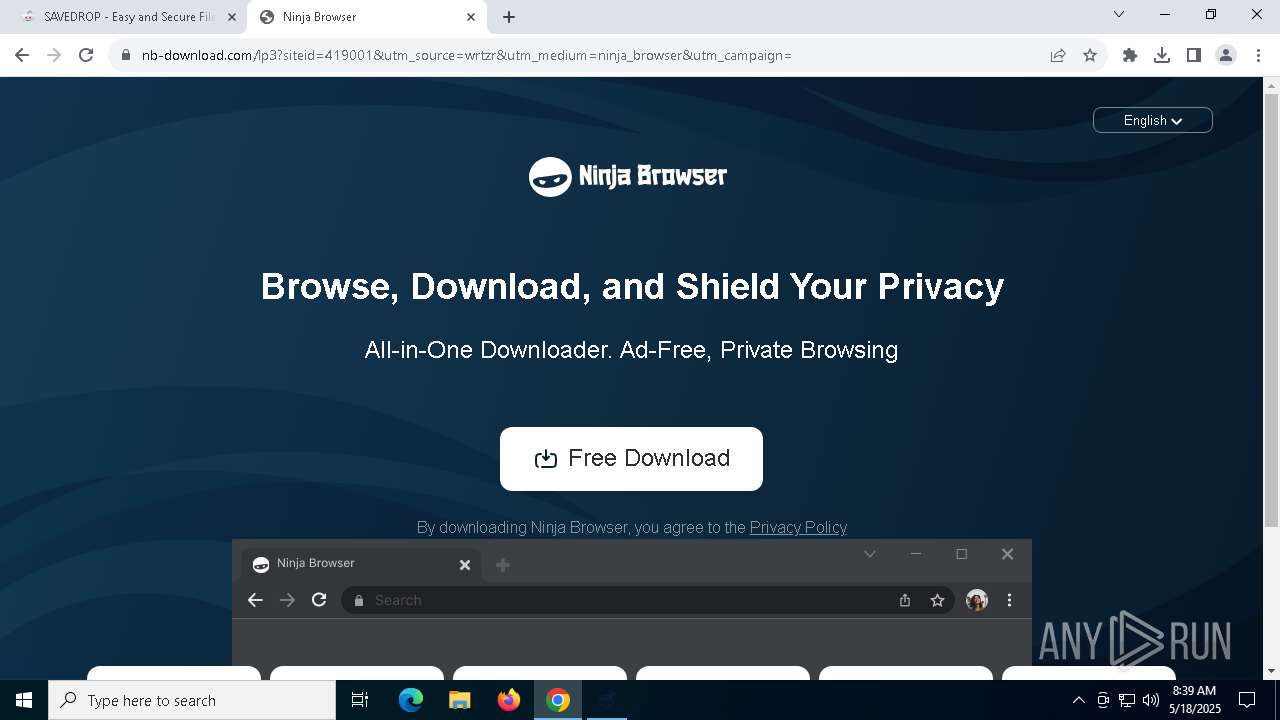
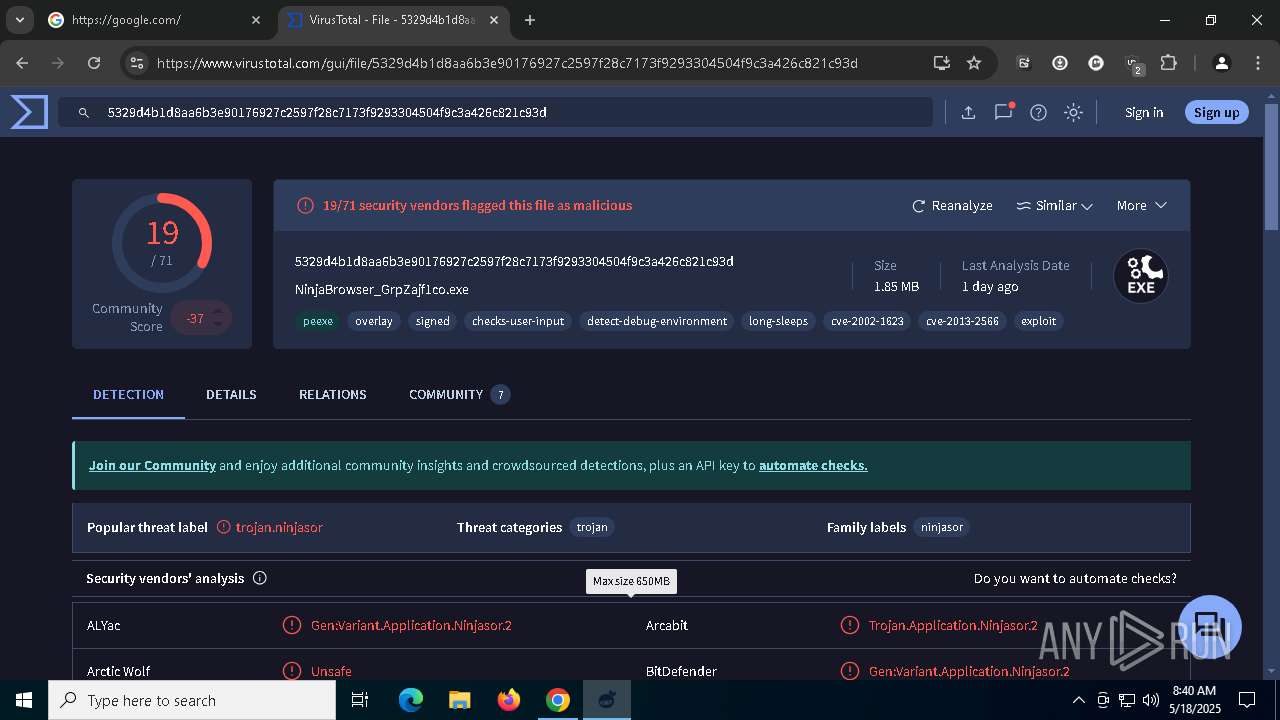
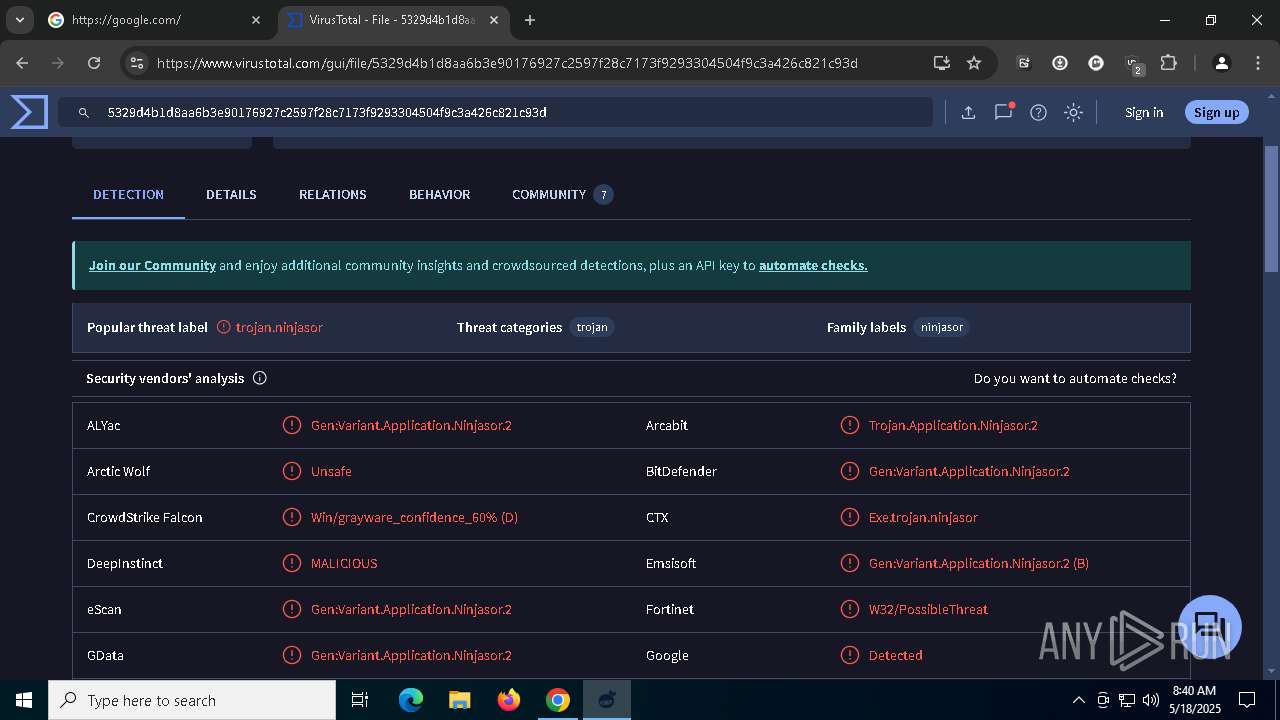
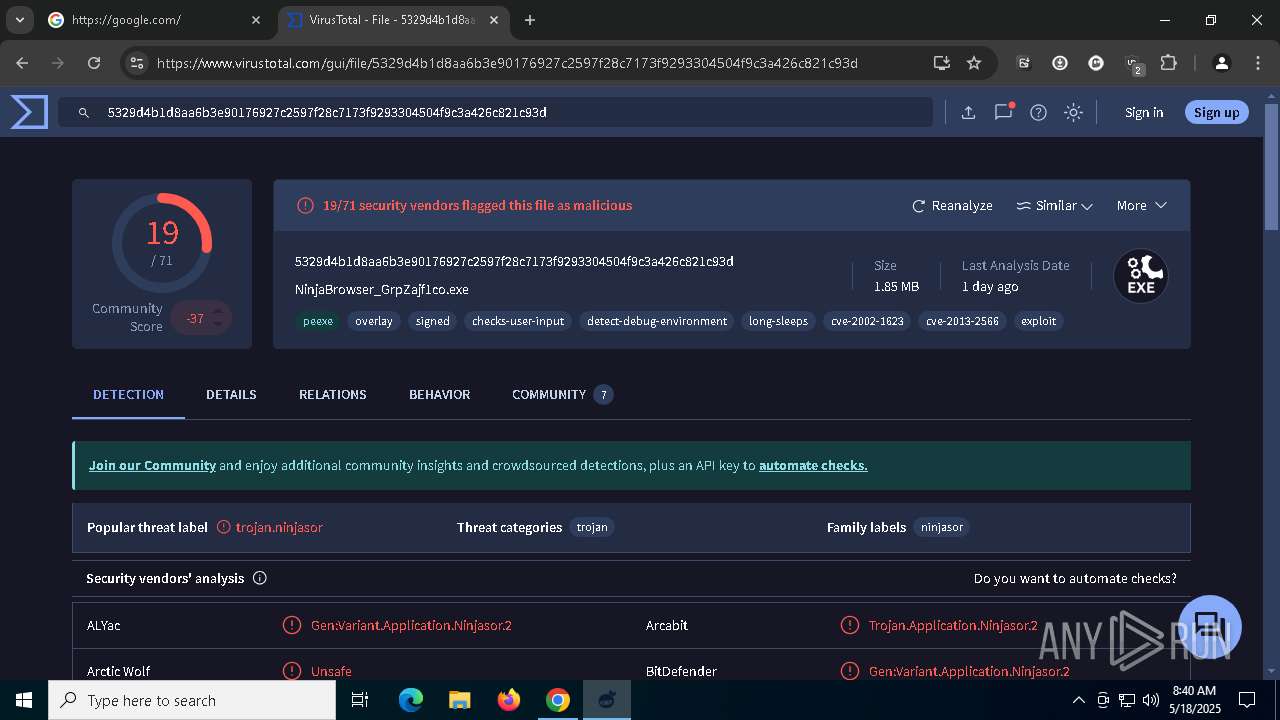
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 08:37:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 20A4426789E2FE15A4F754E77AAC75DB |
| SHA1: | 4658EBE07EB7DF34FCC596C29F48D6F7707F6FCD |
| SHA256: | 9F24C1F93DD048DE6142B639F496A46421CEE78A1B9C295CFF6DC375F72526E9 |
| SSDEEP: | 3:N8FARIhzXxyG1xybE0rVRV1IlazXxo6GDEXbR2WAvjTTn:2PIG+j7VRnXbR2PvT |
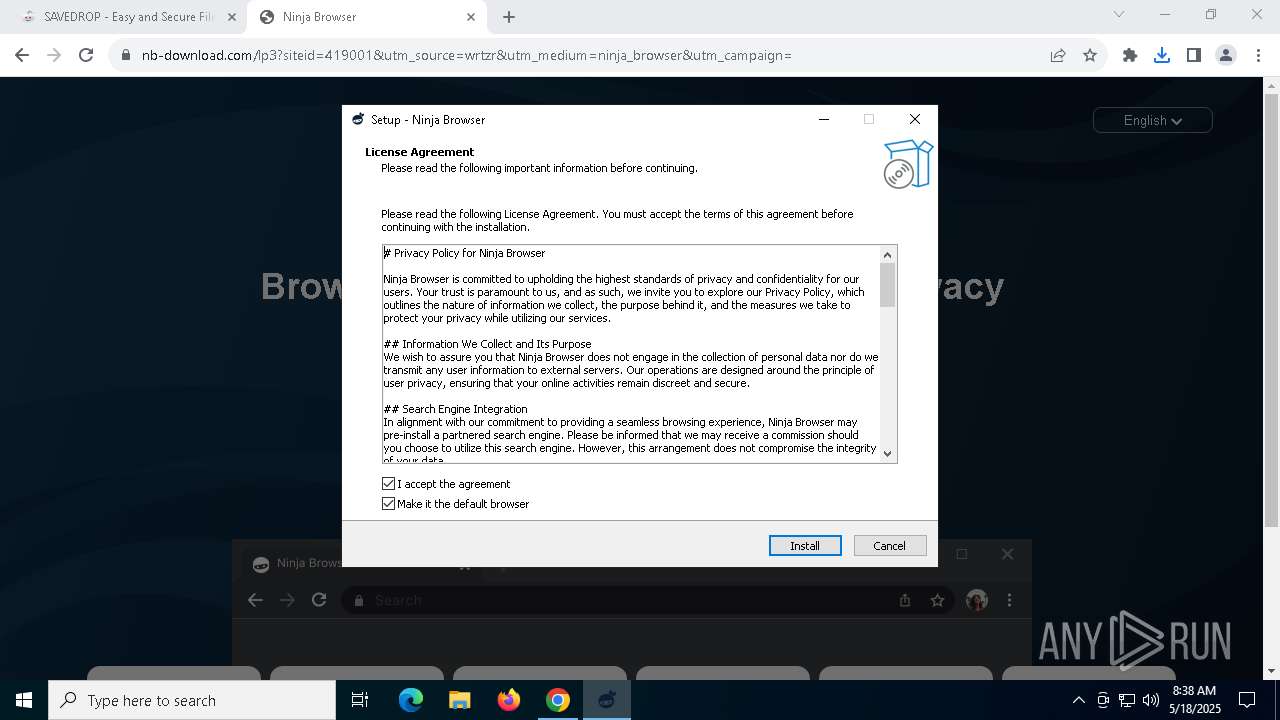
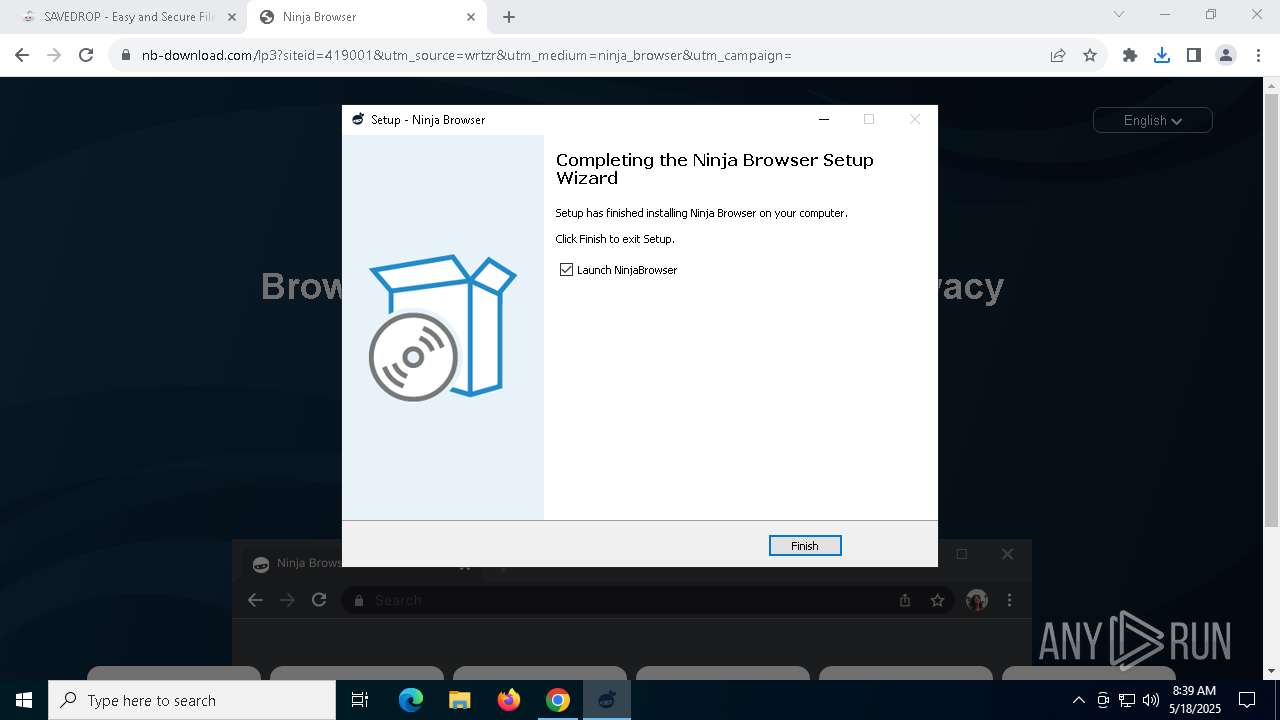
MALICIOUS
GENERIC has been found (auto)
- chrome.exe (PID: 7352)
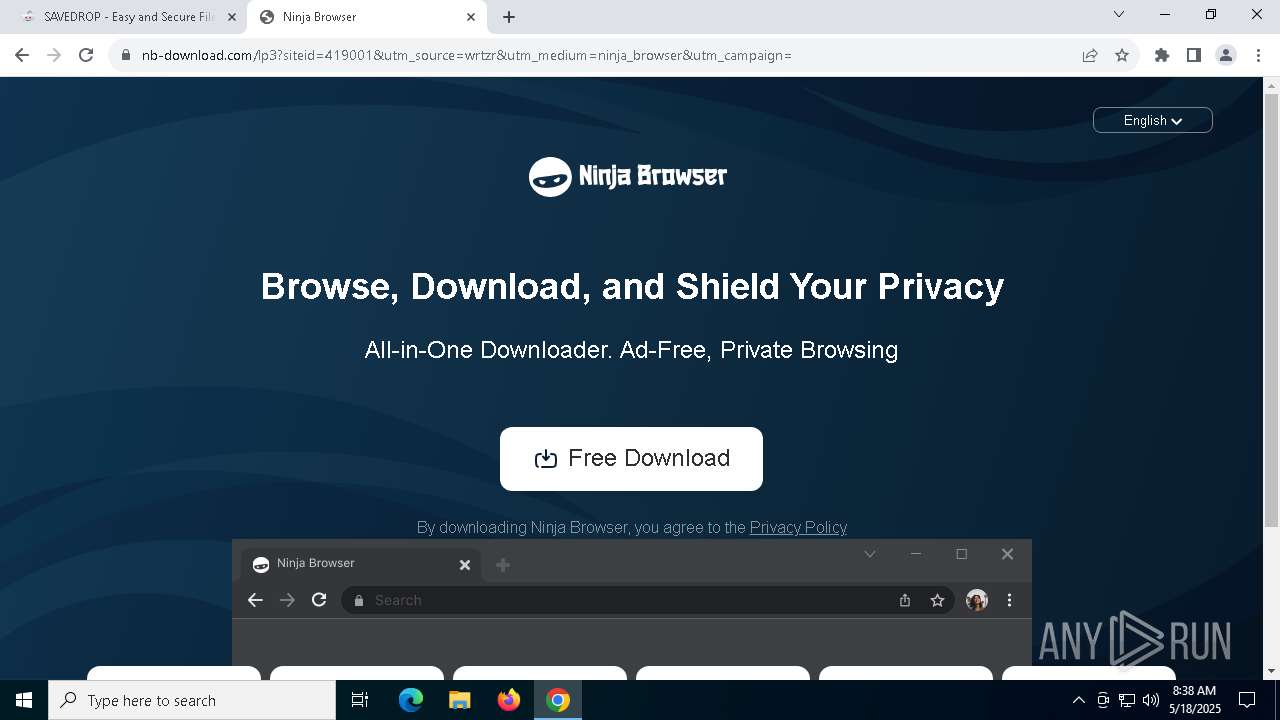
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
Changes the autorun value in the registry
- setup.exe (PID: 8036)
Uses Task Scheduler to autorun other applications
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
Uses Task Scheduler to run other applications
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- mshta.exe (PID: 6572)
- mshta.exe (PID: 7996)
- mshta.exe (PID: 7100)
SUSPICIOUS
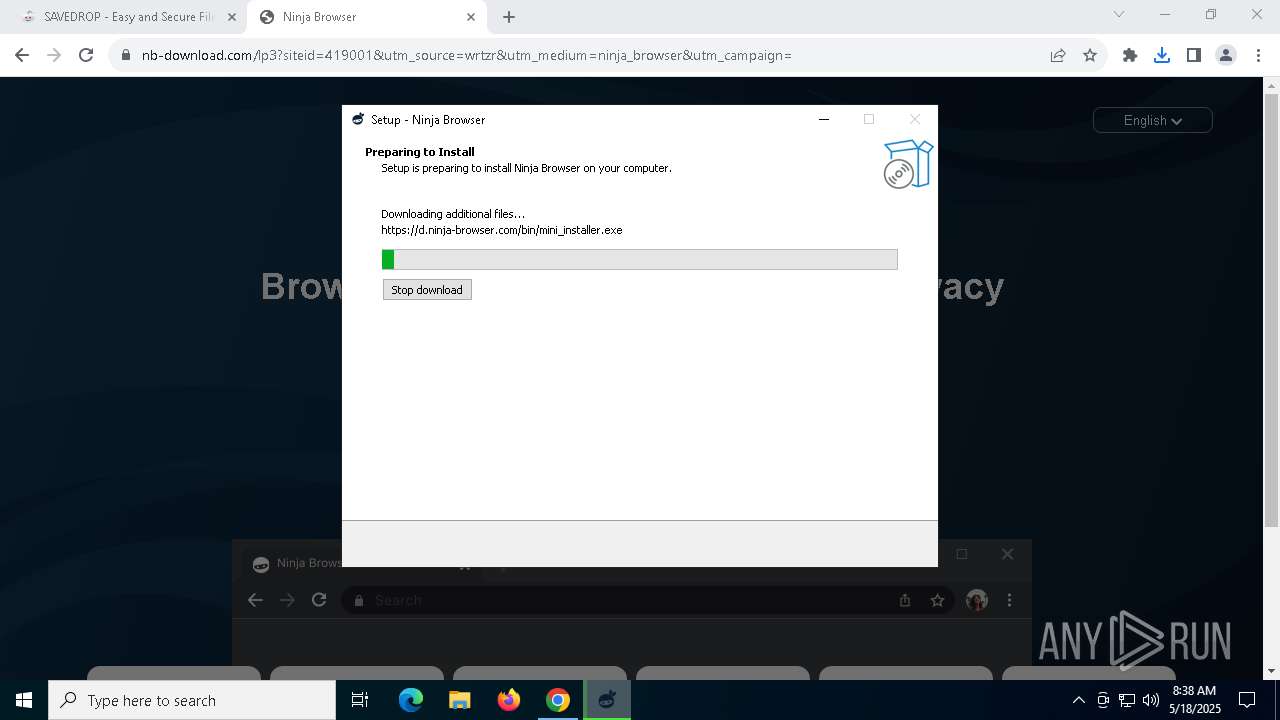
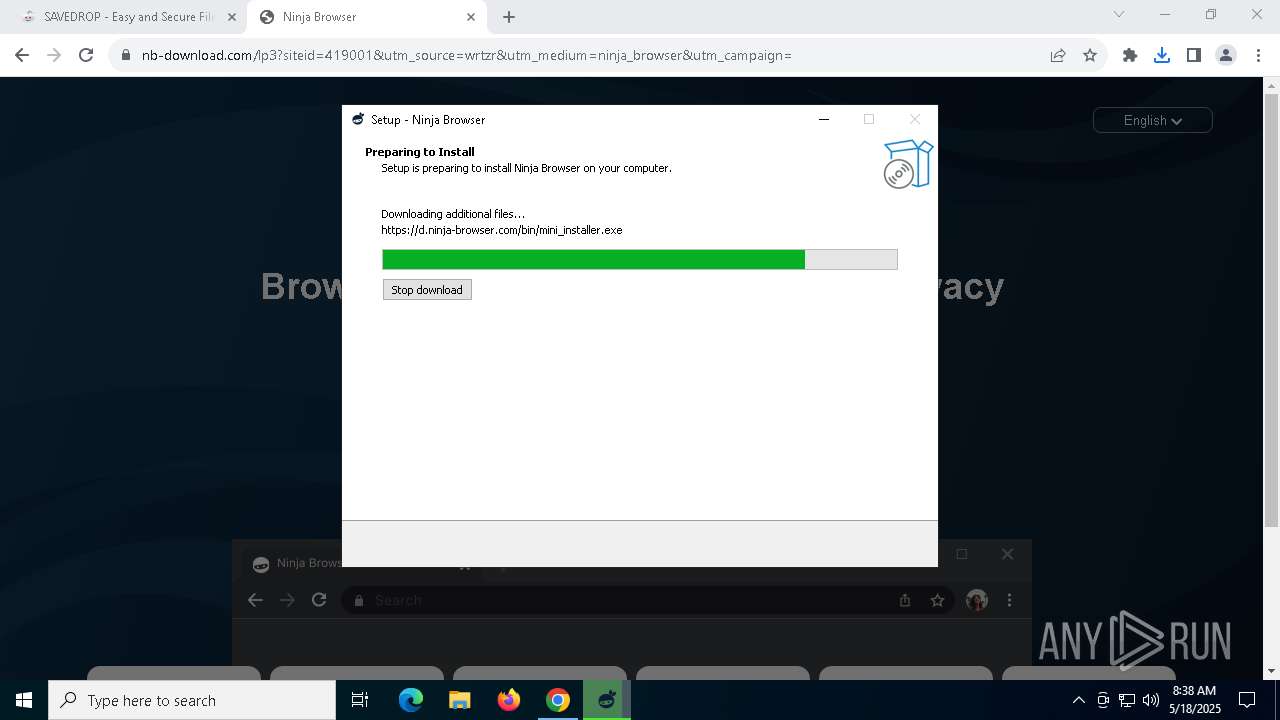
Executable content was dropped or overwritten
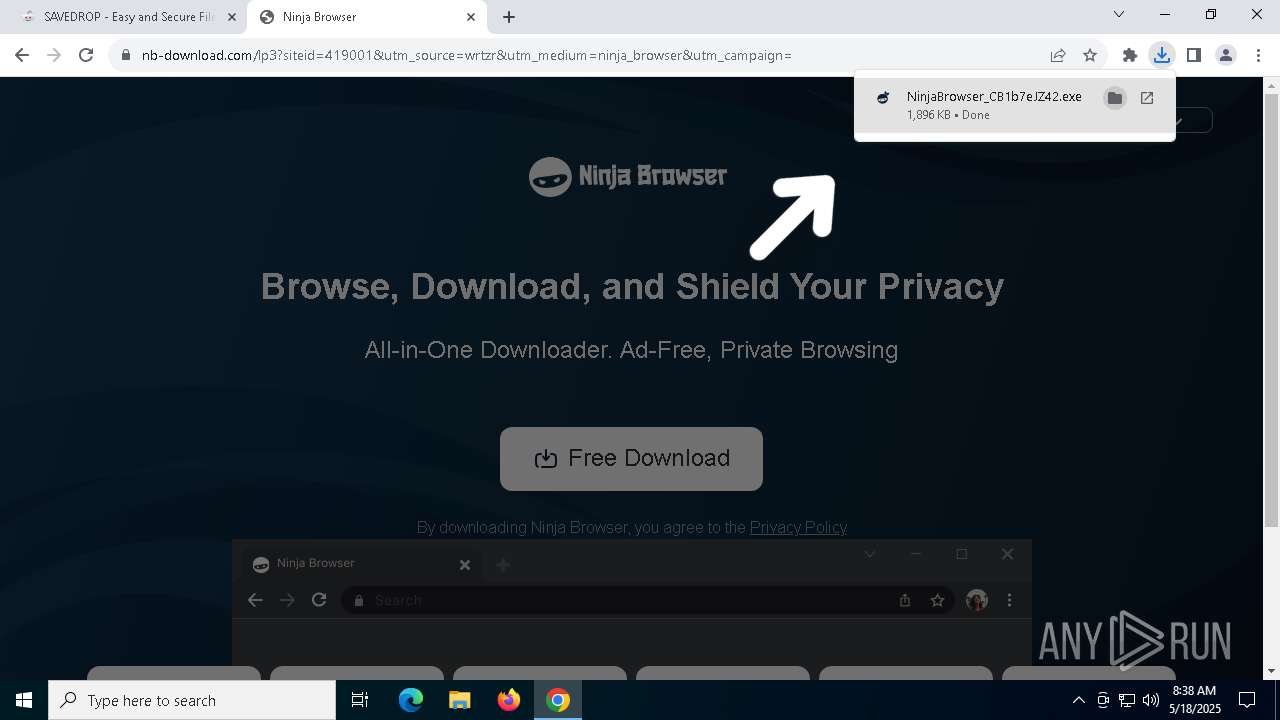
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6048)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- chromium.exe (PID: 8016)
- setup.exe (PID: 8036)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6252)
