| URL: | http://43c6k.r.ah.d.sendibm4.com/mk/cl/f/bybsI3cFsSrNMltIXOY2-yL7W1fcmNh1RdjOw2tOr_rs3NAIPJKXa7GckwRM8YE7GfkCojgLx4CJupnjbzZw4PFyH7mKjJCAOItPxLKytlYFXIg9HDlHOO2RpAf6whLkI9WKHROr9e0iUhsRKiZU4hfeO_ynhgvZPWoC6wNCBs4wa2oKBCMZzZlGaKAow3kRJWcxwRzG8_rJEGOmsU4gavdomvhRcEngyKNi_or-CuOwFIsbpfCFdw_jqnTQBgvOKVKksATp75Gv0AjymwcTyzShcqjC8-ys0GZ4Dm8BPS0RLTP1-w |
| Full analysis: | https://app.any.run/tasks/13698ebb-fc44-4629-a432-51f6cccaadcb |
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2019, 08:15:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E9A9DD2BF2F8A1B7D5AFEC856B4AB142 |
| SHA1: | 86033CEADCECFC35A750E70987F8C81BE7A66D6F |
| SHA256: | 9F140C9BC1DB5A9356CB659632C841D44F271D688AC362E9258DEB9E68D9A8D6 |
| SSDEEP: | 6:CUqeBjYc/Pg8yaISSBJlgUEp9PRIWjI9kX1Ju8DDjuuJWSkpNxfJe3L30HXMGWYJ:nBpPg8j5SBJlgUE3PRIW0OXeYkNM3ql1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2720)
Application launched itself
- iexplore.exe (PID: 2720)
Creates files in the user directory
- iexplore.exe (PID: 3504)
Reads Internet Cache Settings
- iexplore.exe (PID: 3504)
Reads internet explorer settings
- iexplore.exe (PID: 3504)
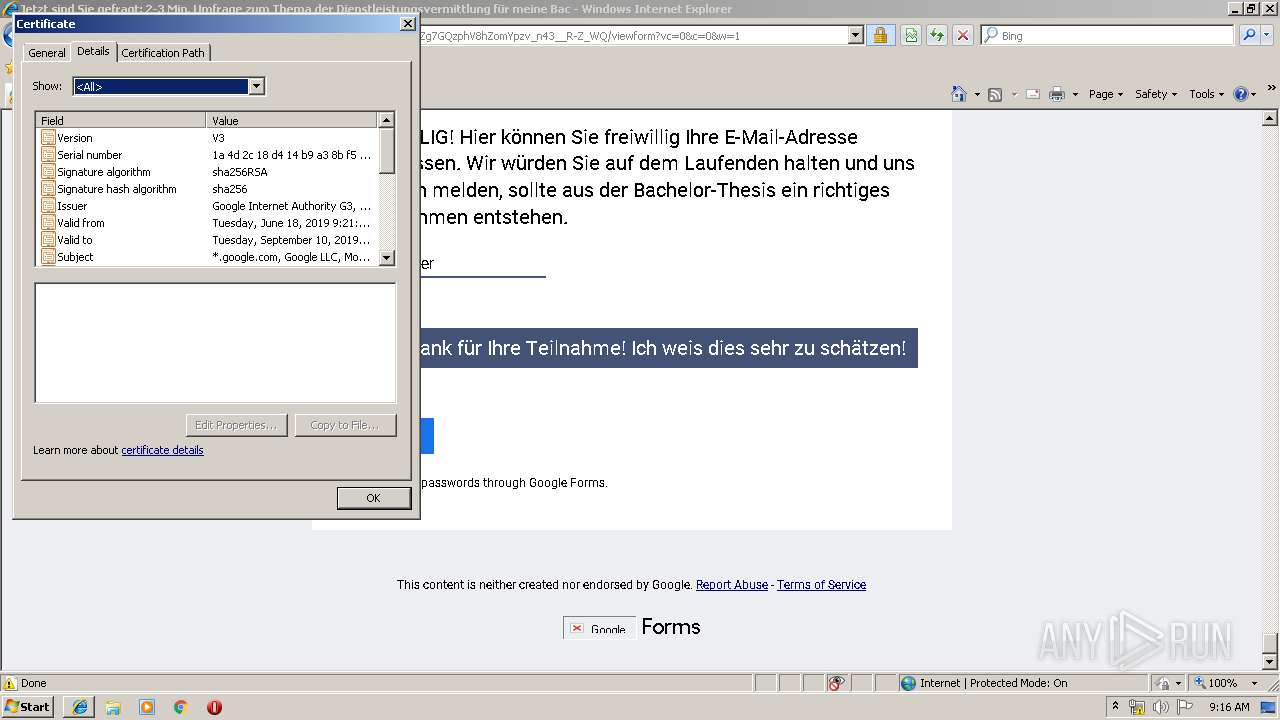
Reads settings of System Certificates
- iexplore.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2720 | "C:\Program Files\Internet Explorer\iexplore.exe" http://43c6k.r.ah.d.sendibm4.com/mk/cl/f/bybsI3cFsSrNMltIXOY2-yL7W1fcmNh1RdjOw2tOr_rs3NAIPJKXa7GckwRM8YE7GfkCojgLx4CJupnjbzZw4PFyH7mKjJCAOItPxLKytlYFXIg9HDlHOO2RpAf6whLkI9WKHROr9e0iUhsRKiZU4hfeO_ynhgvZPWoC6wNCBs4wa2oKBCMZzZlGaKAow3kRJWcxwRzG8_rJEGOmsU4gavdomvhRcEngyKNi_or-CuOwFIsbpfCFdw_jqnTQBgvOKVKksATp75Gv0AjymwcTyzShcqjC8-ys0GZ4Dm8BPS0RLTP1-w | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
402
Read events
347
Write events
55
Delete events
0
Modification events
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000078000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B87C8201-A221-11E9-95C0-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30707000200090008000F002100E602 | |||
Executable files
0
Suspicious files
0
Text files
13
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\8BW8CI0Y\O_ynhgvZPWoC6wNCBs4wa2oKBCMZzZlGaKAow3kRJWcxwRzG8_rJEGOmsU4gavdomvhRcEngyKNi_or-CuOwFIsbpfCFdw_jqnTQBgvOKVKksATp75Gv0AjymwcTyzShcqjC8-ys0GZ4Dm8BPS0RLTP1-w[1].txt | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RIMVM10U\viewform[1].txt | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RIMVM10U\rs=AMjVe6hkGBH8bmuJ3cC01Y3vAtgwpgZJAw[1].txt | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\8BW8CI0Y\googlelogo_dark_clr_74x24px[1].svg | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\THOJPES7\qp_sprite128[1].svg | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\THOJPES7\O_ynhgvZPWoC6wNCBs4wa2oKBCMZzZlGaKAow3kRJWcxwRzG8_rJEGOmsU4gavdomvhRcEngyKNi_or-CuOwFIsbpfCFdw_jqnTQBgvOKVKksATp75Gv0AjymwcTyzShcqjC8-ys0GZ4Dm8BPS0RLTP1-w[1].htm | html | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon_qp2[1].png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
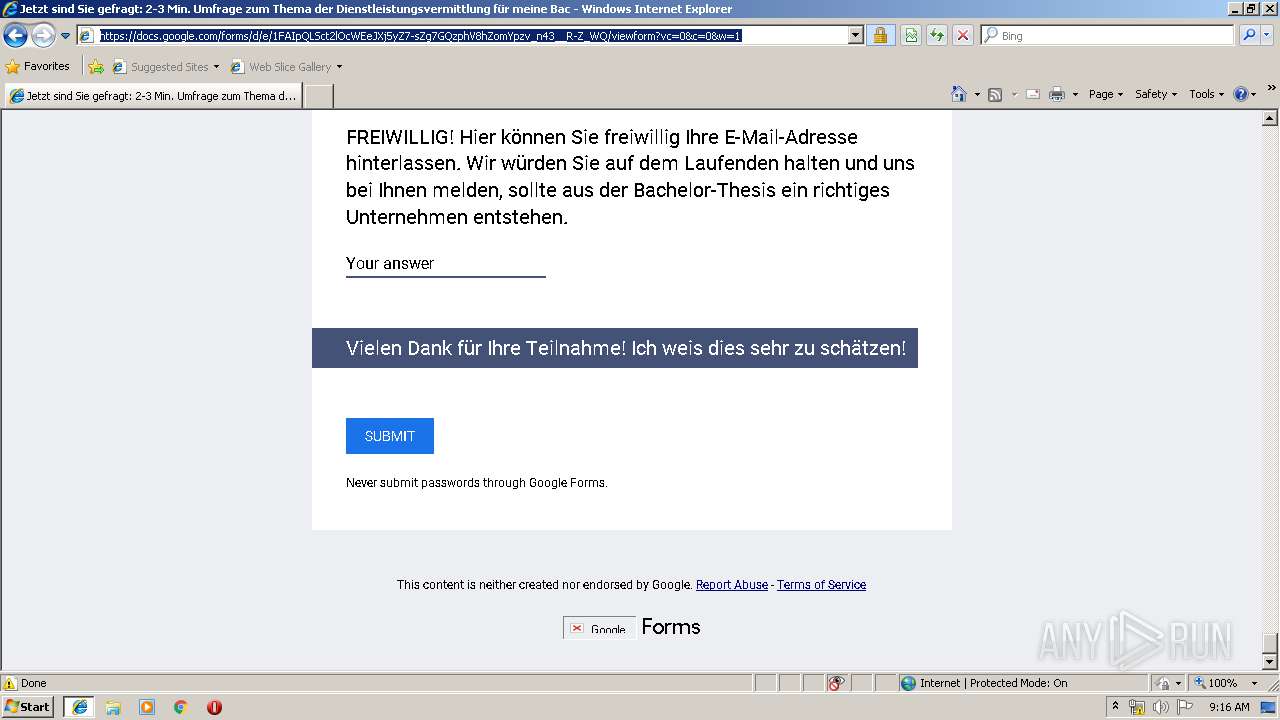
3504 | iexplore.exe | GET | 200 | 185.107.232.244:80 | http://43c6k.r.ah.d.sendibm4.com/mk/cl/f/bybsI3cFsSrNMltIXOY2-yL7W1fcmNh1RdjOw2tOr_rs3NAIPJKXa7GckwRM8YE7GfkCojgLx4CJupnjbzZw4PFyH7mKjJCAOItPxLKytlYFXIg9HDlHOO2RpAf6whLkI9WKHROr9e0iUhsRKiZU4hfeO_ynhgvZPWoC6wNCBs4wa2oKBCMZzZlGaKAow3kRJWcxwRzG8_rJEGOmsU4gavdomvhRcEngyKNi_or-CuOwFIsbpfCFdw_jqnTQBgvOKVKksATp75Gv0AjymwcTyzShcqjC8-ys0GZ4Dm8BPS0RLTP1-w | FR | html | 743 b | suspicious |
2720 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | iexplore.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3504 | iexplore.exe | 185.107.232.244:80 | 43c6k.r.ah.d.sendibm4.com | Sendinblue SAS | FR | suspicious |
2720 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
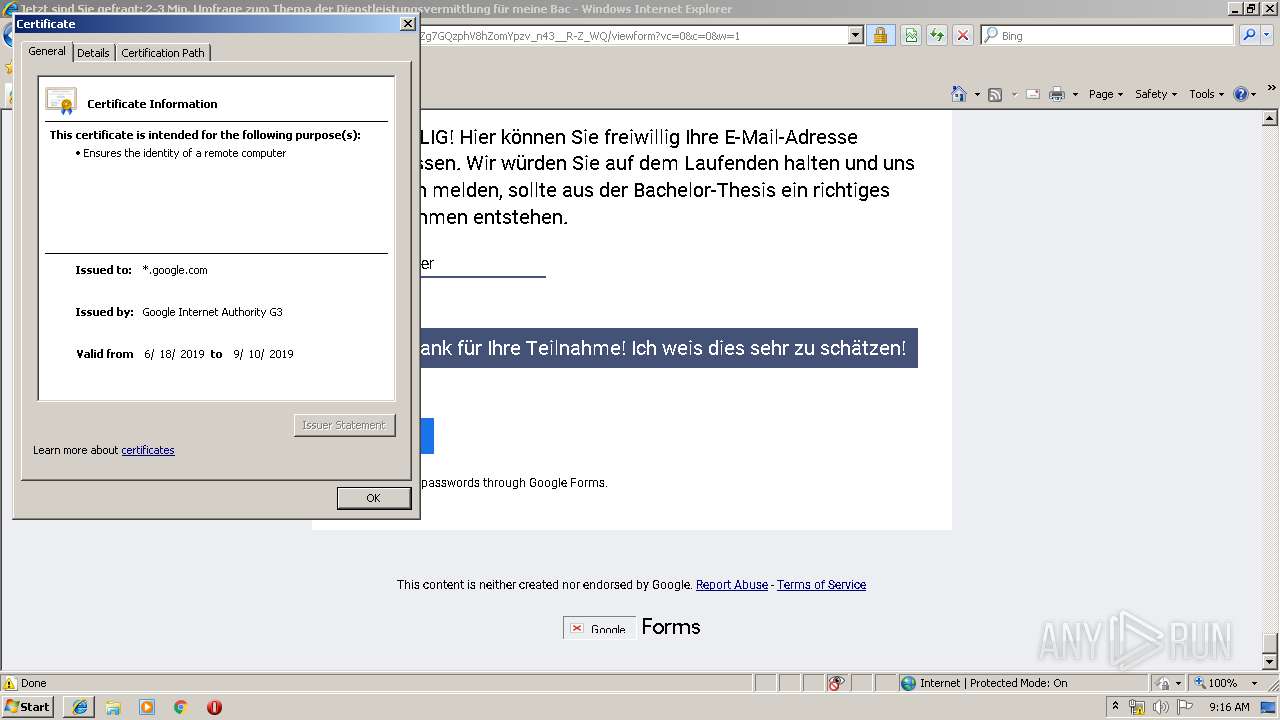
— | — | 172.217.22.14:443 | docs.google.com | Google Inc. | US | whitelisted |
3504 | iexplore.exe | 172.64.129.16:443 | sibautomation.com | Cloudflare Inc | US | shared |
2720 | iexplore.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3504 | iexplore.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3504 | iexplore.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3504 | iexplore.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3504 | iexplore.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
43c6k.r.ah.d.sendibm4.com |
| suspicious |
sibautomation.com |
| whitelisted |
www.bing.com |
| whitelisted |
docs.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |