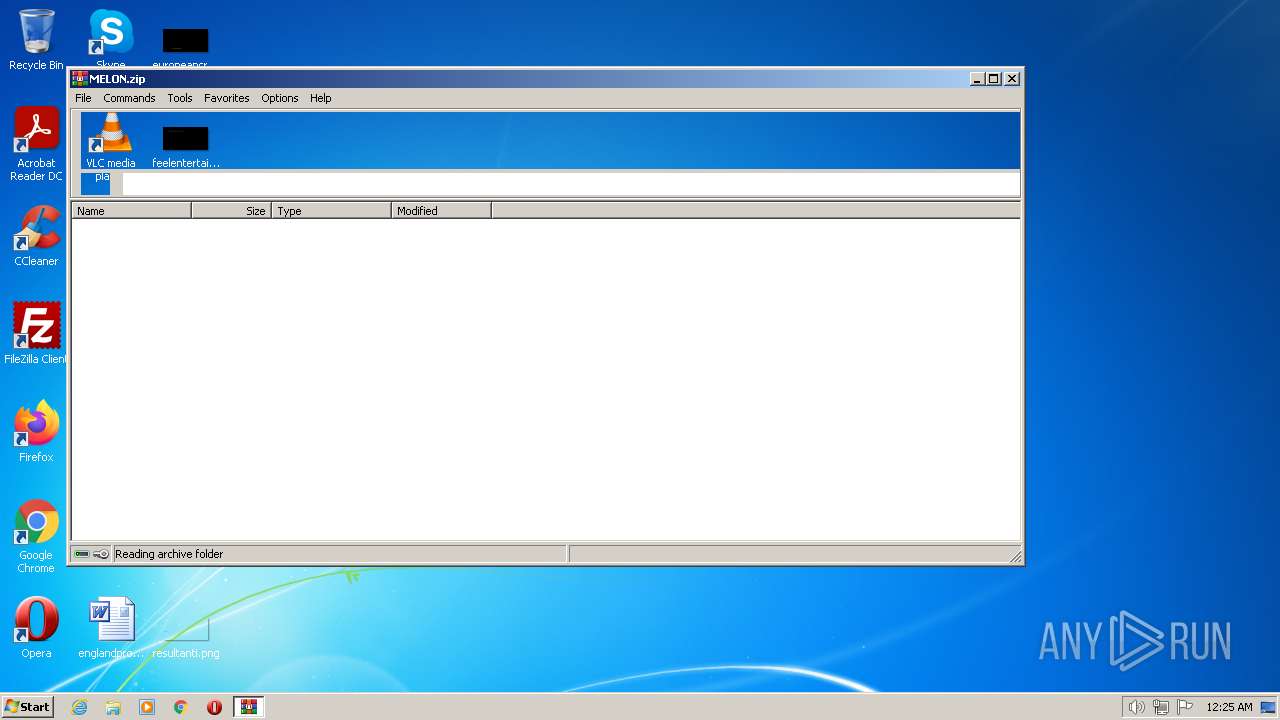
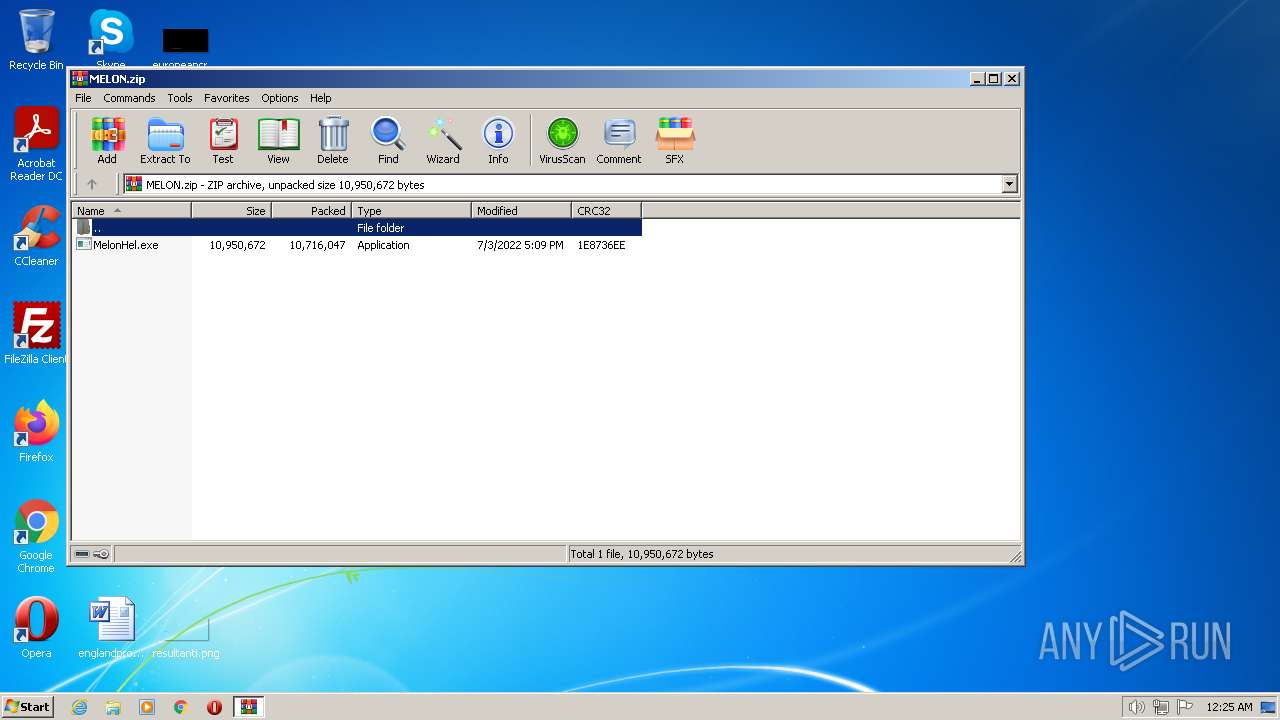
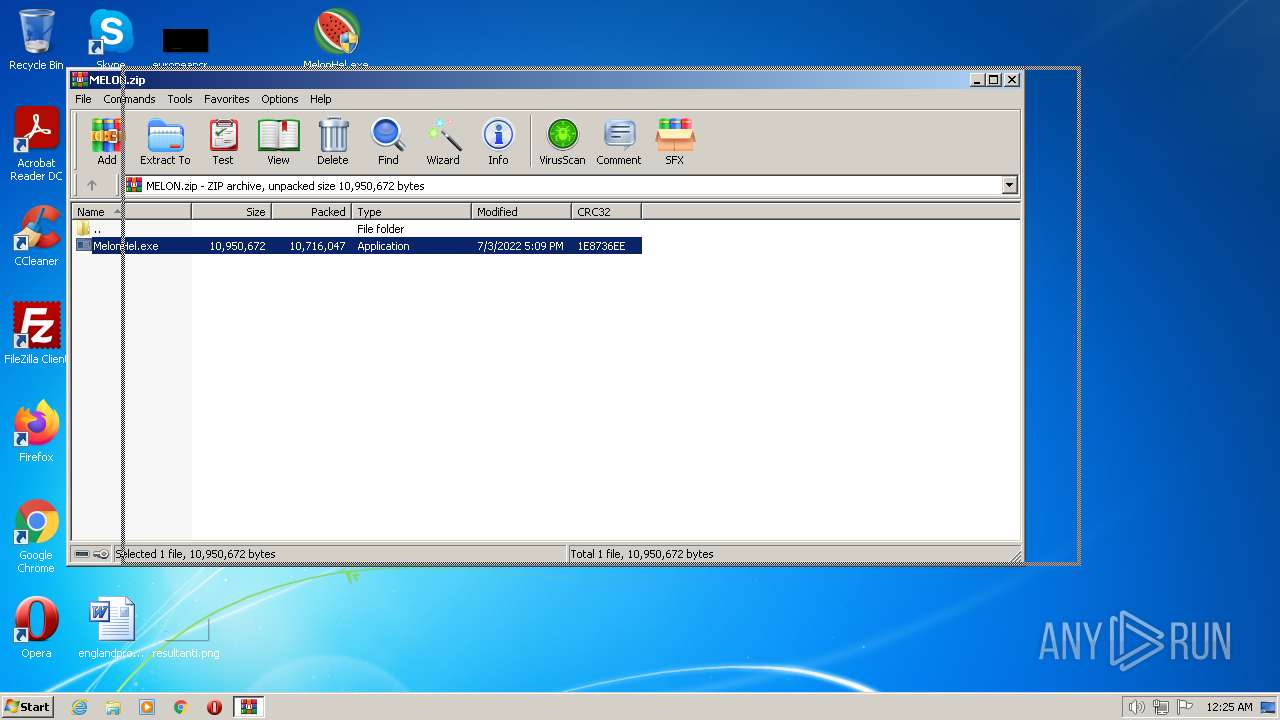
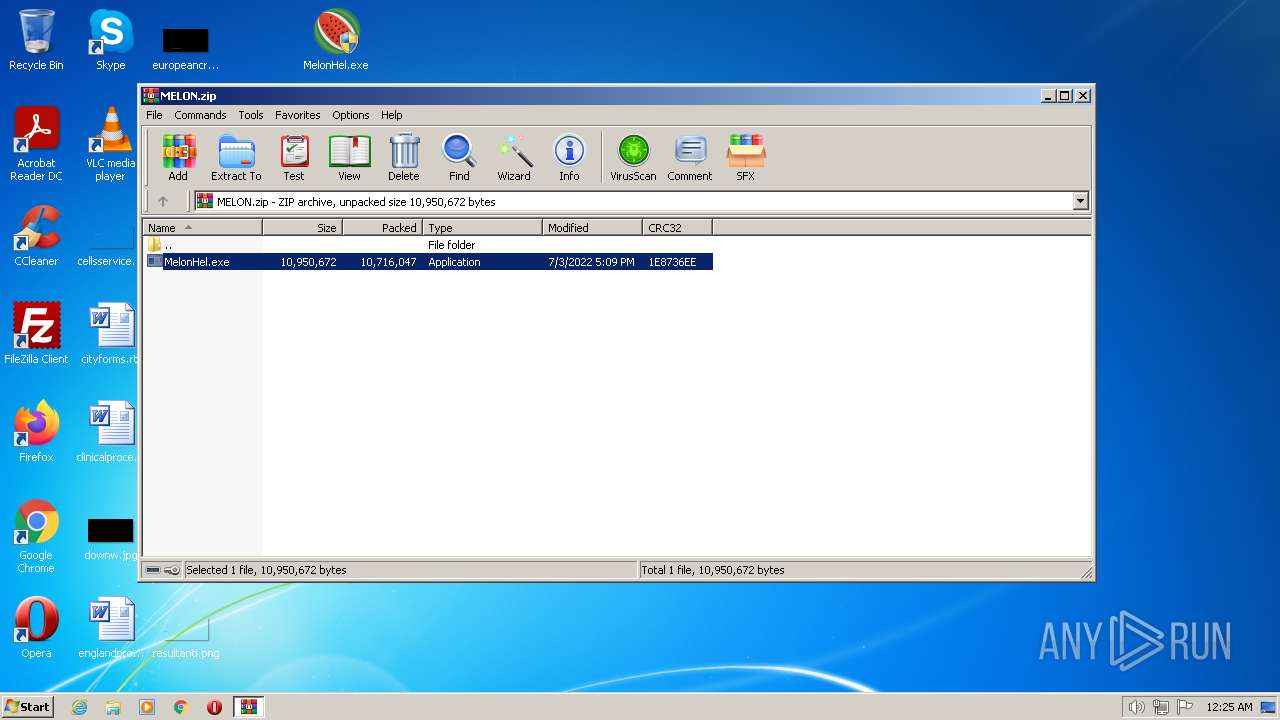
| File name: | MELON.zip |
| Full analysis: | https://app.any.run/tasks/91a35516-aa44-428f-b356-209164a467a6 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 00:25:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E43CE8C06AB93ED1CE56090053C35418 |
| SHA1: | 7FD119A282CC14513E0C4B00E2700E6685CB73E9 |
| SHA256: | 9F09DB949D940FA8650F69FBEC7F6B08730C92733039FBCCE918E08DA0975924 |
| SSDEEP: | 196608:6gTqeMhZdrlhZsFiw1ngxaxwbLFjSUcO1tfntMD6uRL5ms3dmQ1Cr:6gTZMhVhZs7gkgSUT1RtC6u96 |
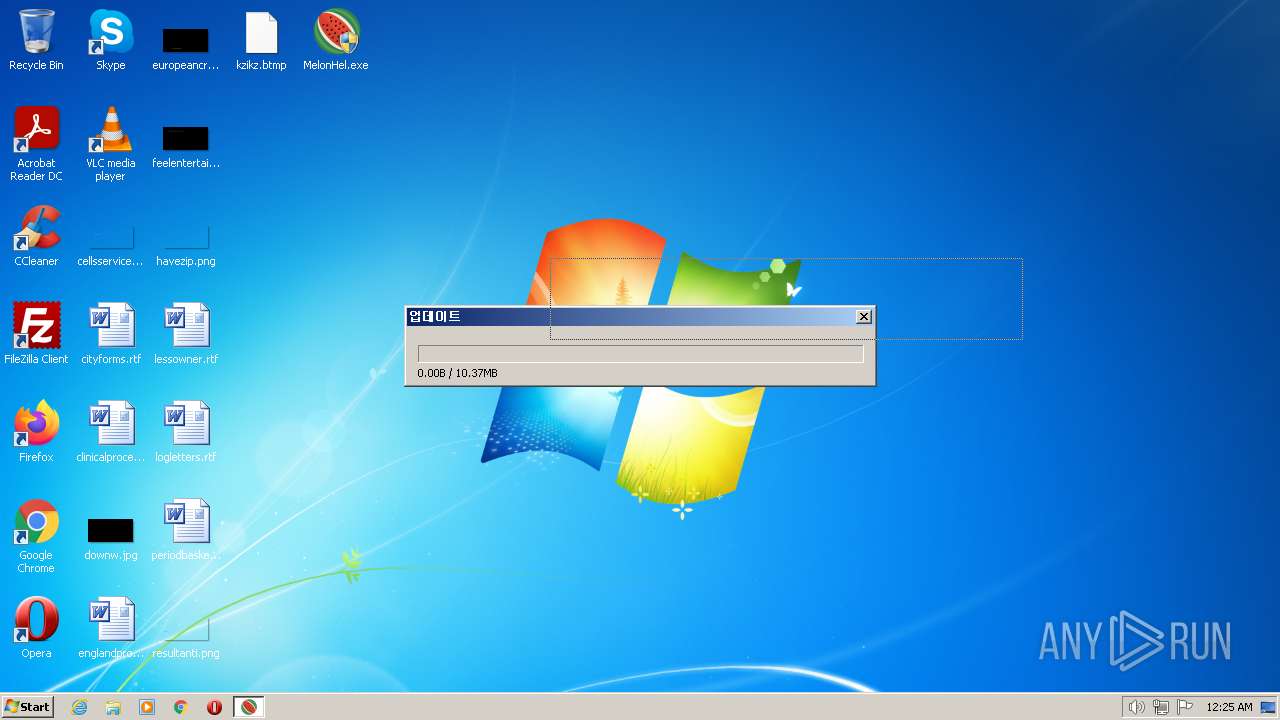
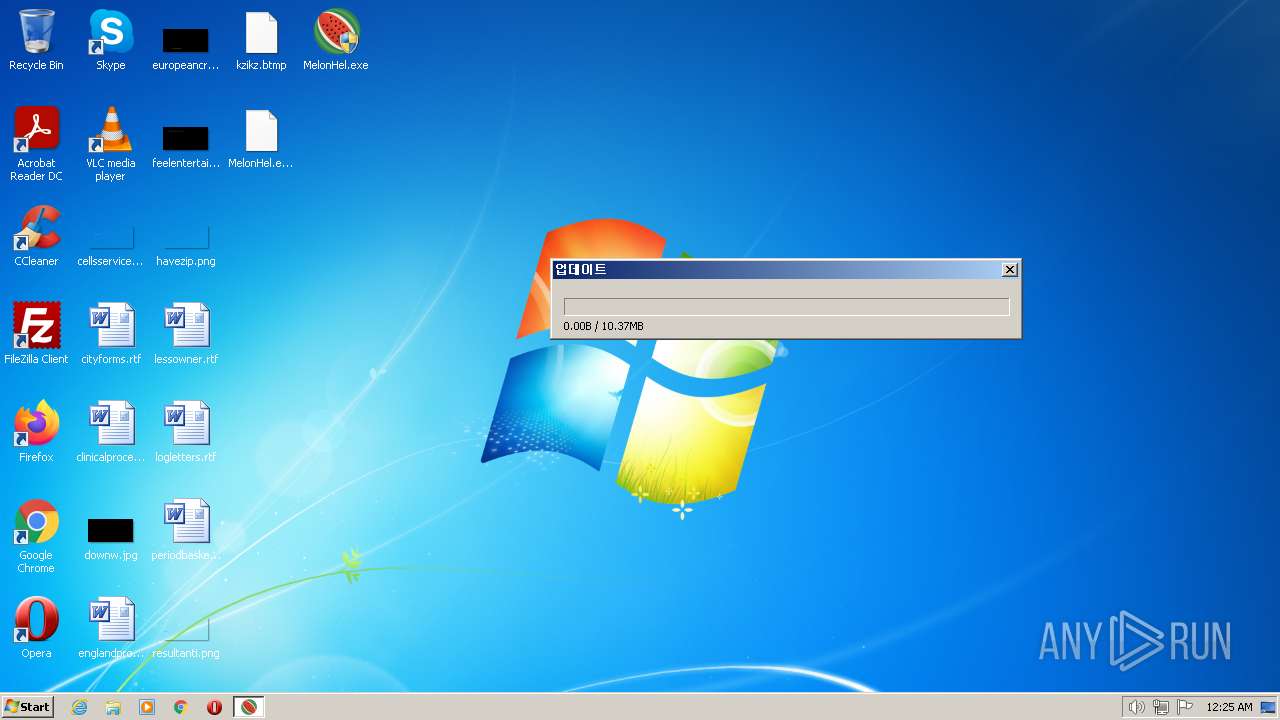
MALICIOUS
Application was dropped or rewritten from another process
- MelonHel.exe (PID: 2160)
- kzikz.btmp (PID: 1588)
SUSPICIOUS
Reads the BIOS version
- kzikz.btmp (PID: 1588)
- MelonHel.exe (PID: 2160)
Connects to unusual port
- kzikz.btmp (PID: 1588)
Starts itself from another location
- MelonHel.exe (PID: 2160)
INFO
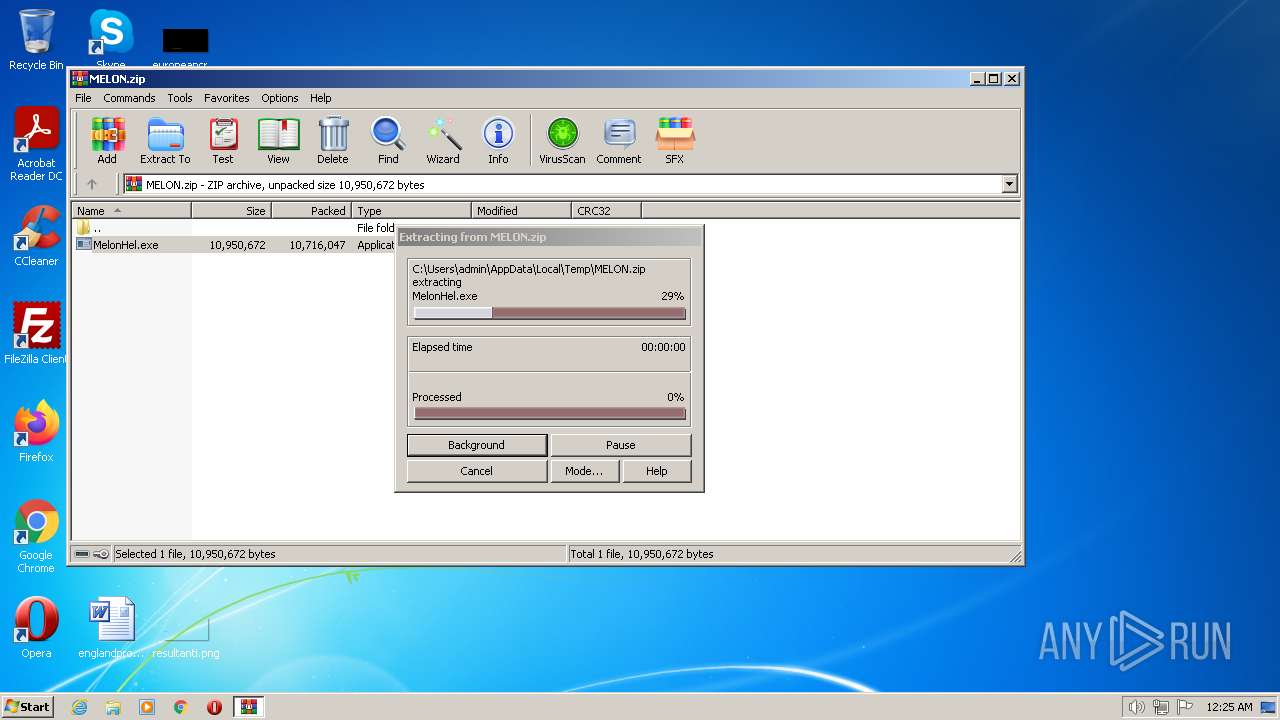
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1752)
Checks supported languages
- MelonHel.exe (PID: 2160)
- kzikz.btmp (PID: 1588)
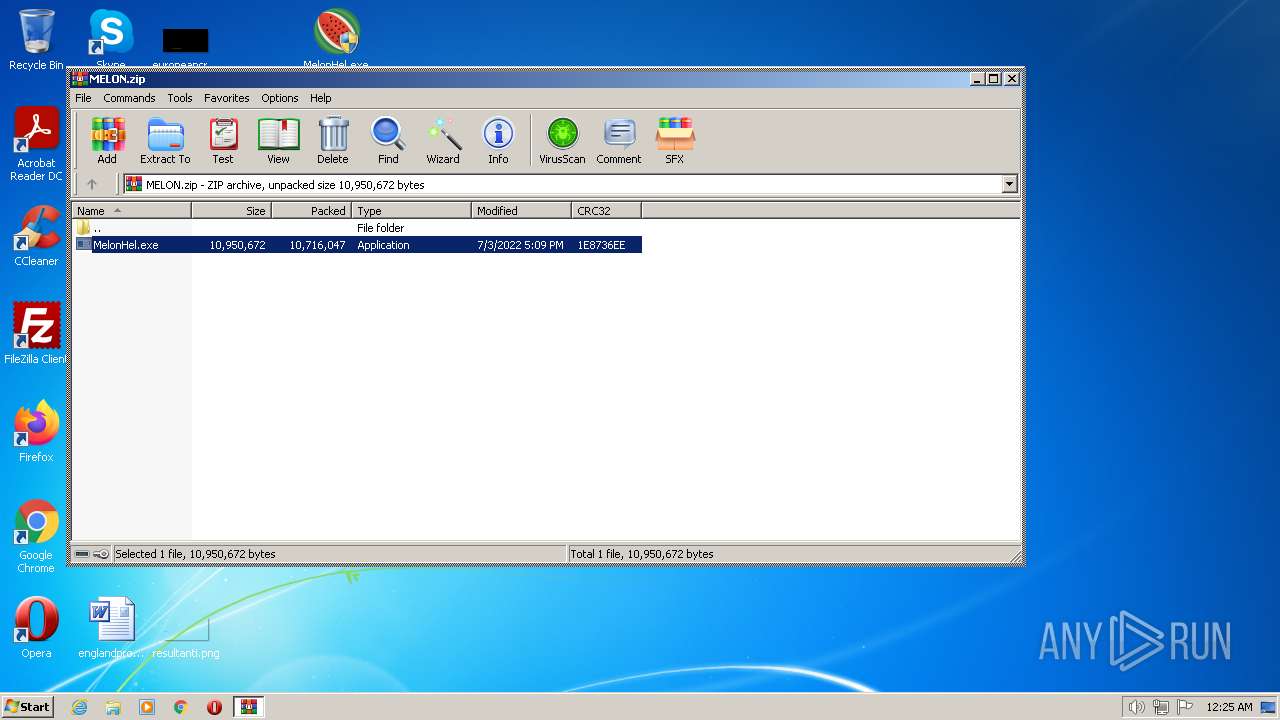
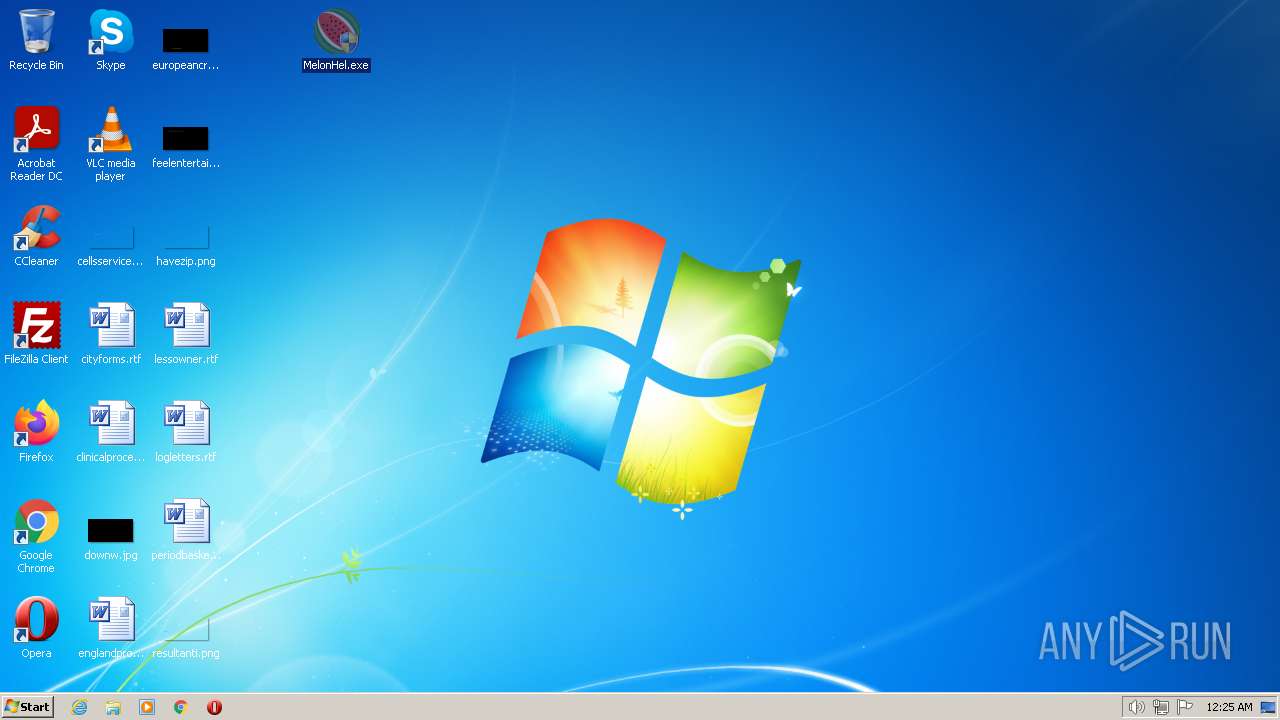
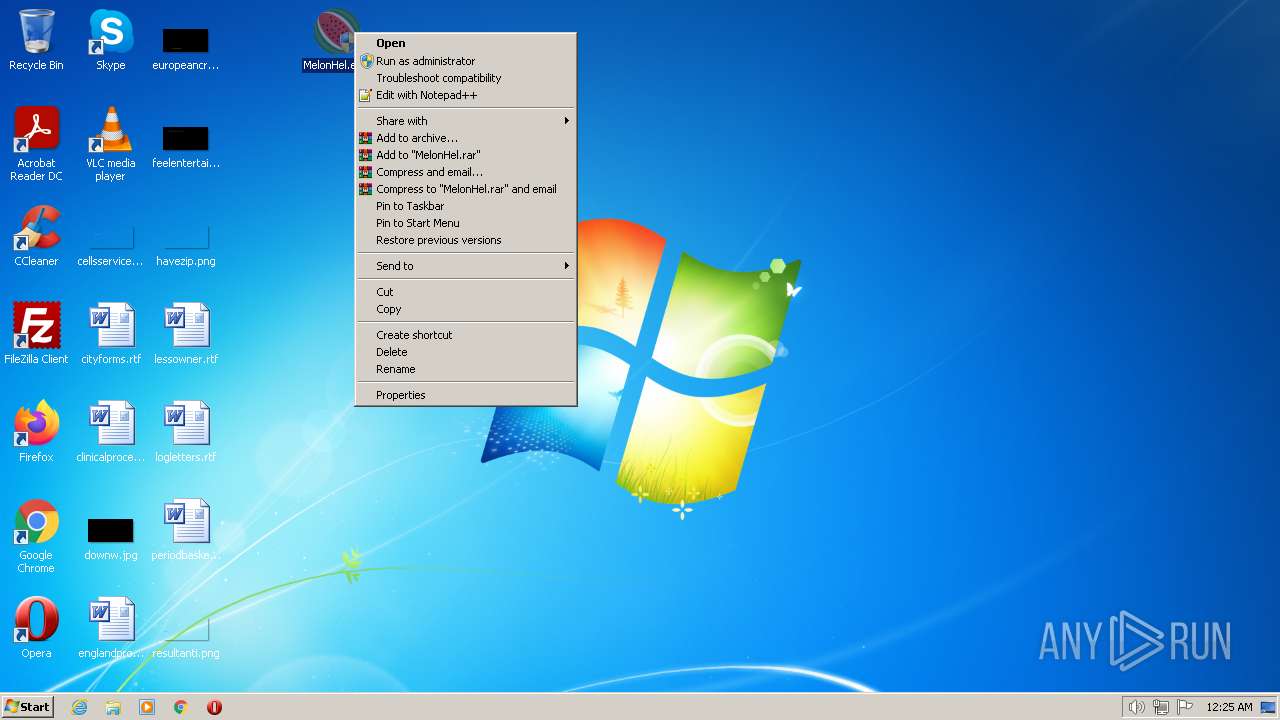
Manual execution by a user
- MelonHel.exe (PID: 2160)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1752)
Reads the computer name
- kzikz.btmp (PID: 1588)
Process checks are UAC notifies on
- kzikz.btmp (PID: 1588)
- MelonHel.exe (PID: 2160)
Reads Environment values
- kzikz.btmp (PID: 1588)
Starts application with an unusual extension
- MelonHel.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
44
Monitored processes
4
Malicious processes
2
Suspicious processes
0
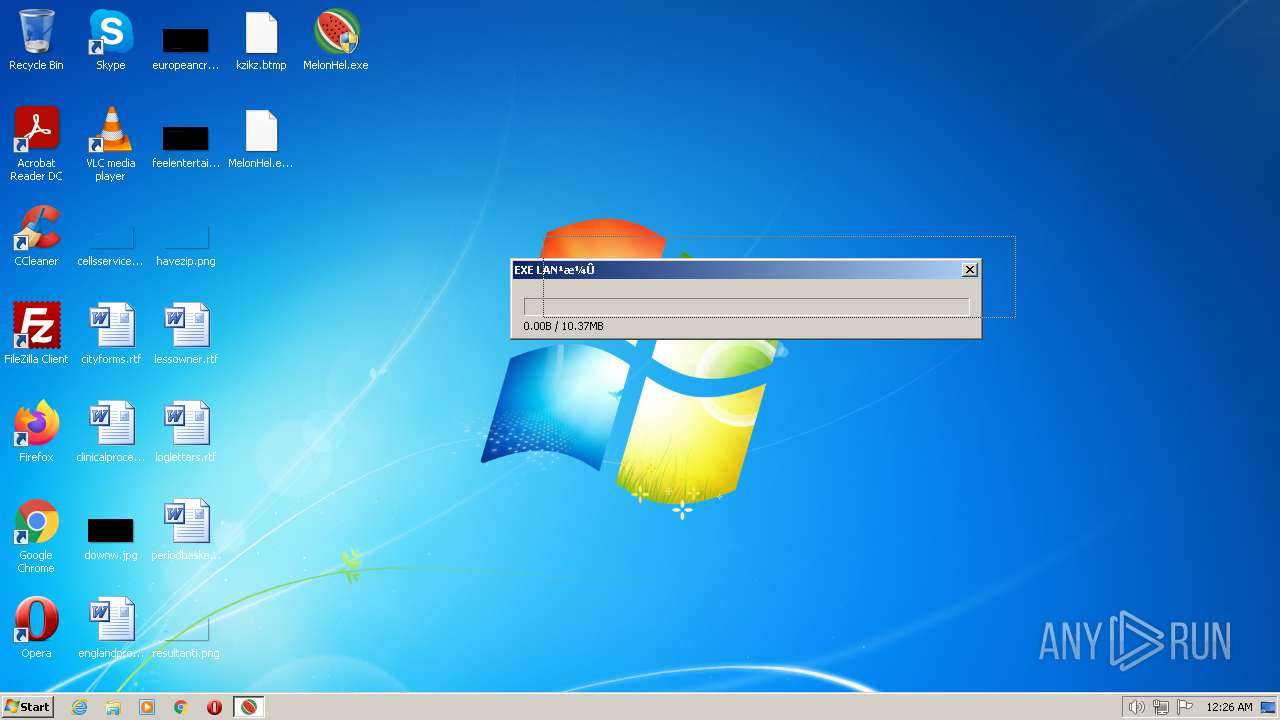
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1588 | "C:\Users\admin\Desktop\MelonHel.exe" | C:\Users\admin\Desktop\kzikz.btmp | MelonHel.exe | ||||||||||||
User: admin Company: MelonAuto Integrity Level: HIGH Description: LinM_Auto Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MELON.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\Desktop\MelonHel.exe" | C:\Users\admin\Desktop\MelonHel.exe | Explorer.EXE | ||||||||||||
User: admin Company: MelonAuto Integrity Level: HIGH Description: LinM_Auto Exit code: 4294967295 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2860 | C:\Windows\system32\cmd.exe /c del *.btmp | C:\Windows\system32\cmd.exe | — | MelonHel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 360
Read events
2 329
Write events
31
Delete events
0
Modification events
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MELON.zip | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
0
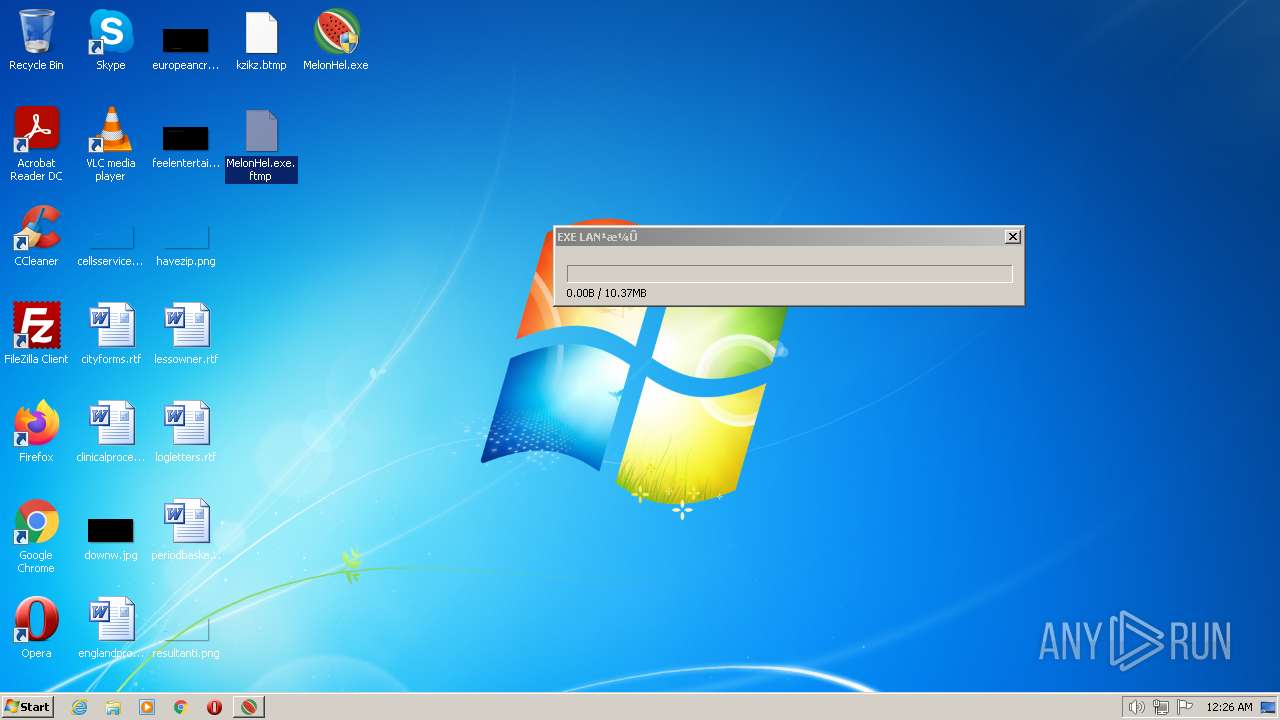
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1588 | kzikz.btmp | C:\Users\admin\Desktop\MelonHel.exe.ftmp | — | |
MD5:— | SHA256:— | |||
| 1588 | kzikz.btmp | C:\Users\admin\AppData\Roaming\Bitcoin\LinM_Auto\peers.f91c | binary | |
MD5:— | SHA256:— | |||
| 1752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1752.30868\MelonHel.exe | executable | |
MD5:— | SHA256:— | |||
| 2160 | MelonHel.exe | C:\Users\admin\Desktop\kzikz.btmp | executable | |
MD5:— | SHA256:— | |||
| 1588 | kzikz.btmp | C:\Users\admin\AppData\Roaming\Bitcoin\LinM_Auto\peers.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1588 | kzikz.btmp | 183.111.79.66:2055 | — | Korea Telecom | KR | unknown |