- chromium.exe (PID: 7876)
- setup.exe (PID: 7916)
Reads security settings of Internet Explorer
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 6744)
Reads the Windows owner or organization settings
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
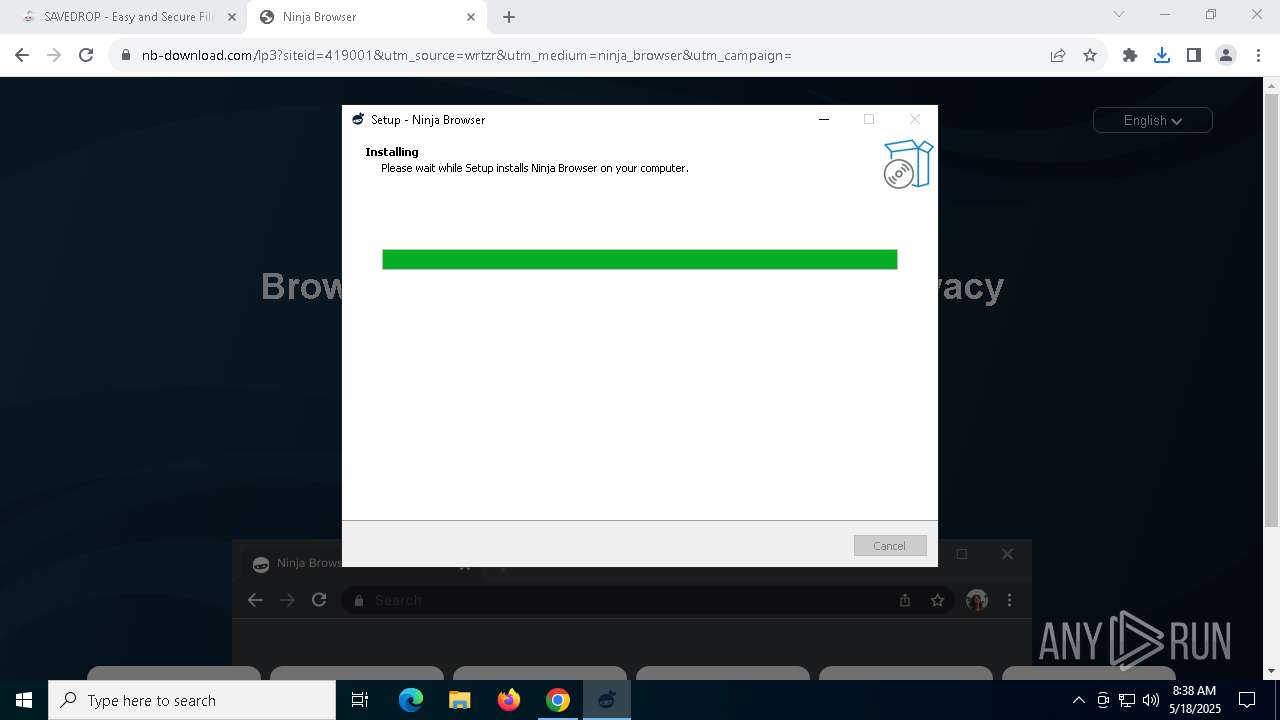
Searches for installed software
- setup.exe (PID: 8036)
- setup.exe (PID: 920)
- setup.exe (PID: 7916)
Creates a software uninstall entry
- setup.exe (PID: 8036)
Application launched itself
- setup.exe (PID: 8036)
- NinjaBrowser.exe (PID: 6512)
- chrmstp.exe (PID: 7840)
INFO
Checks supported languages
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6252)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 6744)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6048)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- chromium.exe (PID: 8016)
- setup.exe (PID: 8036)
- setup.exe (PID: 920)
- setup.exe (PID: 7916)
- def.exe (PID: 1012)
- def.exe (PID: 3176)
- def.exe (PID: 236)
- def.exe (PID: 7980)
- def.exe (PID: 5416)
- NinjaBrowser.exe (PID: 7932)
- NinjaBrowser.exe (PID: 6512)
- NinjaBrowser.exe (PID: 4932)
- NinjaBrowser.exe (PID: 5400)
- NinjaBrowser.exe (PID: 6480)
- chromium.exe (PID: 7876)
- NinjaBrowser.exe (PID: 7228)
- NinjaBrowser.exe (PID: 5796)
- NinjaBrowser.exe (PID: 7100)
- NinjaBrowser.exe (PID: 8116)
- NinjaBrowser.exe (PID: 8184)
- NinjaBrowser.exe (PID: 1300)
- NinjaBrowser.exe (PID: 2692)
- NinjaBrowser.exe (PID: 8128)
- NinjaBrowser.exe (PID: 2136)
- NinjaBrowser.exe (PID: 7084)
- NinjaBrowser.exe (PID: 6388)
- NinjaBrowser.exe (PID: 3176)
- NinjaBrowser.exe (PID: 3096)
- NinjaBrowser.exe (PID: 1276)
- NinjaBrowser.exe (PID: 2980)
- NinjaBrowser.exe (PID: 1672)
- NinjaBrowser.exe (PID: 4300)
- NinjaBrowser.exe (PID: 7948)
- NinjaBrowser.exe (PID: 3884)
- NinjaBrowser.exe (PID: 6136)
Application launched itself
- chrome.exe (PID: 7352)
Create files in a temporary directory
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6252)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6048)
- chromium.exe (PID: 8016)
- chromium.exe (PID: 7876)
- def.exe (PID: 3176)
- def.exe (PID: 1012)
- def.exe (PID: 7980)
- NinjaBrowser.exe (PID: 6512)
Reads the computer name
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 6744)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6048)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- chromium.exe (PID: 8016)
- setup.exe (PID: 8036)
- setup.exe (PID: 920)
- def.exe (PID: 5416)
- def.exe (PID: 1012)
- def.exe (PID: 3176)
- def.exe (PID: 236)
- def.exe (PID: 7980)
- NinjaBrowser.exe (PID: 6512)
- NinjaBrowser.exe (PID: 7932)
- chromium.exe (PID: 7876)
- NinjaBrowser.exe (PID: 5400)
Reads the software policy settings
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- slui.exe (PID: 1812)
Process checks computer location settings
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 6744)
- NinjaBrowser.exe (PID: 6512)
- NinjaBrowser.exe (PID: 6480)
- NinjaBrowser.exe (PID: 8184)
Creates files in the program directory
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- setup.exe (PID: 8036)
- setup.exe (PID: 920)
- setup.exe (PID: 7916)
The sample compiled with english language support
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- chromium.exe (PID: 8016)
- chrome.exe (PID: 7260)
- setup.exe (PID: 8036)
- chromium.exe (PID: 7876)
- setup.exe (PID: 7916)
Checks proxy server information
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- NinjaBrowser.exe (PID: 6512)
Detects InnoSetup installer (YARA)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 6744)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6252)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6048)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
Executable content was dropped or overwritten
- chrome.exe (PID: 7260)
- chrome.exe (PID: 7352)
Compiled with Borland Delphi (YARA)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 6744)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6048)
- NinjaBrowser_CB1b7eJZ42.tmp (PID: 5352)
- NinjaBrowser_CB1b7eJZ42.exe (PID: 6252)
Creates files or folders in the user directory
- setup.exe (PID: 920)
- NinjaBrowser.exe (PID: 6512)
- NinjaBrowser.exe (PID: 7932)
Reads Internet Explorer settings
- mshta.exe (PID: 6572)
- mshta.exe (PID: 7924)
- mshta.exe (PID: 7100)
- mshta.exe (PID: 7276)
- mshta.exe (PID: 4868)
- mshta.exe (PID: 7996)
Reads the machine GUID from the registry
- NinjaBrowser.exe (PID: 6512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
284
Monitored processes
144
Malicious processes
12
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Users\admin\AppData\Local\Temp\is-CMNOL.tmp\def.exe" .htm ChromiumHTM | C:\Users\admin\AppData\Local\Temp\is-CMNOL.tmp\def.exe | — | NinjaBrowser_CB1b7eJZ42.tmp | |||||||||||
User: admin Company: Kolbi.cz Integrity Level: HIGH Description: SetUserFTA from http://kolbi.cz Exit code: 0 Version: 1.8.2 Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | def.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=renderer --extension-process --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=60 --field-trial-handle=10388,i,4267283088217997687,15913306841845290304,262144 --variations-seed-version --mojo-platform-channel-handle=6508 /prefetch:2 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 135.0.6613.124 Modules
| |||||||||||||||
| 920 | "C:\Users\admin\AppData\Local\Temp\is-CMNOL.tmp\CR_95510.tmp\setup.exe" --system-level --verbose-logging --create-shortcuts=0 --install-level=1 | C:\Users\admin\AppData\Local\Temp\is-CMNOL.tmp\CR_95510.tmp\setup.exe | — | setup.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: HIGH Description: Ninja Browser Installer Exit code: 73 Version: 135.0.6613.124 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Local\Temp\is-CMNOL.tmp\def.exe" http ChromiumHTM | C:\Users\admin\AppData\Local\Temp\is-CMNOL.tmp\def.exe | — | NinjaBrowser_CB1b7eJZ42.tmp | |||||||||||
User: admin Company: Kolbi.cz Integrity Level: HIGH Description: SetUserFTA from http://kolbi.cz Exit code: 0 Version: 1.8.2 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --field-trial-handle=4944,i,4267283088217997687,15913306841845290304,262144 --variations-seed-version --mojo-platform-channel-handle=8264 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 135.0.6613.124 Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --field-trial-handle=8636,i,4267283088217997687,15913306841845290304,262144 --variations-seed-version --mojo-platform-channel-handle=8912 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: MEDIUM Description: Ninja Browser Exit code: 0 Version: 135.0.6613.124 Modules
| |||||||||||||||
| 1276 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --field-trial-handle=6720,i,4267283088217997687,15913306841845290304,262144 --variations-seed-version --mojo-platform-channel-handle=6728 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 135.0.6613.124 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --field-trial-handle=3888,i,4267283088217997687,15913306841845290304,262144 --variations-seed-version --mojo-platform-channel-handle=2432 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 135.0.6613.124 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6084 --field-trial-handle=1876,i,1417489304133757490,10974311334667645750,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
24 423
Read events
23 902
Write events
475
Delete events
46
Modification events
| (PID) Process: | (7352) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7352) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7352) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7352) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7352) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7352) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000CB3D2832D0C7DB01 | |||
| (PID) Process: | (8036) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\NinjaBrowser |
| Operation: | write | Name: | InstallerProgress |
Value: 19 | |||
| (PID) Process: | (8036) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\NinjaBrowser |
| Operation: | write | Name: | InstallerProgress |
Value: 25 | |||
| (PID) Process: | (7352) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\RLZs |
| Operation: | write | Name: | C1 |
Value: 1C1GCEB_enFR1162FR1162 | |||
Executable files
30
Suspicious files
1 125
Text files
946
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10cbed.TMP | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10cbed.TMP | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10cbed.TMP | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10cbed.TMP | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10cbed.TMP | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
106
DNS requests
136
Threats
71
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5392 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7352 | chrome.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDB4WVKmt8yfHHrQPdw%3D%3D | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7352 | chrome.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1852 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.15:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7352 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7704 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
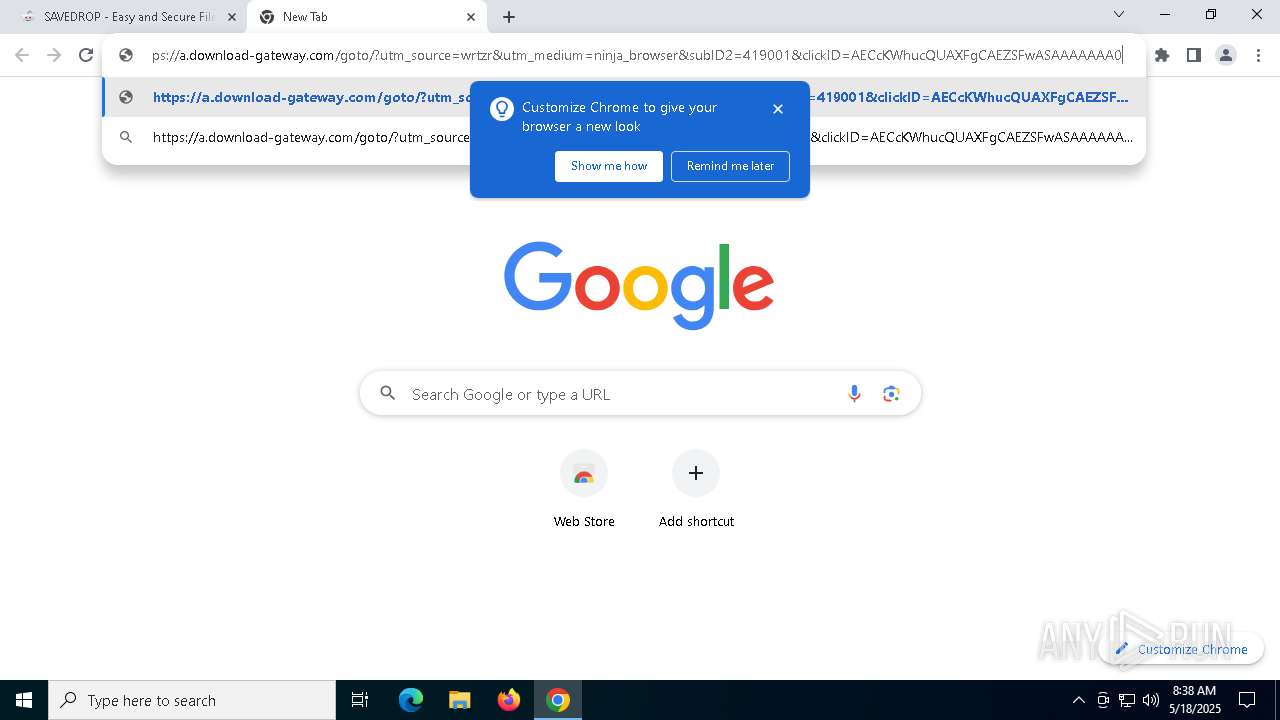
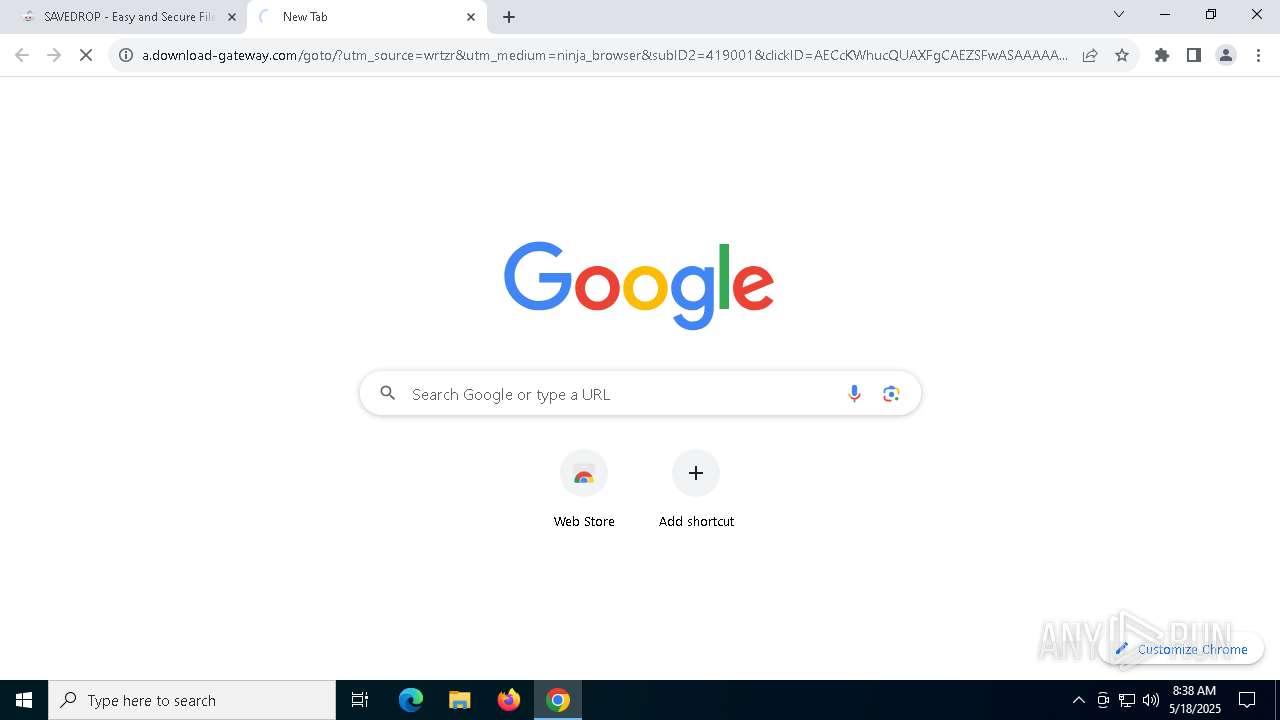
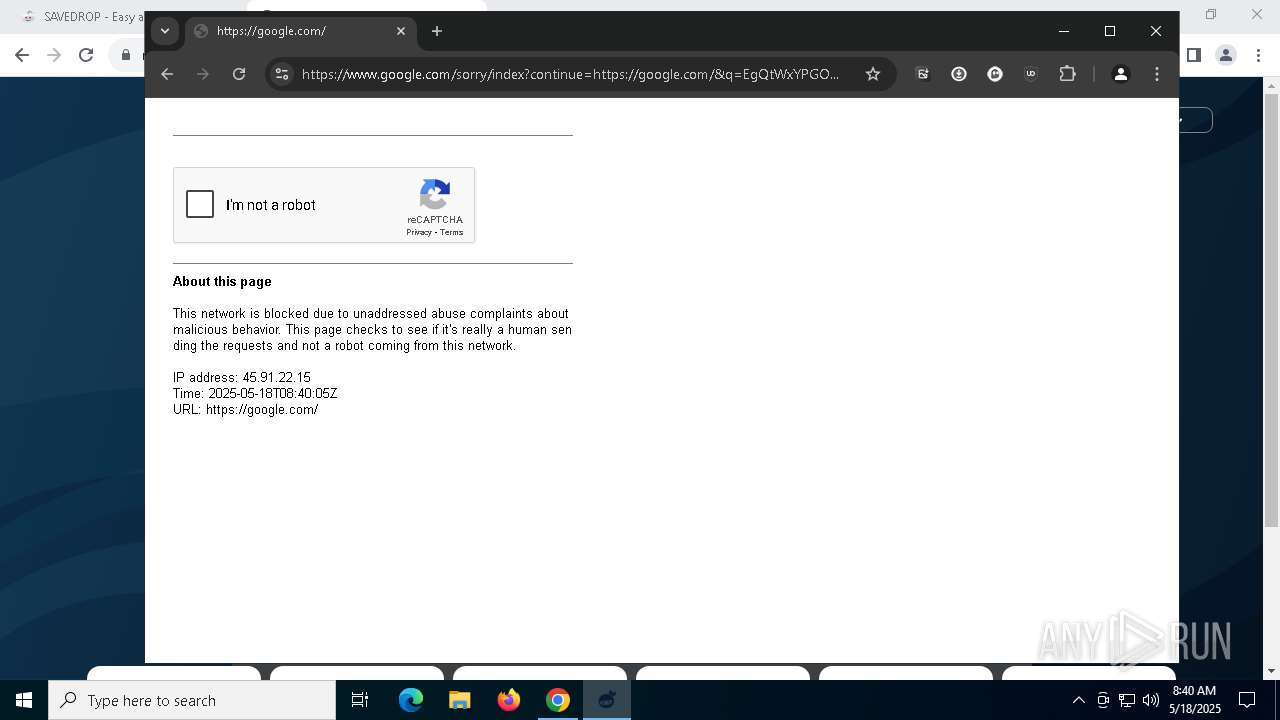
7704 | chrome.exe | 104.21.23.186:443 | thetotoro.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
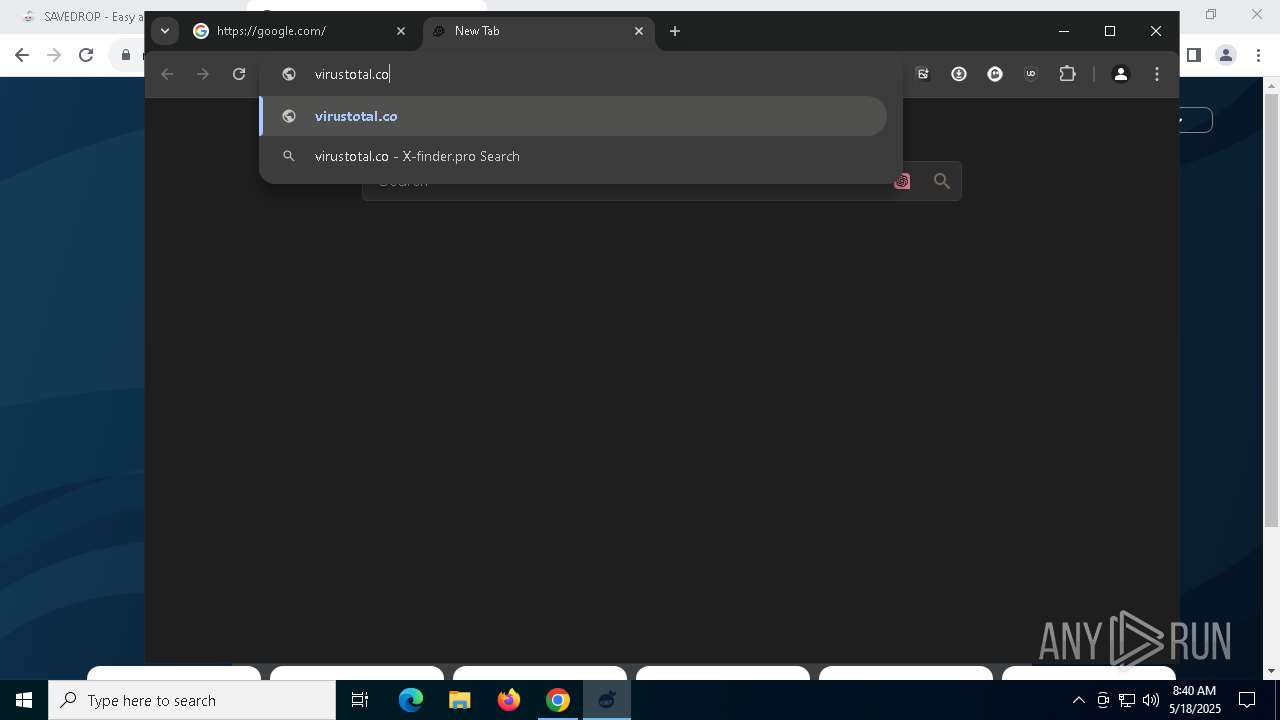
thetotoro.com |
| unknown |
accounts.google.com |
| whitelisted |
www.rolltrk4.com |
| unknown |
pixeltrey.com |
| unknown |
infoaccessnetwork.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
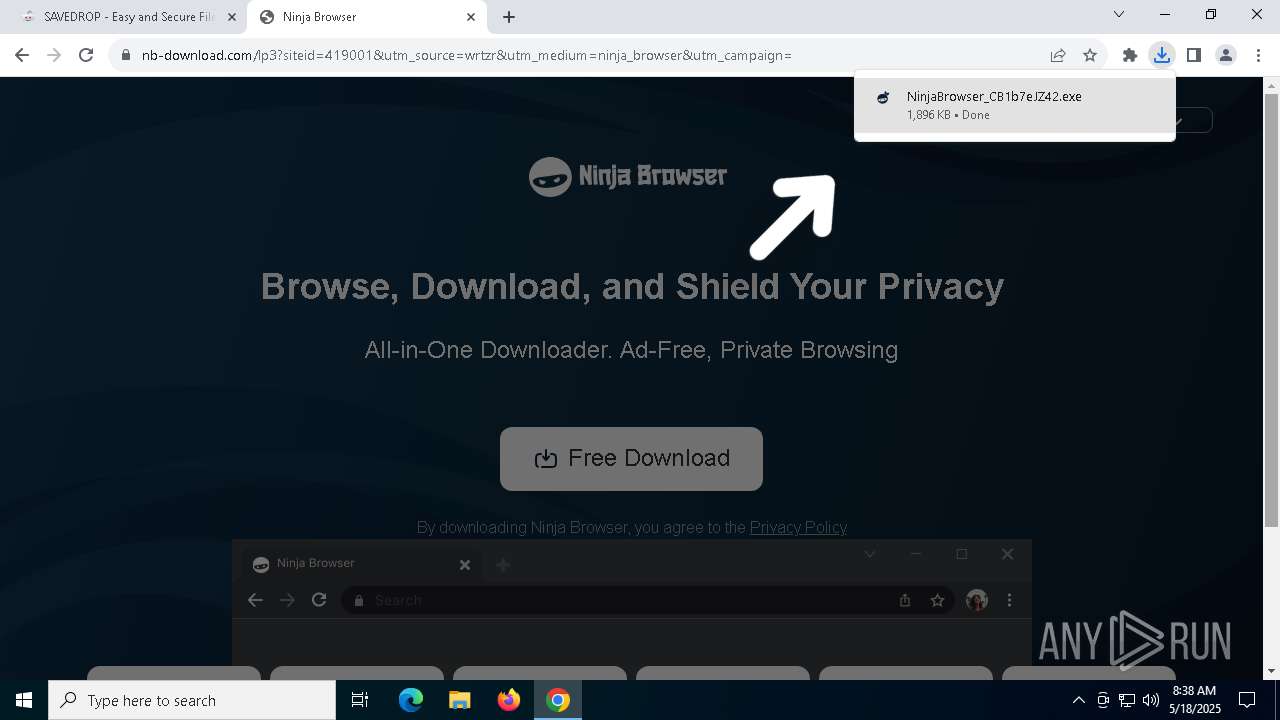
7704 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain (nb-download .com) |
7704 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain (nb-download .com) |
7704 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain (nb-download .com) |
7704 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain (nb-download .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .ninja-browser .com) |
7932 | NinjaBrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |